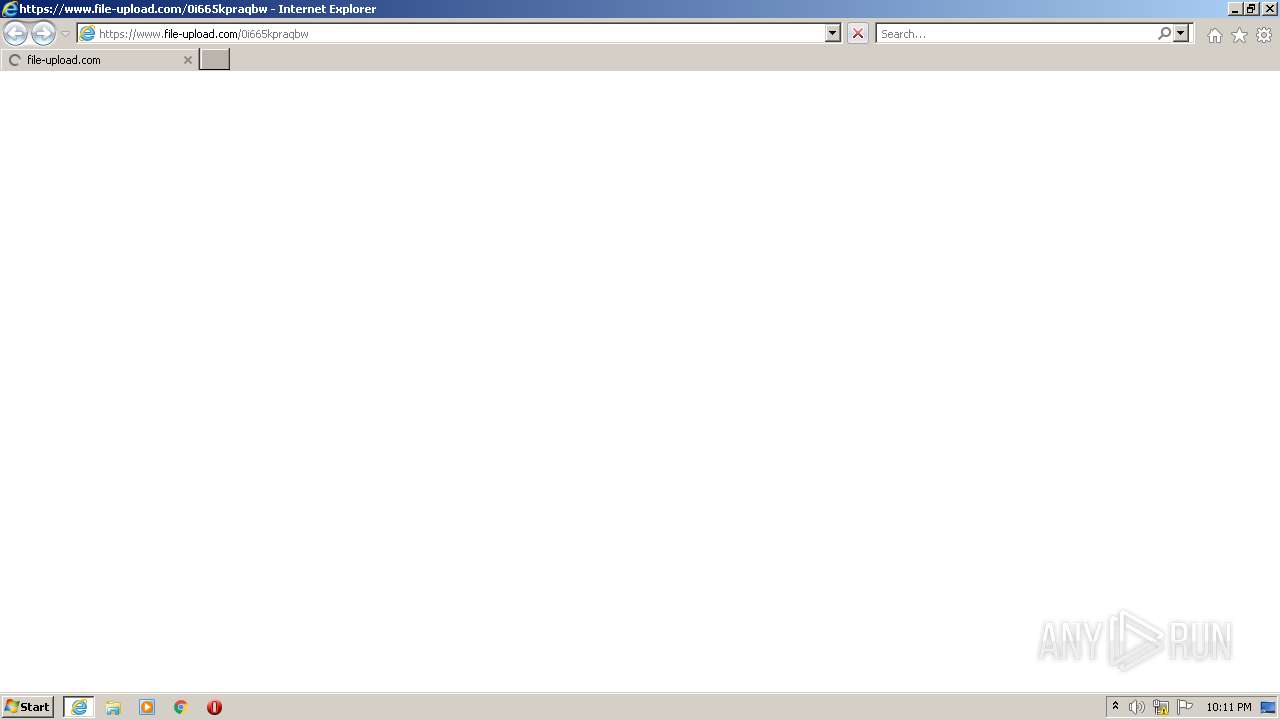
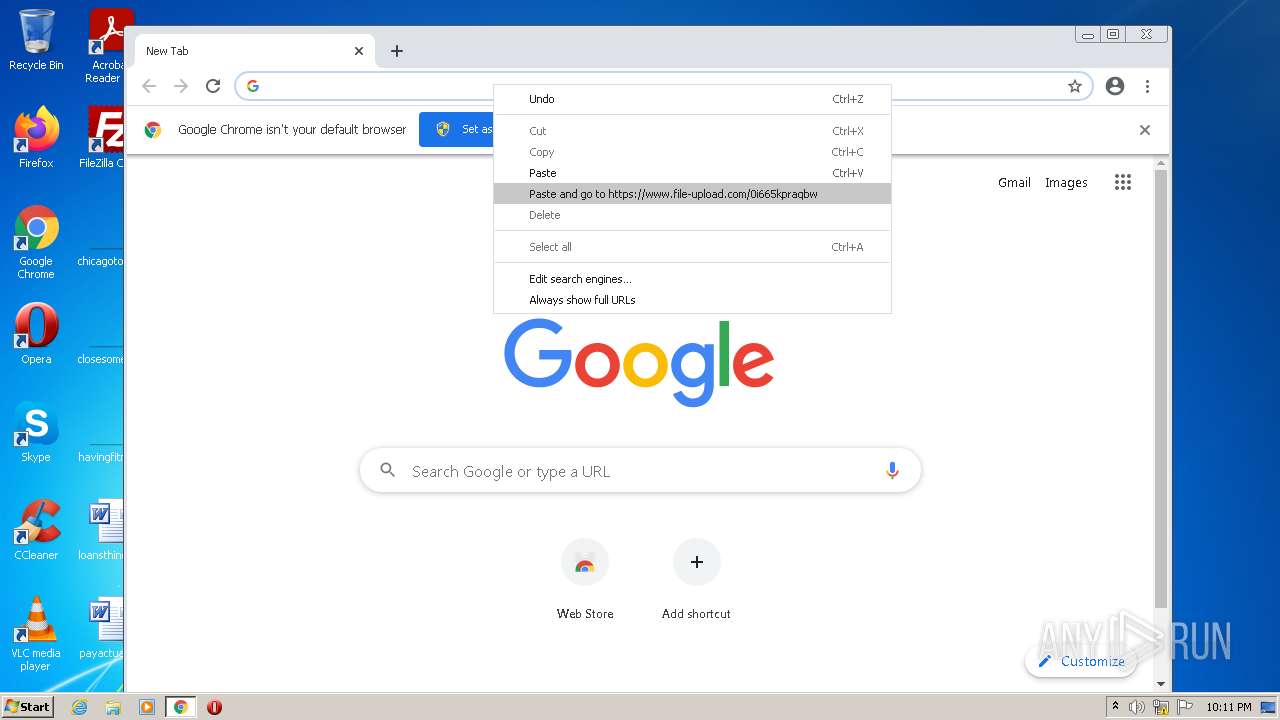
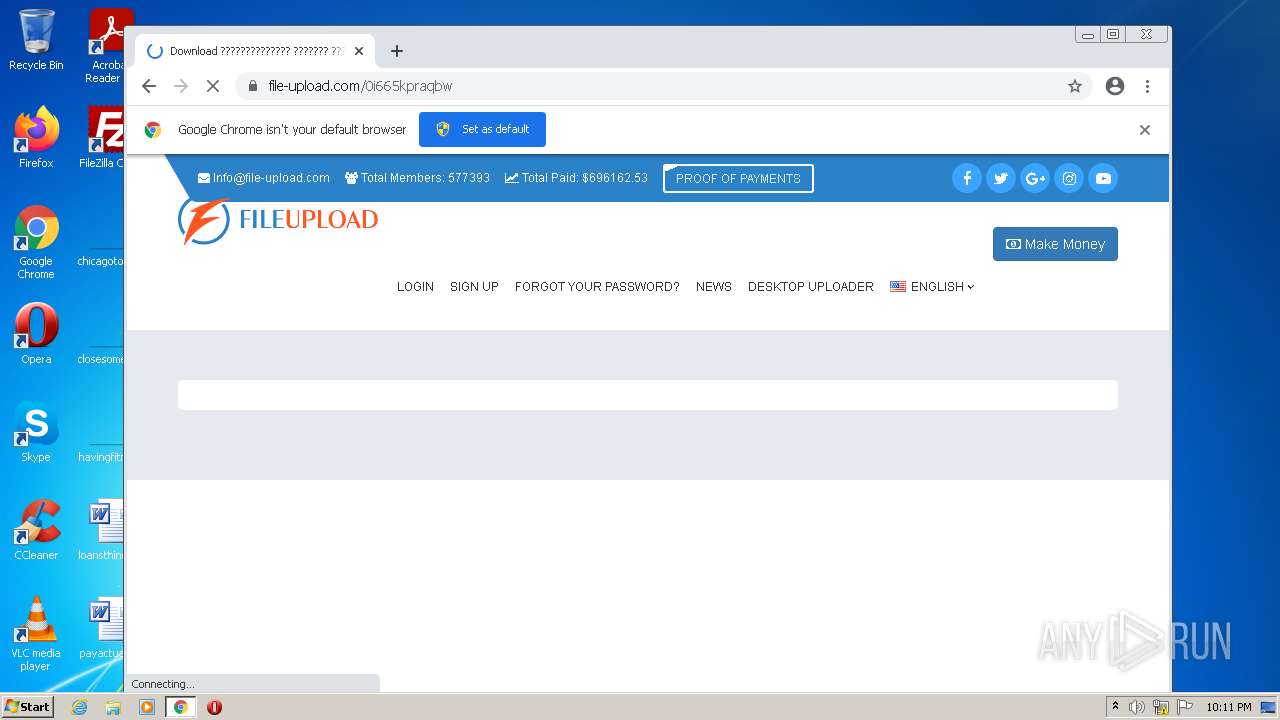
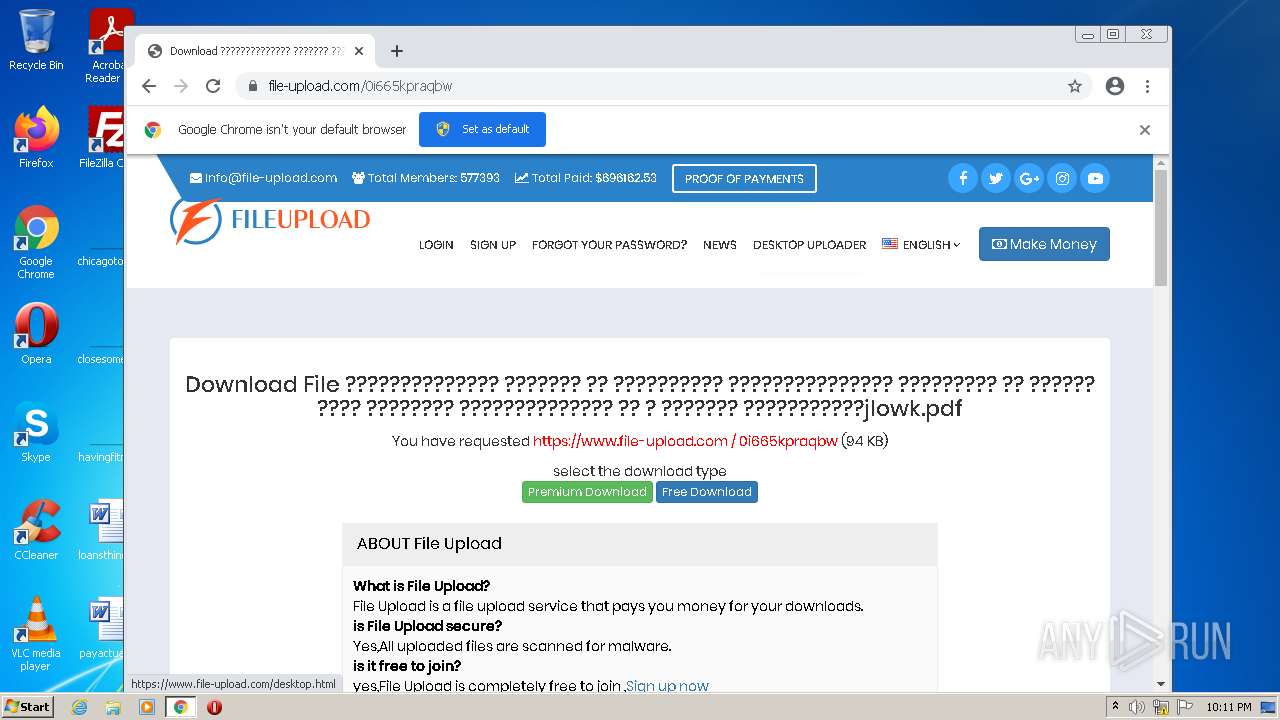
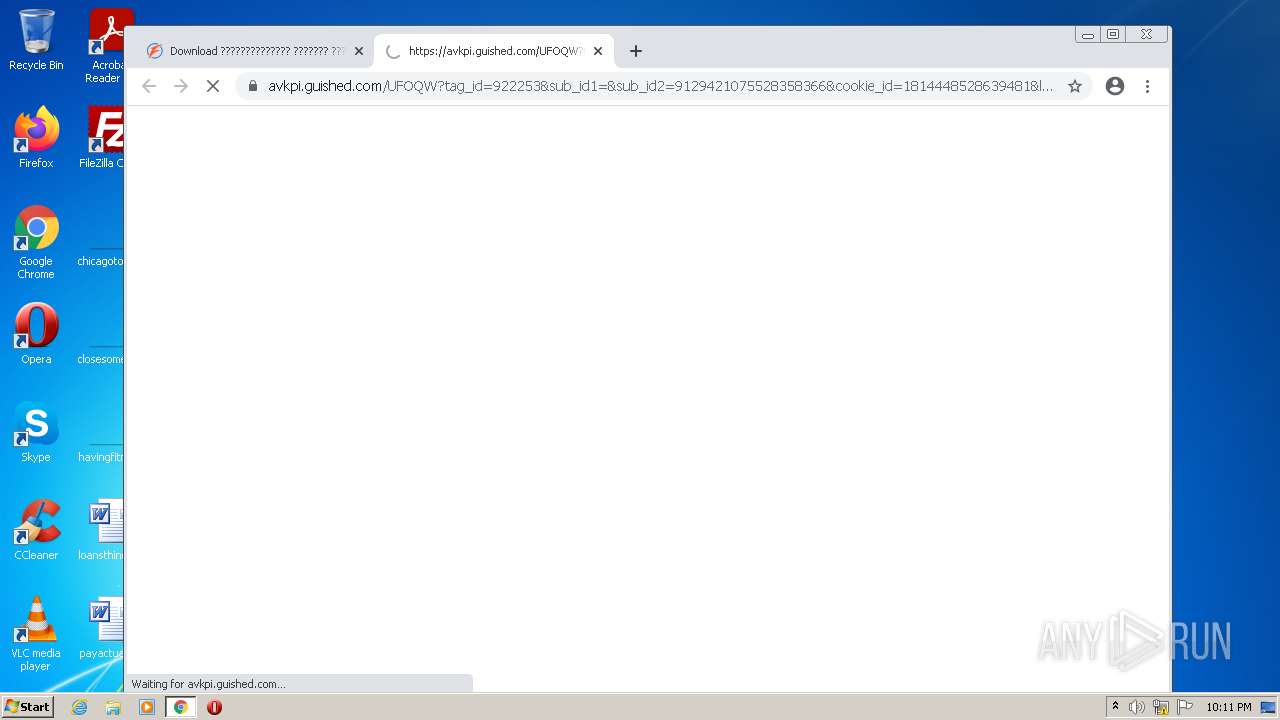
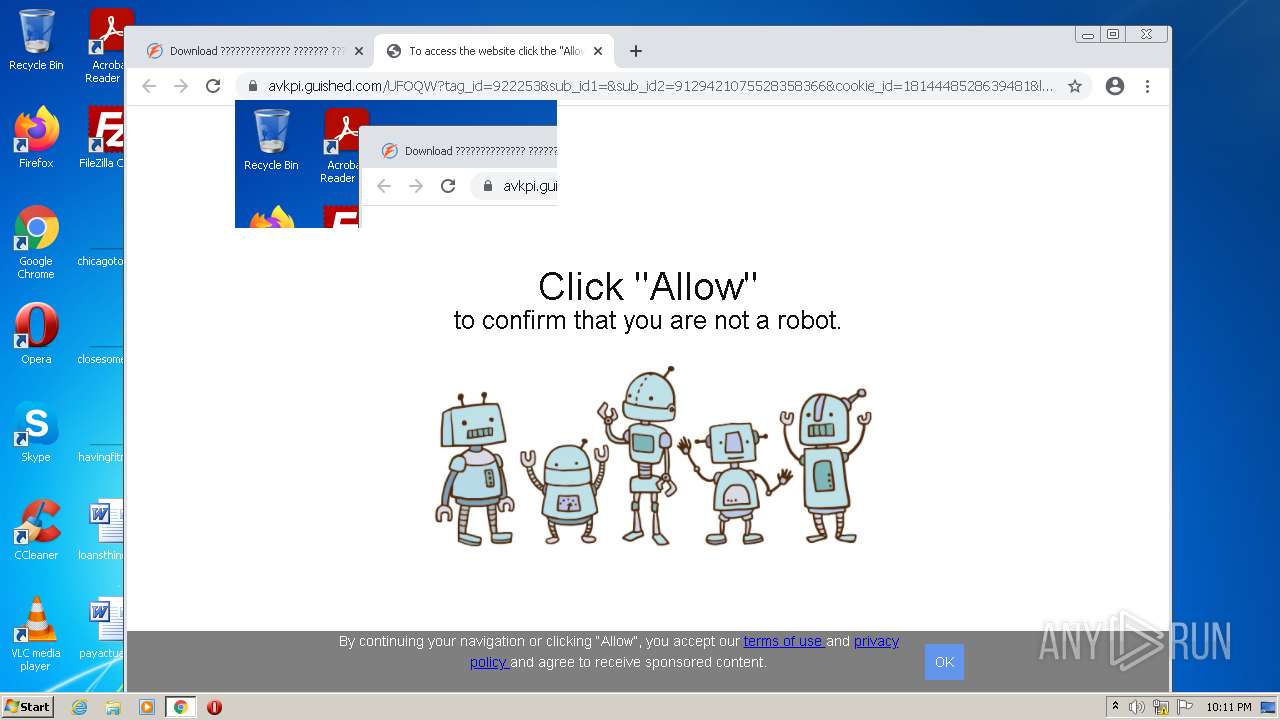
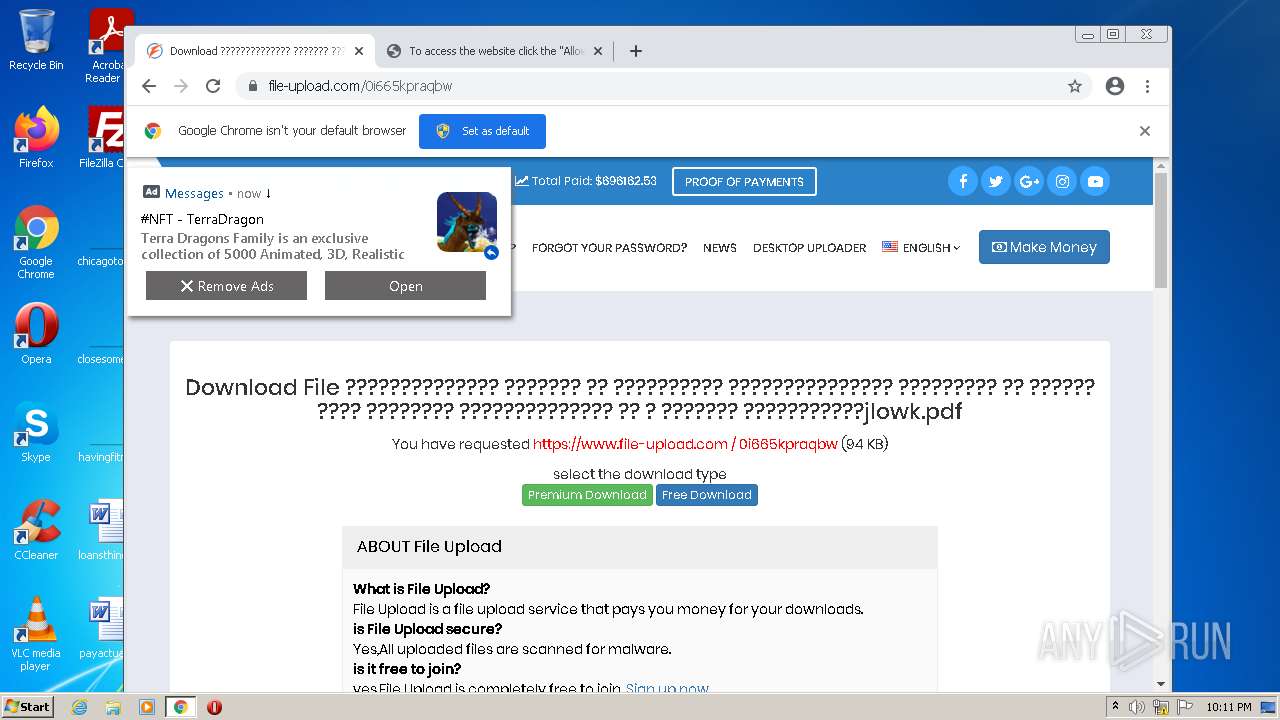
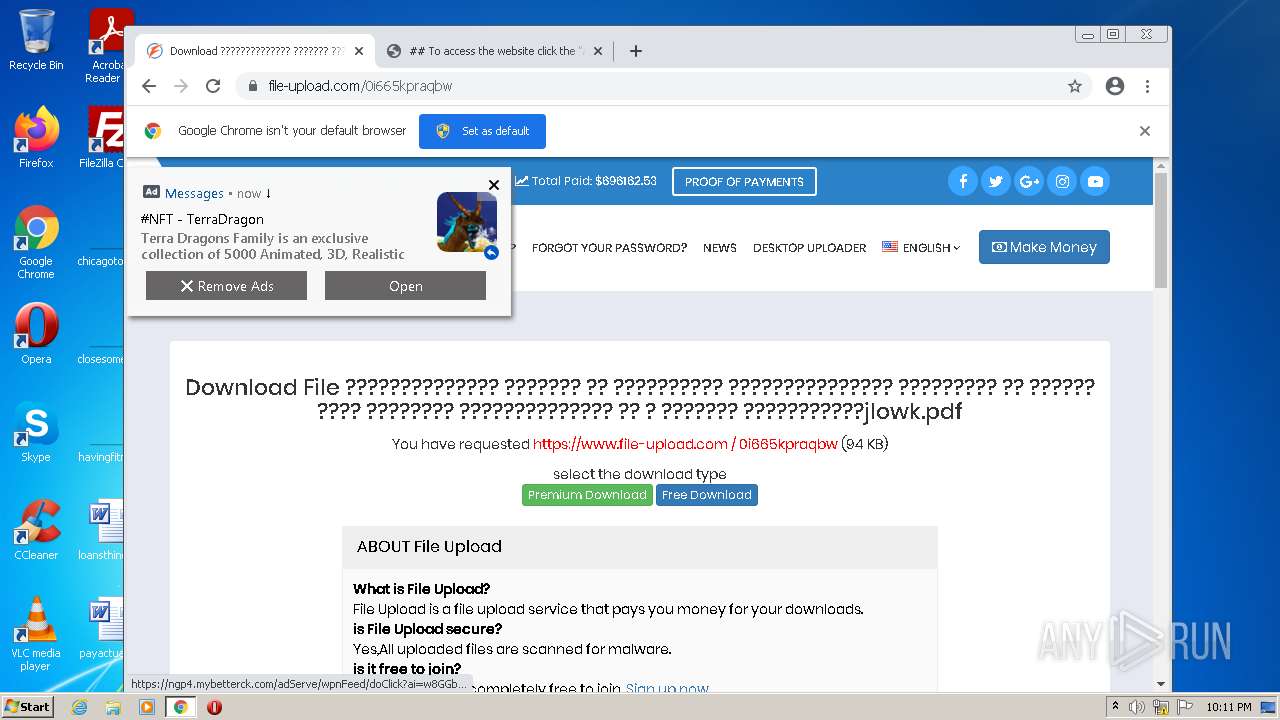
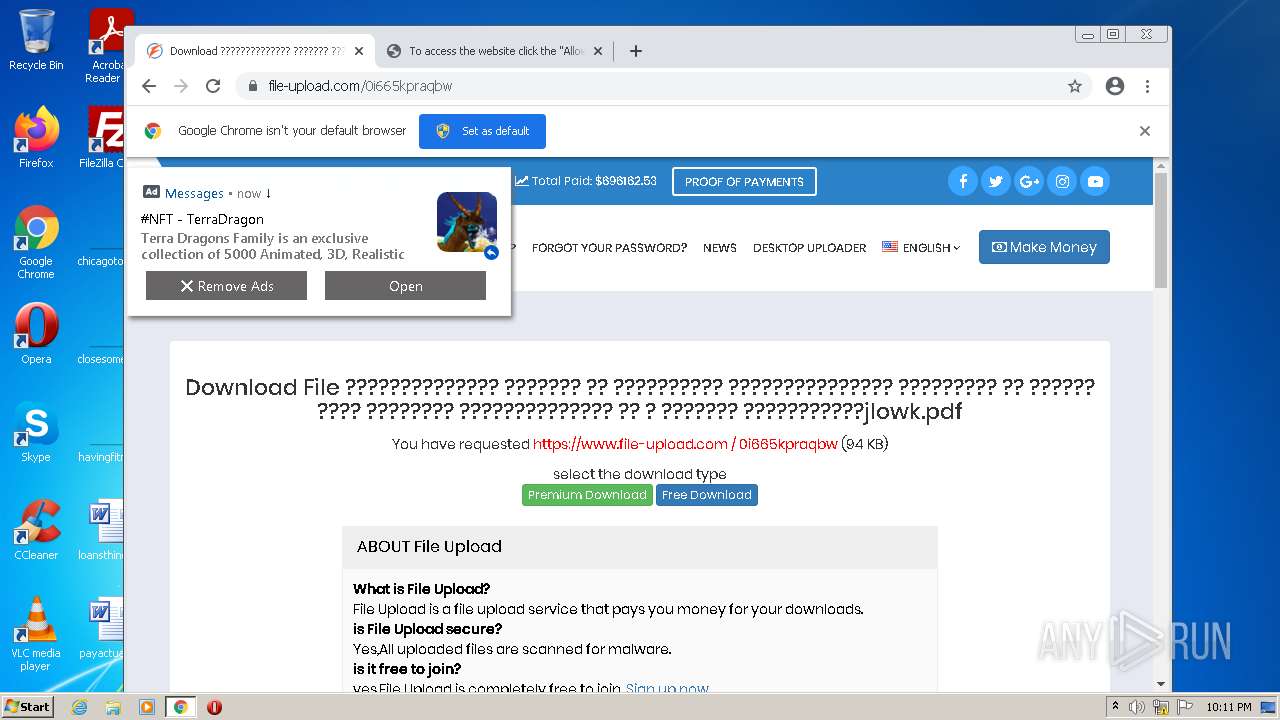
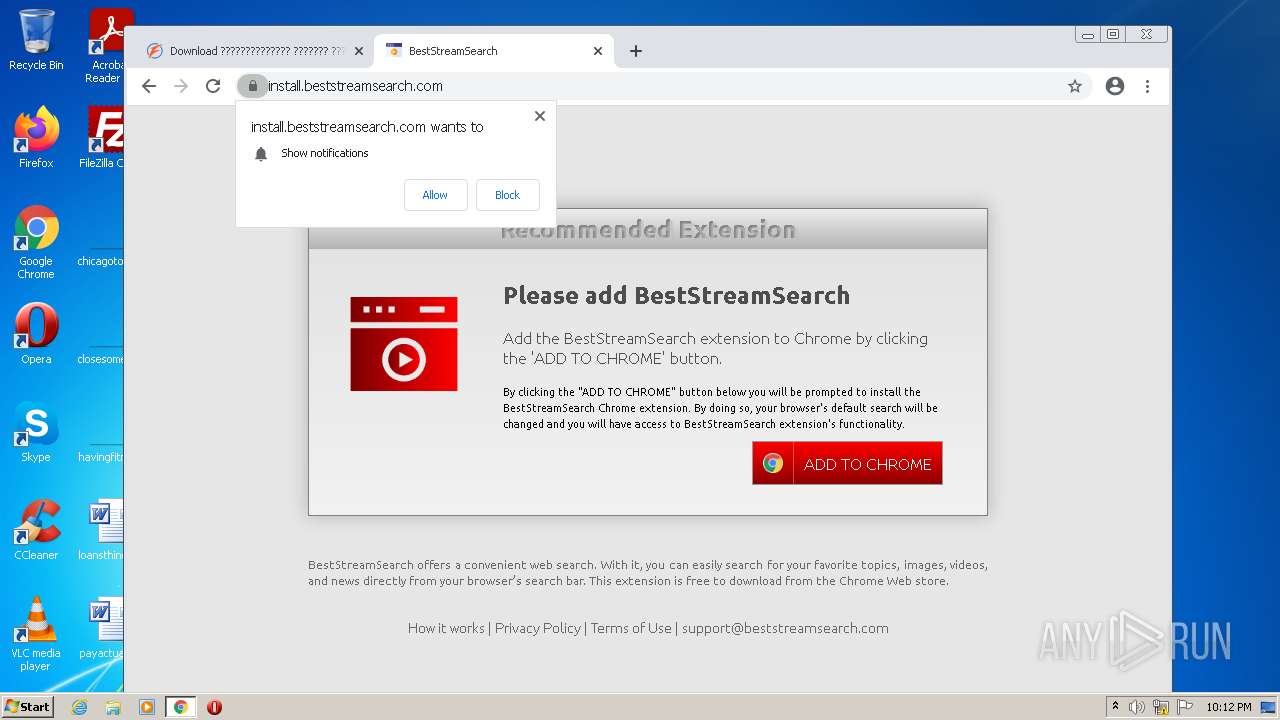
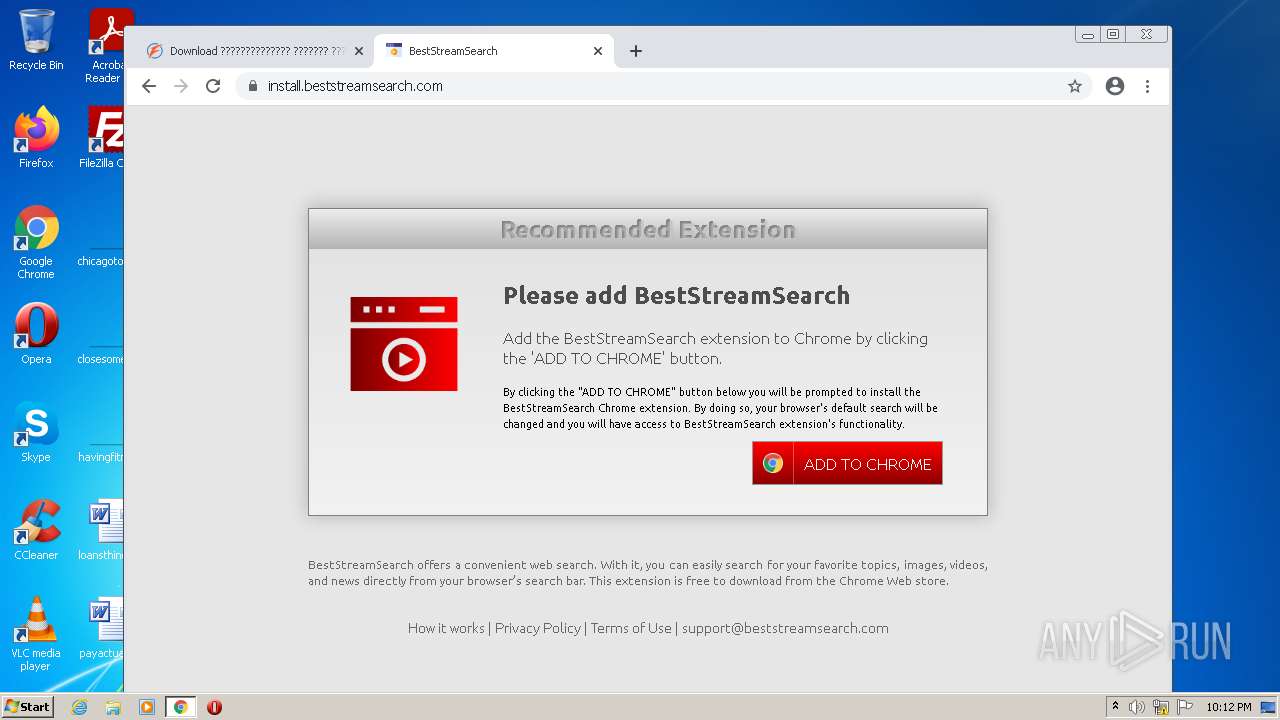
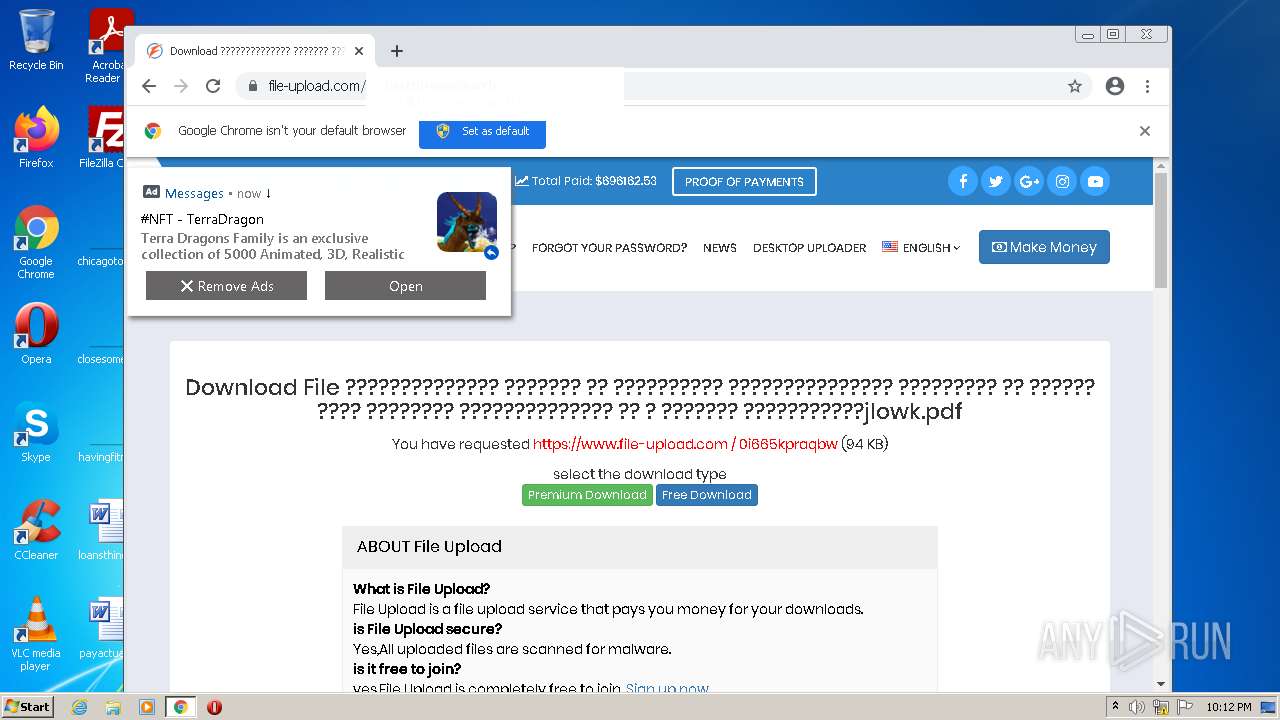
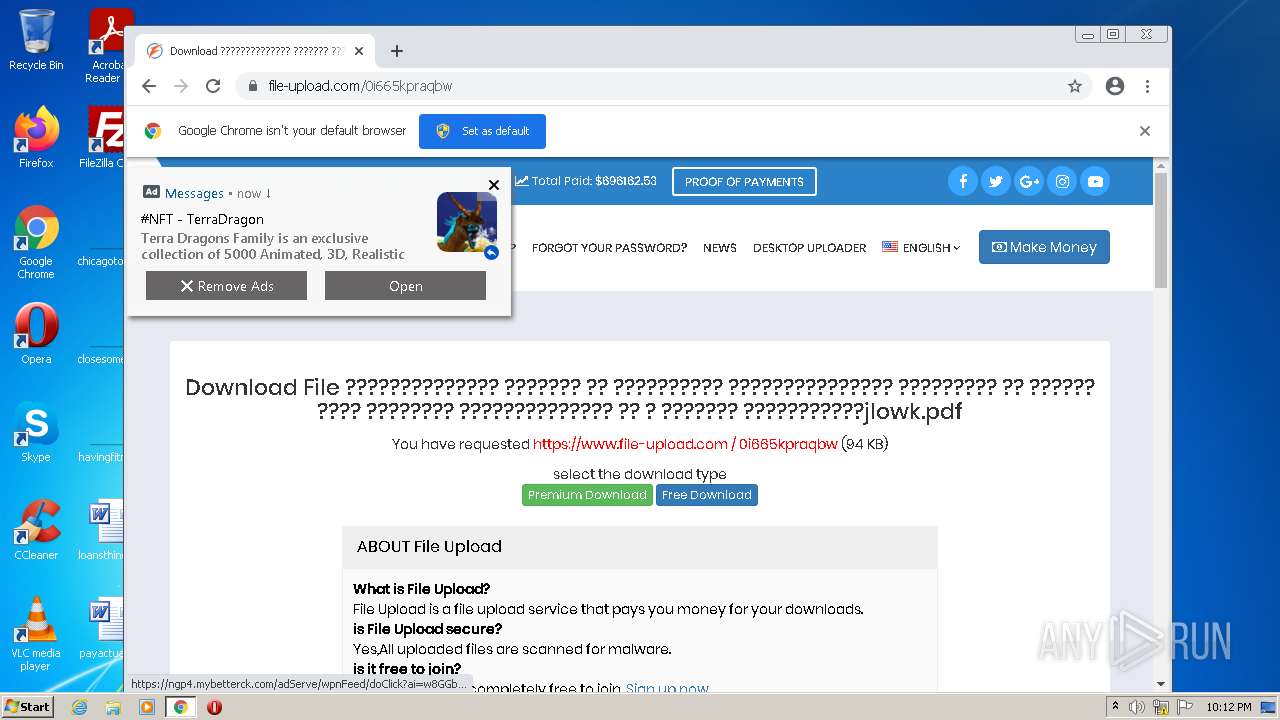
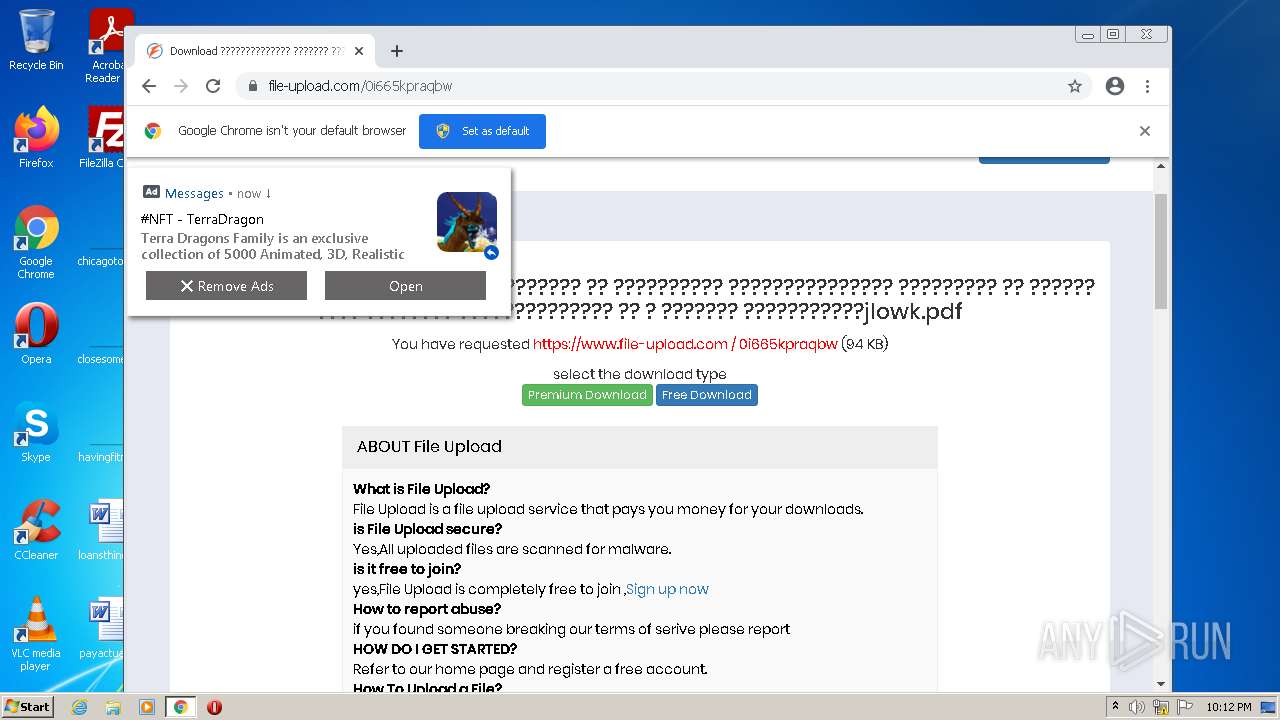
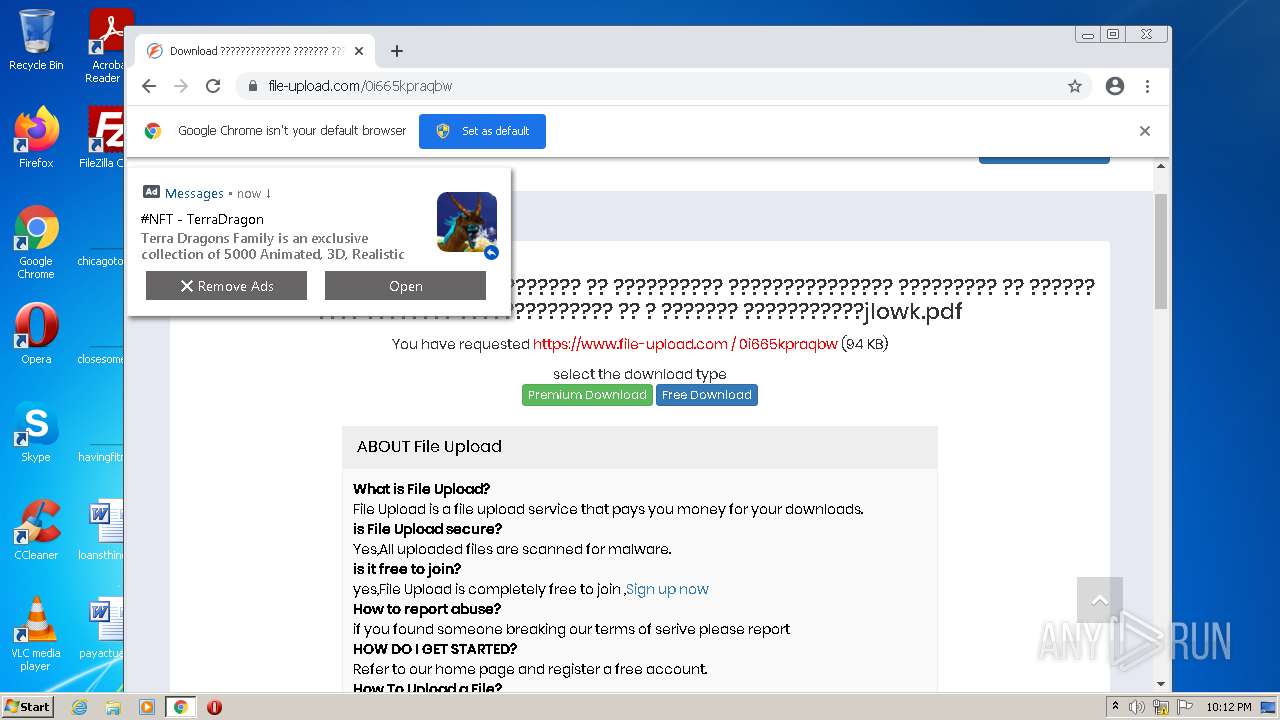
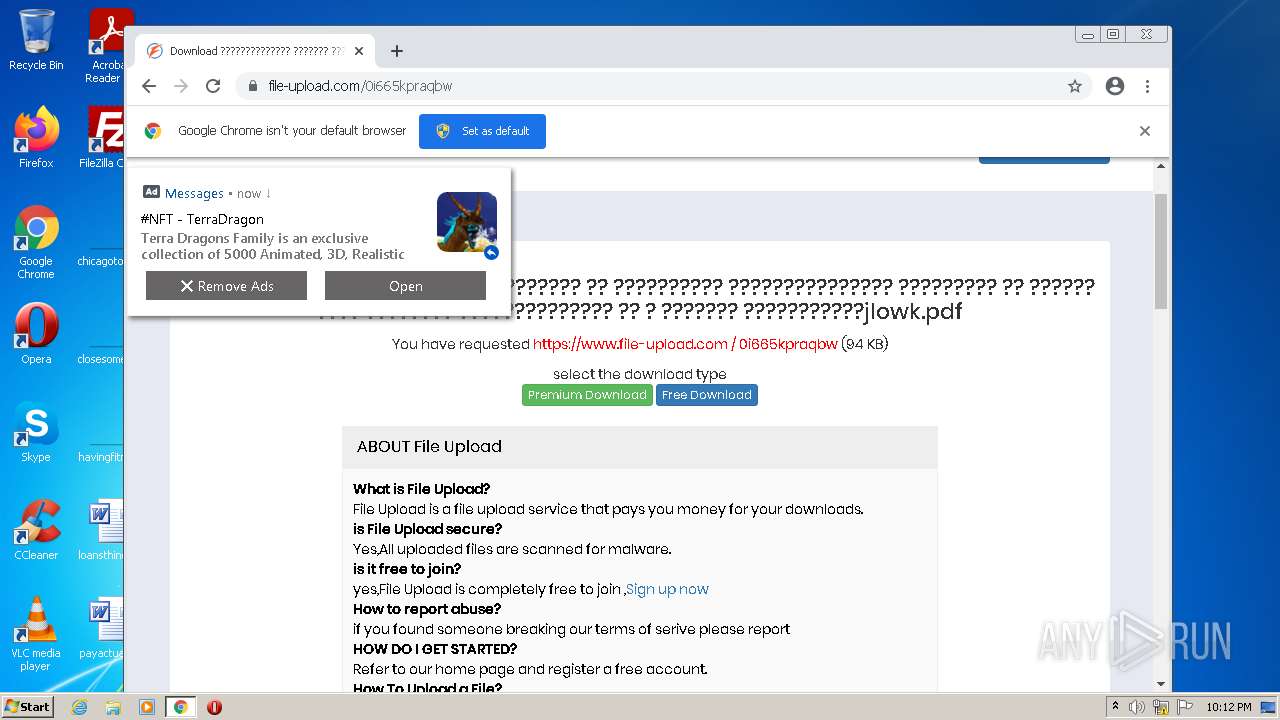
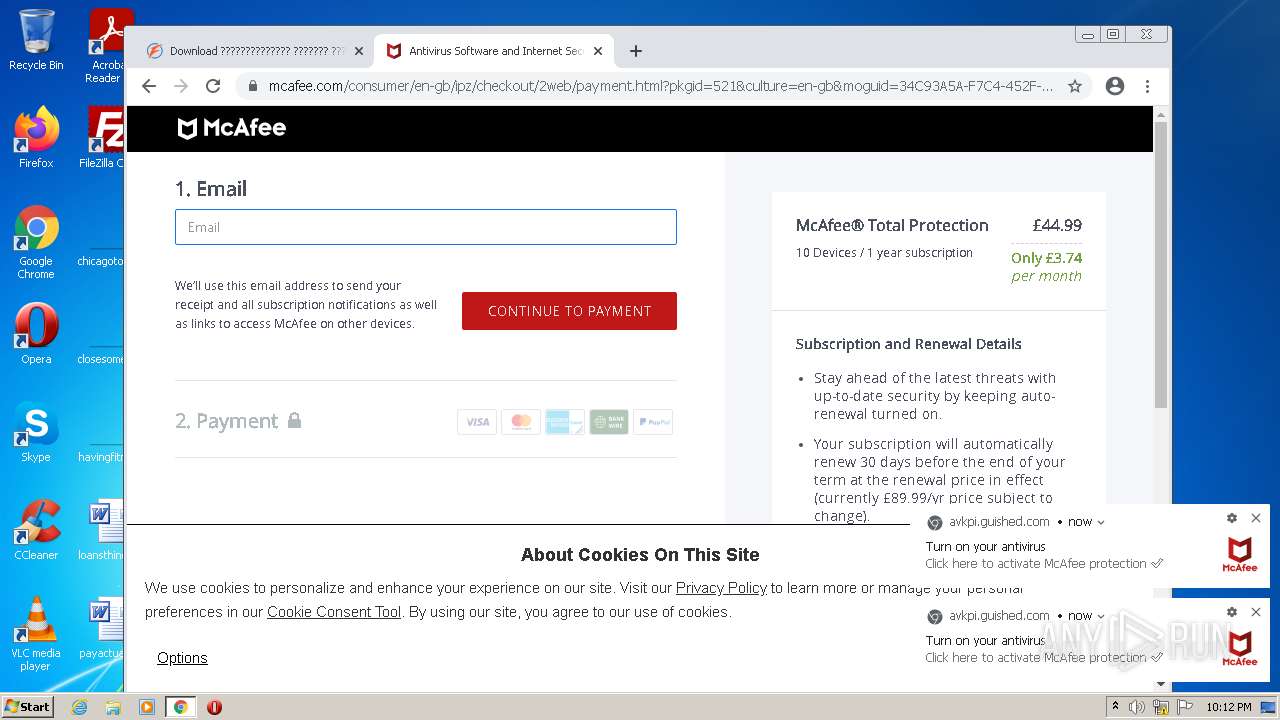
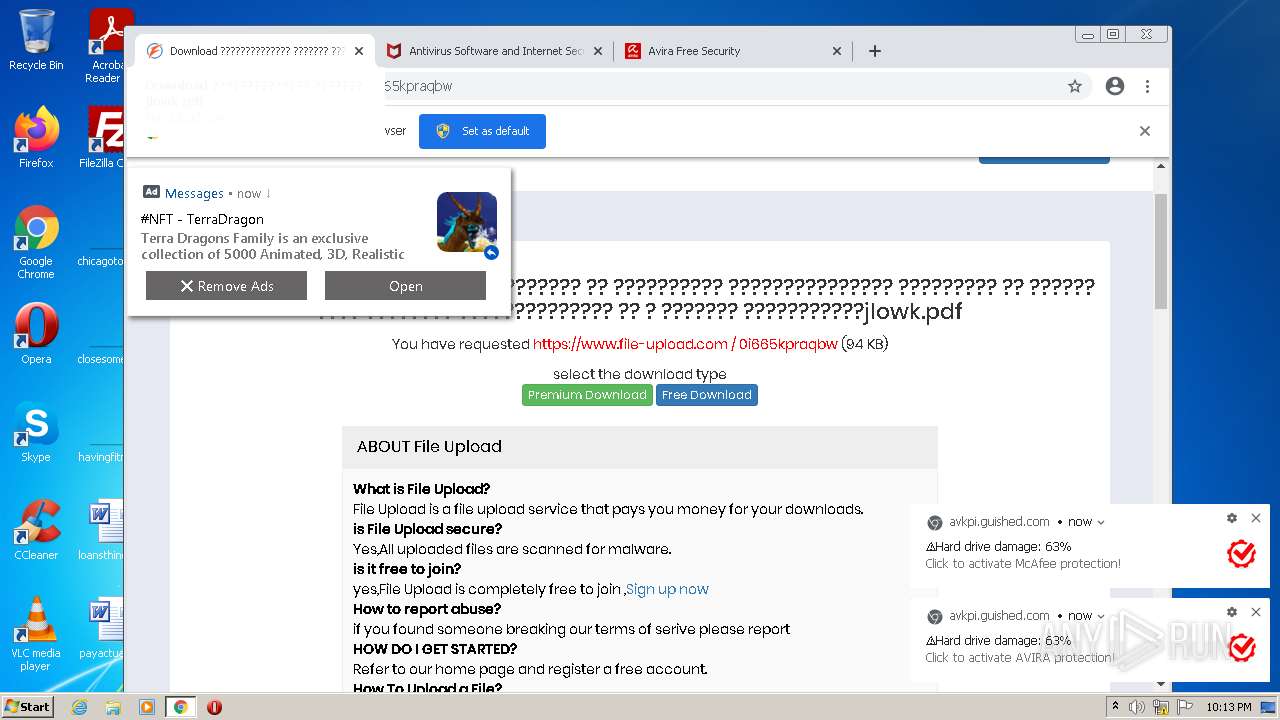
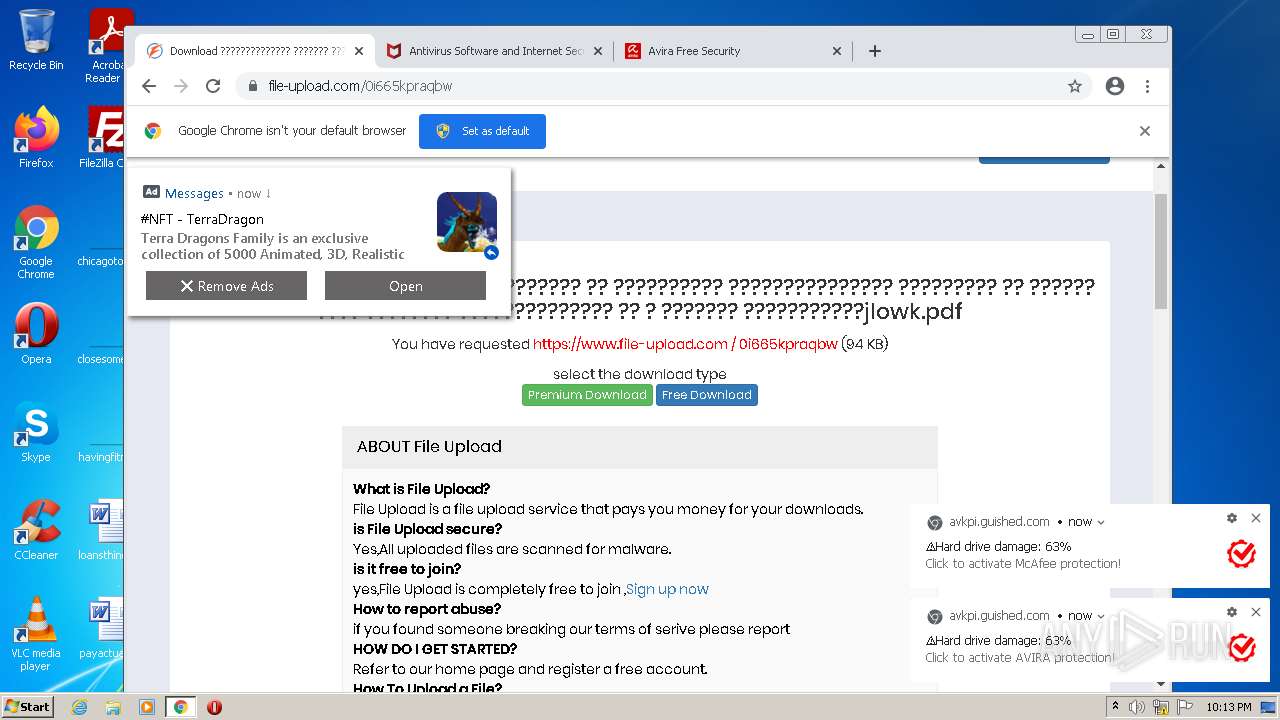
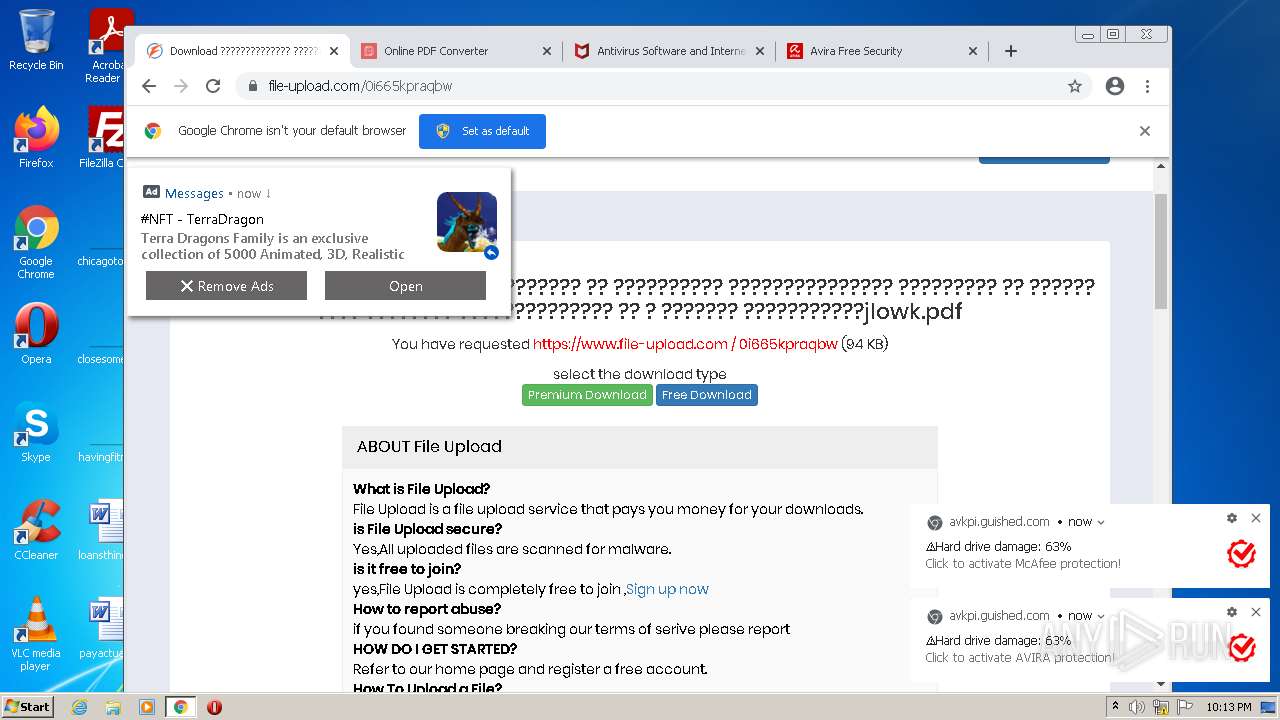
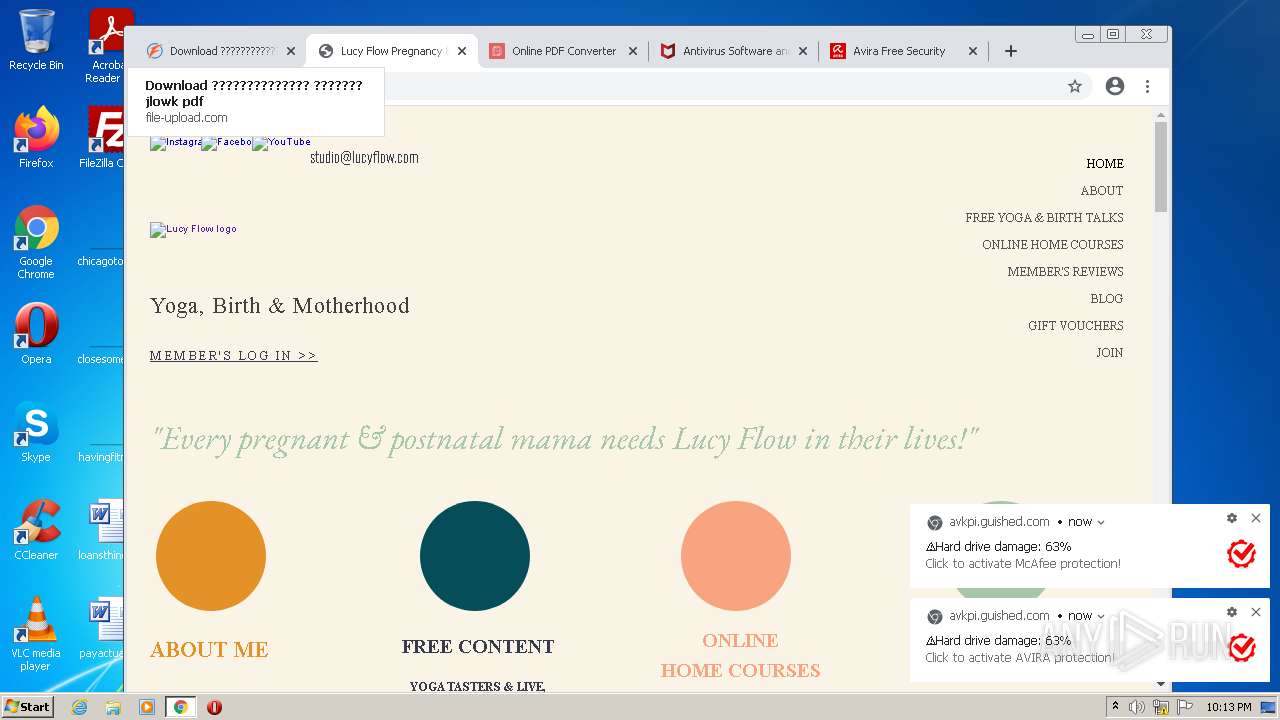
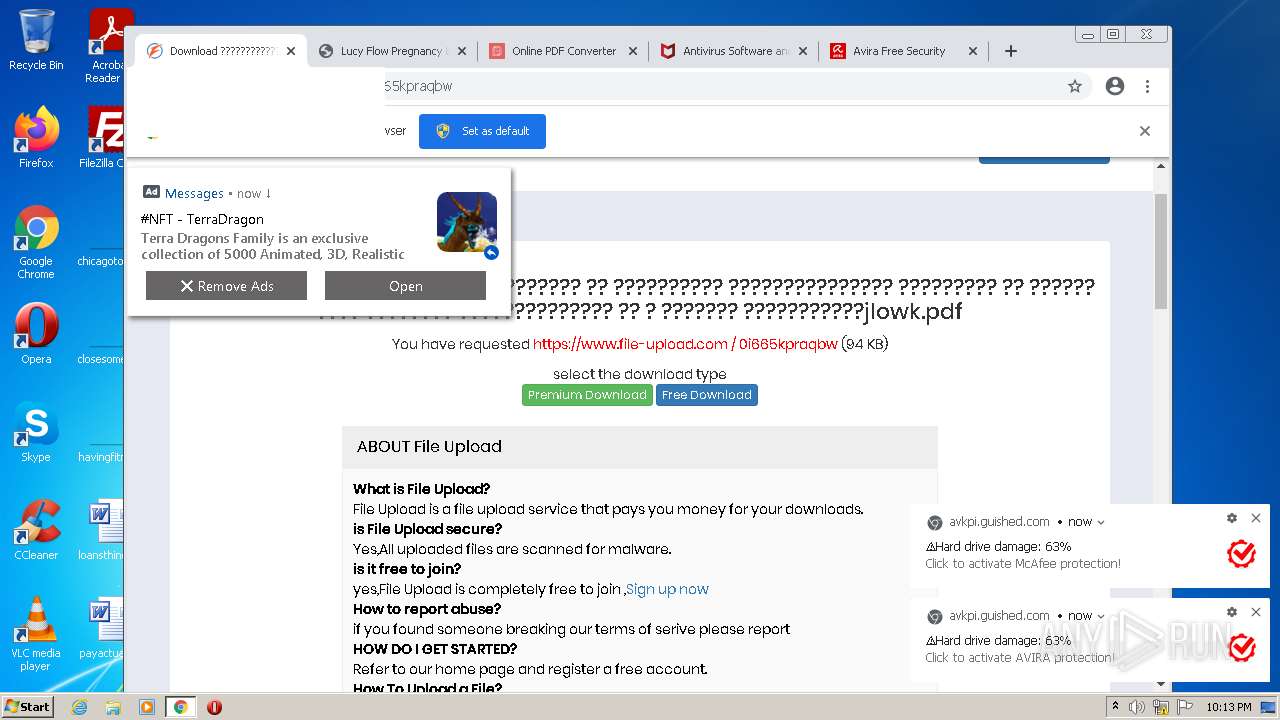
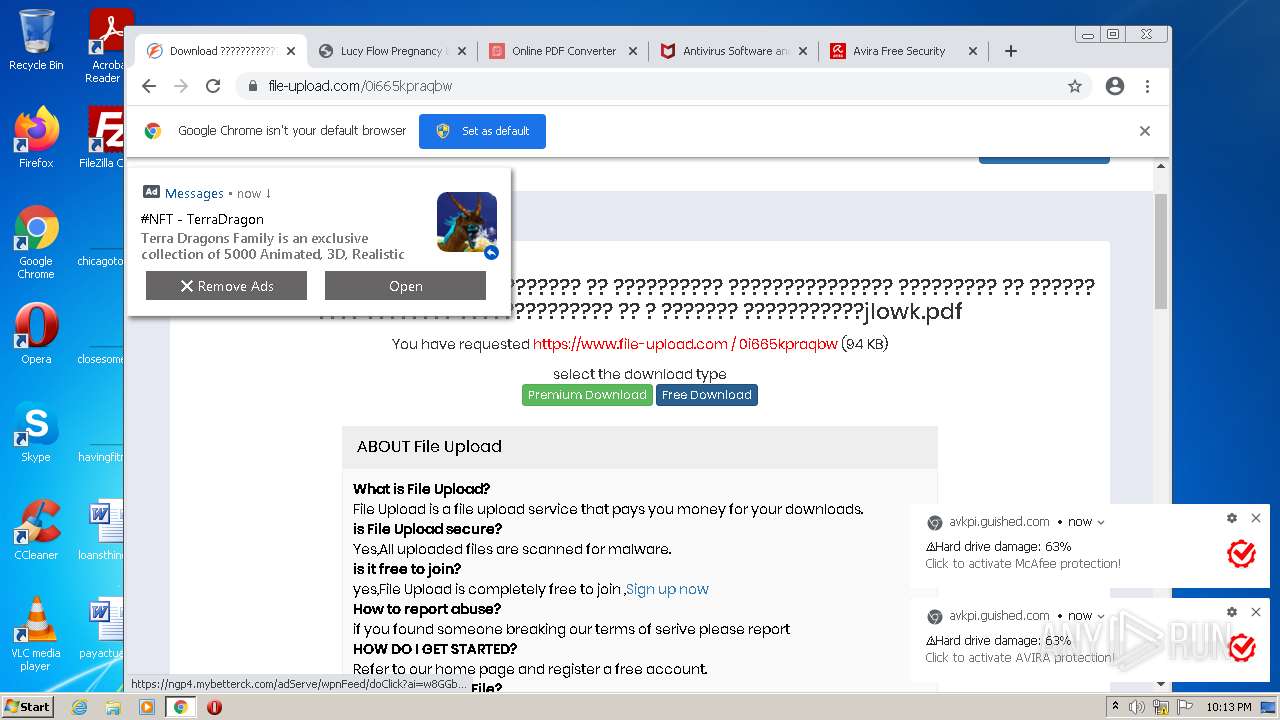
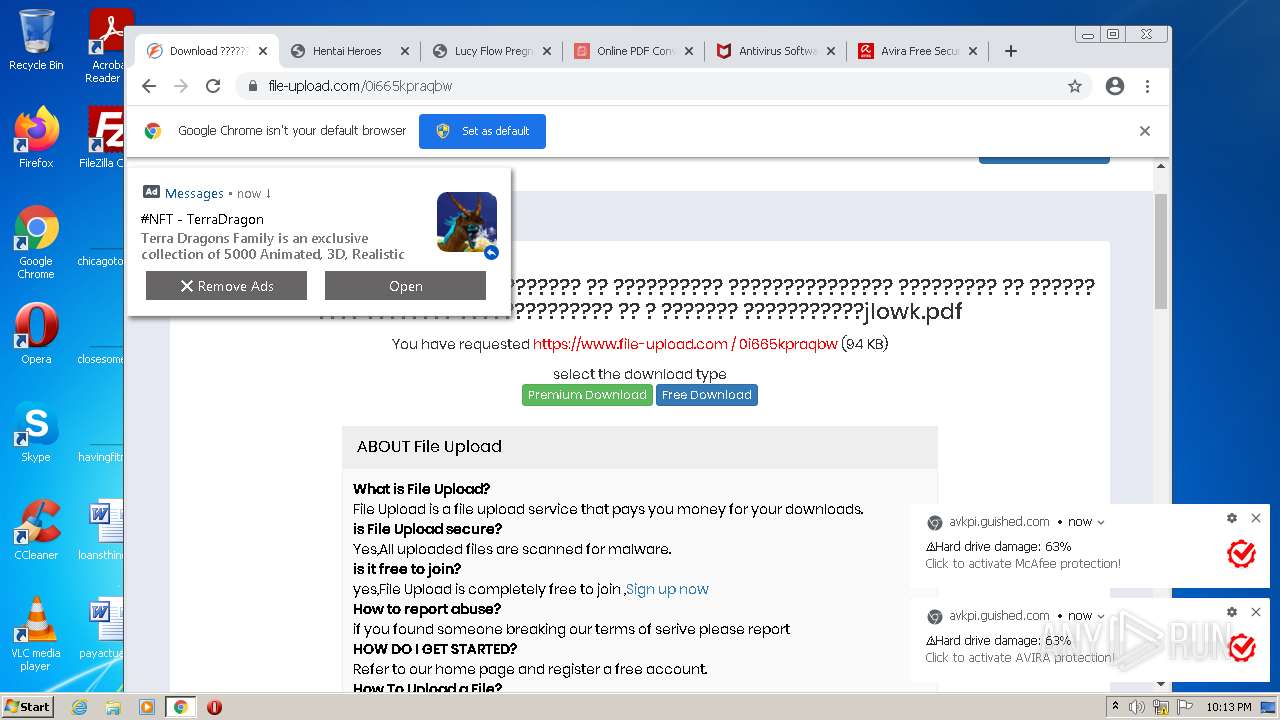
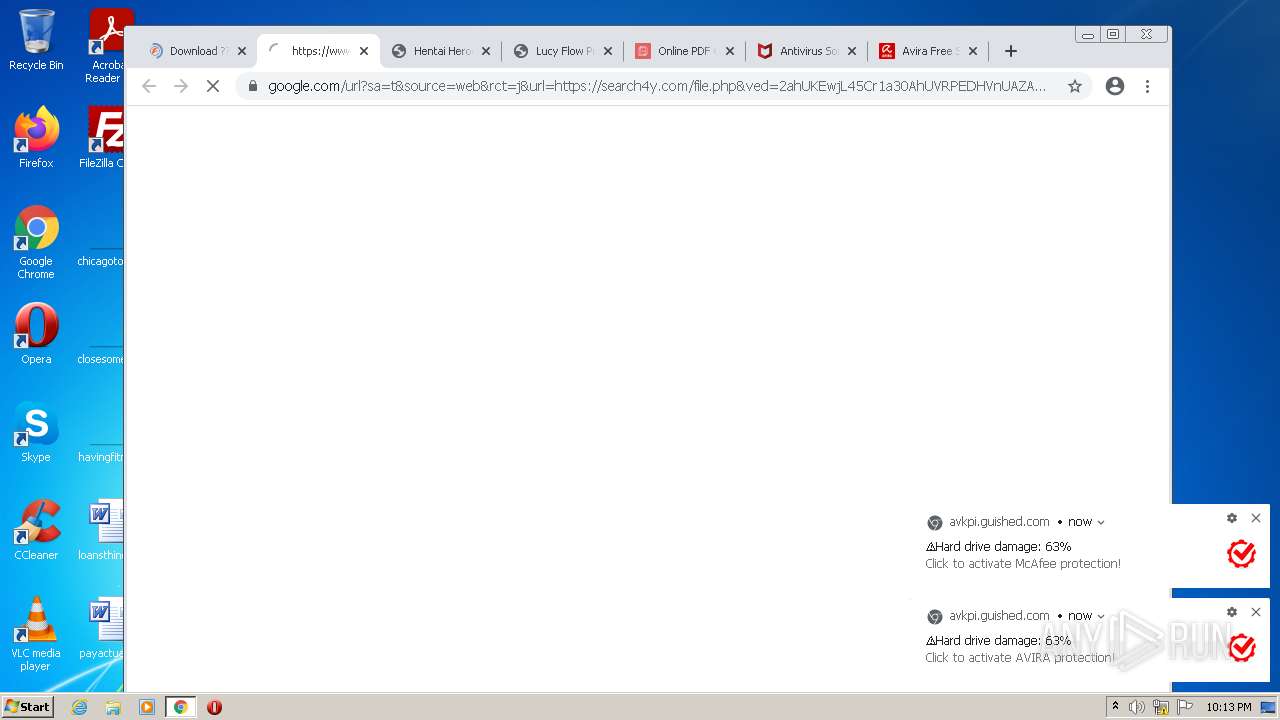
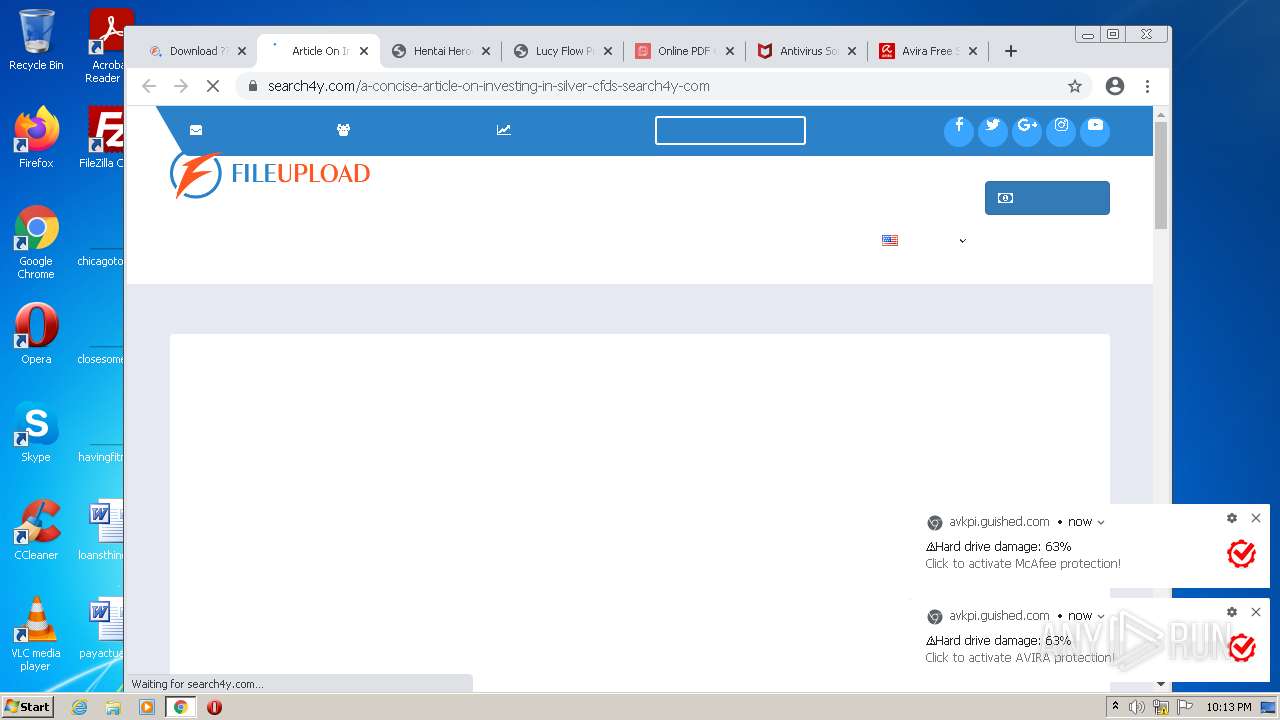
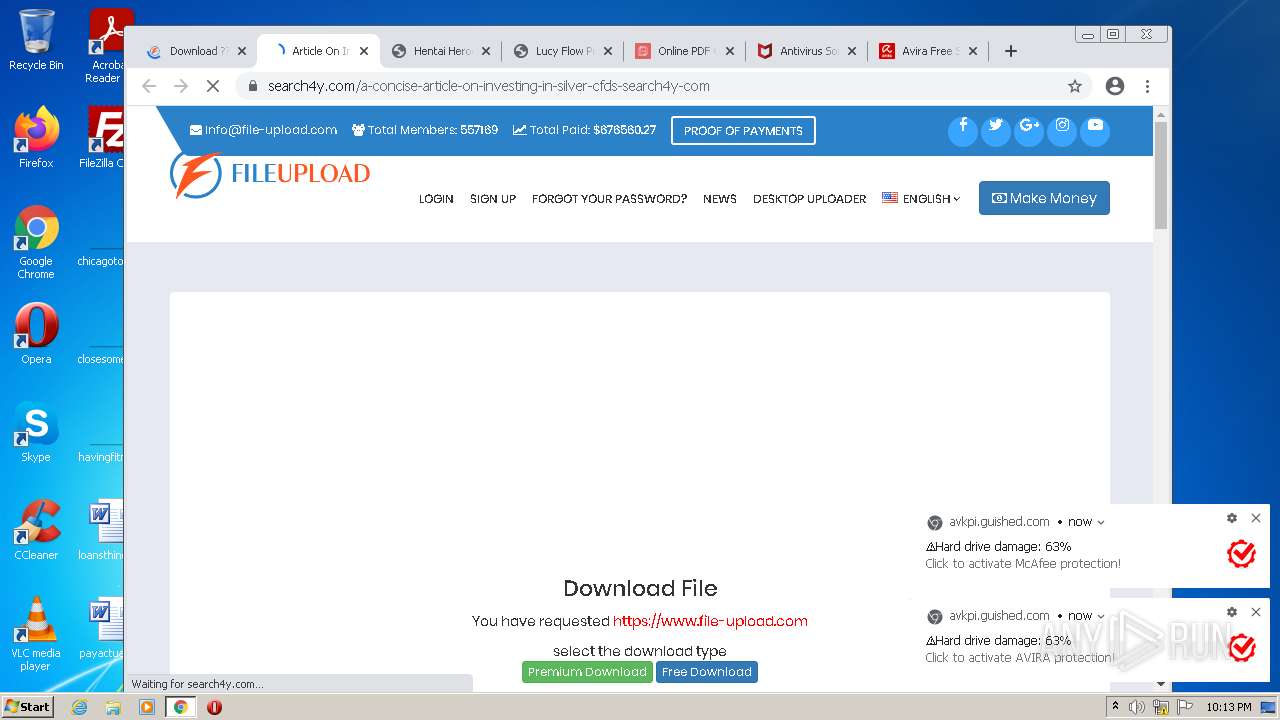
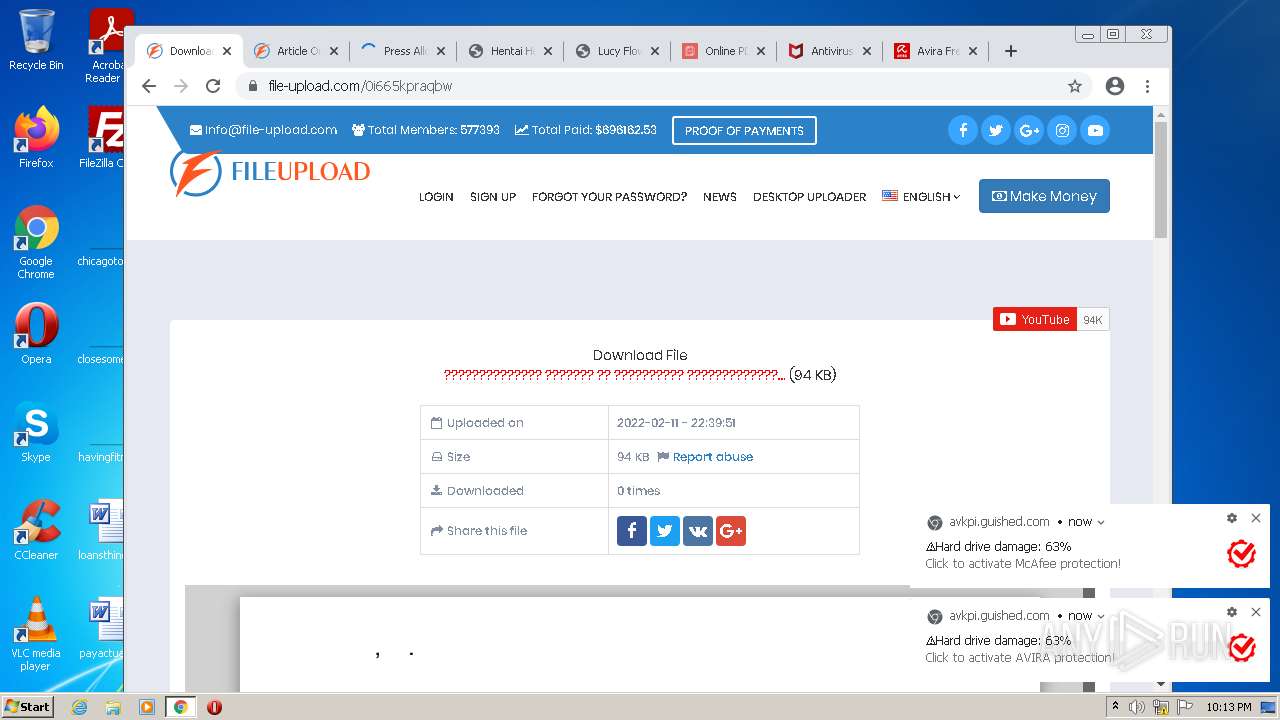
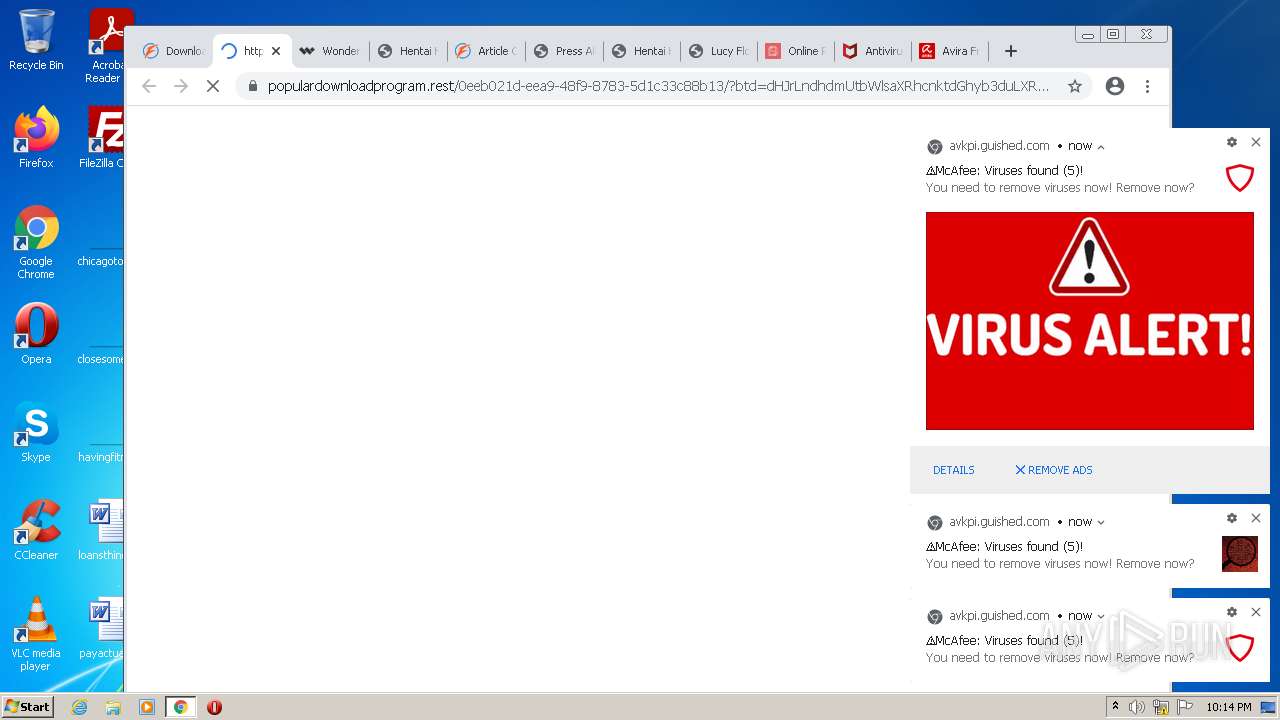
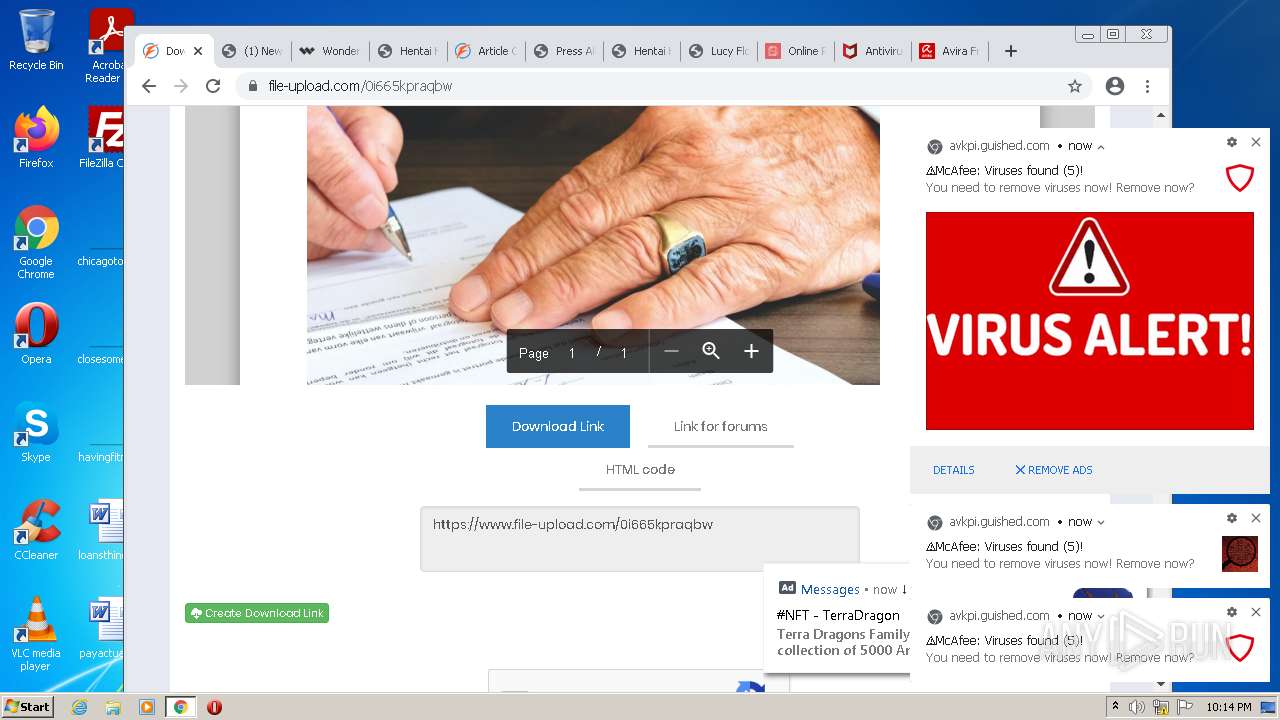
| URL: | https://www.file-upload.com/0i665kpraqbw |
| Full analysis: | https://app.any.run/tasks/1c3c348a-12fc-430f-971d-4fa434ce491e |
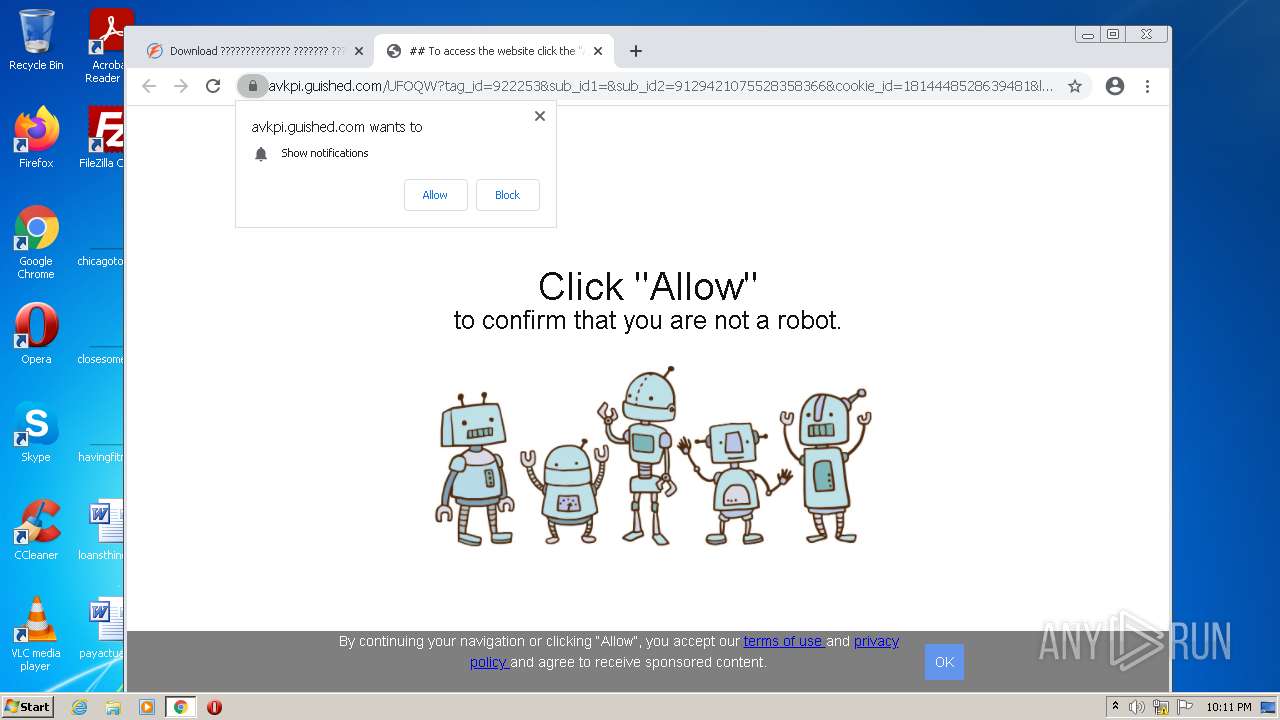
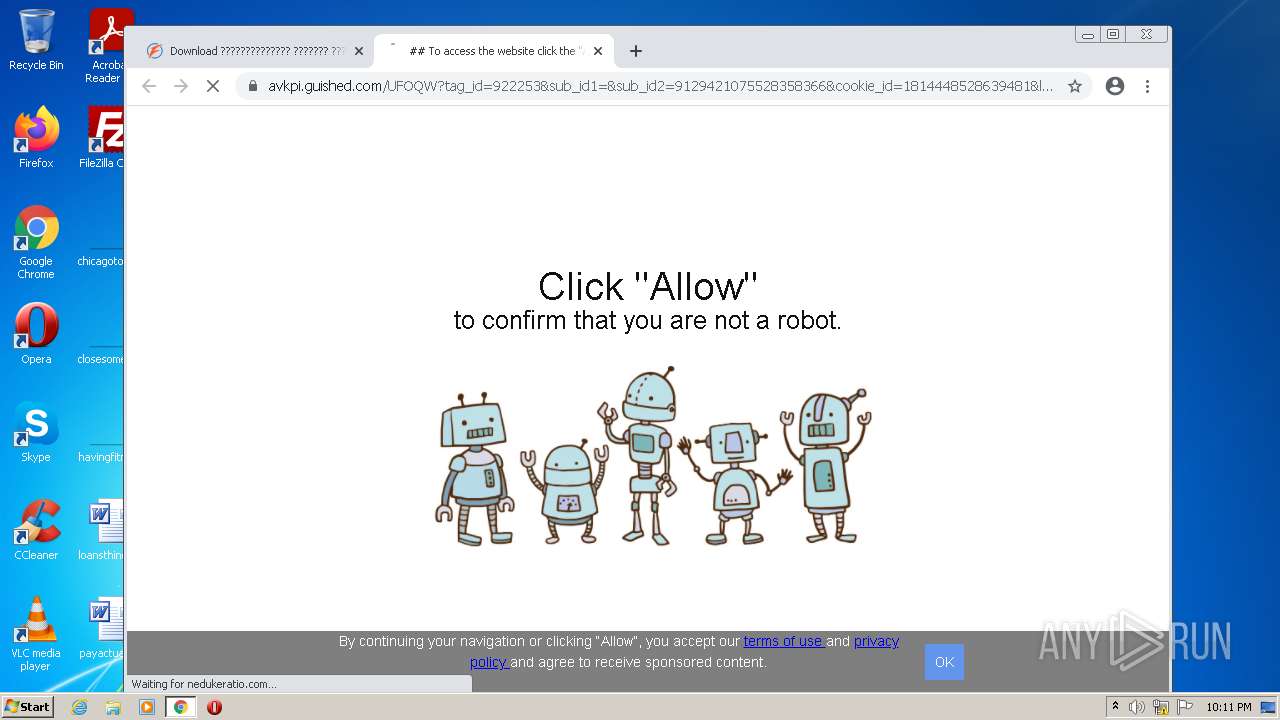
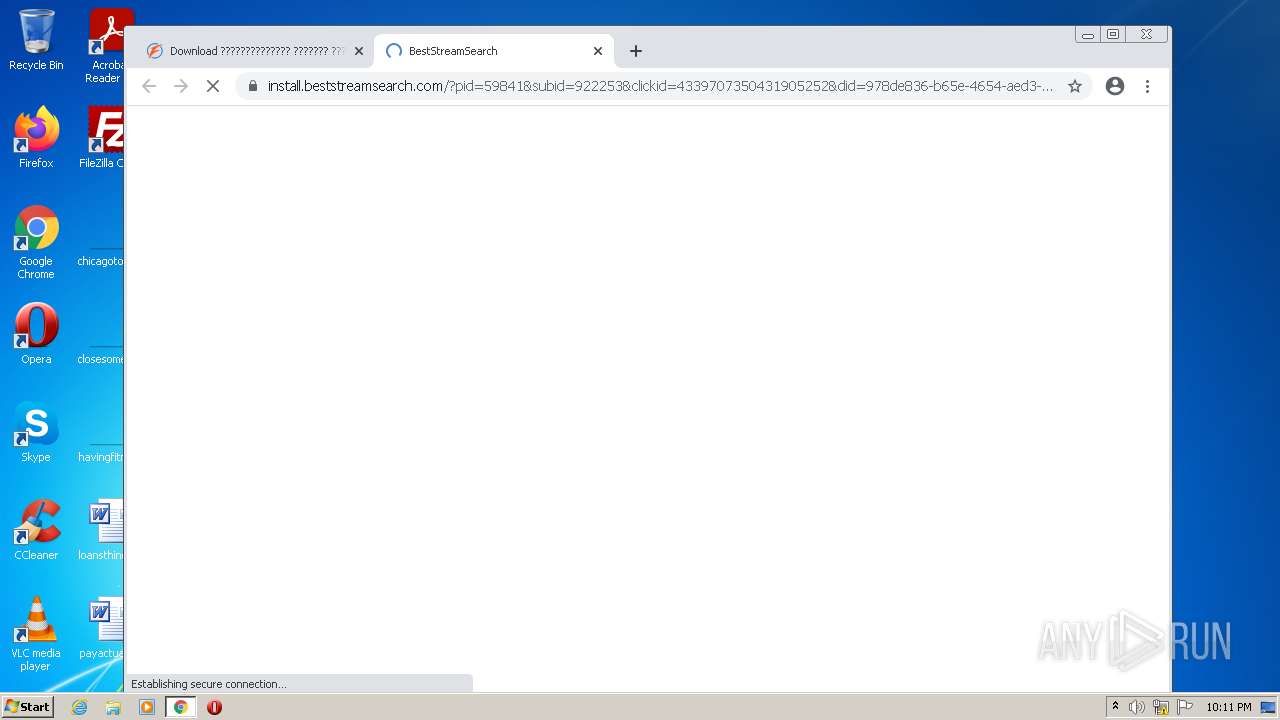
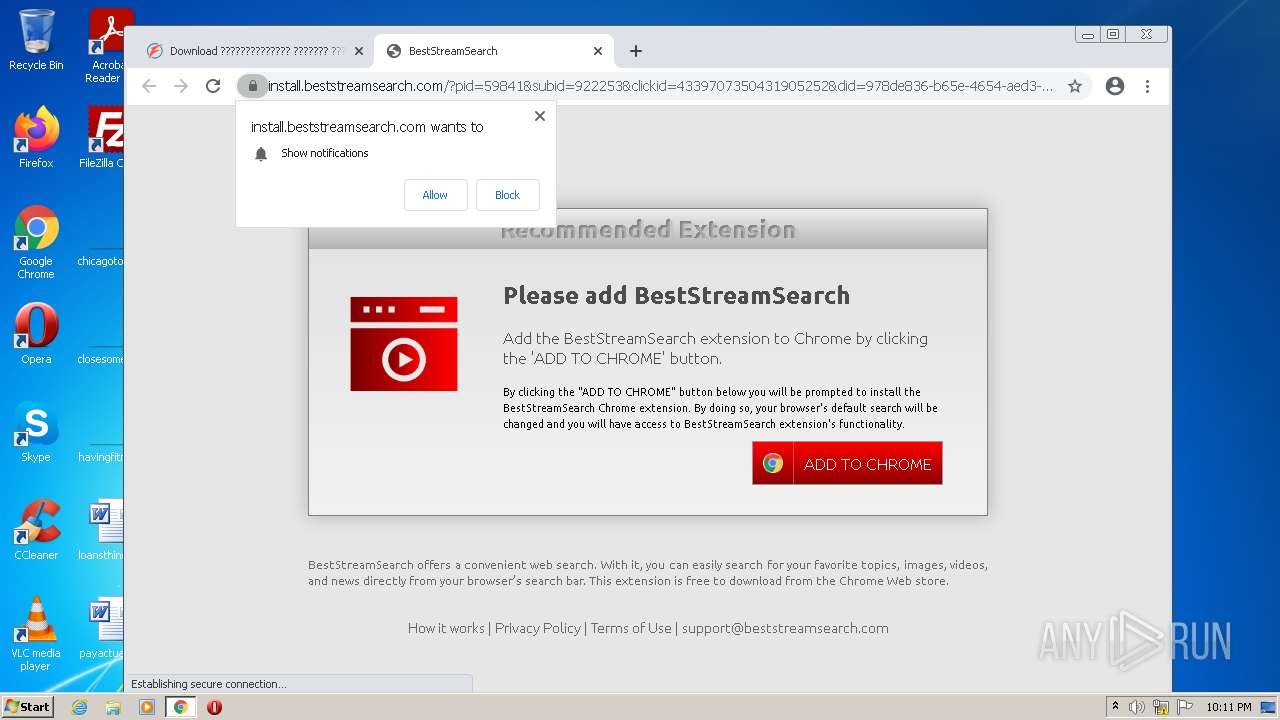
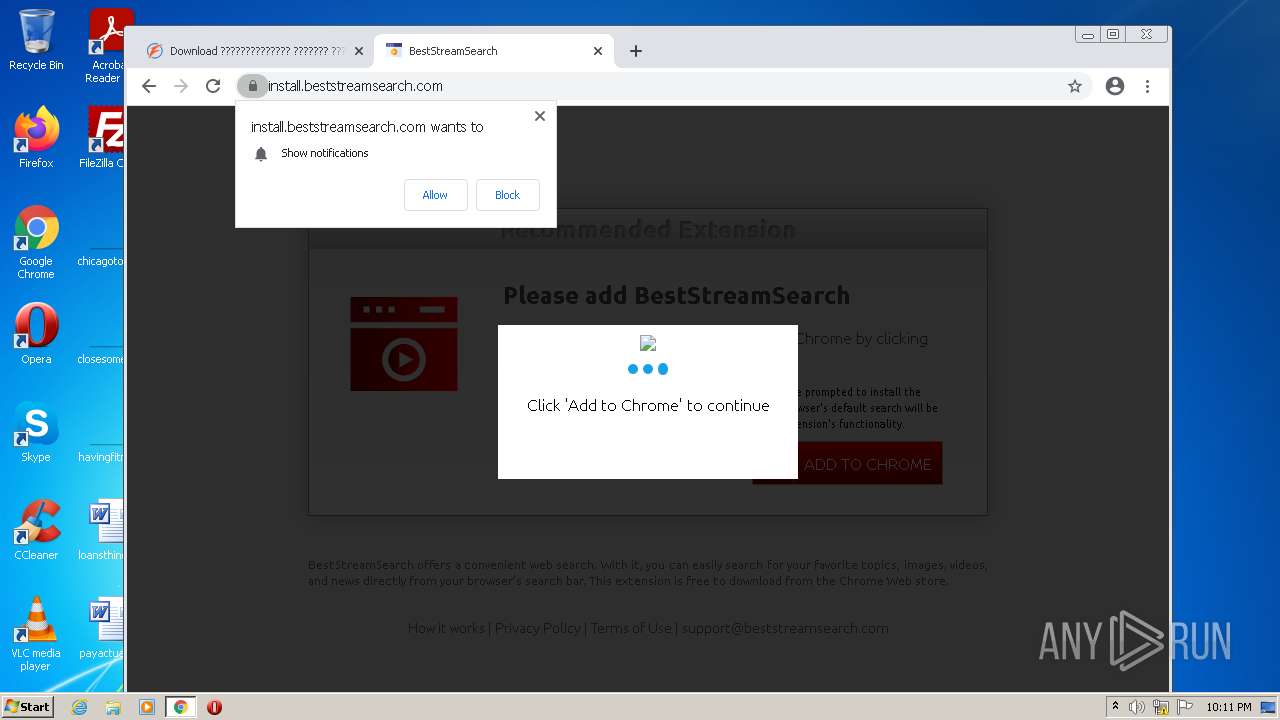
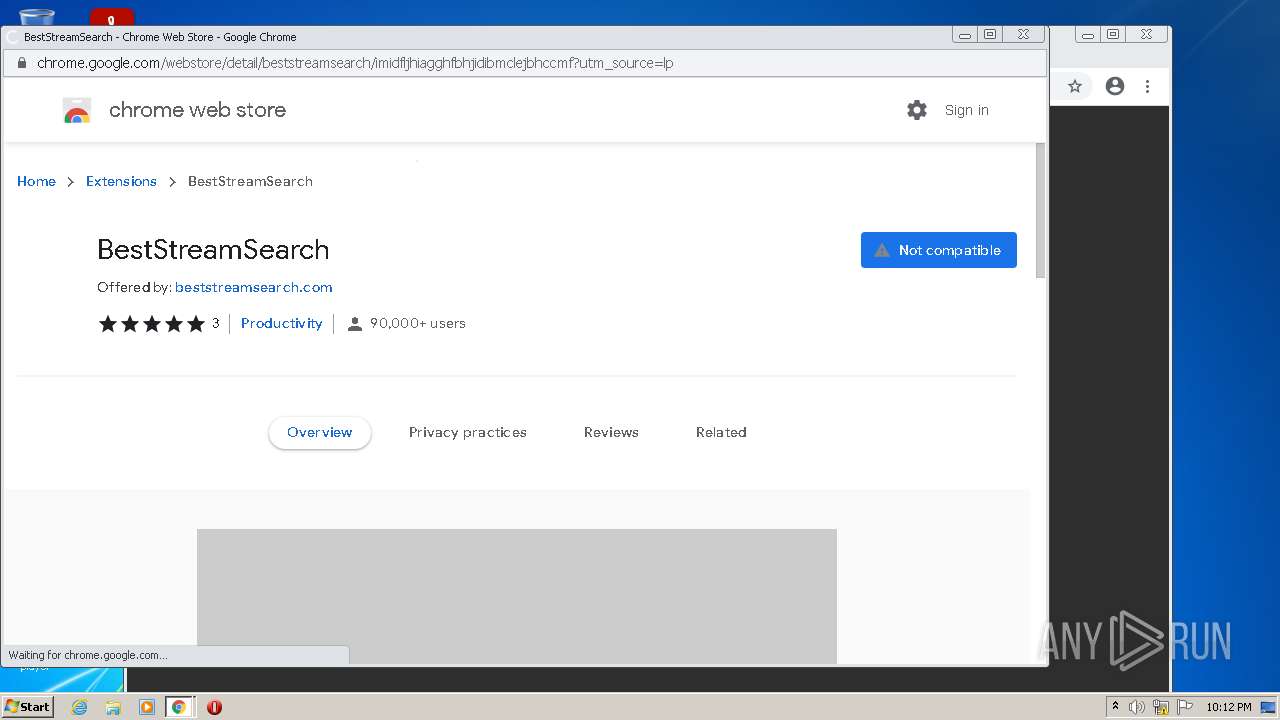
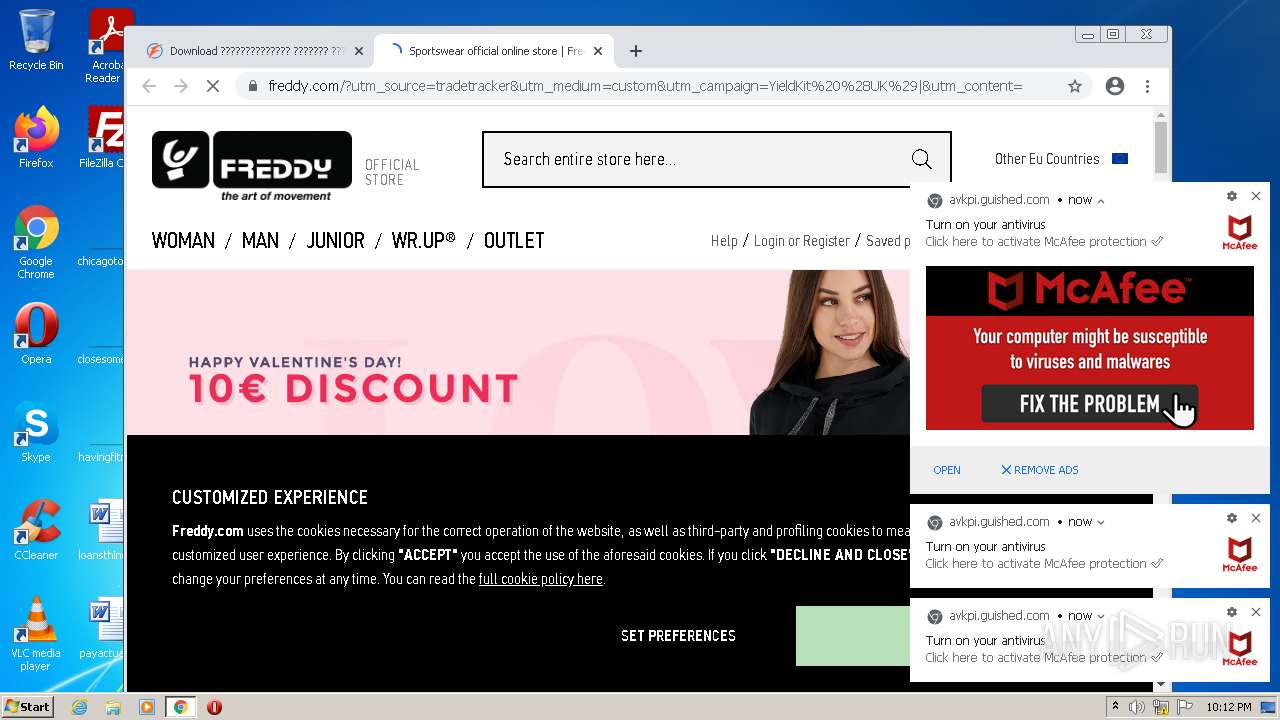
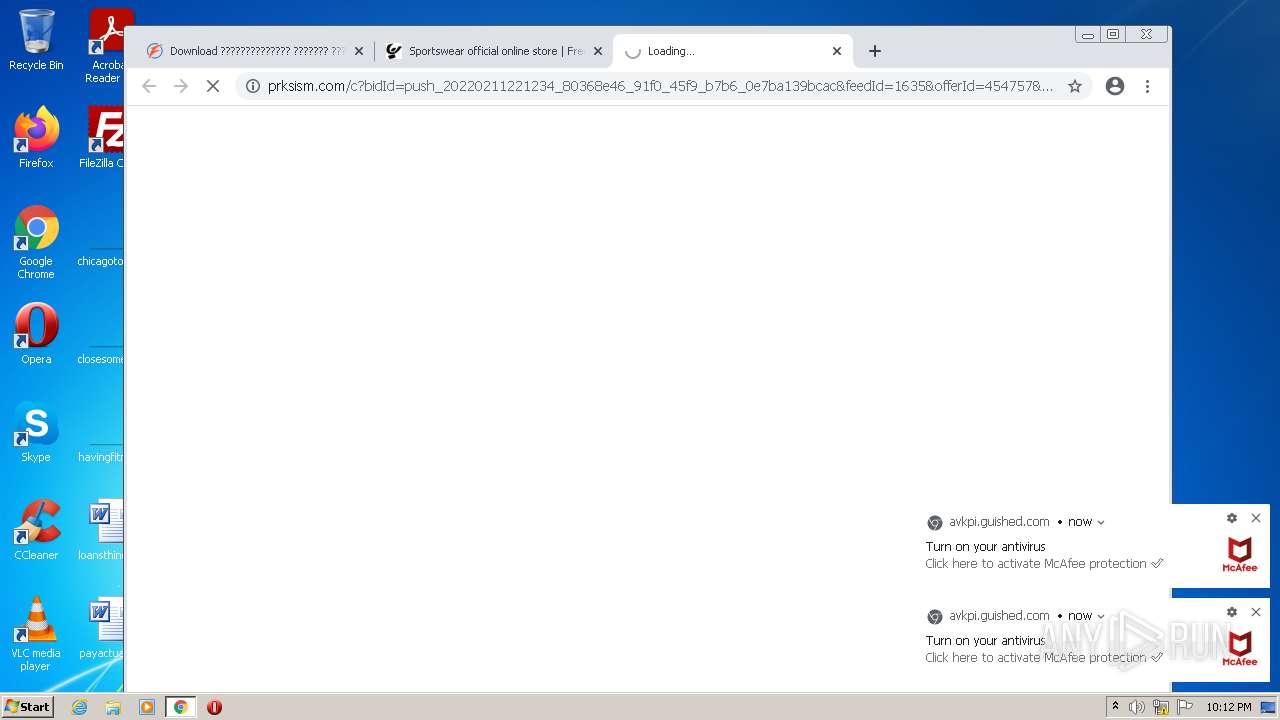
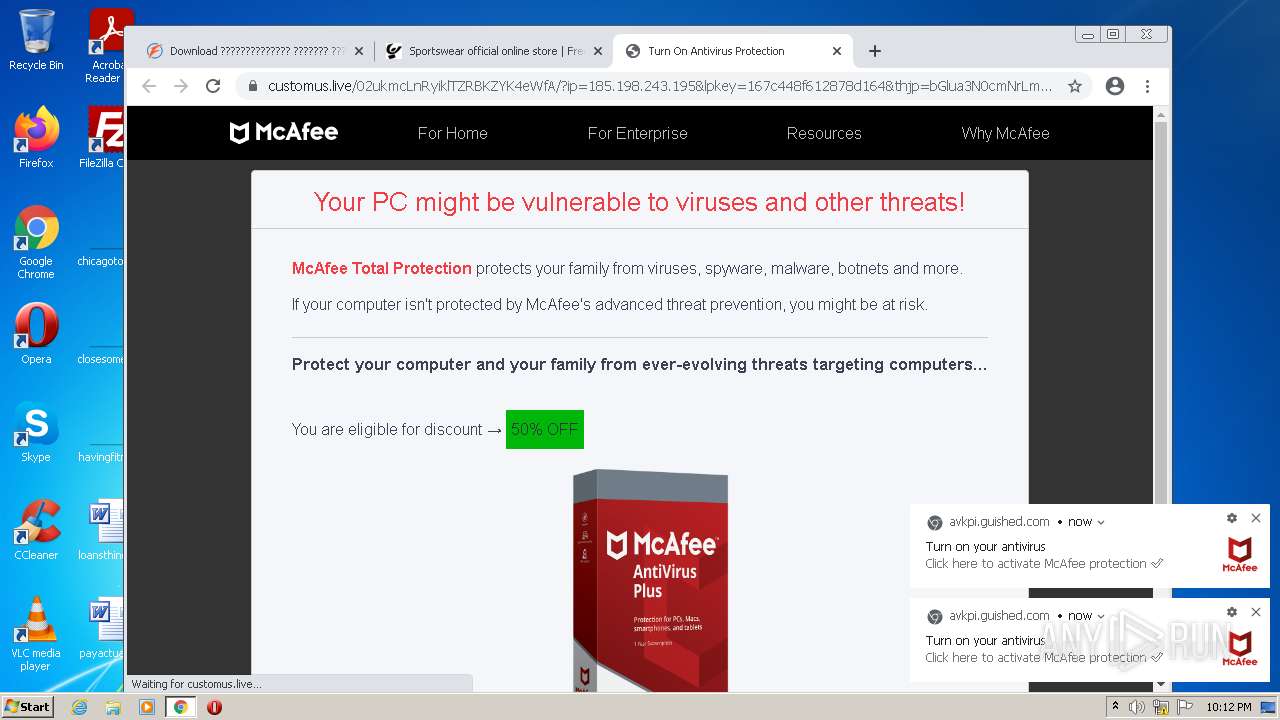
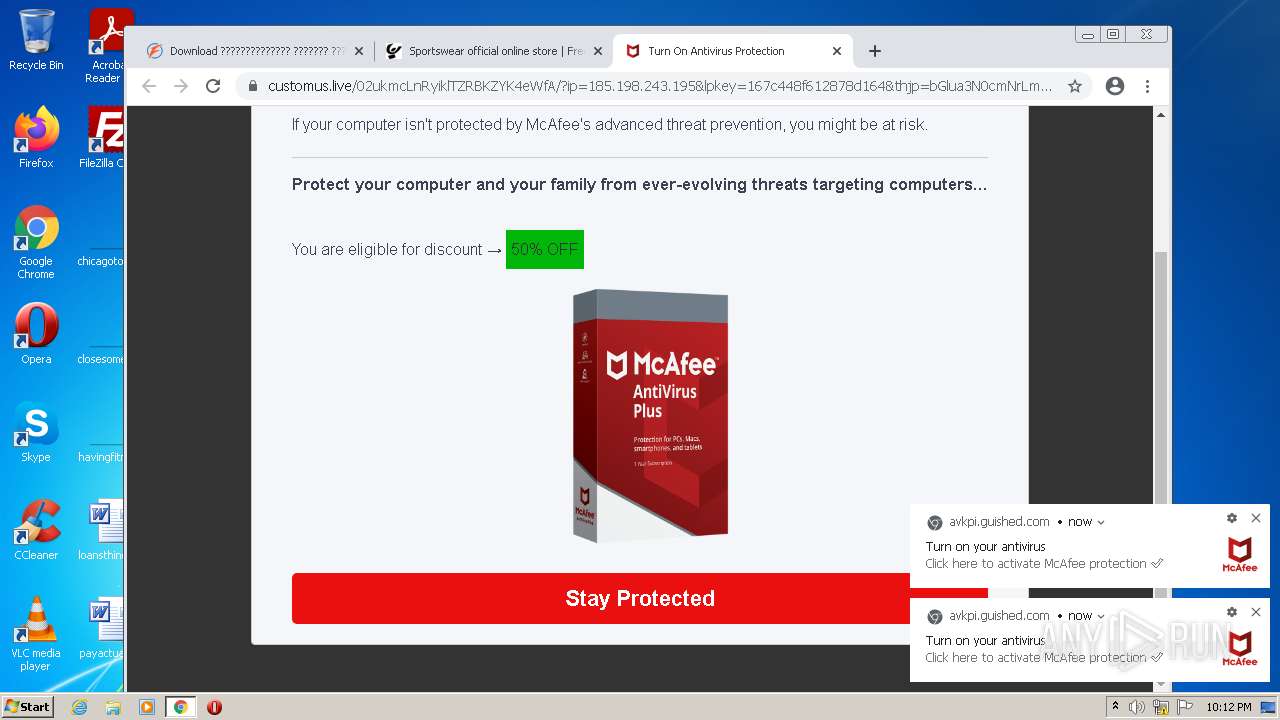
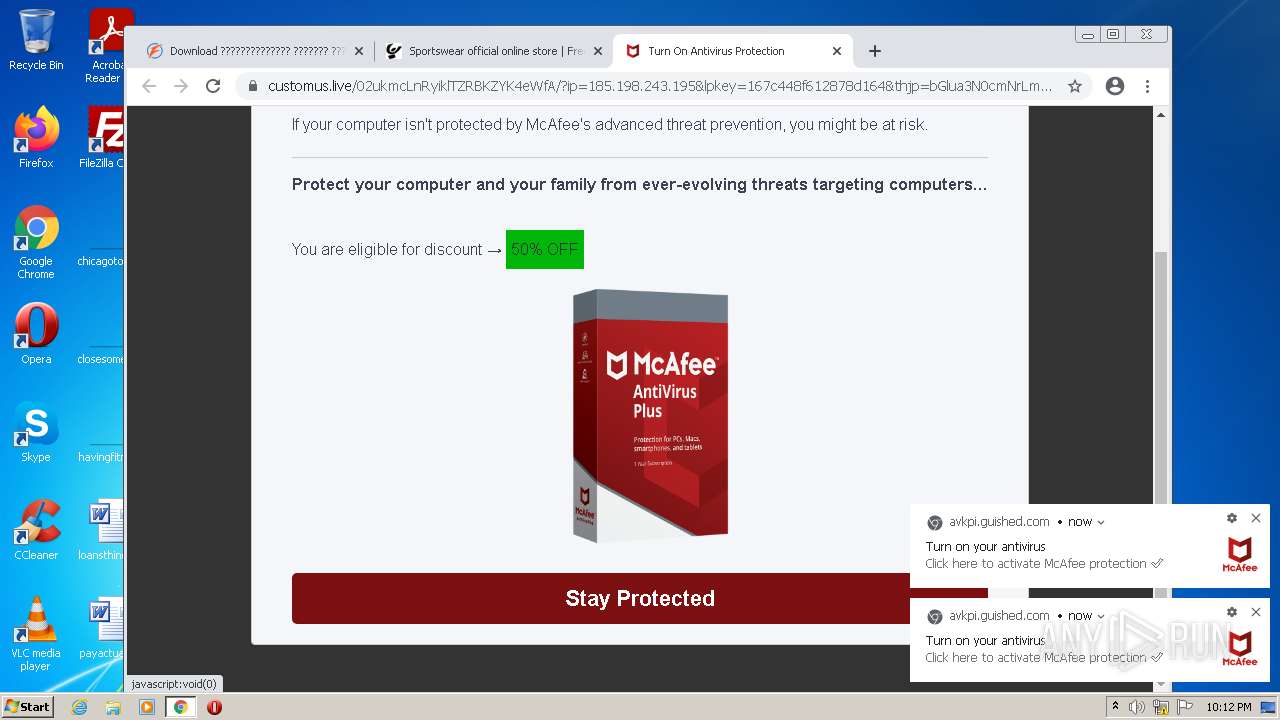
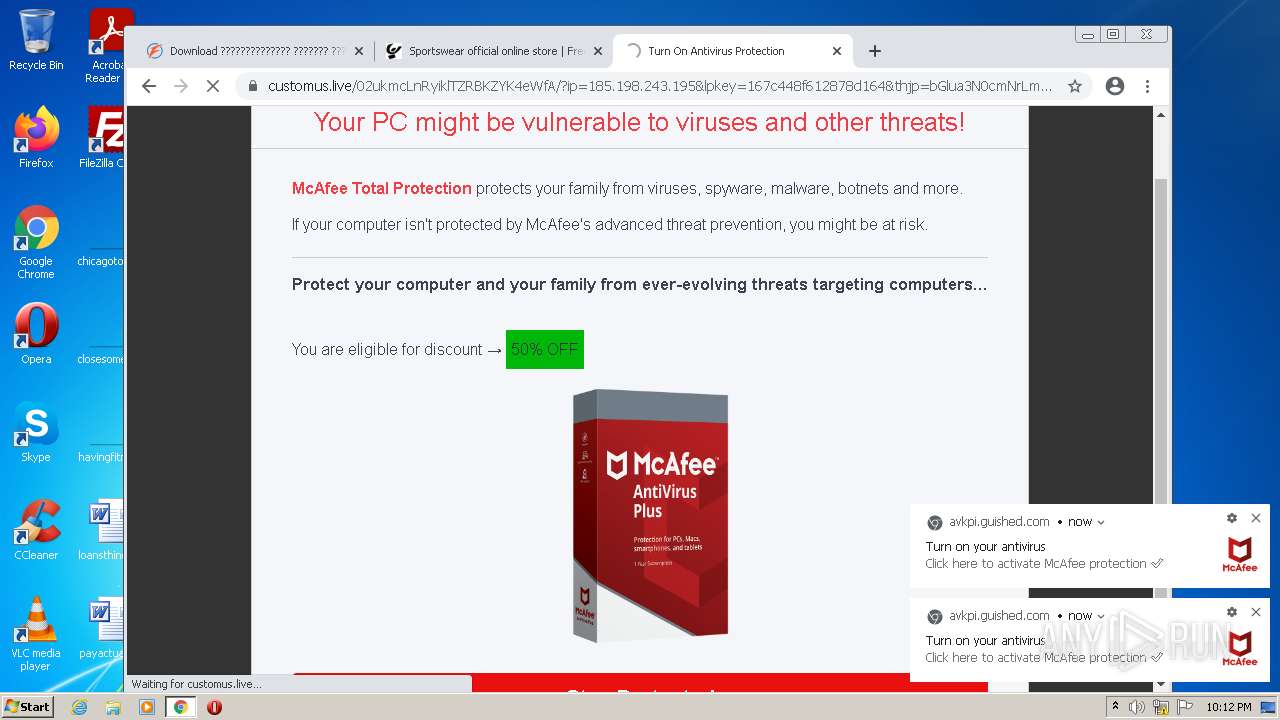
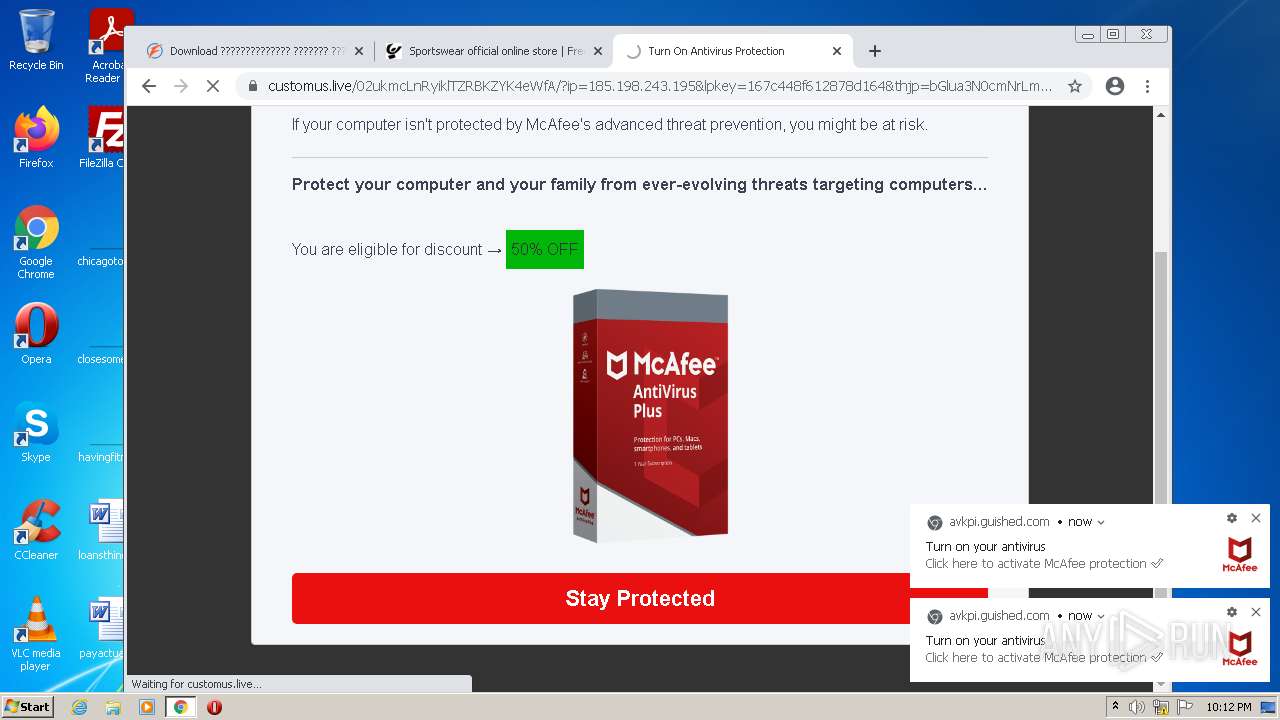
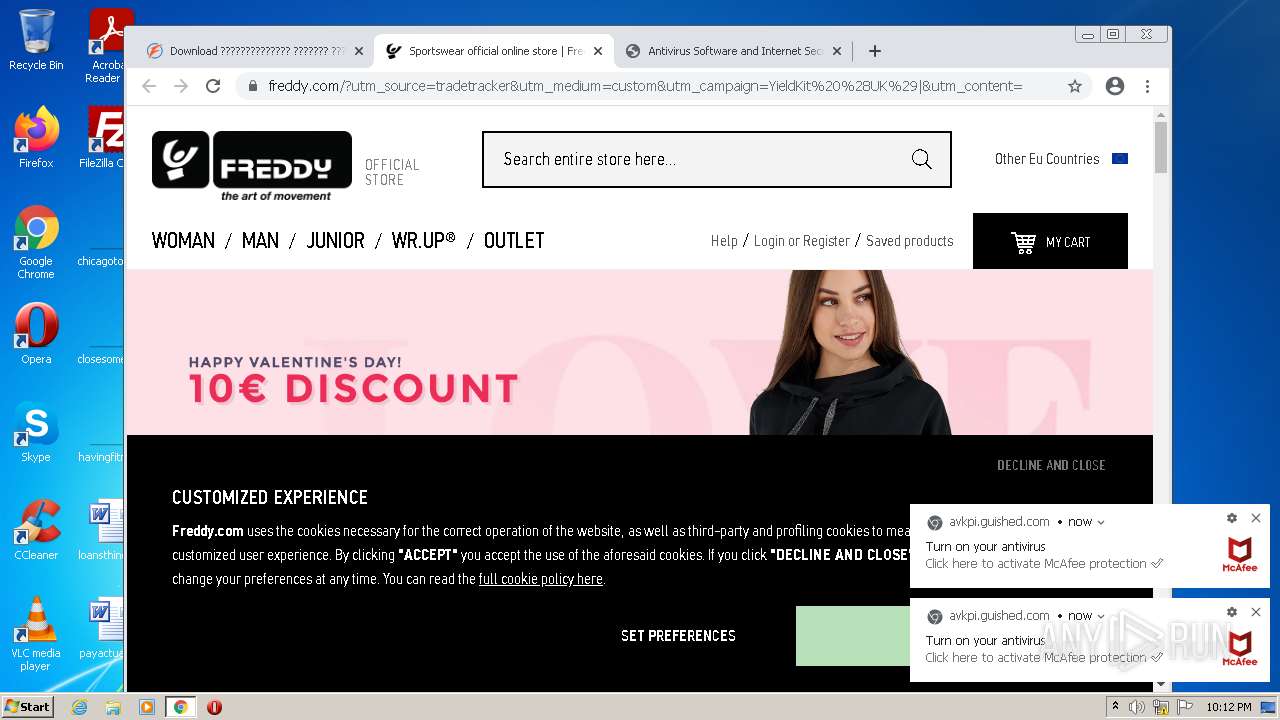
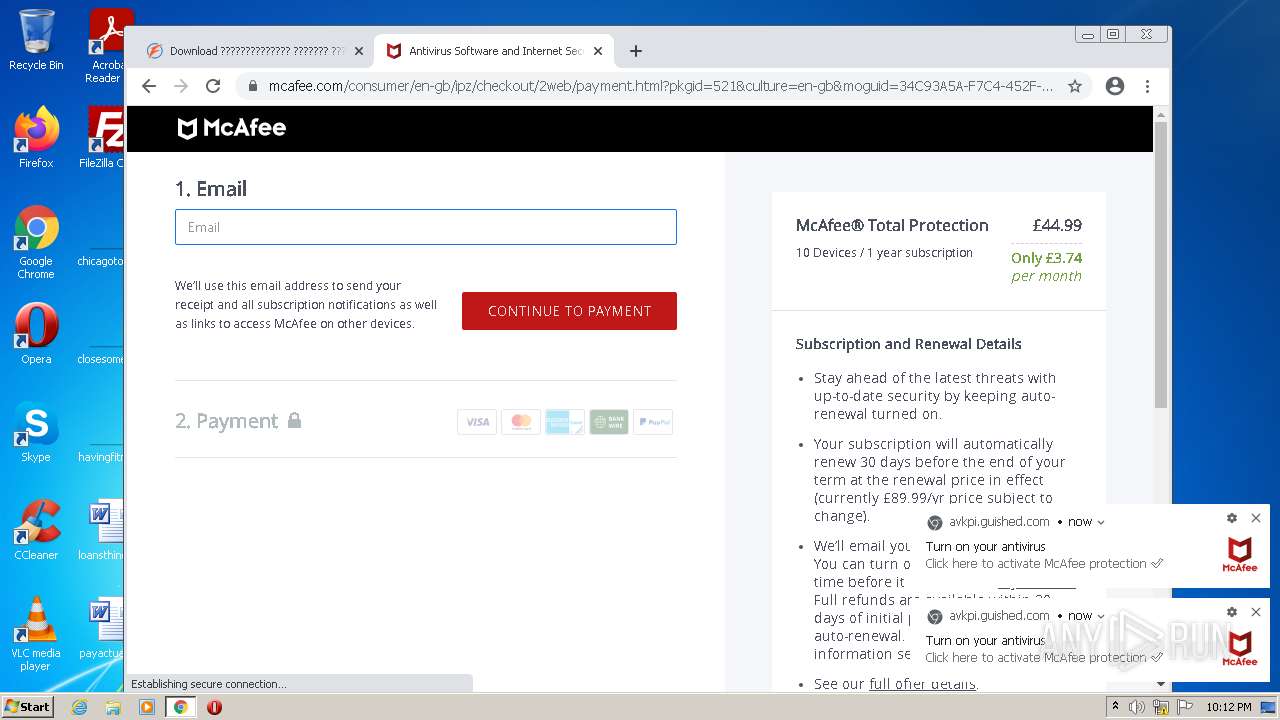
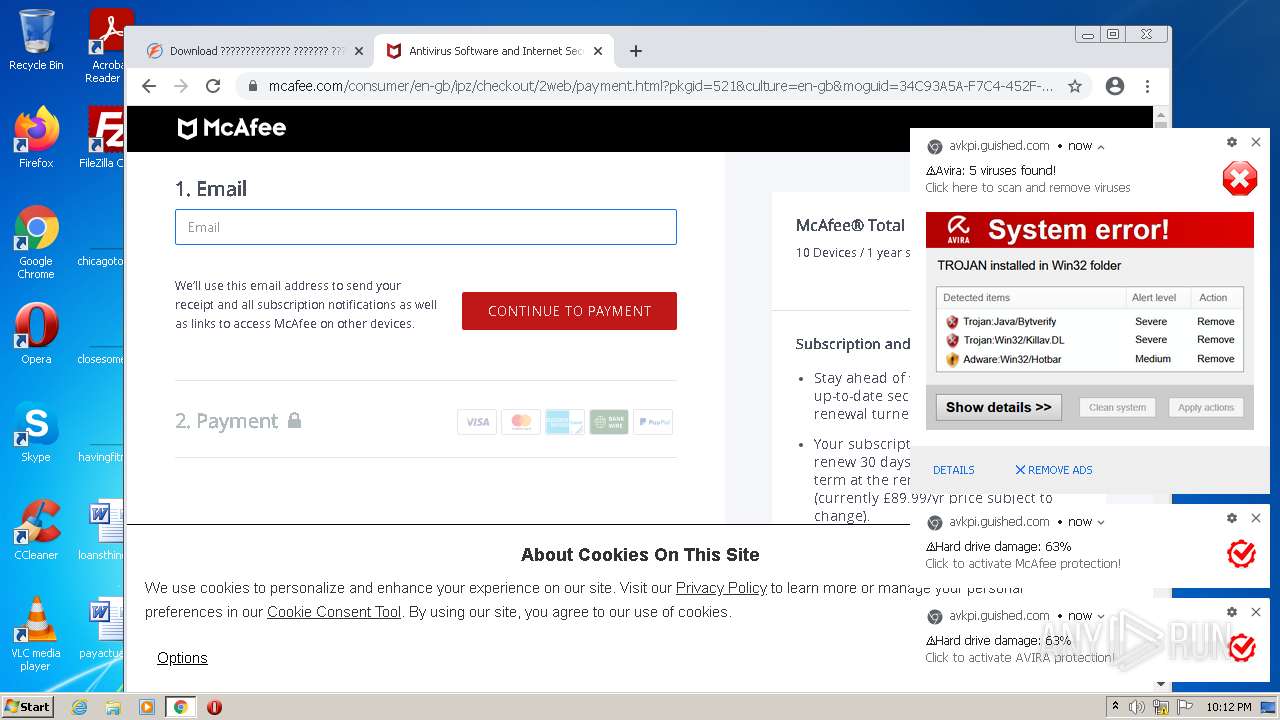
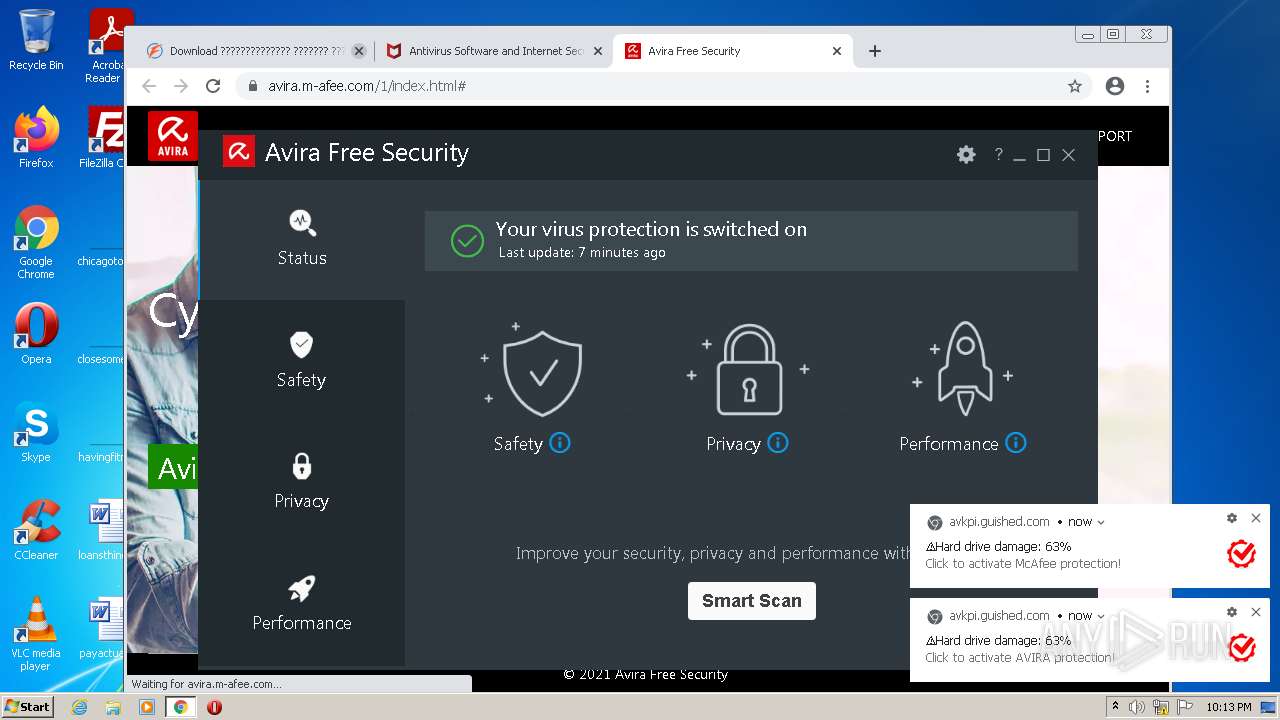
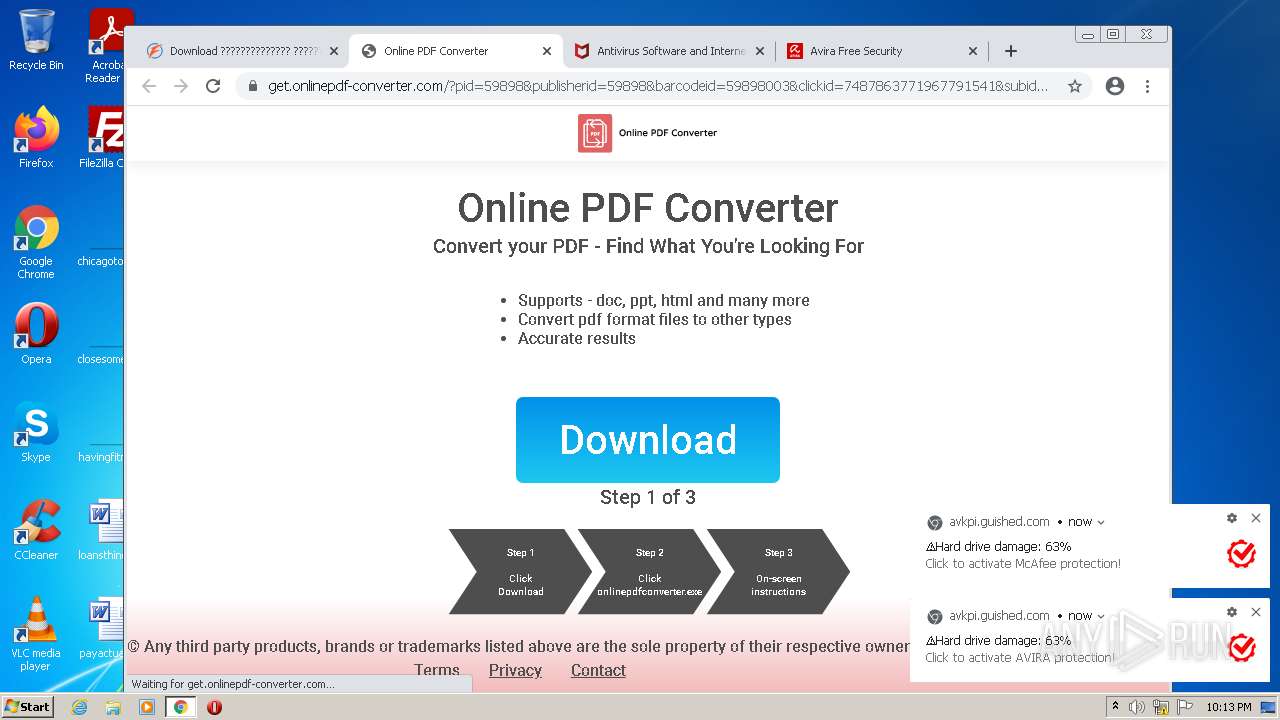
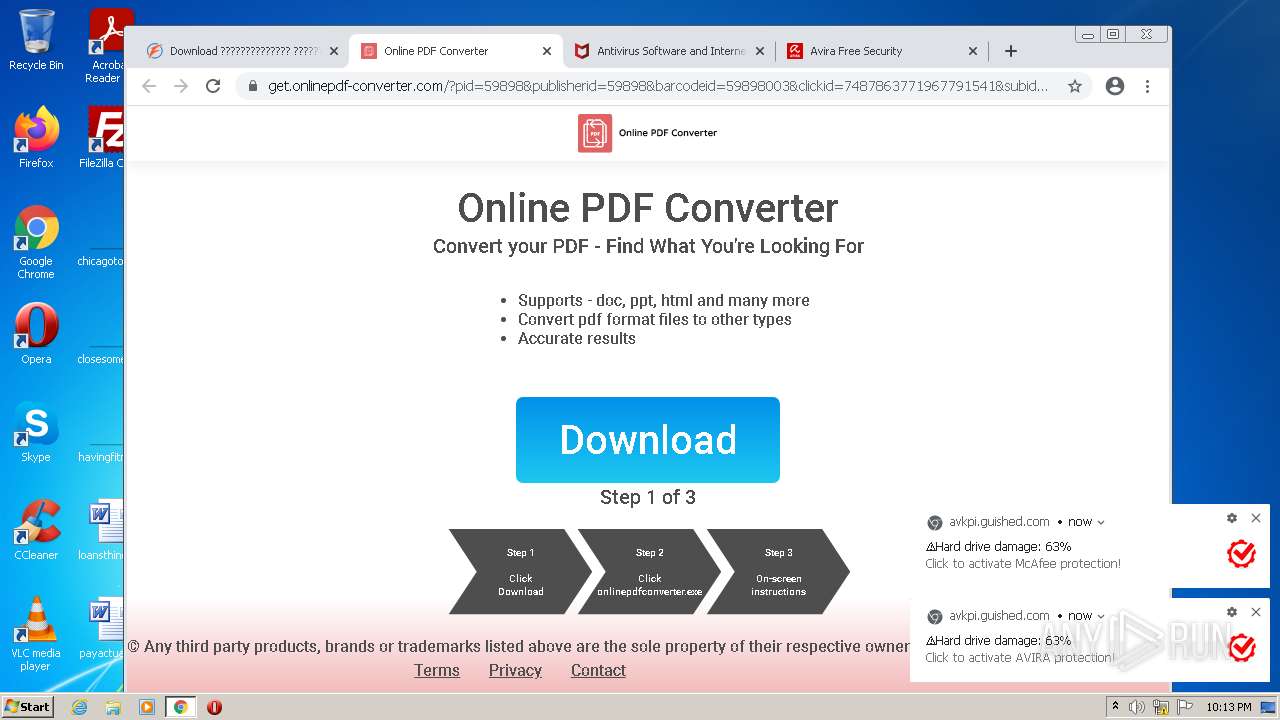
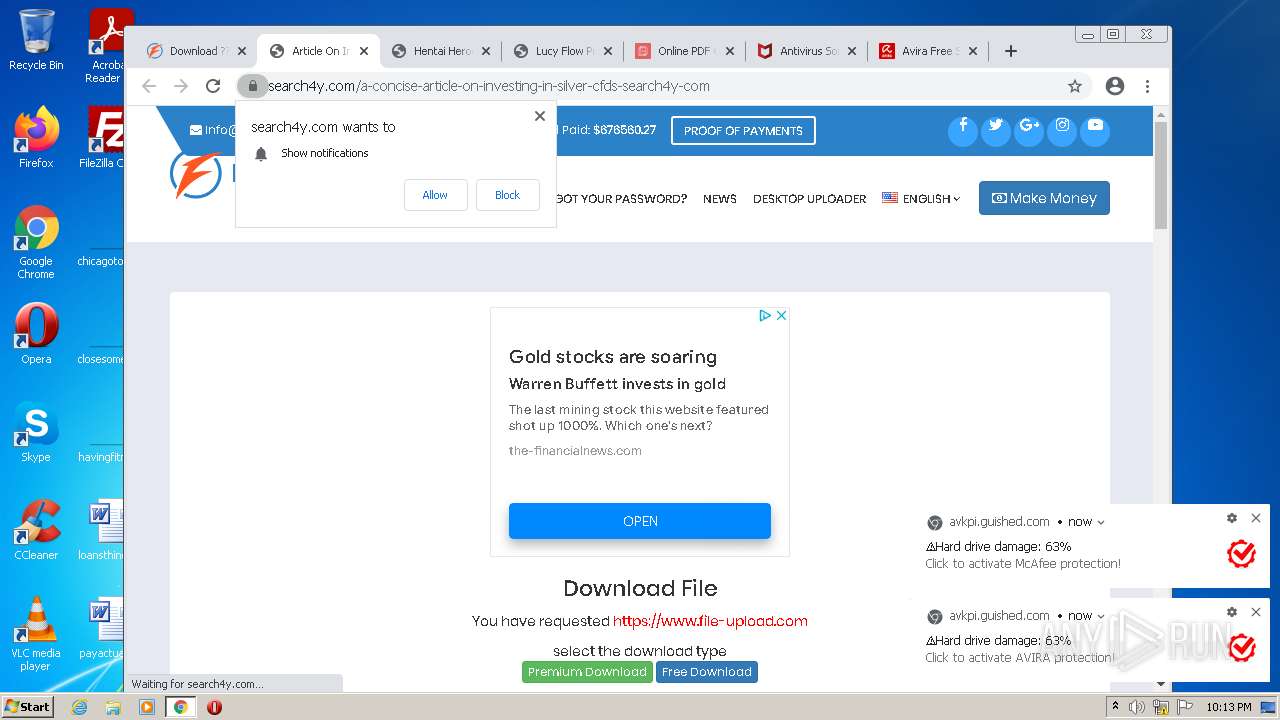
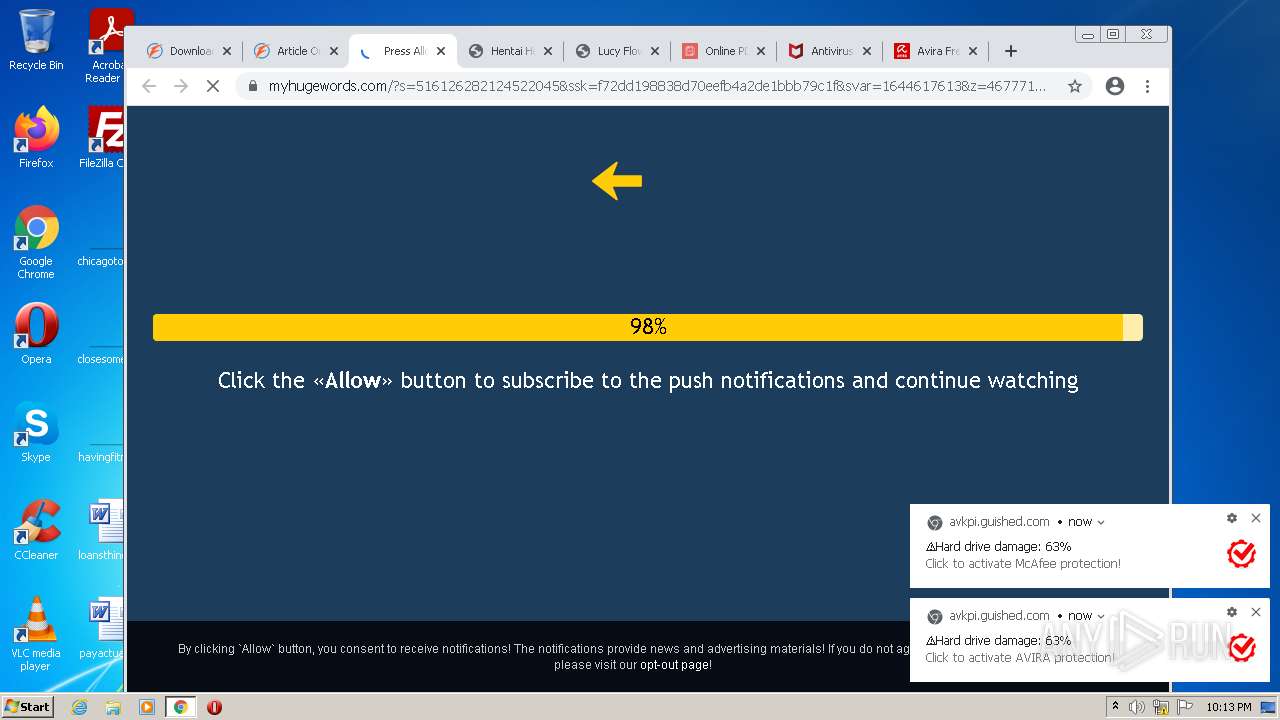
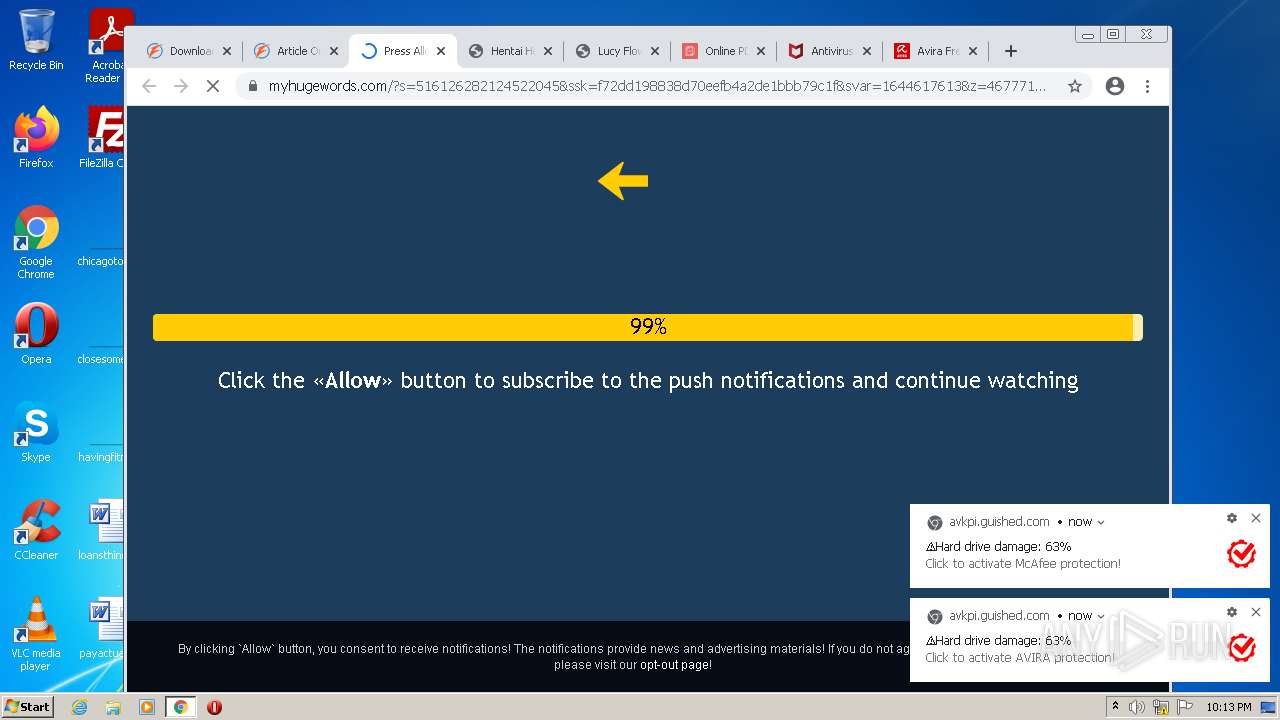
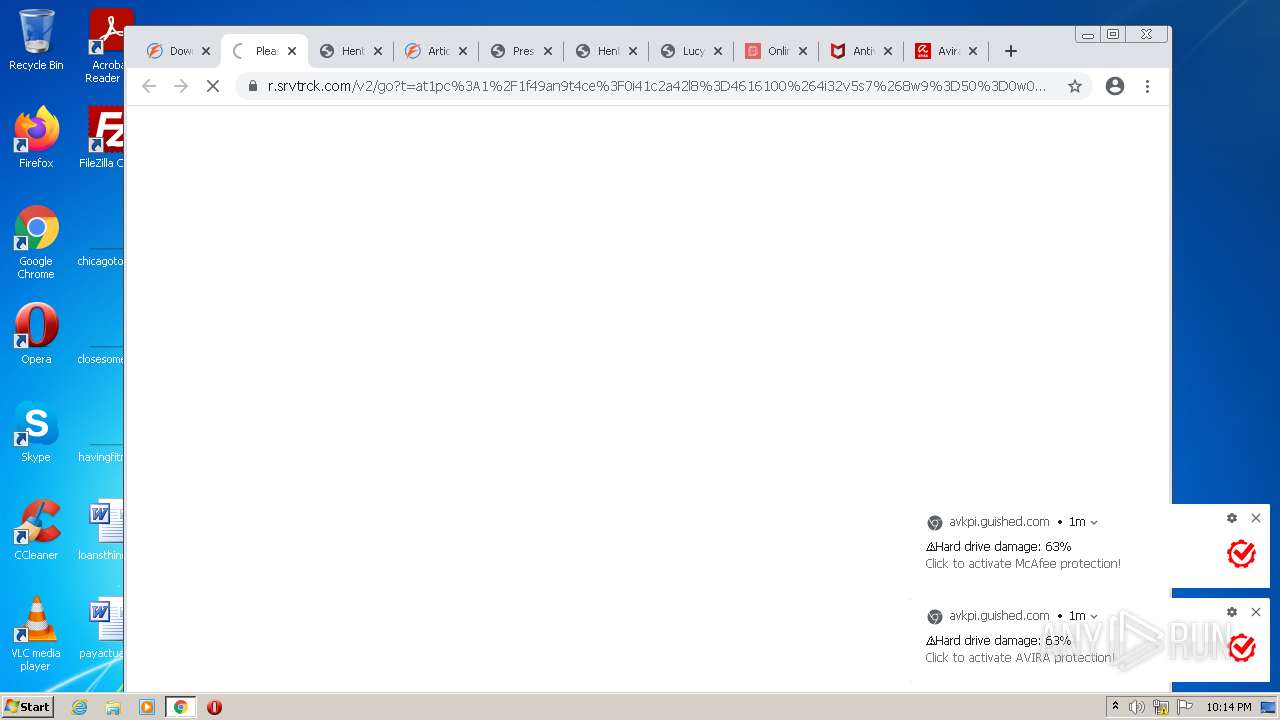
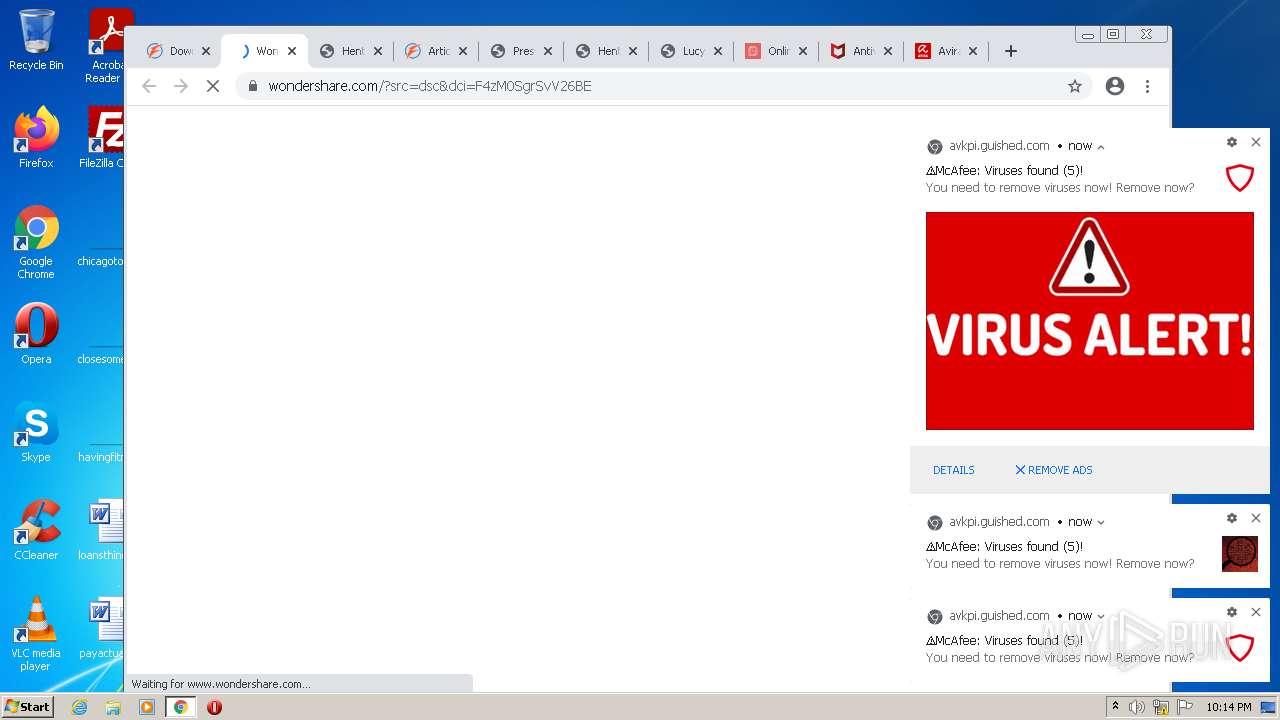
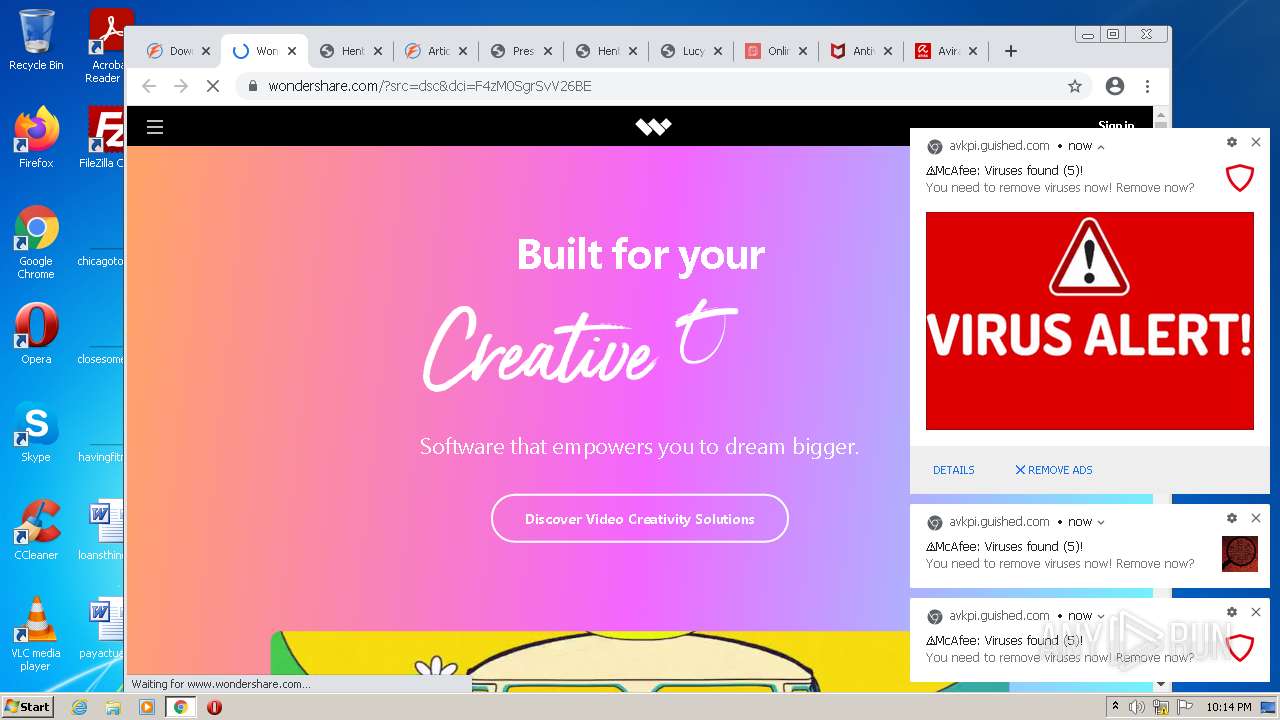
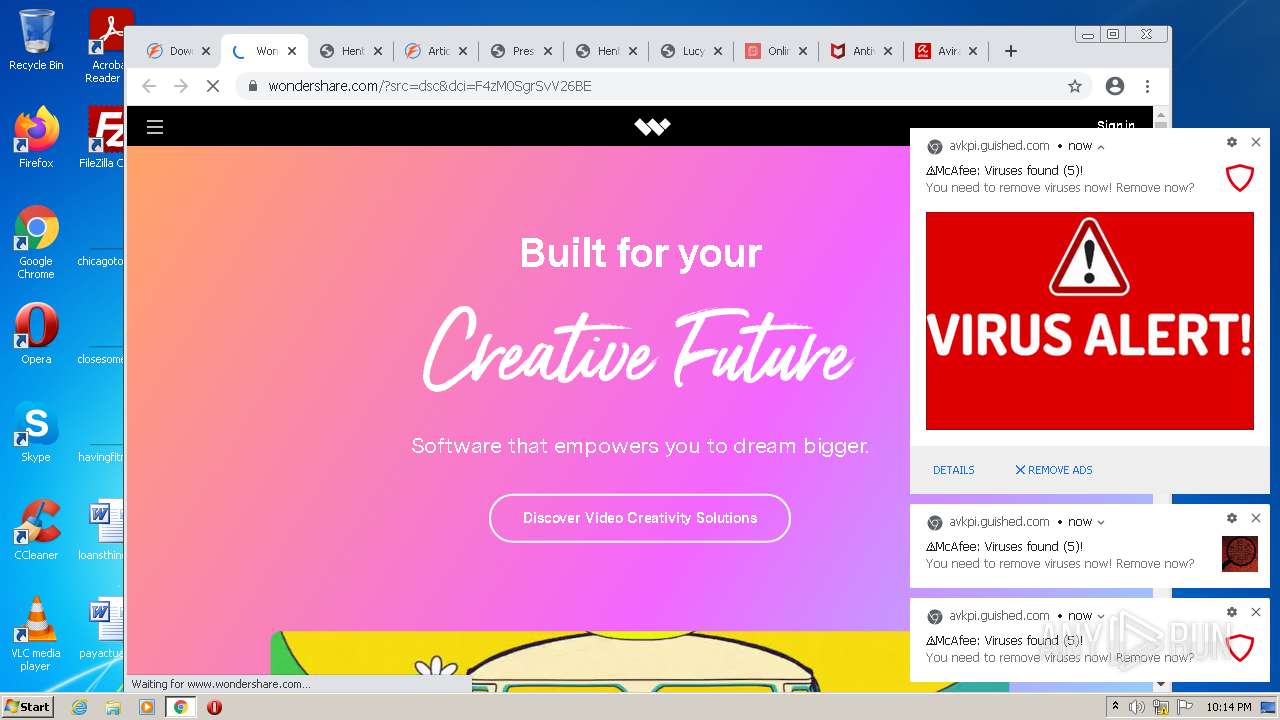
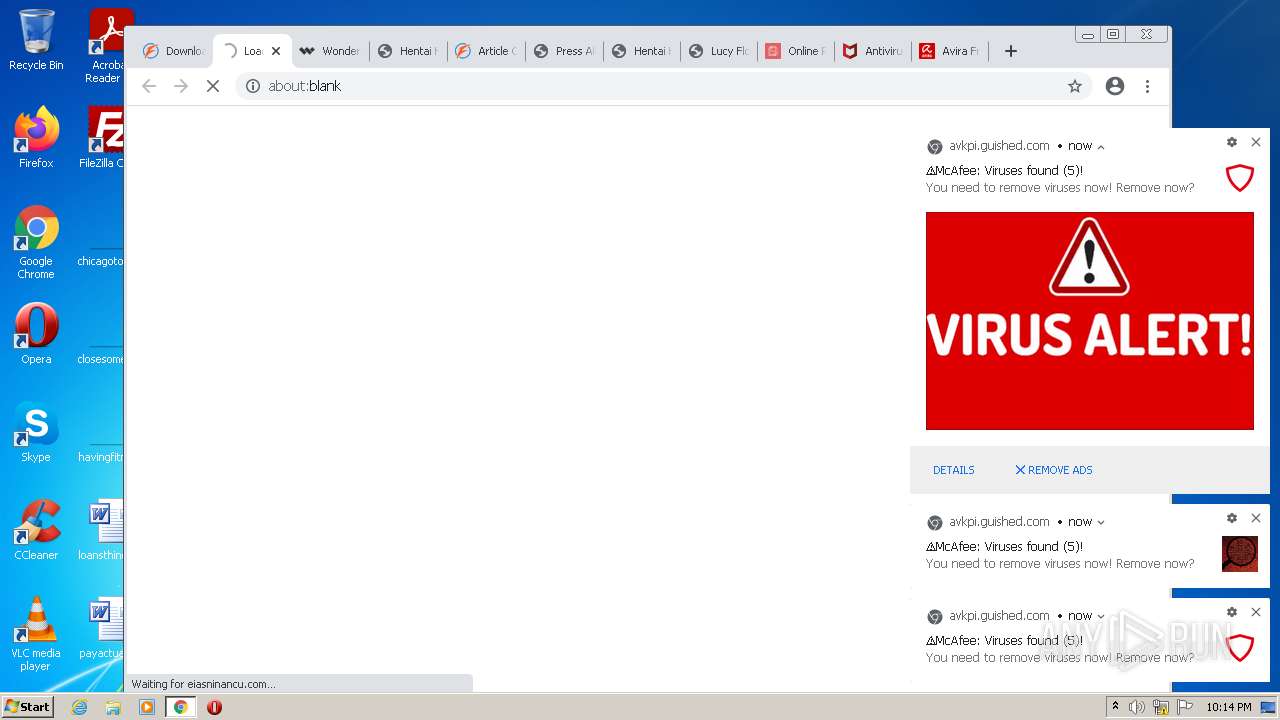
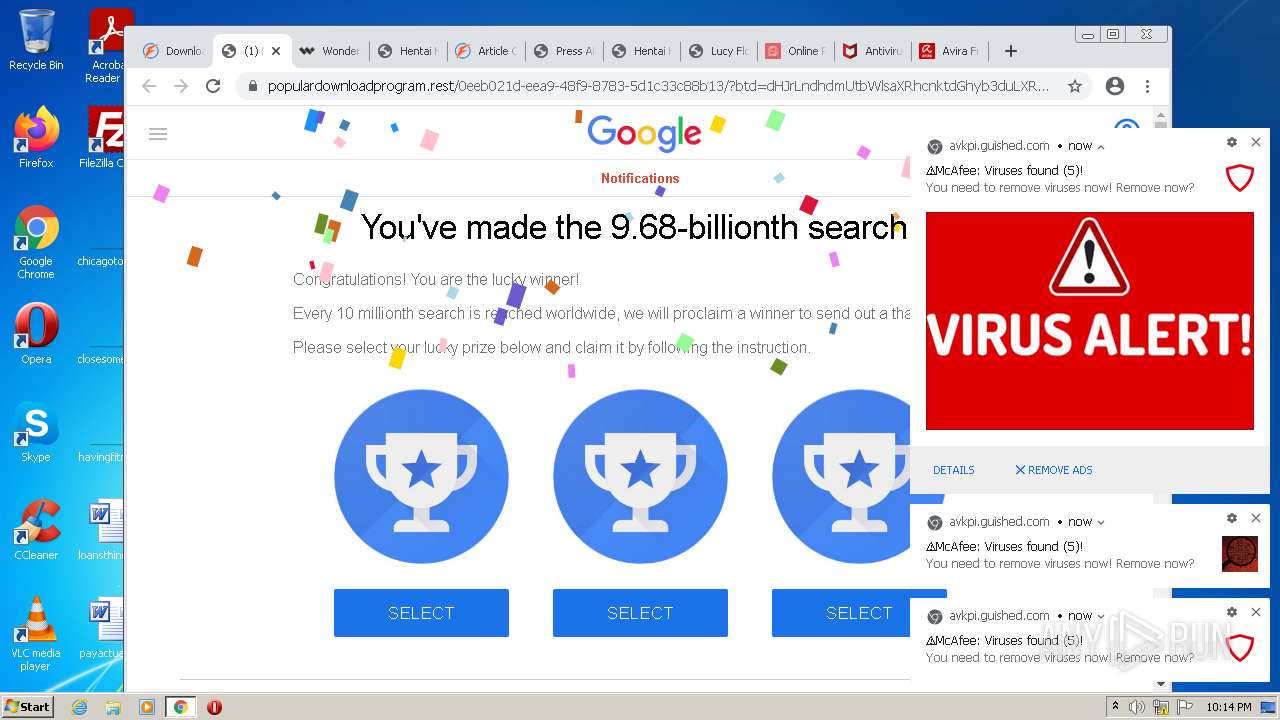
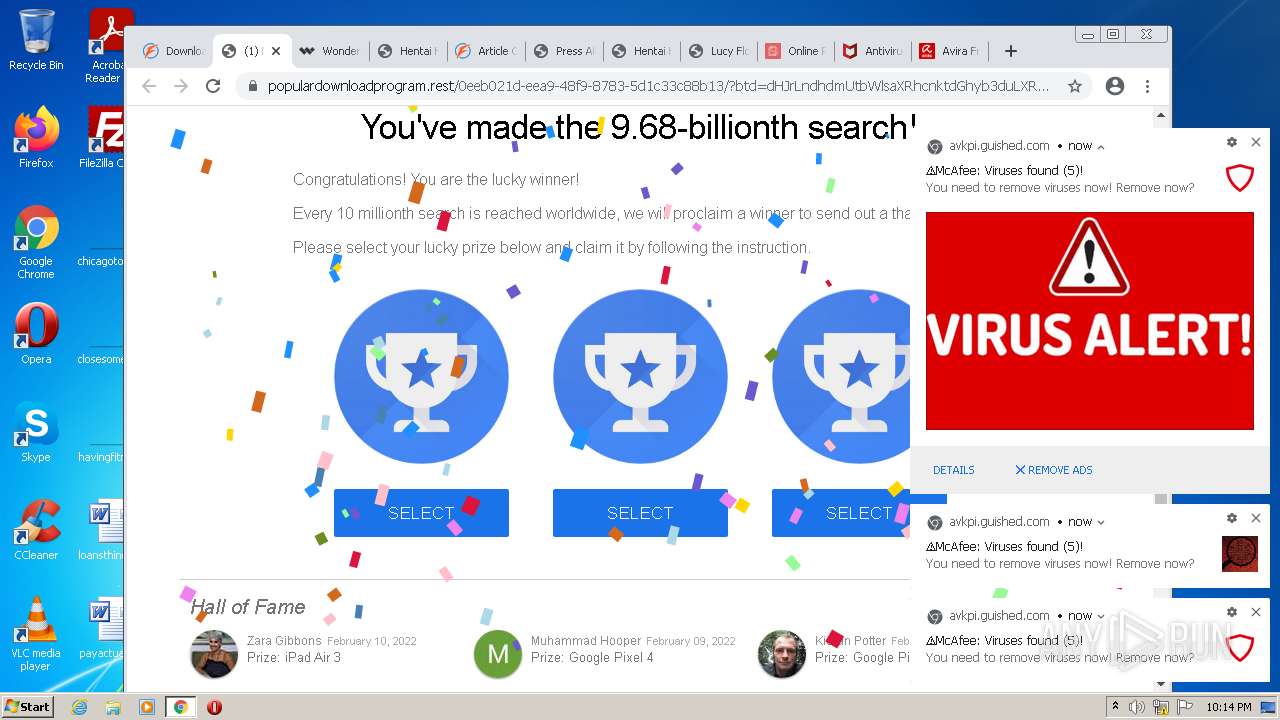
| Verdict: | Malicious activity |
| Analysis date: | February 11, 2022, 22:11:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | A1778B9C081DE3598817D0B1882FB8E1 |
| SHA1: | 82E44BF3C842085AE5441A0CBA4927E695FAFDBA |
| SHA256: | 1E021DD640F43F63A73B13CE63FBC9B3717B1876352AC7B0604F871987965C51 |
| SSDEEP: | 3:N8DSLQnU2HVXEUHS:2OLQntd9y |
MALICIOUS
No malicious indicators.SUSPICIOUS
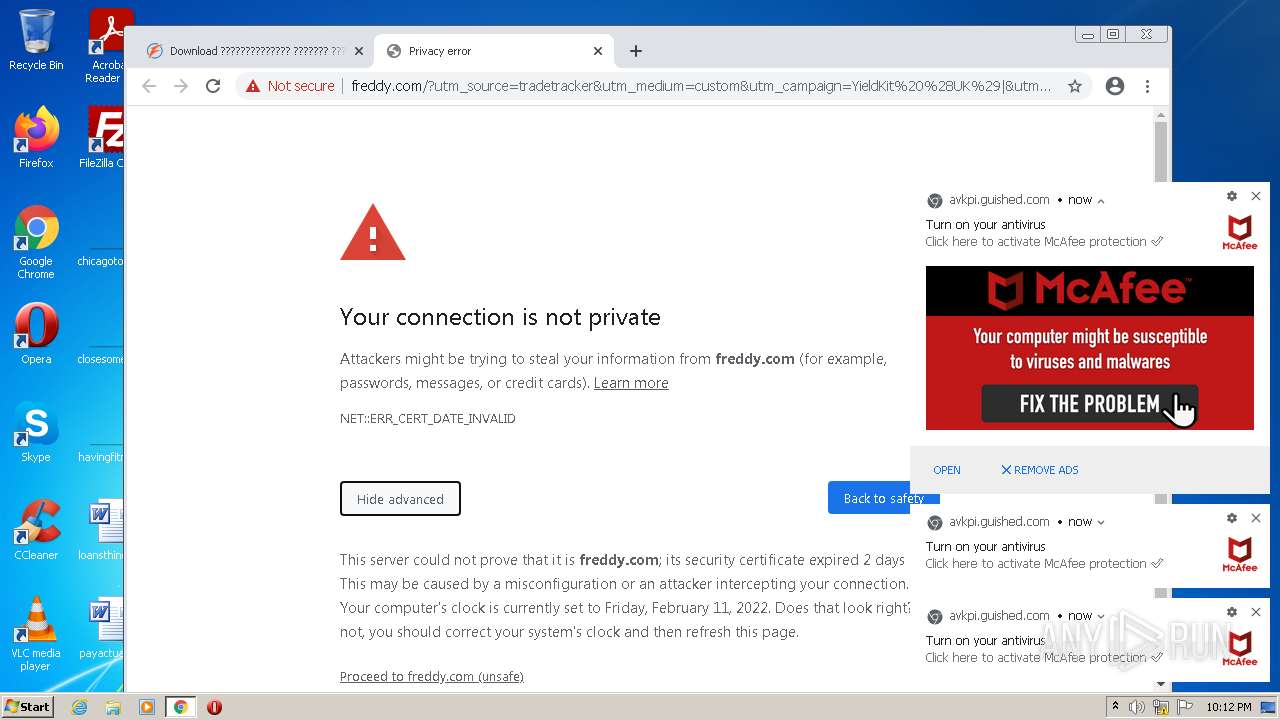
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2684)
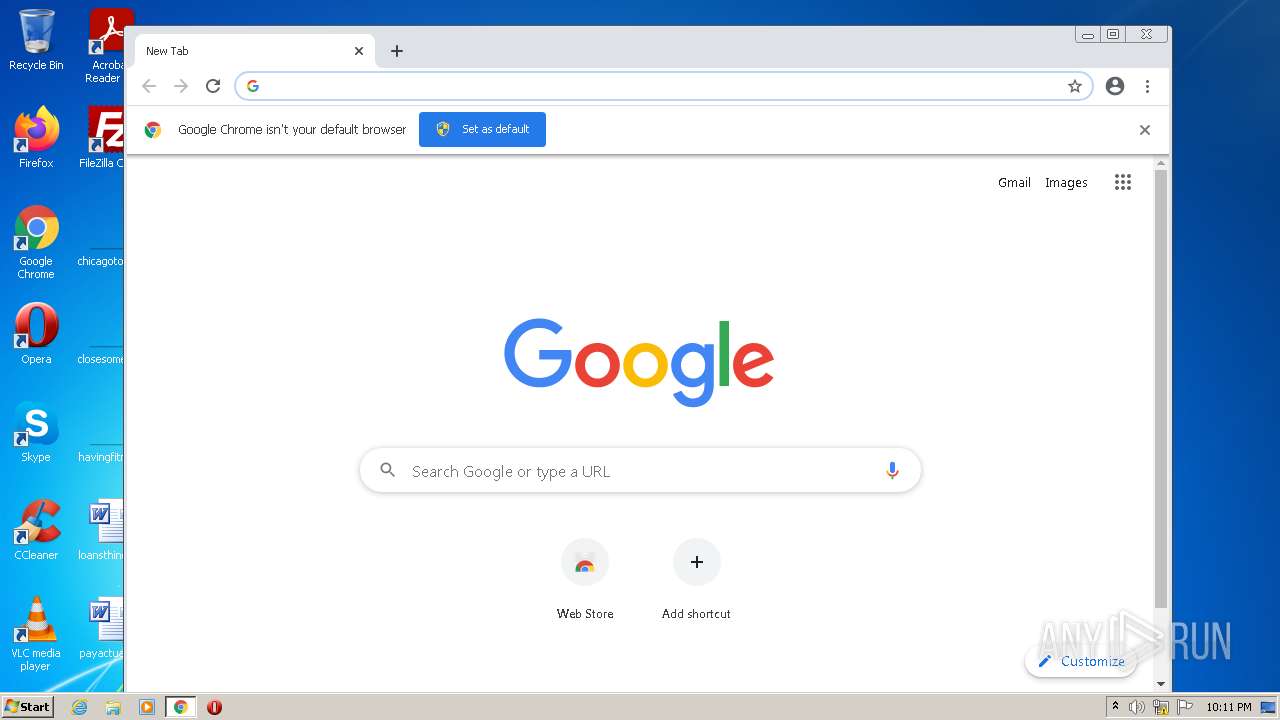
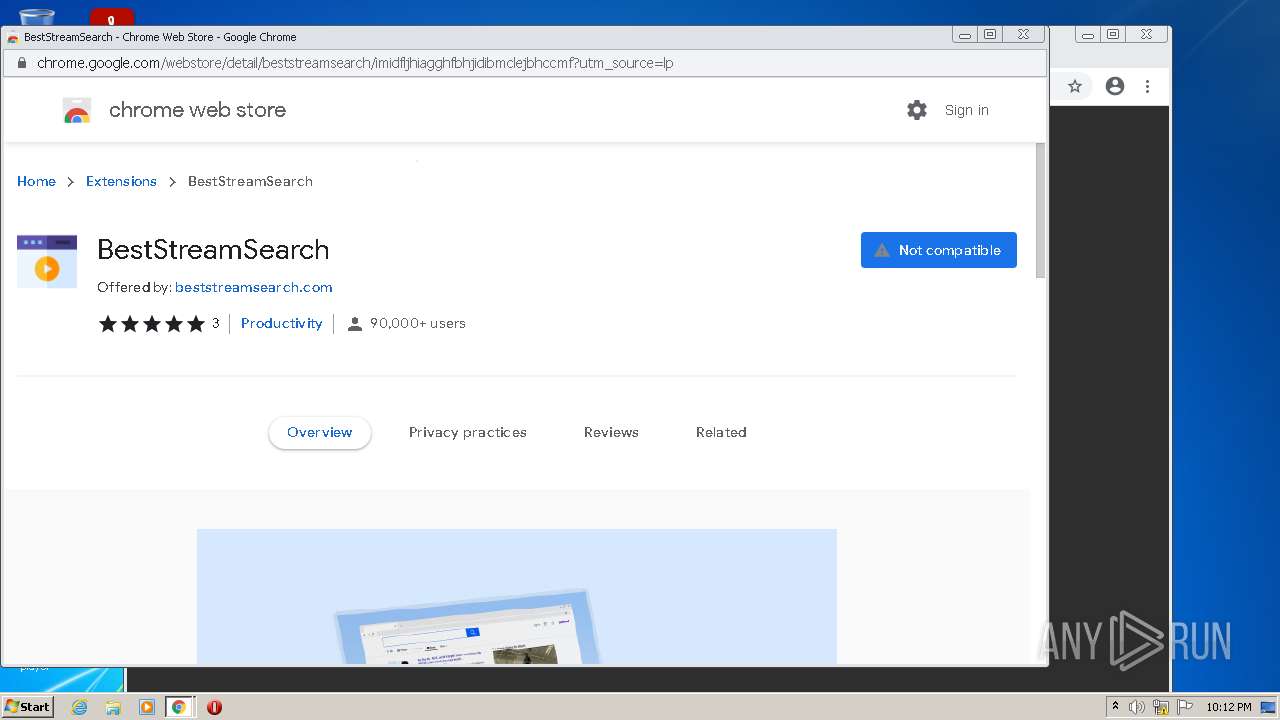
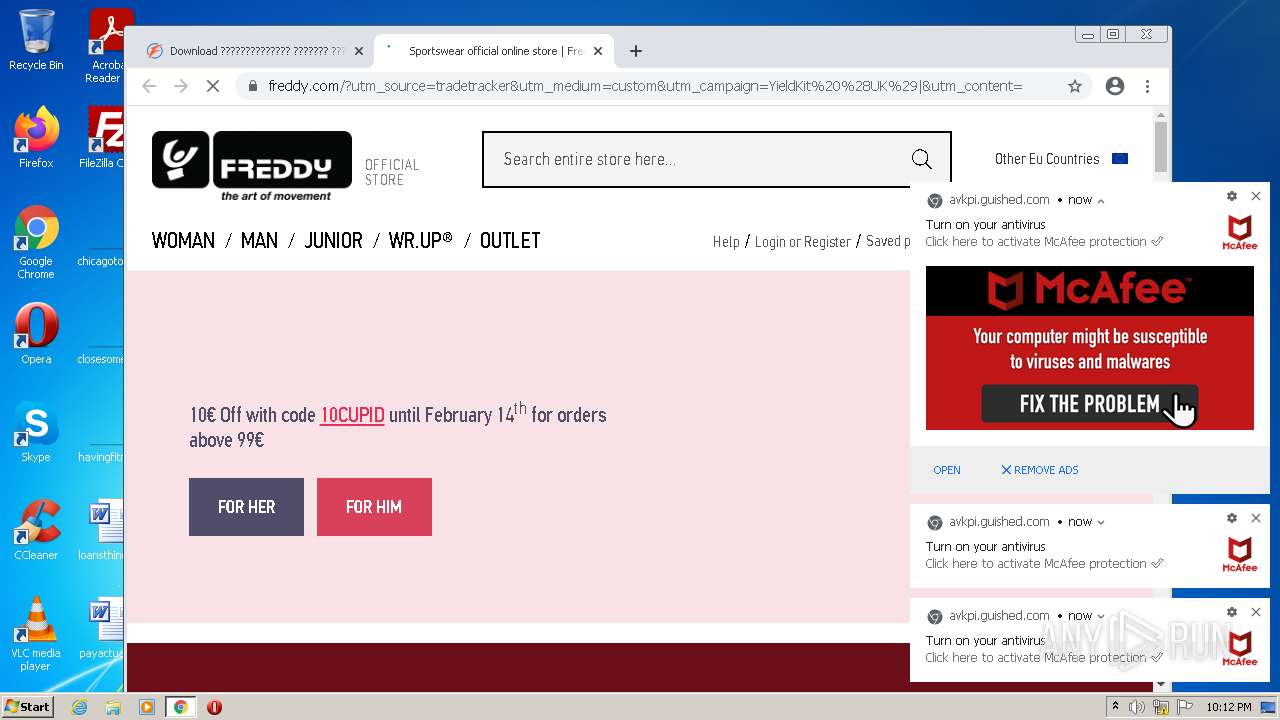
Modifies files in Chrome extension folder
- chrome.exe (PID: 2768)
INFO
Checks supported languages
- iexplore.exe (PID: 1408)
- iexplore.exe (PID: 2684)
- chrome.exe (PID: 2768)
- chrome.exe (PID: 2984)
- chrome.exe (PID: 4052)
- chrome.exe (PID: 2588)
- chrome.exe (PID: 2532)
- chrome.exe (PID: 2252)
- chrome.exe (PID: 3136)
- chrome.exe (PID: 1608)
- chrome.exe (PID: 2248)
- chrome.exe (PID: 2740)
- chrome.exe (PID: 2288)
- chrome.exe (PID: 2836)
- chrome.exe (PID: 2920)
- chrome.exe (PID: 2596)
- chrome.exe (PID: 2320)
- chrome.exe (PID: 1384)
- chrome.exe (PID: 3016)
- chrome.exe (PID: 3524)
- chrome.exe (PID: 3716)
- chrome.exe (PID: 1520)
- chrome.exe (PID: 3112)
- chrome.exe (PID: 1148)
- chrome.exe (PID: 3616)
- chrome.exe (PID: 2704)
- chrome.exe (PID: 2084)
- chrome.exe (PID: 2892)
- chrome.exe (PID: 376)
- chrome.exe (PID: 120)
- chrome.exe (PID: 2524)
- chrome.exe (PID: 3544)
- chrome.exe (PID: 3872)
- chrome.exe (PID: 3352)
- chrome.exe (PID: 1564)
- chrome.exe (PID: 352)
- chrome.exe (PID: 2232)
- chrome.exe (PID: 1876)
- chrome.exe (PID: 2380)
- chrome.exe (PID: 3096)
- chrome.exe (PID: 2140)
- chrome.exe (PID: 3820)
- chrome.exe (PID: 3808)
- chrome.exe (PID: 2896)
- chrome.exe (PID: 888)
- chrome.exe (PID: 2560)
- chrome.exe (PID: 3888)
- chrome.exe (PID: 3136)
- chrome.exe (PID: 4080)
- chrome.exe (PID: 3508)
- chrome.exe (PID: 3956)
- chrome.exe (PID: 3196)
- chrome.exe (PID: 3268)
- chrome.exe (PID: 868)
- chrome.exe (PID: 2384)
- chrome.exe (PID: 2616)
- chrome.exe (PID: 2808)
- chrome.exe (PID: 3068)
- chrome.exe (PID: 1604)
- chrome.exe (PID: 996)
- chrome.exe (PID: 648)
- chrome.exe (PID: 3228)
- chrome.exe (PID: 2184)
- chrome.exe (PID: 552)
- chrome.exe (PID: 760)
- chrome.exe (PID: 612)
- chrome.exe (PID: 2604)
- chrome.exe (PID: 3956)
- chrome.exe (PID: 3836)
- chrome.exe (PID: 3276)
- chrome.exe (PID: 3036)
- chrome.exe (PID: 1256)
- chrome.exe (PID: 3752)
- chrome.exe (PID: 1872)
- chrome.exe (PID: 2980)
- chrome.exe (PID: 3400)
- chrome.exe (PID: 2224)
- chrome.exe (PID: 3984)
- chrome.exe (PID: 2412)
- chrome.exe (PID: 3480)
- chrome.exe (PID: 356)
- chrome.exe (PID: 2284)
- chrome.exe (PID: 2376)
Reads the computer name
- iexplore.exe (PID: 2684)
- iexplore.exe (PID: 1408)
- chrome.exe (PID: 2768)
- chrome.exe (PID: 4052)
- chrome.exe (PID: 2588)
- chrome.exe (PID: 2596)
- chrome.exe (PID: 2248)
- chrome.exe (PID: 2084)
- chrome.exe (PID: 376)
- chrome.exe (PID: 1148)
- chrome.exe (PID: 2140)
- chrome.exe (PID: 888)
Reads internet explorer settings
- iexplore.exe (PID: 2684)
Application launched itself
- iexplore.exe (PID: 1408)
- chrome.exe (PID: 2768)
Changes internet zones settings
- iexplore.exe (PID: 1408)
Reads settings of System Certificates
- iexplore.exe (PID: 1408)
- chrome.exe (PID: 2588)
Manual execution by user
- chrome.exe (PID: 2768)
Checks Windows Trust Settings
- iexplore.exe (PID: 1408)
Reads the date of Windows installation
- iexplore.exe (PID: 1408)
- chrome.exe (PID: 2084)
Reads the hosts file
- chrome.exe (PID: 2768)
- chrome.exe (PID: 2588)
Creates files in the user directory
- chrome.exe (PID: 2768)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
119
Monitored processes
83
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 120 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,5509684971983030803,1474634586997911607,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=28 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3508 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,5509684971983030803,1474634586997911607,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=34 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3496 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1060,5509684971983030803,1474634586997911607,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=6480 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1060,5509684971983030803,1474634586997911607,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3352 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,5509684971983030803,1474634586997911607,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=64 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5824 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 612 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,5509684971983030803,1474634586997911607,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=67 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4400 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 648 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,5509684971983030803,1474634586997911607,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=63 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5568 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,5509684971983030803,1474634586997911607,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=58 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5052 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 868 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,5509684971983030803,1474634586997911607,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=52 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1892 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 888 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=audio.mojom.AudioService --field-trial-handle=1060,5509684971983030803,1474634586997911607,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=audio --mojo-platform-channel-handle=1788 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
544
Text files
350
Unknown types
49
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2768 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6206DF18-AD0.pma | — | |
MD5:— | SHA256:— | |||
| 1408 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 1408 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{886D101D-8B87-11EC-A20C-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 1408 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 1408 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 1408 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFFAB6A3353853089C.TMP | gmc | |
MD5:— | SHA256:— | |||
| 1408 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\{91D51731-8B87-11EC-A20C-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 1408 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\RecoveryStore.{42C873D0-1D90-11EB-BA2C-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 1408 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 1408 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
53
TCP/UDP connections
349
DNS requests
229
Threats
2
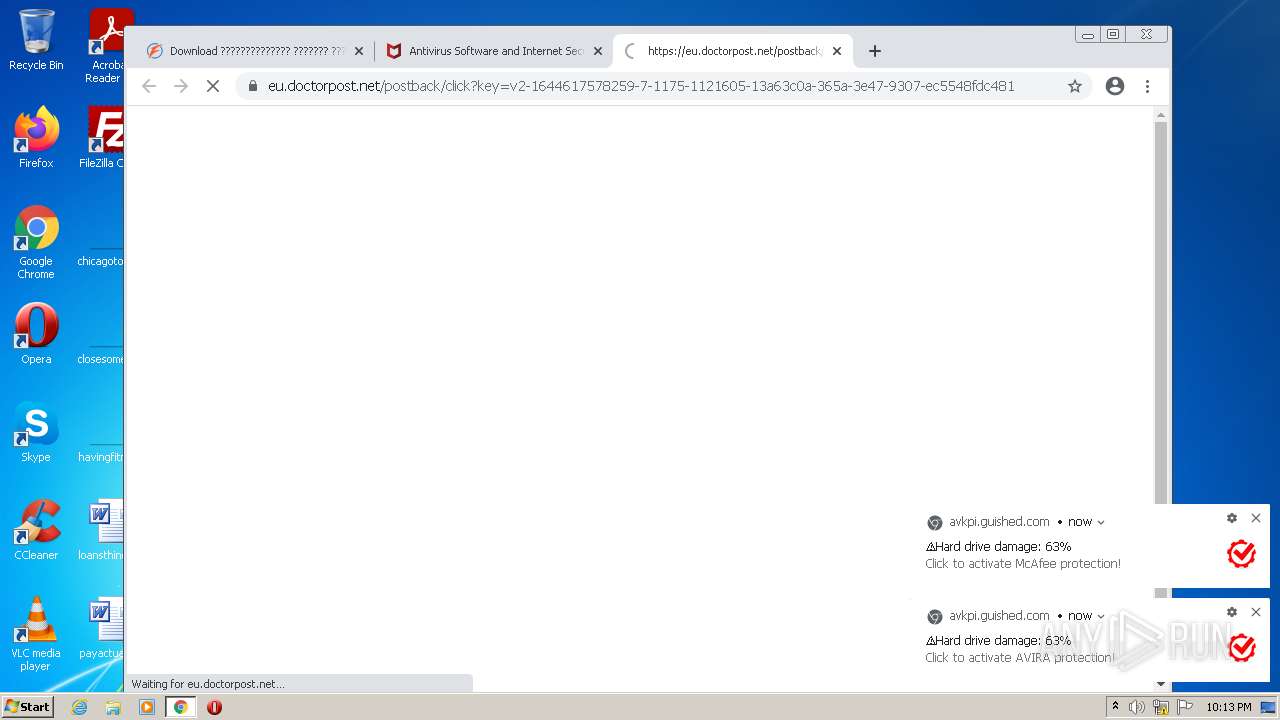
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
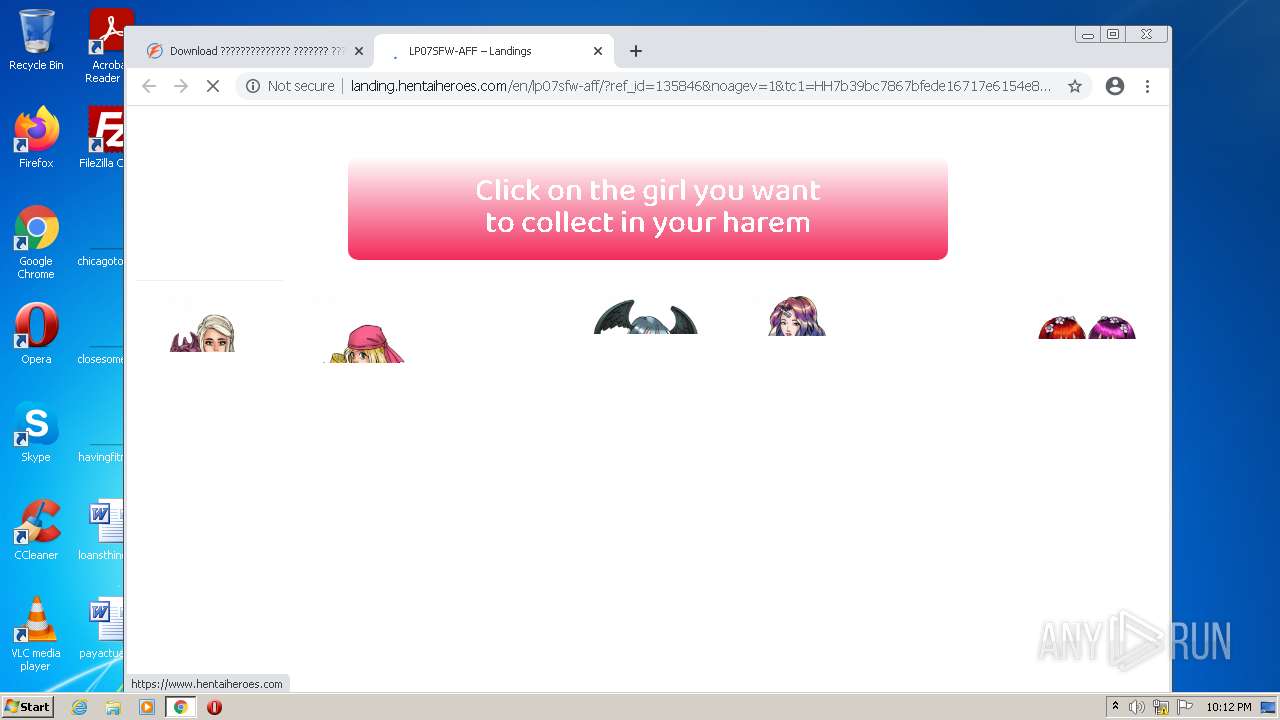
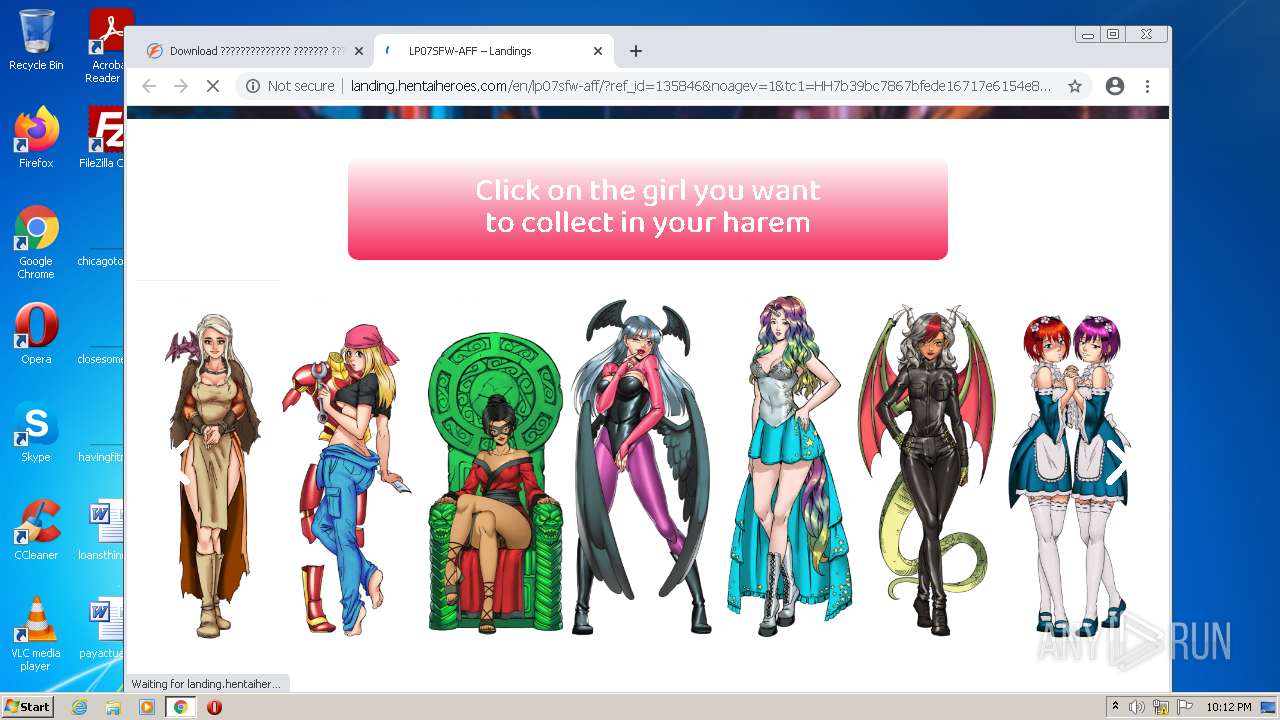
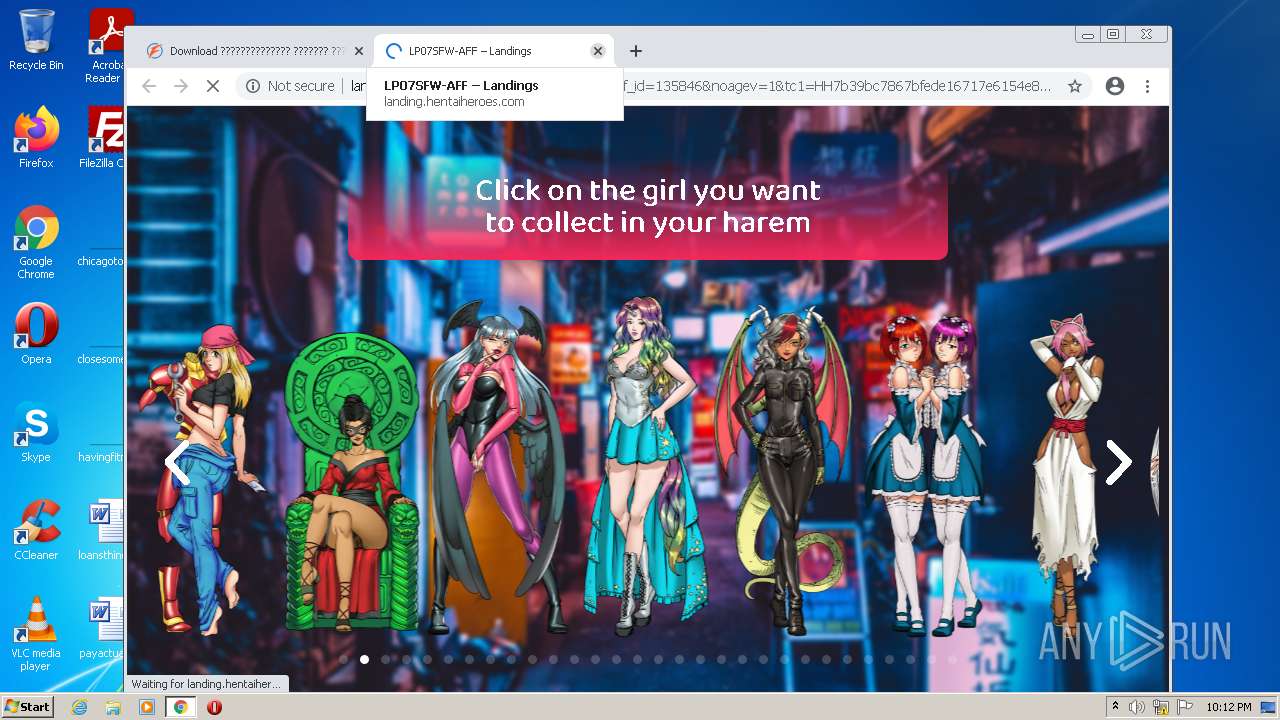
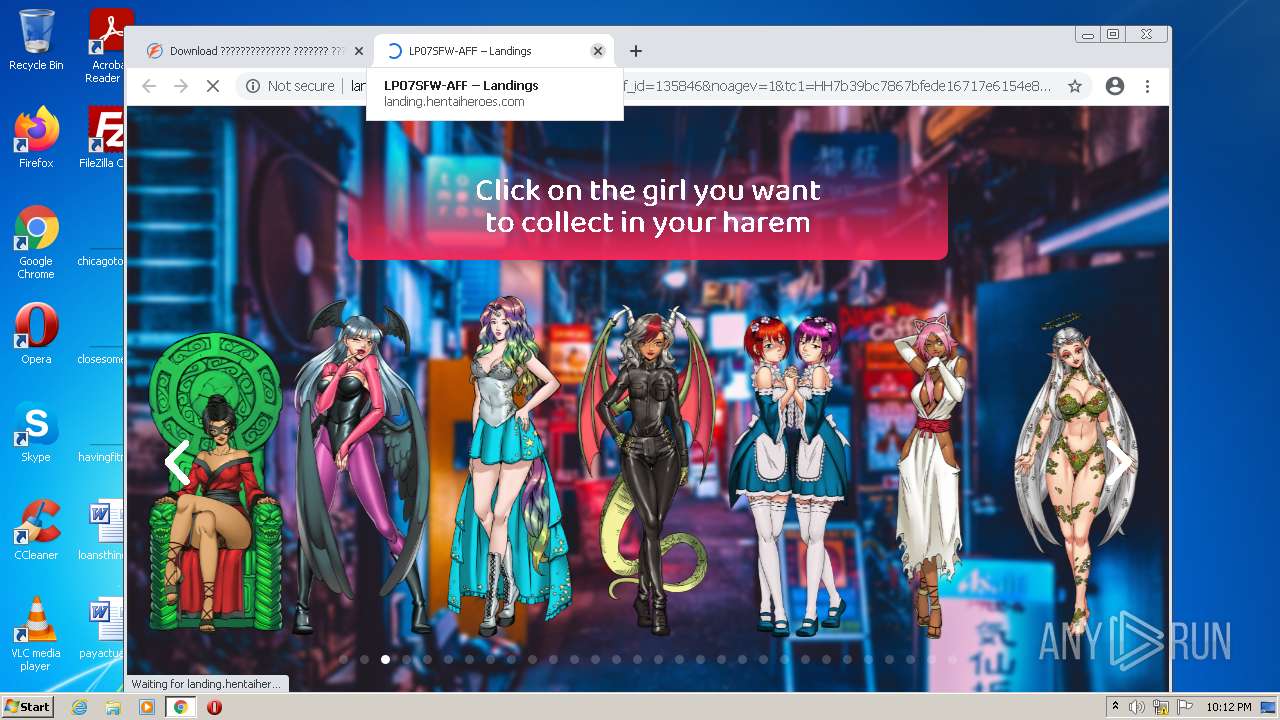
2588 | chrome.exe | GET | 302 | 144.217.67.42:80 | http://landing.hentaiheroes.com/wp-content/uploads/2019/02/ShinjukuBG_Desktop.jpg | CA | — | — | whitelisted |
924 | svchost.exe | HEAD | 200 | 74.125.105.7:80 | http://r2---sn-aigl6ns6.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3?cms_redirect=yes&mh=bj&mip=185.198.243.195&mm=28&mn=sn-aigl6ns6&ms=nvh&mt=1644617303&mv=m&mvi=2&pl=24&rmhost=r3---sn-aigl6ns6.gvt1.com&shardbypass=yes&smhost=r3---sn-aigl6nsk.gvt1.com | US | — | — | whitelisted |
924 | svchost.exe | HEAD | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | — | — | whitelisted |
924 | svchost.exe | HEAD | 302 | 142.250.181.238:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | — | — | whitelisted |
924 | svchost.exe | GET | 206 | 74.125.105.7:80 | http://r2---sn-aigl6ns6.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3?cms_redirect=yes&mh=bj&mip=185.198.243.195&mm=28&mn=sn-aigl6ns6&ms=nvh&mt=1644617303&mv=m&mvi=2&pl=24&rmhost=r3---sn-aigl6ns6.gvt1.com&shardbypass=yes&smhost=r3---sn-aigl6nsk.gvt1.com | US | binary | 9.45 Kb | whitelisted |
2588 | chrome.exe | GET | 302 | 142.250.186.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 558 b | whitelisted |
924 | svchost.exe | GET | 206 | 74.125.105.7:80 | http://r2---sn-aigl6ns6.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3?cms_redirect=yes&mh=bj&mip=185.198.243.195&mm=28&mn=sn-aigl6ns6&ms=nvh&mt=1644617303&mv=m&mvi=2&pl=24&rmhost=r3---sn-aigl6ns6.gvt1.com&shardbypass=yes&smhost=r3---sn-aigl6nsk.gvt1.com | US | binary | 9.45 Kb | whitelisted |
924 | svchost.exe | GET | 302 | 142.250.181.238:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | html | 614 b | whitelisted |
924 | svchost.exe | GET | 206 | 74.125.105.7:80 | http://r2---sn-aigl6ns6.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3?cms_redirect=yes&mh=bj&mip=185.198.243.195&mm=28&mn=sn-aigl6ns6&ms=nvh&mt=1644617303&mv=m&mvi=2&pl=24&rmhost=r3---sn-aigl6ns6.gvt1.com&shardbypass=yes&smhost=r3---sn-aigl6nsk.gvt1.com | US | binary | 20.7 Kb | whitelisted |
924 | svchost.exe | GET | 302 | 142.250.181.238:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | html | 614 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1408 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1408 | iexplore.exe | 23.32.238.178:80 | ctldl.windowsupdate.com | XO Communications | US | suspicious |
2588 | chrome.exe | 142.250.185.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2684 | iexplore.exe | 188.114.97.7:443 | www.file-upload.com | Cloudflare Inc | US | malicious |
2588 | chrome.exe | 142.250.186.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
2588 | chrome.exe | 172.217.16.142:443 | apis.google.com | Google Inc. | US | whitelisted |
2588 | chrome.exe | 142.250.186.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2588 | chrome.exe | 216.58.212.131:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1408 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2588 | chrome.exe | 142.250.185.228:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.file-upload.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
clients2.google.com |
| whitelisted |
www.google.com |
| malicious |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET DNS Query for .cc TLD |
— | — | Potentially Bad Traffic | ET DNS Query for .cc TLD |