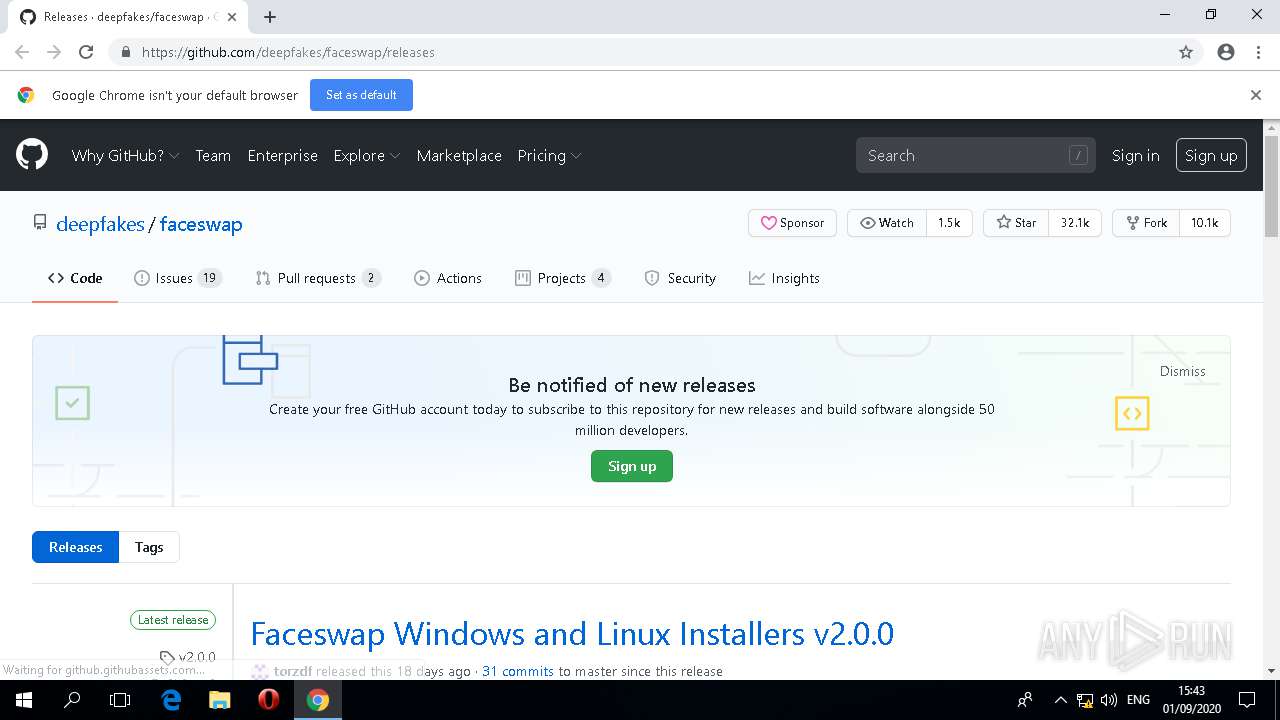
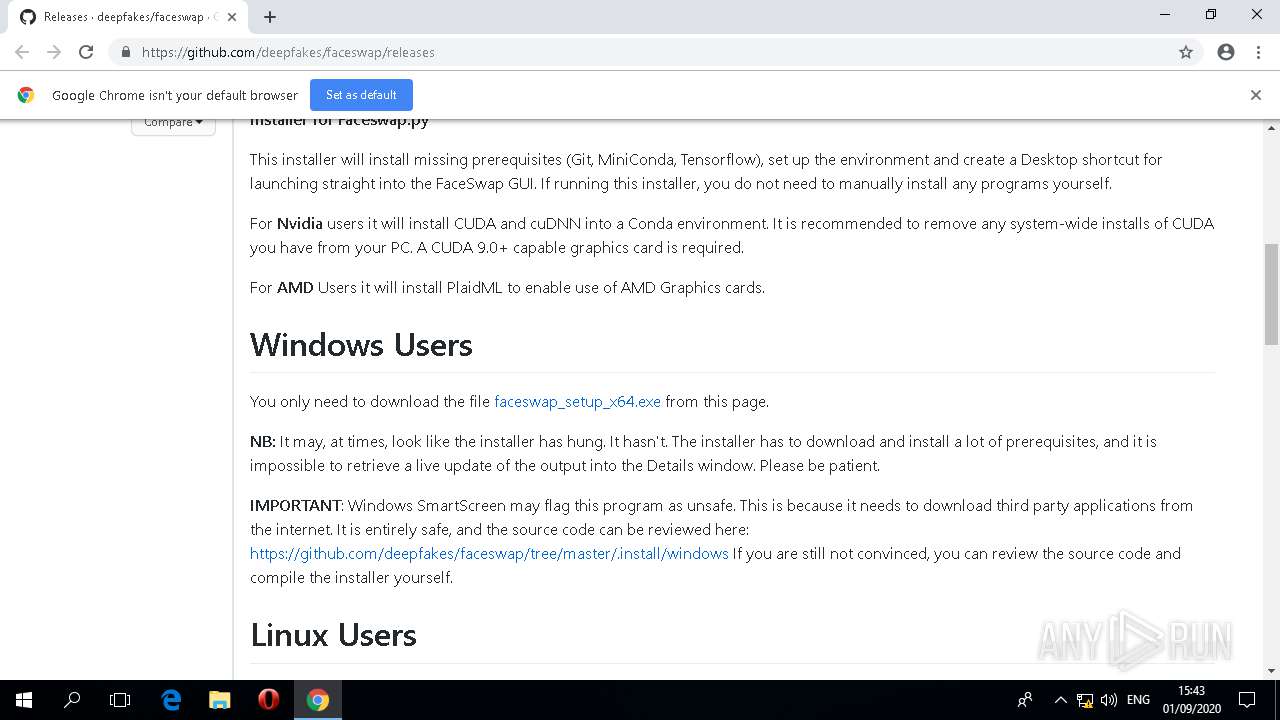
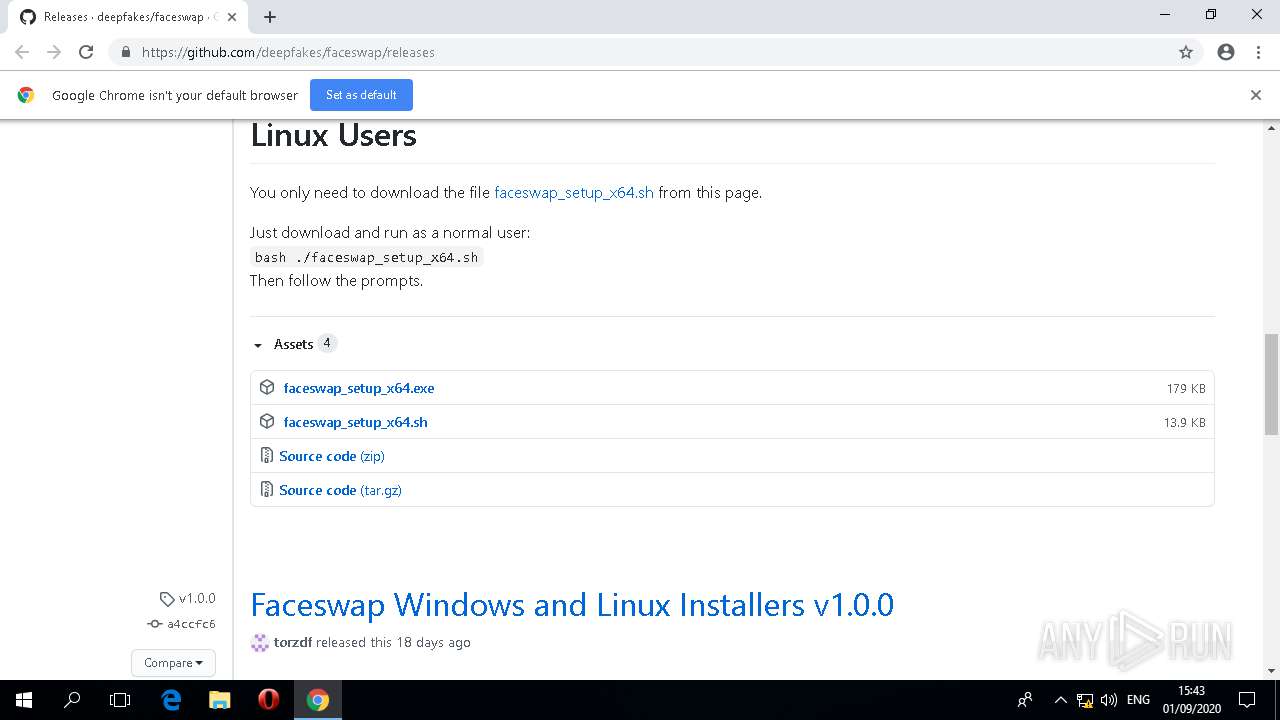
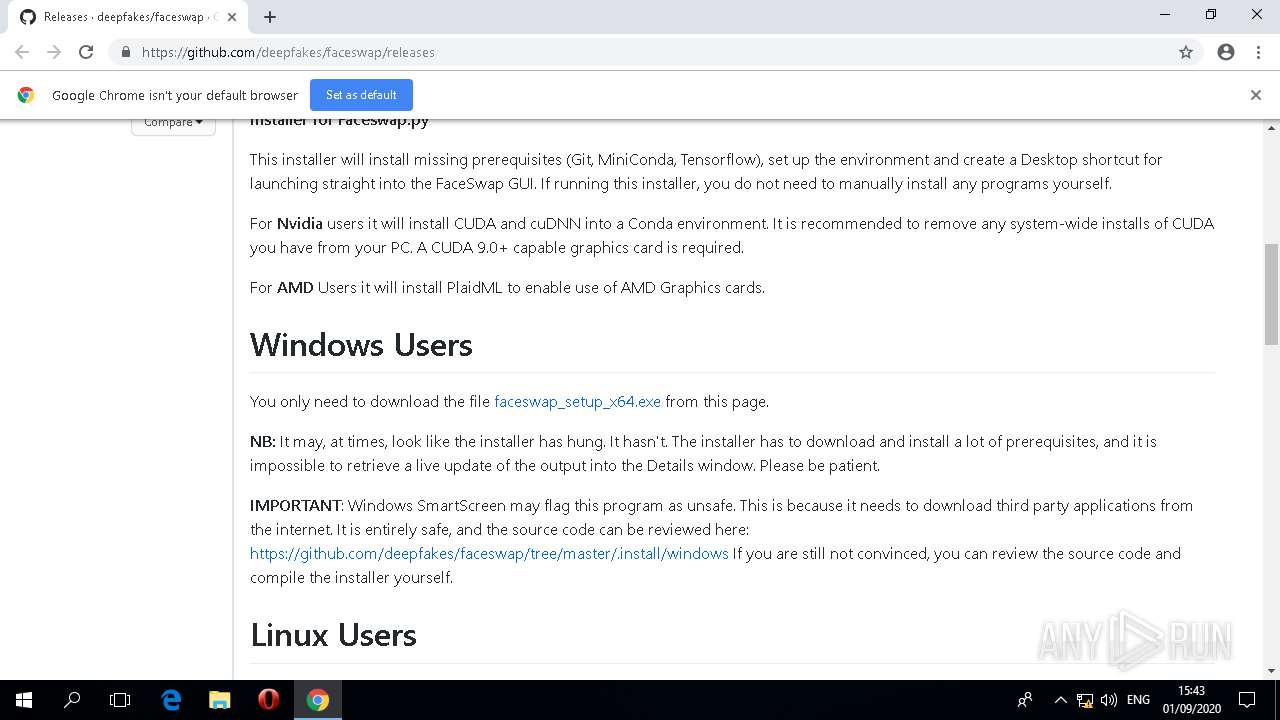
| URL: | https://github.com/deepfakes/faceswap/releases |
| Full analysis: | https://app.any.run/tasks/b3812065-7635-4aa4-8562-b9e5fa08775c |
| Verdict: | Malicious activity |
| Analysis date: | September 01, 2020, 14:42:46 |
| OS: | Windows 10 Professional (build: 16299, 64 bit) |
| Indicators: | |
| MD5: | B1D0C216652B9A99B376138C0790F665 |
| SHA1: | 1F96855EA906FC54159BFF8D871A1E1D4E3CA00D |
| SHA256: | 1E4BE4BCFFD24ED11268C39BC7E9E54A272B35C456169F58E618C56931504968 |
| SSDEEP: | 3:N8tEdxAAVDEvWdWS8IE2n:2uATWdV8Irn |
MALICIOUS
Application was dropped or rewritten from another process
- faceswap_setup_x64.exe (PID: 2168)
- faceswap_setup_x64.exe (PID: 3612)
- _conda.exe (PID: 4836)
- _conda.exe (PID: 3908)
- _conda.exe (PID: 3972)
- _conda.exe (PID: 4040)
- _conda.exe (PID: 1364)
- _conda.exe (PID: 3640)
- _conda.exe (PID: 1972)
- _conda.exe (PID: 3060)
- _conda.exe (PID: 4416)
- _conda.exe (PID: 3408)
- Miniconda3.exe (PID: 1680)
- conda.exe (PID: 1384)
- conda.exe (PID: 2108)
- conda.exe (PID: 2336)
- conda.exe (PID: 2532)
- conda.exe (PID: 324)
- conda.exe (PID: 1512)
- conda.exe (PID: 364)
- python.exe (PID: 3400)
- python.exe (PID: 724)
- python.exe (PID: 4544)
- python.exe (PID: 2820)
- python.exe (PID: 2400)
- python.exe (PID: 2788)
- python.exe (PID: 2684)
- python.exe (PID: 4644)
- python.exe (PID: 3832)
- pythonw.exe (PID: 3132)
- pythonw.exe (PID: 1640)
- pythonw.exe (PID: 2844)
Loads dropped or rewritten executable
- faceswap_setup_x64.exe (PID: 3612)
- Miniconda3.exe (PID: 1680)
- _conda.exe (PID: 1364)
- _conda.exe (PID: 4836)
- _conda.exe (PID: 3908)
- _conda.exe (PID: 4040)
- _conda.exe (PID: 3640)
- _conda.exe (PID: 3060)
- _conda.exe (PID: 3408)
- python.exe (PID: 4544)
- pythonw.exe (PID: 1640)
- pythonw.exe (PID: 2844)
- pythonw.exe (PID: 3132)
- python.exe (PID: 3400)
- python.exe (PID: 2820)
- python.exe (PID: 724)
- python.exe (PID: 2788)
- python.exe (PID: 2400)
- python.exe (PID: 4644)
- python.exe (PID: 3832)
- python.exe (PID: 2684)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2024)
- faceswap_setup_x64.exe (PID: 3612)
- Miniconda3.exe (PID: 1680)
- _conda.exe (PID: 3640)
- _conda.exe (PID: 3972)
- _conda.exe (PID: 4040)
- _conda.exe (PID: 1364)
- _conda.exe (PID: 4836)
- _conda.exe (PID: 3060)
- _conda.exe (PID: 1972)
- _conda.exe (PID: 4416)
- python.exe (PID: 2820)
- python.exe (PID: 3832)
Reads the machine GUID from the registry
- faceswap_setup_x64.exe (PID: 3612)
- _conda.exe (PID: 3908)
- _conda.exe (PID: 3640)
- _conda.exe (PID: 4836)
- _conda.exe (PID: 4040)
- _conda.exe (PID: 1364)
- _conda.exe (PID: 3060)
- python.exe (PID: 4544)
- _conda.exe (PID: 3408)
- pythonw.exe (PID: 3132)
- pythonw.exe (PID: 1640)
- pythonw.exe (PID: 2844)
- python.exe (PID: 3400)
- python.exe (PID: 2820)
- python.exe (PID: 724)
- python.exe (PID: 2400)
Application launched itself
- _conda.exe (PID: 3972)
- _conda.exe (PID: 3908)
- _conda.exe (PID: 1972)
- cmd.exe (PID: 2408)
- _conda.exe (PID: 4416)
- cmd.exe (PID: 4048)
Loads Python modules
- _conda.exe (PID: 3908)
- _conda.exe (PID: 4836)
- _conda.exe (PID: 4040)
- _conda.exe (PID: 1364)
- _conda.exe (PID: 3640)
- _conda.exe (PID: 3060)
- python.exe (PID: 4544)
- pythonw.exe (PID: 2844)
- pythonw.exe (PID: 3132)
- pythonw.exe (PID: 1640)
- _conda.exe (PID: 3408)
- python.exe (PID: 2820)
- python.exe (PID: 3400)
- python.exe (PID: 724)
- python.exe (PID: 2788)
- python.exe (PID: 2400)
- python.exe (PID: 3832)
- python.exe (PID: 2684)
- python.exe (PID: 4644)
Starts CMD.EXE for commands execution
- _conda.exe (PID: 1364)
- _conda.exe (PID: 4040)
- _conda.exe (PID: 4836)
- _conda.exe (PID: 3640)
- cmd.exe (PID: 2408)
- _conda.exe (PID: 3060)
- pythonw.exe (PID: 3132)
- faceswap_setup_x64.exe (PID: 3612)
- cmd.exe (PID: 4048)
- python.exe (PID: 2820)
- python.exe (PID: 3832)
Starts application with an unusual extension
- cmd.exe (PID: 4124)
- cmd.exe (PID: 2408)
- cmd.exe (PID: 1924)
- cmd.exe (PID: 4048)
Creates files in the program directory
- _conda.exe (PID: 3060)
Creates a software uninstall entry
- Miniconda3.exe (PID: 1680)
INFO
Reads the hosts file
- chrome.exe (PID: 2024)
Reads the software policy settings
- chrome.exe (PID: 2024)
Application launched itself
- chrome.exe (PID: 2024)
Reads the machine GUID from the registry
- chrome.exe (PID: 2024)
Reads settings of System Certificates
- chrome.exe (PID: 2024)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2024)
- Miniconda3.exe (PID: 1680)
- _conda.exe (PID: 3972)
- _conda.exe (PID: 4040)
- _conda.exe (PID: 1364)
- _conda.exe (PID: 4836)
- _conda.exe (PID: 1972)
- _conda.exe (PID: 3640)
- _conda.exe (PID: 3060)
- _conda.exe (PID: 4416)
- python.exe (PID: 2820)
- python.exe (PID: 3832)
Searches for installed software
- chrome.exe (PID: 2024)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
266
Monitored processes
168
Malicious processes
28
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||
|---|---|---|---|---|---|---|---|---|---|---|---|
| 216 | C:\WINDOWS\system32\cmd.exe /c "RD /S /Q "C:\Users\admin\MiniConda3\pkgs\certifi-2020.4.5.1-py38_00ptmpva4" > NUL 2> NUL" | C:\WINDOWS\system32\cmd.exe | — | _conda.exe | |||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||
| 216 | C:\WINDOWS\system32\cmd.exe /c "RD /S /Q "C:\Users\admin\MiniConda3\pkgs\urllib3-1.25.8-py38_0ucigv01s" > NUL 2> NUL" | C:\WINDOWS\system32\cmd.exe | — | _conda.exe | |||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||
| 312 | C:\WINDOWS\system32\cmd.exe /c "RD /S /Q "C:\Users\admin\MiniConda3\pkgs\cffi-1.14.0-py38h7a1dbc1_0ojrfaa_r" > NUL 2> NUL" | C:\WINDOWS\system32\cmd.exe | — | _conda.exe | |||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||
| 312 | C:\WINDOWS\system32\cmd.exe /c "RD /S /Q "C:\Users\admin\MiniConda3\pkgs\python-3.8.3-he1778fa_0yuc3gylz" > NUL 2> NUL" | C:\WINDOWS\system32\cmd.exe | — | _conda.exe | |||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||
| 324 | "C:\Users\admin\MiniConda3\condabin\..\Scripts\conda.exe" shell.cmd.exe activate "C:\Users\admin\MiniConda3" | C:\Users\admin\MiniConda3\Scripts\conda.exe | — | cmd.exe | |||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||
| 364 | C:\WINDOWS\system32\cmd.exe /c "RD /S /Q "C:\Users\admin\MiniConda3\pkgs\pycosat-0.6.3-py38he774522_00fz8k0y9" > NUL 2> NUL" | C:\WINDOWS\system32\cmd.exe | — | _conda.exe | |||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||
| 364 | "C:\Users\admin\MiniConda3\condabin\..\Scripts\conda.exe" create -y python=3.8 -n "faceswap" | C:\Users\admin\MiniConda3\Scripts\conda.exe | — | cmd.exe | |||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||
| 452 | C:\WINDOWS\system32\cmd.exe /c "RD /S /Q "C:\Users\admin\MiniConda3\pkgs\vs2015_runtime-14.16.27012-hf0eaf9b_3h7b80a47" > NUL 2> NUL" | C:\WINDOWS\system32\cmd.exe | — | python.exe | |||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||
| 580 | C:\WINDOWS\system32\cmd.exe /c "RD /S /Q "C:\Users\admin\MiniConda3\pkgs\ruamel_yaml-0.15.87-py38he774522_183ft3jhp" > NUL 2> NUL" | C:\WINDOWS\system32\cmd.exe | — | python.exe | |||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||
| 668 | C:\WINDOWS\system32\cmd.exe /c "RD /S /Q "C:\Users\admin\MiniConda3\pkgs\pysocks-1.7.1-py38_08ov1me9n" > NUL 2> NUL" | C:\WINDOWS\system32\cmd.exe | — | _conda.exe | |||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||
Total events
3 553
Read events
3 441
Write events
108
Delete events
4
Modification events
| (PID) Process: | (2024) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2024) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2024) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2024) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2024) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2024) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3164) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2024-13243444981897802 |
Value: 259 | |||
| (PID) Process: | (2024) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2024) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 4000-13240569530726669 |
Value: 0 | |||
| (PID) Process: | (2024) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
1 089
Suspicious files
5 421
Text files
13 577
Unknown types
115
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000012.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\39a8bce8-e045-4cf4-a29b-bd3909346d26.tmp | — | |
MD5:— | SHA256:— | |||
| 2024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Extension Settings\pkedcjkdefgpdelpbcmbmeomcjbeemfm\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\f_00000b | compressed | |
MD5:— | SHA256:— | |||
| 2024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\f_00000c | compressed | |
MD5:— | SHA256:— | |||
| 2024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 2024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
47
DNS requests
23
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2024 | chrome.exe | 172.217.22.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2024 | chrome.exe | 185.199.109.154:443 | github.githubassets.com | GitHub, Inc. | NL | suspicious |
2024 | chrome.exe | 151.101.0.133:443 | avatars1.githubusercontent.com | Fastly | US | malicious |
2024 | chrome.exe | 216.58.208.46:443 | clients1.google.com | Google Inc. | US | whitelisted |
2024 | chrome.exe | 216.58.206.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
2024 | chrome.exe | 172.217.22.78:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2024 | chrome.exe | 52.206.227.240:443 | collector.githubapp.com | Amazon.com, Inc. | US | unknown |
2024 | chrome.exe | 140.82.121.6:443 | api.github.com | — | US | suspicious |
2024 | chrome.exe | 216.58.207.68:443 | www.google.com | Google Inc. | US | whitelisted |
2024 | chrome.exe | 216.58.205.227:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
github.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
github.githubassets.com |
| whitelisted |
avatars1.githubusercontent.com |
| whitelisted |
avatars0.githubusercontent.com |
| whitelisted |
avatars2.githubusercontent.com |
| whitelisted |
avatars3.githubusercontent.com |
| whitelisted |
github-cloud.s3.amazonaws.com |
| shared |
user-images.githubusercontent.com |
| whitelisted |
Threats
Process | Message |
|---|---|
conhost.exe | InitSideBySide failed create an activation context. Error: 1814 |
conhost.exe | InitSideBySide failed create an activation context. Error: 1814 |
_conda.exe | Shortcut cmd is %windir%\System32\cmd.exe, args are ['"/K"', 'C:\\Users\\admin\\MiniConda3\\Scripts\\activate.bat', 'C:\\Users\\admin\\MiniConda3'] |
_conda.exe | Menu: name: 'Anaconda${PY_VER} ${PLATFORM}', prefix: 'C:\Users\admin\MiniConda3', env_name: 'MiniConda3', mode: 'system', used_mode: 'system' |
_conda.exe | Shortcut cmd is %windir%\System32\WindowsPowerShell\v1.0\powershell.exe, args are ['-ExecutionPolicy', 'ByPass', '-NoExit', '-Command', '"& \'C:\\Users\\admin\\MiniConda3\\shell\\condabin\\conda-hook.ps1\' ; conda activate \'C:\\Users\\admin\\MiniConda3\' "'] |
_conda.exe | Menu: name: 'Anaconda${PY_VER} ${PLATFORM}', prefix: 'C:\Users\admin\MiniConda3', env_name: 'MiniConda3', mode: 'system', used_mode: 'system' |
conhost.exe | InitSideBySide failed create an activation context. Error: 1814 |
_conda.exe | Menu: name: 'Anaconda${PY_VER} ${PLATFORM}', prefix: 'C:\Users\admin\MiniConda3', env_name: 'MiniConda3', mode: 'system', used_mode: 'system' |
_conda.exe | Shortcut cmd is %windir%\System32\cmd.exe, args are ['"/K"', 'C:\\Users\\admin\\MiniConda3\\Scripts\\activate.bat', 'C:\\Users\\admin\\MiniConda3'] |
_conda.exe | Shortcut cmd is %windir%\System32\WindowsPowerShell\v1.0\powershell.exe, args are ['-ExecutionPolicy', 'ByPass', '-NoExit', '-Command', '"& \'C:\\Users\\admin\\MiniConda3\\shell\\condabin\\conda-hook.ps1\' ; conda activate \'C:\\Users\\admin\\MiniConda3\' "'] |