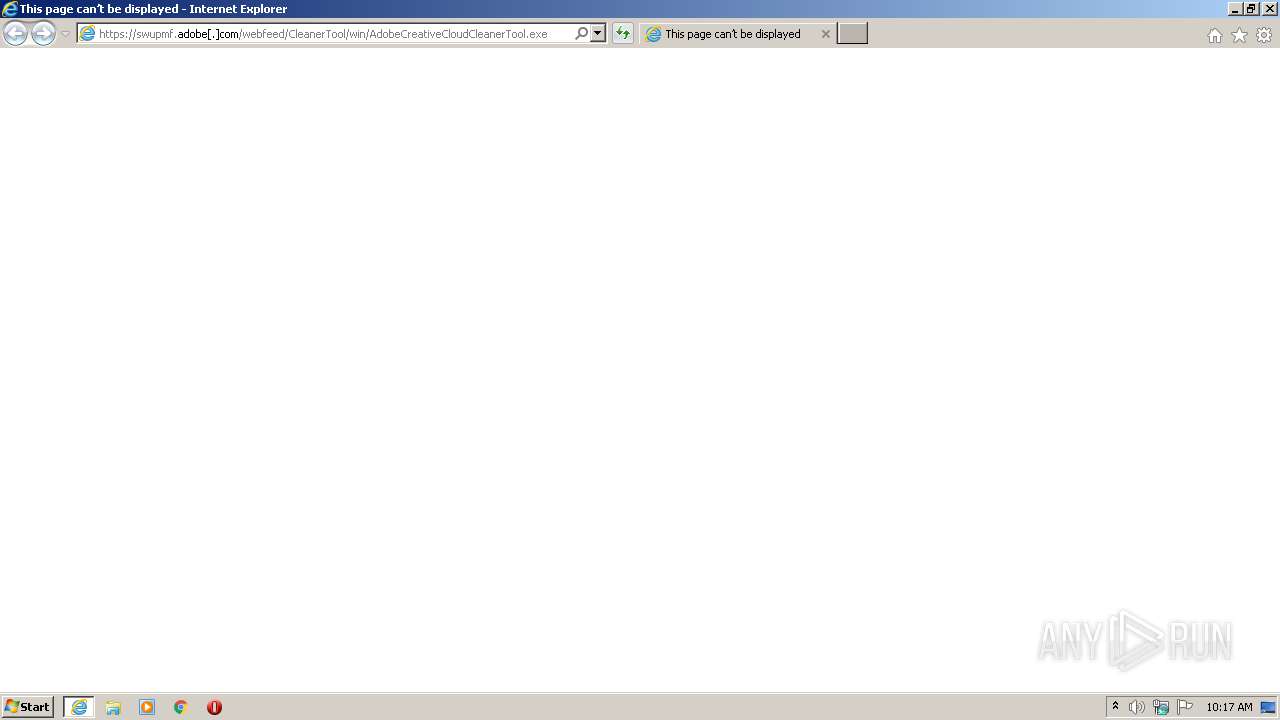
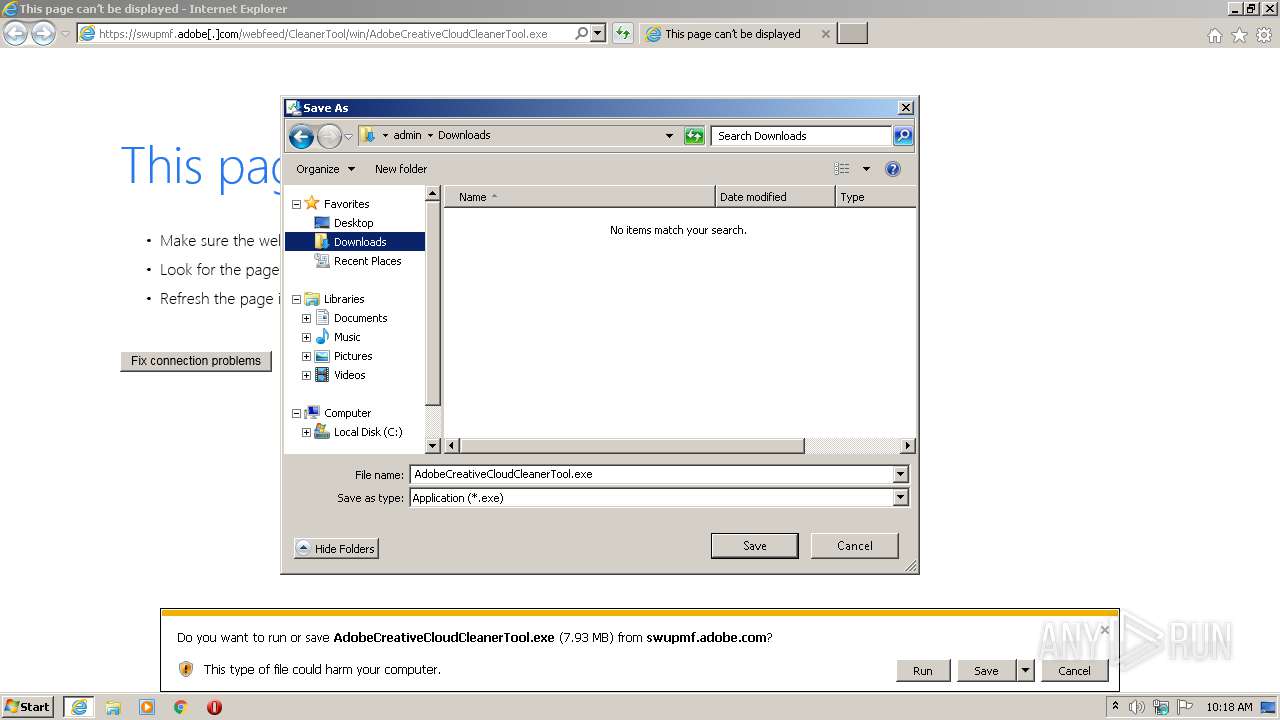
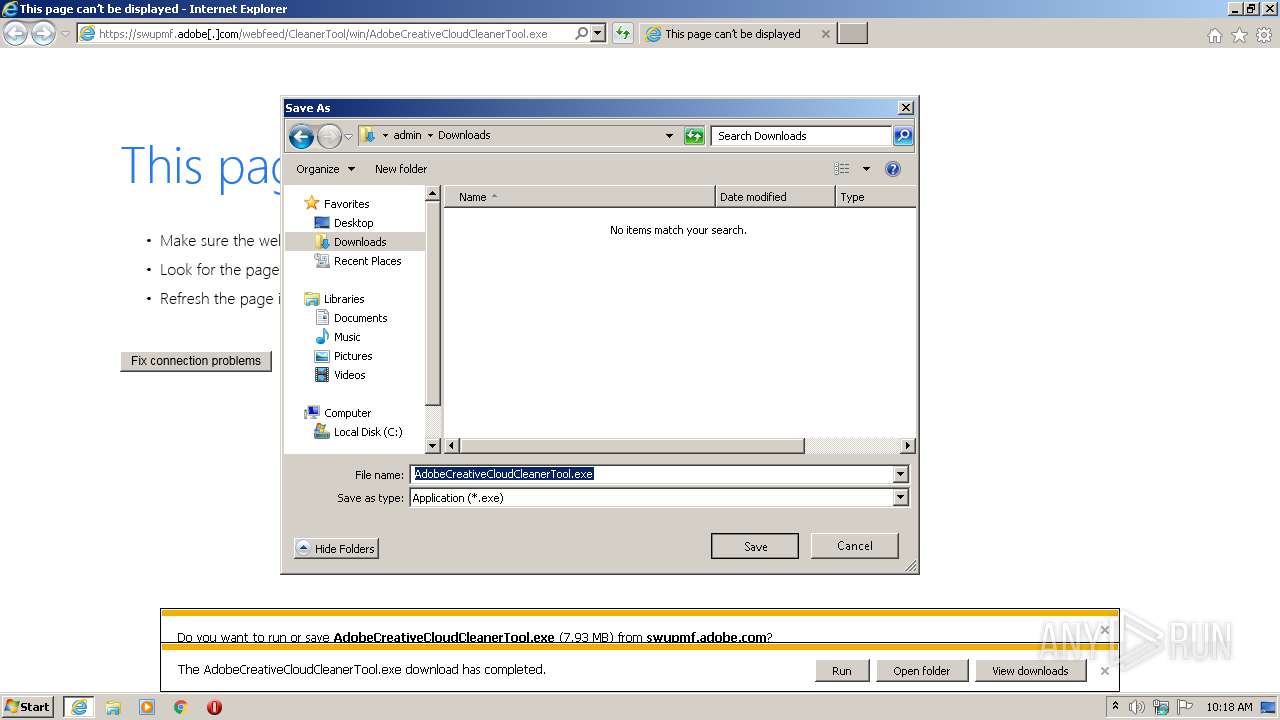
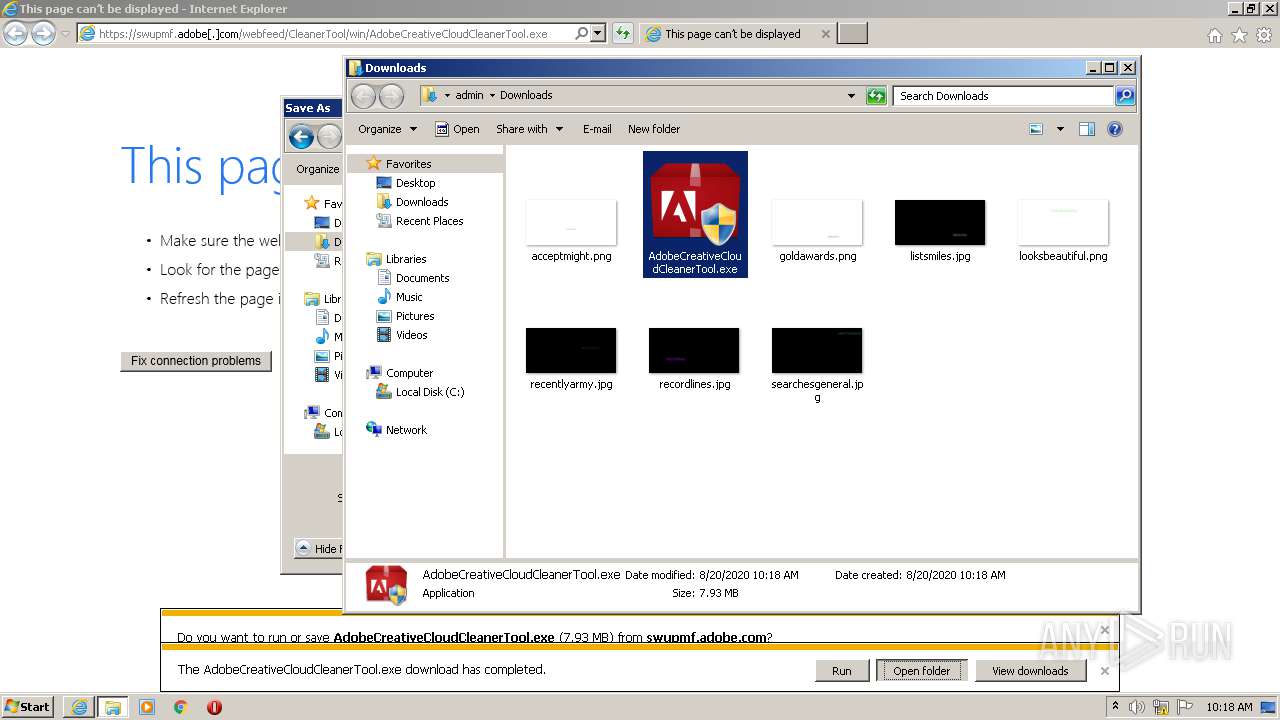
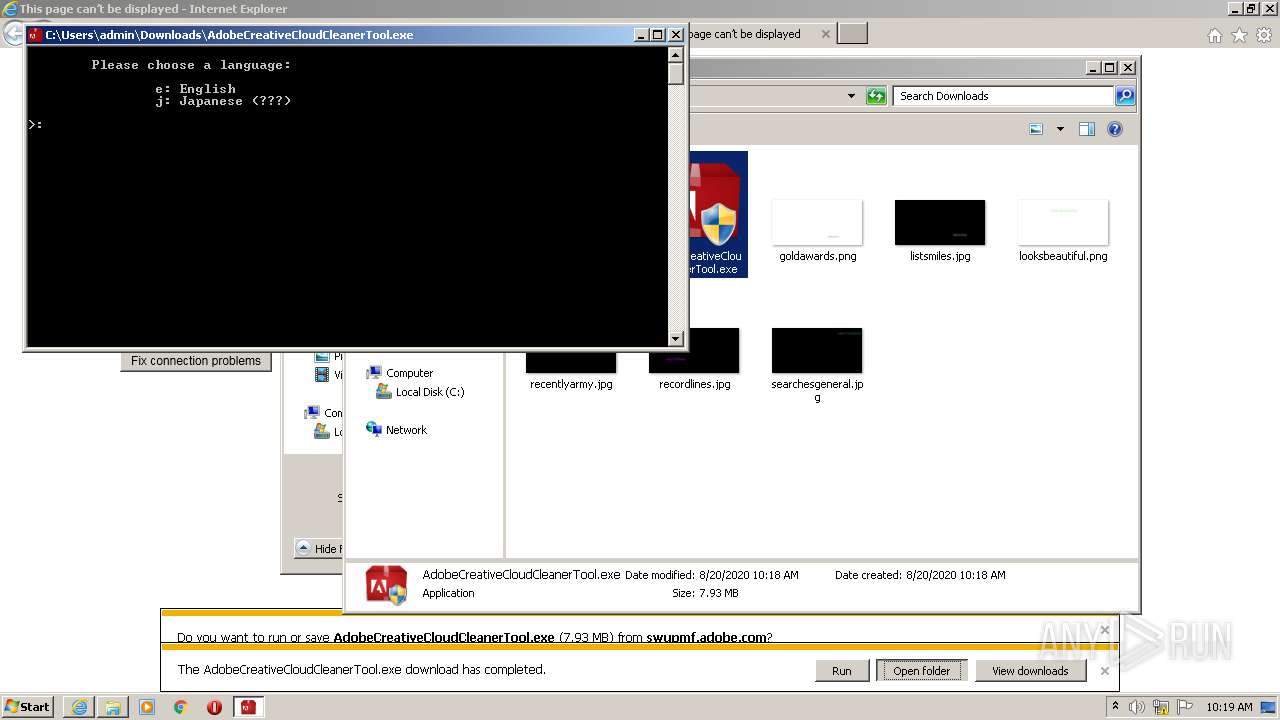
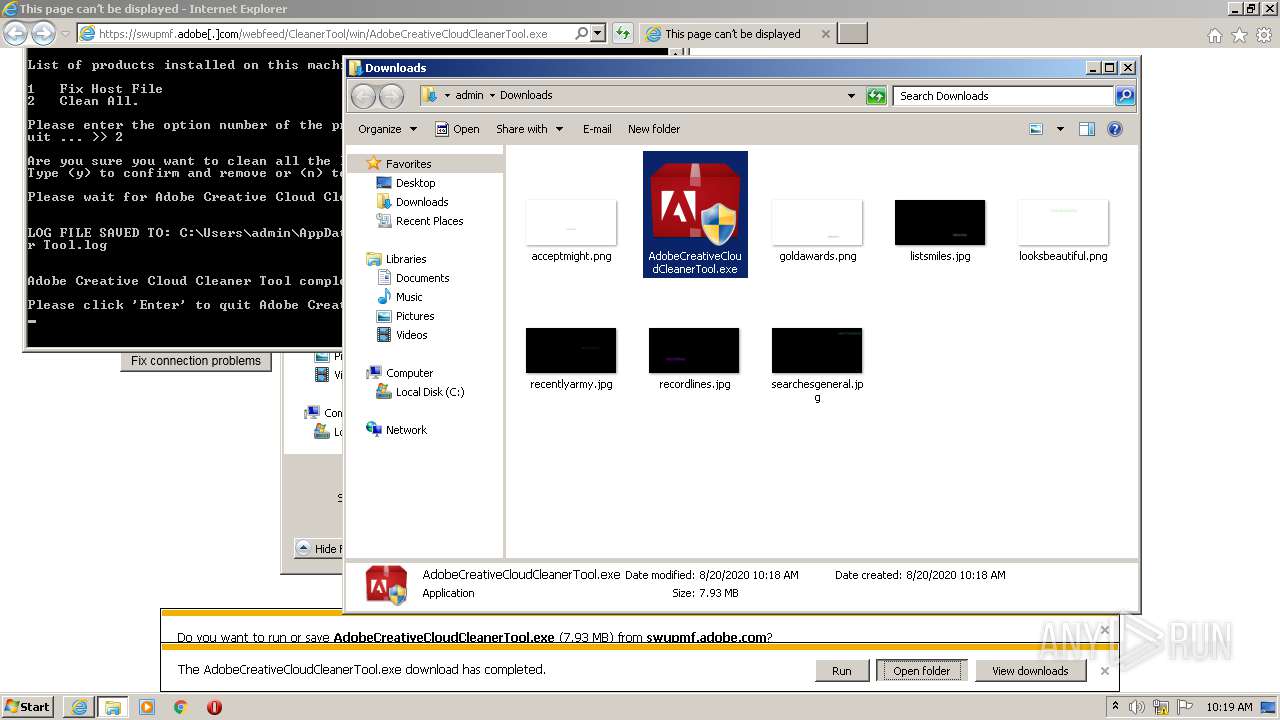
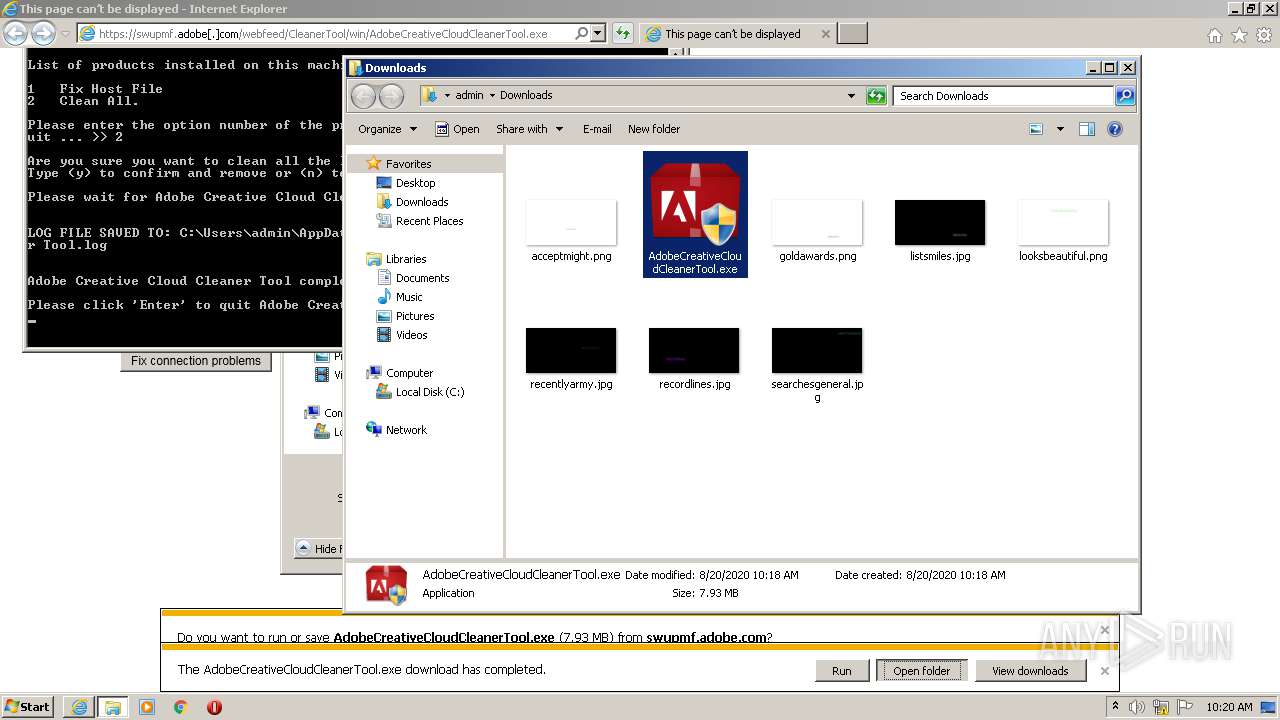
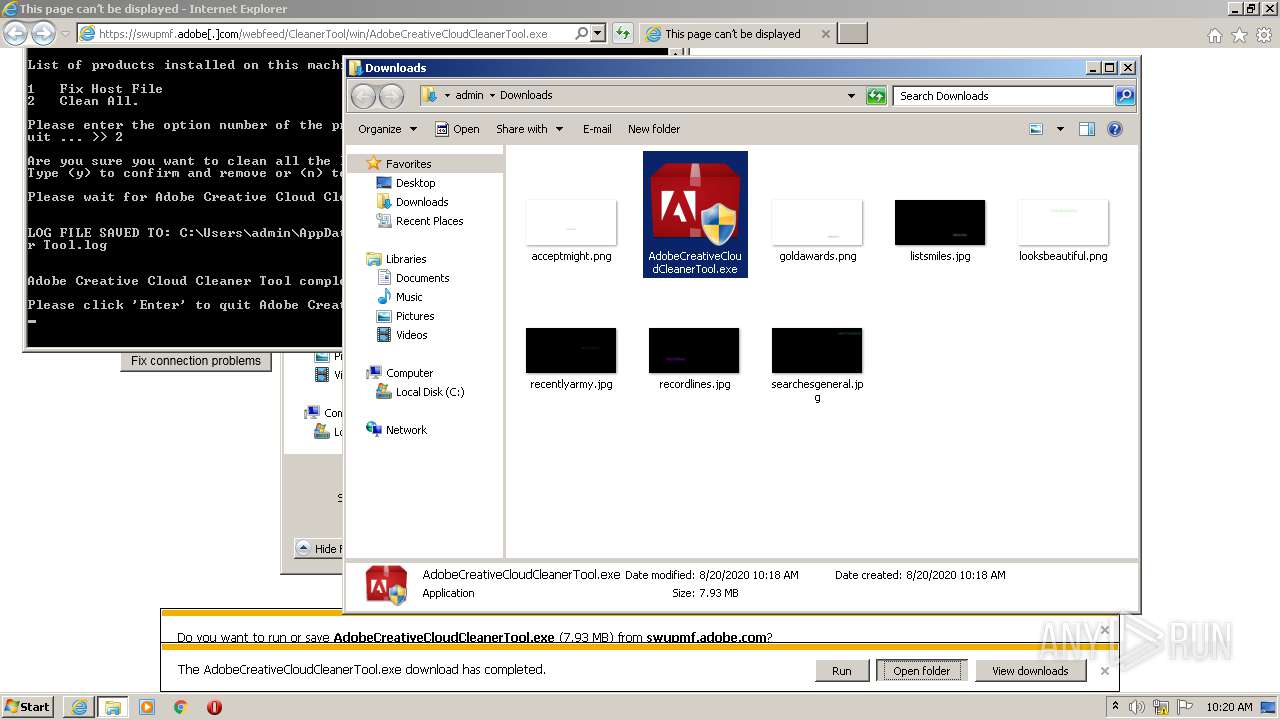
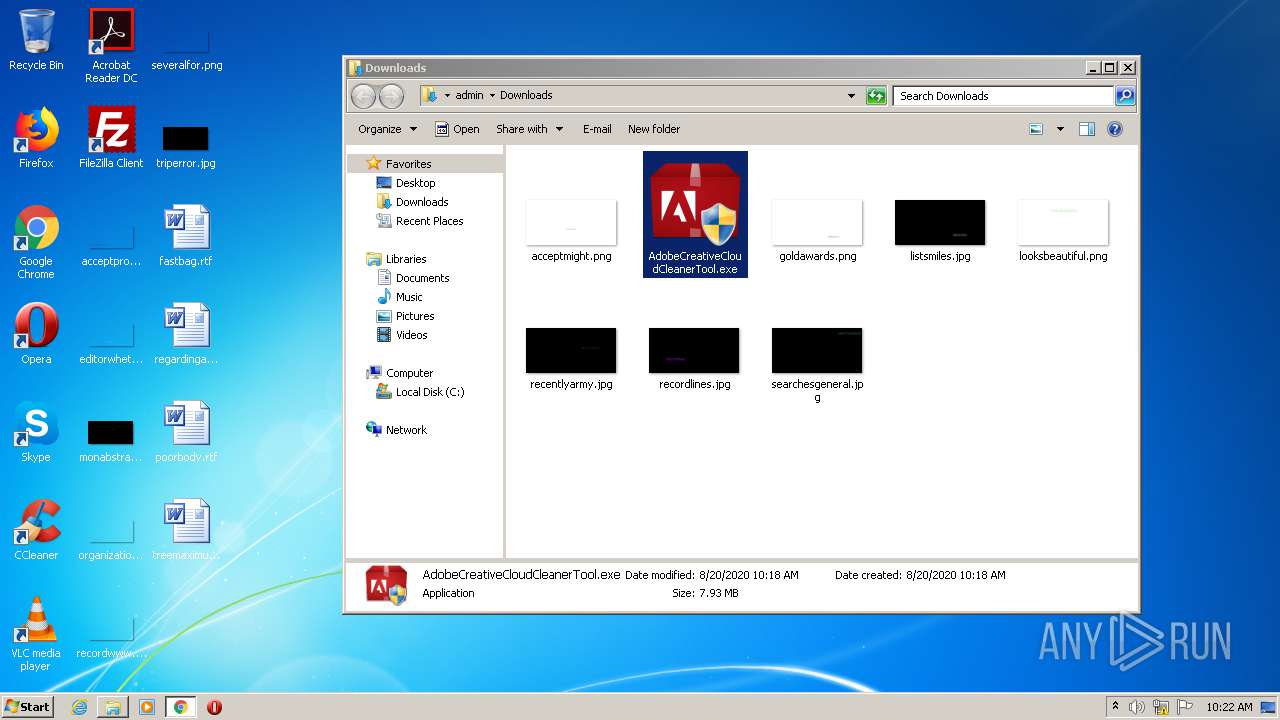
| URL: | https://swupmf.adobe[.]com/webfeed/CleanerTool/win/AdobeCreativeCloudCleanerTool.exe |
| Full analysis: | https://app.any.run/tasks/5fd1f891-0c27-4d85-80df-e877b9dff2ec |
| Verdict: | Malicious activity |
| Analysis date: | August 20, 2020, 09:17:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 20678CB562D342BA3A96AFAAFDCC5D9D |
| SHA1: | E6EDF30CFC135BF2293C8C42633E400E0A7812FE |
| SHA256: | 1DE61FB75D0B1618EBDCAE741F494A27A7A64E5A5B764D3FE91A14F148C299F4 |
| SSDEEP: | 3:N8ftjil8mJhLXlc9RzKmJdA+dAn:2lj83rby3fAj |
MALICIOUS
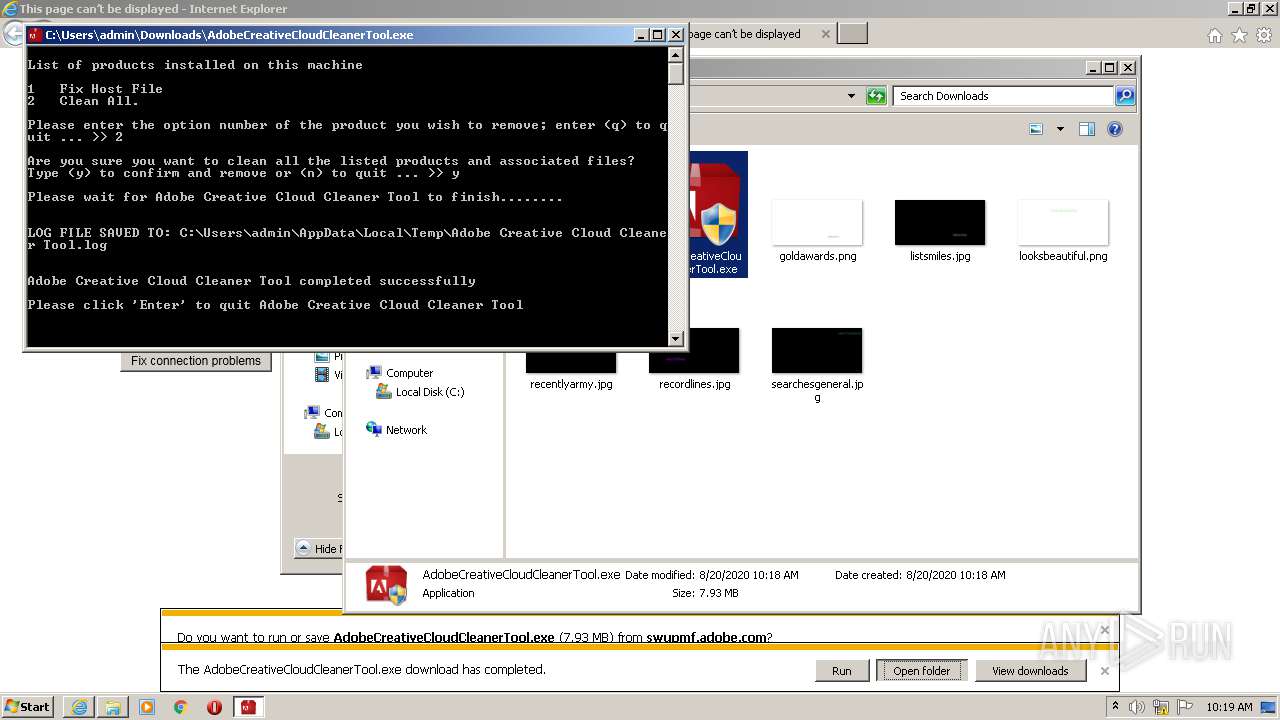
Application was dropped or rewritten from another process
- AdobeCreativeCloudCleanerTool.exe (PID: 2832)
- ACToolMain.exe (PID: 440)
- ACToolMain.exe (PID: 2732)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 3656)
- cmd.exe (PID: 1852)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 3756)
- schtasks.exe (PID: 692)
Loads dropped or rewritten executable
- ACToolMain.exe (PID: 2732)
SUSPICIOUS
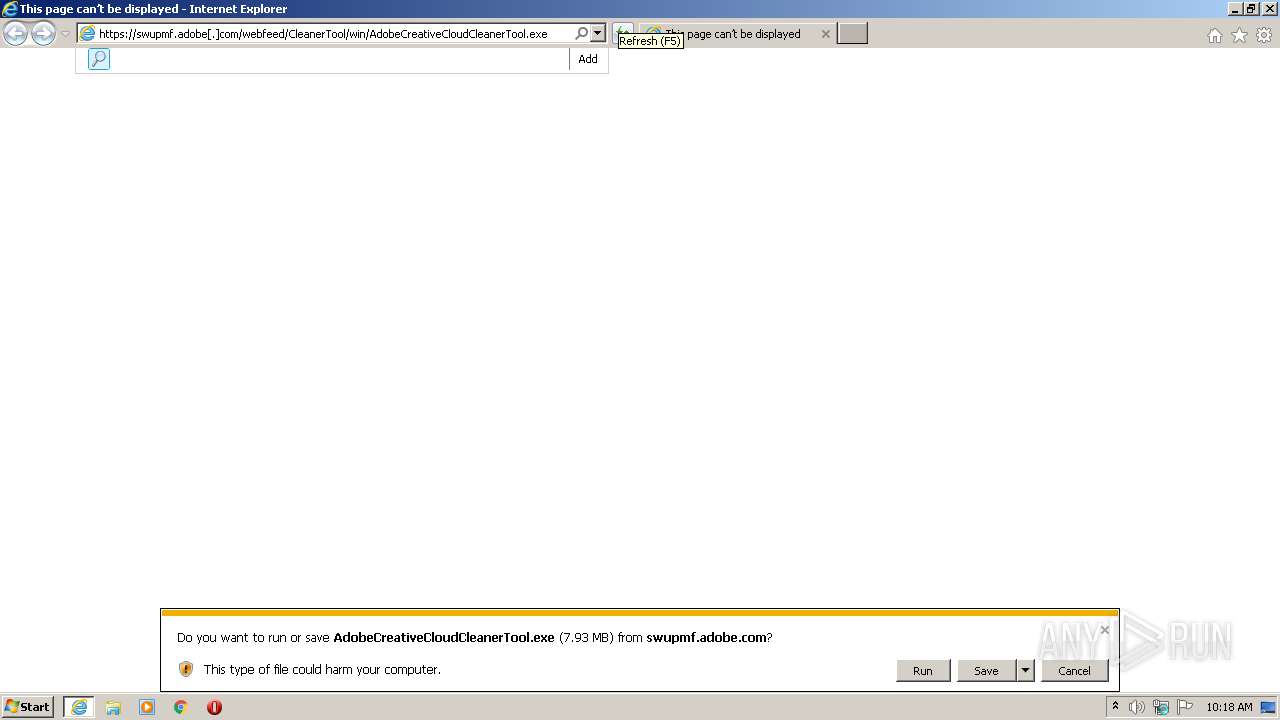
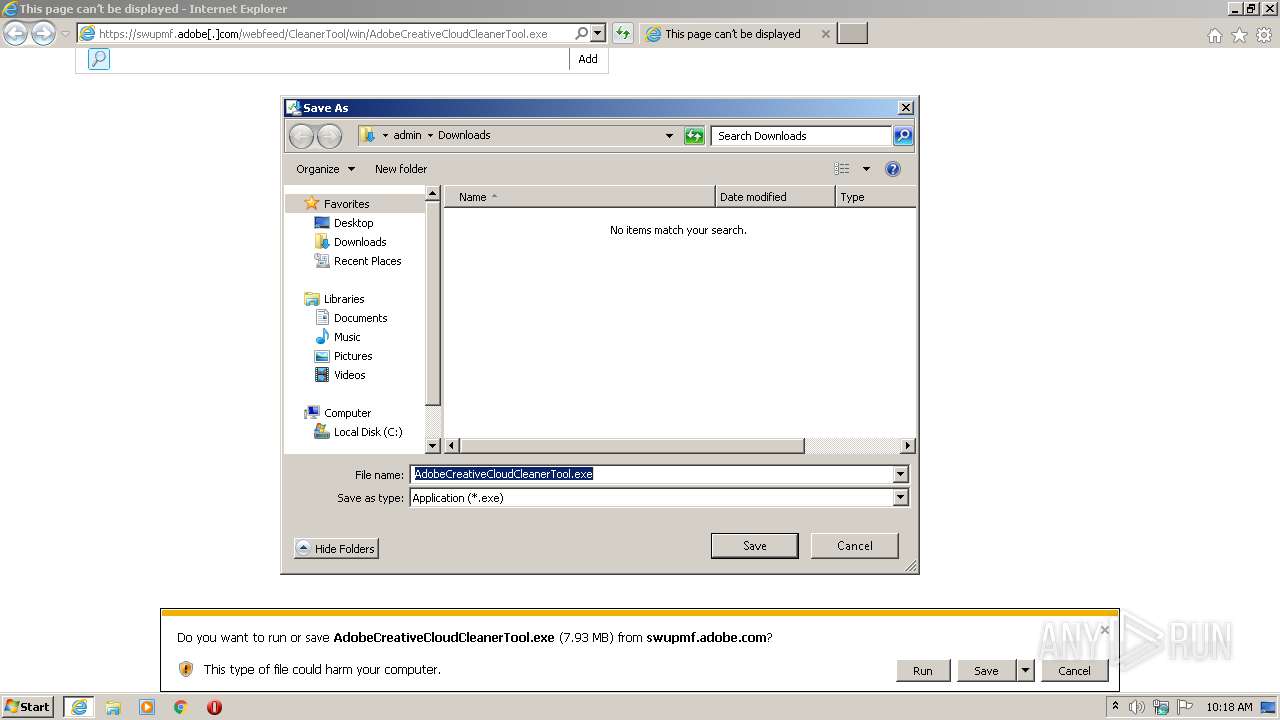
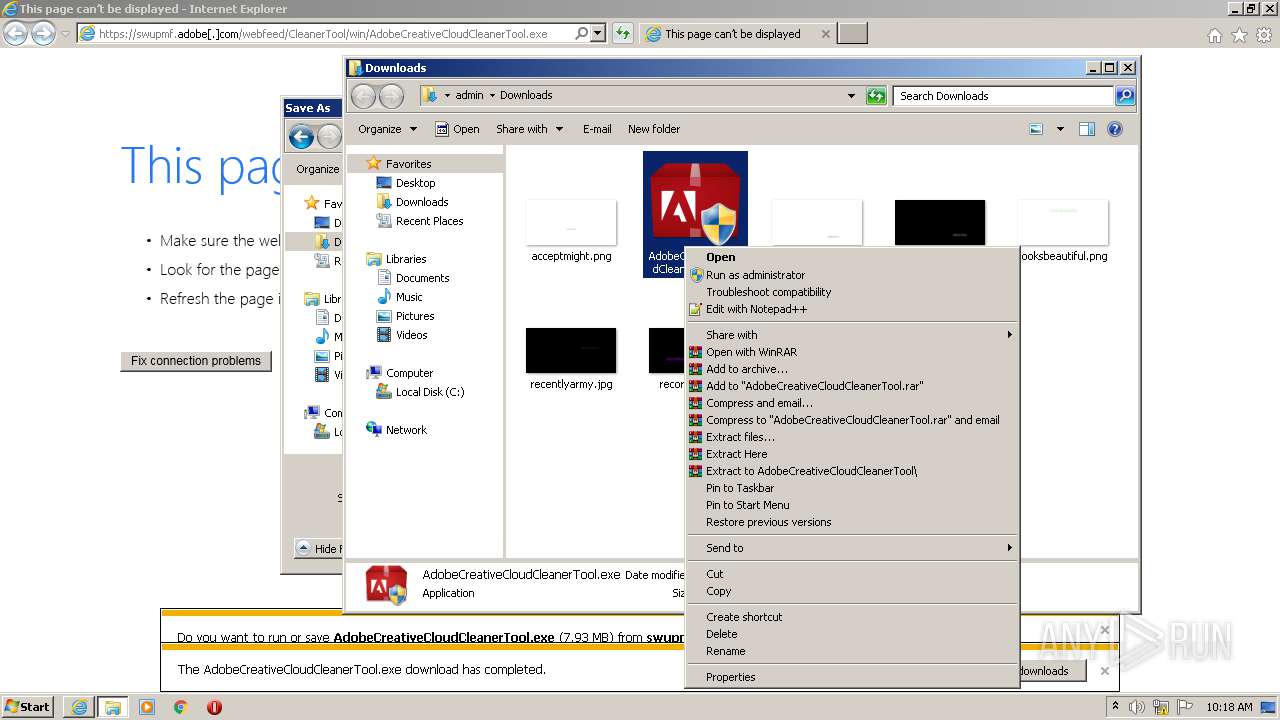
Executable content was dropped or overwritten
- iexplore.exe (PID: 2664)
- iexplore.exe (PID: 2508)
- AdobeCreativeCloudCleanerTool.exe (PID: 2832)
- ACToolMain.exe (PID: 440)
Creates files in the program directory
- AdobeCreativeCloudCleanerTool.exe (PID: 2832)
Application launched itself
- ACToolMain.exe (PID: 440)
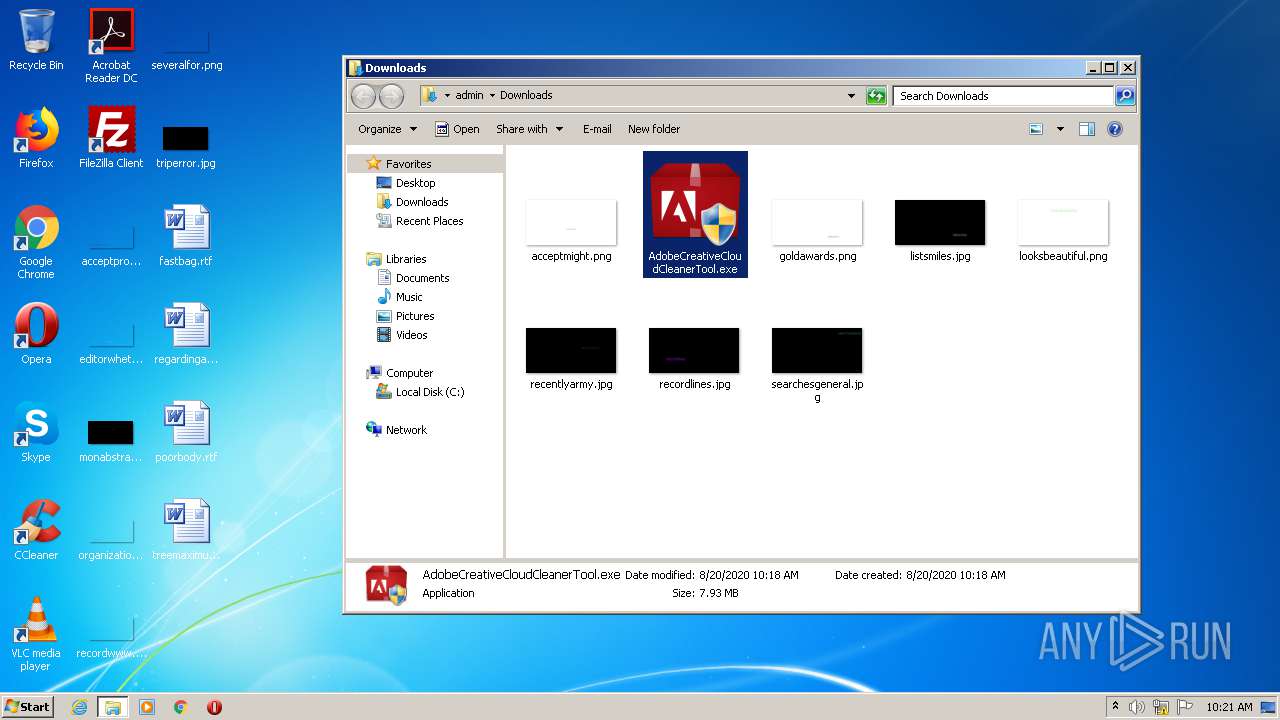
Loads Python modules
- ACToolMain.exe (PID: 2732)
Starts CMD.EXE for commands execution
- ACToolMain.exe (PID: 2732)
Uses TASKKILL.EXE to kill process
- ACToolMain.exe (PID: 2732)
INFO
Application launched itself
- iexplore.exe (PID: 2508)
- chrome.exe (PID: 2084)
Reads Internet Cache Settings
- iexplore.exe (PID: 2508)
- iexplore.exe (PID: 2664)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2508)
Changes internet zones settings
- iexplore.exe (PID: 2508)
Reads internet explorer settings
- iexplore.exe (PID: 2664)
Reads settings of System Certificates
- iexplore.exe (PID: 2664)
- iexplore.exe (PID: 2508)
- chrome.exe (PID: 2392)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2508)
Creates files in the user directory
- iexplore.exe (PID: 2508)
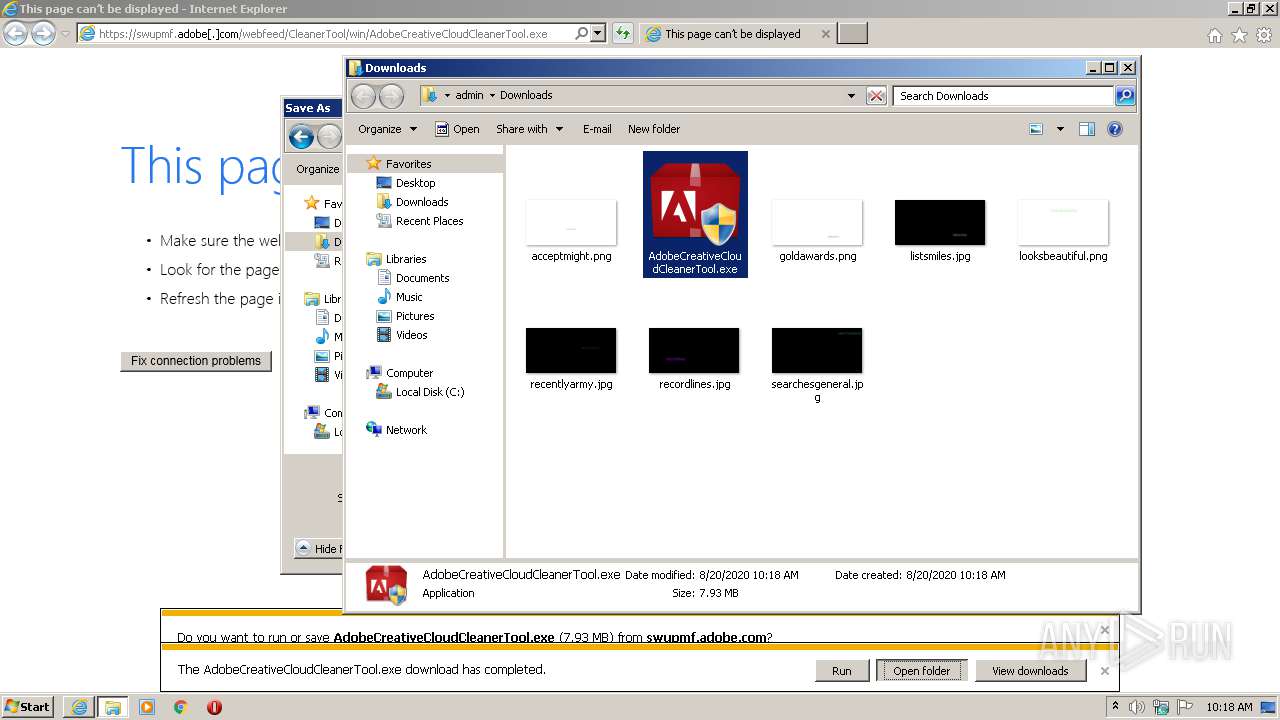
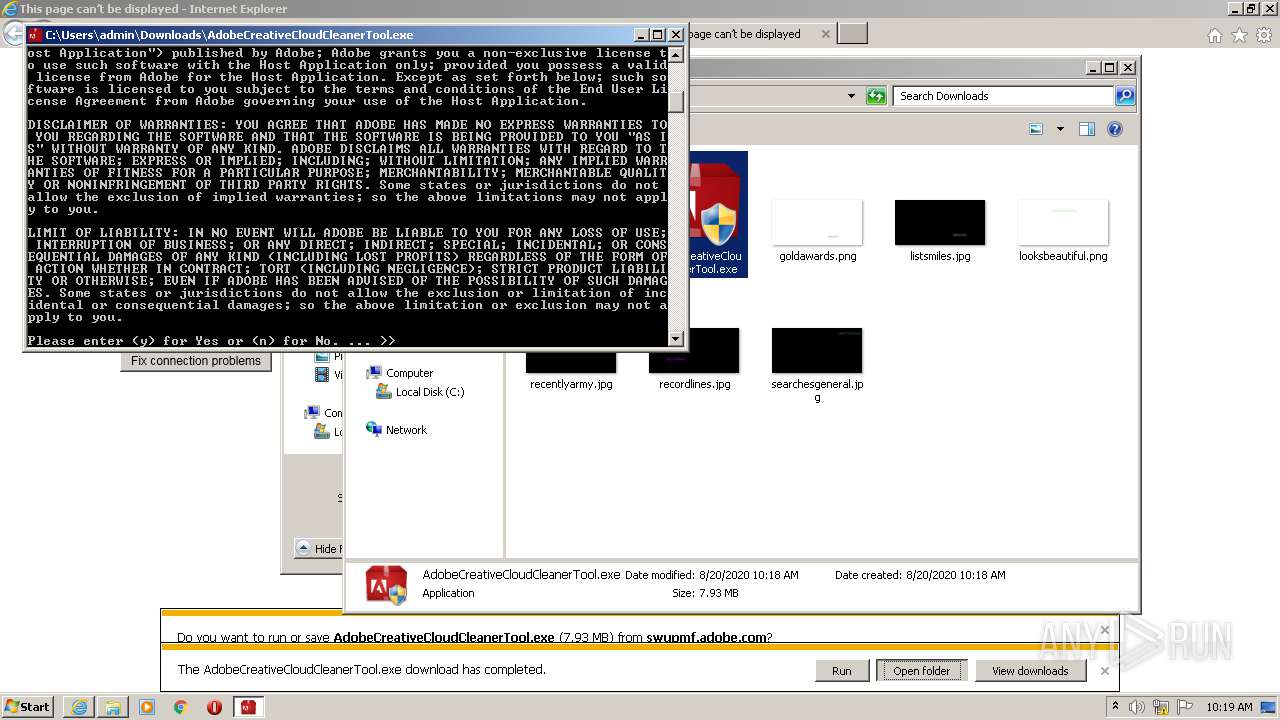
Manual execution by user
- AdobeCreativeCloudCleanerTool.exe (PID: 2832)
- chrome.exe (PID: 2084)
Changes settings of System certificates
- iexplore.exe (PID: 2508)
Dropped object may contain Bitcoin addresses
- AdobeCreativeCloudCleanerTool.exe (PID: 2832)
Reads the hosts file
- chrome.exe (PID: 2084)
- chrome.exe (PID: 2392)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
85
Monitored processes
40
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 440 | "C:\Program Files\Common Files\Adobe\AdobeCreativeCloudCleanerTool\ACToolMain.exe" | C:\Program Files\Common Files\Adobe\AdobeCreativeCloudCleanerTool\ACToolMain.exe | AdobeCreativeCloudCleanerTool.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: HIGH Description: Adobe Creative Cloud Cleaner Tool Exit code: 0 Version: 4.3.0.109 Modules
| |||||||||||||||
| 584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,9690037163143494794,8195326034480696251,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2748606706103477648 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2400 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 692 | schtasks /delete /TN "AdobeUpdater Task-USER-PC-admin" /F | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 948 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,9690037163143494794,8195326034480696251,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11578359179168120612 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3232 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 972 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,9690037163143494794,8195326034480696251,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14759951565022526083 --renderer-client-id=23 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4568 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1020 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,9690037163143494794,8195326034480696251,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17091895886153118550 --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3912 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1452 | taskkill /F /FI "IMAGENAME eq AAM Updates Notifier.exe" | C:\Windows\system32\taskkill.exe | — | ACToolMain.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1852 | C:\Windows\system32\cmd.exe /c schtasks /delete /TN "AdobeUpdater Task-USER-PC-admin" /F | C:\Windows\system32\cmd.exe | — | ACToolMain.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2028 | C:\Windows\system32\cmd.exe /c cls | C:\Windows\system32\cmd.exe | — | ACToolMain.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2084 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 207
Read events
1 939
Write events
254
Delete events
14
Modification events
| (PID) Process: | (2508) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3620941952 | |||
| (PID) Process: | (2508) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30832338 | |||
| (PID) Process: | (2508) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2508) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2508) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2508) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2508) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2508) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A3000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2508) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2508) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
33
Suspicious files
92
Text files
105
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2508 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2664 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab5A7F.tmp | — | |
MD5:— | SHA256:— | |||
| 2664 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar5A80.tmp | — | |
MD5:— | SHA256:— | |||
| 2508 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab8D47.tmp | — | |
MD5:— | SHA256:— | |||
| 2508 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar8D48.tmp | — | |
MD5:— | SHA256:— | |||
| 2508 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\ver8D69.tmp | — | |
MD5:— | SHA256:— | |||
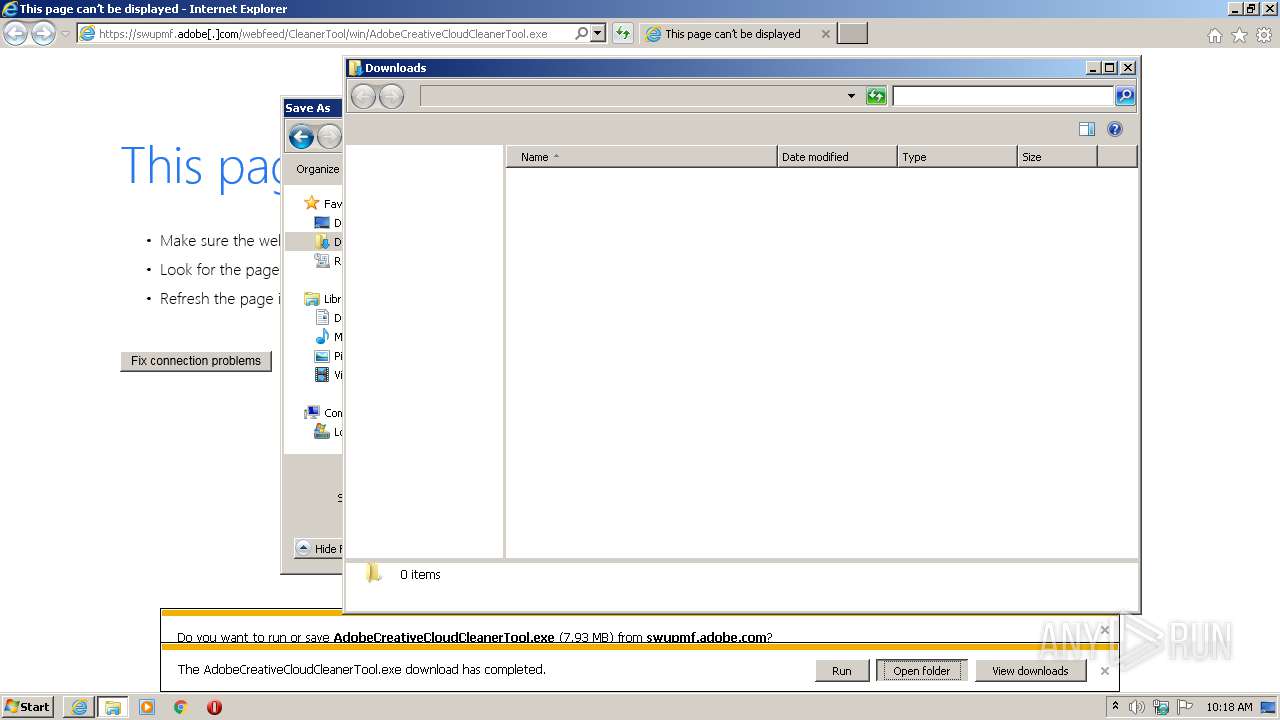
| 2664 | iexplore.exe | C:\Users\admin\Downloads\AdobeCreativeCloudCleanerTool.exe.1za4t3f.partial | — | |
MD5:— | SHA256:— | |||
| 2508 | iexplore.exe | C:\Users\admin\Downloads\AdobeCreativeCloudCleanerTool.exe.1za4t3f.partial:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 2508 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\56FUHQK4.txt | — | |
MD5:— | SHA256:— | |||
| 2508 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\KIMSIFLG.txt | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
113
DNS requests
92
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2664 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
1048 | svchost.exe | GET | 200 | 2.21.38.54:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | FR | der | 813 b | whitelisted |
2664 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
2508 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2508 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2508 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2508 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2508 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2664 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2508 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2508 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2508 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1048 | svchost.exe | 2.21.38.54:80 | www.microsoft.com | GTT Communications Inc. | FR | malicious |
2508 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2392 | chrome.exe | 216.58.212.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2392 | chrome.exe | 172.217.23.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
2392 | chrome.exe | 172.217.18.3:443 | www.google.com.ua | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
swupmf.adobe.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
dns.msftncsi.com |
| shared |
clientservices.googleapis.com |
| whitelisted |