| File name: | VMP.exe |
| Full analysis: | https://app.any.run/tasks/302f23e9-525c-46ee-a4fc-4765bf416950 |
| Verdict: | Malicious activity |
| Analysis date: | May 28, 2024, 07:48:26 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows |
| MD5: | B884ACB314FA194A47620CD31217055F |
| SHA1: | C246150713BA938E3B98F11A6607D07AF6649B12 |
| SHA256: | 1E192445BE27CD9662FCA63B25F586FA928AE8D6DCE3C2251909F77BA3E78DE8 |
| SSDEEP: | 98304:uL1V+MNXnC0CIQf4Wc9eCXFJCnNgRZbr84vxebfRBNgGDtXgJYHXioqa1UG0tzru:Ng5Y0XKP |
MALICIOUS
Renames files like ransomware
- VMPe.exe.new (PID: 4284)
Drops the executable file immediately after the start
- VMPe.exe.new (PID: 4284)
- VMP.exe (PID: 1444)
- VMP.exe (PID: 1016)
- VMP.exe (PID: 4484)
Actions looks like stealing of personal data
- VMP.exe (PID: 4484)
SUSPICIOUS
Reads security settings of Internet Explorer
- VMP.exe (PID: 1016)
- VMPe.exe.new (PID: 4284)
- VMP.exe (PID: 4484)
Executable content was dropped or overwritten
- VMPe.exe.new (PID: 4284)
- VMP.exe (PID: 1016)
- VMP.exe (PID: 1444)
- VMP.exe (PID: 4484)
Reads the date of Windows installation
- VMPe.exe.new (PID: 4284)
Starts application with an unusual extension
- VMP.exe (PID: 1016)
Starts itself from another location
- VMPe.exe.new (PID: 4284)
- VMP.exe (PID: 1444)
Creates a software uninstall entry
- VMP.exe (PID: 4484)
Process drops legitimate windows executable
- VMP.exe (PID: 4484)
Write to the desktop.ini file (may be used to cloak folders)
- VMP.exe (PID: 4484)
INFO
Checks supported languages
- VMPe.exe.new (PID: 4284)
- VMP.exe (PID: 1444)
- VMP.exe (PID: 1016)
- VMP.exe (PID: 4484)
Reads the computer name
- VMPe.exe.new (PID: 4284)
- VMP.exe (PID: 1444)
- VMP.exe (PID: 1016)
- VMP.exe (PID: 4484)
Process checks computer location settings
- VMPe.exe.new (PID: 4284)
Creates files or folders in the user directory
- VMP.exe (PID: 1444)
- VMP.exe (PID: 4484)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:05:17 02:05:23+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.39 |
| CodeSize: | 3398656 |
| InitializedDataSize: | 2068480 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x29176c |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.0.163 |
| ProductVersionNumber: | 2.0.0.163 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | VMP.ir |
| FileDescription: | VMP |
| InternalName: | VMP |
| FileVersion: | 2.0.0.163 |
| LegalCopyright: | (C) 2024-2999 VMP.ir |
| OriginalFileName: | VMP.exe |
| ProductName: | VMP |
| ProductVersion: | 2.0.0.163 |
Total processes
121
Monitored processes
4
Malicious processes
4
Suspicious processes
0
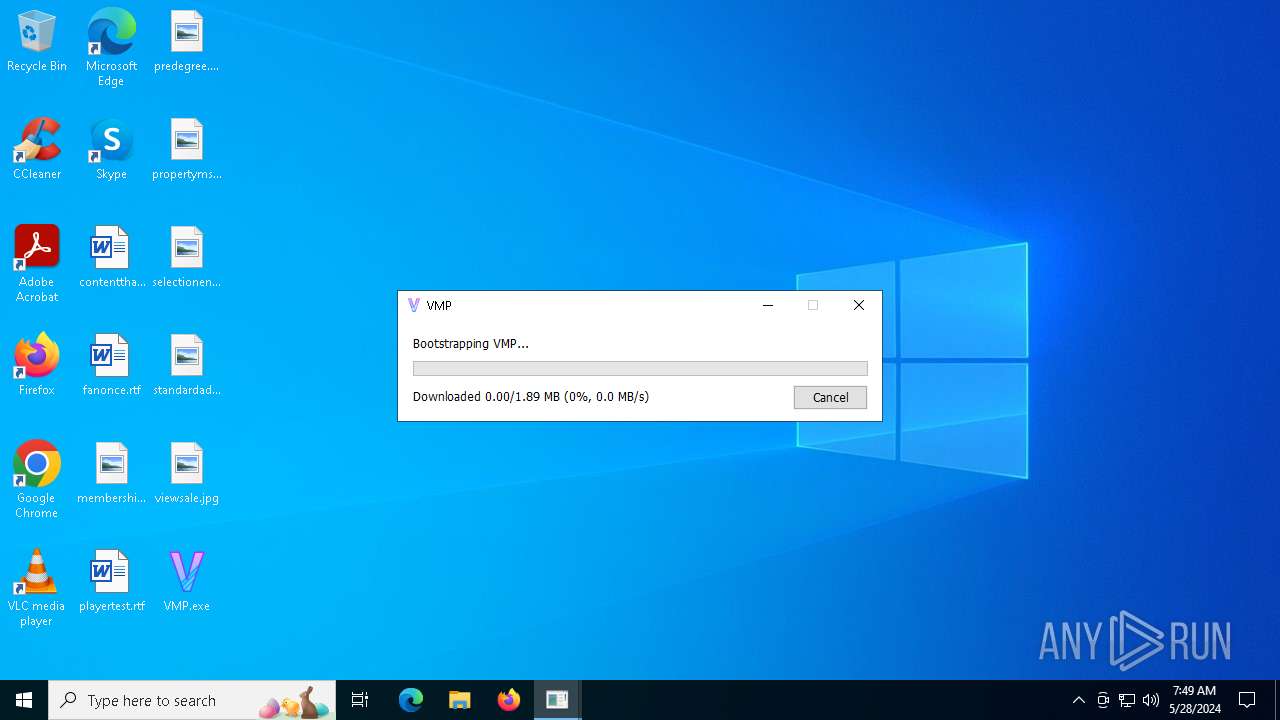
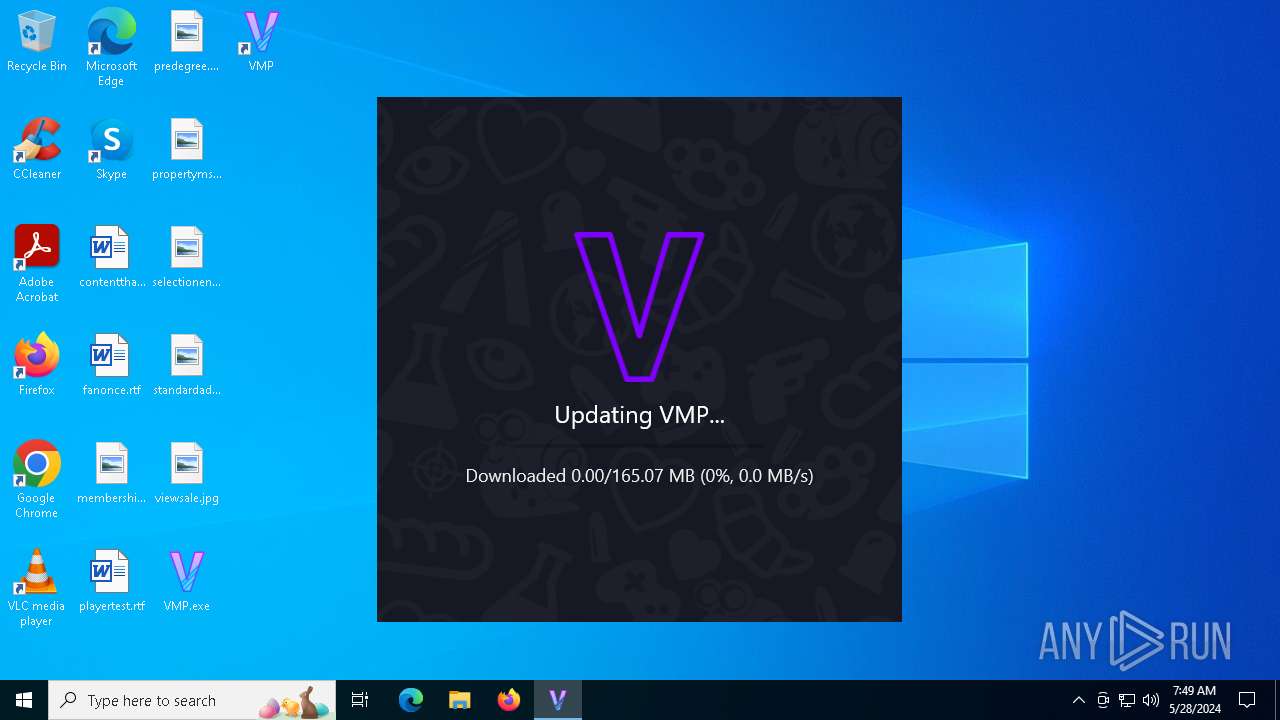
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1016 | "C:\Users\admin\Desktop\VMP.exe" | C:\Users\admin\Desktop\VMP.exe | explorer.exe | ||||||||||||
User: admin Company: VMP.ir Integrity Level: MEDIUM Description: VMP Exit code: 0 Version: 2.0.0.163 Modules
| |||||||||||||||
| 1444 | "C:\Users\admin\Desktop\VMP.exe" | C:\Users\admin\Desktop\VMP.exe | VMPe.exe.new | ||||||||||||
User: admin Company: VMP.ir Integrity Level: MEDIUM Description: VMP Exit code: 0 Version: 2.0.0.225 Modules
| |||||||||||||||
| 4284 | VMPe.exe.new -bootstrap "C:\Users\admin\Desktop\VMP.exe" | C:\Users\admin\Desktop\VMPe.exe.new | VMP.exe | ||||||||||||
User: admin Company: VMP.ir Integrity Level: MEDIUM Description: VMP Exit code: 0 Version: 2.0.0.225 Modules
| |||||||||||||||
| 4484 | "C:\Users\admin\AppData\Local\VMP\VMP.exe" | C:\Users\admin\AppData\Local\VMP\VMP.exe | VMP.exe | ||||||||||||
User: admin Company: VMP.ir Integrity Level: MEDIUM Description: VMP Version: 2.0.0.225 Modules
| |||||||||||||||
Total events
24 153
Read events
24 133
Write events
20
Delete events
0
Modification events
| (PID) Process: | (1016) VMP.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\VMP\VMP |
| Operation: | write | Name: | Last Run Location |
Value: C:\Users\admin\Desktop\ | |||
| (PID) Process: | (4284) VMPe.exe.new | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (4284) VMPe.exe.new | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (4284) VMPe.exe.new | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (4284) VMPe.exe.new | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1444) VMP.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\VMP\VMP |
| Operation: | write | Name: | Last Run Location |
Value: C:\Users\admin\Desktop\ | |||
| (PID) Process: | (4484) VMP.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\VMP\VMP |
| Operation: | write | Name: | Last Run Location |
Value: C:\Users\admin\AppData\Local\VMP\VMP.app\ | |||
| (PID) Process: | (4484) VMP.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\VMP_IR_VMP |
| Operation: | write | Name: | DisplayName |
Value: VMP | |||
| (PID) Process: | (4484) VMP.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\VMP_IR_VMP |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Users\admin\AppData\Local\VMP\VMP.exe,0 | |||
| (PID) Process: | (4484) VMP.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\VMP_IR_VMP |
| Operation: | write | Name: | HelpLink |
Value: https://cfx.re/ | |||
Executable files
175
Suspicious files
8
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4484 | VMP.exe | C:\Users\admin\AppData\Local\VMP\VMP.VisualElementsManifest.xml | text | |
MD5:7215BF5F561D44FDE7C00BA495720948 | SHA256:E392E302B6C63DA6EC916ADF867B5DB3BD9B363CDA0CA969B3E69B43D6E3691E | |||
| 4484 | VMP.exe | C:\Users\admin\AppData\Local\VMP\VMP.app\CitiLaunch_TLSDummy.dll | executable | |
MD5:DD88275202498EECC4B5E3D63C4D0500 | SHA256:9018FAB0FBEDEF8BFFE3097A1F54FD9F7A49E928E73E11EF4AC8DE0CAAB7856B | |||
| 4484 | VMP.exe | C:\Users\admin\AppData\Local\VMP\VMP.app\CitizenFX_SubProcess_game_2189.bin.tmp | executable | |
MD5:4857EA337ED9039FC996FDBE4E5247E0 | SHA256:4D94D64C2FB16D59A64338F9B51297E968E8488EBC841051FF9533CD34D423E3 | |||
| 4484 | VMP.exe | C:\Users\admin\AppData\Local\VMP\VMP.app\CitizenFX_SubProcess_game_1604.bin.tmp | executable | |
MD5:2EFA7E589B21A38ABB0116A3E94273D4 | SHA256:C5197F9E48DE0D272C30437C1D7080BC18DF67A5590220BDDF3E56DBF7819FDC | |||
| 4484 | VMP.exe | C:\Users\admin\AppData\Local\VMP\VMP.app\CitiLaunch_TLSDummy.dll.tmp | executable | |
MD5:DD88275202498EECC4B5E3D63C4D0500 | SHA256:9018FAB0FBEDEF8BFFE3097A1F54FD9F7A49E928E73E11EF4AC8DE0CAAB7856B | |||
| 1444 | VMP.exe | C:\Users\admin\AppData\Local\VMP\VMP.exe | executable | |
MD5:93DEFD130A2D1120BA367EE1134D4BEA | SHA256:424EF64FFB4335EA5AAAA9249292EC046D1848132E6FCED10EF94533E59DBAD3 | |||
| 1444 | VMP.exe | C:\Users\admin\Desktop\VMP.lnk | binary | |
MD5:AE0FEE3B897A740CFB047CACC769B07D | SHA256:7E41C0337CF0B43FF507CABCAE8E22FE1759BF29002FC9AE20D2C5B3CA435448 | |||
| 1016 | VMP.exe | C:\Users\admin\Desktop\VMPe.exe.new | executable | |
MD5:93DEFD130A2D1120BA367EE1134D4BEA | SHA256:424EF64FFB4335EA5AAAA9249292EC046D1848132E6FCED10EF94533E59DBAD3 | |||
| 4484 | VMP.exe | C:\Users\admin\AppData\Local\VMP\VMP.app\desktop.ini | ini | |
MD5:392C4286B61BDF0A8569A627ED044676 | SHA256:6A4064071DEB6207EBAD8B7B7259A4A702CAFAC6357405879350C333E1AFE1B1 | |||
| 4484 | VMP.exe | C:\Users\admin\AppData\Local\VMP\VMP.app\CitizenFX_SubProcess_ac.bin.tmp | executable | |
MD5:C3825276A035A1FFBFBE22ACB130D4C8 | SHA256:361595E306412F2B9B2DD4D6E66ABD605C3B8D7FD43F48208B512250FB80E8E1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
112
TCP/UDP connections
38
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5504 | svchost.exe | GET | 200 | 2.18.79.138:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | AT | binary | 1.01 Kb | unknown |
— | — | GET | 200 | 185.208.182.248:443 | https://cdn.vmp.ir/updates/heads/fivereborn/production?time=1716882518 | IR | text | 7 b | unknown |
5632 | RUXIMICS.exe | GET | 200 | 2.17.245.133:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 973 b | unknown |
5504 | svchost.exe | GET | 200 | 2.17.245.133:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 973 b | unknown |
— | — | GET | 200 | 185.208.182.249:443 | https://cdn.vmp.ir/updates/42/4e/424ef64ffb4335ea5aaaa9249292ec046d1848132e6fced10ef94533e59dbad3.xz | IR | xz | 1.80 Mb | unknown |
5632 | RUXIMICS.exe | GET | 200 | 2.18.79.138:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | AT | binary | 1.01 Kb | unknown |
— | — | GET | 200 | 185.208.182.248:443 | https://cdn.vmp.ir/updates/heads/fivereborn/production?time=1716882561 | IR | text | 7 b | unknown |
— | — | GET | 200 | 2.19.193.8:443 | https://www.bing.com/rb/18/jnc,nj/6hU_LneafI_NFLeDvM367ebFaKQ.js?bu=DyIrb3t-gQF4cnWyAbUBK6UBK7gB&or=w | unknown | s | 21.3 Kb | unknown |
— | — | GET | 200 | 185.208.182.250:443 | https://cdn.vmp.ir/updates/heads/fivereborn/production?time=1716882564 | IR | text | 7 b | unknown |
— | — | GET | 200 | 185.208.182.248:443 | https://cdn.vmp.ir/updates/bb/93/bb93672c0f60e1b8288a352eb121f22aa24e98b13a53a7e2ac9cf92eb23aa8d7 | IR | text | 96.6 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5504 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5632 | RUXIMICS.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5140 | MoUsoCoreWorker.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5140 | MoUsoCoreWorker.exe | 2.18.79.138:80 | crl.microsoft.com | Akamai International B.V. | AT | unknown |
— | — | 239.255.255.250:1900 | — | — | — | unknown |
5504 | svchost.exe | 2.18.79.138:80 | crl.microsoft.com | Akamai International B.V. | AT | unknown |
5632 | RUXIMICS.exe | 2.18.79.138:80 | crl.microsoft.com | Akamai International B.V. | AT | unknown |
5140 | MoUsoCoreWorker.exe | 2.17.245.133:80 | www.microsoft.com | Akamai International B.V. | NL | unknown |
1016 | VMP.exe | 185.208.182.250:443 | cdn.vmp.ir | Asre Pardazeshe Ettelaate Amin Institute | IR | unknown |
5632 | RUXIMICS.exe | 2.17.245.133:80 | www.microsoft.com | Akamai International B.V. | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
cdn.vmp.ir |
| unknown |
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
r.bing.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
VMP.exe | Dev mode : false
|
VMP.exe | Dev mode : false
|