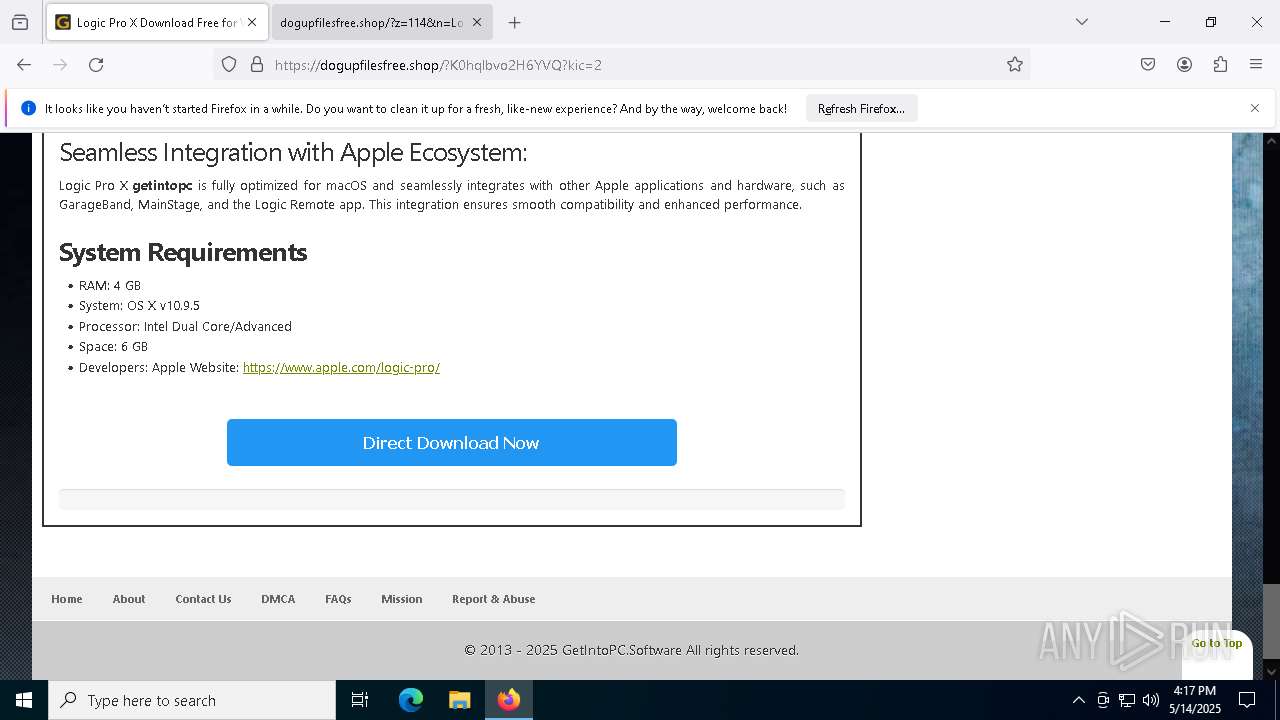
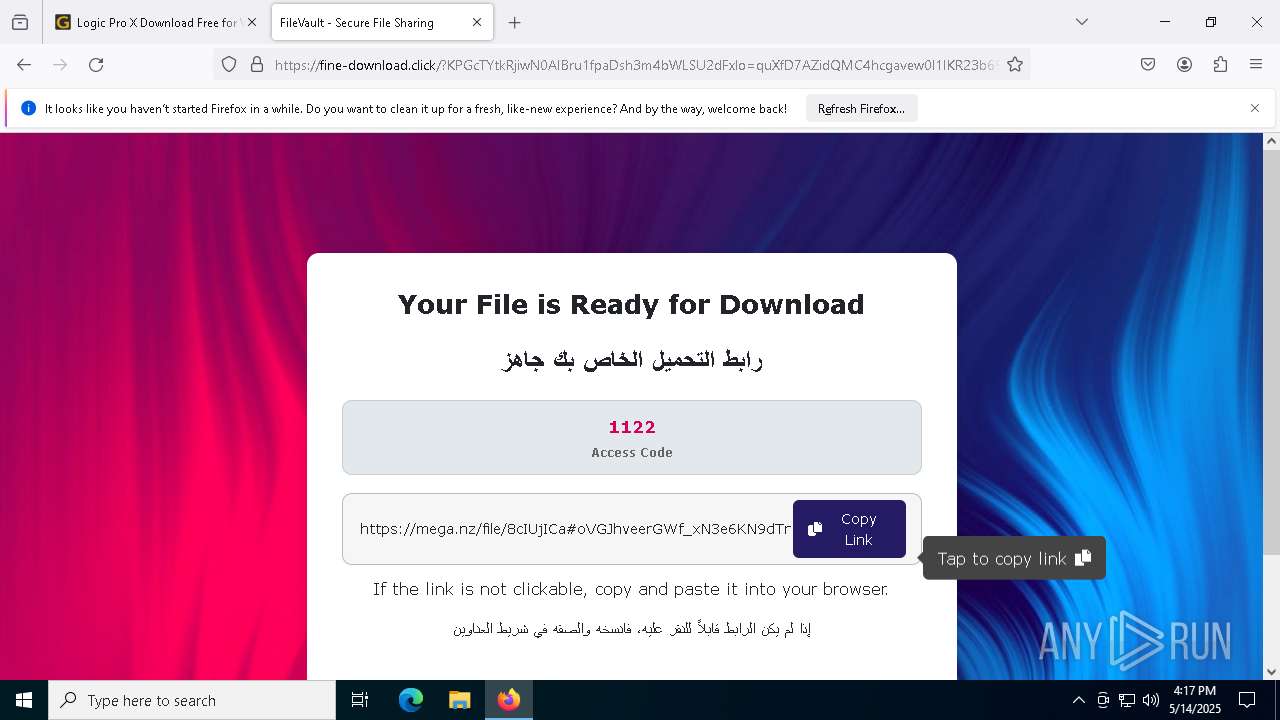
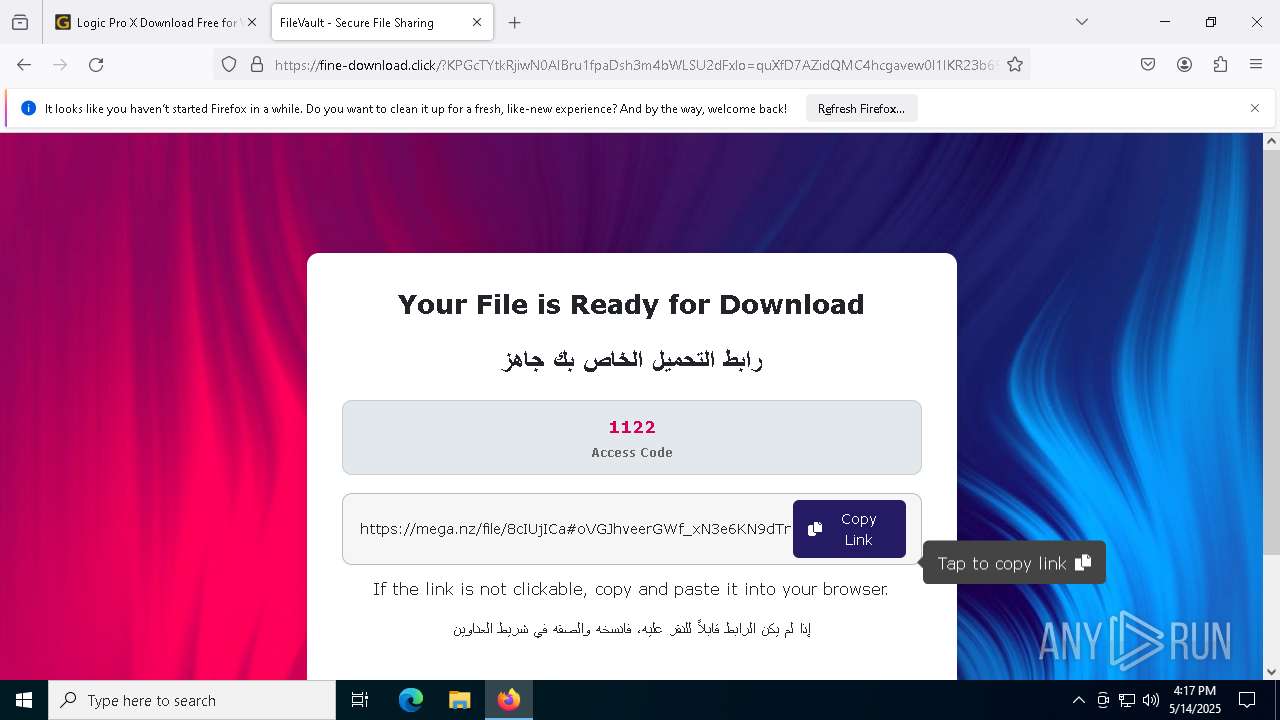
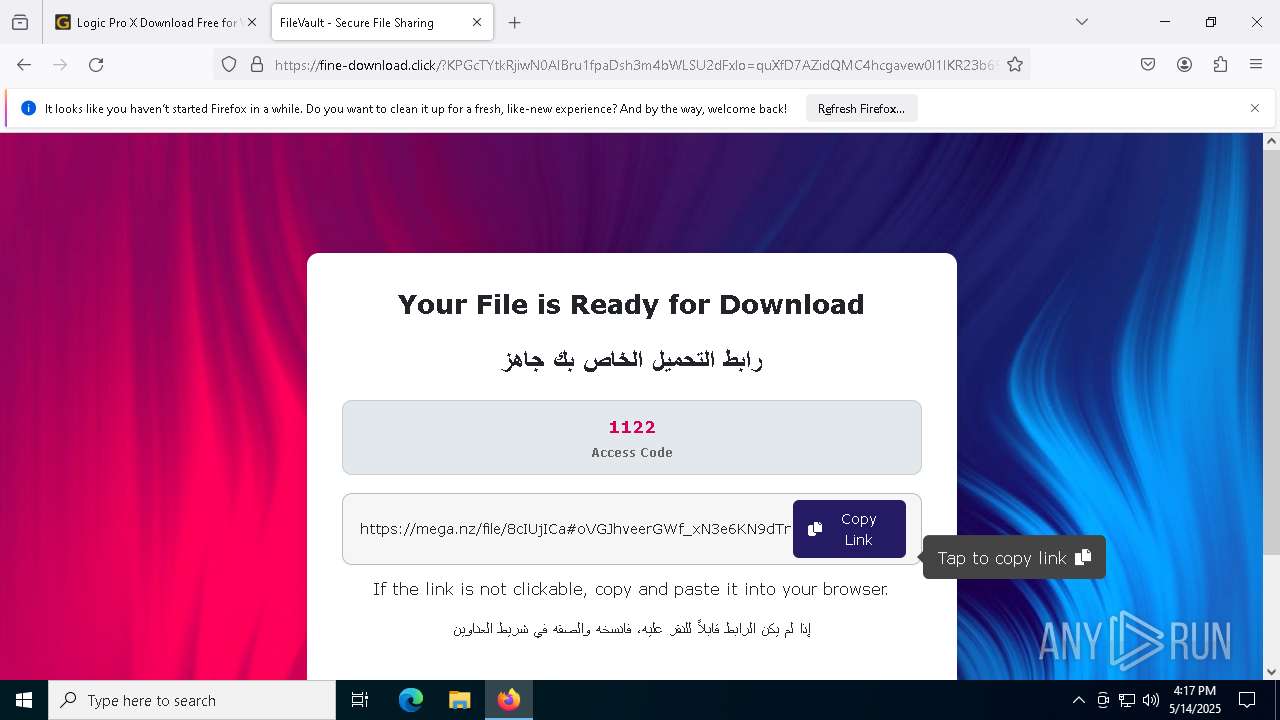
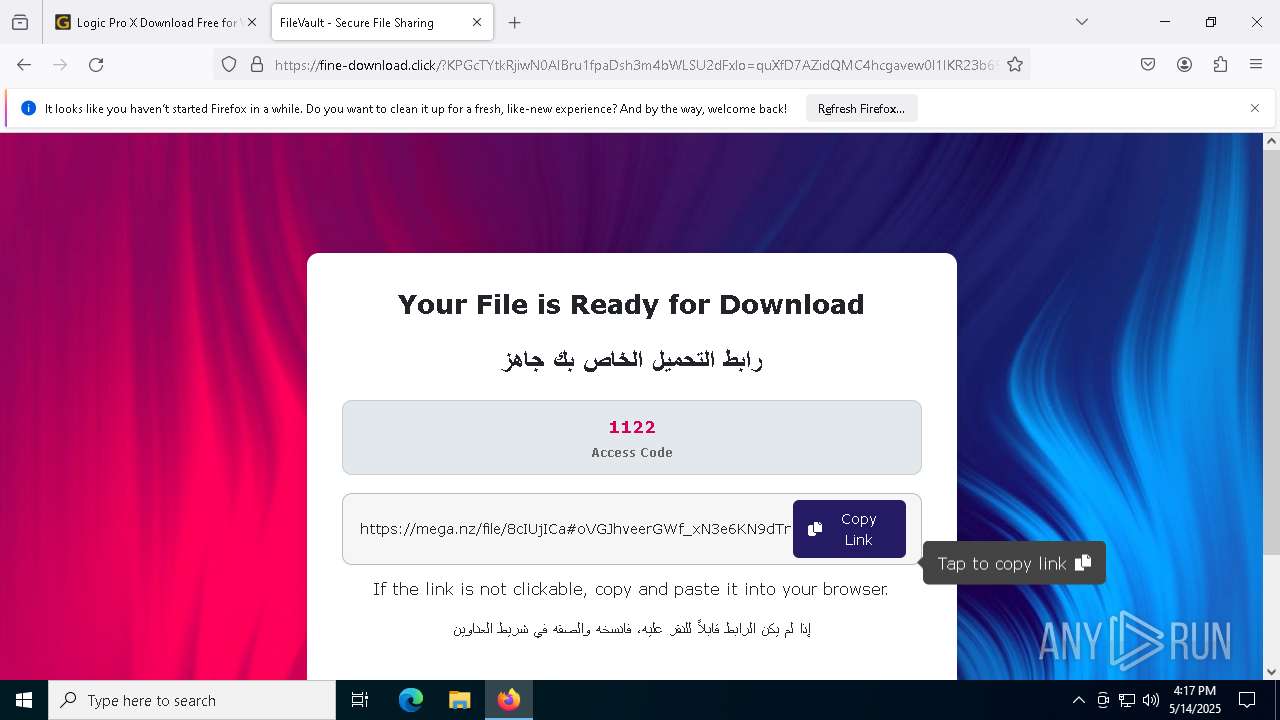
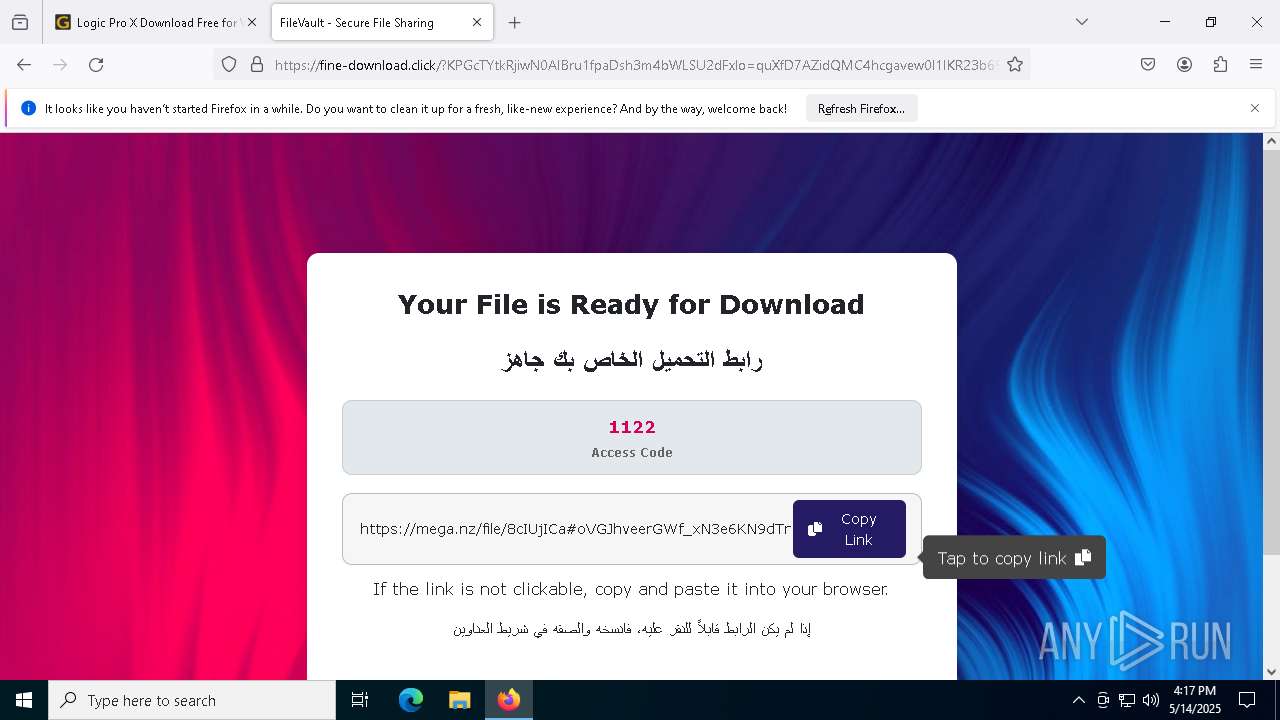
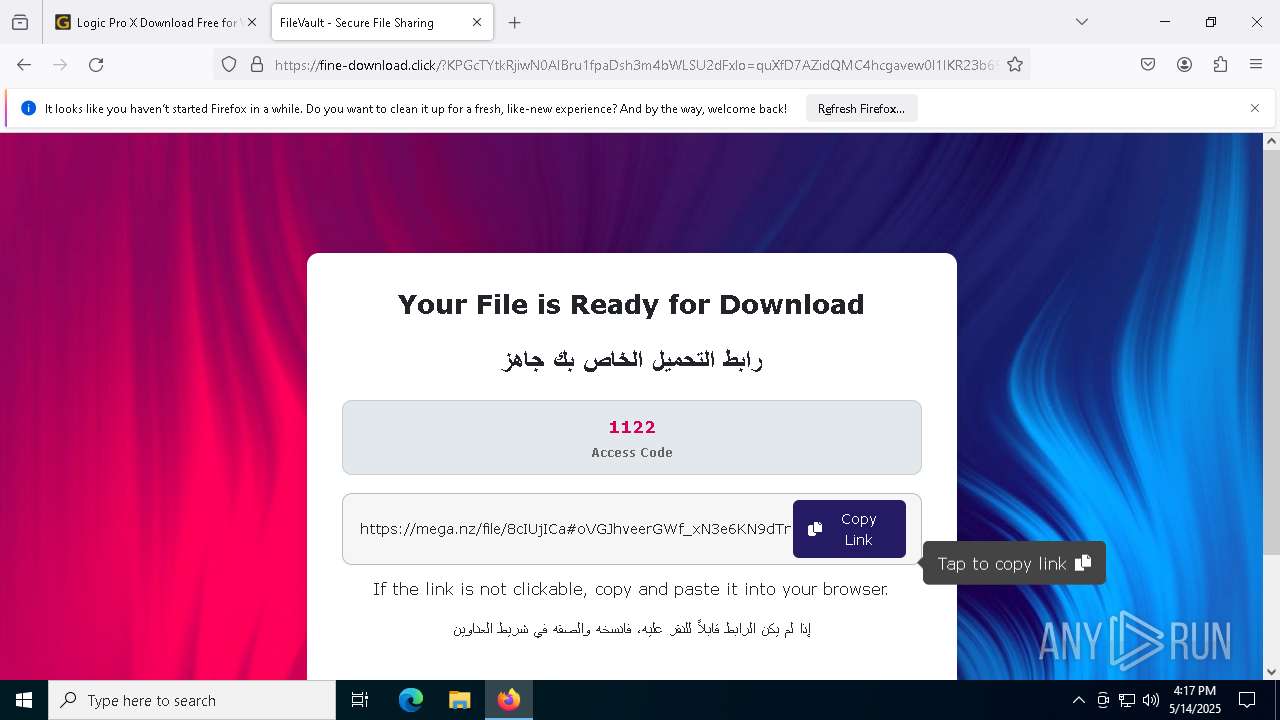
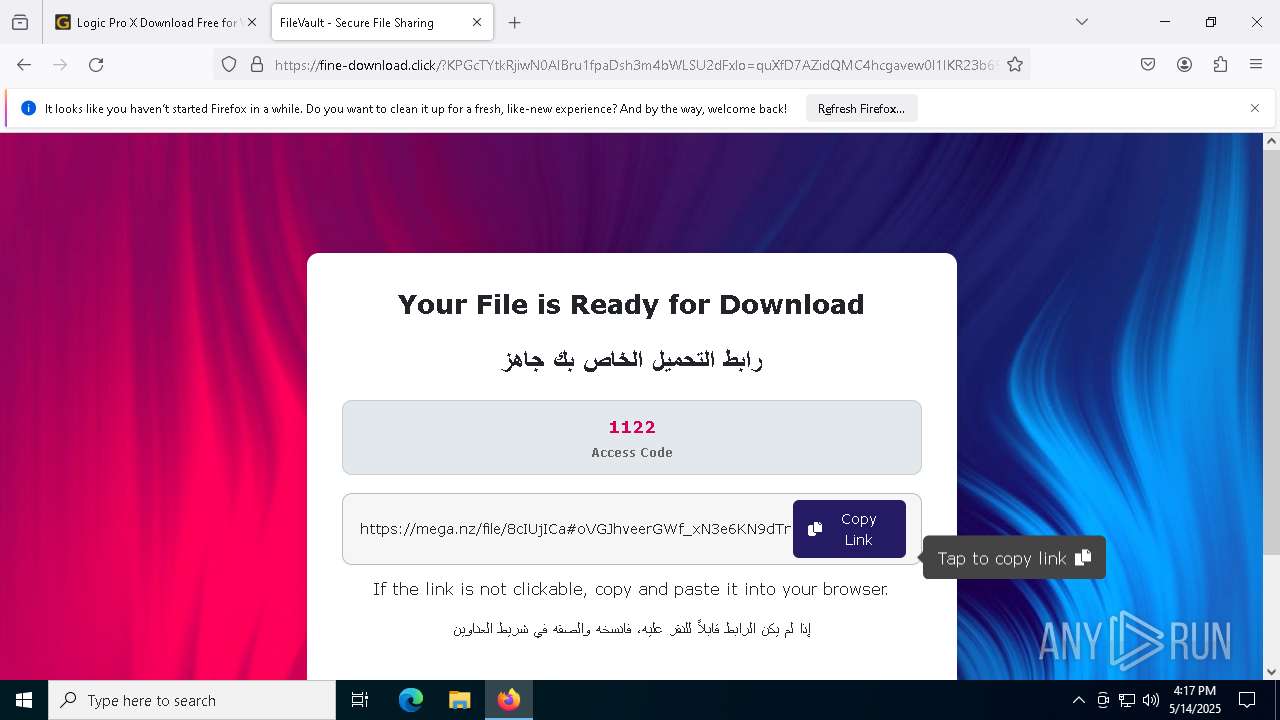
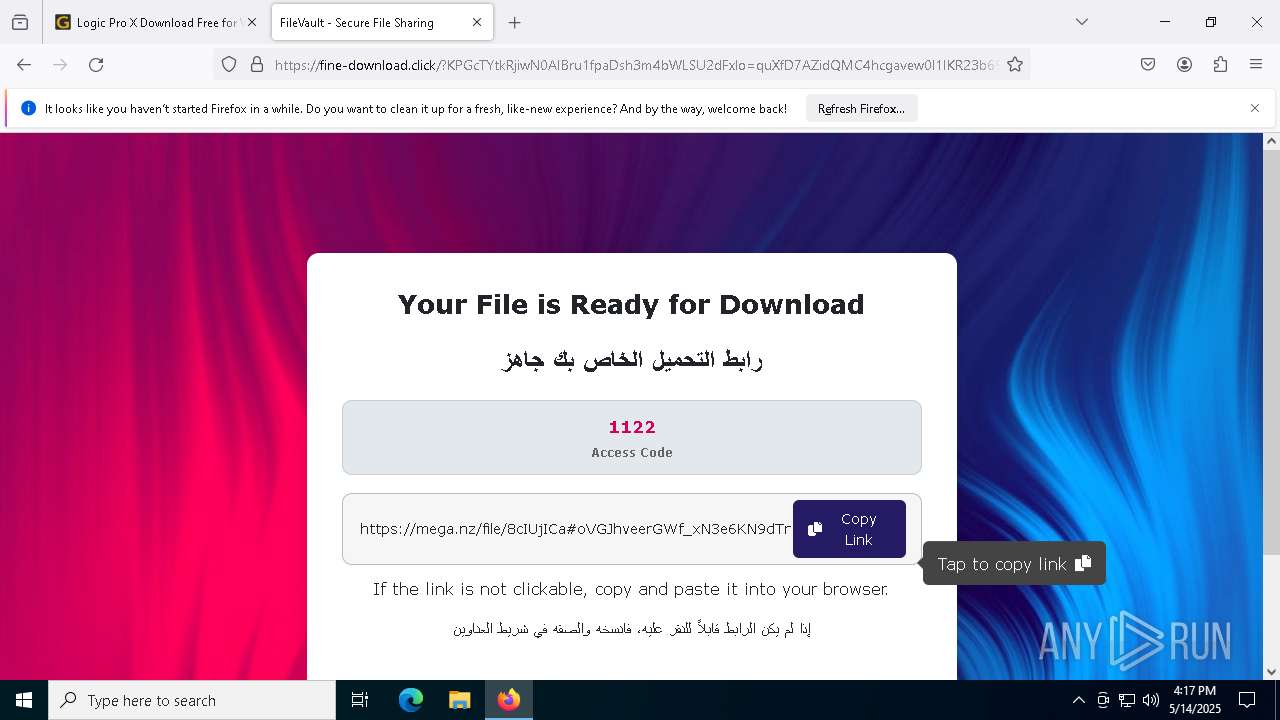
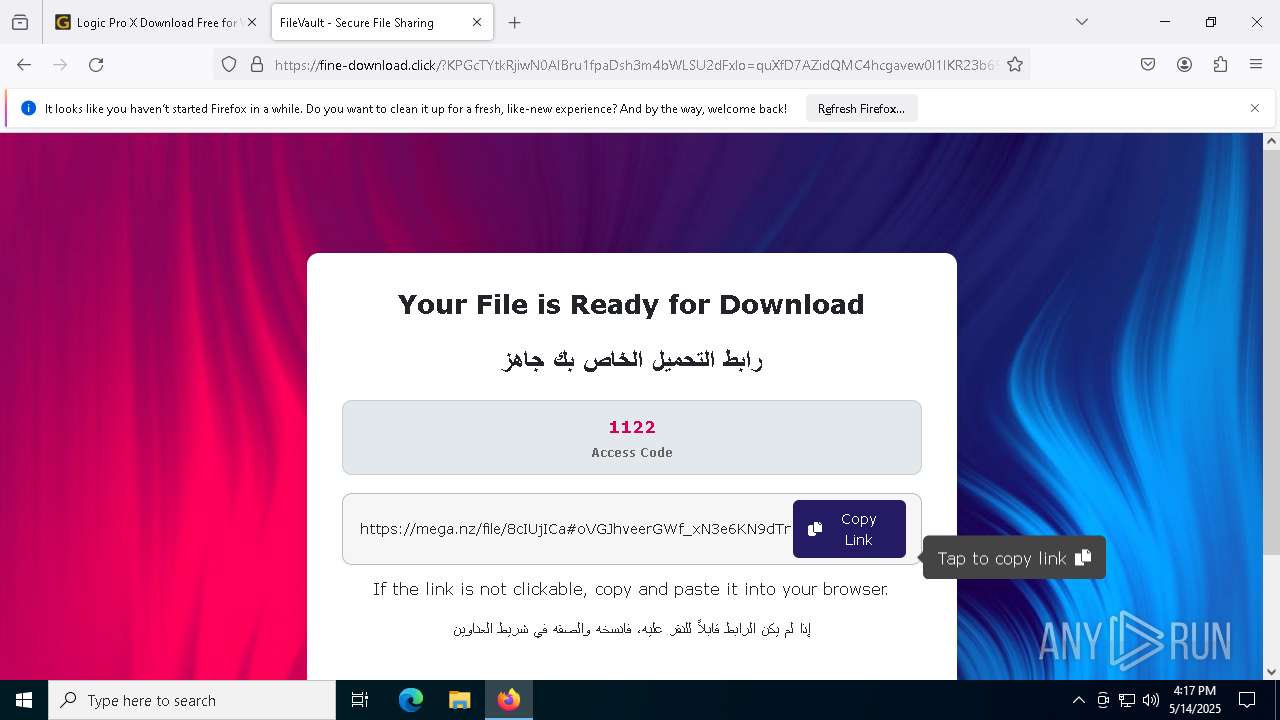
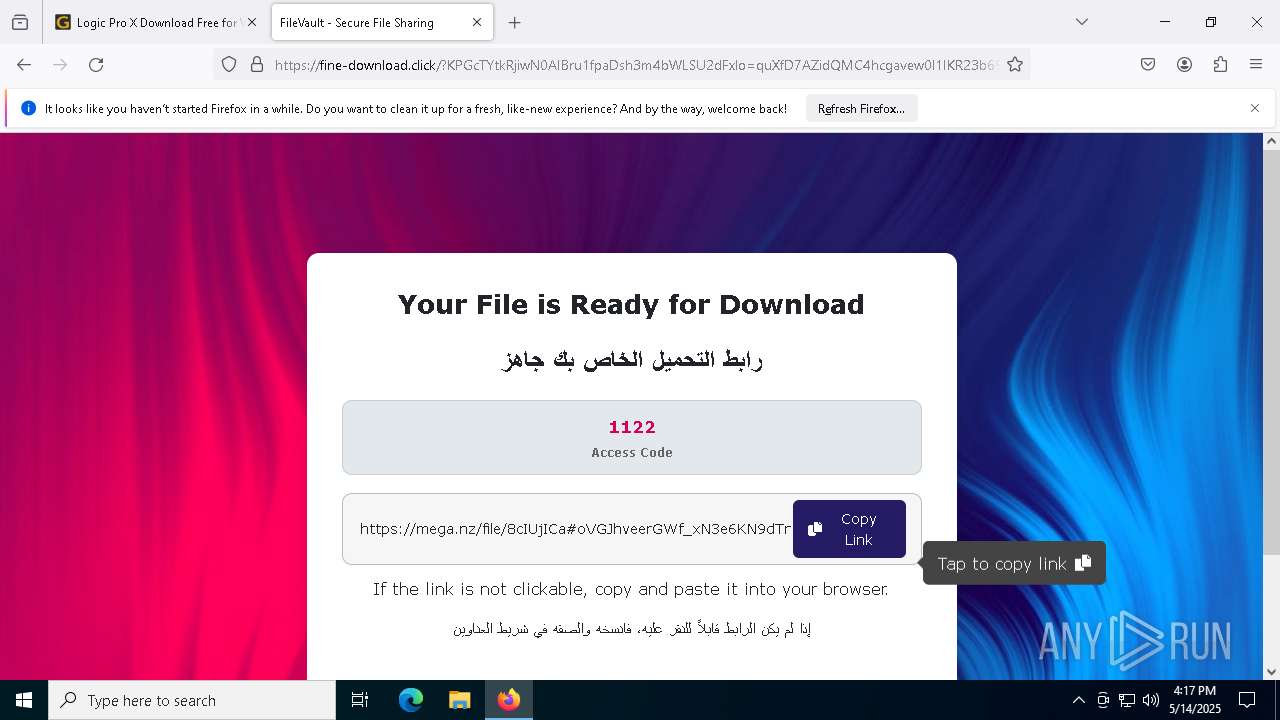
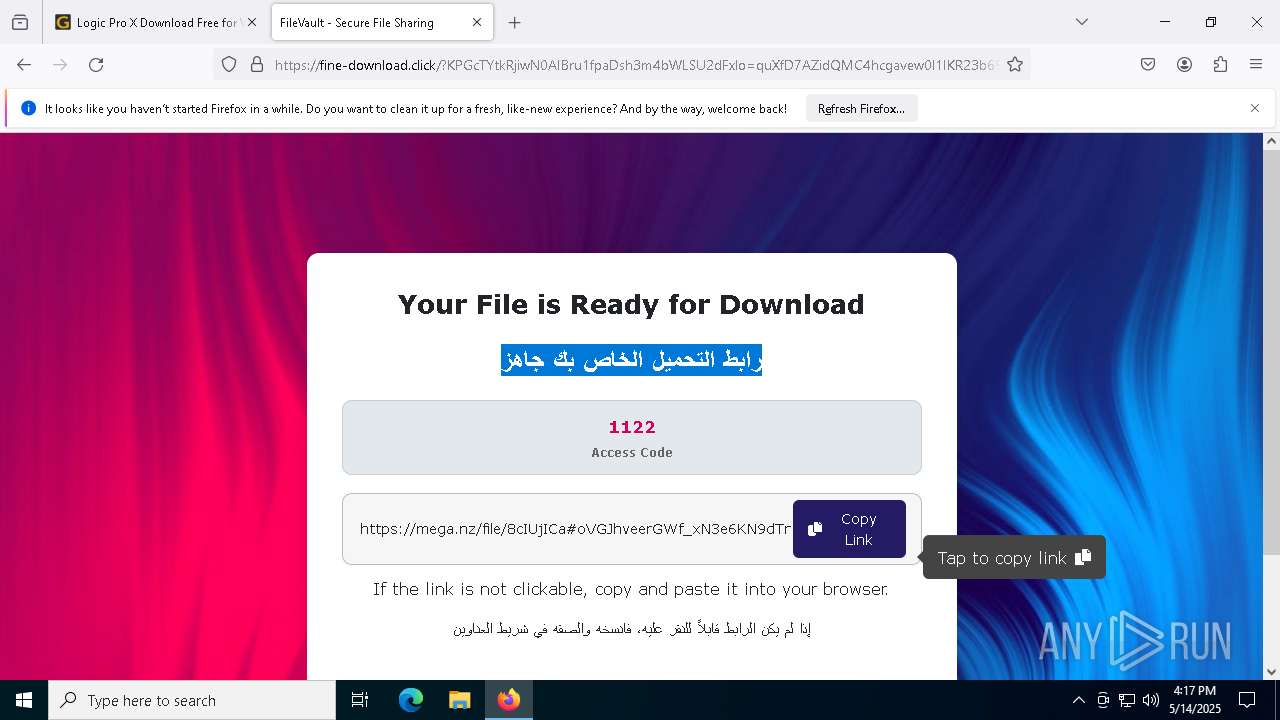
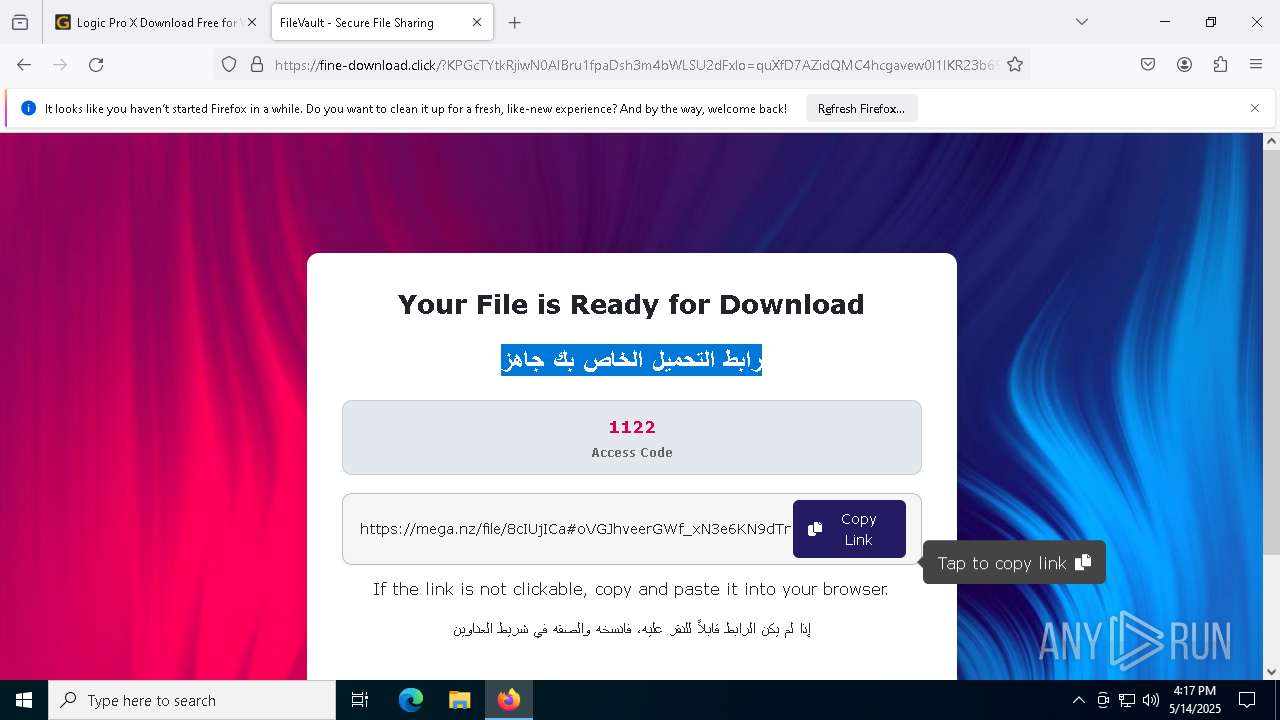
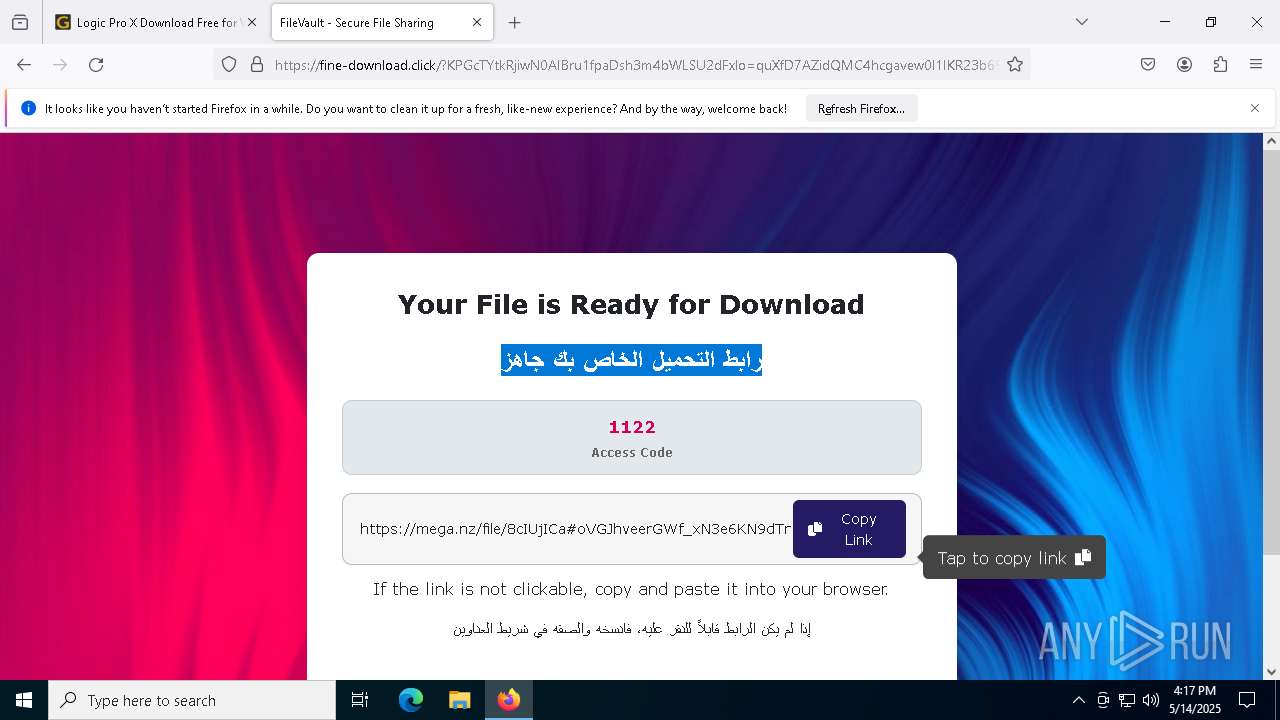
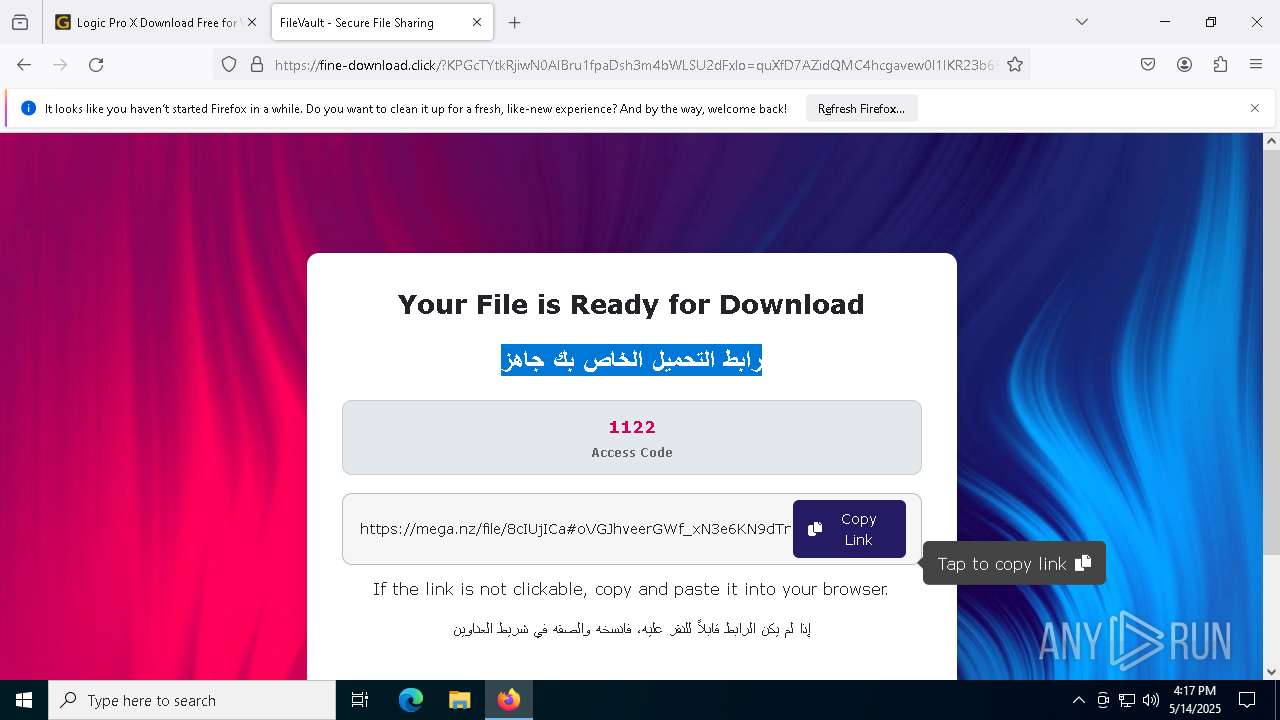
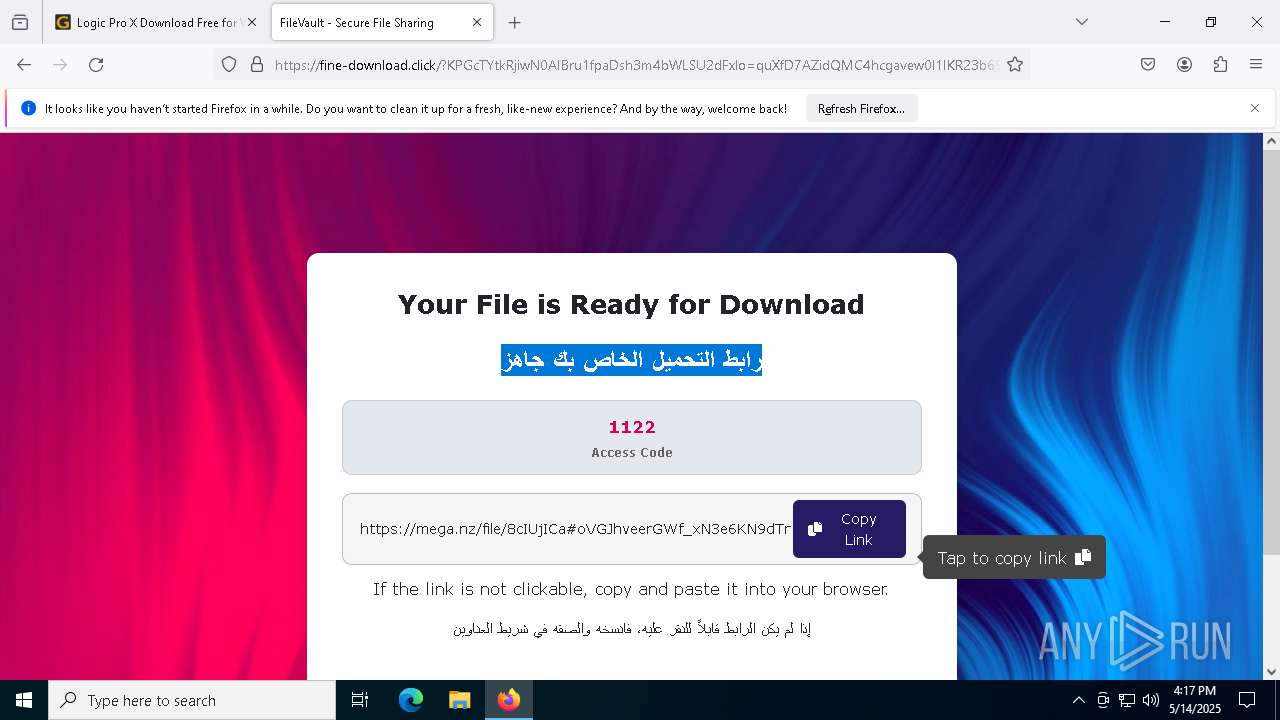
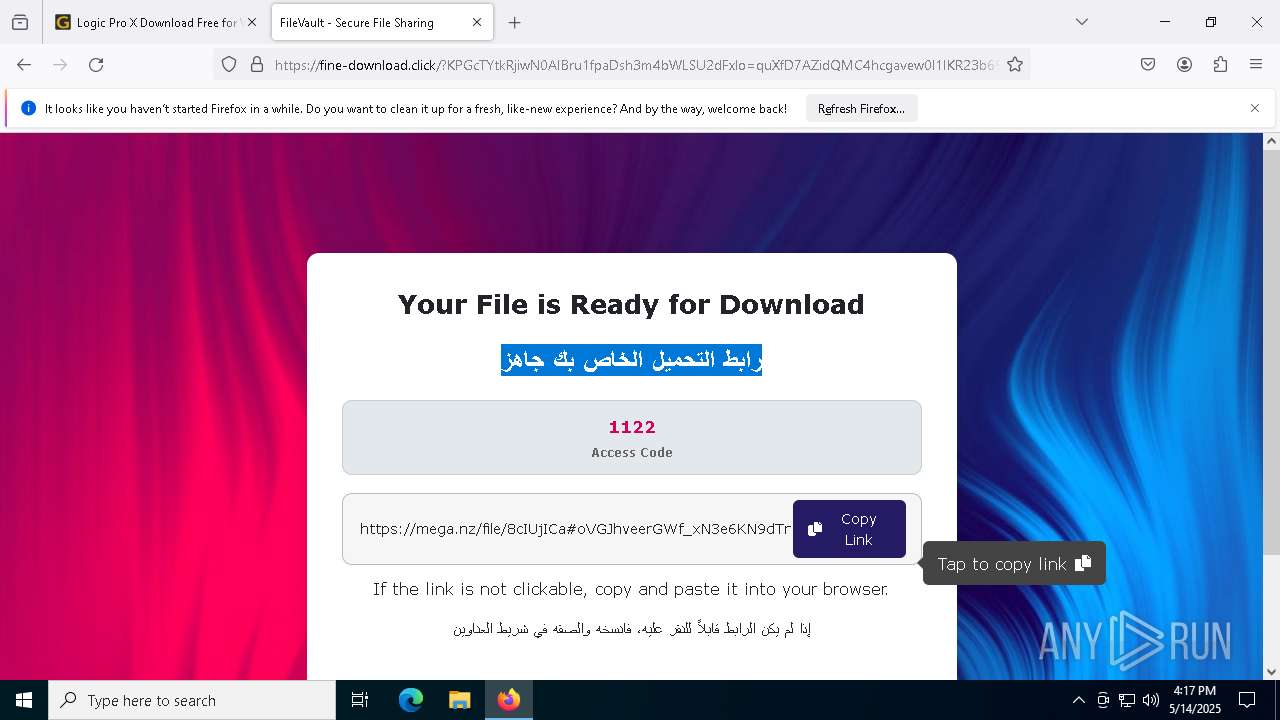
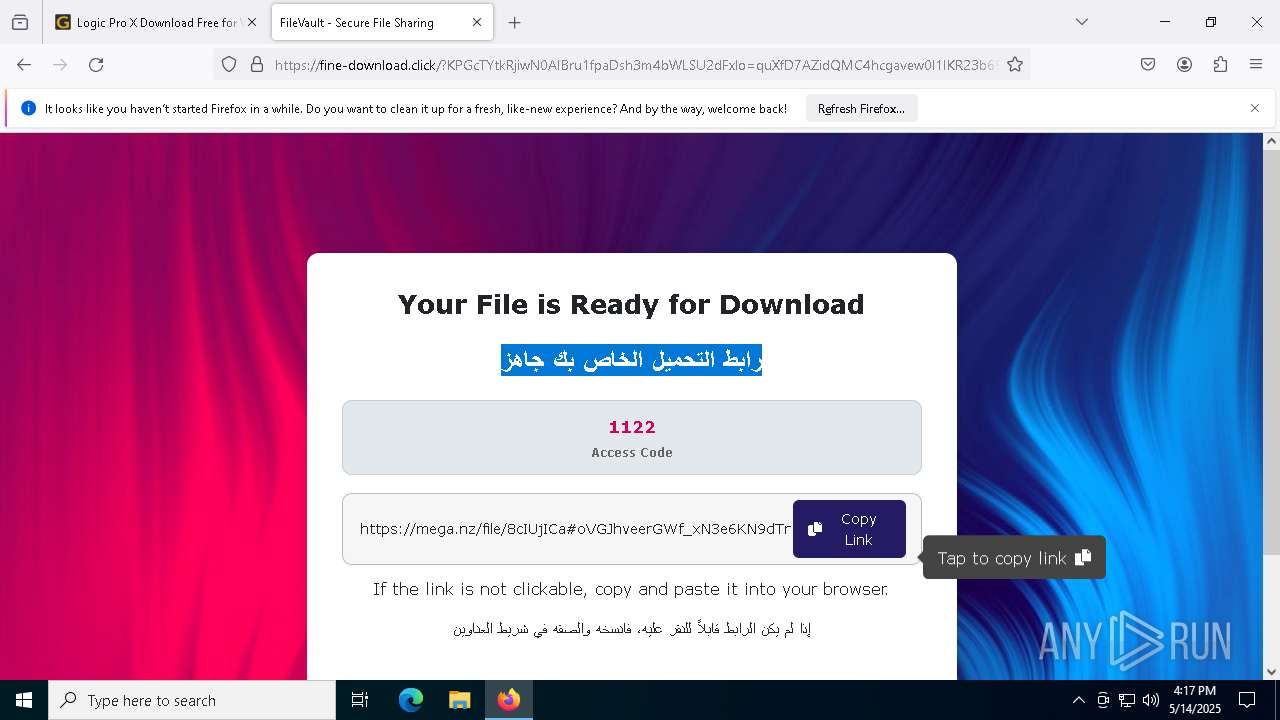
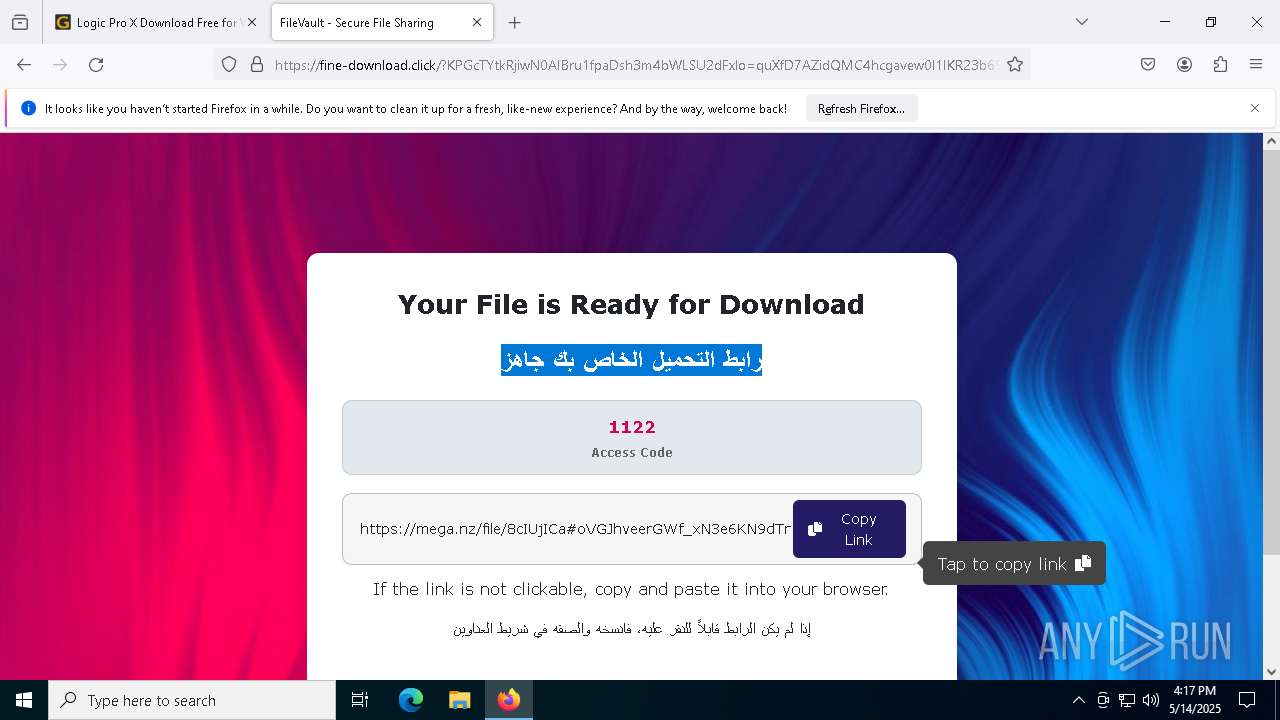
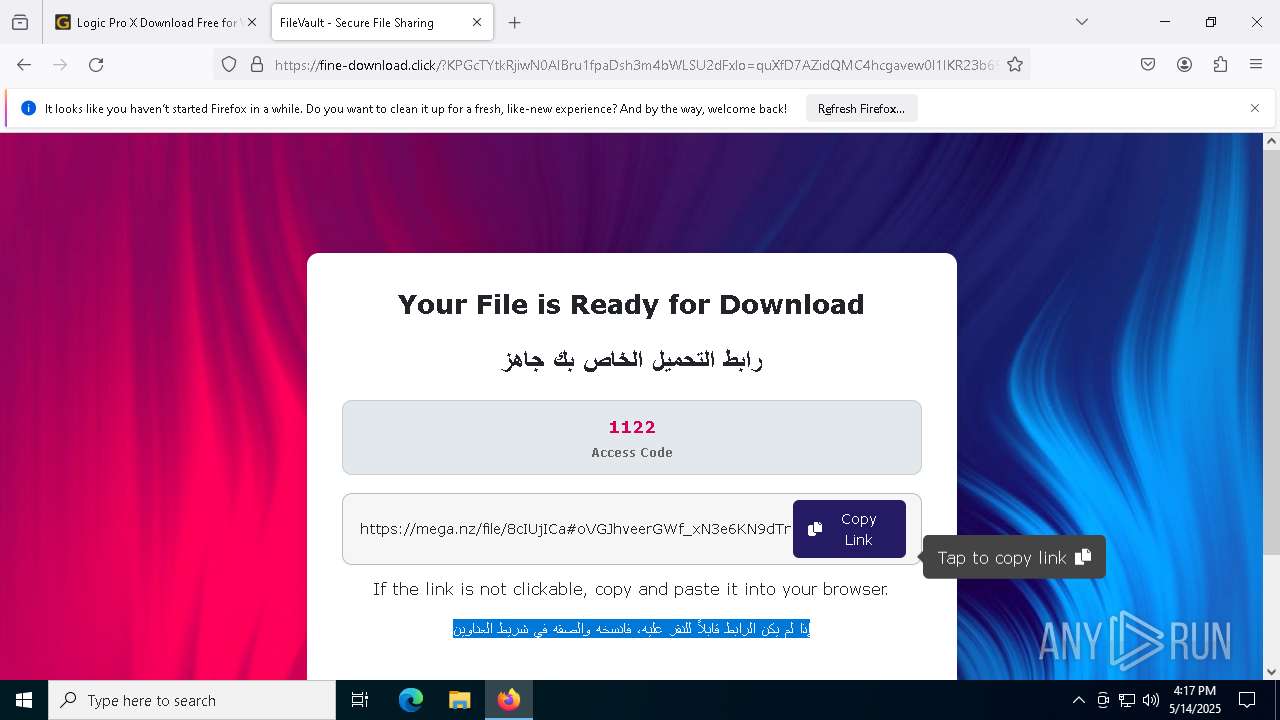
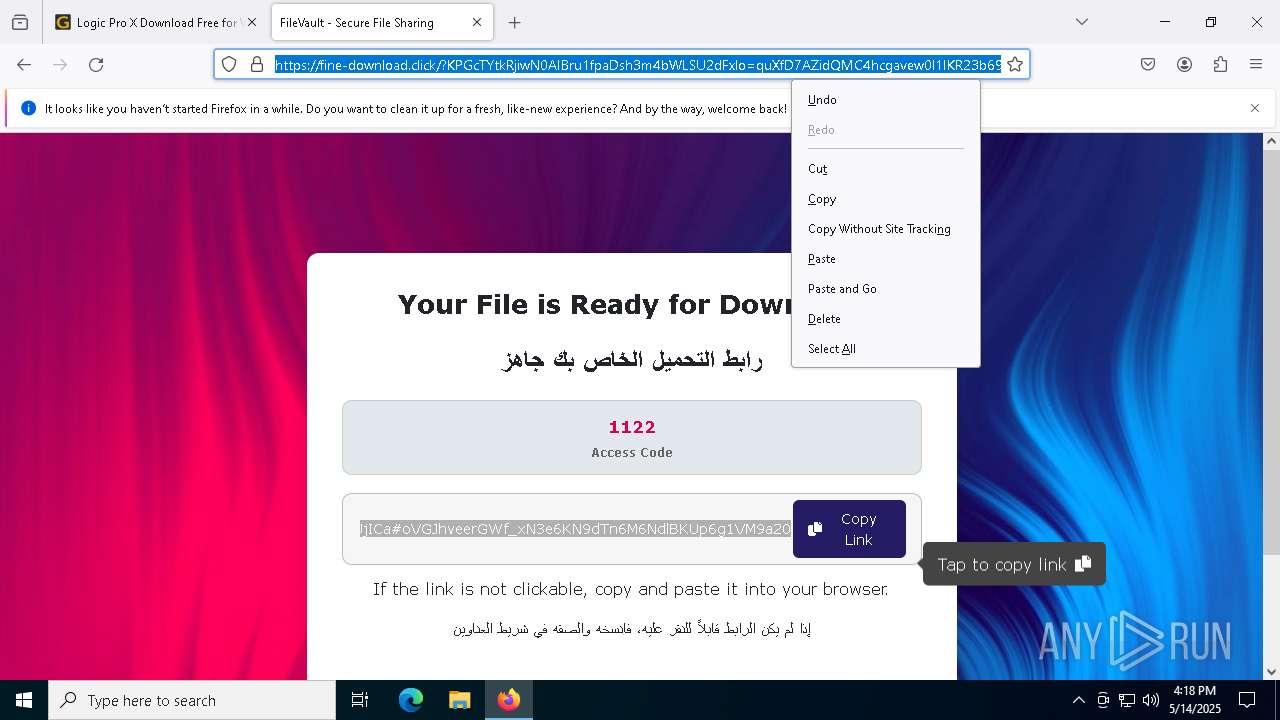
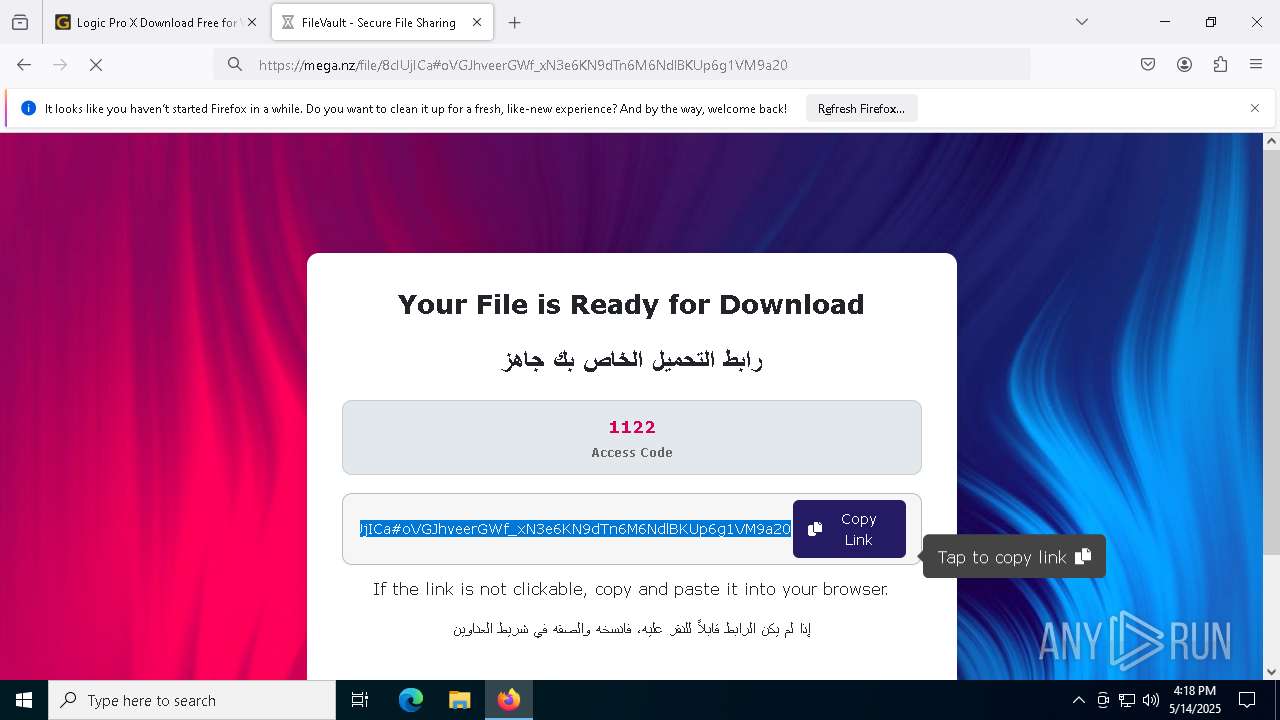
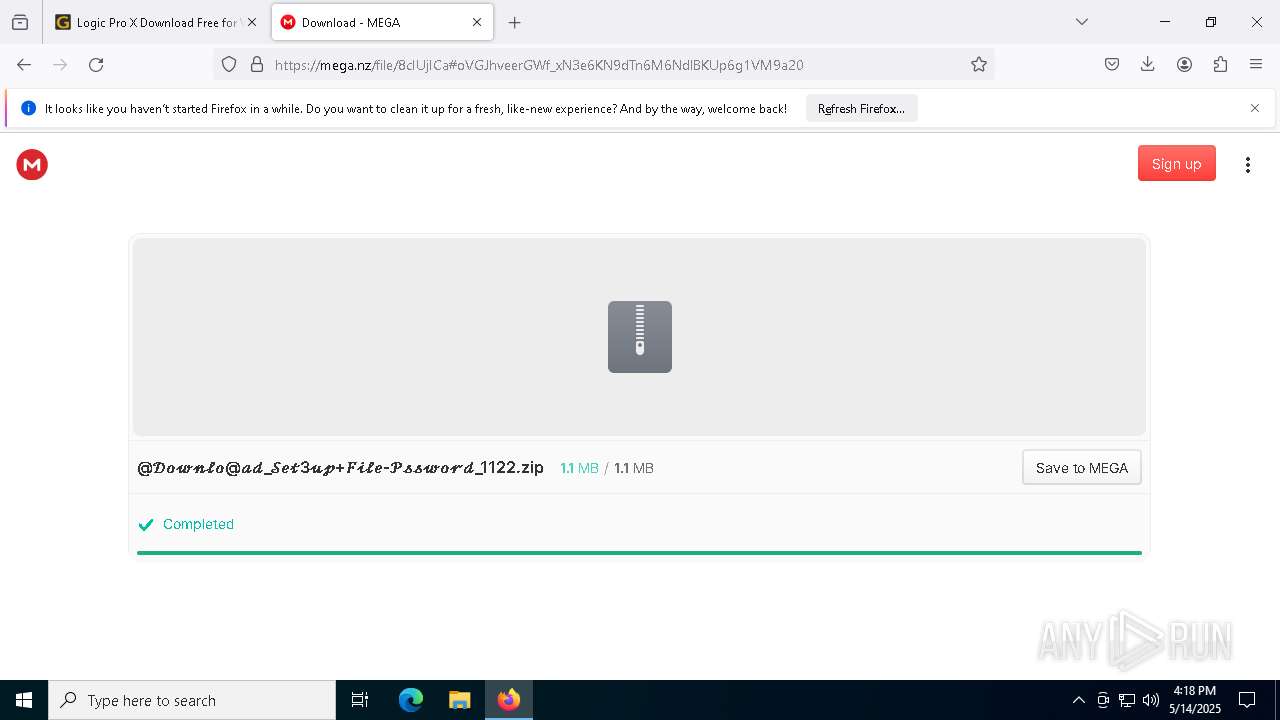
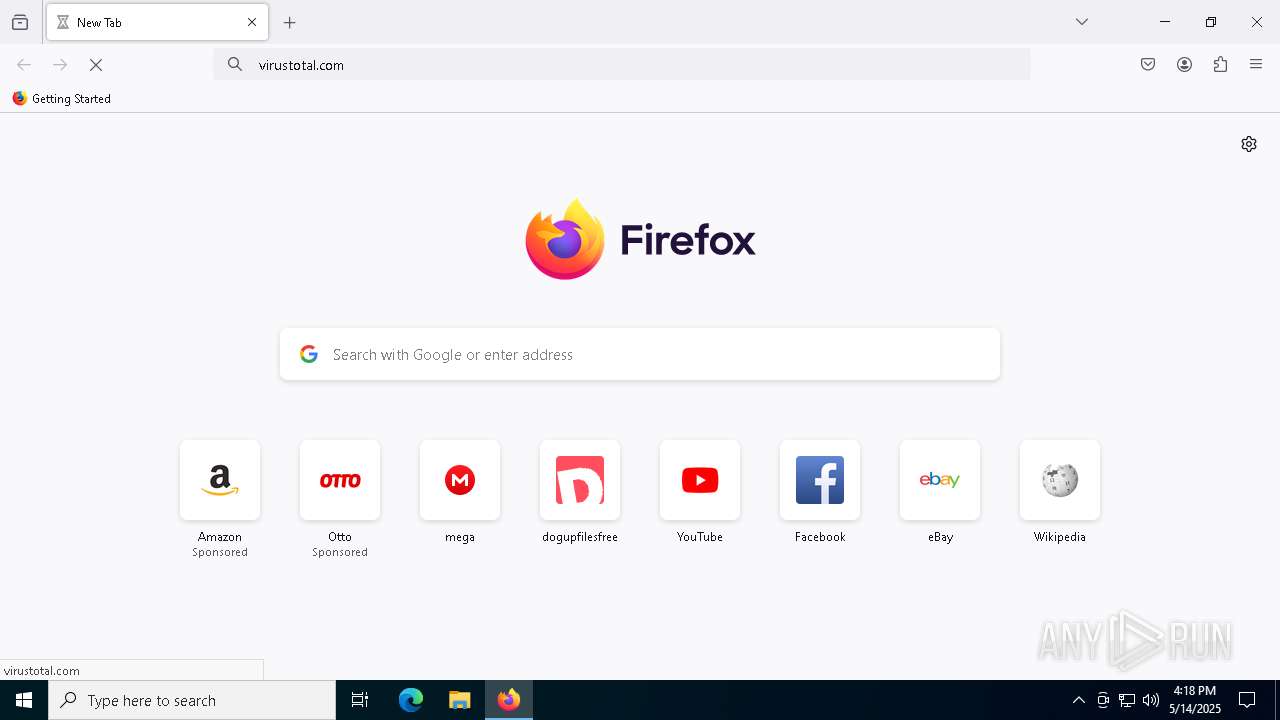
| URL: | https://getintopc.software/ |
| Full analysis: | https://app.any.run/tasks/4ca20031-6778-4b70-b9c6-49036c97a44b |
| Verdict: | Malicious activity |
| Analysis date: | May 14, 2025, 16:16:57 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
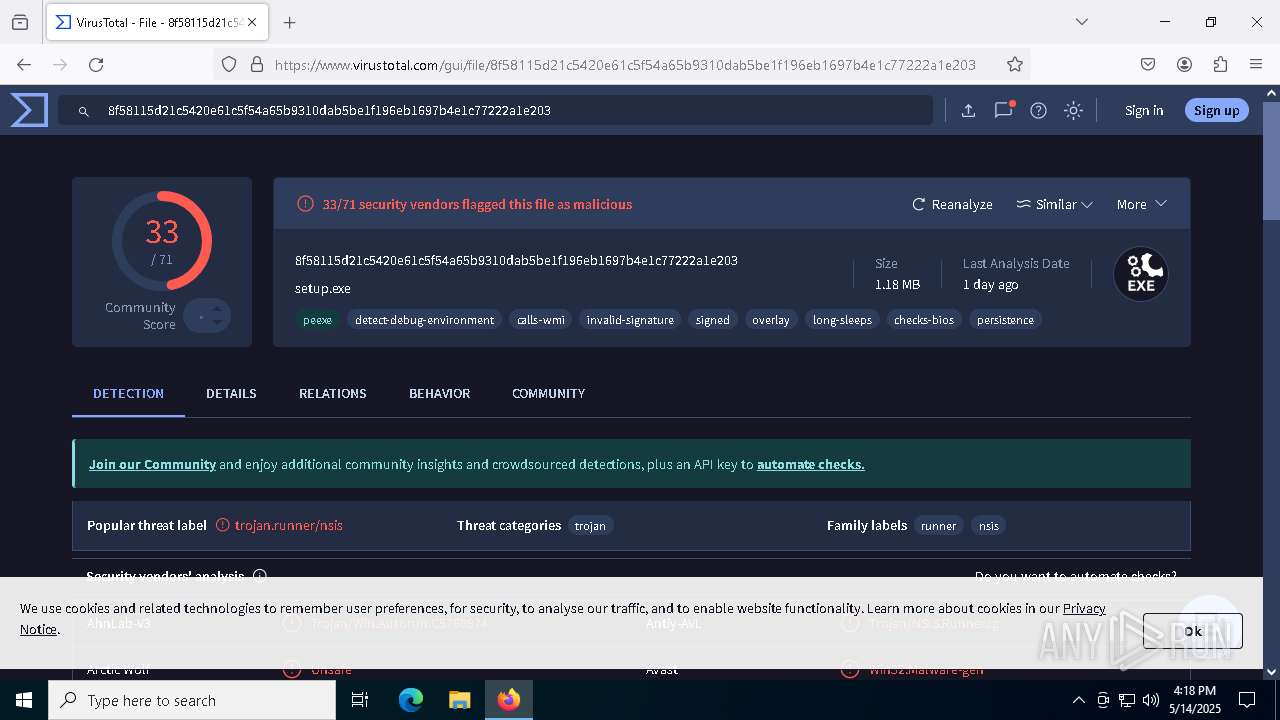
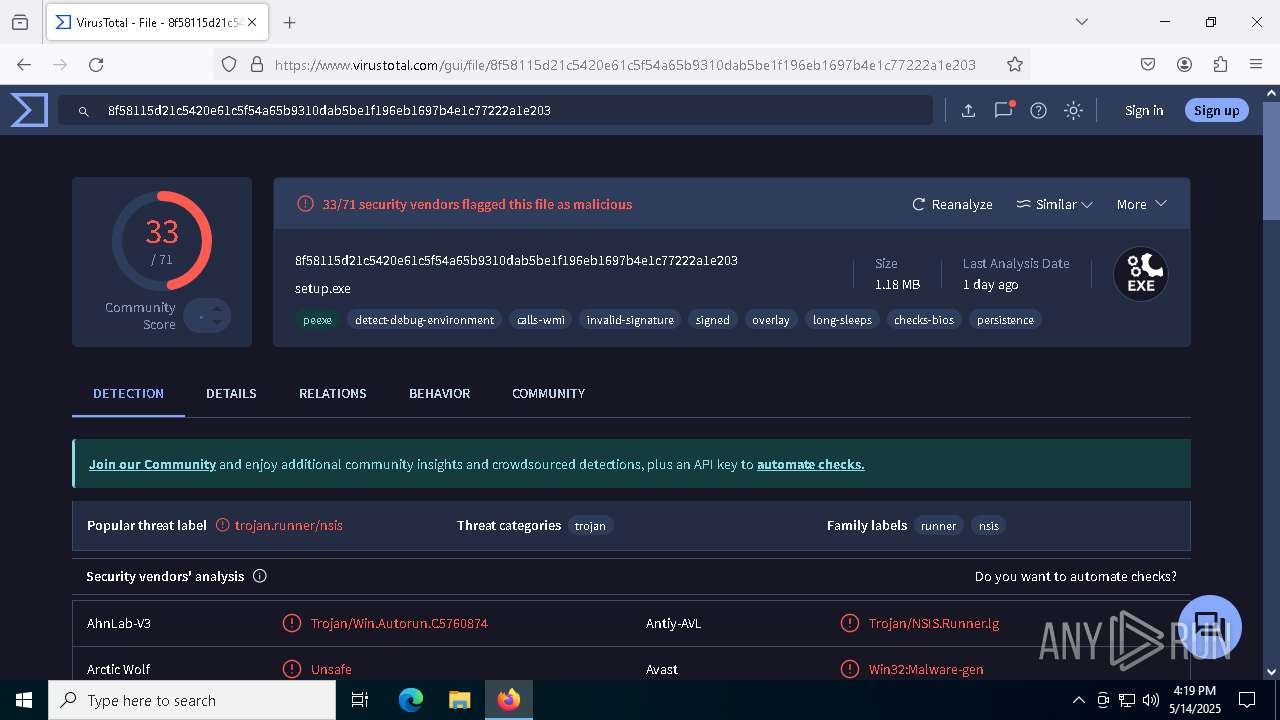
| MD5: | BDED6BA2BE095C845162672095FC473F |
| SHA1: | C4ED6177CCED9481E55B1862C6C88B879CE069C6 |
| SHA256: | 1E53AE62BDEA675AA2AA9C2A63A435B61D8EF4AB2DA65FAD1DD63B01C98FB891 |
| SSDEEP: | 3:N8hILNAEf:2sf |
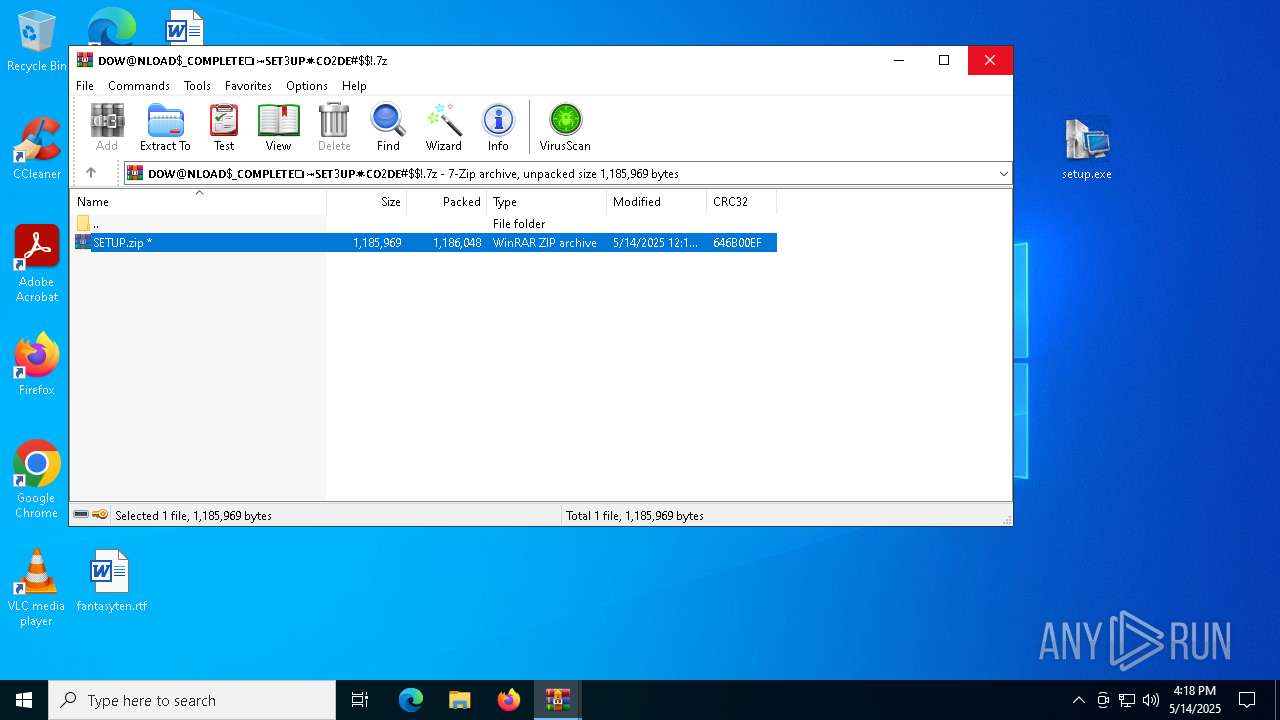
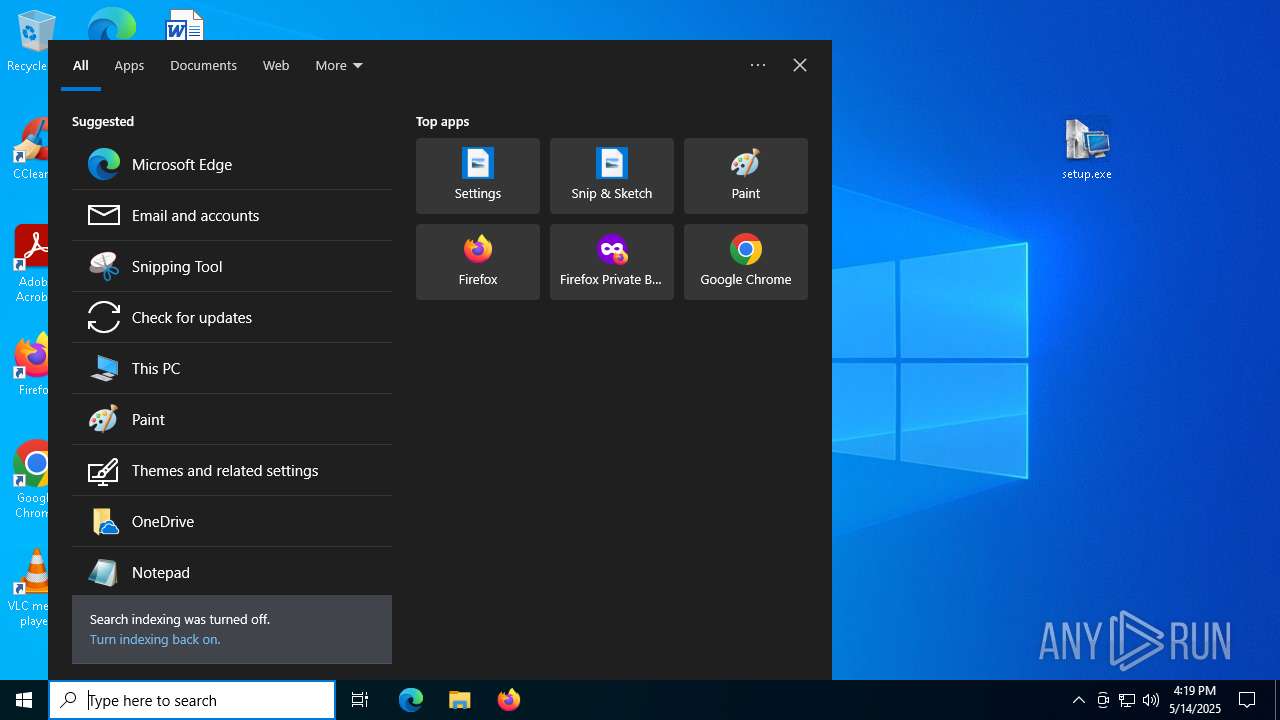
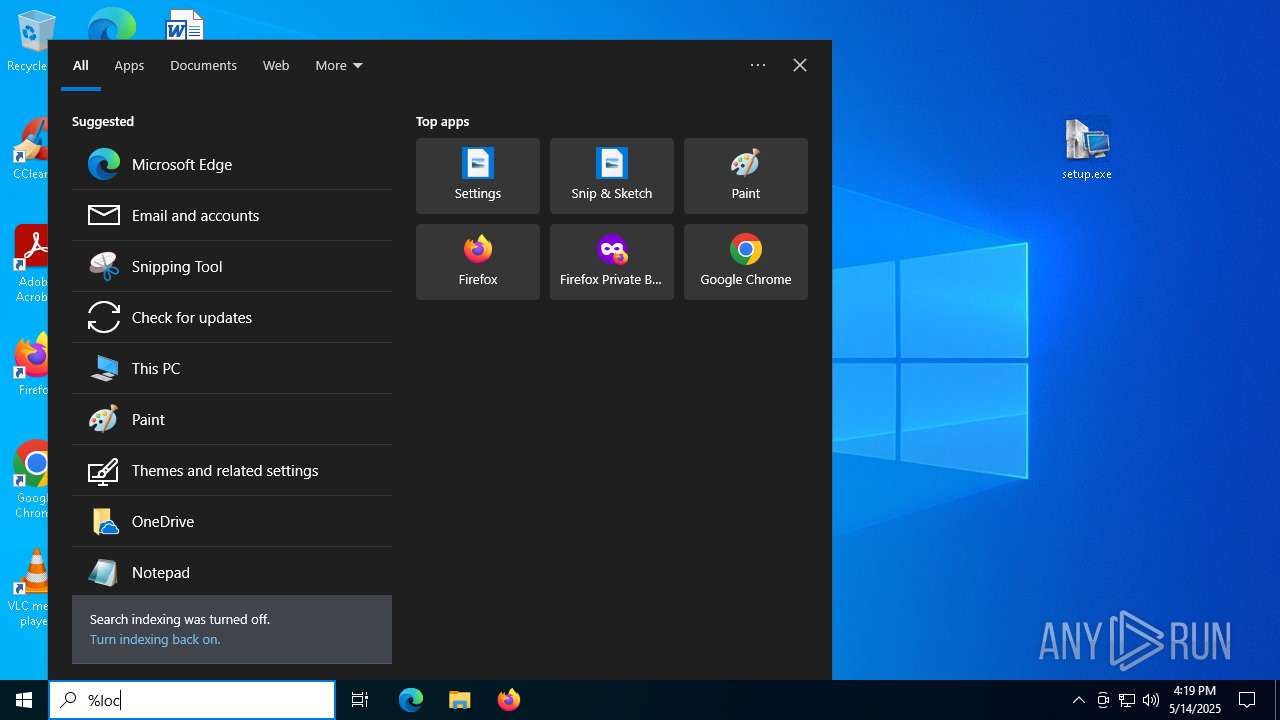
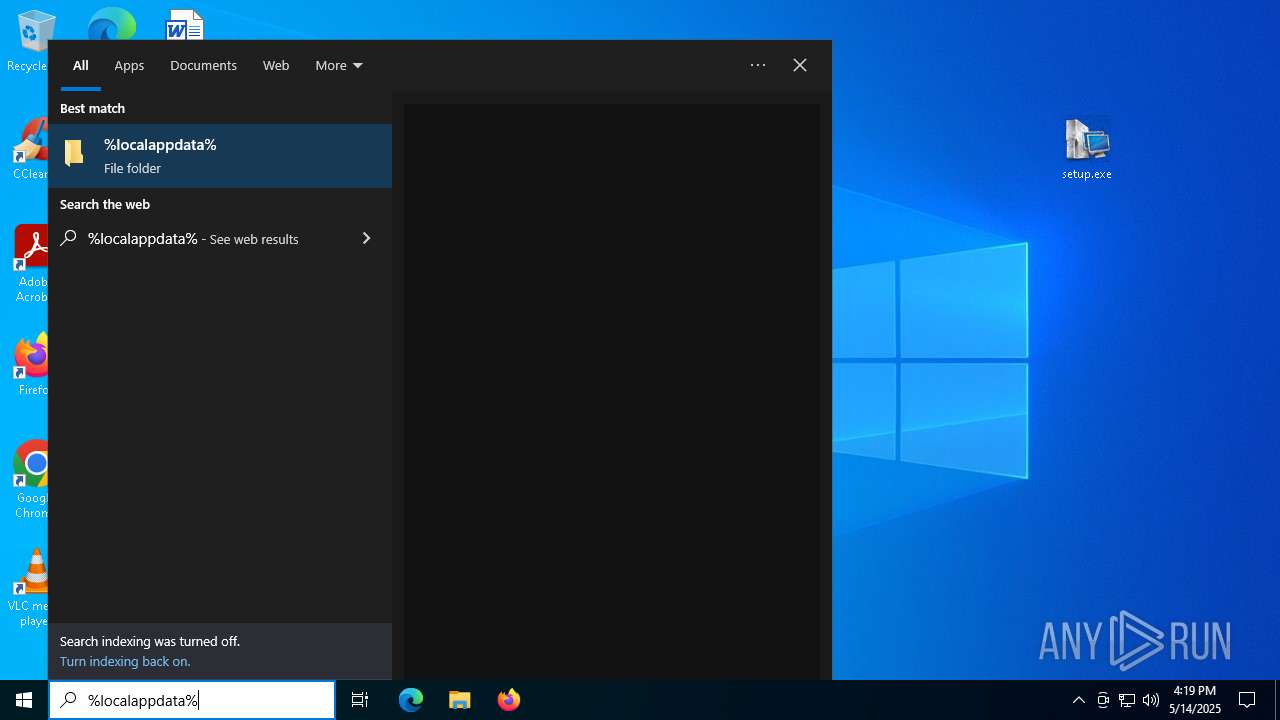
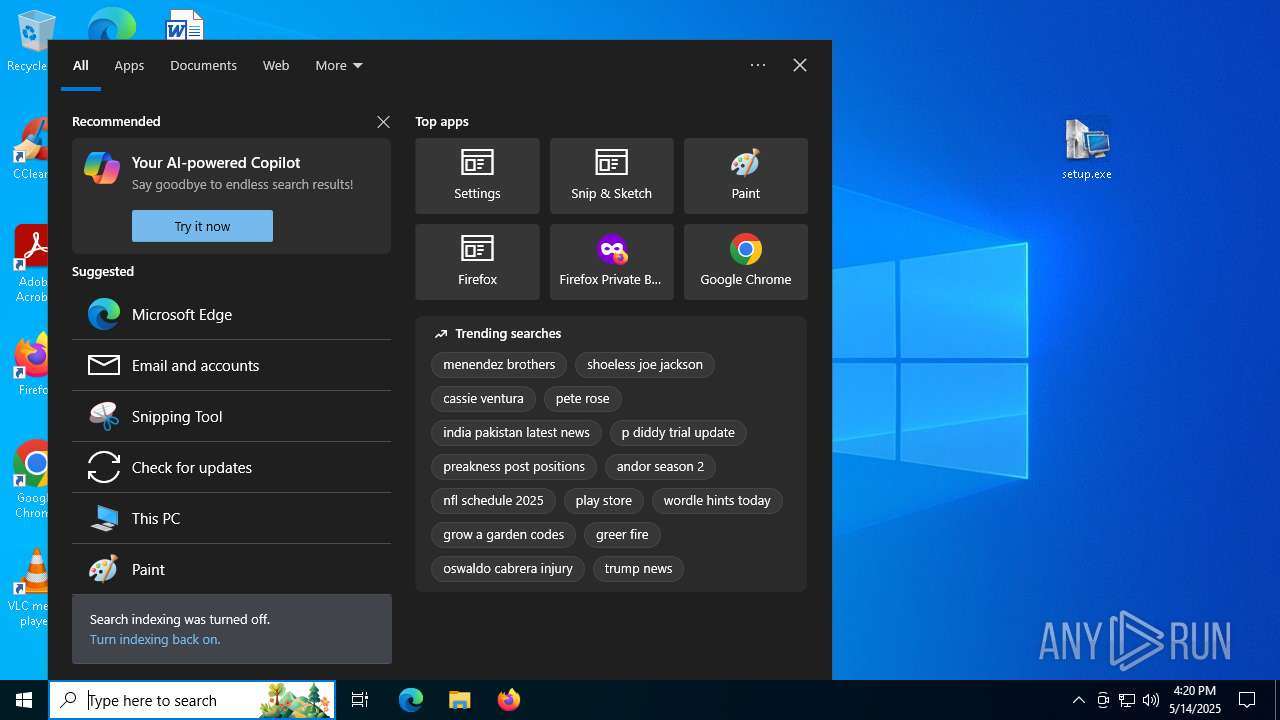
MALICIOUS
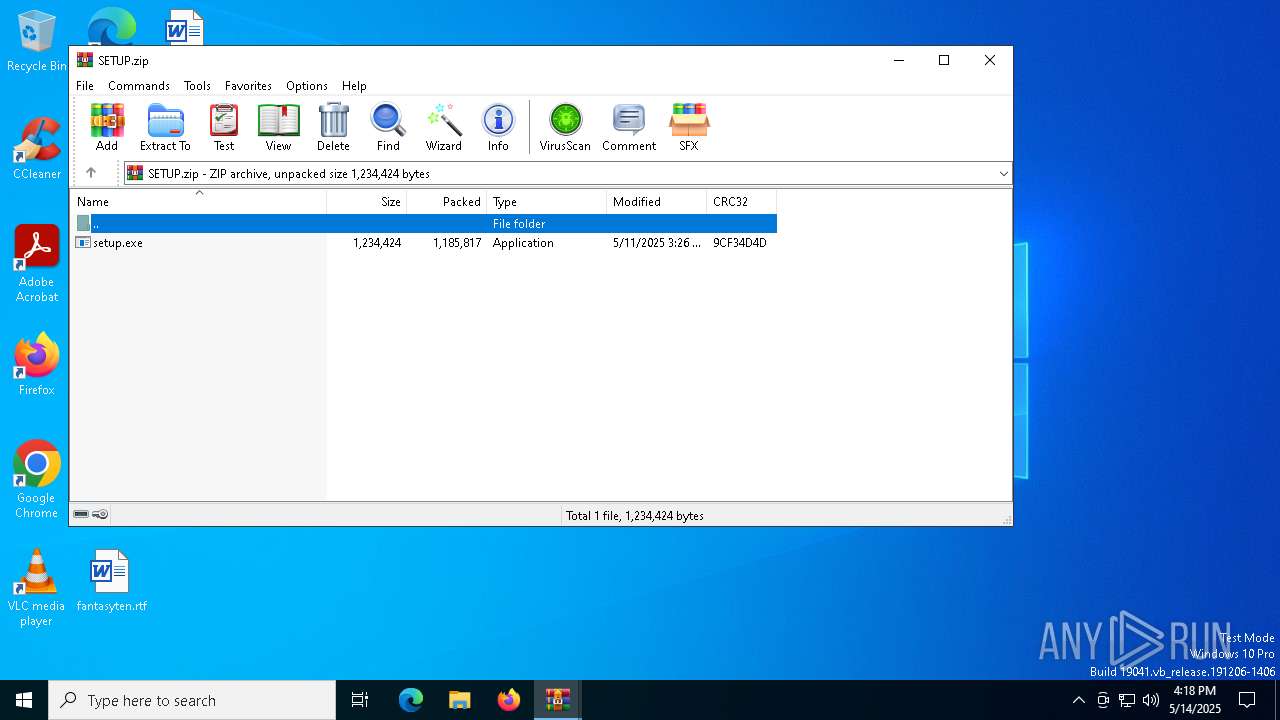
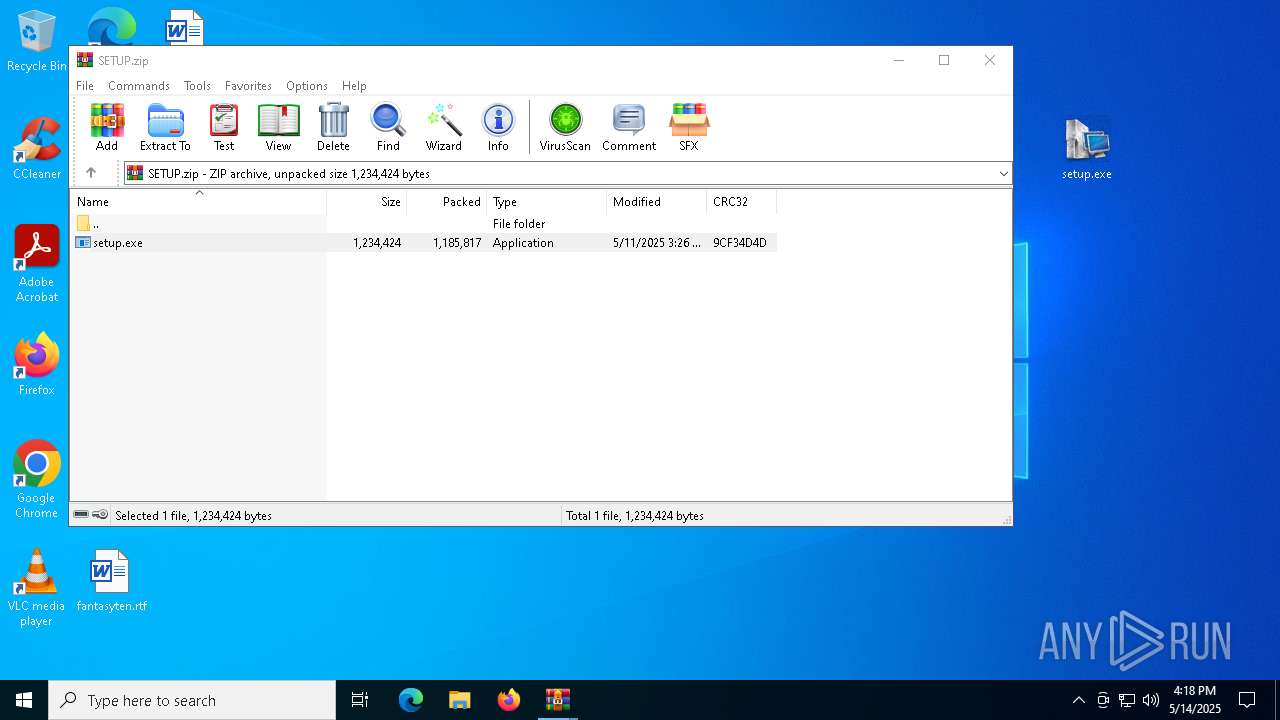
Executing a file with an untrusted certificate
- setup.exe (PID: 5624)
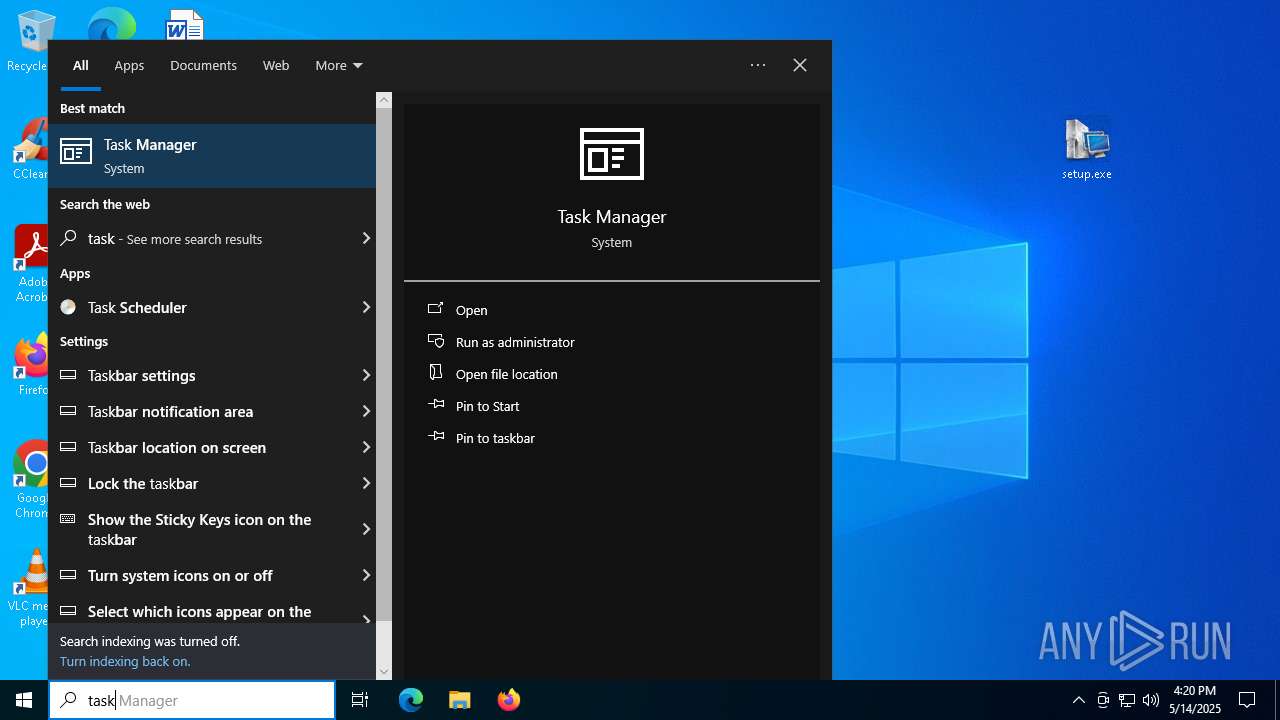
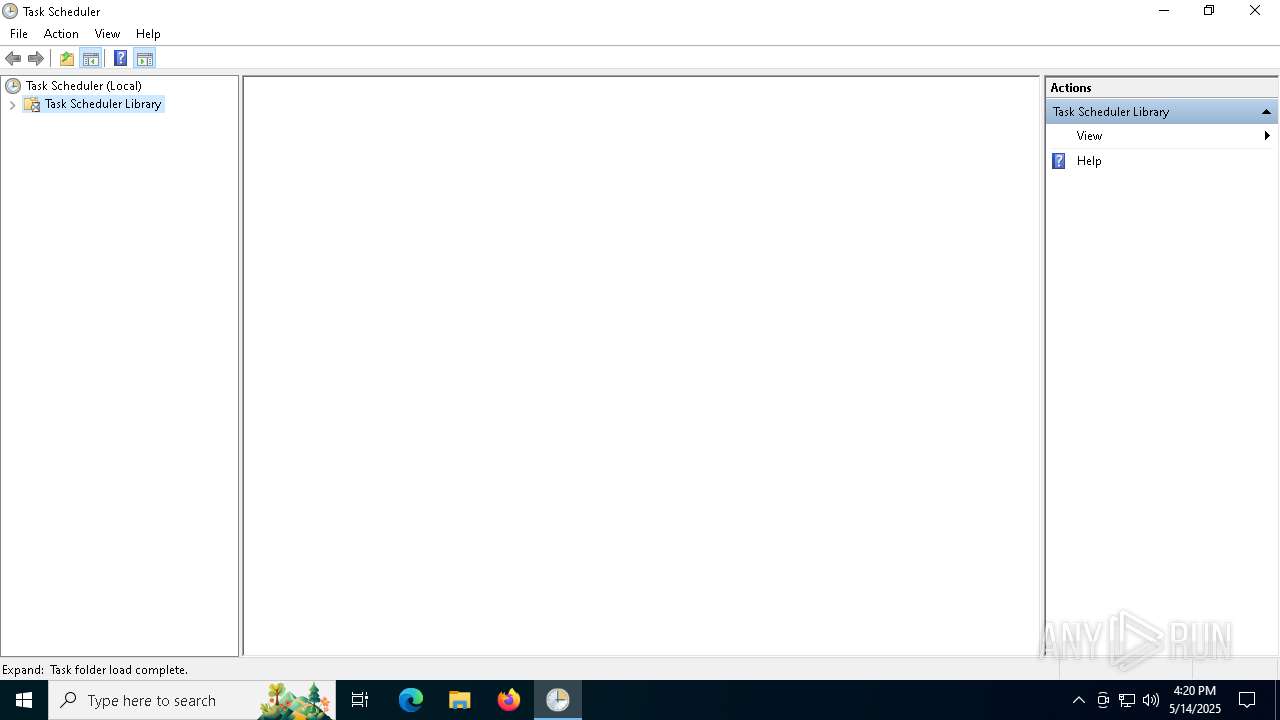
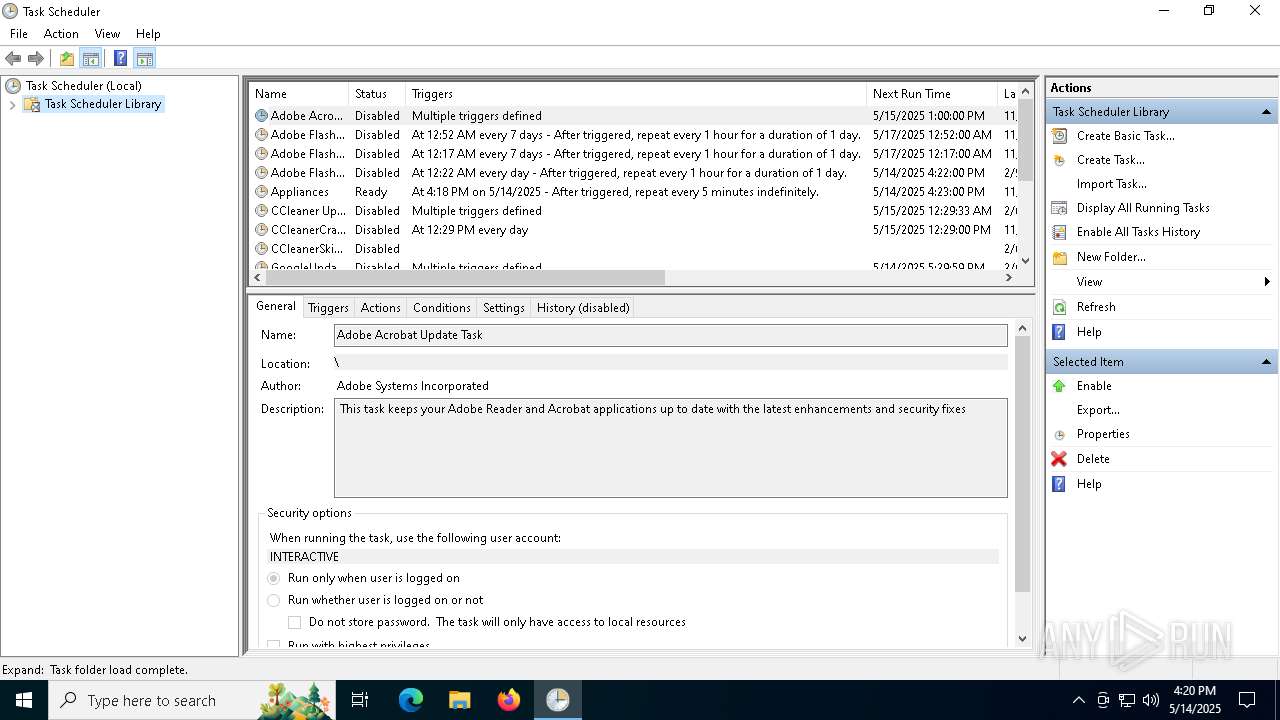
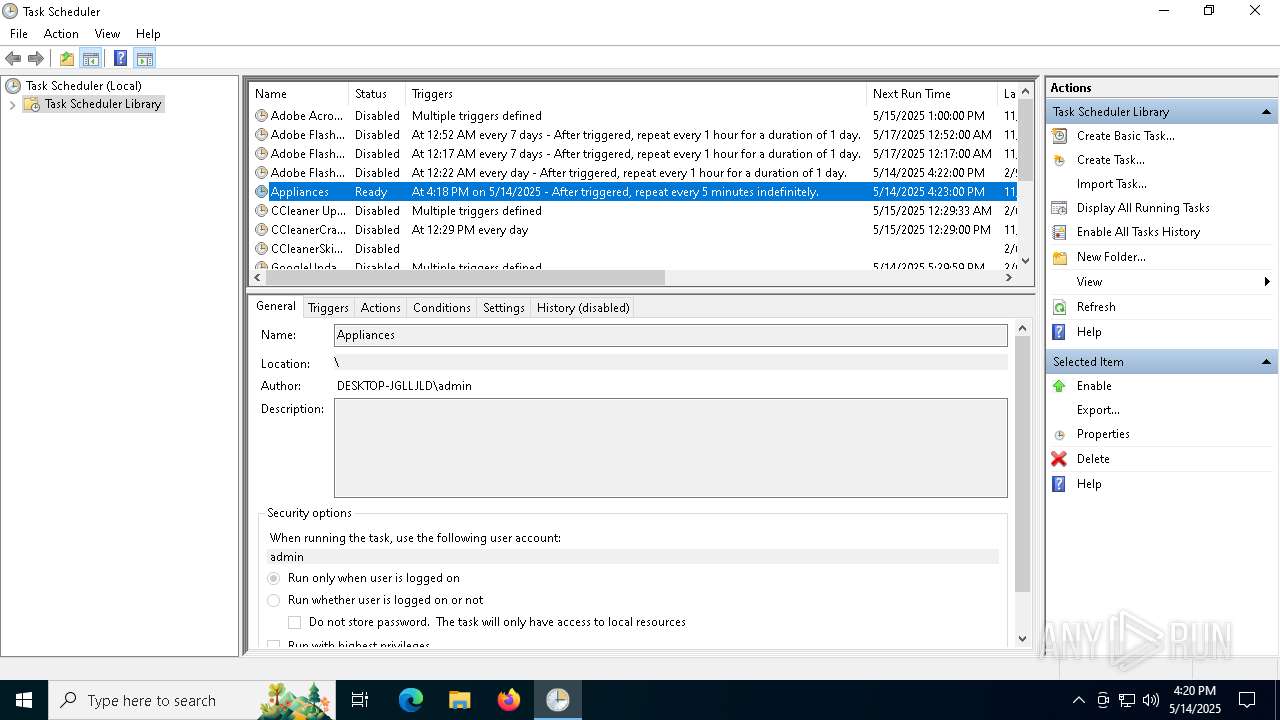
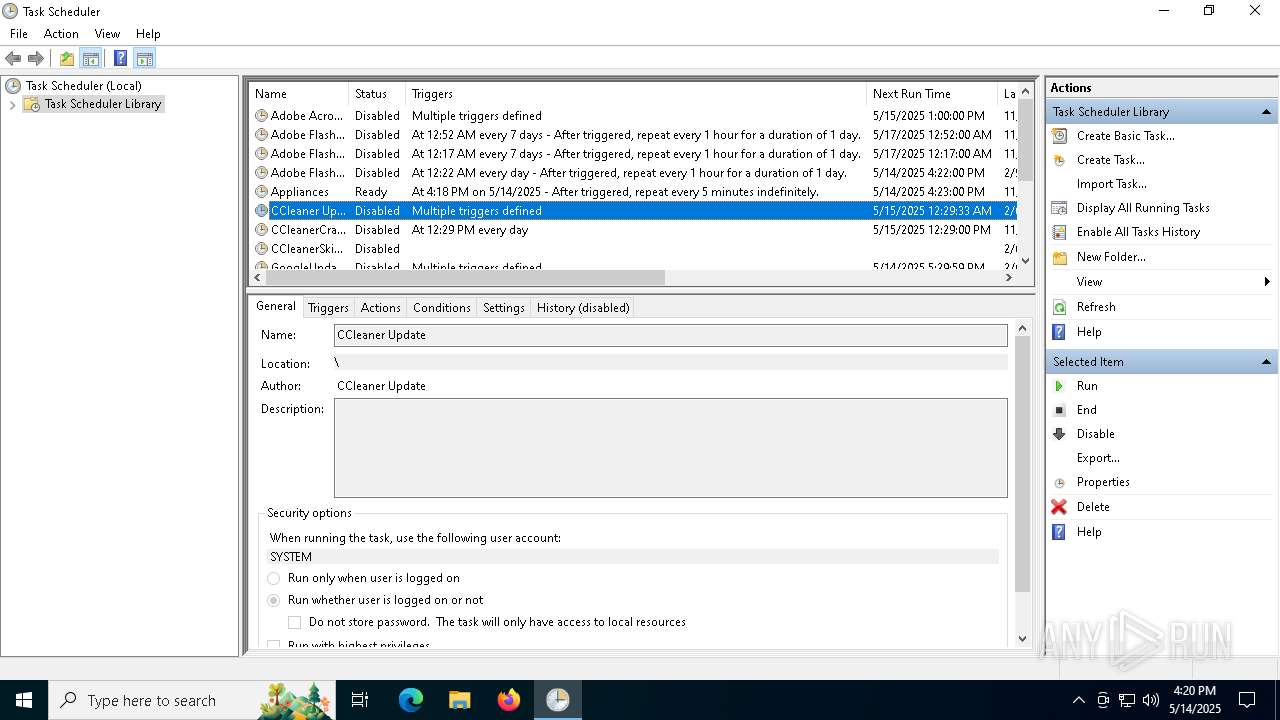
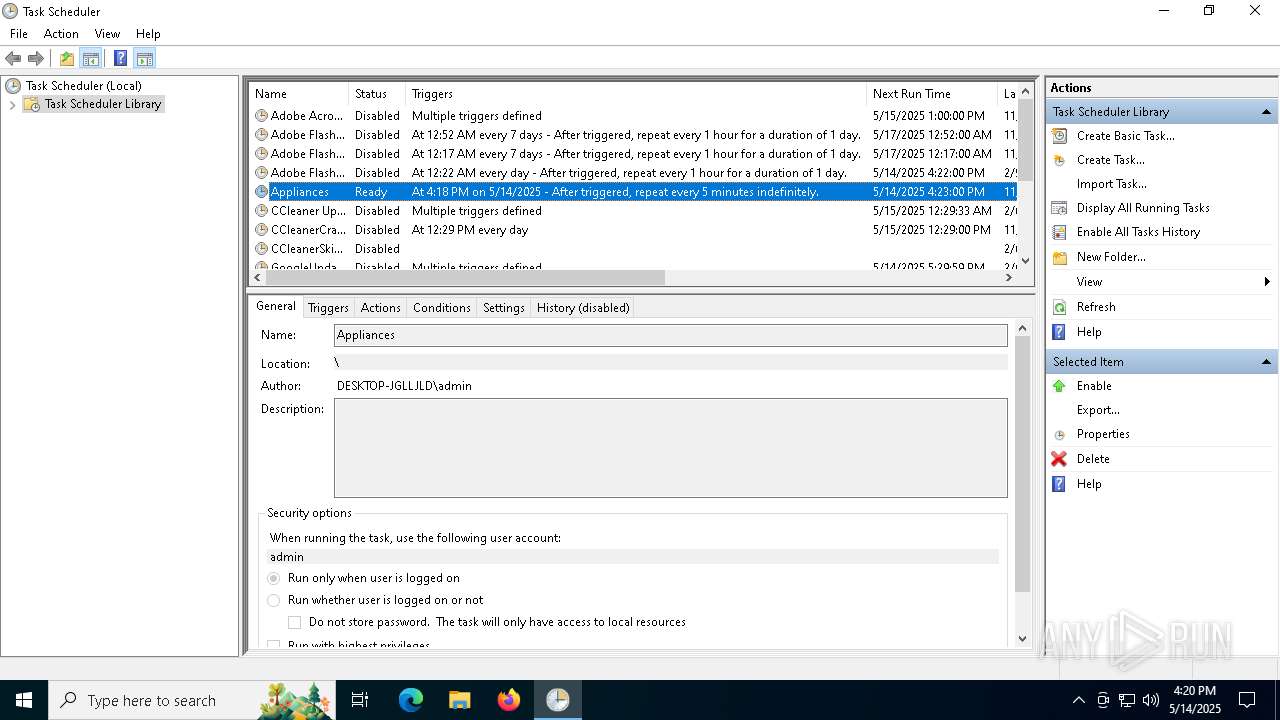
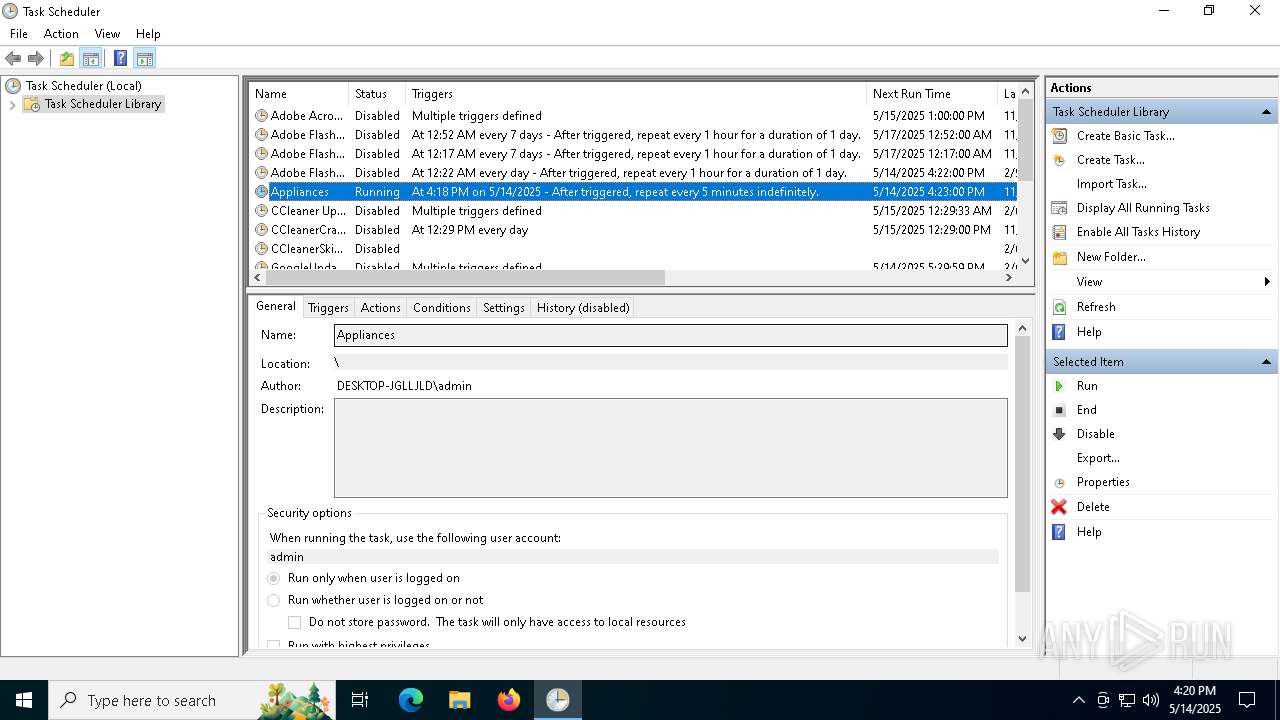
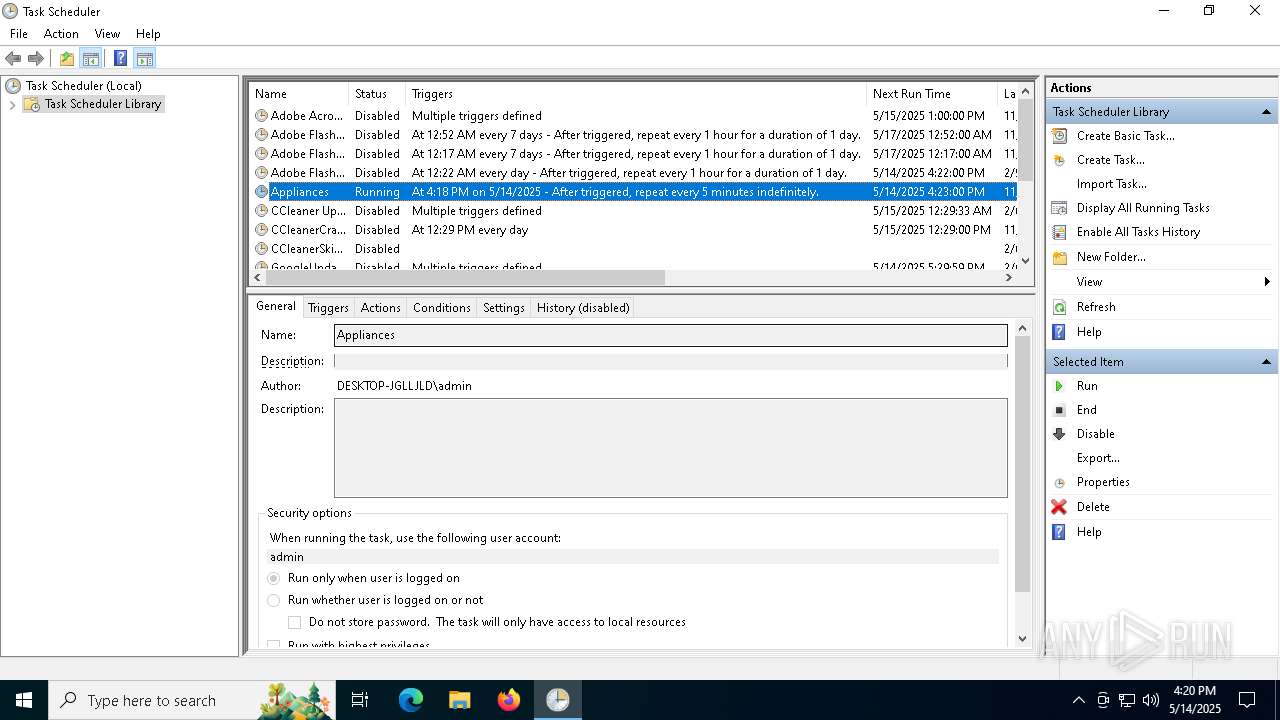
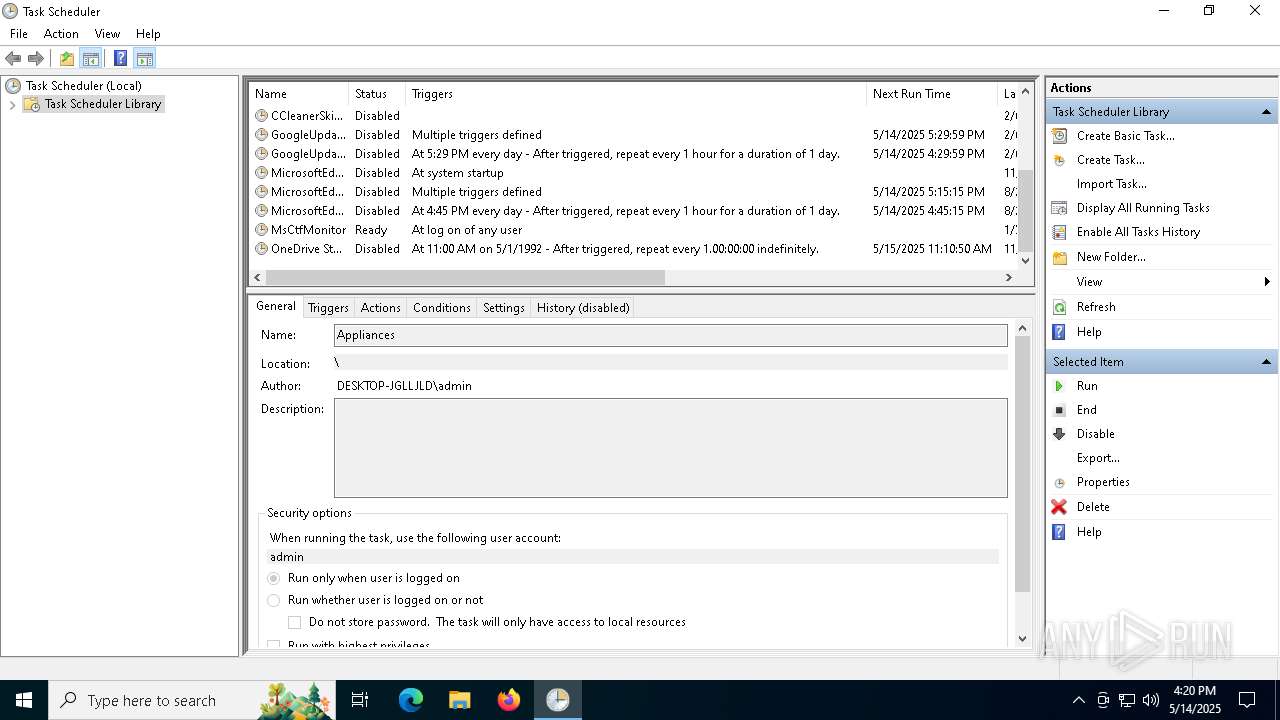
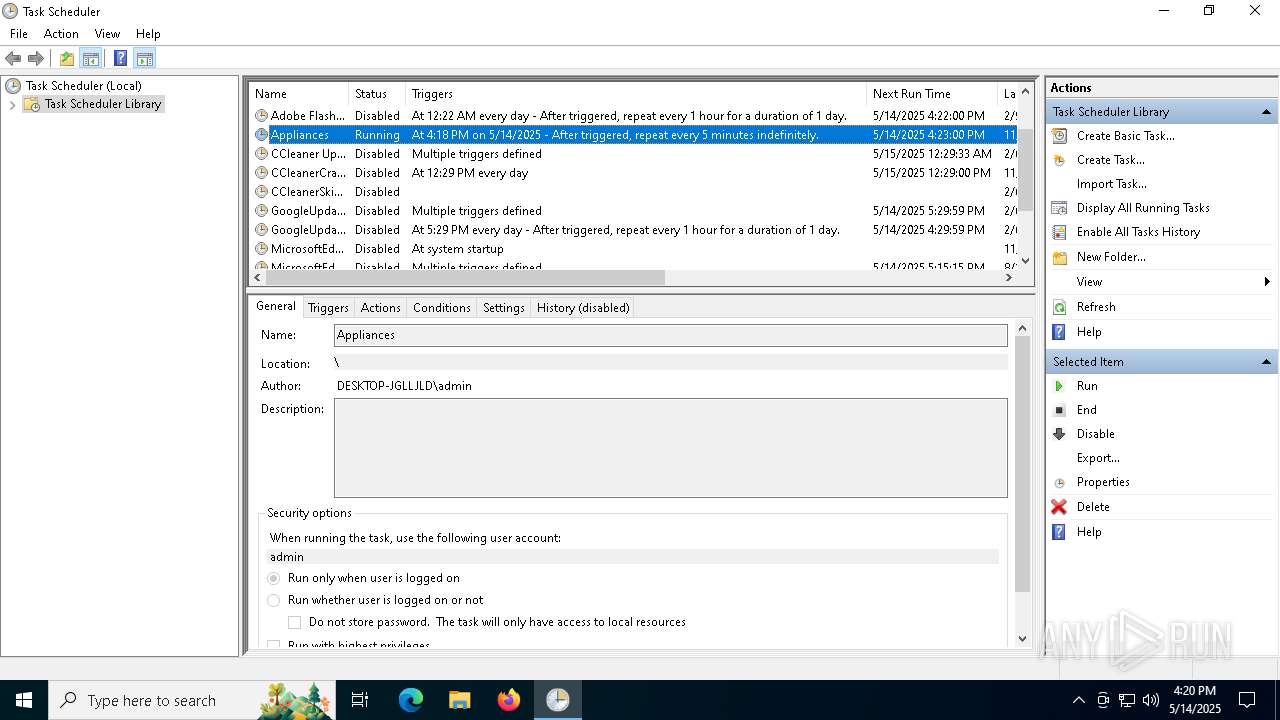
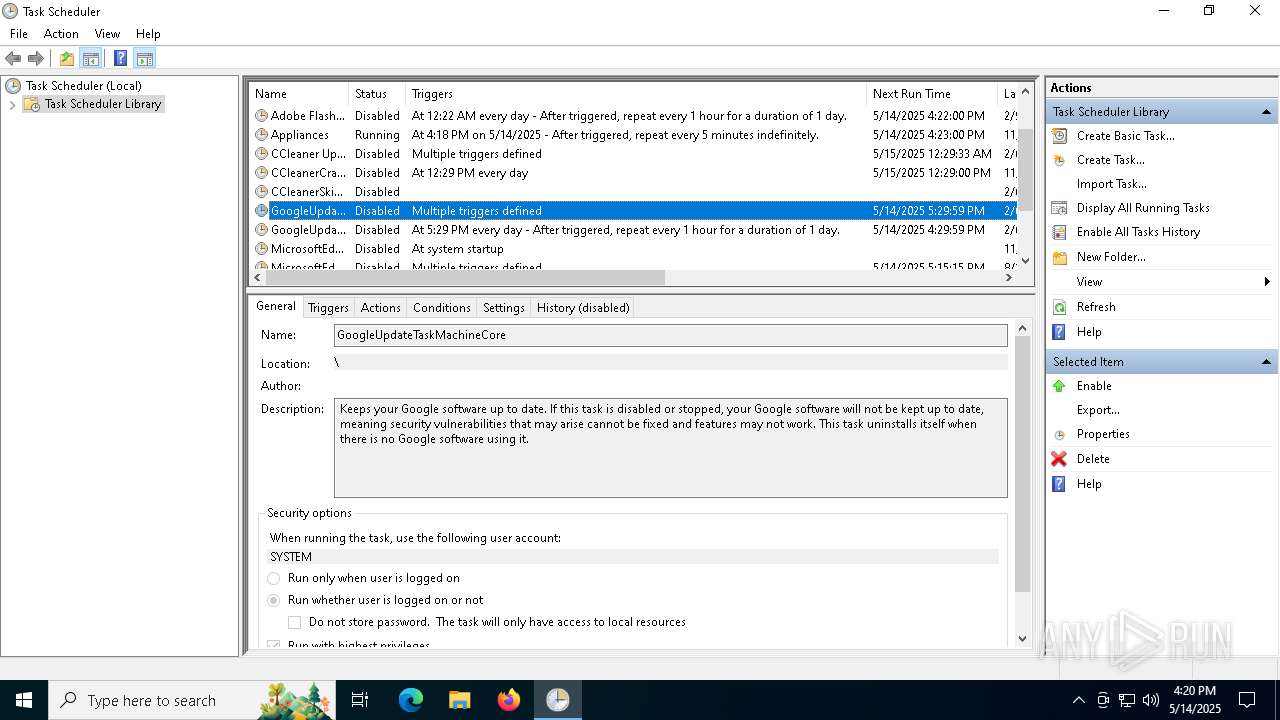
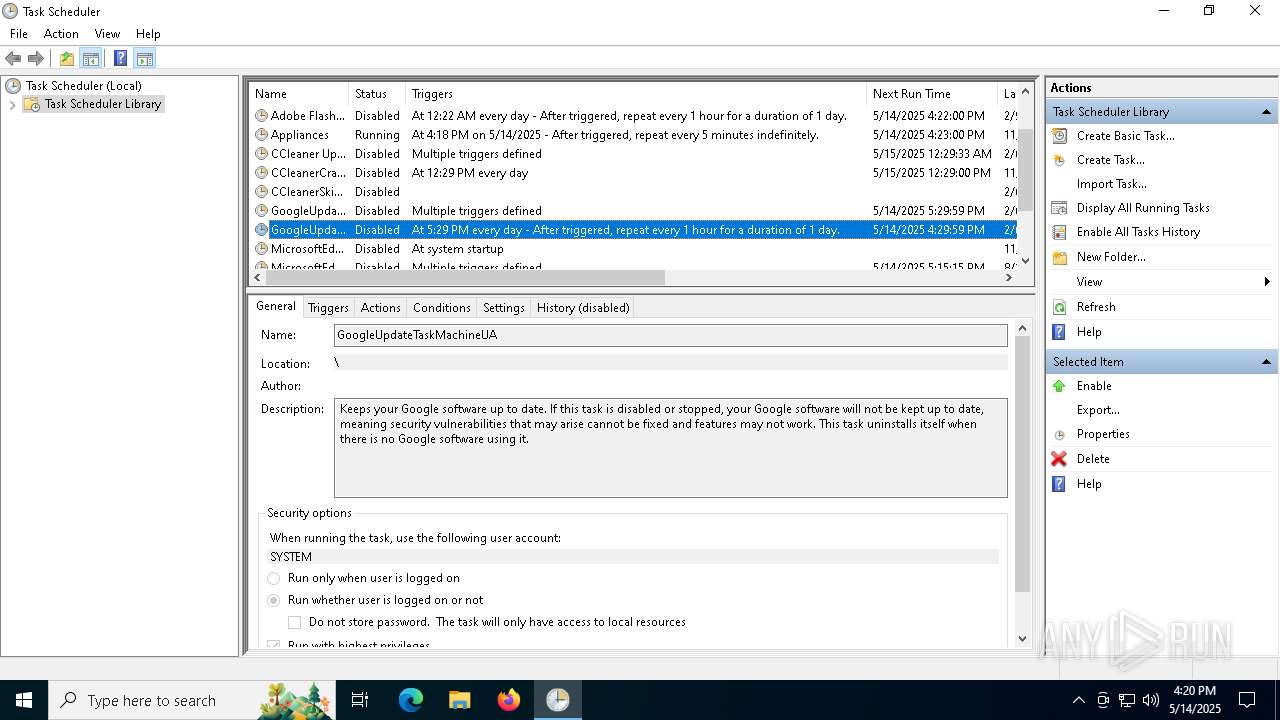
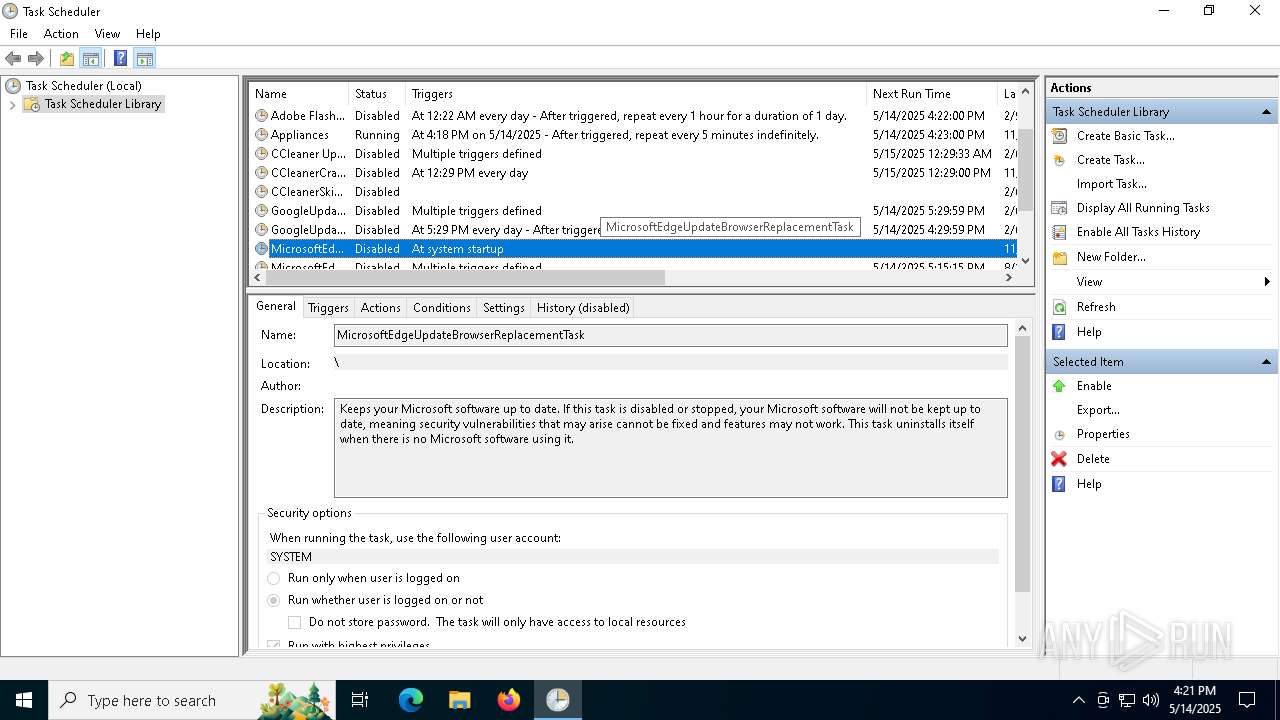
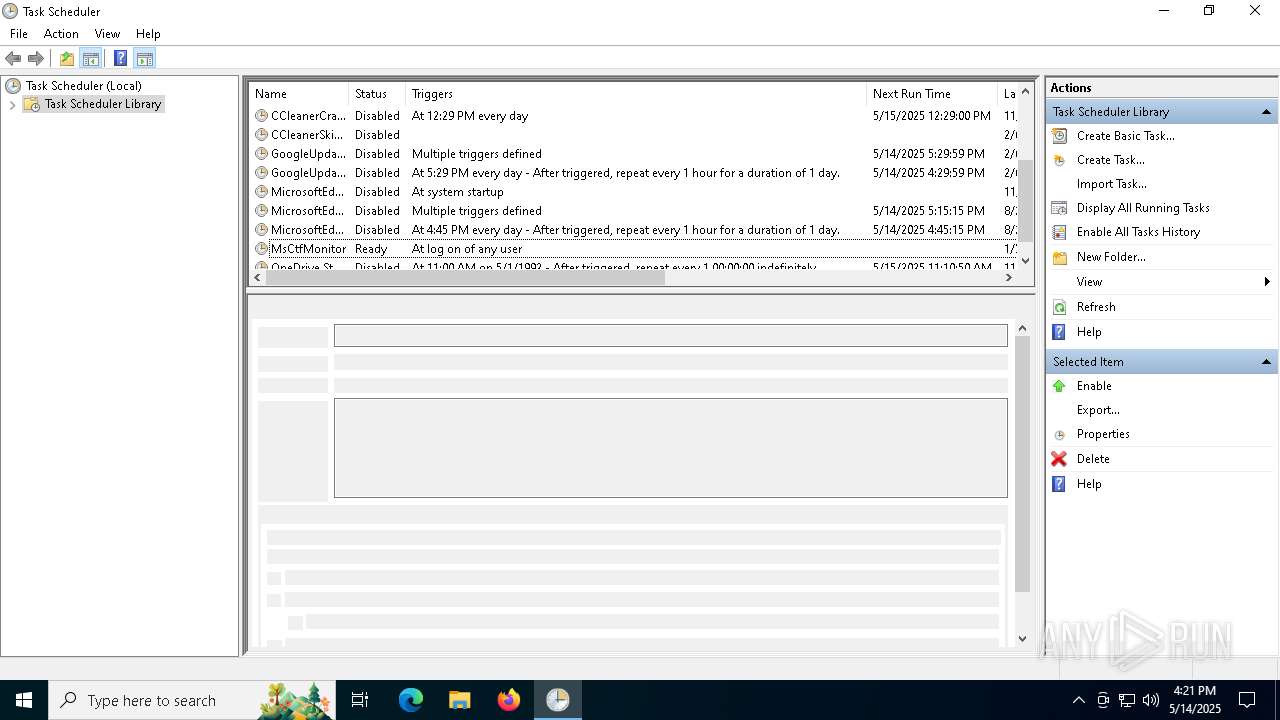
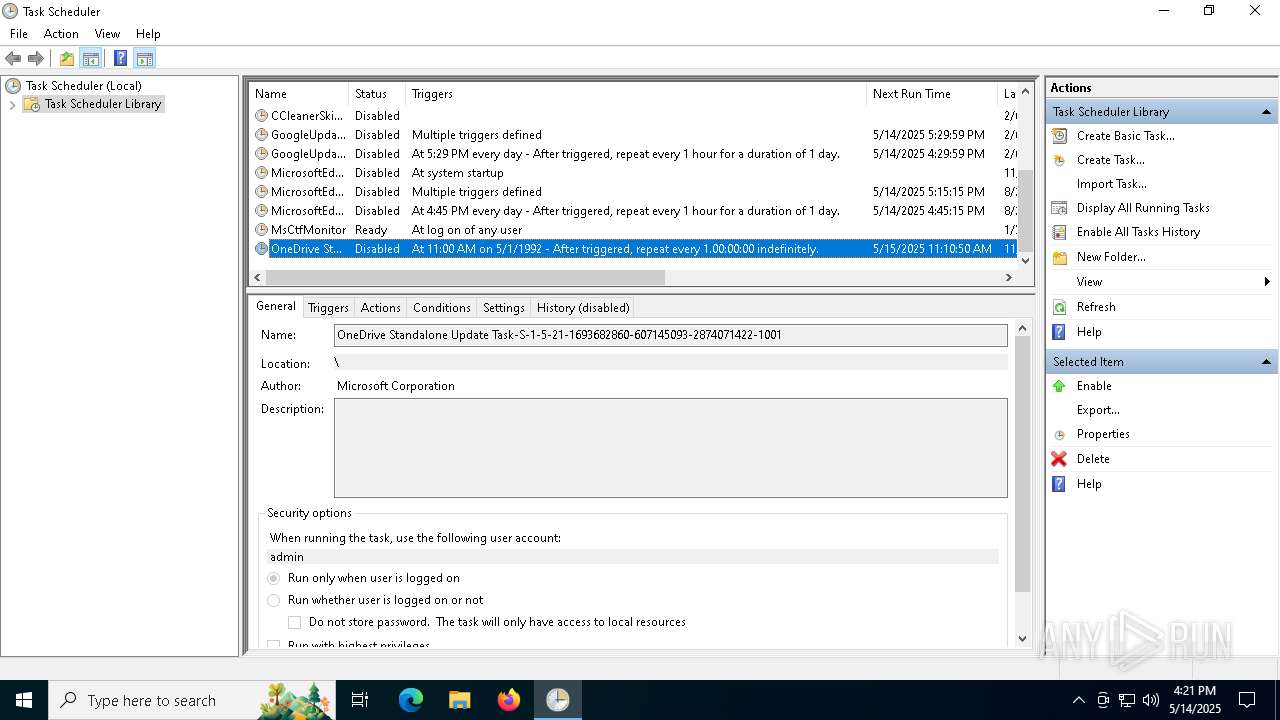
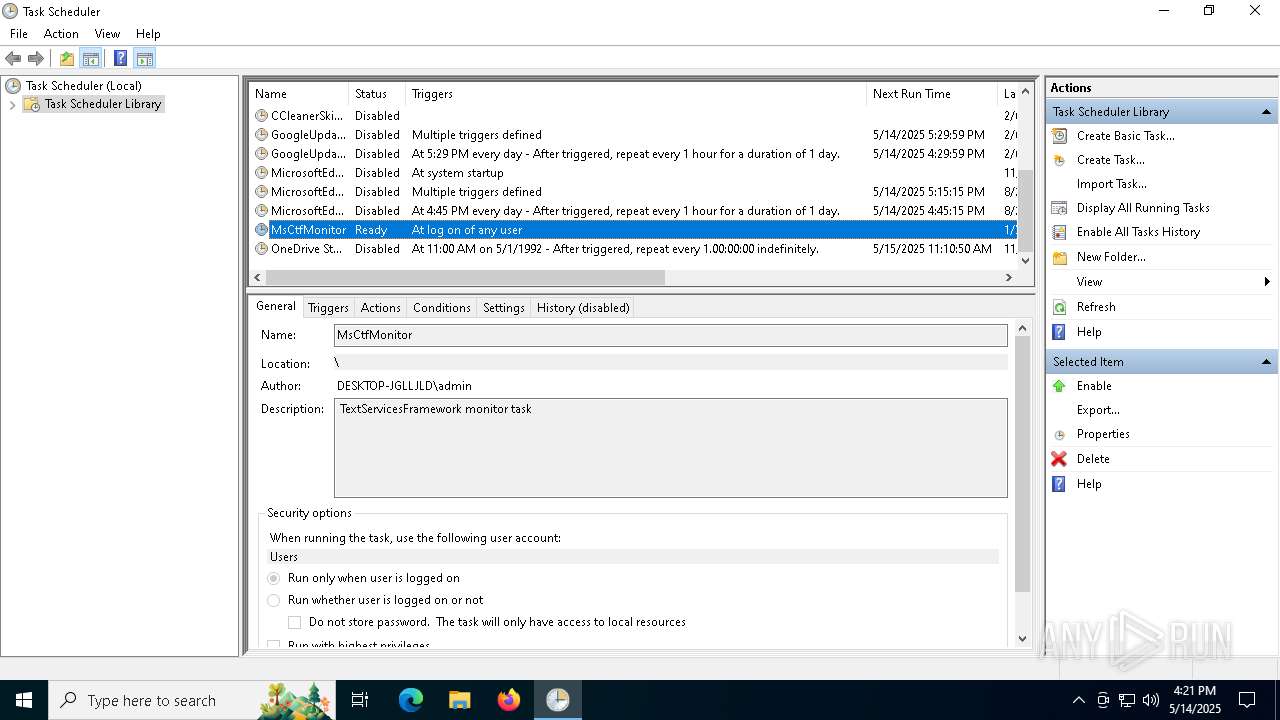
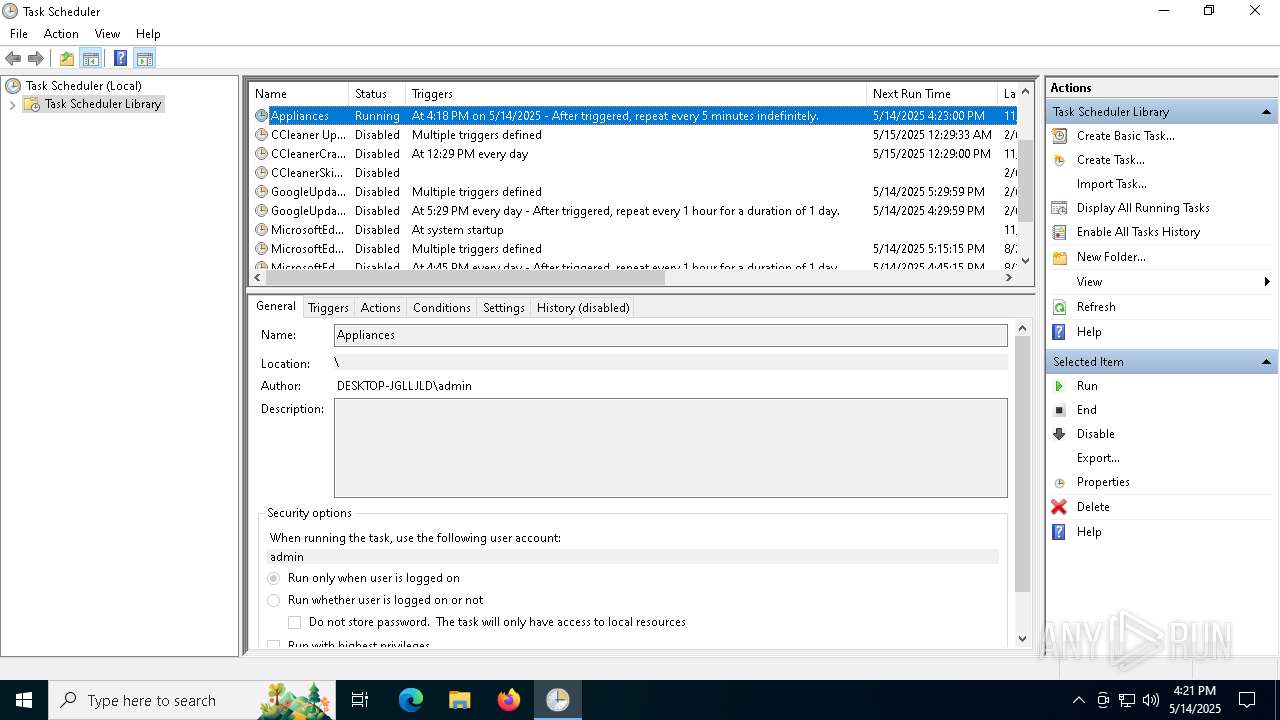
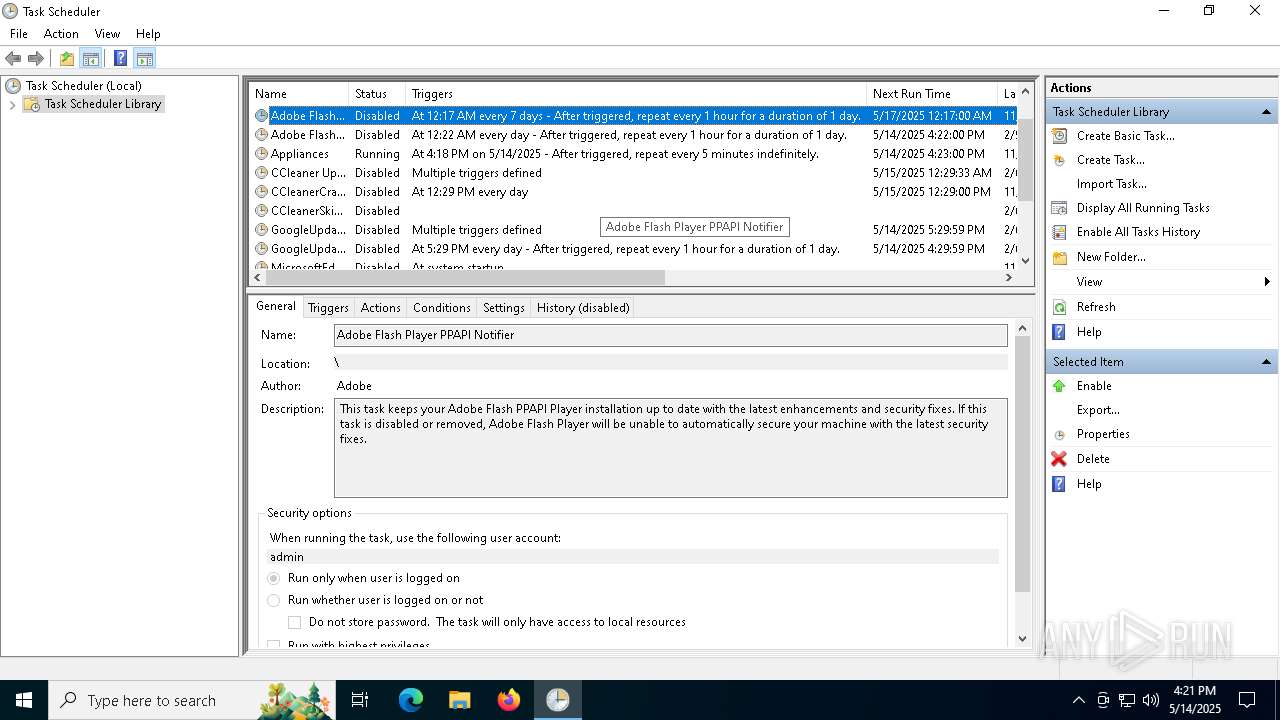
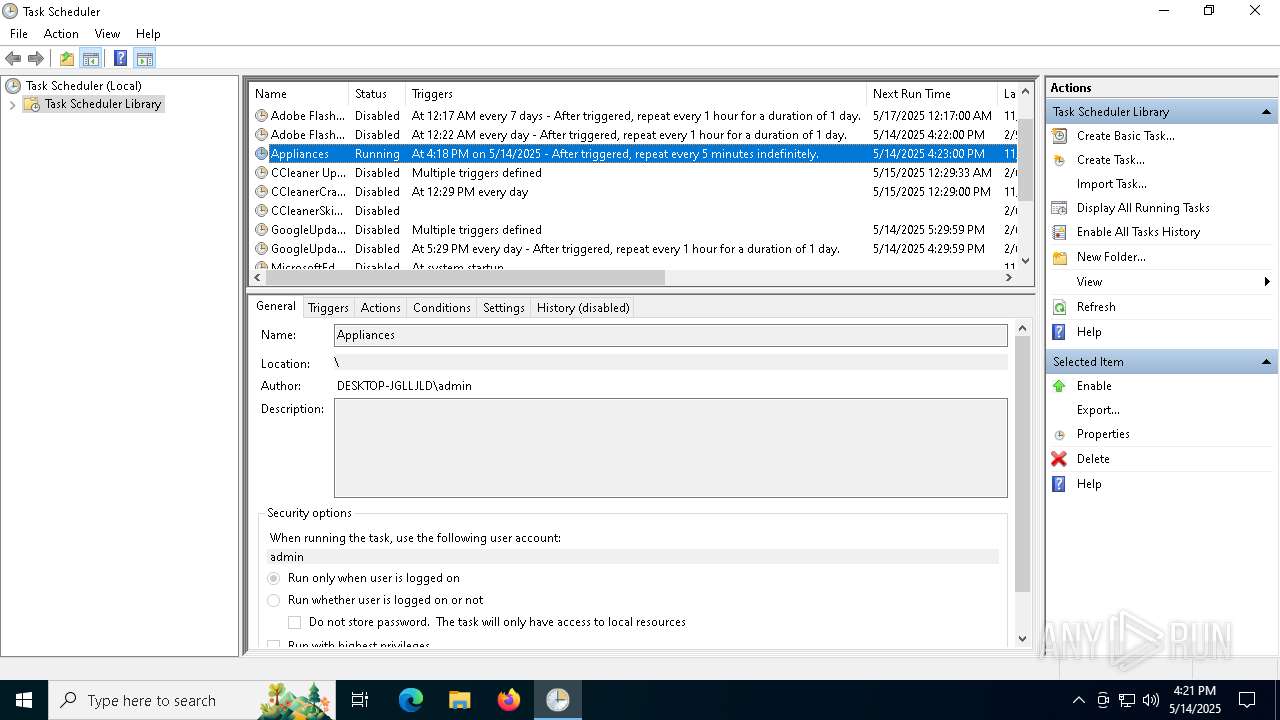
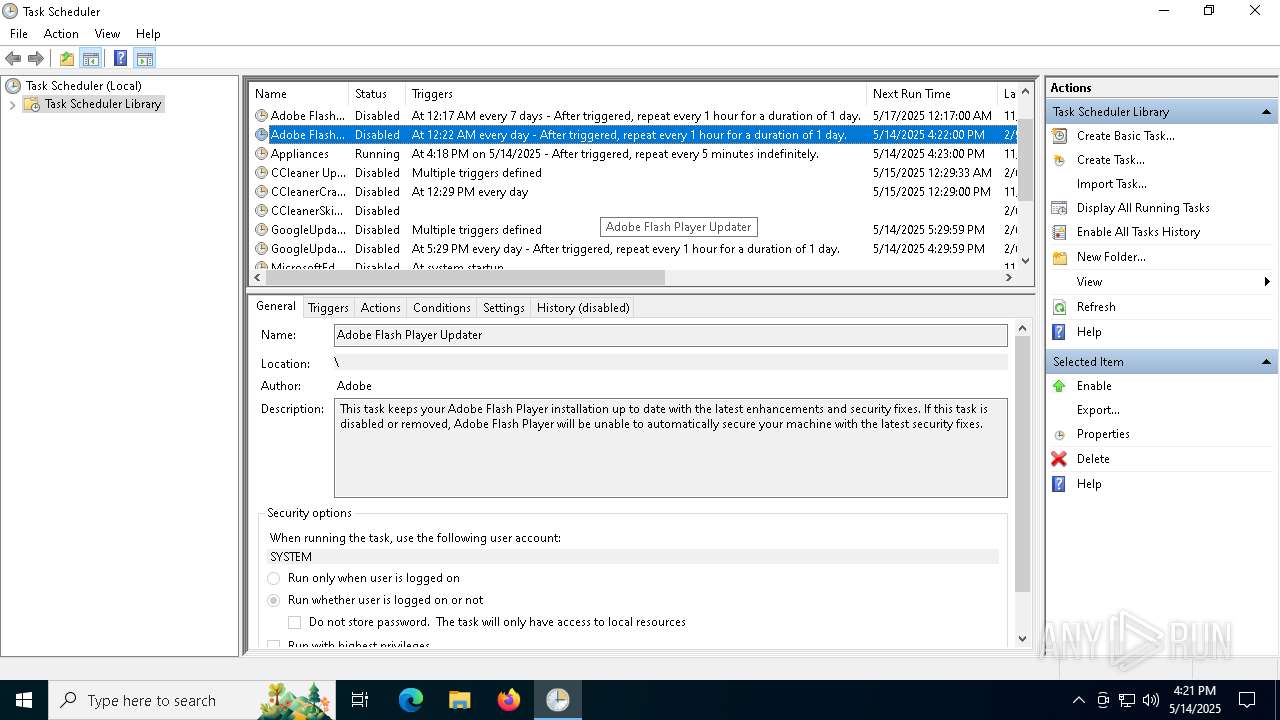
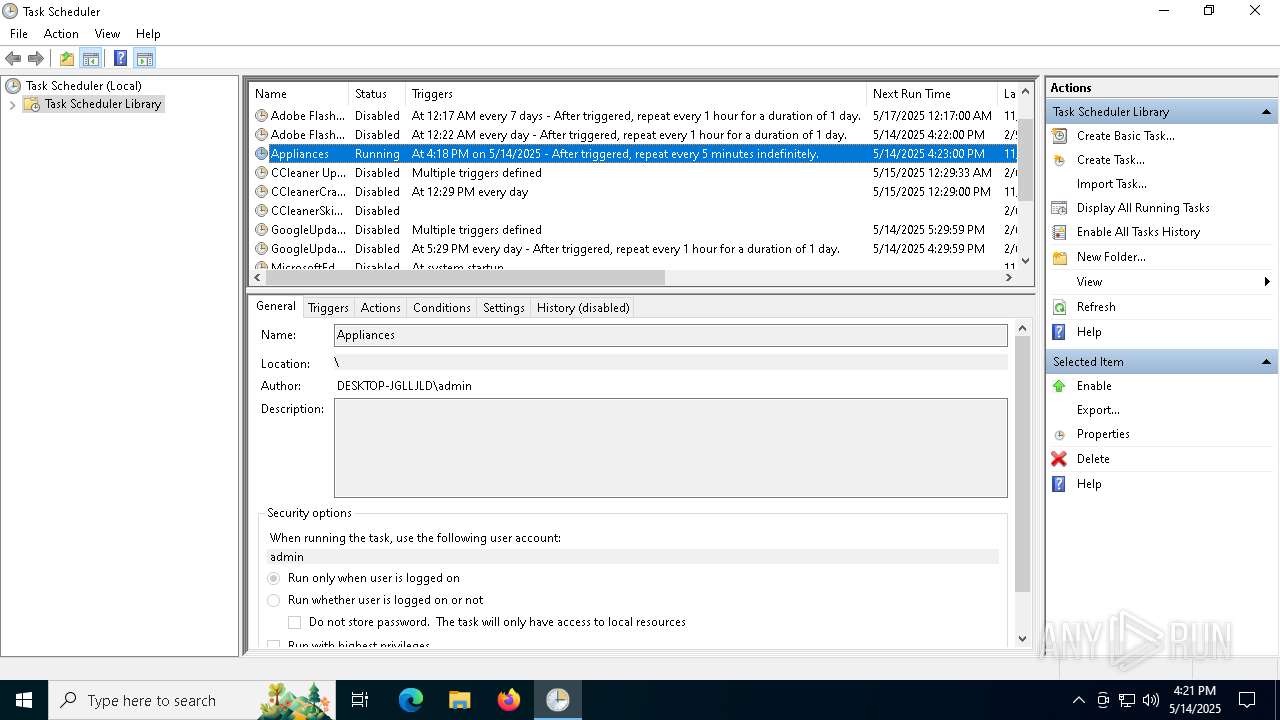
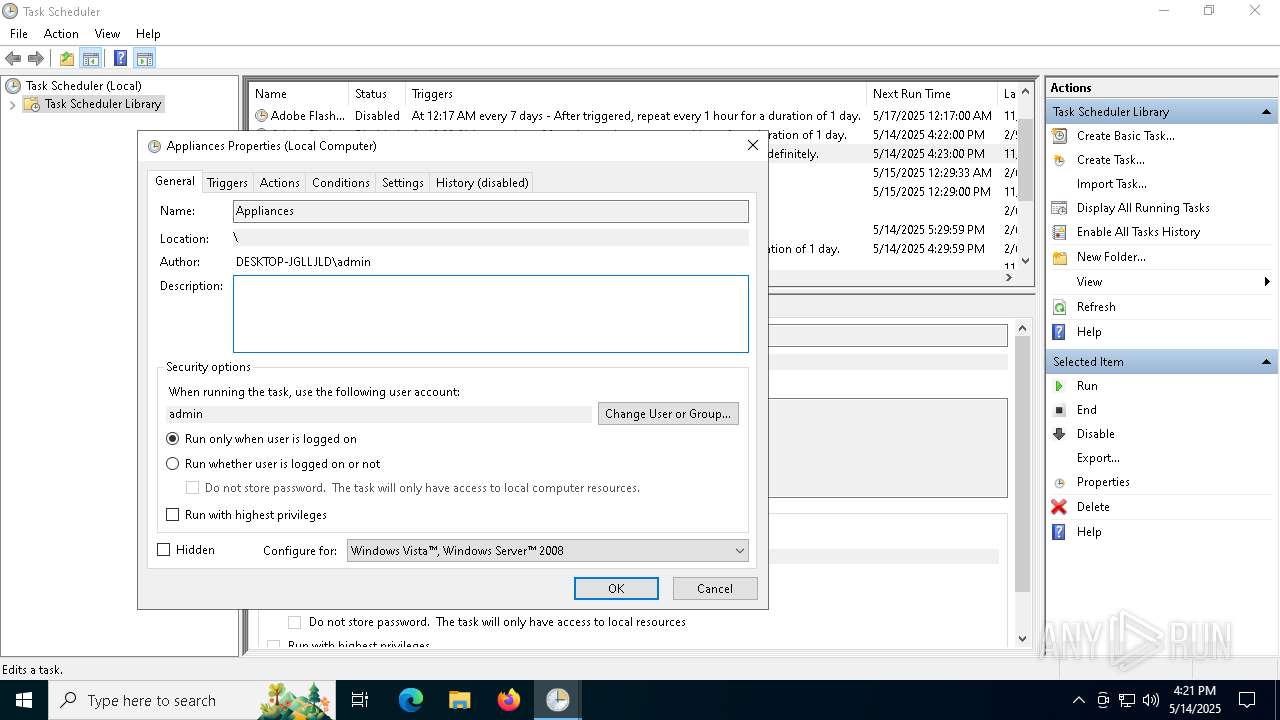
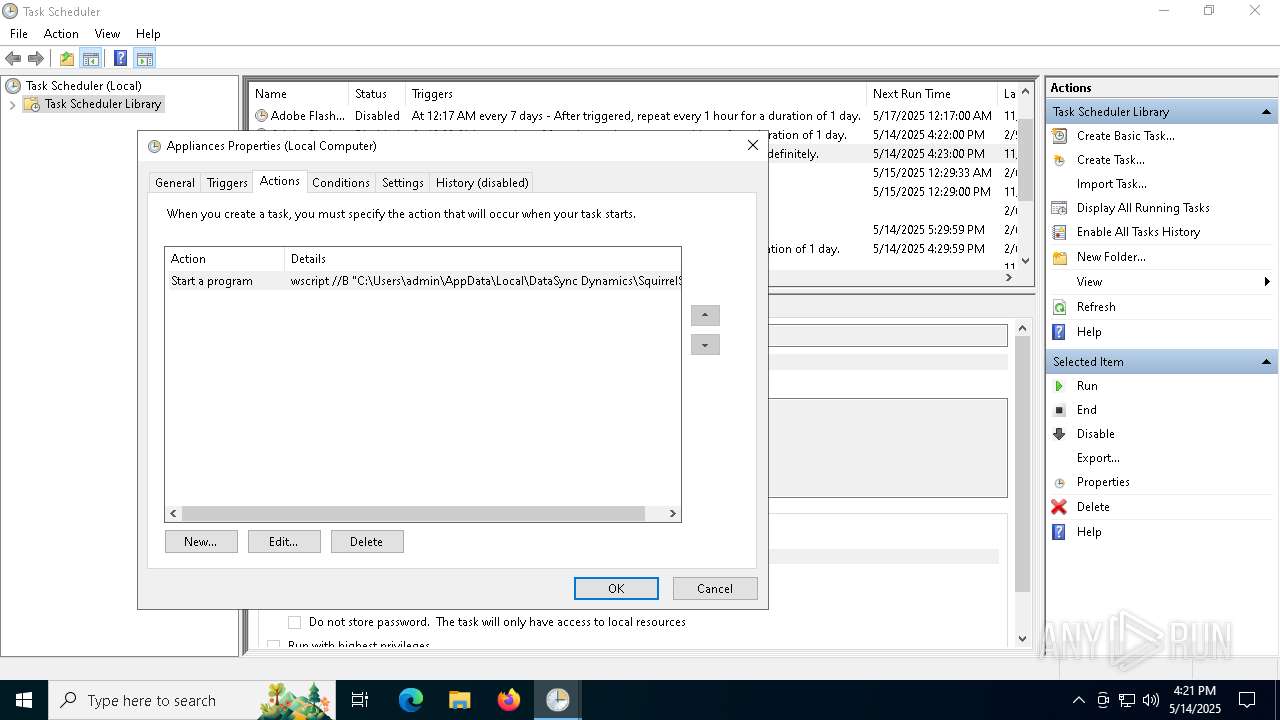
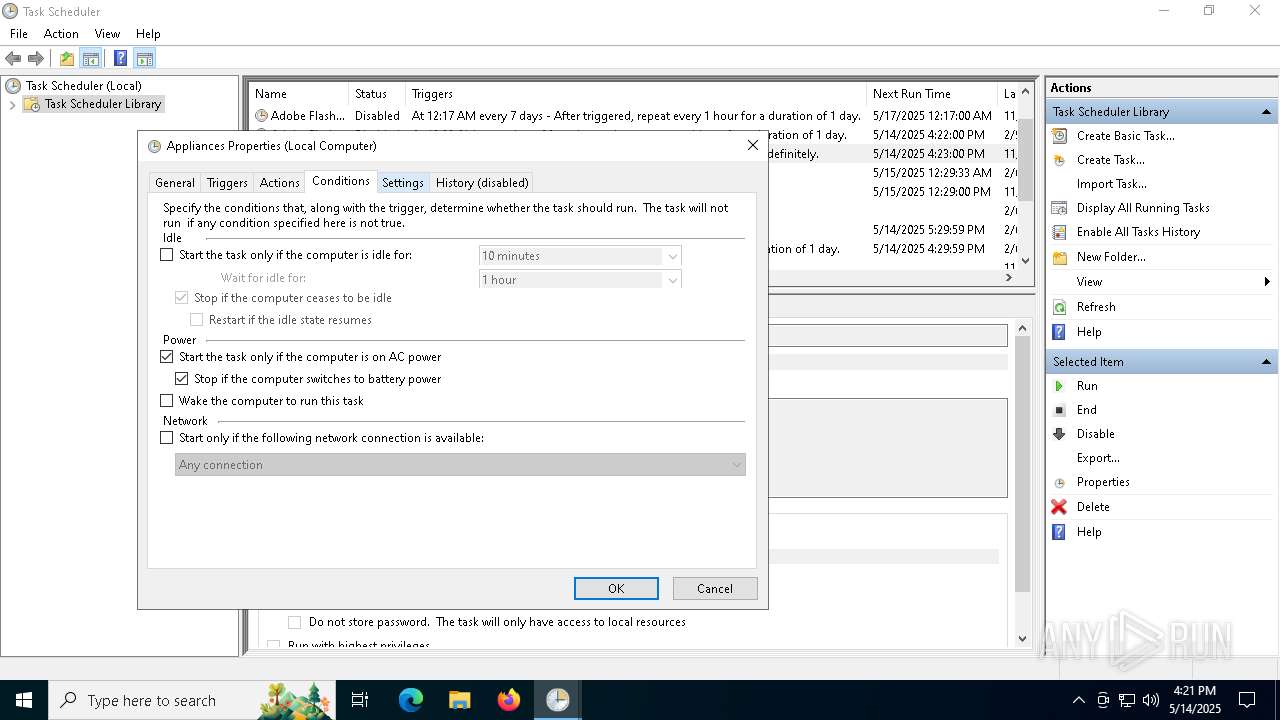
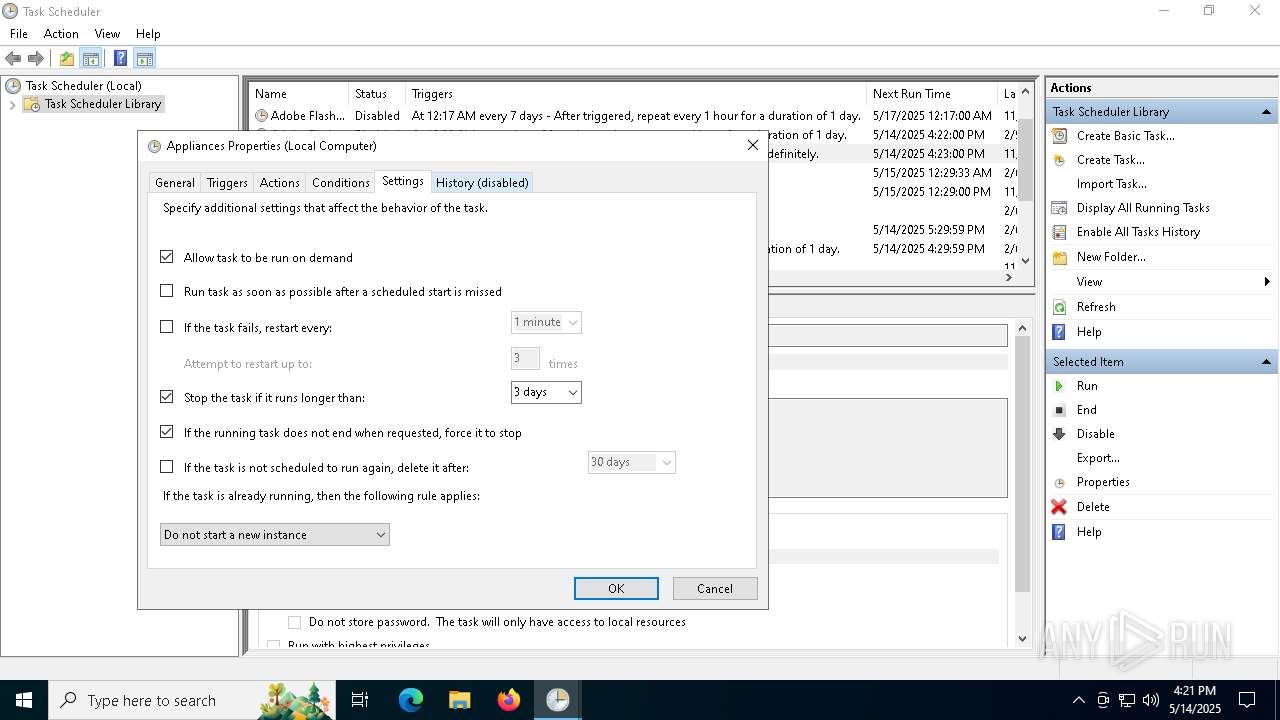
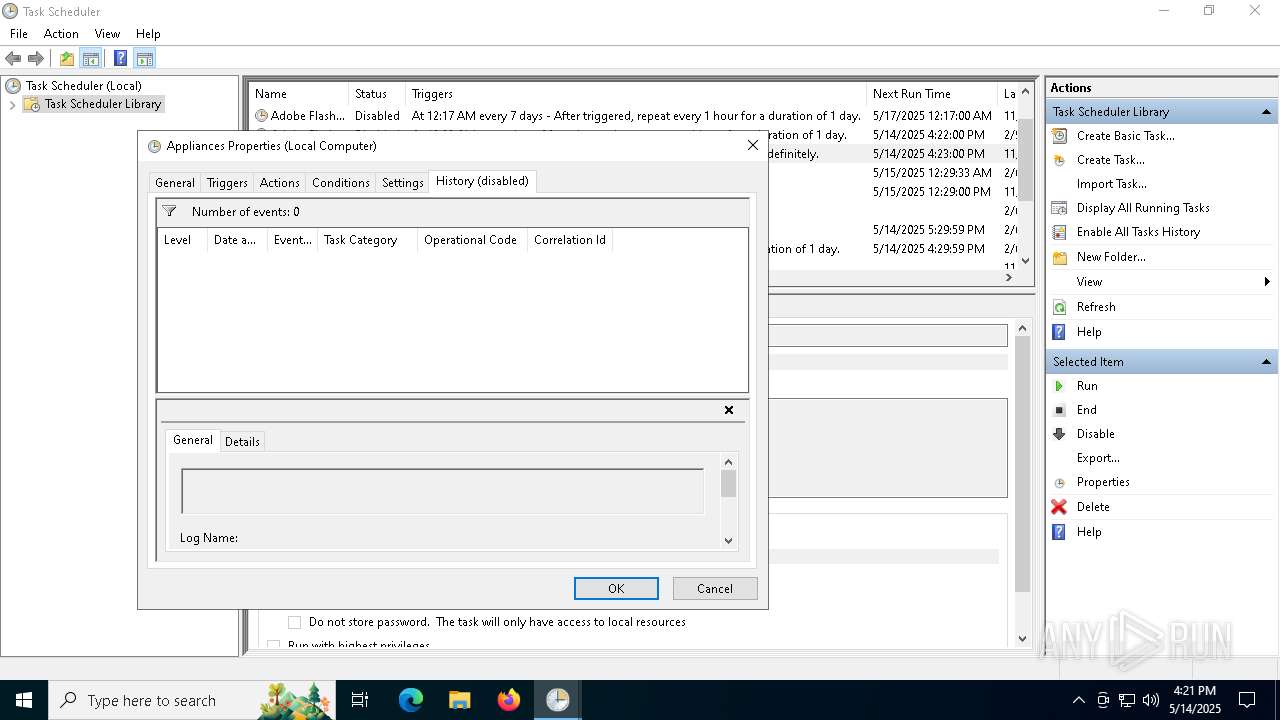
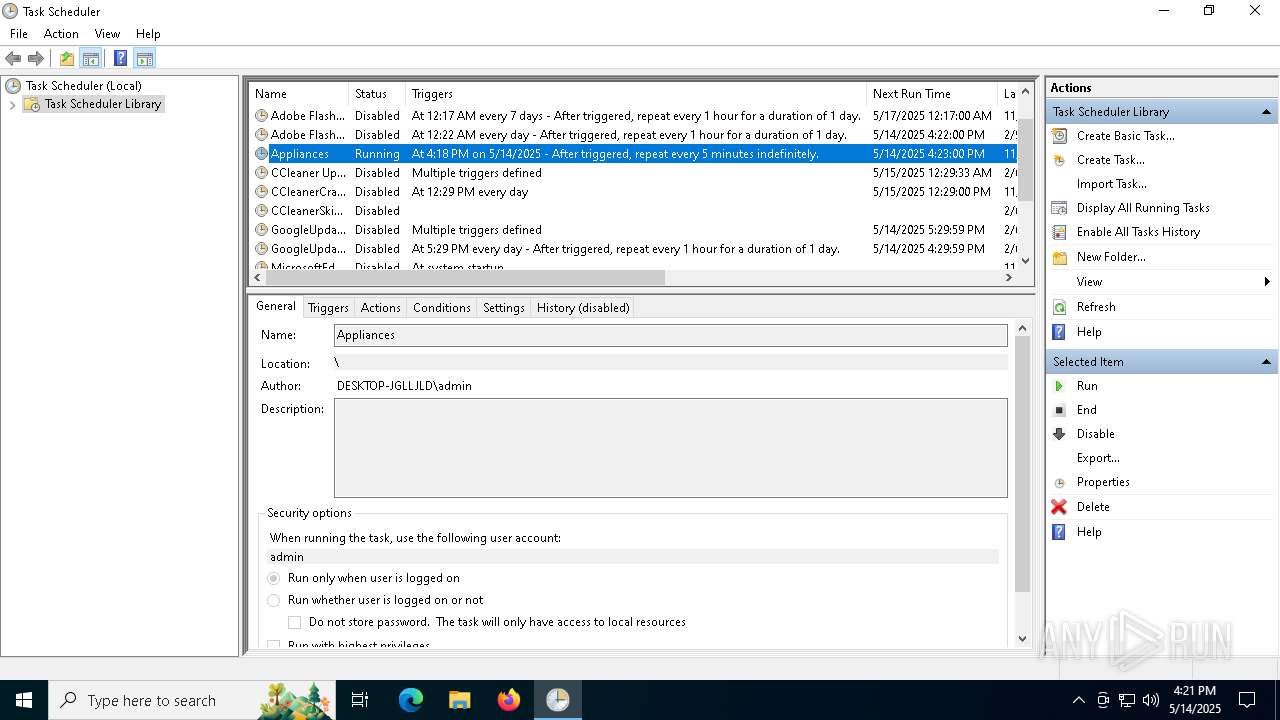
Uses Task Scheduler to run other applications
- cmd.exe (PID: 7420)
SUSPICIOUS
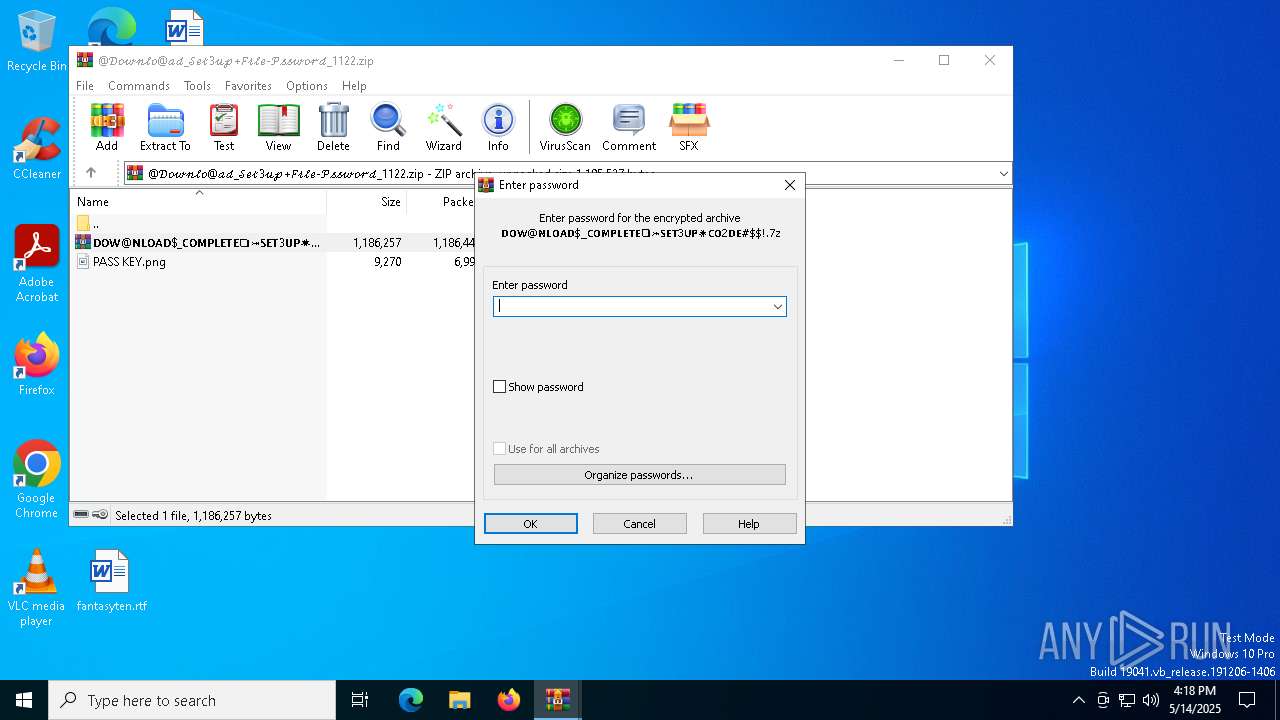
Application launched itself
- WinRAR.exe (PID: 4164)
- WinRAR.exe (PID: 6268)
- cmd.exe (PID: 7176)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6268)
- WinRAR.exe (PID: 4164)
Executing commands from a ".bat" file
- setup.exe (PID: 5624)
Starts CMD.EXE for commands execution
- setup.exe (PID: 5624)
- cmd.exe (PID: 7176)
Get information on the list of running processes
- cmd.exe (PID: 7176)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7176)
Starts the AutoIt3 executable file
- cmd.exe (PID: 7176)
- wscript.exe (PID: 1228)
- wscript.exe (PID: 7812)
Starts application with an unusual extension
- cmd.exe (PID: 7176)
- wscript.exe (PID: 1228)
- wscript.exe (PID: 7812)
Executable content was dropped or overwritten
- Mattress.com (PID: 5800)
There is functionality for taking screenshot (YARA)
- setup.exe (PID: 5624)
- Mattress.com (PID: 5800)
The executable file from the user directory is run by the CMD process
- Mattress.com (PID: 5800)
The process executes via Task Scheduler
- wscript.exe (PID: 7812)
INFO
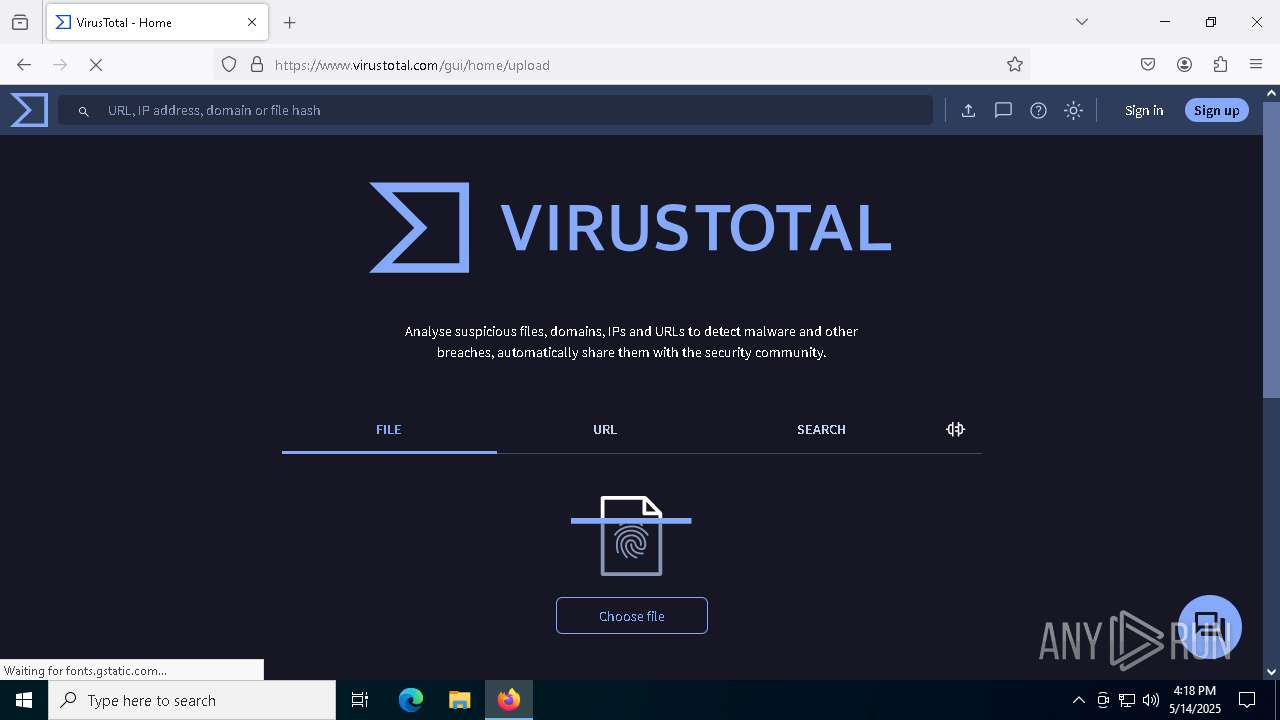
Application launched itself
- firefox.exe (PID: 7592)
- firefox.exe (PID: 7612)
- firefox.exe (PID: 4012)
- firefox.exe (PID: 6724)
Reads the software policy settings
- slui.exe (PID: 2320)
Manual execution by a user
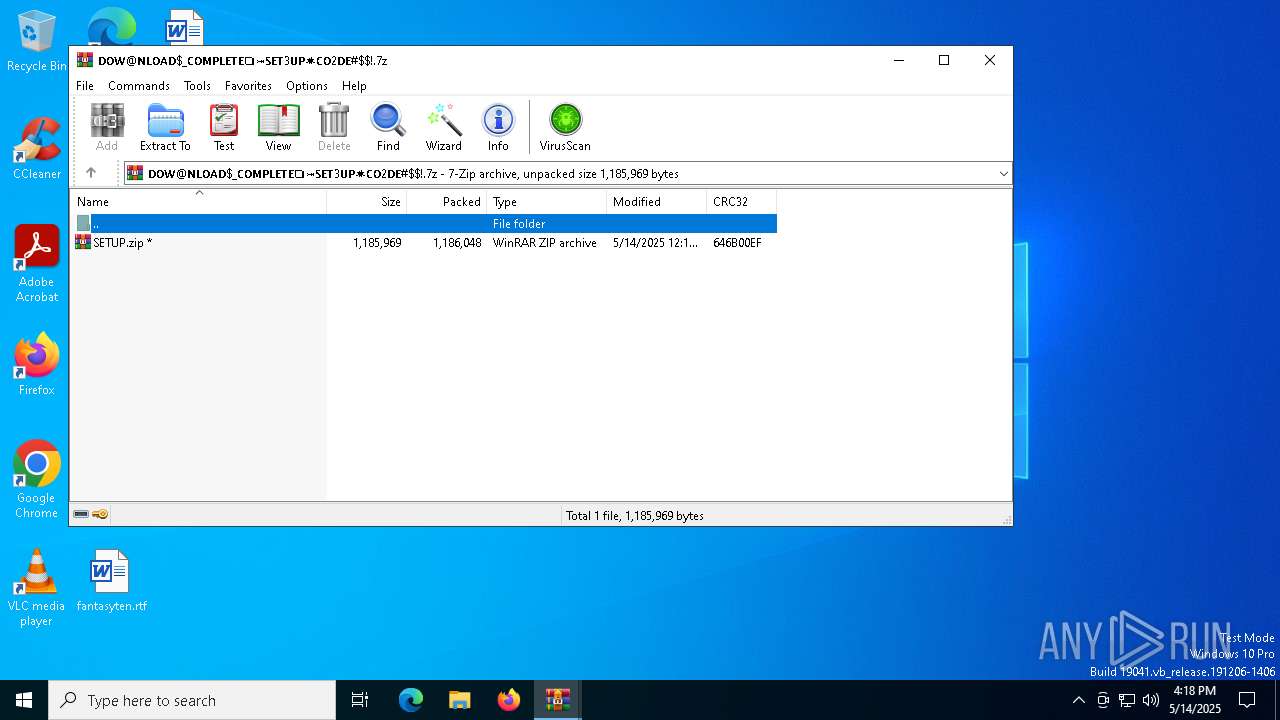
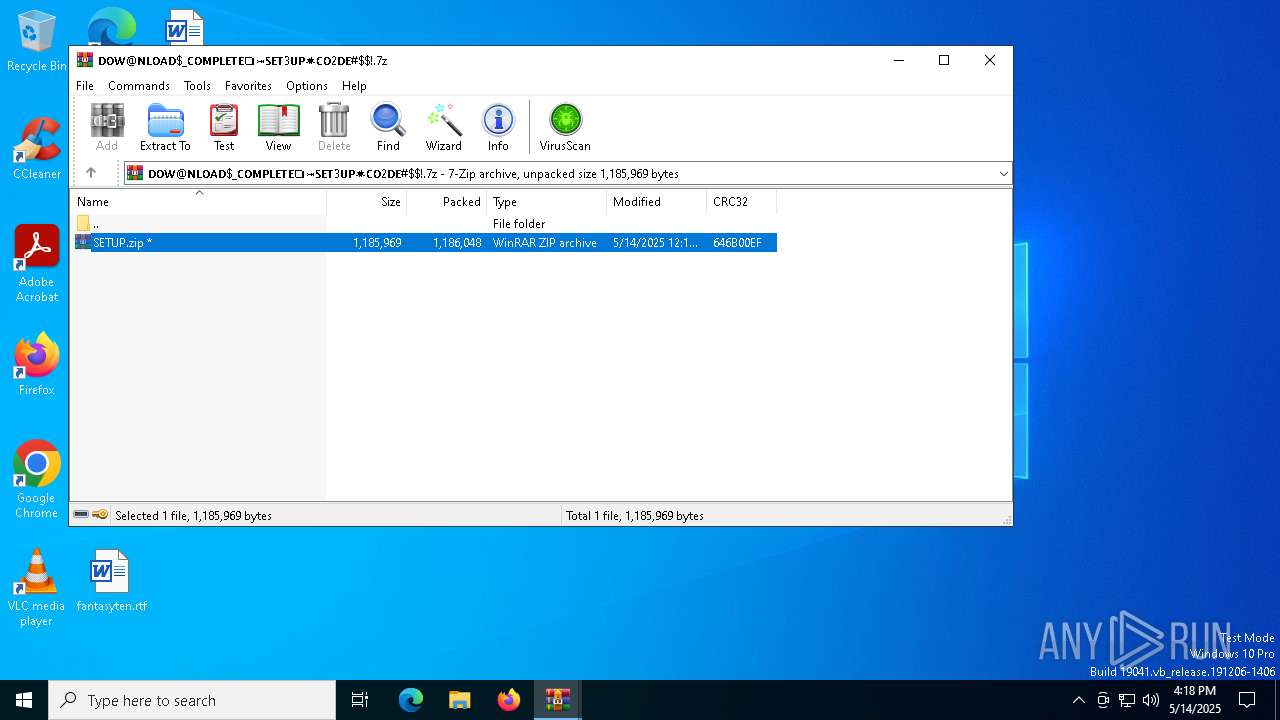
- WinRAR.exe (PID: 4164)
- setup.exe (PID: 5624)
- firefox.exe (PID: 6724)
- cmd.exe (PID: 7952)
- cmd.exe (PID: 7420)
- wscript.exe (PID: 1228)
- notepad++.exe (PID: 2664)
- mmc.exe (PID: 7204)
- notepad++.exe (PID: 736)
- mmc.exe (PID: 7760)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 208)
Checks supported languages
- setup.exe (PID: 5624)
Reads the computer name
- setup.exe (PID: 5624)
Create files in a temporary directory
- setup.exe (PID: 5624)
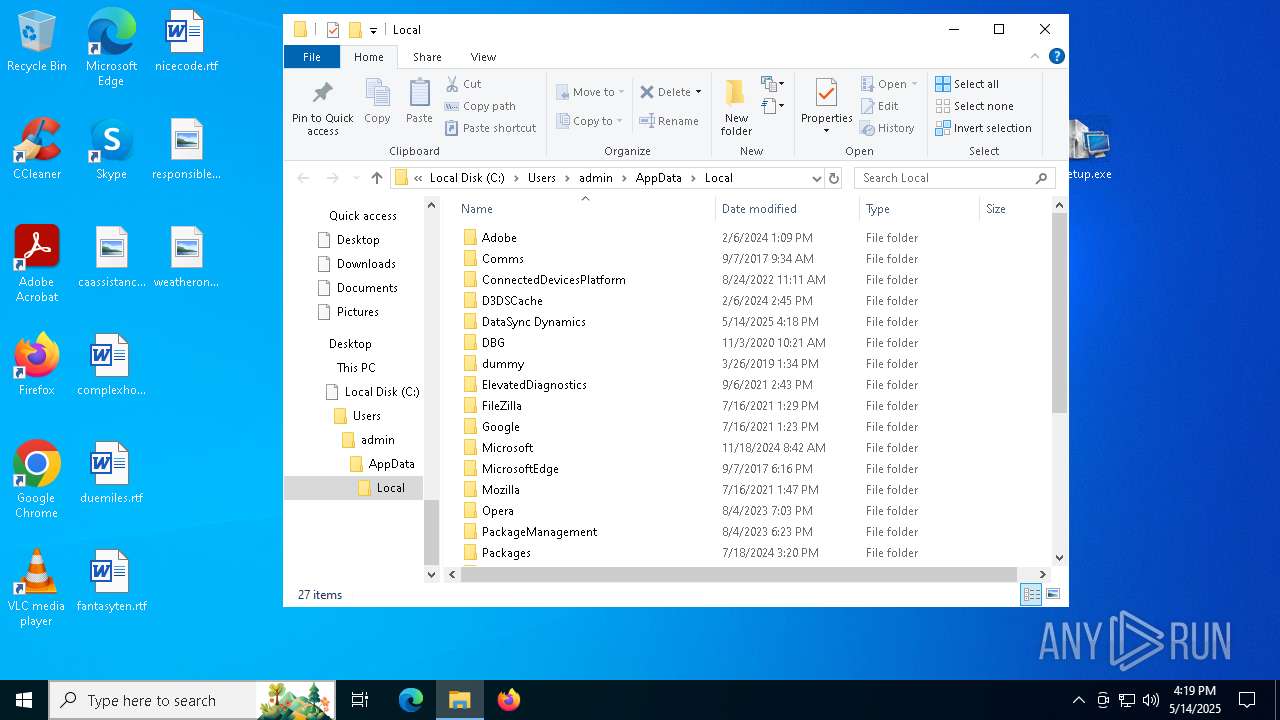
Creates a new folder
- cmd.exe (PID: 5548)
The sample compiled with english language support
- Mattress.com (PID: 5800)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
202
Monitored processes
67
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
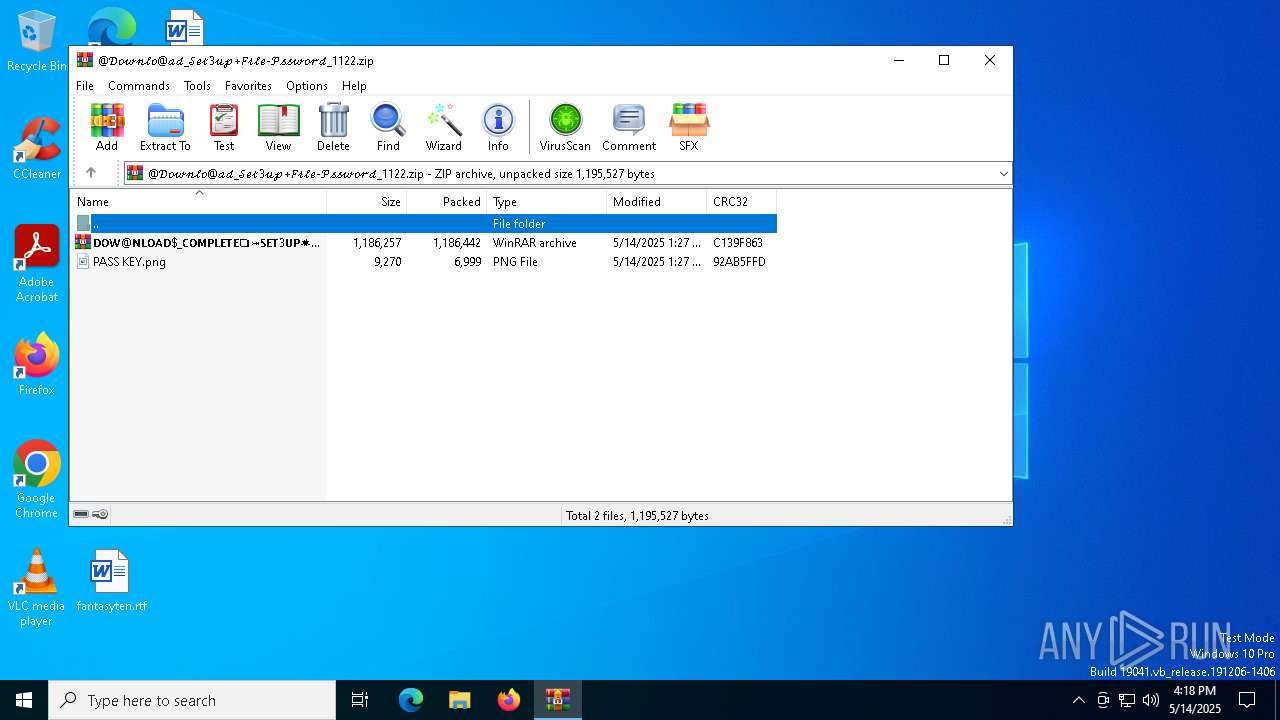
| 208 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Rar$DIb6268.31673\SETUP.zip | C:\Program Files\WinRAR\WinRAR.exe | WinRAR.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 720 | choice /d y /t 5 | C:\Windows\SysWOW64\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Offers the user a choice Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
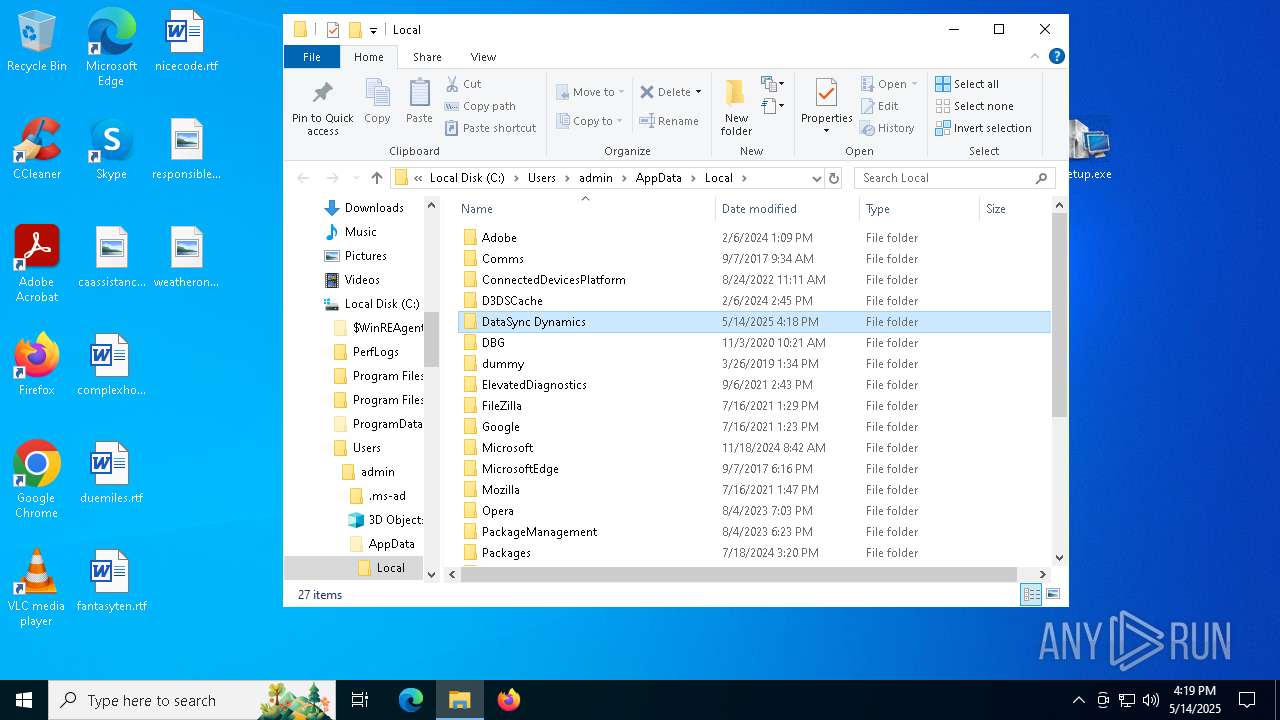
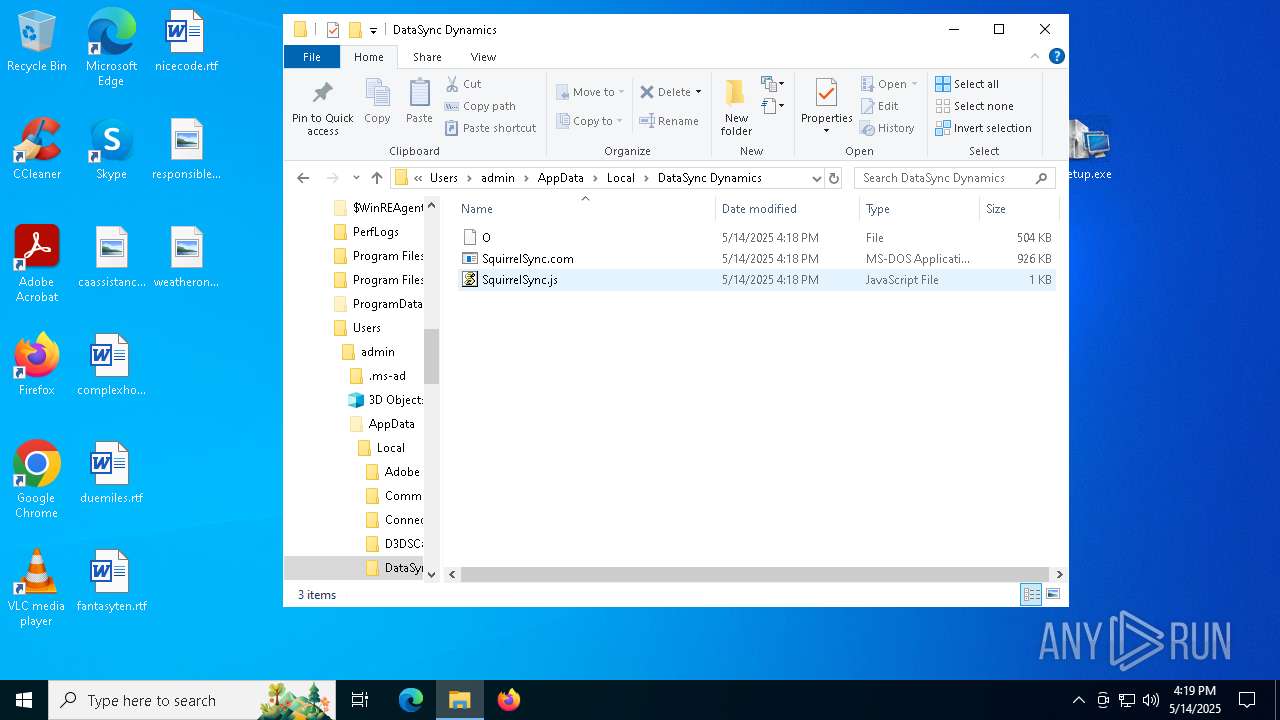
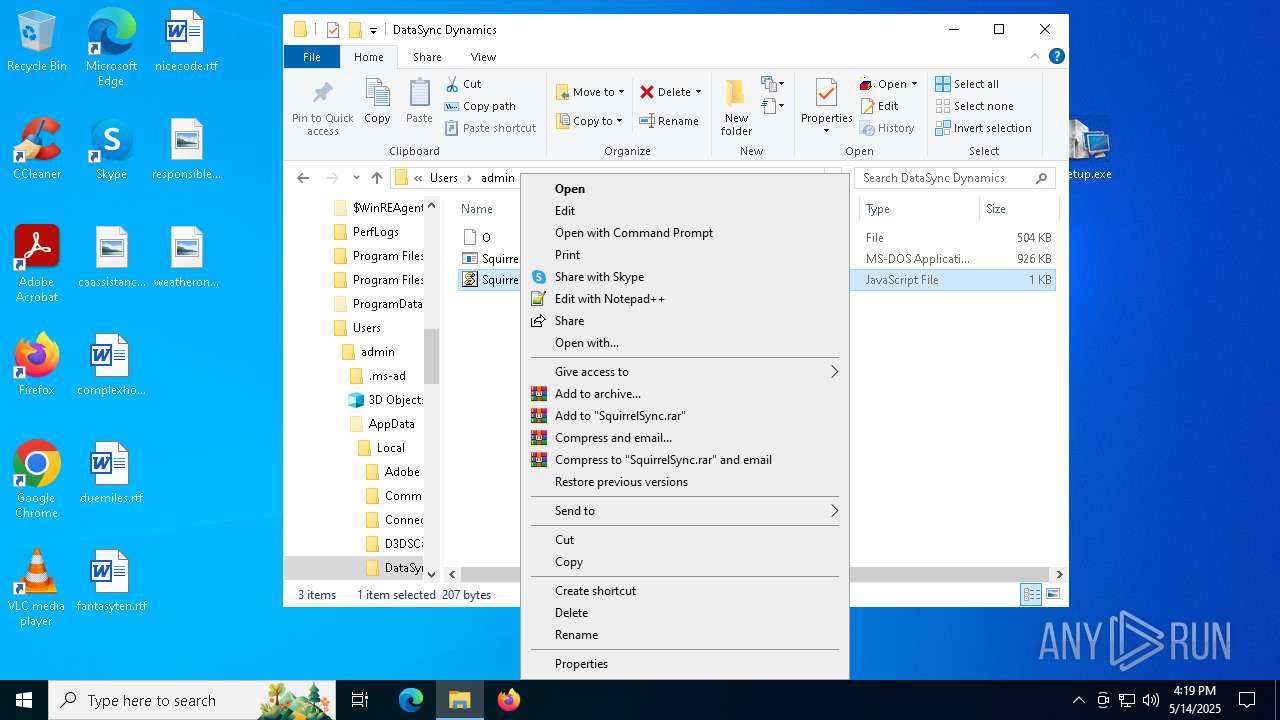
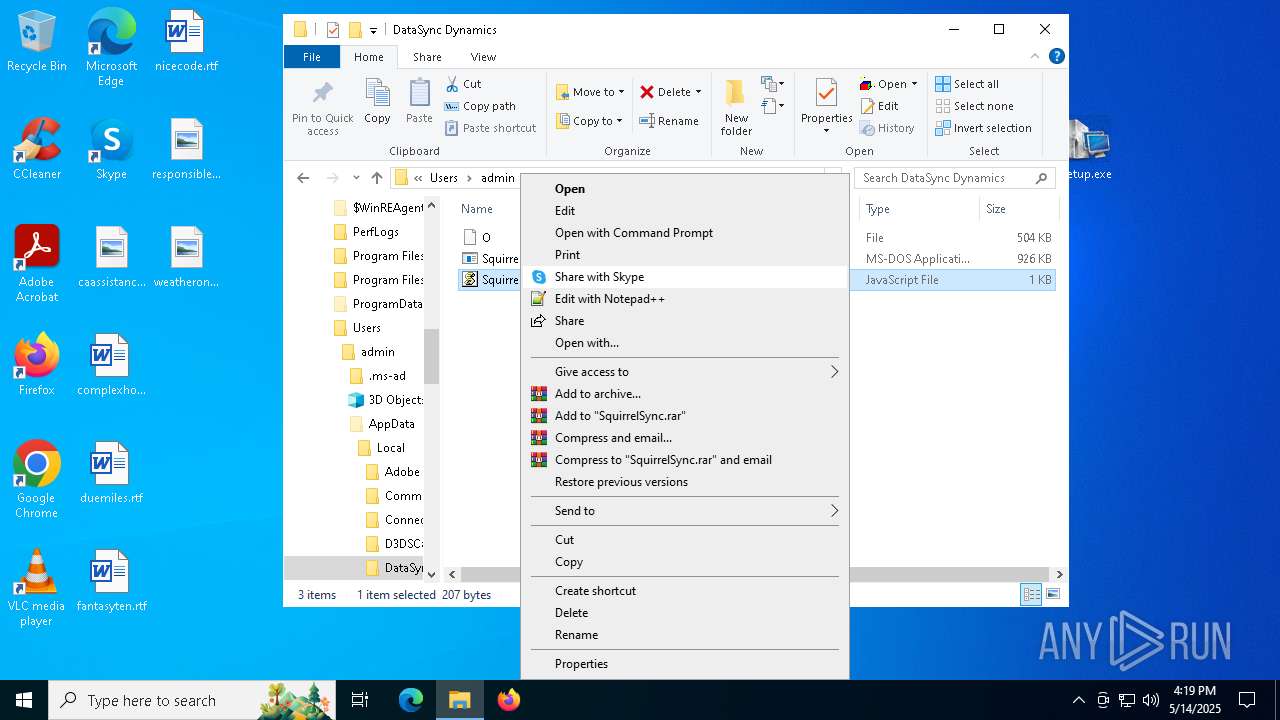
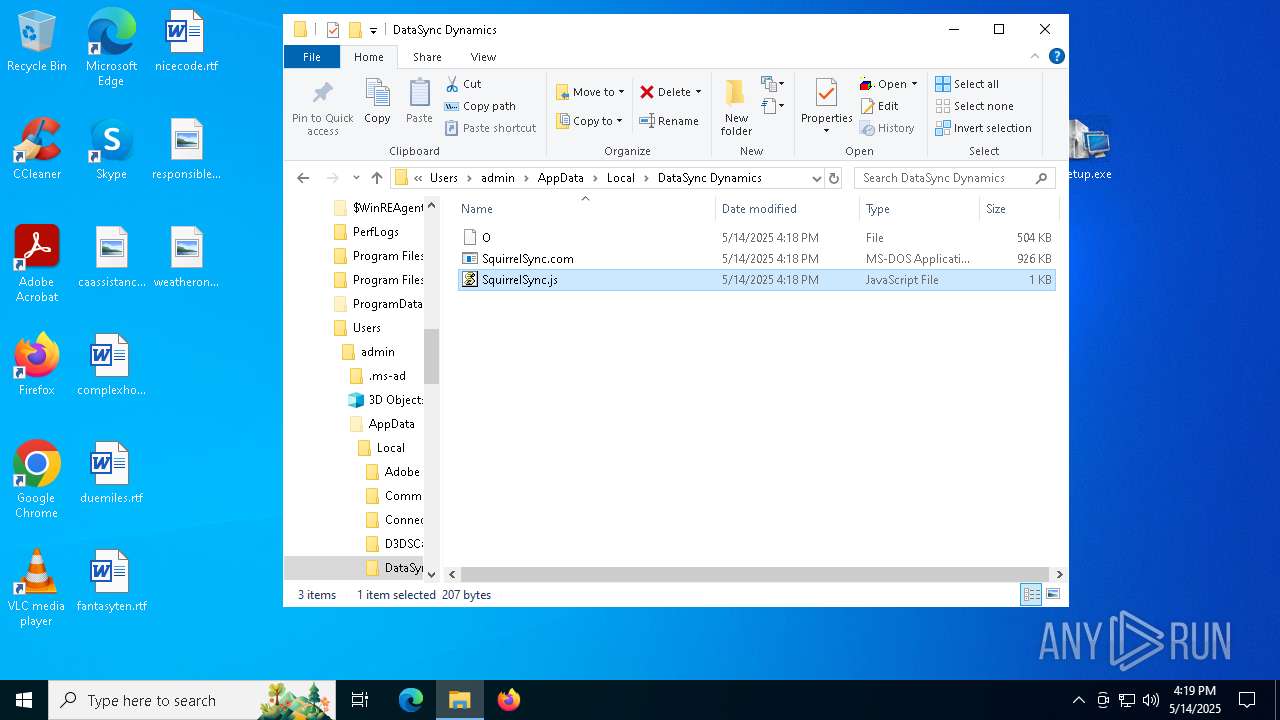
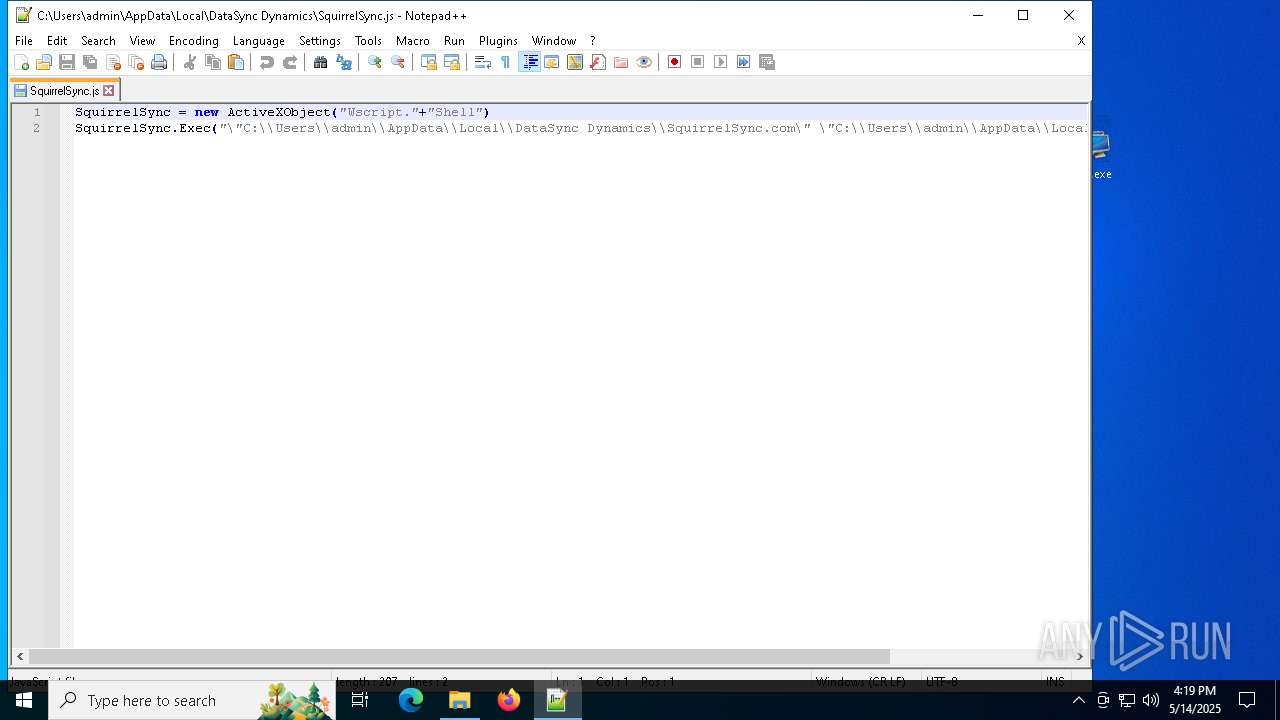
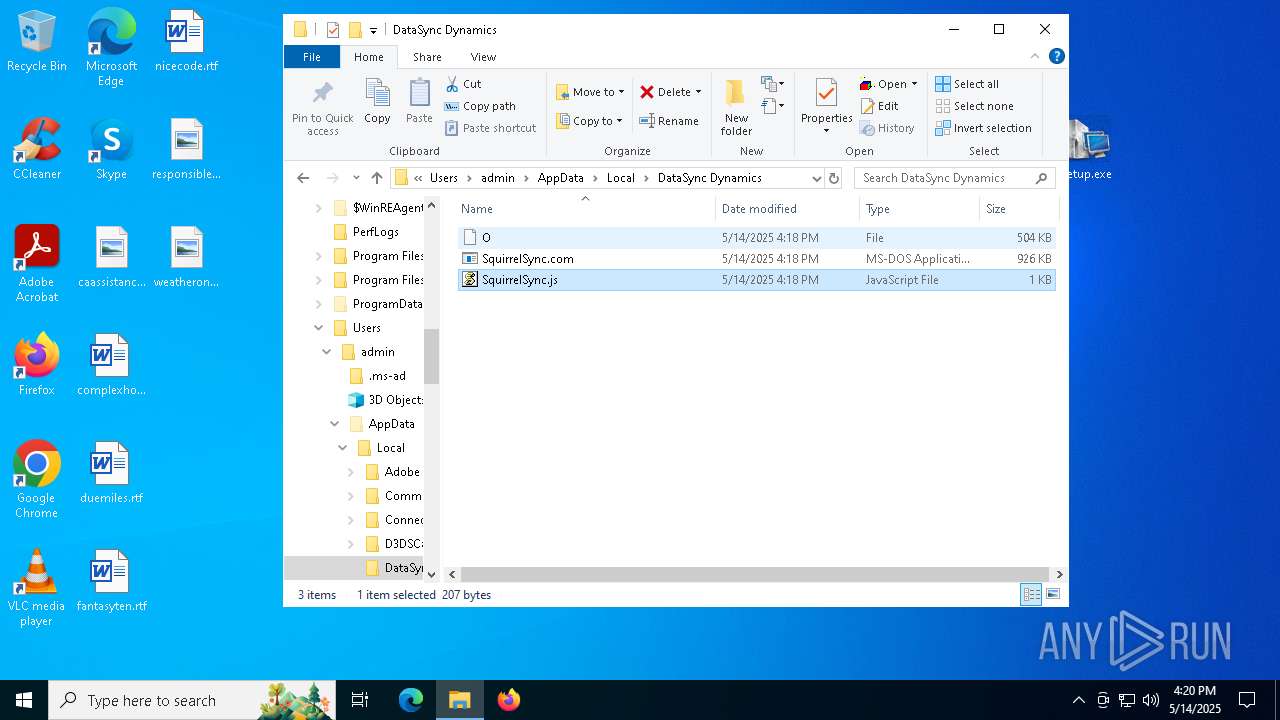
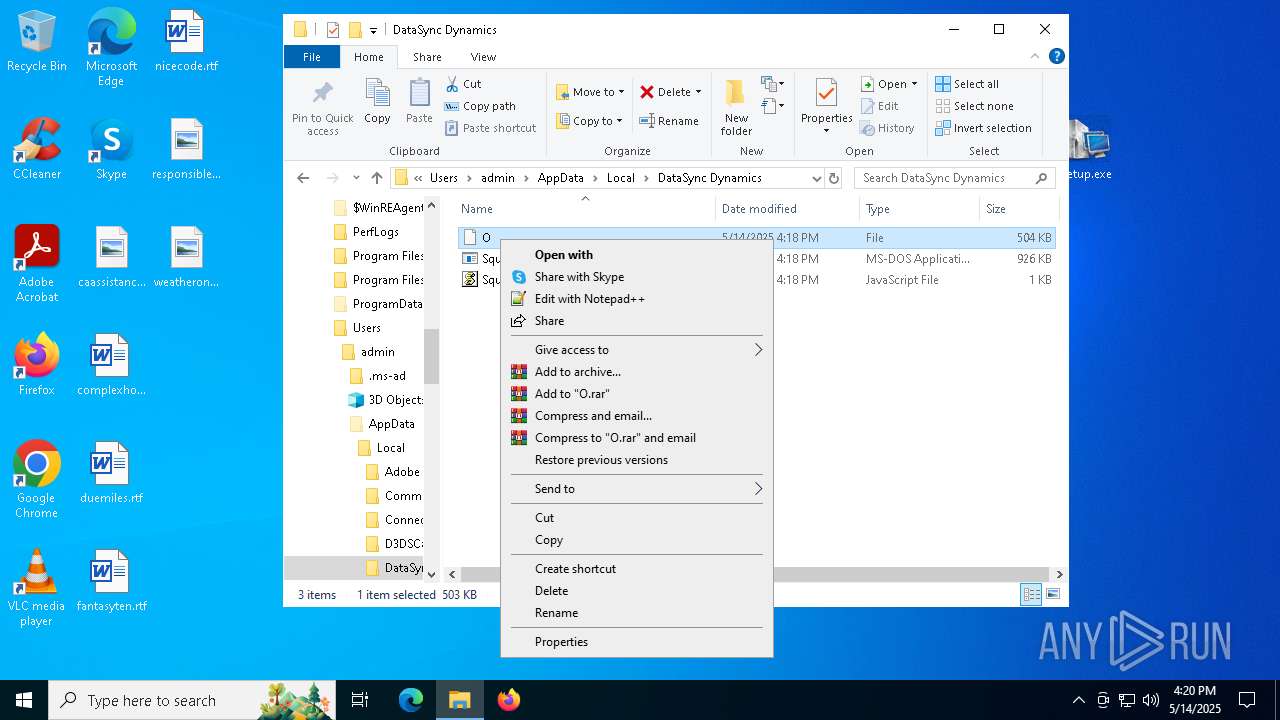
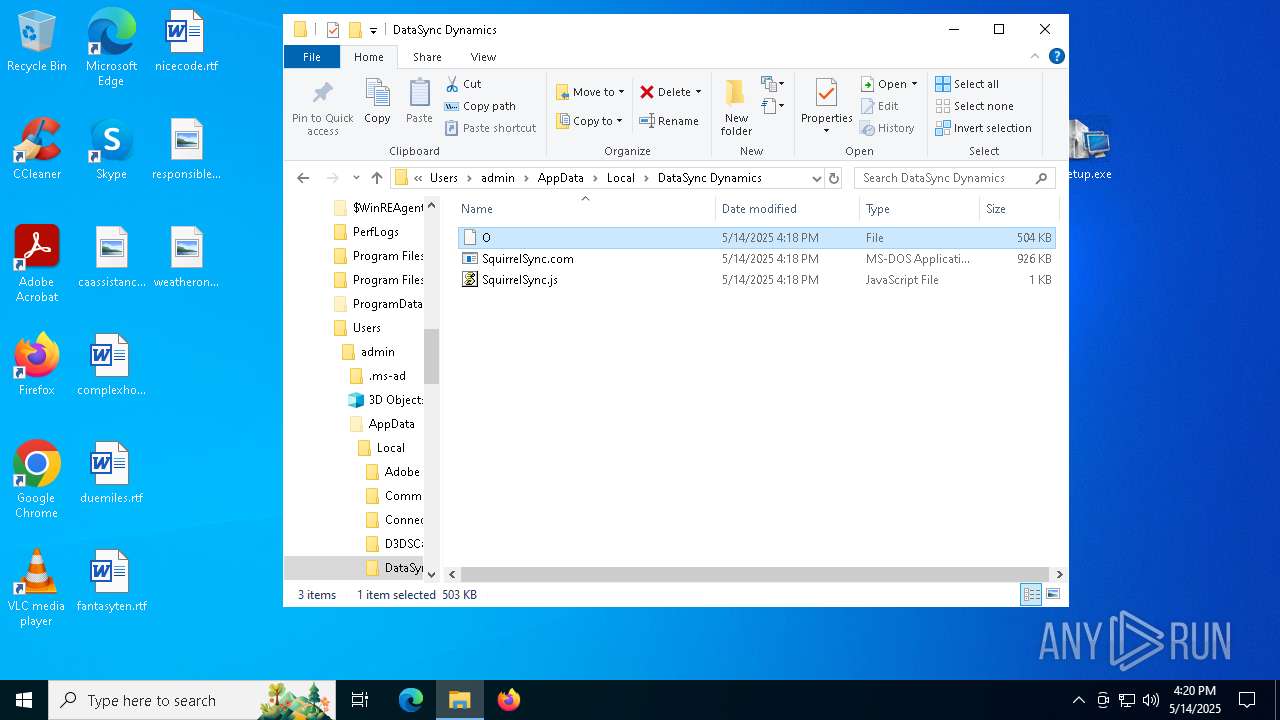
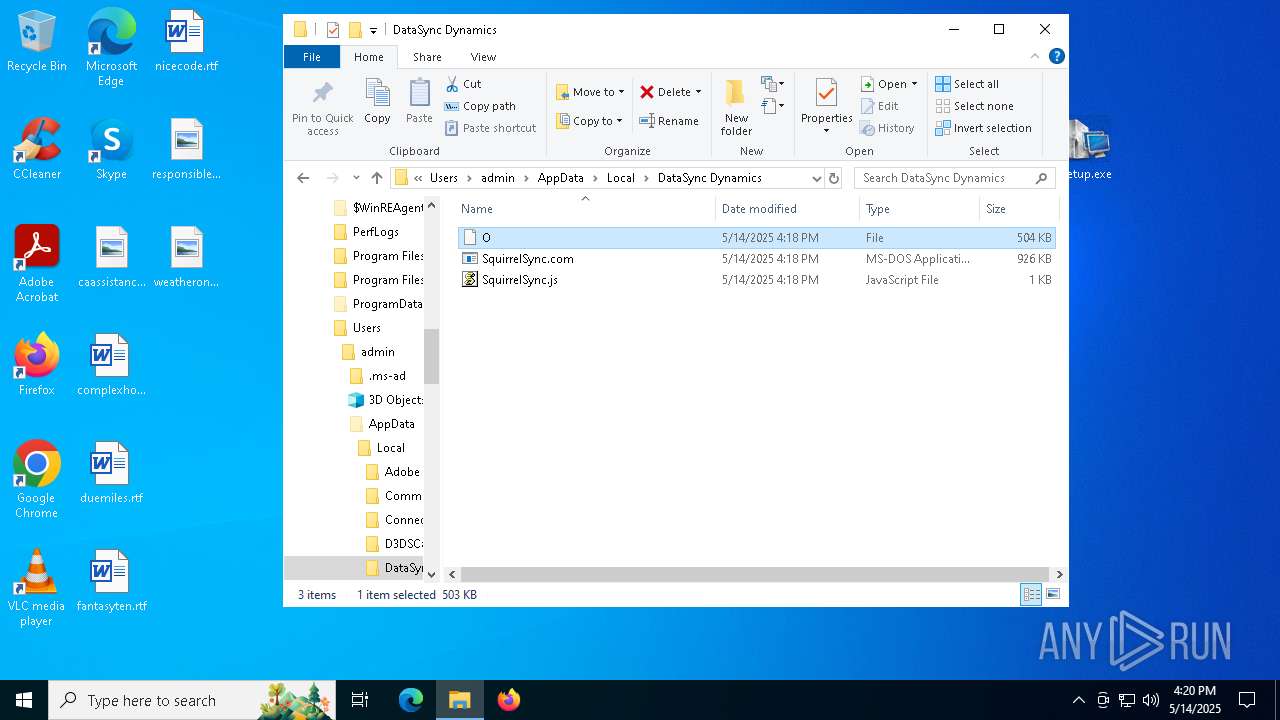
| 736 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\AppData\Local\DataSync Dynamics\SquirrelSync.js" | C:\Program Files\Notepad++\notepad++.exe | — | explorer.exe | |||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.91 Modules
| |||||||||||||||
| 864 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5348 -childID 7 -isForBrowser -prefsHandle 4408 -prefMapHandle 4416 -prefsLen 31324 -prefMapSize 244583 -jsInitHandle 1356 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {3ccd3566-d344-4c76-85ce-577054397785} 7612 "\\.\pipe\gecko-crash-server-pipe.7612" 18aa1924f50 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 1228 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\DataSync Dynamics\SquirrelSync.js" | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 1628 | cmd /c copy /b ..\Carolina.dif + ..\Bit.dif + ..\Requests.dif + ..\Reaching.dif + ..\Naked.dif + ..\Dictionary.dif + ..\Examine.dif + ..\Floors.dif I | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2040 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4584 -childID 9 -isForBrowser -prefsHandle 6108 -prefMapHandle 6104 -prefsLen 31321 -prefMapSize 244583 -jsInitHandle 1256 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {156d8470-1b42-4546-9a2b-04185f25d883} 4012 "\\.\pipe\gecko-crash-server-pipe.4012" 1966d512f50 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 2320 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2340 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4716 -childID 3 -isForBrowser -prefsHandle 4692 -prefMapHandle 4620 -prefsLen 31321 -prefMapSize 244583 -jsInitHandle 1256 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {f39ceafd-4bb4-438d-aa89-085ba16cc446} 4012 "\\.\pipe\gecko-crash-server-pipe.4012" 19667544d90 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 2656 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
41 642
Read events
41 578
Write events
63
Delete events
1
Modification events
| (PID) Process: | (7612) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (4164) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (4164) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4164) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4164) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
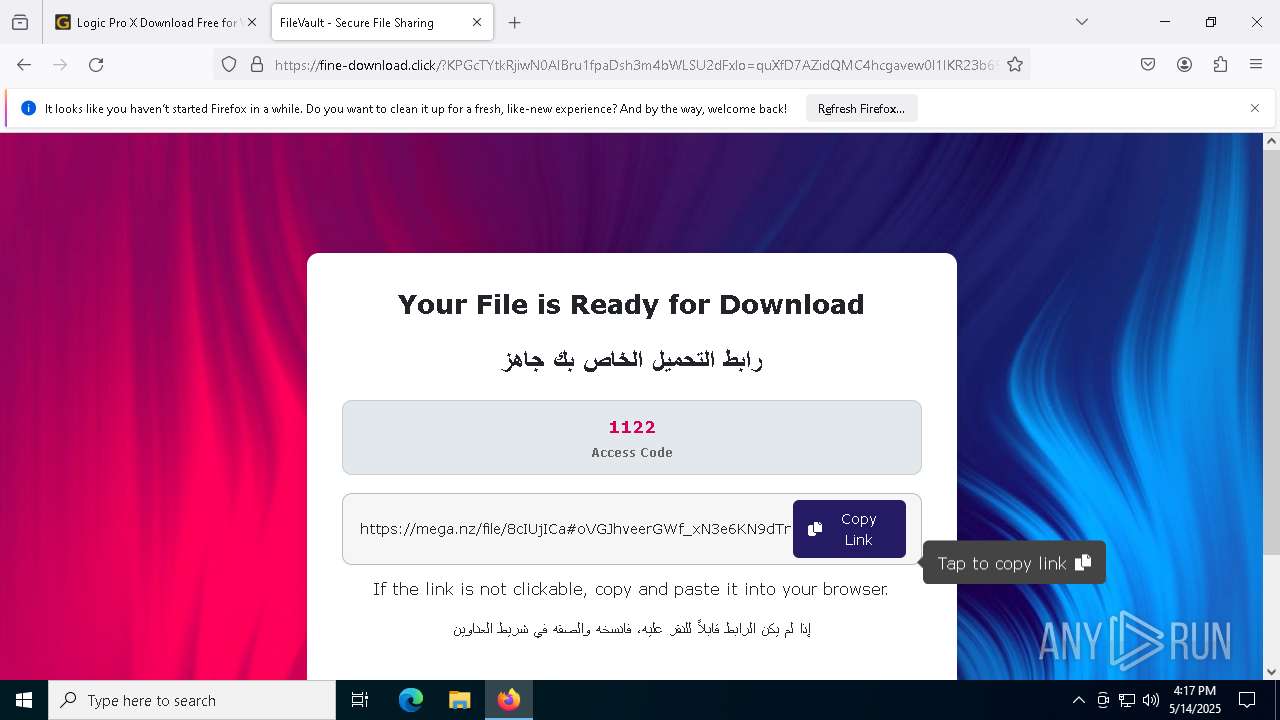
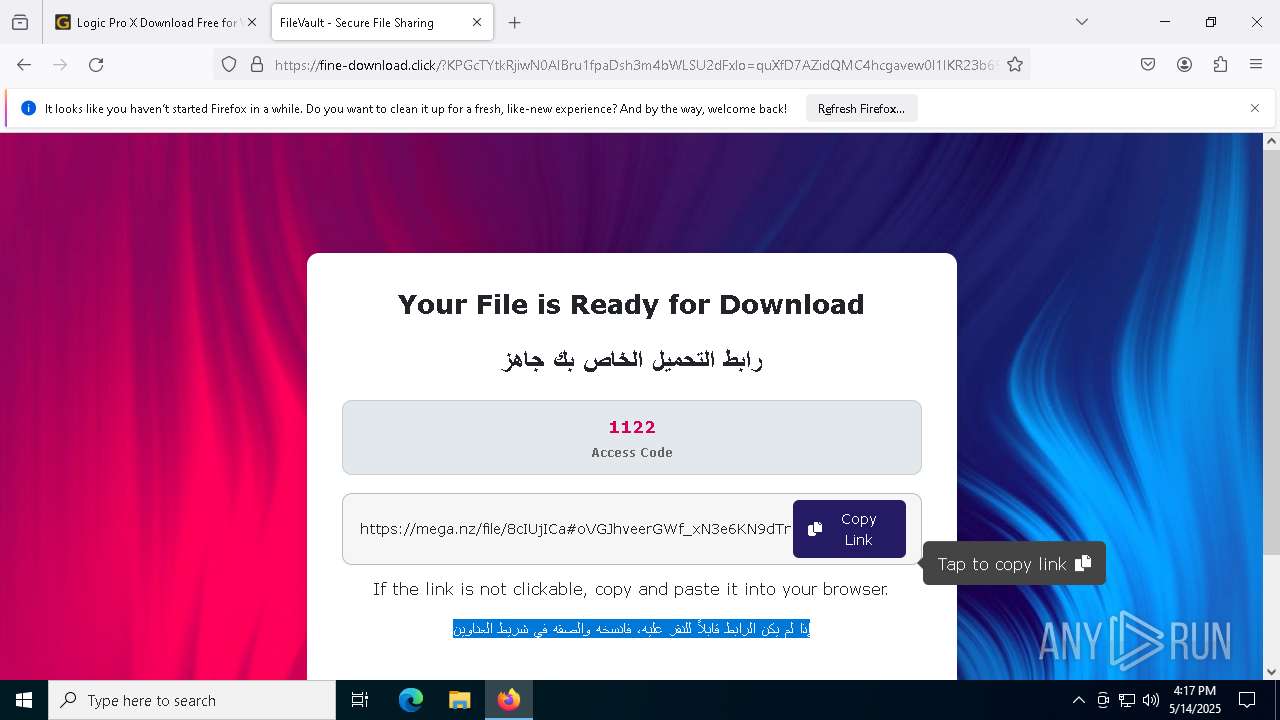
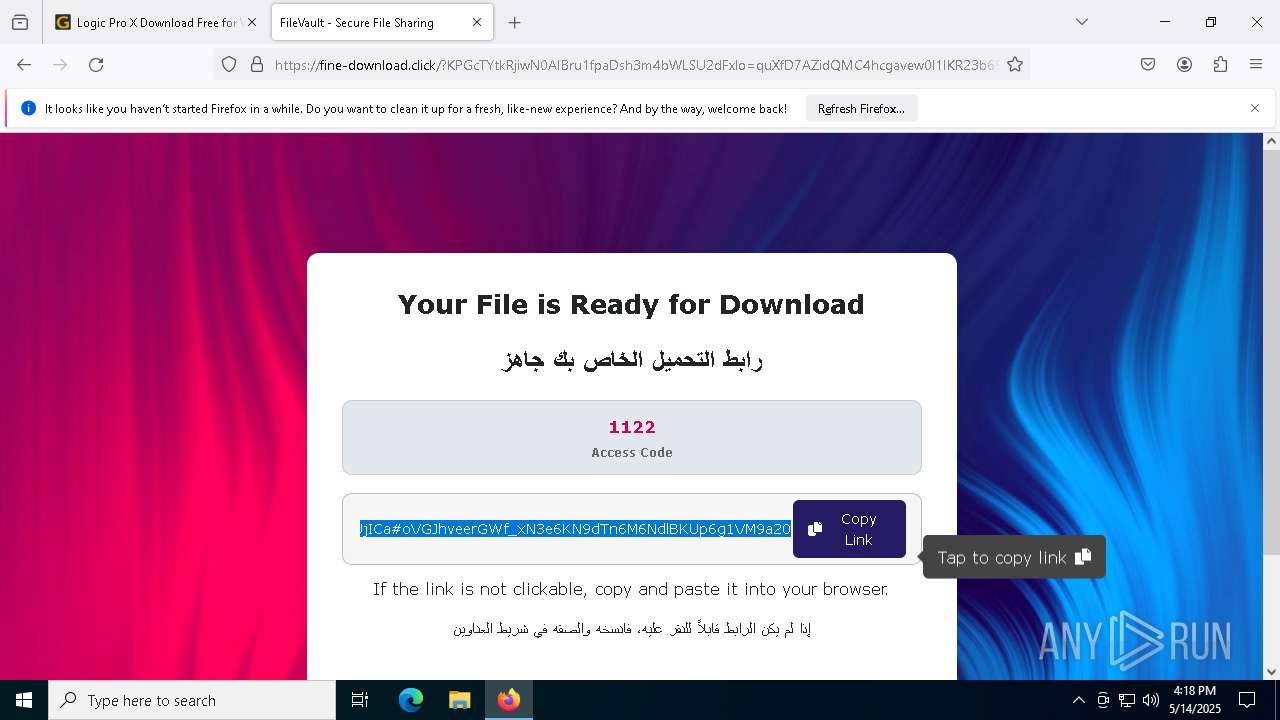
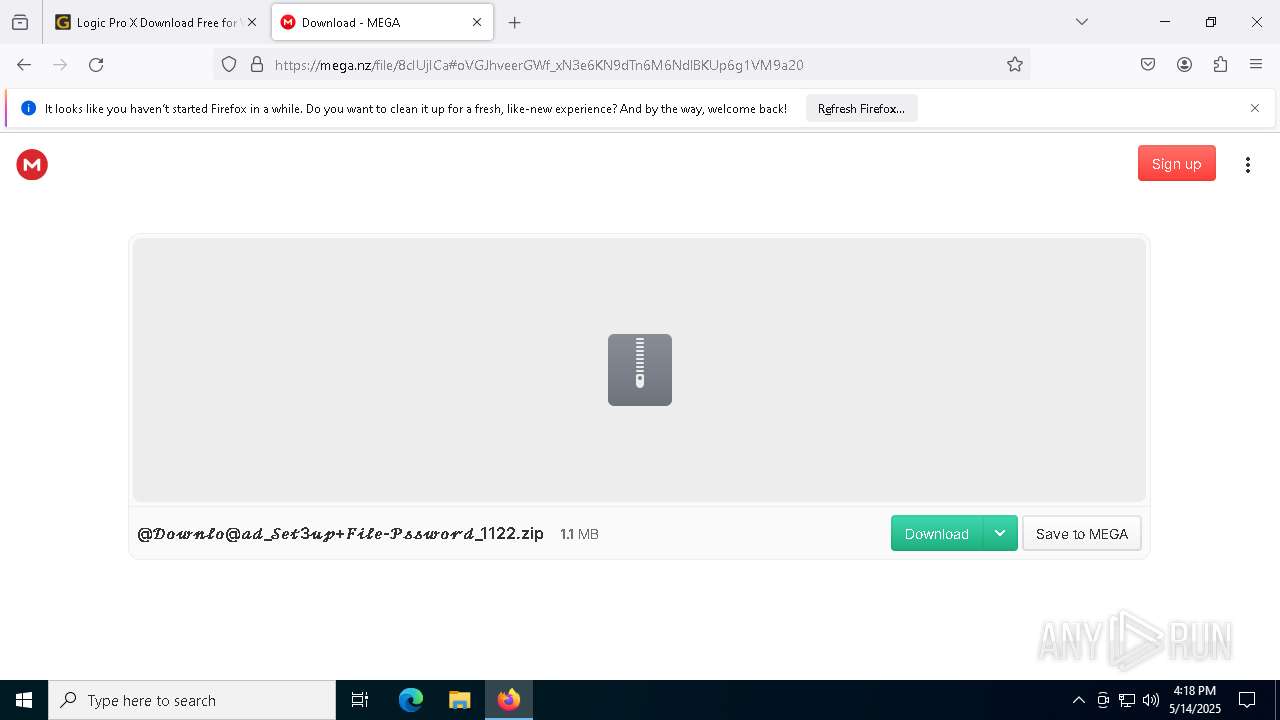
Value: C:\Users\admin\Downloads\@𝒟𝑜𝓌𝓃𝓁𝑜@𝒶𝒹_𝒮𝑒𝓉3𝓊𝓅+𝐹𝒾𝓁𝑒-𝒫𝓈𝓈𝓌𝑜𝓇𝒹_1122.zip | |||
| (PID) Process: | (4164) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4164) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4164) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4164) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6268) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
3
Suspicious files
325
Text files
54
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7612 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 7612 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7612 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-child-current.bin | binary | |
MD5:C95DDC2B1A525D1A243E4C294DA2F326 | SHA256:3A5919E086BFB31E36110CF636D2D5109EB51F2C410B107F126126AB25D67363 | |||
| 7612 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 7612 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs.js | text | |
MD5:0A85C9C5F1FF73951983440E05C375AF | SHA256:8DB4E7A492F54963116530708803979885A07D6429B51ACD39D676CEFEEED2F7 | |||
| 7612 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 7612 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7612 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cert9.db-journal | binary | |
MD5:BBE3A5C4EF4999AE7987245FD037A3E7 | SHA256:EFBEE2D8B2A85828E4D416D7F4A3DD5490AC7BD185A65000E26B4580193839F0 | |||
| 7612 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7612 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cert9.db | binary | |
MD5:6EEAAF3A6364CE5EE1DE4BB4A7DD36DB | SHA256:8F04D3523A4BC73B8F60468DA8F7A68035924E3C7B8F62E44A145C72C74CD51D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
87
TCP/UDP connections
232
DNS requests
241
Threats
29
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.162:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7612 | firefox.exe | POST | 200 | 184.24.77.83:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7612 | firefox.exe | POST | 200 | 216.58.206.35:80 | http://o.pki.goog/s/we1/LaA | unknown | — | — | whitelisted |
7612 | firefox.exe | POST | 200 | 216.58.206.35:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
7612 | firefox.exe | POST | 200 | 184.24.77.83:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
7612 | firefox.exe | POST | 200 | 184.24.77.45:80 | http://e5.o.lencr.org/ | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7612 | firefox.exe | POST | 200 | 184.24.77.45:80 | http://e5.o.lencr.org/ | unknown | — | — | whitelisted |
7612 | firefox.exe | POST | 200 | 216.58.206.35:80 | http://o.pki.goog/s/wr3/3H4 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.48.23.162:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7612 | firefox.exe | 172.67.151.222:443 | getintopc.software | CLOUDFLARENET | US | unknown |
7612 | firefox.exe | 34.36.137.203:443 | contile.services.mozilla.com | — | — | whitelisted |
7612 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
getintopc.software |
| unknown |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
content-signature-2.cdn.mozilla.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
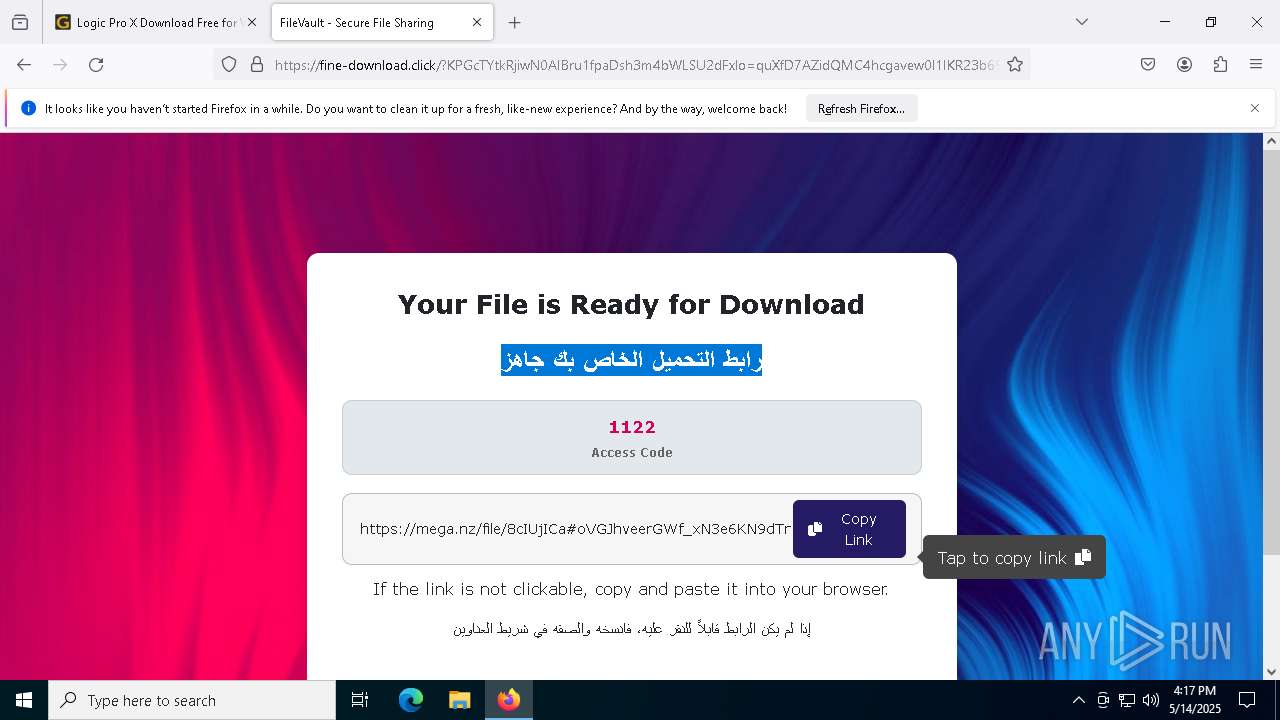
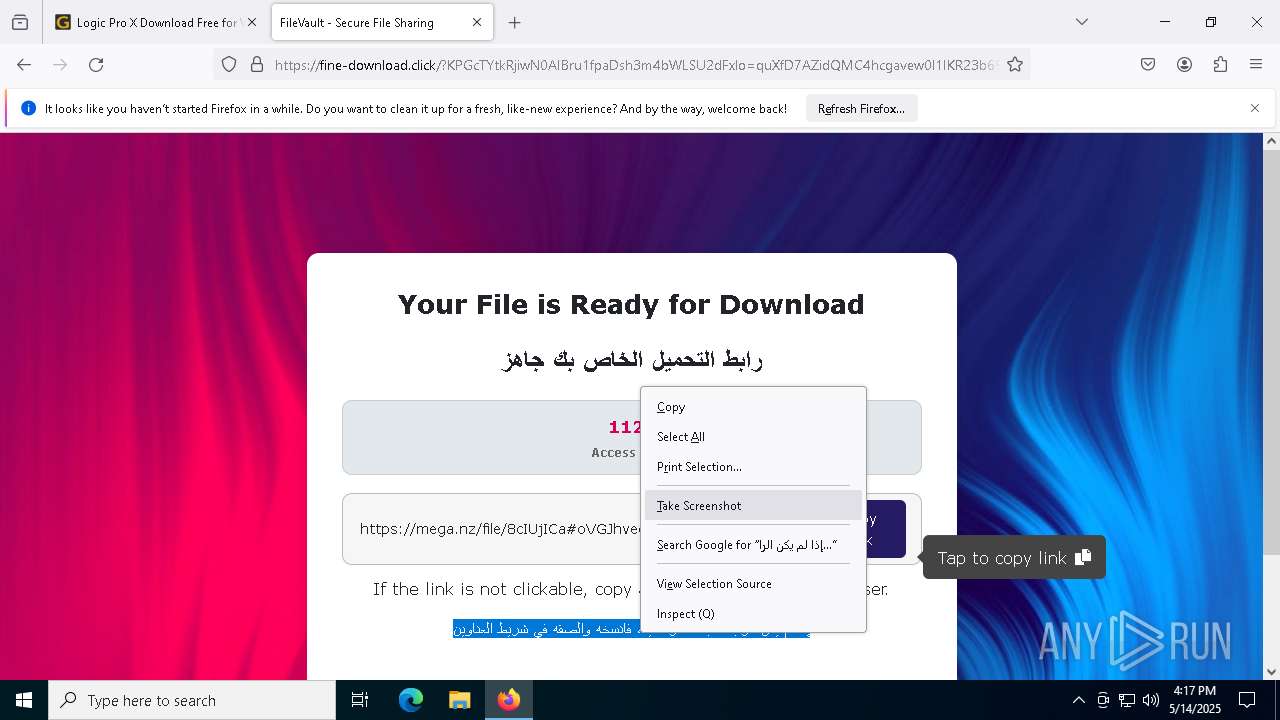
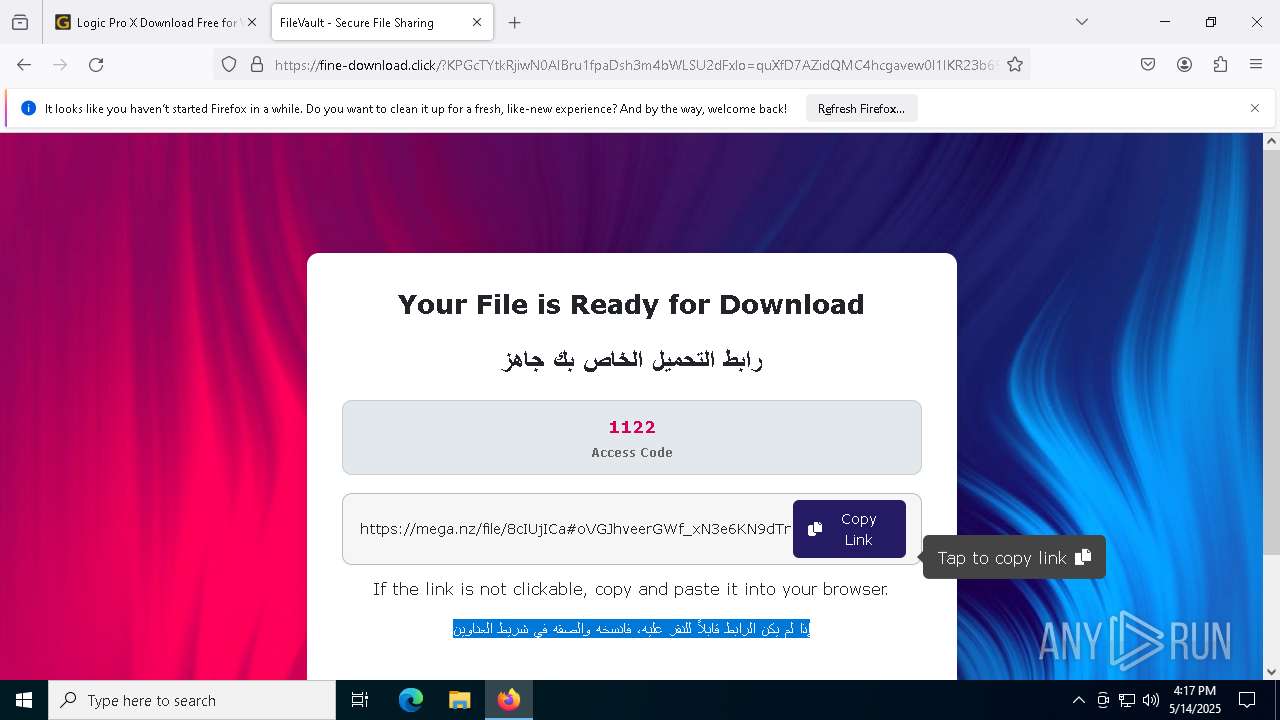
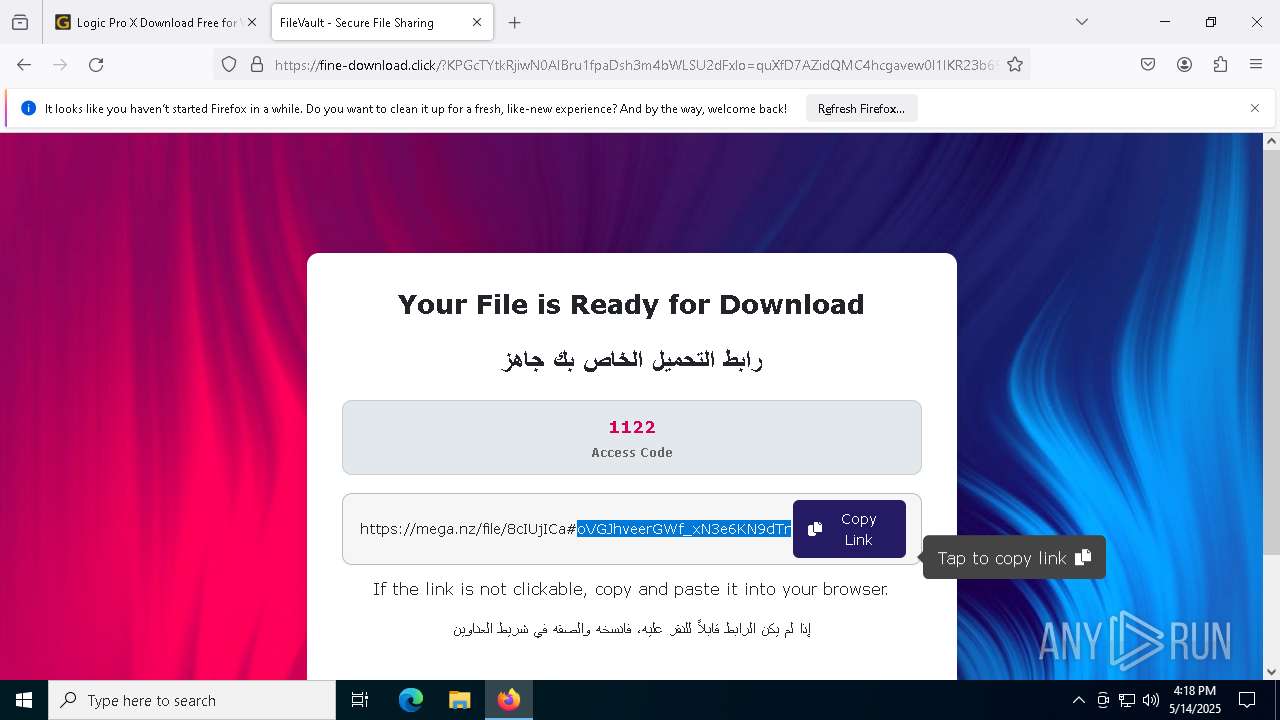
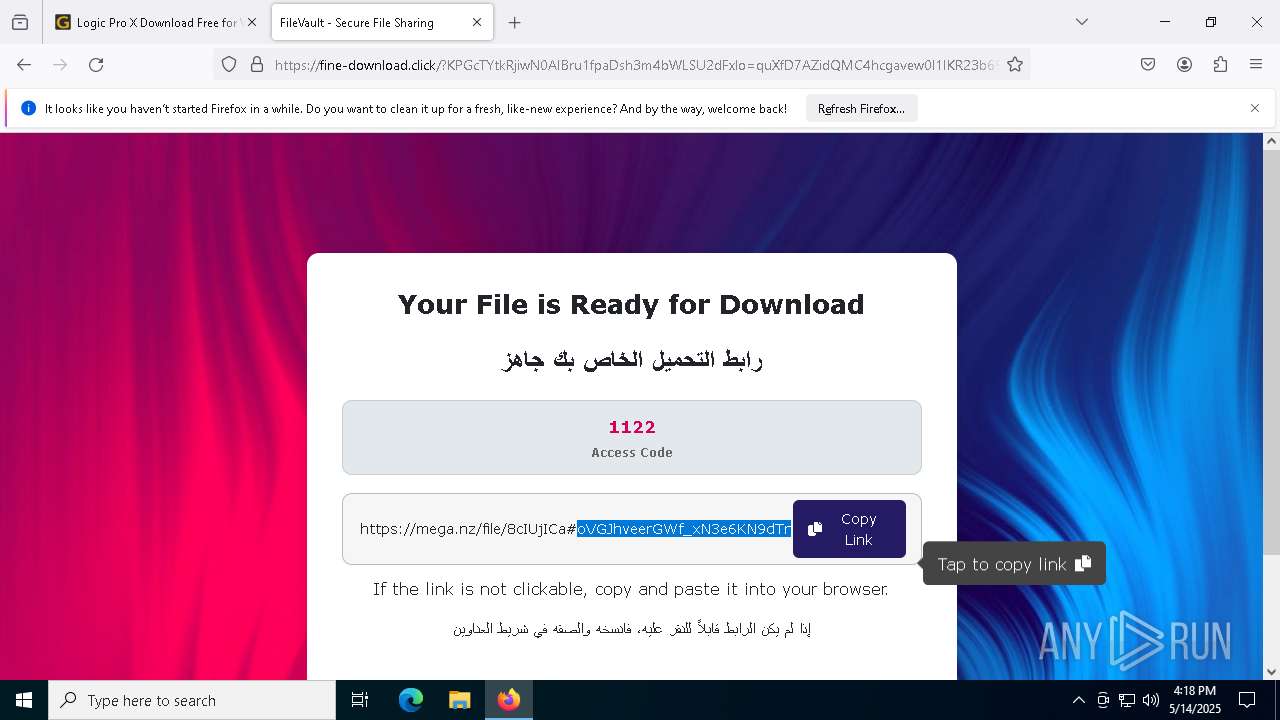
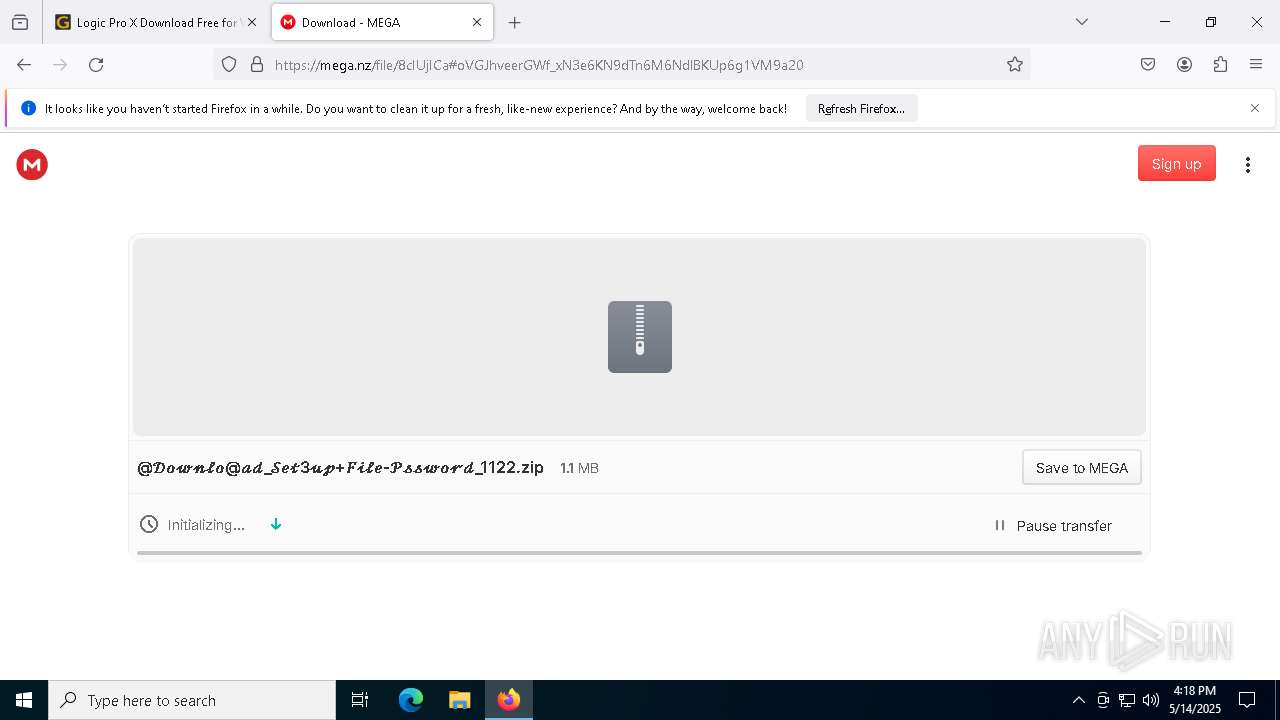
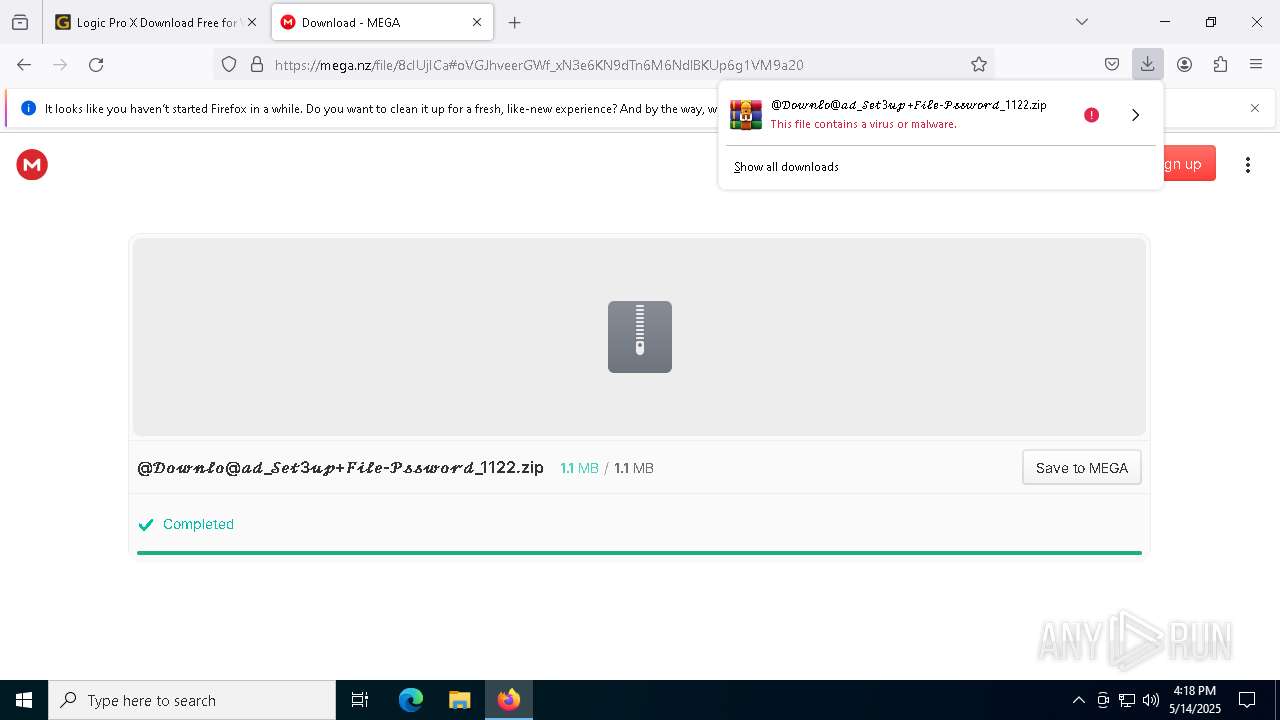
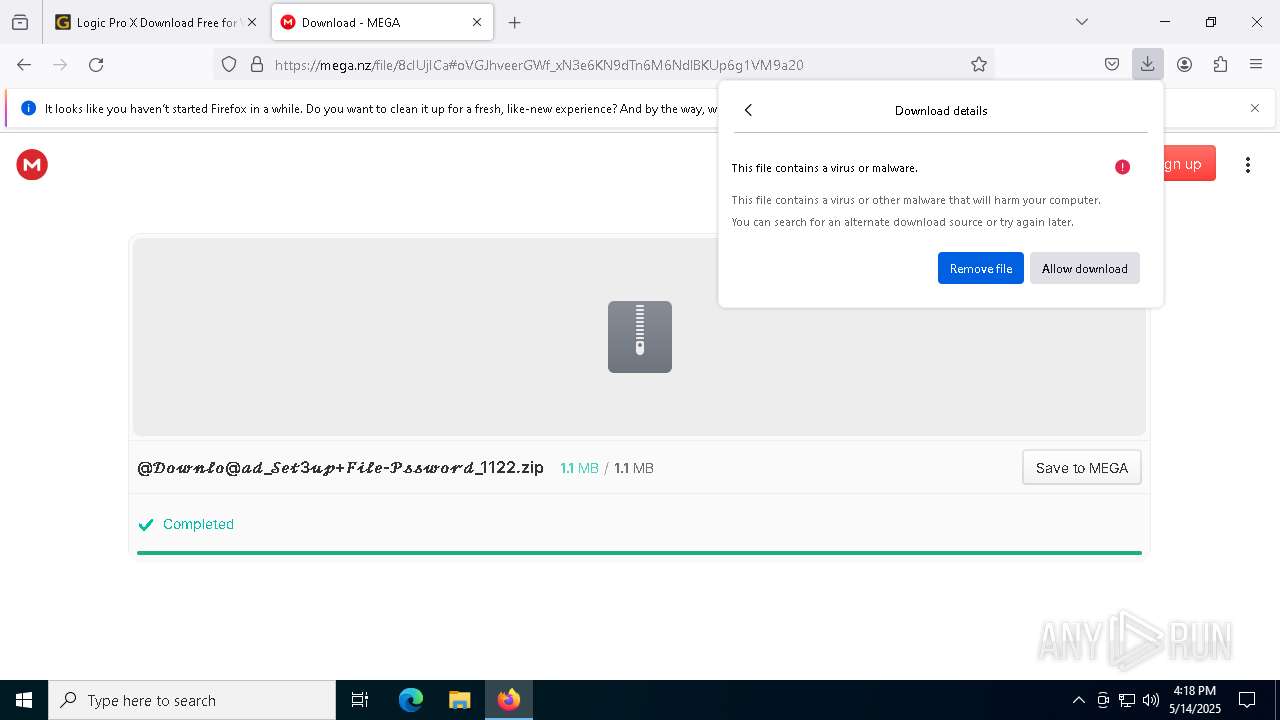
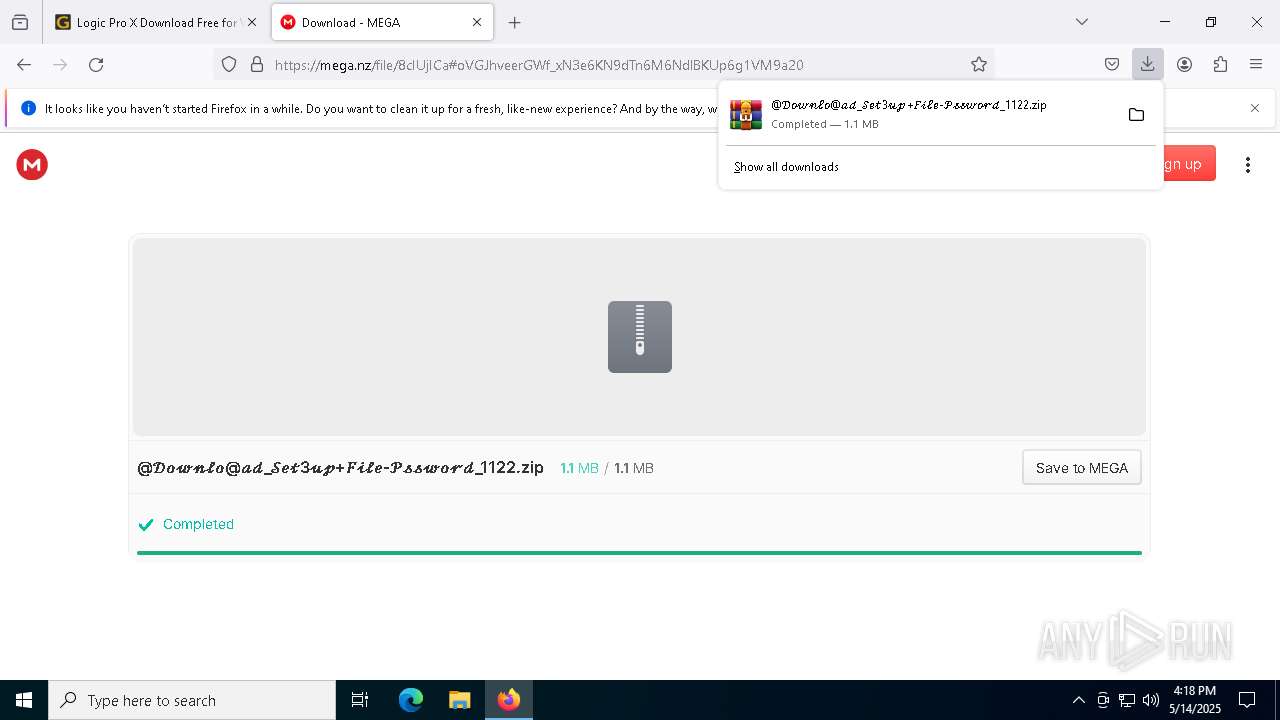
2196 | svchost.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
2196 | svchost.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
2196 | svchost.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |