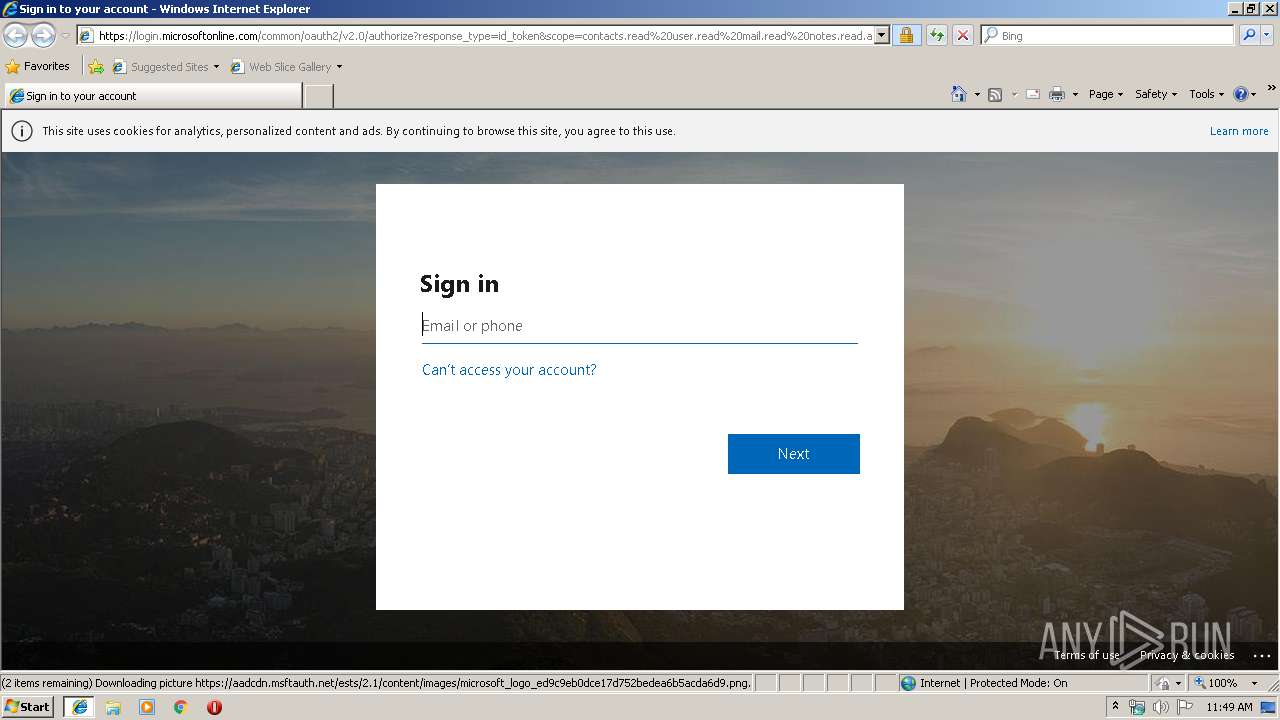
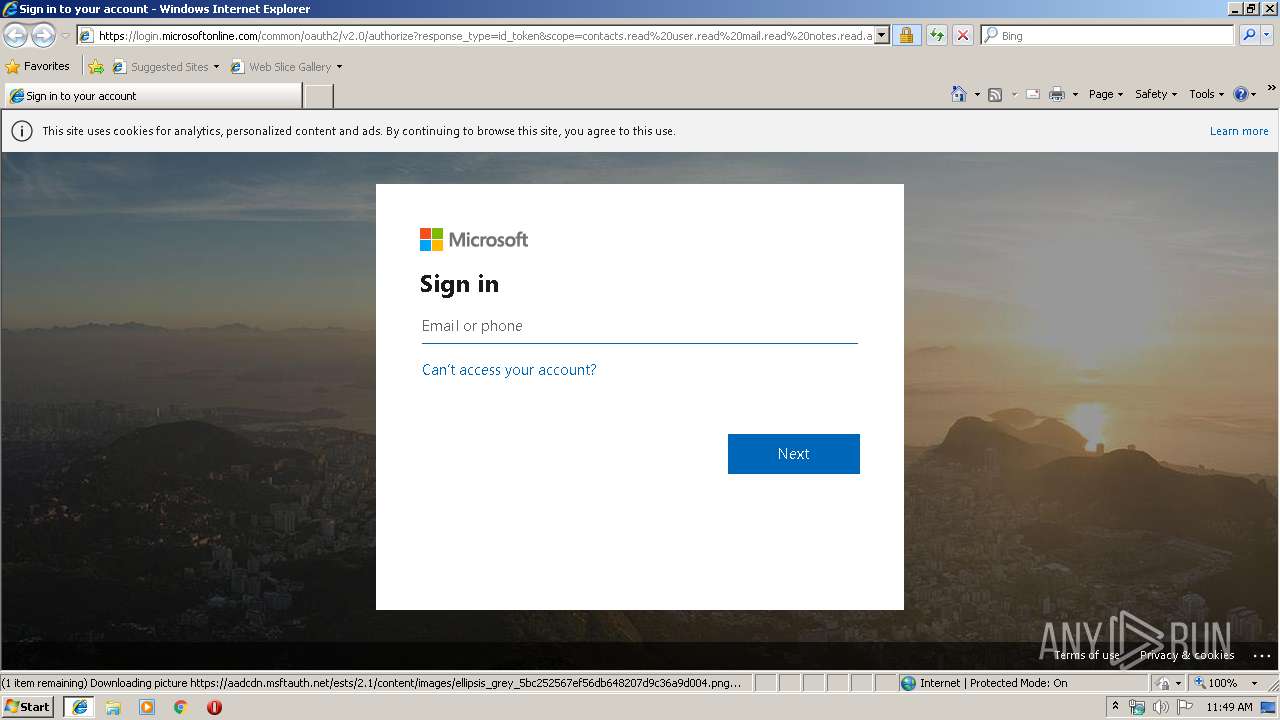
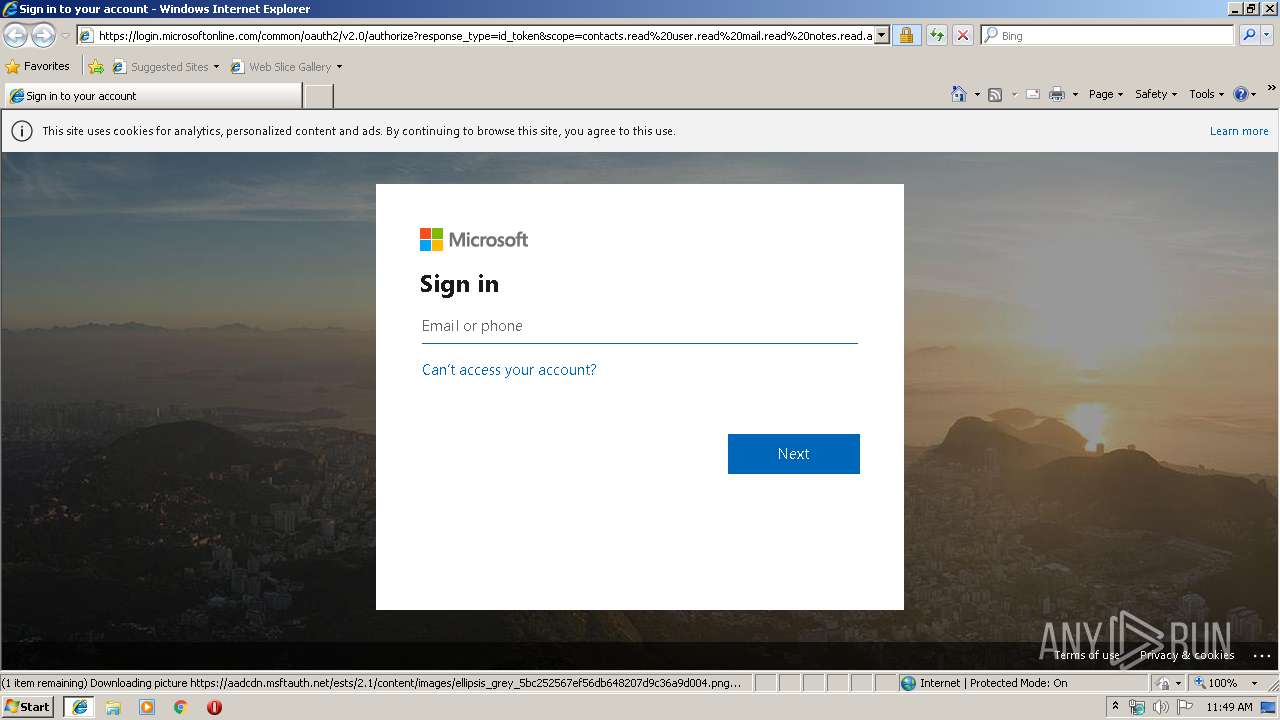
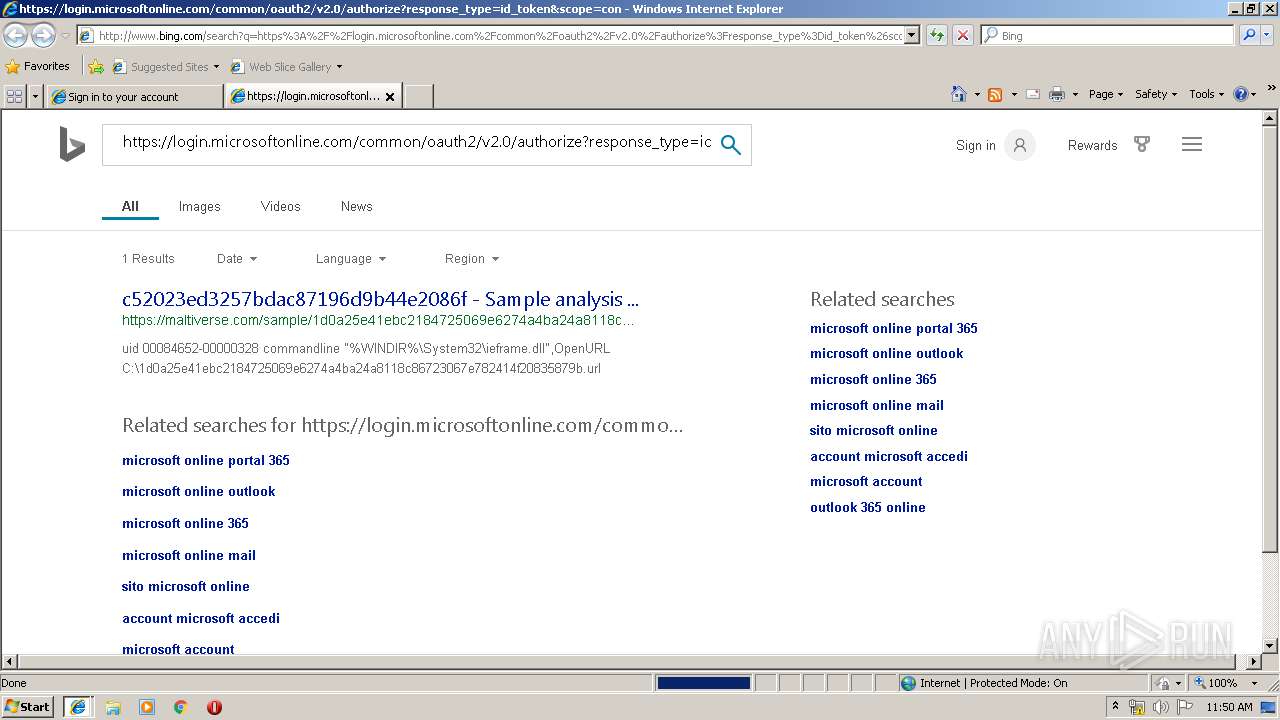
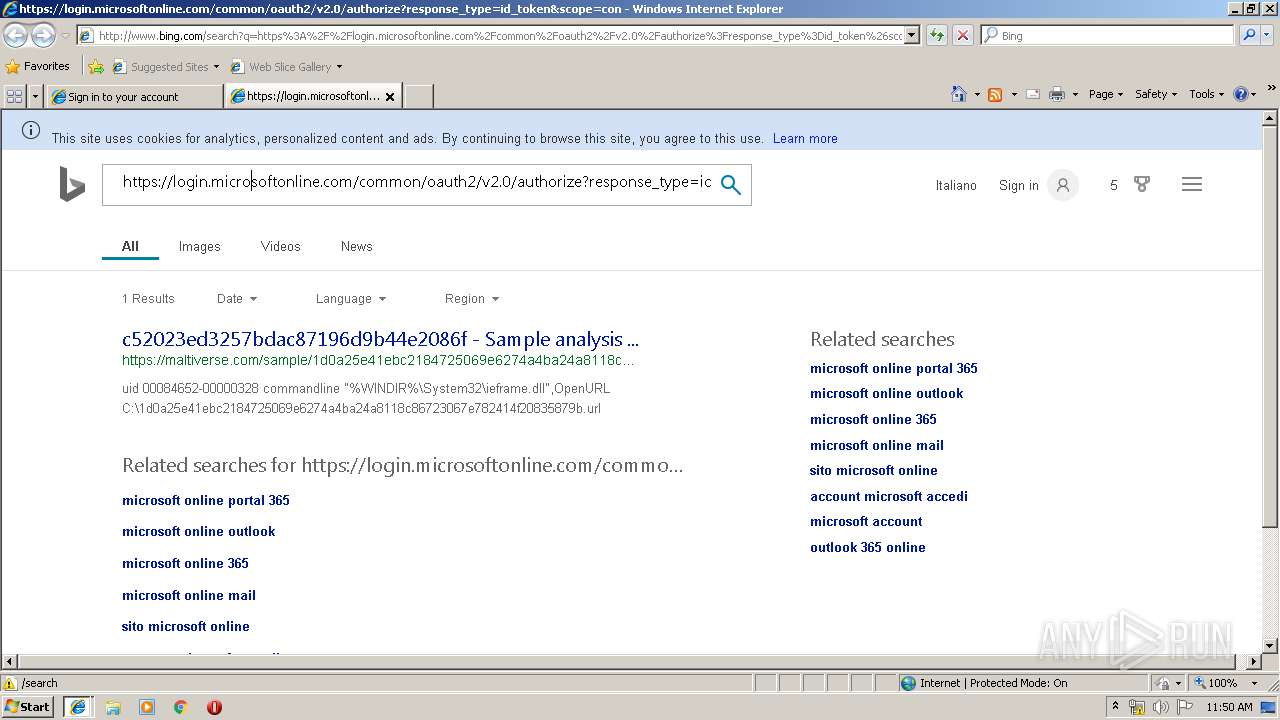
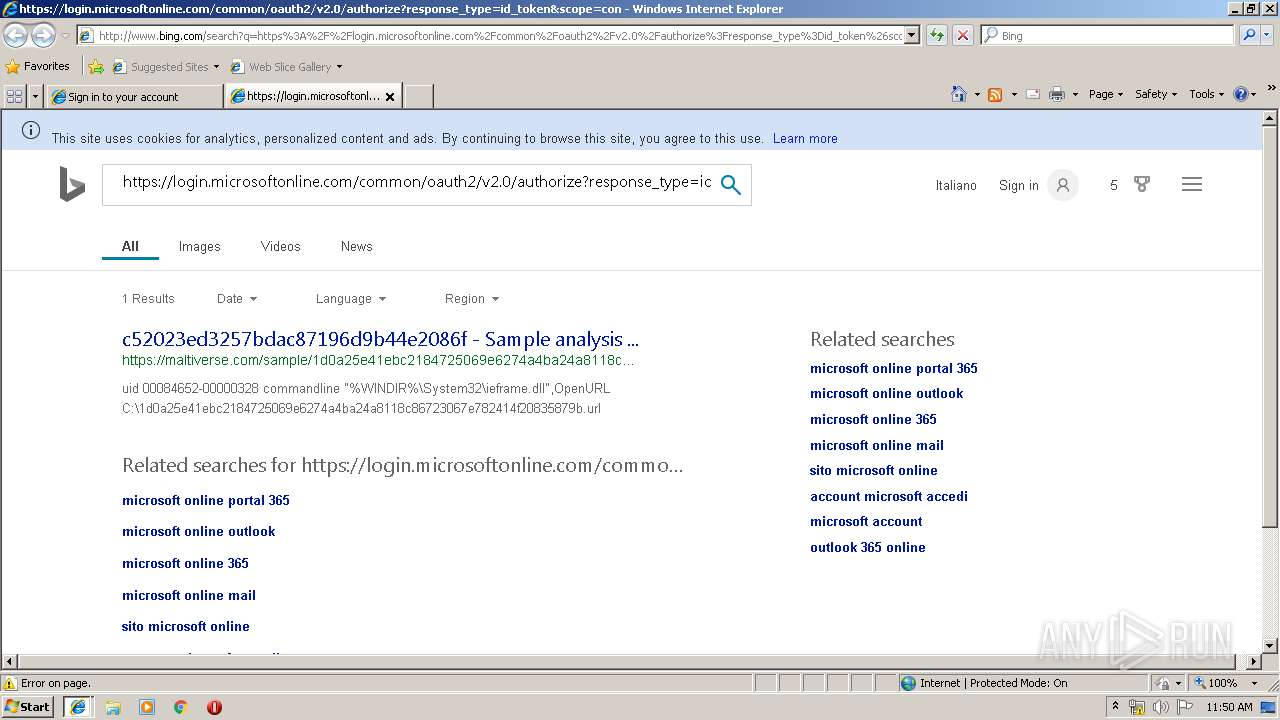
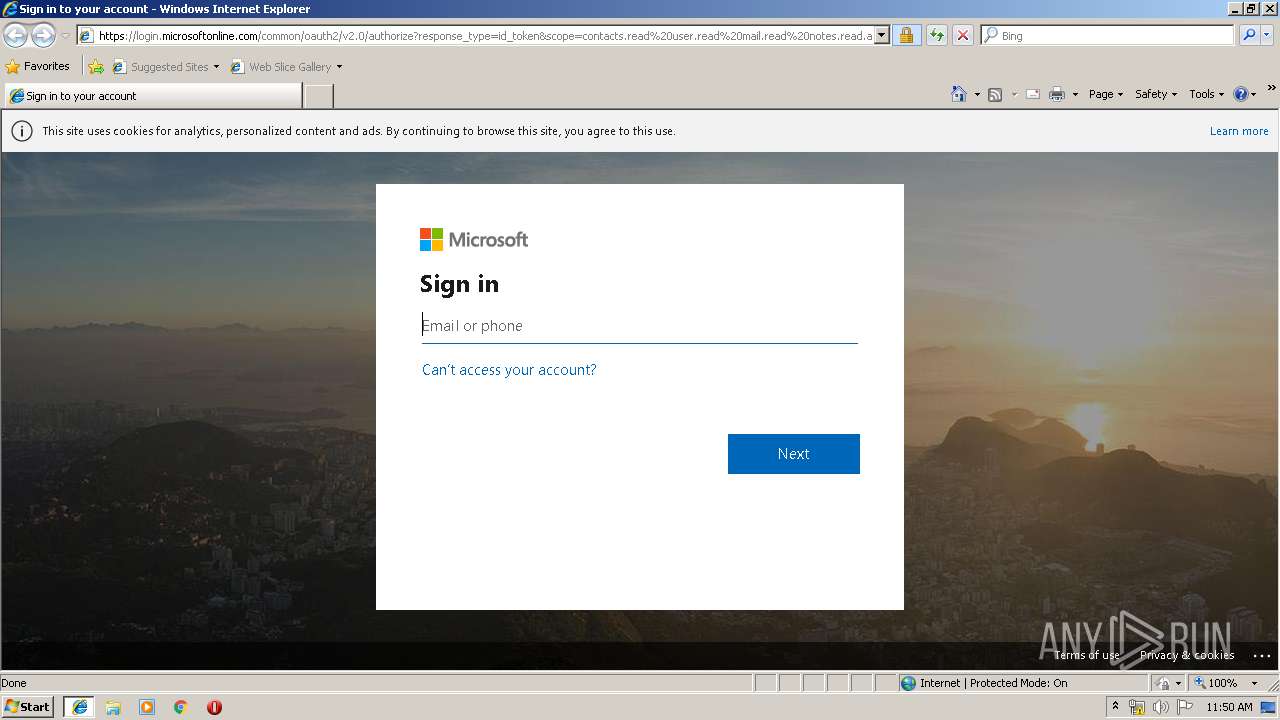
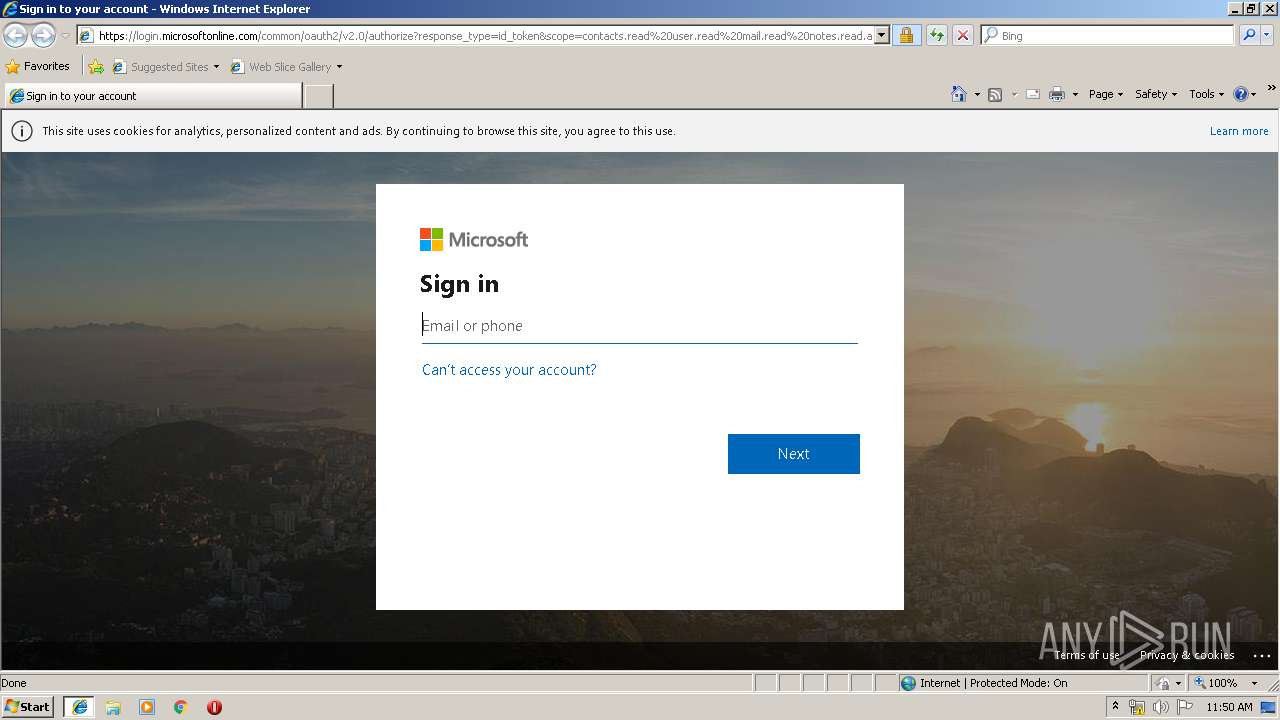
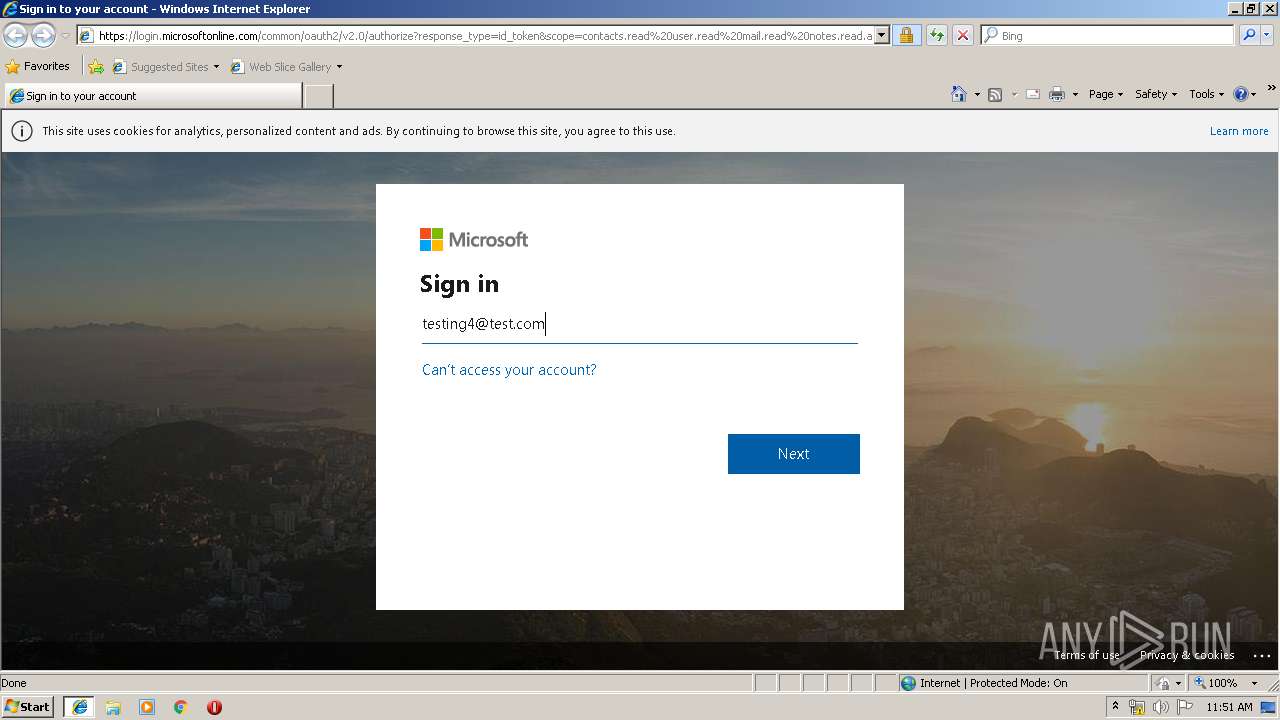
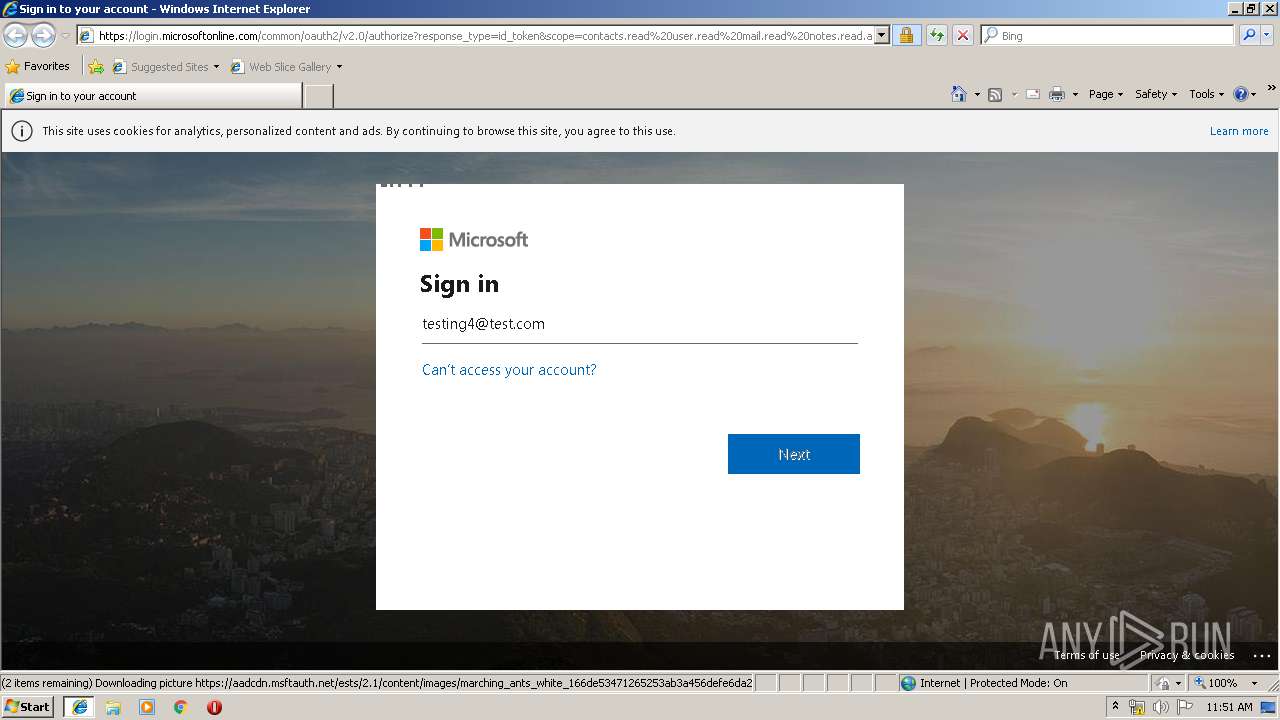
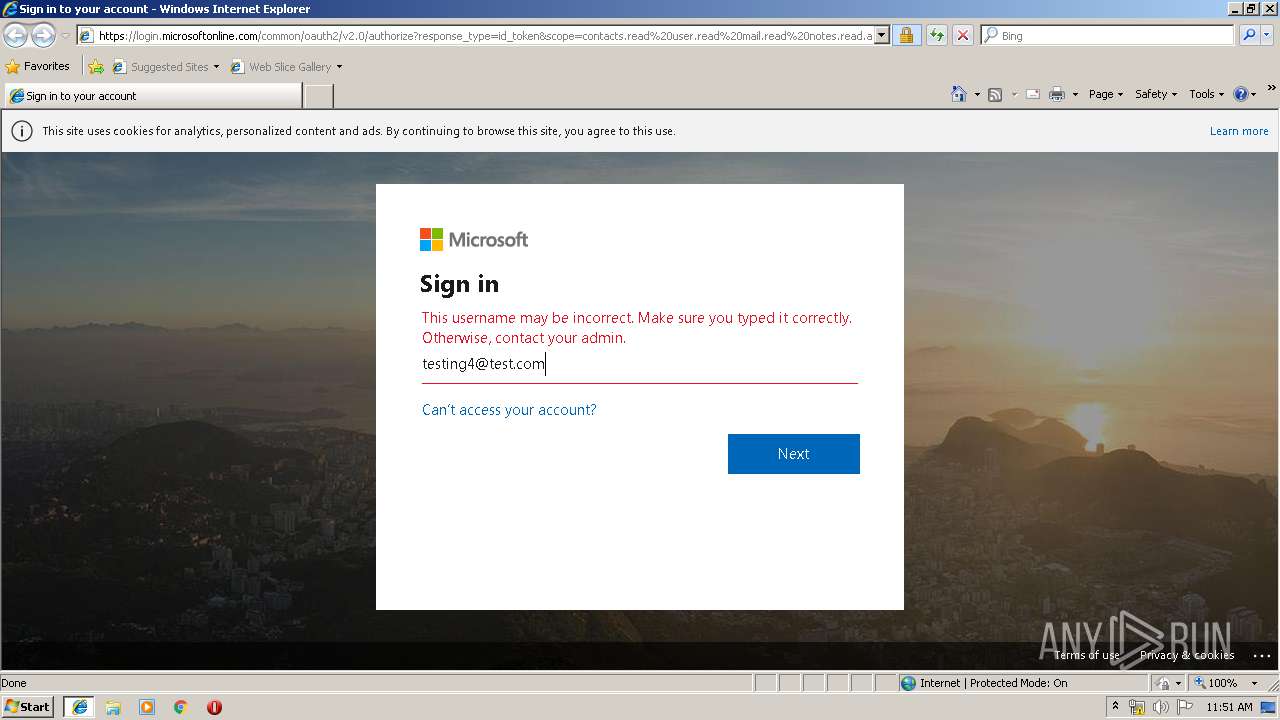
| URL: | https://login.microsoftonline.com/common/oauth2/v2.0/authorize?response_type=id_token&scope=contacts.read%20user.read%20mail.read%20notes.read.all%20mailboxsettings.readwrite%20Files.ReadWrite.All%20openid%20profile&client_id=fc5d3843-d0e8-4c3f-b0ee-6d407f667751&redirect_uri=https%3A%2F%2Fofficemtr.com%3A30662%2F&state=6bab49b7-d750-4d86-b931-c1d0c8fa73de&nonce=1a557734-c543-4c00-b698-35dc7084e6bd&client_info=1&x-client-SKU=MSAL.JS&x-client-Ver=1.0.0&client-request-id=df1f9d77-557e-4d0c-97c1-ceaf920146c1&response_mode=fragment |
| Full analysis: | https://app.any.run/tasks/72849275-249d-4f30-8399-6903885f4d09 |
| Verdict: | No threats detected |
| Analysis date: | December 02, 2019, 11:48:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 6A117CFF2D3DB700FFBA4E0445906117 |
| SHA1: | F5F01CEB7A578C6CB5B10AB039DF6ED25886B2D4 |
| SHA256: | 1D9D2E90517596EFC57F8DD5B6FA2B20A8568288BC7E4220D5426E9FE395B6C1 |
| SSDEEP: | 12:2v+sLcXkMN0KHlN3Rm4IvOCQ9G6TIR1Y56li2k00wVU+mLGCWm3X:2v+sL+N0KHTXCJwrNSd3kGCWm3X |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
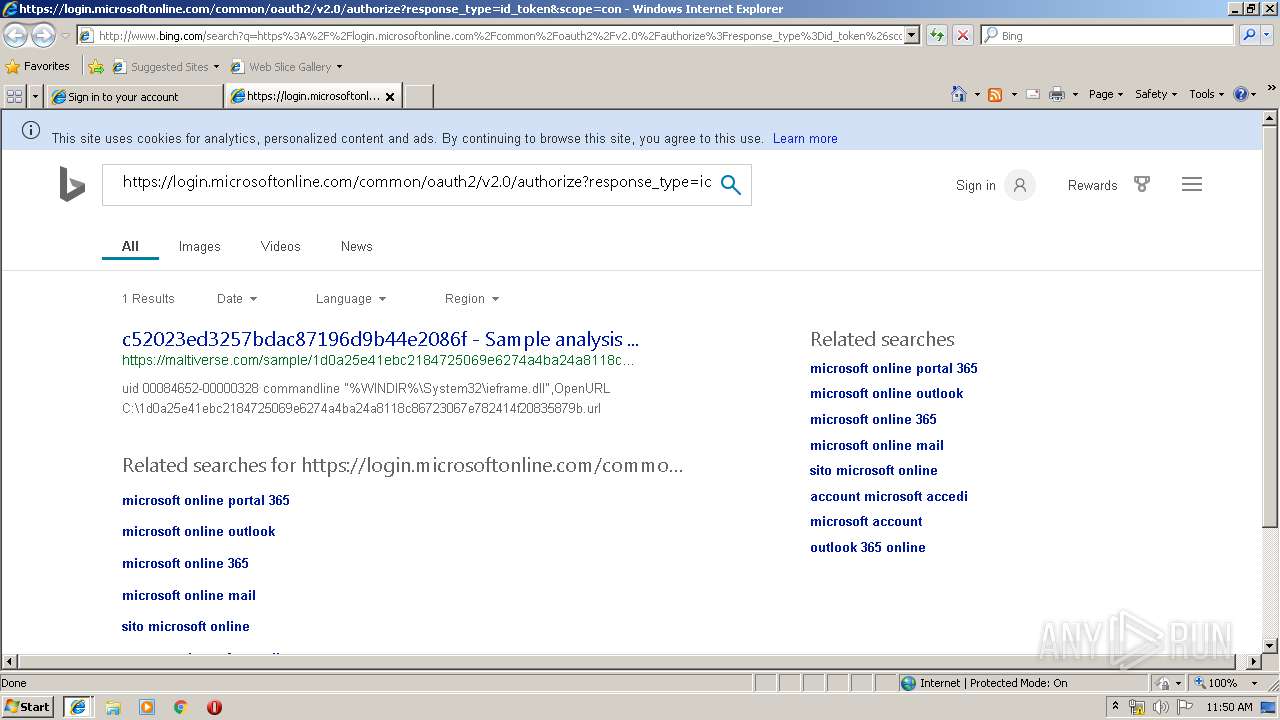
Reads Internet Cache Settings
- iexplore.exe (PID: 2604)
- iexplore.exe (PID: 952)
- iexplore.exe (PID: 1484)
Creates files in the user directory
- iexplore.exe (PID: 2604)
- iexplore.exe (PID: 952)
Reads internet explorer settings
- iexplore.exe (PID: 952)
- iexplore.exe (PID: 2604)
- iexplore.exe (PID: 1484)
Reads settings of System Certificates
- iexplore.exe (PID: 952)
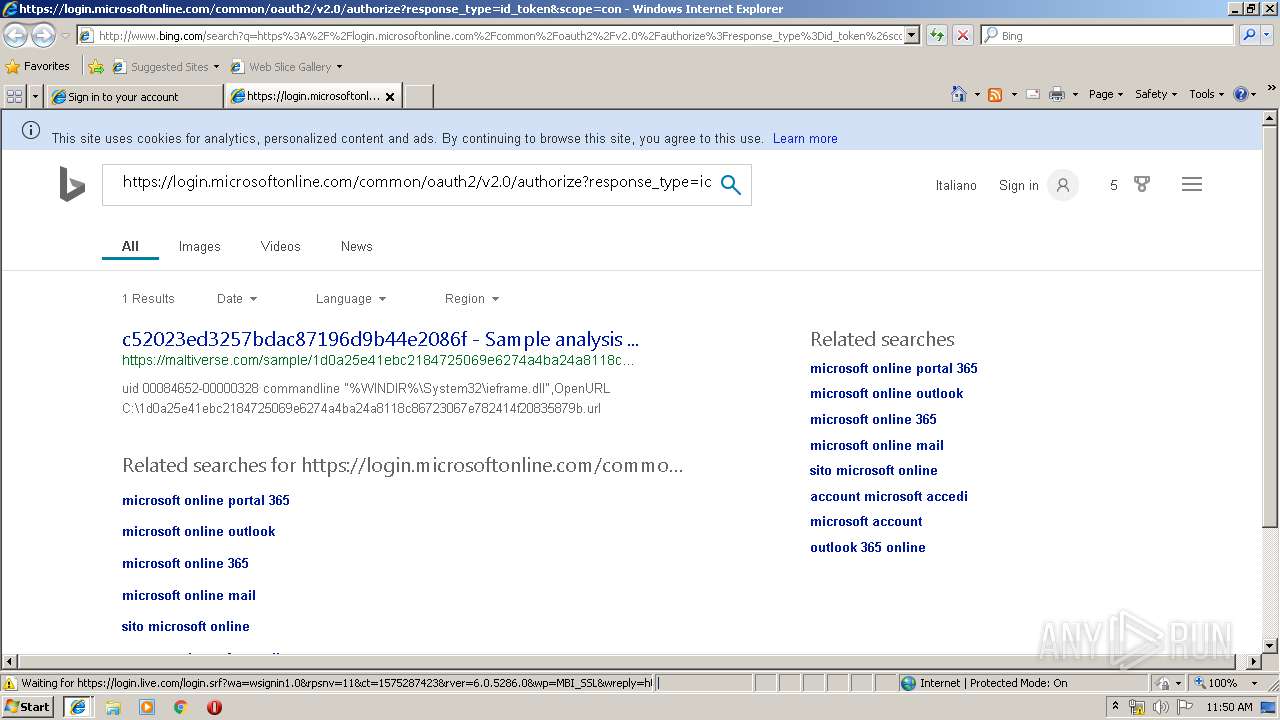
Changes internet zones settings
- iexplore.exe (PID: 3180)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 952)
Application launched itself
- iexplore.exe (PID: 3180)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
39
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 952 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3180 CREDAT:6404 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1484 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3180 CREDAT:203013 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2604 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3180 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3180 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://login.microsoftonline.com/common/oauth2/v2.0/authorize?response_type=id_token&scope=contacts.read%20user.read%20mail.read%20notes.read.all%20mailboxsettings.readwrite%20Files.ReadWrite.All%20openid%20profile&client_id=fc5d3843-d0e8-4c3f-b0ee-6d407f667751&redirect_uri=https%3A%2F%2Fofficemtr.com%3A30662%2F&state=6bab49b7-d750-4d86-b931-c1d0c8fa73de&nonce=1a557734-c543-4c00-b698-35dc7084e6bd&client_info=1&x-client-SKU=MSAL.JS&x-client-Ver=1.0.0&client-request-id=df1f9d77-557e-4d0c-97c1-ceaf920146c1&response_mode=fragment" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
862
Read events
744
Write events
116
Delete events
2
Modification events
| (PID) Process: | (3180) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3180) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3180) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3180) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3180) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3180) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3180) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {BF2B5CE9-14F9-11EA-AB41-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3180) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3180) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (3180) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070C00010002000B0031000800F602 | |||
Executable files
0
Suspicious files
4
Text files
72
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3180 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3180 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2604 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@login.microsoftonline[1].txt | — | |
MD5:— | SHA256:— | |||
| 2604 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OZIJF2KK\authorize[1].txt | — | |
MD5:— | SHA256:— | |||
| 2604 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OZIJF2KK\authorize[1].htm | html | |
MD5:— | SHA256:— | |||
| 2604 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2604 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2604 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@login.microsoftonline[2].txt | text | |
MD5:— | SHA256:— | |||
| 2604 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2604 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OZIJF2KK\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
23
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
952 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/6k/5m/cj,nj/6e795a8b/1c156e04.js | US | text | 1.81 Kb | whitelisted |
952 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/58/2M/cj,nj/4df0cf24/0120f753.js | US | text | 2.92 Kb | whitelisted |
952 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/2Z/23/cj,nj/3f1e2270/f8c6dd44.js | US | text | 773 b | whitelisted |
952 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/6D/w2/nj/d695a46a/a9b12688.js | US | text | 353 b | whitelisted |
952 | iexplore.exe | POST | 200 | 204.79.197.200:80 | http://www.bing.com/rewardsapp/reportActivity?IG=1DDD179B4FBF4081B733A89690F6794A&IID=SERP.5053&q=https%3A%2F%2Flogin.microsoftonline.com%2Fcommon%2Foauth2%2Fv2.0%2Fauthorize%3Fresponse_type%3Did_token%26scope%3Dcontacts.read%2520user.read%2520mail.read%2520notes.read.all%2520mailboxsettings.readwrite%2520Files.ReadWrite.All%2520openid%2520profile%26client_id%3Dfc5d3843-d0e8-4c3f-b0ee-6d407f667751%26redirect_uri%3Dhttps%253A%252F%252Fofficemtr.com%253A30662%252F%26state%3D6bab49b7-d750-4d86-b931-c1d0c8fa73de%26nonce%3D1a557734-c543-4c00-b698-35dc7084e6bd%26client_info%3D1%26x-client-SKU%3DMSAL.JS%26x-client-Ver%3D1.0.0%26client-request-id%3Ddf1f9d77-557e-4d0c-97c1-ceaf920146c1%26response_mode%3Dfragment&src=IE-SearchBox&FORM=IE8SRC | US | html | 1.40 Kb | whitelisted |
952 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/fd/ls/l?IG=1DDD179B4FBF4081B733A89690F6794A&CID=093A372537D666800507390336BD67FC&Type=Event.ClientInst&DATA=[{"T":"CI.GetError","FID":"CI","Name":"JSGetError","Text":"%27SVGElement%27%20is%20undefined","Meta":"http%3A//www.bing.com/search%3Fq%3Dhttps%253A%252F%252Flogin.microsoftonline.com%252Fcommon%252Foauth2%252Fv2.0%252Fauthorize%253Fresponse_type%253Did_token%2526scope%253Dcontacts.read%252520user.read%252520mail.read%252520notes.read.all%252520mailboxsettings.readwrite%252520Files.ReadWrite.All%252520openid%252520profile%2526client_id%253Dfc5d3843-d0e8-4c3f-b0ee-6d407f667751%2526redirect_uri%253Dhttps%25253A%25252F%25252Fofficemtr.com%25253A30662%25252F%2526state%253D6bab49b7-d750-4d86-b931-c1d0c8fa73de%2526nonce%253D1a557734-c543-4c00-b698-35dc7084e6bd%2526client_info%253D1%2526x-client-SKU%253DMSAL.JS%2526x-client-Ver%253D1.0.0%2526client-request-id%253Ddf1f9d77-557e-4d0c-97c1-ceaf920146c1%2526response_mode%253Dfragment%26src%3DIE-SearchBox%26FORM%3DIE8SRC","Line":9595155,"Char":%20undefined}] | US | compressed | 1.81 Kb | whitelisted |
952 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rb/6g/cj,nj/f28dadef/aea7e831.js?bu=AckG | US | text | 174 b | whitelisted |
952 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rb/5h/cj,nj/e174eefe/f2b430ba.js?bu=EoogqyDMH9cfiAXkH-YfuyDoH_If-B-bIJggniCYH48elx6DHw | US | text | 5.10 Kb | whitelisted |
952 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/2Z/2n/cj,nj/4c7364c5/40e1b425.js | US | text | 816 b | whitelisted |
3180 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3180 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2604 | iexplore.exe | 20.190.129.160:443 | login.microsoftonline.com | Microsoft Corporation | US | malicious |
2604 | iexplore.exe | 152.199.23.37:443 | aadcdn.msftauth.net | MCI Communications Services, Inc. d/b/a Verizon Business | US | suspicious |
3180 | iexplore.exe | 152.199.23.37:443 | aadcdn.msftauth.net | MCI Communications Services, Inc. d/b/a Verizon Business | US | suspicious |
952 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2604 | iexplore.exe | 13.107.246.10:443 | aadcdn.msauth.net | Microsoft Corporation | US | whitelisted |
952 | iexplore.exe | 40.90.22.184:443 | login.live.com | Microsoft Corporation | US | malicious |
952 | iexplore.exe | 204.79.197.222:80 | eee677c95860ae527b088687f3addc6c.clo.footprintdns.com | Microsoft Corporation | US | whitelisted |
952 | iexplore.exe | 40.86.215.224:80 | 6be314b26cd06c038a9be3d0c5e315d9.clo.footprintdns.com | Microsoft Corporation | CA | whitelisted |
— | — | 204.79.197.222:80 | eee677c95860ae527b088687f3addc6c.clo.footprintdns.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.microsoftonline.com |
| whitelisted |
www.bing.com |
| whitelisted |
aadcdn.msftauth.net |
| whitelisted |
dns.msftncsi.com |
| shared |
aadcdn.msauth.net |
| whitelisted |
login.live.com |
| whitelisted |
eee677c95860ae527b088687f3addc6c.clo.footprintdns.com |
| suspicious |
9a8a53b4df9efc1e8e23adbaf07da976.clo.footprintdns.com |
| suspicious |
6be314b26cd06c038a9be3d0c5e315d9.clo.footprintdns.com |
| unknown |
fp.msedge.net |
| whitelisted |