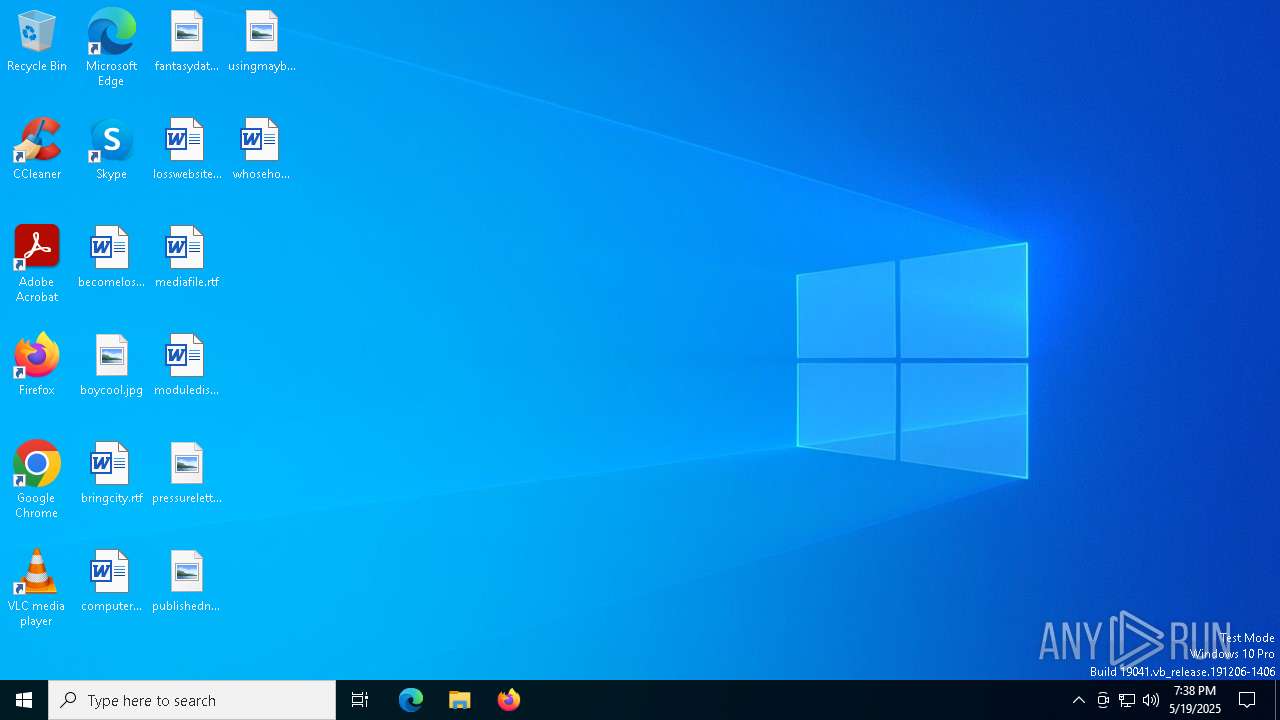
| File name: | BgEVs3zsmY.exe |
| Full analysis: | https://app.any.run/tasks/842679a5-6f3c-42ea-94ba-fcb71e054101 |
| Verdict: | Malicious activity |
| Analysis date: | May 19, 2025, 19:38:11 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 12 sections |
| MD5: | 9AA1FAC86C19E69A39843B7D86435F03 |
| SHA1: | C66A86F05A5F2E19531A7E784DDB37606E56B620 |
| SHA256: | 1DCFAD6DC42B3202E113C87ACD2814301A5AB25A78EEAF199D1285E14D3589FA |
| SSDEEP: | 98304:uZchBjtfk+FBjcOmr3GvC+fOp7OLaOZolwEN2LCpVGDjRiY3q4HJXZLwdQD/kpgJ:H5TVn5Iy0pPeNnLC9IL |
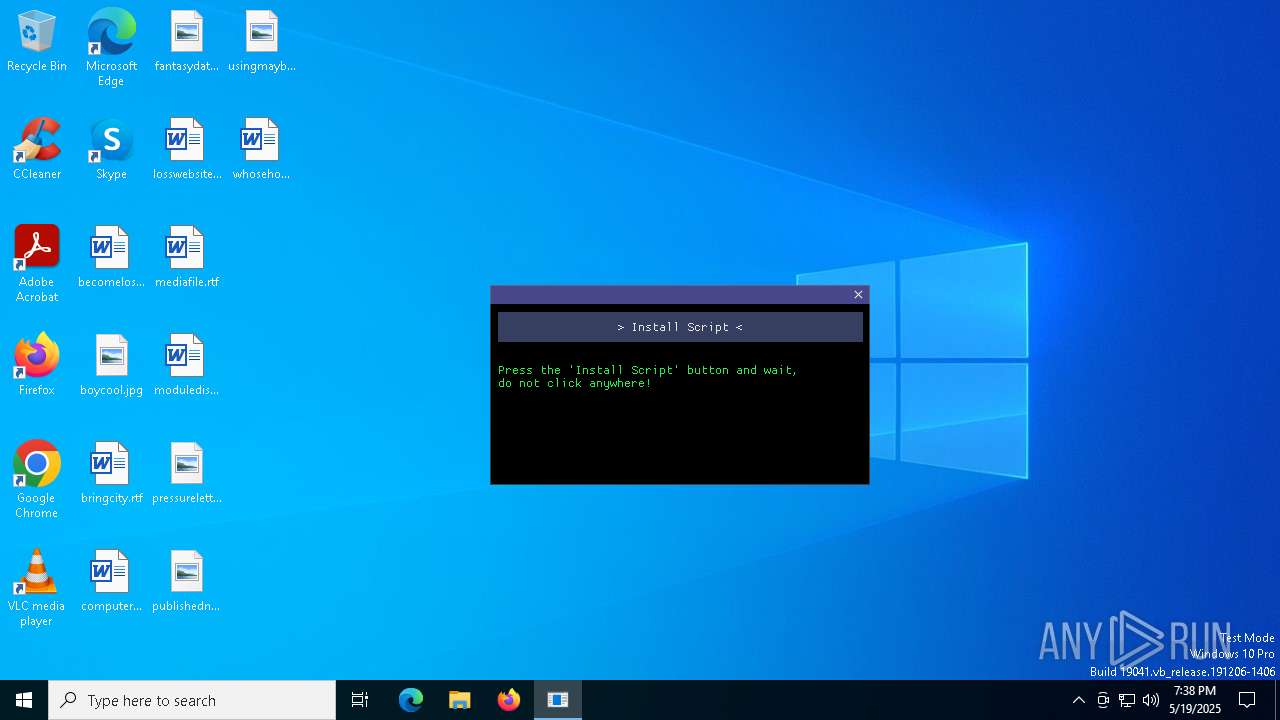
MALICIOUS
Executing a file with an untrusted certificate
- BgEVs3zsmY.exe (PID: 7620)
- BgEVs3zsmY.exe (PID: 7472)
Adds path to the Windows Defender exclusion list
- BgEVs3zsmY.exe (PID: 7620)
- cmd.exe (PID: 7980)
Changes Windows Defender settings
- cmd.exe (PID: 7980)
SUSPICIOUS
Reads the BIOS version
- BgEVs3zsmY.exe (PID: 7620)
Searches and executes a command on selected files
- forfiles.exe (PID: 6036)
- forfiles.exe (PID: 8140)
- forfiles.exe (PID: 5452)
- forfiles.exe (PID: 1532)
- forfiles.exe (PID: 4424)
- forfiles.exe (PID: 1180)
- forfiles.exe (PID: 7676)
- forfiles.exe (PID: 7972)
- forfiles.exe (PID: 7784)
- forfiles.exe (PID: 7988)
Starts CMD.EXE for commands execution
- BgEVs3zsmY.exe (PID: 7620)
The process deletes folder without confirmation
- BgEVs3zsmY.exe (PID: 7620)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 8156)
- cmd.exe (PID: 3268)
- cmd.exe (PID: 7236)
- cmd.exe (PID: 2136)
- cmd.exe (PID: 7684)
- cmd.exe (PID: 7668)
- cmd.exe (PID: 7848)
- cmd.exe (PID: 5344)
- cmd.exe (PID: 536)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 7316)
- cmd.exe (PID: 7780)
- cmd.exe (PID: 4880)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7980)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 7980)
The process creates files with name similar to system file names
- BgEVs3zsmY.exe (PID: 7620)
INFO
Checks supported languages
- BgEVs3zsmY.exe (PID: 7620)
Process checks whether UAC notifications are on
- BgEVs3zsmY.exe (PID: 7620)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7612)
Themida protector has been detected
- BgEVs3zsmY.exe (PID: 7620)
Reads the computer name
- BgEVs3zsmY.exe (PID: 7620)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7612)
Reads the software policy settings
- BgEVs3zsmY.exe (PID: 7620)
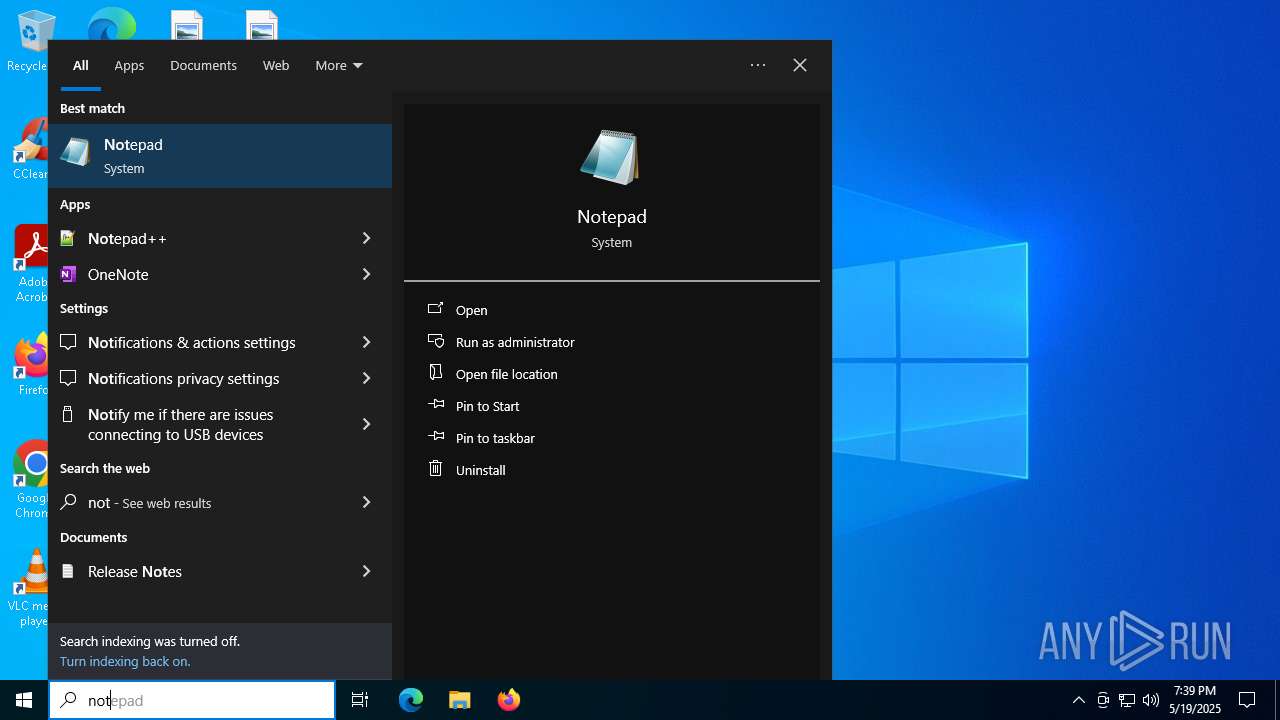
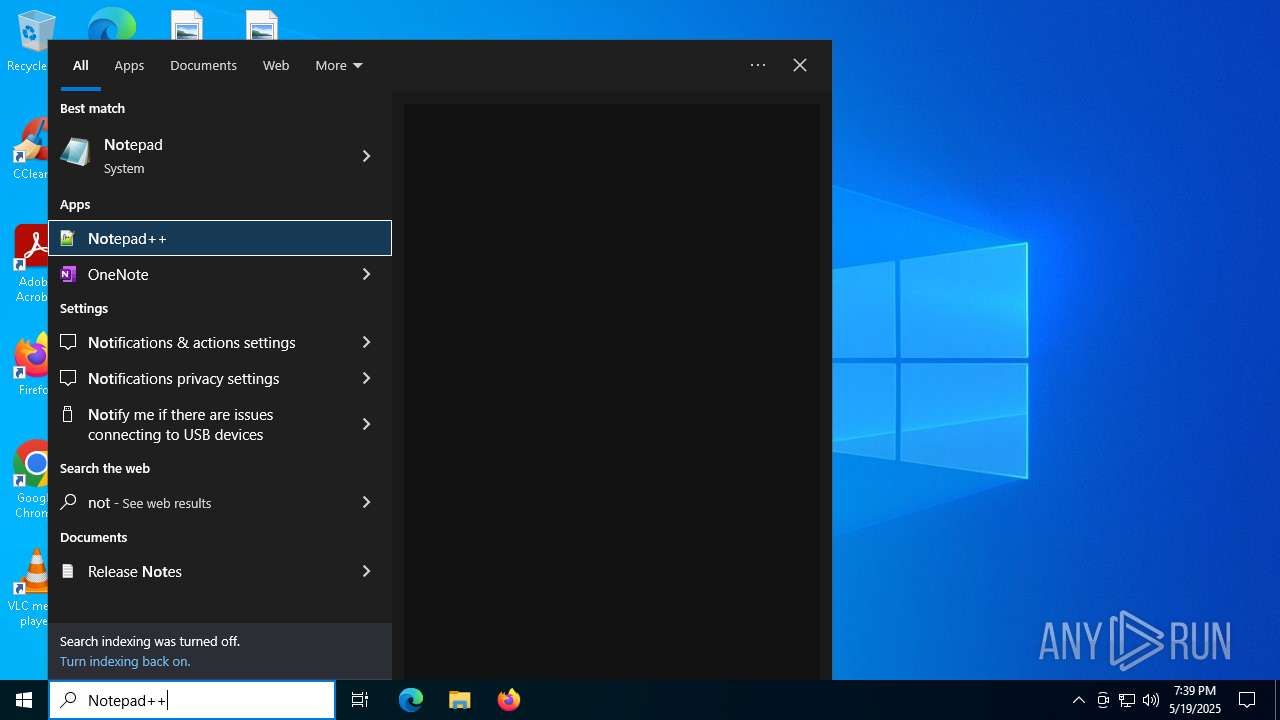
Manual execution by a user
- notepad++.exe (PID: 7232)
Creates files in the program directory
- BgEVs3zsmY.exe (PID: 7620)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:05:18 17:32:31+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.42 |
| CodeSize: | 449536 |
| InitializedDataSize: | 152064 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa2b058 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
271
Monitored processes
140
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 456 | C:\WINDOWS\system32\cmd.exe /c cls | C:\Windows\System32\cmd.exe | — | BgEVs3zsmY.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 536 | C:\WINDOWS\system32\cmd.exe /c REG ADD "HKEY_USERS\%usersid%\Software\Microsoft\Windows\CurrentVersion\Explorer\MountPoints2" | C:\Windows\System32\cmd.exe | — | BgEVs3zsmY.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 664 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 920 | REG ADD "HKEY_USERS\%usersid%\Software\Microsoft\Windows\CurrentVersion\Explorer\MountPoints2" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1072 | C:\WINDOWS\system32\cmd.exe /c forfiles /P "%_Local_Temp%" /M * /C "cmd /c if @ISDir==TRUE rmdir /S /Q @File" | C:\Windows\System32\cmd.exe | — | BgEVs3zsmY.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1180 | forfiles /P "%_windows_temp%" /M * /C "cmd /c if @ISDir==FALSE del @File" | C:\Windows\System32\forfiles.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: ForFiles - Executes a command on selected files Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1180 | C:\WINDOWS\system32\cmd.exe /c DEL /f /q %systemroot%\Prefetch\ReadyBoot\*.fx | C:\Windows\System32\cmd.exe | — | BgEVs3zsmY.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1228 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1324 | C:\WINDOWS\system32\cmd.exe /c DEL /f /q %APPDATA%\Microsoft\Windows\Recent\*.* | C:\Windows\System32\cmd.exe | — | BgEVs3zsmY.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1532 | forfiles /P "%_Local_Temp%" /M * /C "cmd /c if @ISDir==TRUE rmdir /S /Q @File" | C:\Windows\System32\forfiles.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: ForFiles - Executes a command on selected files Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
8 802
Read events
8 802
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
1
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7612 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_2quocnob.vyr.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7612 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:AFC2F6A3D7578C02397E2337CB746B75 | SHA256:E7A1DC818D65A5D94F28622EEA4A54DE0AAD1E5188E0ECF7F615DB1D006B07E1 | |||
| 7232 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\langs.xml | xml | |
MD5:FE22EC5755BC98988F9656F73B2E6FB8 | SHA256:F972C425CE176E960F6347F1CA2F64A8CE2B95A375C33A03E57538052BA0624D | |||
| 7232 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\stylers.xml | xml | |
MD5:312281C4126FA897EF21A7E8CCB8D495 | SHA256:53B4BE3ED1CFD712E53542B30CFE30C5DB35CC48BE7C57727DFEC26C9E882E90 | |||
| 7232 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\shortcuts.xml | text | |
MD5:F11D96162BC521F5CF49FFE6B6841C9B | SHA256:BE9AEAEAB5A2E4899BA7E582274BA592C1B9BAF688B340A754B8EF32B23CFA9C | |||
| 7612 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_50ikk1nm.dp1.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
32
DNS requests
18
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6148 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6148 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.19.11.105:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.128:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
7620 | BgEVs3zsmY.exe | 104.21.48.1:443 | hibakusha.pw | CLOUDFLARENET | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
hibakusha.pw |
| unknown |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |