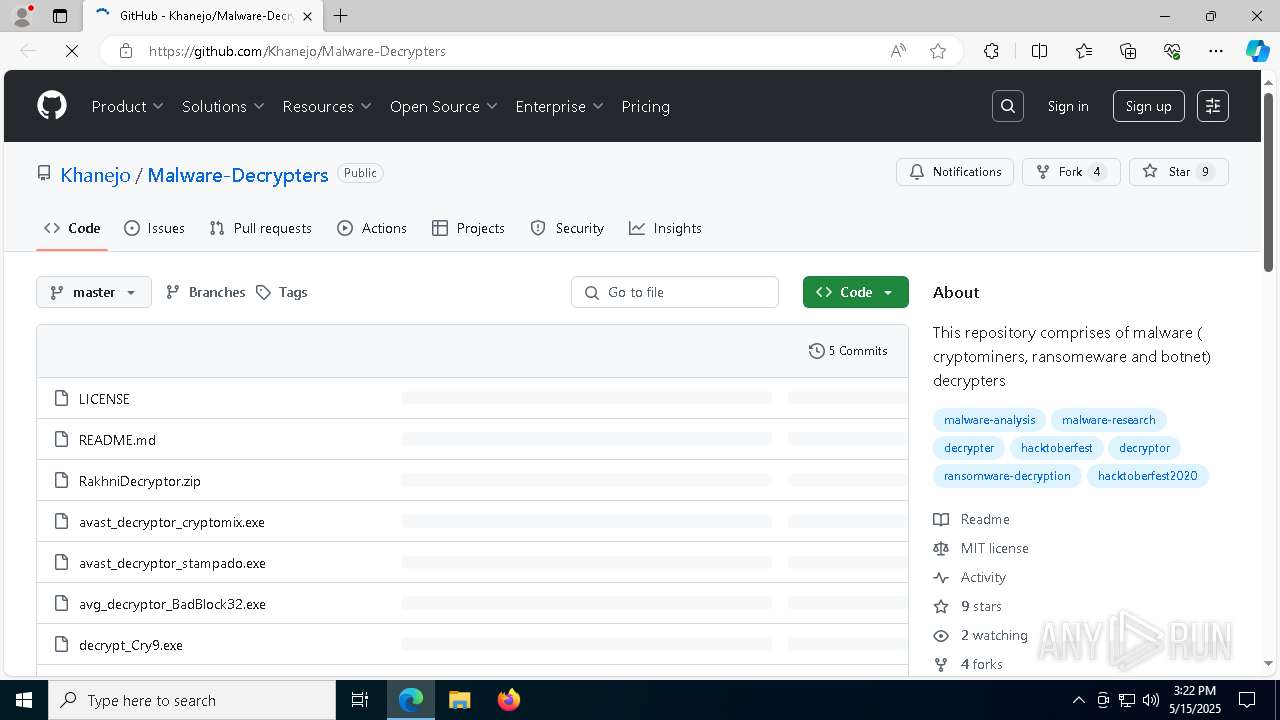
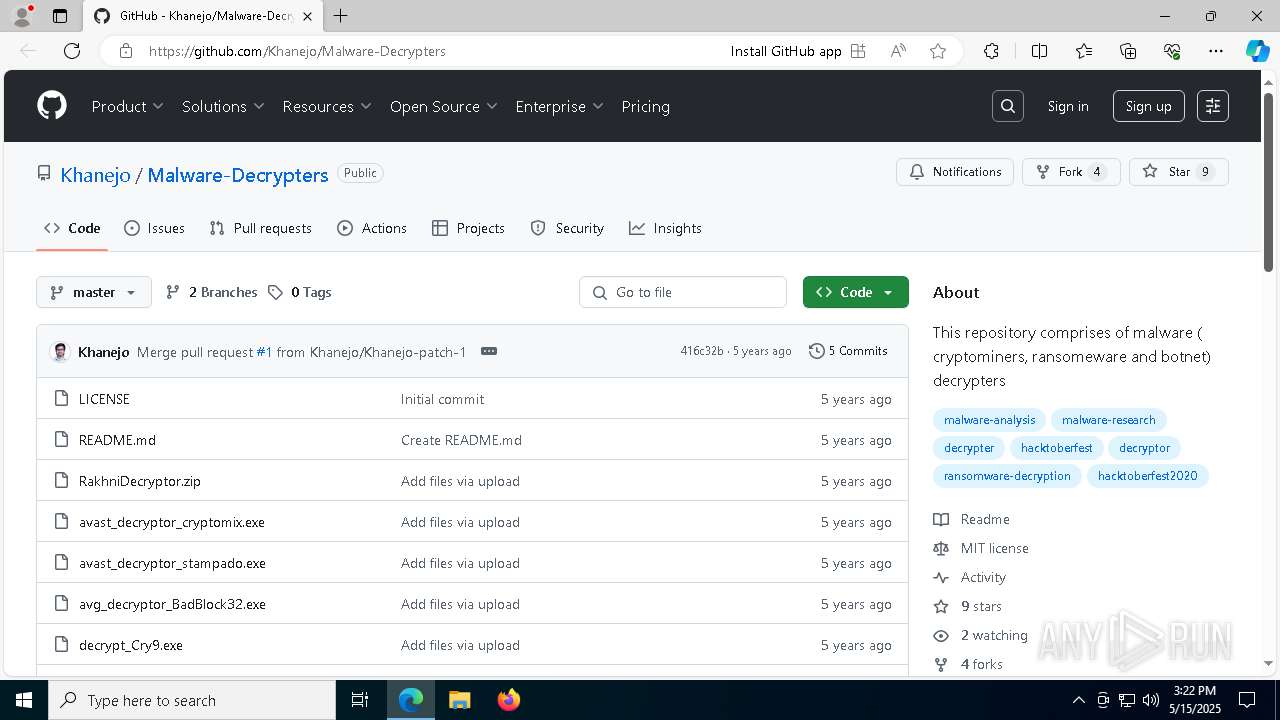
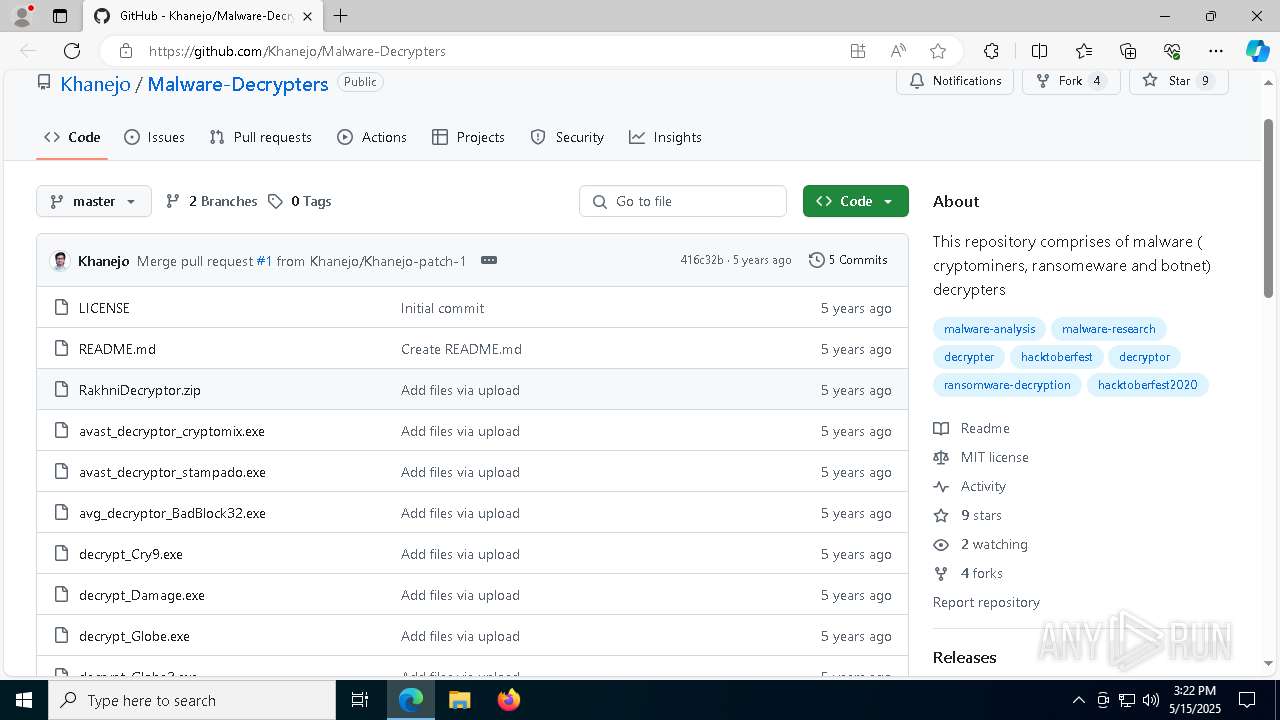
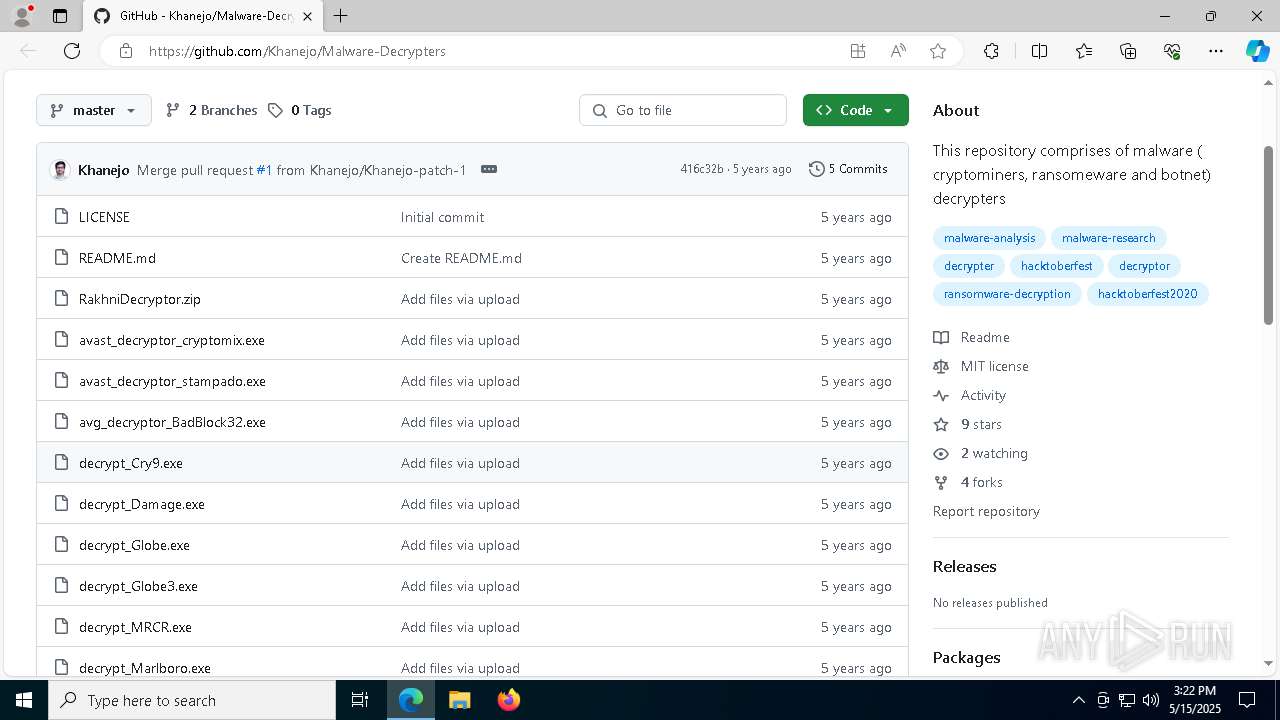
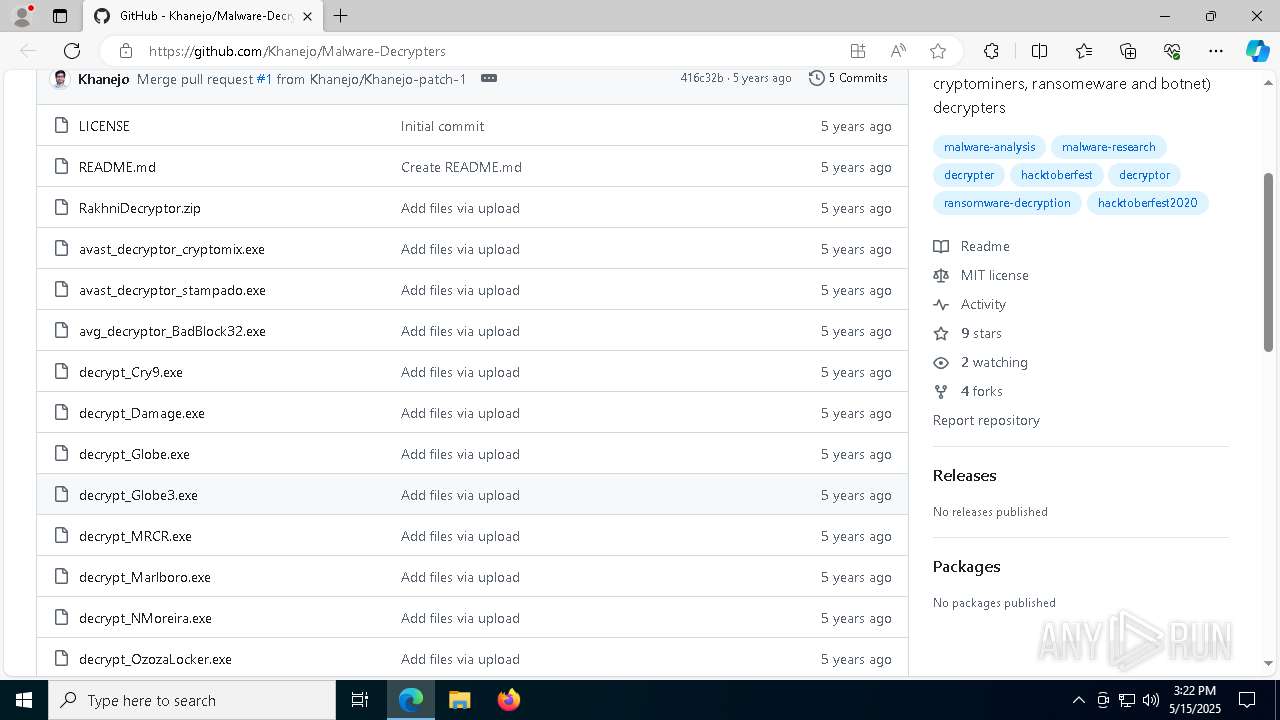
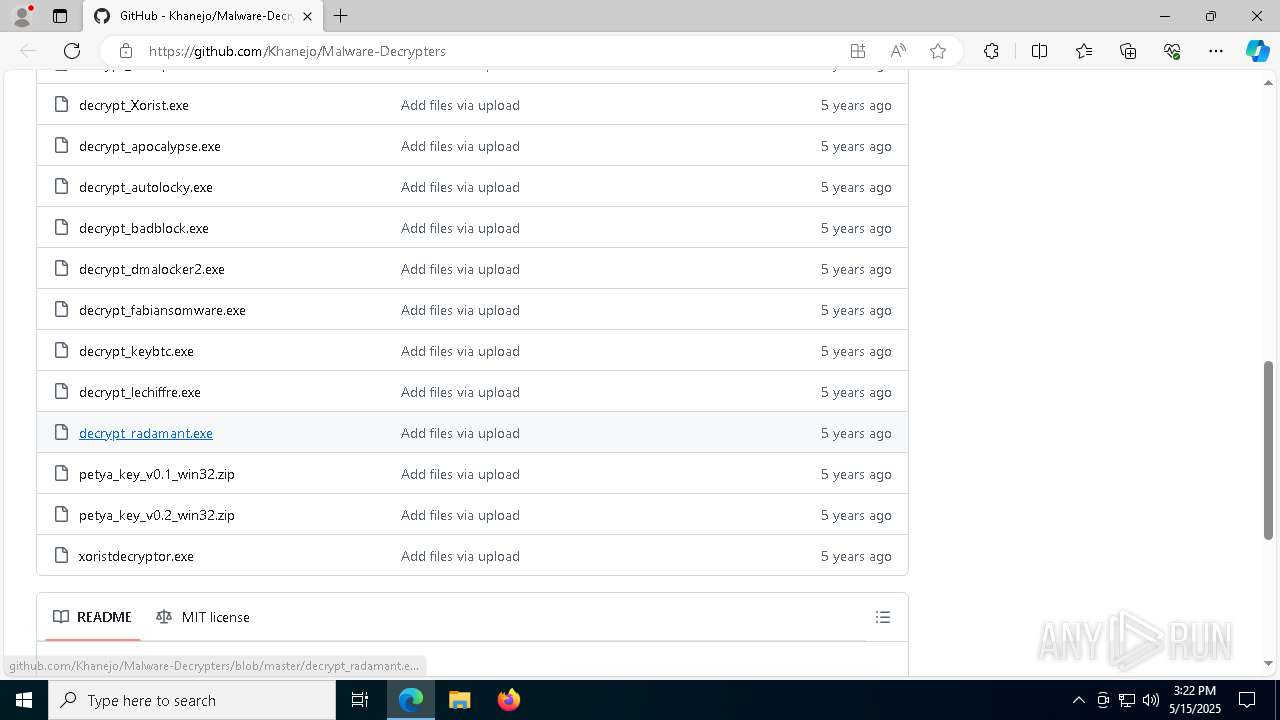
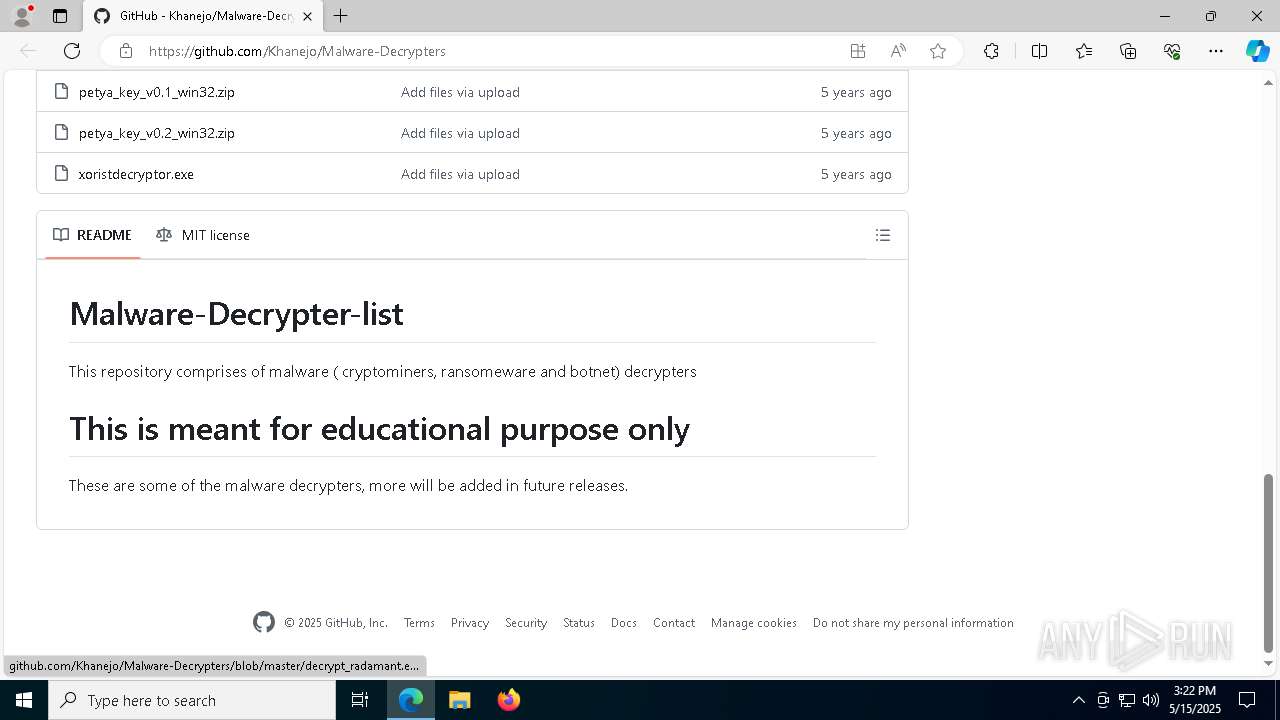
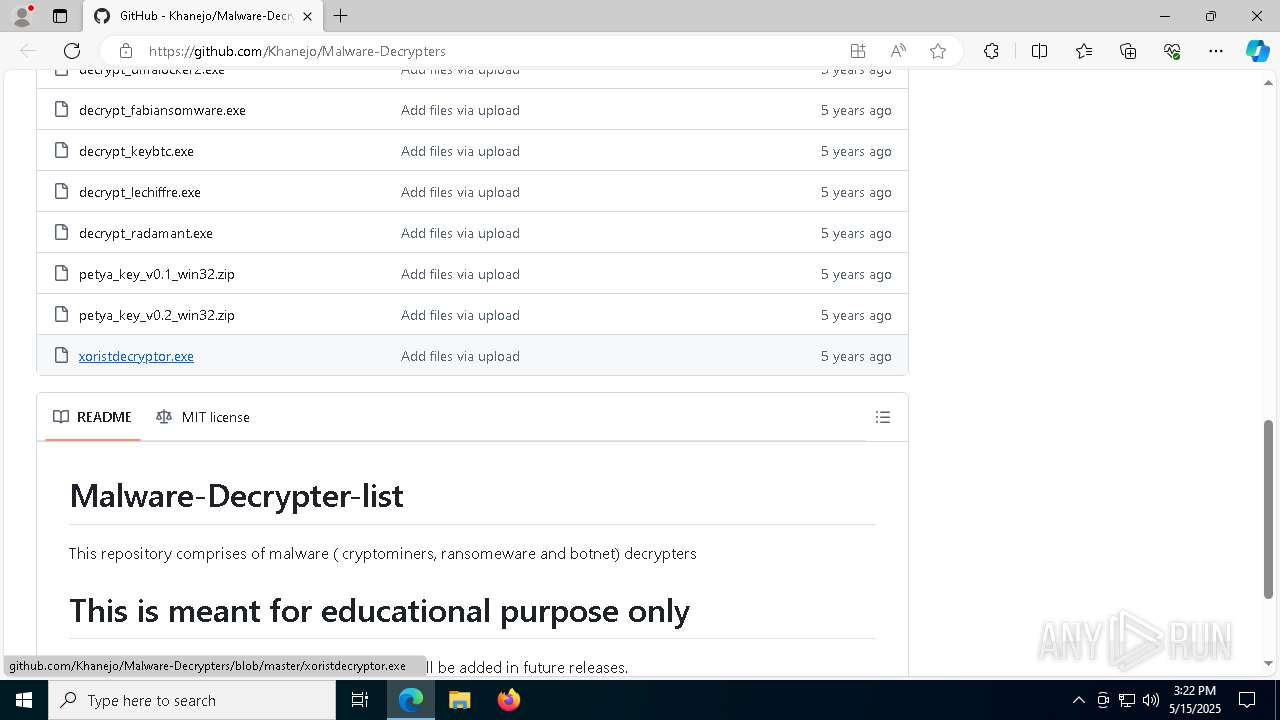
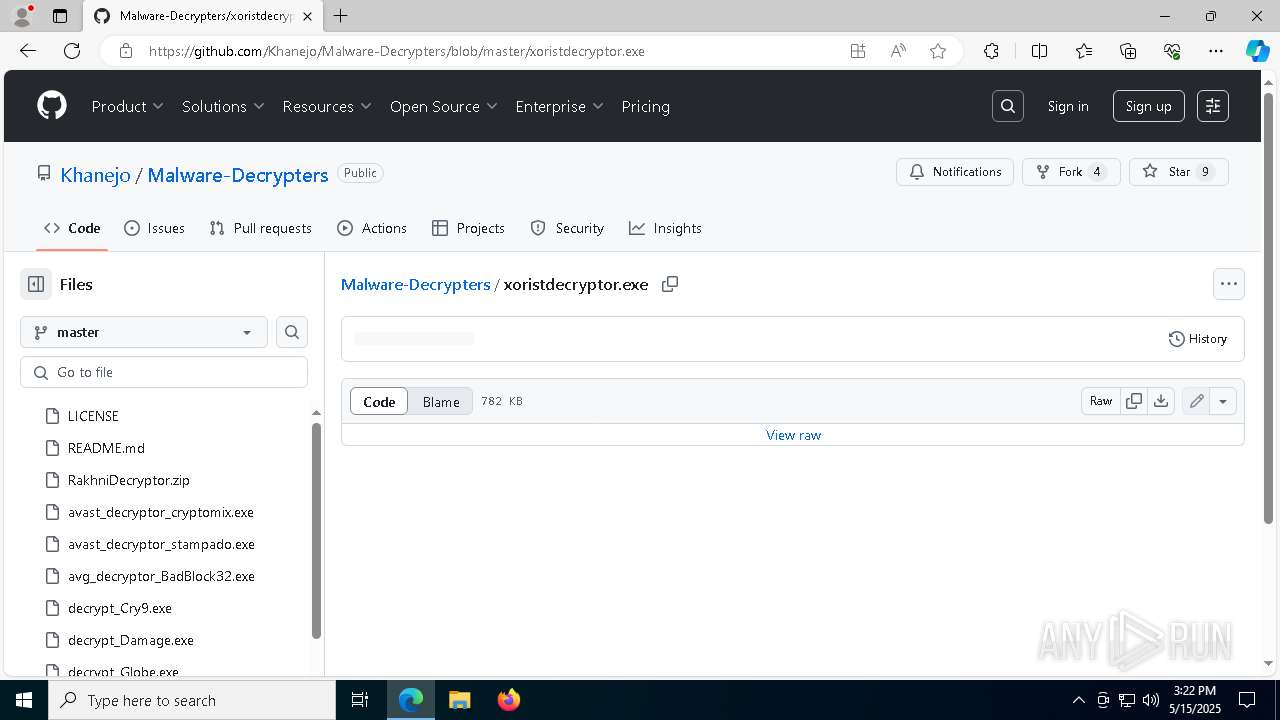
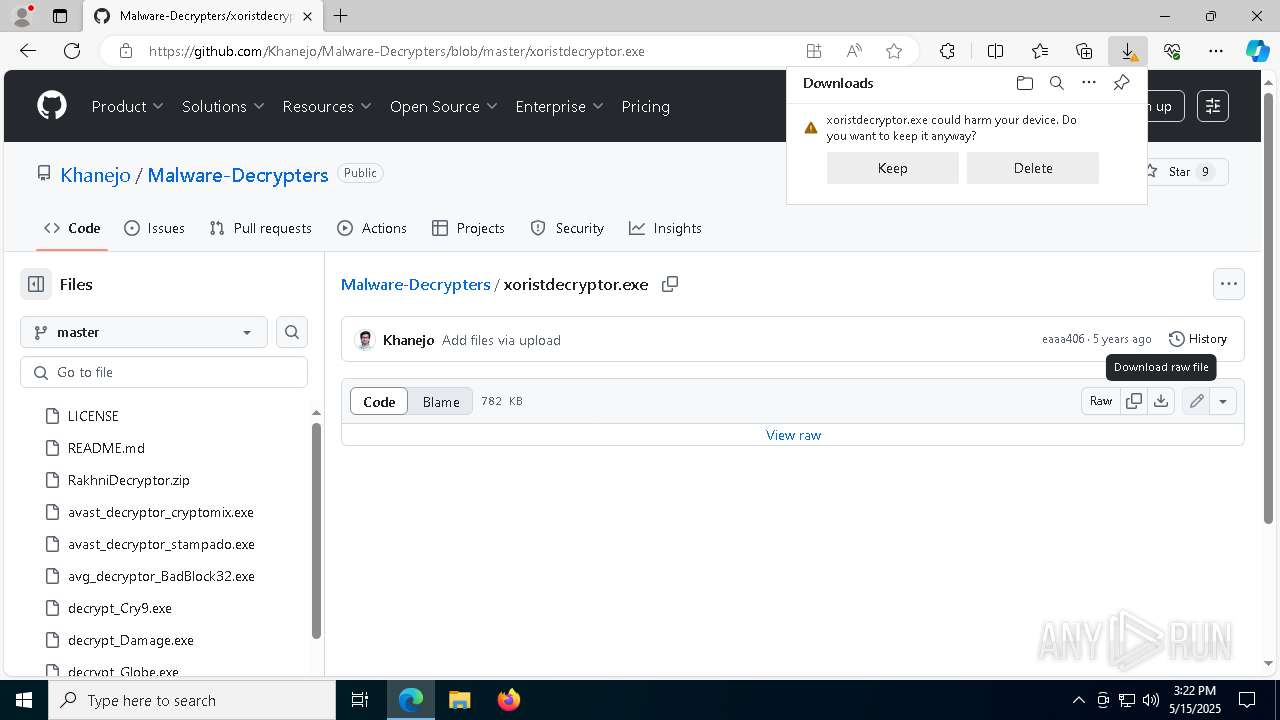
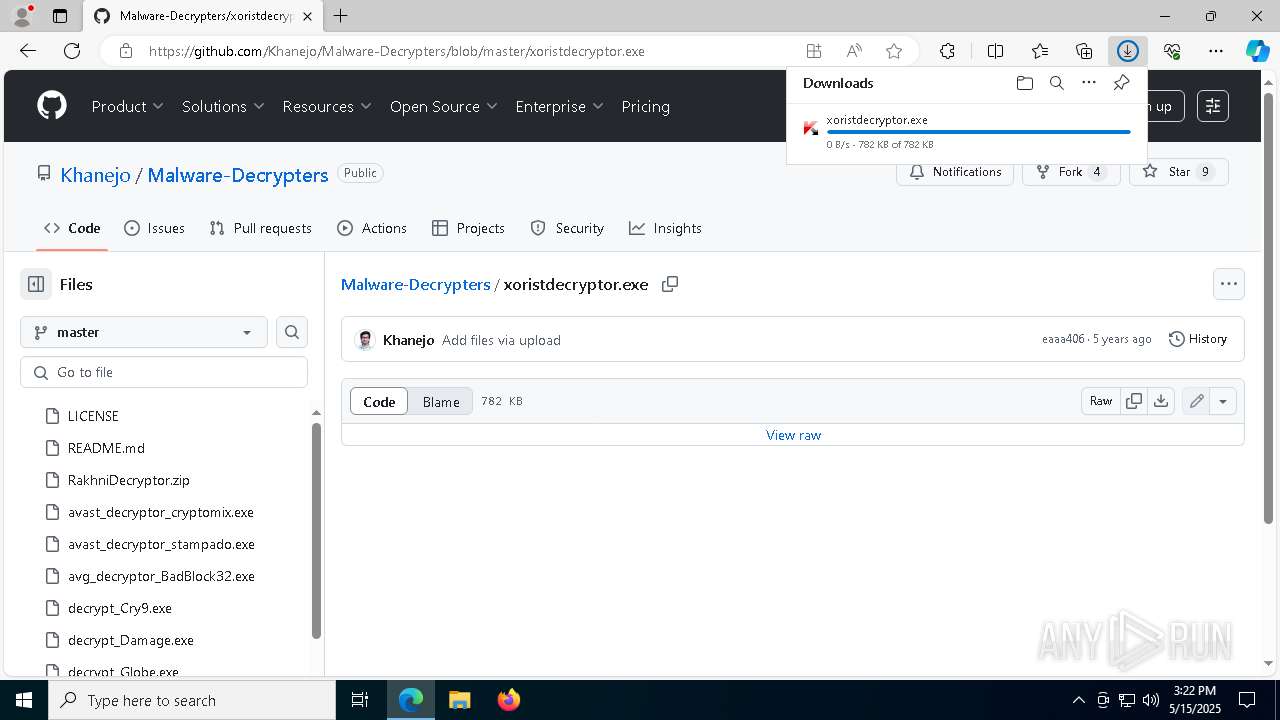
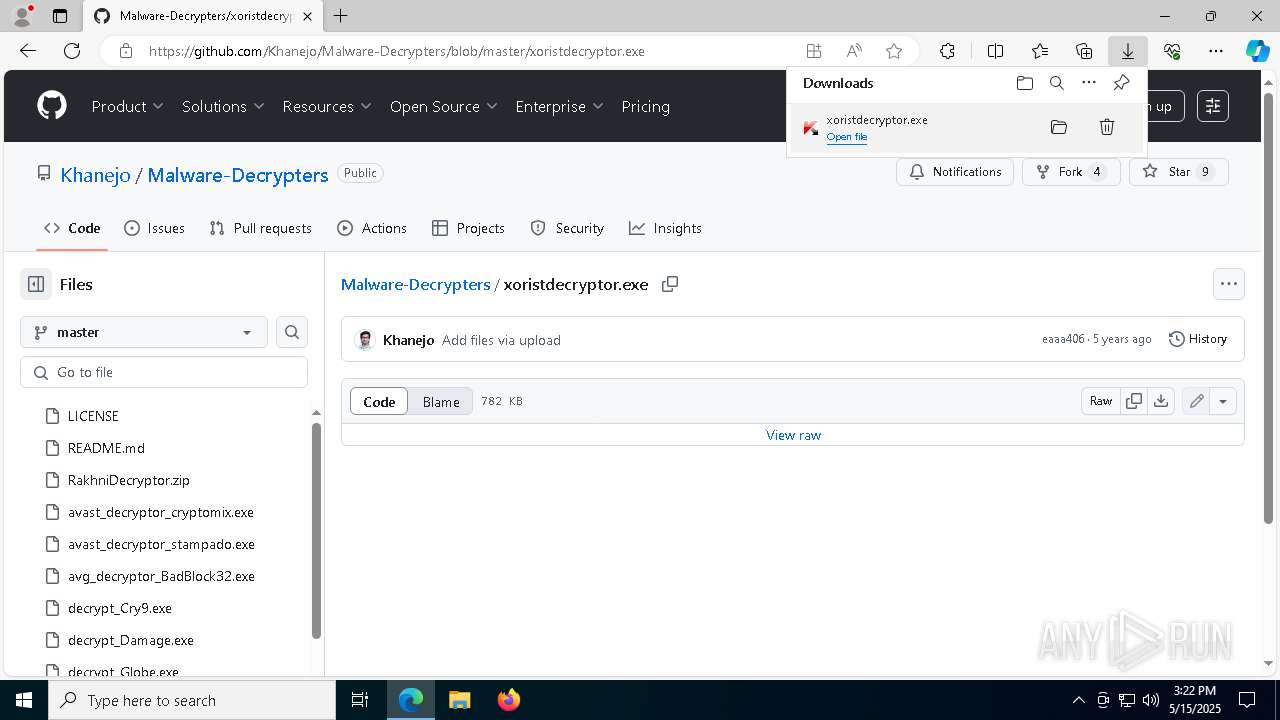
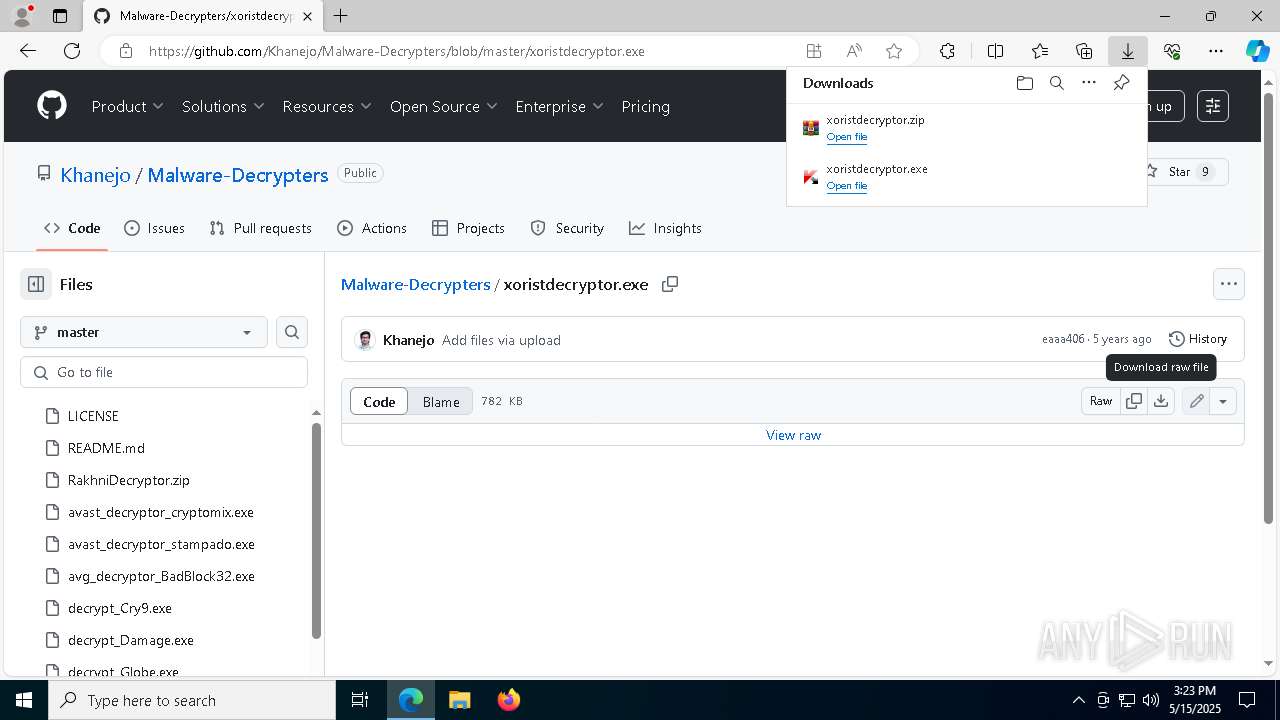
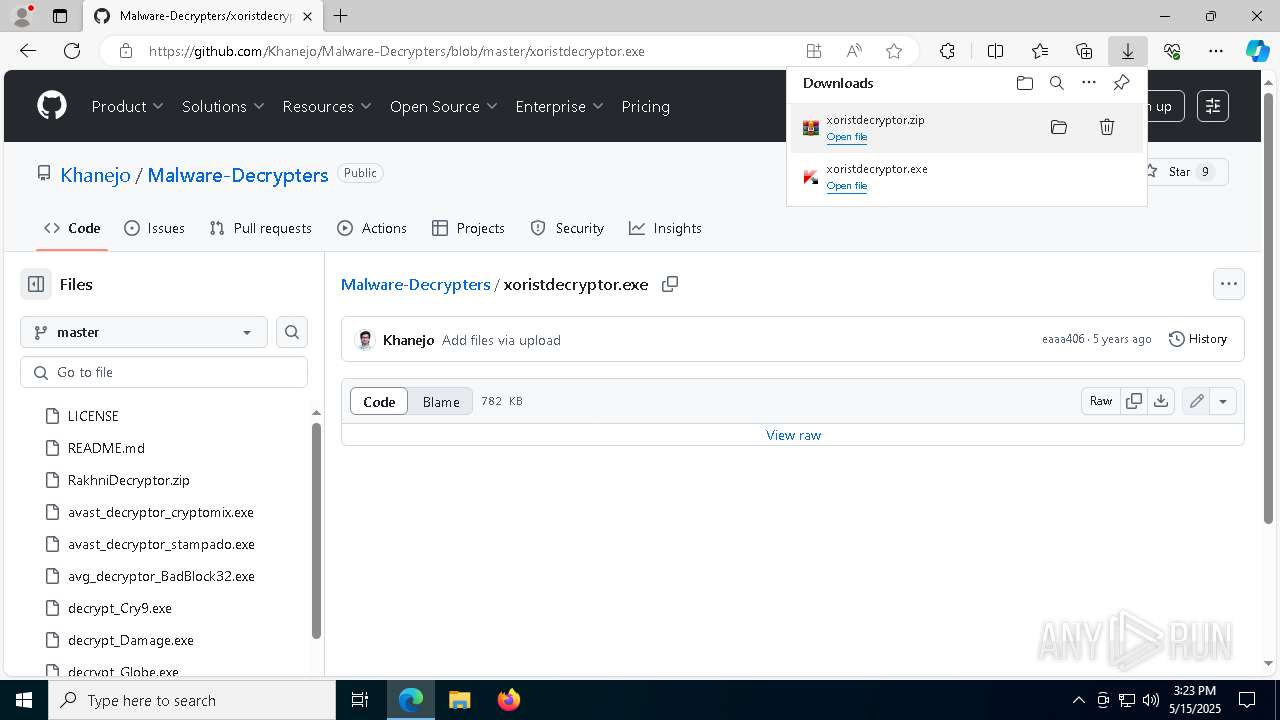
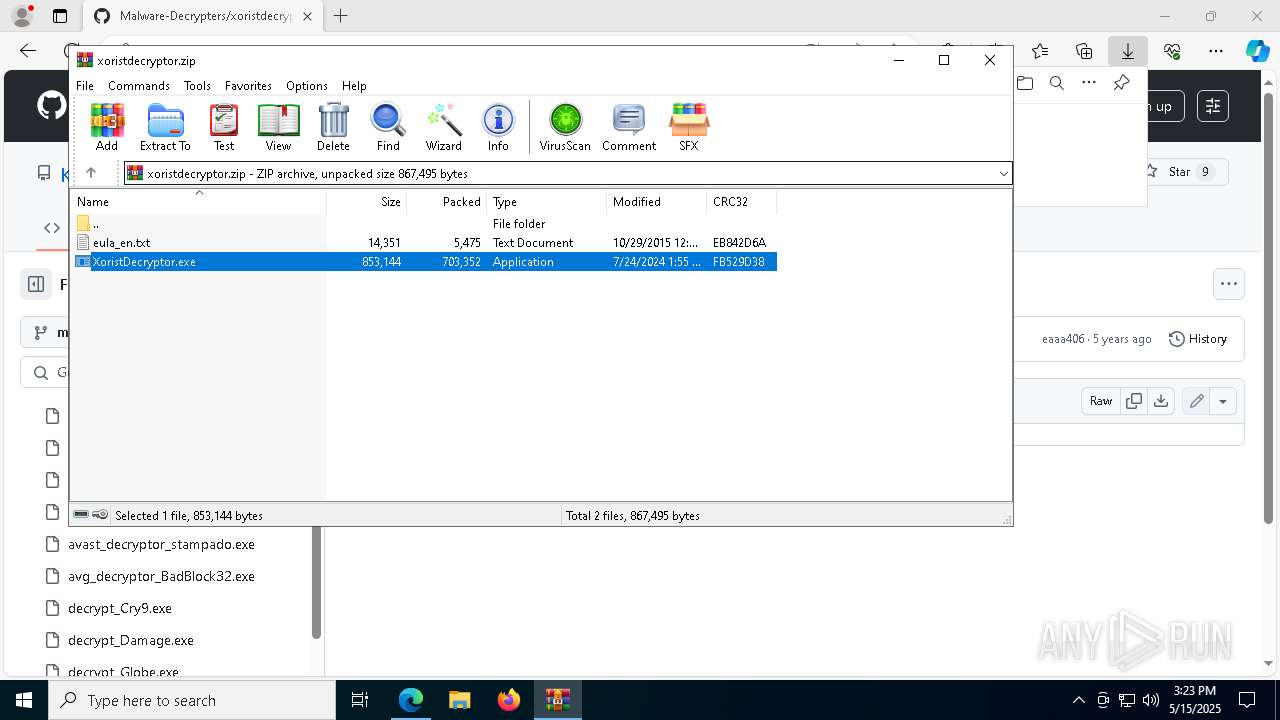
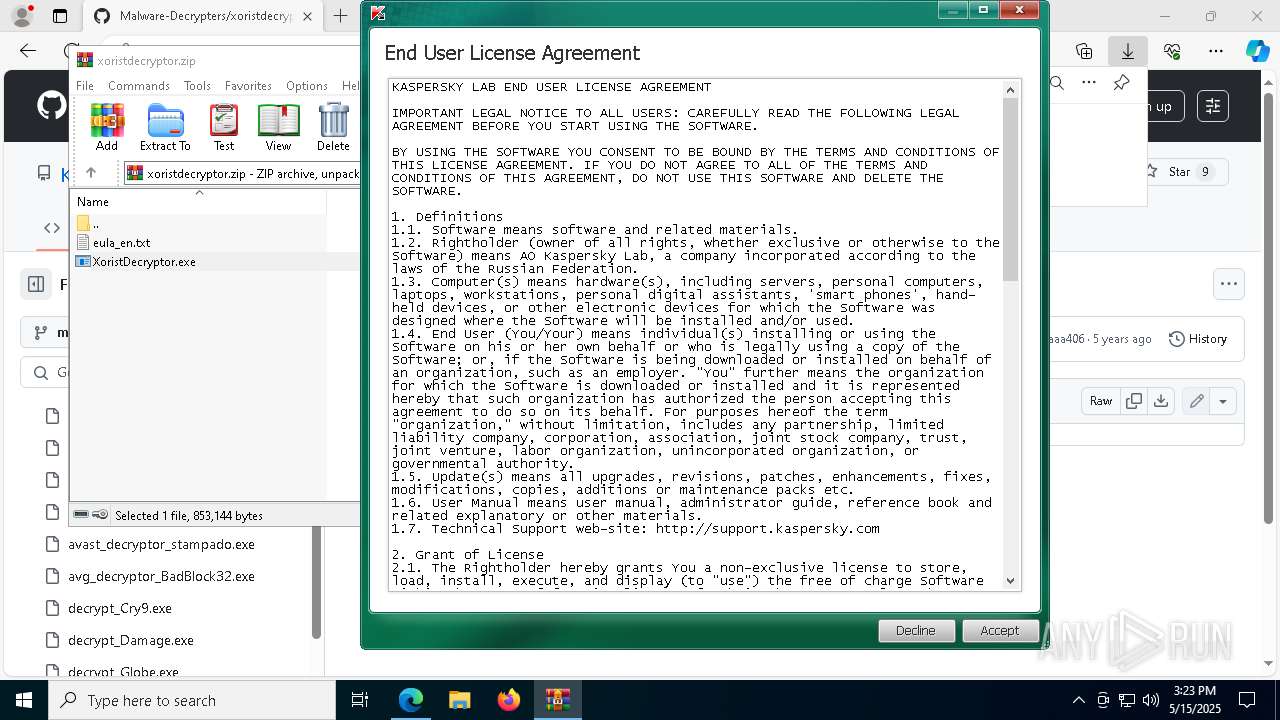
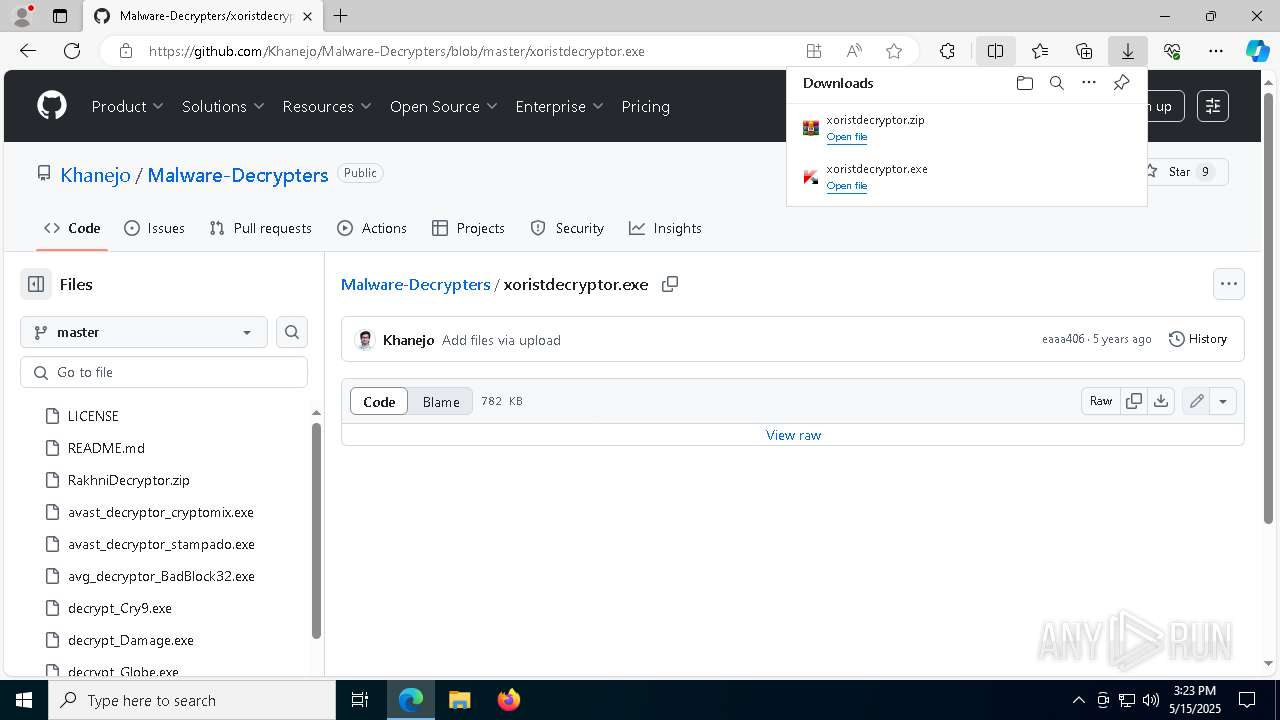
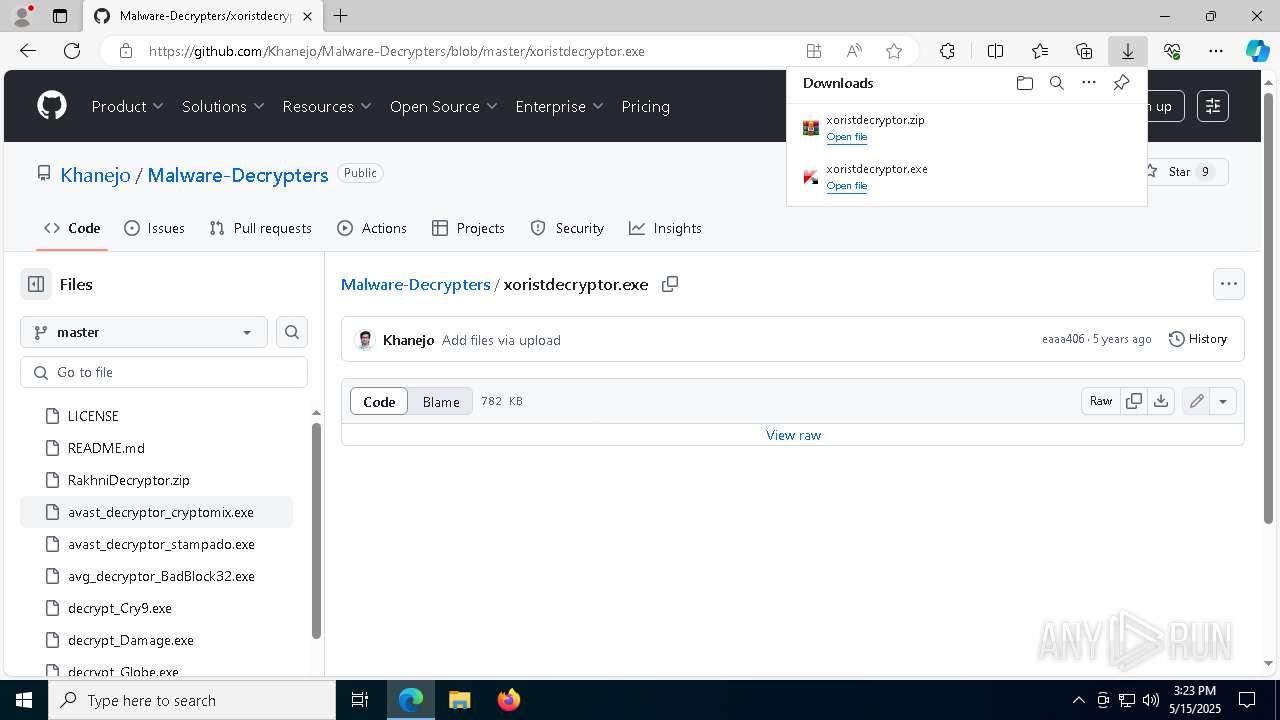
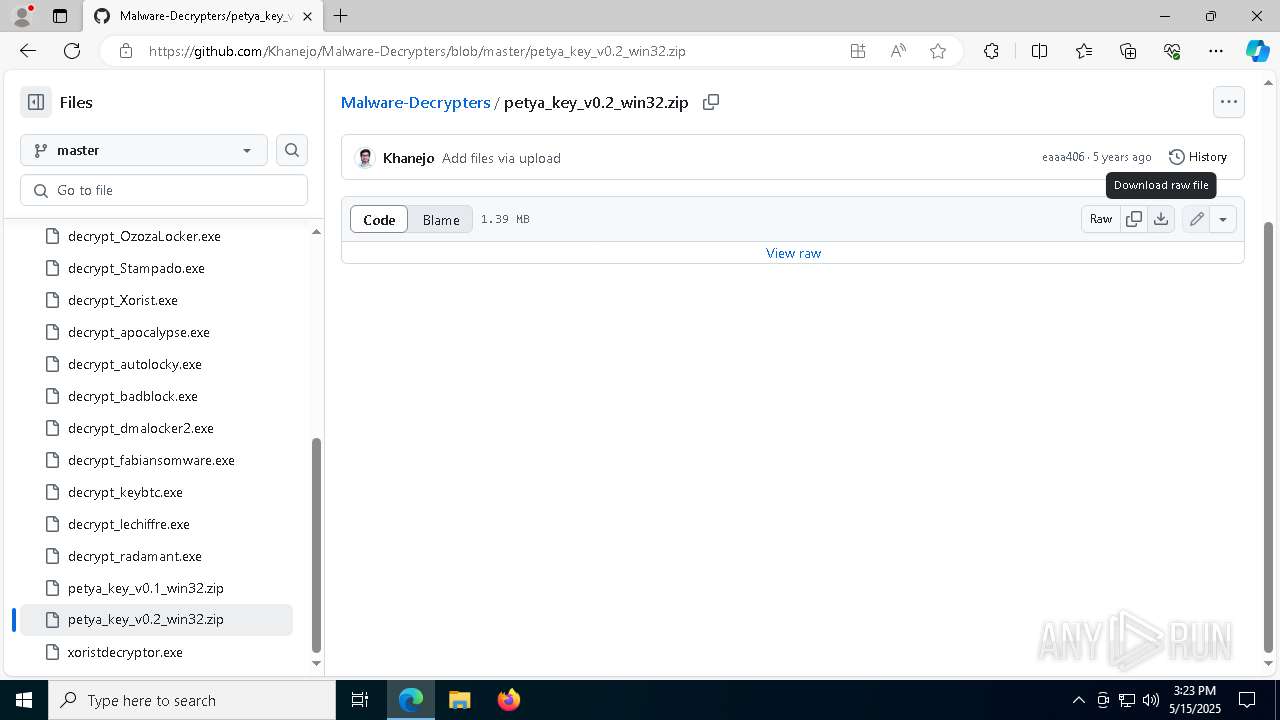
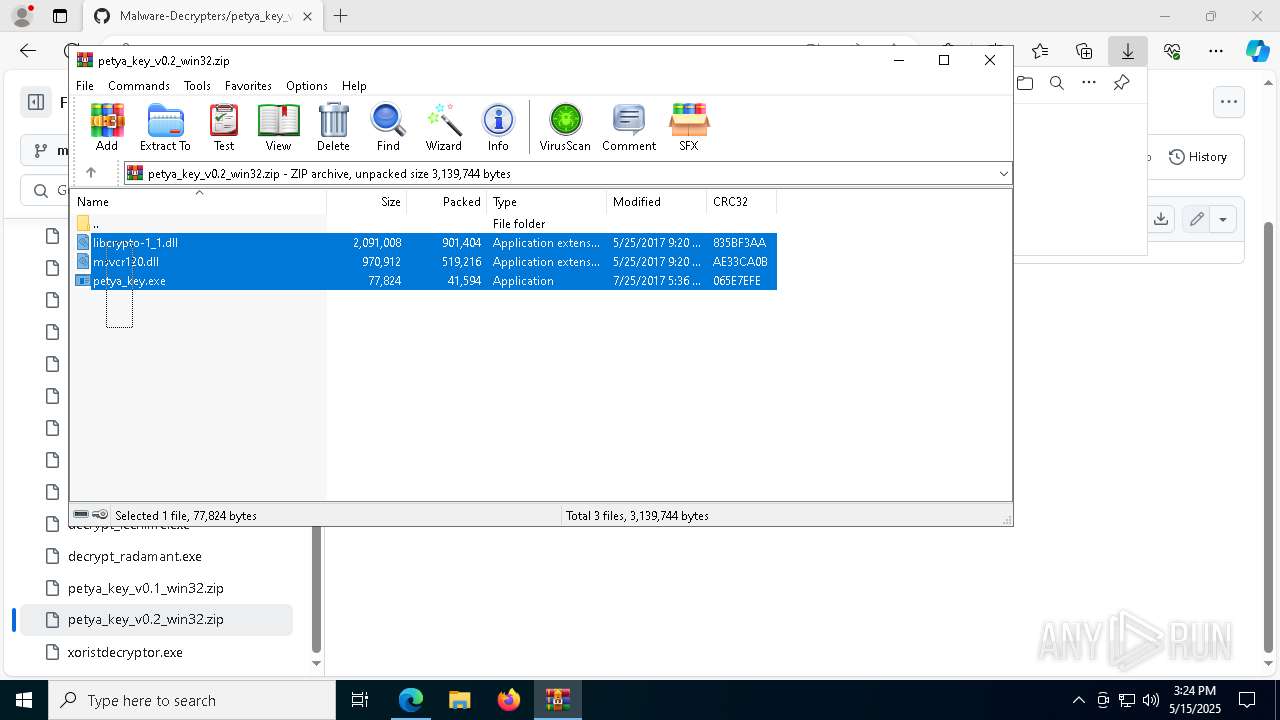
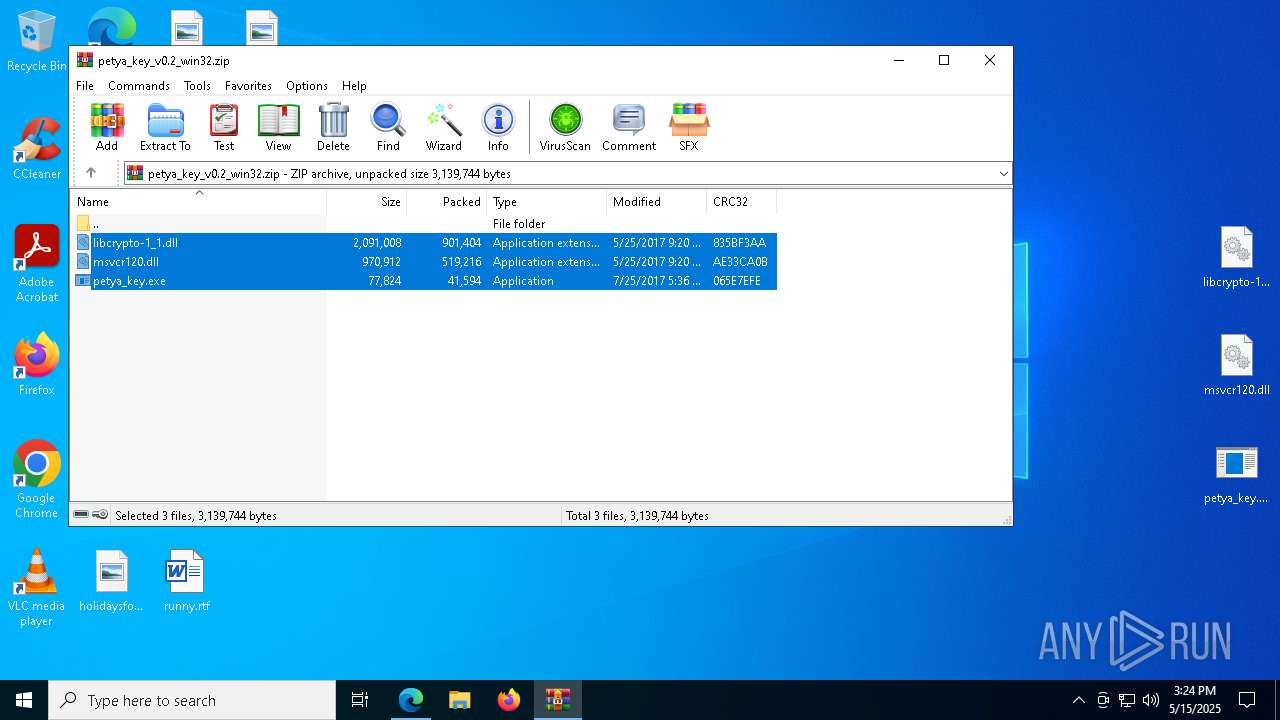
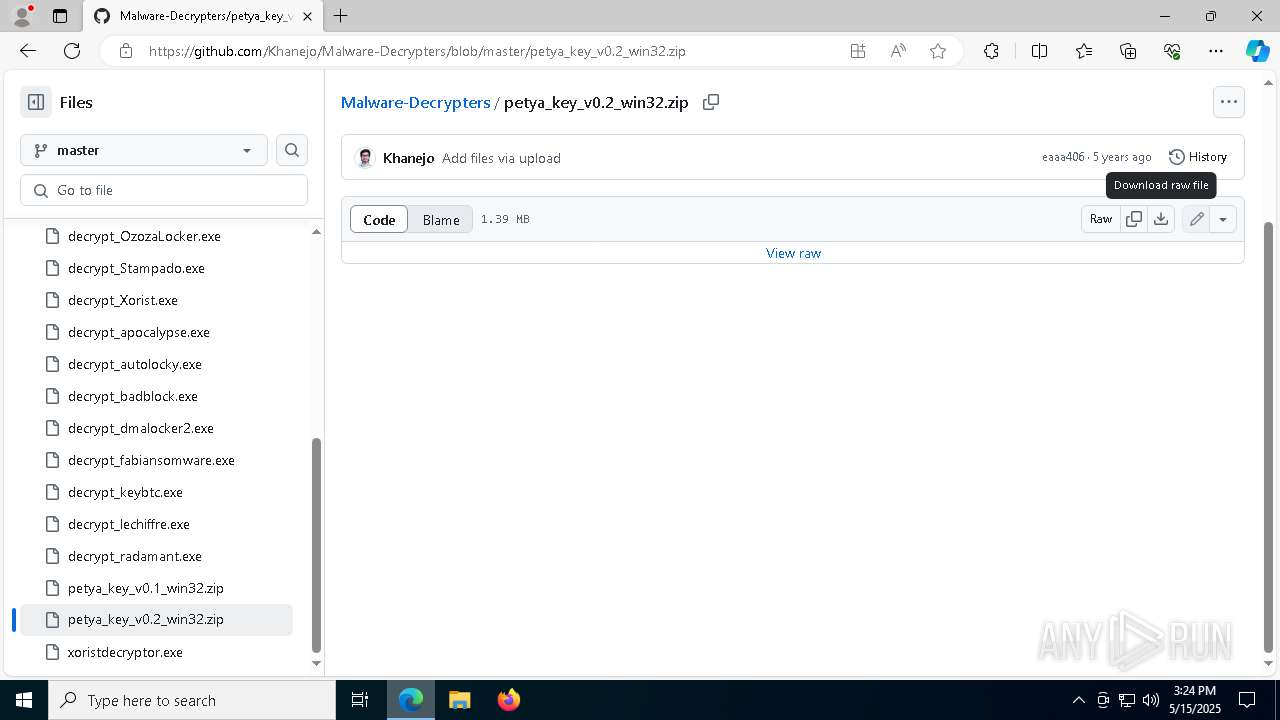
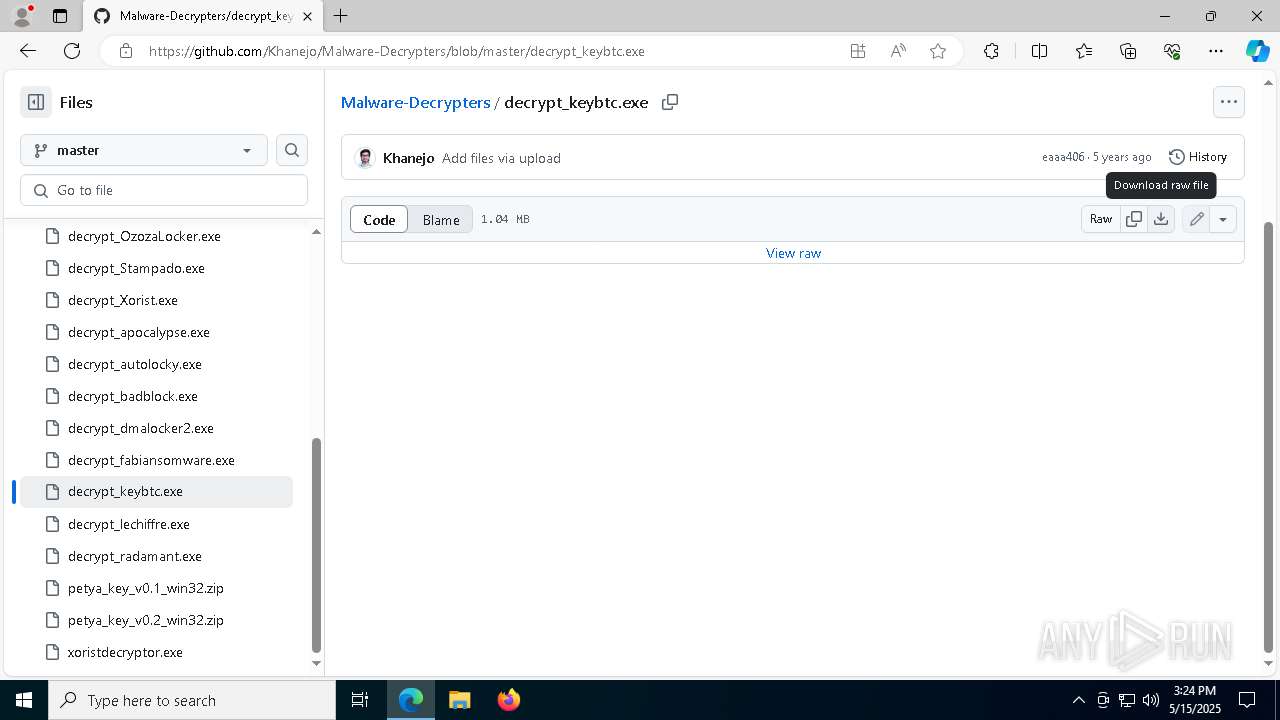
| URL: | https://github.com/Khanejo/Malware-Decrypters |
| Full analysis: | https://app.any.run/tasks/15957c54-f3b6-43dd-8bc3-997e2fb19c8a |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2025, 15:22:22 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 49B50F3CA1EB0C530B06CF6F41445A2A |
| SHA1: | 5B937C14F020800D4C9EDB136CE29B6A764CA36E |
| SHA256: | 1DDDB77BA845F07BDB7E5A840F1A7A51F164DCE2719ED330DD1D555221246F5E |
| SSDEEP: | 3:N8tEd7AyKZcEjAGUT:2uNxLpGc |
MALICIOUS
No malicious indicators.SUSPICIOUS
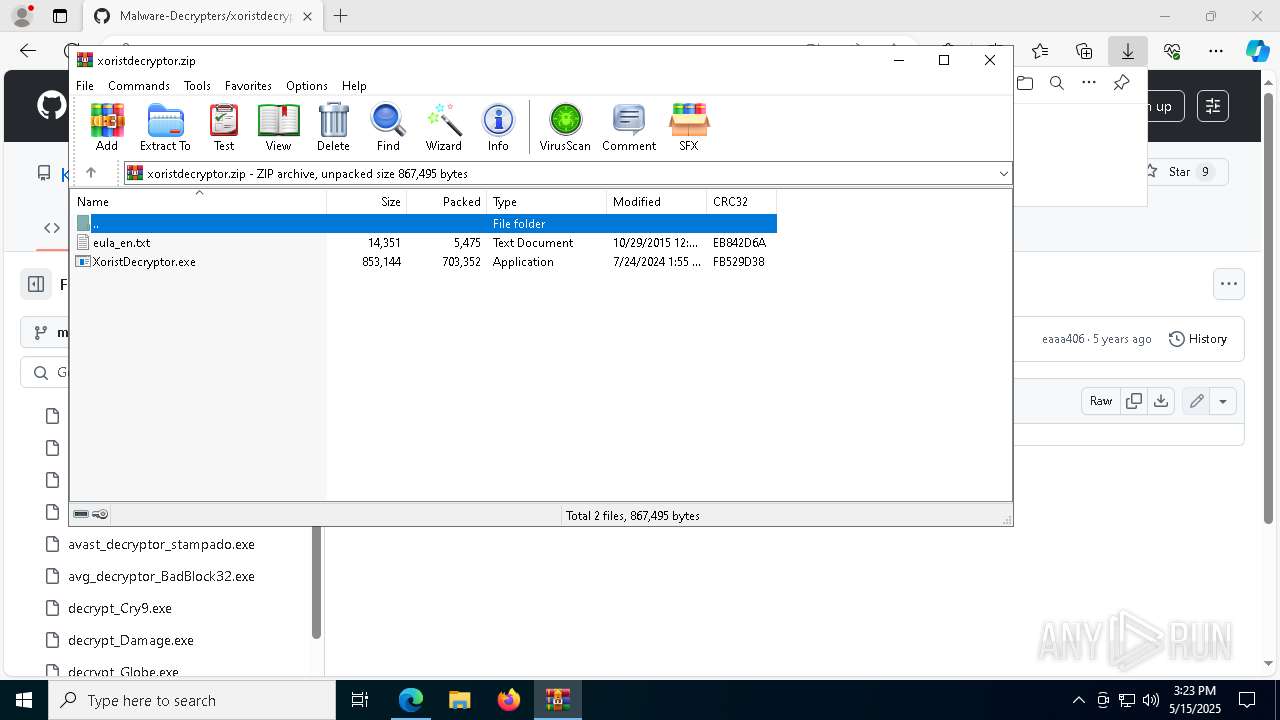
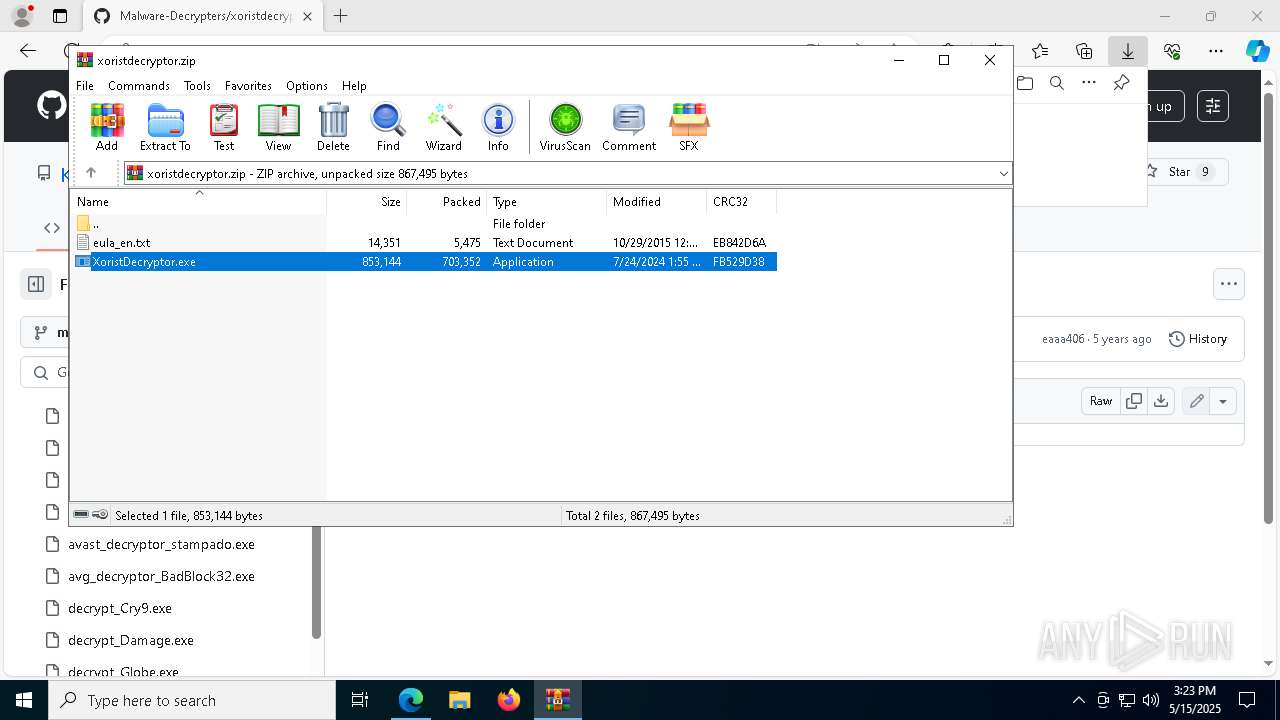
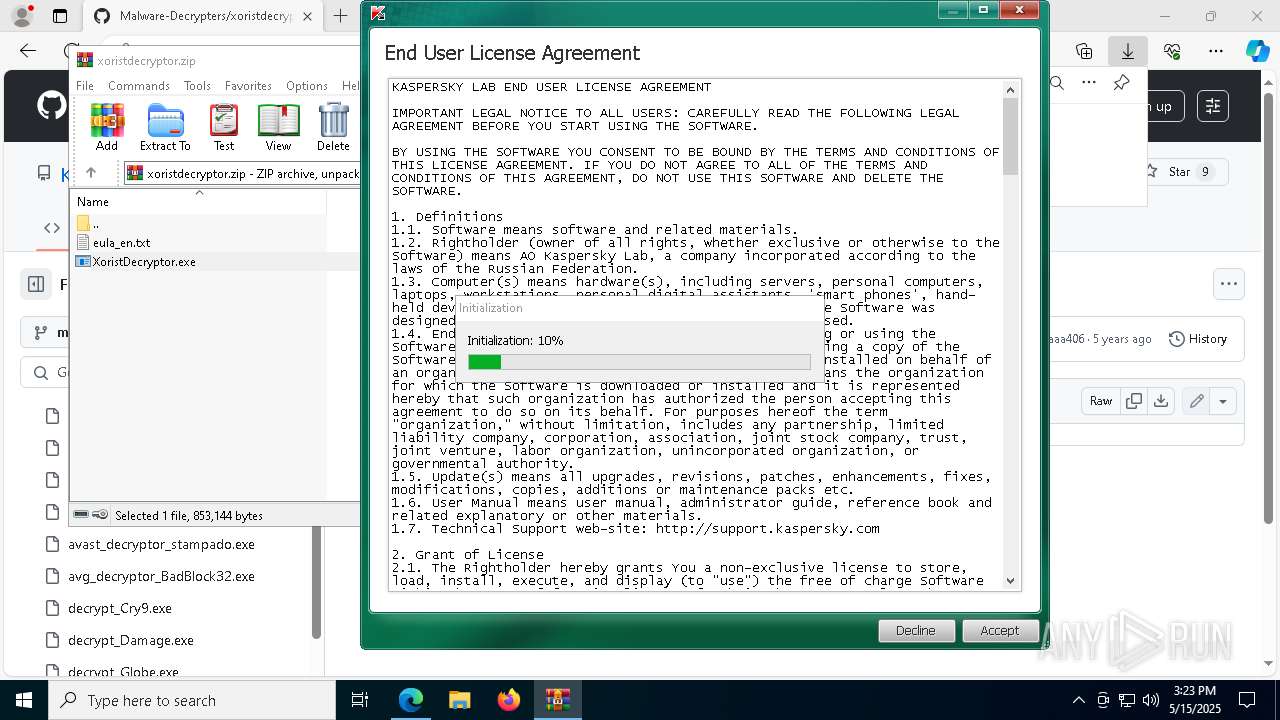
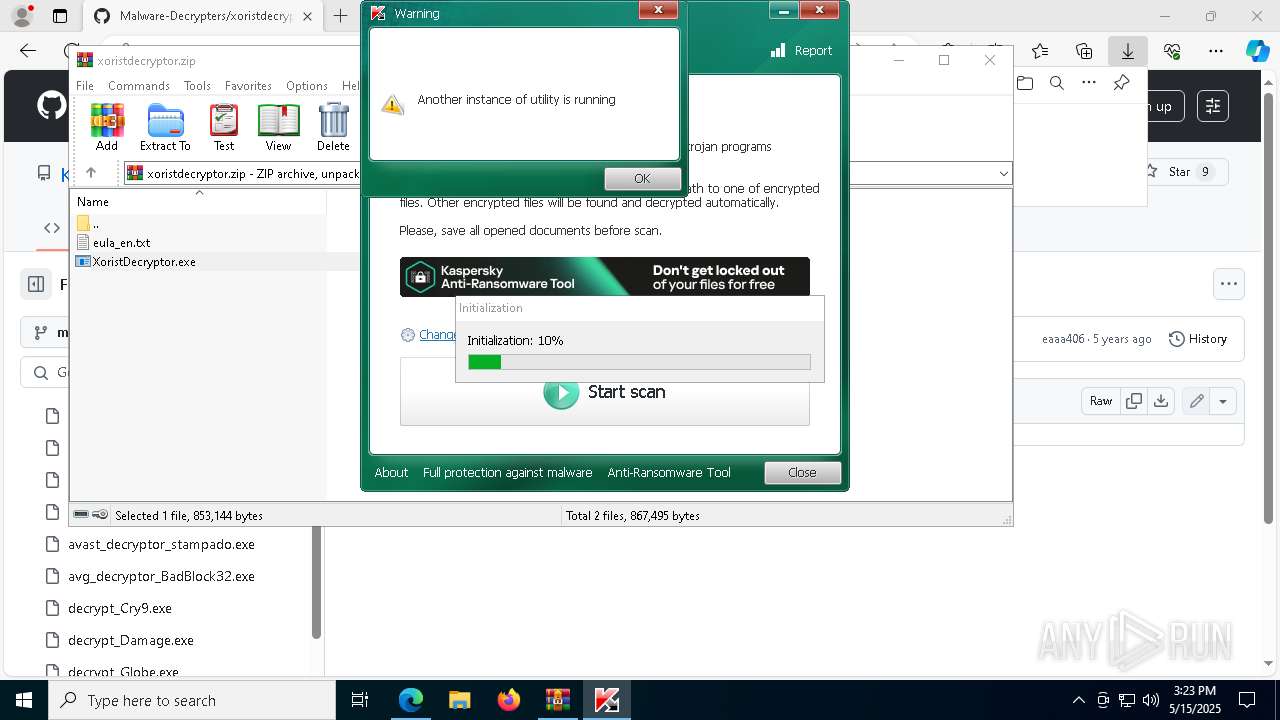
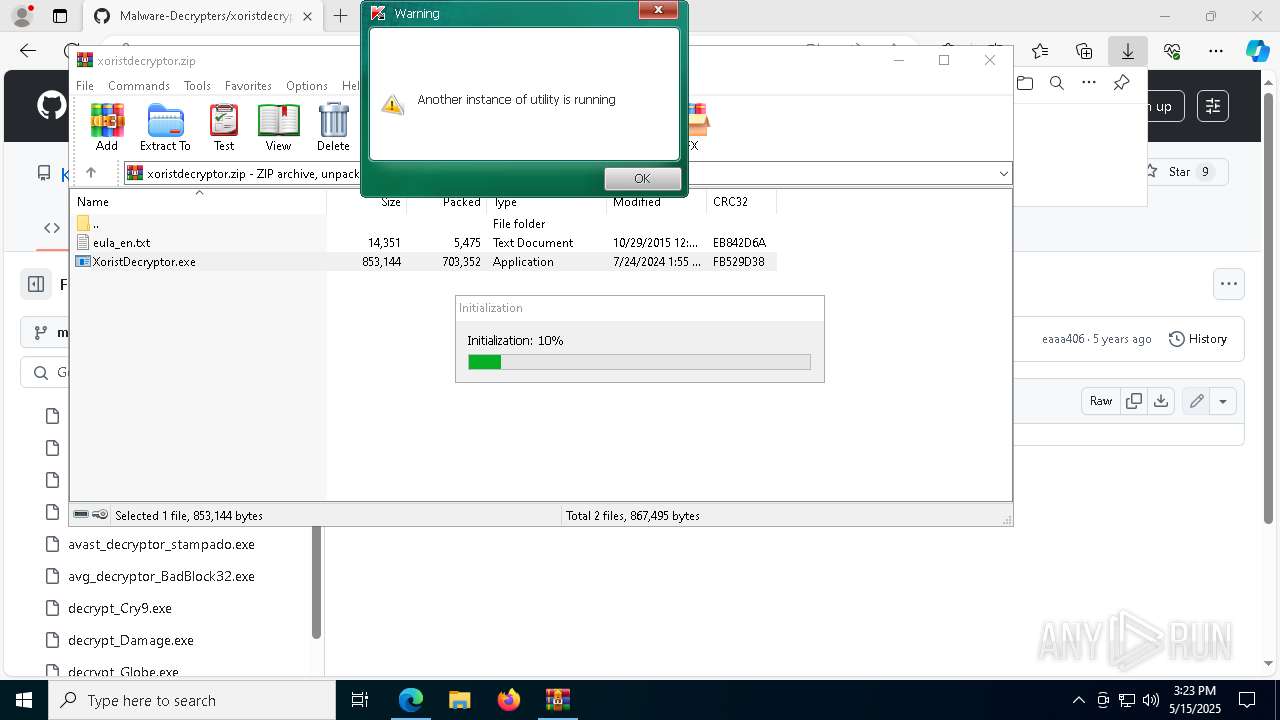
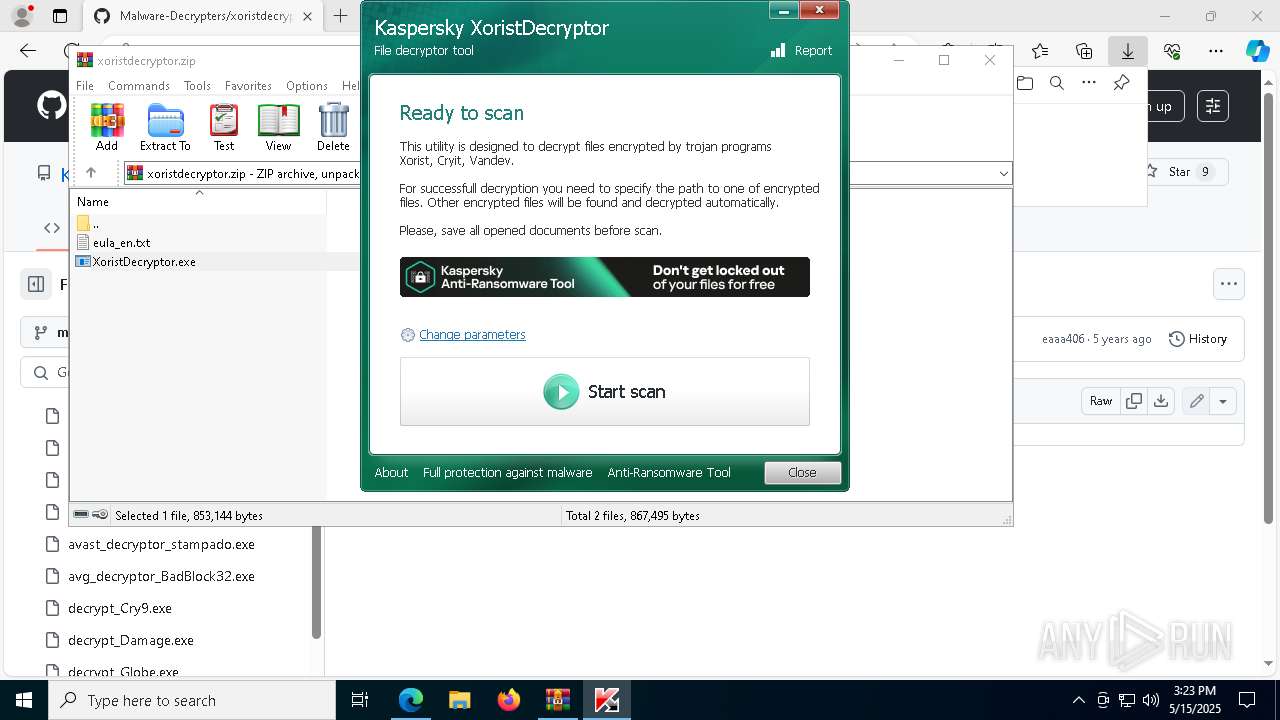
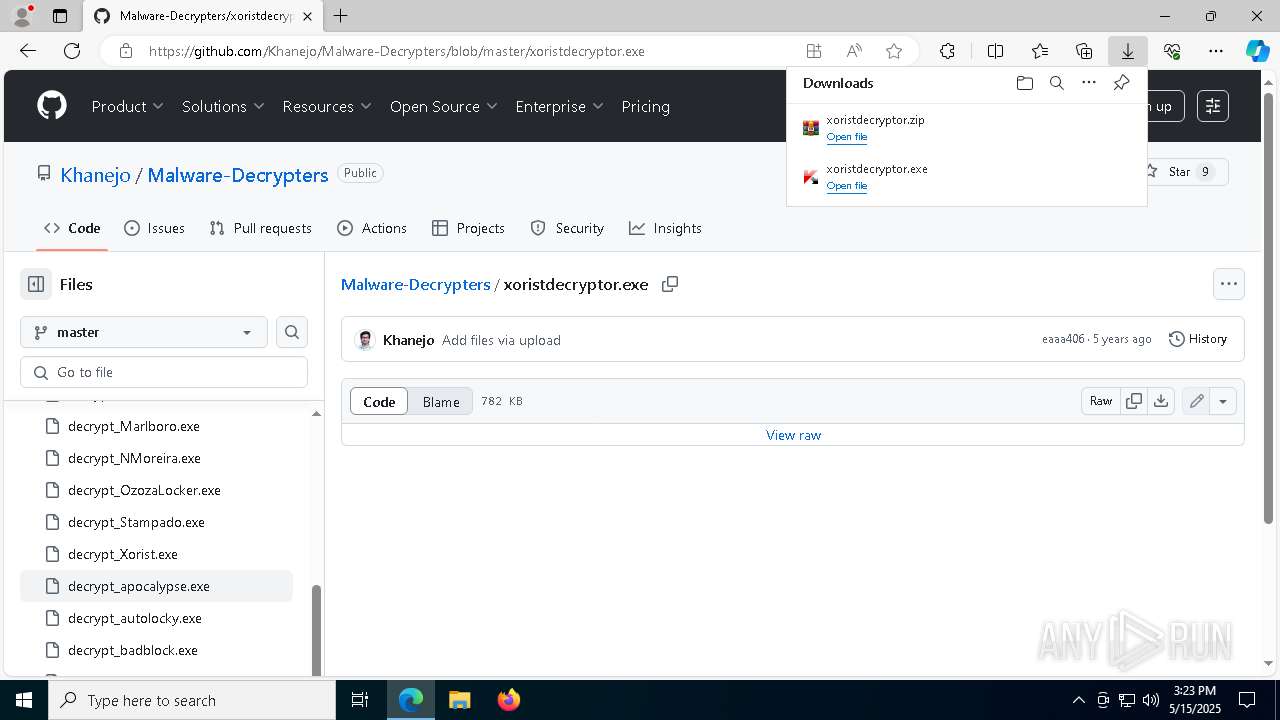
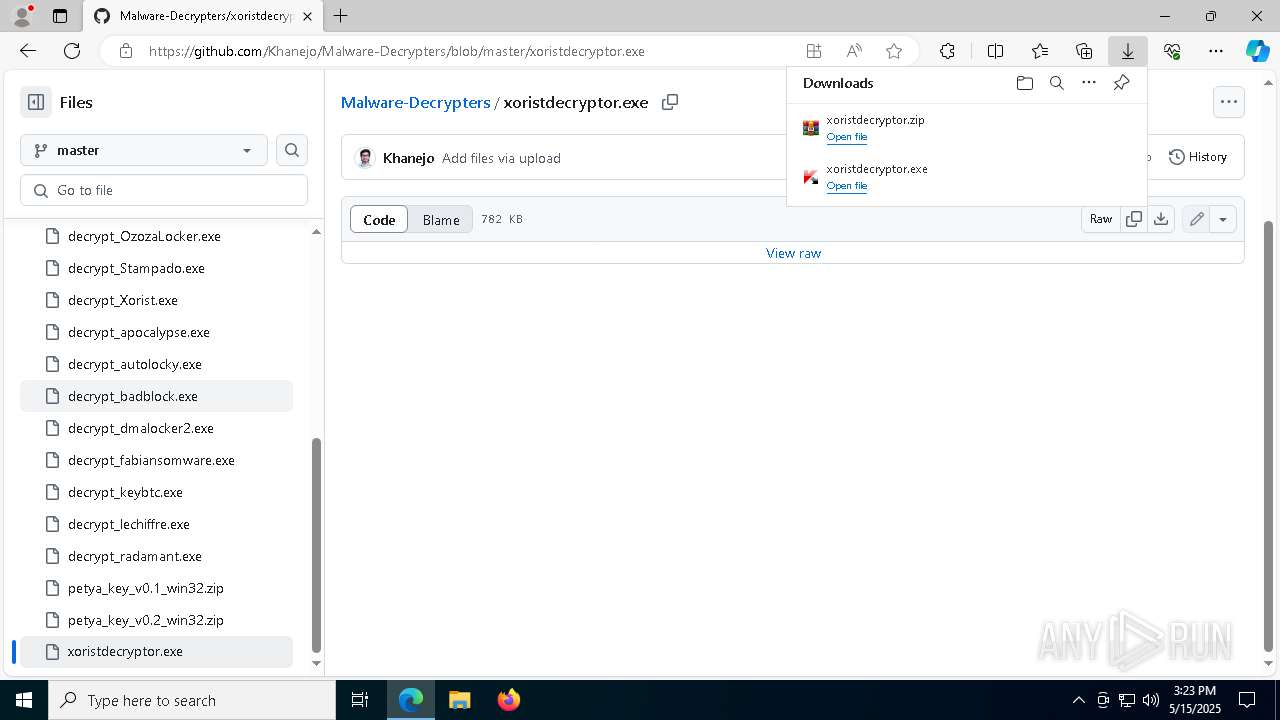
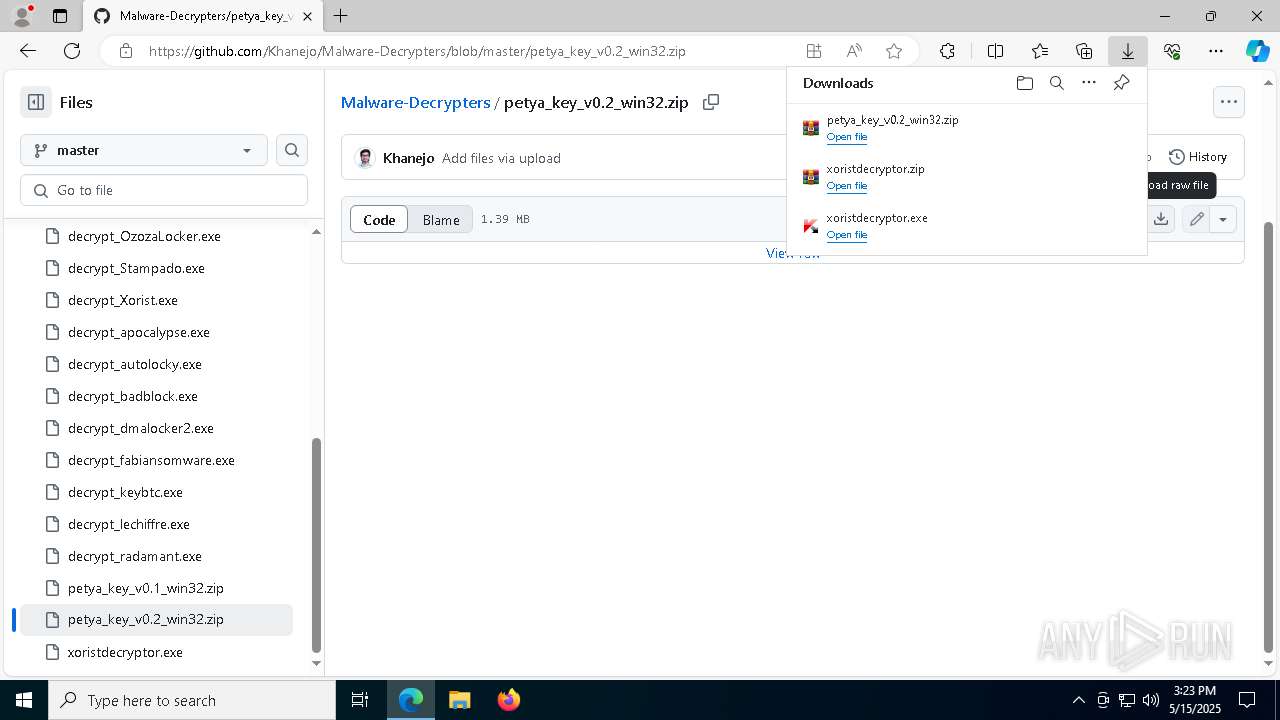
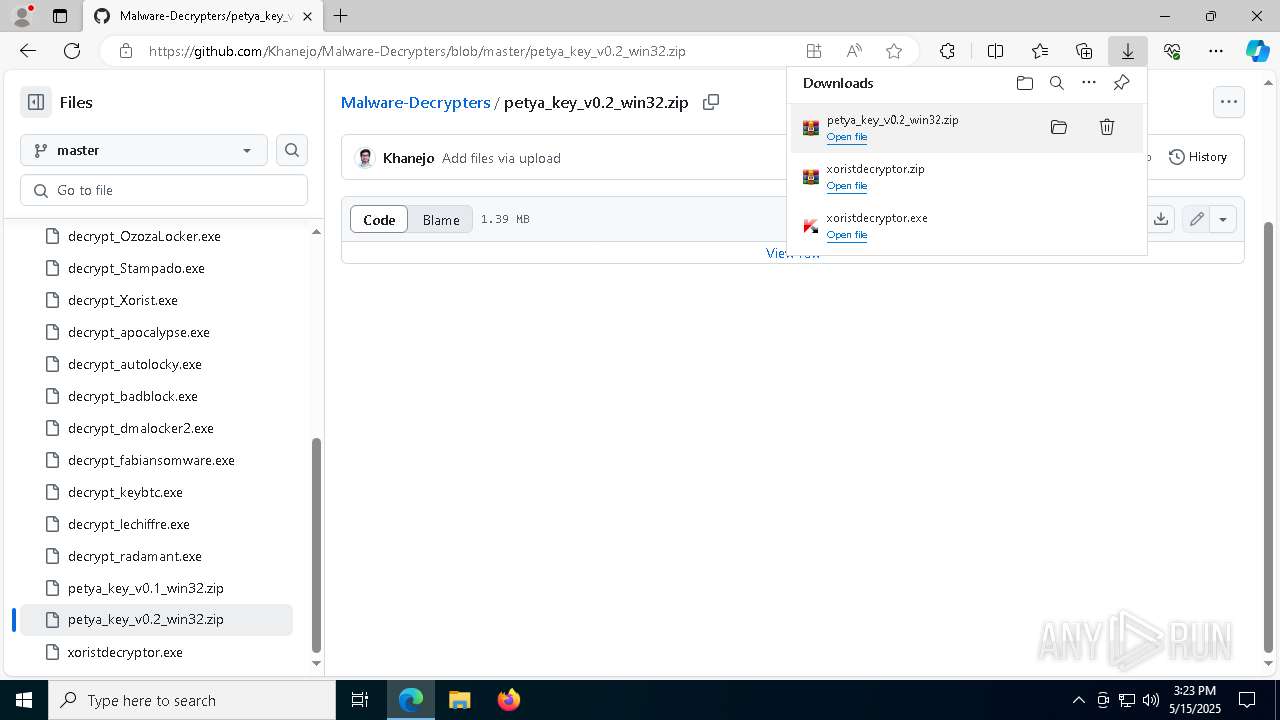
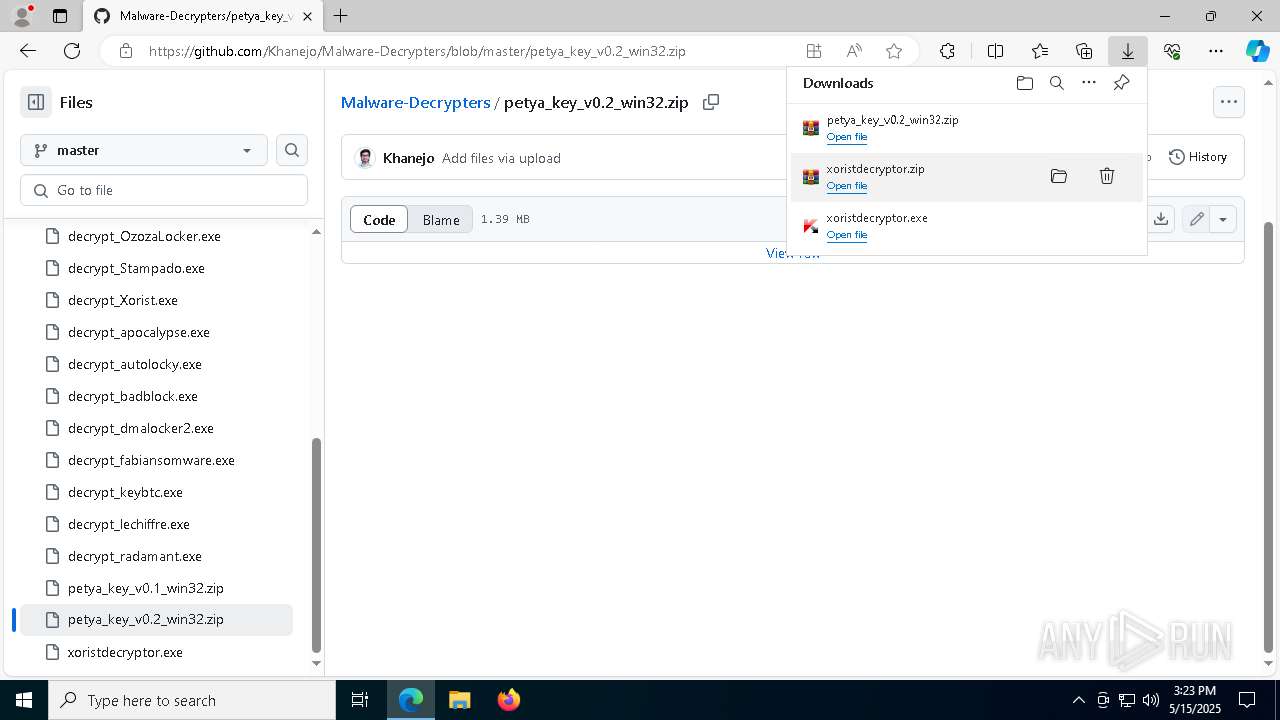
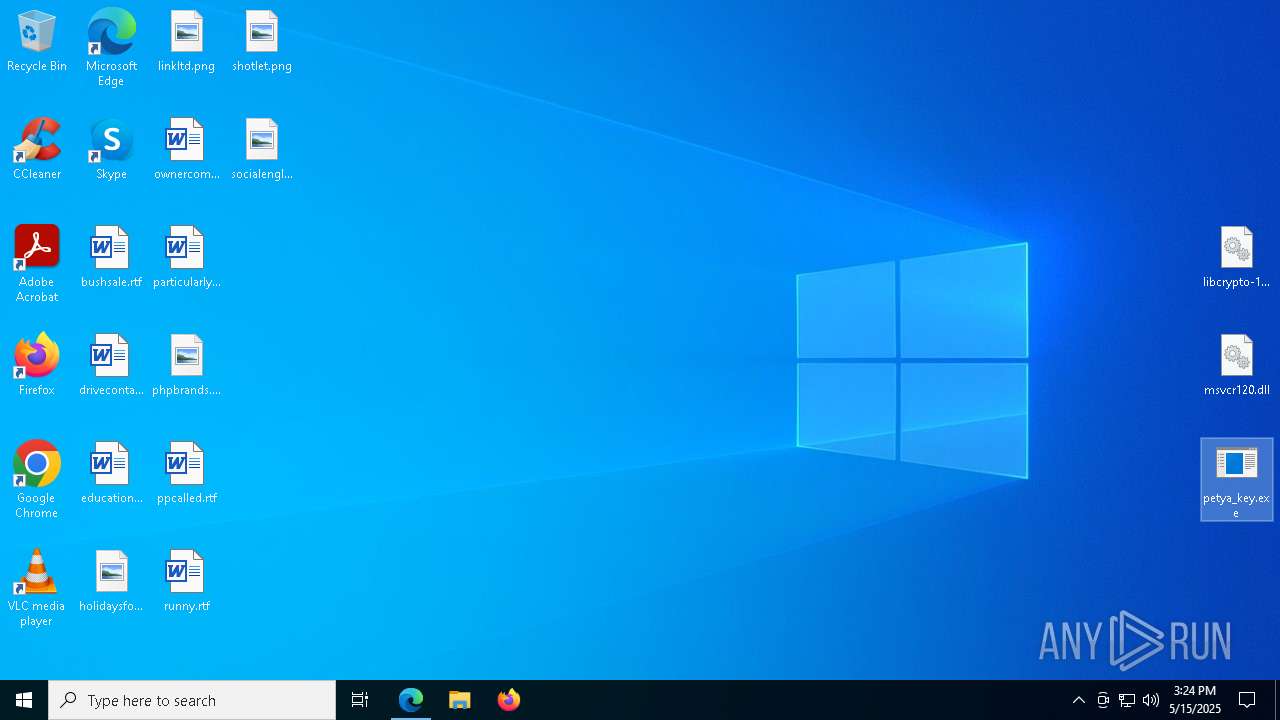
Executable content was dropped or overwritten
- xoristdecryptor.exe (PID: 8012)
- XoristDecryptor.exe (PID: 7036)
- XoristDecryptor.exe (PID: 8024)
- XoristDecryptor.exe (PID: 4112)
Reads security settings of Internet Explorer
- {309C5C25-1E6E-41BA-B05A-C4A5EA78D39B}.exe (PID: 7952)
- WinRAR.exe (PID: 6828)
- WinRAR.exe (PID: 4008)
There is functionality for taking screenshot (YARA)
- {4136618A-FE36-43A2-AF59-4EF37EEE4764}.exe (PID: 2772)
The process drops C-runtime libraries
- msedge.exe (PID: 3020)
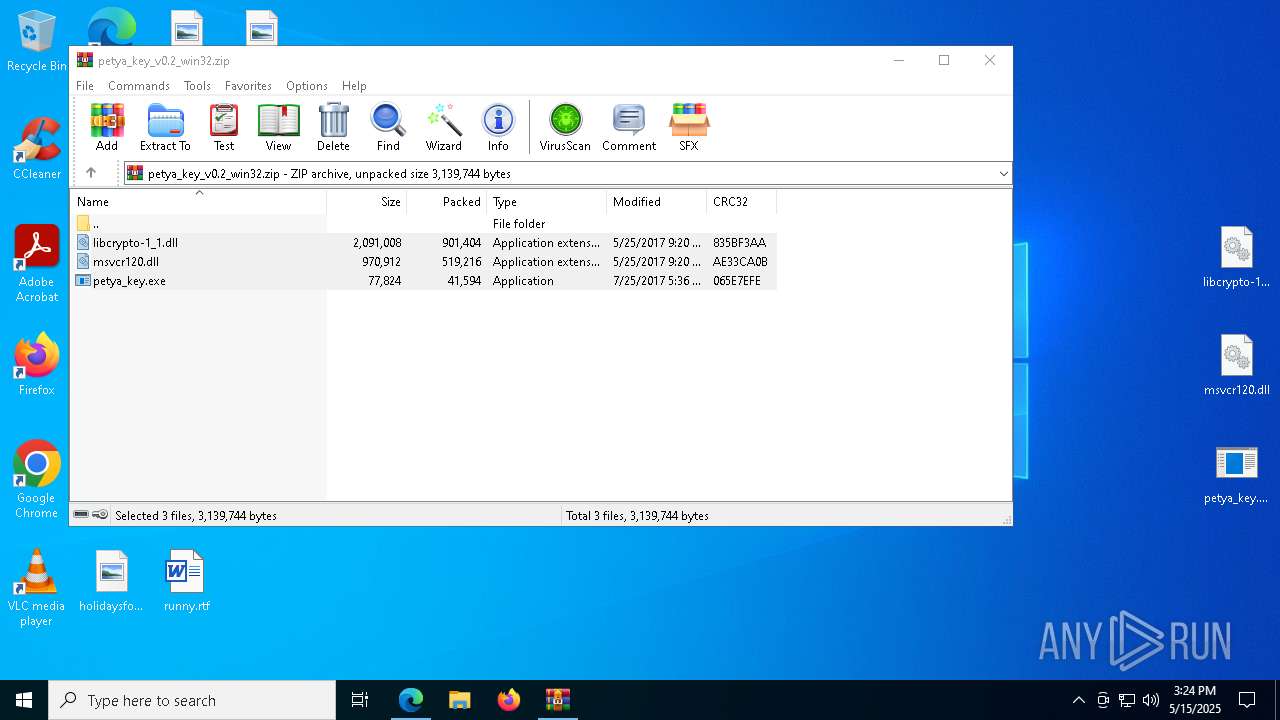
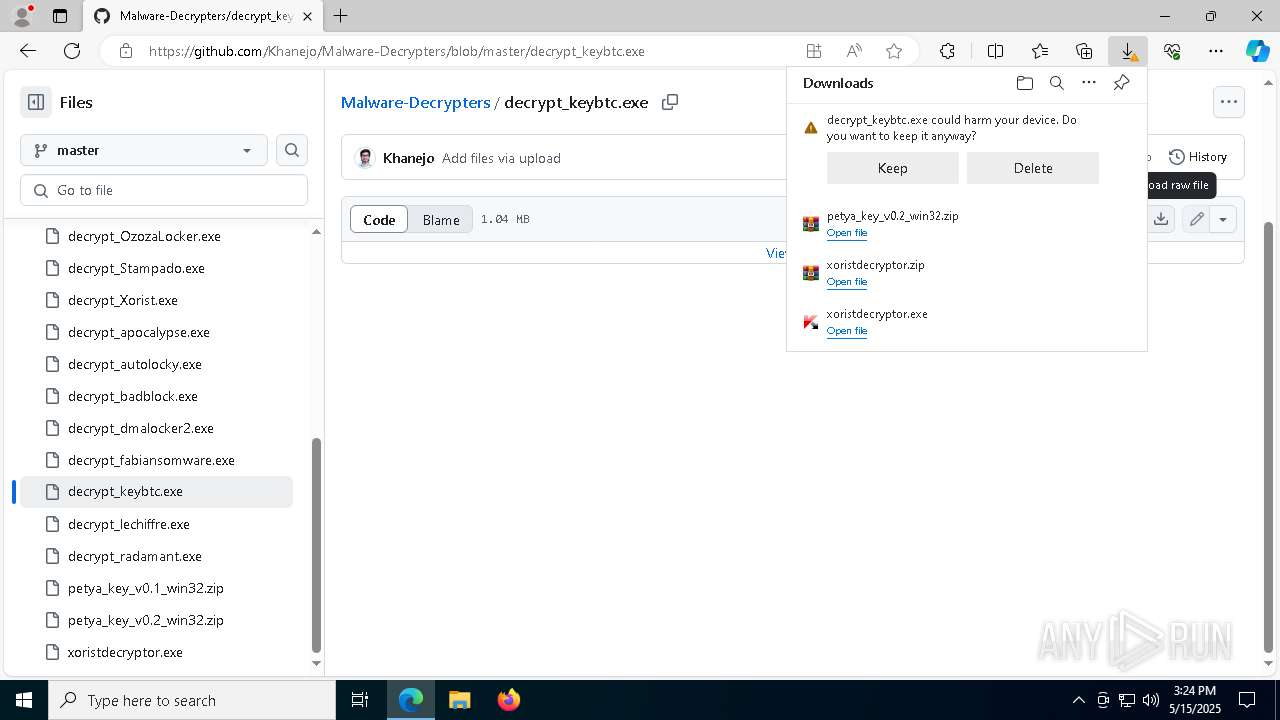
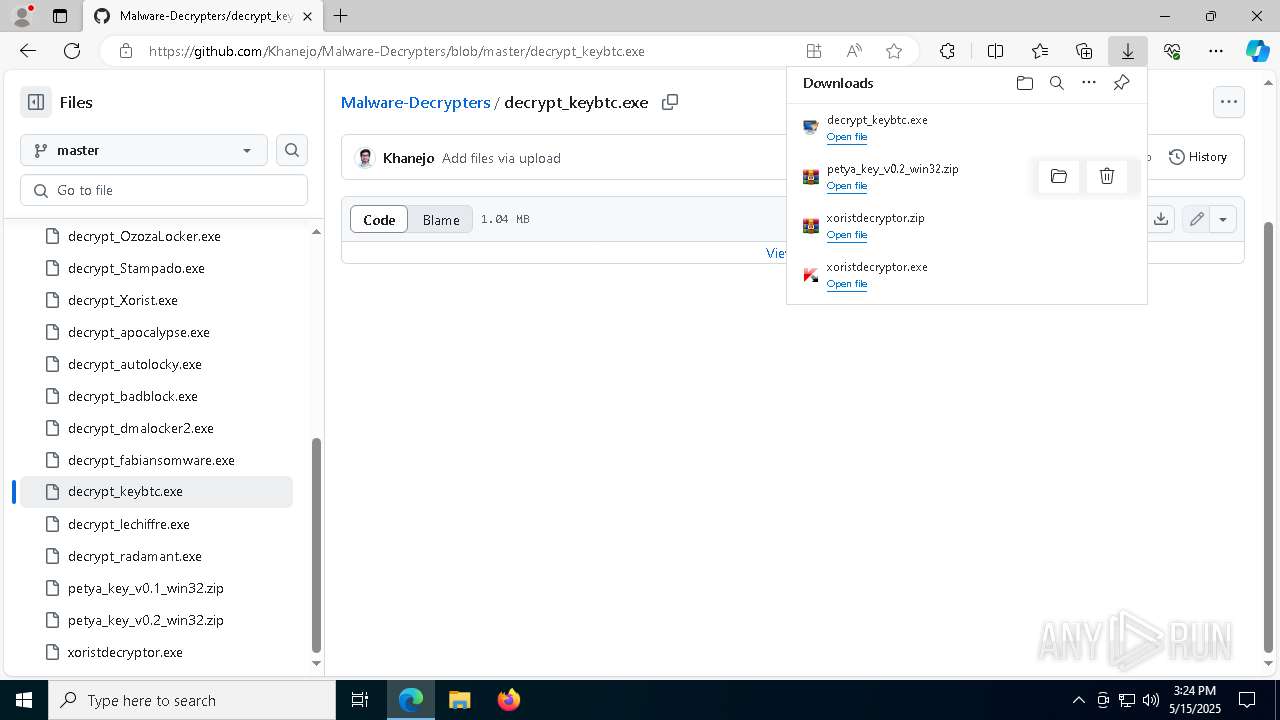
Process drops legitimate windows executable
- msedge.exe (PID: 3020)
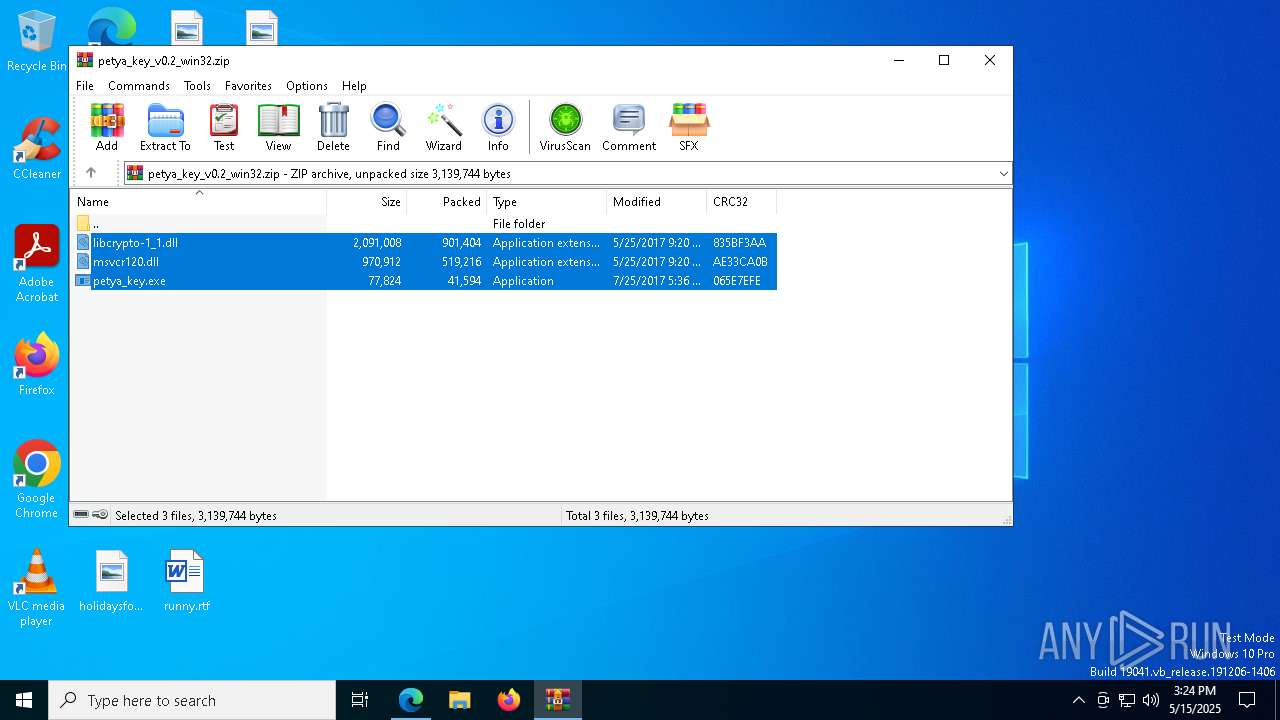
- WinRAR.exe (PID: 4008)
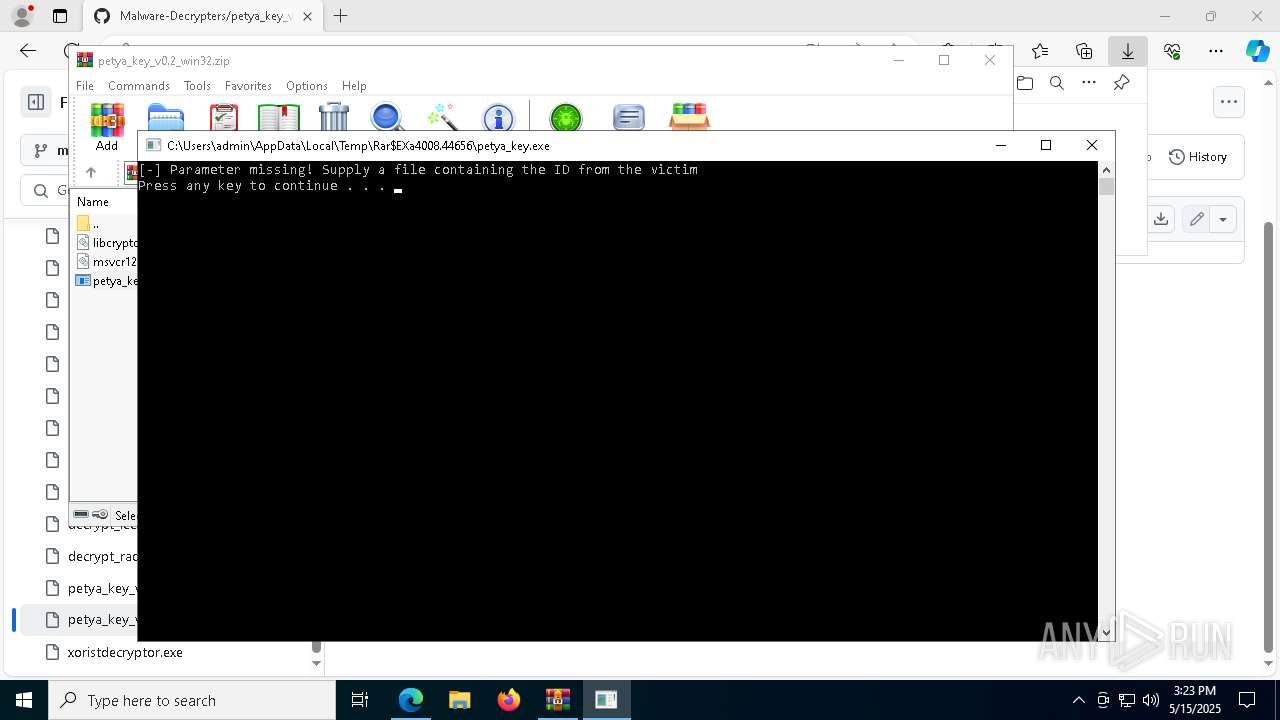
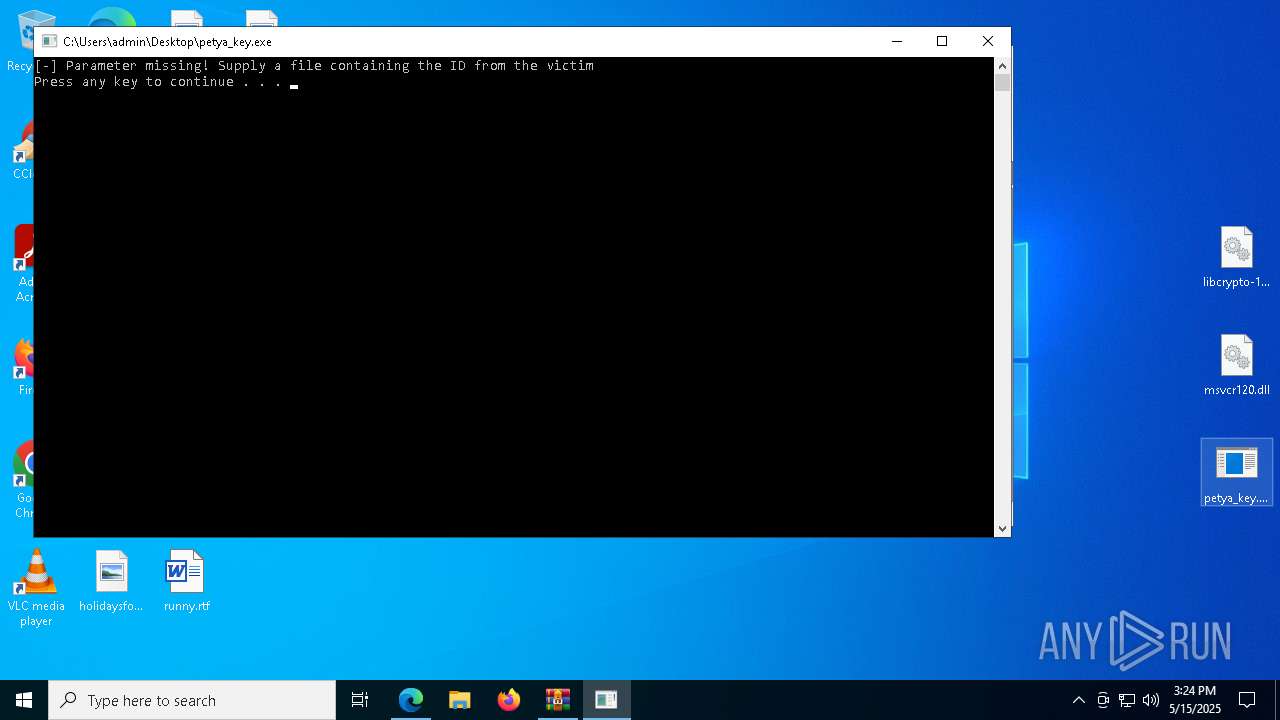
Starts CMD.EXE for commands execution
- petya_key.exe (PID: 7936)
- petya_key.exe (PID: 7328)
INFO
Reads Environment values
- identity_helper.exe (PID: 7792)
Reads the computer name
- identity_helper.exe (PID: 7792)
- {309C5C25-1E6E-41BA-B05A-C4A5EA78D39B}.exe (PID: 7952)
- {39FD0E05-E112-4143-8797-6ED6CC723A3A}.exe (PID: 5352)
- {E91569A3-AD3B-4F47-9C5F-7840FDF57F02}.exe (PID: 7992)
- {4136618A-FE36-43A2-AF59-4EF37EEE4764}.exe (PID: 2772)
Application launched itself
- msedge.exe (PID: 3020)
Checks supported languages
- identity_helper.exe (PID: 7792)
- {309C5C25-1E6E-41BA-B05A-C4A5EA78D39B}.exe (PID: 7952)
- xoristdecryptor.exe (PID: 8012)
- {39FD0E05-E112-4143-8797-6ED6CC723A3A}.exe (PID: 5352)
- XoristDecryptor.exe (PID: 7036)
- XoristDecryptor.exe (PID: 8024)
- {E91569A3-AD3B-4F47-9C5F-7840FDF57F02}.exe (PID: 7992)
- XoristDecryptor.exe (PID: 4112)
- {4136618A-FE36-43A2-AF59-4EF37EEE4764}.exe (PID: 2772)
- petya_key.exe (PID: 7936)
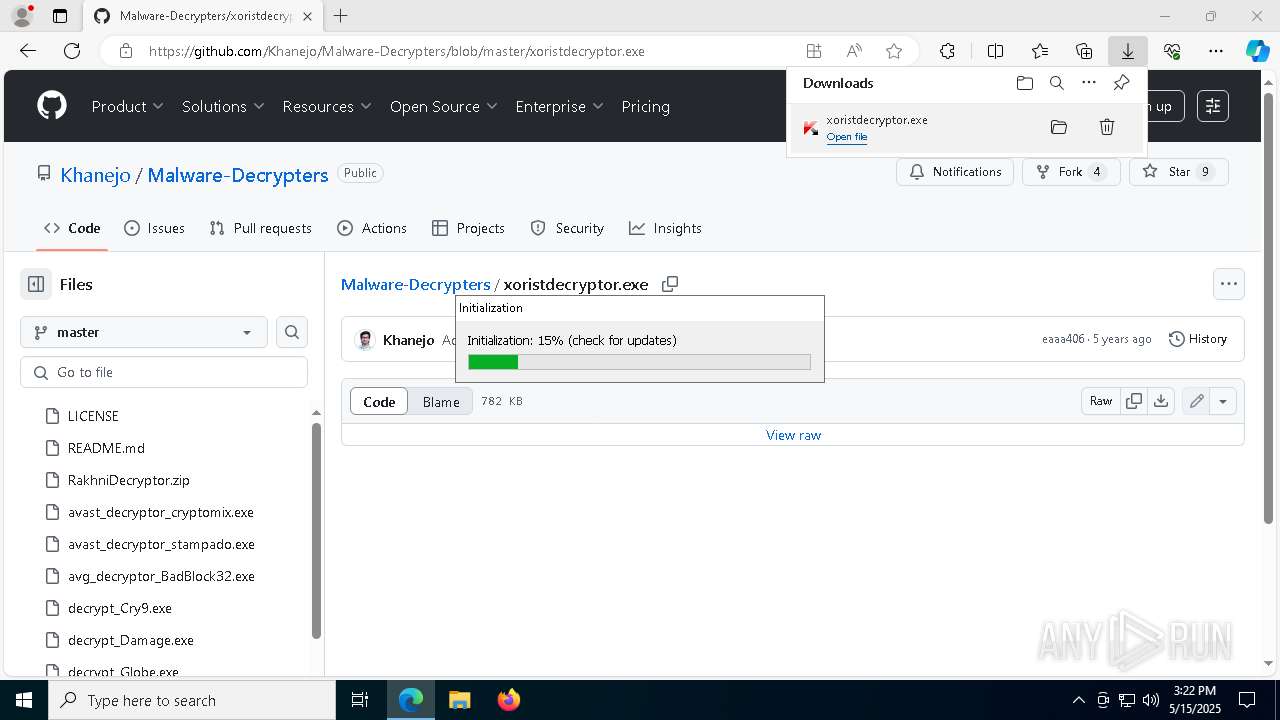
Create files in a temporary directory
- xoristdecryptor.exe (PID: 8012)
- XoristDecryptor.exe (PID: 7036)
- XoristDecryptor.exe (PID: 4112)
- XoristDecryptor.exe (PID: 8024)
Executable content was dropped or overwritten
- msedge.exe (PID: 2236)
- WinRAR.exe (PID: 6828)
- msedge.exe (PID: 3020)
- WinRAR.exe (PID: 4008)
- msedge.exe (PID: 4012)
Reads the software policy settings
- {309C5C25-1E6E-41BA-B05A-C4A5EA78D39B}.exe (PID: 7952)
- {39FD0E05-E112-4143-8797-6ED6CC723A3A}.exe (PID: 5352)
- {4136618A-FE36-43A2-AF59-4EF37EEE4764}.exe (PID: 2772)
- slui.exe (PID: 7696)
Reads Microsoft Office registry keys
- msedge.exe (PID: 3020)
The sample compiled with english language support
- XoristDecryptor.exe (PID: 7036)
- XoristDecryptor.exe (PID: 8024)
- WinRAR.exe (PID: 6828)
- XoristDecryptor.exe (PID: 4112)
- msedge.exe (PID: 3020)
- WinRAR.exe (PID: 4008)
- msedge.exe (PID: 2236)
- msedge.exe (PID: 4012)
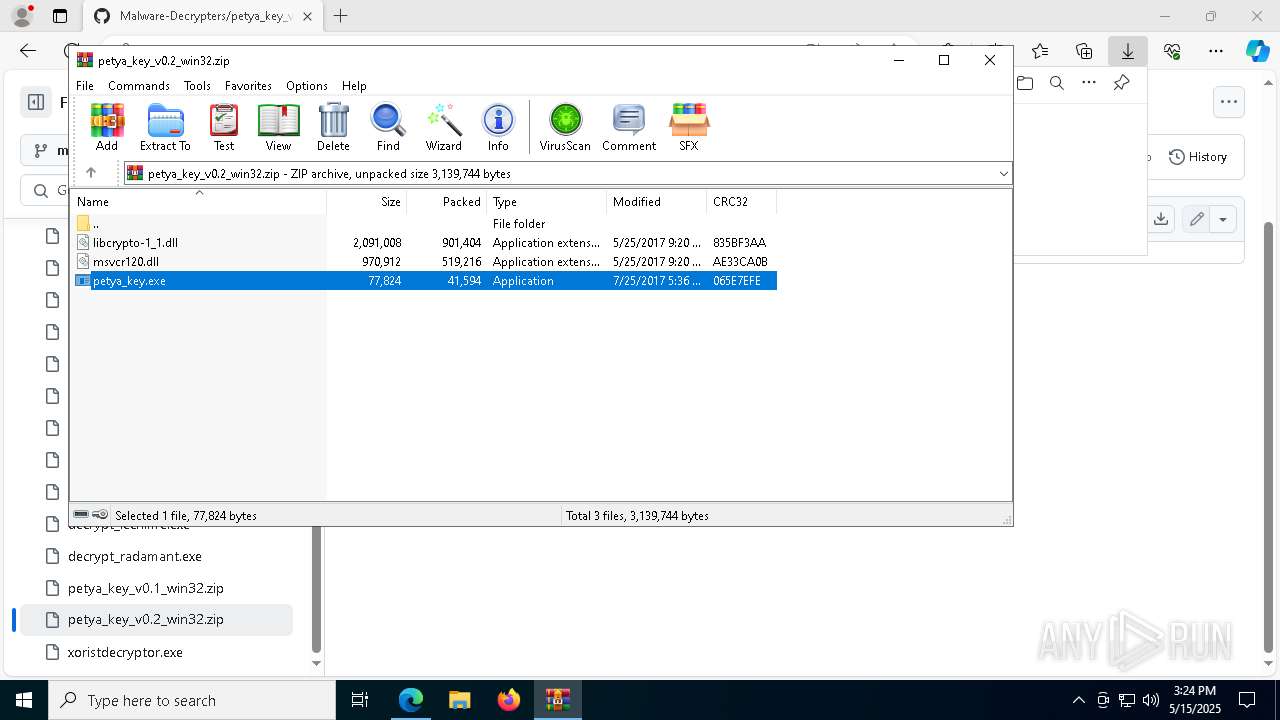
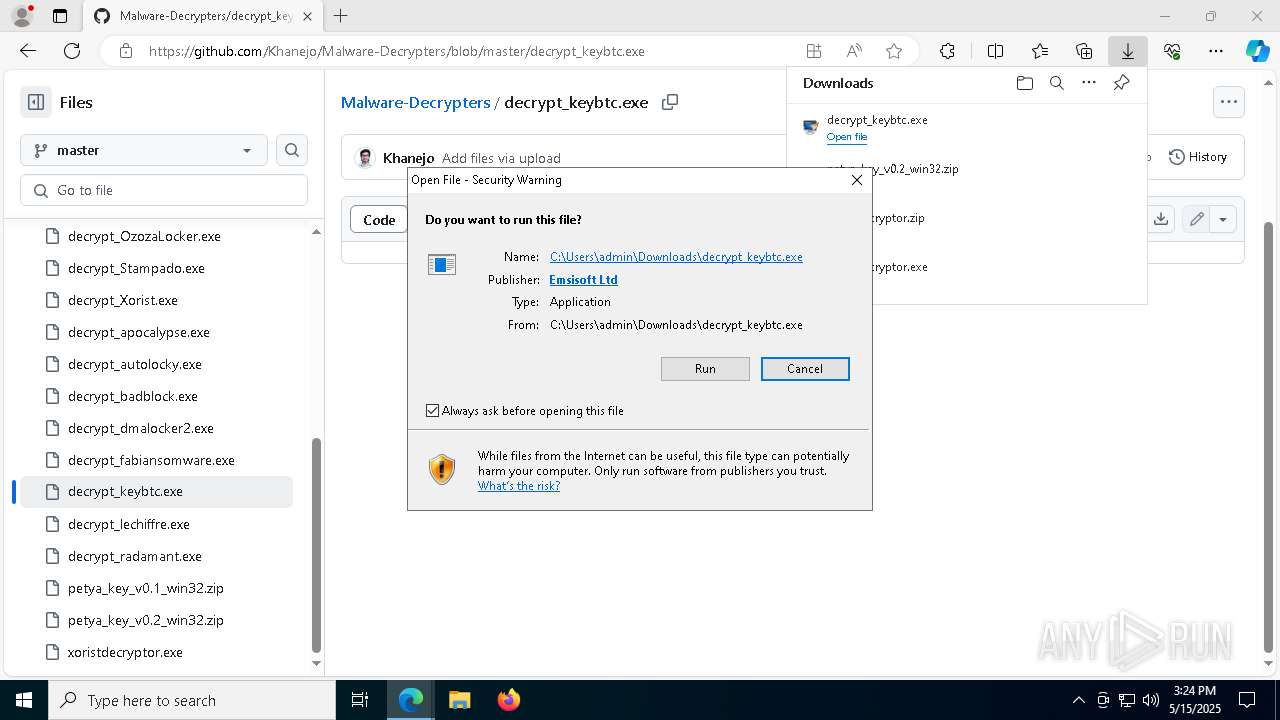
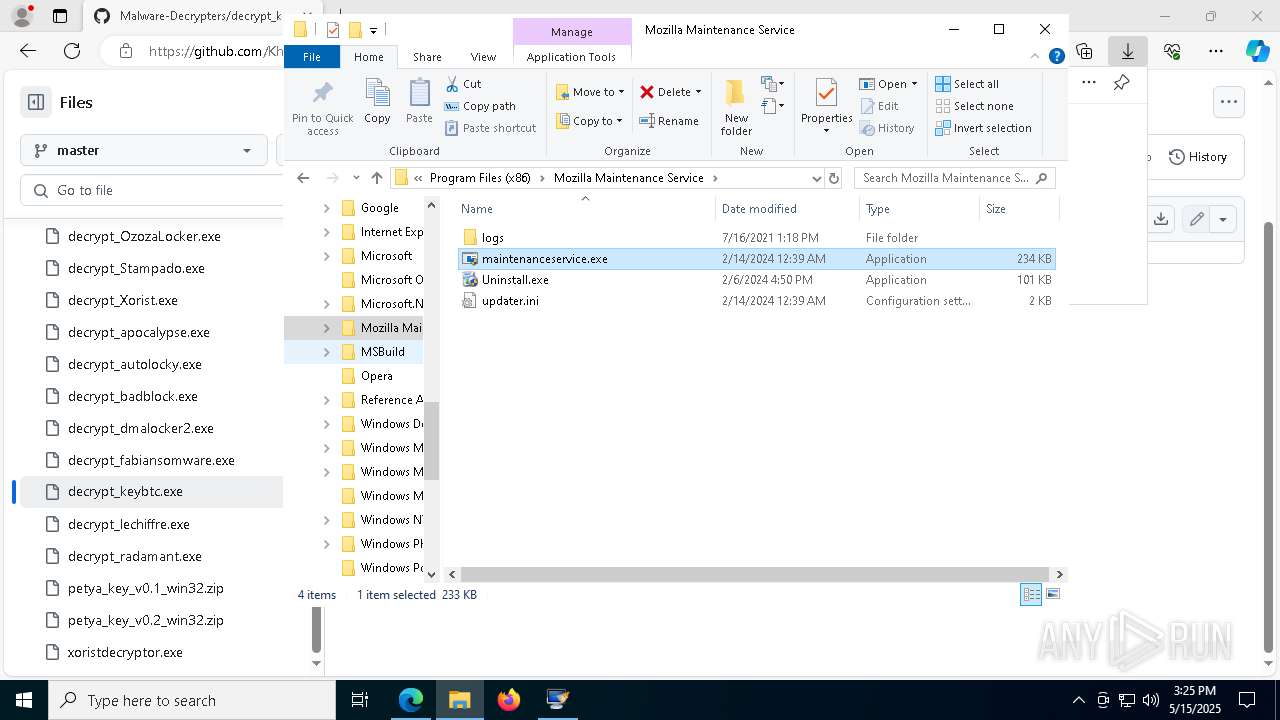
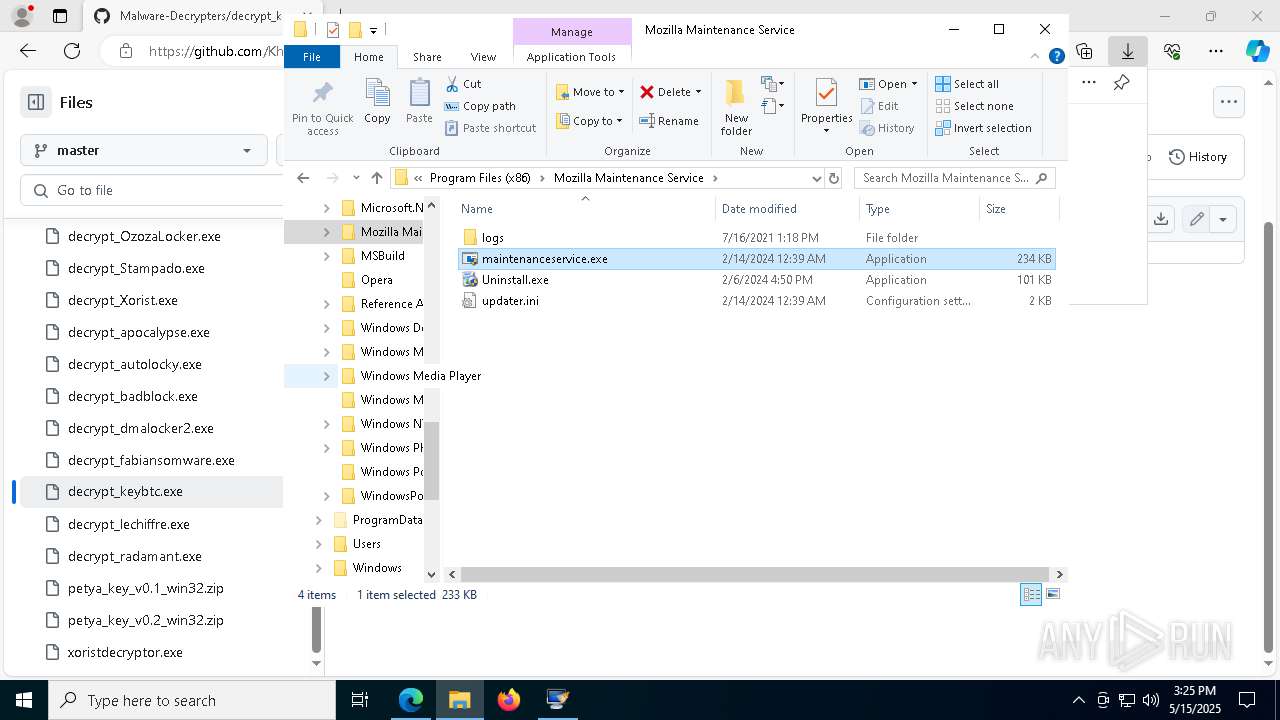
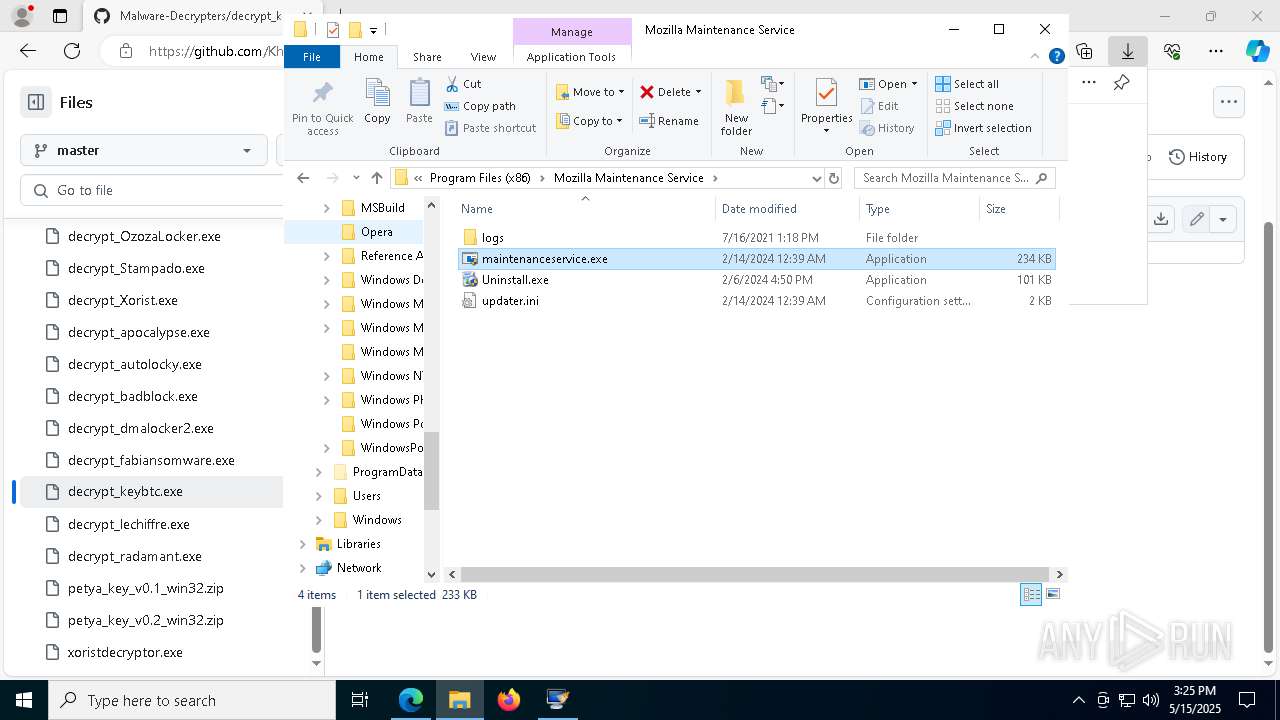
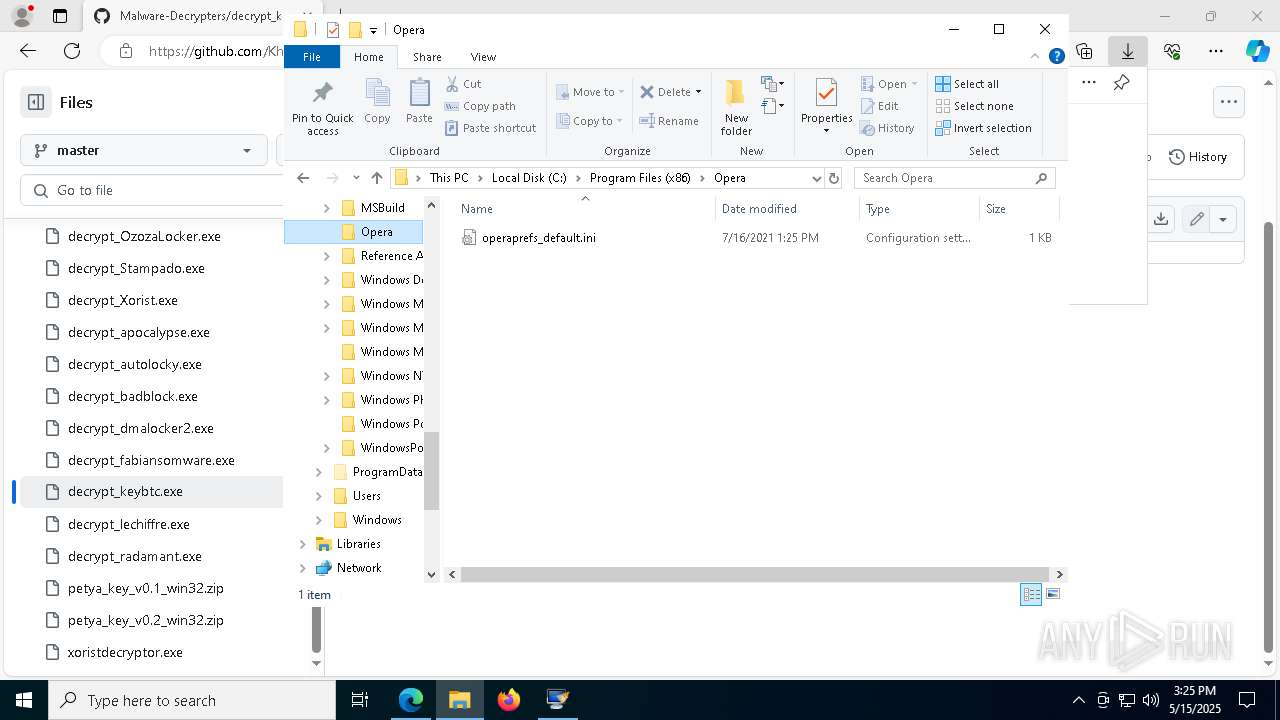
Manual execution by a user
- petya_key.exe (PID: 7328)
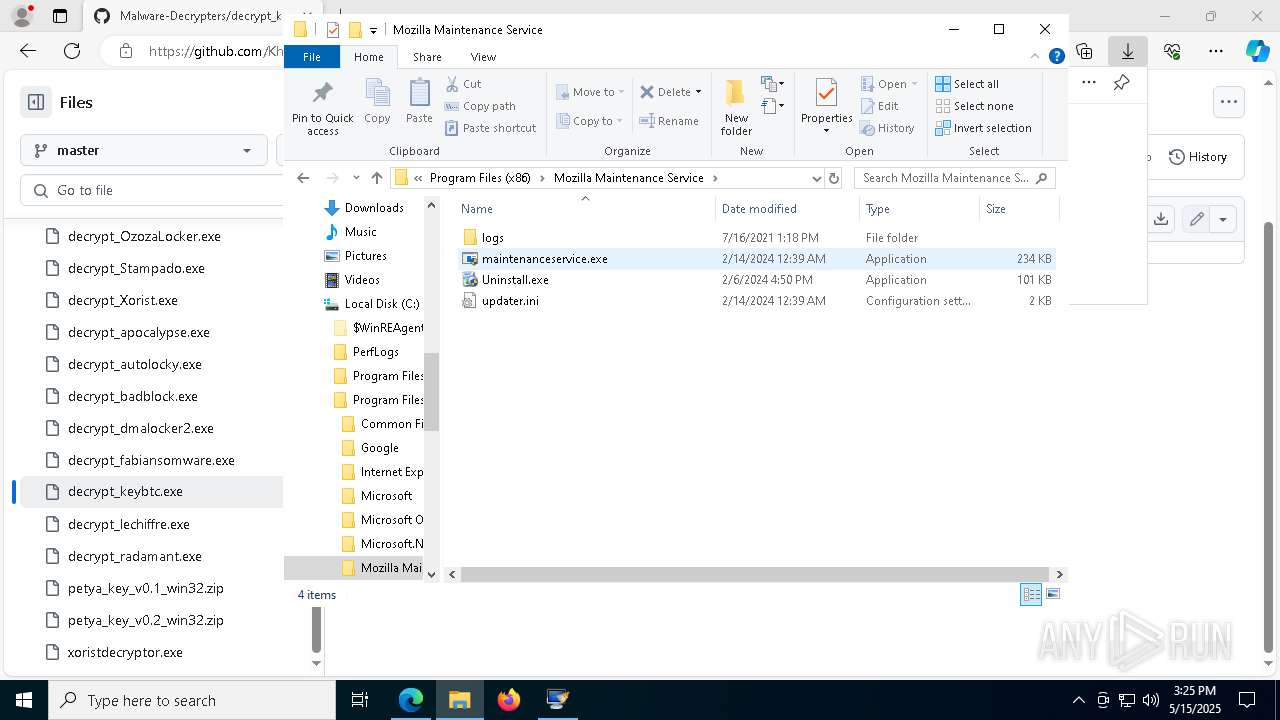
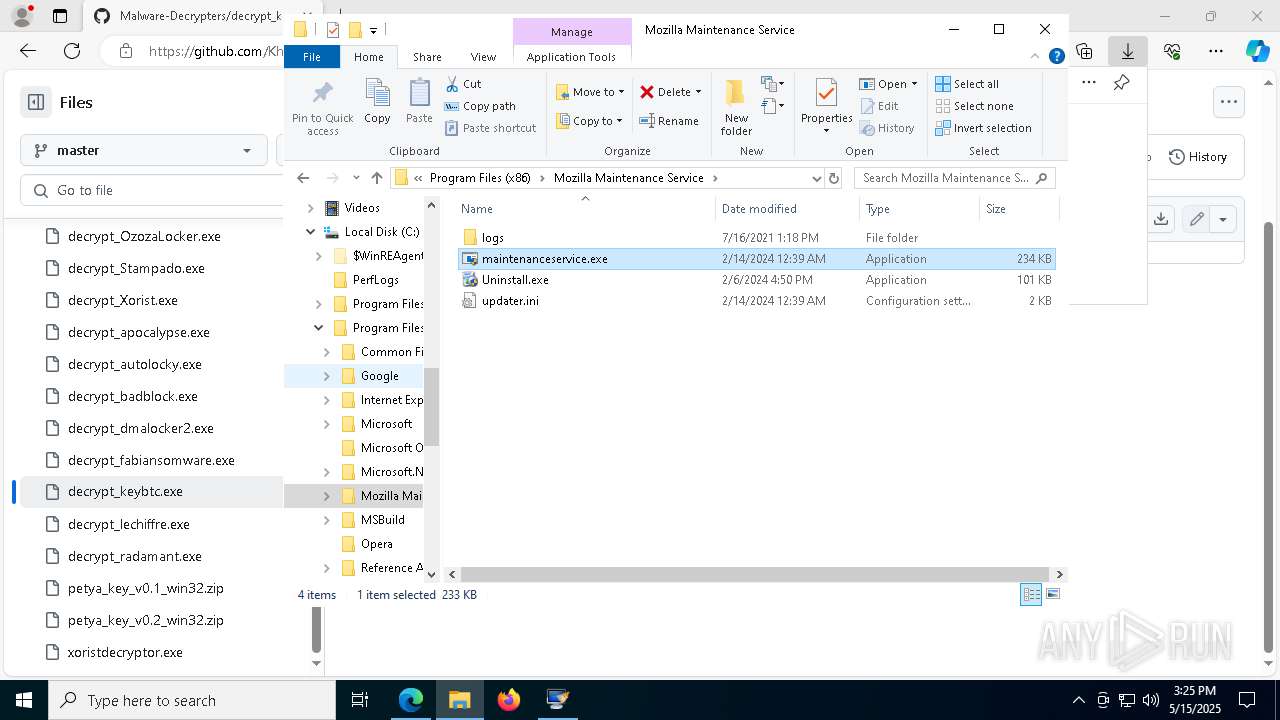
- maintenanceservice.exe (PID: 3968)
- maintenanceservice.exe (PID: 7944)
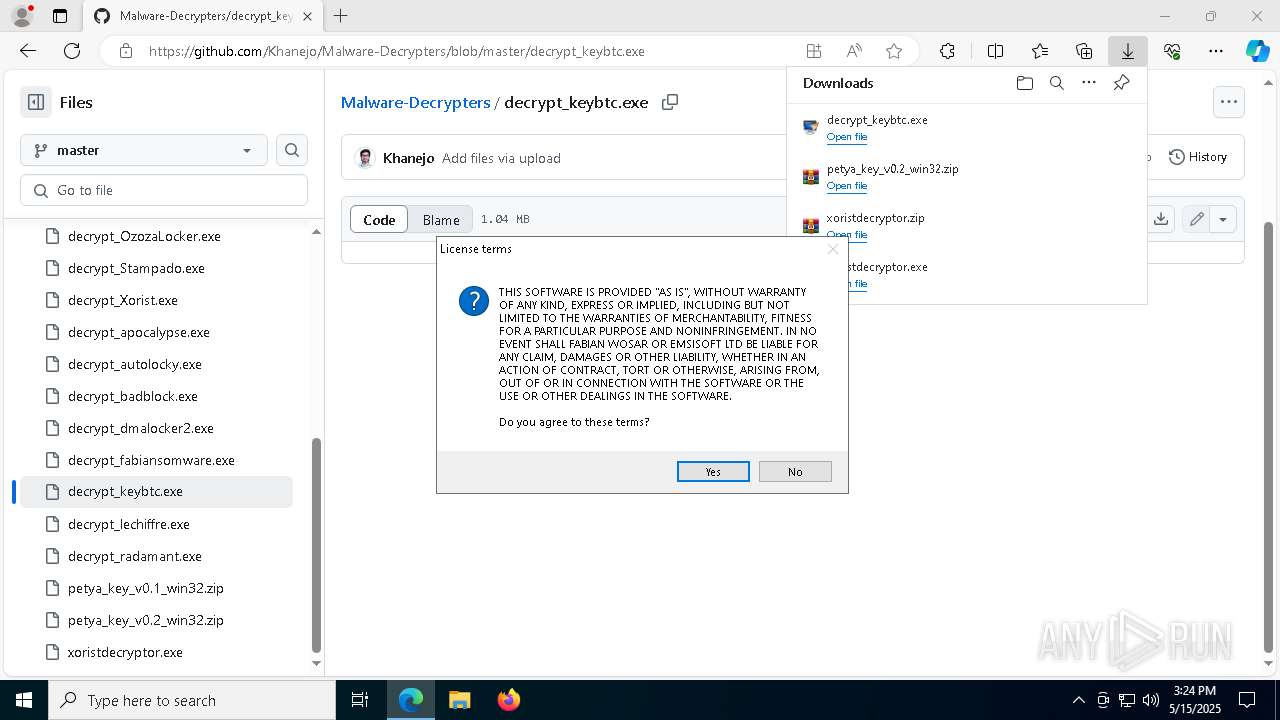
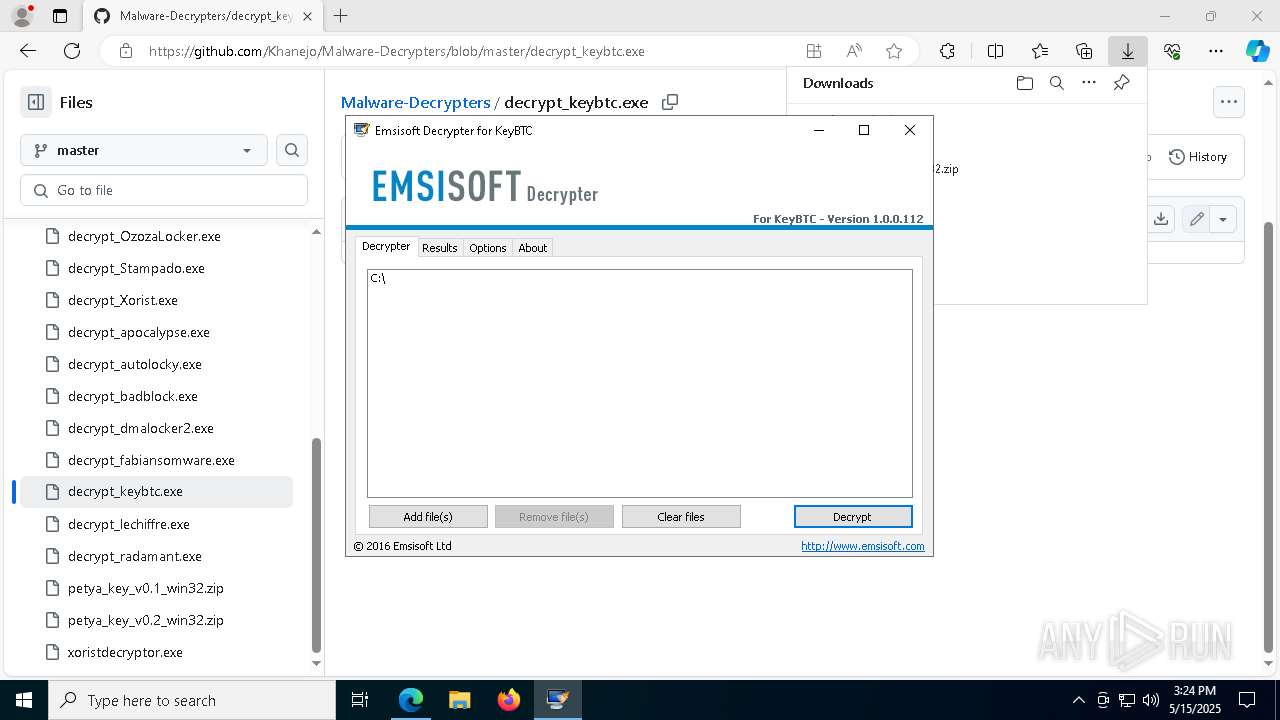
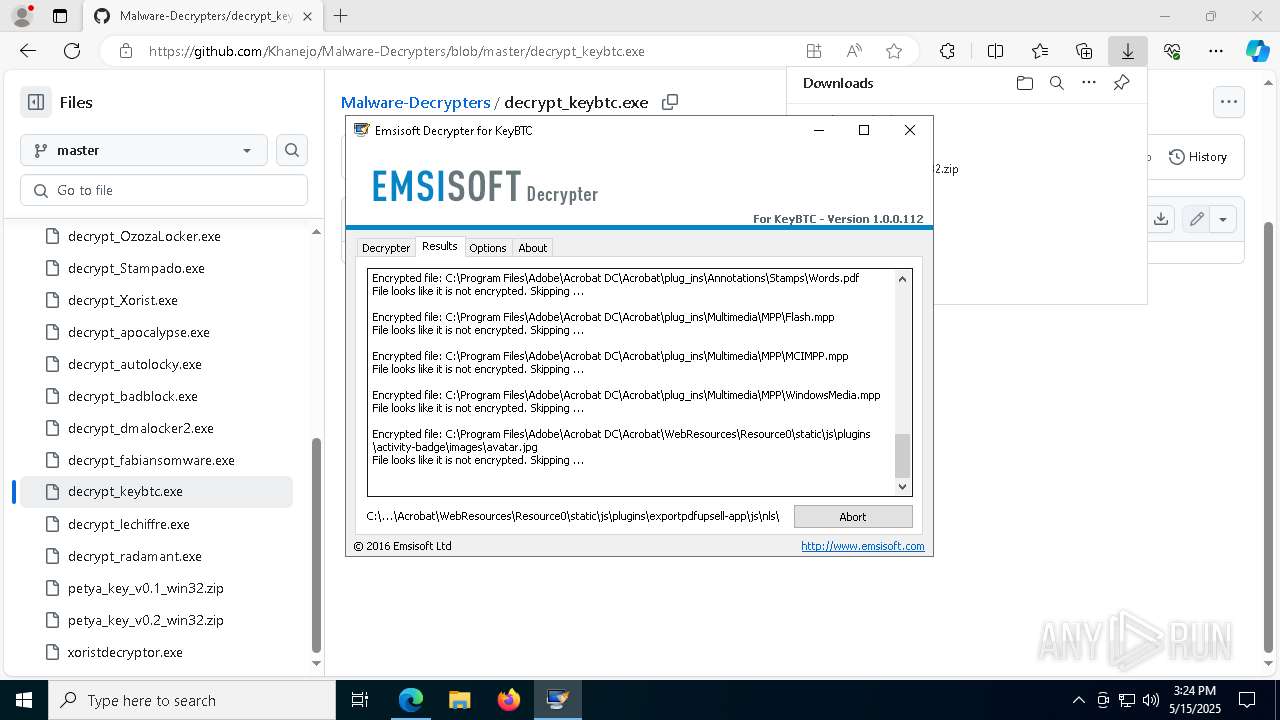
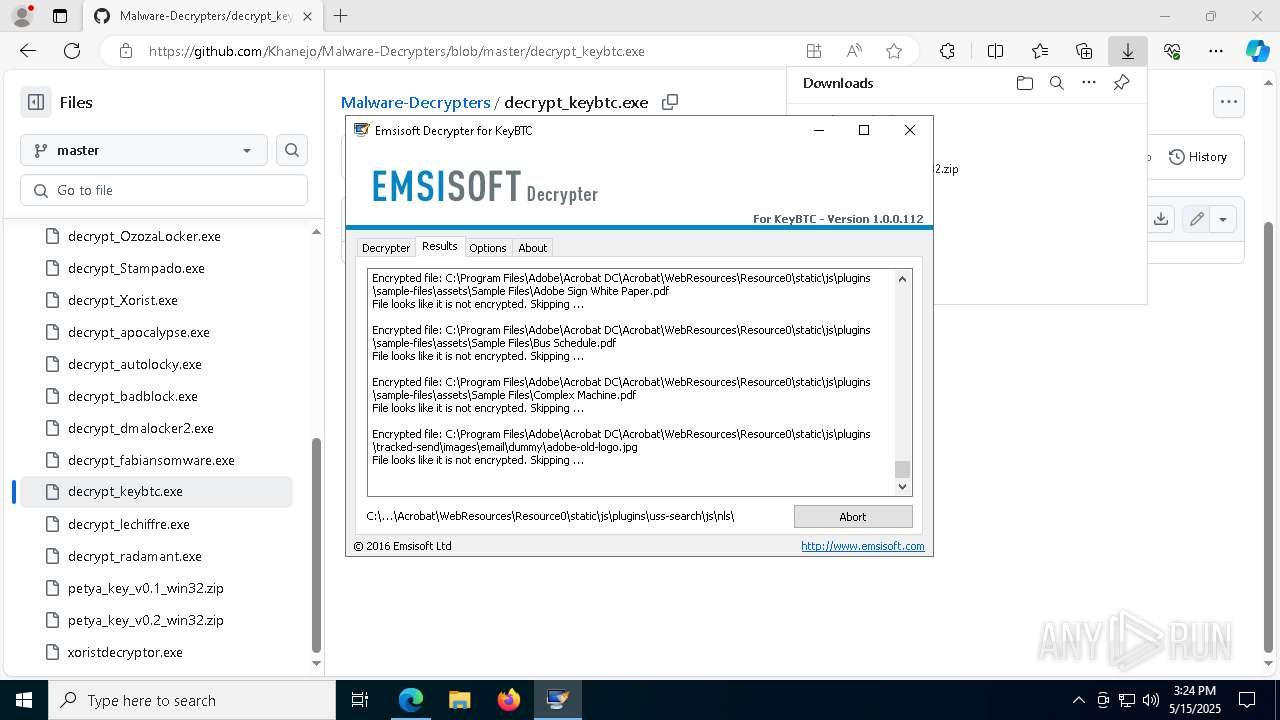
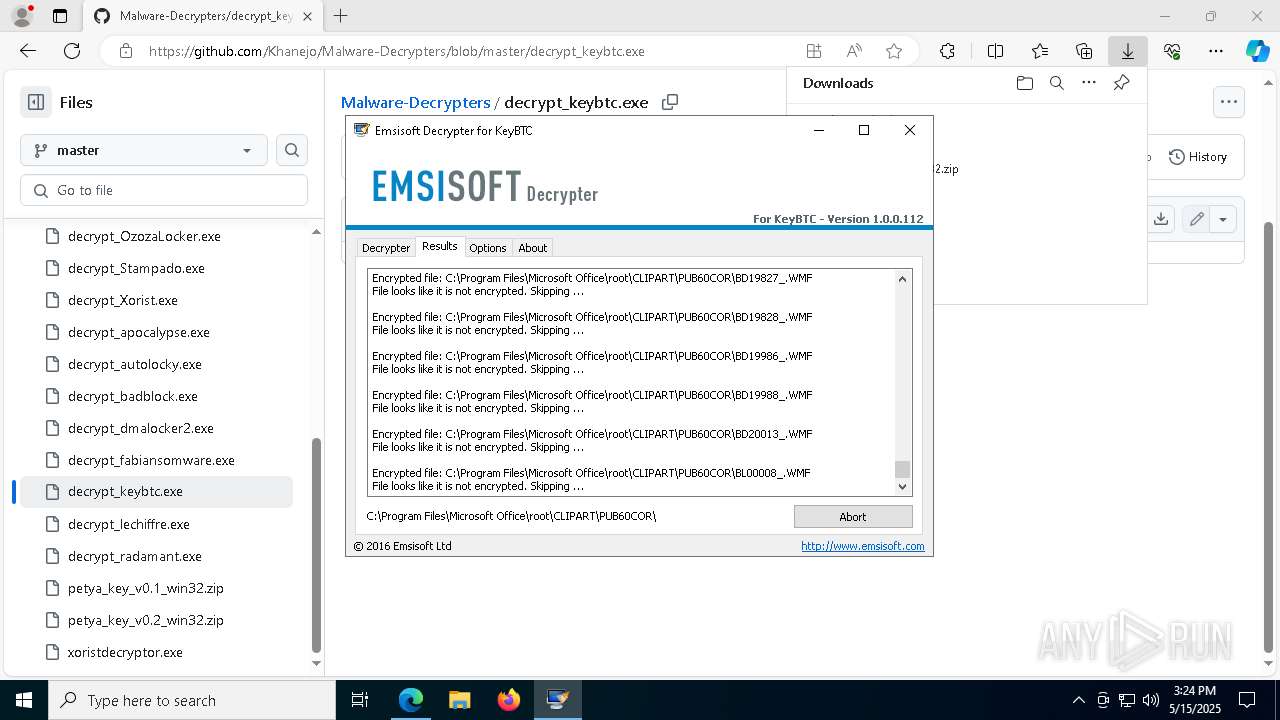
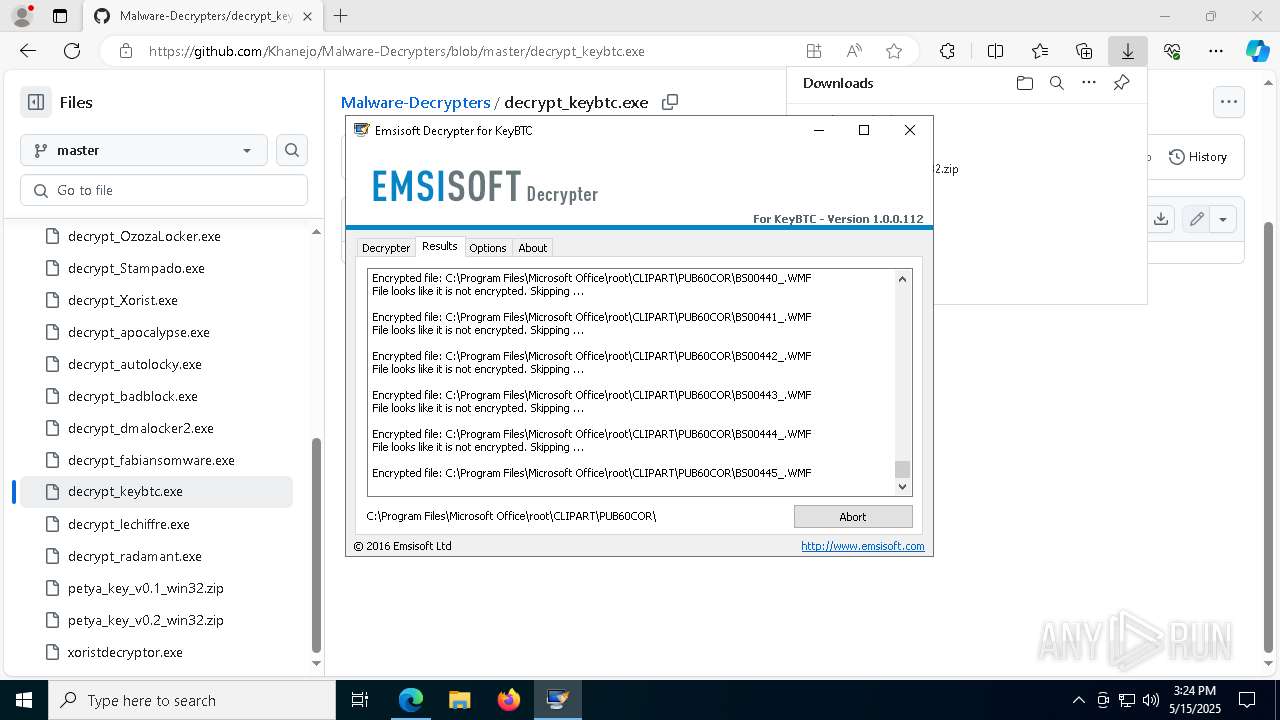
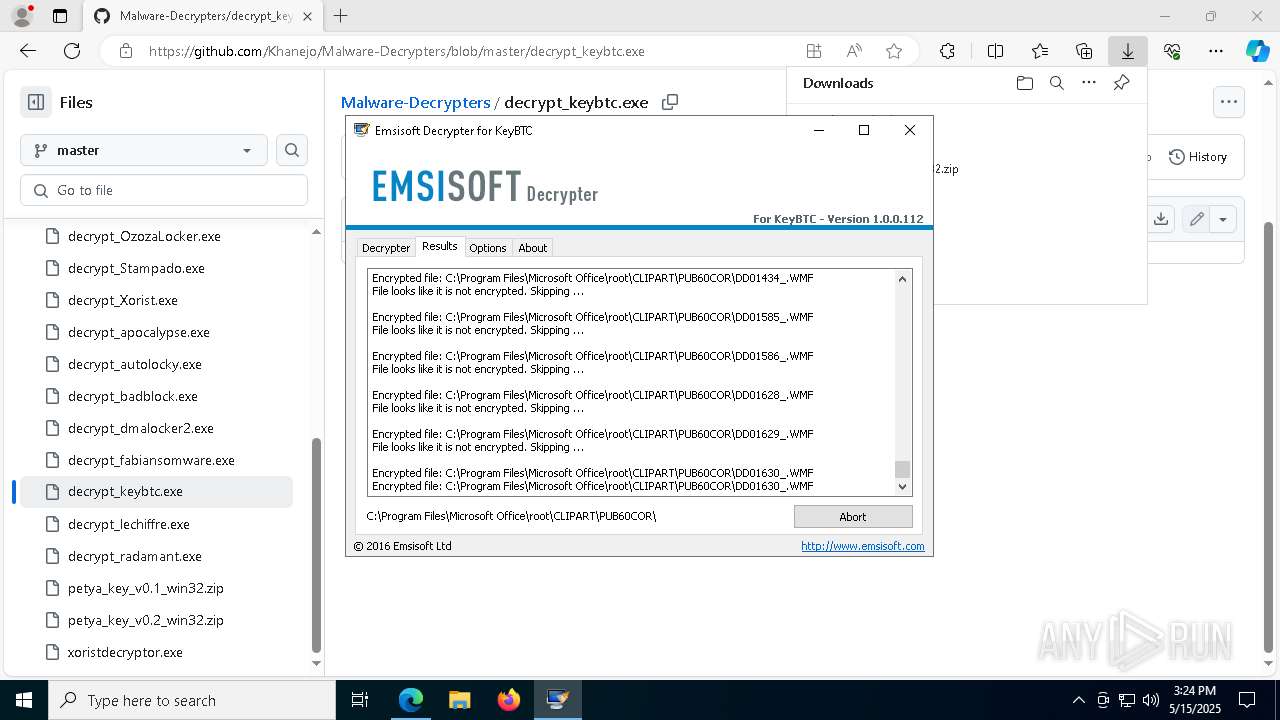
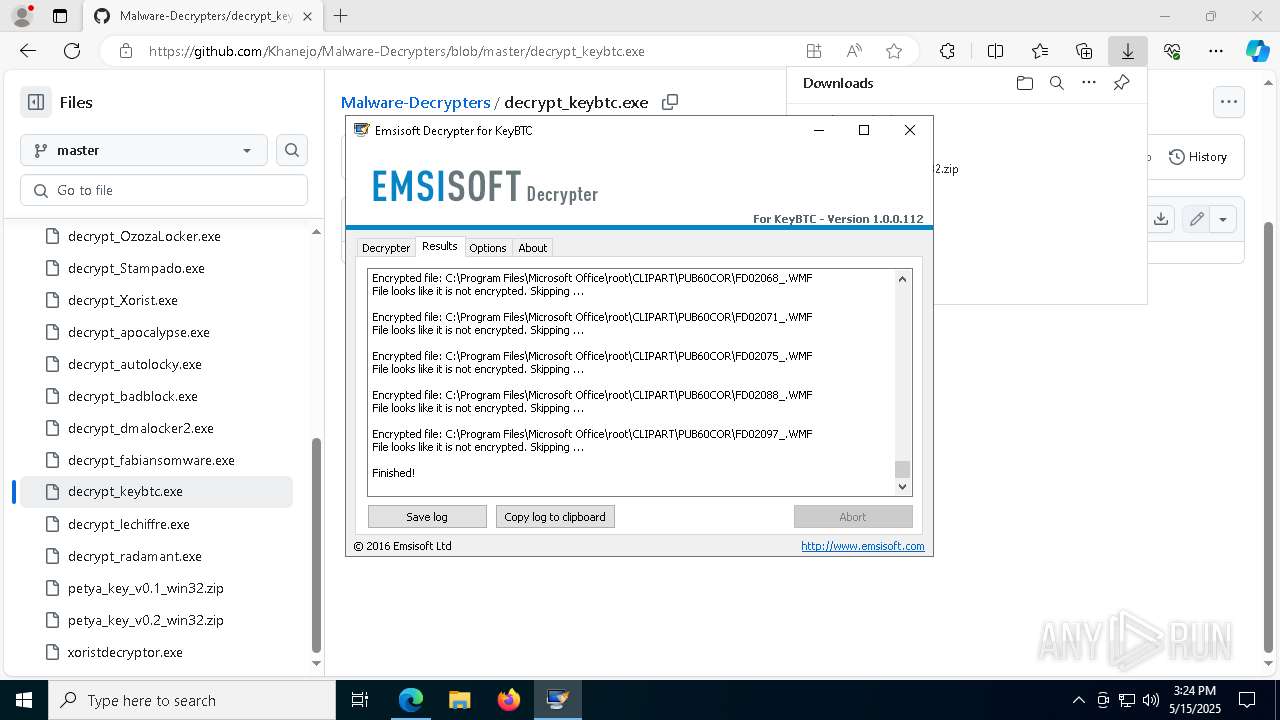
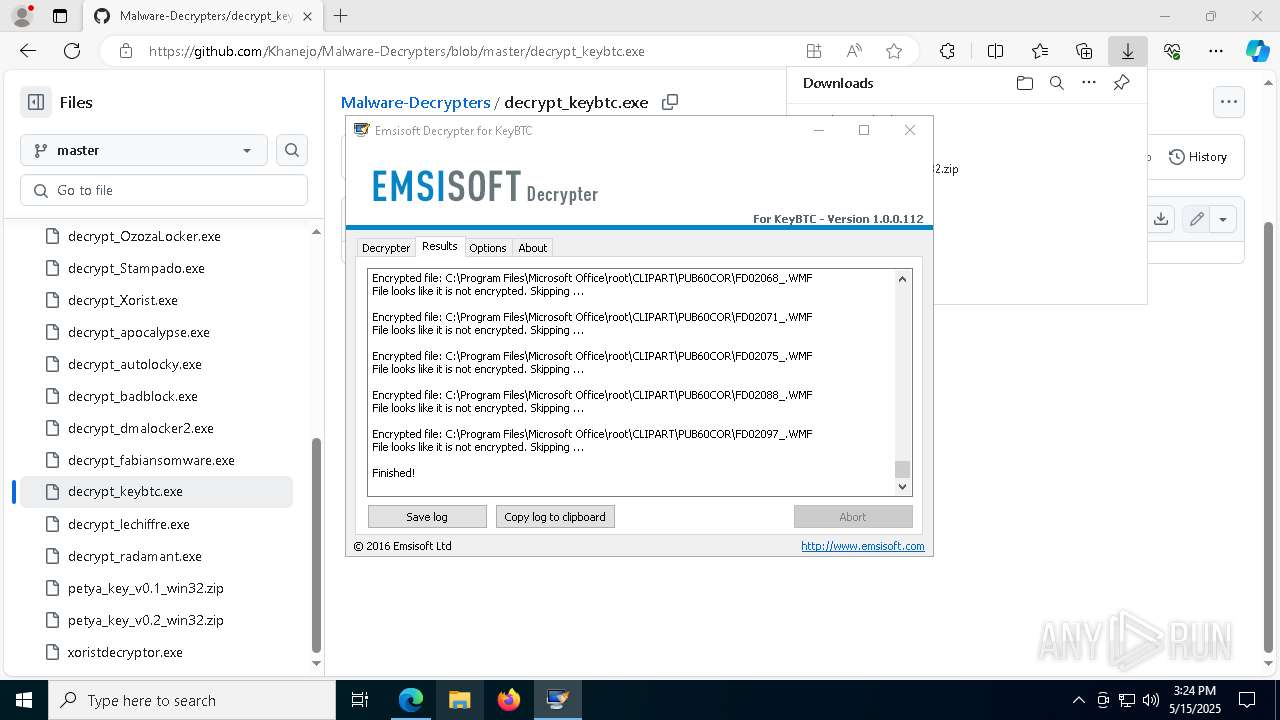
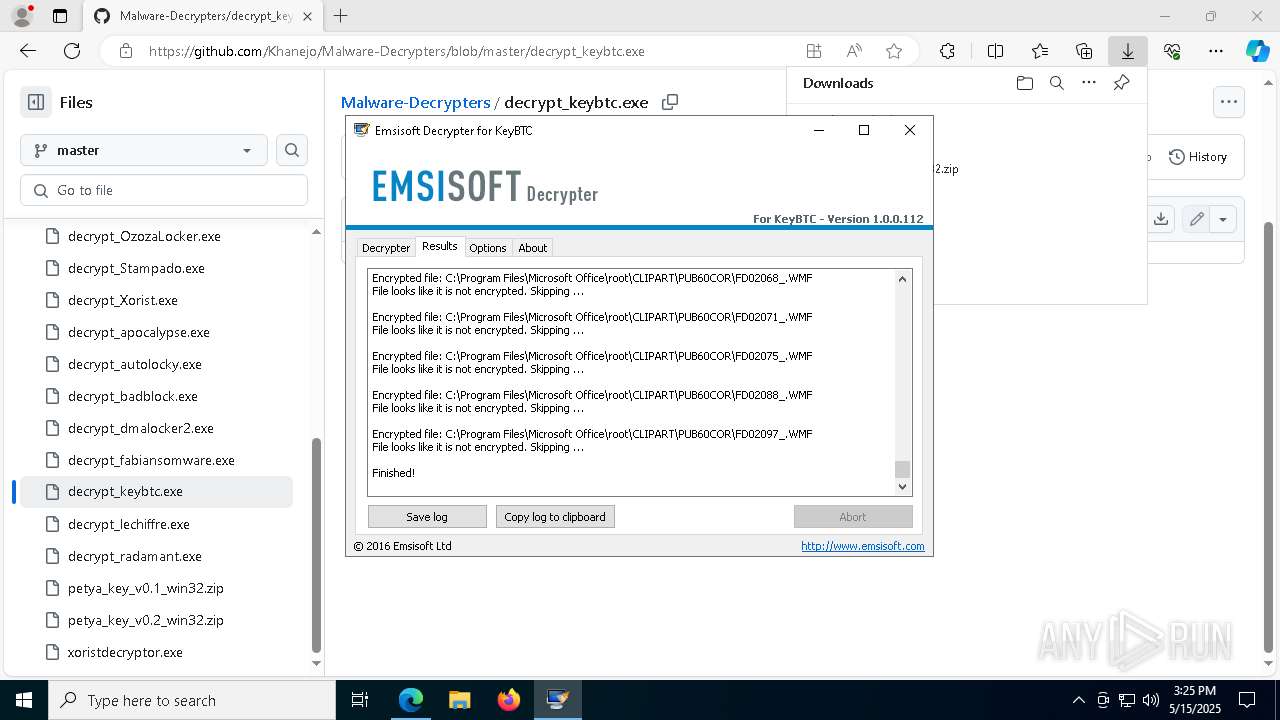
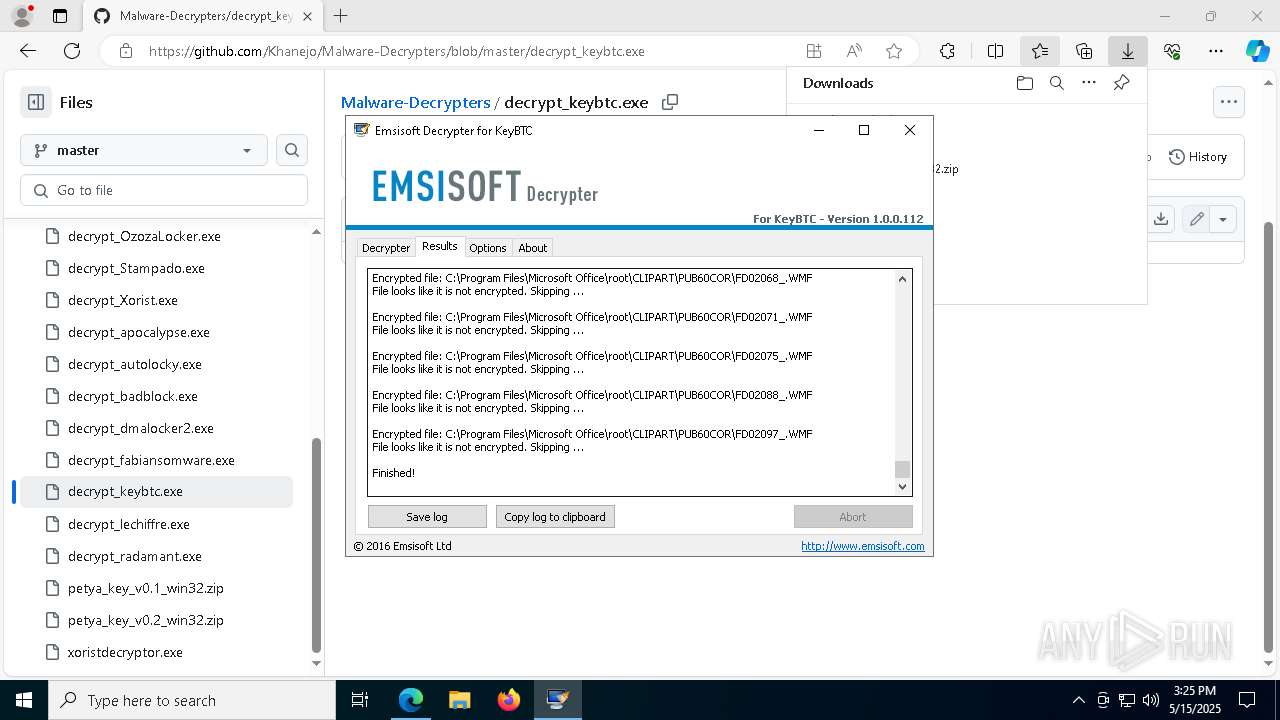
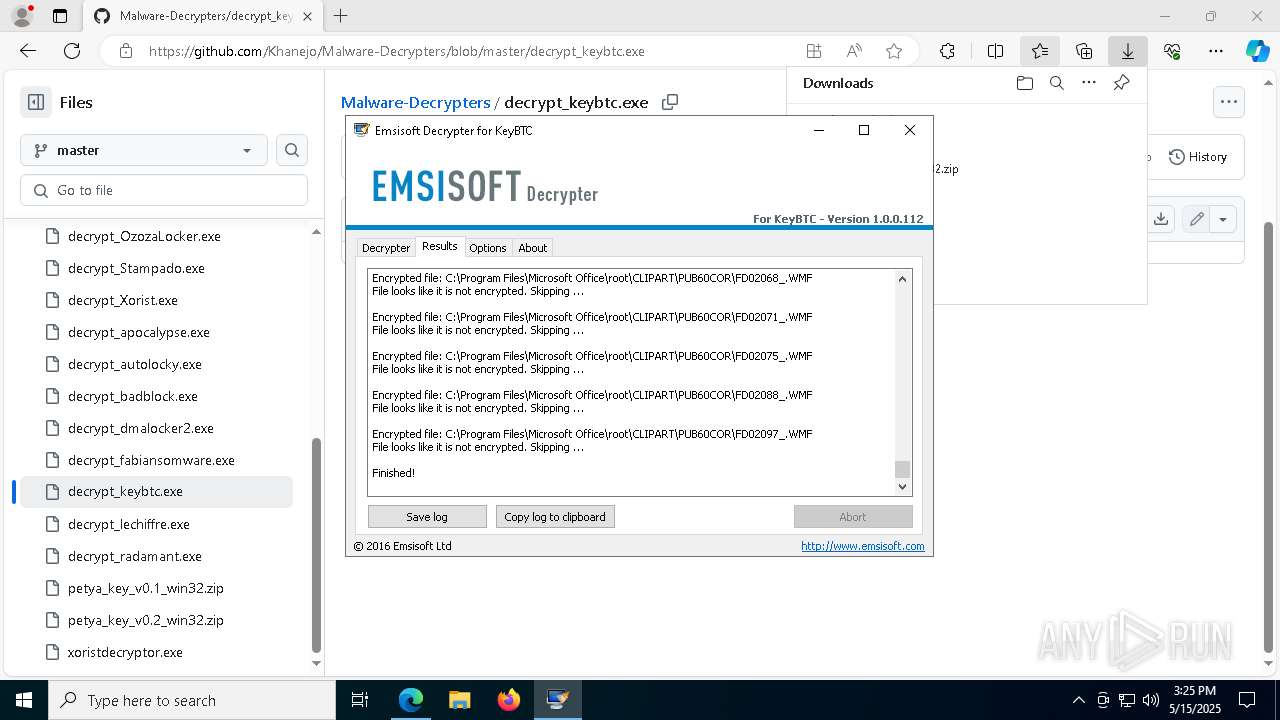
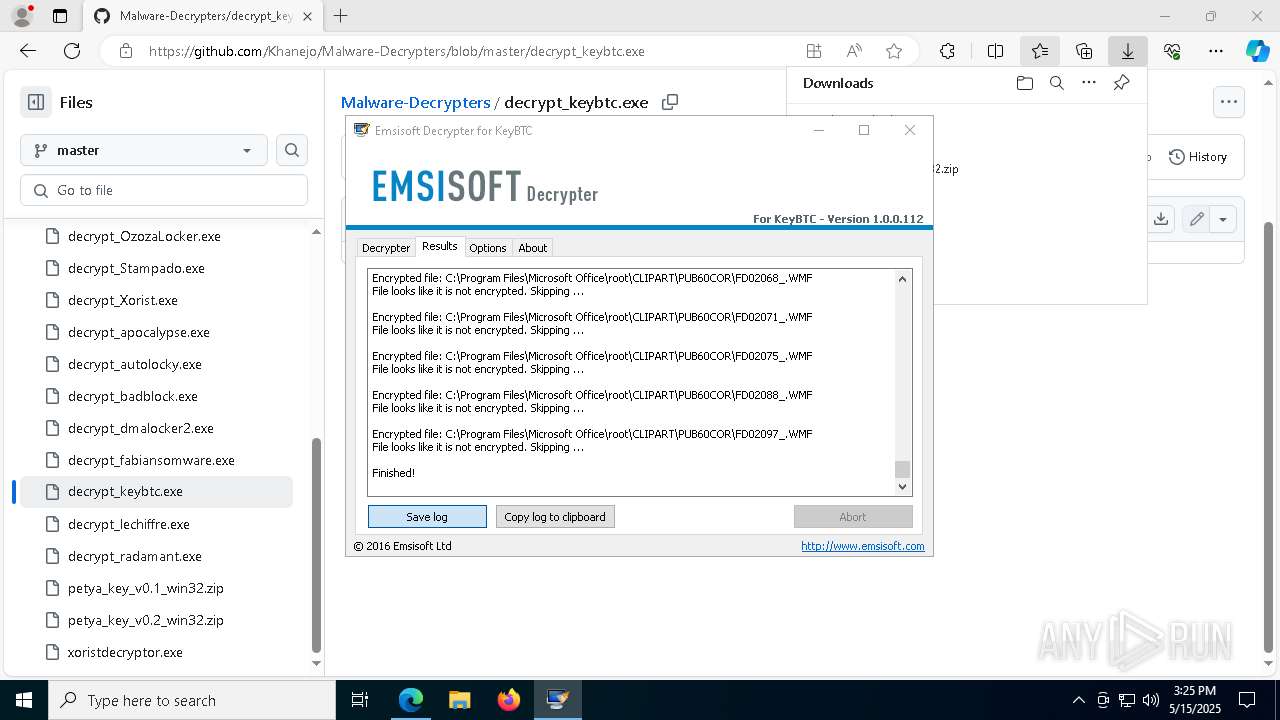
Compiled with Borland Delphi (YARA)
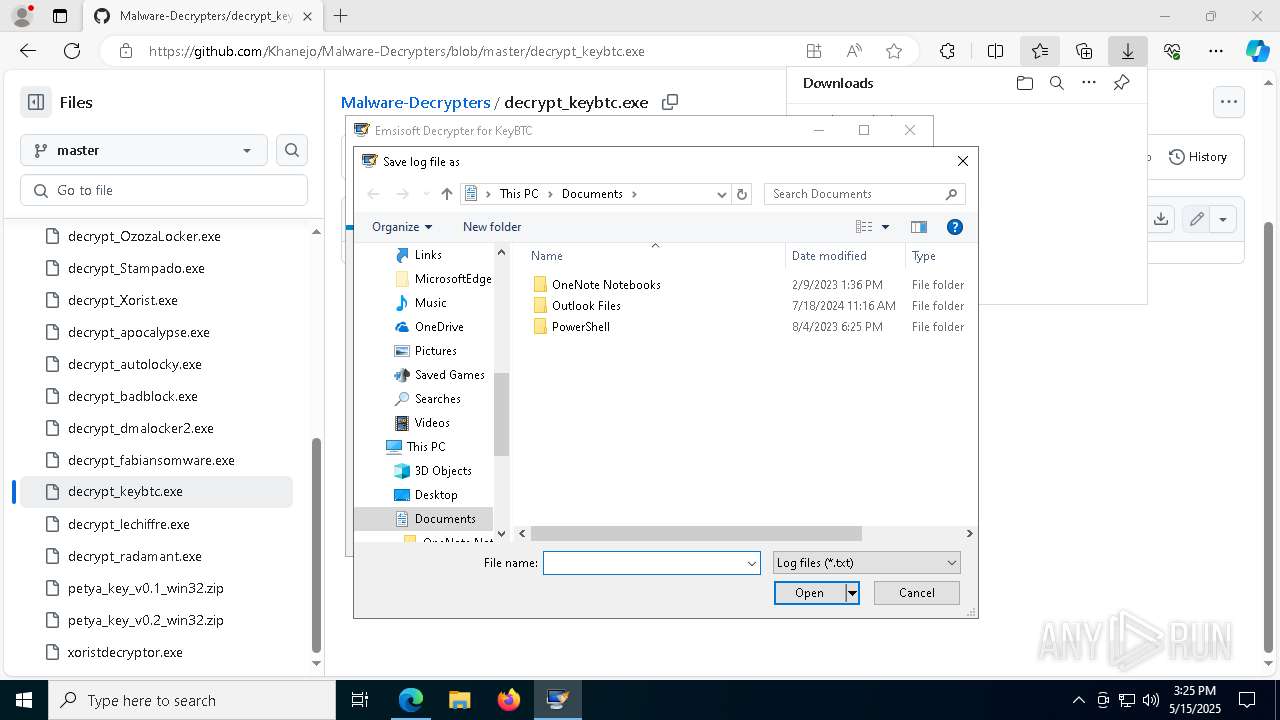
- decrypt_keybtc.exe (PID: 1912)
UPX packer has been detected
- decrypt_keybtc.exe (PID: 1912)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
229
Monitored processes
92
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 472 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=1516 --field-trial-handle=2412,i,15898967589805261944,15020293792994906911,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 616 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=1496 --field-trial-handle=2412,i,15898967589805261944,15020293792994906911,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
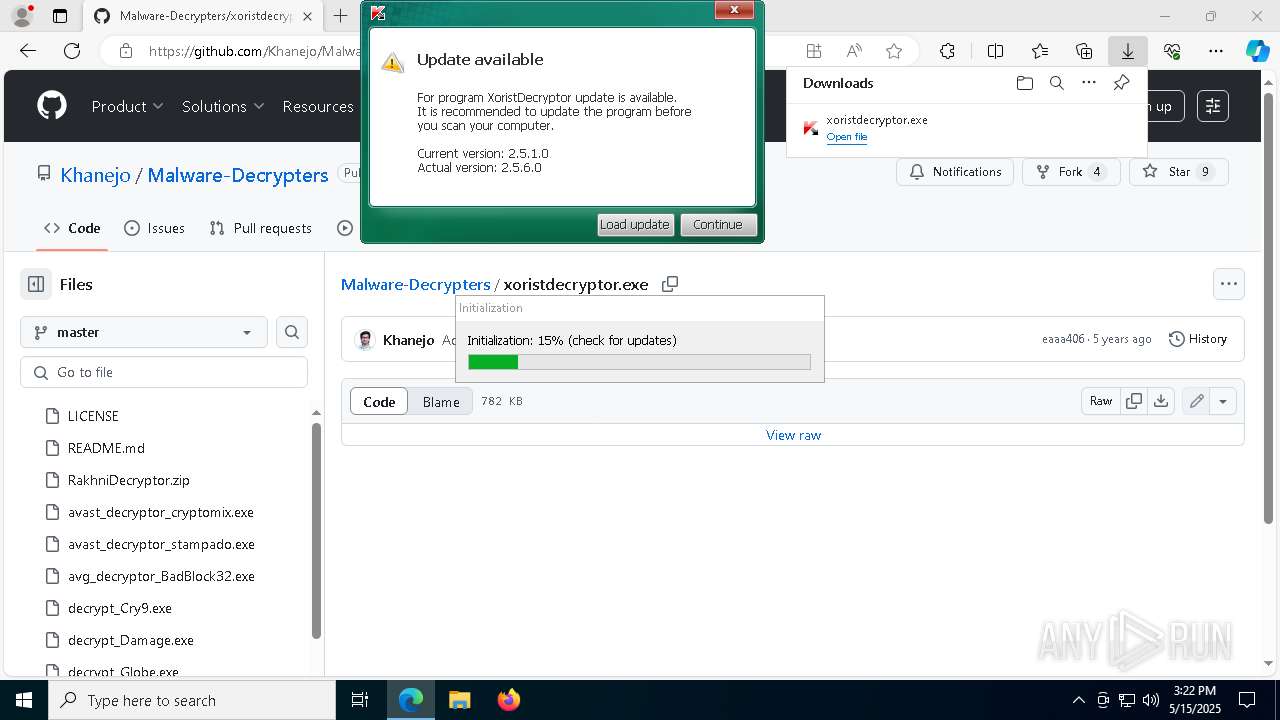
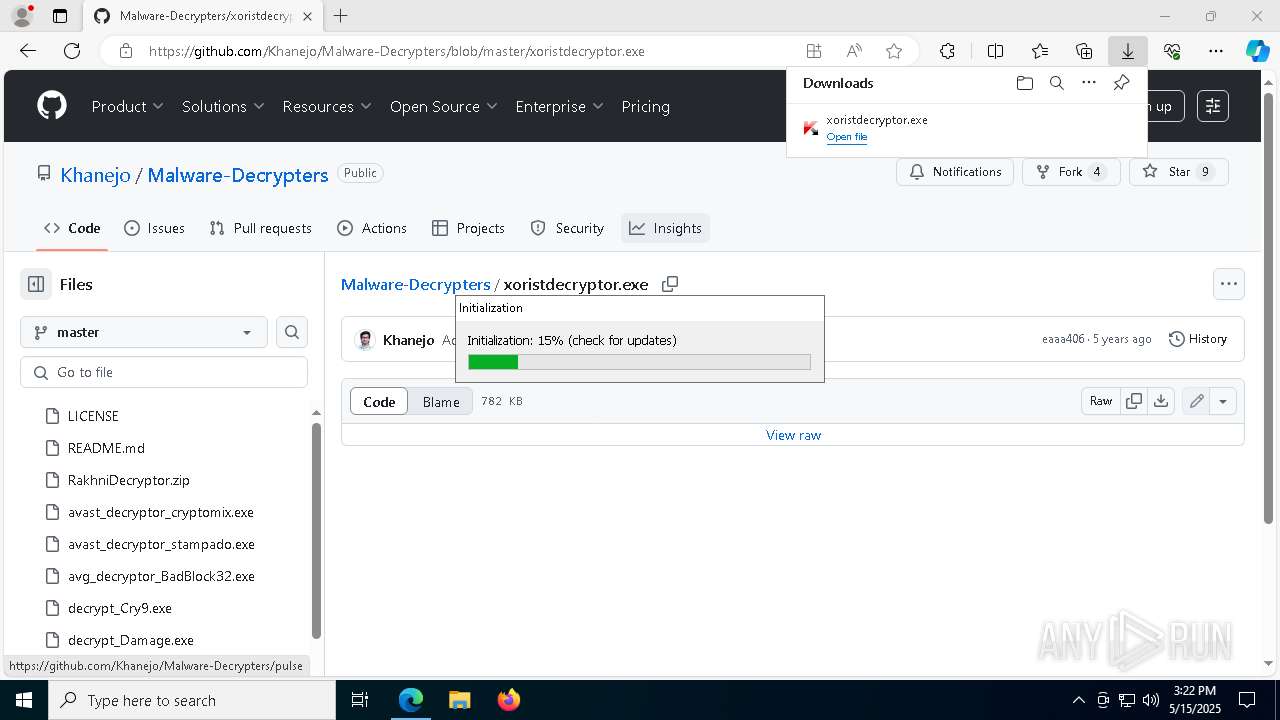
| 632 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa6828.39684\XoristDecryptor.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa6828.39684\XoristDecryptor.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Kaspersky Lab AO Integrity Level: MEDIUM Description: Trojan-Ransom.Win32.Xorist decryptor tool Exit code: 3221226540 Version: 2.5.6.0 Modules
| |||||||||||||||
| 780 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=3728 --field-trial-handle=2412,i,15898967589805261944,15020293792994906911,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 900 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6652 --field-trial-handle=2412,i,15898967589805261944,15020293792994906911,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 968 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4120 --field-trial-handle=2412,i,15898967589805261944,15020293792994906911,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=36 --mojo-platform-channel-handle=6876 --field-trial-handle=2412,i,15898967589805261944,15020293792994906911,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1676 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --single-argument https://media.kaspersky.com/utilities/VirusUtilities/EN/xoristdecryptor.zip | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | {309C5C25-1E6E-41BA-B05A-C4A5EA78D39B}.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1912 | "C:\Users\admin\Downloads\decrypt_keybtc.exe" | C:\Users\admin\Downloads\decrypt_keybtc.exe | — | msedge.exe | |||||||||||
User: admin Company: Emsisoft Ltd Integrity Level: MEDIUM Description: Emsisoft Decrypter for KeyBTC Version: 1.0.0.112 Modules
| |||||||||||||||
| 2236 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2564 --field-trial-handle=2412,i,15898967589805261944,15020293792994906911,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
22 917
Read events
22 797
Write events
118
Delete events
2
Modification events
| (PID) Process: | (3020) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3020) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3020) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3020) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3020) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 79876884C4932F00 | |||
| (PID) Process: | (3020) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: F30E7284C4932F00 | |||
| (PID) Process: | (3020) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197224 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {6307B2C4-D4AC-4983-A674-3D88FED45E90} | |||
| (PID) Process: | (3020) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197224 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {3D855F96-38BC-42A3-A4D5-C69474D60037} | |||
| (PID) Process: | (3020) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197224 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {4DBF22BA-2508-4EE2-BDC3-690F18EF5B45} | |||
| (PID) Process: | (3020) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197224 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {4F20E220-6403-4B6B-B6B6-989B64B78001} | |||
Executable files
34
Suspicious files
594
Text files
64
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3020 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10be12.TMP | — | |
MD5:— | SHA256:— | |||
| 3020 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10be12.TMP | — | |
MD5:— | SHA256:— | |||
| 3020 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3020 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3020 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10be12.TMP | — | |
MD5:— | SHA256:— | |||
| 3020 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3020 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10be22.TMP | — | |
MD5:— | SHA256:— | |||
| 3020 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10be22.TMP | — | |
MD5:— | SHA256:— | |||
| 3020 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3020 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
42
TCP/UDP connections
92
DNS requests
102
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7420 | svchost.exe | GET | 206 | 23.48.23.39:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9530bc3d-28ec-4dca-8d8d-874a68b1b861?P1=1747697097&P2=404&P3=2&P4=jjl48ozJDOXT5iwADHDjnRx5fOJPFvAHFaX3PaRiltlt8Z5D6FHMr2MhuJrx8NMrpuW4wE0LM1WB%2fh1rMrdNrw%3d%3d | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2040 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2040 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
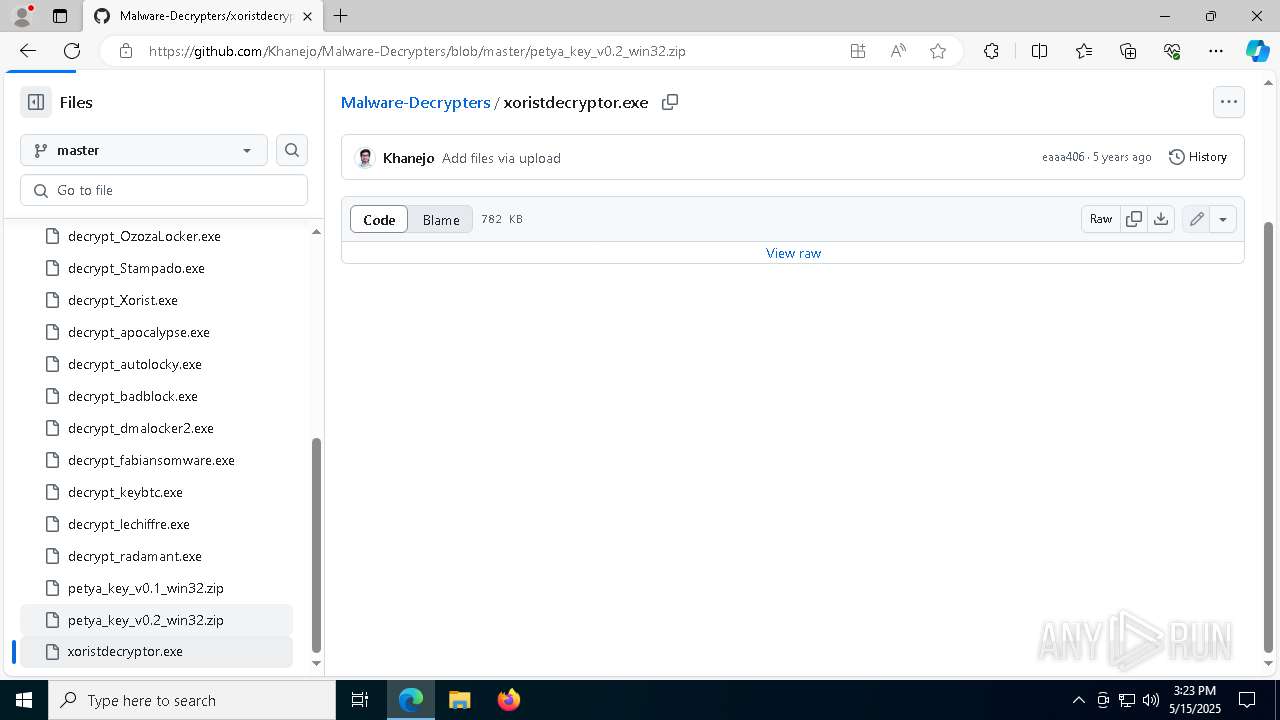
7952 | {309C5C25-1E6E-41BA-B05A-C4A5EA78D39B}.exe | GET | 301 | 185.85.15.38:80 | http://support.kaspersky.com/viruses/xoristdecryptor.xml | unknown | — | — | whitelisted |
5352 | {39FD0E05-E112-4143-8797-6ED6CC723A3A}.exe | GET | 301 | 185.85.15.38:80 | http://support.kaspersky.com/viruses/xoristdecryptor.xml | unknown | — | — | whitelisted |
2772 | {4136618A-FE36-43A2-AF59-4EF37EEE4764}.exe | GET | 301 | 185.85.15.38:80 | http://support.kaspersky.com/viruses/xoristdecryptor.xml | unknown | — | — | whitelisted |
7420 | svchost.exe | HEAD | 200 | 23.48.23.39:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1747697096&P2=404&P3=2&P4=R4lGv4W4D4ryDjxDce8og8GW01x8RcPt99DMyXvtxhaY4z2cjl8JNA3HoSyQO3VbfzjedLq1piy8Q0QMsLqwdg%3d%3d | unknown | — | — | whitelisted |
7420 | svchost.exe | GET | 206 | 23.48.23.39:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1747697096&P2=404&P3=2&P4=R4lGv4W4D4ryDjxDce8og8GW01x8RcPt99DMyXvtxhaY4z2cjl8JNA3HoSyQO3VbfzjedLq1piy8Q0QMsLqwdg%3d%3d | unknown | — | — | whitelisted |
7420 | svchost.exe | GET | 206 | 23.48.23.39:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1747697096&P2=404&P3=2&P4=R4lGv4W4D4ryDjxDce8og8GW01x8RcPt99DMyXvtxhaY4z2cjl8JNA3HoSyQO3VbfzjedLq1piy8Q0QMsLqwdg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2236 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2236 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2236 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2236 | msedge.exe | 140.82.121.4:443 | github.com | GITHUB | US | whitelisted |
2236 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3020 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2236 | msedge.exe | 185.199.111.154:443 | github.githubassets.com | FASTLY | US | whitelisted |
2236 | msedge.exe | 185.199.110.133:443 | avatars.githubusercontent.com | FASTLY | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
github.com |
| whitelisted |
business.bing.com |
| whitelisted |
github.githubassets.com |
| whitelisted |
avatars.githubusercontent.com |
| whitelisted |
www.bing.com |
| whitelisted |
github-cloud.s3.amazonaws.com |
| whitelisted |
user-images.githubusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2236 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2236 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |