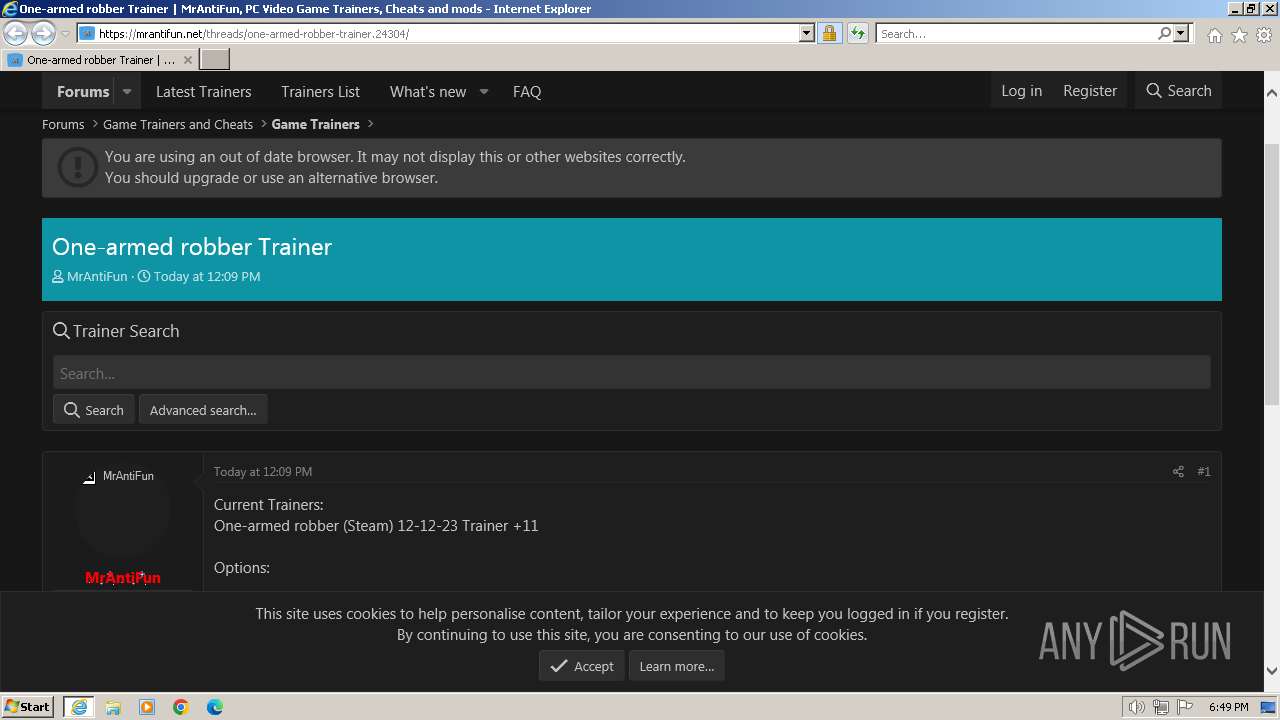
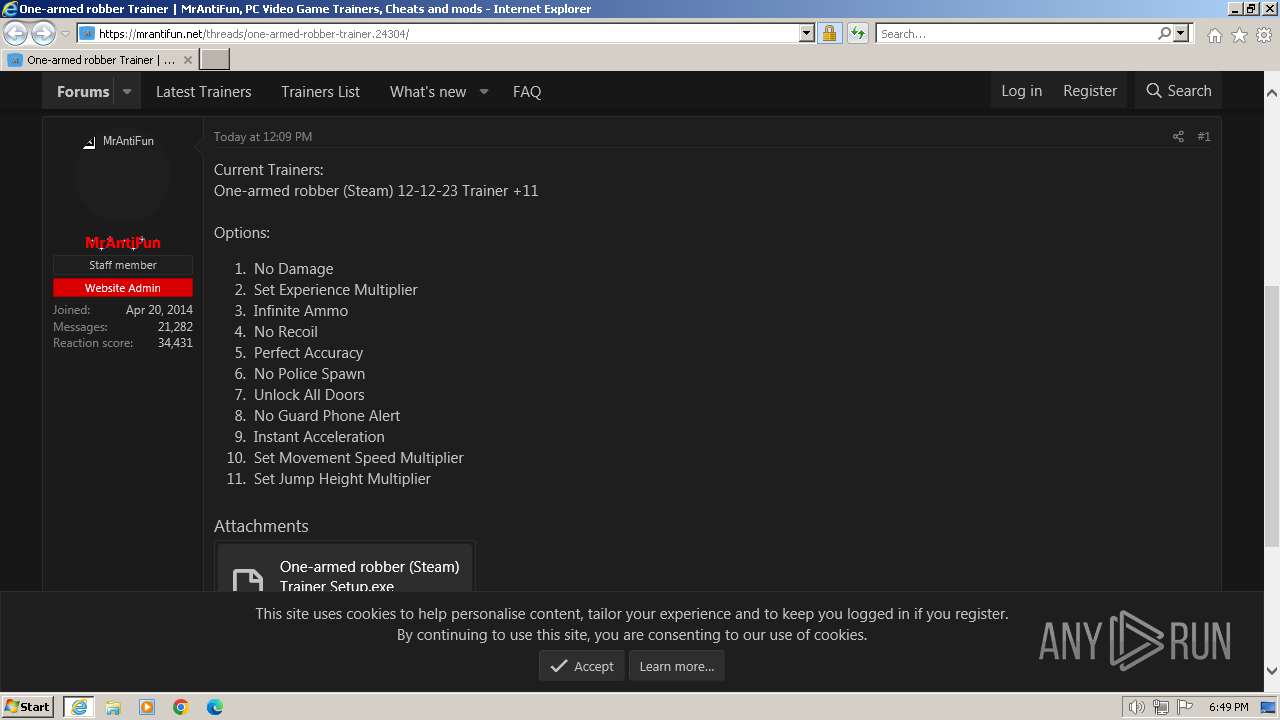
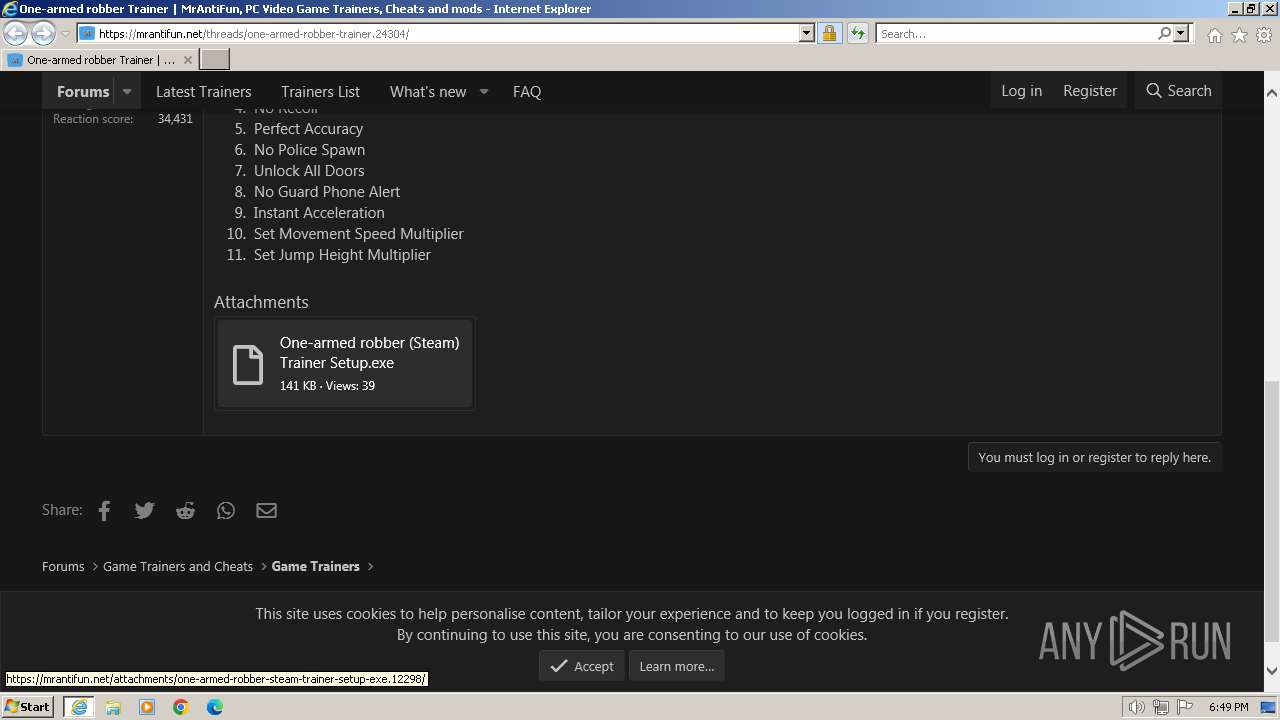
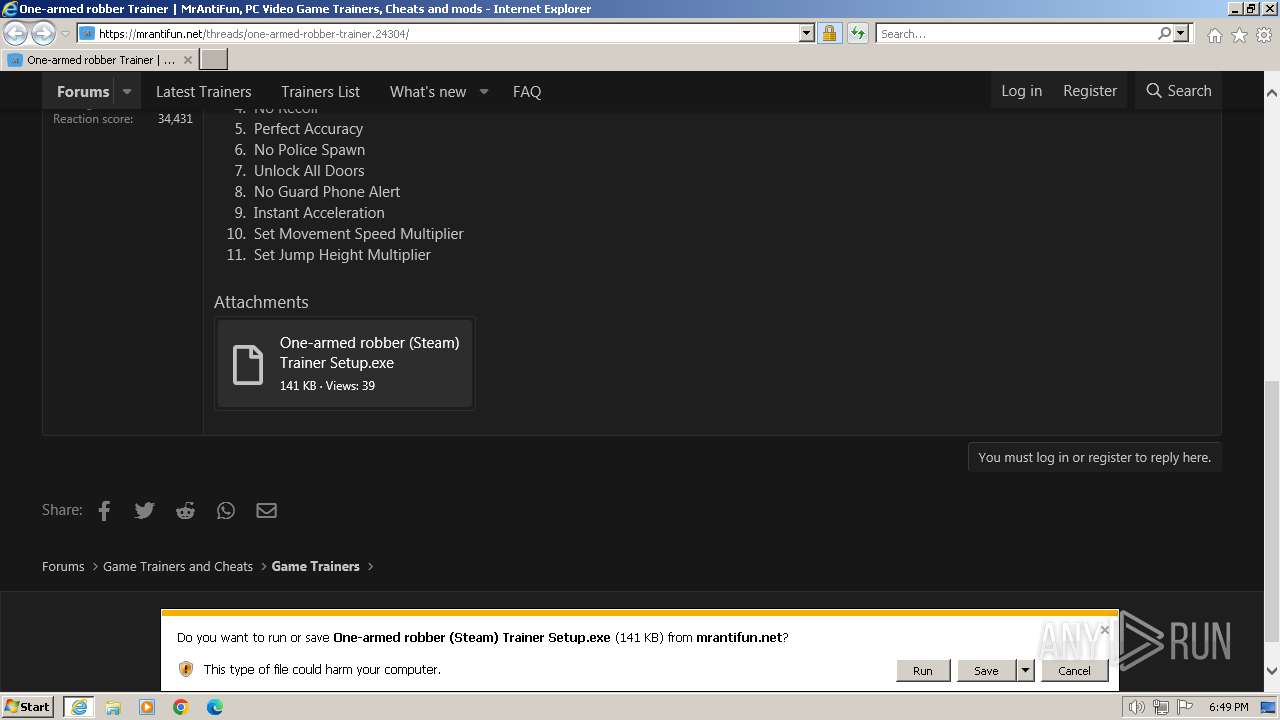
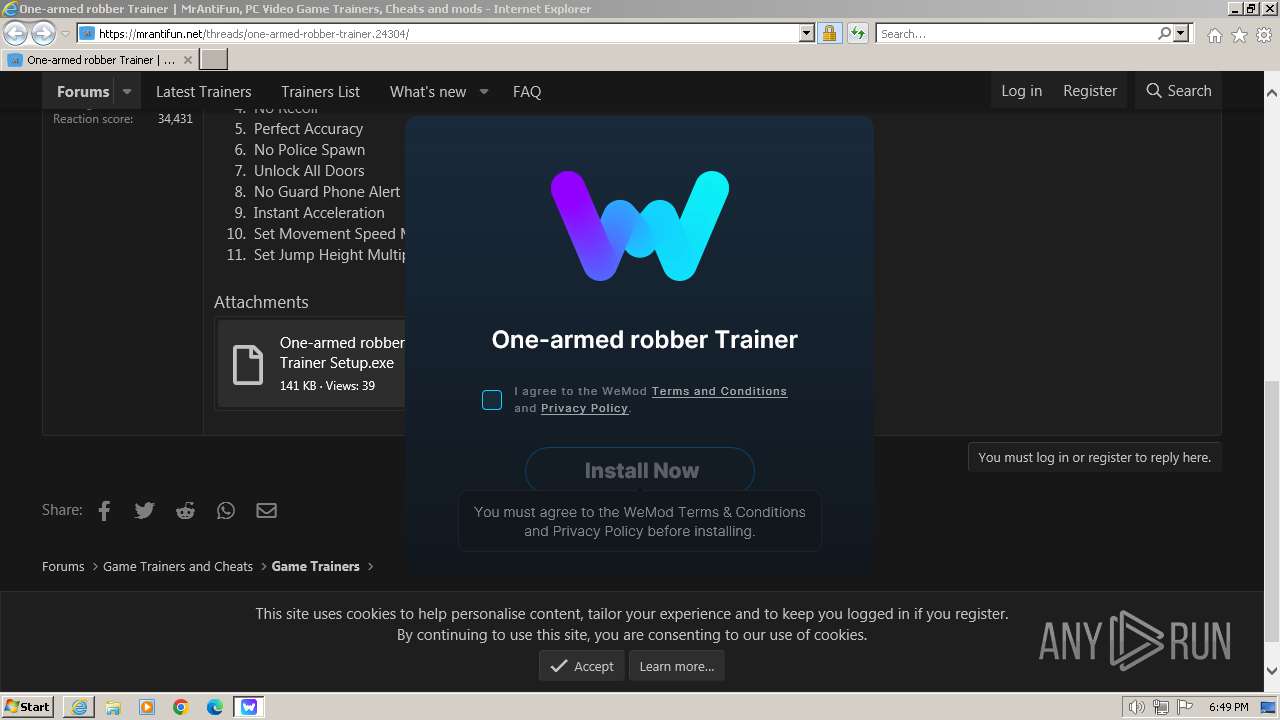
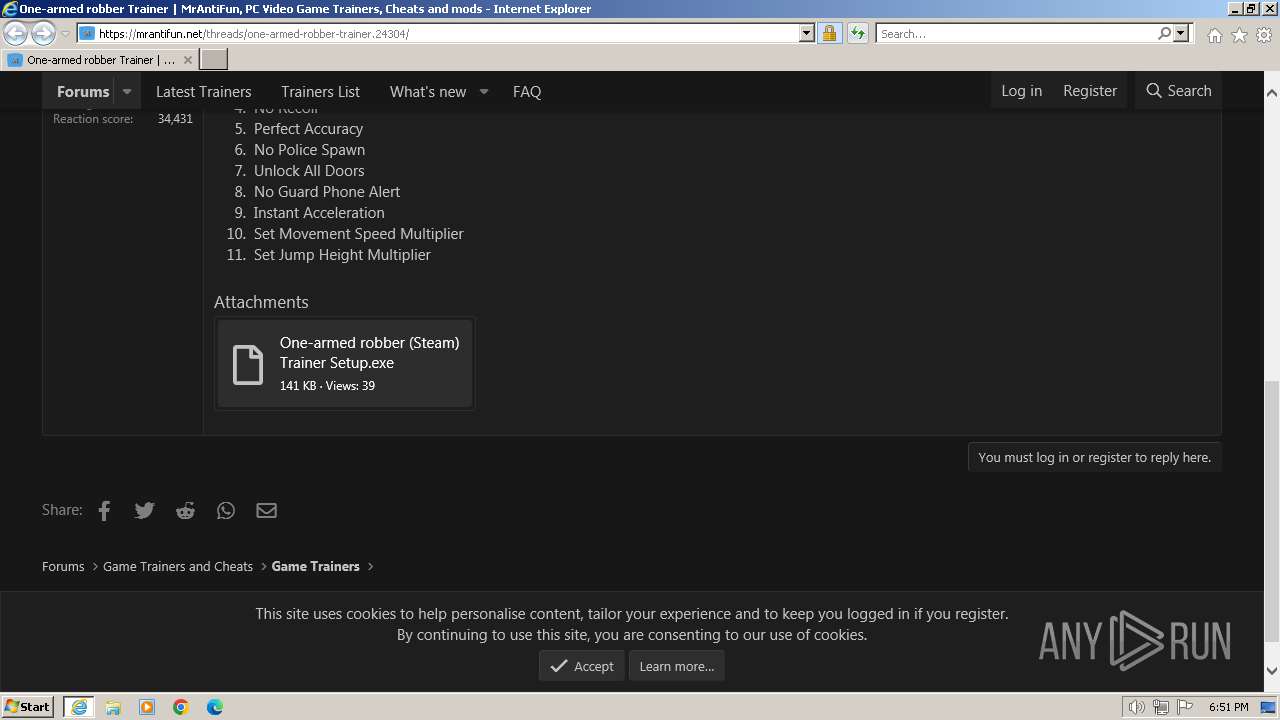
| URL: | https://mrantifun.net/threads/one-armed-robber-trainer.24304/ |
| Full analysis: | https://app.any.run/tasks/f97ccaa3-812a-4419-a6c3-6860bb85e048 |
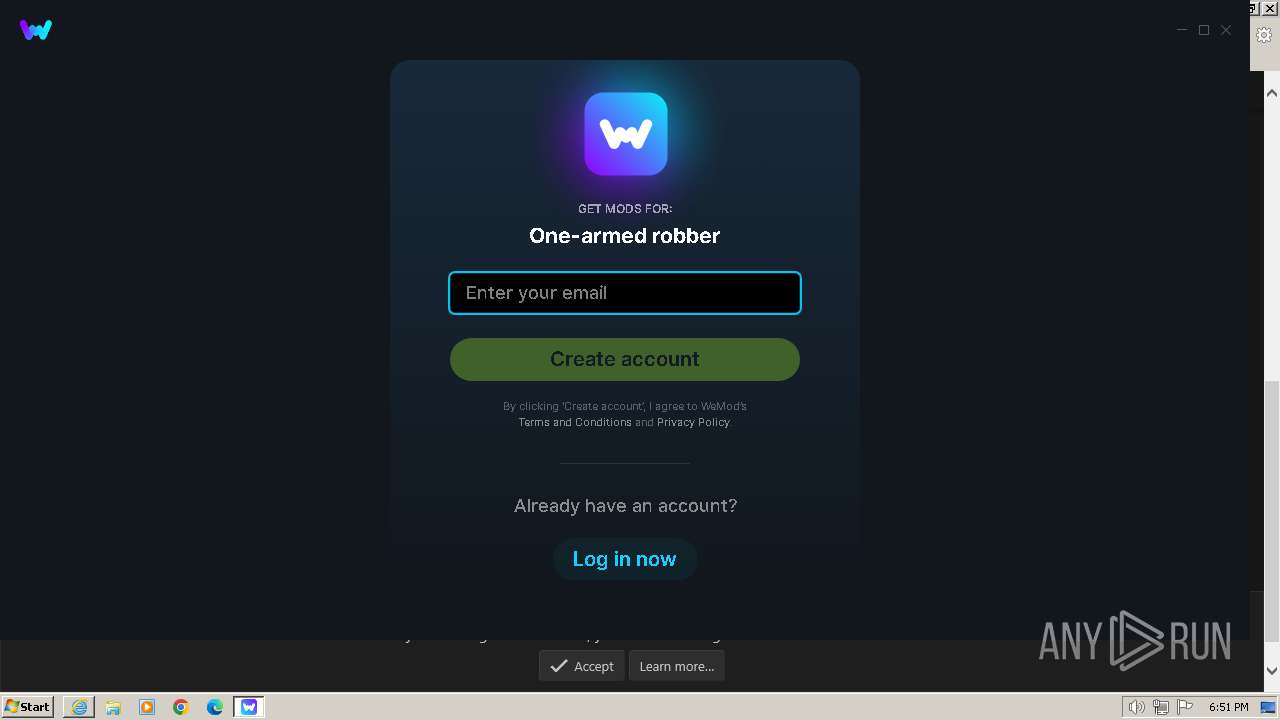
| Verdict: | Malicious activity |
| Analysis date: | December 19, 2023, 18:49:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | D9F7AA2EC79B731CD1395CB67E8BD583 |
| SHA1: | B9C6318E760FE0F5C9CE9AF7C04620EA80FEEA52 |
| SHA256: | 1D9538D060C59586A4A130A739886979EF50C78099C91389017CE303EFD64199 |
| SSDEEP: | 3:N8gwmw0GA83O:2g9w0Xn |
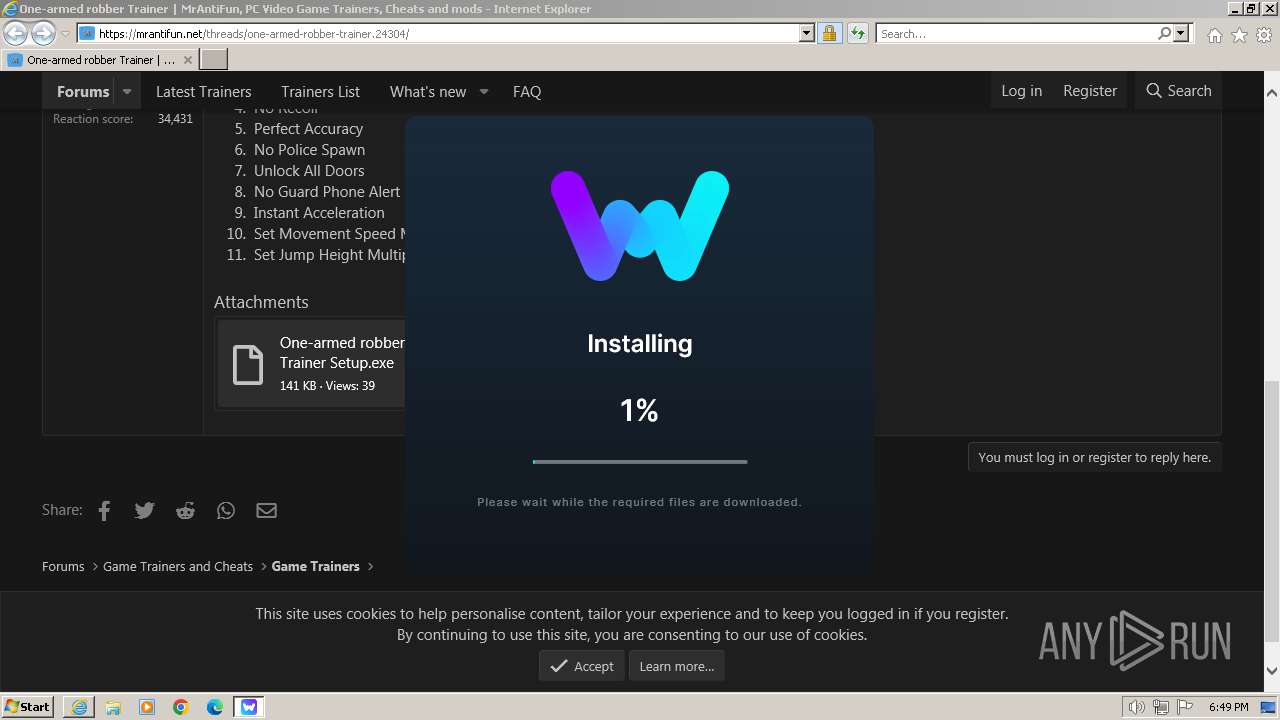
MALICIOUS
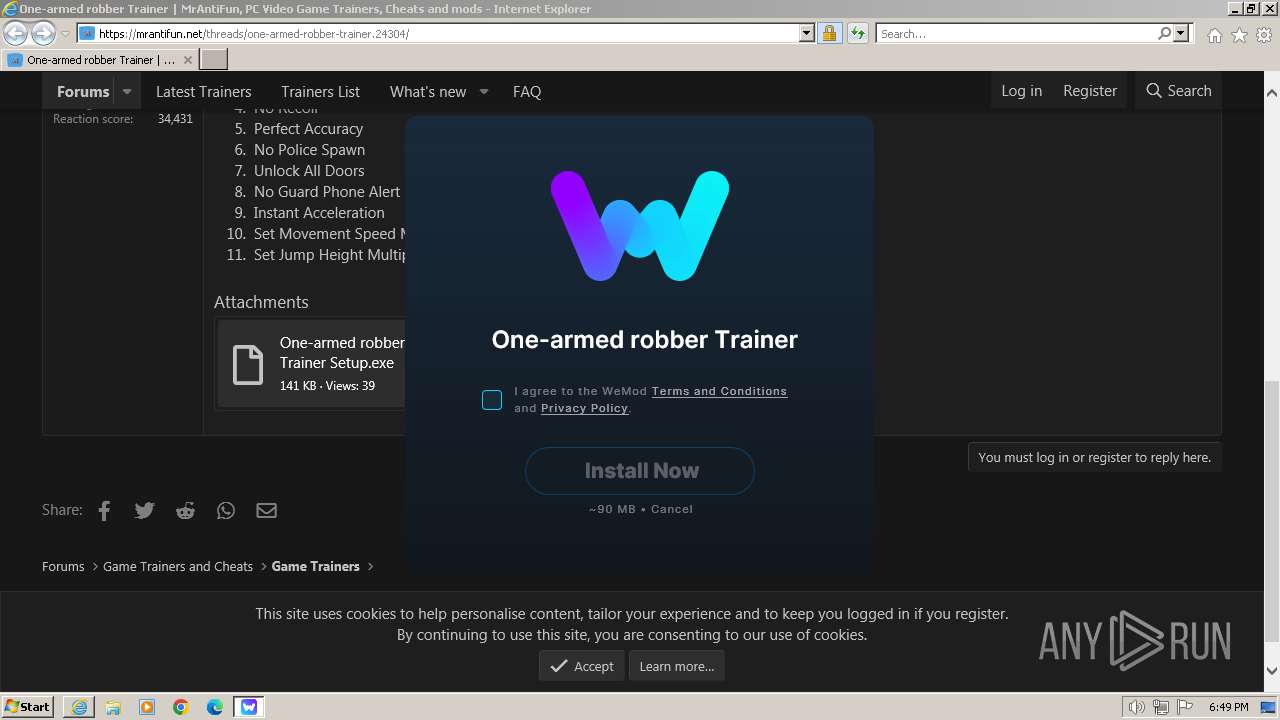
Drops the executable file immediately after the start
- WeMod-Setup-638386085936708438.exe (PID: 2816)
- Update.exe (PID: 2488)
SUSPICIOUS
Reads the Internet Settings
- One-armed robber (Steam) Trainer Setup.exe (PID: 2640)
- Update.exe (PID: 2488)
- Update.exe (PID: 3224)
- WeMod.exe (PID: 3144)
- Update.exe (PID: 4076)
Reads Microsoft Outlook installation path
- One-armed robber (Steam) Trainer Setup.exe (PID: 2640)
Reads security settings of Internet Explorer
- One-armed robber (Steam) Trainer Setup.exe (PID: 2640)
Reads settings of System Certificates
- One-armed robber (Steam) Trainer Setup.exe (PID: 2640)
- Update.exe (PID: 2488)
- WeMod.exe (PID: 3144)
- Update.exe (PID: 4076)
Reads Internet Explorer settings
- One-armed robber (Steam) Trainer Setup.exe (PID: 2640)
Checks Windows Trust Settings
- One-armed robber (Steam) Trainer Setup.exe (PID: 2640)
Process drops legitimate windows executable
- Update.exe (PID: 2488)
Application launched itself
- WeMod.exe (PID: 3144)
INFO
Checks supported languages
- One-armed robber (Steam) Trainer Setup.exe (PID: 2640)
- WeMod-Setup-638386085936708438.exe (PID: 2816)
- squirrel.exe (PID: 1220)
- Update.exe (PID: 2844)
- Update.exe (PID: 2488)
- WeMod.exe (PID: 2508)
- Update.exe (PID: 3224)
- WeMod.exe (PID: 2956)
- WeMod.exe (PID: 3144)
- WeMod.exe (PID: 3188)
- WeMod.exe (PID: 3500)
- Update.exe (PID: 4076)
- WeMod.exe (PID: 3244)
- WeModAuxiliaryService.exe (PID: 3820)
Application launched itself
- iexplore.exe (PID: 2184)
The process uses the downloaded file
- iexplore.exe (PID: 2184)
Checks proxy server information
- One-armed robber (Steam) Trainer Setup.exe (PID: 2640)
Drops the executable file immediately after the start
- iexplore.exe (PID: 2304)
- iexplore.exe (PID: 2184)
Reads the machine GUID from the registry
- One-armed robber (Steam) Trainer Setup.exe (PID: 2640)
- Update.exe (PID: 2488)
- squirrel.exe (PID: 1220)
- Update.exe (PID: 3224)
- Update.exe (PID: 2844)
- WeMod.exe (PID: 3144)
- Update.exe (PID: 4076)
- WeModAuxiliaryService.exe (PID: 3820)
Reads the computer name
- One-armed robber (Steam) Trainer Setup.exe (PID: 2640)
- Update.exe (PID: 2488)
- squirrel.exe (PID: 1220)
- Update.exe (PID: 2844)
- Update.exe (PID: 3224)
- WeMod.exe (PID: 3144)
- WeMod.exe (PID: 2956)
- WeMod.exe (PID: 3500)
- Update.exe (PID: 4076)
- WeMod.exe (PID: 3188)
- WeModAuxiliaryService.exe (PID: 3820)
Creates files or folders in the user directory
- One-armed robber (Steam) Trainer Setup.exe (PID: 2640)
- WeMod-Setup-638386085936708438.exe (PID: 2816)
- Update.exe (PID: 2488)
- squirrel.exe (PID: 1220)
- Update.exe (PID: 3224)
- WeMod.exe (PID: 3144)
- Update.exe (PID: 2844)
- WeMod.exe (PID: 3188)
- Update.exe (PID: 4076)
Reads Environment values
- One-armed robber (Steam) Trainer Setup.exe (PID: 2640)
- WeMod.exe (PID: 2508)
- WeMod.exe (PID: 3144)
- Update.exe (PID: 2488)
- Update.exe (PID: 4076)
Create files in a temporary directory
- One-armed robber (Steam) Trainer Setup.exe (PID: 2640)
- Update.exe (PID: 2488)
- WeMod.exe (PID: 3144)
- Update.exe (PID: 4076)
Reads product name
- WeMod.exe (PID: 2508)
- WeMod.exe (PID: 3144)
Process checks computer location settings
- WeMod.exe (PID: 3144)
- WeMod.exe (PID: 3244)
Reads CPU info
- WeMod.exe (PID: 3144)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
54
Monitored processes
17
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1056 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2184 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1220 | "C:\Users\admin\AppData\Local\WeMod\app-8.13.2\Squirrel.exe" --updateSelf=C:\Users\admin\AppData\Local\SquirrelTemp\Update.exe | C:\Users\admin\AppData\Local\WeMod\app-8.13.2\squirrel.exe | — | Update.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2184 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://mrantifun.net/threads/one-armed-robber-trainer.24304/" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2304 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2184 CREDAT:3020040 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2488 | "C:\Users\admin\AppData\Local\SquirrelTemp\Update.exe" --install . --silent | C:\Users\admin\AppData\Local\SquirrelTemp\Update.exe | WeMod-Setup-638386085936708438.exe | ||||||||||||
User: admin Company: GitHub Integrity Level: MEDIUM Description: Update Exit code: 0 Version: 2.0.1.23 Modules
| |||||||||||||||
| 2508 | "C:\Users\admin\AppData\Local\WeMod\app-8.13.2\WeMod.exe" --squirrel-install 8.13.2 | C:\Users\admin\AppData\Local\WeMod\app-8.13.2\WeMod.exe | — | Update.exe | |||||||||||
User: admin Company: WeMod Integrity Level: MEDIUM Description: WeMod - Cheats and Mods Exit code: 0 Version: 8.13.2 Modules
| |||||||||||||||
| 2640 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\One-armed robber (Steam) Trainer Setup.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\One-armed robber (Steam) Trainer Setup.exe | iexplore.exe | ||||||||||||
User: admin Company: WeMod LLC Integrity Level: MEDIUM Description: WeMod Setup Exit code: 0 Version: 8.0.0.0 Modules
| |||||||||||||||
| 2816 | "C:\Users\admin\AppData\Local\Temp\WeMod-Setup-638386085936708438.exe" --silent | C:\Users\admin\AppData\Local\Temp\WeMod-Setup-638386085936708438.exe | — | One-armed robber (Steam) Trainer Setup.exe | |||||||||||
User: admin Company: WeMod Integrity Level: MEDIUM Description: WeMod - Cheats and Mods Exit code: 0 Version: 8.13.2 Modules
| |||||||||||||||
| 2844 | C:\Users\admin\AppData\Local\WeMod\Update.exe --createShortcut WeMod.exe | C:\Users\admin\AppData\Local\WeMod\Update.exe | — | WeMod.exe | |||||||||||
User: admin Company: GitHub Integrity Level: MEDIUM Description: Update Exit code: 0 Version: 2.0.1.23 Modules
| |||||||||||||||
| 2956 | "C:\Users\admin\AppData\Local\WeMod\app-8.13.2\WeMod.exe" --type=gpu-process --user-data-dir="C:\Users\admin\AppData\Roaming\WeMod" --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1024 --field-trial-handle=1056,i,9771440765447595847,17629812880921782658,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:2 | C:\Users\admin\AppData\Local\WeMod\app-8.13.2\WeMod.exe | — | WeMod.exe | |||||||||||
User: admin Company: WeMod Integrity Level: LOW Description: WeMod - Cheats and Mods Exit code: 0 Version: 8.13.2 Modules
| |||||||||||||||
Total events
36 528
Read events
36 321
Write events
205
Delete events
2
Modification events
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
25
Suspicious files
142
Text files
66
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1056 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 1056 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\jquery-3.5.1.min[1].js | text | |
MD5:DC5E7F18C8D36AC1D3D4753A87C98D0A | SHA256:F7F6A5894F1D19DDAD6FA392B2ECE2C5E578CBF7DA4EA805B6885EB6985B6E3D | |||
| 1056 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:1B85D099DA4C3504A326FABE28CD6440 | SHA256:C13670B269B48759F57A5B91030C8533BAAF8E6B0D270FF8DCEA01698230036D | |||
| 1056 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\core-compiled[1].js | text | |
MD5:28D09B54E488936077C586B5D8F3B03E | SHA256:6EF90AE4C6DED80301FD8DAA7CFD472BA690821E8BA52EB2758A333AAFCA2224 | |||
| 1056 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:FC6310B5BB34BF2268FD00740F963764 | SHA256:2DB35715DCDD5D0EADFE2F21921CCC6FA50003EB16DB146F7F563FB9A0BE0265 | |||
| 1056 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\logo[1].png | image | |
MD5:338F054B5B0049D80F4F92E65B5ED204 | SHA256:F1043796FF9AA9C00395AF69C4EF311A3D297035094A6075E5BE568EDBD5E5DD | |||
| 1056 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\css[2].css | text | |
MD5:036B4567D85FBB0241B26B37155F9786 | SHA256:C444CFDB3E06C58BD845FB89276E96455410D16B128D1EFF6E425ADAAA4799F2 | |||
| 1056 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\preamble.min[1].js | text | |
MD5:3940087D344461DEC137C845EC295DAA | SHA256:B48FC223D524430EF86336E524CA8B95B74927CA840ABC04A0407B58E5905823 | |||
| 1056 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | der | |
MD5:AC89A852C2AAA3D389B2D2DD312AD367 | SHA256:0B720E19270C672F9B6E0EC40B468AC49376807DE08A814573FE038779534F45 | |||
| 1056 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\1[1].jpg | image | |
MD5:94B521965090477A1A65A4A28448CE1C | SHA256:F84B65195E79CEC94138174346A2BC8D7B06EC6EBB1B4F20D8B4915058F508D1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
64
DNS requests
32
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1056 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?7a9d8baceff24343 | unknown | compressed | 4.66 Kb | unknown |
1056 | iexplore.exe | GET | 200 | 172.217.16.195:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | binary | 1.41 Kb | unknown |
1056 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?16e53a13f7f2d96f | unknown | compressed | 4.66 Kb | unknown |
1056 | iexplore.exe | GET | 200 | 172.217.16.195:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFCjJ1PwkYAi7fE%3D | unknown | binary | 724 b | unknown |
1056 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | unknown | binary | 1.47 Kb | unknown |
1056 | iexplore.exe | GET | 200 | 172.217.16.195:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | unknown | binary | 724 b | unknown |
1056 | iexplore.exe | GET | 200 | 172.217.16.195:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCZXmpIP%2Bo%2BHhJmodADfw%2Fc | unknown | binary | 472 b | unknown |
2184 | iexplore.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?85105a2067e5fff2 | unknown | — | — | unknown |
2184 | iexplore.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?67308e0939100114 | unknown | — | — | unknown |
2184 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | unknown | binary | 313 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1056 | iexplore.exe | 104.21.96.100:443 | mrantifun.net | CLOUDFLARENET | — | unknown |
1056 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
1056 | iexplore.exe | 172.217.16.195:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
1056 | iexplore.exe | 172.217.23.104:443 | www.googletagmanager.com | GOOGLE | US | unknown |
1056 | iexplore.exe | 104.19.147.8:443 | script.crazyegg.com | CLOUDFLARENET | — | shared |
1056 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1056 | iexplore.exe | 216.239.34.36:443 | region1.google-analytics.com | GOOGLE | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mrantifun.net |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
script.crazyegg.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
region1.google-analytics.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
api.wemod.com |
| unknown |