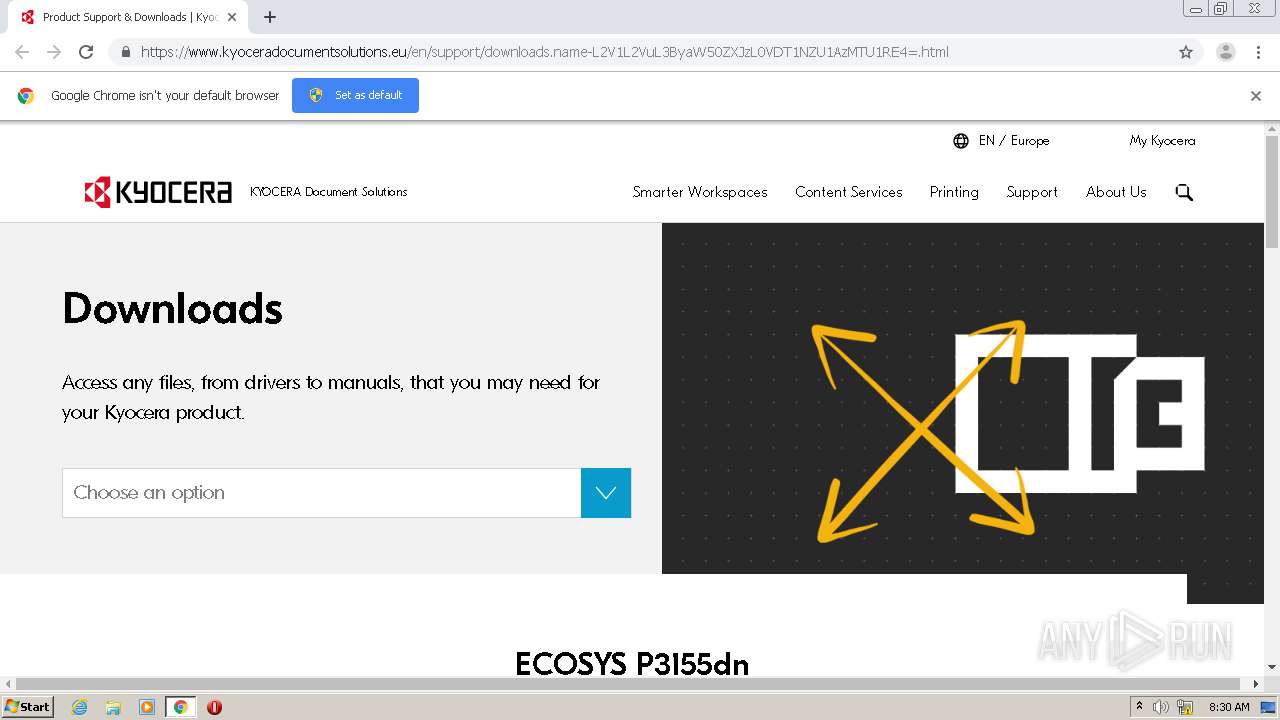
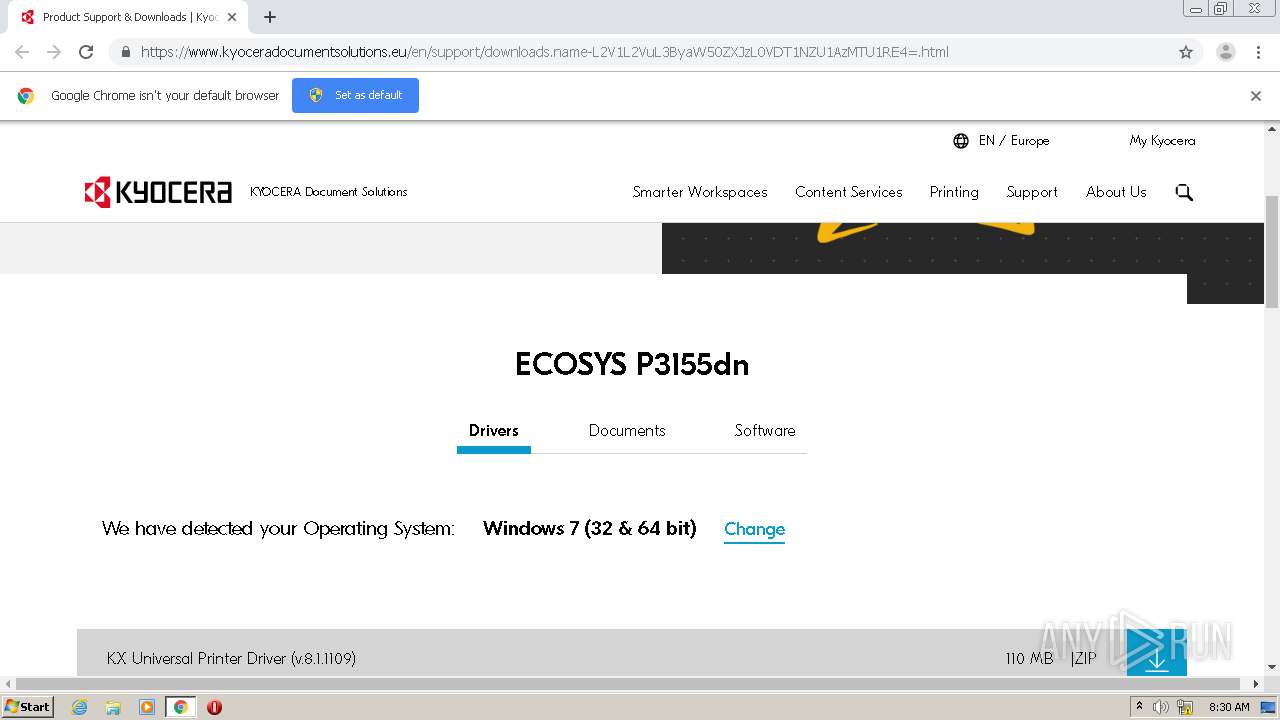
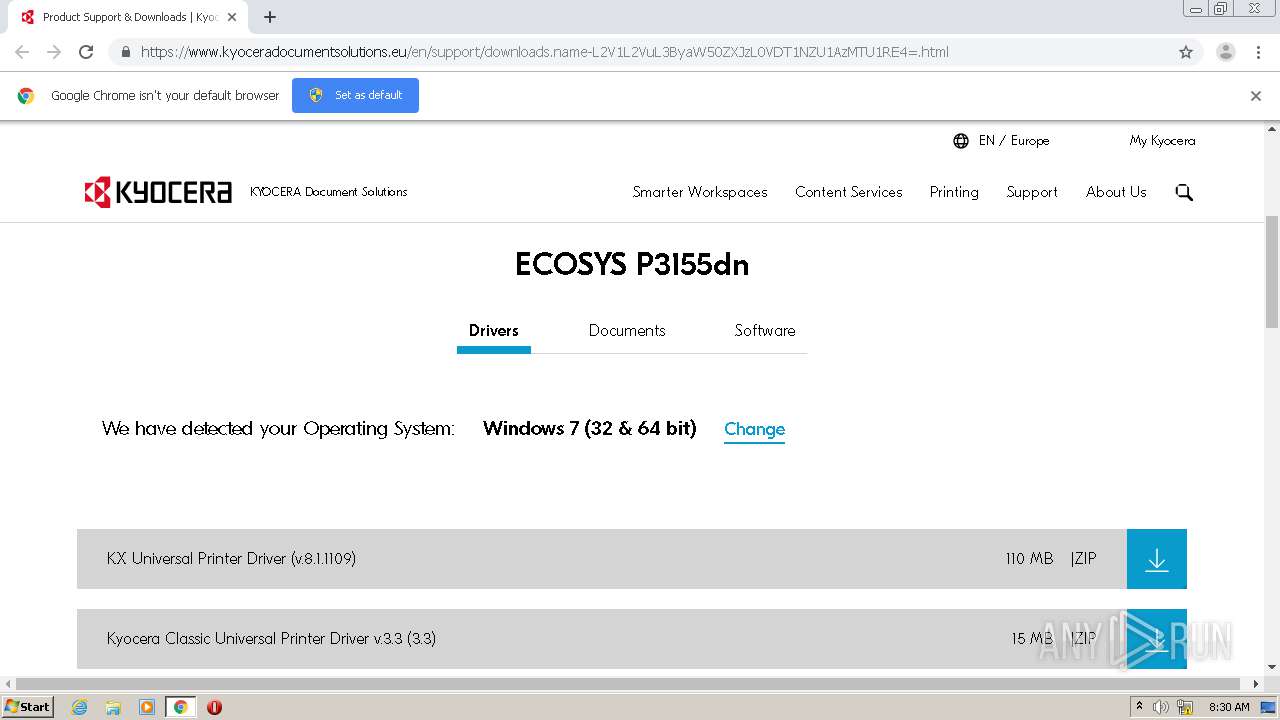
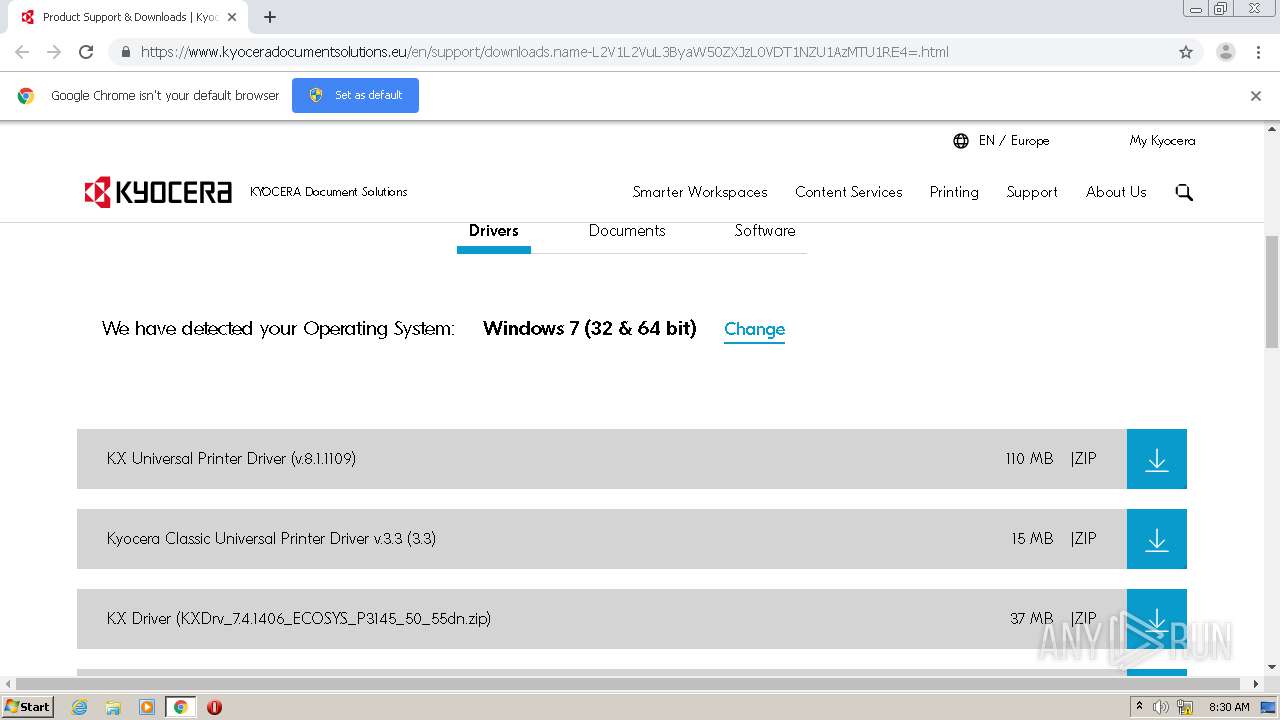
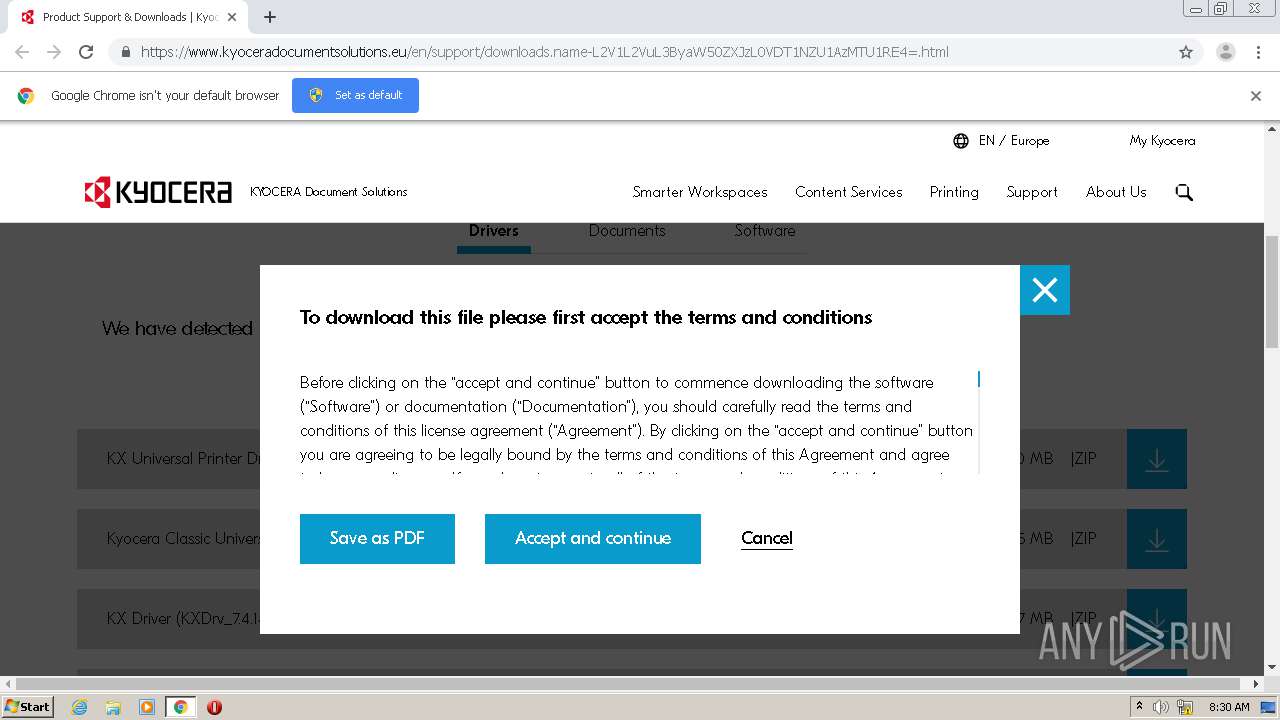
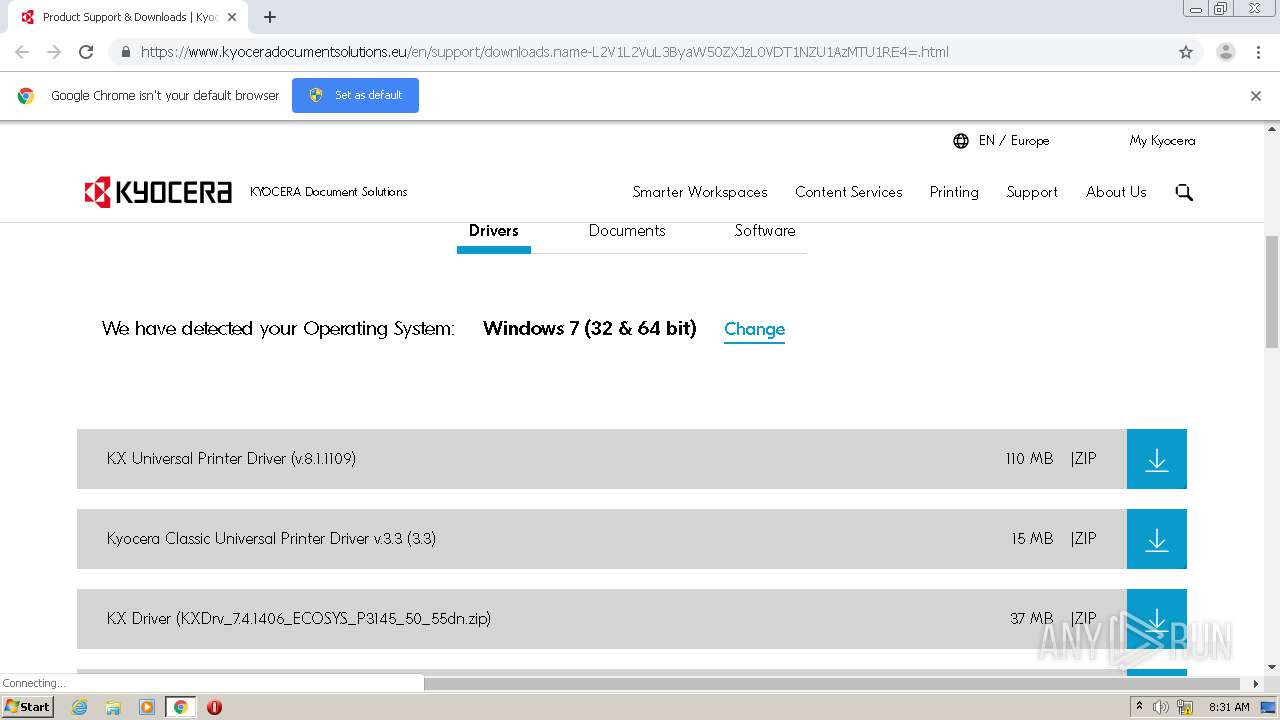
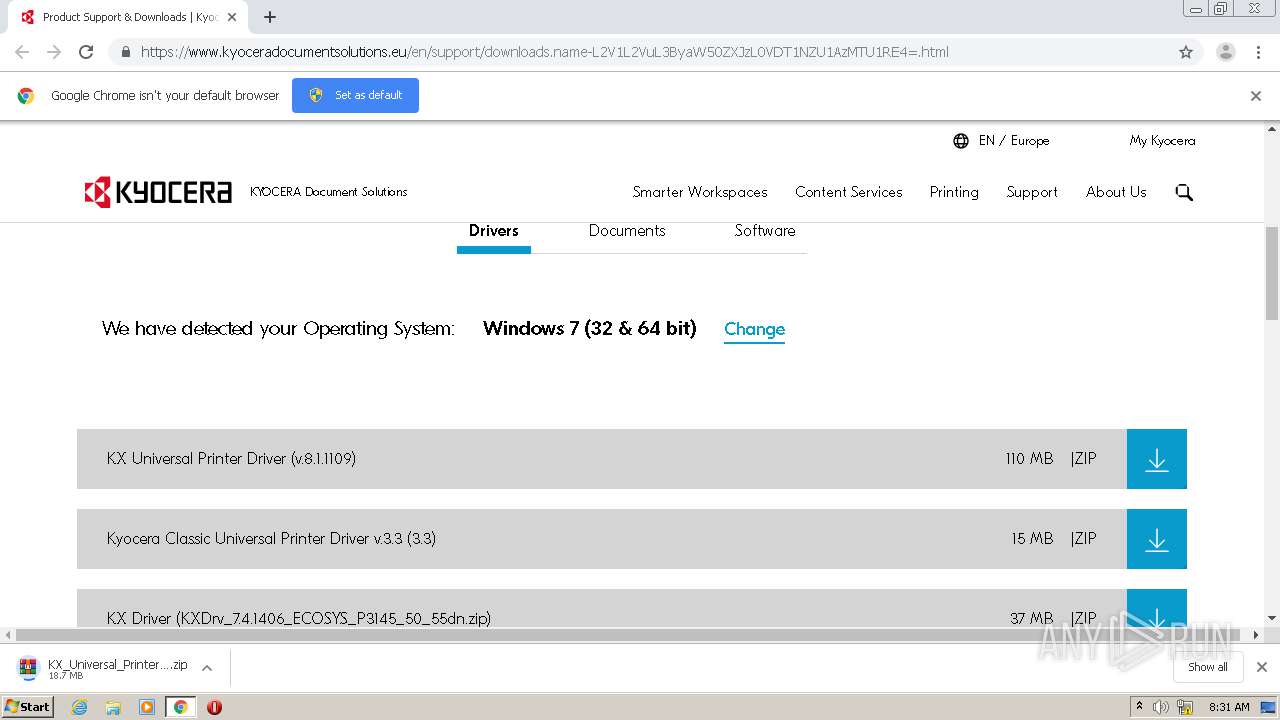
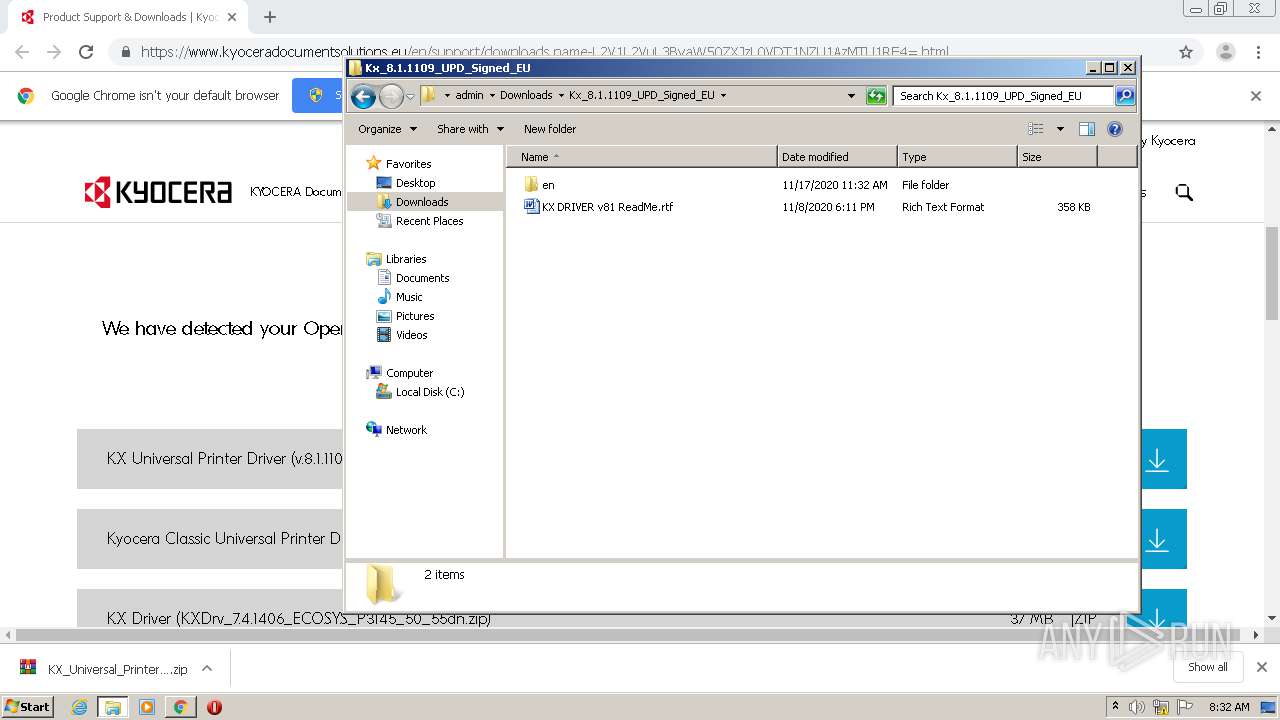
| URL: | https://www.kyoceradocumentsolutions.eu/en/support/downloads.name-L2V1L2VuL3ByaW50ZXJzL0VDT1NZU1AzMTU1RE4=.html |
| Full analysis: | https://app.any.run/tasks/31af8ea3-d517-4777-830c-775c20ba5020 |
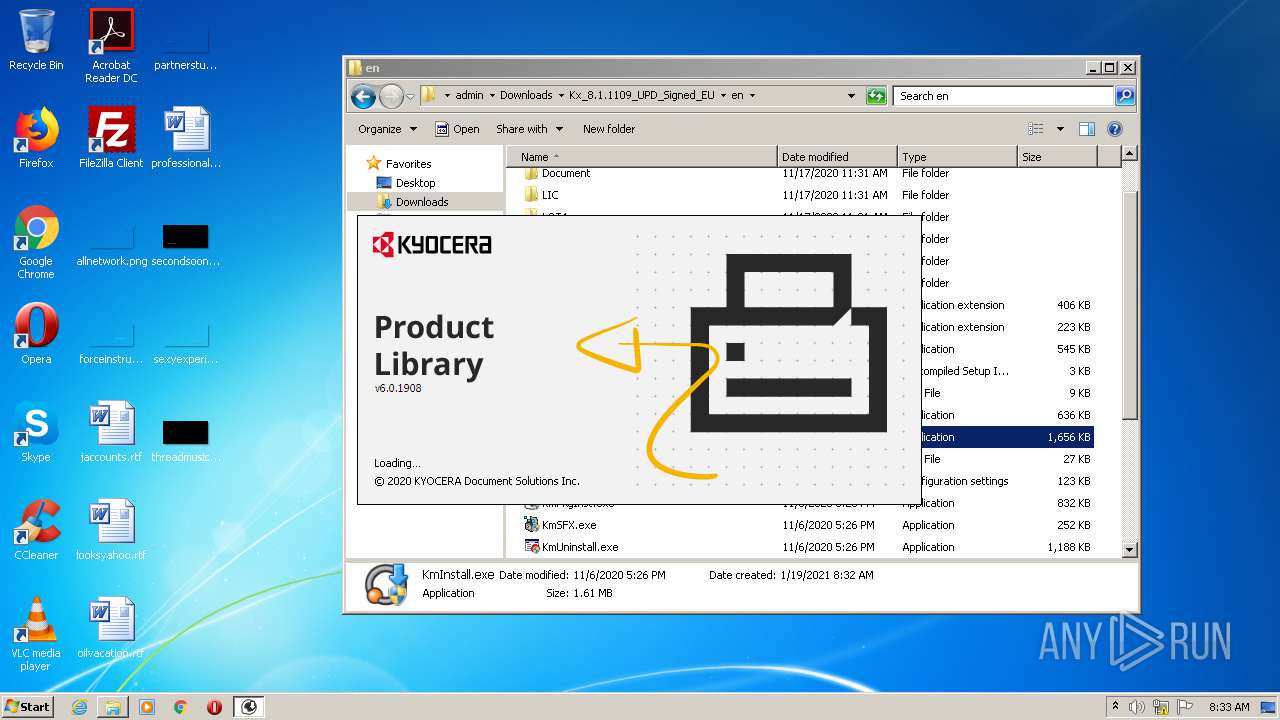
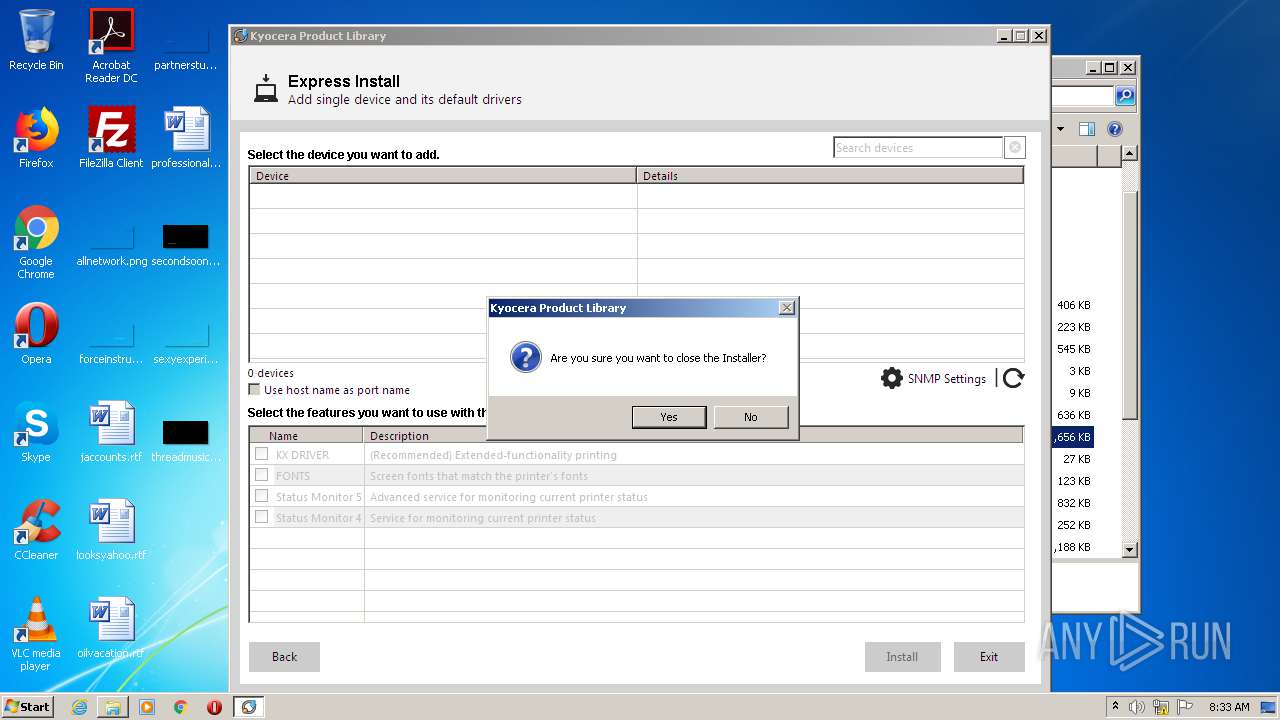
| Verdict: | Malicious activity |
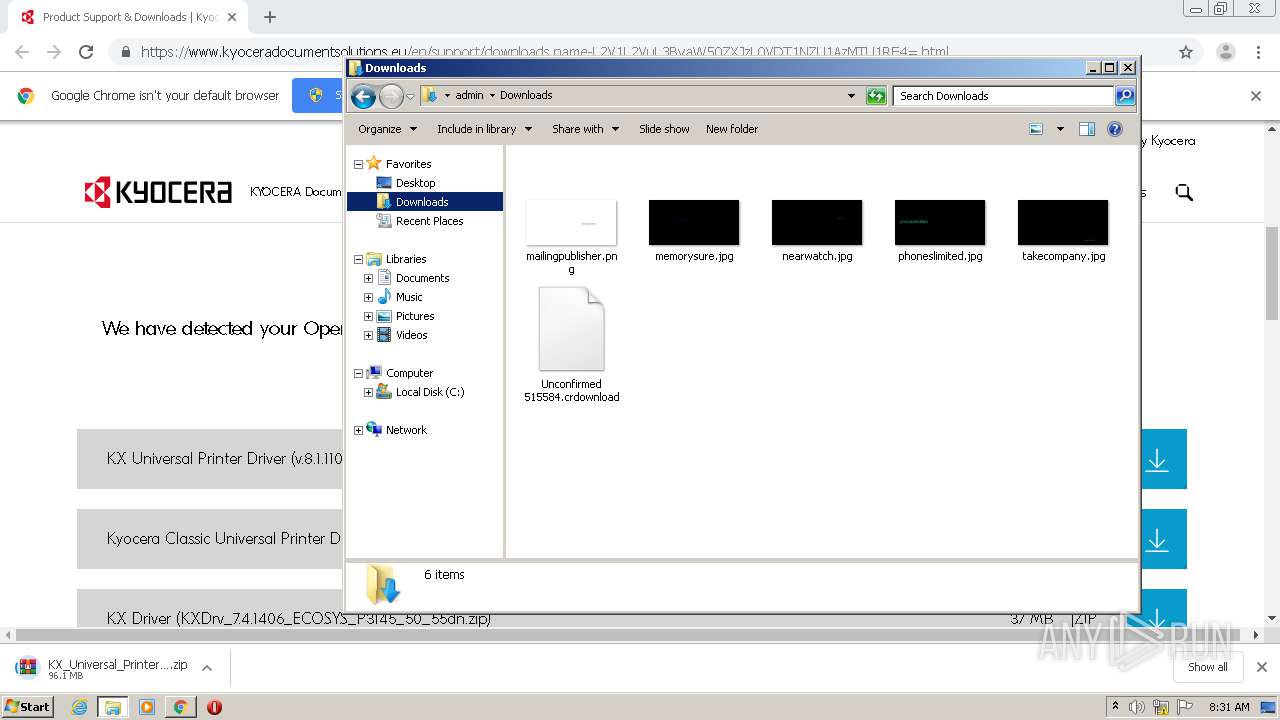
| Analysis date: | January 19, 2021, 08:30:28 |
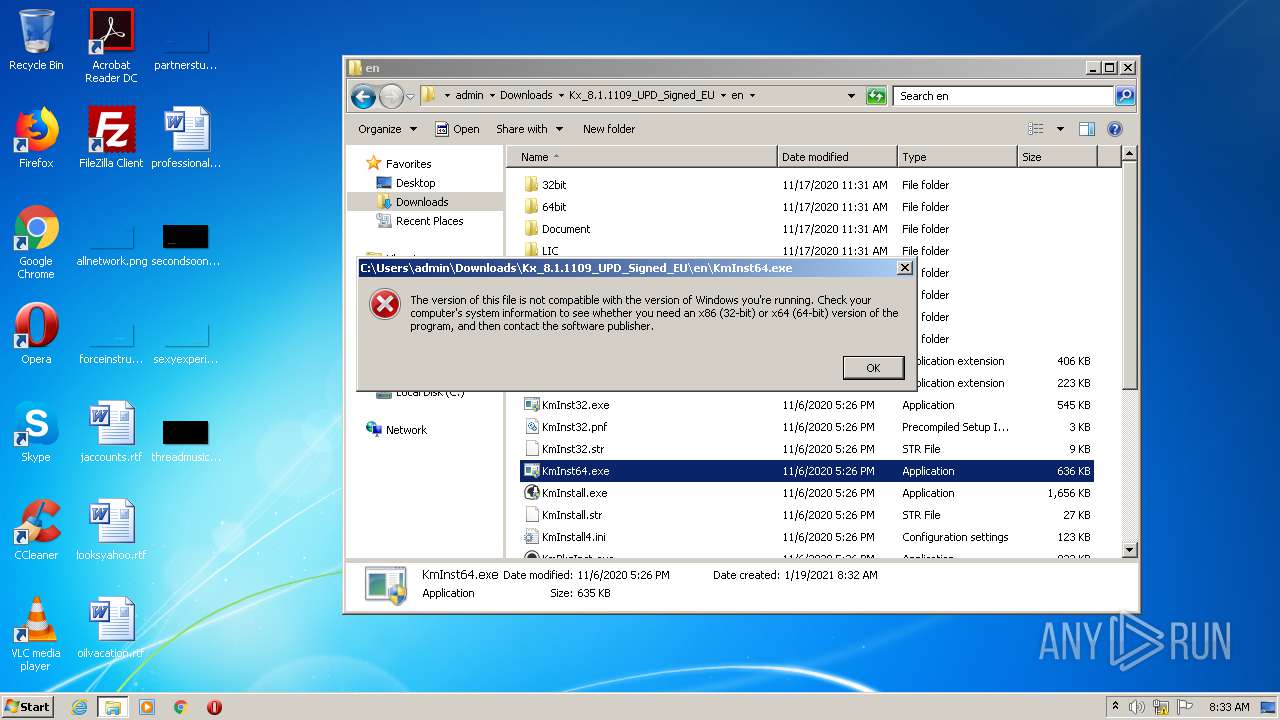
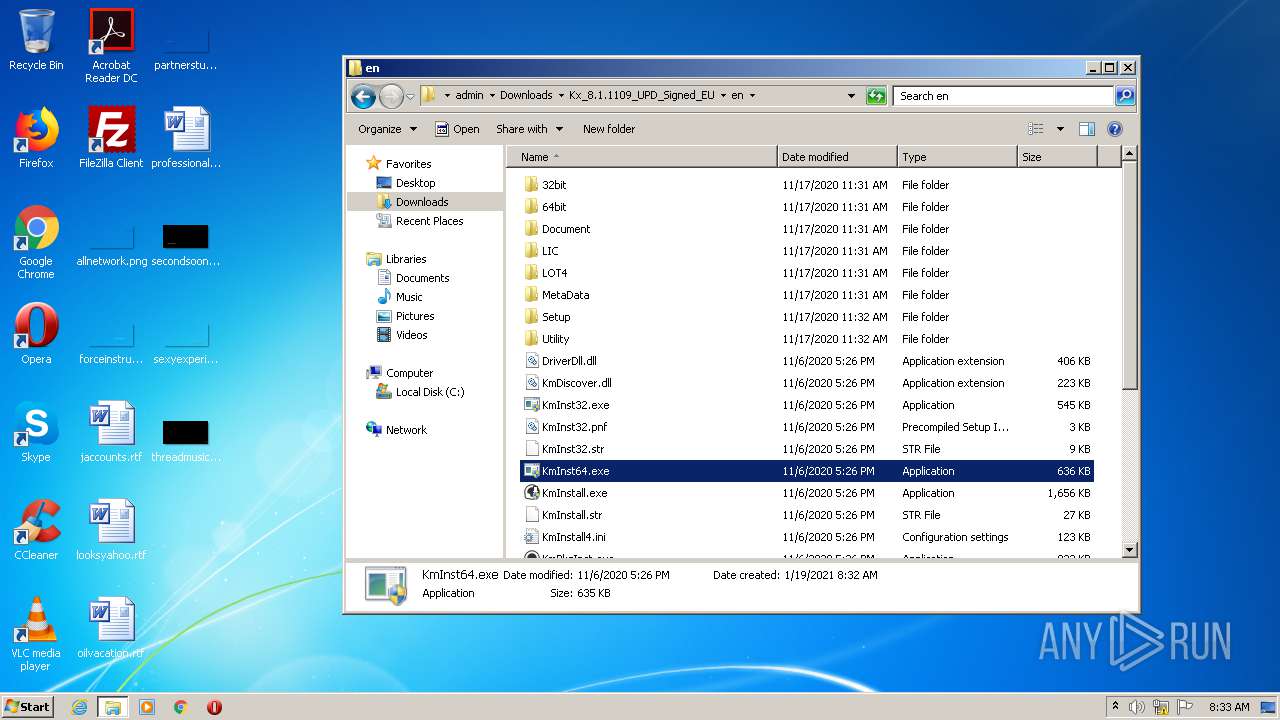
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 28F2EA947095459FEFCDBDC5A3B6AC57 |
| SHA1: | E8F4A437FA83441FE4E9A48D95F2407993DF2C87 |
| SHA256: | 1DFEF328AF8EEDA4BA07FBBE26AA834C3A631D827C75800BF5E13CA92ED46AEA |
| SSDEEP: | 3:N8DSLaHpRsUfK8SeL9AU8QpWcbQ5qhDgR6uJ:2OLyVkN3Q4crgVJ |
MALICIOUS
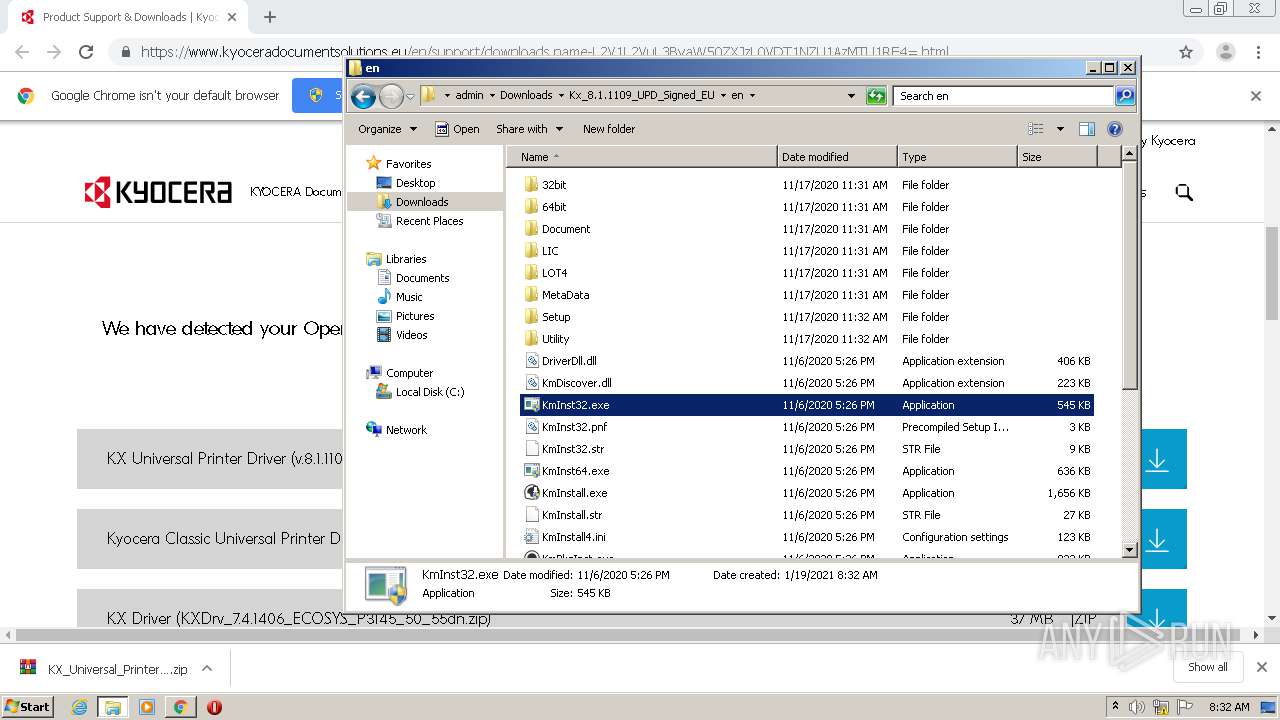
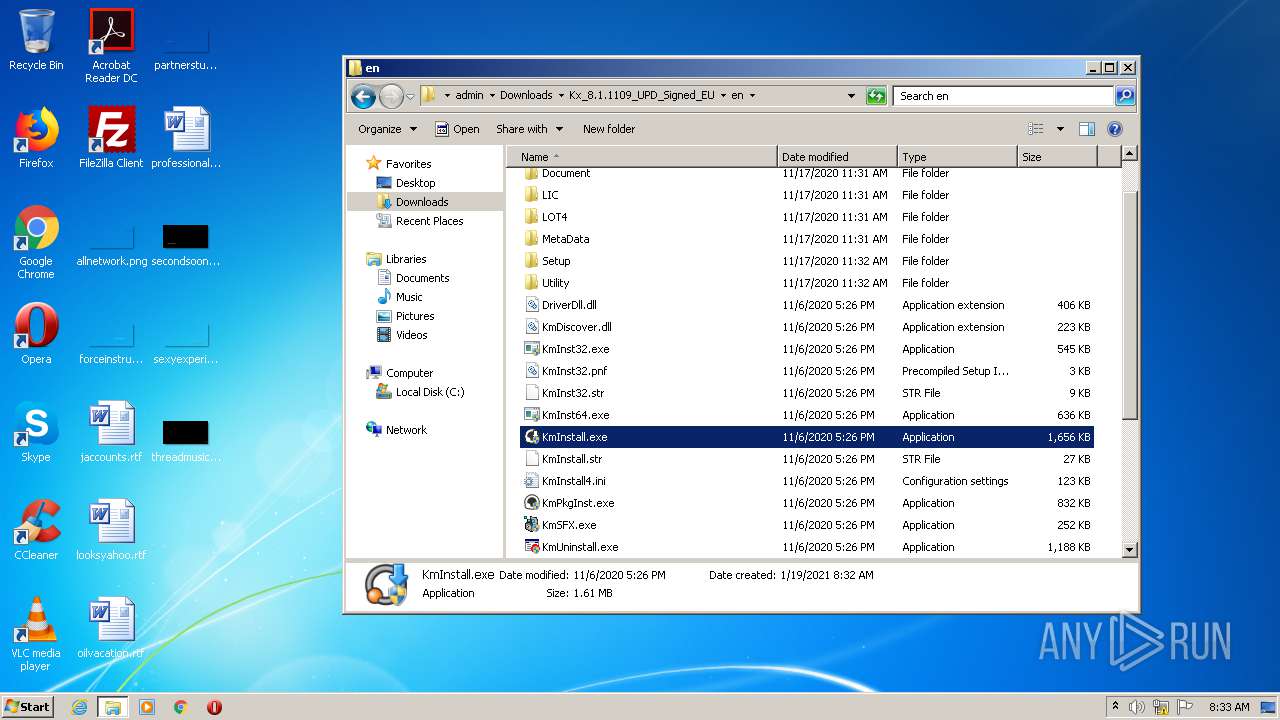
Application was dropped or rewritten from another process
- KmInst32.exe (PID: 3356)
- KmInst32.exe (PID: 3572)
- KmInstall.exe (PID: 3364)
- KmInstall.exe (PID: 3440)
- KmInst32.exe (PID: 3708)
- KmInst32.exe (PID: 1308)
- KmInst32.exe (PID: 2176)
- KmInst32.exe (PID: 312)
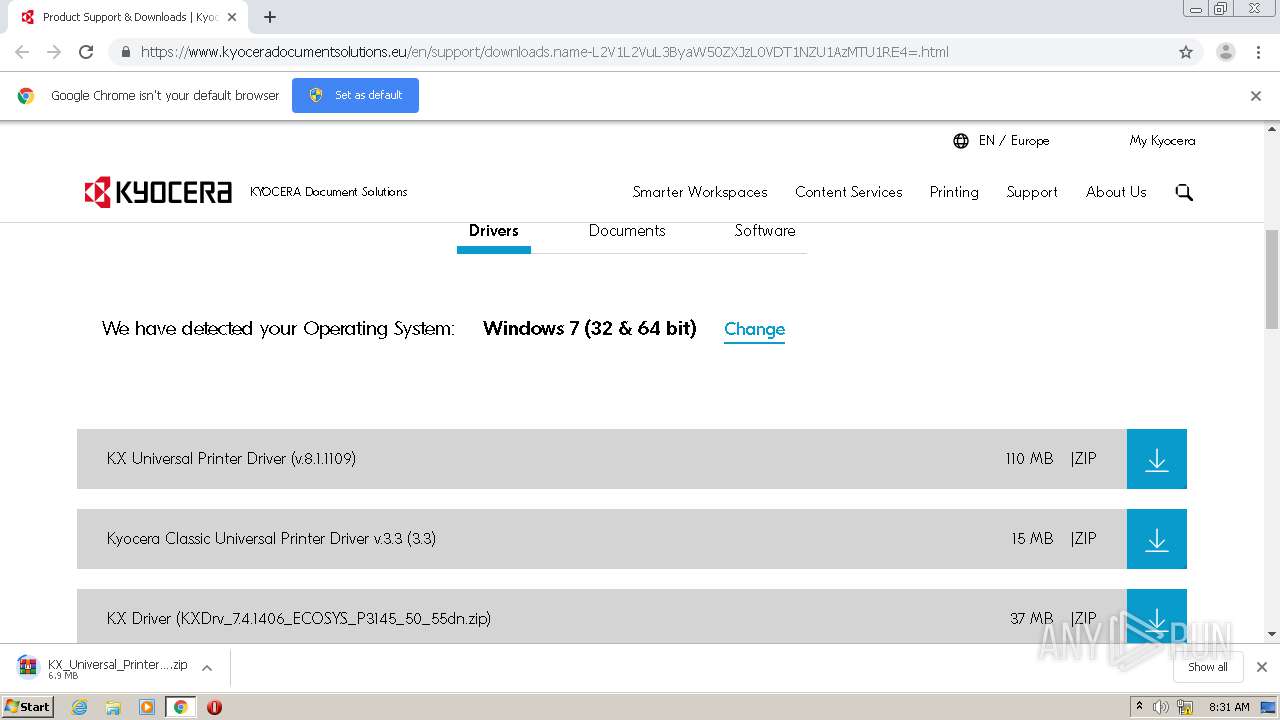
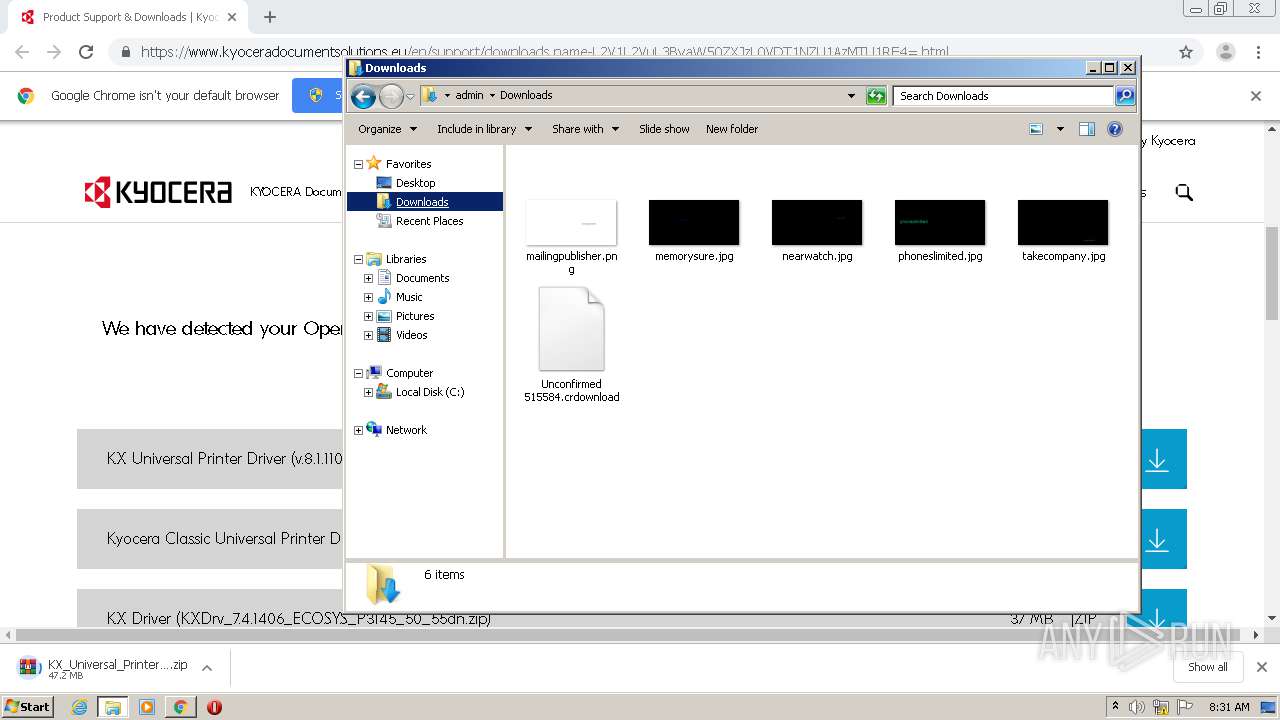
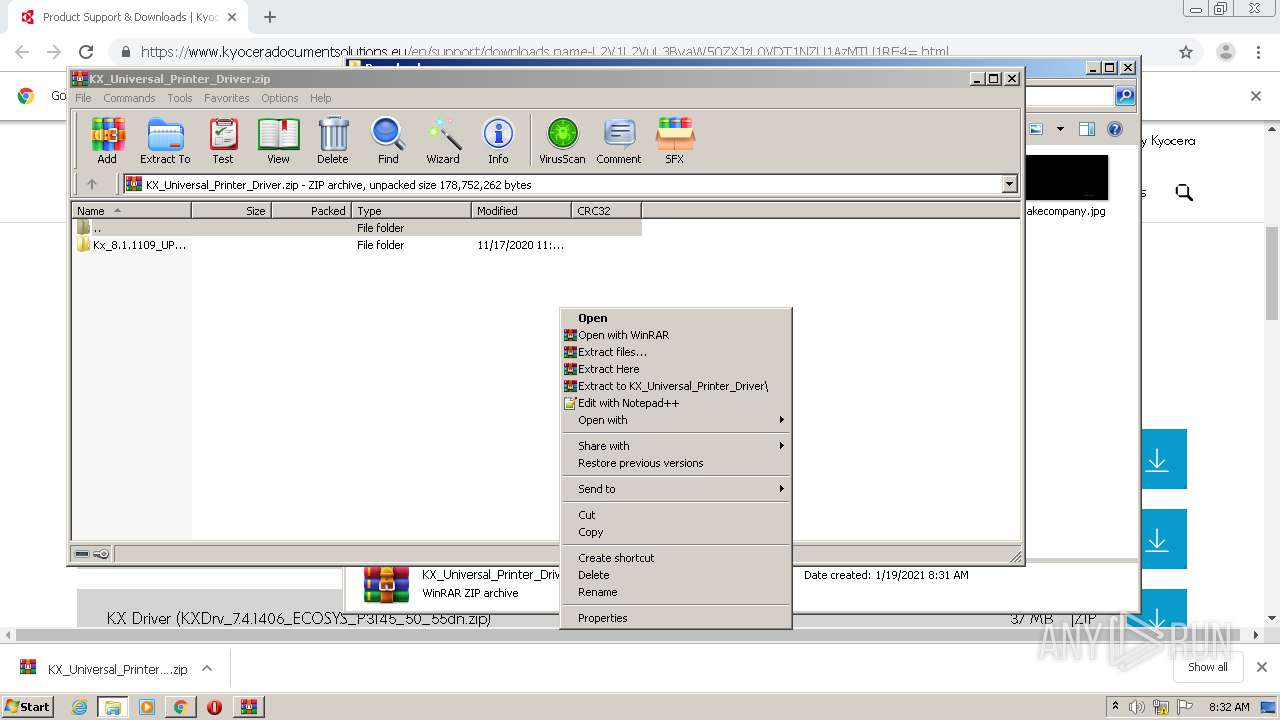
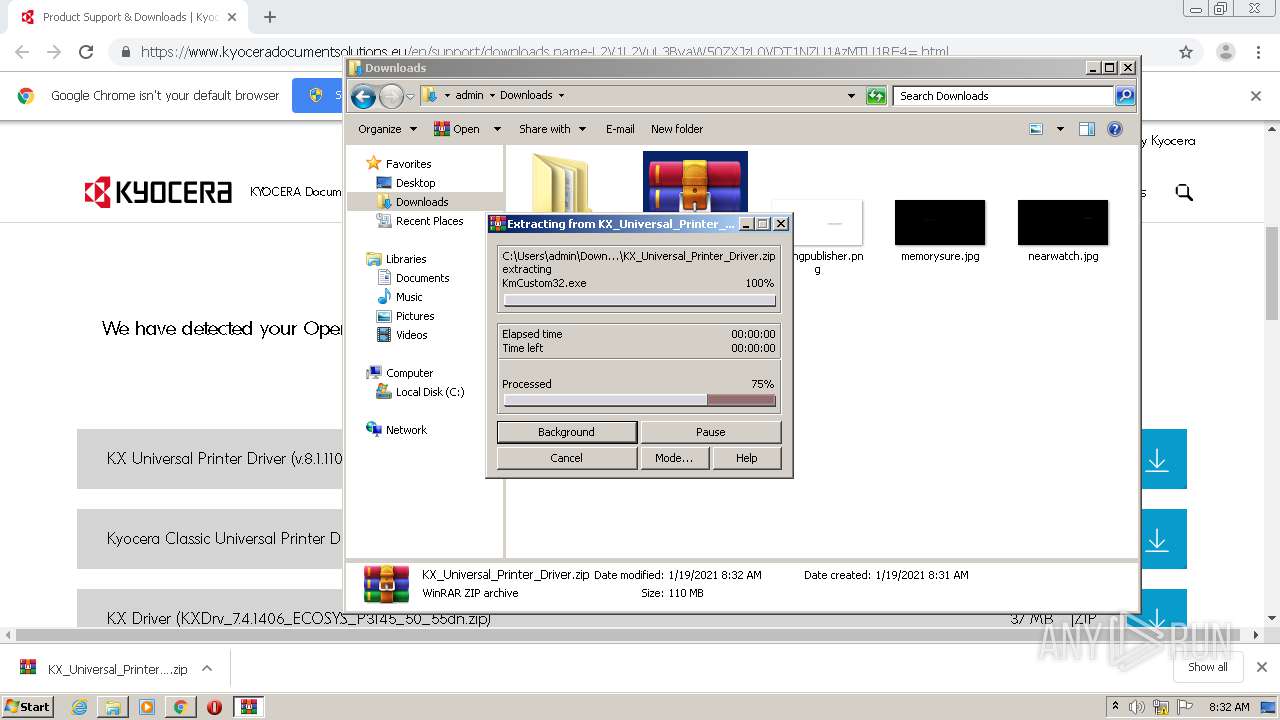
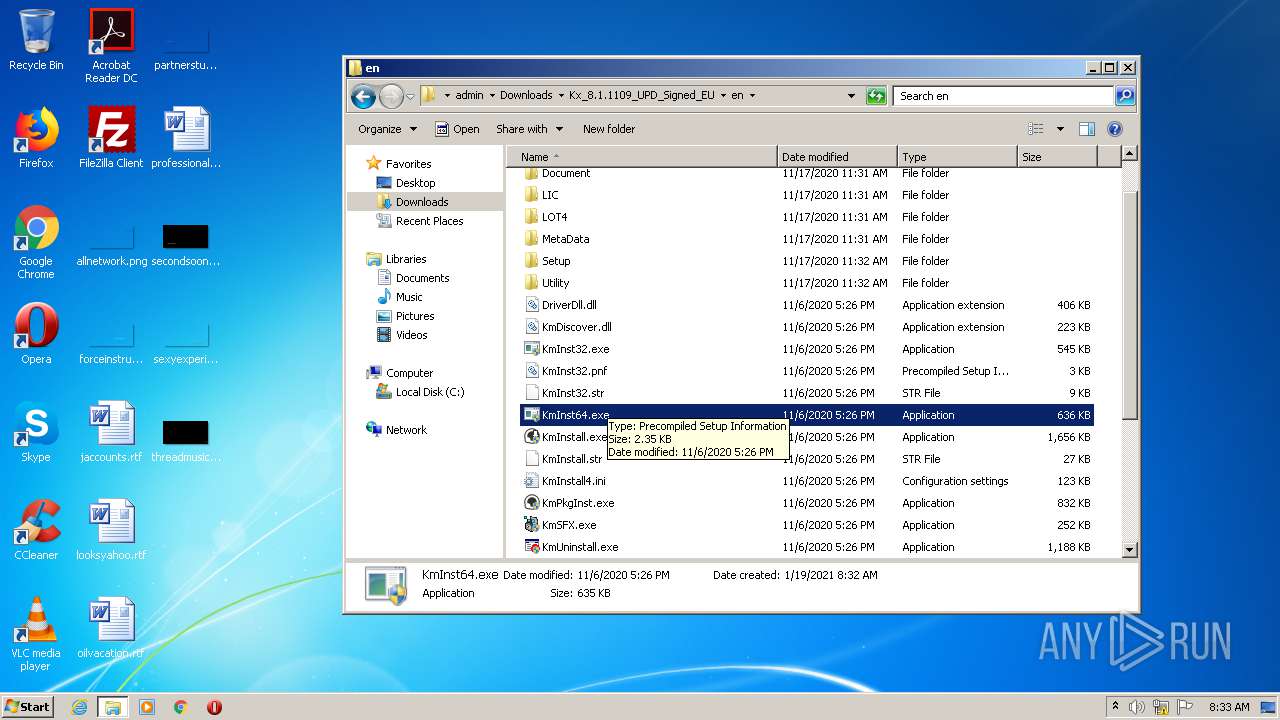
Drops executable file immediately after starts
- WinRAR.exe (PID: 1992)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 2820)
- KmInstall.exe (PID: 3440)
SUSPICIOUS
Drops a file with too old compile date
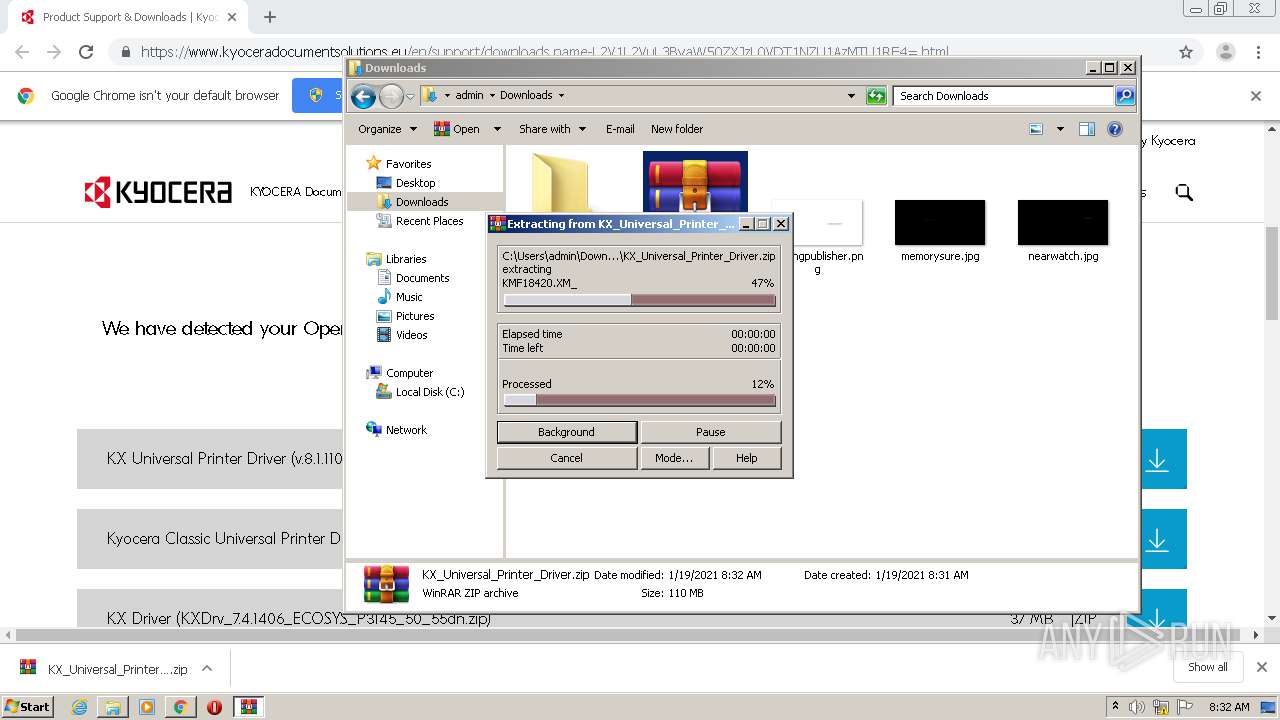
- WinRAR.exe (PID: 1992)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 1992)
- KmInstall.exe (PID: 3440)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1992)
- KmInstall.exe (PID: 3440)
Creates files in the Windows directory
- KmInstall.exe (PID: 3440)
INFO
Application launched itself
- chrome.exe (PID: 3740)
Manual execution by user
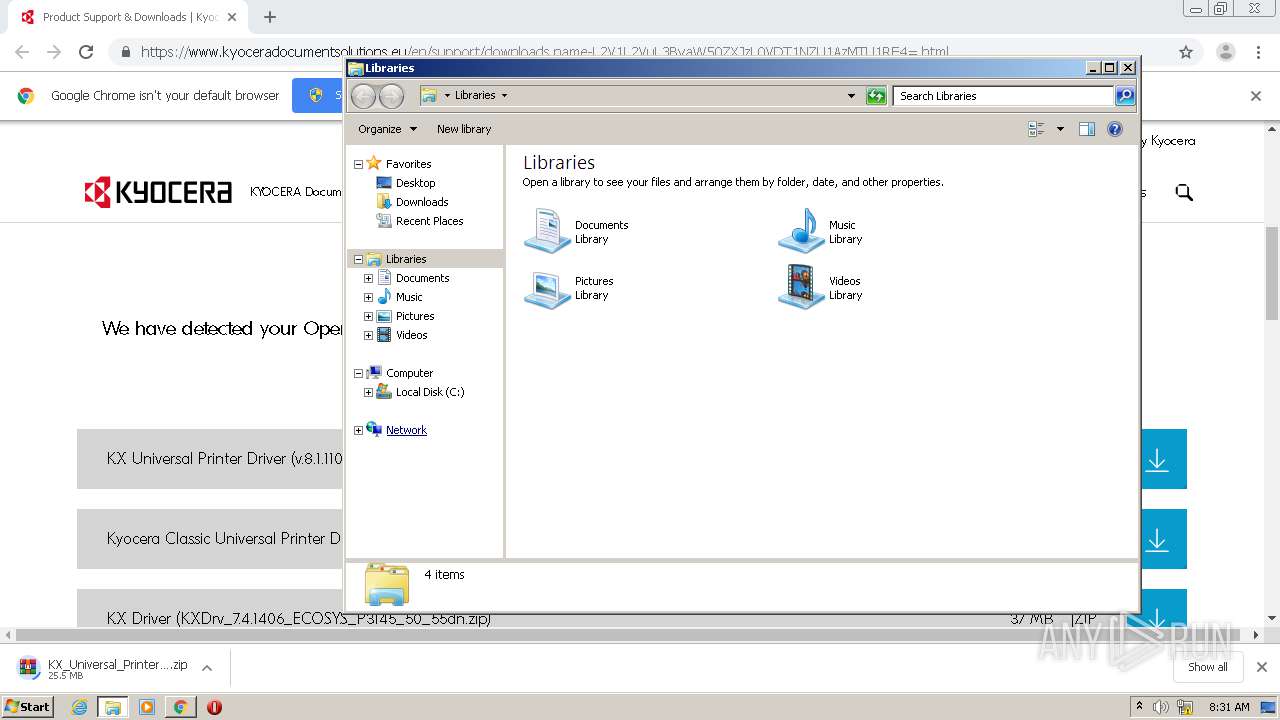
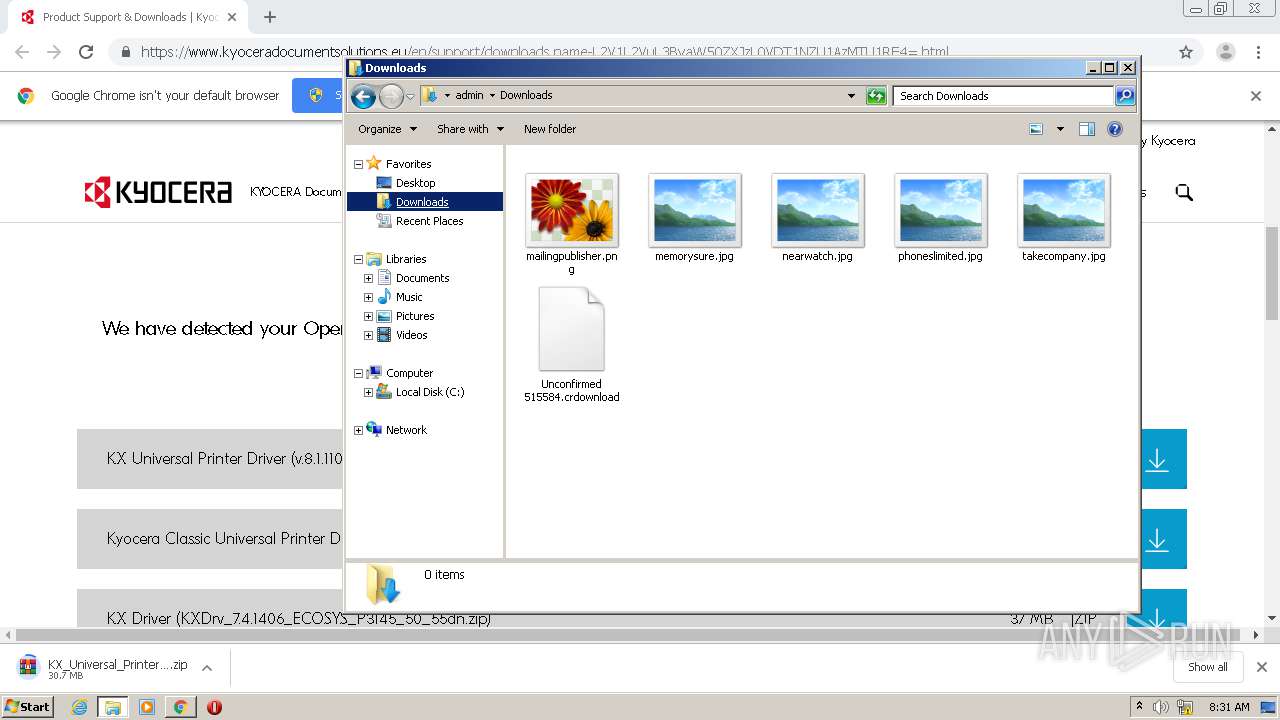
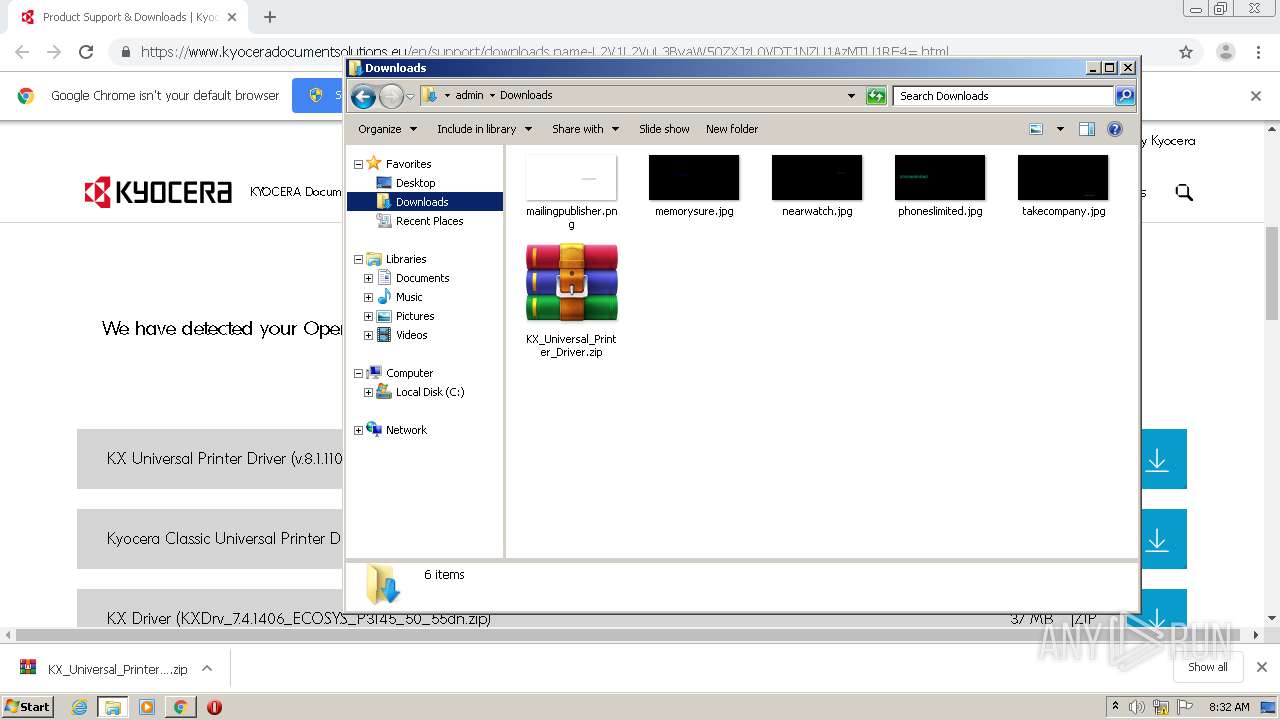
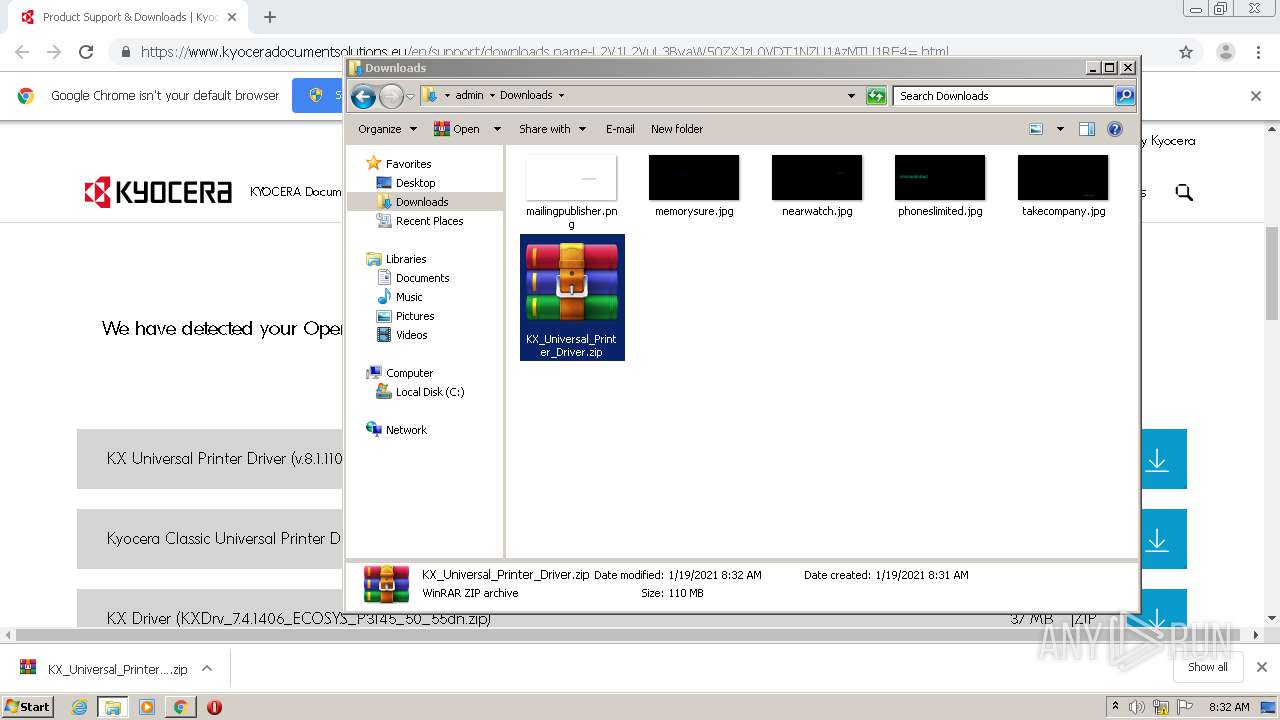
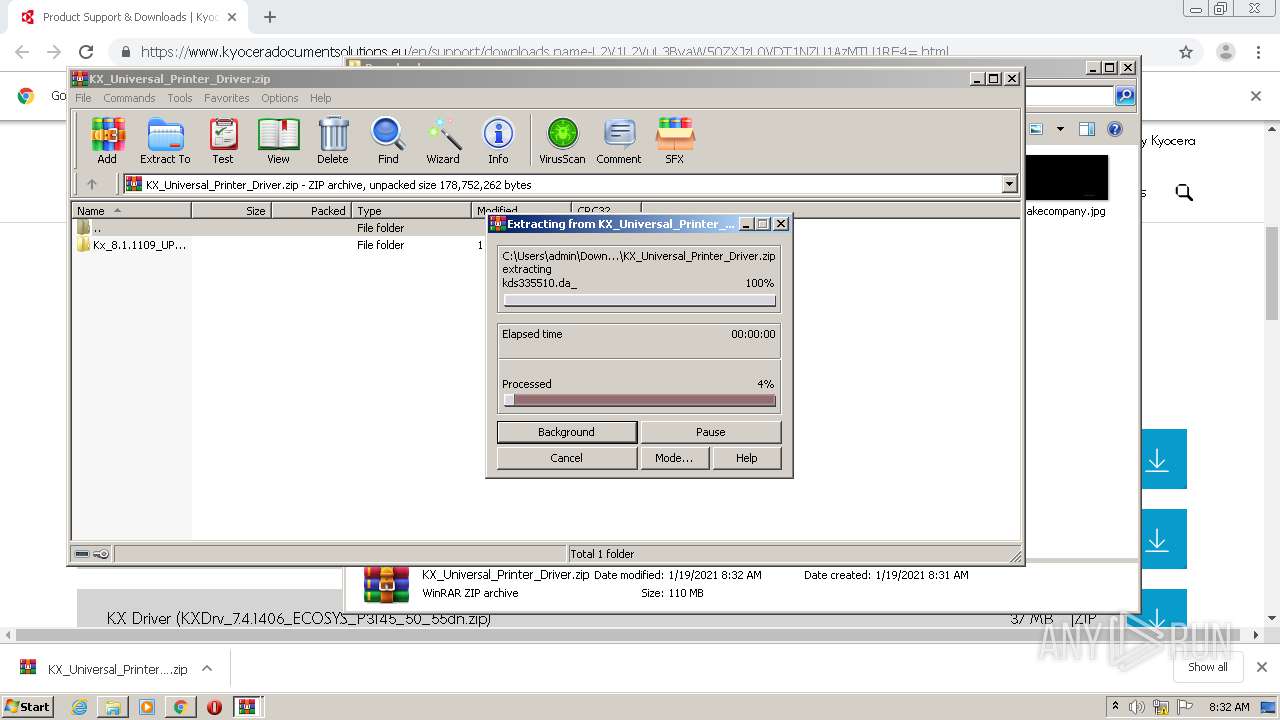
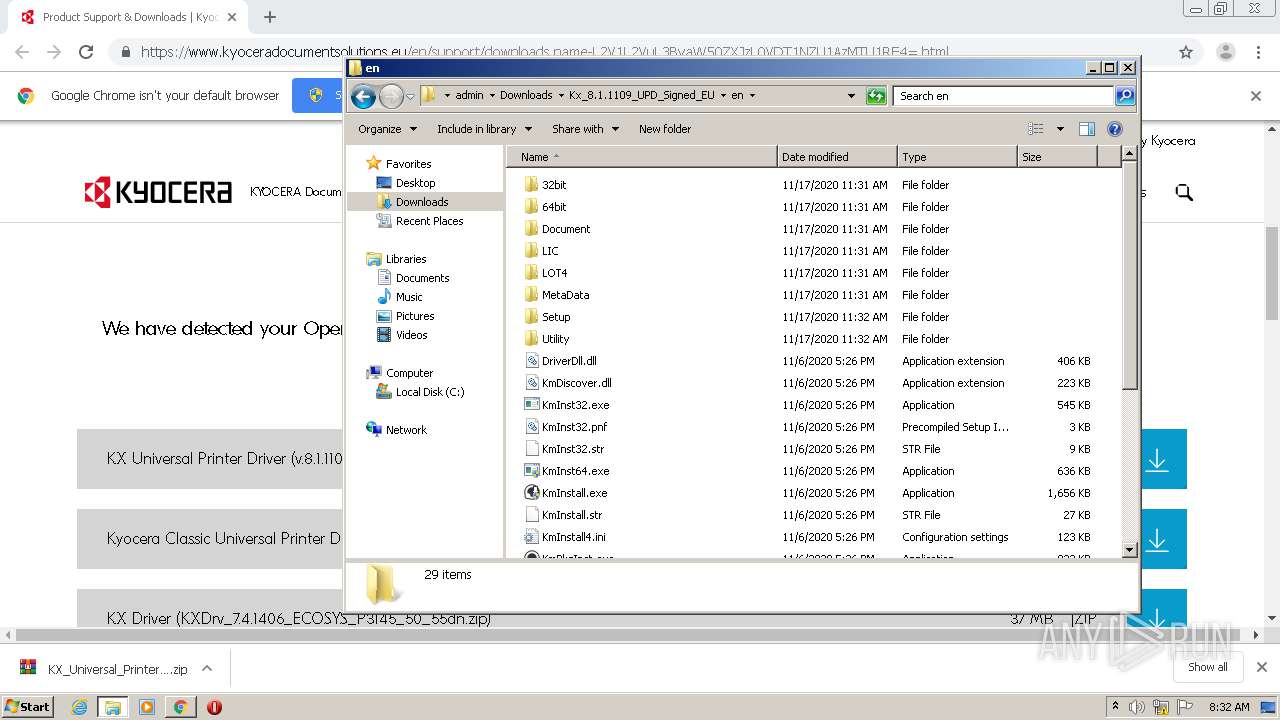
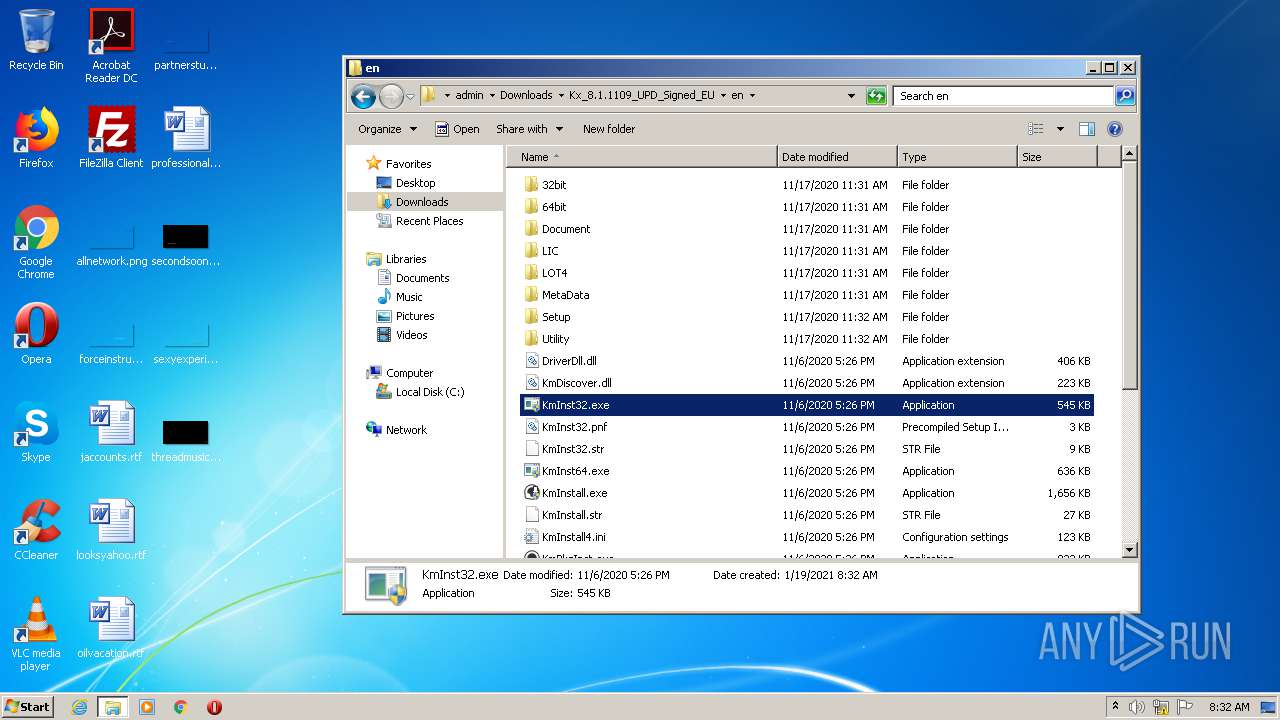
- WinRAR.exe (PID: 1504)
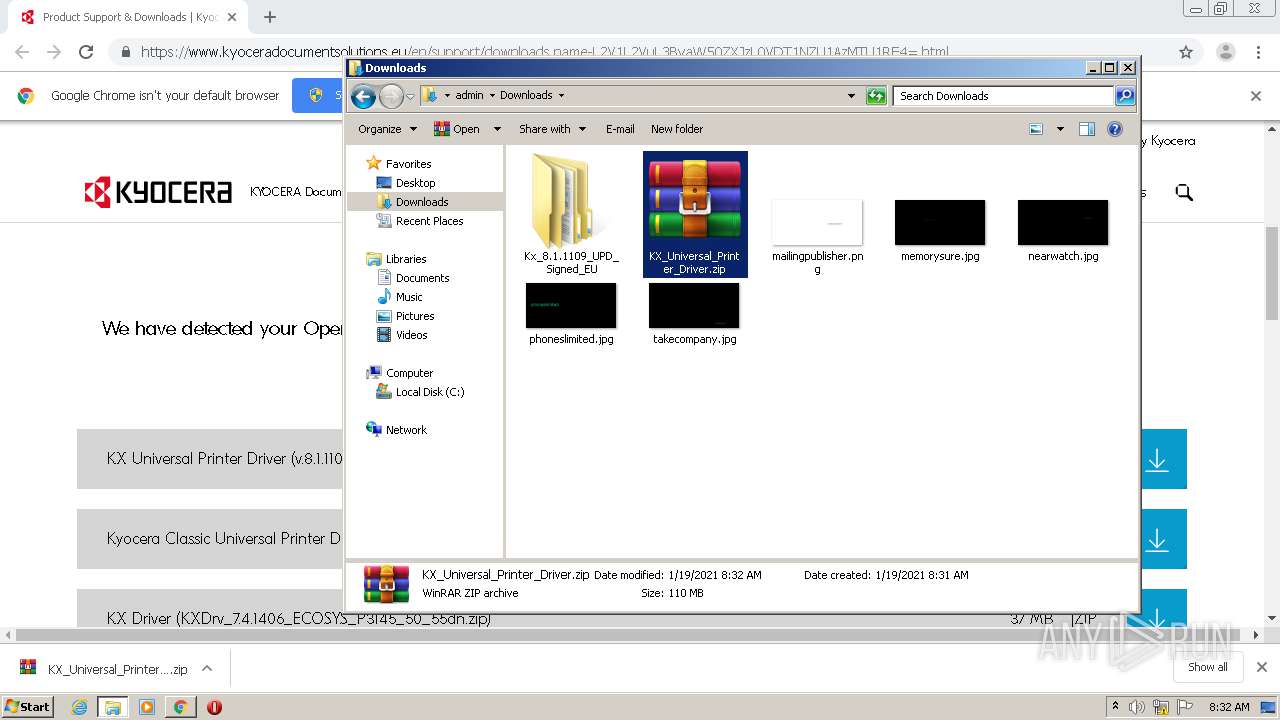
- explorer.exe (PID: 3980)
- WinRAR.exe (PID: 1992)
- KmInst32.exe (PID: 3356)
- KmInst32.exe (PID: 3572)
- KmInstall.exe (PID: 3364)
- KmInstall.exe (PID: 3440)
Reads the hosts file
- chrome.exe (PID: 3592)
- chrome.exe (PID: 3740)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
74
Monitored processes
24
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6ed4a9d0,0x6ed4a9e0,0x6ed4a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 312 | "C:\Users\admin\Downloads\Kx_8.1.1109_UPD_Signed_EU\en\KmInst32.exe" API 0 KmInst32{A38C69CE-81C5-4CAF-9B5C-0D1C6939FB70} | C:\Users\admin\Downloads\Kx_8.1.1109_UPD_Signed_EU\en\KmInst32.exe | — | KmInstall.exe | |||||||||||
User: admin Company: KYOCERA Document Solutions Inc. Integrity Level: HIGH Description: KmInst32 Exit code: 0 Version: 5, 1, 1202, 0 Modules
| |||||||||||||||
| 1268 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1052,13810734568086177134,8751685887769232213,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6260059155684836295 --mojo-platform-channel-handle=1248 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1052,13810734568086177134,8751685887769232213,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=299000131932430519 --mojo-platform-channel-handle=1140 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1308 | "C:\Users\admin\Downloads\Kx_8.1.1109_UPD_Signed_EU\en\KmInst32.exe" API 0 KmInst32{851080C2-1231-4E34-A9D6-18636A87CA7A} | C:\Users\admin\Downloads\Kx_8.1.1109_UPD_Signed_EU\en\KmInst32.exe | — | KmInstall.exe | |||||||||||
User: admin Company: KYOCERA Document Solutions Inc. Integrity Level: HIGH Description: KmInst32 Exit code: 0 Version: 5, 1, 1202, 0 Modules
| |||||||||||||||
| 1504 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\KX_Universal_Printer_Driver.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1992 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\KX_Universal_Printer_Driver.zip" C:\Users\admin\Downloads\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2176 | "C:\Users\admin\Downloads\Kx_8.1.1109_UPD_Signed_EU\en\KmInst32.exe" API 0 KmInst32{E6FBD949-594B-4302-A2AF-561AA4D8B025} | C:\Users\admin\Downloads\Kx_8.1.1109_UPD_Signed_EU\en\KmInst32.exe | — | KmInstall.exe | |||||||||||
User: admin Company: KYOCERA Document Solutions Inc. Integrity Level: HIGH Description: KmInst32 Exit code: 0 Version: 5, 1, 1202, 0 Modules
| |||||||||||||||
| 2408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1052,13810734568086177134,8751685887769232213,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=1513266730819499095 --mojo-platform-channel-handle=3972 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,13810734568086177134,8751685887769232213,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9133354569065593342 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2416 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 862
Read events
1 759
Write events
100
Delete events
3
Modification events
| (PID) Process: | (3740) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3740) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3740) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3740) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3996) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3740-13255518645154750 |
Value: 259 | |||
| (PID) Process: | (3740) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3740) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3740) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3740) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (3740) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
88
Suspicious files
134
Text files
239
Unknown types
1 397
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3740 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-600698B5-E9C.pma | — | |
MD5:— | SHA256:— | |||
| 3740 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\14d91298-617d-4545-a255-39c8c9ff0b44.tmp | — | |
MD5:— | SHA256:— | |||
| 3740 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3740 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | — | |
MD5:— | SHA256:— | |||
| 3740 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF25c9d.TMP | text | |
MD5:D4322EEBAC92D1B8F7A6F5E39F6264B7 | SHA256:A3EEDF21B850DCC7CE5AE04395ECDD2D29DA4EA549C8A185DD9E8B552A87B8C2 | |||
| 3740 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:D4322EEBAC92D1B8F7A6F5E39F6264B7 | SHA256:A3EEDF21B850DCC7CE5AE04395ECDD2D29DA4EA549C8A185DD9E8B552A87B8C2 | |||
| 3740 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF25e04.TMP | text | |
MD5:73D23E129C733CCC599F9ACE77EB7F72 | SHA256:871981ECC6E3324F89CFF0A85196CFB4A7C9E97347459AAC36BC04243A83EB0B | |||
| 3740 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF25ccc.TMP | text | |
MD5:FB5B20517A0D1F7DAD485989565BEE5E | SHA256:99405F66EDBEB2306F4D0B4469DCADFF5293B5E1549C588CCFACEA439BB3B101 | |||
| 3740 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3740 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF25edf.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
23
DNS requests
14
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3592 | chrome.exe | 52.213.189.68:443 | www.kyoceradocumentsolutions.eu | Amazon.com, Inc. | IE | unknown |
3592 | chrome.exe | 172.217.212.102:443 | clients1.google.com | Google Inc. | US | whitelisted |
3592 | chrome.exe | 142.250.125.84:443 | accounts.google.com | Google Inc. | US | unknown |
3592 | chrome.exe | 104.75.88.252:443 | assets.adobedtm.com | Akamai Technologies, Inc. | NL | unknown |
3592 | chrome.exe | 52.17.73.77:443 | dpm.demdex.net | Amazon.com, Inc. | IE | unknown |
3592 | chrome.exe | 216.58.212.174:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3592 | chrome.exe | 52.31.176.223:443 | dpm.demdex.net | Amazon.com, Inc. | IE | unknown |
3592 | chrome.exe | 66.102.1.156:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
3592 | chrome.exe | 52.51.251.137:443 | kdc.tt.omtrdc.net | Amazon.com, Inc. | IE | unknown |
3592 | chrome.exe | 172.217.18.163:443 | www.google.co.uk | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.kyoceradocumentsolutions.eu |
| unknown |
accounts.google.com |
| shared |
clients1.google.com |
| whitelisted |
assets.adobedtm.com |
| whitelisted |
dpm.demdex.net |
| whitelisted |
www.google-analytics.com |
| whitelisted |
kdc.demdex.net |
| unknown |
cm.everesttech.net |
| whitelisted |
kdc.tt.omtrdc.net |
| suspicious |
stats.g.doubleclick.net |
| whitelisted |
Threats
Process | Message |
|---|---|
KmInstall.exe | rcCT.bottom: 13, rcCT.top: 0
|
KmInstall.exe | rcCT.bottom: 13, rcCT.top: 0
|
KmInstall.exe | rcCT.bottom: 13, rcCT.top: 0
|
KmInstall.exe | rcCT.bottom: 13, rcCT.top: 0
|
KmInstall.exe | rcCT.bottom: 13, rcCT.top: 0
|
KmInstall.exe | rcCT.bottom: 13, rcCT.top: 0
|
KmInstall.exe | rcCT.bottom: 13, rcCT.top: 0
|
KmInstall.exe | rcCT.bottom: 13, rcCT.top: 0
|
KmInstall.exe | rcCT.bottom: 13, rcCT.top: 0
|
KmInstall.exe | rcCT.bottom: 13, rcCT.top: 0
|