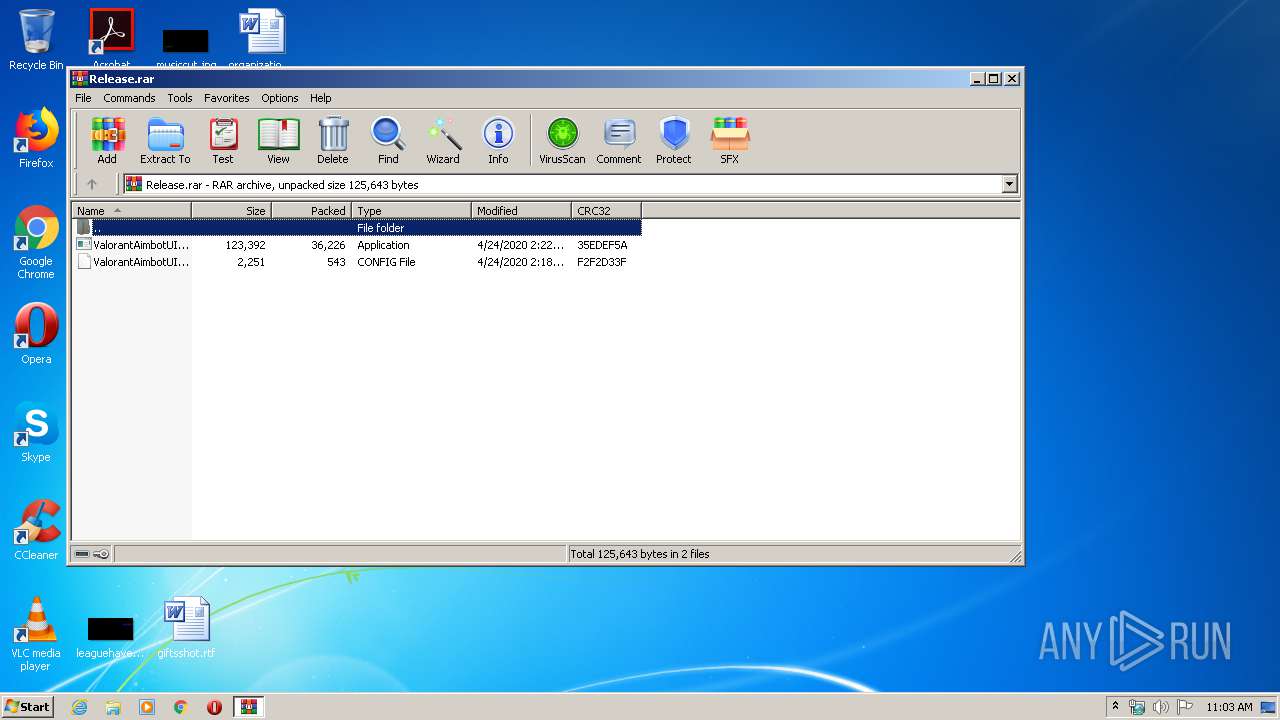
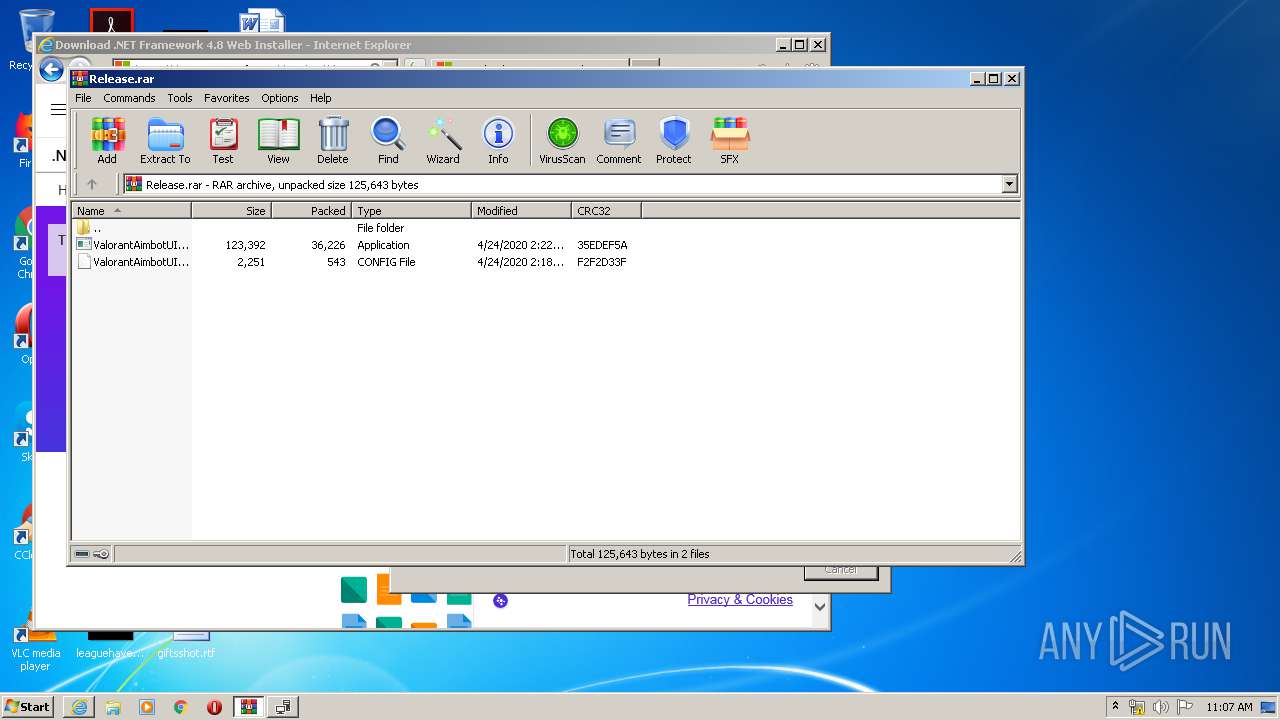
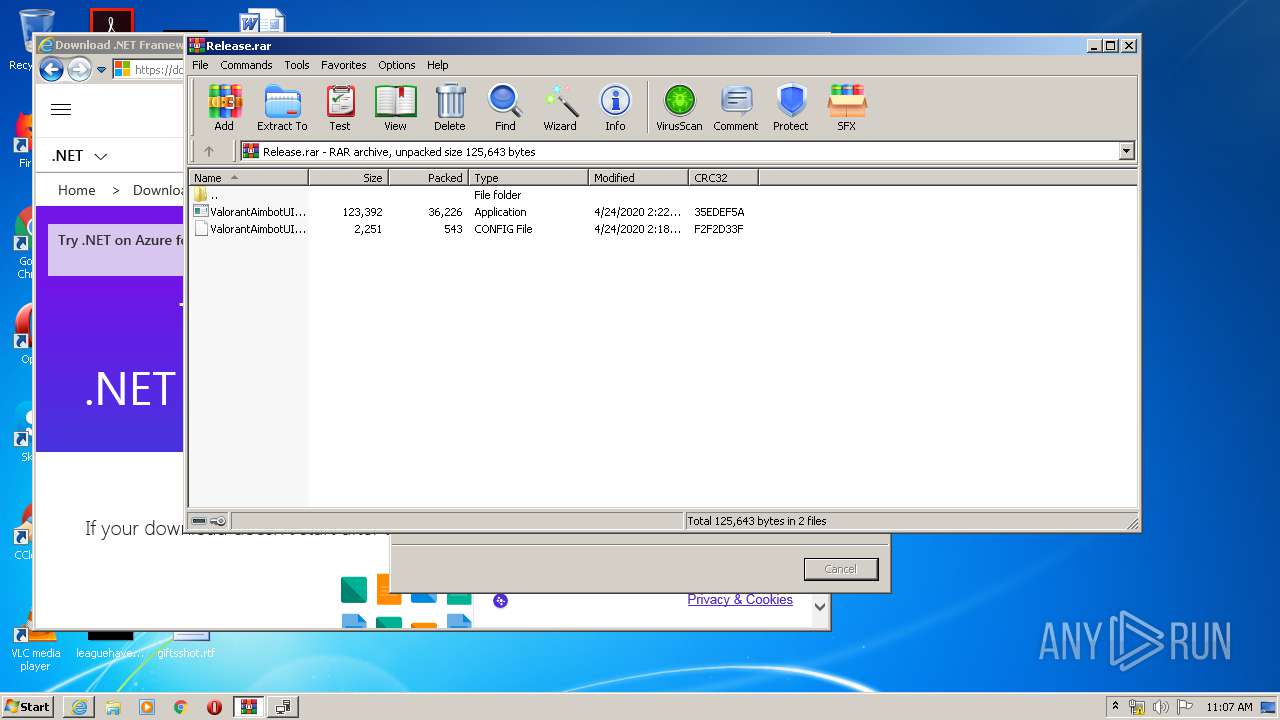
| File name: | Release.rar |
| Full analysis: | https://app.any.run/tasks/1baf707c-c590-484a-aac5-34f8a01edade |
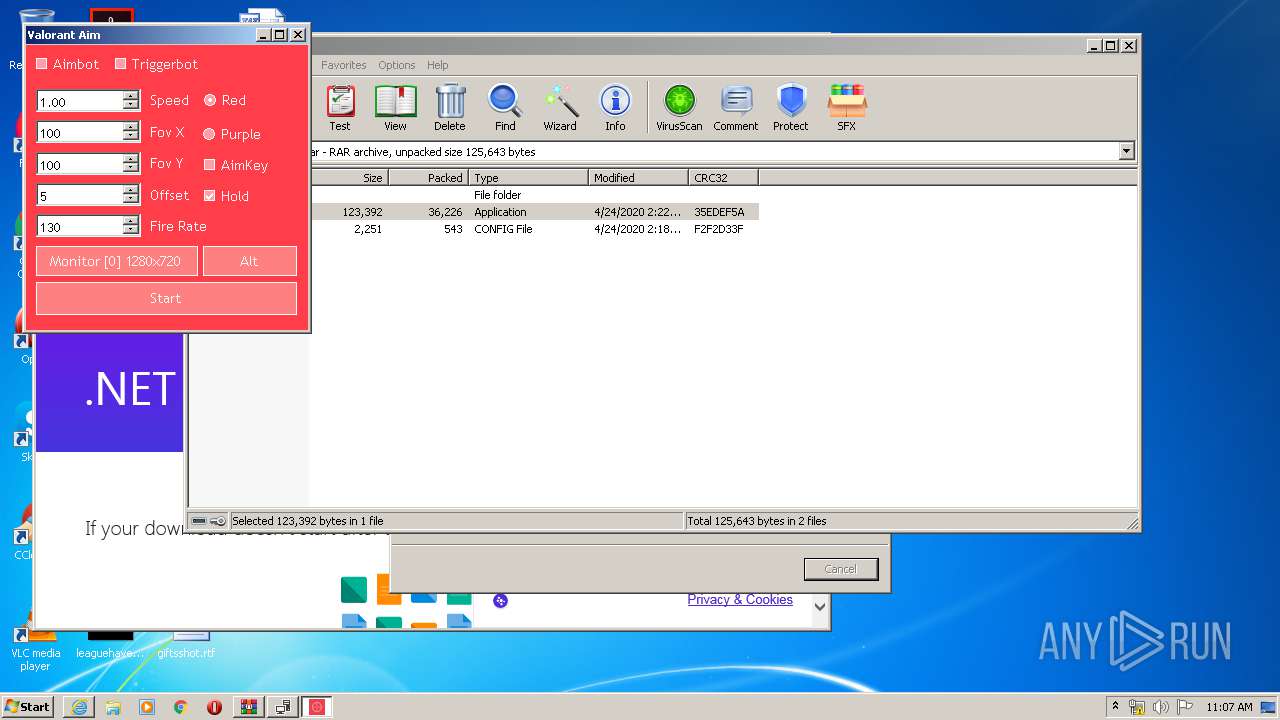
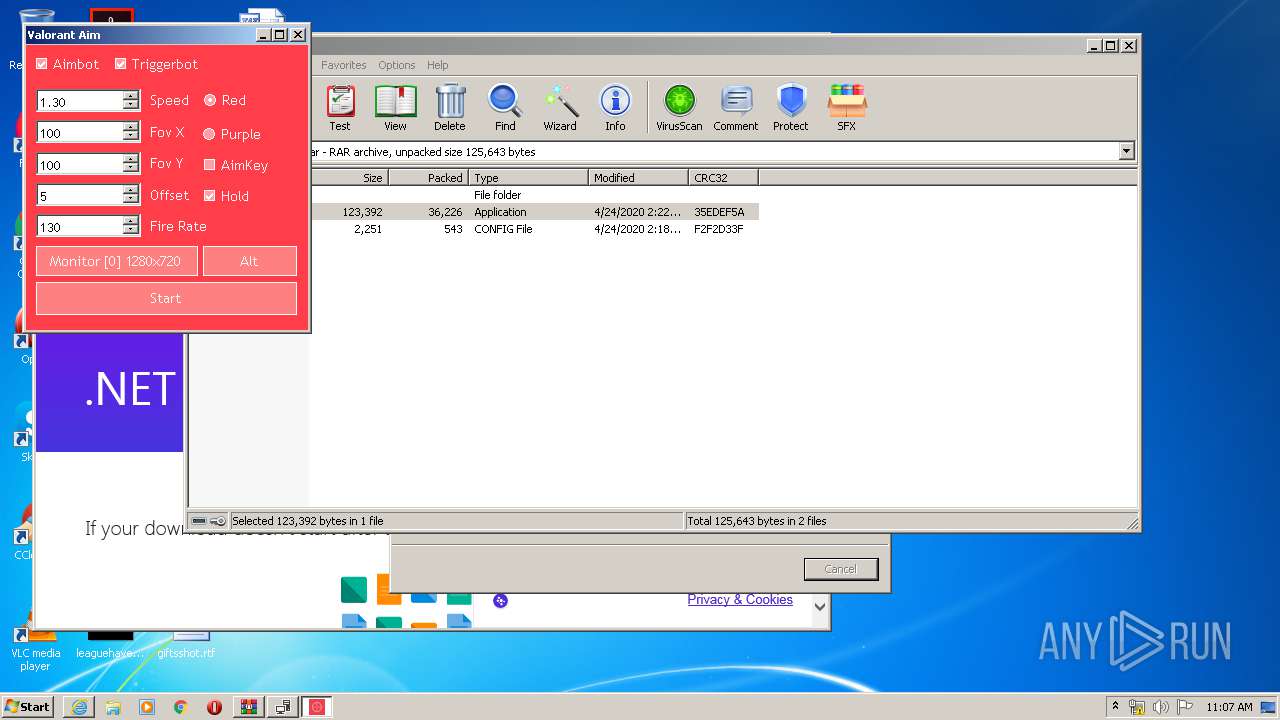
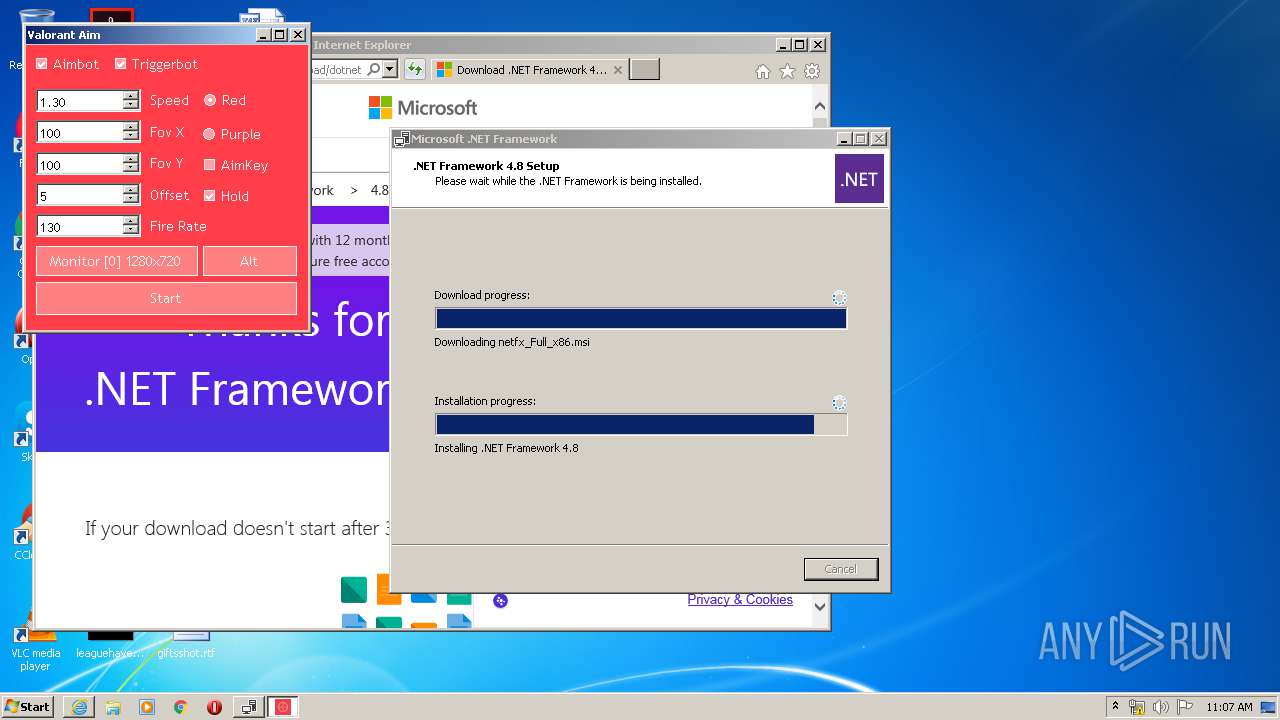
| Verdict: | Malicious activity |
| Analysis date: | April 30, 2020, 10:02:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | B5DE41E9786D78C7A6D57ADEFD12F484 |
| SHA1: | 75514B5FB136EA1BF245E634A9C7DE09C423ED2E |
| SHA256: | 1E1C8167F301606147E9370AAED0A68ECFB266CE05820AE909DD1562E49D5719 |
| SSDEEP: | 768:hoKX/6xWyu5Iw2fusHiPtKtmrkRgFHNd4N2/1yU30Rz1qFQYQ1POX:hLPu77l5IctmrjF0UtQz1WU2X |
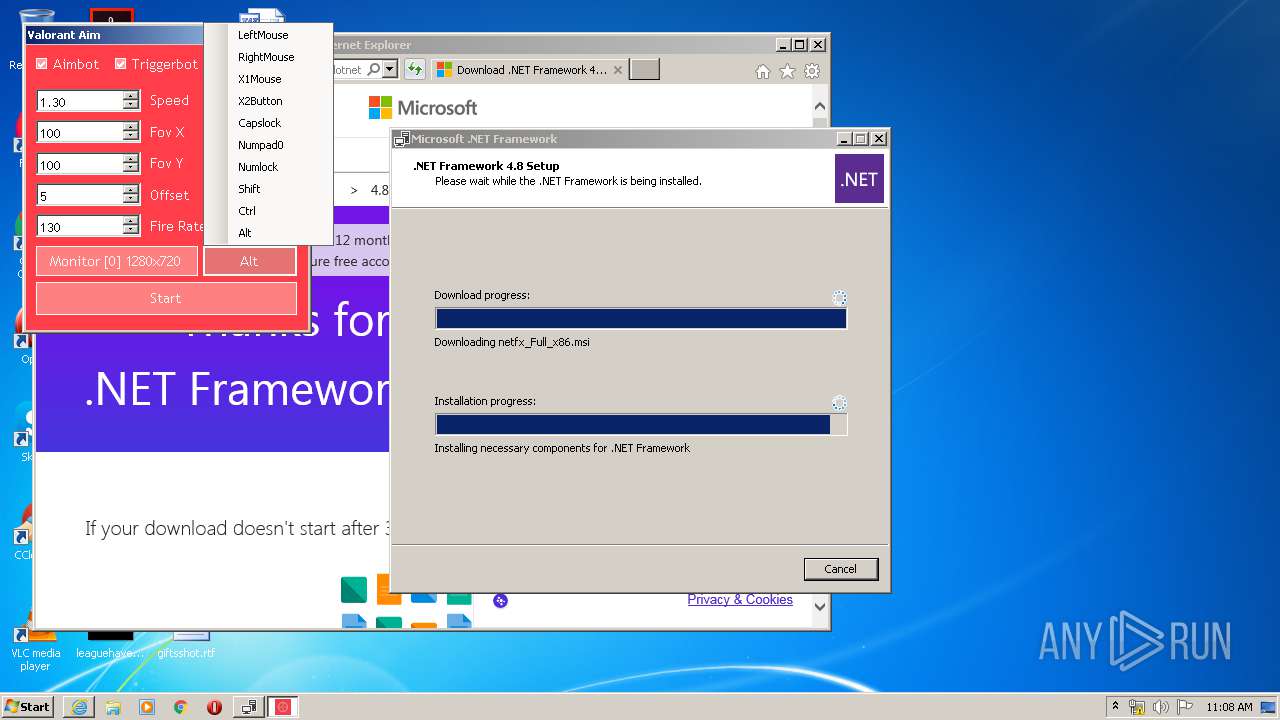
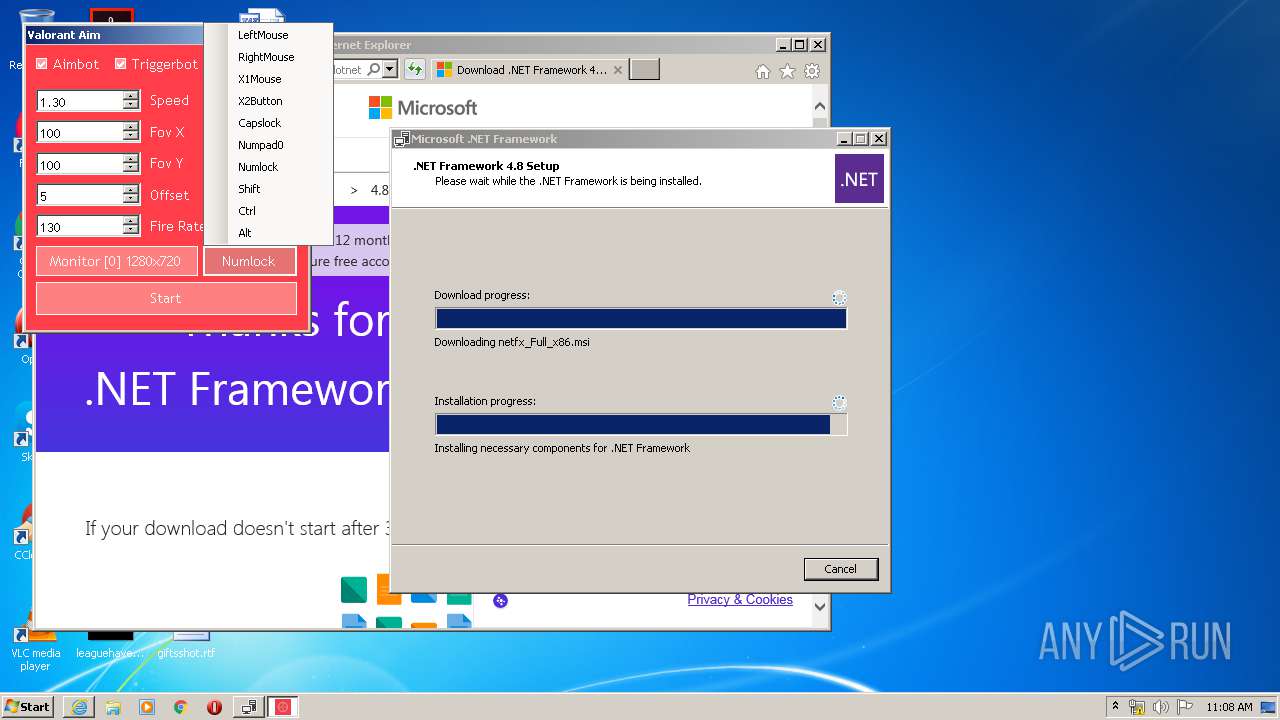
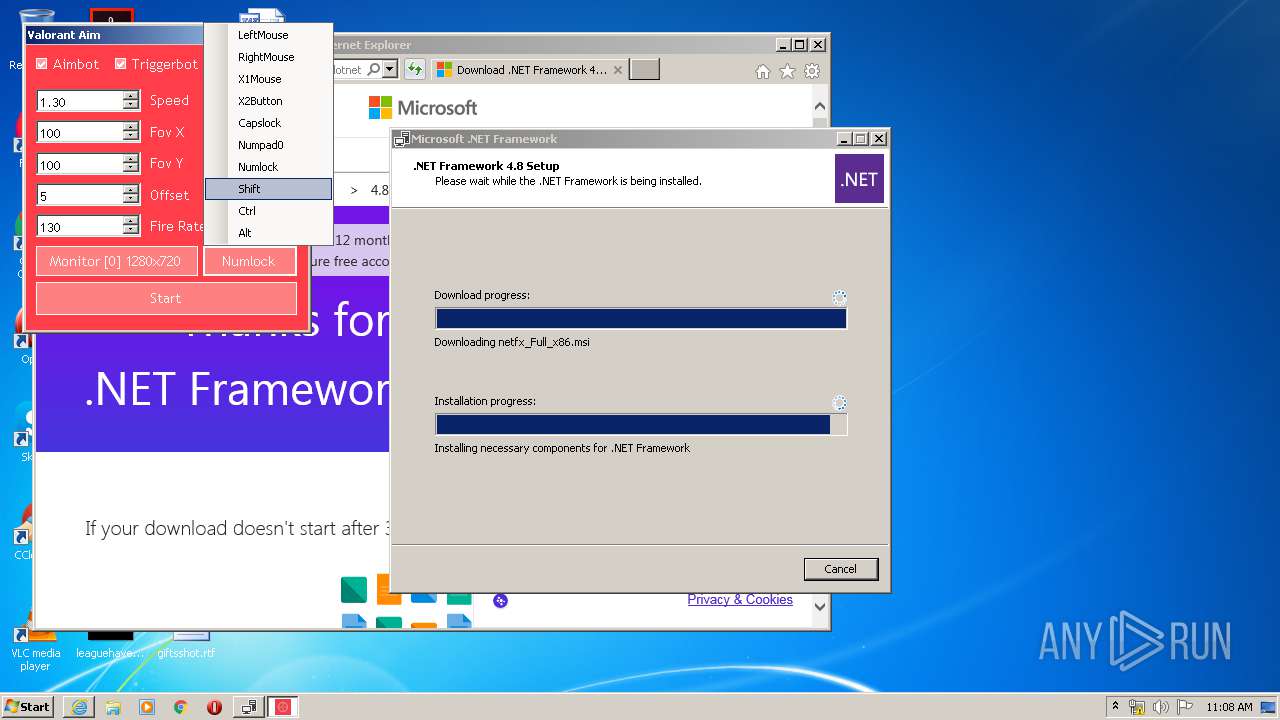
MALICIOUS
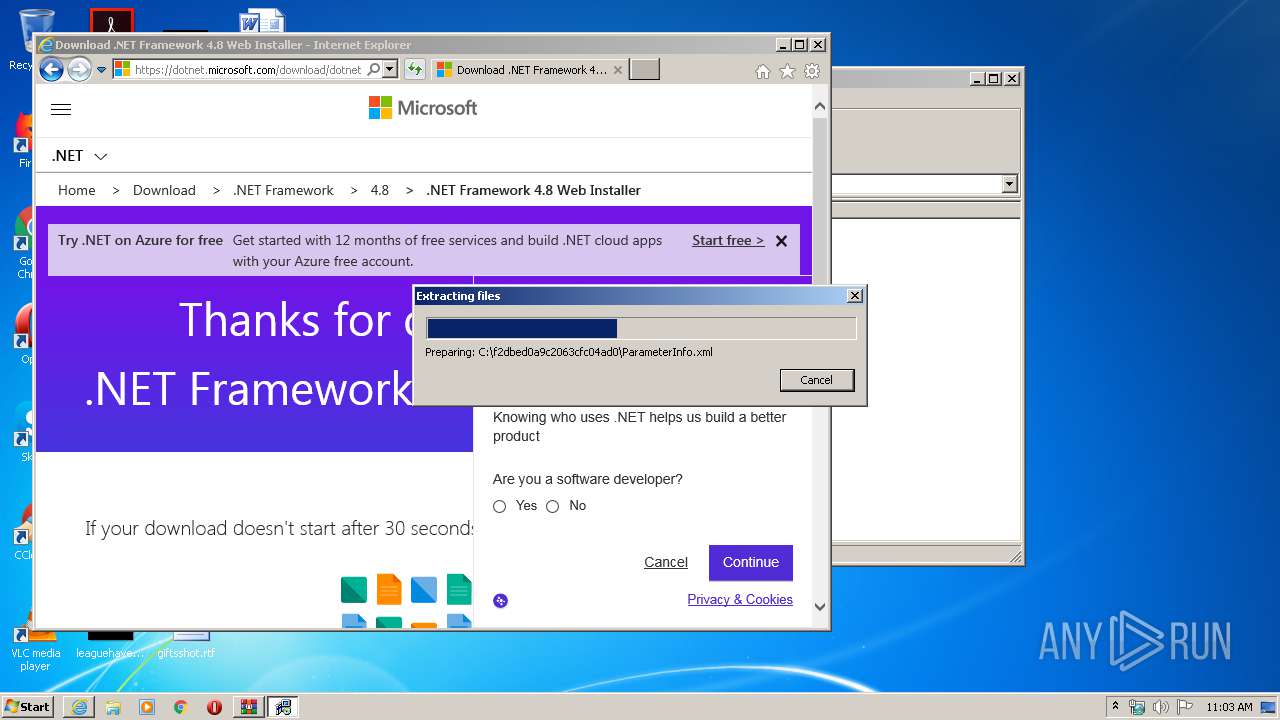
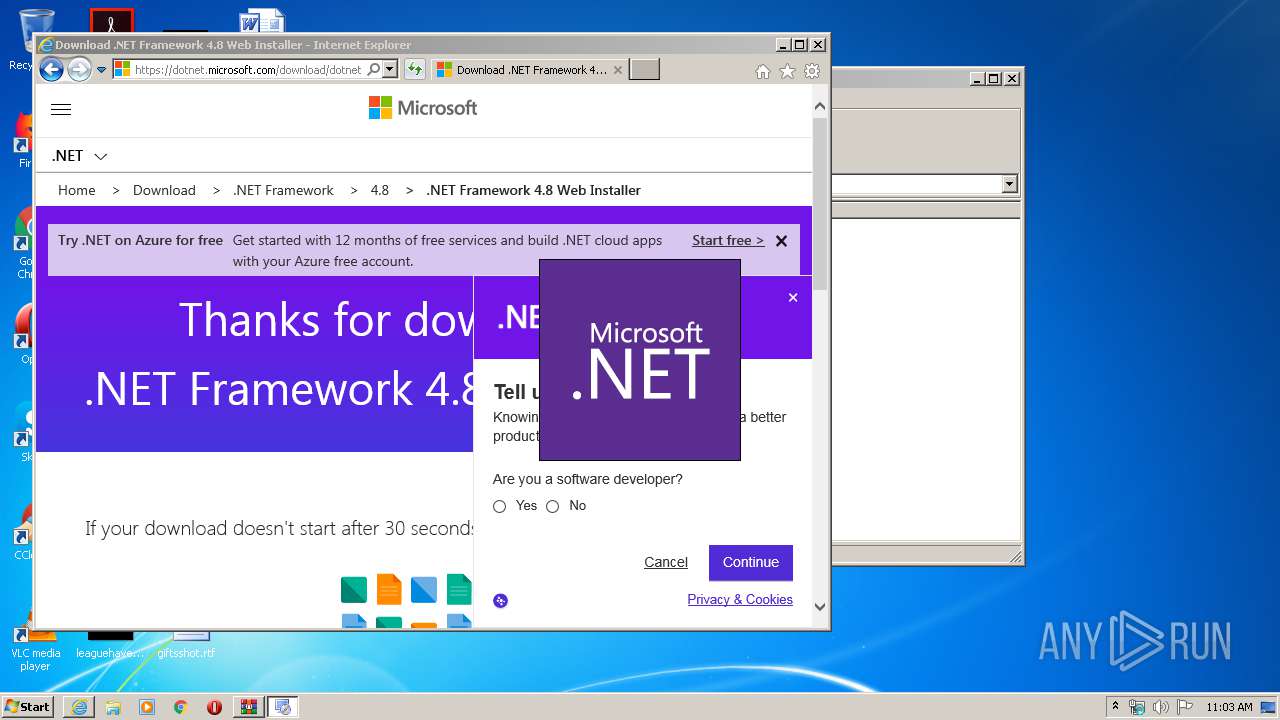
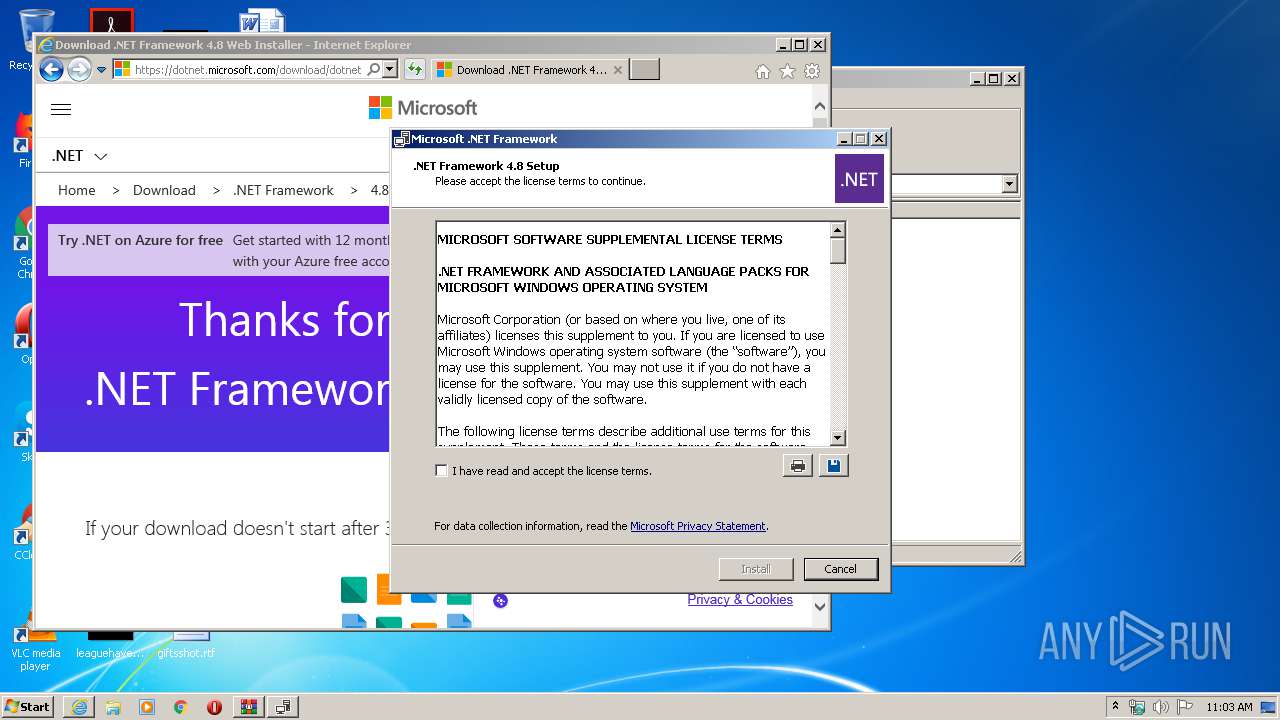
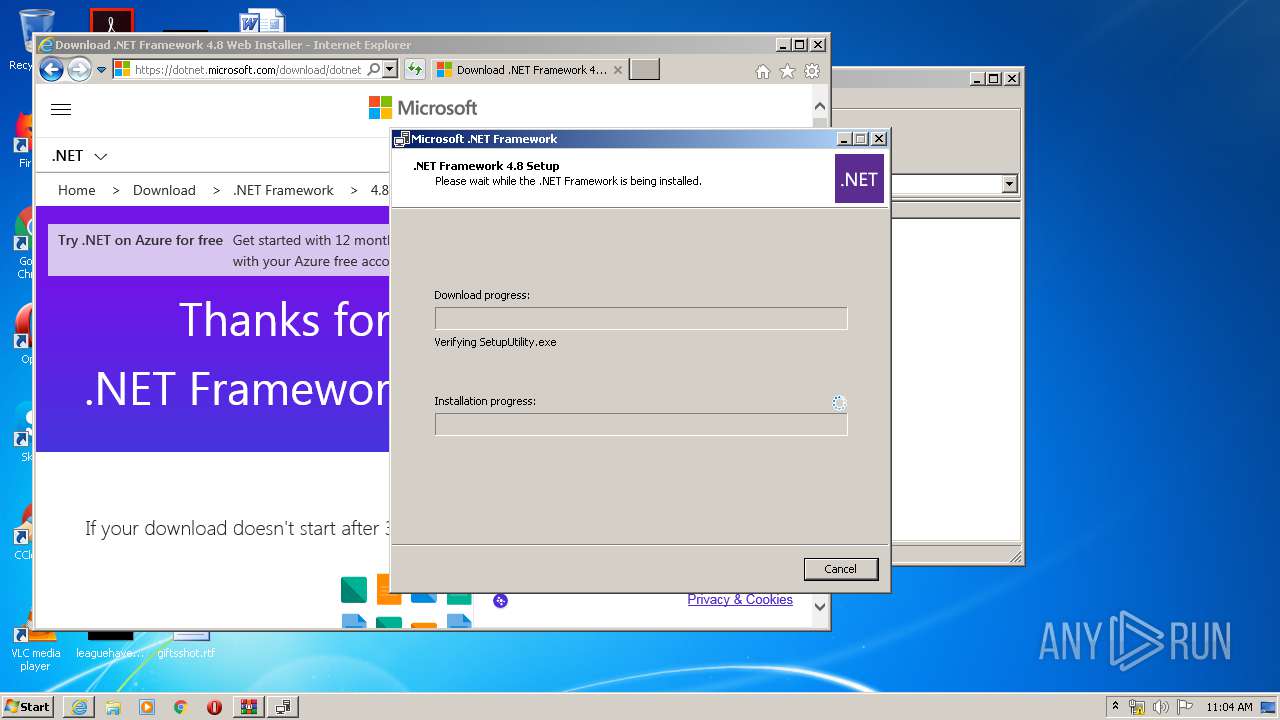
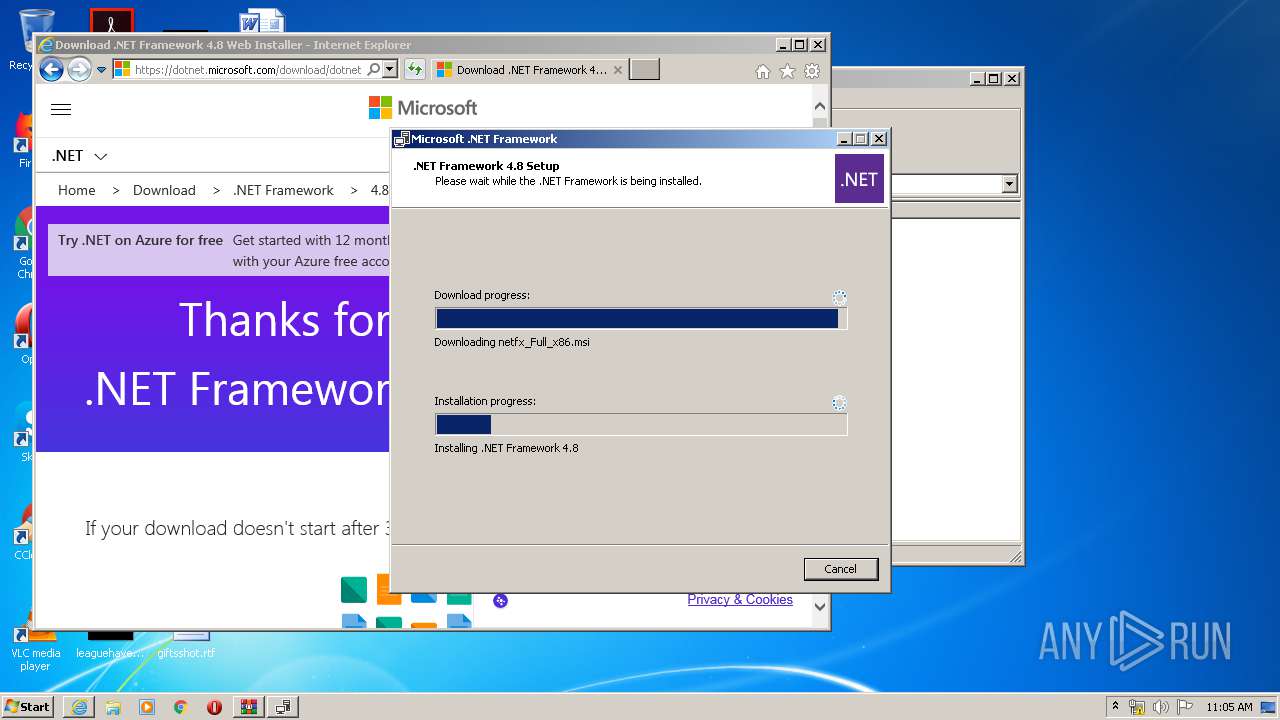
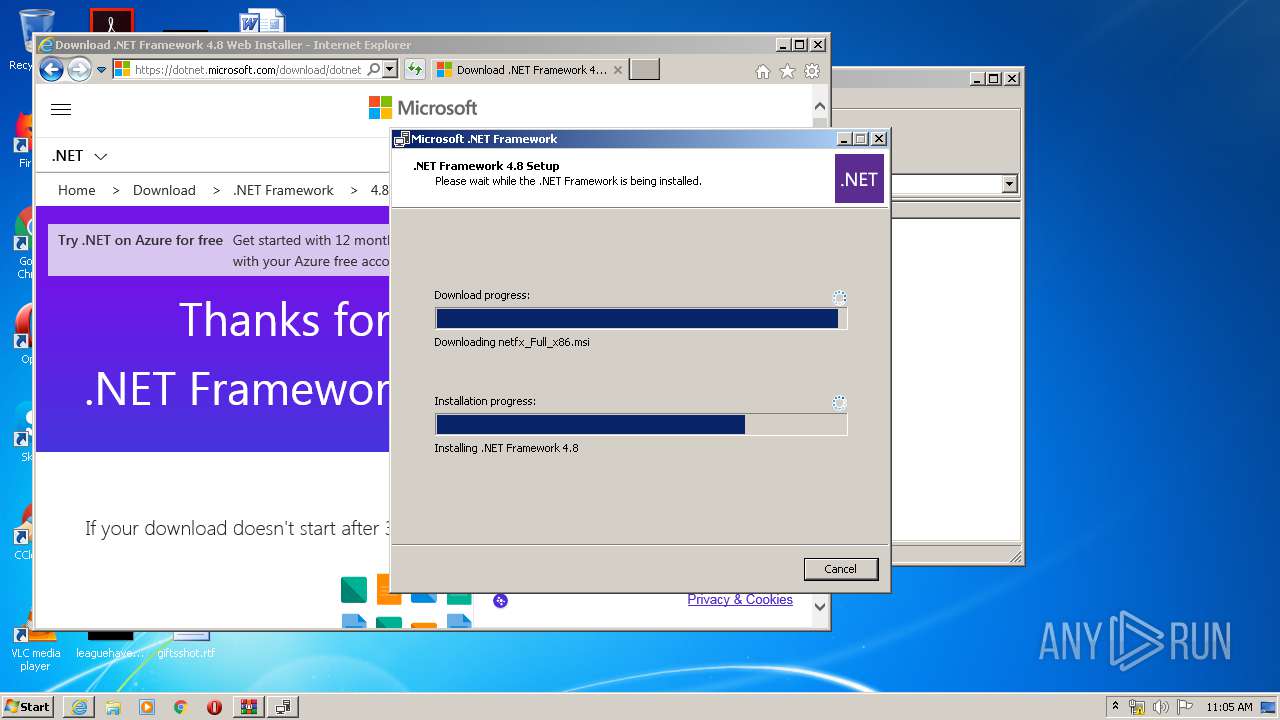
Application was dropped or rewritten from another process
- ValorantAimbotUI.exe (PID: 1064)
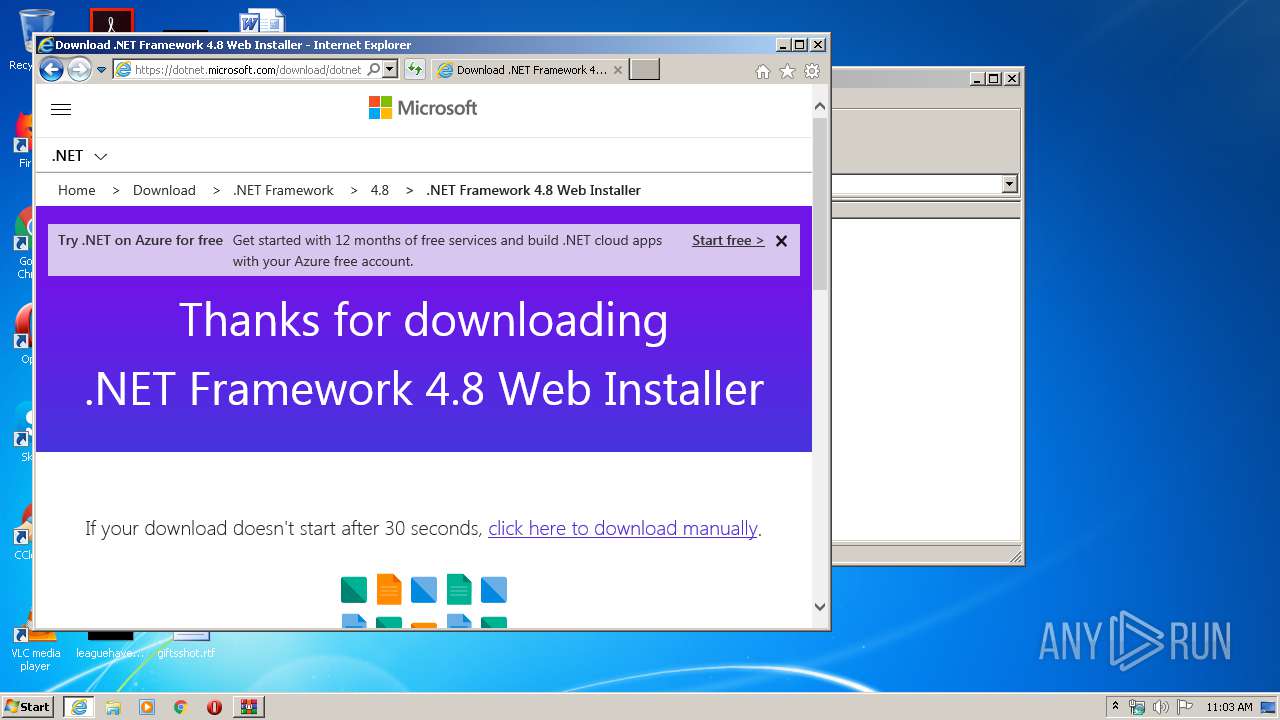
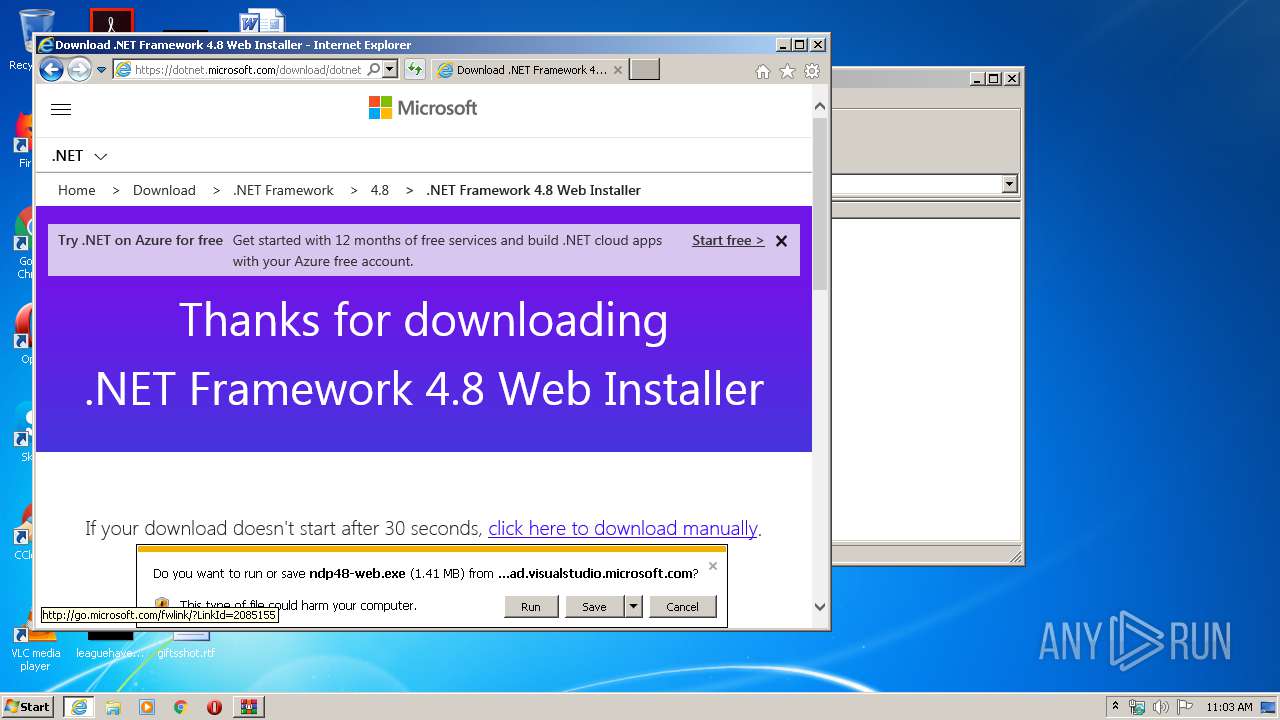
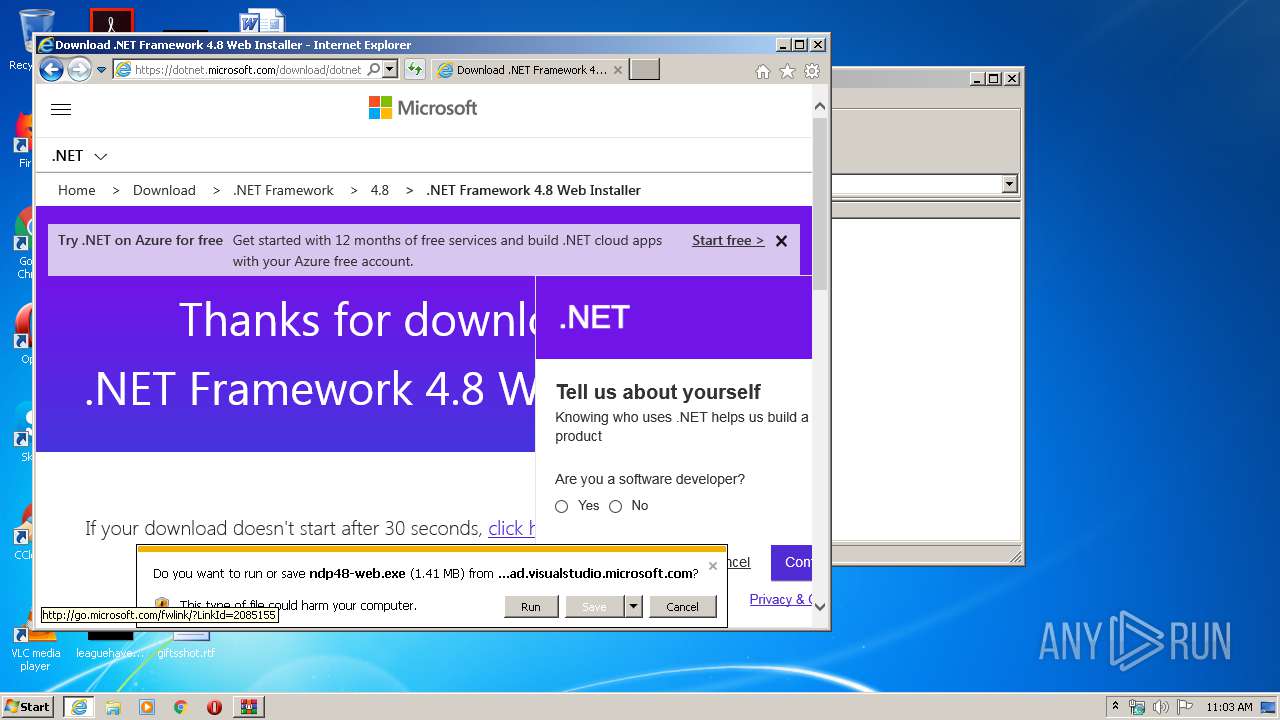
- ndp48-web.exe (PID: 1632)
- ndp48-web.exe (PID: 1784)
- SetupUtility.exe (PID: 2356)
- SetupUtility.exe (PID: 2420)
- Setup.exe (PID: 3024)
- aspnet_regiis.exe (PID: 2724)
- regtlibv12.exe (PID: 1356)
- regtlibv12.exe (PID: 2812)
- regtlibv12.exe (PID: 4056)
- regtlibv12.exe (PID: 2500)
- ServiceModelReg.exe (PID: 4076)
- ngen.exe (PID: 3992)
- regtlibv12.exe (PID: 1772)
- regtlibv12.exe (PID: 3660)
- regtlibv12.exe (PID: 3016)
- mscorsvw.exe (PID: 312)
- ngen.exe (PID: 3524)
- ngen.exe (PID: 2864)
- mscorsvw.exe (PID: 2216)
- mscorsvw.exe (PID: 2468)
- mscorsvw.exe (PID: 792)
- mscorsvw.exe (PID: 2784)
- mscorsvw.exe (PID: 552)
- mscorsvw.exe (PID: 3828)
- mscorsvw.exe (PID: 1440)
- mscorsvw.exe (PID: 1196)
- mscorsvw.exe (PID: 1340)
- mscorsvw.exe (PID: 2284)
- mscorsvw.exe (PID: 2668)
- mscorsvw.exe (PID: 3584)
- mscorsvw.exe (PID: 2116)
- mscorsvw.exe (PID: 3236)
- mscorsvw.exe (PID: 872)
- mscorsvw.exe (PID: 1016)
- mscorsvw.exe (PID: 3264)
- mscorsvw.exe (PID: 3088)
- mscorsvw.exe (PID: 3108)
- mscorsvw.exe (PID: 1708)
- mscorsvw.exe (PID: 3076)
- mscorsvw.exe (PID: 4004)
- mscorsvw.exe (PID: 2944)
- mscorsvw.exe (PID: 3044)
- mscorsvw.exe (PID: 3516)
- mscorsvw.exe (PID: 2596)
- mscorsvw.exe (PID: 3468)
- mscorsvw.exe (PID: 3960)
- mscorsvw.exe (PID: 2276)
- mscorsvw.exe (PID: 3600)
- mscorsvw.exe (PID: 2620)
- mscorsvw.exe (PID: 3868)
- mscorsvw.exe (PID: 3788)
- mscorsvw.exe (PID: 3472)
- mscorsvw.exe (PID: 2872)
- mscorsvw.exe (PID: 4040)
- mscorsvw.exe (PID: 3532)
- mscorsvw.exe (PID: 2360)
- mscorsvw.exe (PID: 2412)
- mscorsvw.exe (PID: 4004)
- mscorsvw.exe (PID: 3760)
- mscorsvw.exe (PID: 3812)
- mscorsvw.exe (PID: 3508)
- mscorsvw.exe (PID: 2612)
- mscorsvw.exe (PID: 3216)
- mscorsvw.exe (PID: 2468)
- mscorsvw.exe (PID: 2288)
- mscorsvw.exe (PID: 3624)
- ValorantAimbotUI.exe (PID: 3964)
- mscorsvw.exe (PID: 2736)
- mscorsvw.exe (PID: 2124)
- mscorsvw.exe (PID: 2748)
- mscorsvw.exe (PID: 2696)
- mscorsvw.exe (PID: 3072)
- mscorsvw.exe (PID: 2228)
- mscorsvw.exe (PID: 2160)
- mscorsvw.exe (PID: 392)
- mscorsvw.exe (PID: 2456)
- mscorsvw.exe (PID: 1028)
- mscorsvw.exe (PID: 3228)
- mscorsvw.exe (PID: 576)
- mscorsvw.exe (PID: 2116)
- mscorsvw.exe (PID: 3504)
- mscorsvw.exe (PID: 3076)
- mscorsvw.exe (PID: 2208)
- mscorsvw.exe (PID: 3808)
- mscorsvw.exe (PID: 2320)
- mscorsvw.exe (PID: 2620)
- mscorsvw.exe (PID: 3336)
- mscorsvw.exe (PID: 2608)
- mscorsvw.exe (PID: 3928)
- mscorsvw.exe (PID: 2128)
- mscorsvw.exe (PID: 2624)
- mscorsvw.exe (PID: 3900)
- mscorsvw.exe (PID: 3112)
- mscorsvw.exe (PID: 2644)
- mscorsvw.exe (PID: 3140)
- mscorsvw.exe (PID: 1520)
- mscorsvw.exe (PID: 1016)
- mscorsvw.exe (PID: 2252)
- mscorsvw.exe (PID: 2512)
- mscorsvw.exe (PID: 2184)
- mscorsvw.exe (PID: 1252)
- mscorsvw.exe (PID: 2228)
- mscorsvw.exe (PID: 2668)
- mscorsvw.exe (PID: 1168)
- mscorsvw.exe (PID: 1784)
- mscorsvw.exe (PID: 2388)
- mscorsvw.exe (PID: 4040)
- mscorsvw.exe (PID: 2508)
- mscorsvw.exe (PID: 3172)
- mscorsvw.exe (PID: 3652)
- mscorsvw.exe (PID: 4032)
- mscorsvw.exe (PID: 2080)
- mscorsvw.exe (PID: 2108)
- mscorsvw.exe (PID: 3428)
- mscorsvw.exe (PID: 956)
- mscorsvw.exe (PID: 628)
- mscorsvw.exe (PID: 2056)
- mscorsvw.exe (PID: 3040)
- mscorsvw.exe (PID: 3624)
- mscorsvw.exe (PID: 744)
- mscorsvw.exe (PID: 3484)
- mscorsvw.exe (PID: 3972)
- mscorsvw.exe (PID: 3984)
- mscorsvw.exe (PID: 1704)
- mscorsvw.exe (PID: 3712)
- mscorsvw.exe (PID: 4072)
- mscorsvw.exe (PID: 3348)
- mscorsvw.exe (PID: 3308)
- mscorsvw.exe (PID: 3684)
- mscorsvw.exe (PID: 2276)
- mscorsvw.exe (PID: 2772)
- mscorsvw.exe (PID: 3308)
- mscorsvw.exe (PID: 3408)
- SetupUtility.exe (PID: 3608)
- mscorsvw.exe (PID: 3656)
Actions looks like stealing of personal data
- ndp48-web.exe (PID: 1632)
- Setup.exe (PID: 3024)
- WinRAR.exe (PID: 3008)
Loads dropped or rewritten executable
- Setup.exe (PID: 3024)
- mscorsvw.exe (PID: 312)
- svchost.exe (PID: 756)
- ngen.exe (PID: 2864)
- mscorsvw.exe (PID: 2468)
- mscorsvw.exe (PID: 2216)
- ngen.exe (PID: 3524)
- mscorsvw.exe (PID: 1196)
- mscorsvw.exe (PID: 552)
- mscorsvw.exe (PID: 3828)
- mscorsvw.exe (PID: 1440)
- ngen.exe (PID: 3992)
- mscorsvw.exe (PID: 2284)
- mscorsvw.exe (PID: 2668)
- mscorsvw.exe (PID: 3584)
- mscorsvw.exe (PID: 2116)
- mscorsvw.exe (PID: 3236)
- mscorsvw.exe (PID: 1016)
- mscorsvw.exe (PID: 872)
- mscorsvw.exe (PID: 3264)
- mscorsvw.exe (PID: 3088)
- mscorsvw.exe (PID: 3108)
- mscorsvw.exe (PID: 2696)
- mscorsvw.exe (PID: 1708)
- mscorsvw.exe (PID: 4004)
- mscorsvw.exe (PID: 3076)
- mscorsvw.exe (PID: 2944)
- mscorsvw.exe (PID: 1340)
- mscorsvw.exe (PID: 3044)
- mscorsvw.exe (PID: 3960)
- mscorsvw.exe (PID: 3468)
- mscorsvw.exe (PID: 2612)
- mscorsvw.exe (PID: 3600)
- mscorsvw.exe (PID: 2276)
- mscorsvw.exe (PID: 2596)
- mscorsvw.exe (PID: 2784)
- mscorsvw.exe (PID: 3868)
- mscorsvw.exe (PID: 4040)
- mscorsvw.exe (PID: 3472)
- mscorsvw.exe (PID: 3516)
- mscorsvw.exe (PID: 2620)
- mscorsvw.exe (PID: 3788)
- mscorsvw.exe (PID: 2412)
- mscorsvw.exe (PID: 2360)
- mscorsvw.exe (PID: 3532)
- mscorsvw.exe (PID: 3508)
- mscorsvw.exe (PID: 3624)
- mscorsvw.exe (PID: 2468)
- mscorsvw.exe (PID: 2288)
- mscorsvw.exe (PID: 4004)
- mscorsvw.exe (PID: 3216)
- ValorantAimbotUI.exe (PID: 3964)
- mscorsvw.exe (PID: 3760)
- mscorsvw.exe (PID: 2872)
- mscorsvw.exe (PID: 3812)
- mscorsvw.exe (PID: 2124)
- mscorsvw.exe (PID: 2748)
- mscorsvw.exe (PID: 2736)
- mscorsvw.exe (PID: 2228)
- mscorsvw.exe (PID: 392)
- mscorsvw.exe (PID: 2160)
- mscorsvw.exe (PID: 3072)
- mscorsvw.exe (PID: 2456)
- mscorsvw.exe (PID: 3504)
- mscorsvw.exe (PID: 1028)
- mscorsvw.exe (PID: 2208)
- mscorsvw.exe (PID: 3228)
- mscorsvw.exe (PID: 576)
- mscorsvw.exe (PID: 3076)
- mscorsvw.exe (PID: 2116)
- mscorsvw.exe (PID: 2320)
- mscorsvw.exe (PID: 2620)
- mscorsvw.exe (PID: 3336)
- mscorsvw.exe (PID: 3808)
- mscorsvw.exe (PID: 2624)
- mscorsvw.exe (PID: 2608)
- mscorsvw.exe (PID: 3928)
- mscorsvw.exe (PID: 2128)
- mscorsvw.exe (PID: 3900)
- mscorsvw.exe (PID: 3112)
- mscorsvw.exe (PID: 3140)
- mscorsvw.exe (PID: 2512)
- mscorsvw.exe (PID: 2644)
- mscorsvw.exe (PID: 2184)
- mscorsvw.exe (PID: 1520)
- mscorsvw.exe (PID: 2252)
- mscorsvw.exe (PID: 1252)
- mscorsvw.exe (PID: 2228)
- mscorsvw.exe (PID: 2668)
- mscorsvw.exe (PID: 4040)
- mscorsvw.exe (PID: 1168)
- mscorsvw.exe (PID: 1784)
- mscorsvw.exe (PID: 2388)
- mscorsvw.exe (PID: 2508)
- mscorsvw.exe (PID: 4032)
- mscorsvw.exe (PID: 3172)
- mscorsvw.exe (PID: 2080)
- mscorsvw.exe (PID: 2108)
- mscorsvw.exe (PID: 3652)
- mscorsvw.exe (PID: 1016)
- mscorsvw.exe (PID: 956)
- mscorsvw.exe (PID: 628)
- aspnet_regiis.exe (PID: 2724)
- mscorsvw.exe (PID: 3408)
- mscorsvw.exe (PID: 2772)
- mscorsvw.exe (PID: 3348)
- mscorsvw.exe (PID: 3624)
- mscorsvw.exe (PID: 3428)
- mscorsvw.exe (PID: 3484)
- mscorsvw.exe (PID: 3656)
- mscorsvw.exe (PID: 744)
- mscorsvw.exe (PID: 3984)
- mscorsvw.exe (PID: 4072)
- mscorsvw.exe (PID: 1704)
- mscorsvw.exe (PID: 3308)
- mscorsvw.exe (PID: 3972)
- mscorsvw.exe (PID: 2056)
- mscorsvw.exe (PID: 3684)
- mscorsvw.exe (PID: 3712)
- mscorsvw.exe (PID: 3308)
- mscorsvw.exe (PID: 2276)
- mscorsvw.exe (PID: 792)
- mscorsvw.exe (PID: 3040)
Loads the Task Scheduler COM API
- ngen.exe (PID: 3992)
- ngen.exe (PID: 2864)
- mscorsvw.exe (PID: 312)
Changes settings of System certificates
- Setup.exe (PID: 3024)
SUSPICIOUS
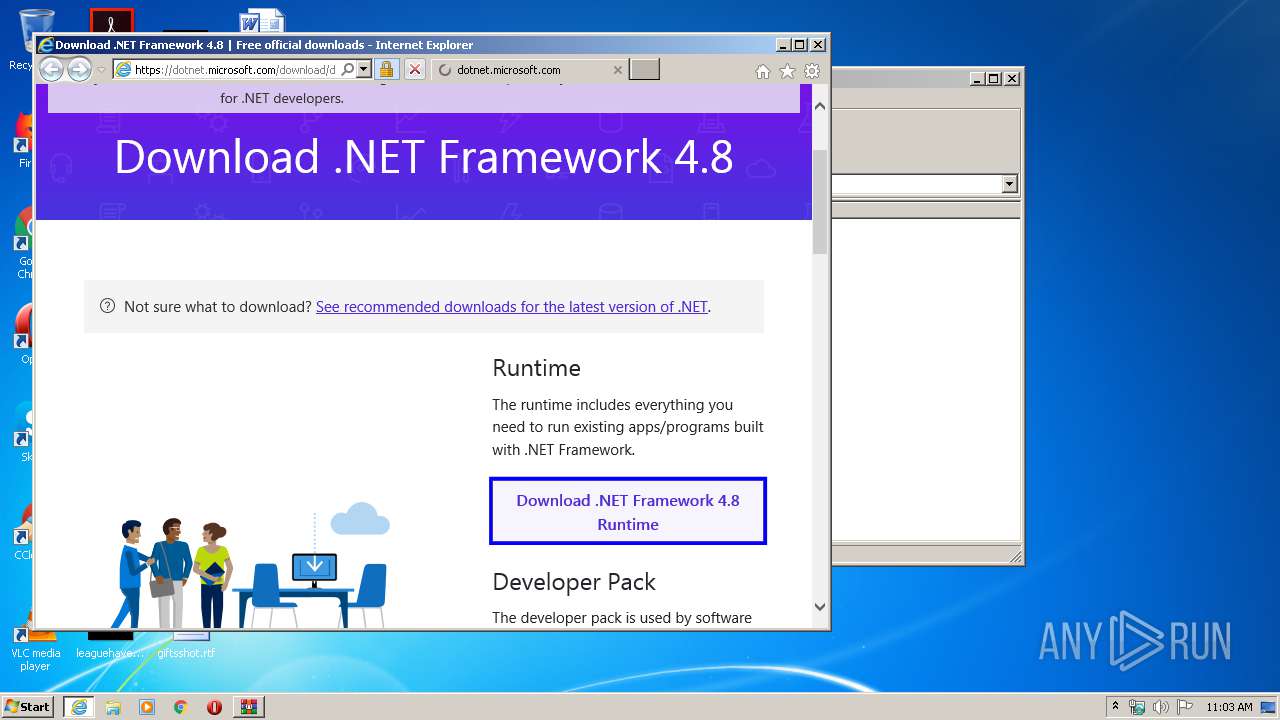
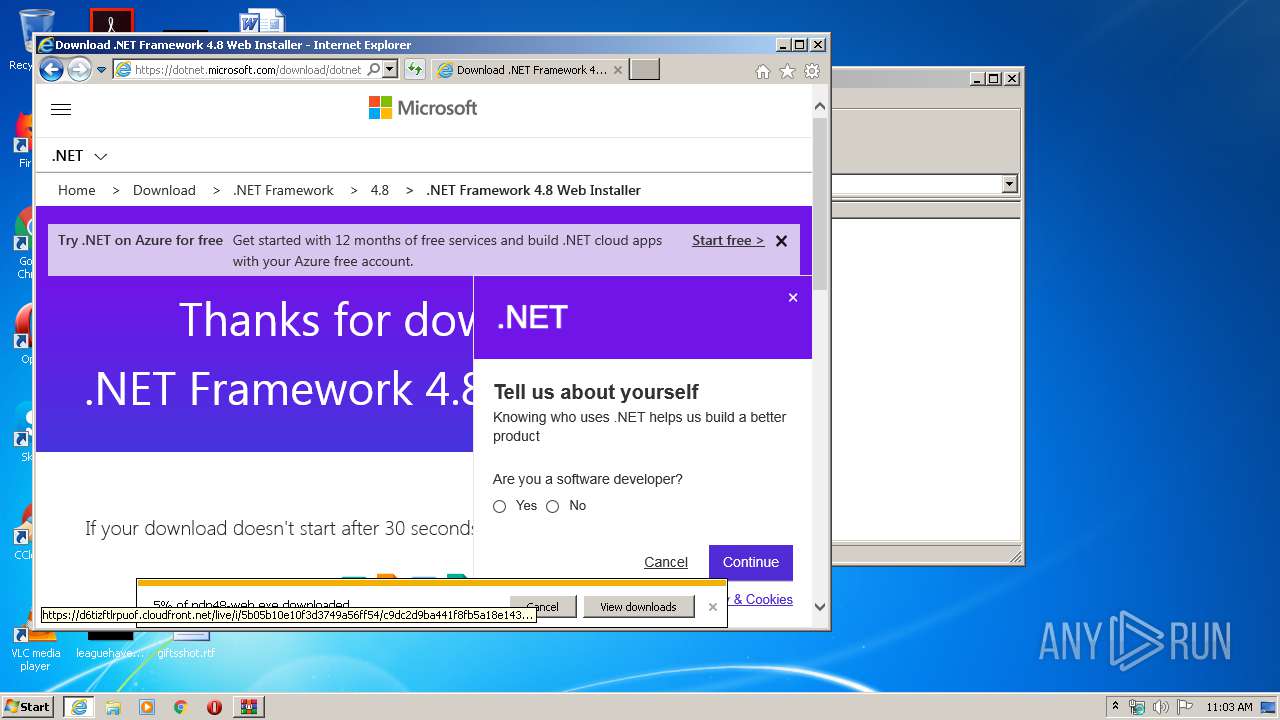
Starts Internet Explorer
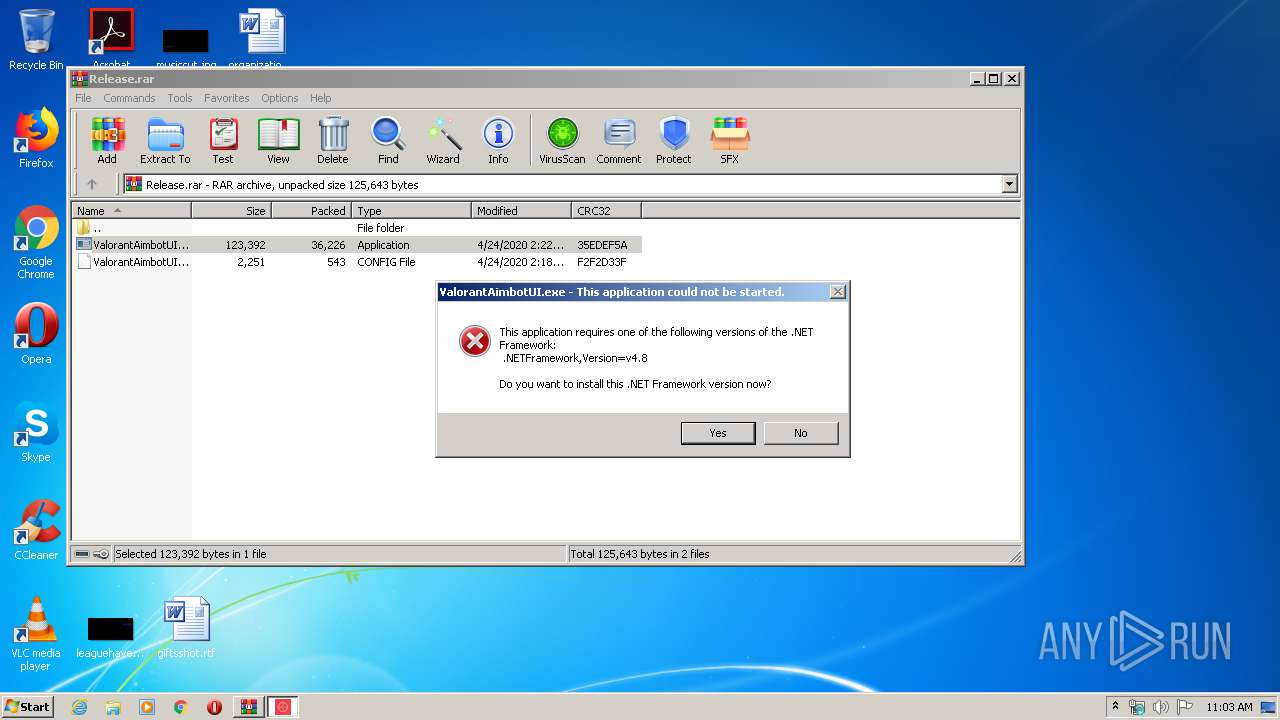
- ValorantAimbotUI.exe (PID: 1064)
Executable content was dropped or overwritten
- iexplore.exe (PID: 2404)
- iexplore.exe (PID: 1944)
- WinRAR.exe (PID: 3008)
- ndp48-web.exe (PID: 1632)
- TMPE664.tmp.exe (PID: 1900)
- Setup.exe (PID: 3024)
- msiexec.exe (PID: 3476)
- mscorsvw.exe (PID: 2784)
- mscorsvw.exe (PID: 3044)
- mscorsvw.exe (PID: 3468)
- mscorsvw.exe (PID: 2160)
- mscorsvw.exe (PID: 3960)
- mscorsvw.exe (PID: 1028)
- mscorsvw.exe (PID: 2116)
- mscorsvw.exe (PID: 3076)
- mscorsvw.exe (PID: 3808)
- mscorsvw.exe (PID: 3336)
- mscorsvw.exe (PID: 3928)
- mscorsvw.exe (PID: 2124)
- mscorsvw.exe (PID: 2128)
- mscorsvw.exe (PID: 3112)
- mscorsvw.exe (PID: 1520)
- mscorsvw.exe (PID: 1252)
- mscorsvw.exe (PID: 1016)
- mscorsvw.exe (PID: 2388)
- mscorsvw.exe (PID: 1784)
- mscorsvw.exe (PID: 4032)
- mscorsvw.exe (PID: 2508)
- mscorsvw.exe (PID: 628)
- mscorsvw.exe (PID: 1168)
Changes the autorun value in the registry
- msiexec.exe (PID: 3476)
Creates files in the Windows directory
- msiexec.exe (PID: 3476)
- lodctr.exe (PID: 2828)
- ngen.exe (PID: 3992)
- aspnet_regiis.exe (PID: 2724)
- lodctr.exe (PID: 1920)
- lodctr.exe (PID: 3744)
- lodctr.exe (PID: 1520)
- ngen.exe (PID: 2864)
- lodctr.exe (PID: 3660)
- ngen.exe (PID: 3524)
- mscorsvw.exe (PID: 312)
- mscorsvw.exe (PID: 3960)
- mscorsvw.exe (PID: 3044)
- mscorsvw.exe (PID: 2784)
- mscorsvw.exe (PID: 3468)
- mscorsvw.exe (PID: 2160)
- mscorsvw.exe (PID: 1028)
- mscorsvw.exe (PID: 2116)
- mscorsvw.exe (PID: 3076)
- mscorsvw.exe (PID: 3808)
- mscorsvw.exe (PID: 3336)
- mscorsvw.exe (PID: 2124)
- mscorsvw.exe (PID: 2128)
- mscorsvw.exe (PID: 3928)
- mscorsvw.exe (PID: 3112)
- mscorsvw.exe (PID: 1520)
- mscorsvw.exe (PID: 1252)
- mscorsvw.exe (PID: 2388)
- mscorsvw.exe (PID: 1168)
- mscorsvw.exe (PID: 4032)
- mscorsvw.exe (PID: 2508)
- mscorsvw.exe (PID: 628)
- mscorsvw.exe (PID: 2056)
- mscorsvw.exe (PID: 3040)
- mscorsvw.exe (PID: 3624)
- mscorsvw.exe (PID: 3484)
- mscorsvw.exe (PID: 744)
- mscorsvw.exe (PID: 3972)
- mscorsvw.exe (PID: 3984)
- mscorsvw.exe (PID: 3712)
- mscorsvw.exe (PID: 1704)
- mscorsvw.exe (PID: 1016)
- mscorsvw.exe (PID: 2772)
- mscorsvw.exe (PID: 3308)
- mscorsvw.exe (PID: 3684)
- mscorsvw.exe (PID: 3348)
- mscorsvw.exe (PID: 4072)
- mscorsvw.exe (PID: 3408)
- mscorsvw.exe (PID: 3656)
- mscorsvw.exe (PID: 1784)
- mscorsvw.exe (PID: 3308)
- mscorsvw.exe (PID: 2276)
Creates COM task schedule object
- msiexec.exe (PID: 3476)
- aspnet_regiis.exe (PID: 2724)
Removes files from Windows directory
- lodctr.exe (PID: 2828)
- msiexec.exe (PID: 3476)
- aspnet_regiis.exe (PID: 2724)
- lodctr.exe (PID: 1520)
- lodctr.exe (PID: 1920)
- lodctr.exe (PID: 3744)
- lodctr.exe (PID: 3660)
- mscorsvw.exe (PID: 3960)
- mscorsvw.exe (PID: 2784)
- mscorsvw.exe (PID: 3044)
- mscorsvw.exe (PID: 3468)
- mscorsvw.exe (PID: 2160)
- mscorsvw.exe (PID: 1028)
- mscorsvw.exe (PID: 3076)
- mscorsvw.exe (PID: 3808)
- mscorsvw.exe (PID: 2116)
- mscorsvw.exe (PID: 3336)
- mscorsvw.exe (PID: 3928)
- mscorsvw.exe (PID: 2124)
- mscorsvw.exe (PID: 2128)
- mscorsvw.exe (PID: 3112)
- mscorsvw.exe (PID: 1520)
- mscorsvw.exe (PID: 1252)
- mscorsvw.exe (PID: 1016)
- mscorsvw.exe (PID: 1784)
- mscorsvw.exe (PID: 2388)
- mscorsvw.exe (PID: 4032)
- mscorsvw.exe (PID: 1168)
- mscorsvw.exe (PID: 2508)
- mscorsvw.exe (PID: 2056)
- mscorsvw.exe (PID: 3040)
- mscorsvw.exe (PID: 3624)
- mscorsvw.exe (PID: 744)
- mscorsvw.exe (PID: 628)
- mscorsvw.exe (PID: 3484)
- mscorsvw.exe (PID: 3984)
- mscorsvw.exe (PID: 1704)
- mscorsvw.exe (PID: 2772)
- mscorsvw.exe (PID: 3712)
- mscorsvw.exe (PID: 4072)
- mscorsvw.exe (PID: 3684)
- mscorsvw.exe (PID: 3308)
- mscorsvw.exe (PID: 3348)
- mscorsvw.exe (PID: 3972)
- mscorsvw.exe (PID: 3308)
- mscorsvw.exe (PID: 2276)
- mscorsvw.exe (PID: 3408)
- mscorsvw.exe (PID: 3656)
Adds / modifies Windows certificates
- Setup.exe (PID: 3024)
Reads Internet Cache Settings
- Setup.exe (PID: 3024)
INFO
Changes internet zones settings
- iexplore.exe (PID: 1944)
Creates files in the user directory
- iexplore.exe (PID: 2404)
- iexplore.exe (PID: 1944)
Reads Internet Cache Settings
- iexplore.exe (PID: 1944)
- iexplore.exe (PID: 2404)
Reads internet explorer settings
- iexplore.exe (PID: 2404)
Modifies the phishing filter of IE
- iexplore.exe (PID: 1944)
Reads settings of System Certificates
- Setup.exe (PID: 3024)
- iexplore.exe (PID: 2404)
- iexplore.exe (PID: 1944)
Dropped object may contain Bitcoin addresses
- msiexec.exe (PID: 3476)
- iexplore.exe (PID: 1944)
- mscorsvw.exe (PID: 312)
Creates or modifies windows services
- msiexec.exe (PID: 3476)
Application launched itself
- msiexec.exe (PID: 3476)
Creates a software uninstall entry
- msiexec.exe (PID: 3476)
Loads dropped or rewritten executable
- msiexec.exe (PID: 3476)
Changes settings of System certificates
- iexplore.exe (PID: 1944)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1944)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
217
Monitored processes
157
Malicious processes
119
Suspicious processes
14
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 312 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: .NET Runtime Optimization Service Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
| 392 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe -StartupEvent 214 -InterruptEvent 0 -NGENProcess 200 -Pipe 2ac -Comment "NGen Worker Process" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe | — | ngen.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: .NET Runtime Optimization Service Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
| 552 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe -StartupEvent 1bc -InterruptEvent 0 -NGENProcess 174 -Pipe 1a4 -Comment "NGen Worker Process" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe | — | ngen.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: .NET Runtime Optimization Service Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
| 576 | "C:\Windows\system32\lodctr.exe" /m:"C:\Windows\Microsoft.NET\Framework\v4.0.30319\WorkflowServiceHostPerformanceCounters.man" | C:\Windows\system32\lodctr.exe | — | MsiExec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Load PerfMon Counters Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 576 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe -StartupEvent 2d0 -InterruptEvent 0 -NGENProcess 298 -Pipe 200 -Comment "NGen Worker Process" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe | — | ngen.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: .NET Runtime Optimization Service Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
| 628 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe -StartupEvent 378 -InterruptEvent 0 -NGENProcess 31c -Pipe 324 -Comment "NGen Worker Process" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe | ngen.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: .NET Runtime Optimization Service Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
| 744 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe -StartupEvent 388 -InterruptEvent 0 -NGENProcess 384 -Pipe 378 -Comment "NGen Worker Process" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe | — | ngen.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: .NET Runtime Optimization Service Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
| 756 | C:\Windows\System32\svchost.exe -k LocalServiceNetworkRestricted | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 792 | "C:\Windows\system32\lodctr.exe" /m:"C:\Windows\Microsoft.NET\Framework\v4.0.30319\ServiceModelPerformanceCounters.man" | C:\Windows\system32\lodctr.exe | — | MsiExec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Load PerfMon Counters Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 792 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe -StartupEvent 1a8 -InterruptEvent 0 -NGENProcess 18c -Pipe 114 -Comment "NGen Worker Process" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe | — | ngen.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: .NET Runtime Optimization Service Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
Total events
40 311
Read events
17 469
Write events
18 698
Delete events
4 144
Modification events
| (PID) Process: | (3008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3008) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Release.rar | |||
| (PID) Process: | (3008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
2 489
Suspicious files
98
Text files
575
Unknown types
47
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2404 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab1698.tmp | — | |
MD5:— | SHA256:— | |||
| 2404 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar1699.tmp | — | |
MD5:— | SHA256:— | |||
| 3008 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3008.33295\ValorantAimbotUI.exe | executable | |
MD5:— | SHA256:— | |||
| 2404 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_BEB37ABADF39714871232B4792417E04 | binary | |
MD5:— | SHA256:— | |||
| 2404 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\general.min[1].js | text | |
MD5:— | SHA256:— | |||
| 2404 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_C9FB72B5AE80778A08024D8B0FDECC6F | der | |
MD5:— | SHA256:— | |||
| 2404 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_BEB37ABADF39714871232B4792417E04 | der | |
MD5:— | SHA256:— | |||
| 2404 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_C9FB72B5AE80778A08024D8B0FDECC6F | binary | |
MD5:— | SHA256:— | |||
| 2404 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\dotnet-framework-runtime[1].svg | image | |
MD5:— | SHA256:— | |||
| 2404 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\bootstrap-custom.min[1].css | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
38
TCP/UDP connections
73
DNS requests
39
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2404 | iexplore.exe | GET | 302 | 23.61.218.119:80 | http://go.microsoft.com/fwlink/?prd=11324&pver=4.5&sbp=AppLaunch&plcid=0x409&o1=.NETFramework,Version=v4.8&processName=ValorantAimbotUI.exe&platform=0000&osver=5&isServer=0&shimver=4.0.30319.0 | US | — | — | whitelisted |
2404 | iexplore.exe | GET | 200 | 143.204.208.23:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
2404 | iexplore.exe | GET | 200 | 23.37.43.27:80 | http://s.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCEGMYDTj7gJd4qdA1oxYY%2BEA%3D | NL | der | 1.71 Kb | shared |
2404 | iexplore.exe | GET | 200 | 143.204.208.160:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
2404 | iexplore.exe | GET | 200 | 172.217.22.3:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
2404 | iexplore.exe | GET | 200 | 143.204.208.127:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
2404 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAiIzVJfGSRETRSlgpHeuVI%3D | US | der | 1.47 Kb | whitelisted |
3024 | Setup.exe | GET | 200 | 2.16.186.74:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | der | 1.11 Kb | whitelisted |
2404 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAtb9ltrp%2FvQiykNkEU33uA%3D | US | der | 471 b | whitelisted |
2404 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2404 | iexplore.exe | 2.16.186.16:443 | statics-marketingsites-wcus-ms-com.akamaized.net | Akamai International B.V. | — | whitelisted |
2404 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2404 | iexplore.exe | 172.217.23.168:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
2404 | iexplore.exe | 23.61.218.119:80 | go.microsoft.com | Akamai Technologies, Inc. | US | whitelisted |
2404 | iexplore.exe | 172.217.23.110:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2404 | iexplore.exe | 2.21.38.54:443 | www.microsoft.com | GTT Communications Inc. | FR | malicious |
2404 | iexplore.exe | 2.16.186.27:443 | img-prod-cms-rt-microsoft-com.akamaized.net | Akamai International B.V. | — | whitelisted |
2404 | iexplore.exe | 72.247.225.227:443 | uhf.microsoft.com | Akamai Technologies, Inc. | US | whitelisted |
2404 | iexplore.exe | 72.247.226.83:443 | c.s-microsoft.com | Akamai Technologies, Inc. | US | whitelisted |
1944 | iexplore.exe | 13.107.246.10:443 | dotnet.microsoft.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
go.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
dotnet.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
statics-marketingsites-wcus-ms-com.akamaized.net |
| whitelisted |
c.s-microsoft.com |
| whitelisted |
img-prod-cms-rt-microsoft-com.akamaized.net |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
www.google-analytics.com |
| whitelisted |
Threats
Process | Message |
|---|---|
msiexec.exe | Failed to release Service
|