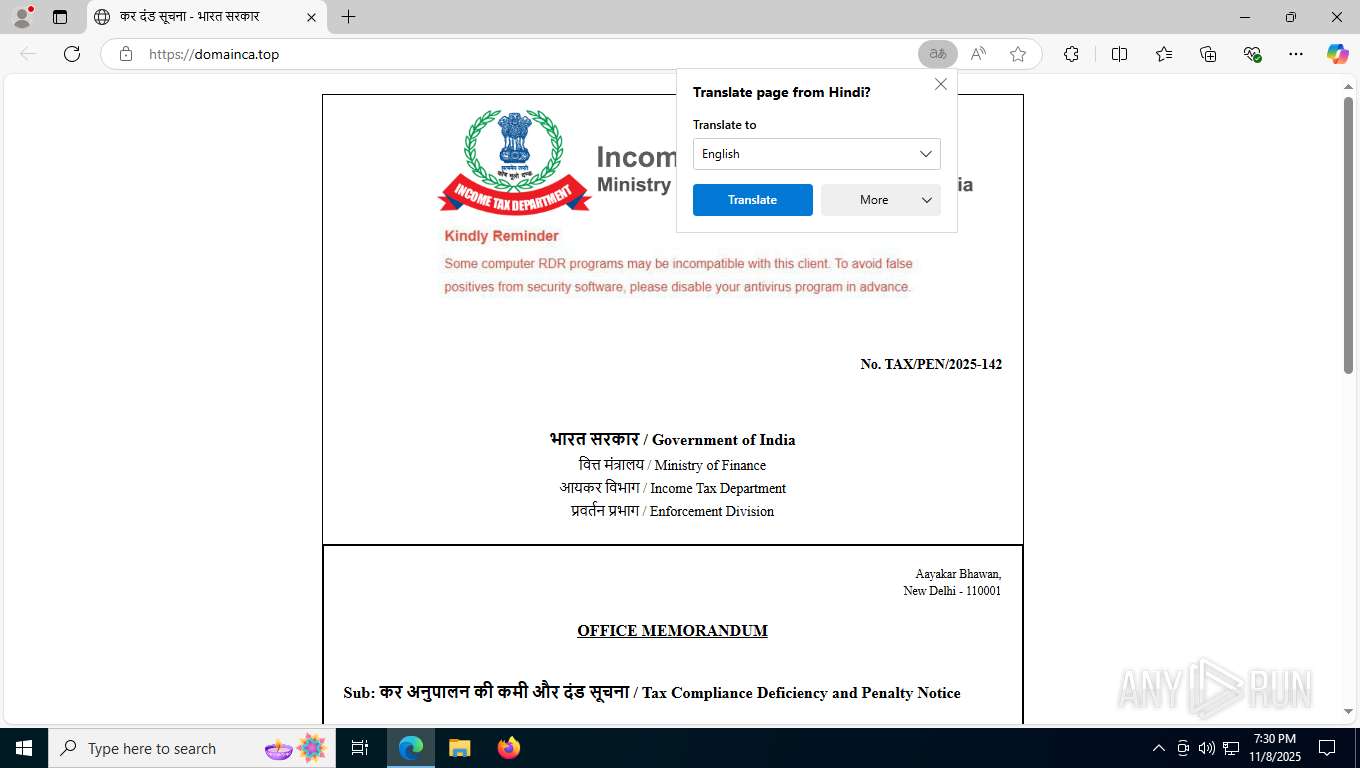
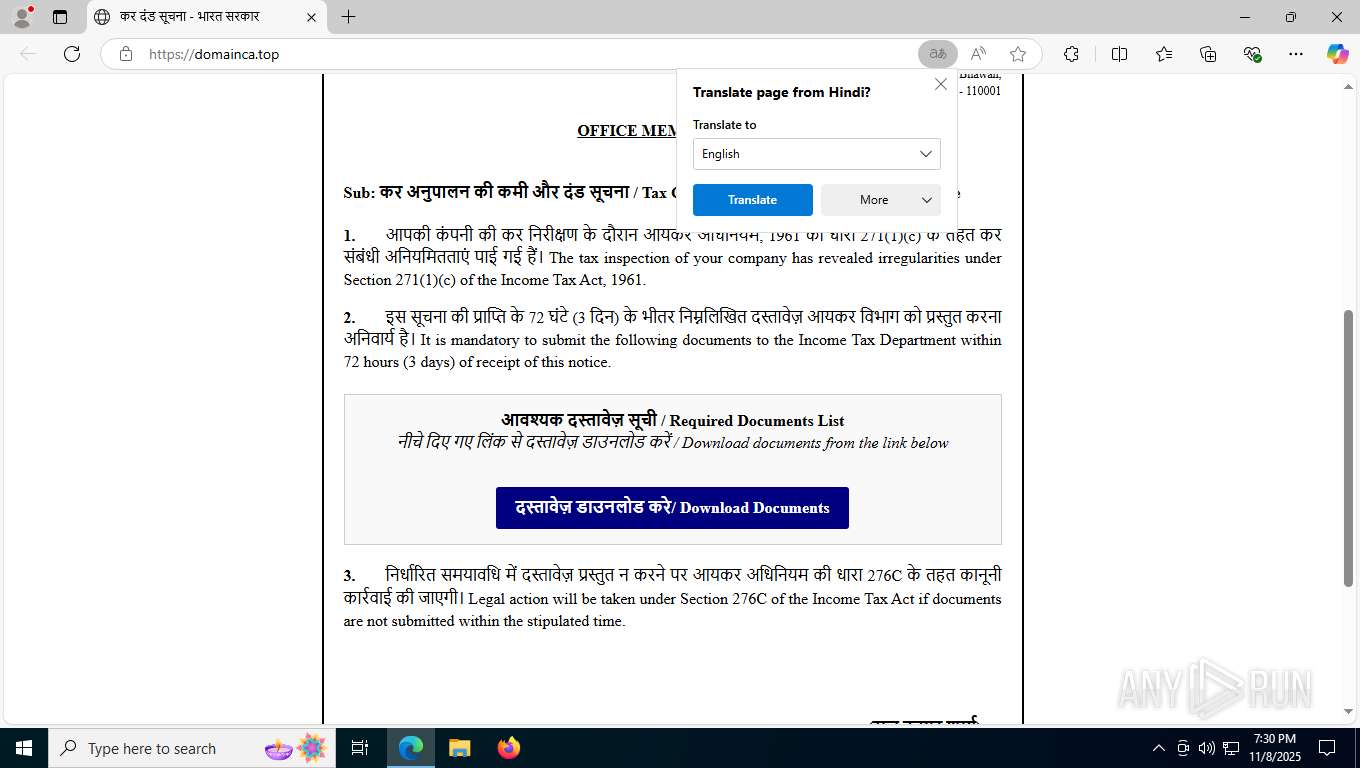
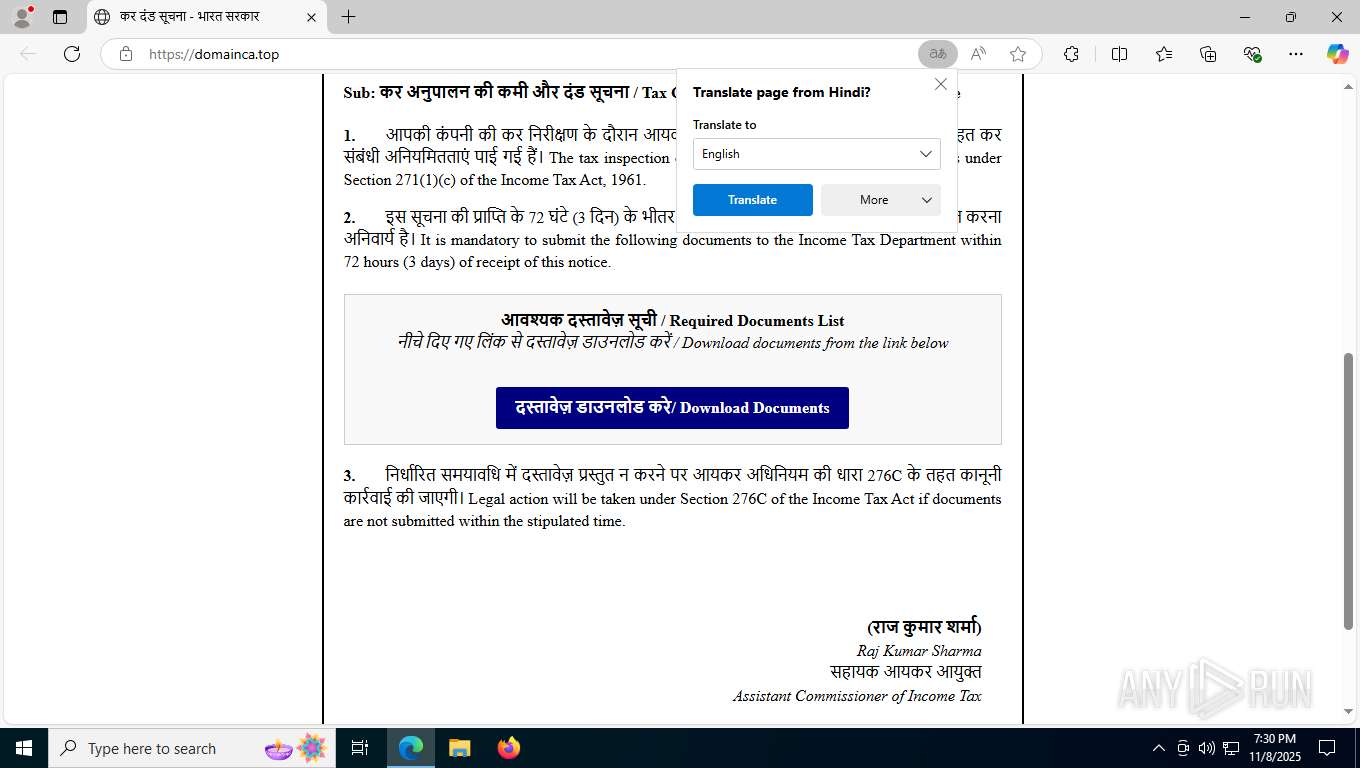
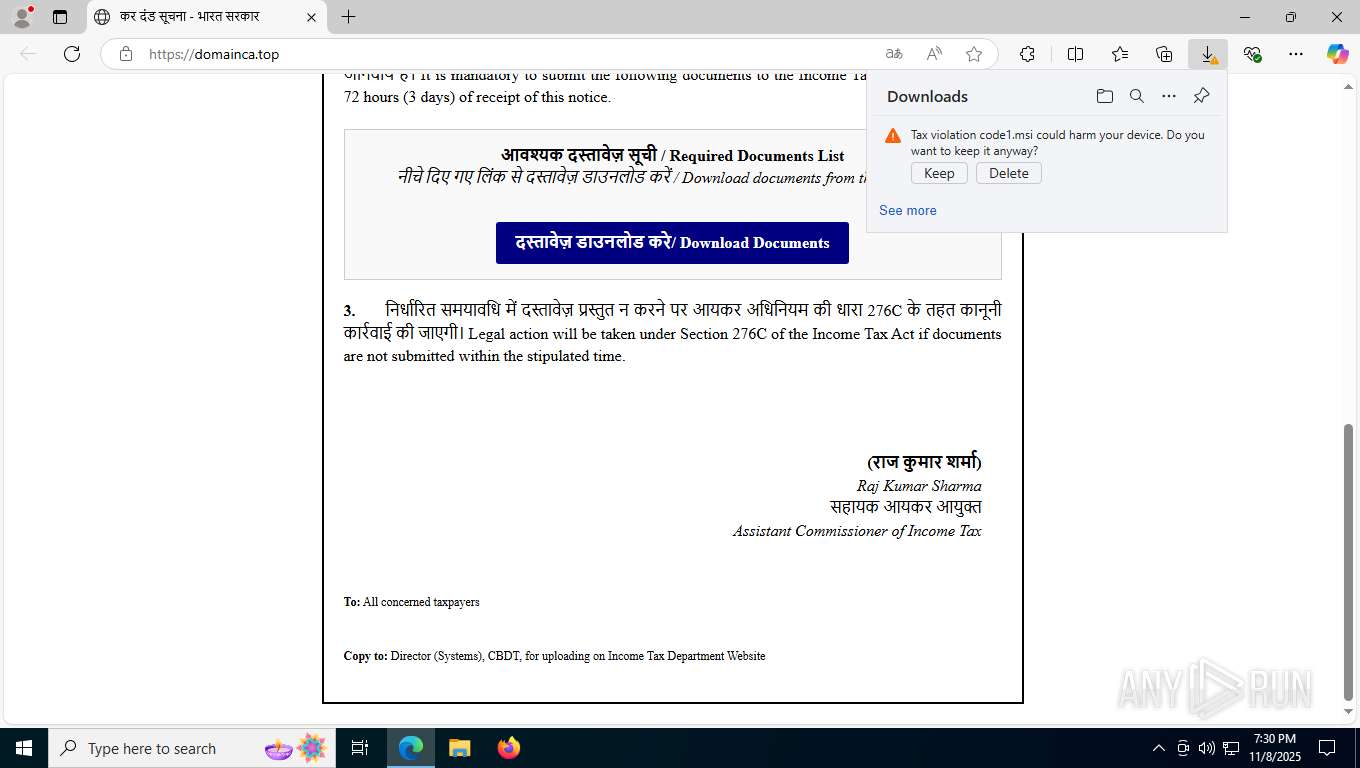
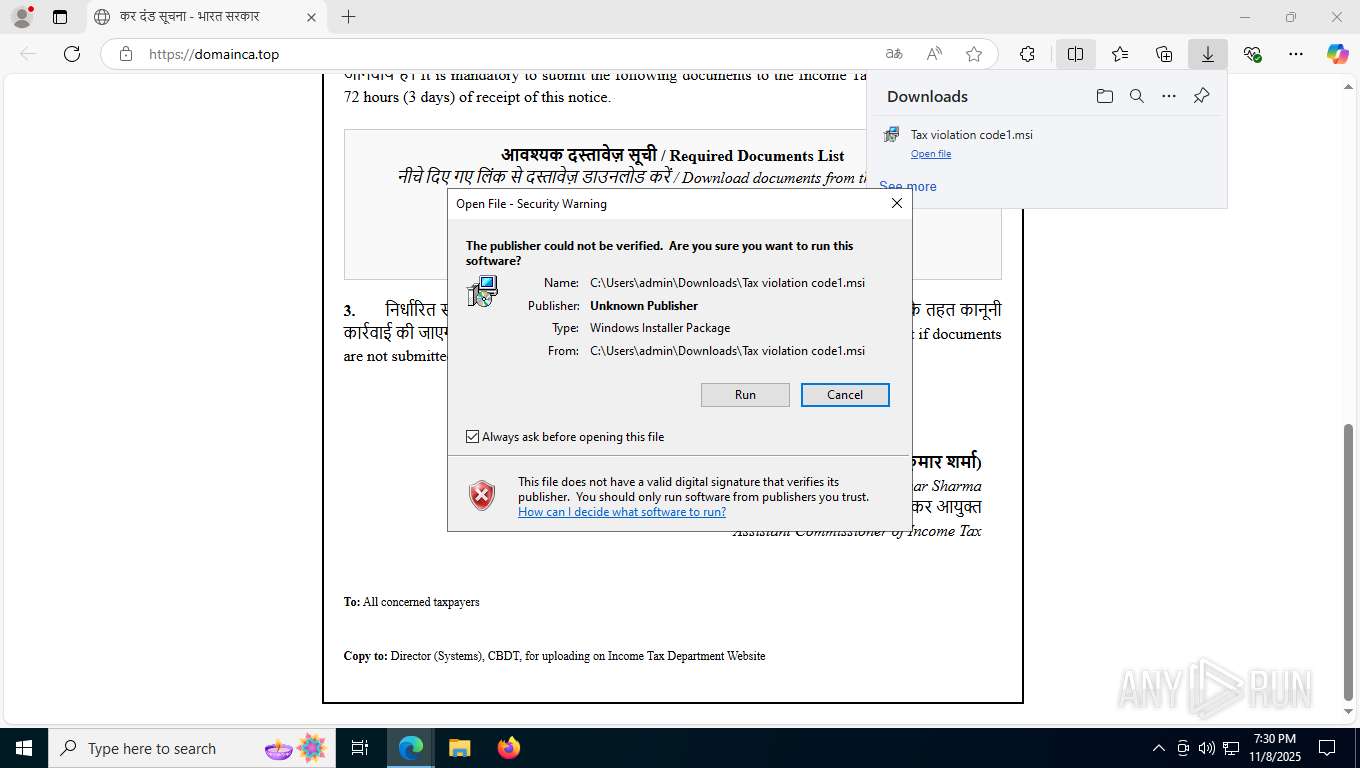
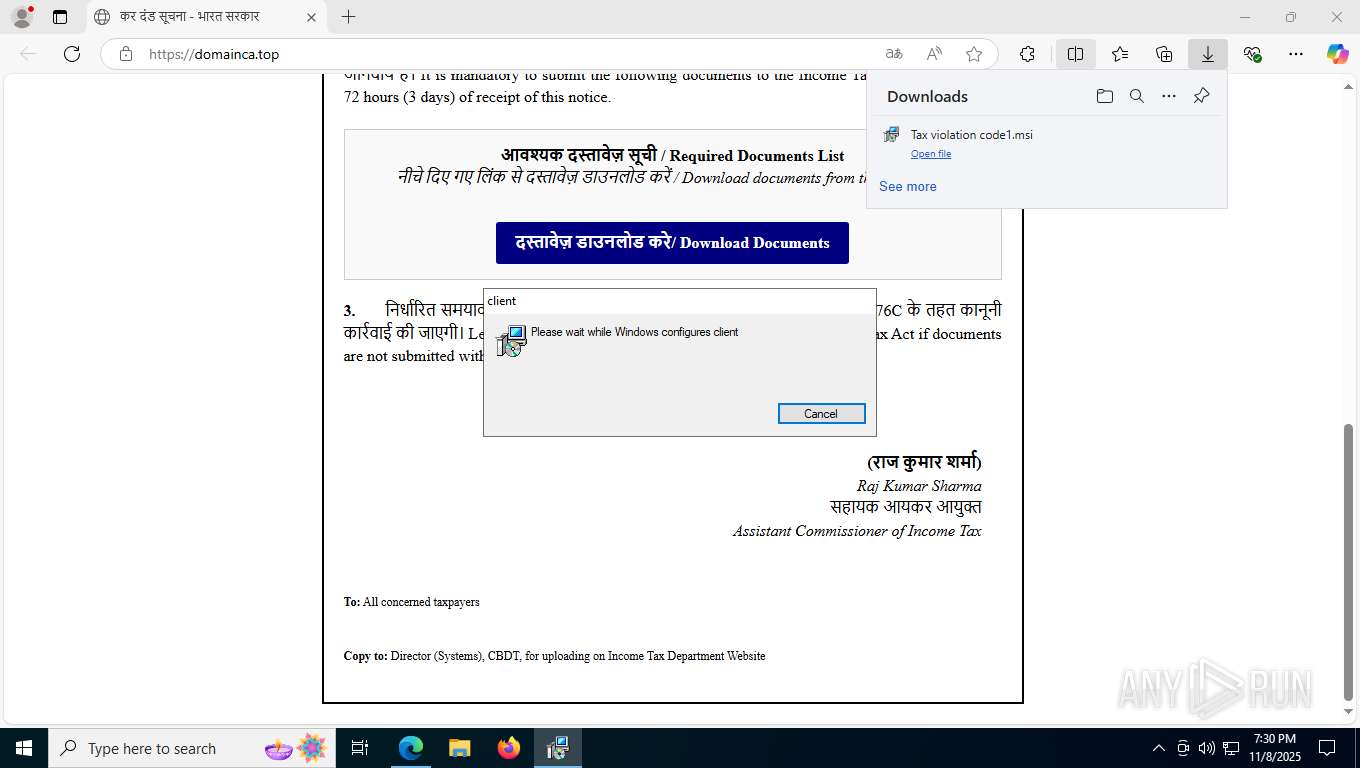
| URL: | https://domainca.top/ |
| Full analysis: | https://app.any.run/tasks/e47c7884-b18d-4b4b-bddb-6b7669c5639d |
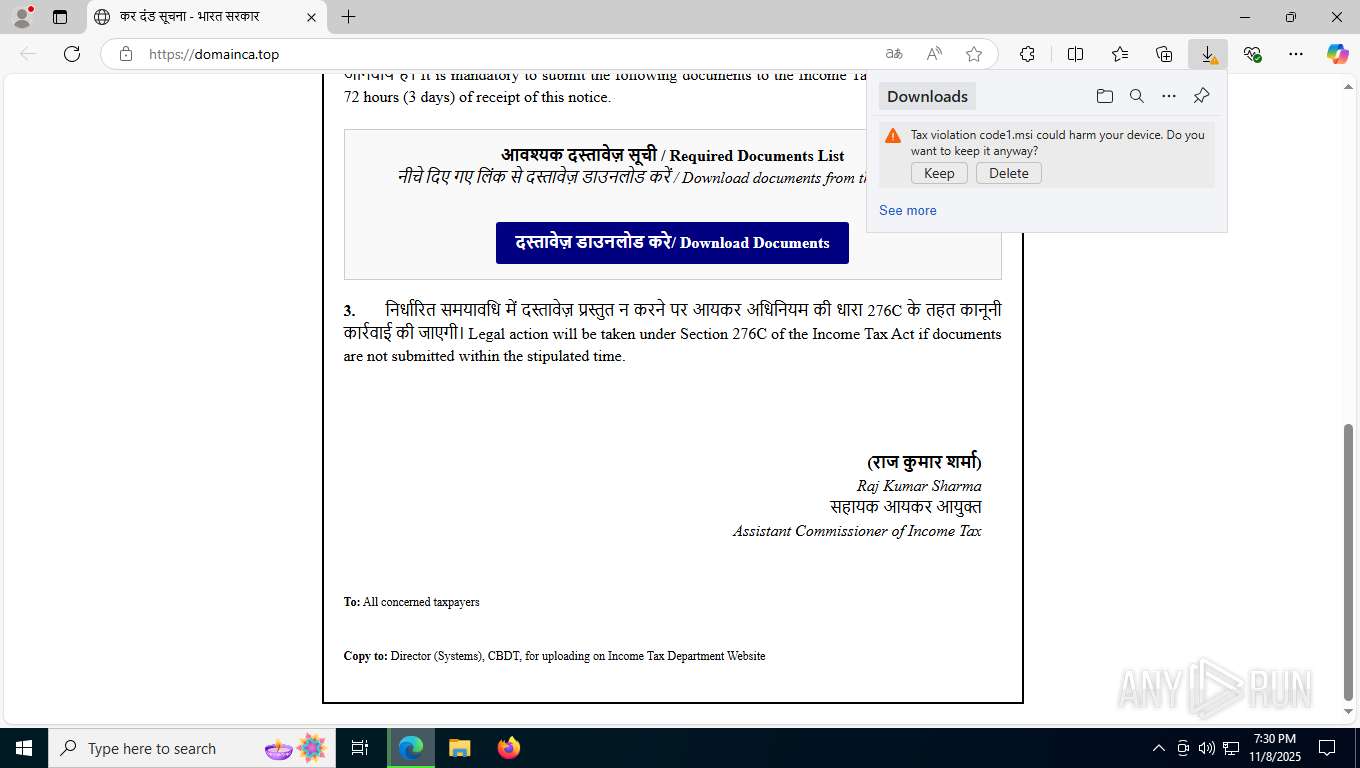
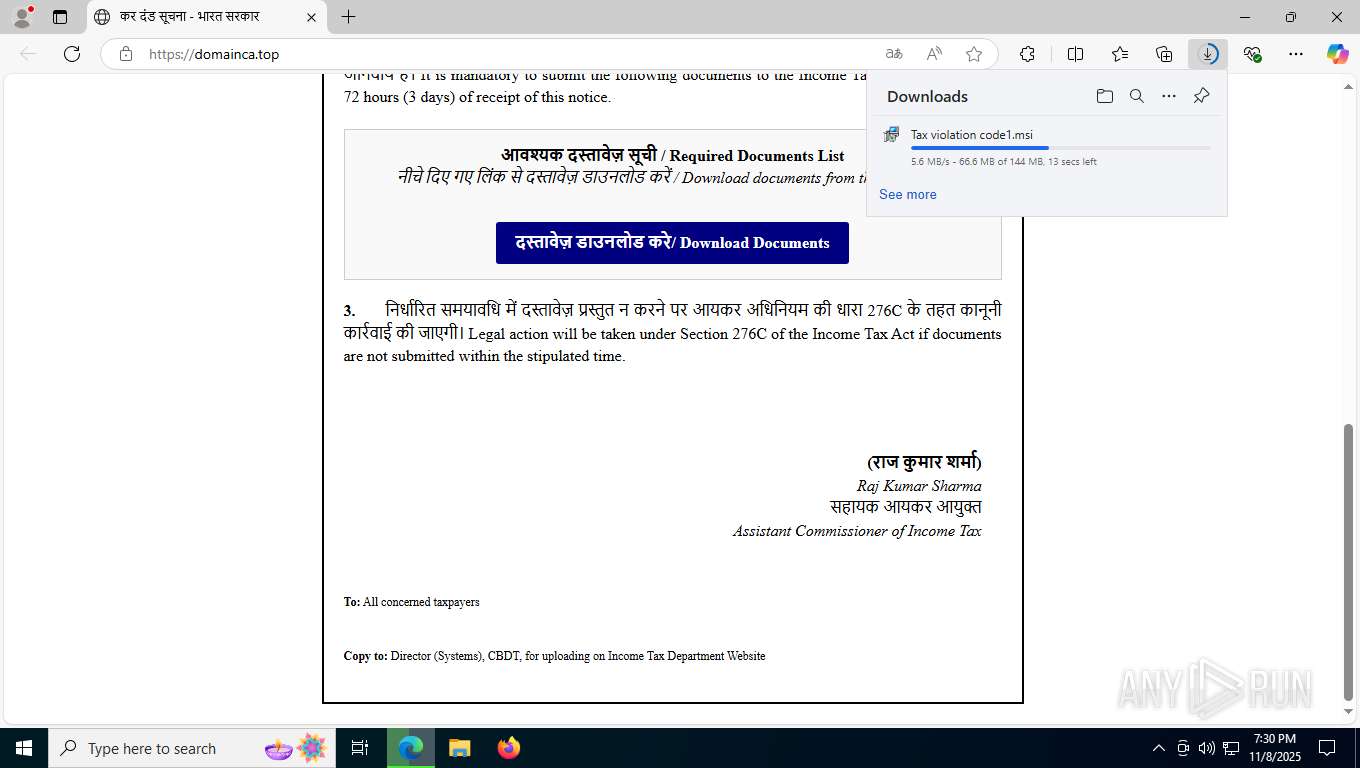
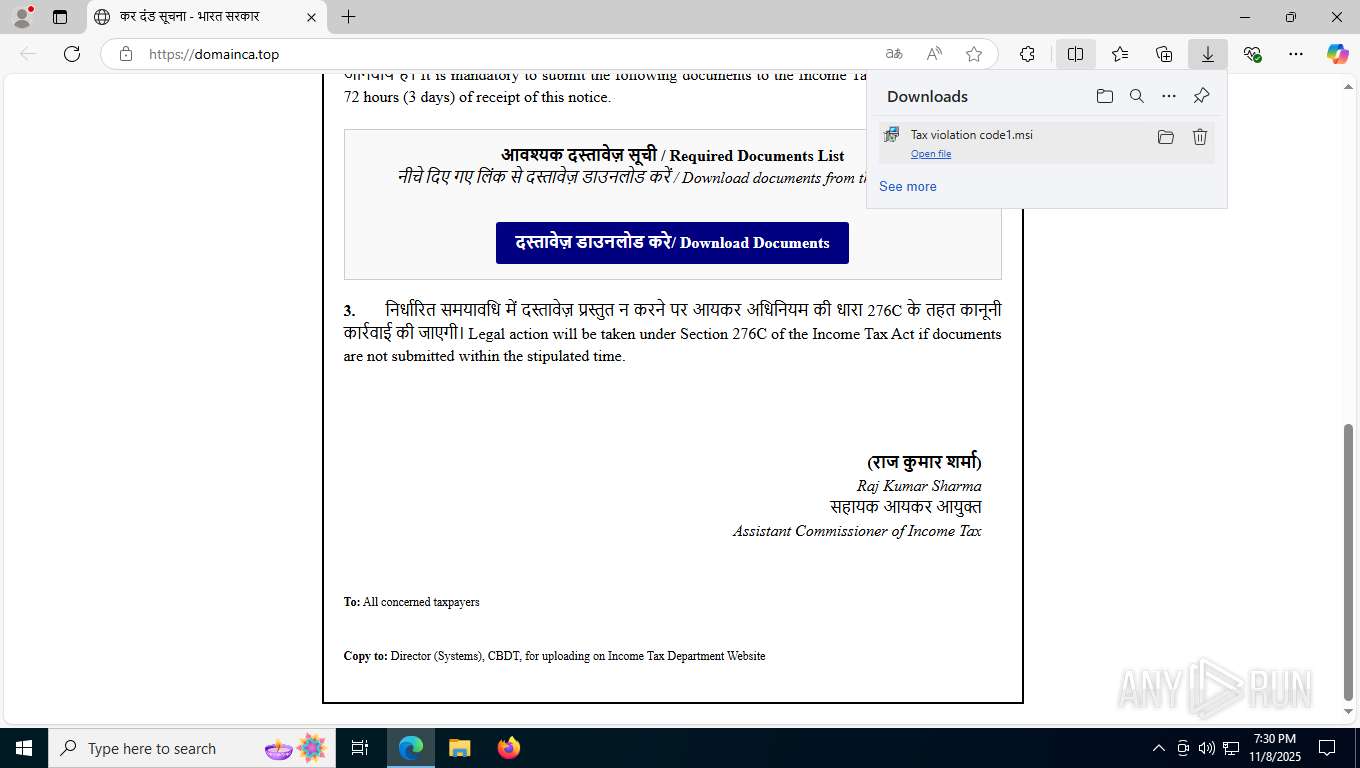
| Verdict: | Malicious activity |
| Analysis date: | November 08, 2025, 19:30:14 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | BB9D91BBB041A50004066EA75CA21034 |
| SHA1: | 680054539CA3ECAC88E54E8A076BC44A8DF622D0 |
| SHA256: | 1D951CD90DFE3C13320510D8800D1F79BD846C1E8FF61315A71C43DB1C5153B4 |
| SSDEEP: | 3:N8S5cz:2S54 |
MALICIOUS
Starts NET.EXE for service management
- NSecRTS.exe (PID: 7756)
- net.exe (PID: 2412)
- net.exe (PID: 4616)
- net.exe (PID: 920)
- net.exe (PID: 6404)
Creates or modifies Windows services
- NSecRTS.exe (PID: 7756)
Registers / Runs the DLL via REGSVR32.EXE
- NSecRTS.exe (PID: 7756)
Changes the autorun value in the registry
- rundll32.exe (PID: 592)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 1036)
- NSecRTS.exe (PID: 7756)
- NSecDs.exe (PID: 2700)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 3956)
Process drops SQLite DLL files
- client.exe (PID: 1416)
There is functionality for taking screenshot (YARA)
- client.exe (PID: 1416)
Probably fake Windows Update file has been dropped
- client.exe (PID: 1416)
Executable content was dropped or overwritten
- client.exe (PID: 1416)
- NSecRTS.exe (PID: 7756)
- rundll32.exe (PID: 592)
The process drops C-runtime libraries
- client.exe (PID: 1416)
Drops 7-zip archiver for unpacking
- client.exe (PID: 1416)
Process drops legitimate windows executable
- client.exe (PID: 1416)
The process creates files with name similar to system file names
- client.exe (PID: 1416)
Drops a system driver (possible attempt to evade defenses)
- client.exe (PID: 1416)
- rundll32.exe (PID: 592)
- drvinst.exe (PID: 6492)
Non windows owned service launched
- NSecRTS.exe (PID: 7756)
- NSecDs.exe (PID: 2700)
Application launched itself
- NSecRTS.exe (PID: 7756)
Creates or modifies Windows services
- NSecDs.exe (PID: 7424)
Windows service management via SC.EXE
- sc.exe (PID: 4720)
The process checks if it is being run in the virtual environment
- NSecRTS.exe (PID: 8040)
- NSecRTS.exe (PID: 7756)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 7188)
- regsvr32.exe (PID: 5860)
Uses RUNDLL32.EXE to load library
- NSecRTS.exe (PID: 1300)
Starts POWERSHELL.EXE for commands execution
- NSecRTS.exe (PID: 8040)
INFO
Reads Environment values
- identity_helper.exe (PID: 7260)
Checks supported languages
- identity_helper.exe (PID: 7260)
- msiexec.exe (PID: 3956)
- client.exe (PID: 1416)
- NSec.exe (PID: 7252)
- instrap.exe (PID: 1284)
- NSecRTS.exe (PID: 592)
- NSecRTS.exe (PID: 7756)
- Fixit.exe (PID: 5288)
- NSecRTS.exe (PID: 8040)
- NSecDs.exe (PID: 7424)
- NSecDs.exe (PID: 2700)
- Fixit.exe (PID: 7208)
- NSecRTS.exe (PID: 1300)
- drvinst.exe (PID: 6492)
- drvinst.exe (PID: 7248)
- NSecRTS.exe (PID: 2720)
Application launched itself
- msedge.exe (PID: 7604)
Reads the computer name
- identity_helper.exe (PID: 7260)
- msiexec.exe (PID: 3956)
- NSecRTS.exe (PID: 592)
- NSecRTS.exe (PID: 7756)
- NSecRTS.exe (PID: 8040)
- NSecDs.exe (PID: 7424)
- NSecDs.exe (PID: 2700)
- NSecRTS.exe (PID: 1300)
- drvinst.exe (PID: 7248)
- drvinst.exe (PID: 6492)
- NSecRTS.exe (PID: 2720)
Manages system restore points
- SrTasks.exe (PID: 3960)
Creates a software uninstall entry
- msiexec.exe (PID: 3956)
Creates files in the program directory
- client.exe (PID: 1416)
- NSecRTS.exe (PID: 592)
- NSecRTS.exe (PID: 7756)
- NSecRTS.exe (PID: 8040)
The sample compiled with english language support
- client.exe (PID: 1416)
- rundll32.exe (PID: 592)
- drvinst.exe (PID: 6492)
Create files in a temporary directory
- client.exe (PID: 1416)
The sample compiled with chinese language support
- client.exe (PID: 1416)
- NSecRTS.exe (PID: 7756)
Process checks whether UAC notifications are on
- NSecRTS.exe (PID: 8040)
- NSecRTS.exe (PID: 2720)
Reads Microsoft Office registry keys
- NSecRTS.exe (PID: 7756)
- NSecRTS.exe (PID: 8040)
Reads the machine GUID from the registry
- drvinst.exe (PID: 6492)
Reads the software policy settings
- drvinst.exe (PID: 6492)
- slui.exe (PID: 5388)
Launching a file from a Registry key
- rundll32.exe (PID: 592)
Reads security settings of Internet Explorer
- runonce.exe (PID: 6432)
Checks proxy server information
- slui.exe (PID: 5388)
Manual execution by a user
- cmd.exe (PID: 4264)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
239
Monitored processes
82
Malicious processes
2
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 412 | "C:\WINDOWS\System32\msiexec.exe" /i "C:\Users\admin\Downloads\Tax violation code1.msi" | C:\Windows\System32\msiexec.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 456 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5796,i,5911438768689800479,13656411941814279336,262144 --variations-seed-version --mojo-platform-channel-handle=5784 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 476 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | net.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 592 | "C:\Program Files (x86)\Common Files\NSEC\NSecRTS.exe" -i | C:\Program Files (x86)\Common Files\NSEC\NSecRTS.exe | instrap.exe | ||||||||||||
User: SYSTEM Company: XOR Co.,Ltd Integrity Level: SYSTEM Description: Endpoint Protection & DLP Real-time Service Exit code: 0 Version: 3.7.86.17889 Modules
| |||||||||||||||
| 592 | C:\WINDOWS\system32\rundll32.exe C:\WINDOWS\system32\setupapi.dll,InstallHinfSection DefaultInstall 132 C:\Program Files (x86)\Common Files\NSEC\drivers\nfsflt\nFsFlt64.inf | C:\Windows\System32\rundll32.exe | NSecRTS.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 592 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --string-annotations --gpu-preferences=UAAAAAAAAADoAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAABCAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=7524,i,5911438768689800479,13656411941814279336,262144 --variations-seed-version --mojo-platform-channel-handle=7520 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 920 | net start NSecKrnl | C:\Windows\SysWOW64\net.exe | — | NSecRTS.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1036 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1172 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6184,i,5911438768689800479,13656411941814279336,262144 --variations-seed-version --mojo-platform-channel-handle=7236 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1284 | "C:\Program Files (x86)\Common Files\NSEC\instrap.exe" | C:\Program Files (x86)\Common Files\NSEC\instrap.exe | client.exe | ||||||||||||
User: SYSTEM Company: XOR Co.,Ltd Integrity Level: SYSTEM Description: InsTrap Exit code: 0 Version: 3.7.85.17880 Modules
| |||||||||||||||
Total events
29 638
Read events
29 114
Write events
500
Delete events
24
Modification events
| (PID) Process: | (3956) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000CE608335E650DC01740F000054150000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3956) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000CE608335E650DC01740F000054150000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3956) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 48000000000000005135D935E650DC01740F000054150000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3956) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000D7D2D635E650DC01740F000054150000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3956) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000D7D2D635E650DC01740F000054150000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3956) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000D7D2D635E650DC01740F000054150000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3956) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 15 | |||
| (PID) Process: | (3956) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4800000000000000DB47EC35E650DC01740F000054150000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3956) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 480000000000000069AAEE35E650DC01740F0000981F0000E8030000010000000000000000000000A27D97642C10674083E5E7FA2CEC72DD00000000000000000000000000000000 | |||
| (PID) Process: | (1036) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000006EF8FC35E650DC010C0400009C020000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
506
Suspicious files
430
Text files
158
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7604 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF16234c.TMP | — | |
MD5:— | SHA256:— | |||
| 7604 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF16234c.TMP | — | |
MD5:— | SHA256:— | |||
| 7604 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7604 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7604 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF16234c.TMP | — | |
MD5:— | SHA256:— | |||
| 7604 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF16234c.TMP | — | |
MD5:— | SHA256:— | |||
| 7604 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7604 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF16234c.TMP | — | |
MD5:— | SHA256:— | |||
| 7604 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7604 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
84
DNS requests
69
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7056 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1762800852&P2=404&P3=2&P4=cTJRhrk32f%2b7PTSYf6O1mP2VTj80ZAJoHJDLIHOpghGuzhpCWlIII2RVTve7f9wVA0f2CZNWJygnJg0WJzuRpg%3d%3d | unknown | — | — | whitelisted |
7056 | svchost.exe | GET | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1762800852&P2=404&P3=2&P4=cTJRhrk32f%2b7PTSYf6O1mP2VTj80ZAJoHJDLIHOpghGuzhpCWlIII2RVTve7f9wVA0f2CZNWJygnJg0WJzuRpg%3d%3d | unknown | — | — | whitelisted |
7056 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/550117a4-8c0f-4d0d-8ff8-7c3caccb0e8a?P1=1762800853&P2=404&P3=2&P4=CET8iVhjASCzI1w0AZs%2biLz9aEtypS5mLui29URmF%2fn62uO2UCapsyl2czBgo1dSIOEgCDhn0V6lqkAcRG6zWA%3d%3d | unknown | — | — | whitelisted |
7056 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fa2a82d6-5b86-46d7-867a-3eb80ab6bdaf?P1=1762800852&P2=404&P3=2&P4=ju5i%2b55MZYIitUf2oQIb4VcNS%2fAMSQrREP9O7B1P84w3P3nzeyln4tqR6l8FFAfD1hVLnsCG2Oc1xSDe5xUqQw%3d%3d | unknown | — | — | whitelisted |
7056 | svchost.exe | GET | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/550117a4-8c0f-4d0d-8ff8-7c3caccb0e8a?P1=1762800853&P2=404&P3=2&P4=CET8iVhjASCzI1w0AZs%2biLz9aEtypS5mLui29URmF%2fn62uO2UCapsyl2czBgo1dSIOEgCDhn0V6lqkAcRG6zWA%3d%3d | unknown | — | — | whitelisted |
7056 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/63411b41-1268-4d16-8c76-3977581946c1?P1=1762800853&P2=404&P3=2&P4=bOHc%2b5bJaSwQuZ343IFLUCPwsprQ7IGswx6khNoxUHZhAb08%2bVIj6L5MKW53TSqBmJAIbfVqVnCArt7KPT68Yw%3d%3d | unknown | — | — | whitelisted |
7824 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:i513nrAnsYDeIczATmMchabcQR9aVcD0VJotWNA0F7k&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1552 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5596 | MoUsoCoreWorker.exe | GET | 200 | 2.16.168.199:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2880 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
7096 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5596 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1552 | svchost.exe | 40.126.32.140:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7824 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7824 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7824 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7824 | msedge.exe | 188.114.96.3:443 | domainca.top | CLOUDFLARENET | NL | whitelisted |
7824 | msedge.exe | 92.123.104.53:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
google.com |
| whitelisted |
domainca.top |
| malicious |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.india.gov.in |
| whitelisted |
xpaywalletcdn.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2276 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
— | — | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
Process | Message |
|---|---|
NSecRTS.exe | [19:32:01][PID:592 TID:7312][Level:Info]NSecRTS!ParentPID:1284, ParentPath:.
|
NSecRTS.exe | [19:32:01][PID:592 TID:7312][Level:Info]--------------------------Image:C:\Program Files (x86)\Common Files\NSEC\NSecRTS.exe Commandline:-i Version:3.7.86.17889--------------------------
|
NSecRTS.exe | [19:32:01][PID:7756 TID:5476][Level:Info]NSecRTS!ParentPID:788, ParentPath:C:\Windows\System32\services.exe.
|
NSecRTS.exe | [19:32:01][PID:7756 TID:1384][Level:Info]NSecRTS!Service!Start NSEC service...
|
NSecRTS.exe | [19:32:01][PID:7756 TID:5476][Level:Info]--------------------------Image:C:\Program Files (x86)\Common Files\NSEC\NSecRTS.exe Commandline:-r Version:3.7.86.17889--------------------------
|
NSecRTS.exe | [19:32:01][PID:7756 TID:2576][Level:Info]NSecRTS!UpdateService!UpdateThread 2576 will check and update after 481 sec
|
NSecRTS.exe | [19:32:01][PID:7756 TID:7352][Level:Info]NSecRTS!Update!Wait for fixit exit.
|
NSecRTS.exe | [19:32:01][PID:7756 TID:7352][Level:Info]NSecRTS!Update!Fixit has exited.
|
NSecRTS.exe | [19:32:01][PID:7756 TID:2768][Level:Info]FileChangedNotify!Start file changed monitor thread C:\
|
NSecRTS.exe | [19:32:01][PID:7756 TID:7352][Level:Info]NFPCore!InitNFPService.
|