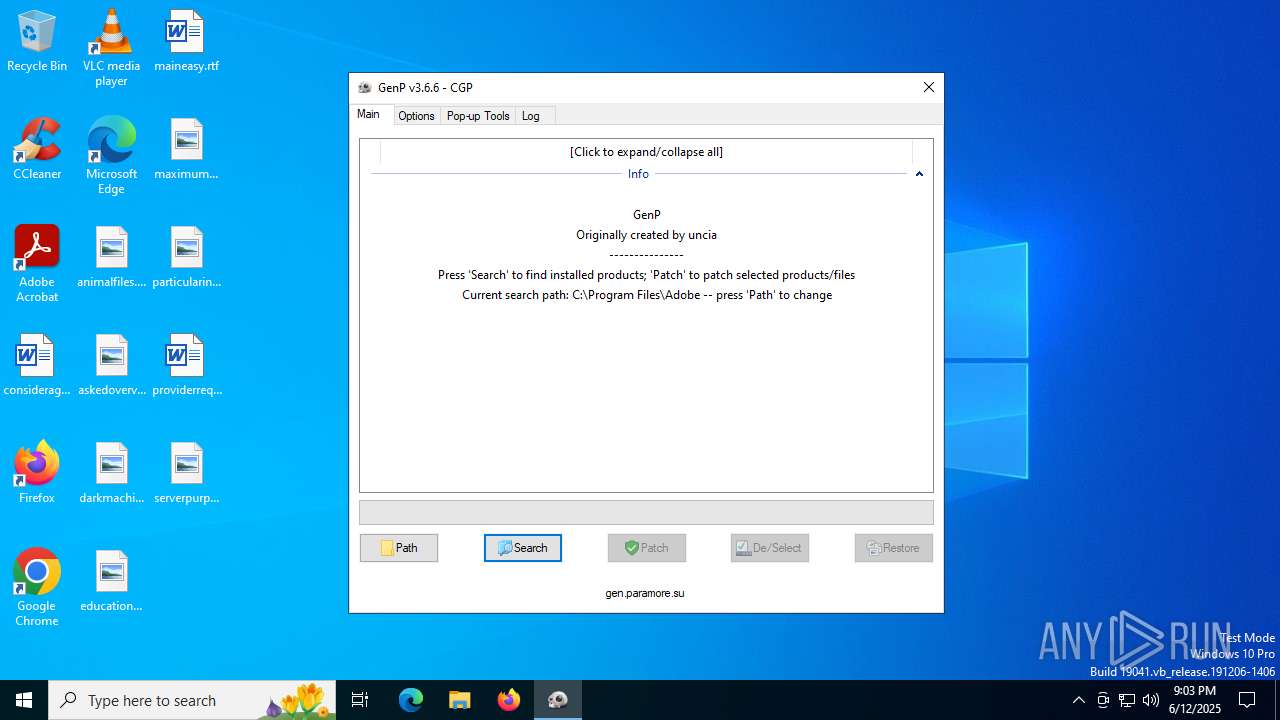
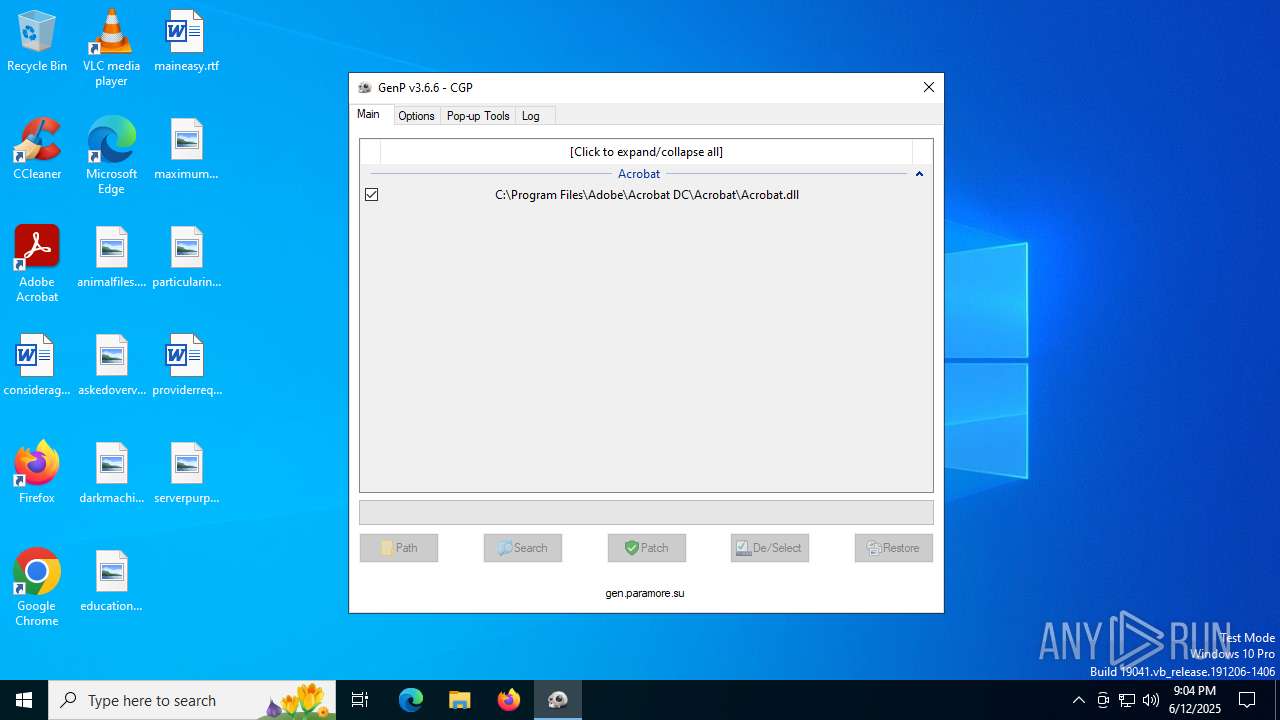
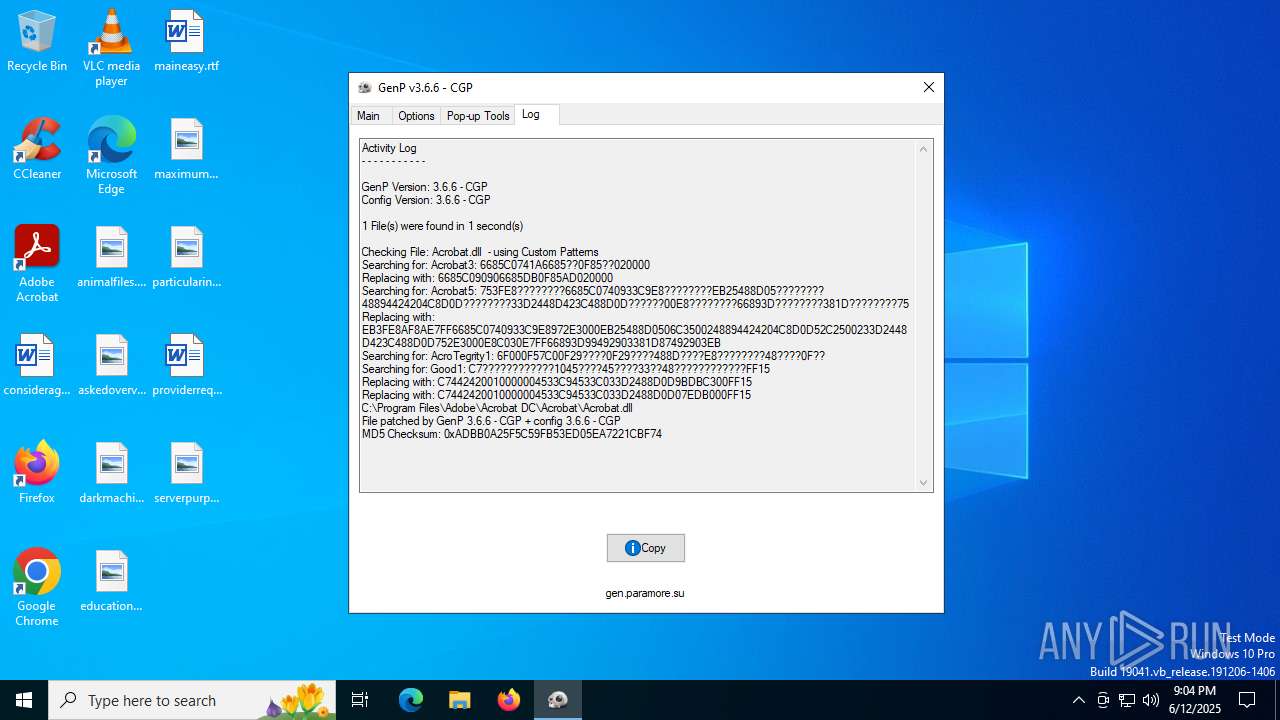
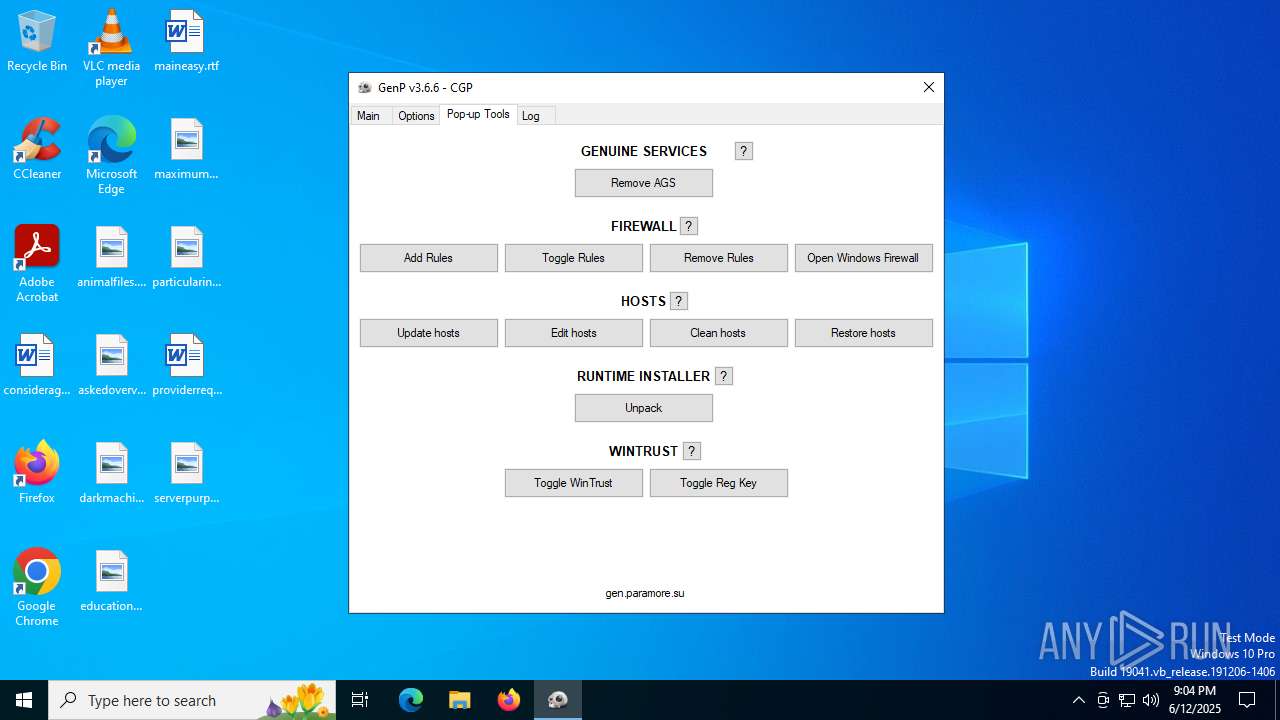
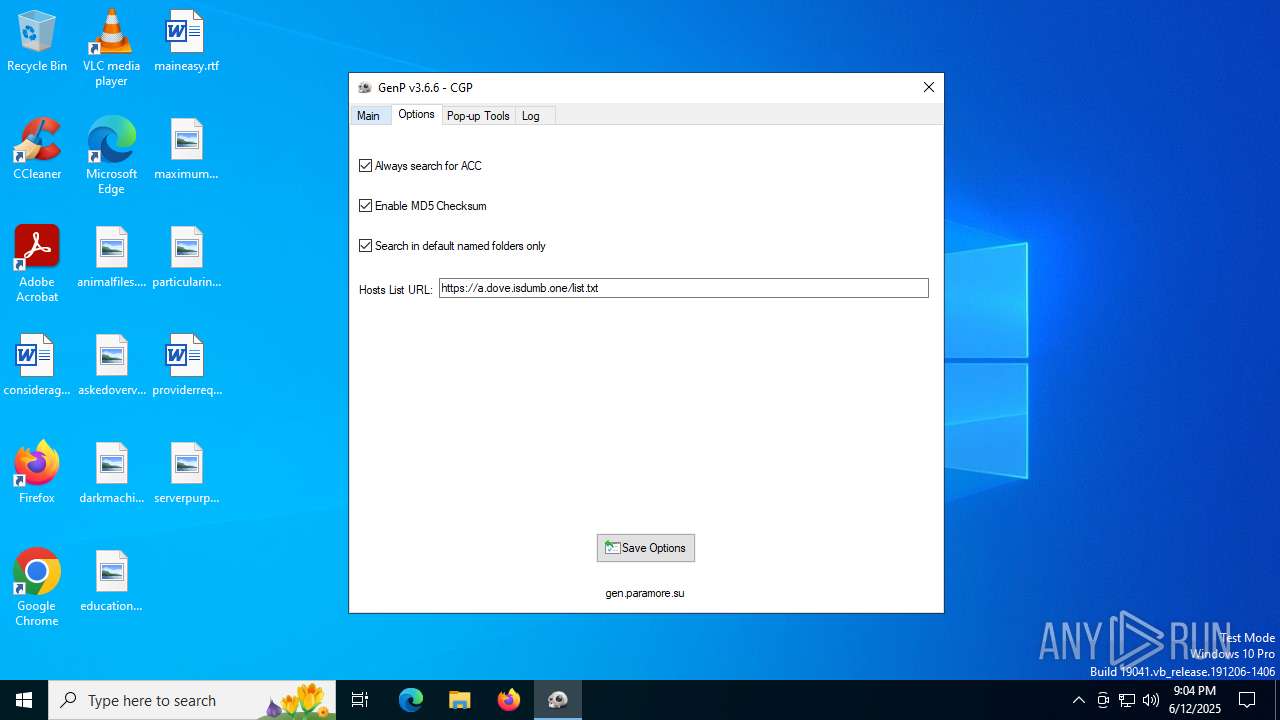
| File name: | GenP-v3.6.6.exe |
| Full analysis: | https://app.any.run/tasks/98ba4d7e-b556-4979-9dc4-a1a42ad90166 |
| Verdict: | Malicious activity |
| Analysis date: | June 12, 2025, 21:03:48 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 3 sections |
| MD5: | F7CDC7B76C80DCED39E24BC5E0995F0F |
| SHA1: | 10D1765F0292E386A753B4D9559AE155302385FD |
| SHA256: | 1DCB04625F4555B6988C7D9309C49E872FFF584E913AAD8530227CF641FD018D |
| SSDEEP: | 49152:ketKmupSfNHjl4ClQaig25jSHY7GvXiADpB/TmPkRzbkR91Z/KlNKYOJCTOB2U2f:VtKDpSRjVKjg25j1Shpp8sbAj5OKYYCx |
MALICIOUS
No malicious indicators.SUSPICIOUS
There is functionality for taking screenshot (YARA)
- GenP-v3.6.6.exe (PID: 6364)
INFO
The sample compiled with english language support
- GenP-v3.6.6.exe (PID: 6364)
Create files in a temporary directory
- GenP-v3.6.6.exe (PID: 6364)
Reads mouse settings
- GenP-v3.6.6.exe (PID: 6364)
Reads the computer name
- GenP-v3.6.6.exe (PID: 6364)
Checks supported languages
- GenP-v3.6.6.exe (PID: 6364)
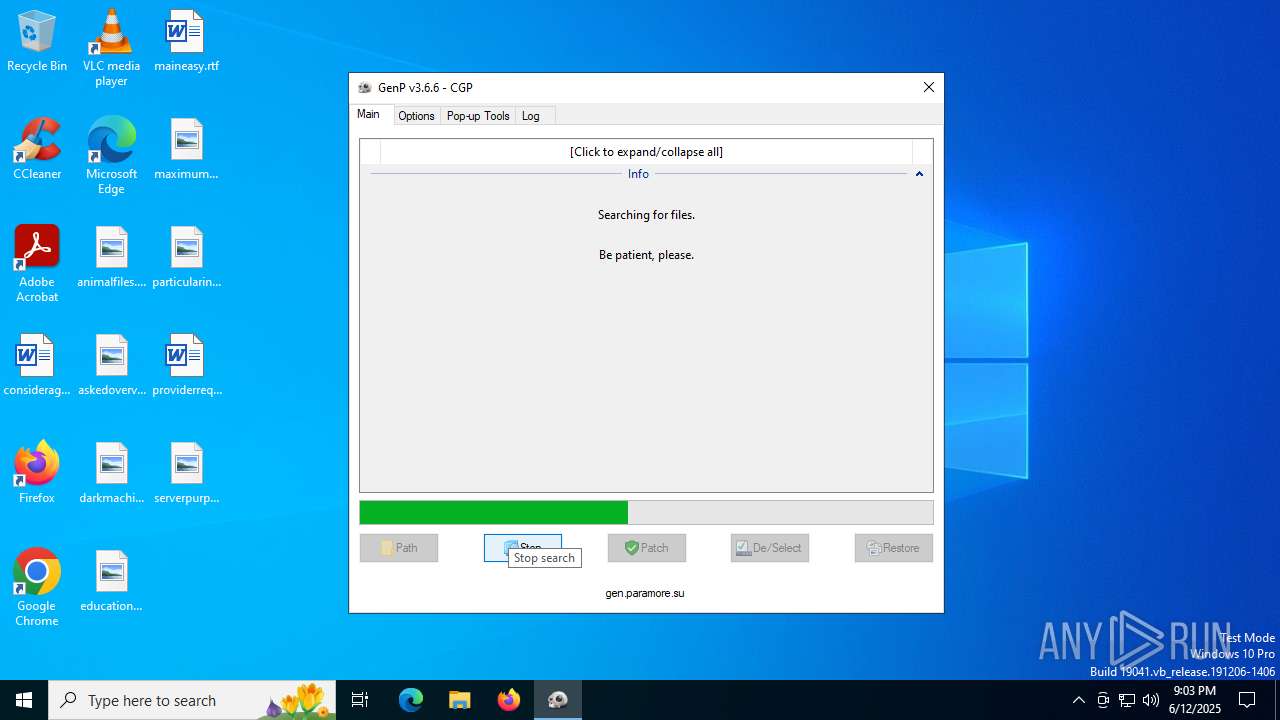
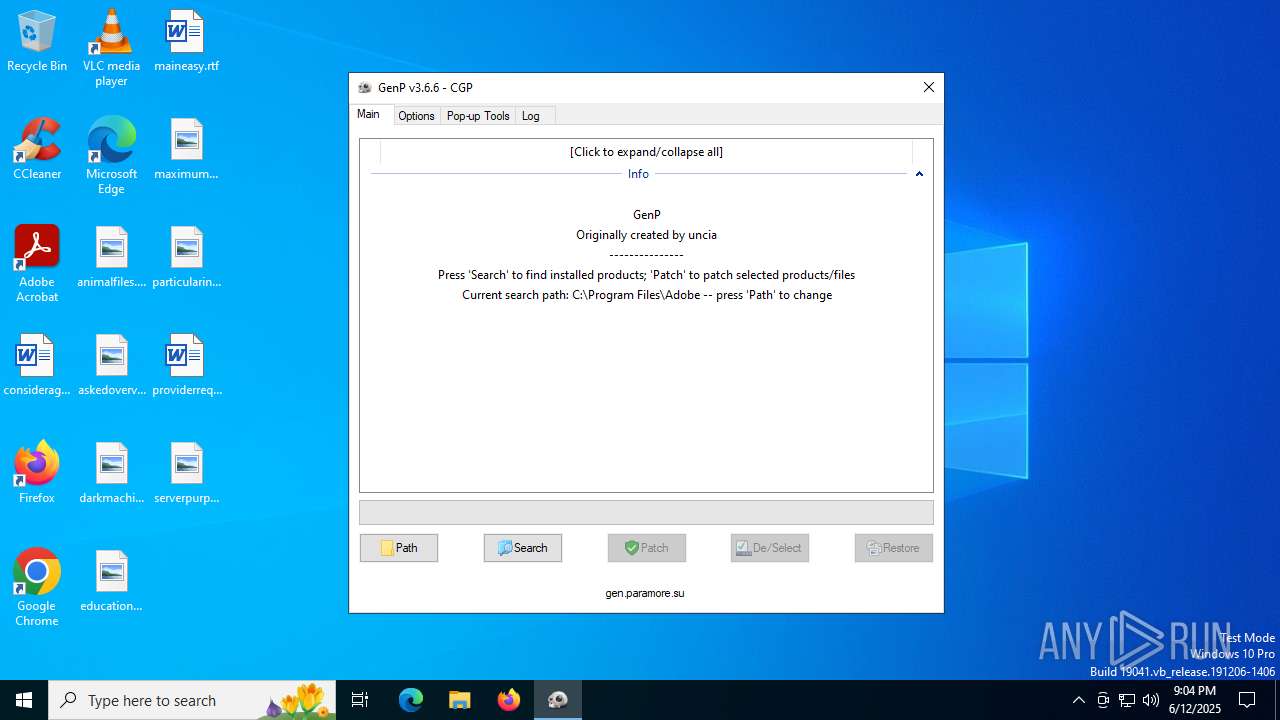
The process uses AutoIt
- GenP-v3.6.6.exe (PID: 6364)
UPX packer has been detected
- GenP-v3.6.6.exe (PID: 6364)
Creates files in the program directory
- GenP-v3.6.6.exe (PID: 6364)
Reads the machine GUID from the registry
- GenP-v3.6.6.exe (PID: 6364)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (87.1) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.4) |
| .exe | | | DOS Executable Generic (6.4) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:06:05 03:04:17+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.16 |
| CodeSize: | 421888 |
| InitializedDataSize: | 1105920 |
| UninitializedDataSize: | 1736704 |
| EntryPoint: | 0x20ee60 |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.6.6.0 |
| ProductVersionNumber: | 3.6.6.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
| FileVersion: | 3.6.6.0 |
| Comments: | GenP |
| FileDescription: | GenP |
| ProductName: | GenP |
| ProductVersion: | 3.6.6 |
| CompanyName: | GenP |
| LegalCopyright: | GenP 2025 |
| LegalTradeMarks: | GenP 2025 |
Total processes
138
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6364 | "C:\Users\admin\AppData\Local\Temp\GenP-v3.6.6.exe" | C:\Users\admin\AppData\Local\Temp\GenP-v3.6.6.exe | explorer.exe | ||||||||||||
User: admin Company: GenP Integrity Level: HIGH Description: GenP Version: 3.6.6.0 Modules
| |||||||||||||||
| 6584 | "C:\Users\admin\AppData\Local\Temp\GenP-v3.6.6.exe" | C:\Users\admin\AppData\Local\Temp\GenP-v3.6.6.exe | — | explorer.exe | |||||||||||
User: admin Company: GenP Integrity Level: MEDIUM Description: GenP Exit code: 3221226540 Version: 3.6.6.0 Modules
| |||||||||||||||
Total events
38
Read events
38
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
1
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
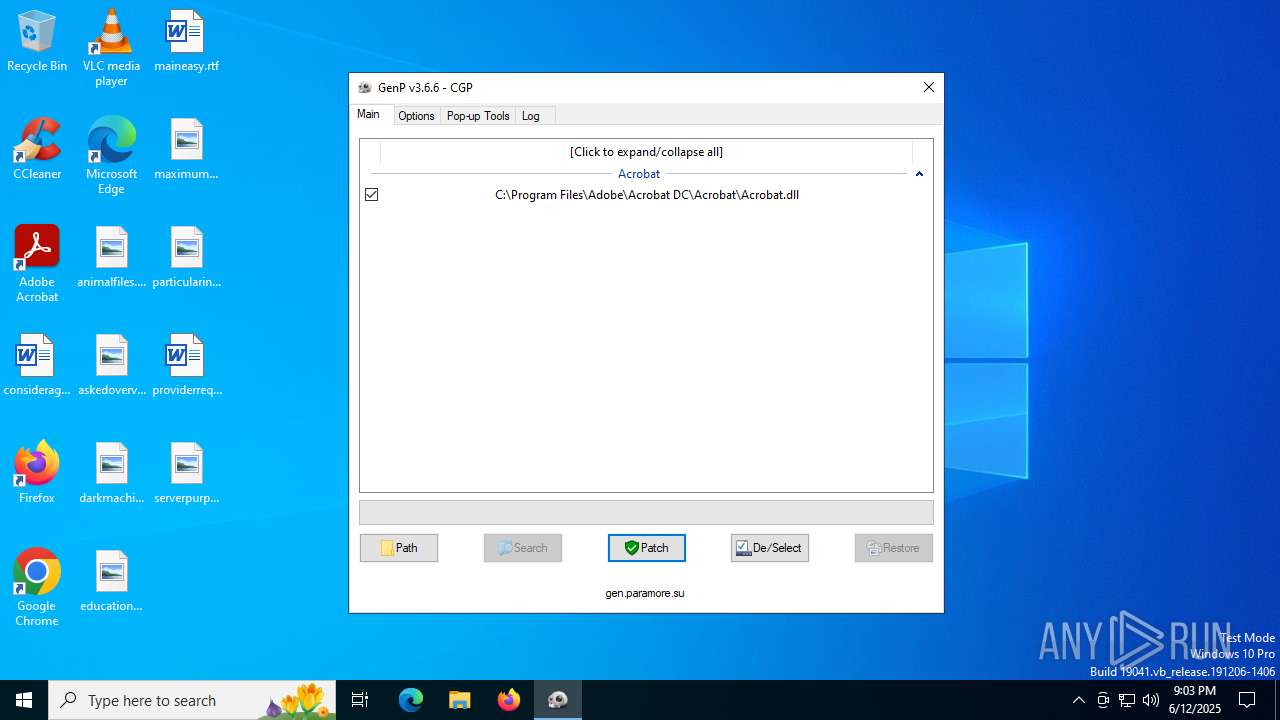
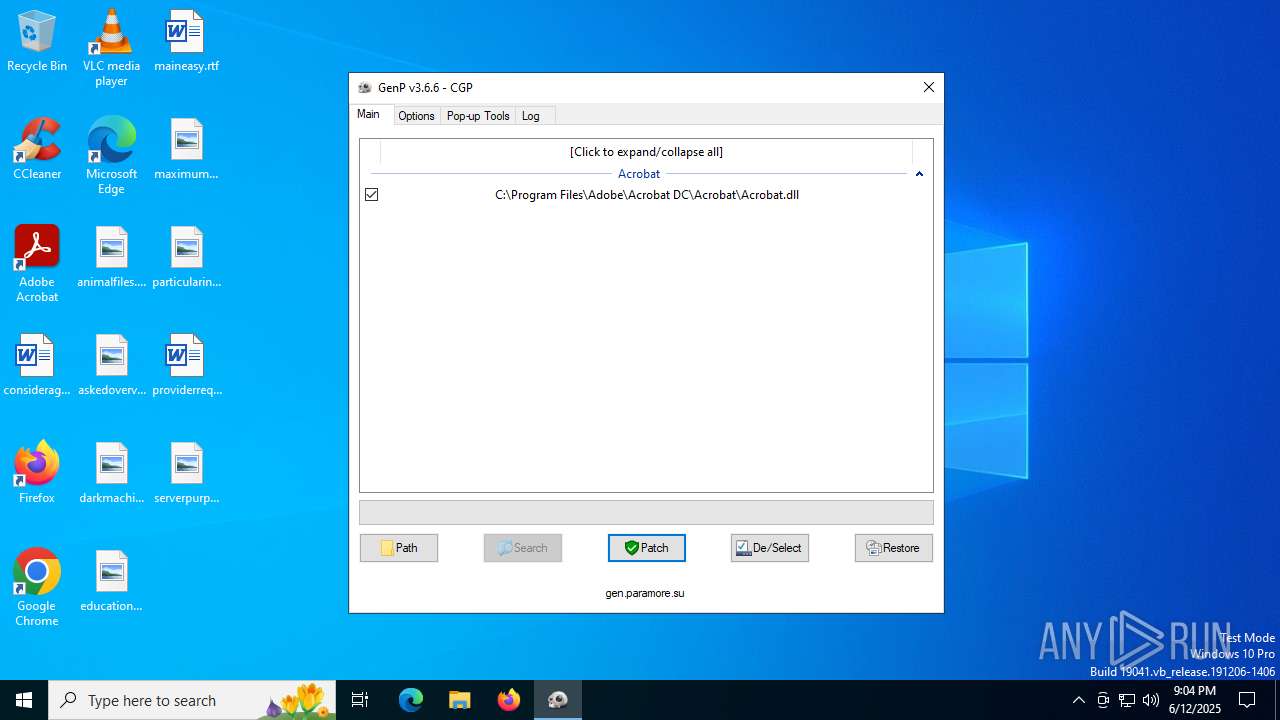
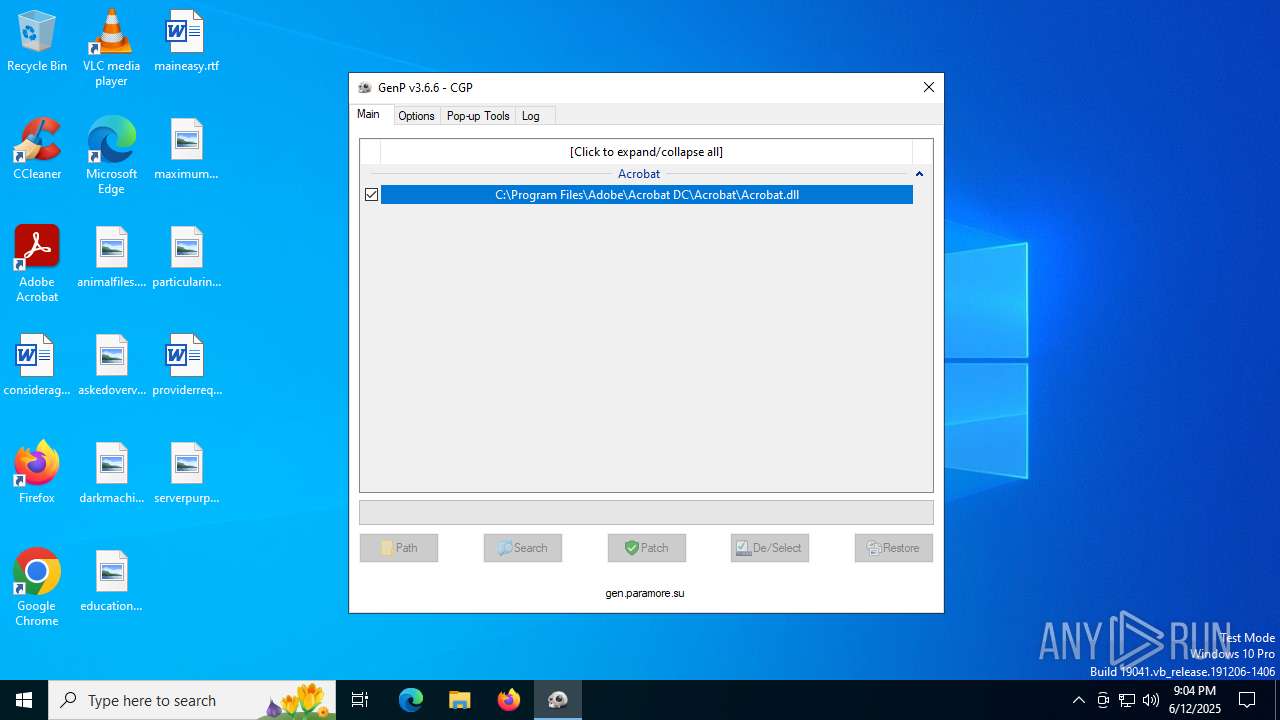
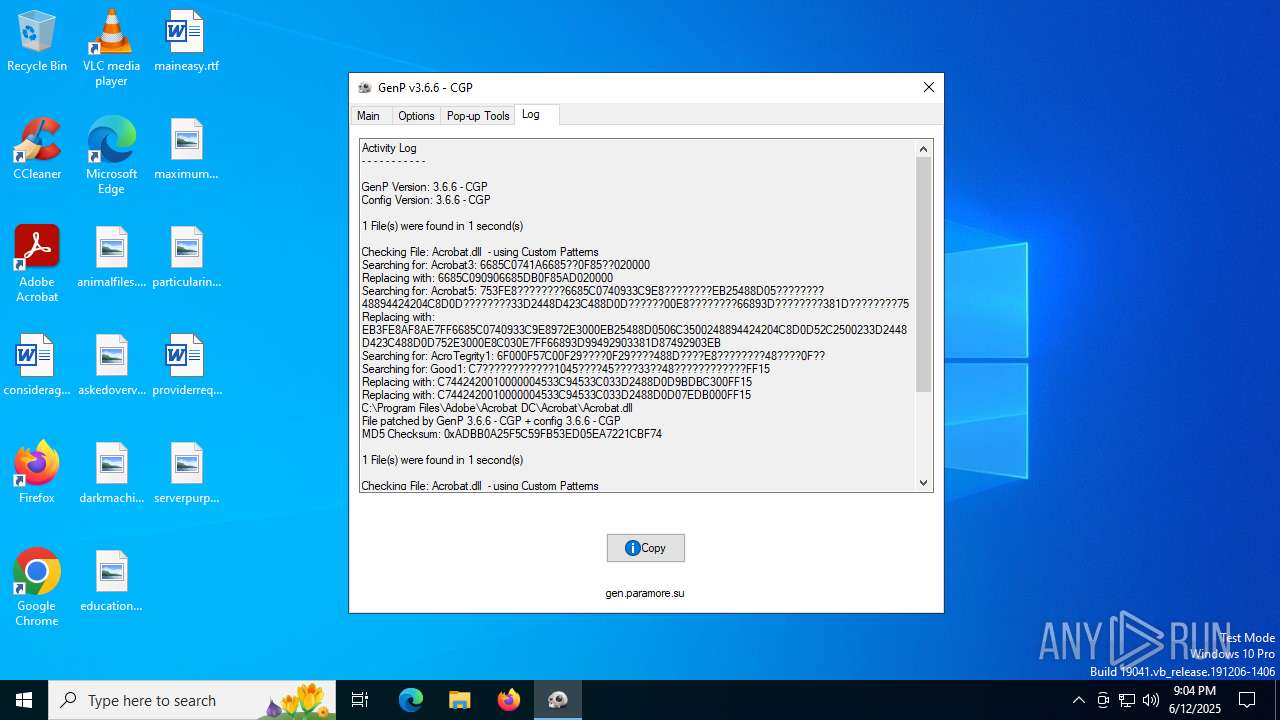
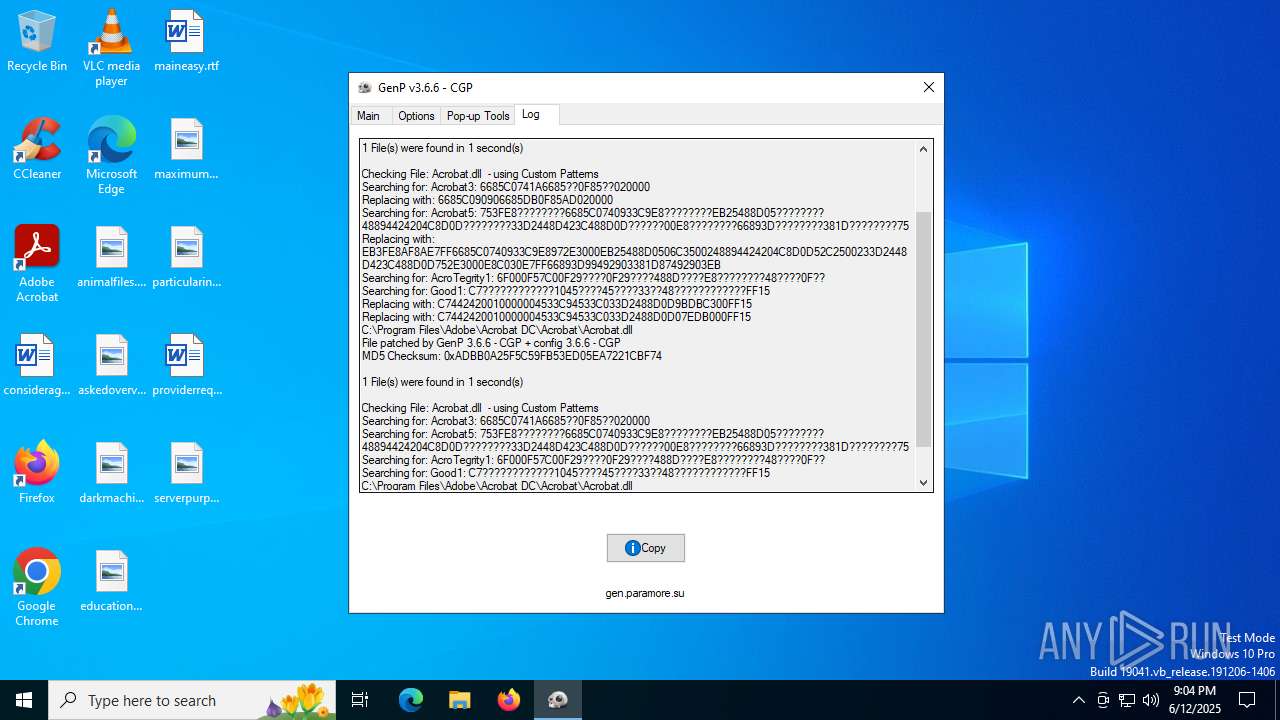
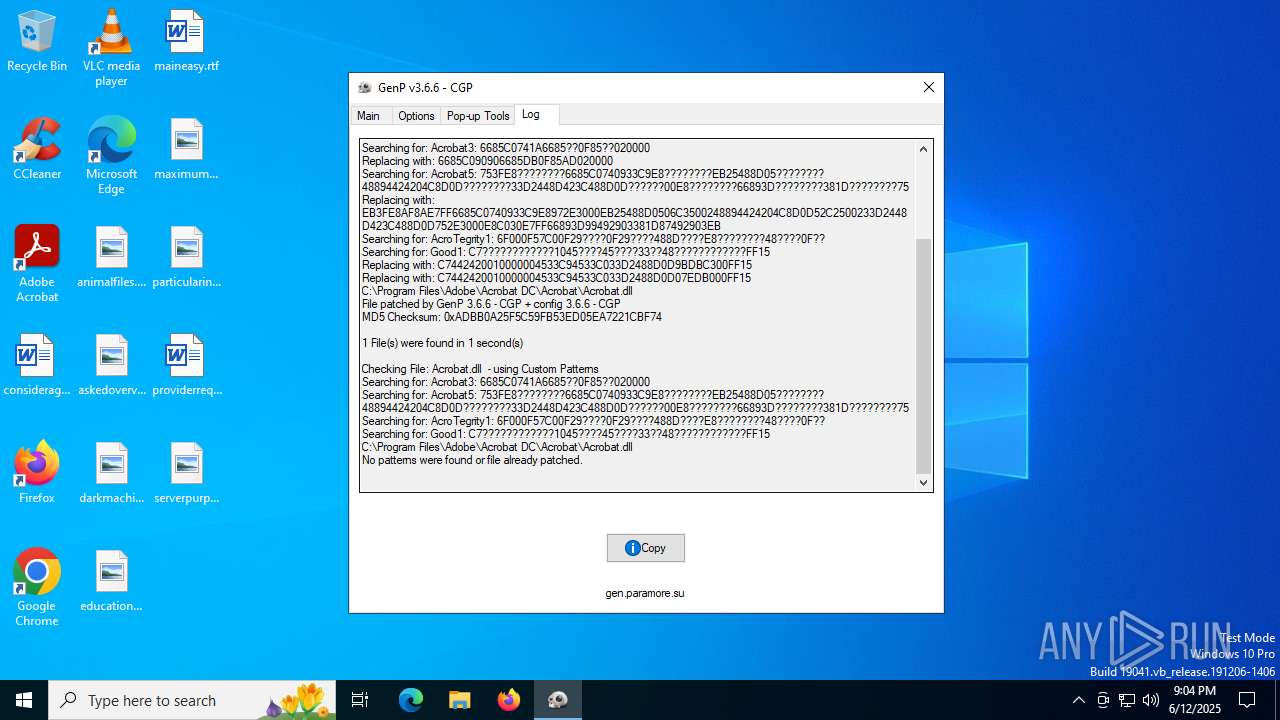
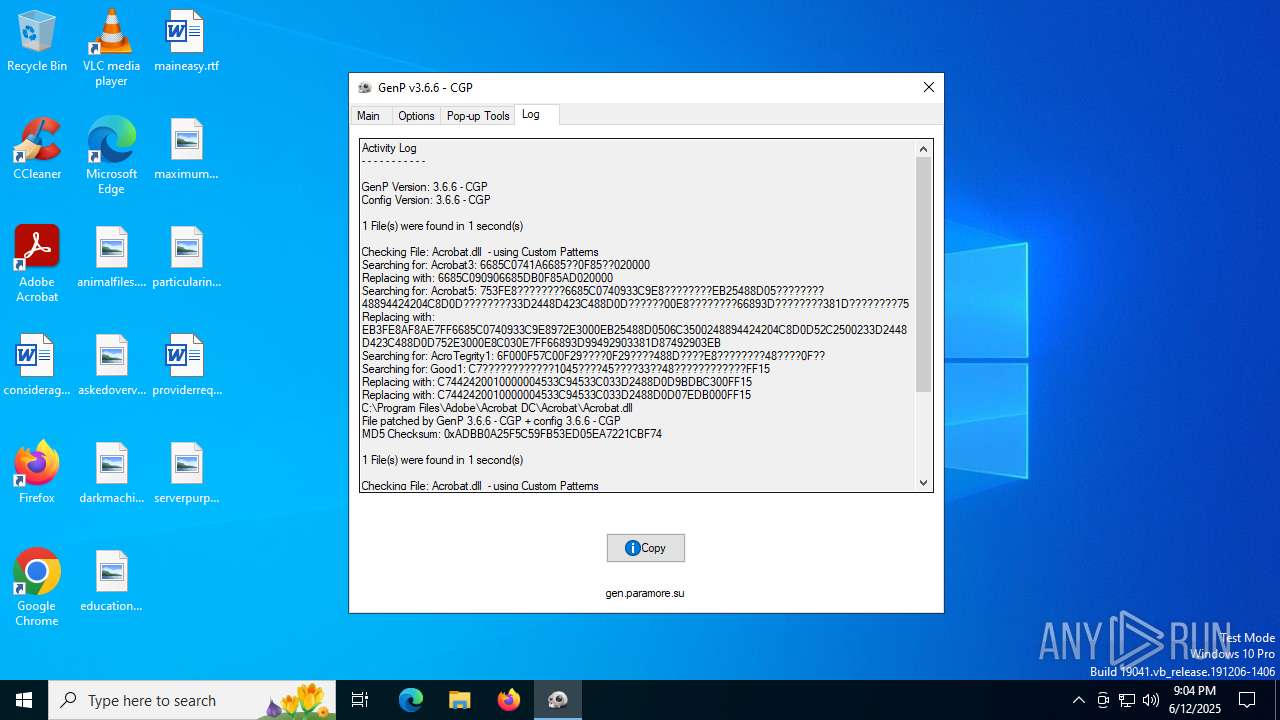
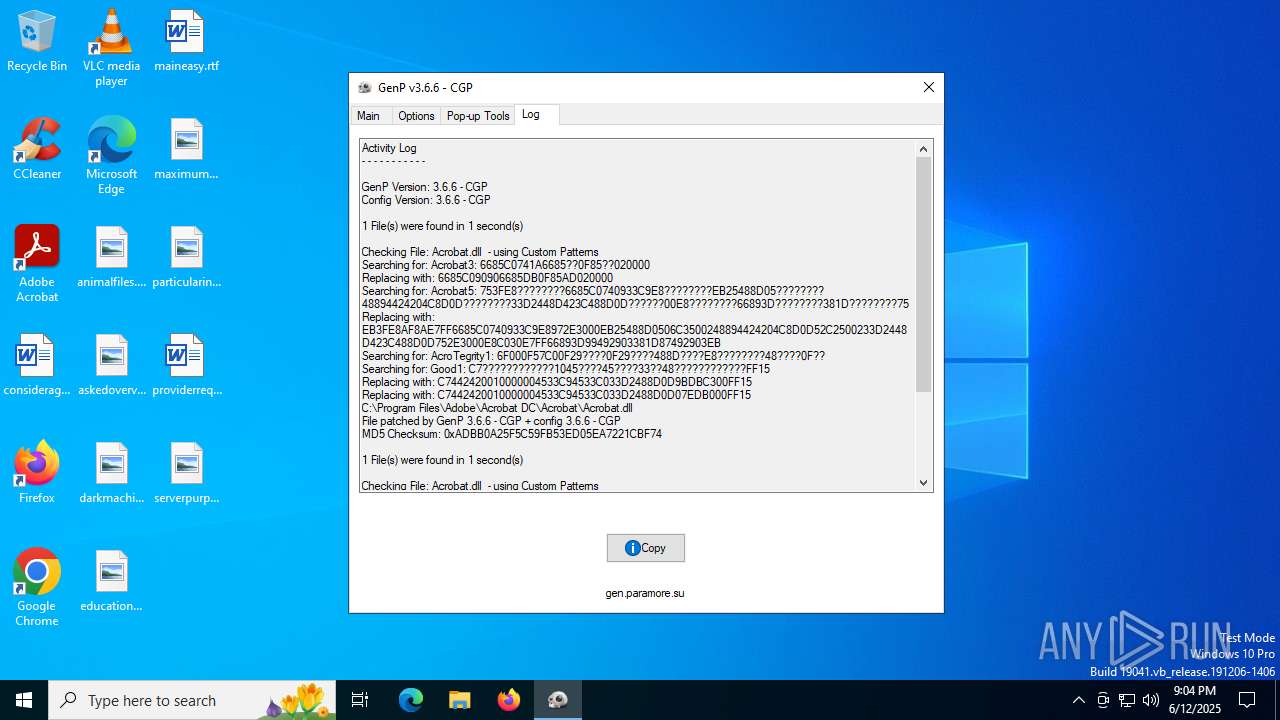
| 6364 | GenP-v3.6.6.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.dll.bak | — | |
MD5:— | SHA256:— | |||
| 6364 | GenP-v3.6.6.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.dll | — | |
MD5:— | SHA256:— | |||
| 6364 | GenP-v3.6.6.exe | C:\Users\admin\AppData\Local\Temp\config.ini | ini | |
MD5:A7BC5A7ADC2E89426BF18A6F1EC1AE4B | SHA256:35916985B869D72085BDB3D10B146D751631B10E4C61099EF339C3E72E2182F8 | |||
| 6364 | GenP-v3.6.6.exe | C:\Users\admin\AppData\Local\Temp\aut57E4.tmp | binary | |
MD5:77612C3BDBB4A29A03069936058257DC | SHA256:6D65555624E836950295587A300C0241859BB5AA1D576D083944F691C58FB35A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
23
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.48.23.183:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2464 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3636 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3636 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2348 | RUXIMICS.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
1268 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2336 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2464 | svchost.exe | 40.126.32.133:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2464 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 23.48.23.183:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |