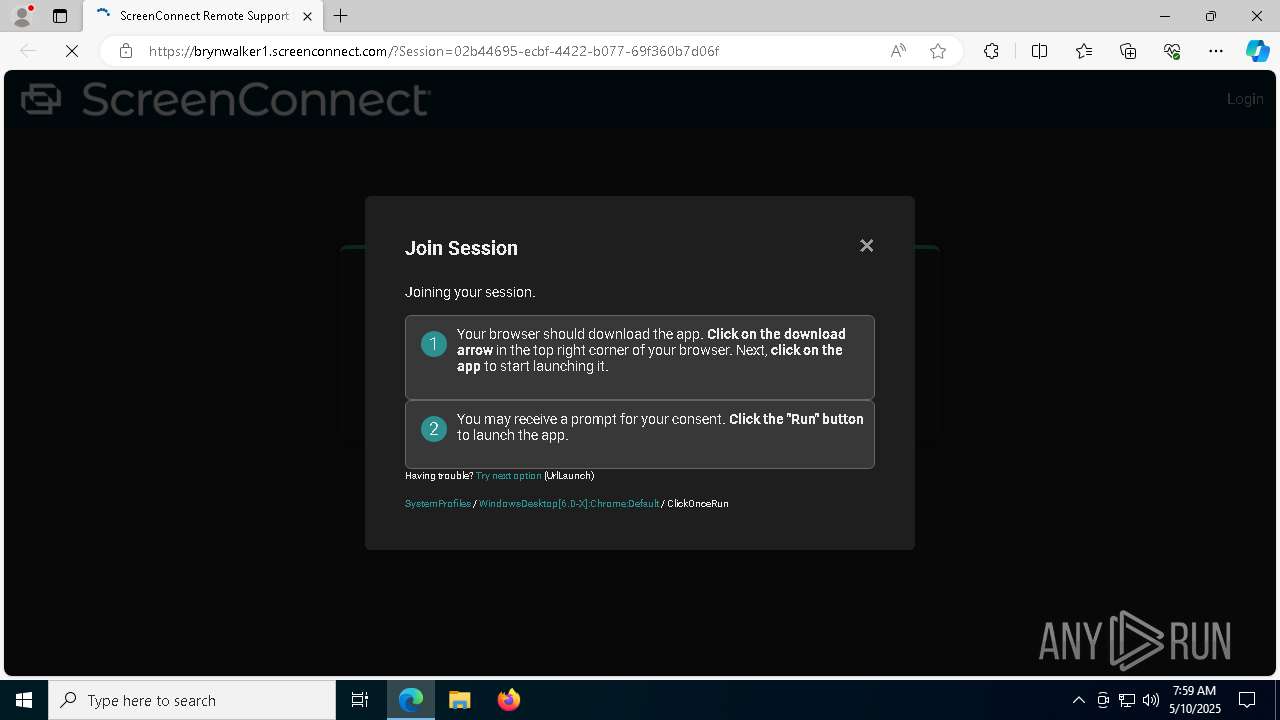
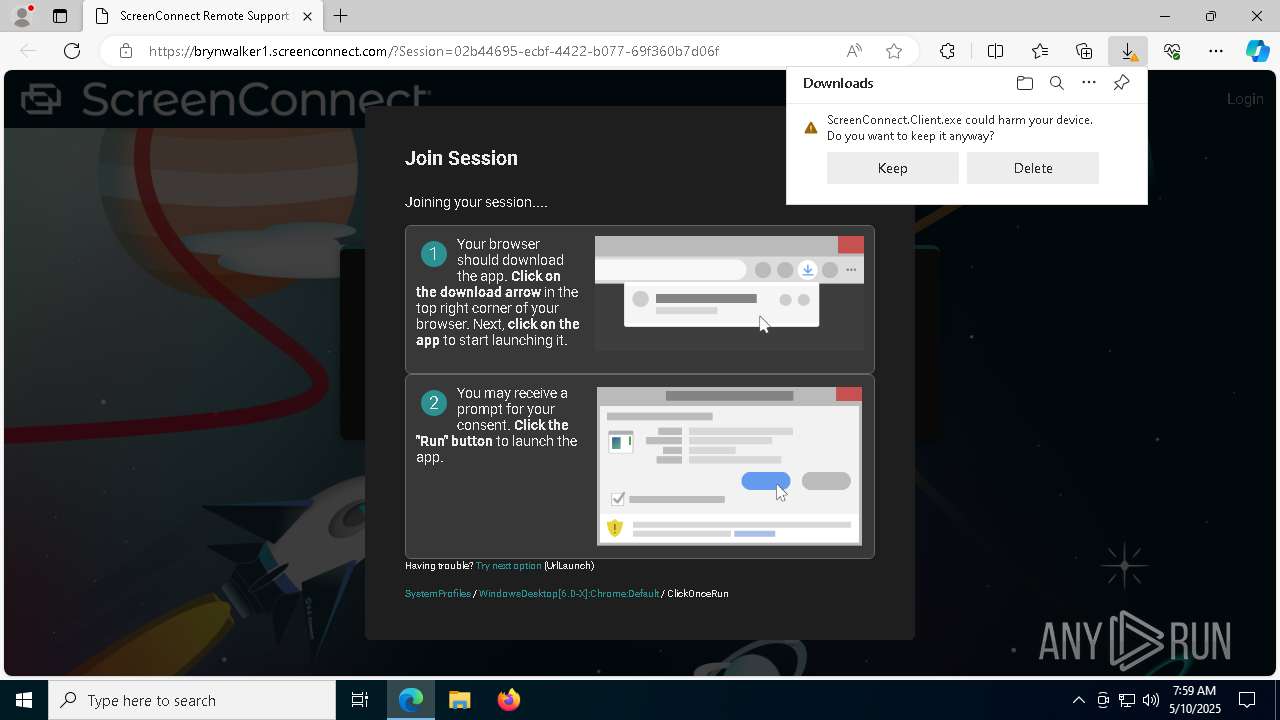
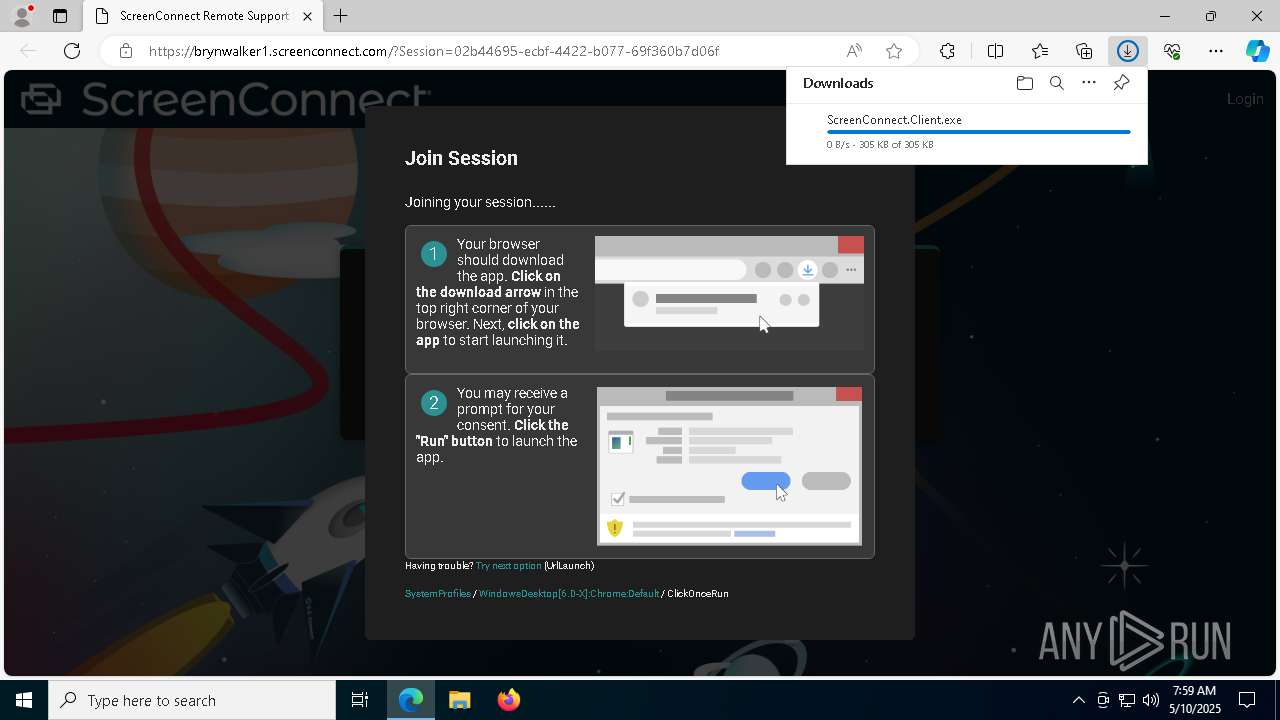
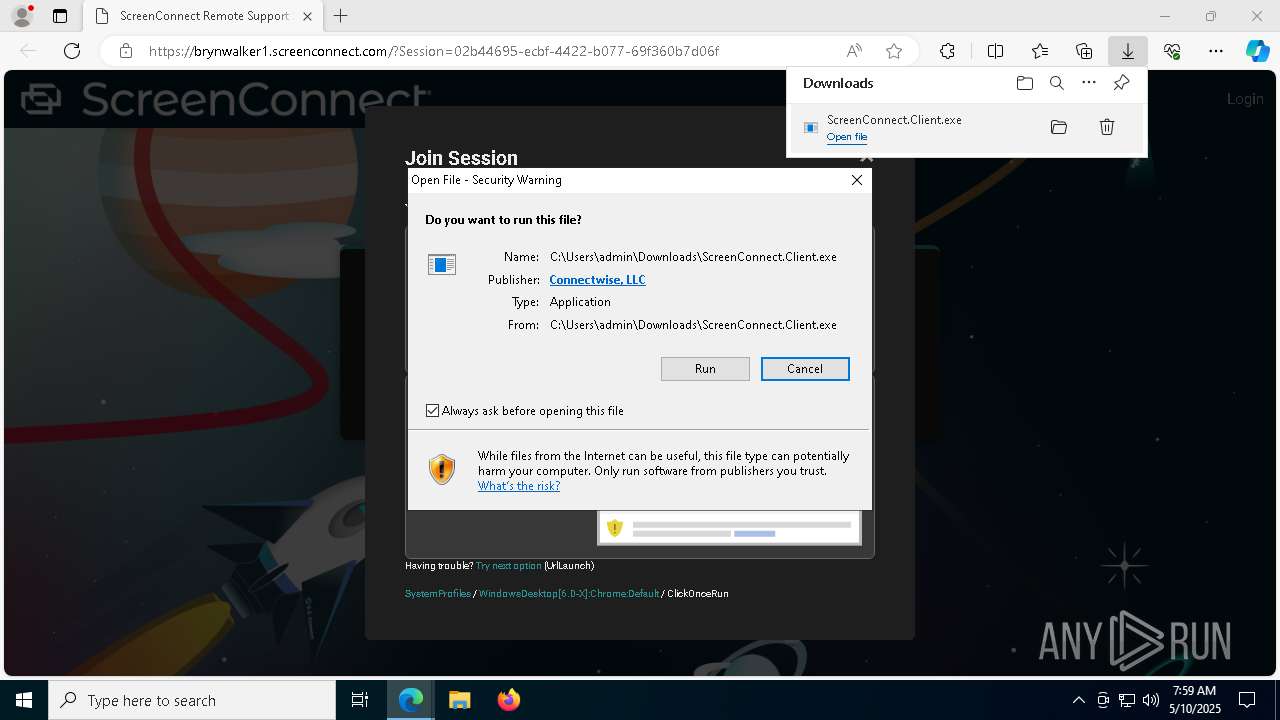
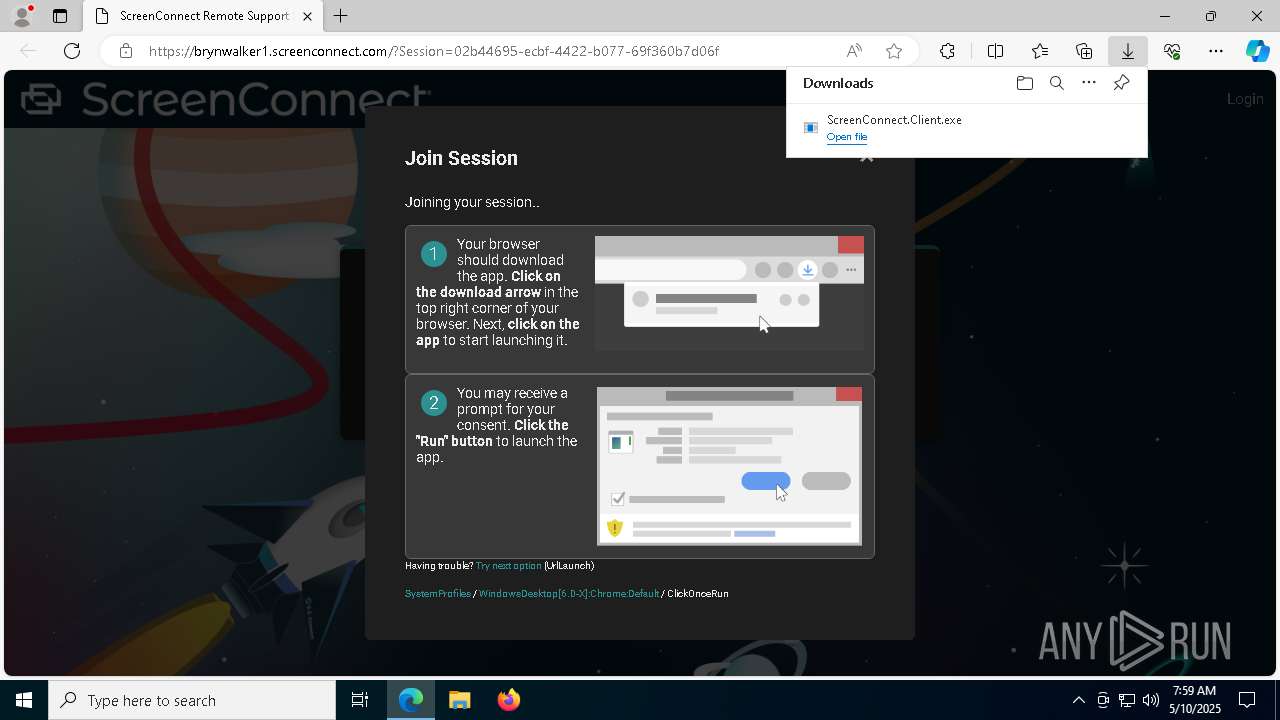
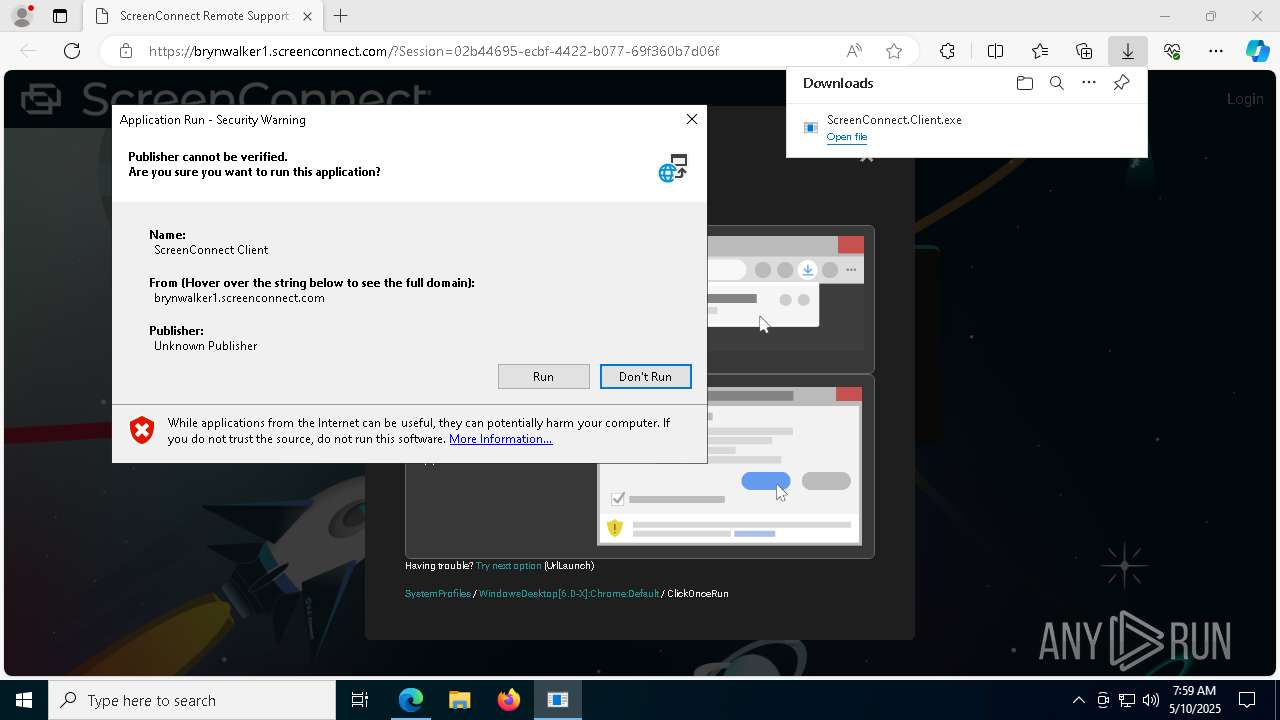
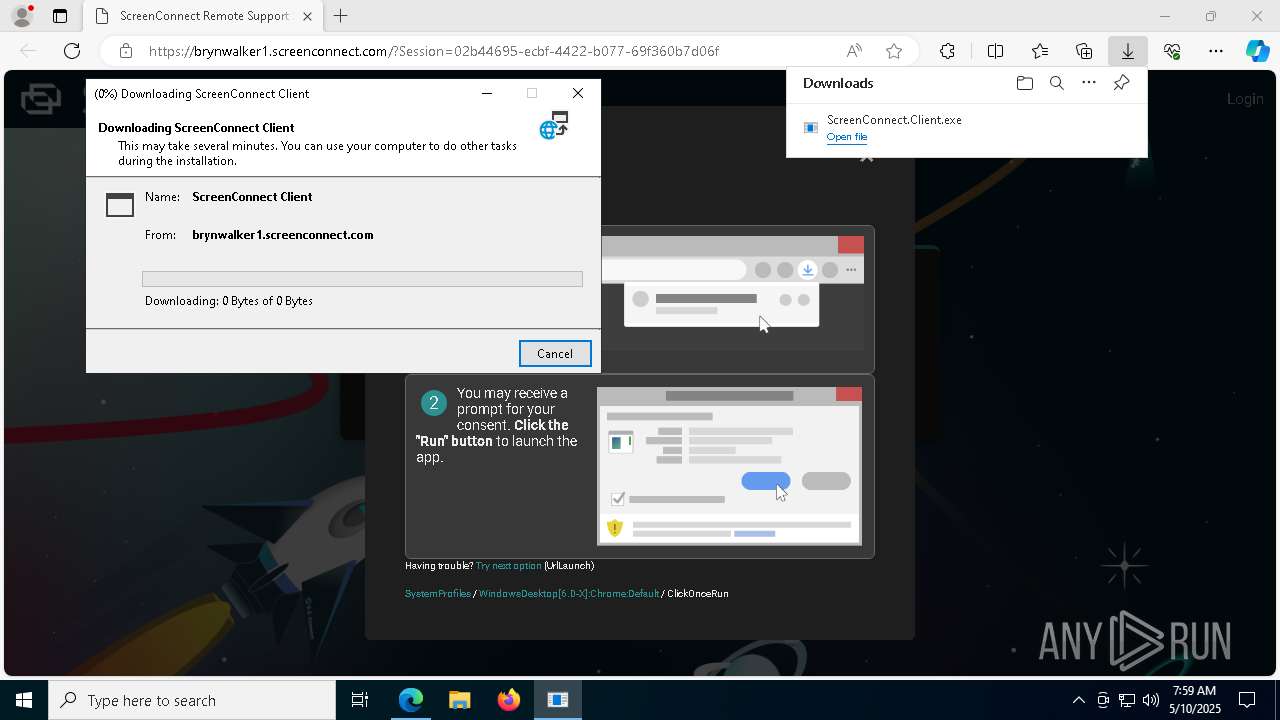
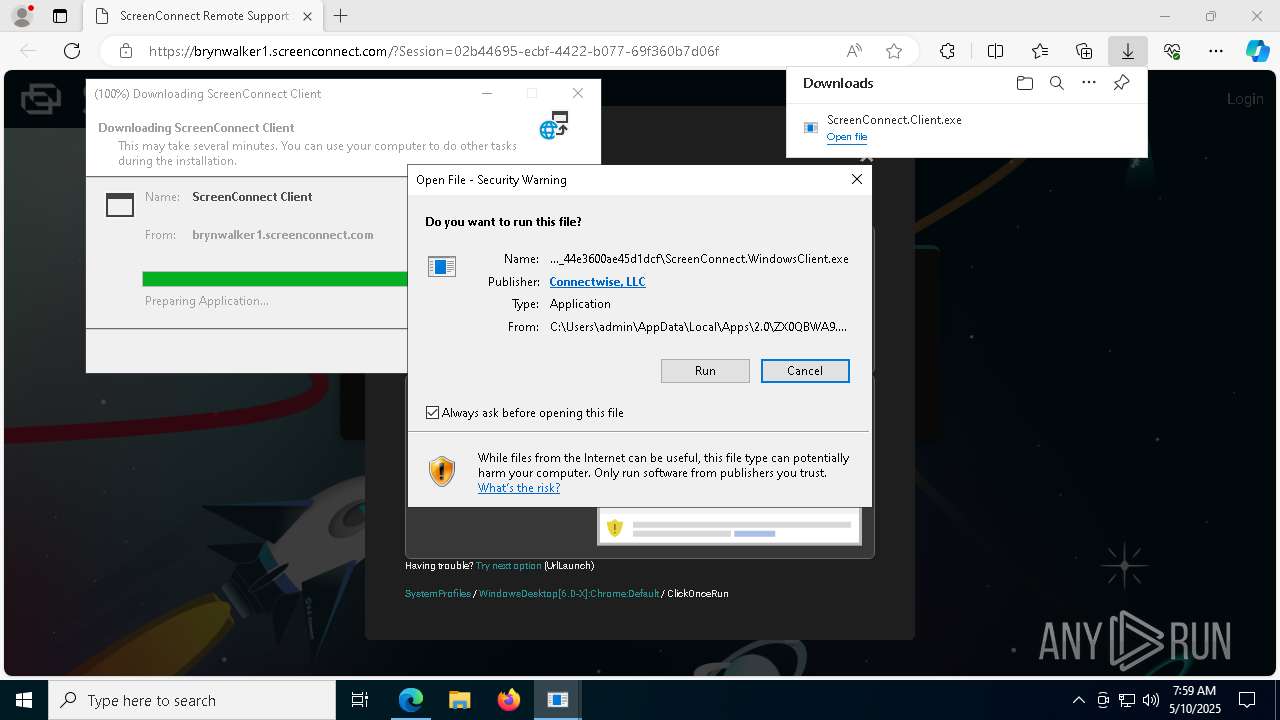
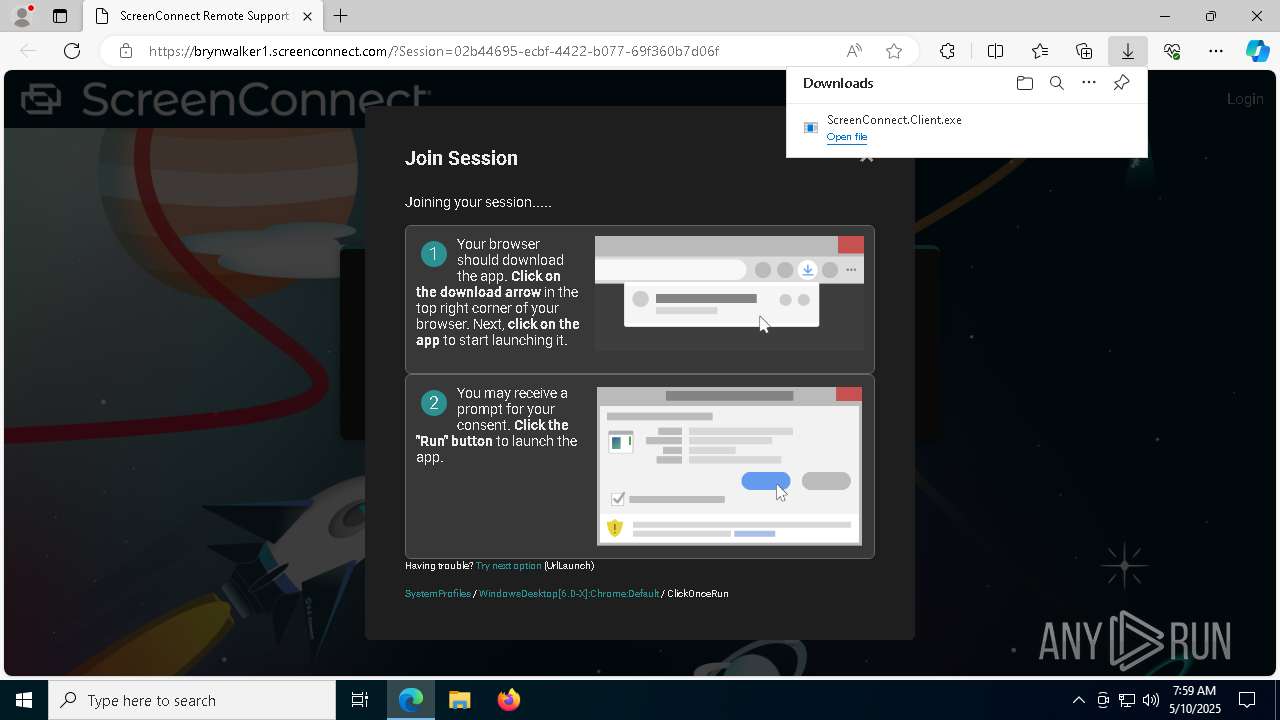
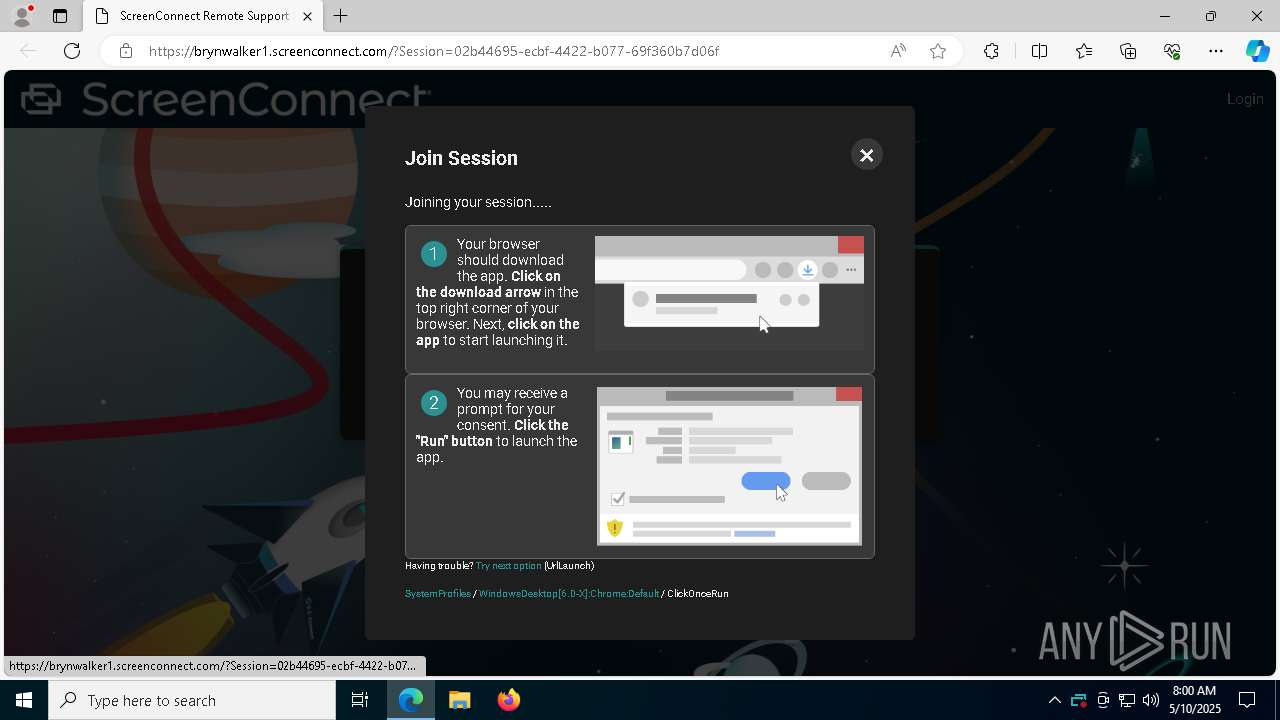
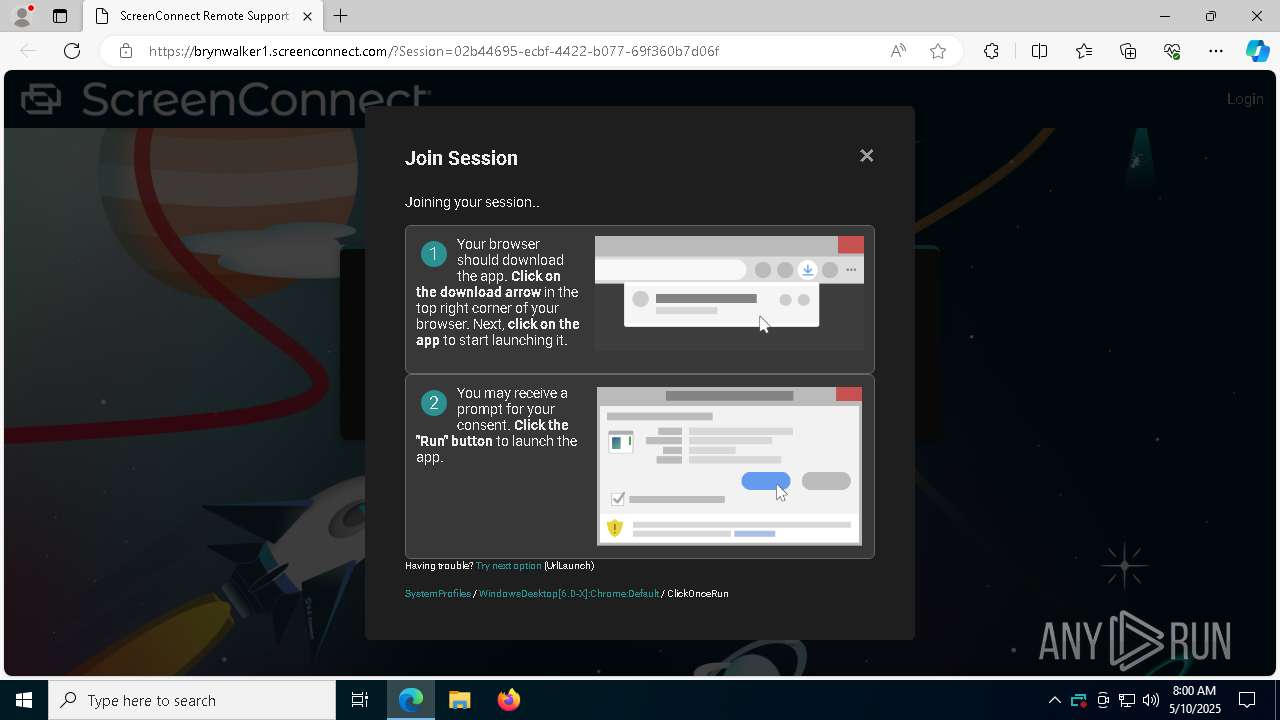
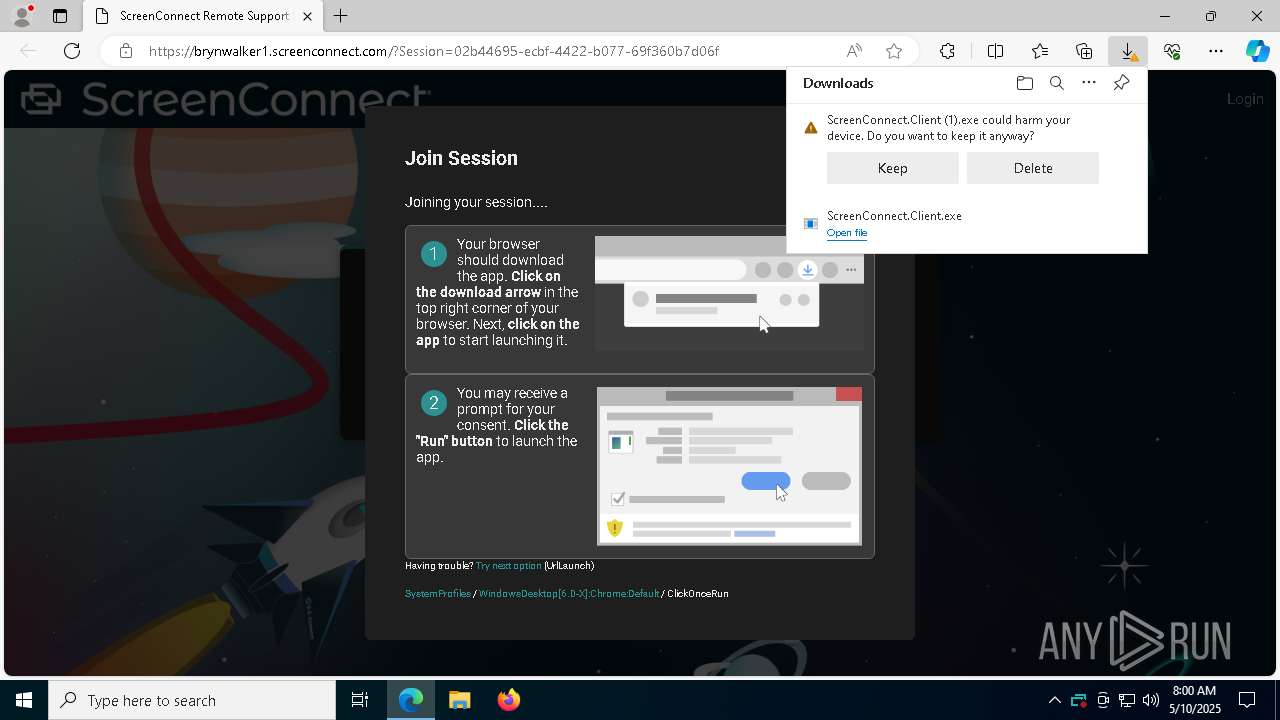
| URL: | https://brynwalker1.screenconnect.com/?Session=02b44695-ecbf-4422-b077-69f360b7d06f |
| Full analysis: | https://app.any.run/tasks/9c48db4e-0977-4789-a5cd-9517231fb9fe |
| Verdict: | Malicious activity |
| Analysis date: | May 10, 2025, 07:59:15 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 4887D5D96ADEB86A28420F01D7687D91 |
| SHA1: | FA14665CF889A33F1B9225A33D3F9708E742C835 |
| SHA256: | 1E139671E875512554B8F367FB9A4838346779F7AABAB9490519546C9AFDFDD4 |
| SSDEEP: | 3:N8Cgrd7GWW/axWQ9QDInX+SC1Dn:2J7GNaACQUno1D |
MALICIOUS
SCREENCONNECT has been detected (SURICATA)
- ScreenConnect.ClientService.exe (PID: 6244)
SUSPICIOUS
Adds/modifies Windows certificates
- ScreenConnect.Client.exe (PID: 8900)
- dfsvc.exe (PID: 8940)
Reads security settings of Internet Explorer
- dfsvc.exe (PID: 8940)
- ScreenConnect.WindowsClient.exe (PID: 6988)
- ScreenConnect.ClientService.exe (PID: 8476)
- ScreenConnect.ClientService.exe (PID: 6244)
- ScreenConnect.WindowsClient.exe (PID: 8444)
Reads Internet Explorer settings
- dfsvc.exe (PID: 8940)
Reads the date of Windows installation
- dfsvc.exe (PID: 8940)
- ScreenConnect.WindowsClient.exe (PID: 6988)
The process creates files with name similar to system file names
- dfsvc.exe (PID: 8940)
Executes as Windows Service
- ScreenConnect.ClientService.exe (PID: 6244)
Executable content was dropped or overwritten
- dfsvc.exe (PID: 8940)
Creates or modifies Windows services
- ScreenConnect.ClientService.exe (PID: 6244)
SCREENCONNECT mutex has been found
- ScreenConnect.ClientService.exe (PID: 6244)
Potential Corporate Privacy Violation
- ScreenConnect.ClientService.exe (PID: 6244)
Screenconnect has been detected
- ScreenConnect.ClientService.exe (PID: 6244)
INFO
Reads the computer name
- identity_helper.exe (PID: 7312)
- ScreenConnect.Client.exe (PID: 8900)
- dfsvc.exe (PID: 8940)
- ScreenConnect.ClientService.exe (PID: 6244)
- ScreenConnect.WindowsClient.exe (PID: 6988)
- ScreenConnect.ClientService.exe (PID: 8476)
- ScreenConnect.WindowsClient.exe (PID: 8444)
Application launched itself
- msedge.exe (PID: 7380)
Checks supported languages
- dfsvc.exe (PID: 8940)
- ScreenConnect.Client.exe (PID: 8900)
- identity_helper.exe (PID: 7312)
- ScreenConnect.WindowsClient.exe (PID: 6988)
- ScreenConnect.ClientService.exe (PID: 8476)
- ScreenConnect.ClientService.exe (PID: 6244)
- ScreenConnect.WindowsClient.exe (PID: 8444)
Executable content was dropped or overwritten
- msedge.exe (PID: 7676)
- msedge.exe (PID: 7380)
Disables trace logs
- dfsvc.exe (PID: 8940)
Reads Environment values
- identity_helper.exe (PID: 7312)
- dfsvc.exe (PID: 8940)
Reads the machine GUID from the registry
- ScreenConnect.Client.exe (PID: 8900)
- dfsvc.exe (PID: 8940)
- ScreenConnect.WindowsClient.exe (PID: 6988)
- ScreenConnect.ClientService.exe (PID: 8476)
- ScreenConnect.WindowsClient.exe (PID: 8444)
- ScreenConnect.ClientService.exe (PID: 6244)
Create files in a temporary directory
- dfsvc.exe (PID: 8940)
Creates files or folders in the user directory
- dfsvc.exe (PID: 8940)
- ScreenConnect.WindowsClient.exe (PID: 6988)
- ScreenConnect.ClientService.exe (PID: 6244)
Process checks whether UAC notifications are on
- dfsvc.exe (PID: 8940)
Checks proxy server information
- dfsvc.exe (PID: 8940)
Reads the software policy settings
- dfsvc.exe (PID: 8940)
- slui.exe (PID: 960)
Process checks computer location settings
- ScreenConnect.WindowsClient.exe (PID: 6988)
- dfsvc.exe (PID: 8940)
SCREENCONNECT has been detected
- ScreenConnect.ClientService.exe (PID: 6244)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
181
Monitored processes
49
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 616 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --no-appcompat-clear --mojo-platform-channel-handle=5720 --field-trial-handle=2296,i,9913310715960472410,2609670642453920012,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 728 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6728 --field-trial-handle=2296,i,9913310715960472410,2609670642453920012,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 960 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2136 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6324 --field-trial-handle=2296,i,9913310715960472410,2609670642453920012,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2284 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_xpay_wallet.mojom.EdgeXPayWalletService --lang=en-US --service-sandbox-type=utility --no-appcompat-clear --mojo-platform-channel-handle=4940 --field-trial-handle=2296,i,9913310715960472410,2609670642453920012,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2384 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --onnx-enabled-for-ee --no-appcompat-clear --mojo-platform-channel-handle=4948 --field-trial-handle=2296,i,9913310715960472410,2609670642453920012,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2616 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6404 --field-trial-handle=2296,i,9913310715960472410,2609670642453920012,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4068 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --message-loop-type-ui --no-appcompat-clear --mojo-platform-channel-handle=1720 --field-trial-handle=2296,i,9913310715960472410,2609670642453920012,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4120 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4776 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4476 --field-trial-handle=2296,i,9913310715960472410,2609670642453920012,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
17 647
Read events
17 423
Write events
192
Delete events
32
Modification events
| (PID) Process: | (7380) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7380) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7380) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7380) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7380) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 2BA54DBE59932F00 | |||
| (PID) Process: | (7380) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: D0EA61BE59932F00 | |||
| (PID) Process: | (7380) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197214 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {06E3C1B1-41AC-4718-8432-CC2FA466FE3B} | |||
| (PID) Process: | (7380) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197214 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {65C51273-8111-4A1D-84F5-94E1021B2CC0} | |||
| (PID) Process: | (7380) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197214 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {F482EB01-1504-4EC2-AB12-4AF5A2B1F65F} | |||
| (PID) Process: | (7380) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197214 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {B6256AED-98C4-4639-BCAA-FFD5AC761705} | |||
Executable files
33
Suspicious files
267
Text files
62
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7380 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b095.TMP | — | |
MD5:— | SHA256:— | |||
| 7380 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b095.TMP | — | |
MD5:— | SHA256:— | |||
| 7380 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b095.TMP | — | |
MD5:— | SHA256:— | |||
| 7380 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7380 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7380 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7380 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b085.TMP | — | |
MD5:— | SHA256:— | |||
| 7380 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7380 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b095.TMP | — | |
MD5:— | SHA256:— | |||
| 7380 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
75
DNS requests
65
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 868 b | whitelisted |
7380 | msedge.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | DE | binary | 471 b | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
9116 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | QA | binary | 419 b | whitelisted |
6576 | svchost.exe | GET | 206 | 208.89.74.21:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1747346562&P2=404&P3=2&P4=CDaqTRPd2VrZ%2bCtJpXrke7qXG4fnvXz0S36nQYDkjriXaLAId7TLKAdTtomPvDdSte6KxSav0BdGX7aKBXcMrA%3d%3d | US | binary | 1.33 Kb | whitelisted |
9116 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | QA | binary | 407 b | whitelisted |
7380 | msedge.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAuTYAUbzPZmQpmJmNW6l84%3D | DE | binary | 727 b | whitelisted |
6576 | svchost.exe | HEAD | 200 | 208.89.74.21:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1747346562&P2=404&P3=2&P4=CDaqTRPd2VrZ%2bCtJpXrke7qXG4fnvXz0S36nQYDkjriXaLAId7TLKAdTtomPvDdSte6KxSav0BdGX7aKBXcMrA%3d%3d | US | — | — | whitelisted |
7380 | msedge.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | DE | binary | 727 b | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7380 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7676 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7676 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7676 | msedge.exe | 147.75.50.206:443 | brynwalker1.screenconnect.com | PACKET | CA | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
brynwalker1.screenconnect.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7676 | msedge.exe | Misc activity | ET REMOTE_ACCESS Observed DNS Query to Known ScreenConnect/ConnectWise Remote Desktop Service Domain |
7676 | msedge.exe | Misc activity | ET REMOTE_ACCESS Observed DNS Query to Known ScreenConnect/ConnectWise Remote Desktop Service Domain |
7676 | msedge.exe | Misc activity | ET REMOTE_ACCESS Observed DNS Query to Known ScreenConnect/ConnectWise Remote Desktop Service Domain |
7676 | msedge.exe | Misc activity | ET REMOTE_ACCESS Observed DNS Query to Known ScreenConnect/ConnectWise Remote Desktop Service Domain |
7676 | msedge.exe | Misc activity | ET REMOTE_ACCESS Observed DNS Query to Known ScreenConnect/ConnectWise Remote Desktop Service Domain |
7676 | msedge.exe | Misc activity | ET REMOTE_ACCESS Observed DNS Query to Known ScreenConnect/ConnectWise Remote Desktop Service Domain |
7676 | msedge.exe | Misc activity | ET REMOTE_ACCESS Observed DNS Query to Known ScreenConnect/ConnectWise Remote Desktop Service Domain |
7676 | msedge.exe | Misc activity | ET REMOTE_ACCESS Observed DNS Query to Known ScreenConnect/ConnectWise Remote Desktop Service Domain |
2196 | svchost.exe | Misc activity | ET REMOTE_ACCESS Observed DNS Query to Known ScreenConnect/ConnectWise Remote Desktop Service Domain |
2196 | svchost.exe | Misc activity | ET REMOTE_ACCESS Observed DNS Query to Known ScreenConnect/ConnectWise Remote Desktop Service Domain |