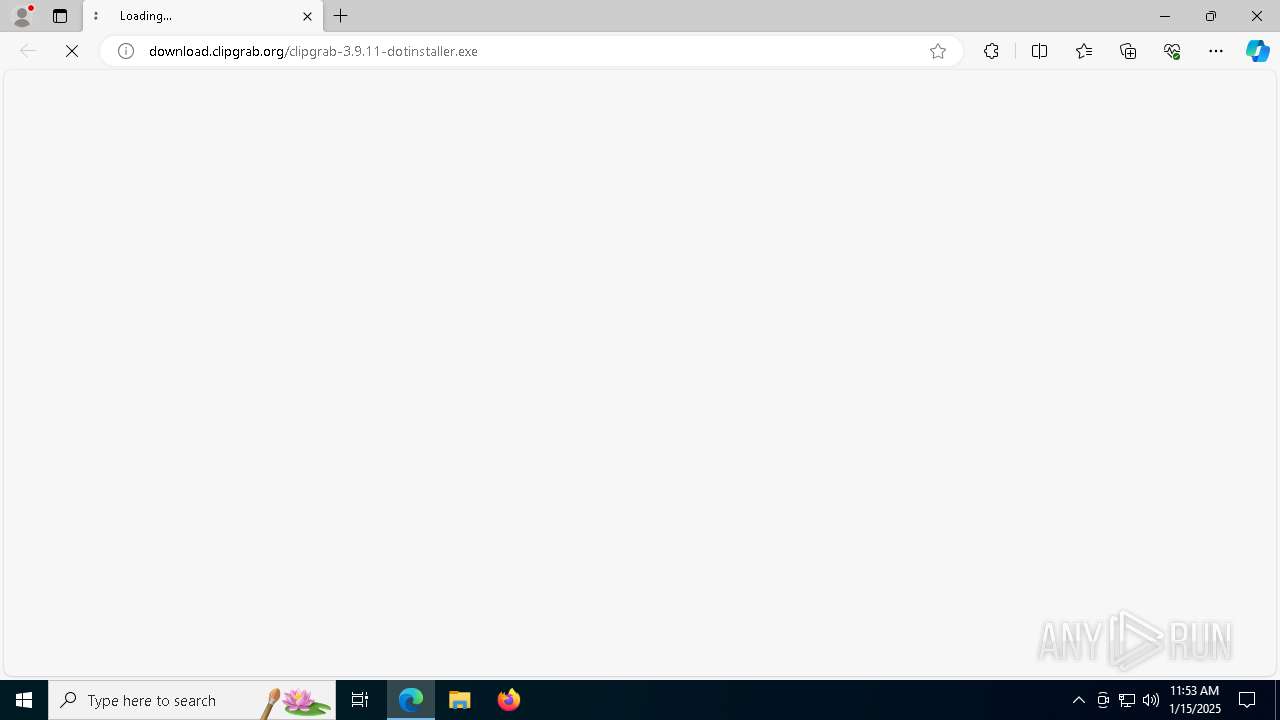
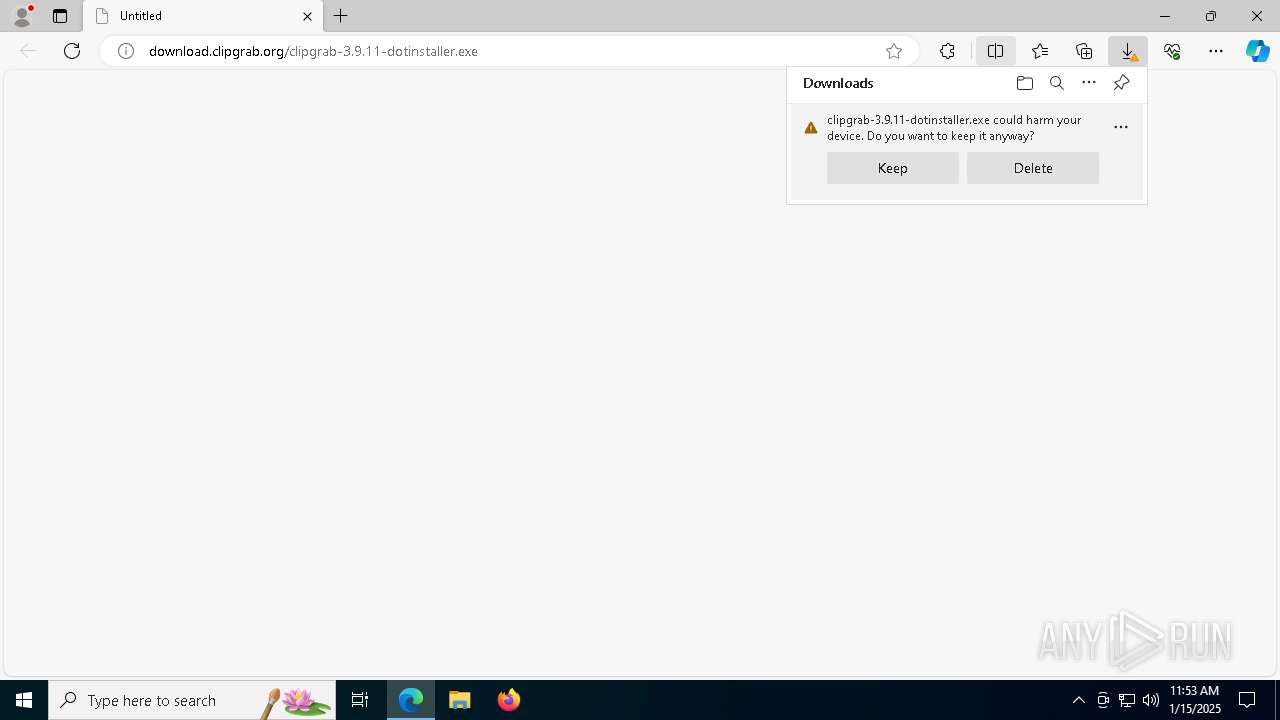
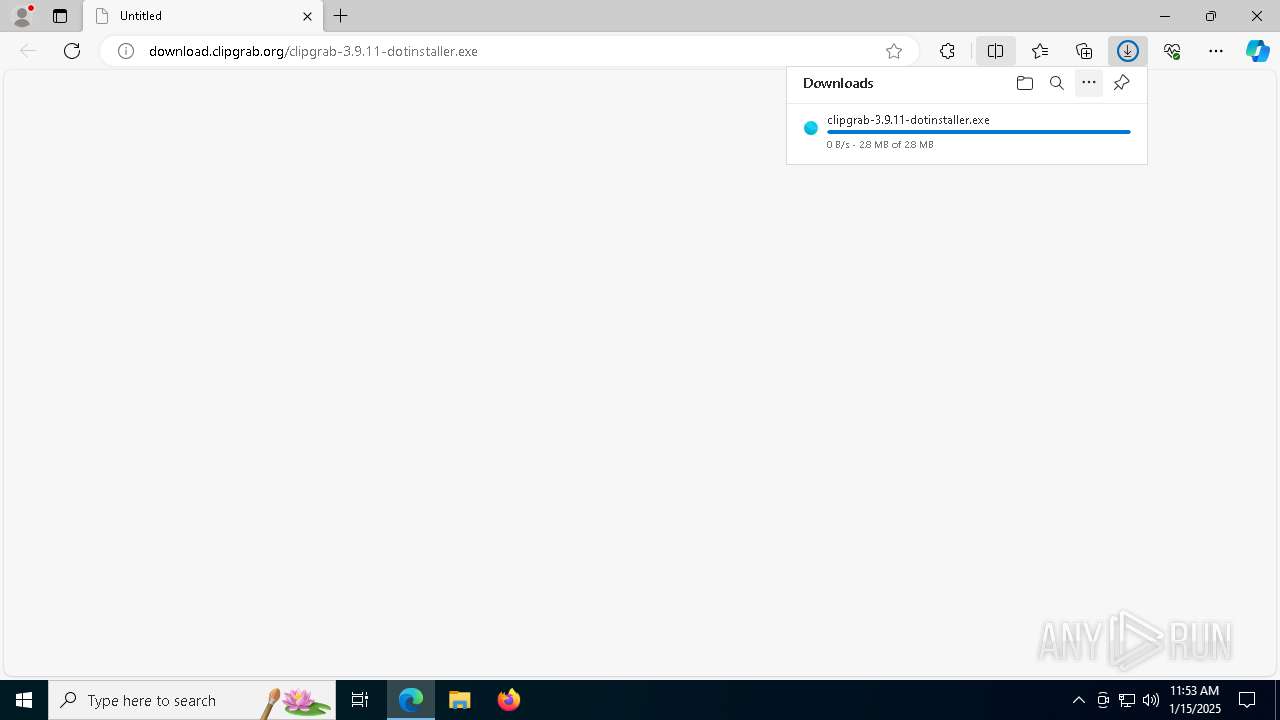
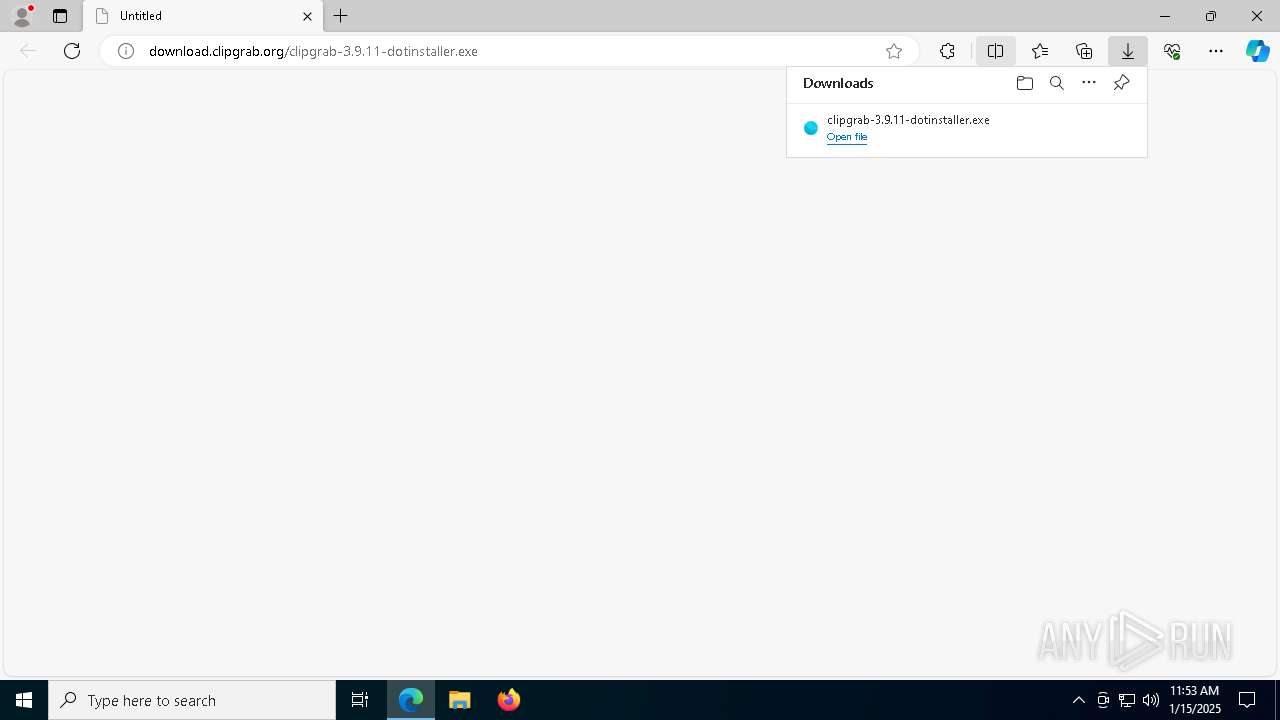
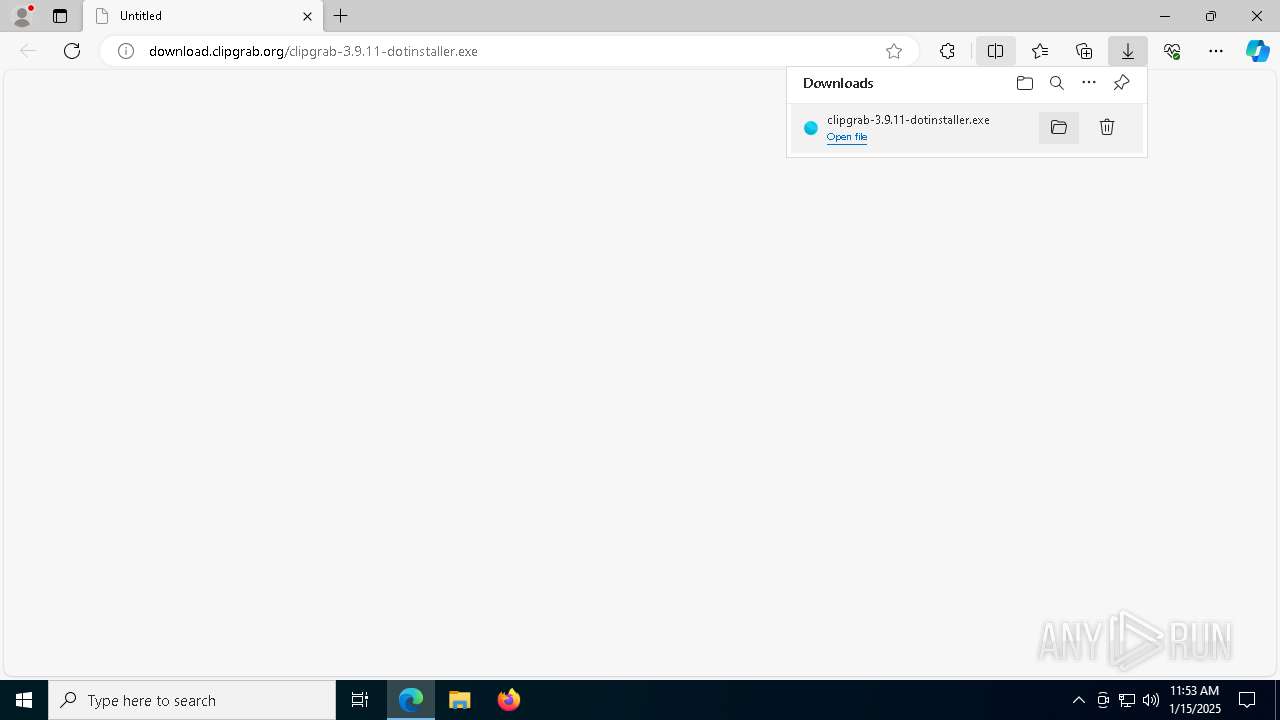
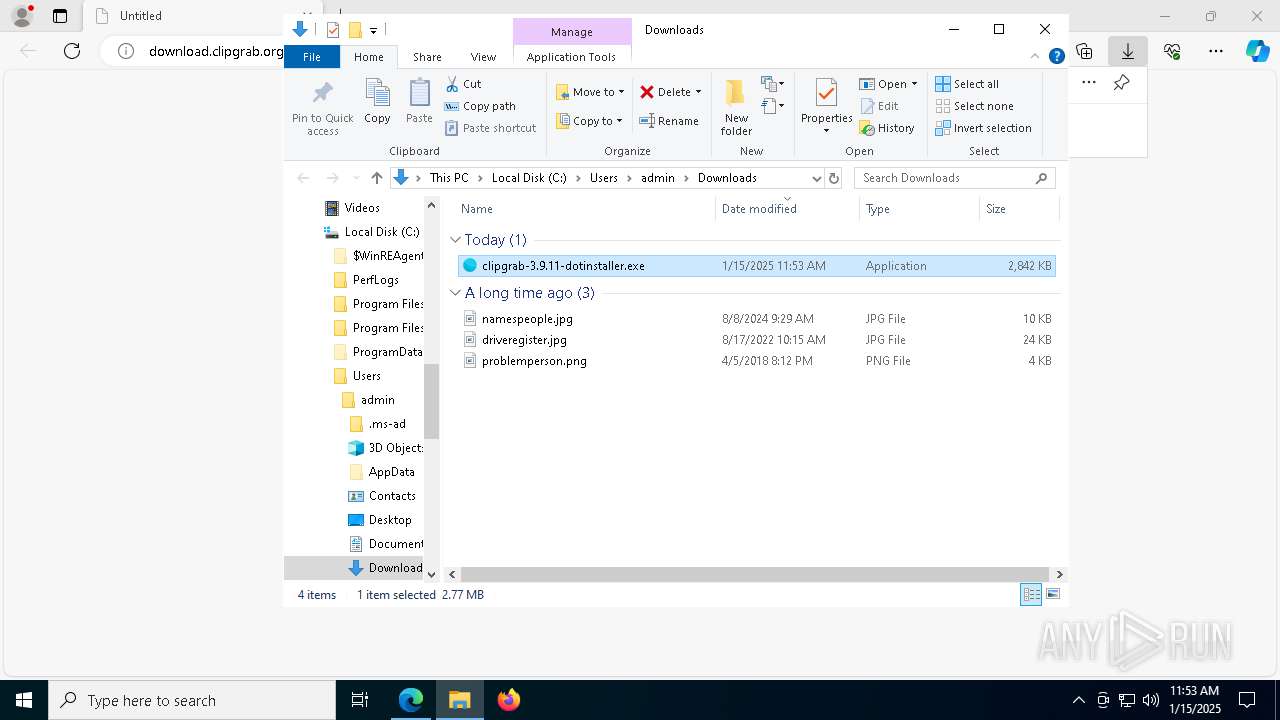
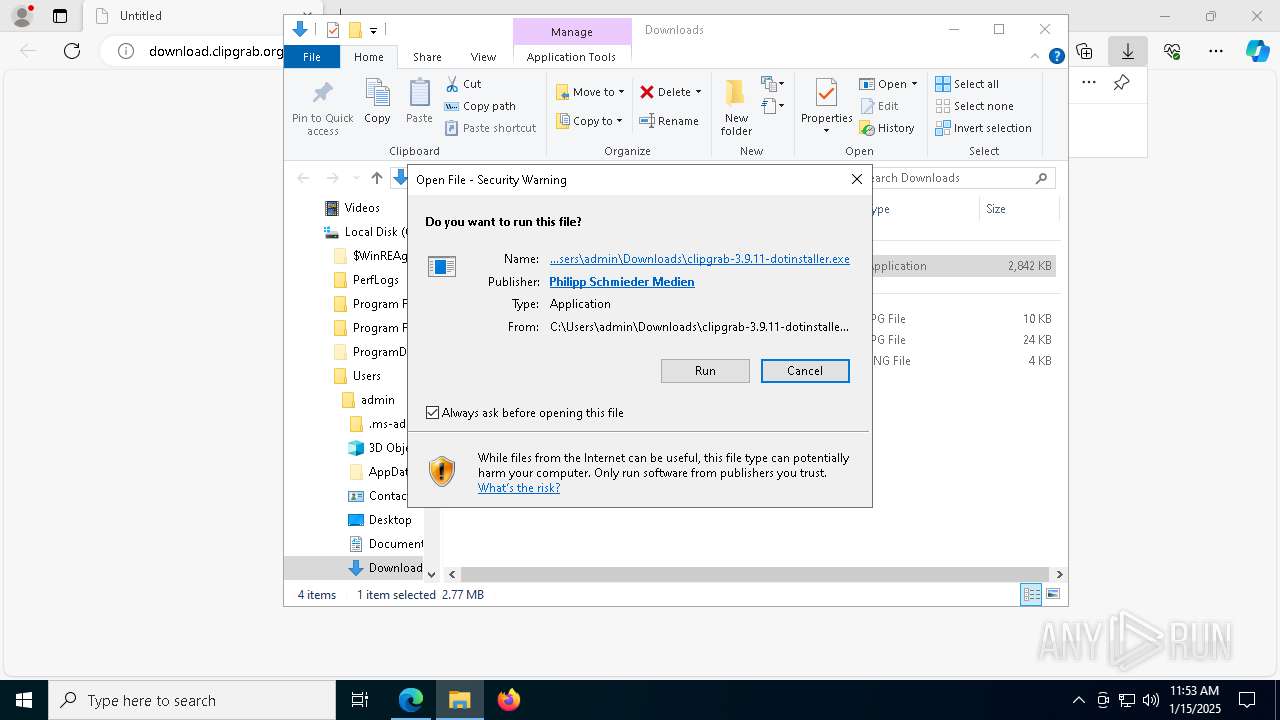
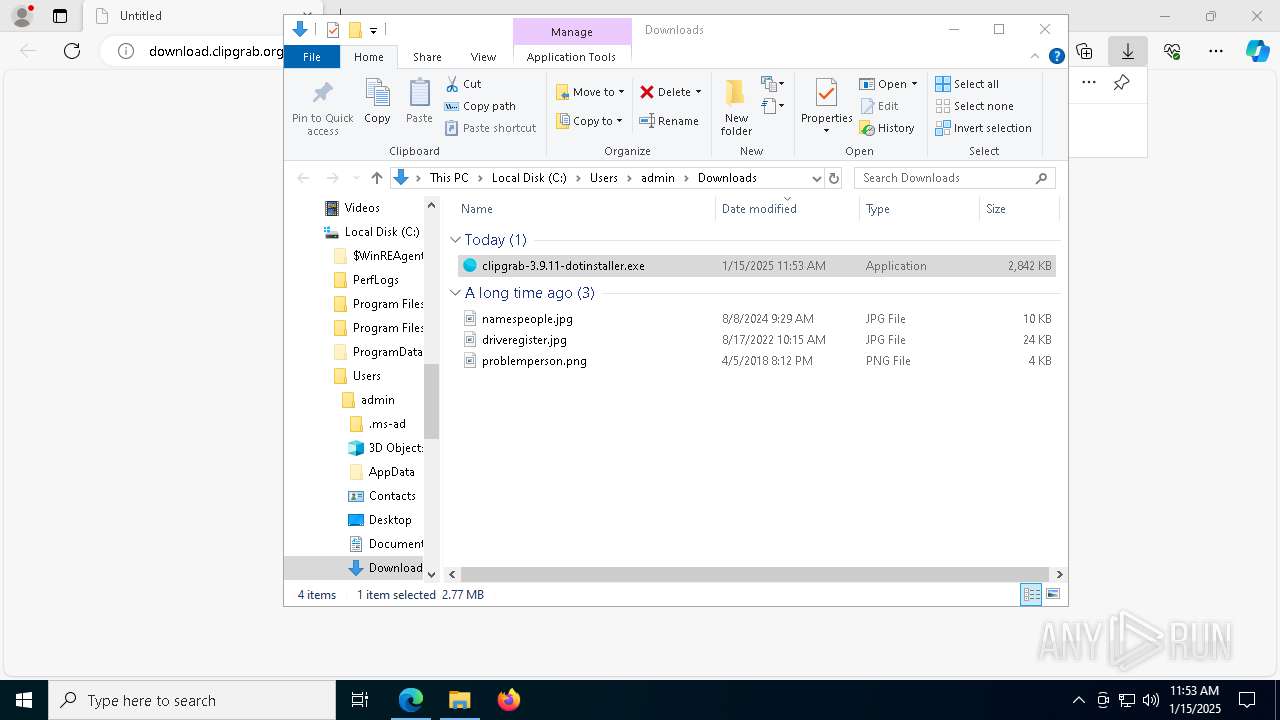
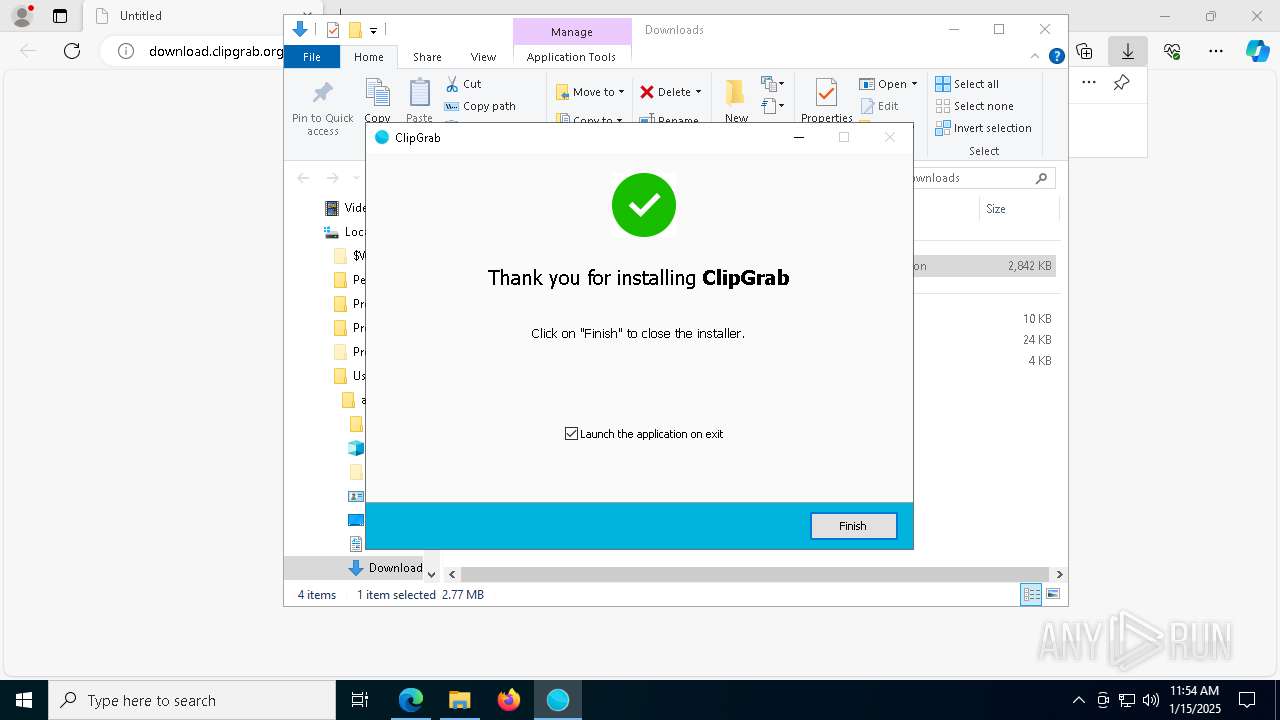
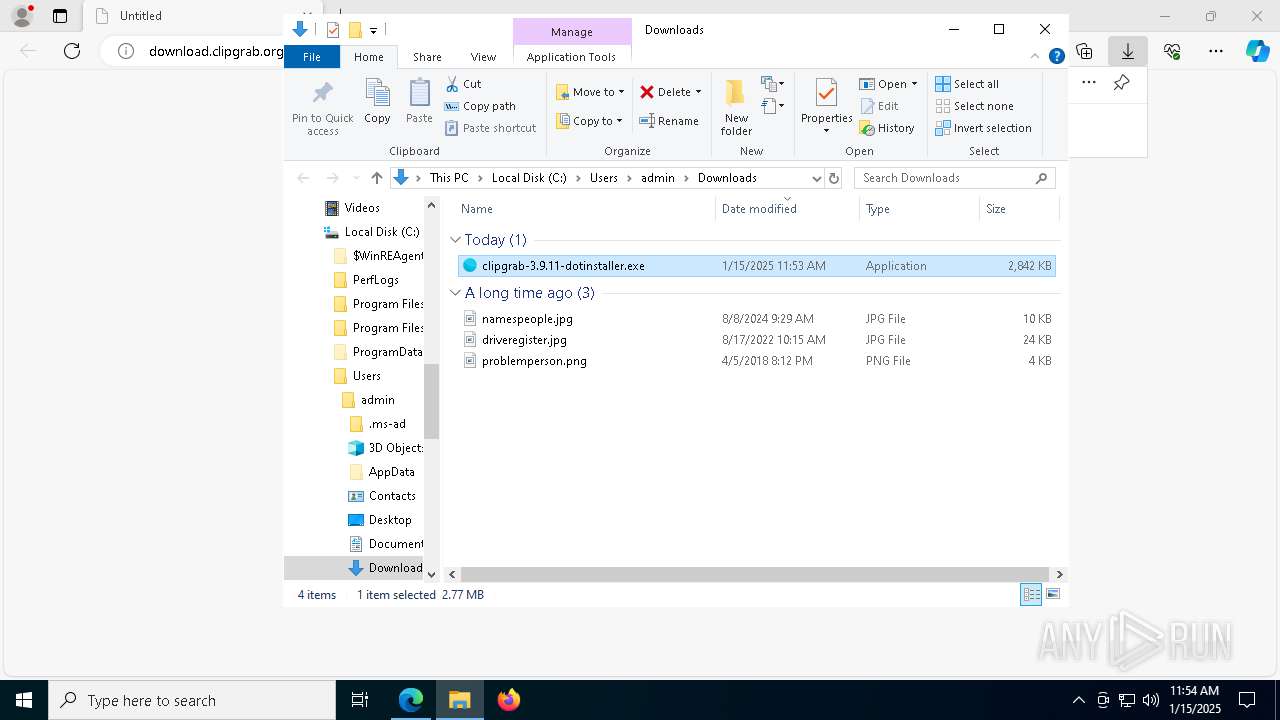
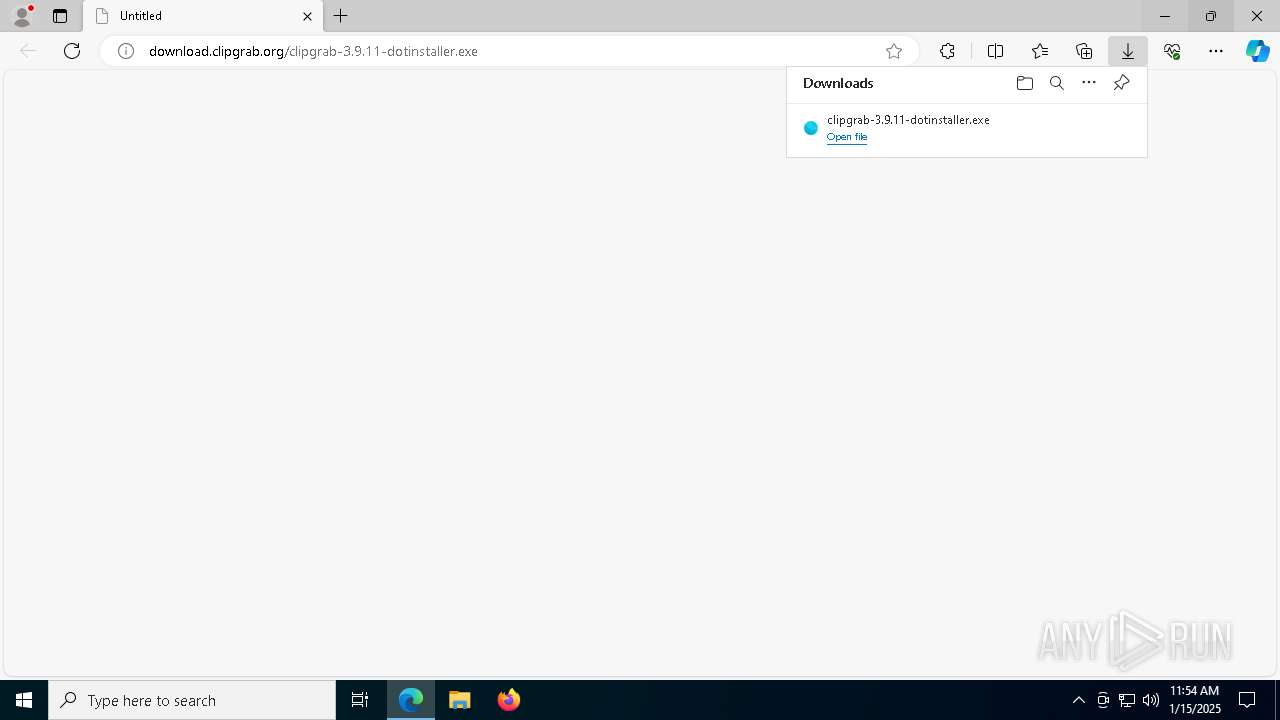
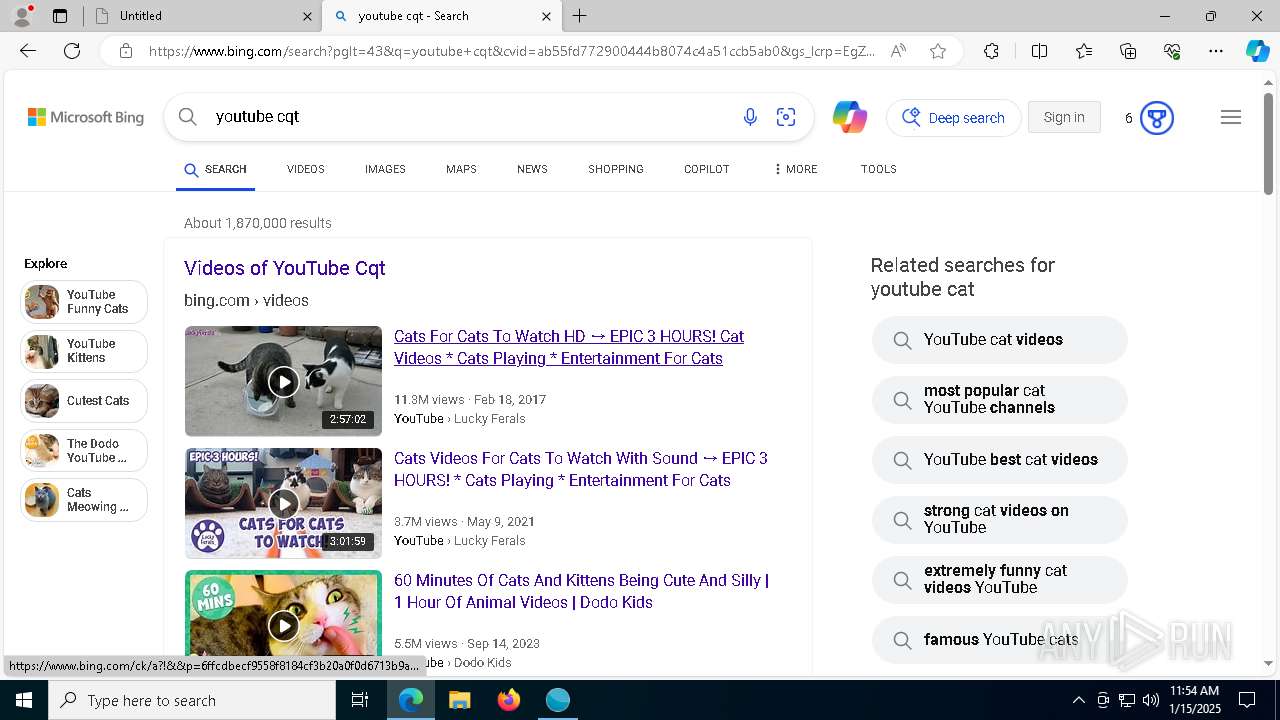
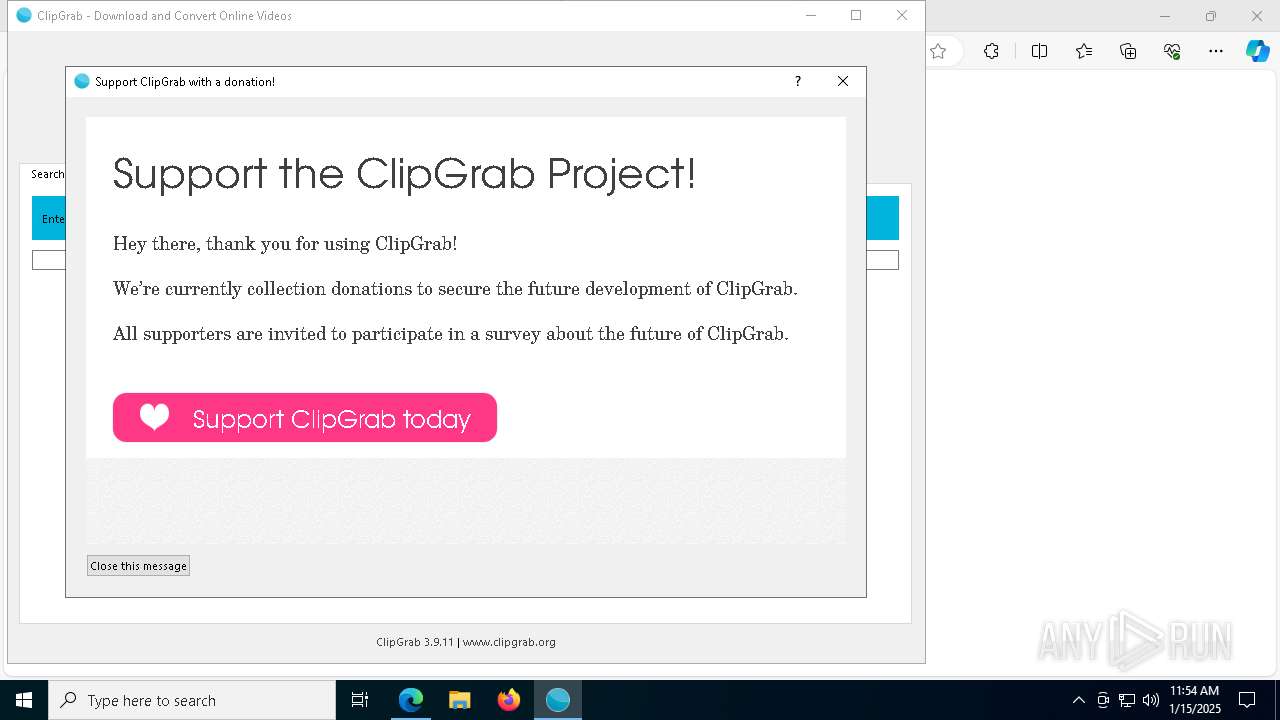
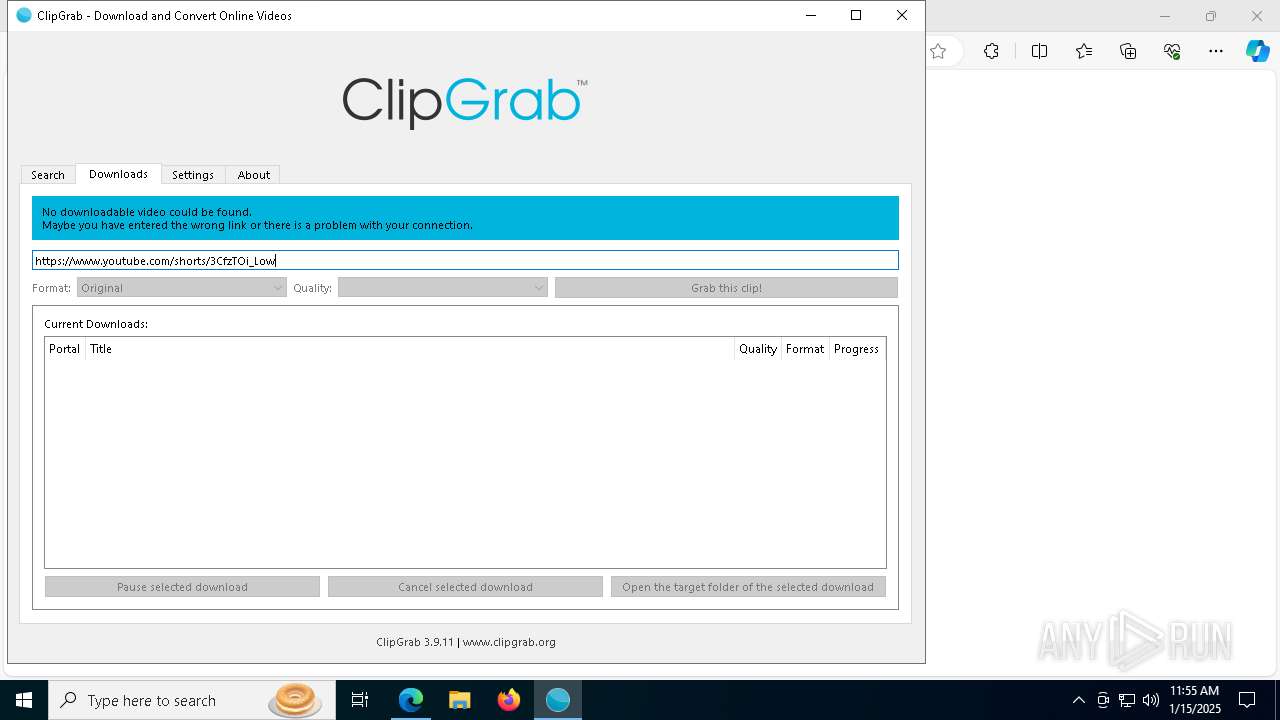
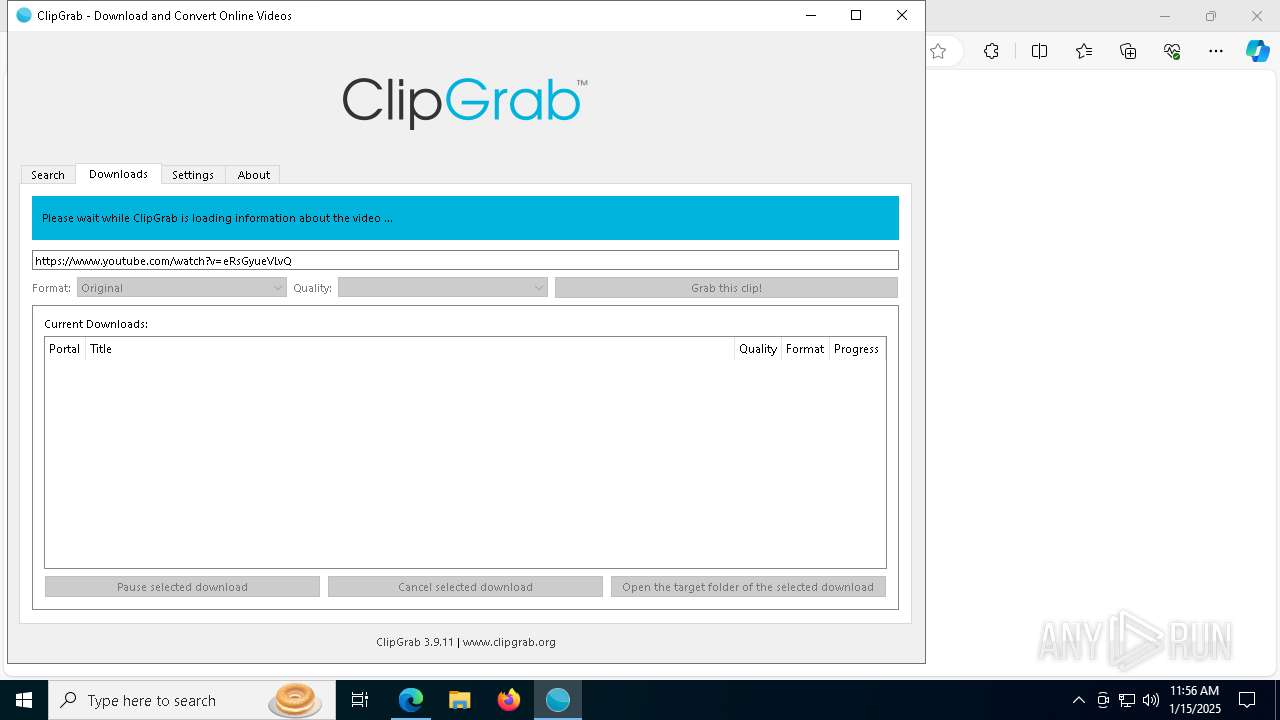
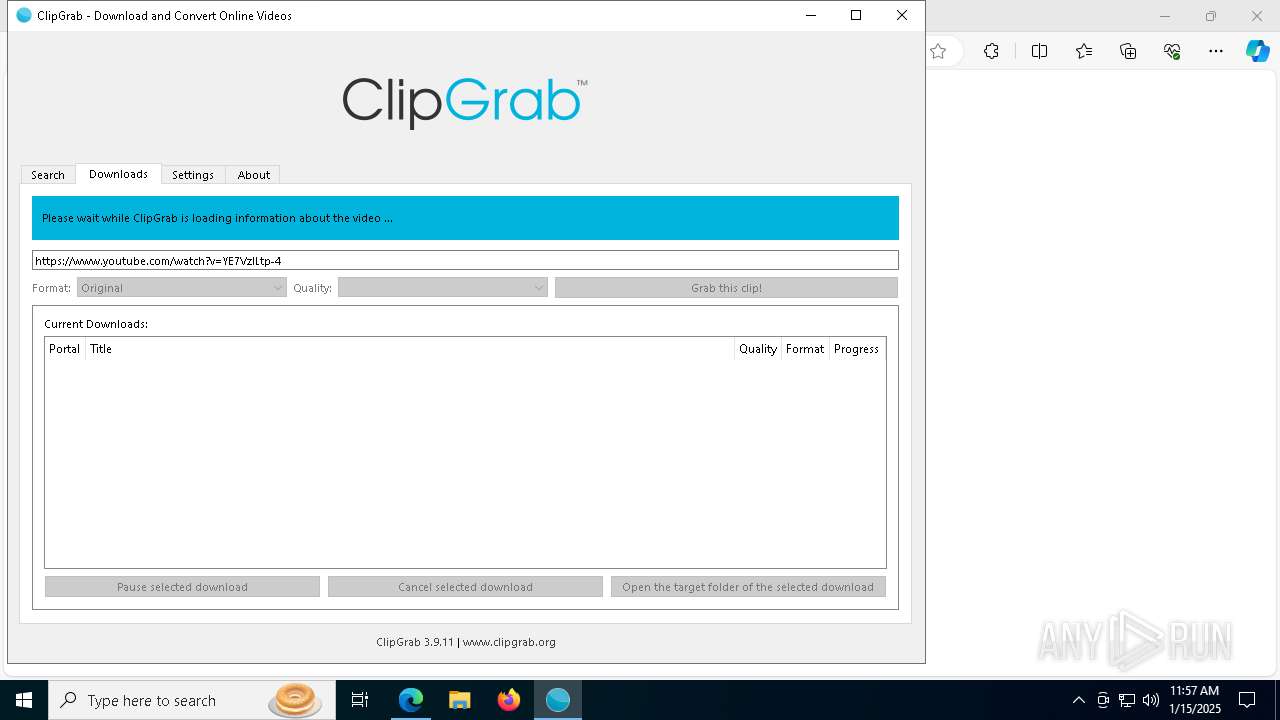
| URL: | download.clipgrab.org/clipgrab-3.9.11-dotinstaller.exe |
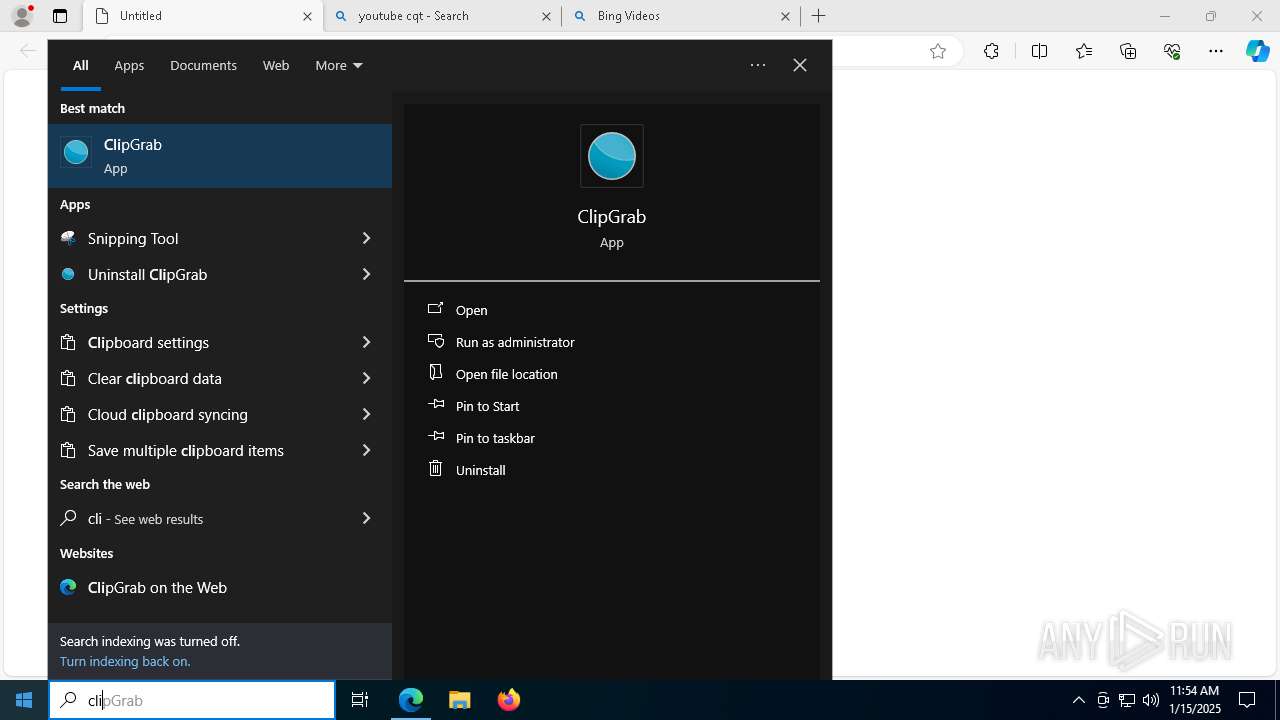
| Full analysis: | https://app.any.run/tasks/0ae39c81-da63-45c0-95ce-37da7946469f |
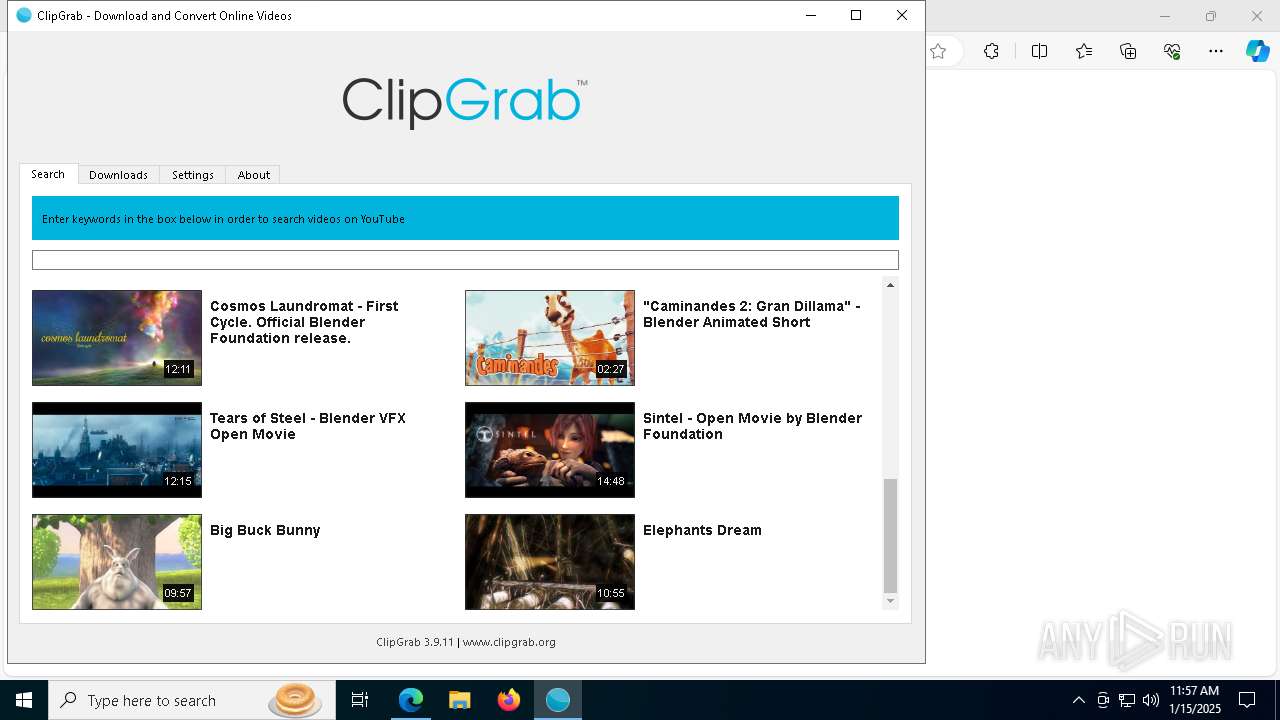
| Verdict: | Malicious activity |
| Analysis date: | January 15, 2025, 11:52:55 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | B42215CA6B0294FE4F6933C4D35C082D |
| SHA1: | 5E5650C6F4414761B5DD3468F4294CB3FA30CBCC |
| SHA256: | 1DC569FACFBA30BFB61772D70123D649EB523F4E4DDC03D42B155F8E7C4B2B2A |
| SSDEEP: | 3:ZKWTAfCc6UUbRNqOXLNn:ZlUfxyNqOXLN |
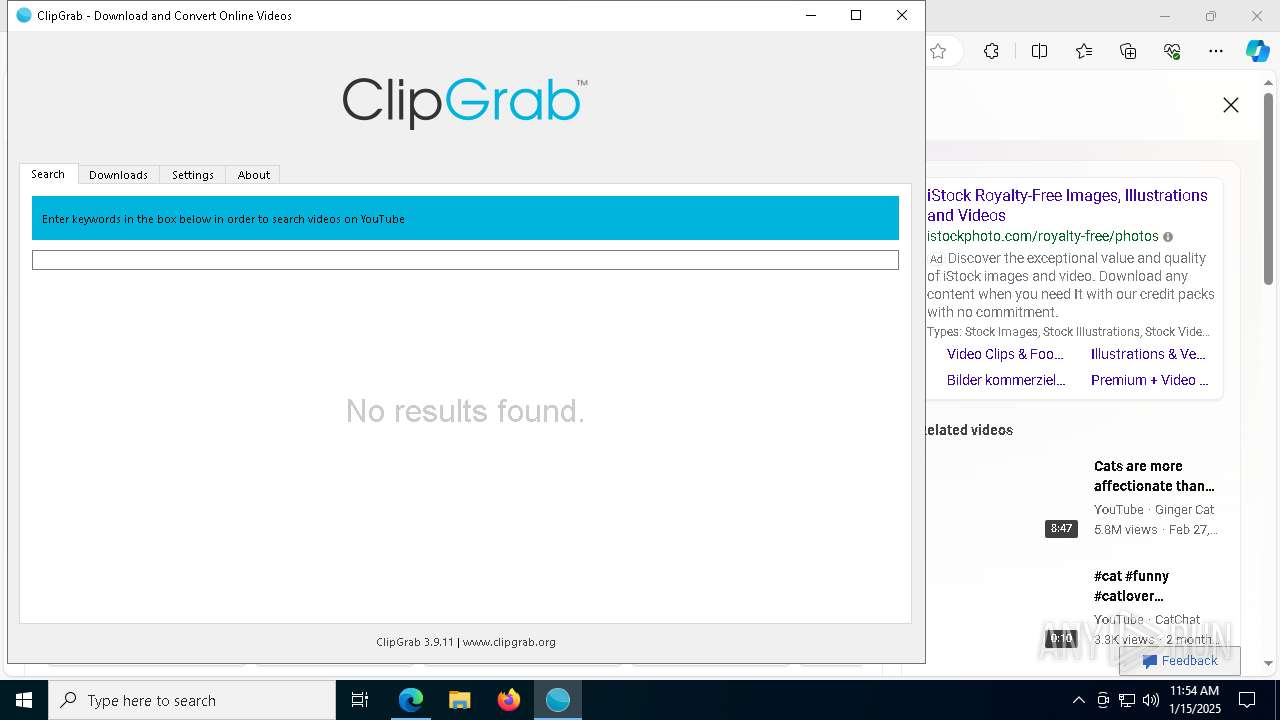
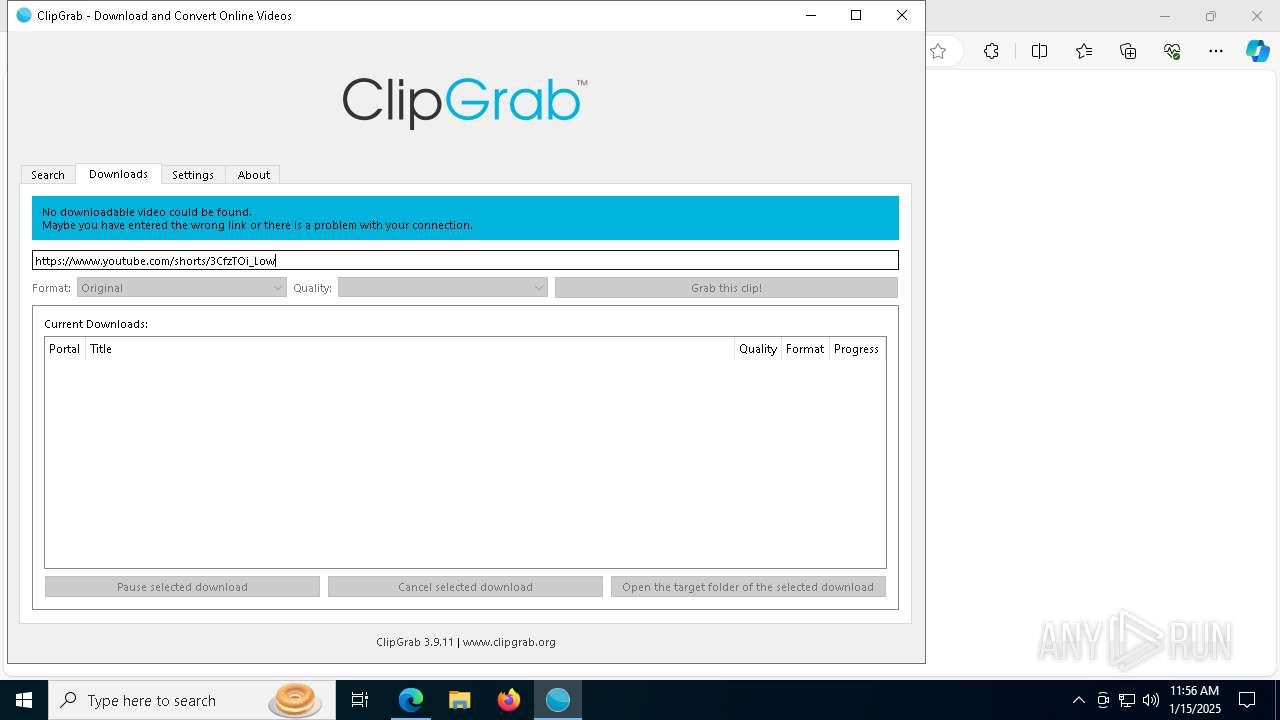
MALICIOUS
Executing a file with an untrusted certificate
- QtWebEngineProcess.exe (PID: 1760)
SUSPICIOUS
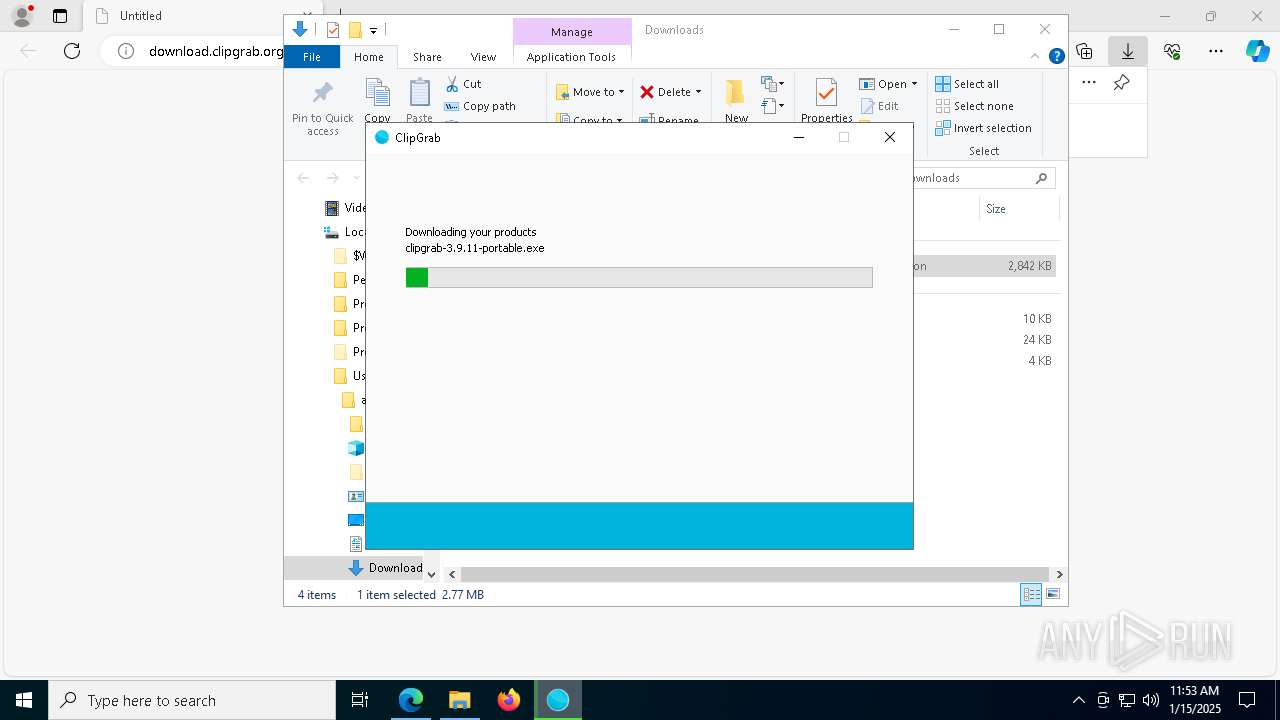
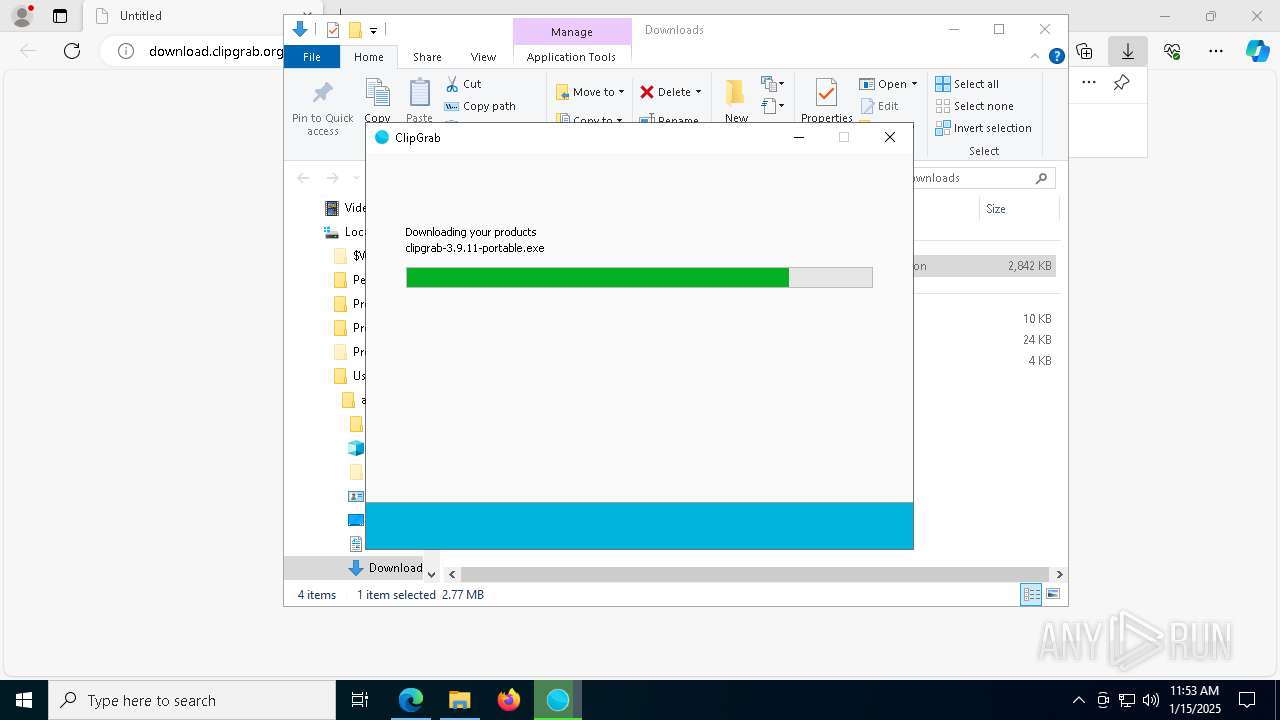
Executable content was dropped or overwritten
- clipgrab-3.9.11-dotinstaller.exe (PID: 2212)
- clipgrab-3.9.11-dotinstaller.exe (PID: 4052)
- clipgrab-3.9.11-portable.exe (PID: 7208)
- clipgrab-3.9.11-portable.tmp (PID: 3296)
- clipgrab-3.9.11-dotinstaller.tmp (PID: 7412)
- vc_redist.x86.exe (PID: 3912)
- vc_redist.x86.exe (PID: 4528)
Reads security settings of Internet Explorer
- clipgrab-3.9.11-dotinstaller.tmp (PID: 3988)
Creates file in the systems drive root
- explorer.exe (PID: 4488)
Reads the Windows owner or organization settings
- clipgrab-3.9.11-dotinstaller.tmp (PID: 7412)
Process drops legitimate windows executable
- clipgrab-3.9.11-portable.tmp (PID: 3296)
- vc_redist.x86.exe (PID: 3912)
Process drops python dynamic module
- clipgrab-3.9.11-portable.tmp (PID: 3296)
The process drops C-runtime libraries
- clipgrab-3.9.11-portable.tmp (PID: 3296)
Starts a Microsoft application from unusual location
- vc_redist.x86.exe (PID: 3912)
- vc_redist.x86.exe (PID: 4528)
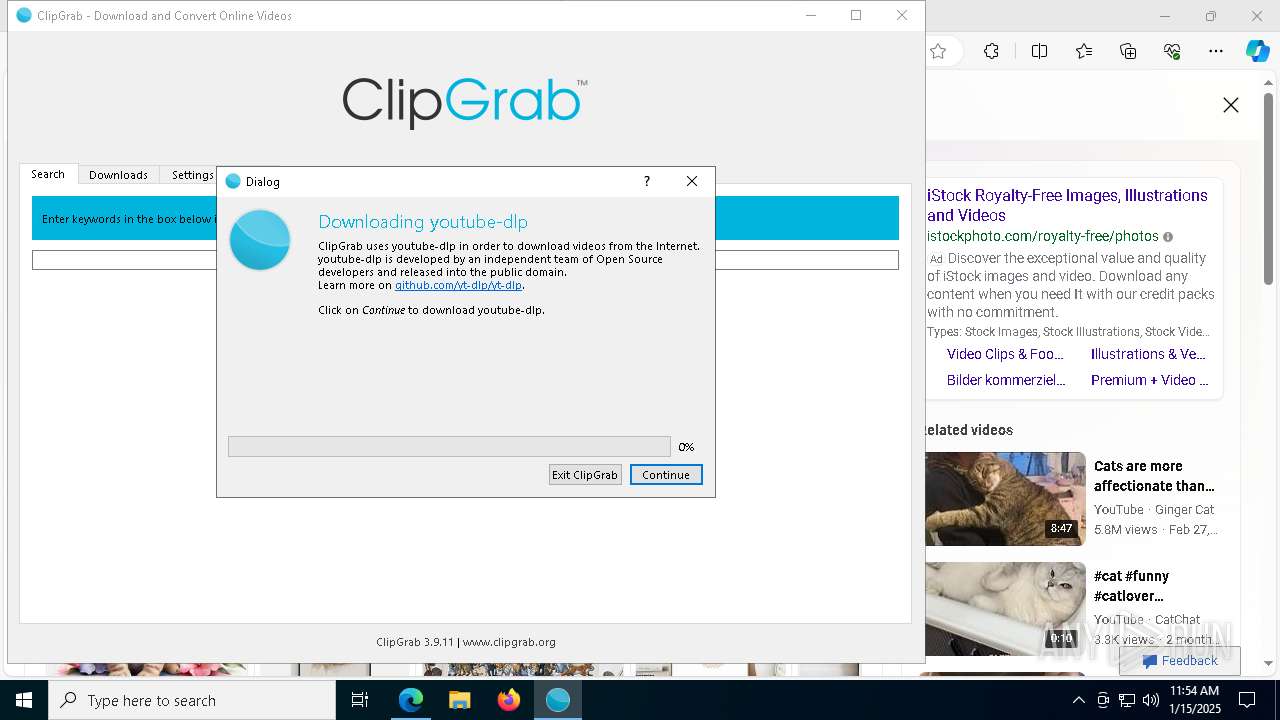
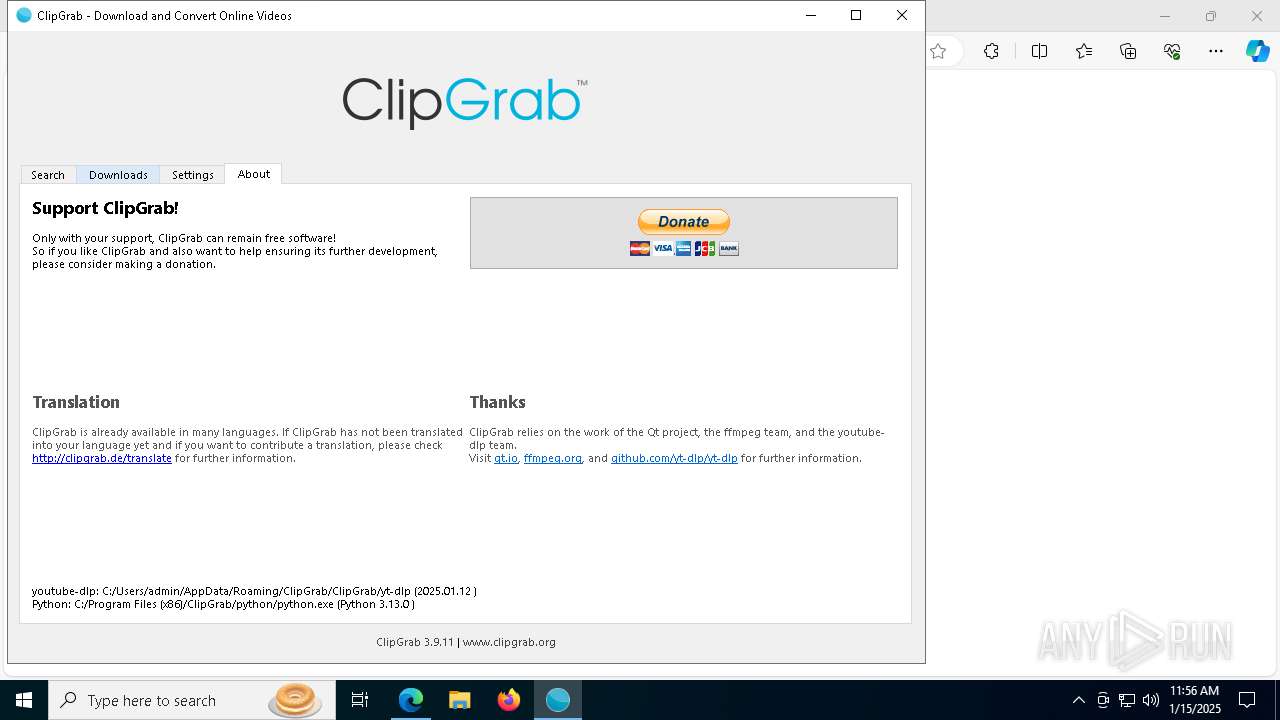
Loads Python modules
- python.exe (PID: 6464)
- python.exe (PID: 716)
- python.exe (PID: 7292)
- python.exe (PID: 7220)
- python.exe (PID: 6472)
- python.exe (PID: 1540)
- python.exe (PID: 2788)
- python.exe (PID: 7280)
- python.exe (PID: 5788)
- python.exe (PID: 5304)
- python.exe (PID: 4228)
- python.exe (PID: 4304)
- python.exe (PID: 2152)
- python.exe (PID: 5496)
- python.exe (PID: 5880)
- python.exe (PID: 1796)
- python.exe (PID: 7620)
- python.exe (PID: 3436)
- python.exe (PID: 2220)
- python.exe (PID: 7416)
Starts CMD.EXE for commands execution
- python.exe (PID: 6660)
INFO
Application launched itself
- msedge.exe (PID: 6512)
Reads the computer name
- clipgrab-3.9.11-dotinstaller.tmp (PID: 3988)
- identity_helper.exe (PID: 7756)
- clipgrab-3.9.11-portable.tmp (PID: 3296)
- clipgrab-3.9.11-dotinstaller.tmp (PID: 7412)
- clipgrab.exe (PID: 640)
- clipgrab.exe (PID: 1576)
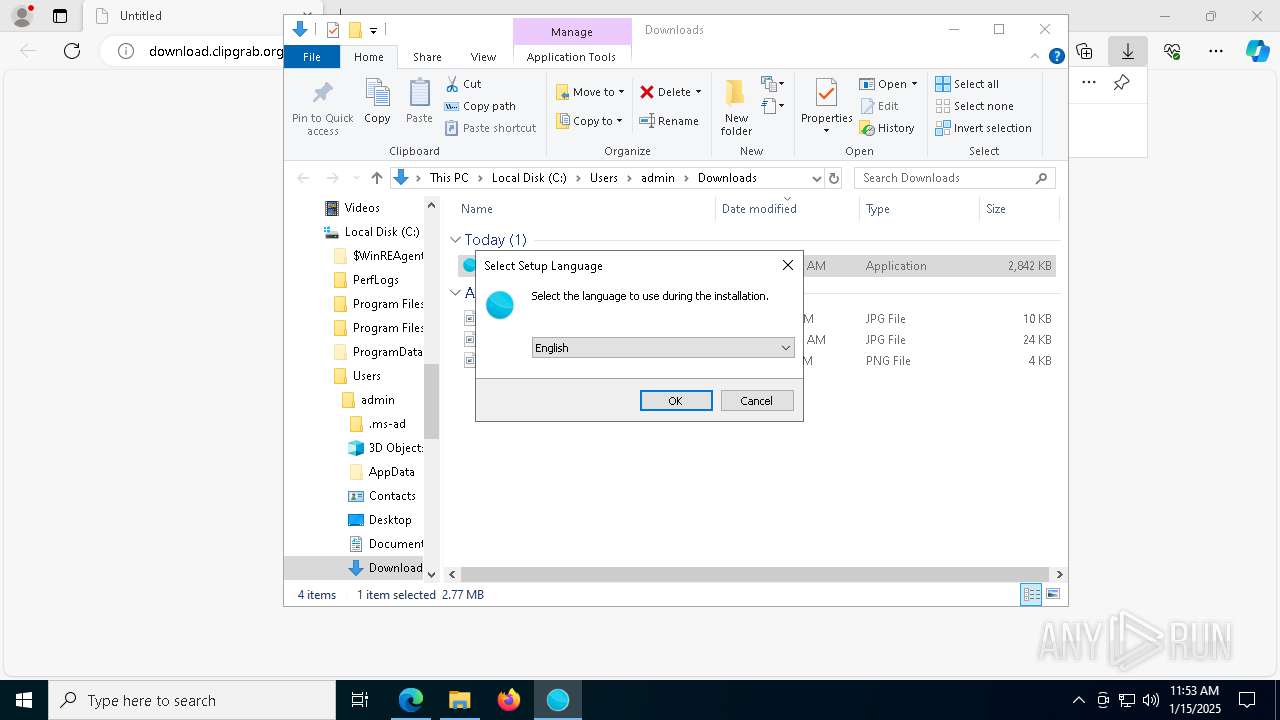
Checks supported languages
- clipgrab-3.9.11-dotinstaller.exe (PID: 2212)
- clipgrab-3.9.11-dotinstaller.tmp (PID: 3988)
- clipgrab-3.9.11-dotinstaller.exe (PID: 4052)
- identity_helper.exe (PID: 7756)
- clipgrab-3.9.11-dotinstaller.tmp (PID: 7412)
- clipgrab-3.9.11-portable.tmp (PID: 3296)
- clipgrab-3.9.11-portable.exe (PID: 7208)
- vc_redist.x86.exe (PID: 3912)
- clipgrab.exe (PID: 640)
- ffmpeg.exe (PID: 1512)
- ffmpeg.exe (PID: 6644)
- python.exe (PID: 7292)
- python.exe (PID: 7220)
- python.exe (PID: 6472)
- python.exe (PID: 2788)
- python.exe (PID: 5788)
- python.exe (PID: 5304)
- python.exe (PID: 4228)
- python.exe (PID: 4304)
- QtWebEngineProcess.exe (PID: 1760)
- QtWebEngineProcess.exe (PID: 7524)
- QtWebEngineProcess.exe (PID: 7456)
- python.exe (PID: 5880)
- python.exe (PID: 5496)
- python.exe (PID: 1796)
- clipgrab.exe (PID: 1576)
- ffmpeg.exe (PID: 4228)
- ffmpeg.exe (PID: 8164)
- python.exe (PID: 2220)
- python.exe (PID: 7416)
- python.exe (PID: 8152)
- python.exe (PID: 4024)
- python.exe (PID: 4944)
- python.exe (PID: 4544)
- QtWebEngineProcess.exe (PID: 6508)
- QtWebEngineProcess.exe (PID: 1488)
- QtWebEngineProcess.exe (PID: 5720)
- QtWebEngineProcess.exe (PID: 5464)
- QtWebEngineProcess.exe (PID: 2280)
- python.exe (PID: 4504)
Create files in a temporary directory
- clipgrab-3.9.11-dotinstaller.exe (PID: 2212)
- clipgrab-3.9.11-dotinstaller.exe (PID: 4052)
- clipgrab-3.9.11-dotinstaller.tmp (PID: 7412)
- clipgrab-3.9.11-portable.tmp (PID: 3296)
Process checks computer location settings
- clipgrab-3.9.11-dotinstaller.tmp (PID: 3988)
Executable content was dropped or overwritten
- msedge.exe (PID: 6744)
- msedge.exe (PID: 6512)
Reads Environment values
- identity_helper.exe (PID: 7756)
The process uses the downloaded file
- explorer.exe (PID: 4488)
Reads the software policy settings
- clipgrab-3.9.11-dotinstaller.tmp (PID: 7412)
- explorer.exe (PID: 4488)
- clipgrab.exe (PID: 640)
- clipgrab.exe (PID: 1576)
The sample compiled with english language support
- clipgrab-3.9.11-dotinstaller.tmp (PID: 7412)
- clipgrab-3.9.11-portable.tmp (PID: 3296)
- vc_redist.x86.exe (PID: 3912)
- vc_redist.x86.exe (PID: 4528)
Reads the machine GUID from the registry
- clipgrab-3.9.11-dotinstaller.tmp (PID: 7412)
- ffmpeg.exe (PID: 1512)
- ffmpeg.exe (PID: 6644)
- clipgrab.exe (PID: 640)
- ffmpeg.exe (PID: 8164)
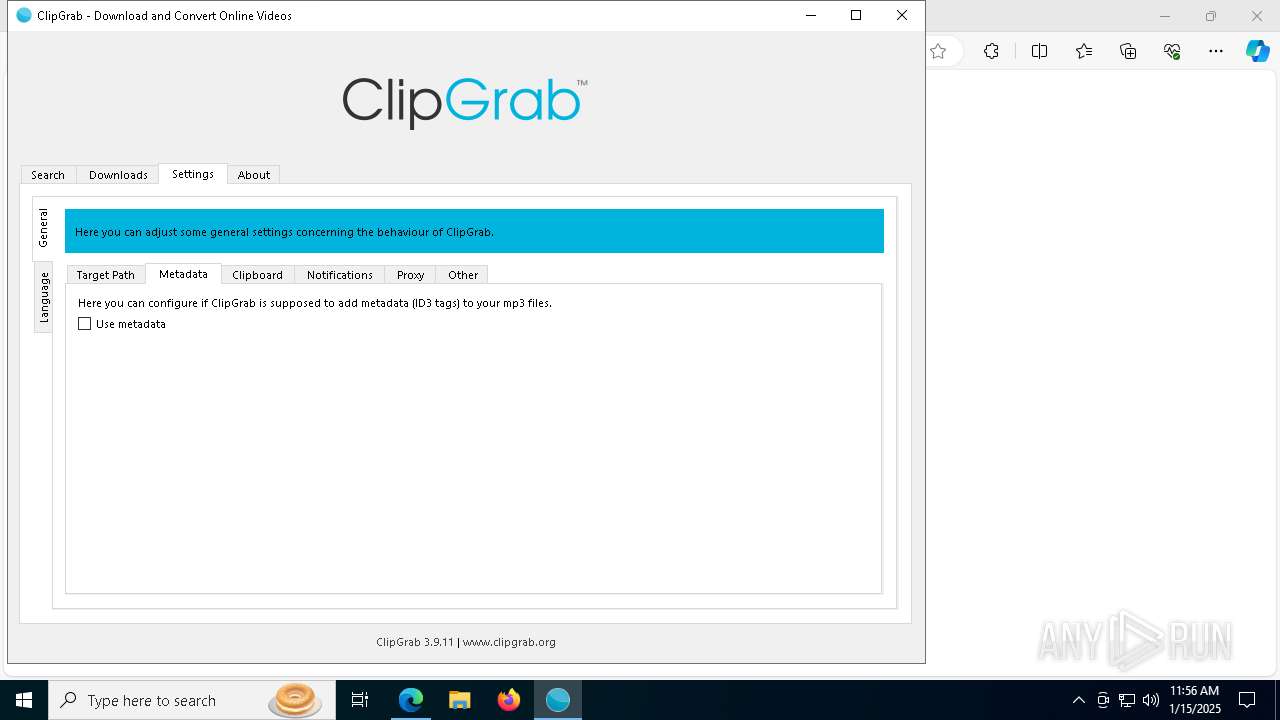
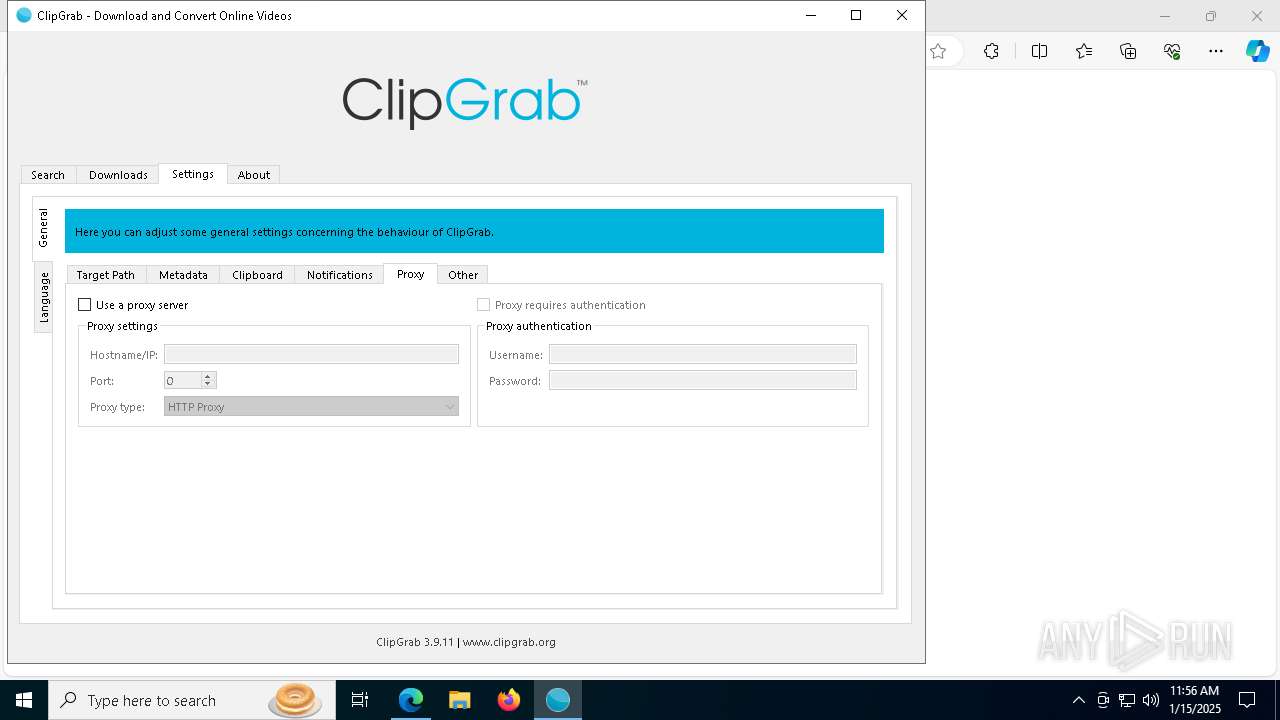
Checks proxy server information
- clipgrab-3.9.11-dotinstaller.tmp (PID: 7412)
- explorer.exe (PID: 4488)
Creates files in the program directory
- clipgrab-3.9.11-portable.tmp (PID: 3296)
Local mutex for internet shortcut management
- explorer.exe (PID: 4488)
Reads security settings of Internet Explorer
- explorer.exe (PID: 4488)
Python executable
- python.exe (PID: 6464)
- python.exe (PID: 716)
- python.exe (PID: 7292)
- python.exe (PID: 7220)
- python.exe (PID: 6472)
- python.exe (PID: 1540)
- python.exe (PID: 7280)
- python.exe (PID: 2788)
- python.exe (PID: 5788)
- python.exe (PID: 5304)
- python.exe (PID: 4228)
- python.exe (PID: 4304)
- python.exe (PID: 2152)
- python.exe (PID: 5496)
- python.exe (PID: 3436)
- python.exe (PID: 1796)
- python.exe (PID: 7620)
- python.exe (PID: 5880)
- python.exe (PID: 2220)
- python.exe (PID: 7416)
- python.exe (PID: 640)
- python.exe (PID: 8152)
- python.exe (PID: 4684)
- python.exe (PID: 6452)
- python.exe (PID: 4024)
- python.exe (PID: 936)
- python.exe (PID: 4944)
- python.exe (PID: 3556)
- python.exe (PID: 6660)
- python.exe (PID: 4544)
- python.exe (PID: 4008)
- python.exe (PID: 2260)
- python.exe (PID: 4504)
- python.exe (PID: 5912)
- python.exe (PID: 6240)
- python.exe (PID: 7092)
- python.exe (PID: 3972)
- python.exe (PID: 4944)
- python.exe (PID: 3824)
- python.exe (PID: 4648)
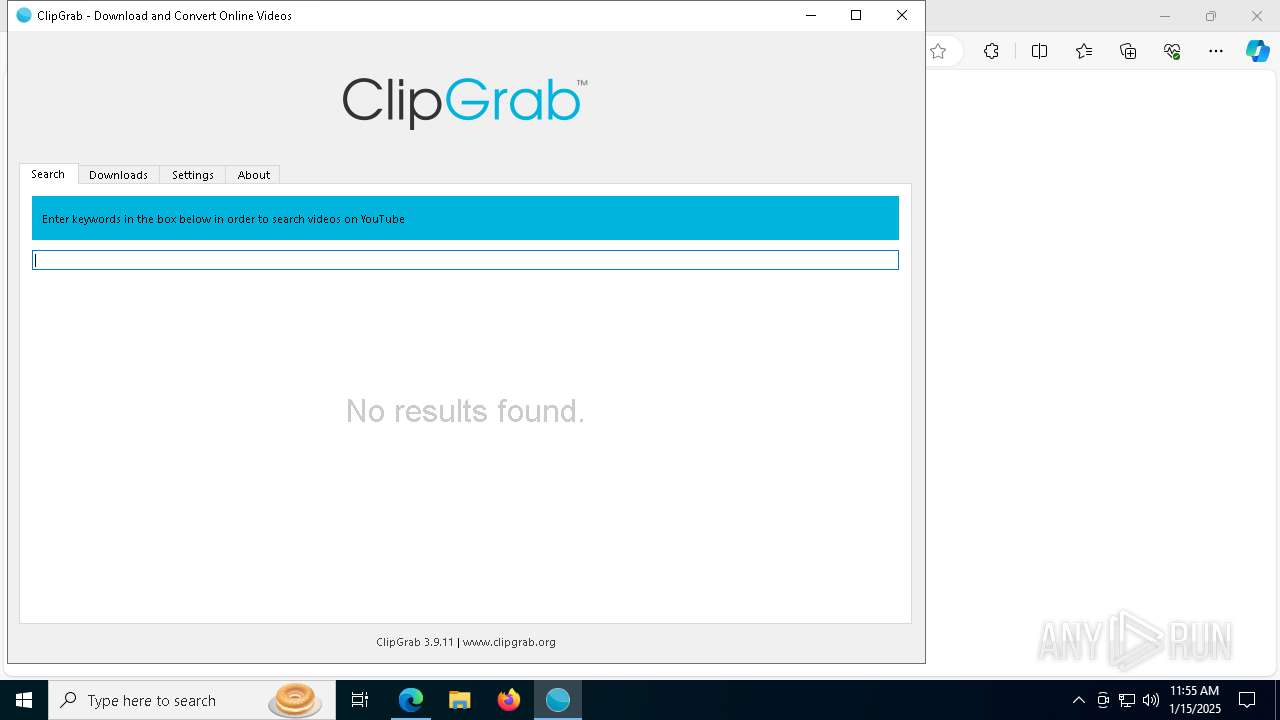
Drops encrypted VBS script (Microsoft Script Encoder)
- clipgrab.exe (PID: 640)
- clipgrab.exe (PID: 1576)
Sends debugging messages
- clipgrab.exe (PID: 640)
- clipgrab.exe (PID: 1576)
Drops encrypted JS script (Microsoft Script Encoder)
- clipgrab.exe (PID: 640)
- clipgrab.exe (PID: 1576)
Creates files or folders in the user directory
- explorer.exe (PID: 4488)
Reads the time zone
- QtWebEngineProcess.exe (PID: 7456)
Checks operating system version
- python.exe (PID: 6660)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
299
Monitored processes
166
Malicious processes
4
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 640 | "C:\Program Files (x86)\ClipGrab\clipgrab.exe" | C:\Program Files (x86)\ClipGrab\clipgrab.exe | clipgrab-3.9.11-dotinstaller.tmp | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 640 | "C:\Program Files (x86)\ClipGrab\python\python.exe" "" --version | C:\Program Files (x86)\ClipGrab\python\python.exe | — | clipgrab.exe | |||||||||||
User: admin Company: Python Software Foundation Integrity Level: MEDIUM Description: Python Exit code: 1 Version: 3.13.0 | |||||||||||||||
| 716 | "C:\Program Files (x86)\ClipGrab\python\python.exe" "" --version | C:\Program Files (x86)\ClipGrab\python\python.exe | — | clipgrab.exe | |||||||||||
User: admin Company: Python Software Foundation Integrity Level: HIGH Description: Python Exit code: 1 Version: 3.13.0 Modules
| |||||||||||||||
| 716 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7512 --field-trial-handle=2388,i,4374146469072547225,2352873484602321070,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | |||||||||||||||
| 776 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=42 --mojo-platform-channel-handle=5972 --field-trial-handle=2388,i,4374146469072547225,2352873484602321070,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | |||||||||||||||
| 936 | "C:\Program Files (x86)\ClipGrab\python\python.exe" "" --version | C:\Program Files (x86)\ClipGrab\python\python.exe | — | clipgrab.exe | |||||||||||
User: admin Company: Python Software Foundation Integrity Level: MEDIUM Description: Python Exit code: 1 Version: 3.13.0 | |||||||||||||||
| 936 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4216 --field-trial-handle=2388,i,4374146469072547225,2352873484602321070,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | |||||||||||||||
| 1216 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5468 --field-trial-handle=2388,i,4374146469072547225,2352873484602321070,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | |||||||||||||||
| 1220 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | ffmpeg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 1288 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | python.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
Total events
52 800
Read events
52 591
Write events
187
Delete events
22
Modification events
| (PID) Process: | (6336) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6336) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6336) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6336) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (6512) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
| (PID) Process: | (6512) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
| (PID) Process: | (6512) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\Profiles |
| Operation: | write | Name: | EnhancedLinkOpeningDefault |
Value: Default | |||
| (PID) Process: | (6512) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\263006 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {C756127A-4A4D-489F-85CE-37D590162887} | |||
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 040000000E0000000300000000000000100000000F0000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
Executable files
176
Suspicious files
726
Text files
167
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6512 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF136d44.TMP | — | |
MD5:— | SHA256:— | |||
| 6512 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6512 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF136d44.TMP | — | |
MD5:— | SHA256:— | |||
| 6512 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6512 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF136d53.TMP | — | |
MD5:— | SHA256:— | |||
| 6512 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF136d73.TMP | — | |
MD5:— | SHA256:— | |||
| 6512 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6512 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6512 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF136d73.TMP | — | |
MD5:— | SHA256:— | |||
| 6512 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
55
TCP/UDP connections
220
DNS requests
179
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4488 | explorer.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEEj8k7RgVZSNNqfJionWlBY%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4488 | explorer.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBQVD%2BnGf79Hpedv3mhy6uKMVZkPCQQUDyrLIIcouOxvSK4rVKYpqhekzQwCEQDkRzNBwfQQWSPKLzwR4XbI | unknown | — | — | whitelisted |
4488 | explorer.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSdE3gf41WAic8Uh9lF92%2BIJqh5qwQUMuuSmv81lkgvKEBCcCA2kVwXheYCEGIdbQxSAZ47kHkVIIkhHAo%3D | unknown | — | — | whitelisted |
7496 | svchost.exe | HEAD | 200 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/6ca9004c-2afd-40c0-a9b1-4fec460952e5?P1=1737531507&P2=404&P3=2&P4=et59PQoiSjQwmutE6WcUKKoCe6CBG2ETllz0%2fjNqmBuiPjcb433M17YdfwhkRtogdjBxkiWsrVZcgXPxxjwDZQ%3d%3d | unknown | — | — | whitelisted |
7496 | svchost.exe | GET | 206 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/6ca9004c-2afd-40c0-a9b1-4fec460952e5?P1=1737531507&P2=404&P3=2&P4=et59PQoiSjQwmutE6WcUKKoCe6CBG2ETllz0%2fjNqmBuiPjcb433M17YdfwhkRtogdjBxkiWsrVZcgXPxxjwDZQ%3d%3d | unknown | — | — | whitelisted |
7556 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4824 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 92.205.197.54:80 | download.clipgrab.org | — | DE | unknown |
— | — | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
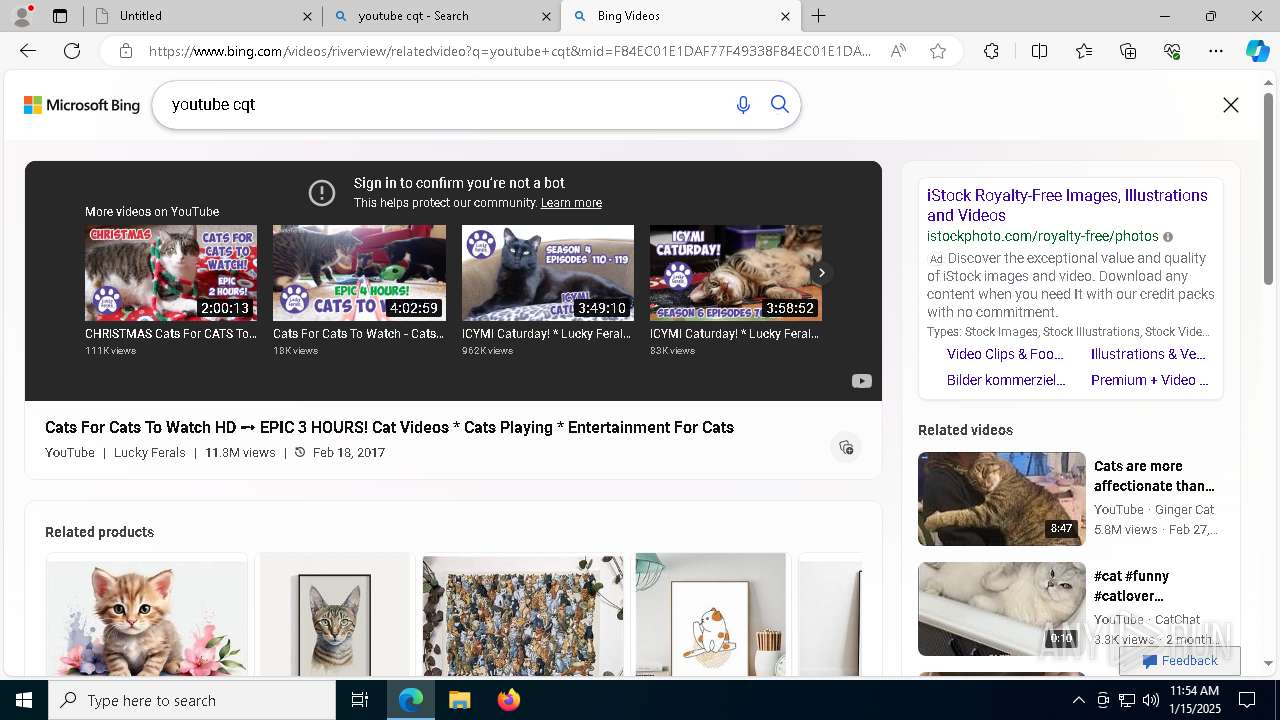
download.clipgrab.org |
| unknown |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
update.googleapis.com |
| whitelisted |
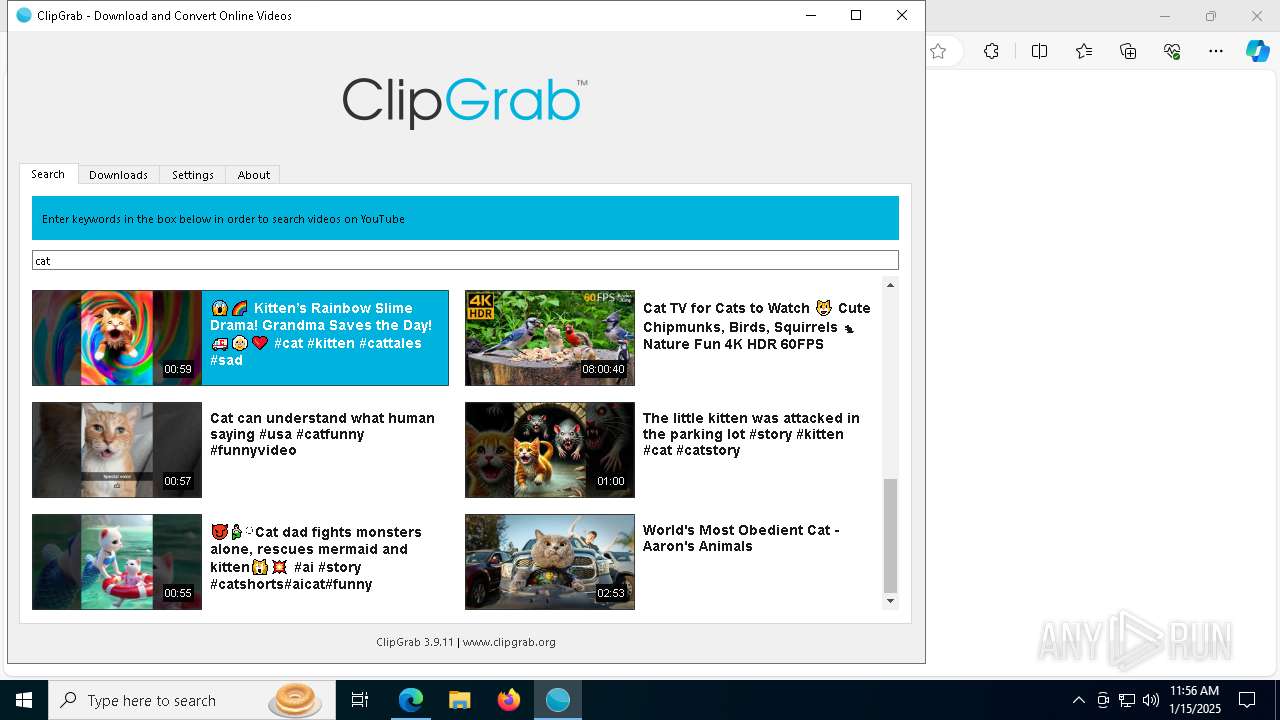
Threats
Process | Message |
|---|---|
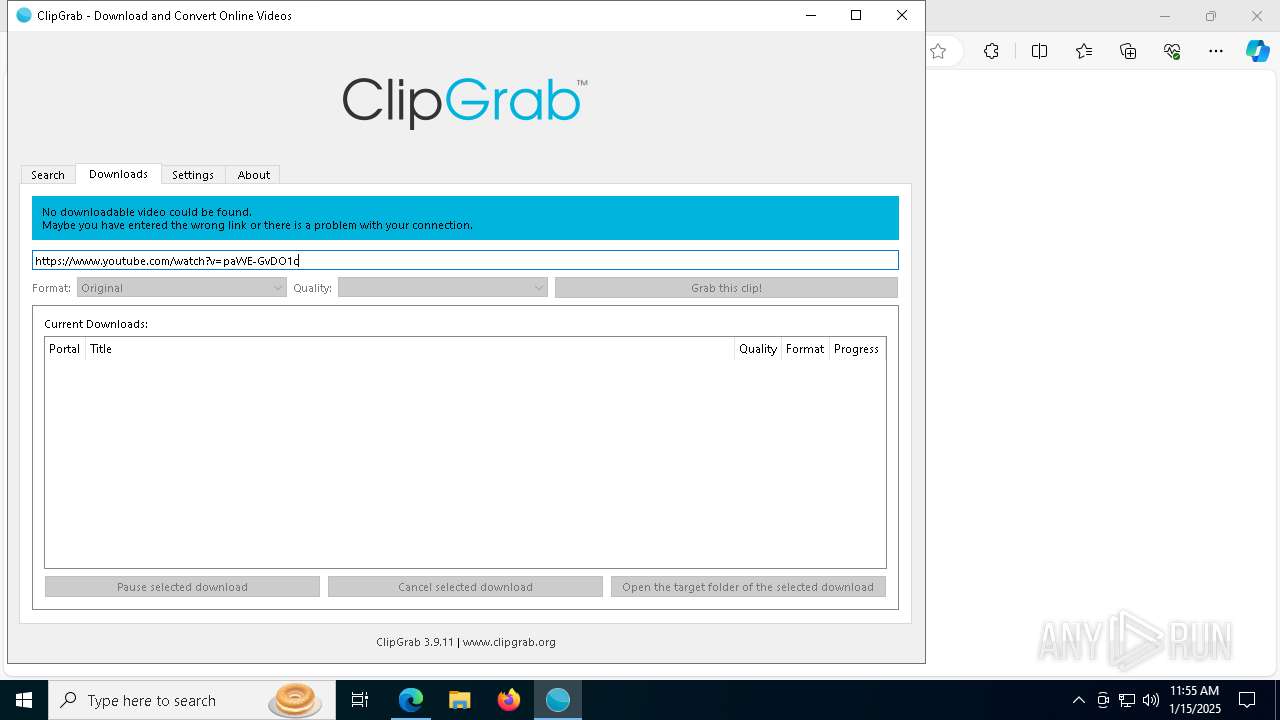
clipgrab.exe | QObject::connect: signal not found in QTreeView
|
clipgrab.exe | "C:\\Program Files (x86)\\ClipGrab\\python\\python.exe: can't find '__main__' module in 'C:\\\\Users\\\\admin\\\\AppData\\\\Local\\\\Temp'\r\n"
|
clipgrab.exe | Release of profile requested but WebEnginePage still not deleted. Expect troubles !
|
clipgrab.exe | QObject::connect: signal not found in QTreeView
|