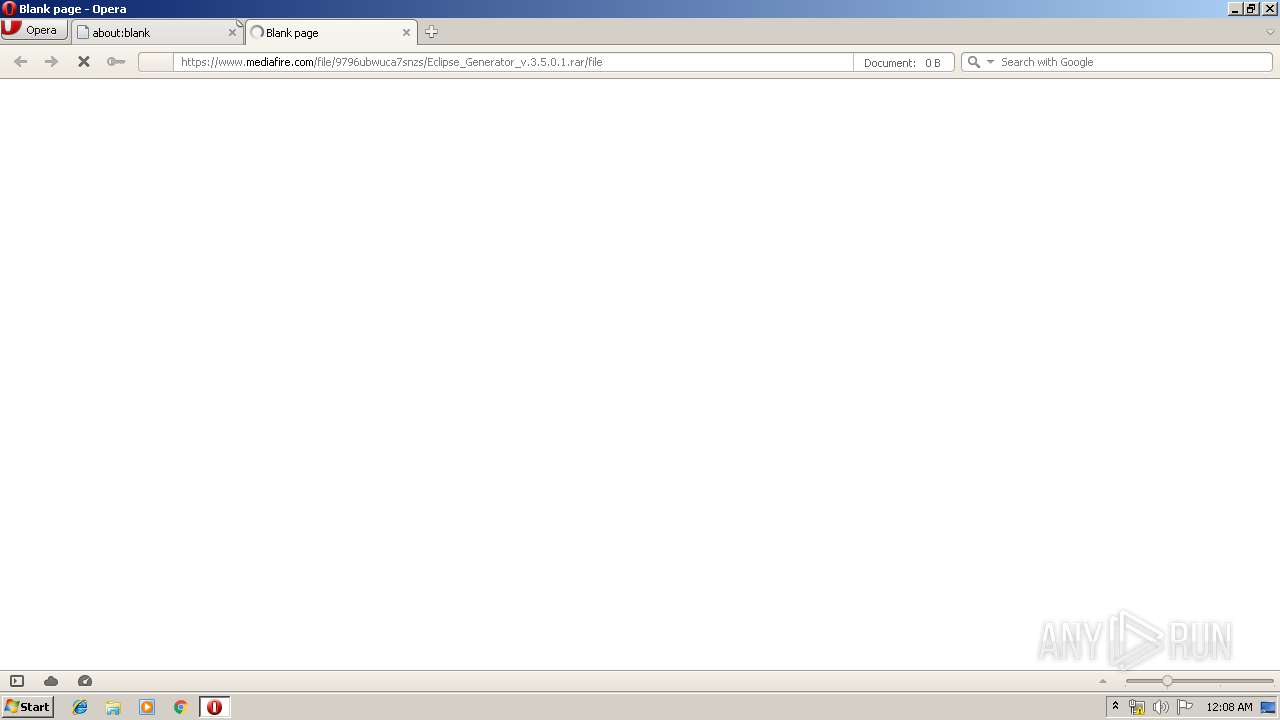
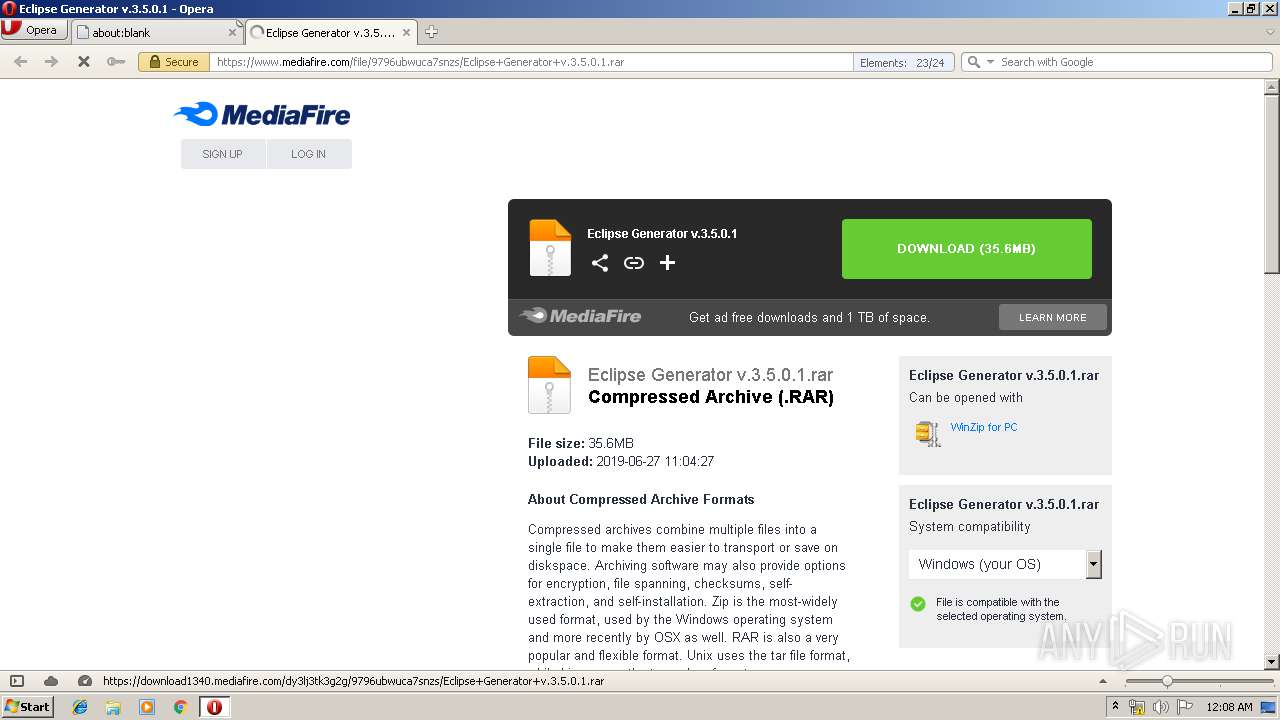
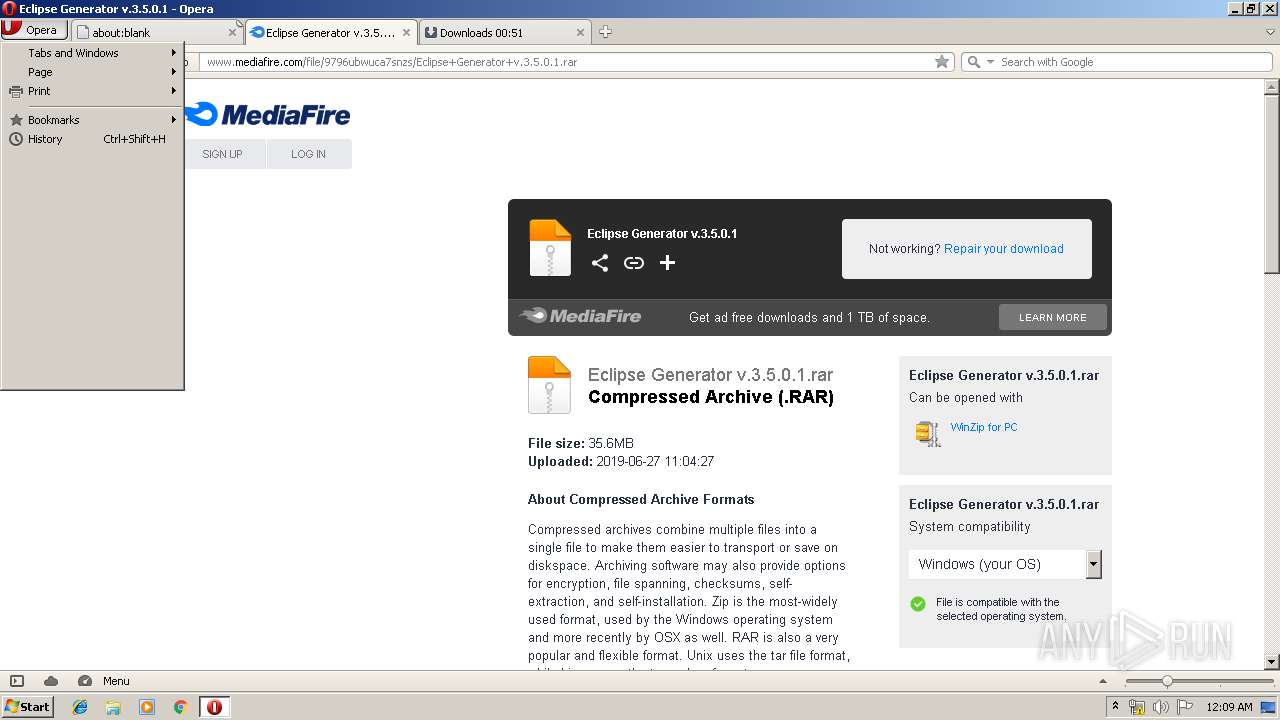
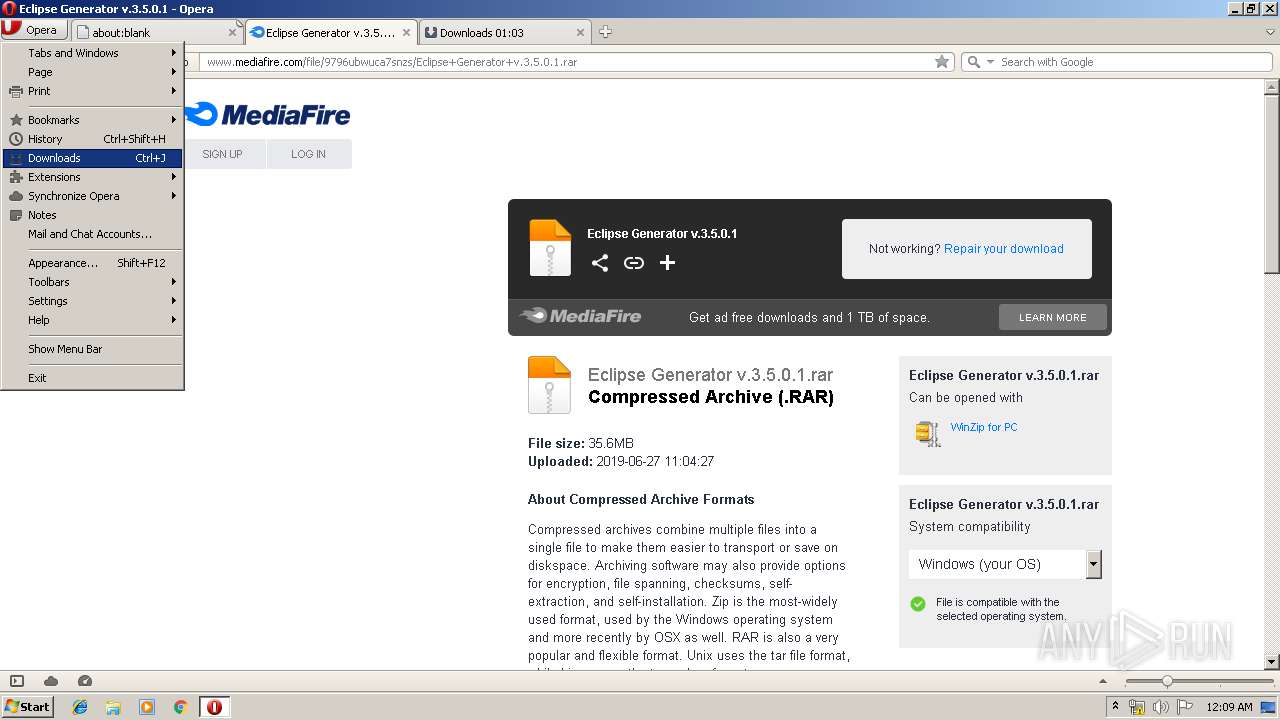
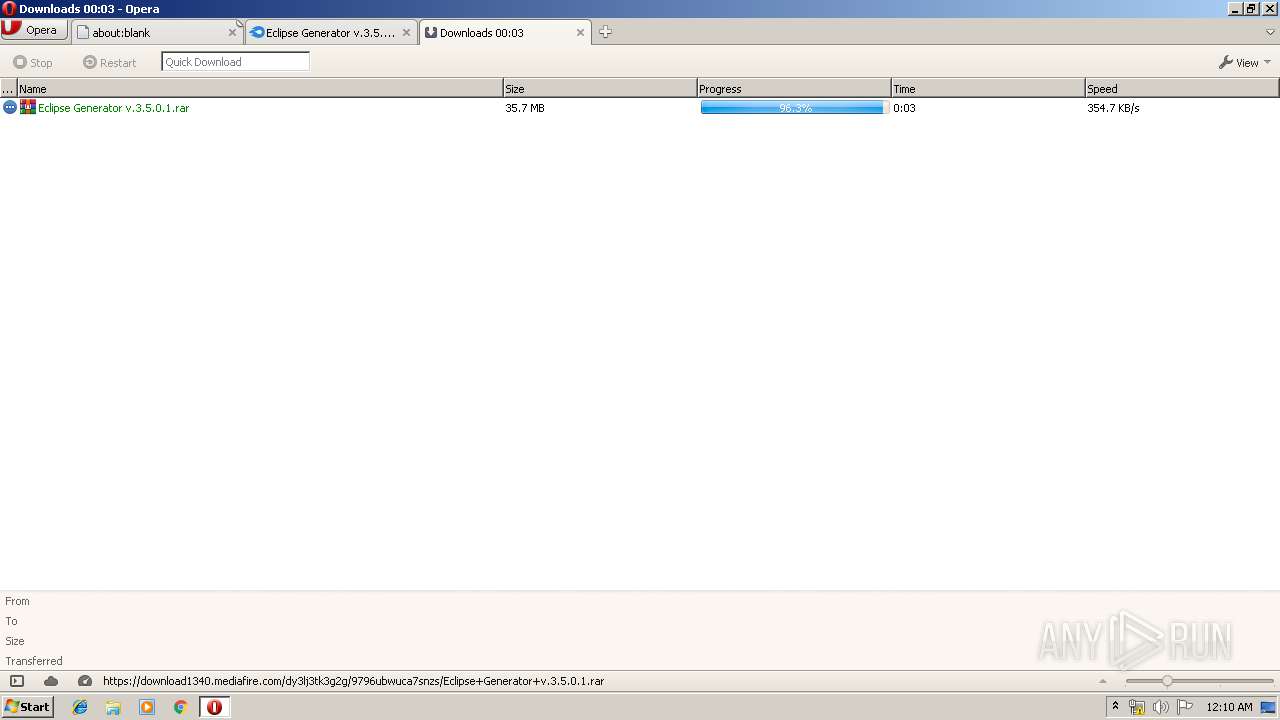
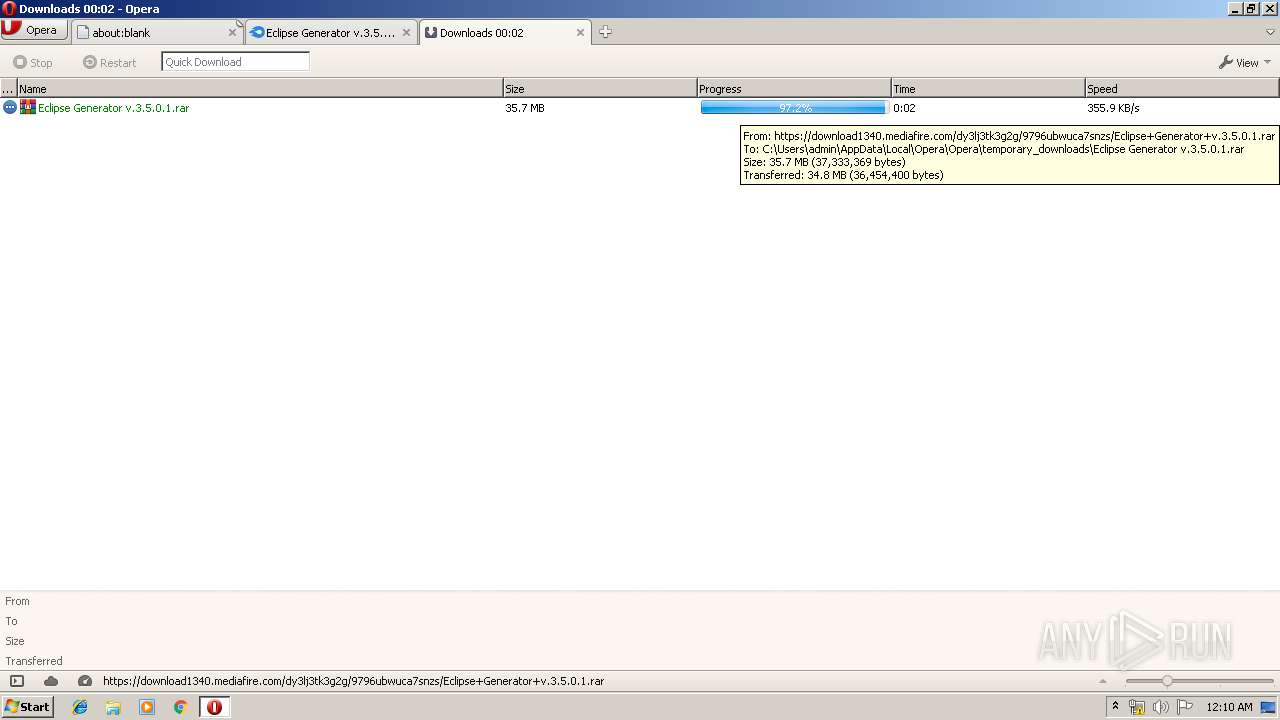
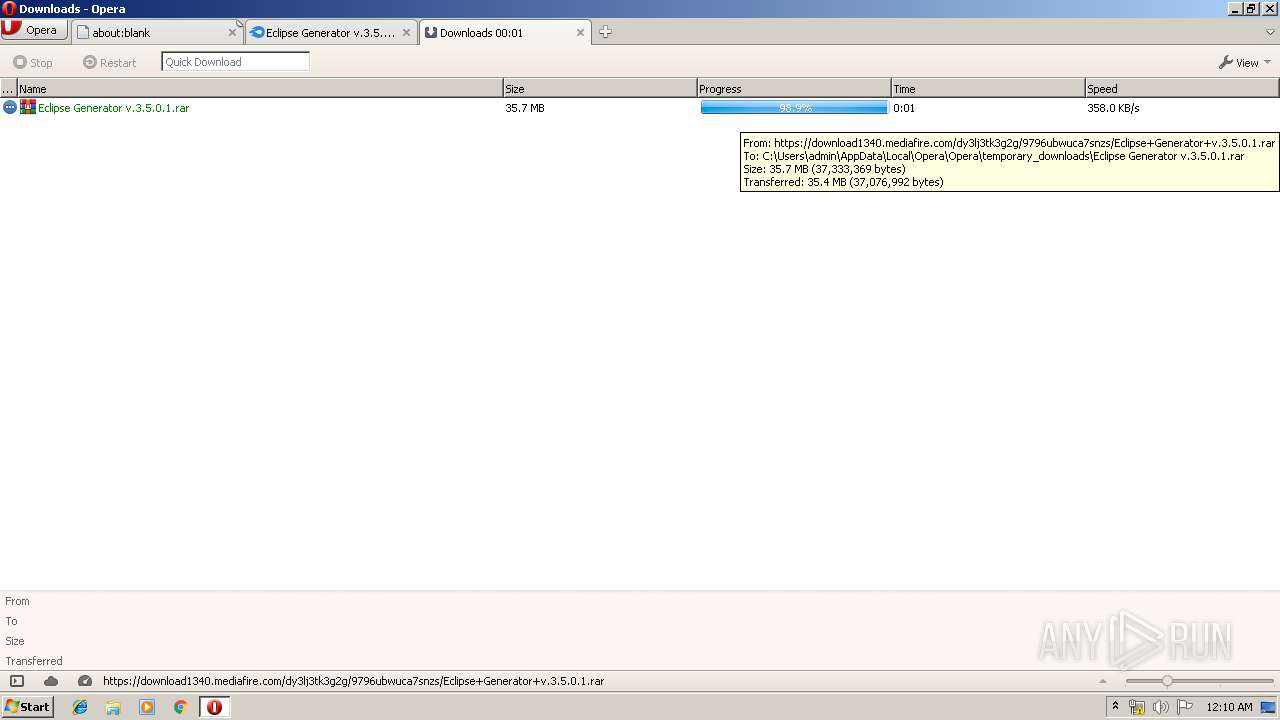
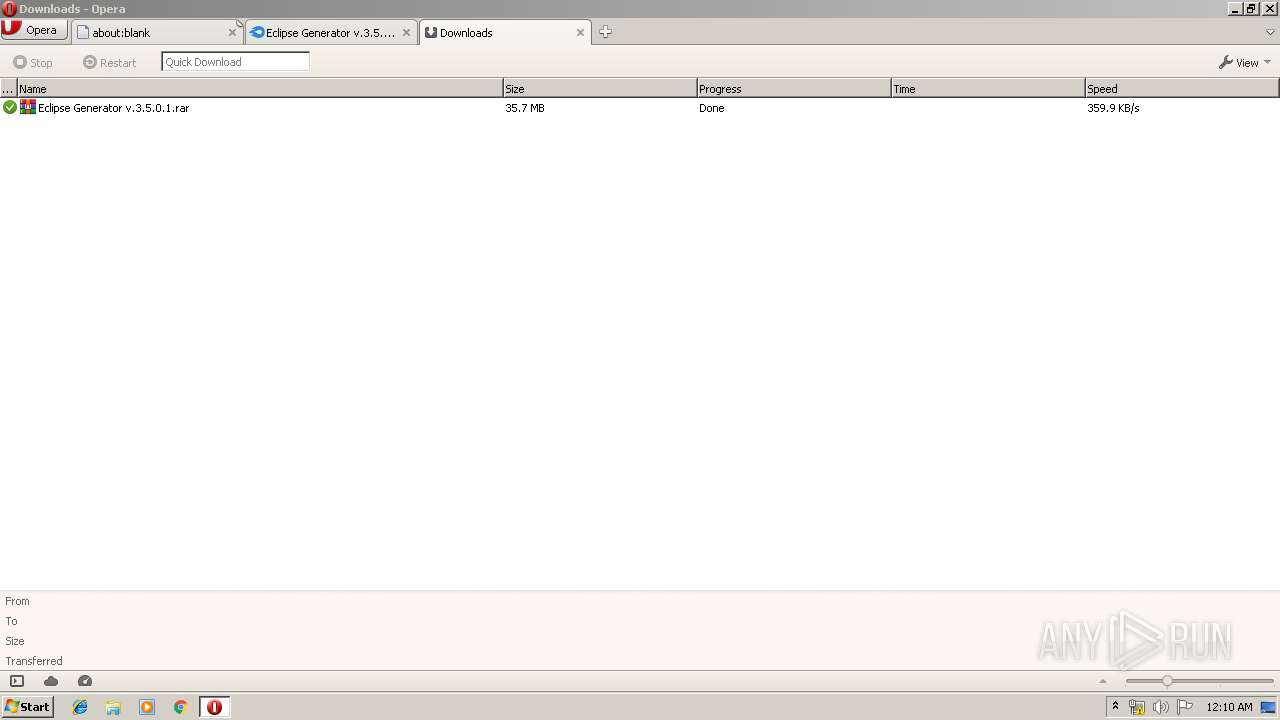
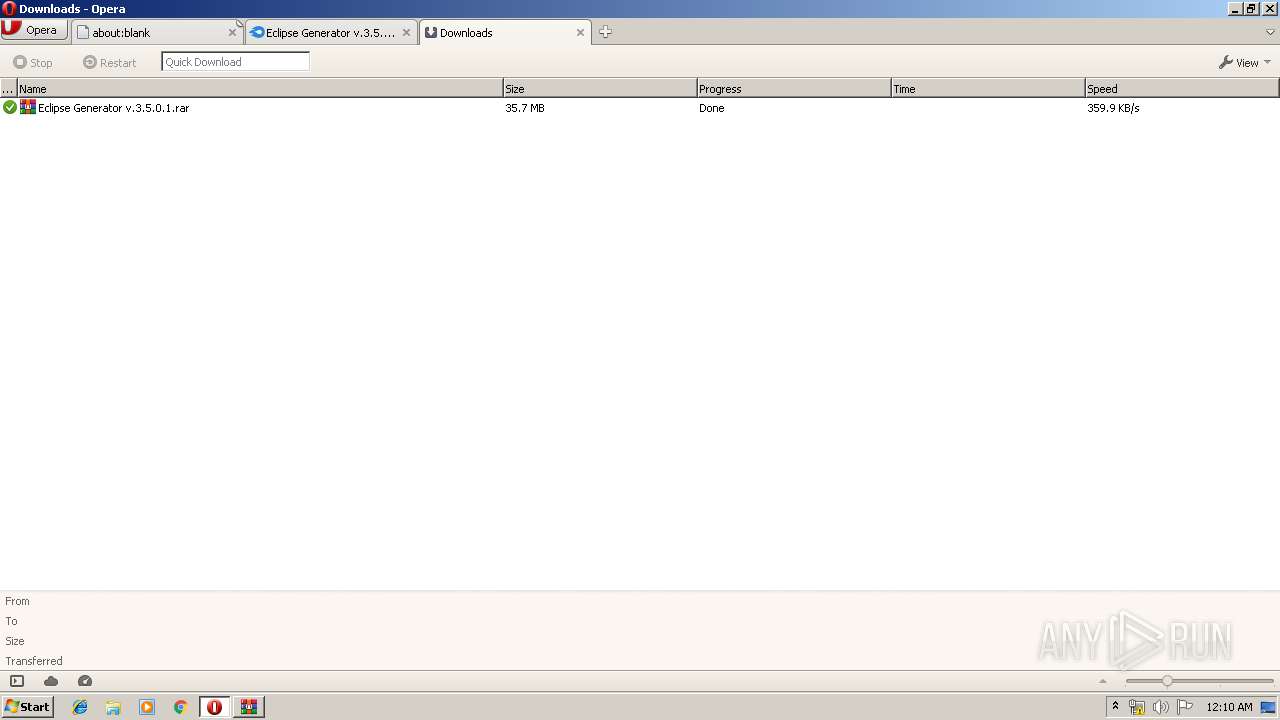
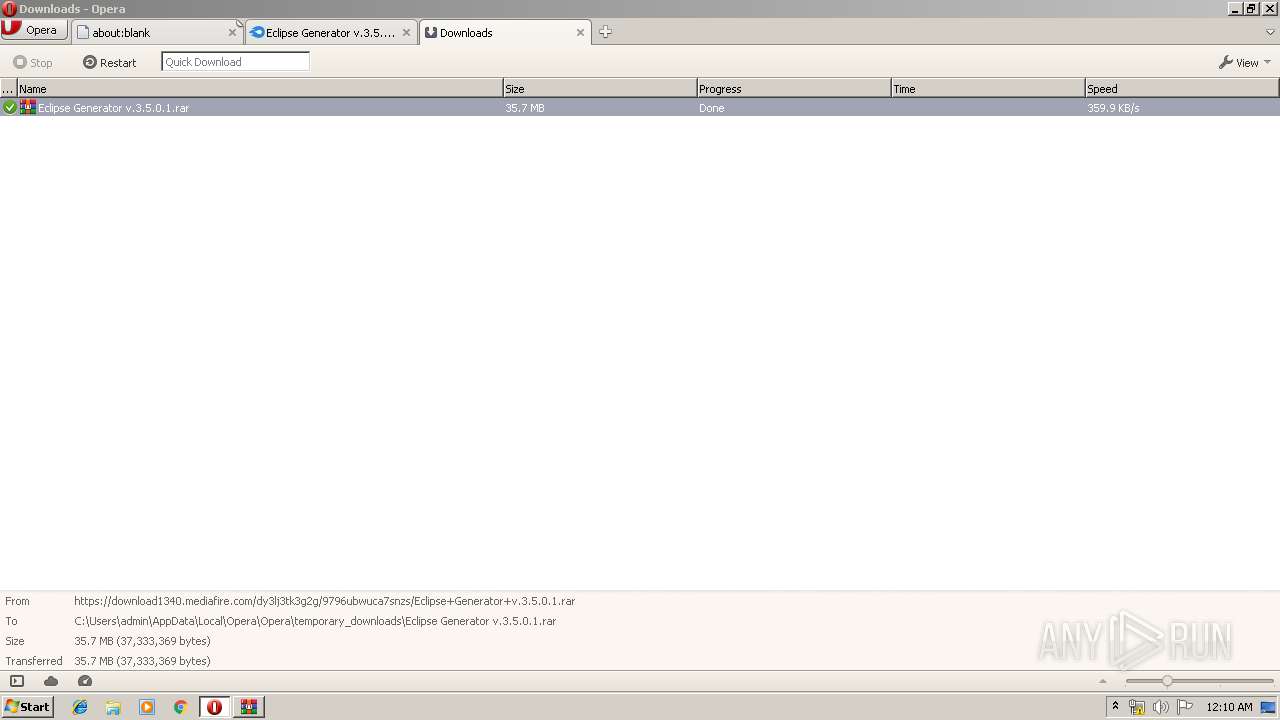
| URL: | https://www.mediafire.com/file/9796ubwuca7snzs/Eclipse_Generator_v.3.5.0.1.rar/file |
| Full analysis: | https://app.any.run/tasks/98fc10ba-309f-454c-b310-3f2045ca7976 |
| Verdict: | Malicious activity |
| Analysis date: | June 28, 2019, 23:08:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | E83C3B2A71C2B5597C4D30B8758D7F96 |
| SHA1: | 28E39FF020D83D350825DC3D1905880452D5F11F |
| SHA256: | 1E4D642B99E54FAE6284BC5FCEC5EC1D209E93AB7590C354199A7F0EDE6D5BF3 |
| SSDEEP: | 3:N8DSLw3eGUocvTRSNVMVHJwLnZfA:2OLw3eG0TmmVydfA |
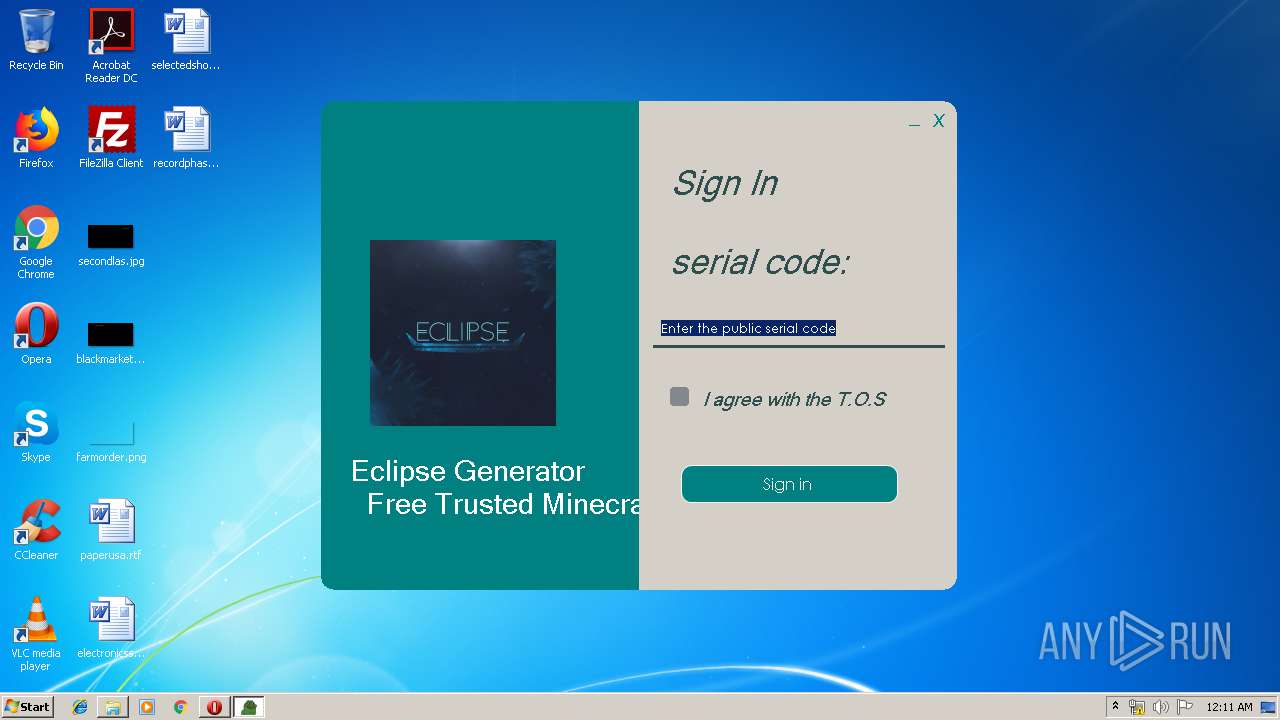
MALICIOUS
Loads dropped or rewritten executable
- Eclipse Generator v3.5.0.1.exe (PID: 2812)
- SearchProtocolHost.exe (PID: 3116)
SUSPICIOUS
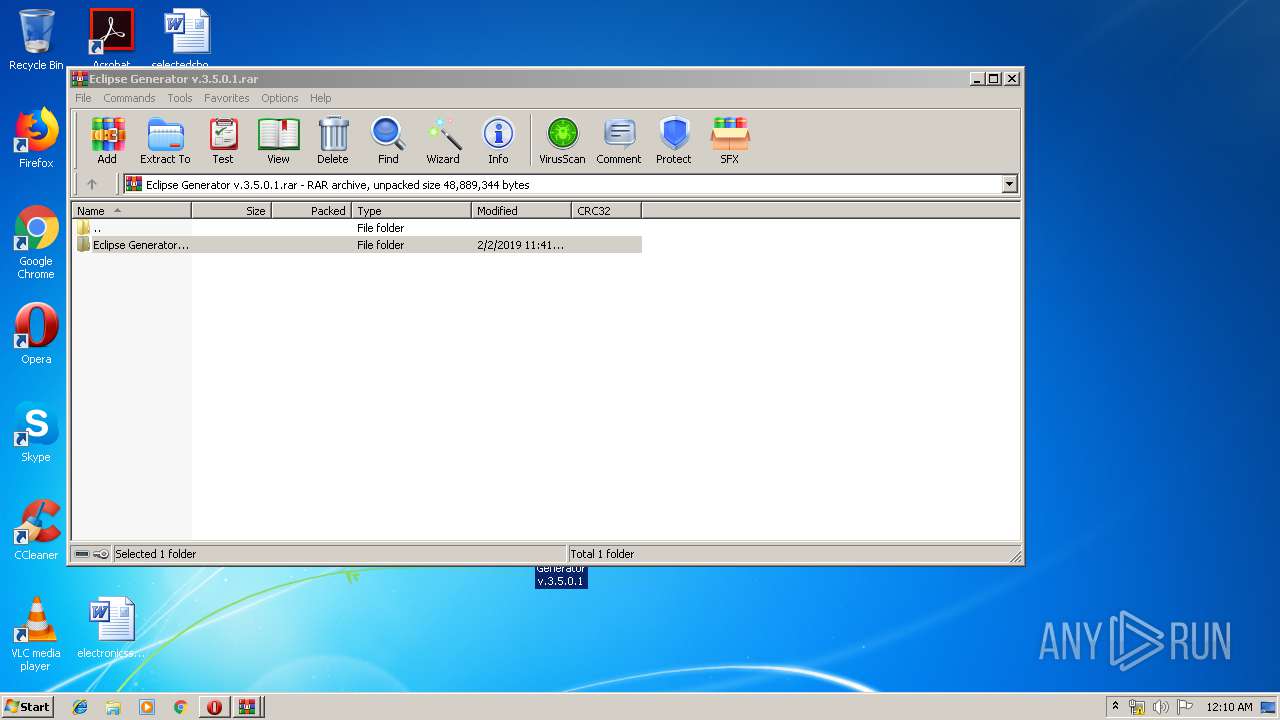
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2632)
INFO
Creates files in the user directory
- opera.exe (PID: 3372)
Dropped object may contain Bitcoin addresses
- opera.exe (PID: 3372)
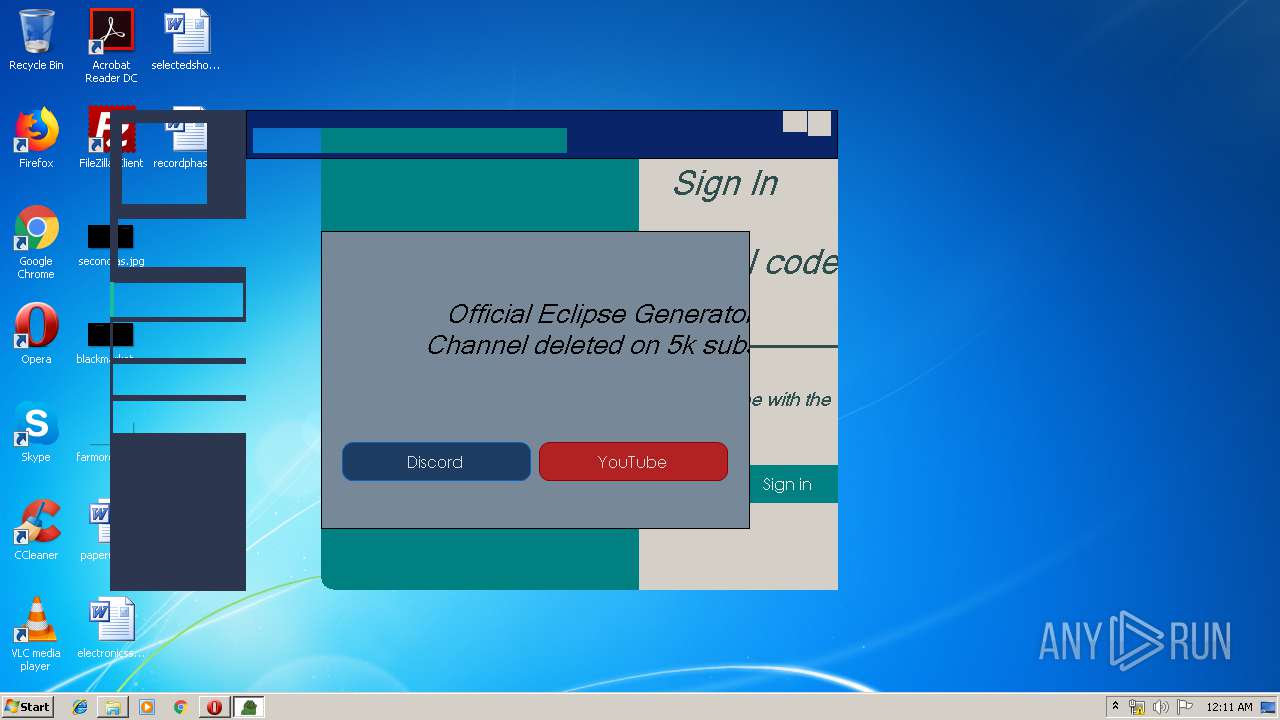
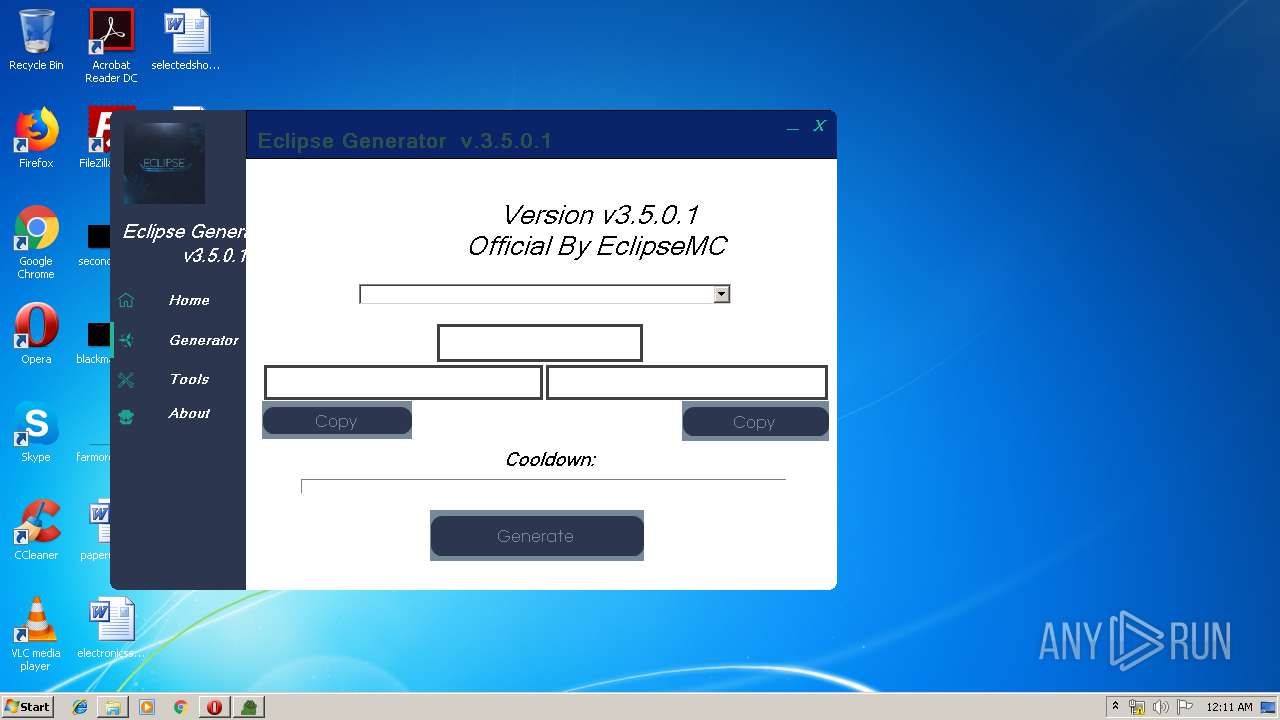
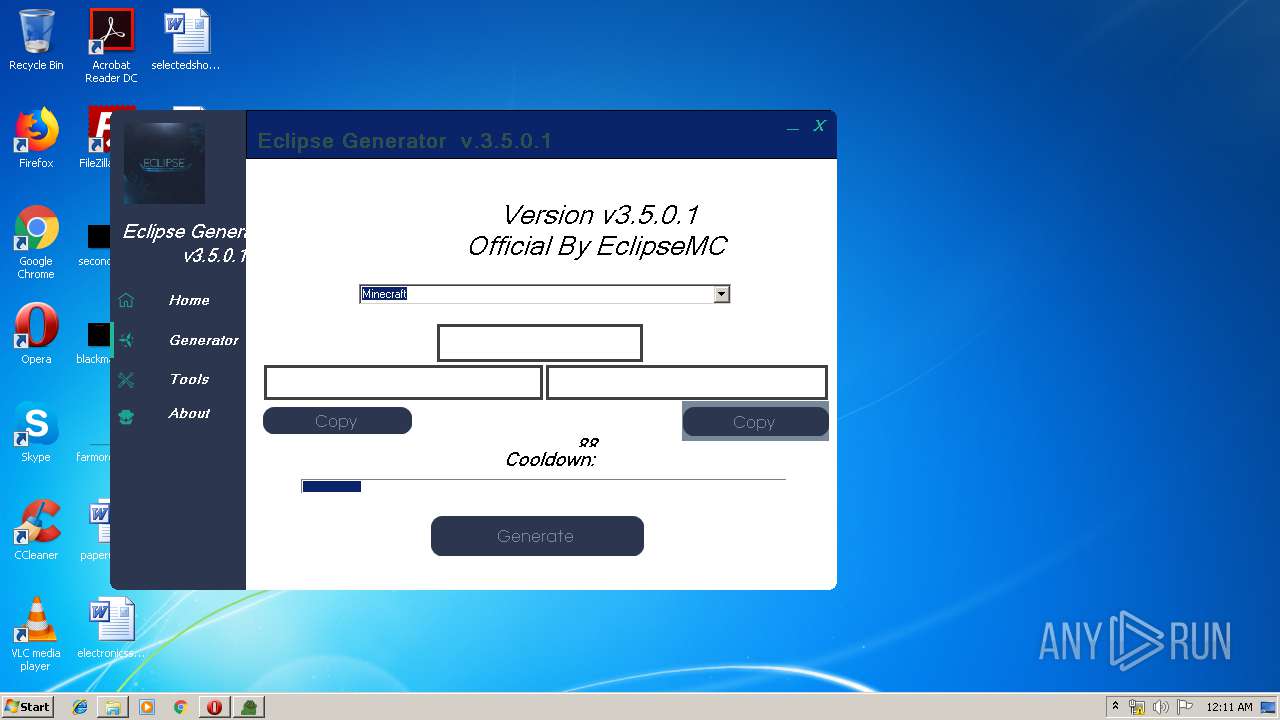
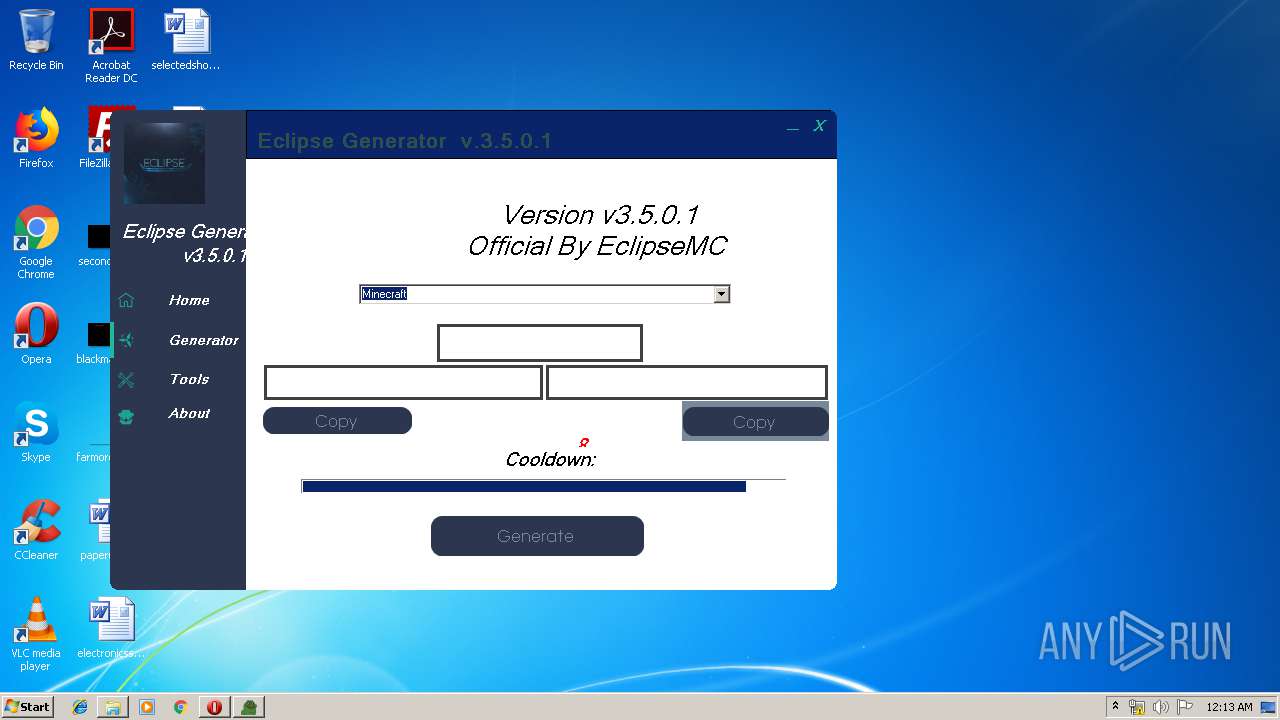
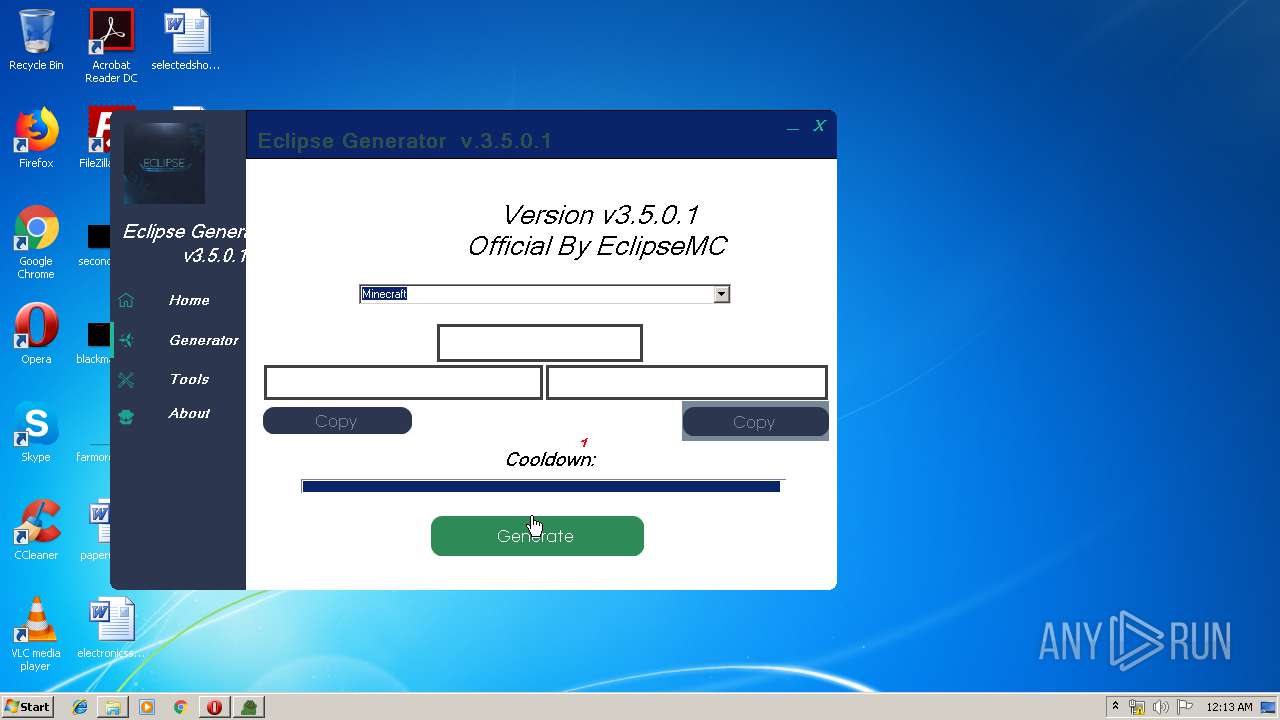
Manual execution by user
- Eclipse Generator v3.5.0.1.exe (PID: 2812)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
38
Monitored processes
5
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
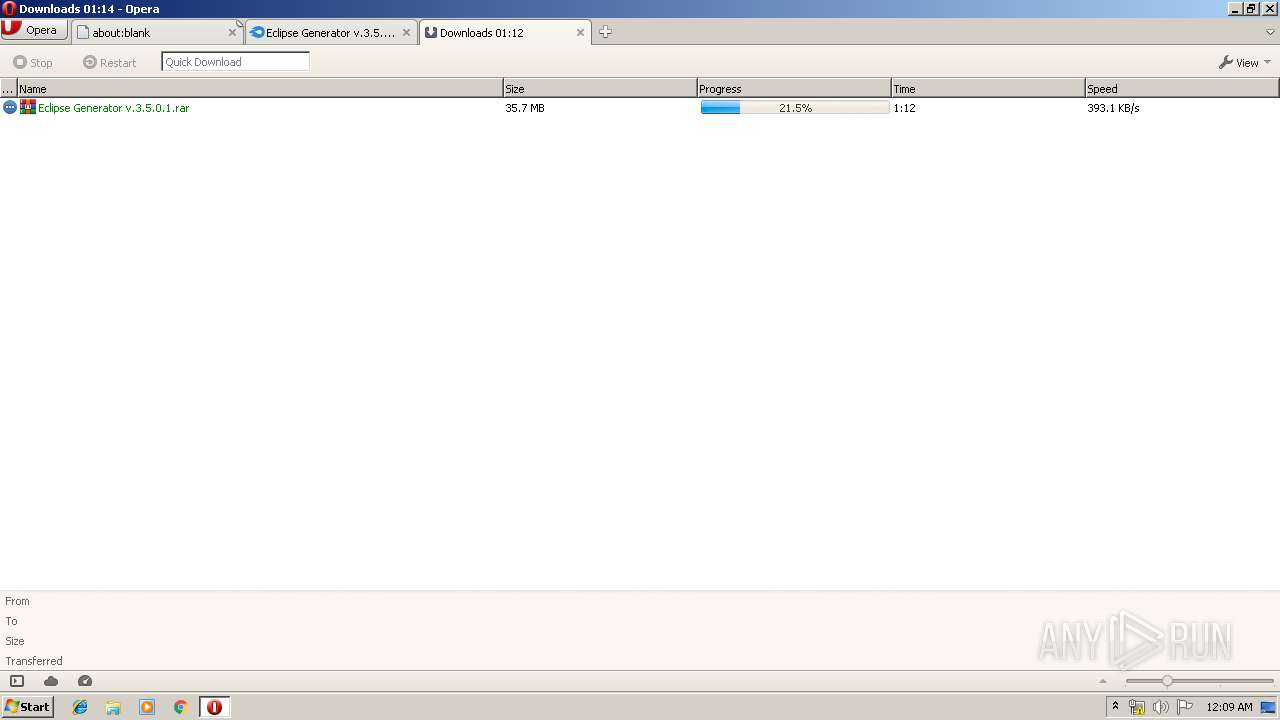
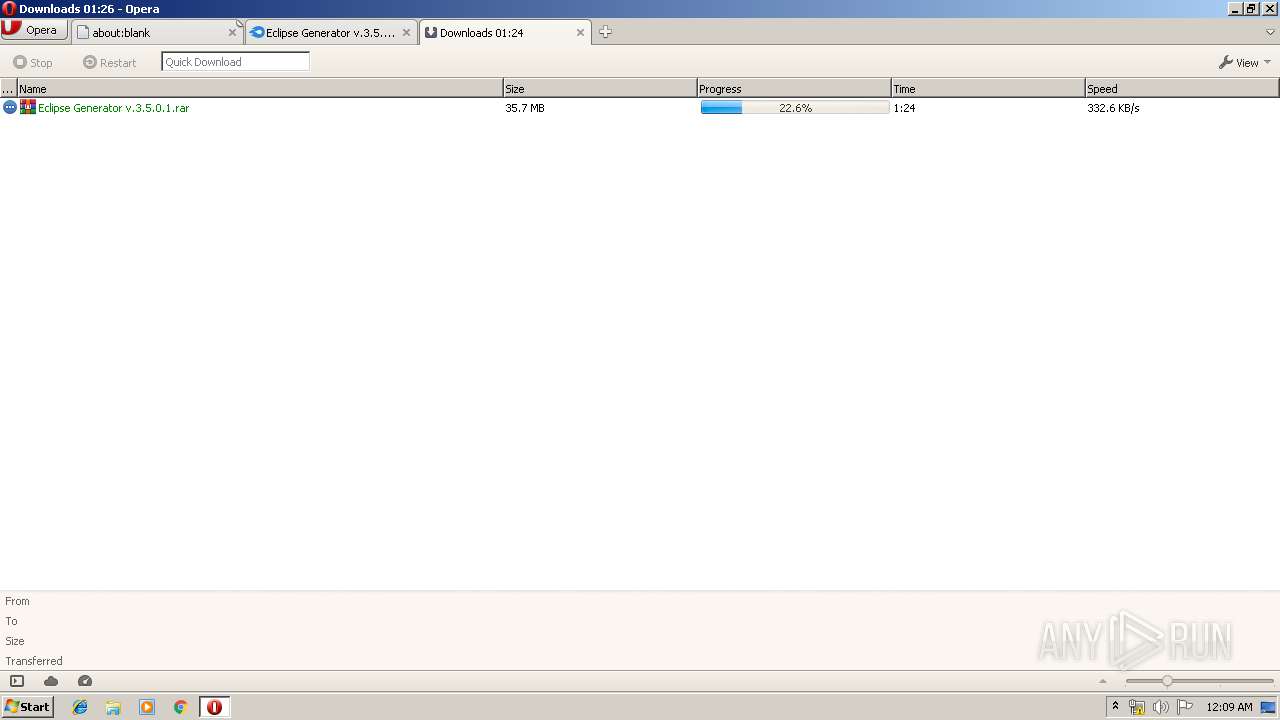
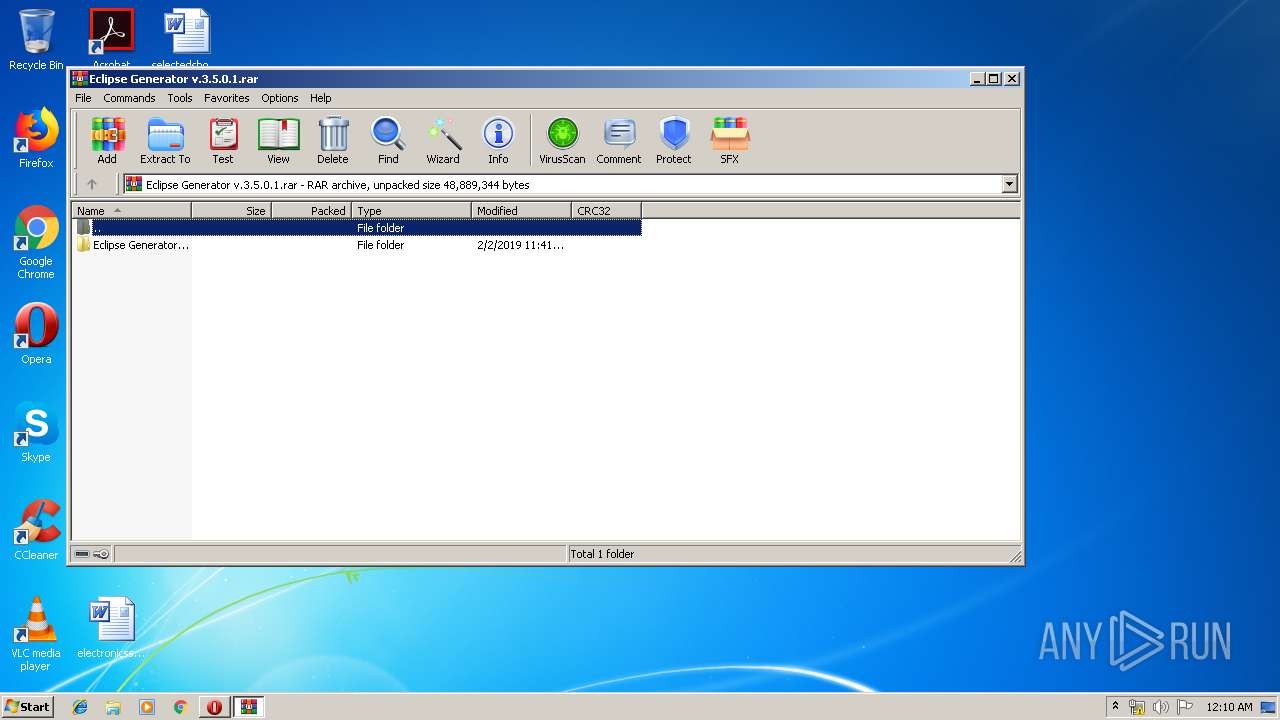
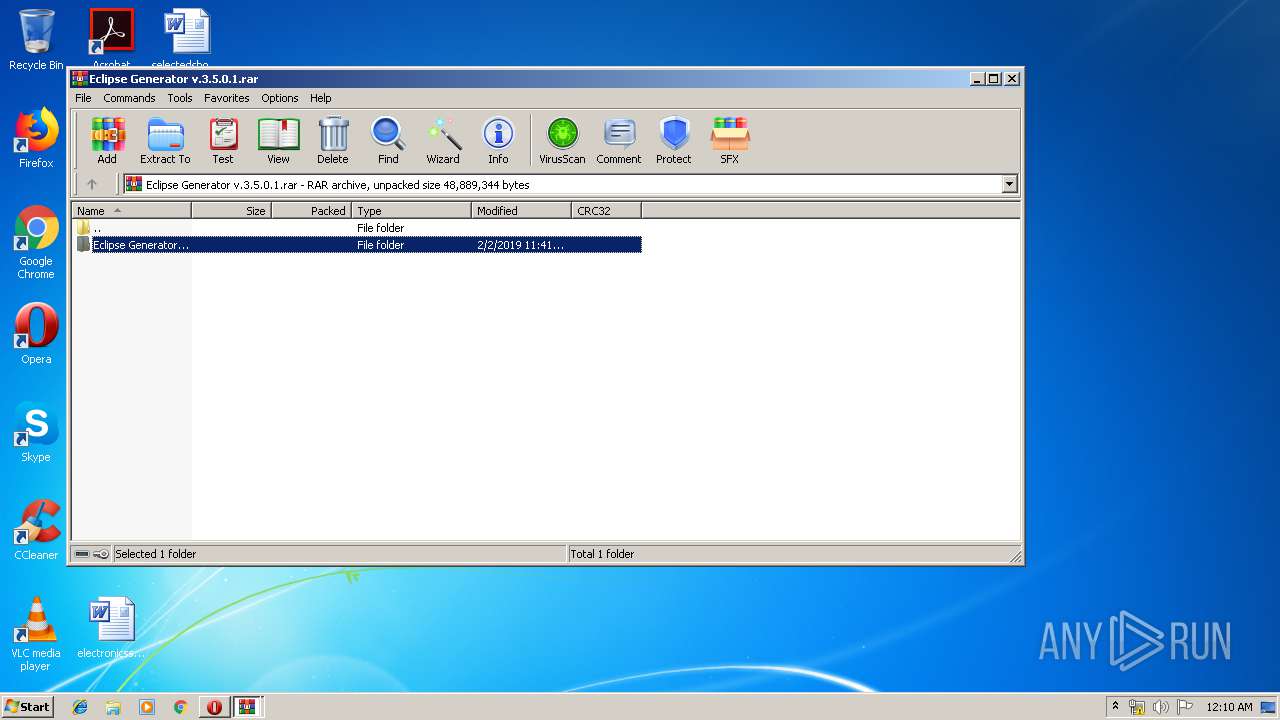
| 2632 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Opera\Opera\temporary_downloads\Eclipse Generator v.3.5.0.1.rar" | C:\Program Files\WinRAR\WinRAR.exe | opera.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
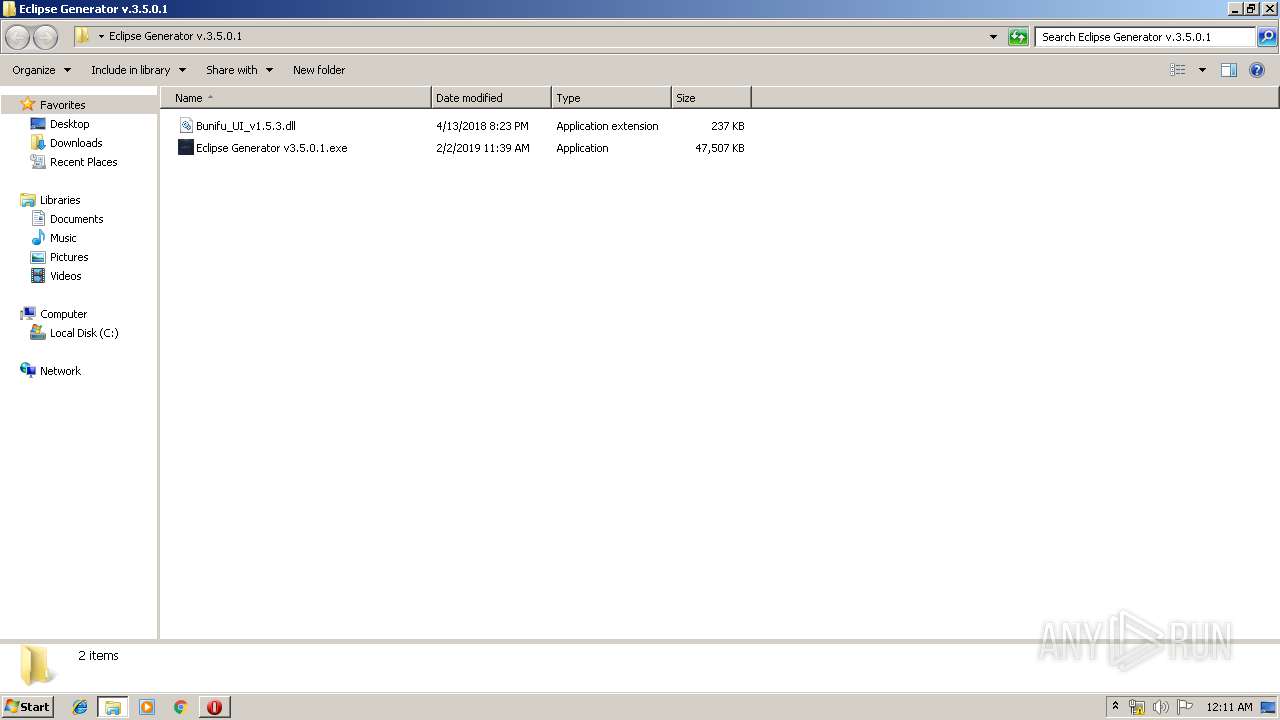
| 2812 | "C:\Users\admin\Desktop\Eclipse Generator v.3.5.0.1\Eclipse Generator v3.5.0.1.exe" | C:\Users\admin\Desktop\Eclipse Generator v.3.5.0.1\Eclipse Generator v3.5.0.1.exe | — | explorer.exe | |||||||||||
User: admin Company: EclipseMC Integrity Level: MEDIUM Description: EclipseGenerator3501 Exit code: 0 Version: 3.5.0.1 Modules
| |||||||||||||||
| 3116 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe6_ Global\UsGthrCtrlFltPipeMssGthrPipe6 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
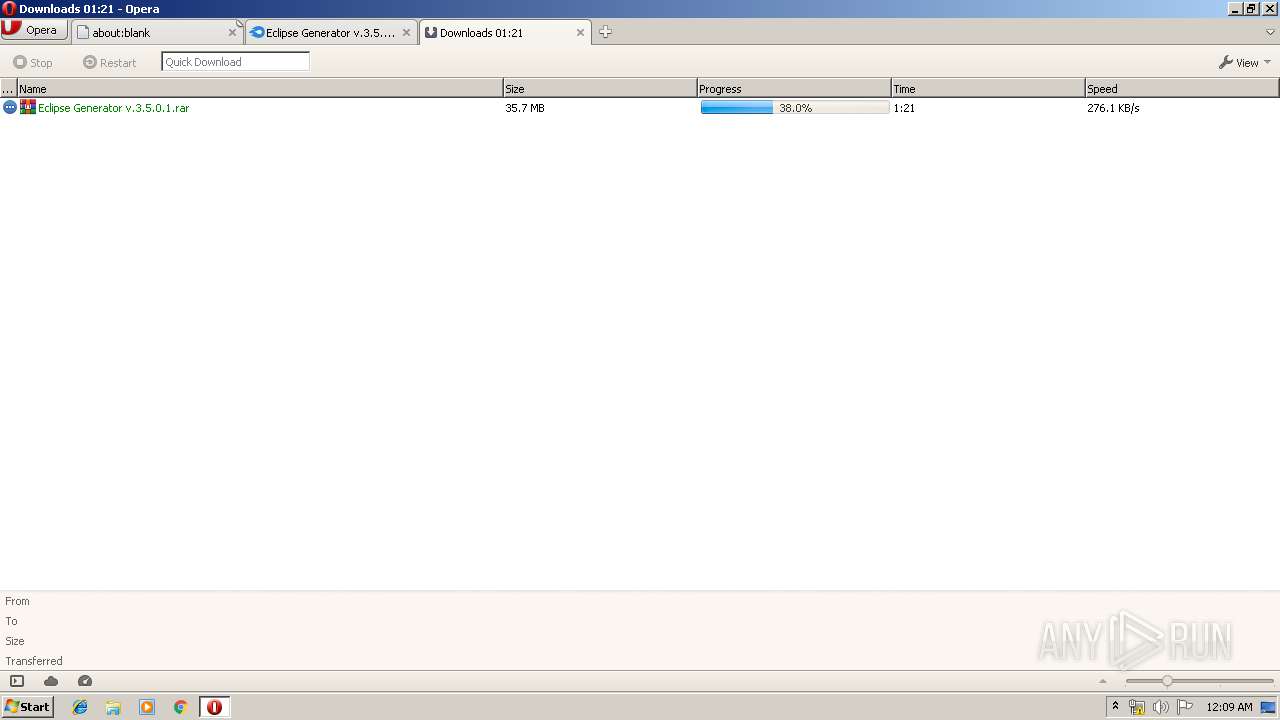
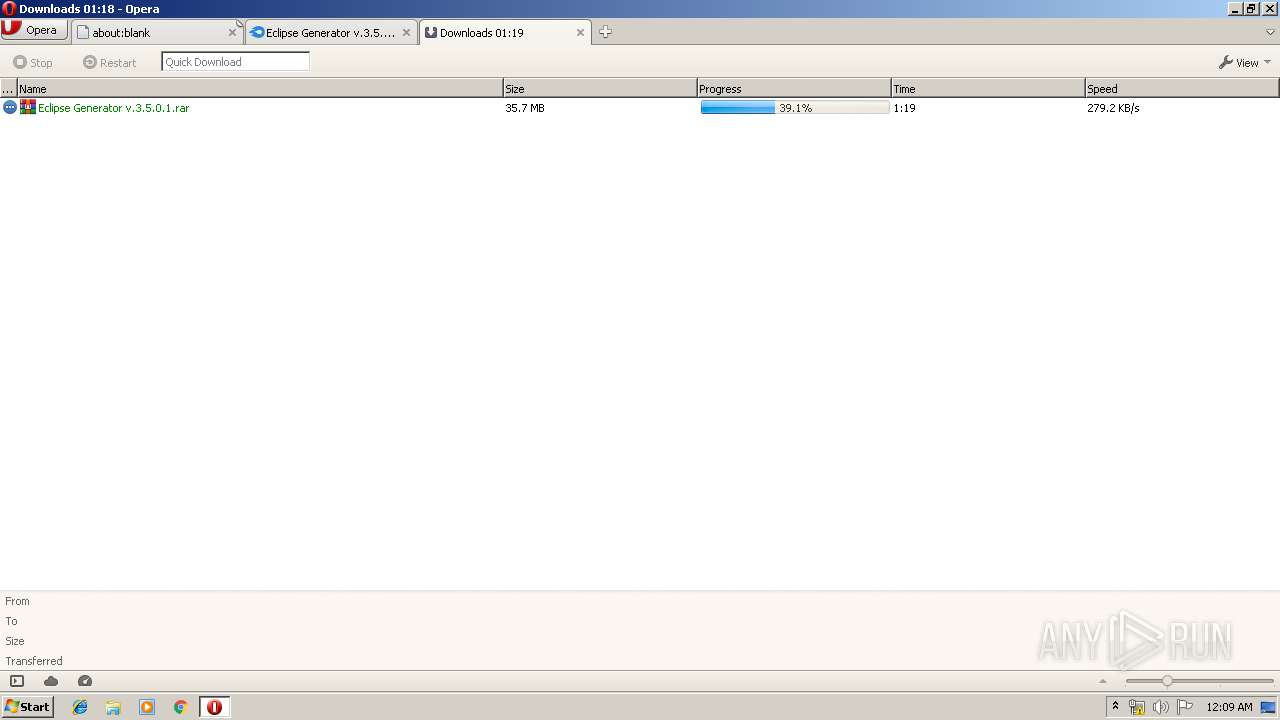
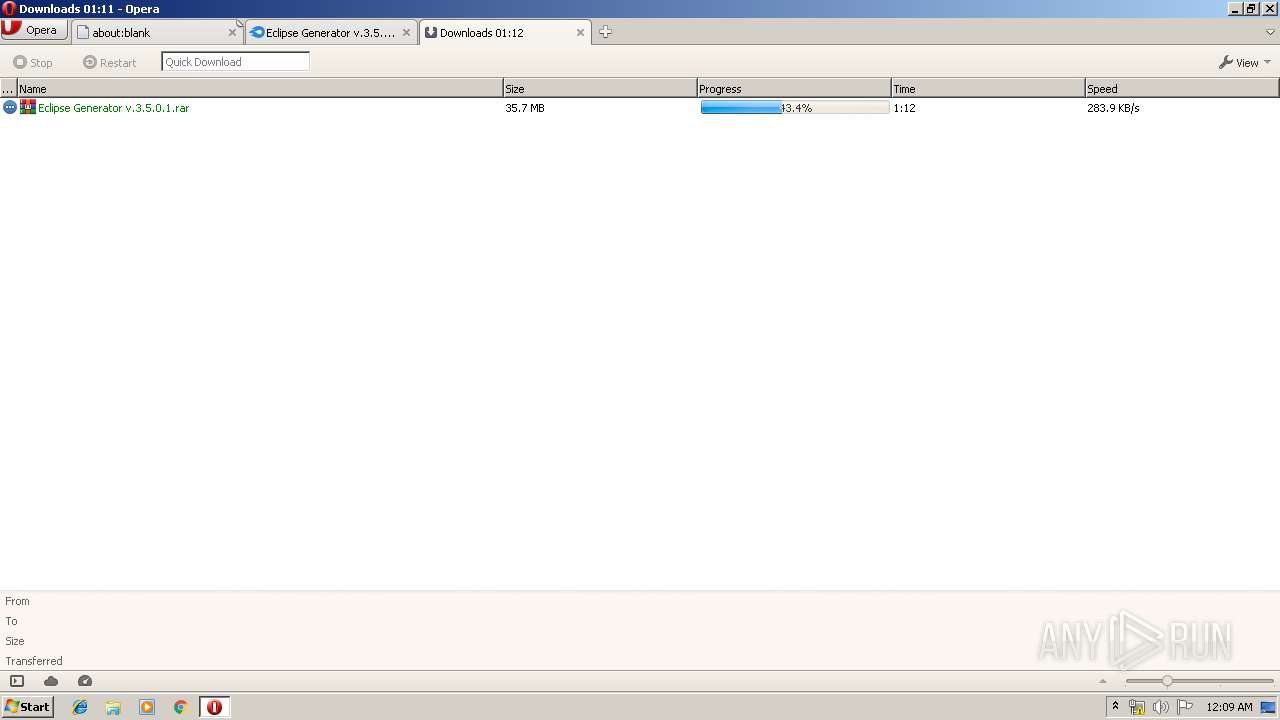
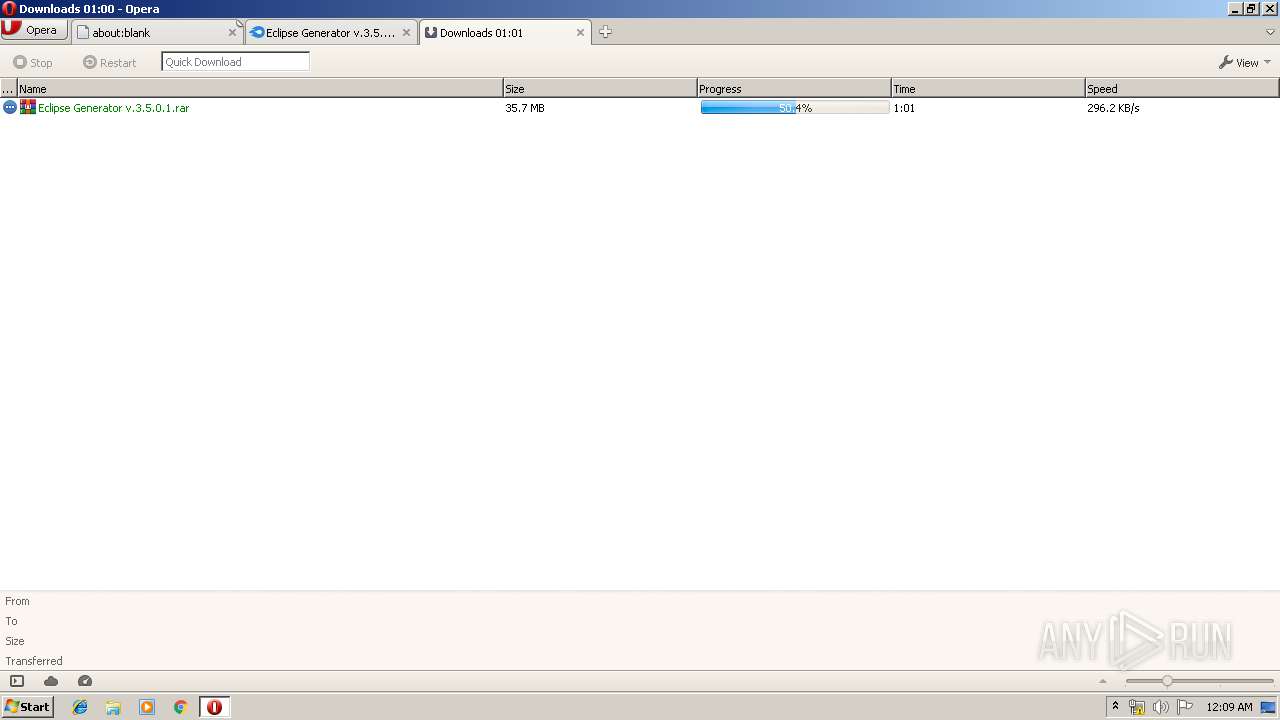
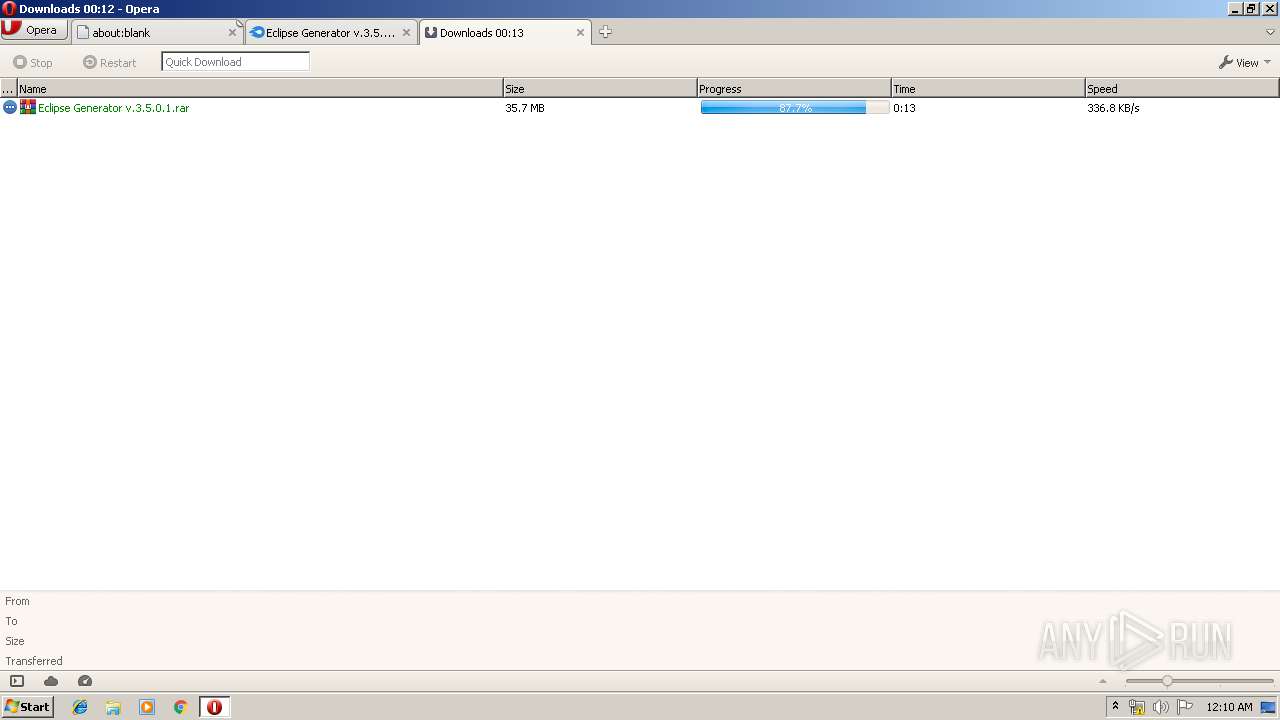
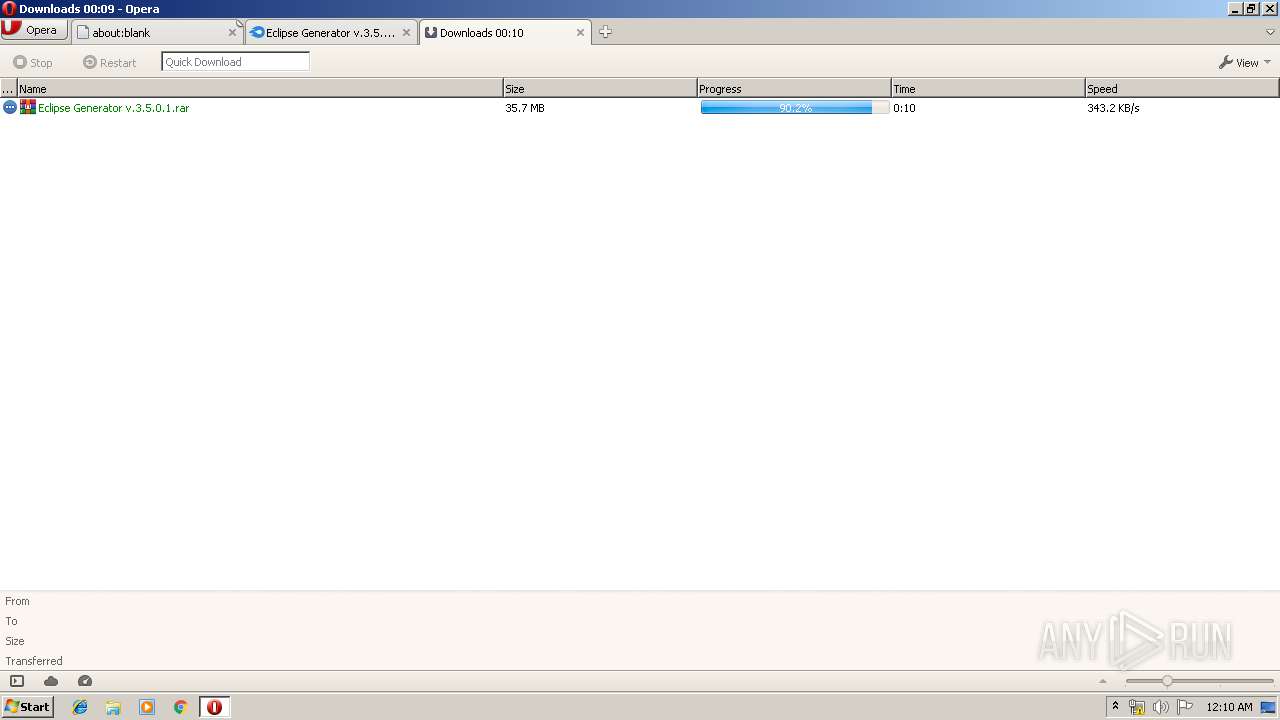
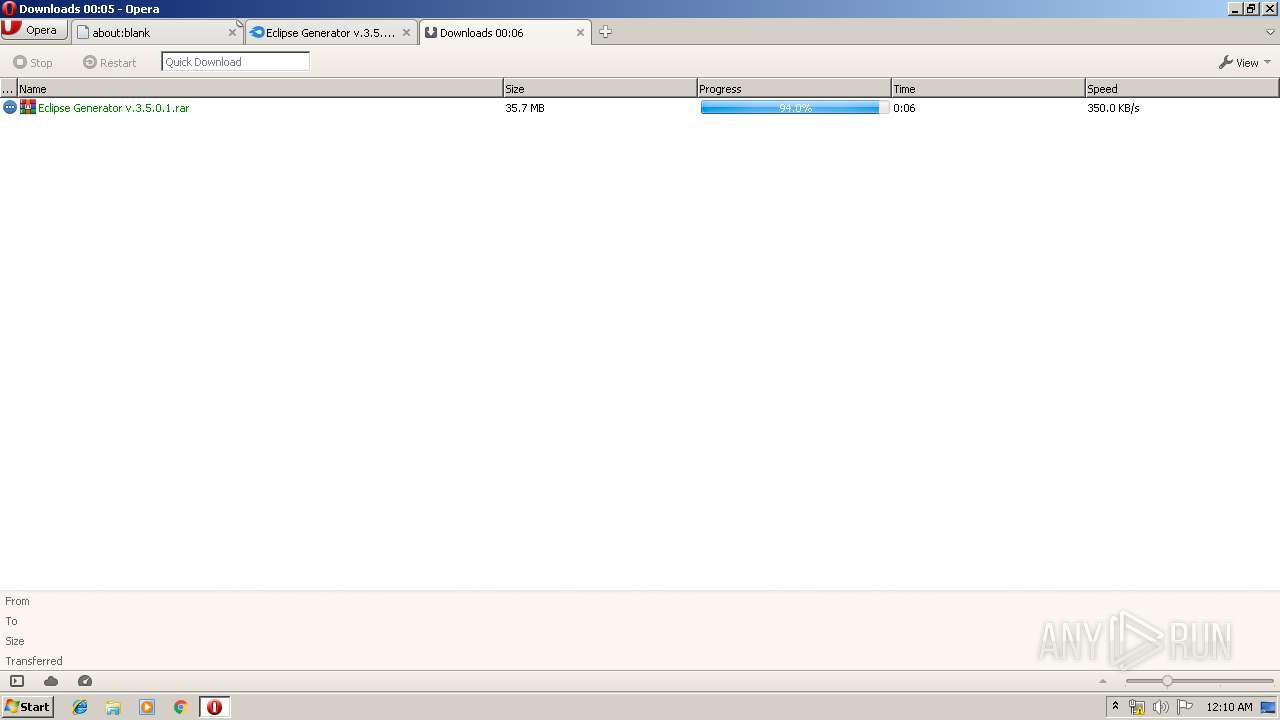
| 3372 | "C:\Program Files\Opera\opera.exe" https://www.mediafire.com/file/9796ubwuca7snzs/Eclipse_Generator_v.3.5.0.1.rar/file | C:\Program Files\Opera\opera.exe | explorer.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
| 3840 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Opera\Opera\temporary_downloads\Eclipse Generator v.3.5.0.1.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | opera.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
1 742
Read events
1 640
Write events
102
Delete events
0
Modification events
| (PID) Process: | (3372) opera.exe | Key: | HKEY_CURRENT_USER\Software\Opera Software |
| Operation: | write | Name: | Last CommandLine v2 |
Value: C:\Program Files\Opera\opera.exe https://www.mediafire.com/file/9796ubwuca7snzs/Eclipse_Generator_v.3.5.0.1.rar/file | |||
| (PID) Process: | (3372) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3372) opera.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3372) opera.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3840) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Opera\Opera\temporary_downloads\Eclipse Generator v.3.5.0.1.rar | |||
| (PID) Process: | (3840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
Executable files
1
Suspicious files
65
Text files
32
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3372 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\opr56.tmp | — | |
MD5:— | SHA256:— | |||
| 3372 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr76.tmp | — | |
MD5:— | SHA256:— | |||
| 3372 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr104.tmp | — | |
MD5:— | SHA256:— | |||
| 3372 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\sesn\opr00001.tmp | — | |
MD5:— | SHA256:— | |||
| 3372 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\IFG22HQFRYTCFR0GVIMK.temp | — | |
MD5:— | SHA256:— | |||
| 3372 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\opr15F4.tmp | — | |
MD5:— | SHA256:— | |||
| 3372 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\pstorage\00\0D\opr248C.tmp | — | |
MD5:— | SHA256:— | |||
| 3372 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opssl6.dat | binary | |
MD5:— | SHA256:— | |||
| 3372 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\operaprefs.ini | text | |
MD5:— | SHA256:— | |||
| 3372 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\tasks.xml | xml | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
97
DNS requests
43
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3372 | opera.exe | GET | 200 | 151.139.128.14:80 | http://crl.comodoca.com/COMODORSACertificationAuthority.crl | US | der | 812 b | whitelisted |
3372 | opera.exe | GET | 200 | 216.58.205.227:80 | http://crl.pki.goog/gsr2/gsr2.crl | US | der | 546 b | whitelisted |
3372 | opera.exe | GET | 200 | 93.184.220.29:80 | http://status.geotrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR3enuod9bxDxzpICGW%2B2sabjf17QQUkFj%2FsJx1qFFUd7Ht8qNDFjiebMUCEAqGuQR2WDHiQMxiERAfVzY%3D | US | der | 471 b | whitelisted |
3372 | opera.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBR64T7ooMQqLLQoy%2BemBUYZQOKh6QQUkK9qOpRaC9iQ6hJWc99DtDoo2ucCEQCscnq%2Bs%2FXK96FH3ZtSIwGm | US | der | 472 b | whitelisted |
3372 | opera.exe | GET | 200 | 216.58.206.3:80 | http://ocsp.pki.goog/GTSGIAG3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT27bBjYjKBmjX2jXWgnQJKEapsrQQUd8K4UJpndnaxLcKG0IOgfqZ%2BuksCEAifIe9cOJ8hyOMxEdYgMQE%3D | US | der | 471 b | whitelisted |
3372 | opera.exe | GET | 200 | 216.58.206.3:80 | http://ocsp.pki.goog/GTSGIAG3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT27bBjYjKBmjX2jXWgnQJKEapsrQQUd8K4UJpndnaxLcKG0IOgfqZ%2BuksCEBl1xyUAOEjM3OSOkk45op0%3D | US | der | 471 b | whitelisted |
3372 | opera.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca4.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBQAU7Bfe6xSRj1%2Bo83zCN%2BY2wTgIAQU1LD0%2FU%2BcQqRs3D0u7ltBGMmtA%2FYCEQCuHQcLY0uBp81sSvCqHS43 | US | der | 472 b | whitelisted |
3372 | opera.exe | GET | 200 | 216.58.206.3:80 | http://ocsp.pki.goog/GTSGIAG3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT27bBjYjKBmjX2jXWgnQJKEapsrQQUd8K4UJpndnaxLcKG0IOgfqZ%2BuksCEGMqb1HLYP7nYb%2FlnA%2FsZJ0%3D | US | der | 471 b | whitelisted |
3372 | opera.exe | GET | 200 | 2.16.186.43:80 | http://crl.trustwave.com/STCA.crl | unknown | der | 758 b | whitelisted |
3372 | opera.exe | GET | 200 | 216.58.206.3:80 | http://ocsp.pki.goog/GTSGIAG3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT27bBjYjKBmjX2jXWgnQJKEapsrQQUd8K4UJpndnaxLcKG0IOgfqZ%2BuksCEEE3wtwoKwbocfwwBVcsm60%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3372 | opera.exe | 104.19.195.29:443 | www.mediafire.com | Cloudflare Inc | US | shared |
3372 | opera.exe | 93.184.220.29:80 | crl4.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3372 | opera.exe | 185.26.182.94:443 | sitecheck2.opera.com | Opera Software AS | — | whitelisted |
3372 | opera.exe | 185.26.182.93:443 | sitecheck2.opera.com | Opera Software AS | — | whitelisted |
3372 | opera.exe | 216.58.206.3:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3372 | opera.exe | 151.139.128.14:80 | crl.comodoca.com | Highwinds Network Group, Inc. | US | suspicious |
3372 | opera.exe | 216.58.206.2:443 | securepubads.g.doubleclick.net | Google Inc. | US | whitelisted |
3372 | opera.exe | 216.58.210.2:443 | www.googletagservices.com | Google Inc. | US | whitelisted |
3372 | opera.exe | 172.217.18.110:443 | translate.google.com | Google Inc. | US | whitelisted |
3372 | opera.exe | 104.19.194.29:443 | www.mediafire.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.mediafire.com |
| shared |
sitecheck2.opera.com |
| whitelisted |
certs.opera.com |
| whitelisted |
crl.comodoca.com |
| whitelisted |
crl.usertrust.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |
www.googletagservices.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
crl.pki.goog |
| whitelisted |
securepubads.g.doubleclick.net |
| whitelisted |