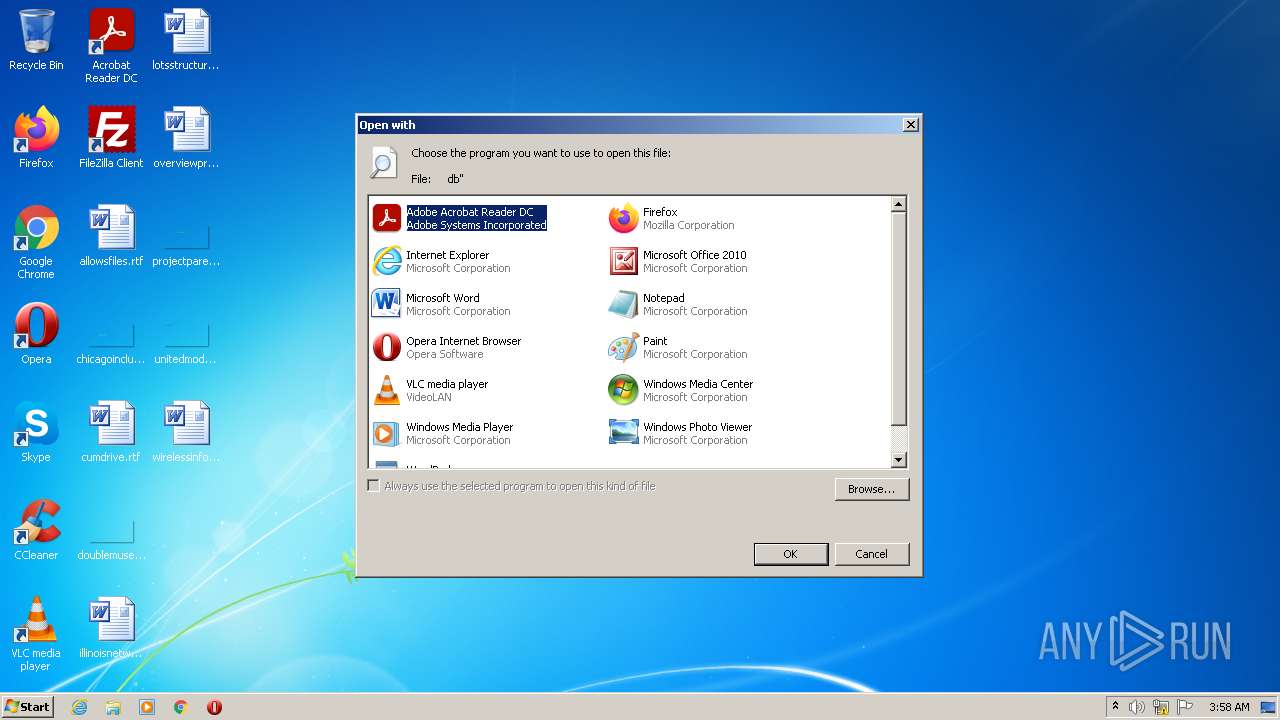
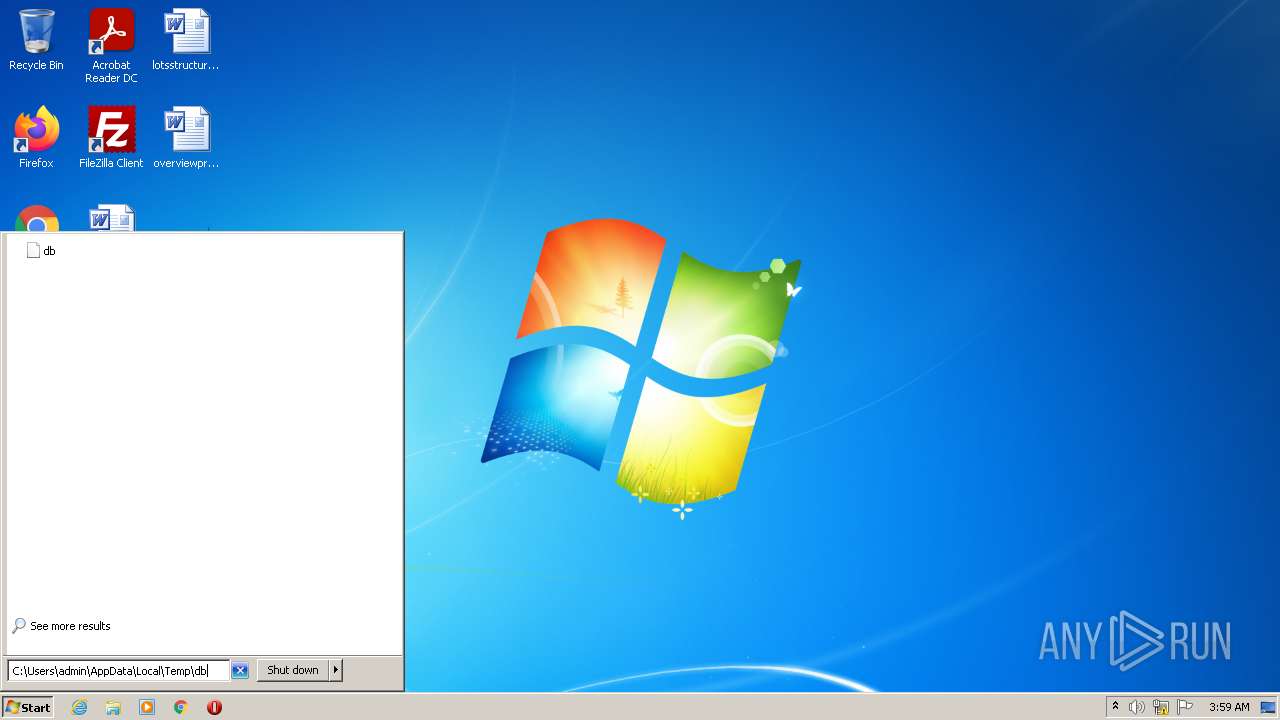
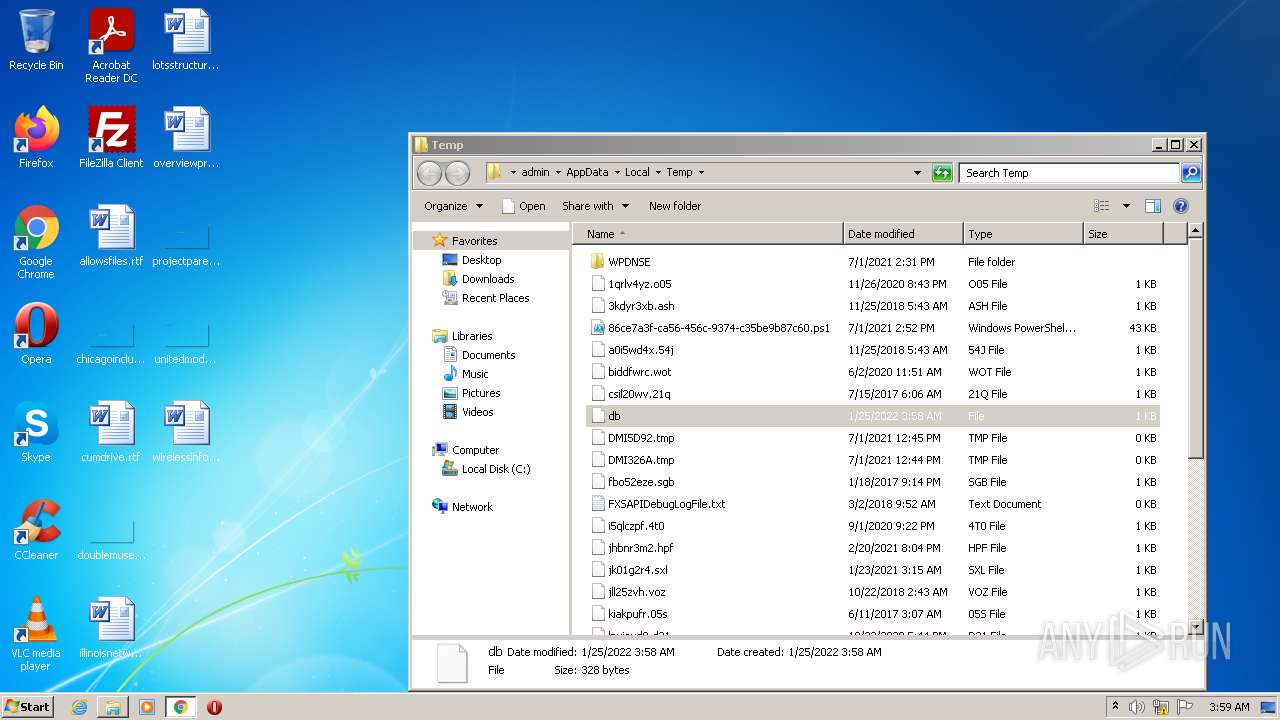
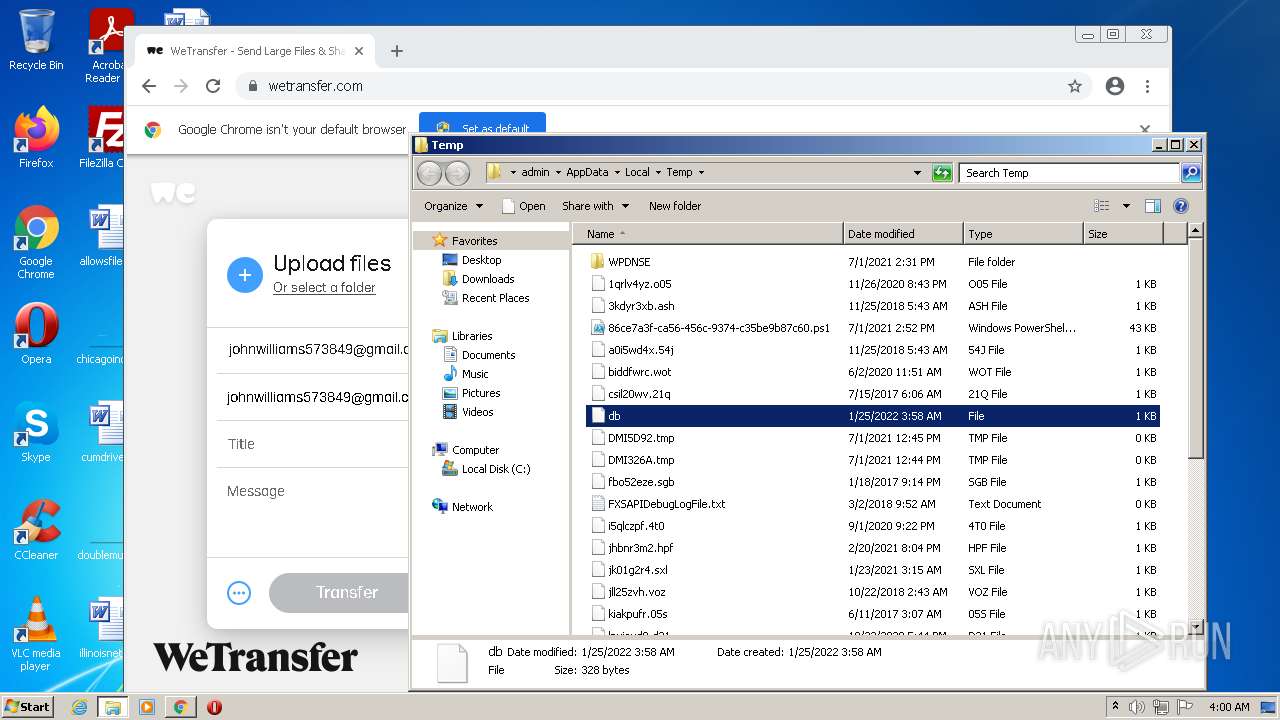
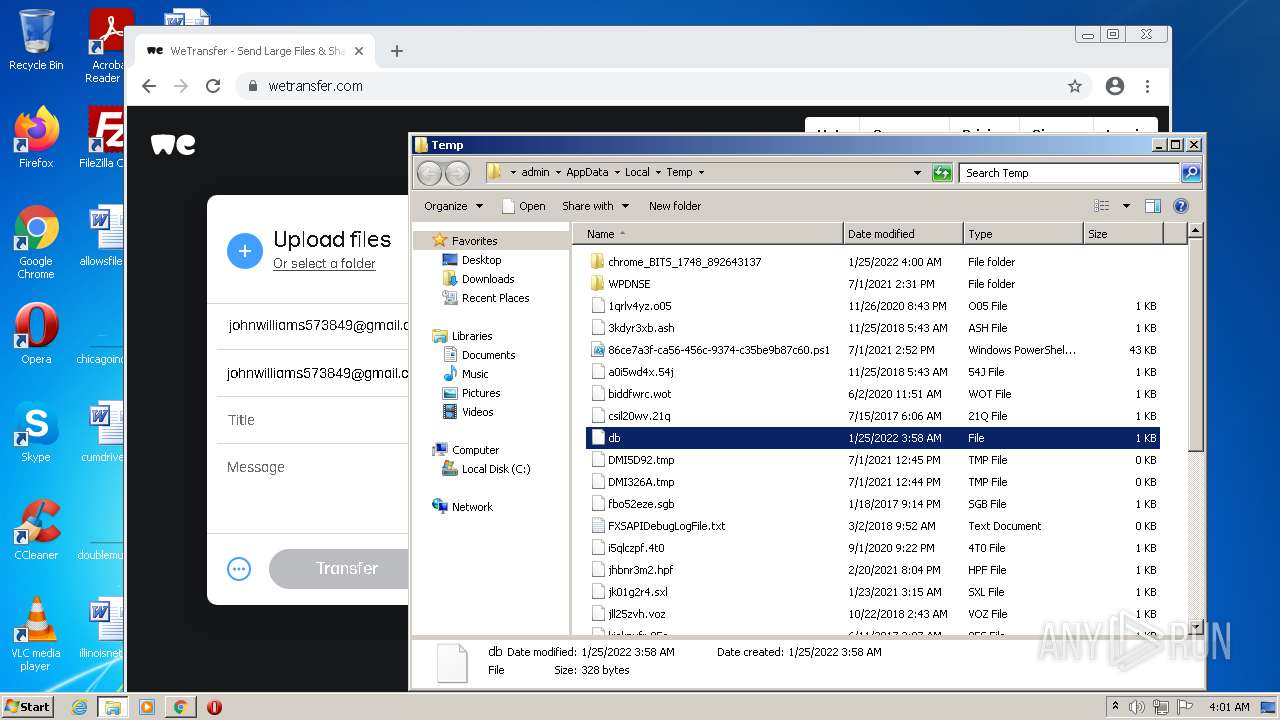
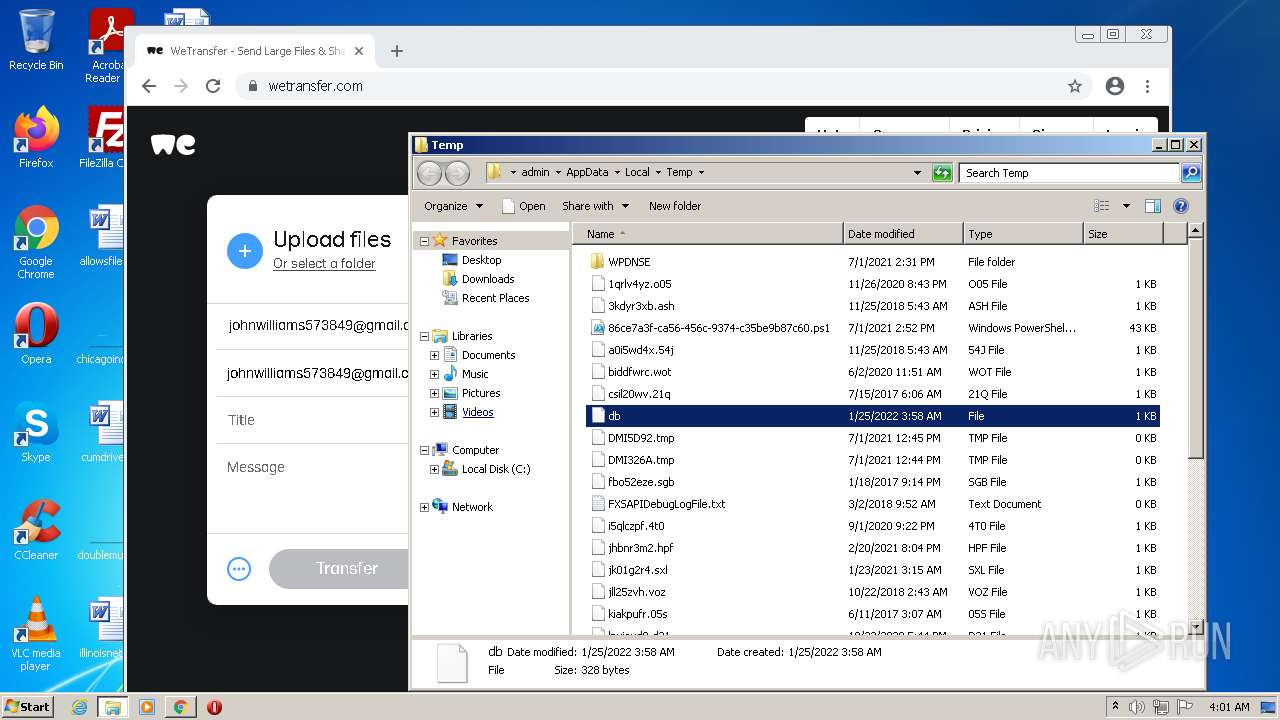
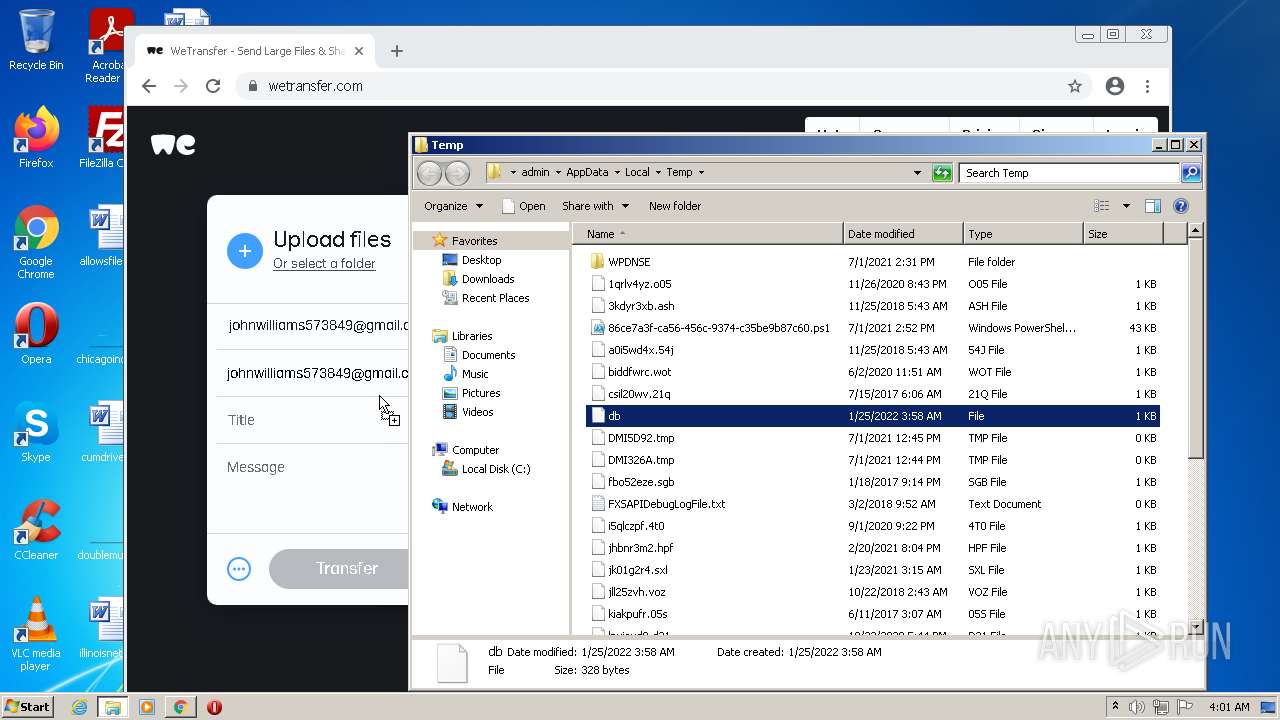
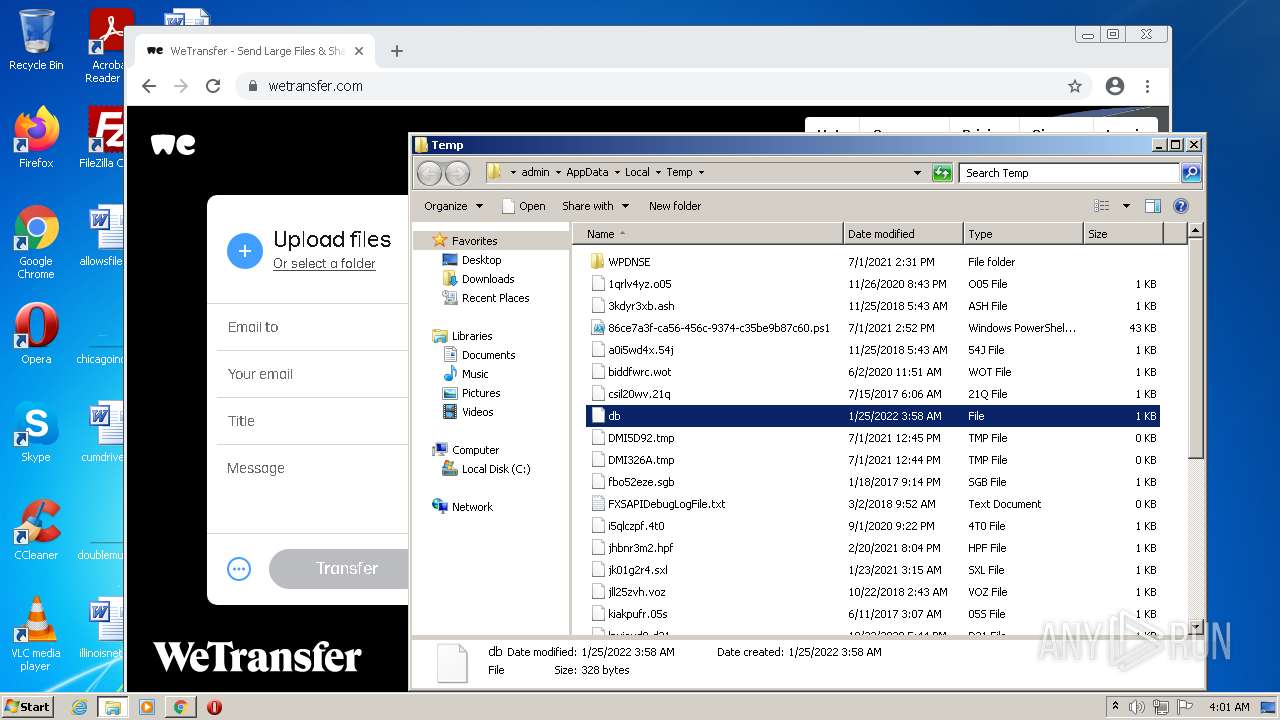
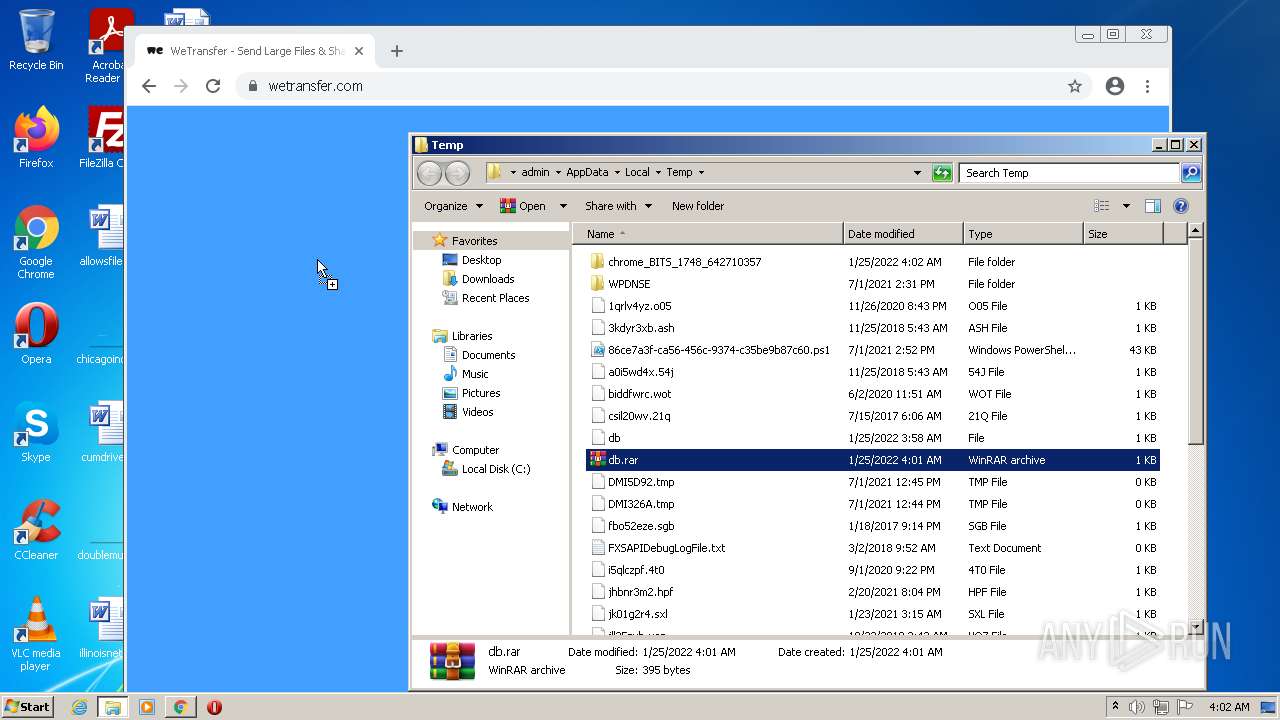
| File name: | C:\Users\admin\Documents\db |
| Full analysis: | https://app.any.run/tasks/dc7b3742-0e1e-4881-9c00-96bf04b5eb02 |
| Verdict: | Malicious activity |
| Analysis date: | January 25, 2022, 03:58:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/octet-stream |
| File info: | data |
| MD5: | 094BF47A15B388316983CF246435B312 |
| SHA1: | CF0F4517F3BD27D3446C339086C1D04A20718F01 |
| SHA256: | 1E2273789D7DFC61CF9CCE5B3DAB409D7954015248C532F5199028B502DF833F |
| SSDEEP: | 6:+JHQItuq2CBoxs8T4L//MElMy33cvHrbw17io4fDkFrpUXvOaoBLGjpUsVBZeT6F:+JQIsMB2UL3MElMy33cvHfw17iIFrpOH |
MALICIOUS
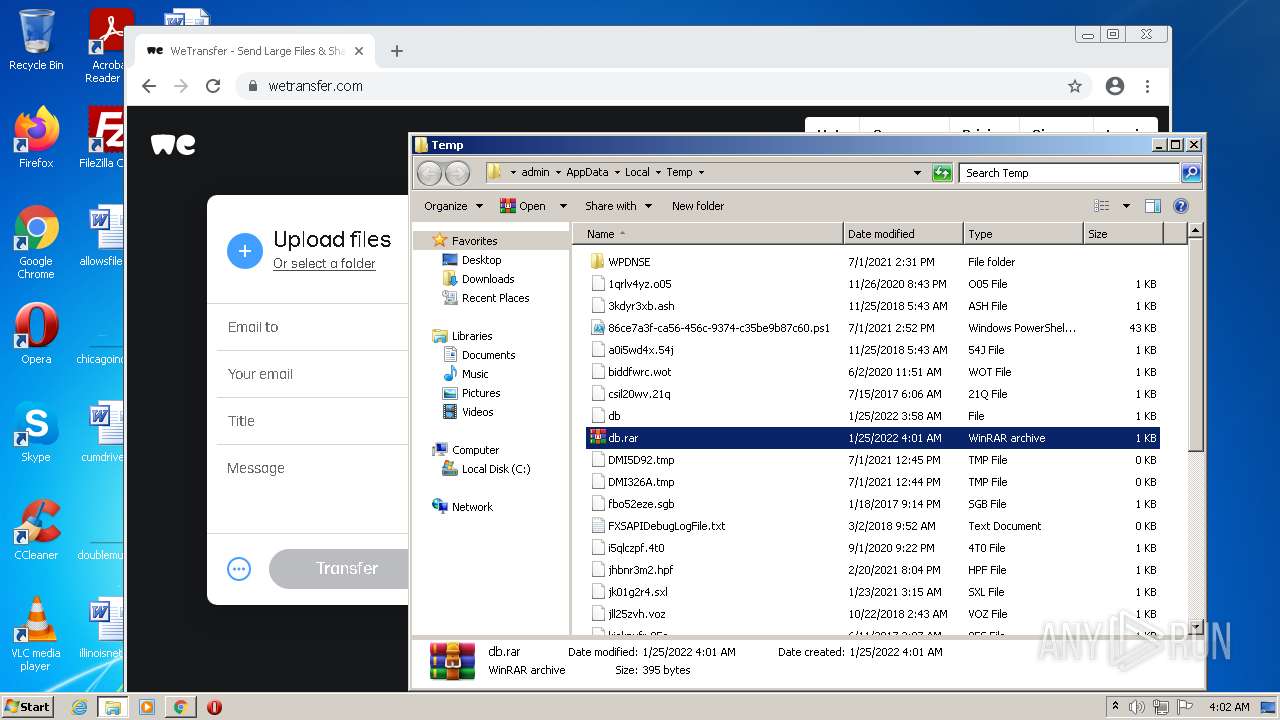
Drops executable file immediately after starts
- chrome.exe (PID: 3972)
SUSPICIOUS
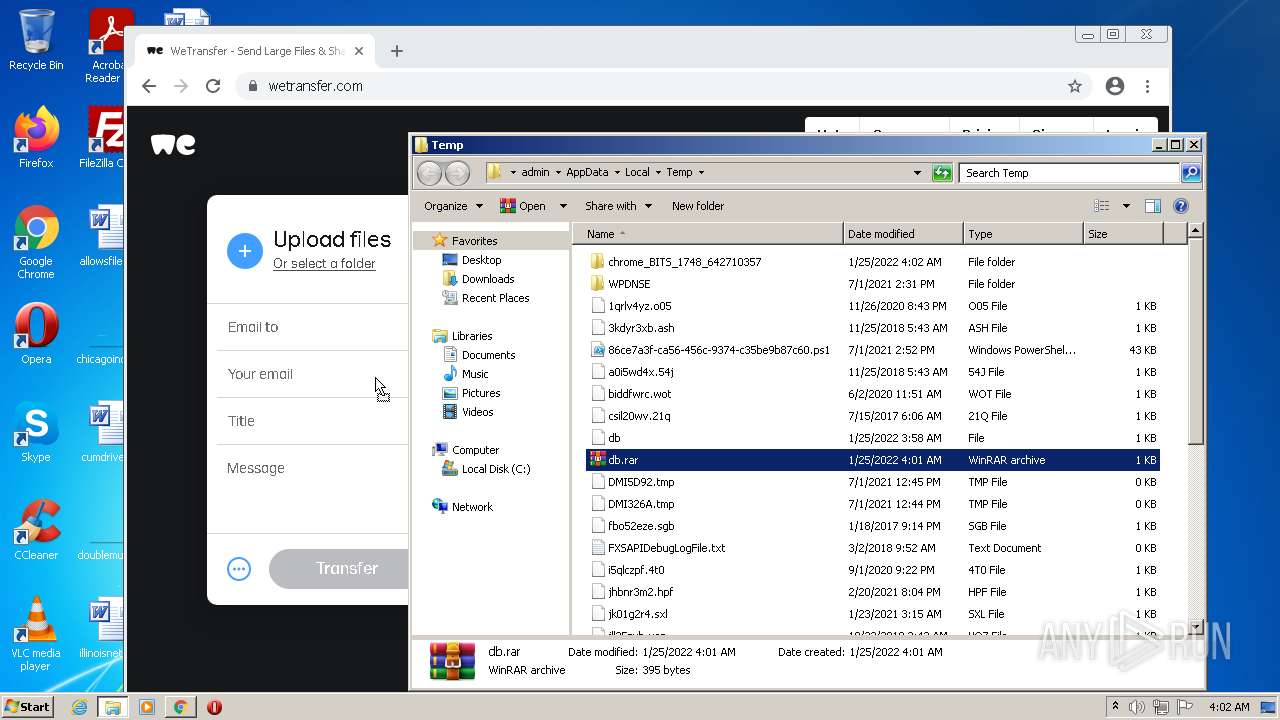
Modifies files in Chrome extension folder
- chrome.exe (PID: 1748)
Checks supported languages
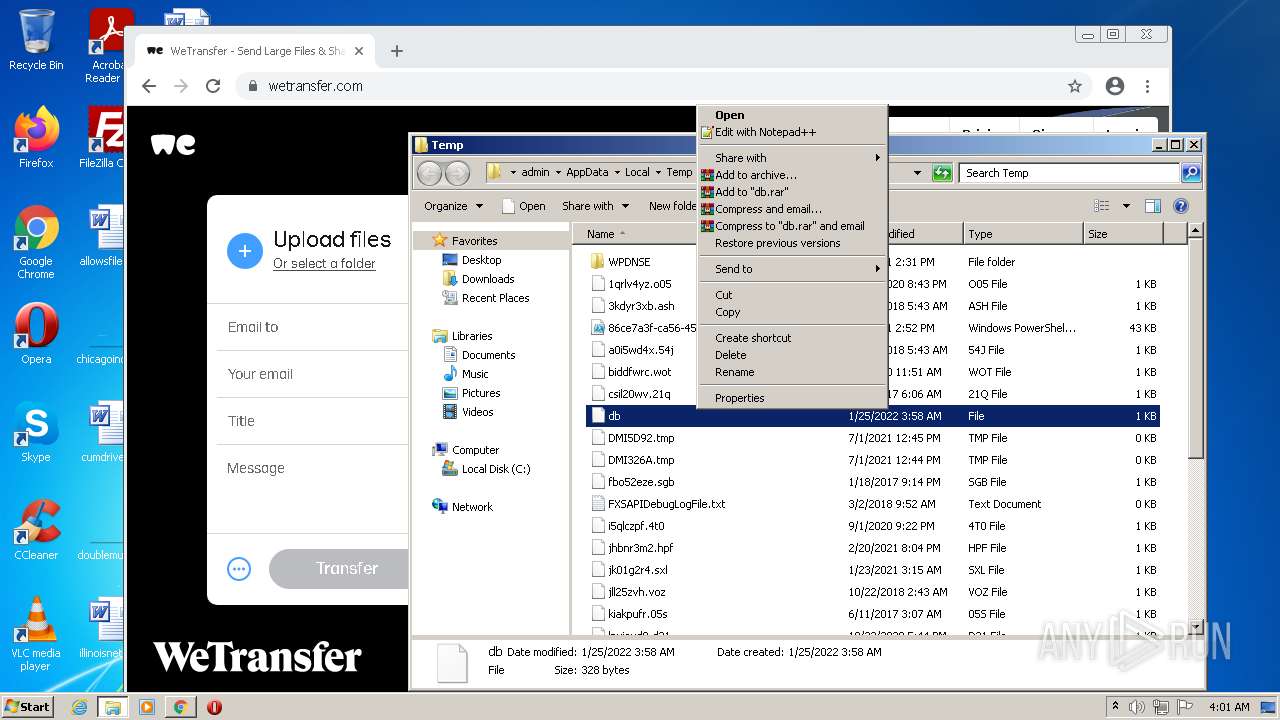
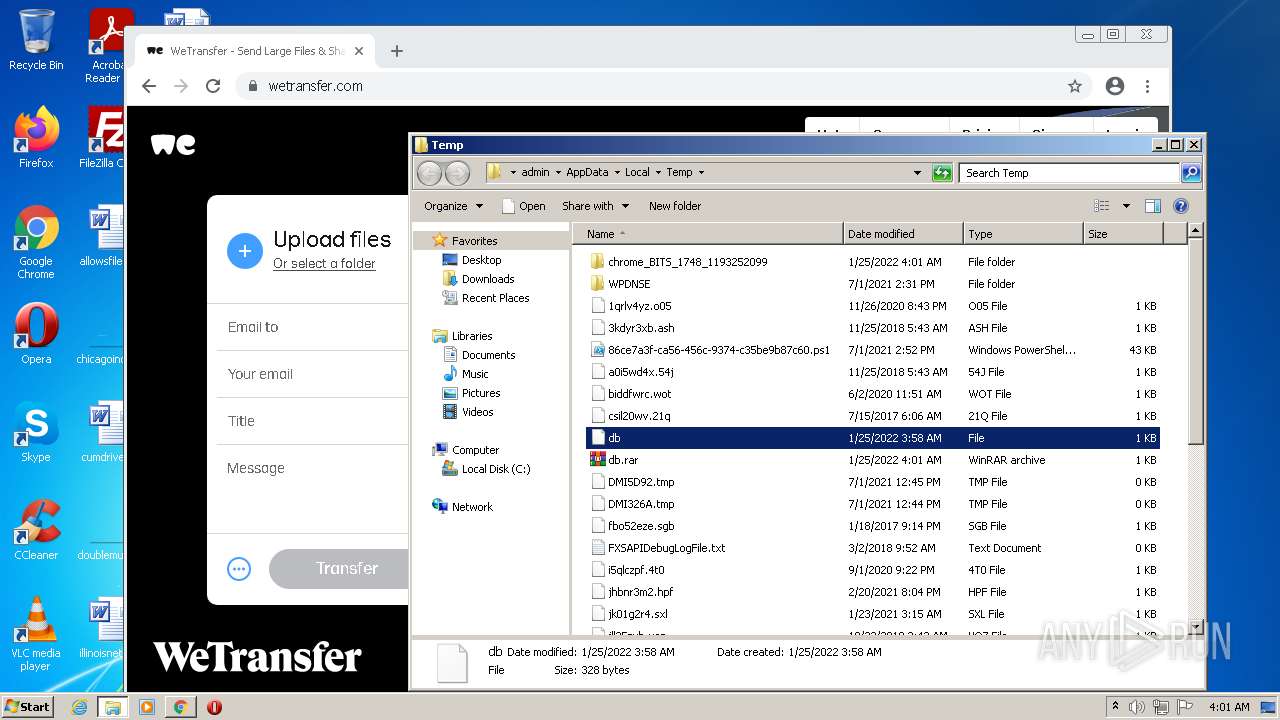
- WinRAR.exe (PID: 1260)
Reads the computer name
- WinRAR.exe (PID: 1260)
Drops a file that was compiled in debug mode
- chrome.exe (PID: 3972)
Executable content was dropped or overwritten
- chrome.exe (PID: 3972)
INFO
Checks supported languages
- rundll32.exe (PID: 1252)
- chrome.exe (PID: 1748)
- chrome.exe (PID: 1808)
- verclsid.exe (PID: 3732)
- chrome.exe (PID: 2376)
- chrome.exe (PID: 3608)
- chrome.exe (PID: 3200)
- chrome.exe (PID: 3492)
- chrome.exe (PID: 3228)
- chrome.exe (PID: 1596)
- chrome.exe (PID: 2336)
- chrome.exe (PID: 1968)
- chrome.exe (PID: 3912)
- chrome.exe (PID: 3616)
- chrome.exe (PID: 3180)
- chrome.exe (PID: 2412)
- chrome.exe (PID: 2420)
- chrome.exe (PID: 888)
- chrome.exe (PID: 1160)
- chrome.exe (PID: 3924)
- chrome.exe (PID: 4076)
- chrome.exe (PID: 3644)
- chrome.exe (PID: 3680)
- chrome.exe (PID: 3552)
- chrome.exe (PID: 1552)
- chrome.exe (PID: 2852)
- chrome.exe (PID: 3412)
- chrome.exe (PID: 2512)
- chrome.exe (PID: 2252)
- chrome.exe (PID: 2520)
- chrome.exe (PID: 3860)
- chrome.exe (PID: 1088)
- chrome.exe (PID: 3504)
- chrome.exe (PID: 1472)
- chrome.exe (PID: 2436)
- chrome.exe (PID: 3976)
- chrome.exe (PID: 2728)
- chrome.exe (PID: 2792)
- chrome.exe (PID: 3972)
- chrome.exe (PID: 520)
- chrome.exe (PID: 2524)
- chrome.exe (PID: 1436)
- chrome.exe (PID: 1592)
- chrome.exe (PID: 3384)
- chrome.exe (PID: 2868)
- chrome.exe (PID: 4088)
- chrome.exe (PID: 188)
- chrome.exe (PID: 2112)
- chrome.exe (PID: 868)
- chrome.exe (PID: 2288)
- chrome.exe (PID: 532)
- chrome.exe (PID: 1240)
- chrome.exe (PID: 3032)
- chrome.exe (PID: 3576)
- chrome.exe (PID: 2504)
- chrome.exe (PID: 2832)
- chrome.exe (PID: 3972)
- chrome.exe (PID: 272)
- chrome.exe (PID: 3832)
- chrome.exe (PID: 3792)
- chrome.exe (PID: 3124)
- chrome.exe (PID: 3372)
- chrome.exe (PID: 3572)
- chrome.exe (PID: 740)
- chrome.exe (PID: 3632)
- chrome.exe (PID: 1408)
- chrome.exe (PID: 828)
- chrome.exe (PID: 2940)
- chrome.exe (PID: 3972)
- chrome.exe (PID: 2612)
- chrome.exe (PID: 2056)
- chrome.exe (PID: 2320)
- chrome.exe (PID: 4072)
- chrome.exe (PID: 1888)
- chrome.exe (PID: 868)
- chrome.exe (PID: 1096)
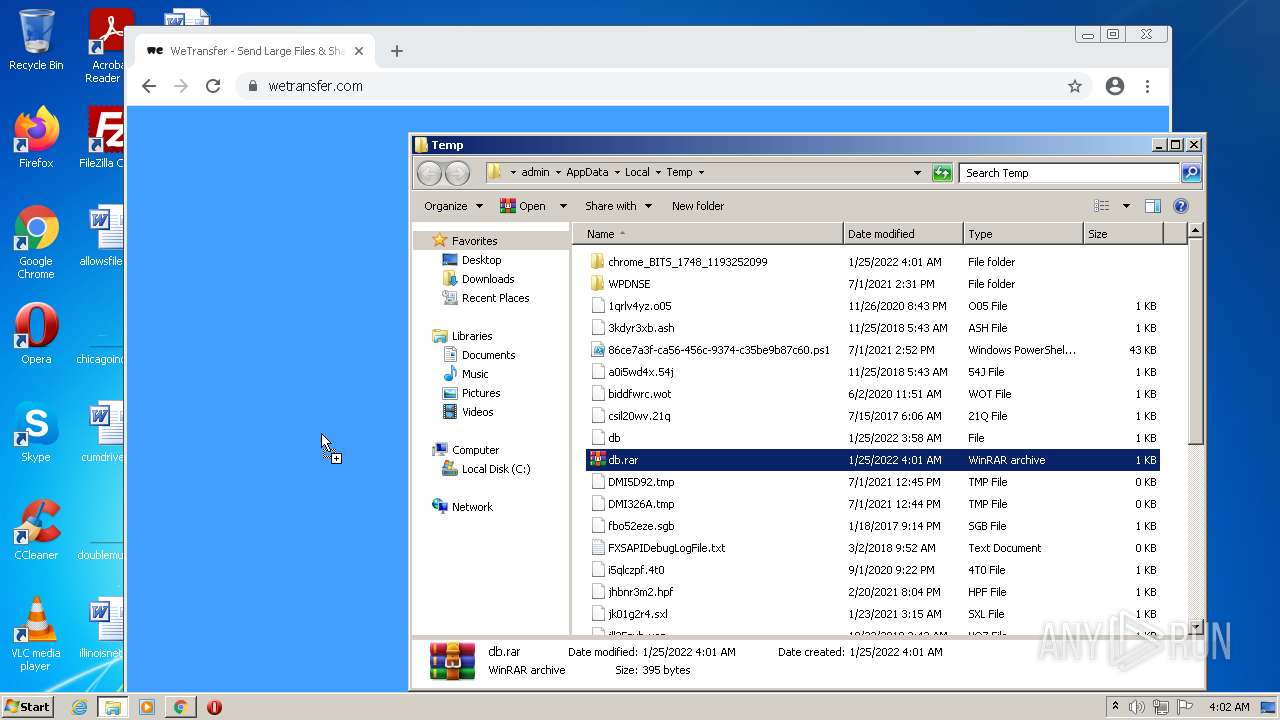
Manual execution by user
- chrome.exe (PID: 1748)
- verclsid.exe (PID: 3732)
- WinRAR.exe (PID: 1260)
Reads the computer name
- rundll32.exe (PID: 1252)
- chrome.exe (PID: 1748)
- chrome.exe (PID: 1808)
- chrome.exe (PID: 3492)
- chrome.exe (PID: 1596)
- chrome.exe (PID: 3924)
- chrome.exe (PID: 3860)
- chrome.exe (PID: 2520)
- chrome.exe (PID: 3504)
Application launched itself
- chrome.exe (PID: 1748)
Reads the hosts file
- chrome.exe (PID: 3492)
- chrome.exe (PID: 1748)
Reads settings of System Certificates
- chrome.exe (PID: 3492)
Reads the date of Windows installation
- chrome.exe (PID: 2520)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
114
Monitored processes
77
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1060,12752699945844104804,1509877209365278002,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2088 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,12752699945844104804,1509877209365278002,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=49 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1468 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,12752699945844104804,1509877209365278002,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --instant-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=31 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3308 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,12752699945844104804,1509877209365278002,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=52 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2080 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 740 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1060,12752699945844104804,1509877209365278002,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2772 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 828 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,12752699945844104804,1509877209365278002,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=66 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2076 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 868 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1060,12752699945844104804,1509877209365278002,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3236 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 868 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1060,12752699945844104804,1509877209365278002,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3544 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 888 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1060,12752699945844104804,1509877209365278002,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3372 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1088 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1060,12752699945844104804,1509877209365278002,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2632 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
26 432
Read events
26 259
Write events
165
Delete events
8
Modification events
| (PID) Process: | (1252) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\eHome\ehshell.exe |
Value: Windows Media Center | |||
| (PID) Process: | (1252) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: Firefox | |||
| (PID) Process: | (1252) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\mspaint.exe |
Value: Paint | |||
| (PID) Process: | (1252) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\NOTEPAD.EXE |
Value: Notepad | |||
| (PID) Process: | (1252) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\PROGRA~1\MICROS~1\Office14\OIS.EXE |
Value: Microsoft Office 2010 | |||
| (PID) Process: | (1252) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Opera\Opera.exe |
Value: Opera Internet Browser | |||
| (PID) Process: | (1252) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Windows Photo Viewer\PhotoViewer.dll |
Value: Windows Photo Viewer | |||
| (PID) Process: | (1252) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\VideoLAN\VLC\vlc.exe |
Value: VLC media player | |||
| (PID) Process: | (1252) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE |
Value: Microsoft Word | |||
| (PID) Process: | (1252) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
1
Suspicious files
224
Text files
217
Unknown types
31
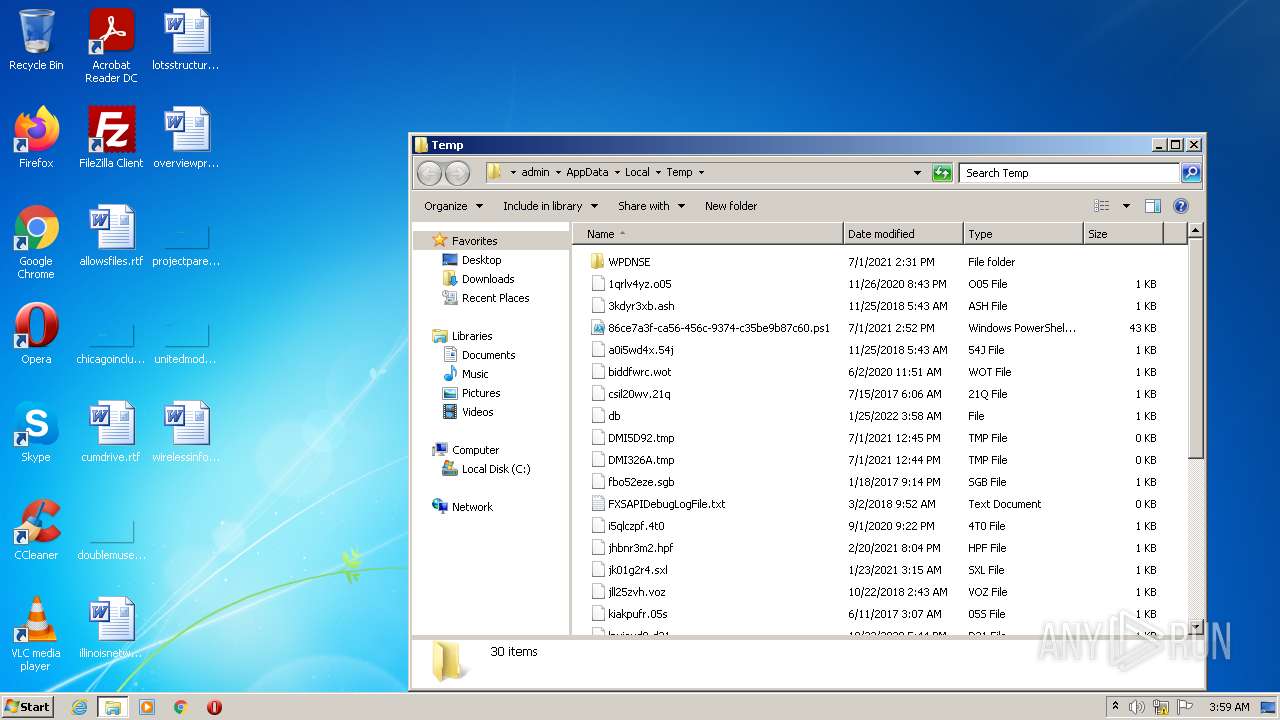
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61EF75B4-6D4.pma | — | |
MD5:— | SHA256:— | |||
| 1748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\075a8416-368c-4d9e-acb8-a62f2eda75a3.tmp | text | |
MD5:— | SHA256:— | |||
| 3492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\index | binary | |
MD5:— | SHA256:— | |||
| 1748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 1748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 1748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 1748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF153310.TMP | text | |
MD5:B628564B8042F6E2CC2F53710AAECDC0 | SHA256:1D3B022BDEE9F48D79E3EC1E93F519036003642D3D72D10B05CFD47F43EFBF13 | |||
| 1748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF153264.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 1748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 1748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:995C92837E4775CAFFE387D51ADBA520 | SHA256:51247C3464FD988B72670002D01A57FBFF1348704D325DC8FF8817ED2459D0D9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
62
TCP/UDP connections
224
DNS requests
186
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
924 | svchost.exe | HEAD | 200 | 74.125.104.231:80 | http://r2---sn-ixh7yn7e.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=196.244.192.6&mm=28&mn=sn-ixh7yn7e&ms=nvh&mt=1643082984&mv=m&mvi=2&pl=27&rmhost=r3---sn-ixh7yn7e.gvt1.com&shardbypass=yes | US | — | — | whitelisted |
3492 | chrome.exe | GET | 302 | 142.250.186.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 556 b | whitelisted |
924 | svchost.exe | GET | 302 | 142.250.186.174:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | html | 577 b | whitelisted |
924 | svchost.exe | GET | 206 | 74.125.104.231:80 | http://r2---sn-ixh7yn7e.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=196.244.192.6&mm=28&mn=sn-ixh7yn7e&ms=nvh&mt=1643082984&mv=m&mvi=2&pl=27&rmhost=r3---sn-ixh7yn7e.gvt1.com&shardbypass=yes | US | binary | 9.49 Kb | whitelisted |
924 | svchost.exe | GET | 206 | 74.125.104.231:80 | http://r2---sn-ixh7yn7e.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=196.244.192.6&mm=28&mn=sn-ixh7yn7e&ms=nvh&mt=1643082984&mv=m&mvi=2&pl=27&rmhost=r3---sn-ixh7yn7e.gvt1.com&shardbypass=yes | US | binary | 9.49 Kb | whitelisted |
924 | svchost.exe | GET | 302 | 142.250.186.174:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | html | 577 b | whitelisted |
924 | svchost.exe | GET | 206 | 74.125.104.231:80 | http://r2---sn-ixh7yn7e.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=196.244.192.6&mm=28&mn=sn-ixh7yn7e&ms=nvh&mt=1643082984&mv=m&mvi=2&pl=27&rmhost=r3---sn-ixh7yn7e.gvt1.com&shardbypass=yes | US | binary | 43.3 Kb | whitelisted |
924 | svchost.exe | GET | 206 | 74.125.104.231:80 | http://r2---sn-ixh7yn7e.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=196.244.192.6&mm=28&mn=sn-ixh7yn7e&ms=nvh&mt=1643083221&mv=m&mvi=2&pl=27&rmhost=r3---sn-ixh7yn7e.gvt1.com&shardbypass=yes | US | binary | 88.4 Kb | whitelisted |
924 | svchost.exe | GET | 302 | 142.250.186.174:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | html | 577 b | whitelisted |
924 | svchost.exe | GET | 206 | 74.125.104.231:80 | http://r2---sn-ixh7yn7e.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=196.244.192.6&mm=28&mn=sn-ixh7yn7e&ms=nvh&mt=1643082984&mv=m&mvi=2&pl=27&rmhost=r3---sn-ixh7yn7e.gvt1.com&shardbypass=yes | US | binary | 9.49 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
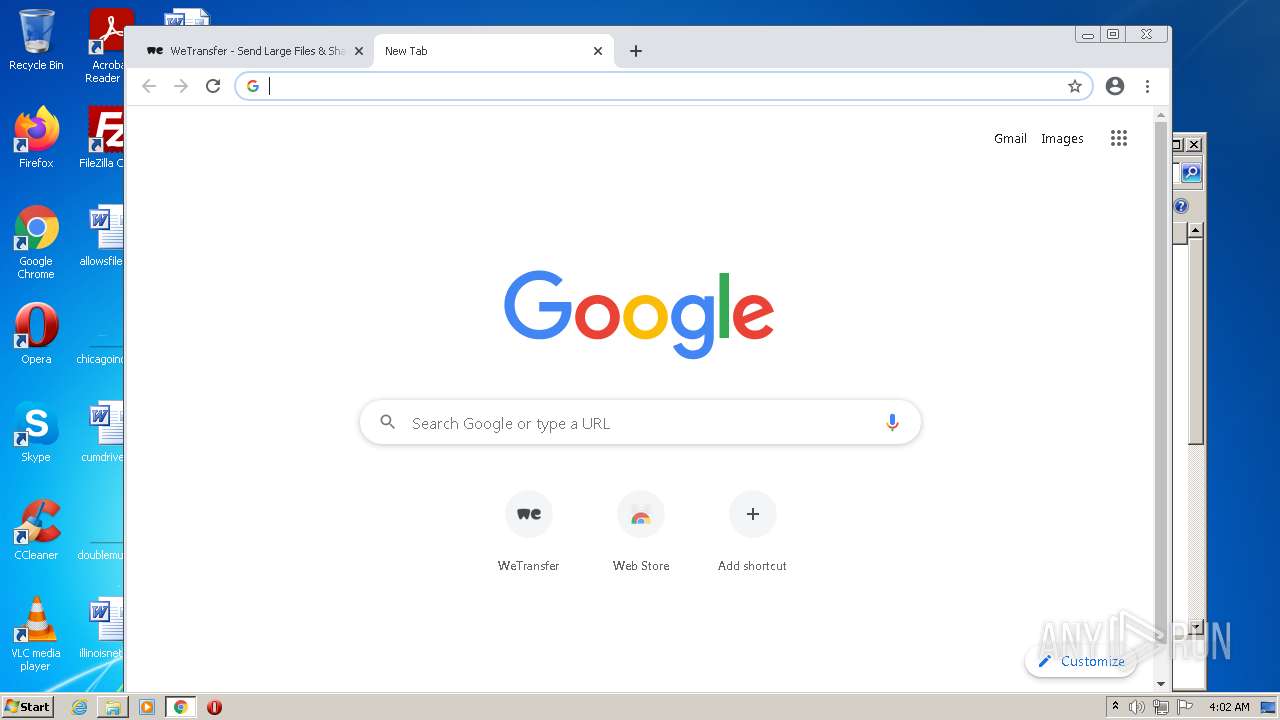
3492 | chrome.exe | 142.250.186.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
3492 | chrome.exe | 142.250.179.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
3492 | chrome.exe | 142.250.179.196:443 | www.google.com | Google Inc. | US | whitelisted |
3492 | chrome.exe | 172.217.168.206:443 | encrypted-tbn0.gstatic.com | Google Inc. | US | whitelisted |
3492 | chrome.exe | 142.250.179.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3492 | chrome.exe | 142.250.179.193:443 | lh5.googleusercontent.com | Google Inc. | US | whitelisted |
3492 | chrome.exe | 172.217.168.195:443 | www.gstatic.com | Google Inc. | US | whitelisted |
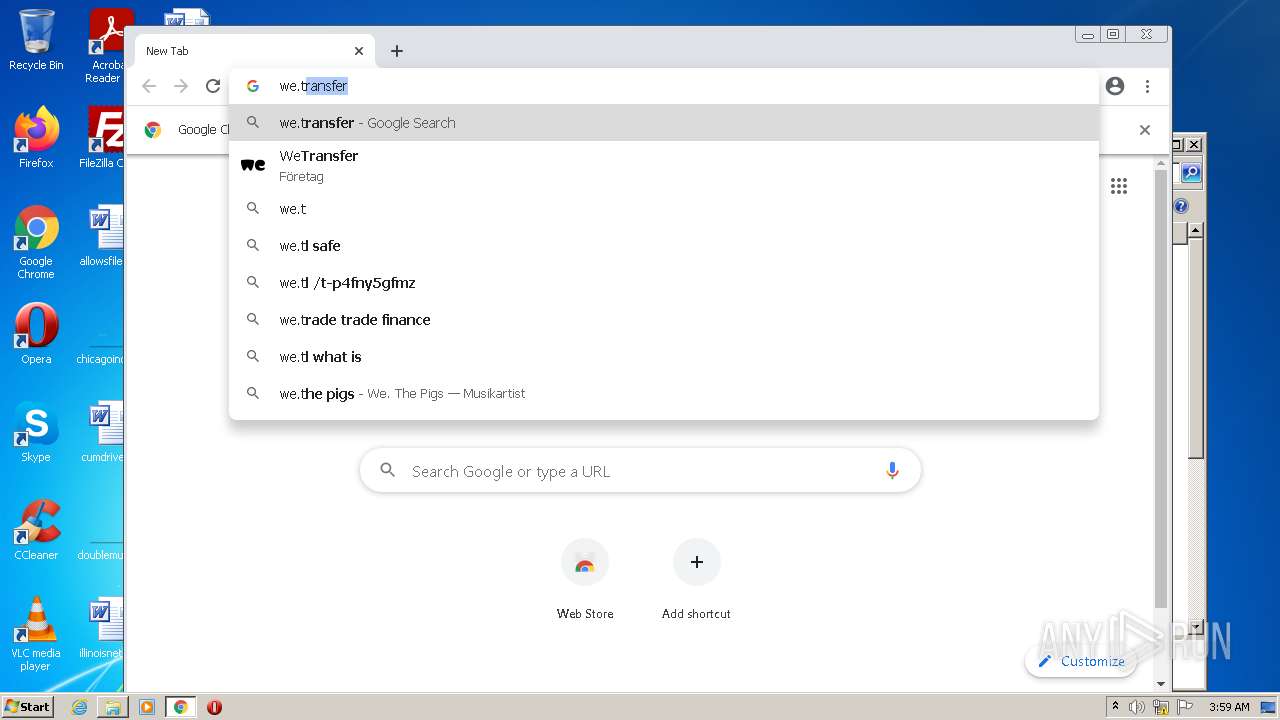
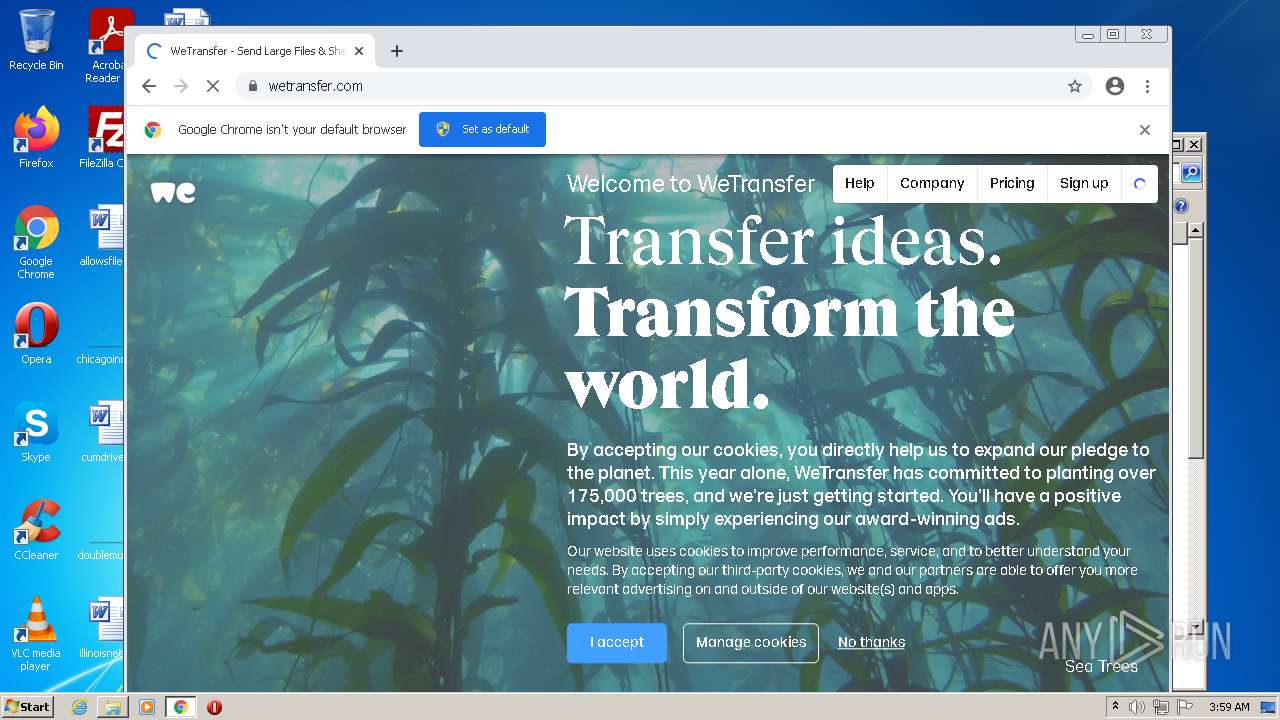
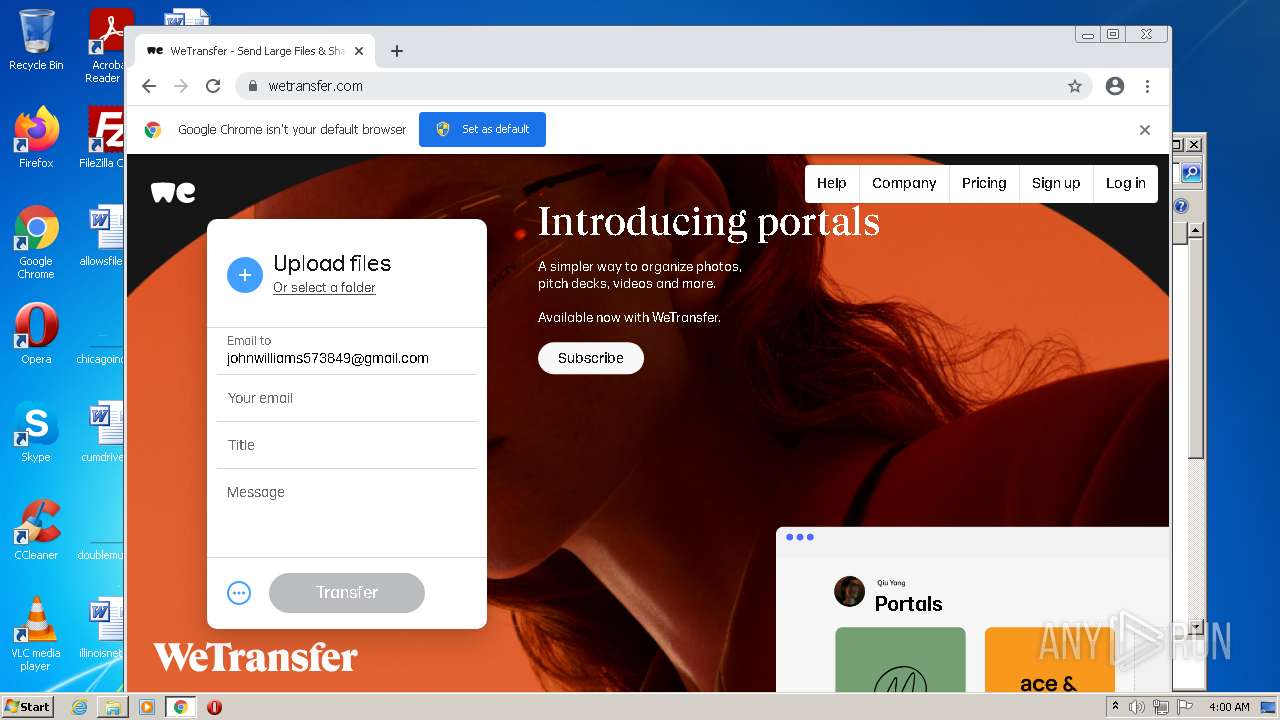
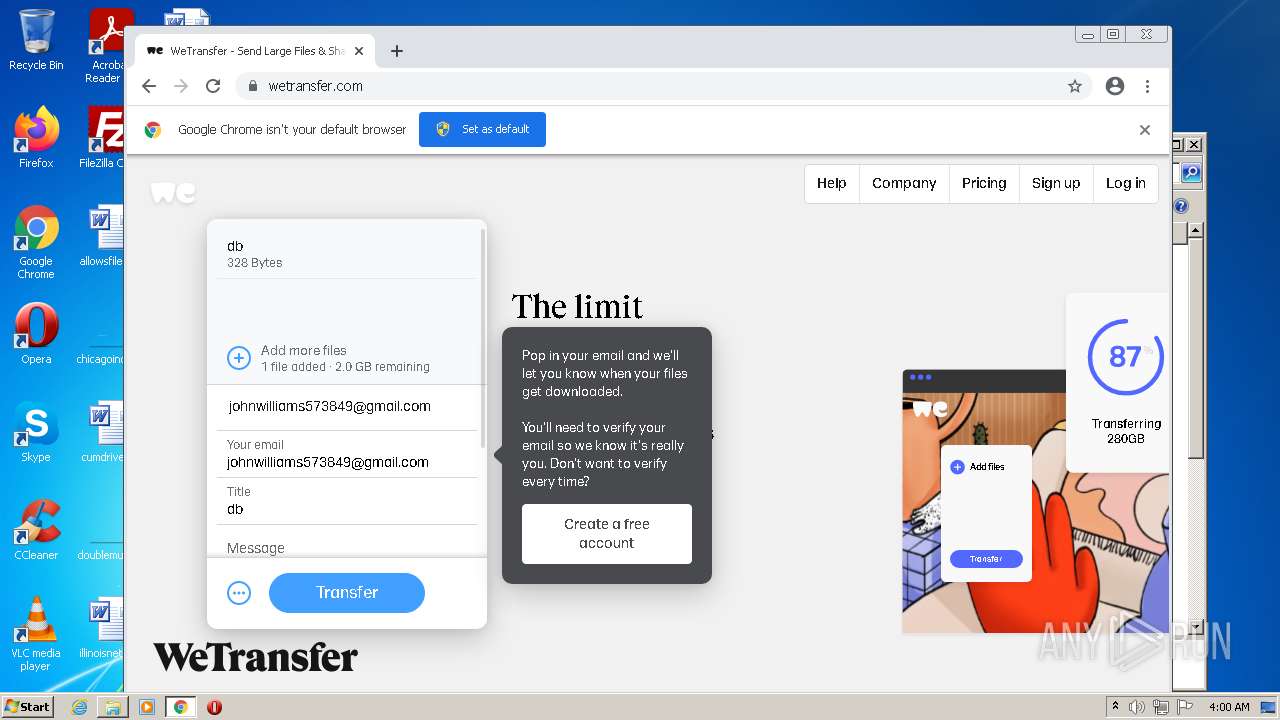
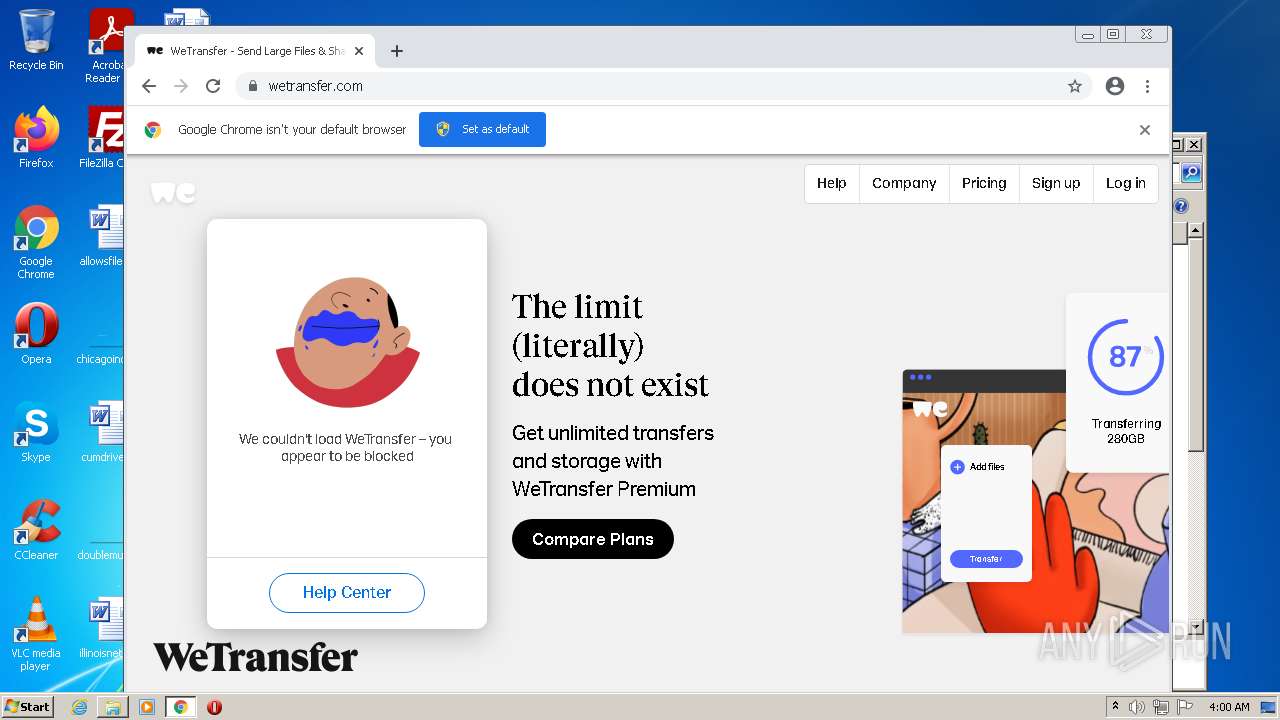
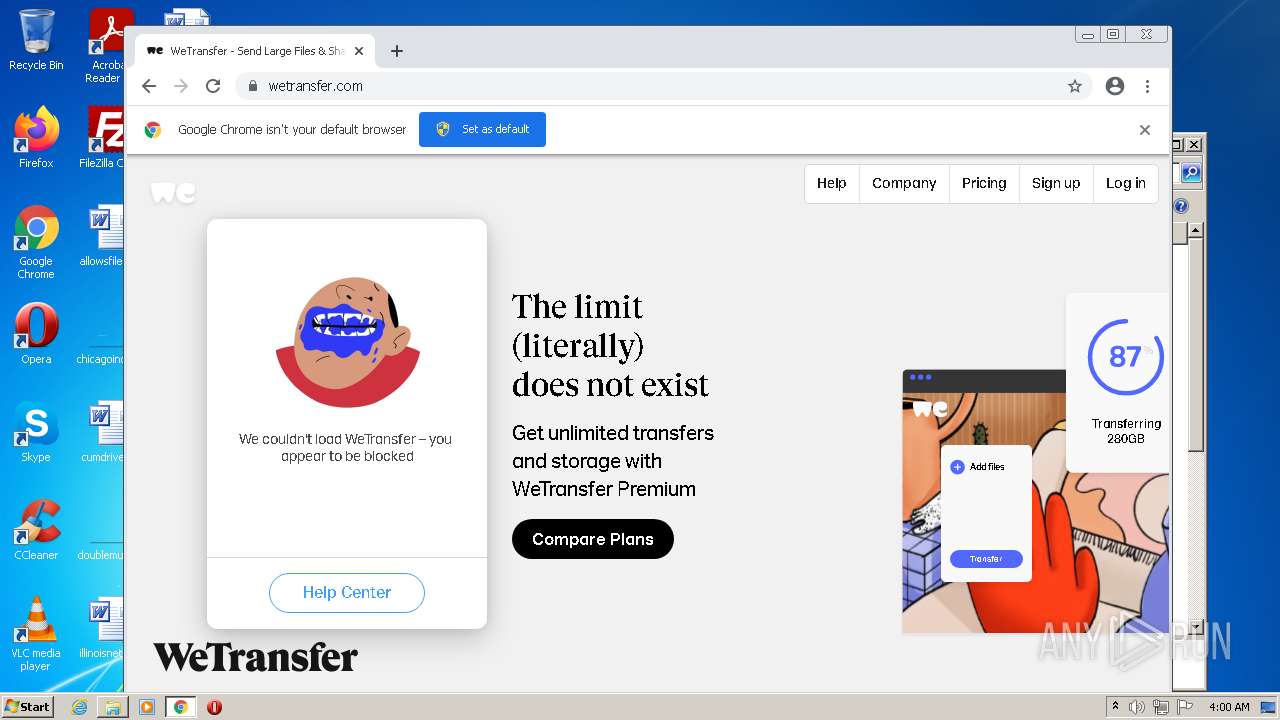
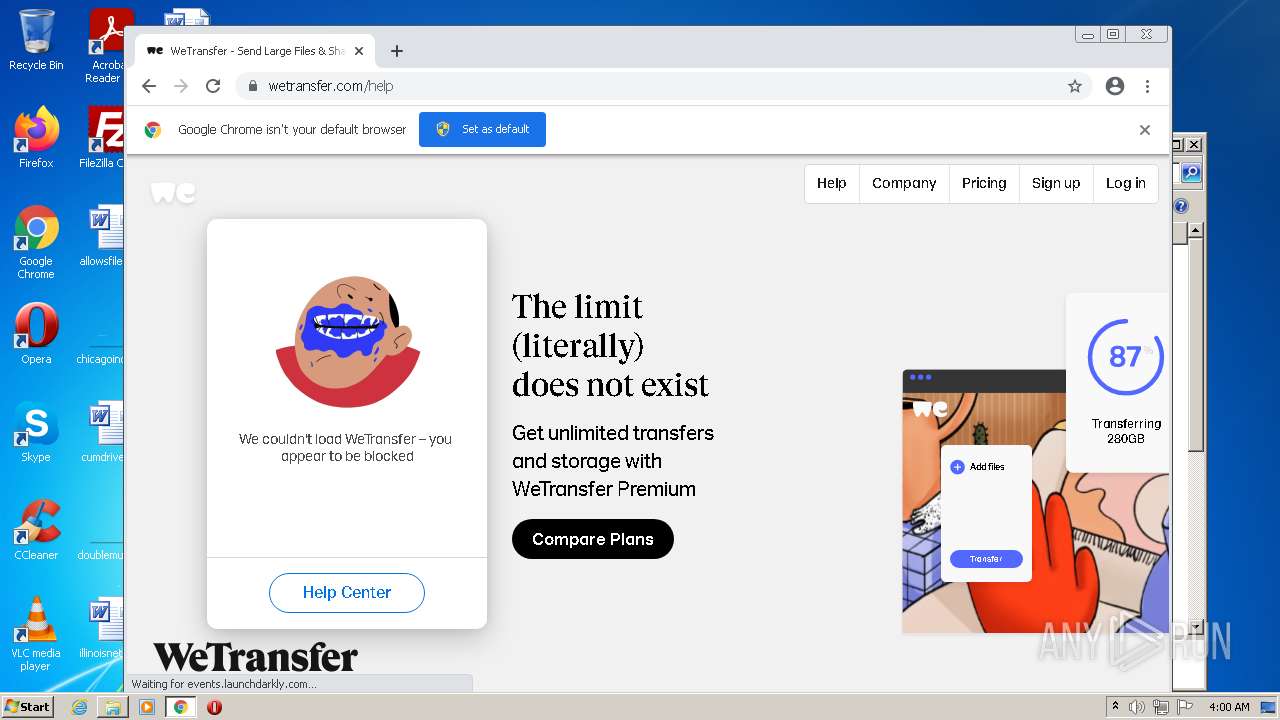
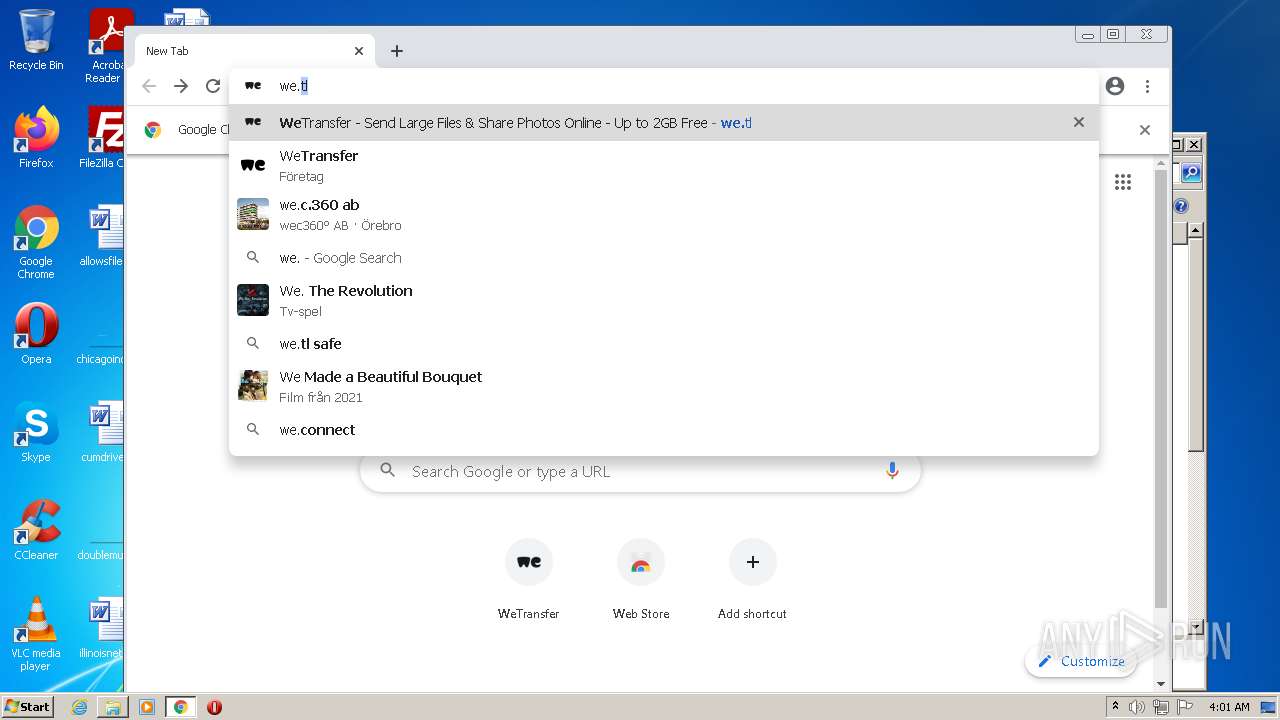
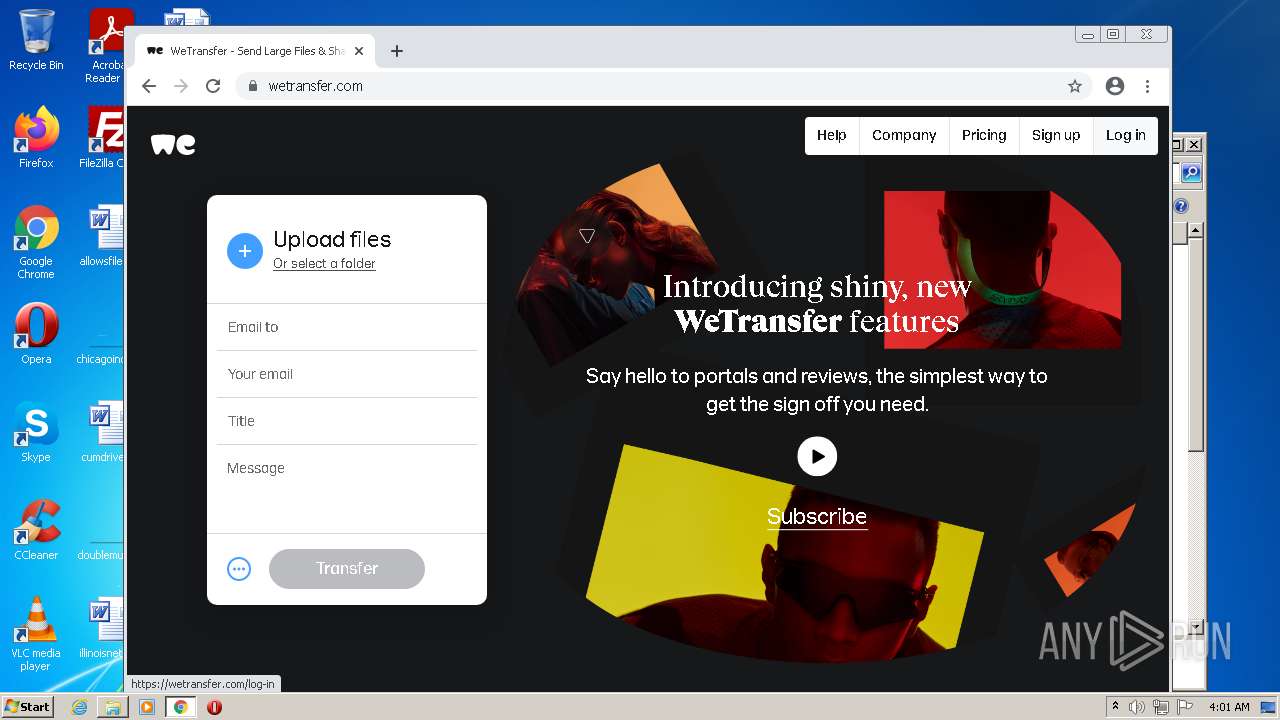
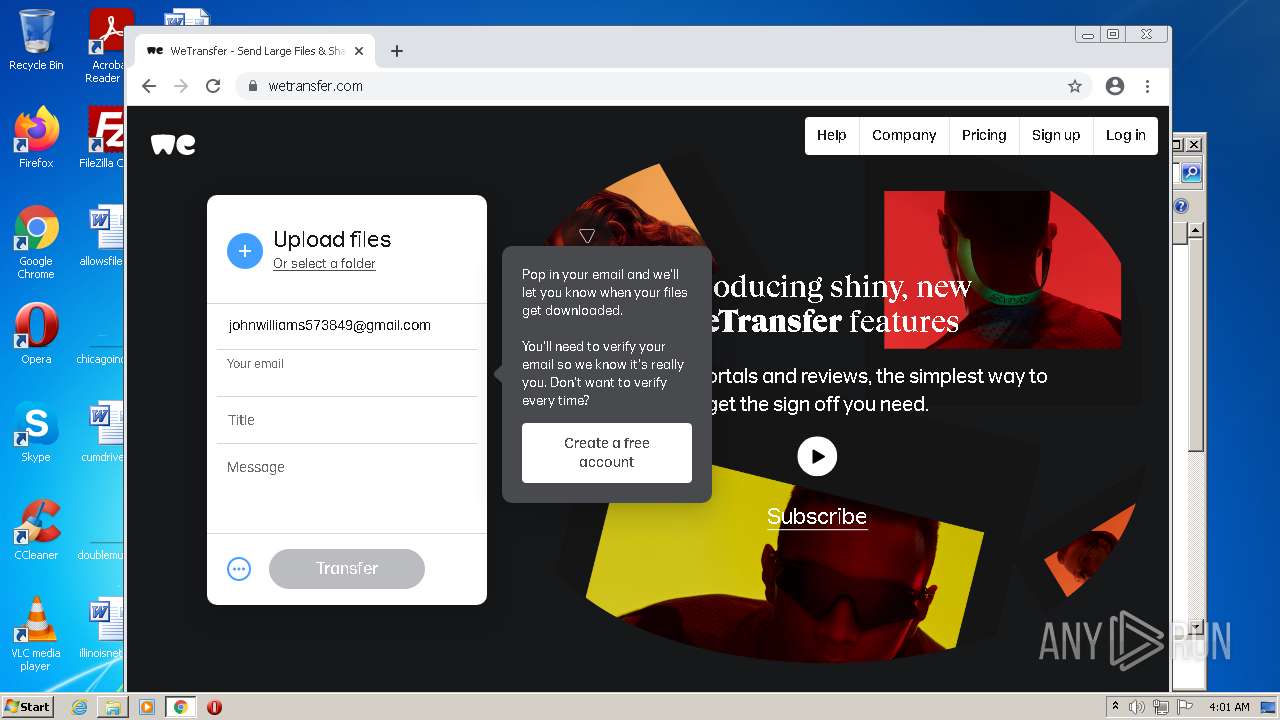
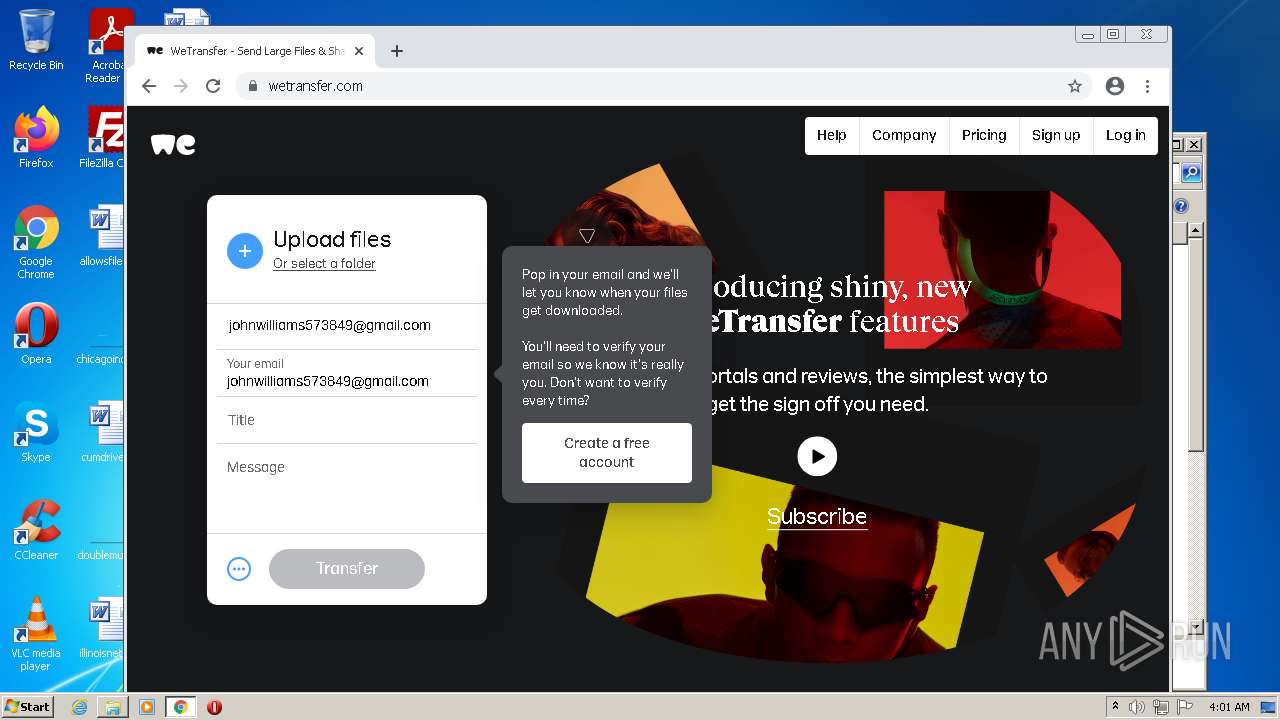
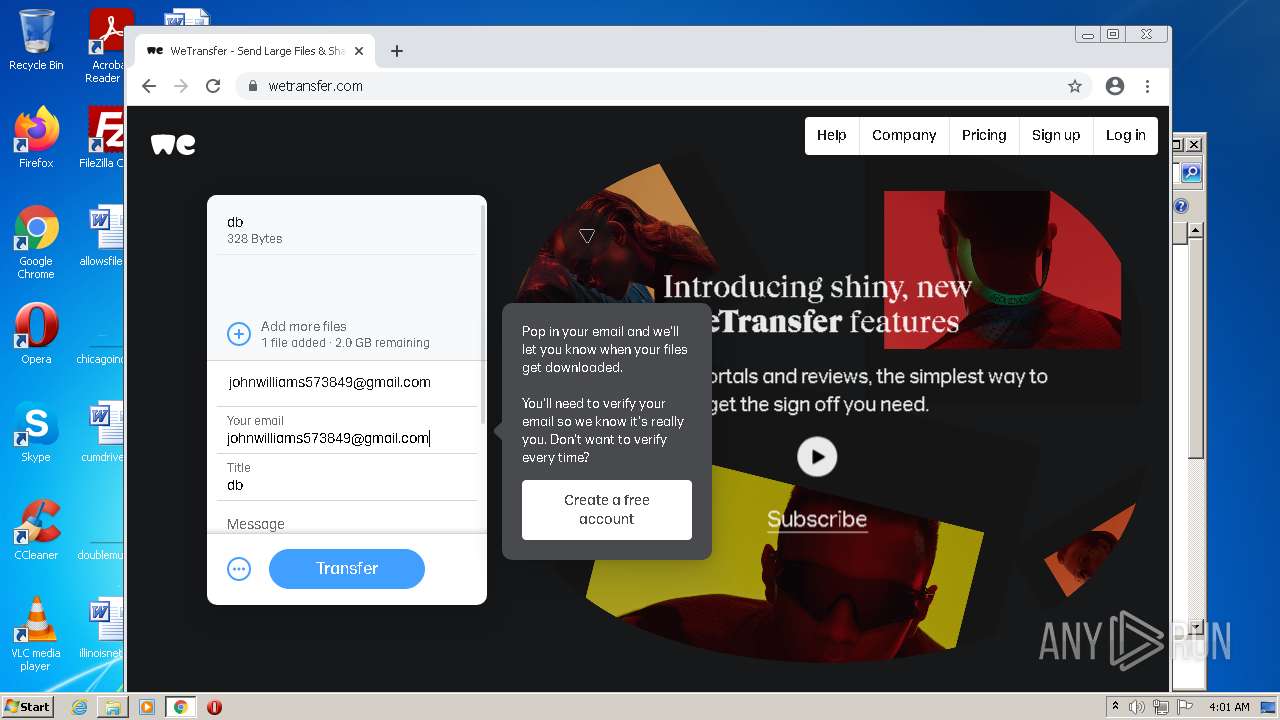
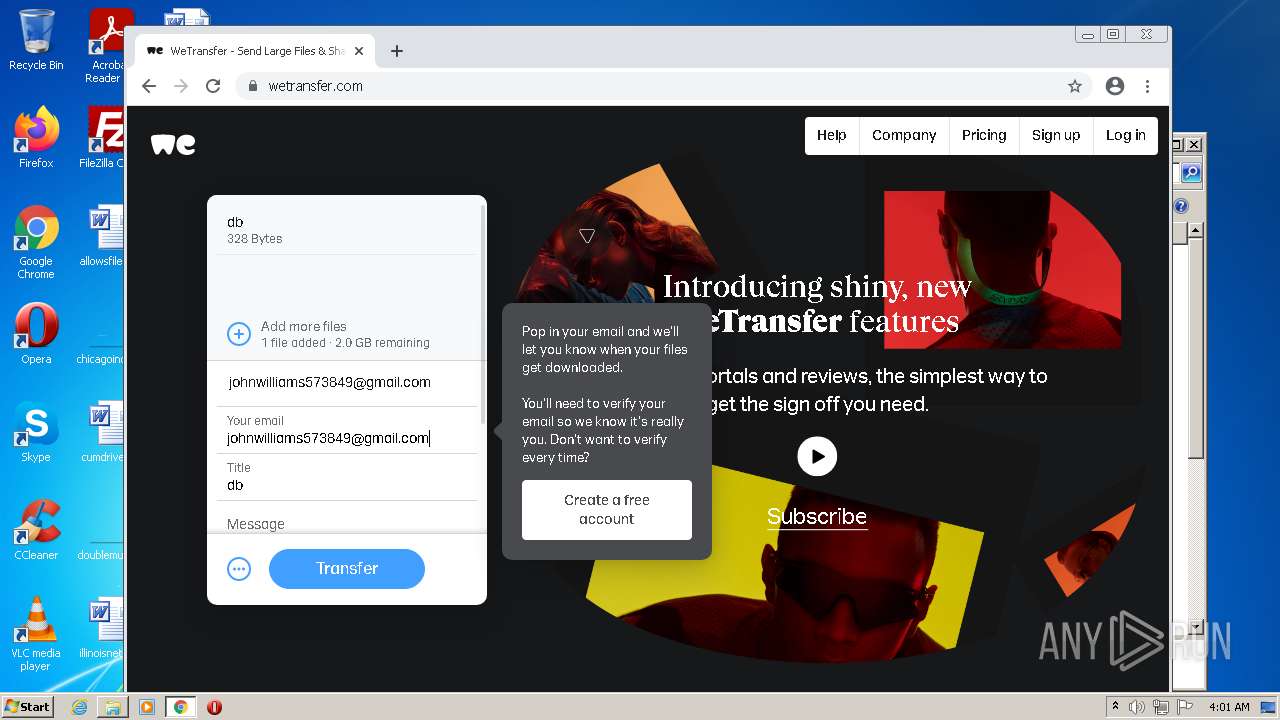
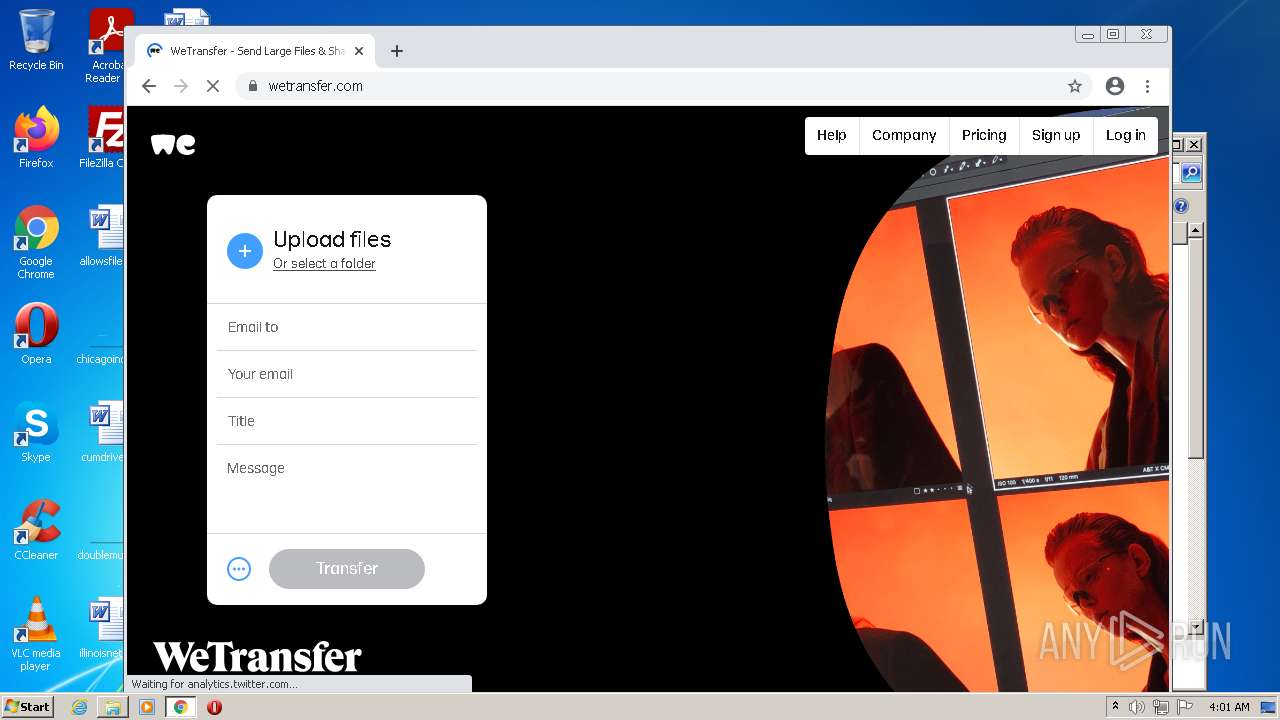
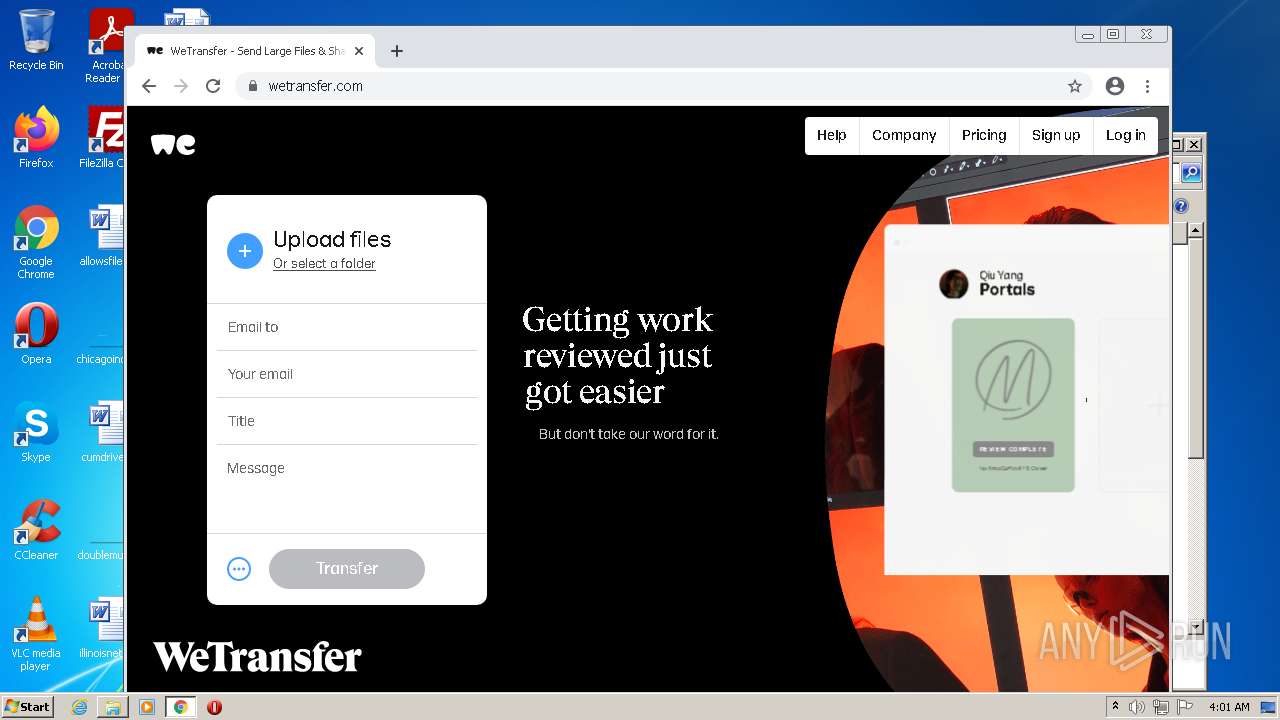
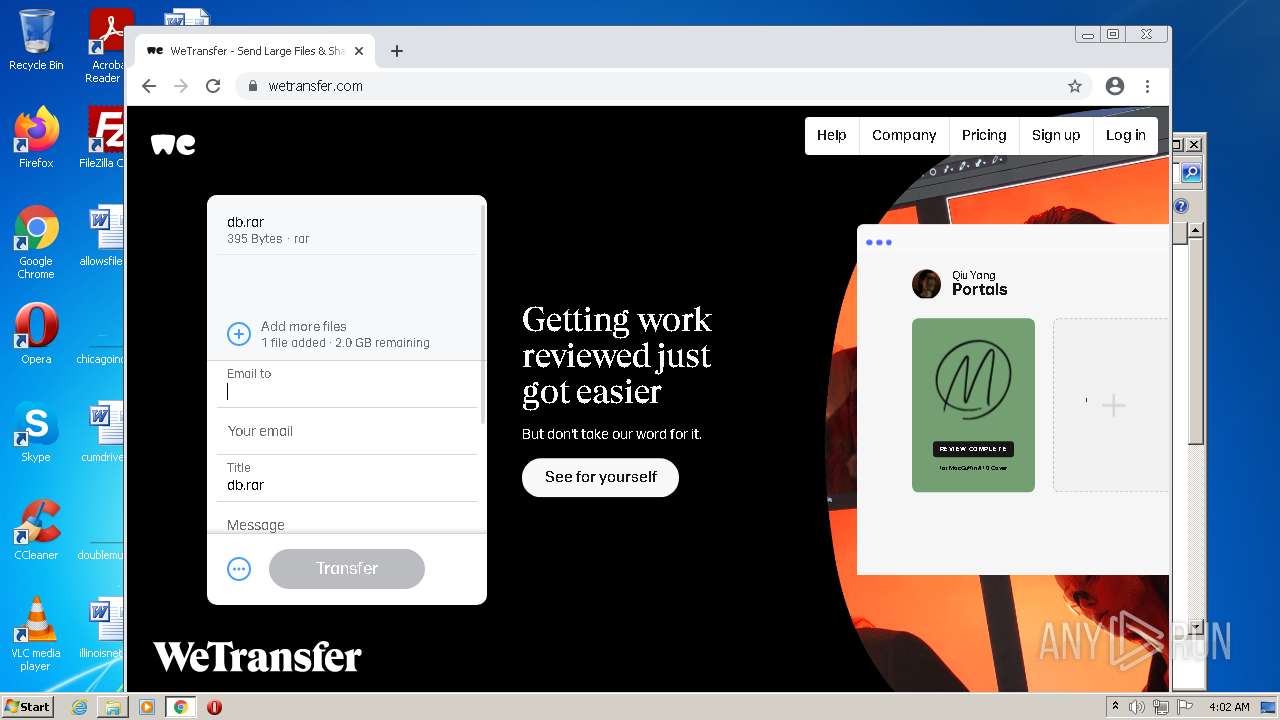
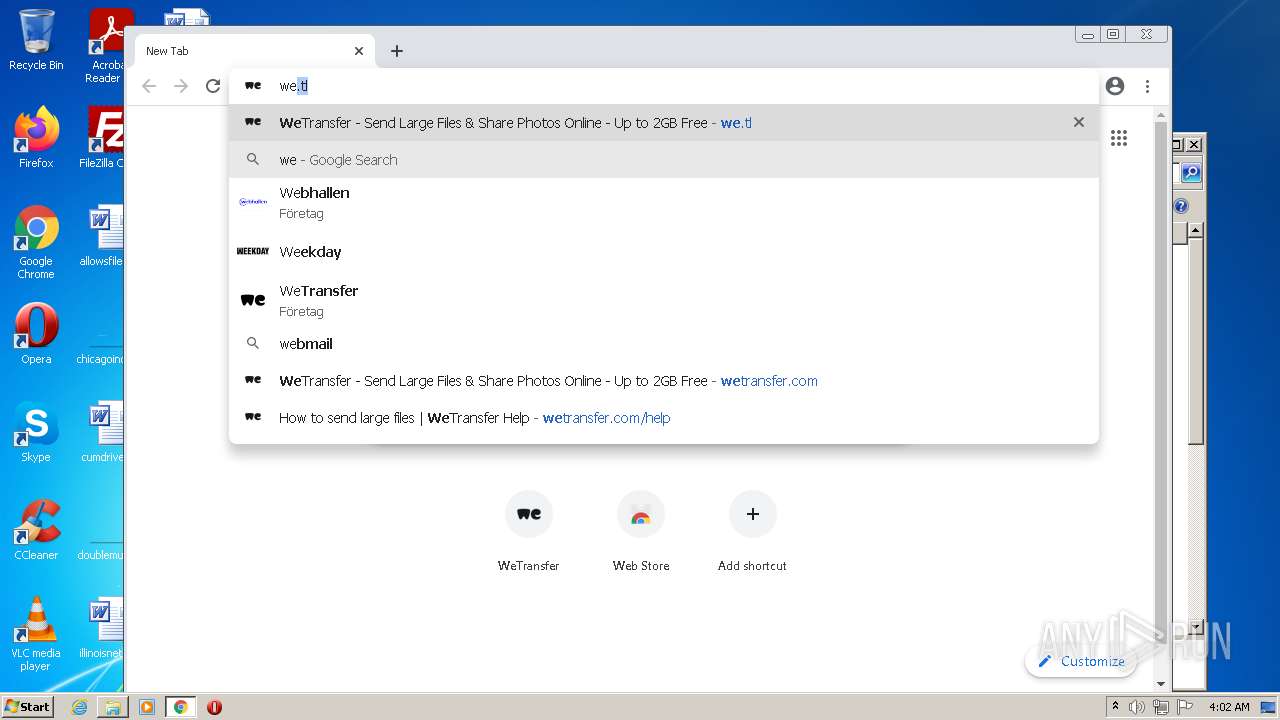
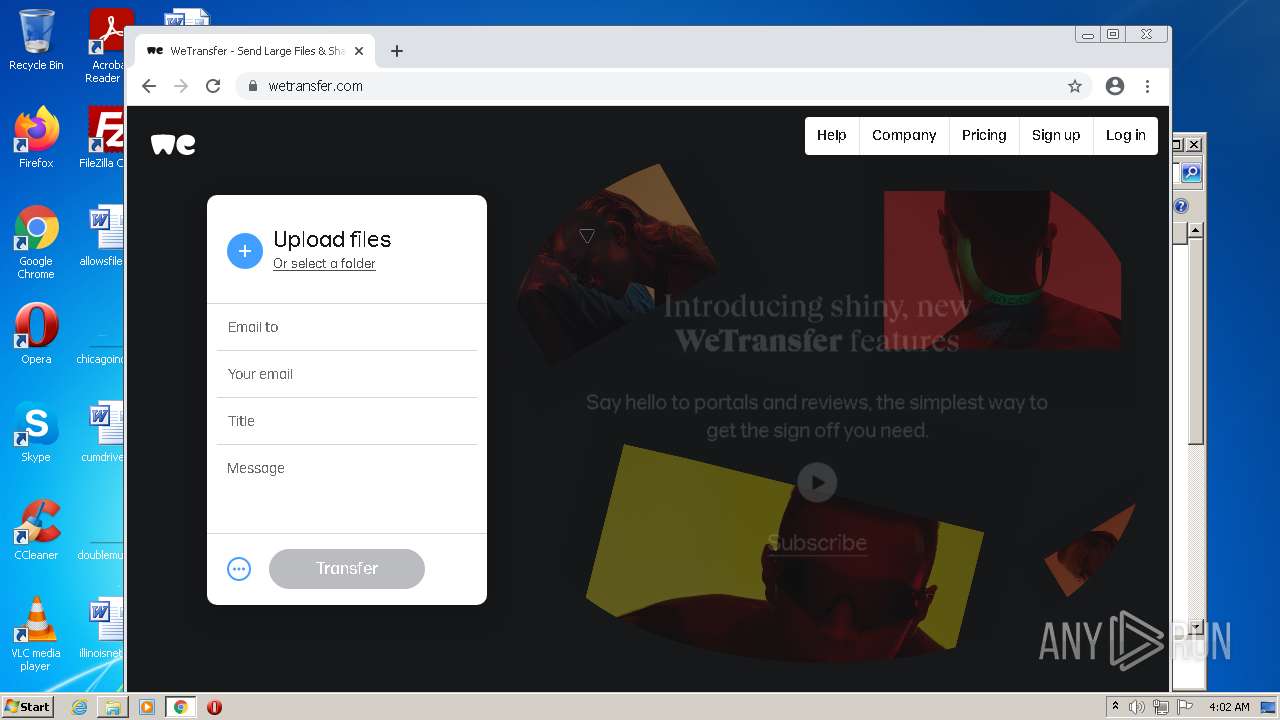
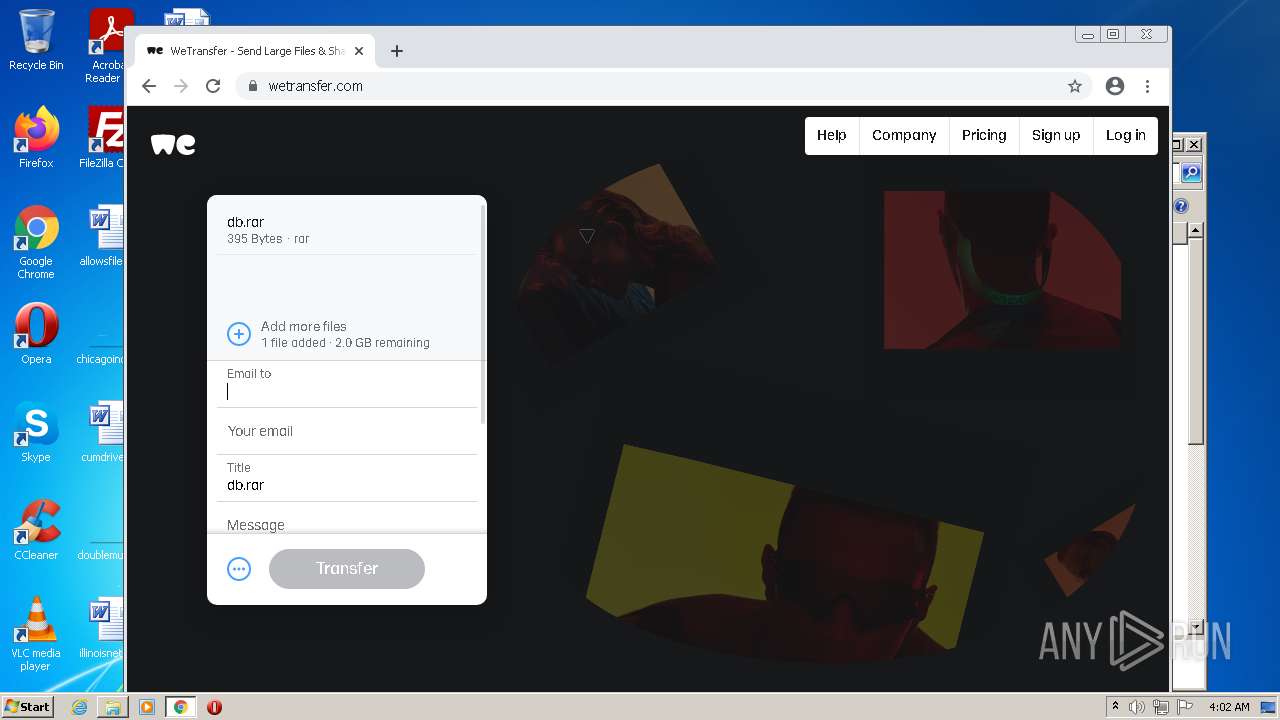
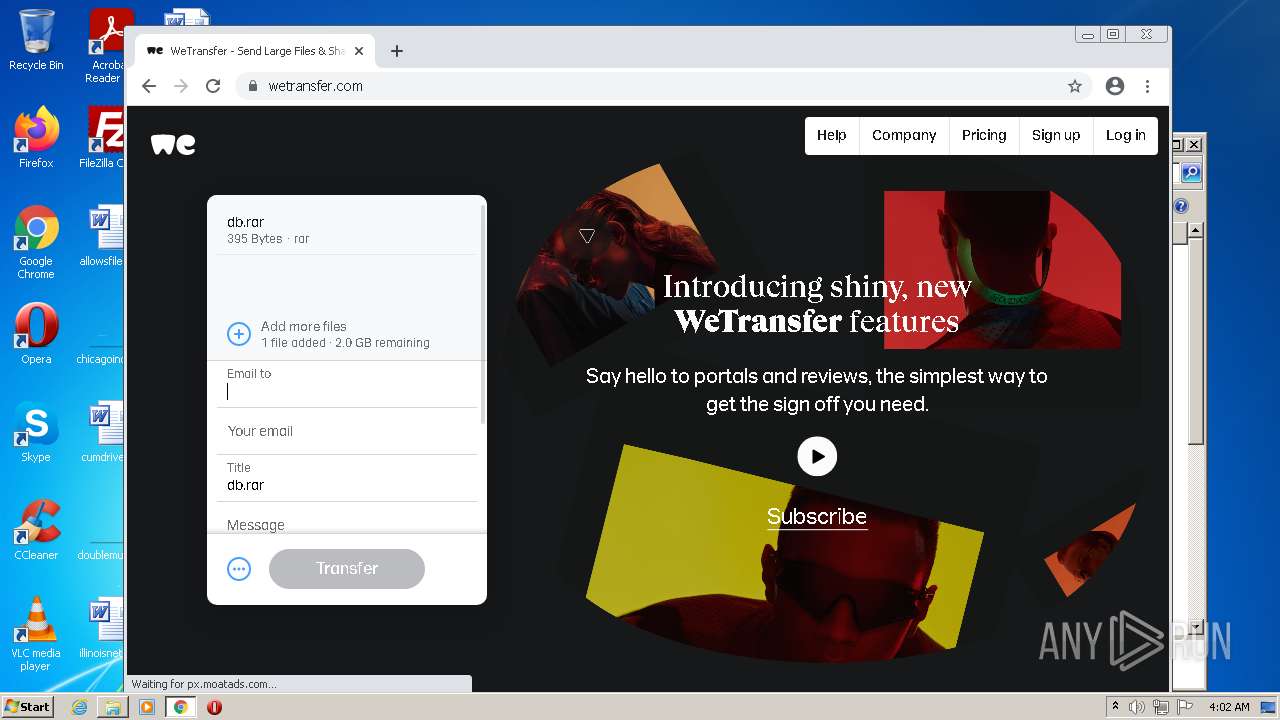
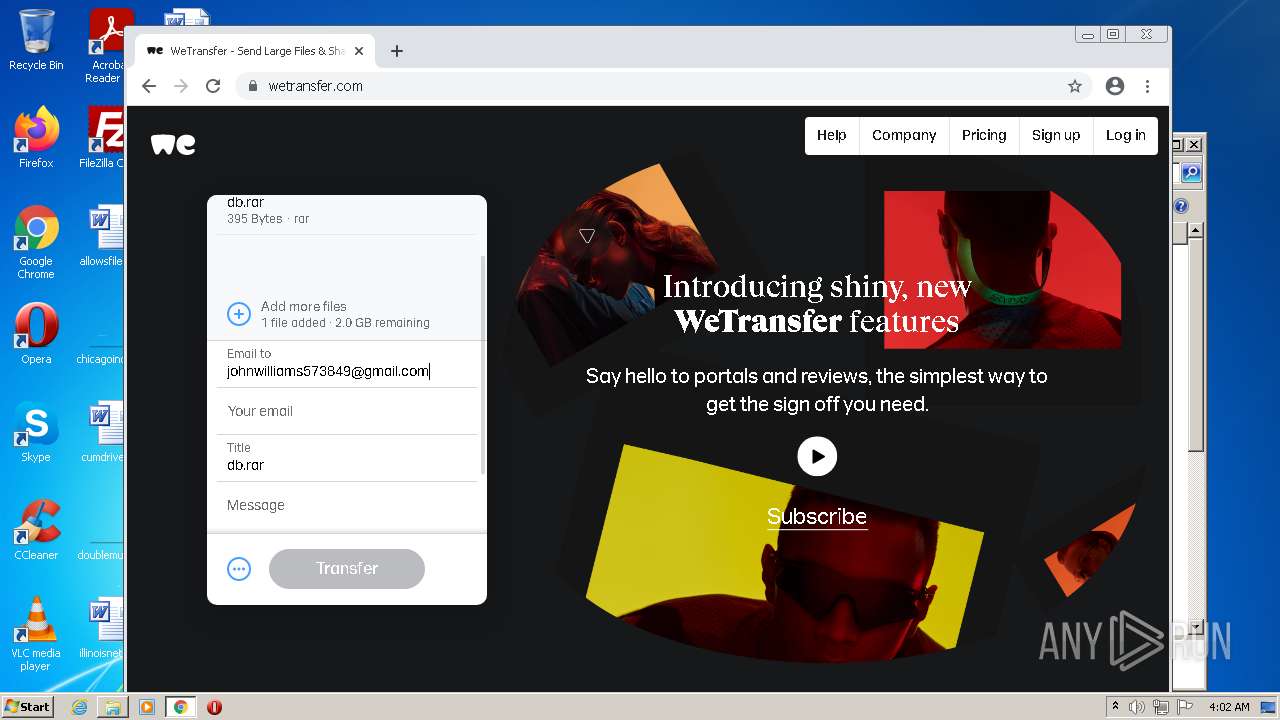
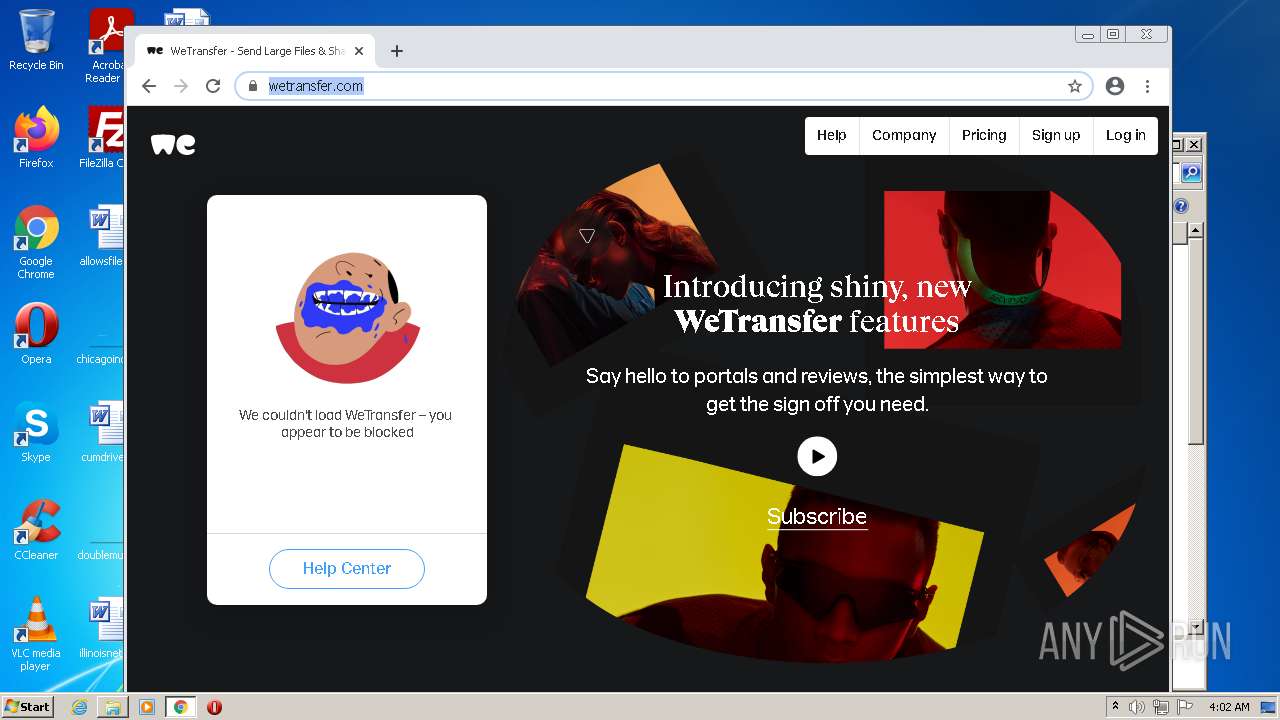
3492 | chrome.exe | 18.66.139.97:443 | we.tl | Massachusetts Institute of Technology | US | unknown |
3492 | chrome.exe | 34.225.30.212:443 | e-10220.adzerk.net | Amazon.com, Inc. | US | unknown |
3492 | chrome.exe | 216.58.208.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
encrypted-tbn0.gstatic.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
lh5.googleusercontent.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |