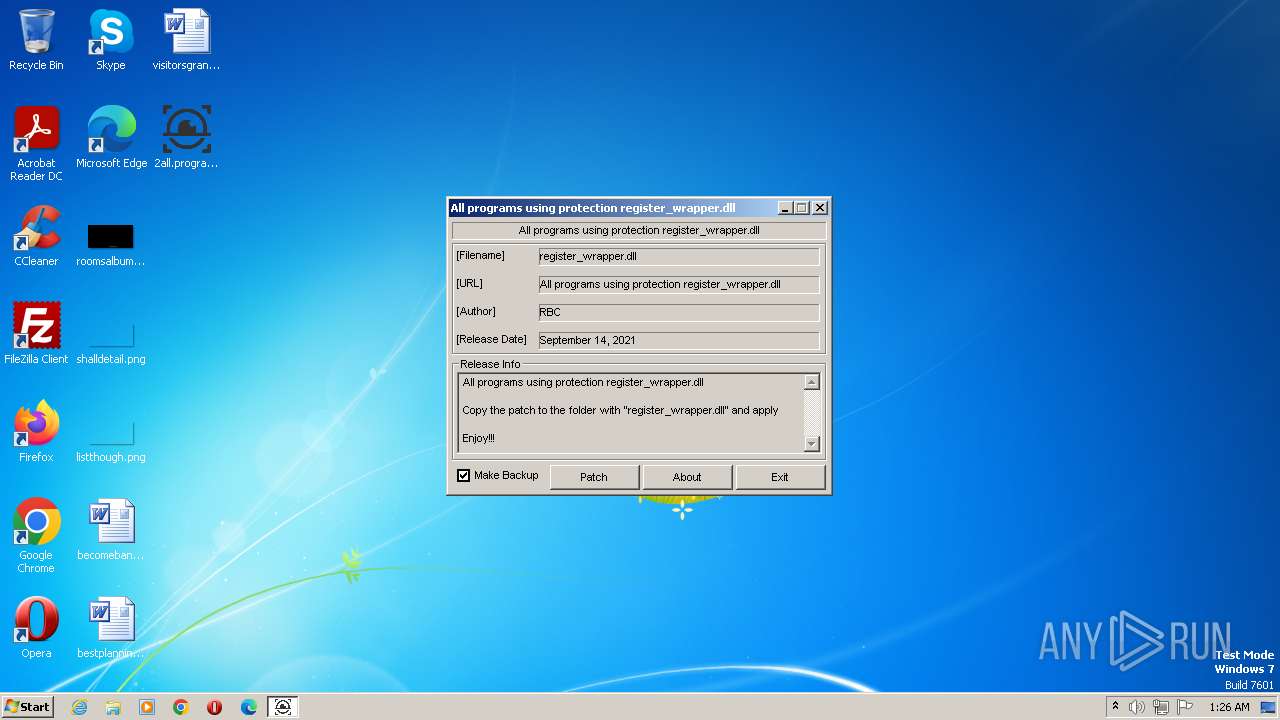
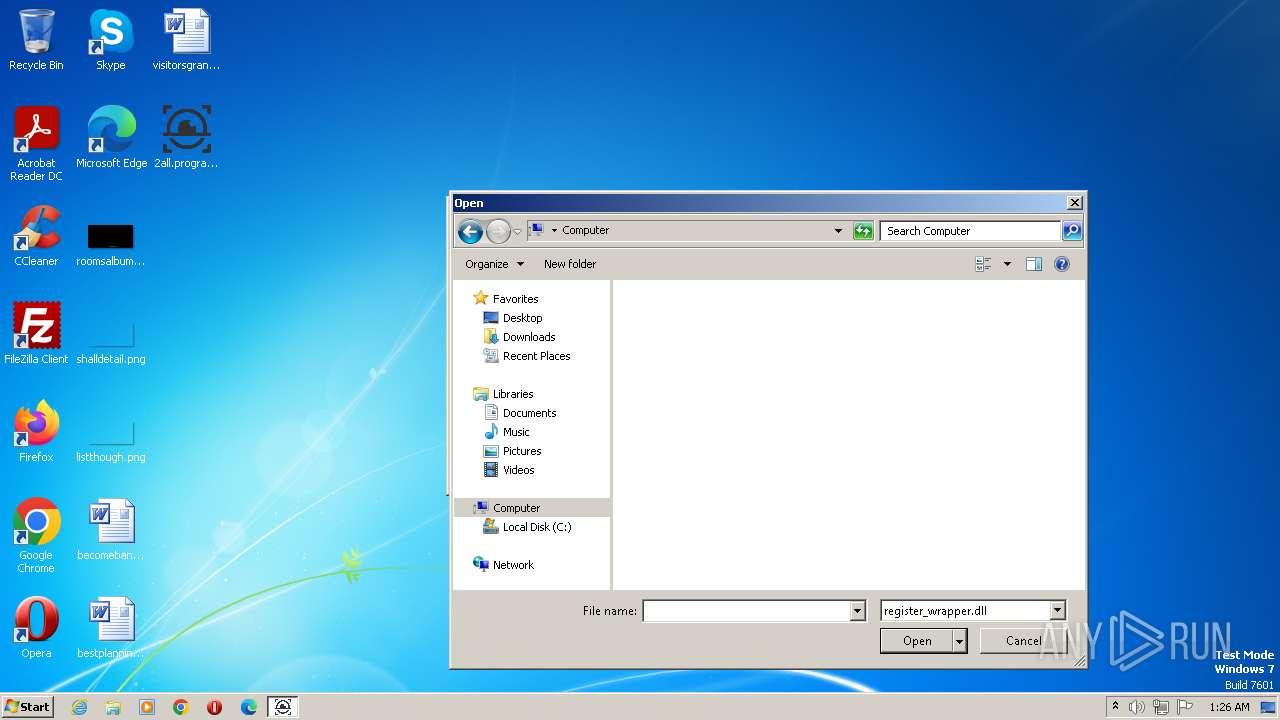
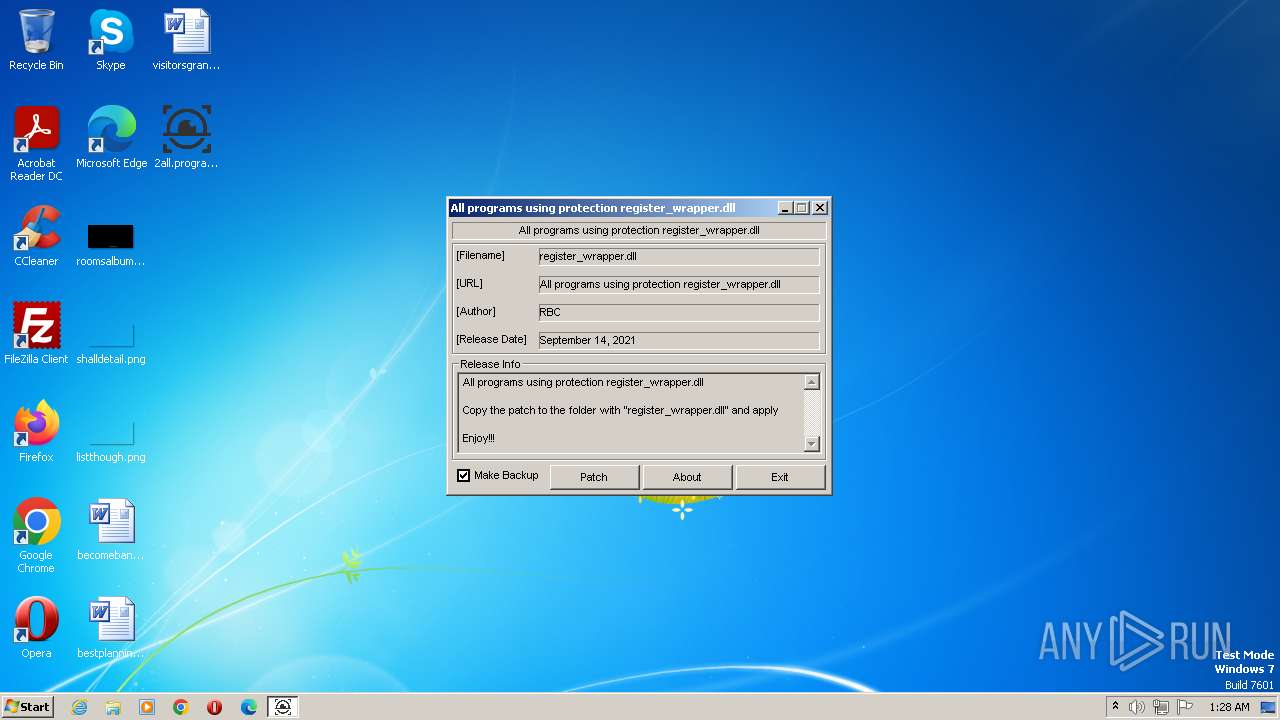
| File name: | 2all.programs.using.protection.register_wrapper.dll-patch.exe |
| Full analysis: | https://app.any.run/tasks/c80355b2-ba0e-4c69-be72-9db7d3b8aad7 |
| Verdict: | Malicious activity |
| Analysis date: | August 25, 2023, 00:25:57 |
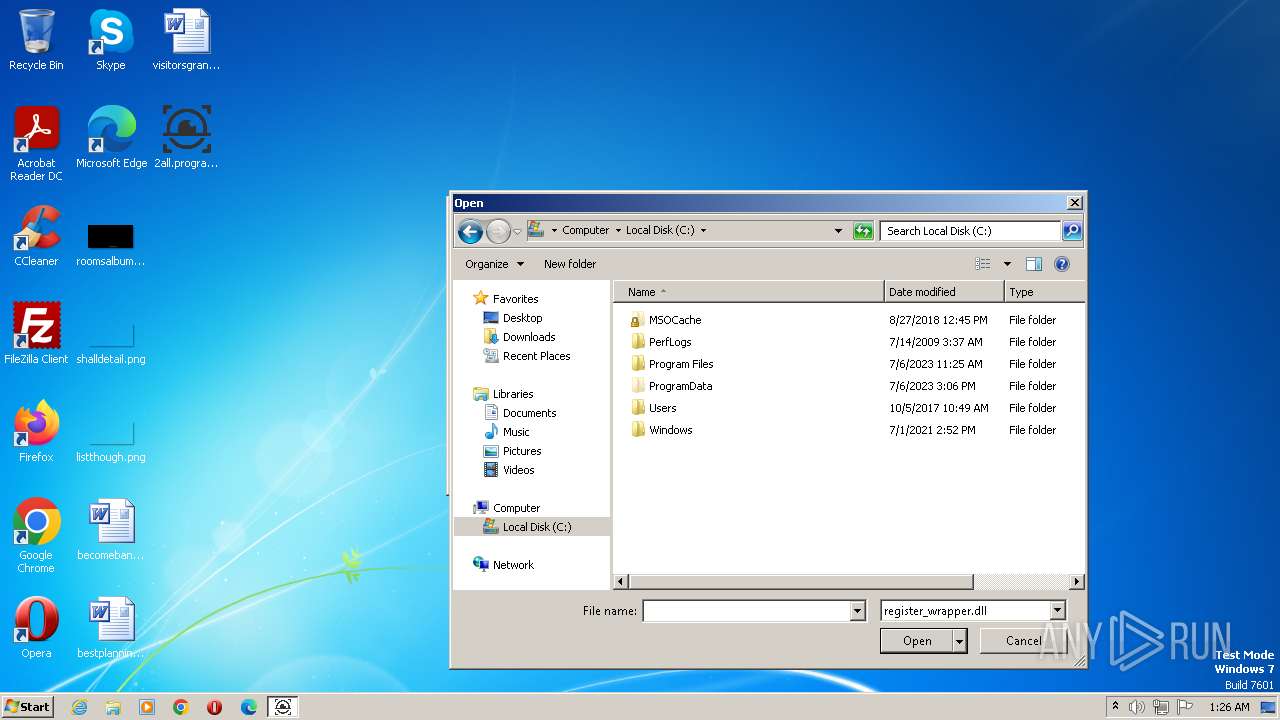
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | D0AEFE064046757EB0CB337BB20E8A92 |
| SHA1: | 790B83ECF9D22BBE1D8483395525E733BAB4FEEA |
| SHA256: | 1E4C9B52CB26777D5A349AAFA8414A81D9251974E29D8425312A97036DADD0C9 |
| SSDEEP: | 1536:iiEUNDEa47r+j3bbbUX/QIrp0h+VpD8Z8+Cg9:Vv44gX/Qbh+UJN |
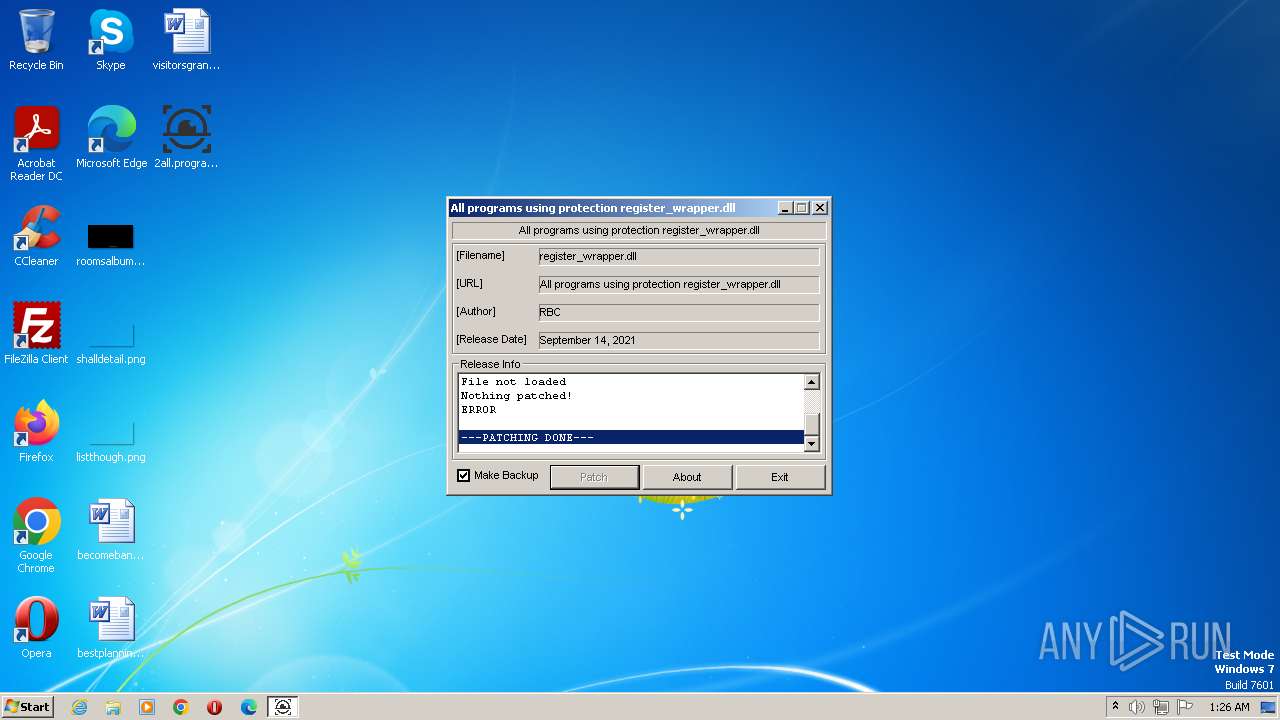
MALICIOUS
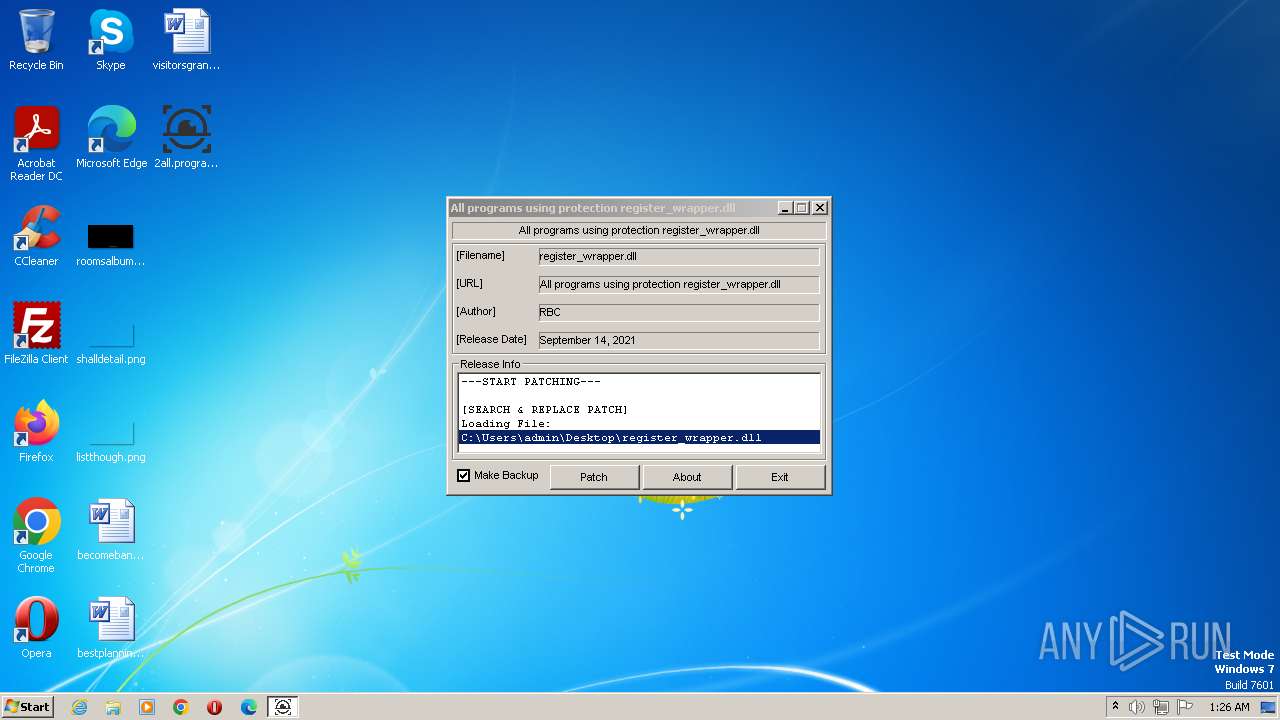
Loads dropped or rewritten executable
- 2all.programs.using.protection.register_wrapper.dll-patch.exe (PID: 124)
- 2all.programs.using.protection.register_wrapper.dll-patch.exe (PID: 2688)
SUSPICIOUS
Executable content was dropped or overwritten
- 2all.programs.using.protection.register_wrapper.dll-patch.exe (PID: 124)
- 2all.programs.using.protection.register_wrapper.dll-patch.exe (PID: 2688)
INFO
Checks supported languages
- 2all.programs.using.protection.register_wrapper.dll-patch.exe (PID: 124)
- 2all.programs.using.protection.register_wrapper.dll-patch.exe (PID: 2688)
Create files in a temporary directory
- 2all.programs.using.protection.register_wrapper.dll-patch.exe (PID: 124)
- 2all.programs.using.protection.register_wrapper.dll-patch.exe (PID: 2688)
Reads the computer name
- 2all.programs.using.protection.register_wrapper.dll-patch.exe (PID: 124)
Reads the machine GUID from the registry
- 2all.programs.using.protection.register_wrapper.dll-patch.exe (PID: 124)
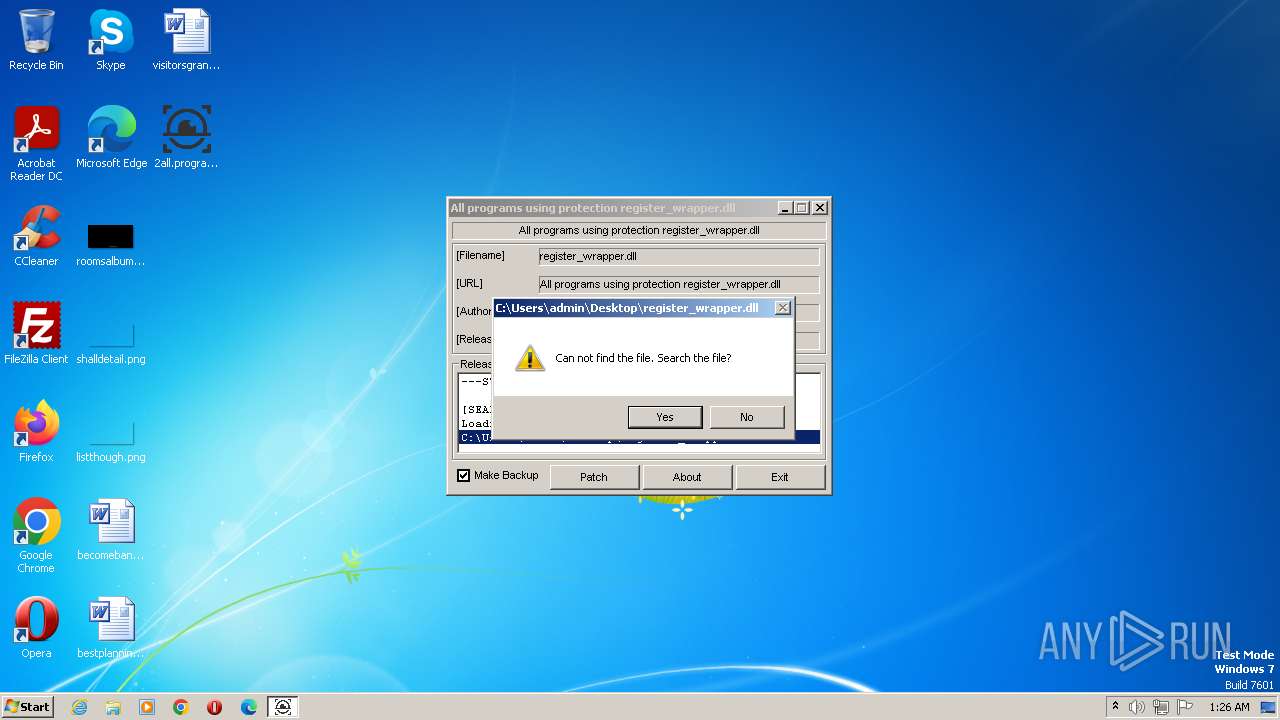
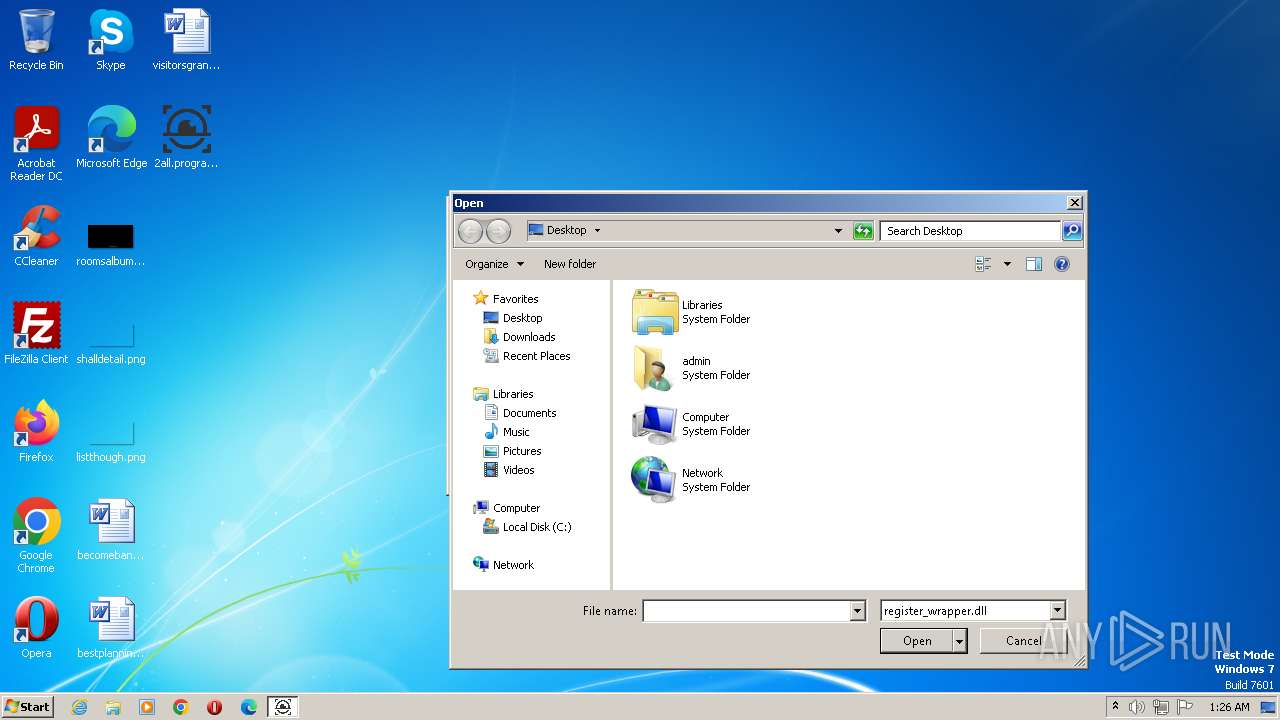
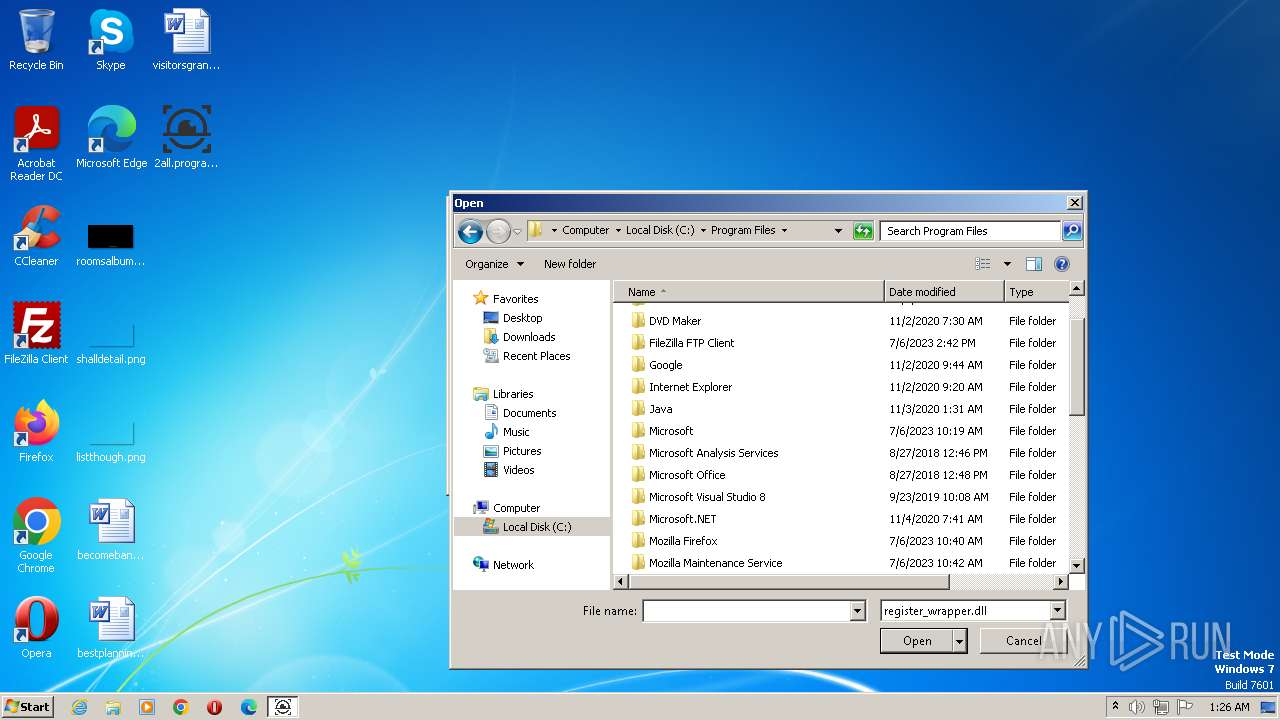
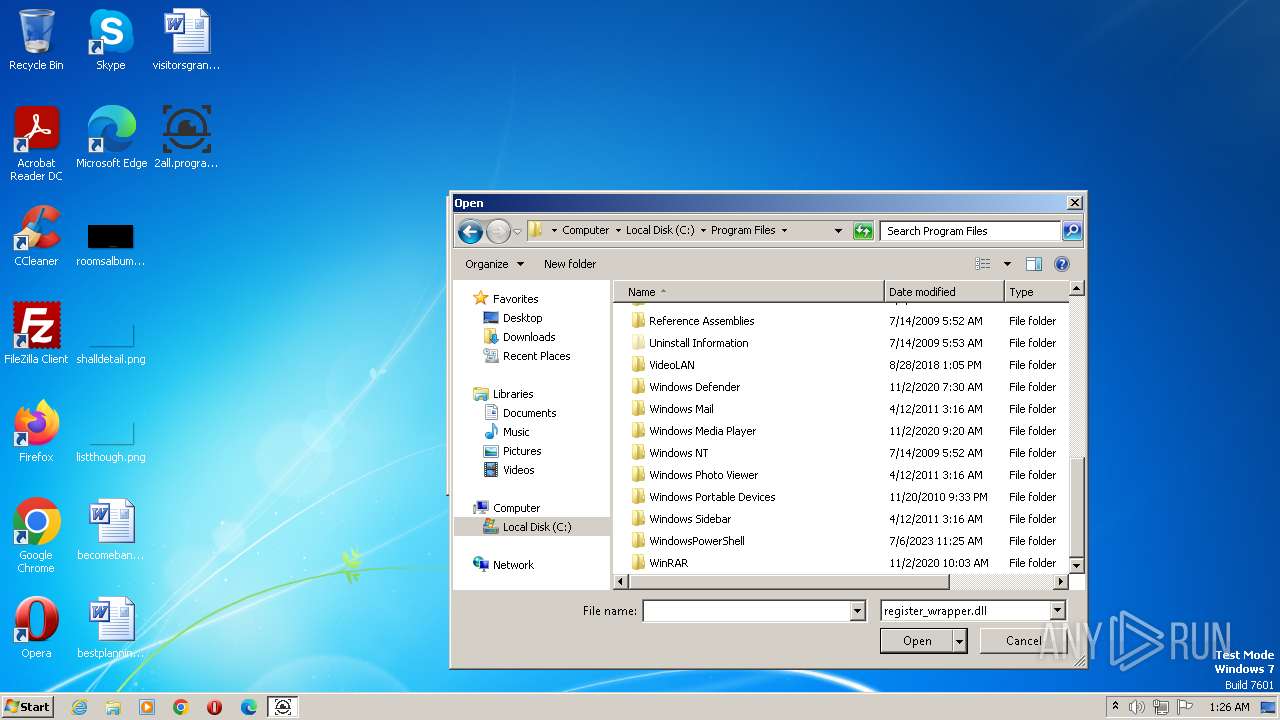
Manual execution by a user
- 2all.programs.using.protection.register_wrapper.dll-patch.exe (PID: 2688)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 5 |
| ImageVersion: | - |
| OSVersion: | 5 |
| EntryPoint: | 0x102b |
| UninitializedDataSize: | - |
| InitializedDataSize: | 128000 |
| CodeSize: | 512 |
| LinkerVersion: | 10 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, 32-bit |
| TimeStamp: | 2012:12:21 20:59:46+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 21-Dec-2012 20:59:46 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 21-Dec-2012 20:59:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000001F6 | 0x00000200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.06408 |
.rdata | 0x00002000 | 0x000001D8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.27064 |
.data | 0x00003000 | 0x00000034 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.568988 |
.rsrc | 0x00004000 | 0x0001ECEC | 0x0001EE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.59059 |
.reloc | 0x00023000 | 0x00000052 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.736046 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.85948 | 887 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
500 | 1.98048 | 20 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
DLL | 7.99708 | 57344 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
kernel32.dll |
Total processes
38
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
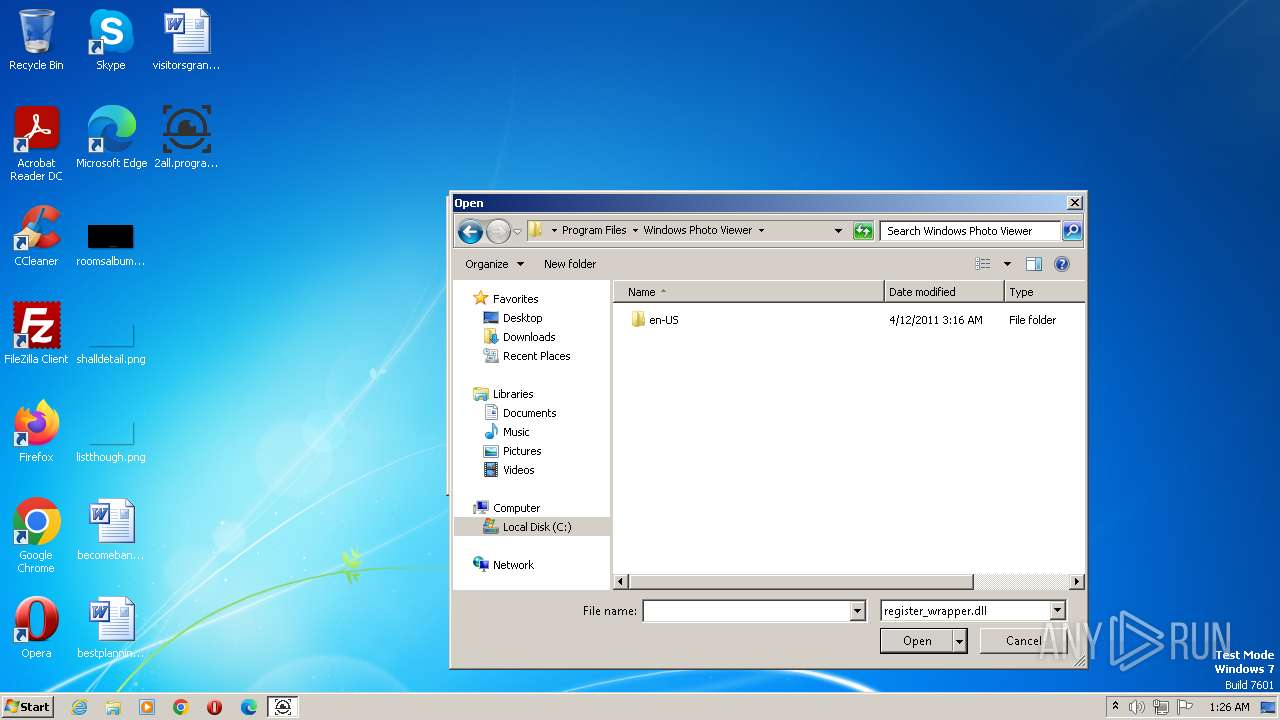
| 124 | "C:\Users\admin\Desktop\2all.programs.using.protection.register_wrapper.dll-patch.exe" | C:\Users\admin\Desktop\2all.programs.using.protection.register_wrapper.dll-patch.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2688 | "C:\Users\admin\Desktop\2all.programs.using.protection.register_wrapper.dll-patch.exe" | C:\Users\admin\Desktop\2all.programs.using.protection.register_wrapper.dll-patch.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
3 134
Read events
3 009
Write events
124
Delete events
1
Modification events
| (PID) Process: | (124) 2all.programs.using.protection.register_wrapper.dll-patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (124) 2all.programs.using.protection.register_wrapper.dll-patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 07000000020000000000000006000000010000000C0000000B0000000D0000000A0000000900000008000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (124) 2all.programs.using.protection.register_wrapper.dll-patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\178\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (124) 2all.programs.using.protection.register_wrapper.dll-patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\82\ComDlg\{5C4F28B5-F869-4E84-8E60-F11DB97C5CC7} |
| Operation: | write | Name: | Mode |
Value: 6 | |||
| (PID) Process: | (124) 2all.programs.using.protection.register_wrapper.dll-patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\82\ComDlg\{5C4F28B5-F869-4E84-8E60-F11DB97C5CC7} |
| Operation: | write | Name: | LogicalViewMode |
Value: 2 | |||
| (PID) Process: | (124) 2all.programs.using.protection.register_wrapper.dll-patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\82\ComDlg\{5C4F28B5-F869-4E84-8E60-F11DB97C5CC7} |
| Operation: | write | Name: | FFlags |
Value: 1 | |||
| (PID) Process: | (124) 2all.programs.using.protection.register_wrapper.dll-patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\82\ComDlg\{5C4F28B5-F869-4E84-8E60-F11DB97C5CC7} |
| Operation: | write | Name: | IconSize |
Value: 48 | |||
| (PID) Process: | (124) 2all.programs.using.protection.register_wrapper.dll-patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\82\ComDlg\{5C4F28B5-F869-4E84-8E60-F11DB97C5CC7} |
| Operation: | write | Name: | ColInfo |
Value: 00000000000000000000000000000000FDDFDFFD100000000000000000000000040000001800000030F125B7EF471A10A5F102608C9EEBAC0A000000A000000030F125B7EF471A10A5F102608C9EEBAC0C00000050000000A66A63283D95D211B5D600C04FD918D00B0000007800000030F125B7EF471A10A5F102608C9EEBAC0E00000078000000 | |||
| (PID) Process: | (124) 2all.programs.using.protection.register_wrapper.dll-patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\82\ComDlg\{5C4F28B5-F869-4E84-8E60-F11DB97C5CC7} |
| Operation: | write | Name: | Sort |
Value: 000000000000000000000000000000000100000030F125B7EF471A10A5F102608C9EEBAC0A00000001000000 | |||
| (PID) Process: | (124) 2all.programs.using.protection.register_wrapper.dll-patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\82\ComDlg\{5C4F28B5-F869-4E84-8E60-F11DB97C5CC7} |
| Operation: | write | Name: | GroupView |
Value: 0 | |||
Executable files
2
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2688 | 2all.programs.using.protection.register_wrapper.dll-patch.exe | C:\Users\admin\AppData\Local\Temp\dup2patcher.dll | executable | |
MD5:B1ACBF7DE7838005DCD9EABE095BBCDB | SHA256:AA34484CDB1C8623B5B892BE3246807F5297685757219E5841053C6E4436E455 | |||
| 124 | 2all.programs.using.protection.register_wrapper.dll-patch.exe | C:\Users\admin\AppData\Local\Temp\dup2patcher.dll | executable | |
MD5:B1ACBF7DE7838005DCD9EABE095BBCDB | SHA256:AA34484CDB1C8623B5B892BE3246807F5297685757219E5841053C6E4436E455 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3284 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |