| File name: | 7z920.exe |
| Full analysis: | https://app.any.run/tasks/4274be7e-39fd-4fe3-a8a9-f14c514ecb66 |
| Verdict: | Malicious activity |
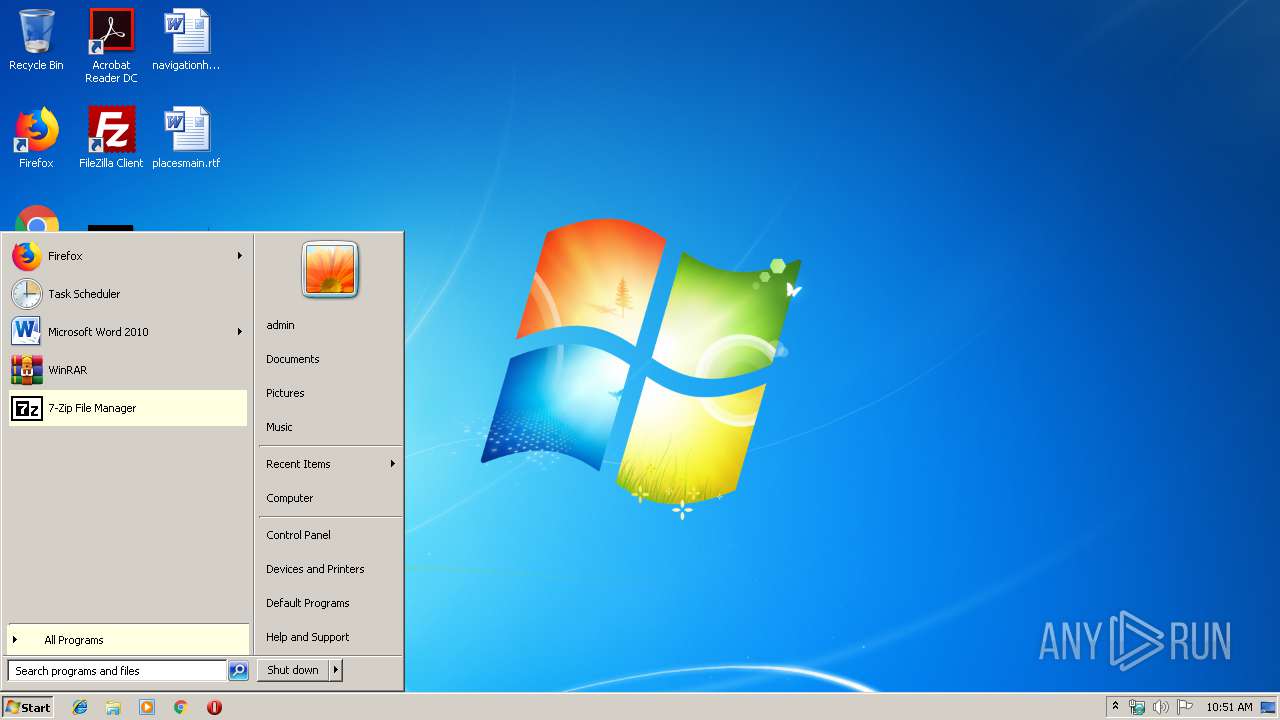
| Analysis date: | October 11, 2019, 09:51:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | B3FDF6E7B0AECD48CA7E4921773FB606 |
| SHA1: | 55283AD59439134673FC32FC097BDD9AE920FBC6 |
| SHA256: | 1E2F2A8FB52D3972B9B65B8AD1BEBB66965C47A2994F89B3D652C31E6F6E4C3C |
| SSDEEP: | 24576:c7Rz+6GVlkicMgH6I7kuF7Xc+qaM9oXDEmHbGrXjk5rOTm:E+6cY75ZLqaMsDp6ro6m |
MALICIOUS
Loads dropped or rewritten executable
- 7z920.exe (PID: 3924)
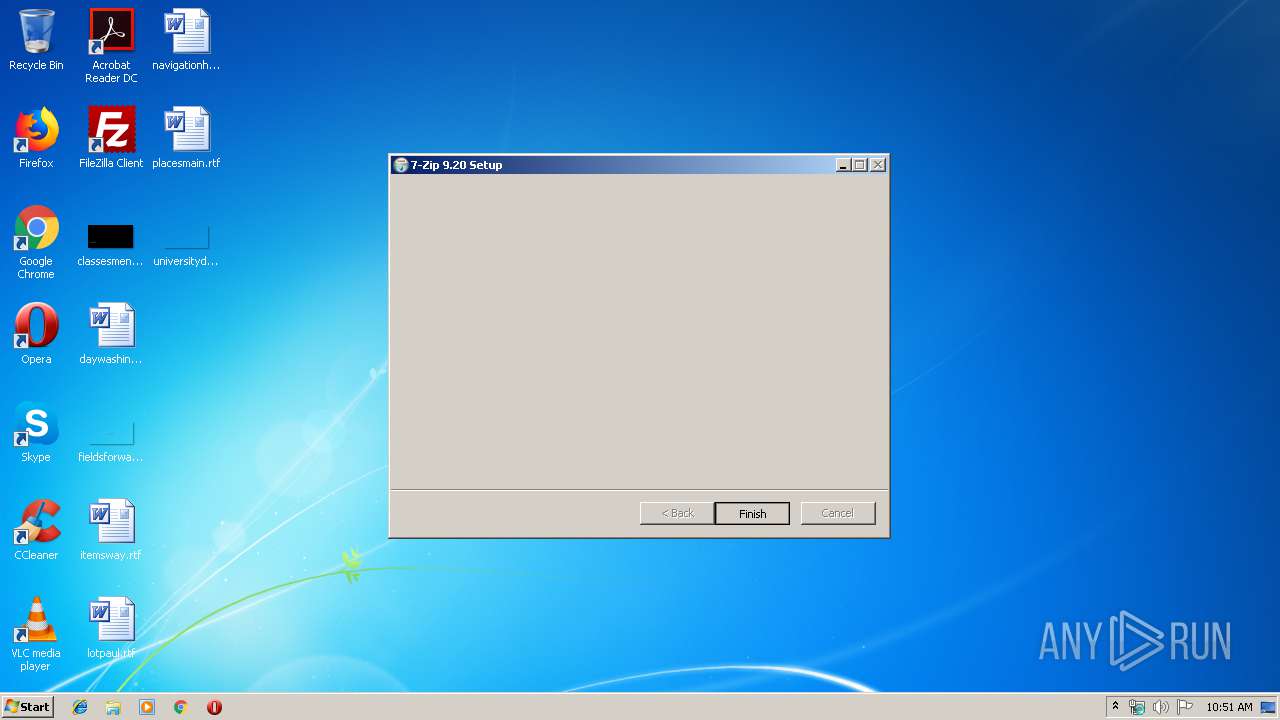
Application was dropped or rewritten from another process
- 7zFM.exe (PID: 2684)
SUSPICIOUS
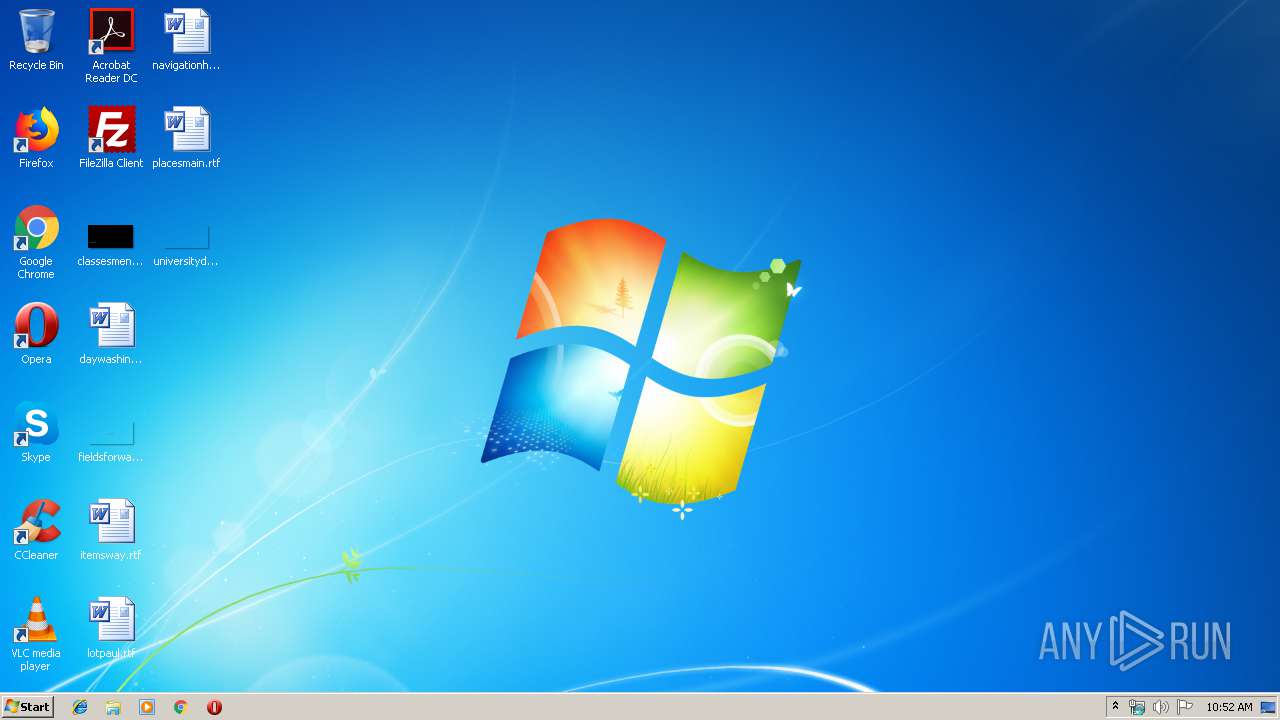
Executable content was dropped or overwritten
- 7z920.exe (PID: 3924)
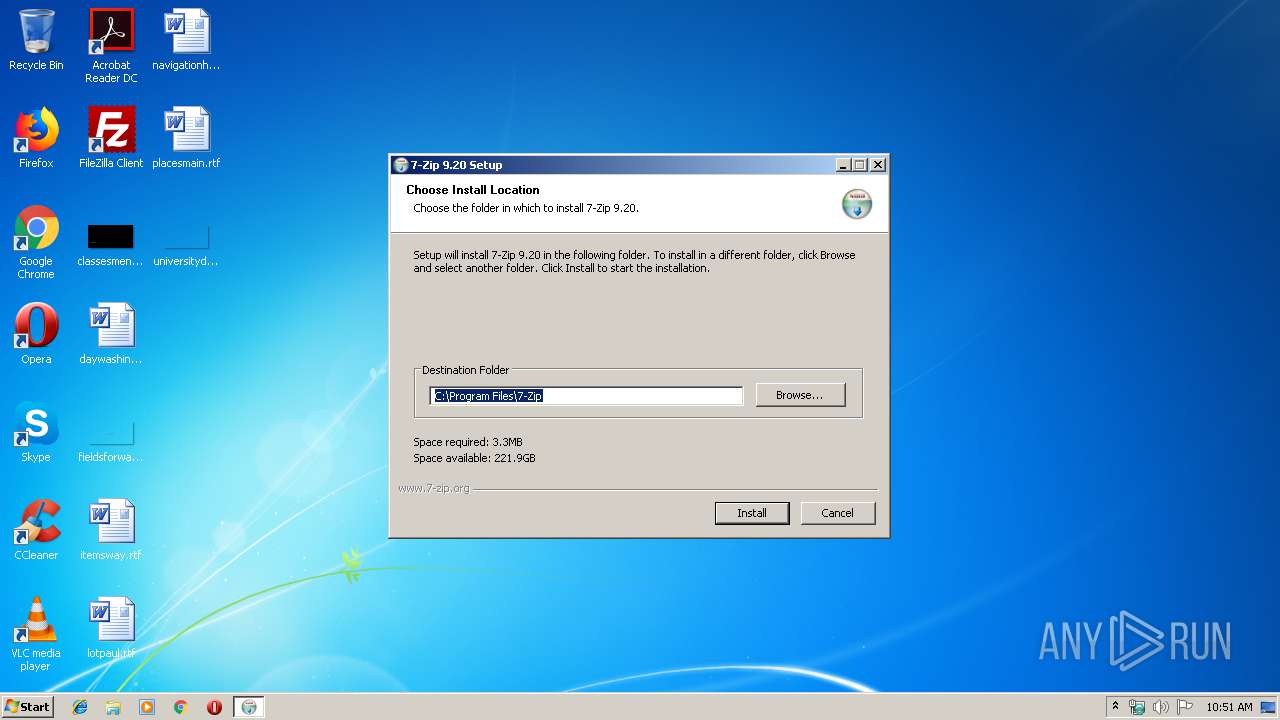
Creates a software uninstall entry
- 7z920.exe (PID: 3924)
Creates COM task schedule object
- 7z920.exe (PID: 3924)
Creates files in the program directory
- 7z920.exe (PID: 3924)
INFO
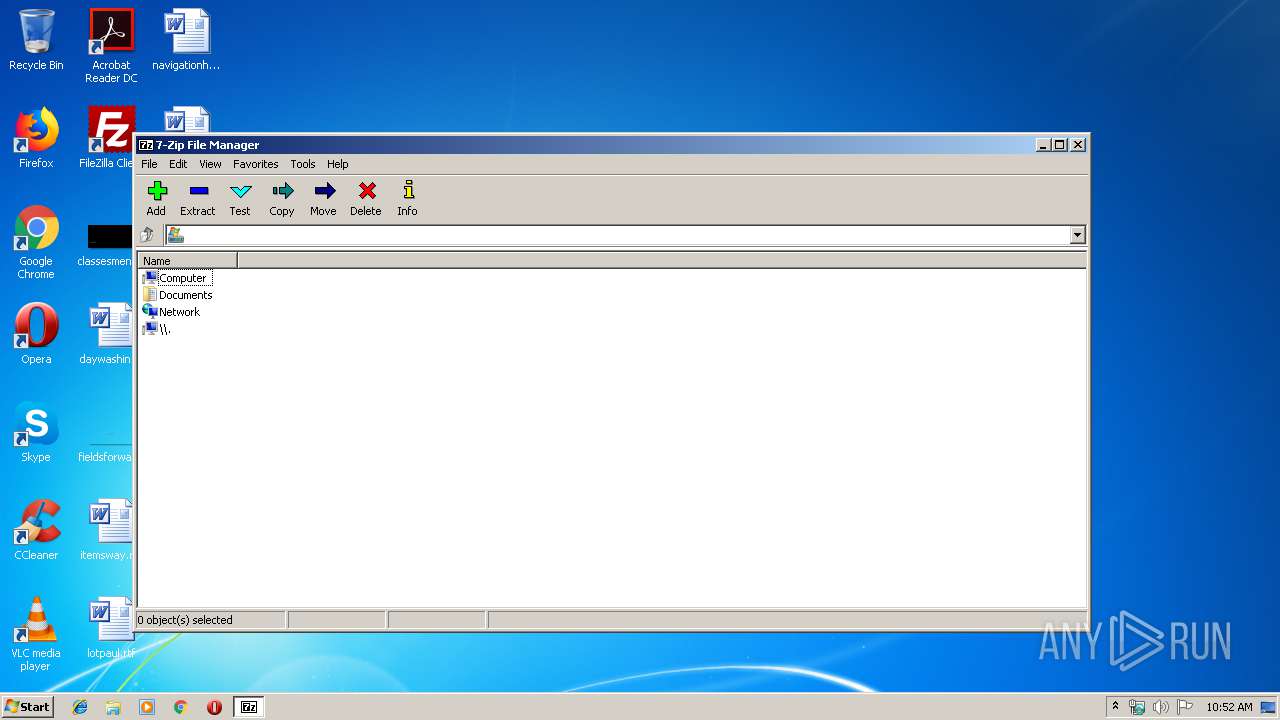
Manual execution by user
- 7zFM.exe (PID: 2684)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:12:05 23:50:46+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 23552 |
| InitializedDataSize: | 119808 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x323c |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Dec-2009 22:50:46 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-Dec-2009 22:50:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005A5A | 0x00005C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4177 |
.rdata | 0x00007000 | 0x00001190 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.18163 |
.data | 0x00009000 | 0x0001AF98 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.70903 |
.ndata | 0x00024000 | 0x00009000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0002D000 | 0x00004118 | 0x00004200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.85366 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.10394 | 533 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.9993 | 3752 | UNKNOWN | English - United States | RT_ICON |
3 | 6.24459 | 2216 | UNKNOWN | English - United States | RT_ICON |
4 | 5.01502 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 6.16057 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 3.34146 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 3.04232 | 296 | UNKNOWN | English - United States | RT_ICON |
103 | 2.6691 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
39
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 960 | "C:\Users\admin\AppData\Local\Temp\7z920.exe" | C:\Users\admin\AppData\Local\Temp\7z920.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2684 | "C:\Program Files\7-Zip\7zFM.exe" | C:\Program Files\7-Zip\7zFM.exe | — | explorer.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip File Manager Exit code: 0 Version: 9.20 Modules
| |||||||||||||||
| 3924 | "C:\Users\admin\AppData\Local\Temp\7z920.exe" | C:\Users\admin\AppData\Local\Temp\7z920.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
398
Read events
380
Write events
18
Delete events
0
Modification events
| (PID) Process: | (3924) 7z920.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\7-Zip |
| Operation: | write | Name: | Path |
Value: C:\Program Files\7-Zip | |||
| (PID) Process: | (3924) 7z920.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip |
| Operation: | write | Name: | Path |
Value: C:\Program Files\7-Zip | |||
| (PID) Process: | (3924) 7z920.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{23170F69-40C1-278A-1000-000100020000} |
| Operation: | write | Name: | |
Value: 7-Zip Shell Extension | |||
| (PID) Process: | (3924) 7z920.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{23170F69-40C1-278A-1000-000100020000}\InprocServer32 |
| Operation: | write | Name: | |
Value: C:\Program Files\7-Zip\7-zip.dll | |||
| (PID) Process: | (3924) 7z920.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{23170F69-40C1-278A-1000-000100020000}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Apartment | |||
| (PID) Process: | (3924) 7z920.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\*\shellex\ContextMenuHandlers\7-Zip |
| Operation: | write | Name: | |
Value: {23170F69-40C1-278A-1000-000100020000} | |||
| (PID) Process: | (3924) 7z920.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Directory\shellex\ContextMenuHandlers\7-Zip |
| Operation: | write | Name: | |
Value: {23170F69-40C1-278A-1000-000100020000} | |||
| (PID) Process: | (3924) 7z920.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Directory\shellex\DragDropHandlers\7-Zip |
| Operation: | write | Name: | |
Value: {23170F69-40C1-278A-1000-000100020000} | |||
| (PID) Process: | (3924) 7z920.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Drive\shellex\DragDropHandlers\7-Zip |
| Operation: | write | Name: | |
Value: {23170F69-40C1-278A-1000-000100020000} | |||
| (PID) Process: | (3924) 7z920.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Approved |
| Operation: | write | Name: | {23170F69-40C1-278A-1000-000100020000} |
Value: 7-Zip Shell Extension | |||
Executable files
9
Suspicious files
0
Text files
88
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3924 | 7z920.exe | C:\Users\admin\AppData\Local\Temp\nsdA96B.tmp\ioSpecial.ini | text | |
MD5:— | SHA256:— | |||
| 3924 | 7z920.exe | C:\Users\admin\AppData\Local\Temp\nsdA96B.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
| 3924 | 7z920.exe | C:\Program Files\7-Zip\History.txt | text | |
MD5:9E5CDA548C986D78266FF93715A246D1 | SHA256:B41E94FC1018B2AE481C26F796E1A927AE8C007B8AFF9BAE27659D2C6EE5FF4D | |||
| 3924 | 7z920.exe | C:\Program Files\7-Zip\descript.ion | text | |
MD5:C39327F0BBB6EA743EB13FB884115337 | SHA256:06B7D929CB88AC23177BF1D82260128E523CDD0CC9FE28BF0F3FBF1EF5A35358 | |||
| 3924 | 7z920.exe | C:\Program Files\7-Zip\7zFM.exe | executable | |
MD5:1BCE2C02487972FF0D5E6702D79E7A75 | SHA256:581404635ECC46E2639144B248D85BED113DC4B1C9844F3A2A36DF418CB74B32 | |||
| 3924 | 7z920.exe | C:\Program Files\7-Zip\Lang\af.txt | text | |
MD5:77704967107C3119D163BF9C0505D764 | SHA256:6E2BD0855211D6498E399F6E75670CA5E52C6900E9FB8C0D3298EFB0F92C3D9F | |||
| 3924 | 7z920.exe | C:\Program Files\7-Zip\7z.sfx | executable | |
MD5:22B7B63701E266B7A78B2A0D225E0118 | SHA256:DBC65C261DA5DAEEF2C8F2A513276D0826FC1A18983777B47EB844C2F2EFB590 | |||
| 3924 | 7z920.exe | C:\Program Files\7-Zip\License.txt | text | |
MD5:6C46F4C2FB35B12B6909F82185E000C0 | SHA256:2D8543C36AE06CFDC87B9F93EBE2DF3055ABE967AC0E3CF5E9B25E6DC4FA25A7 | |||
| 3924 | 7z920.exe | C:\Program Files\7-Zip\7z.exe | executable | |
MD5:A51D90F2F9394F5EA0A3ACAE3BD2B219 | SHA256:AC9674FEB8F2FAD20C1E046DE67F899419276AE79A60E8CC021A4BF472AE044F | |||
| 3924 | 7z920.exe | C:\Program Files\7-Zip\7z.dll | executable | |
MD5:04AD4B80880B32C94BE8D0886482C774 | SHA256:A1E1D1F0FFF4FCCCFBDFA313F3BDFEA4D3DFE2C2D9174A615BBC39A0A6929338 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report