| File name: | Ratool.exe |
| Full analysis: | https://app.any.run/tasks/b6c315a4-77b1-4164-85b6-864ca308eb65 |
| Verdict: | Malicious activity |
| Analysis date: | July 16, 2020, 10:42:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 9C67C0C65B1E045662CBE9ADE83742E7 |
| SHA1: | BEBE8C2A2BC0EB74D18FF2E82987303C49A81E20 |
| SHA256: | 1E0E51061A67E15197B2BD1B47CA08C88809FC25F843D40503940713A142CC3F |
| SSDEEP: | 12288:naWzgMg7v3qnCidErQohh0F4kCJ8lny+QAkOhzL2xLJ9G/x4kCq6Z3:aaHMv6Clrjcny+Q9O5yxe/x4kN6Z3 |
MALICIOUS
No malicious indicators.SUSPICIOUS
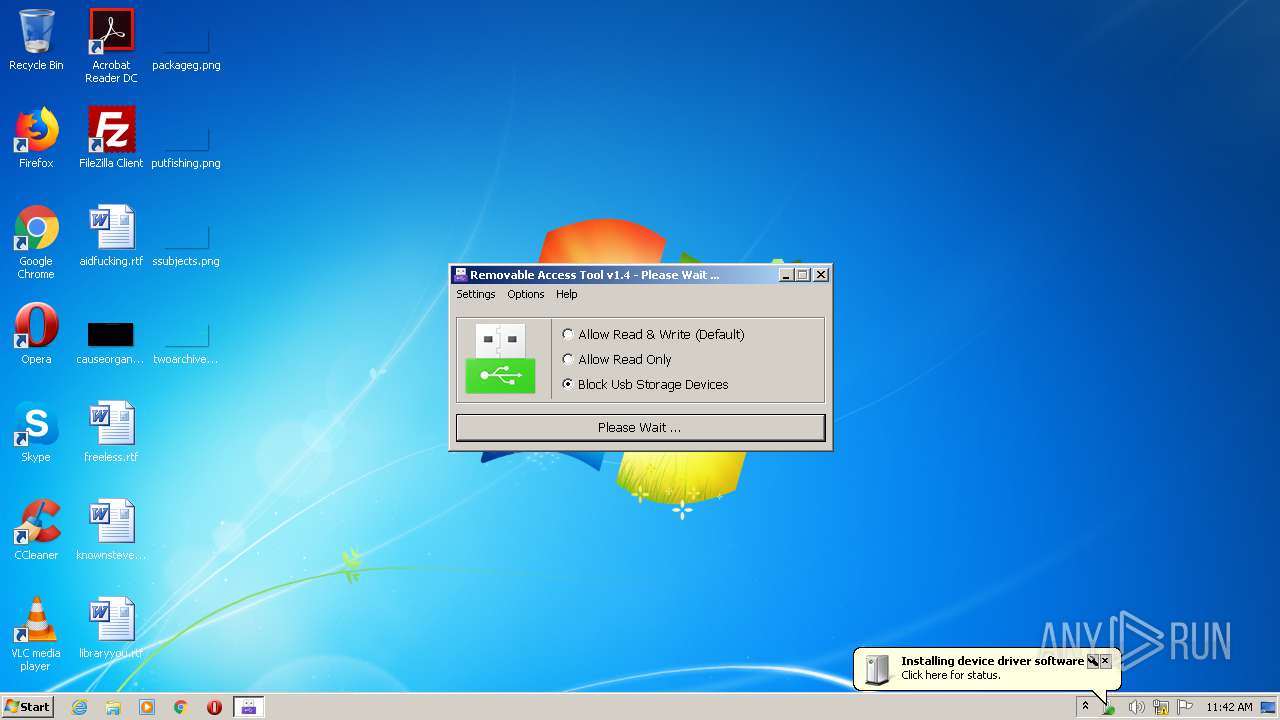
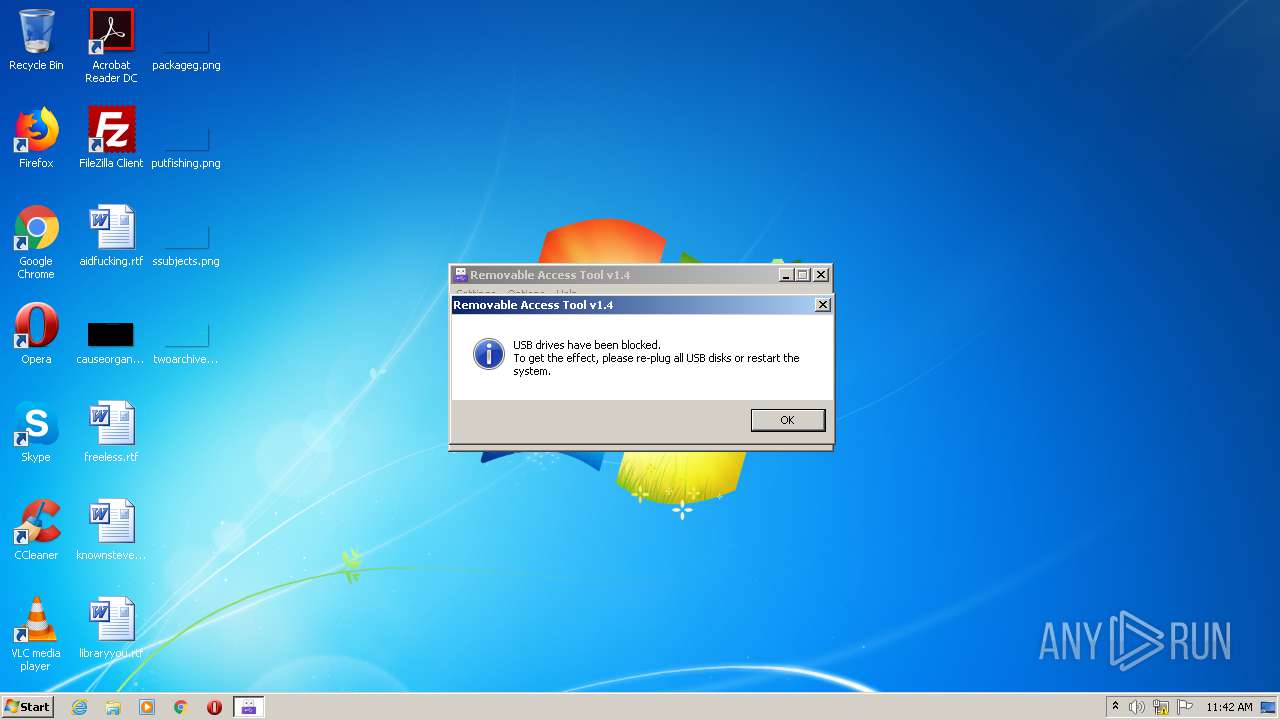
Creates or modifies windows services
- Ratool.exe (PID: 2976)
Executed via COM
- rundll32.exe (PID: 548)
- rundll32.exe (PID: 3076)
- DrvInst.exe (PID: 3144)
- DrvInst.exe (PID: 2488)
Creates files in the Windows directory
- Ratool.exe (PID: 2976)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:04:16 09:47:33+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 524800 |
| InitializedDataSize: | 195584 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x16310 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.4.0.0 |
| ProductVersionNumber: | 1.4.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
| FileVersion: | 1.4.0.0 |
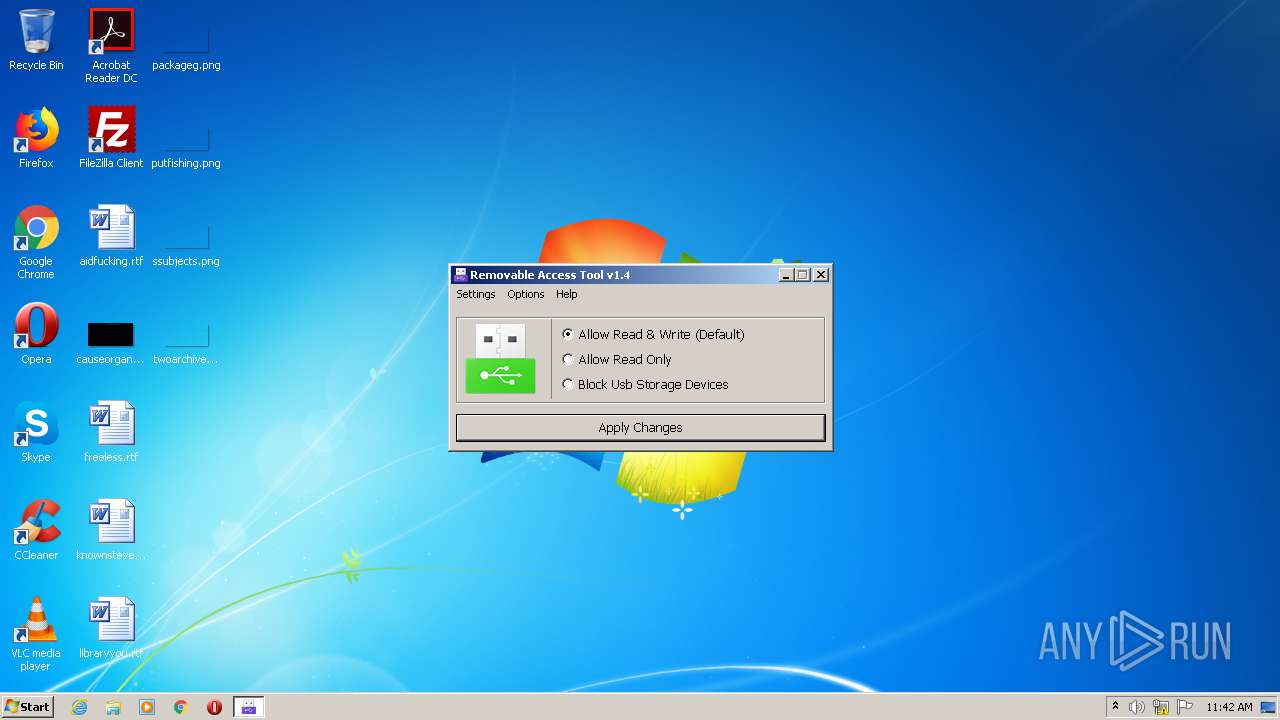
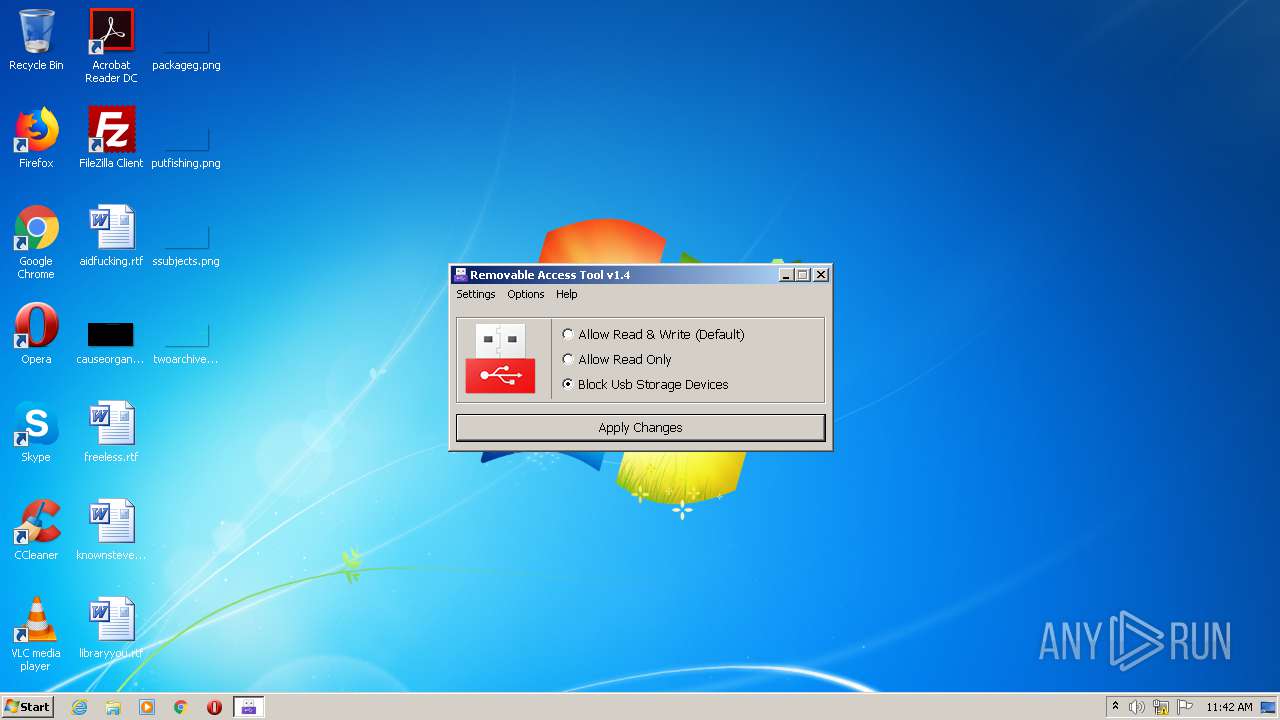
| Comments: | Block Usb Storage Devices |
| FileDescription: | Removable Access Tool |
| LegalCopyright: | Copyright © 2013 - 2020 www.sordum.org All Rights Reserved. |
| CompanyName: | www.sordum.org |
| ProductVersion: | 1.4.0.0 |
| OriginalFileName: | Ratool.exe |
| Coder: | By BlueLife |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 16-Apr-2010 07:47:33 |
| Detected languages: |
|
| FileVersion: | 1.4.0.0 |
| Comments: | Block Usb Storage Devices |
| FileDescription: | Removable Access Tool |
| LegalCopyright: | Copyright © 2013 - 2020 www.sordum.org All Rights Reserved. |
| CompanyName: | www.sordum.org |
| ProductVersion: | 1.4.0.0 |
| OriginalFilename: | Ratool.exe |
| Coder: | By BlueLife |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 16-Apr-2010 07:47:33 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00080017 | 0x00080200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.63487 |
.rdata | 0x00082000 | 0x0000D95C | 0x0000DA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.86682 |
.data | 0x00090000 | 0x0001A518 | 0x00006800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.20213 |
.rsrc | 0x000AB000 | 0x0001B804 | 0x0001BA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.74191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25292 | 1182 | Latin 1 / Western European | English - United Kingdom | RT_MANIFEST |
2 | 3.41079 | 594 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
3 | 3.33032 | 1188 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
4 | 3.38743 | 638 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
5 | 5.17703 | 9640 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
6 | 5.4223 | 4264 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
13 | 0.916632 | 176 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
14 | 5.79192 | 1128 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
50 | 4.57188 | 1128 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
99 | 2.50899 | 62 | Latin 1 / Western European | English - United Kingdom | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
KERNEL32.dll |
MPR.dll |
OLEAUT32.dll |
PSAPI.DLL |
SHELL32.dll |
USER32.dll |
Total processes
44
Monitored processes
7
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 548 | C:\Windows\System32\rundll32.exe shell32.dll,SHCreateLocalServerRunDll {995C996E-D918-4a8c-A302-45719A6F4EA7} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2144 | "C:\Users\admin\AppData\Local\Temp\Ratool.exe" | C:\Users\admin\AppData\Local\Temp\Ratool.exe | — | explorer.exe | |||||||||||
User: admin Company: www.sordum.org Integrity Level: MEDIUM Description: Removable Access Tool Exit code: 3221226540 Version: 1.4.0.0 Modules
| |||||||||||||||
| 2488 | DrvInst.exe "1" "200" "SCSI\Disk&Ven_Msft&Prod_Virtual_Disk\2&1f4adffe&0&000001" "" "" "69911eaf3" "00000000" "00000544" "0000060C" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2976 | "C:\Users\admin\AppData\Local\Temp\Ratool.exe" | C:\Users\admin\AppData\Local\Temp\Ratool.exe | explorer.exe | ||||||||||||
User: admin Company: www.sordum.org Integrity Level: HIGH Description: Removable Access Tool Exit code: 0 Version: 1.4.0.0 Modules
| |||||||||||||||
| 3076 | rundll32.exe C:\Windows\system32\newdev.dll,pDiDeviceInstallNotification \\.\pipe\PNP_Device_Install_Pipe_1.{5d9d0e2c-5780-480c-8b7c-644d1b453514} "(null)" | C:\Windows\system32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3144 | DrvInst.exe "1" "200" "{8e7bd593-6e6c-4c52-86a6-77175494dd8e}\MsVhdHba\1&3030e83&0&01" "" "" "66583b687" "00000000" "000005D4" "000004BC" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3772 | "C:\Windows\System32\dinotify.exe" pnpui.dll,SimplifiedDINotification | C:\Windows\System32\dinotify.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Device Installation Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
164
Read events
115
Write events
49
Delete events
0
Modification events
| (PID) Process: | (2976) Ratool.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\USBSTOR |
| Operation: | write | Name: | Start |
Value: 4 | |||
| (PID) Process: | (2976) Ratool.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet002\services\USBSTOR |
| Operation: | write | Name: | Start |
Value: 4 | |||
| (PID) Process: | (2976) Ratool.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\StorageDevicePolicies |
| Operation: | write | Name: | WriteProtect |
Value: 1 | |||
| (PID) Process: | (2976) Ratool.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet002\Control\StorageDevicePolicies |
| Operation: | write | Name: | WriteProtect |
Value: 1 | |||
| (PID) Process: | (2976) Ratool.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\RemovableStorageDevices\{53f5630d-b6bf-11d0-94f2-00a0c91efb8b} |
| Operation: | write | Name: | Deny_All |
Value: 1 | |||
| (PID) Process: | (2976) Ratool.exe | Key: | HKEY_CURRENT_USER\Software\Policies\Microsoft\Windows\RemovableStorageDevices\{53f5630d-b6bf-11d0-94f2-00a0c91efb8b} |
| Operation: | write | Name: | Deny_All |
Value: 1 | |||
| (PID) Process: | (2976) Ratool.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\RemovableStorageDevices\{53f5630d-b6bf-11d0-94f2-00a0c91efb8b} |
| Operation: | write | Name: | Deny_Read |
Value: 1 | |||
| (PID) Process: | (2976) Ratool.exe | Key: | HKEY_CURRENT_USER\Software\Policies\Microsoft\Windows\RemovableStorageDevices\{53f5630d-b6bf-11d0-94f2-00a0c91efb8b} |
| Operation: | write | Name: | Deny_Read |
Value: 1 | |||
| (PID) Process: | (2976) Ratool.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\RemovableStorageDevices\{53f5630d-b6bf-11d0-94f2-00a0c91efb8b} |
| Operation: | write | Name: | Deny_Write |
Value: 1 | |||
| (PID) Process: | (2976) Ratool.exe | Key: | HKEY_CURRENT_USER\Software\Policies\Microsoft\Windows\RemovableStorageDevices\{53f5630d-b6bf-11d0-94f2-00a0c91efb8b} |
| Operation: | write | Name: | Deny_Write |
Value: 1 | |||
Executable files
0
Suspicious files
9
Text files
91
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2976 | Ratool.exe | C:\Users\admin\AppData\Local\Temp\autE26.tmp | — | |
MD5:— | SHA256:— | |||
| 2976 | Ratool.exe | C:\Users\admin\AppData\Local\Temp\acfhkvy | — | |
MD5:— | SHA256:— | |||
| 3144 | DrvInst.exe | C:\Windows\INF\setupapi.dev.log | ini | |
MD5:— | SHA256:— | |||
| 2976 | Ratool.exe | C:\Windows\System32\GroupPolicy\Machine\Registry.pol | binary | |
MD5:— | SHA256:— | |||
| 3144 | DrvInst.exe | C:\Windows\INF\setupapi.ev3 | binary | |
MD5:— | SHA256:— | |||
| 2976 | Ratool.exe | C:\Windows\System32\GroupPolicy\User\Registry.pol | binary | |
MD5:— | SHA256:— | |||
| 3144 | DrvInst.exe | C:\Windows\INF\setupapi.ev1 | binary | |
MD5:— | SHA256:— | |||
| 3144 | DrvInst.exe | C:\Windows\System32\DriverStore\FileRepository\vhdmp.inf_x86_neutral_efa659e9a38d5b8c\vhdmp.PNF | pnf | |
MD5:— | SHA256:— | |||
| 3144 | DrvInst.exe | C:\Windows\INF\setupapi.ev2 | binary | |
MD5:— | SHA256:— | |||
| 2976 | Ratool.exe | C:\Users\admin\AppData\Local\Temp\Ratool.ini | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report