| URL: | https://mcas-proxyweb.mcas.ms/certificate-checker?login=false&originalUrl=https%3A%2F%2Fter943552066-my.sharepoint.com.mcas.ms%2F%3Ao%3A%2Fg%2Fpersonal%2Fa_martin_agui_com%2FIgDLuPOli_RHSKE55cln3z9MAfLiUtVukmlumlpusVTZgnc%3Fe%3DBdwSDY%26xsdata%3DMDV8MDJ8YWxiZXJ0by5zZWxpbmdlQHZpYWNlbGVyZS5lc3wyNjg0YWNmYWVjNjY0ZmIxZDEwNjA4ZGU1NDBkODM4MHxmZGI2NzZlOTJmNTE0NzkyODQyNmJhMDY3ODRkNmQ3ZnwwfDB8NjM5MDQwNjE0NDA3NTYzNTE4fFVua25vd258VFdGcGJHWnNiM2Q4ZXlKRmJYQjBlVTFoY0draU9uUnlkV1VzSWxZaU9pSXdMakF1TURBd01DSXNJbEFpT2lKWGFXNHpNaUlzSWtGT0lqb2lUV0ZwYkNJc0lsZFVJam95ZlE9PXwwfHx8%26sdata%3DMURqYTRWcHNGZ2dsNmEwbnRJaU5OdFdxcW1BSENKOVFqSzNxQTlXSGFZcz0%253d%26McasTsid%3D20893&McasCSRF=c22892d2a8f77033706bf6d0d893558b8683951eefa74d3077f00fbaa4bcca40 |
| Full analysis: | https://app.any.run/tasks/936a23fa-22b4-422b-8604-5b248b10bbb5 |
| Verdict: | Malicious activity |
| Analysis date: | January 16, 2026, 08:32:31 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 45F2D9D001522B8B4C364DB3BE788228 |
| SHA1: | 0304821CB9A94F9F2635C6A9AD04F177EF79F5CB |
| SHA256: | 1D8B2C3BCD1F976CFB19DADE41221D6BD7A61D4F48A3B5E1398B17D376388F96 |
| SSDEEP: | 12:2CQNo7qgduCIGKWky8/2d/MB1dpM/gDpUSUnNvwkSQkZUDu7hbdtb/MWAlXBfdUY:2Cl7qEYygE+x2OGLnNok7kZUq7/hMDRh |
MALICIOUS
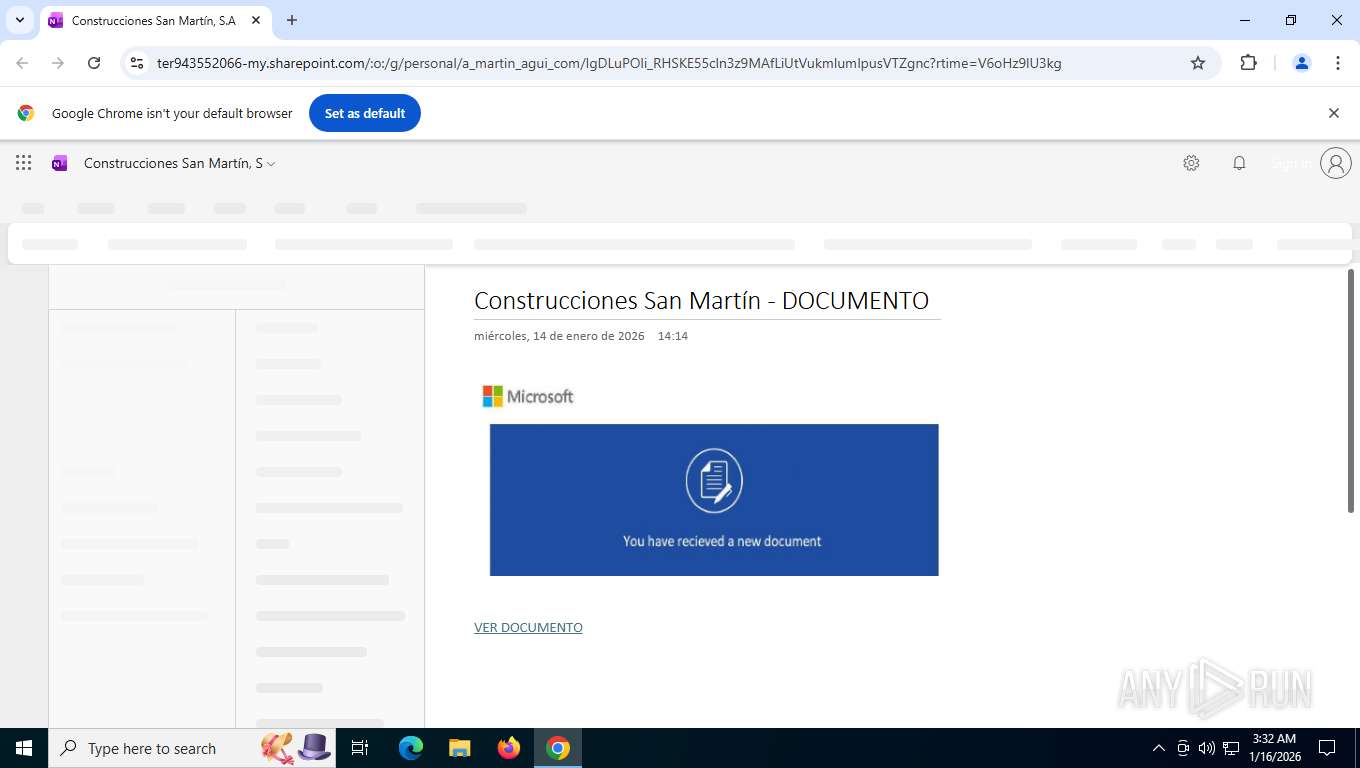
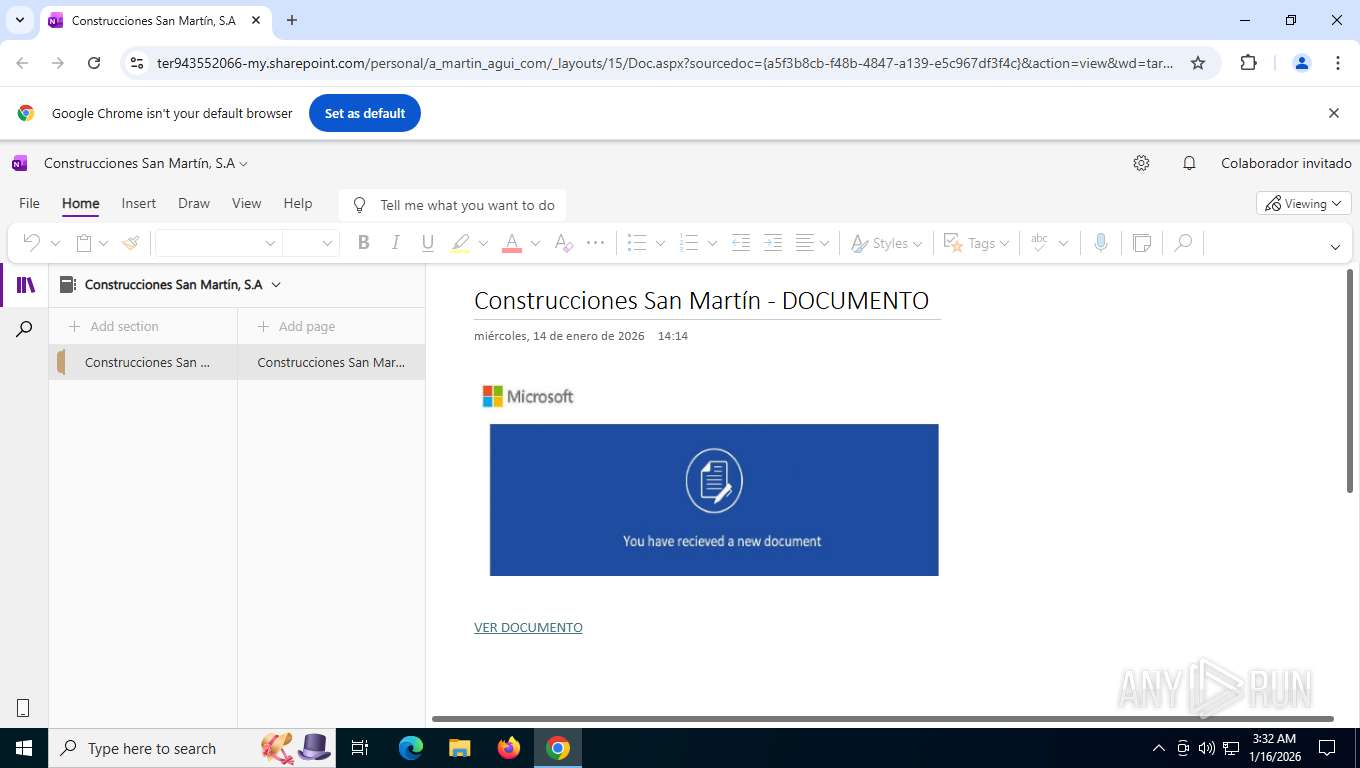
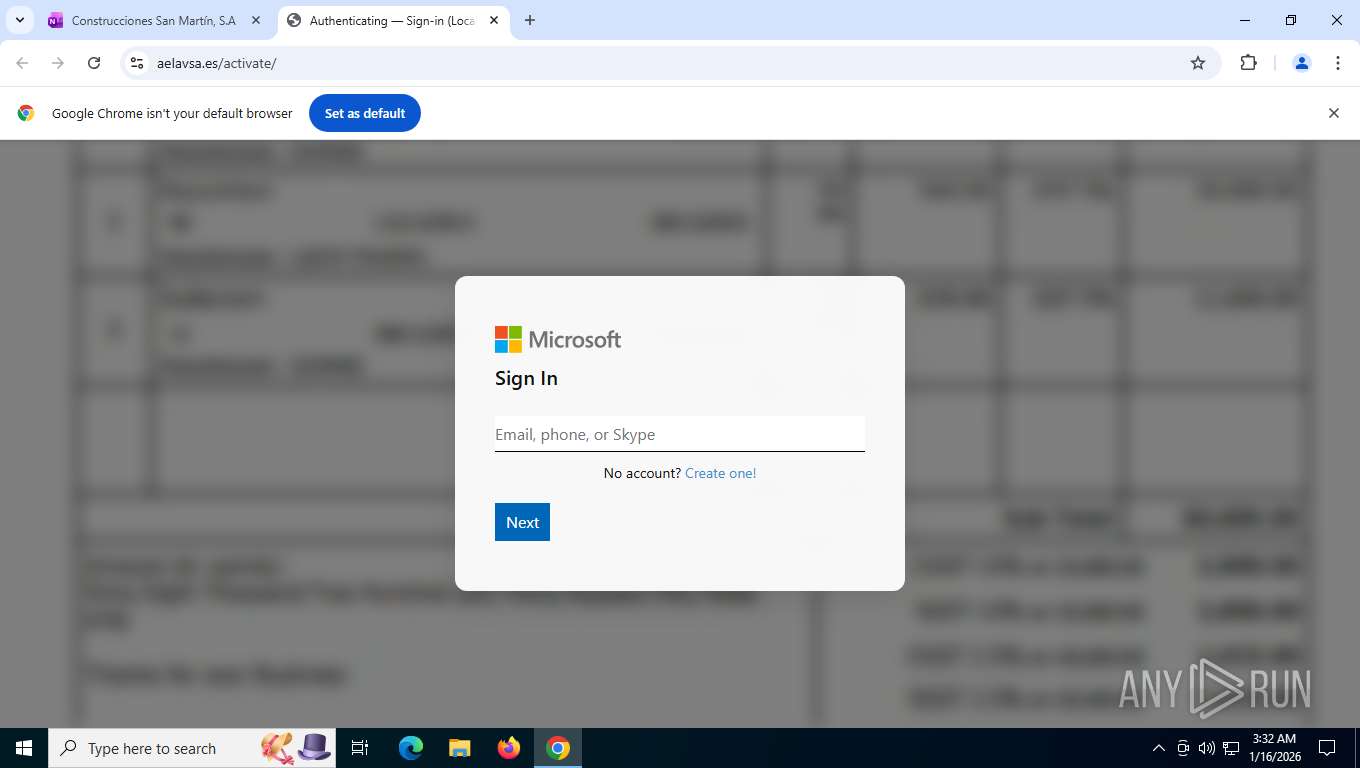
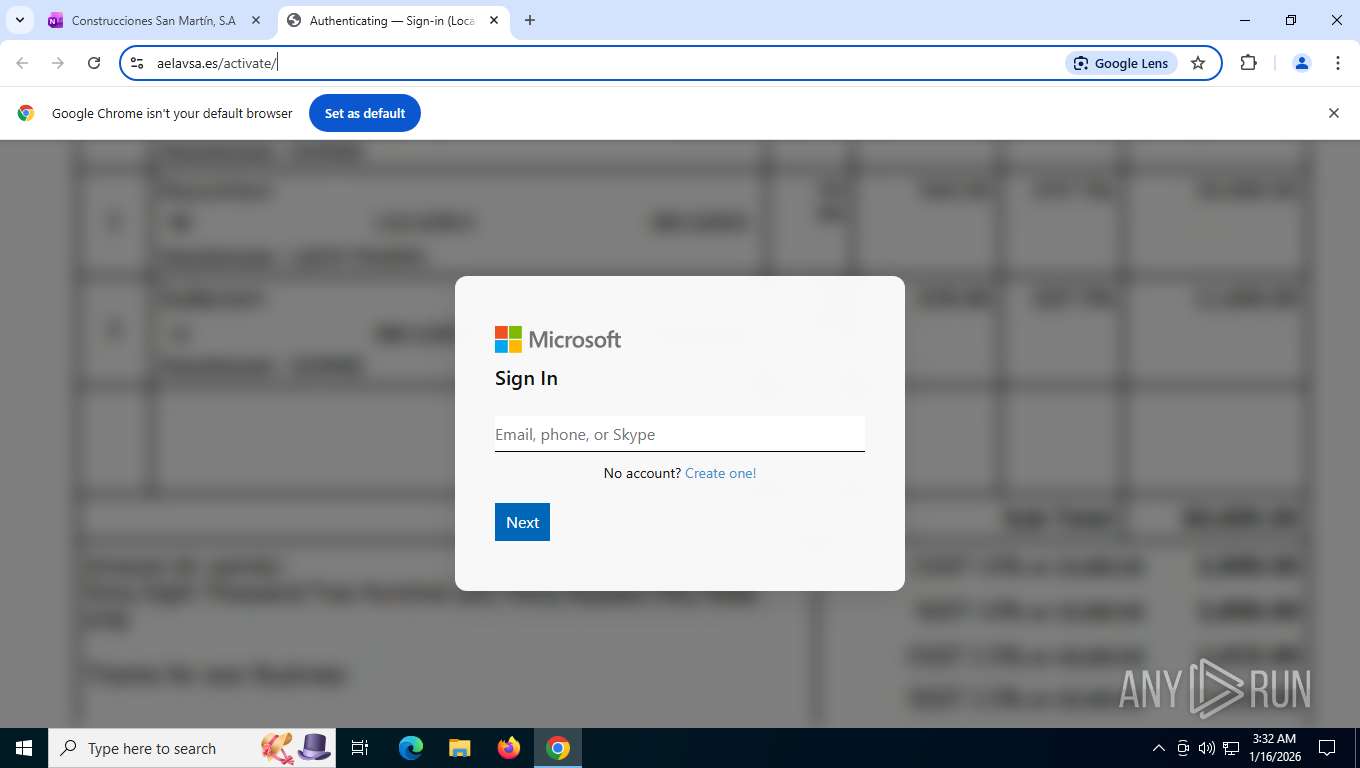
Fake Microsoft Authentication Page has been detected
- chrome.exe (PID: 7480)
PHISHING has been detected (SURICATA)
- chrome.exe (PID: 7740)
SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 7480)
Drops script file
- chrome.exe (PID: 7480)
Reads the computer name
- TextInputHost.exe (PID: 6188)
Checks supported languages
- TextInputHost.exe (PID: 6188)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
160
Monitored processes
16
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=12 --field-trial-handle=4616,i,1834686398798188161,12079886336112681111,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=4628 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2900 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=10 --field-trial-handle=3296,i,1834686398798188161,12079886336112681111,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=3328 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2912 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=4620,i,1834686398798188161,12079886336112681111,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=4632 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 6188 | "C:\WINDOWS\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe" -ServerName:InputApp.AppXjd5de1g66v206tj52m9d0dtpppx4cgpn.mca | C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Version: 123.26505.0.0 Modules
| |||||||||||||||
| 6944 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7424 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=9 --field-trial-handle=4236,i,1834686398798188161,12079886336112681111,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=3848 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 7480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "https://mcas-proxyweb.mcas.ms/certificate-checker?login=false&originalUrl=https%3A%2F%2Fter943552066-my.sharepoint.com.mcas.ms%2F%3Ao%3A%2Fg%2Fpersonal%2Fa_martin_agui_com%2FIgDLuPOli_RHSKE55cln3z9MAfLiUtVukmlumlpusVTZgnc%3Fe%3DBdwSDY%26xsdata%3DMDV8MDJ8YWxiZXJ0by5zZWxpbmdlQHZpYWNlbGVyZS5lc3wyNjg0YWNmYWVjNjY0ZmIxZDEwNjA4ZGU1NDBkODM4MHxmZGI2NzZlOTJmNTE0NzkyODQyNmJhMDY3ODRkNmQ3ZnwwfDB8NjM5MDQwNjE0NDA3NTYzNTE4fFVua25vd258VFdGcGJHWnNiM2Q4ZXlKRmJYQjBlVTFoY0draU9uUnlkV1VzSWxZaU9pSXdMakF1TURBd01DSXNJbEFpT2lKWGFXNHpNaUlzSWtGT0lqb2lUV0ZwYkNJc0lsZFVJam95ZlE9PXwwfHx8%26sdata%3DMURqYTRWcHNGZ2dsNmEwbnRJaU5OdFdxcW1BSENKOVFqSzNxQTlXSGFZcz0%253d%26McasTsid%3D20893&McasCSRF=c22892d2a8f77033706bf6d0d893558b8683951eefa74d3077f00fbaa4bcca40" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 7584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=133.0.6943.127 --initial-client-data=0x21c,0x220,0x224,0x1f8,0x228,0x7ffd7198fff8,0x7ffd71990004,0x7ffd71990010 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 7728 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgABAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --field-trial-handle=1464,i,1834686398798188161,12079886336112681111,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=1852 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 7740 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=2060,i,1834686398798188161,12079886336112681111,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=2068 /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
Total events
621
Read events
621
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
8
Text files
37
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RFfdd09.TMP | — | |
MD5:— | SHA256:— | |||
| 7480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old~RFfdd18.TMP | — | |
MD5:— | SHA256:— | |||
| 7480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RFfdd18.TMP | — | |
MD5:— | SHA256:— | |||
| 7480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SignalDB\LOG.old~RFfdd28.TMP | — | |
MD5:— | SHA256:— | |||
| 7480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SignalDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RFfdd18.TMP | — | |
MD5:— | SHA256:— | |||
| 7480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RFfdd28.TMP | — | |
MD5:— | SHA256:— | |||
| 7480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
250
TCP/UDP connections
94
DNS requests
114
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7740 | chrome.exe | GET | 200 | 142.251.140.174:80 | http://clients2.google.com/time/1/current?cup2key=8:1K4FYGlxFA2OkhyMByv1Tr5JBDc-LMfqF39oPjNxEM0&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 105 b | whitelisted |
7740 | chrome.exe | POST | 200 | 74.125.206.84:443 | https://accounts.google.com/ListAccounts?gpsia=1&source=ChromiumBrowser&json=standard | US | text | 17 b | whitelisted |
7740 | chrome.exe | GET | 302 | 13.107.136.10:443 | https://ter943552066-my.sharepoint.com/:o:/g/personal/a_martin_agui_com/IgDLuPOli_RHSKE55cln3z9MAfLiUtVukmlumlpusVTZgnc | US | html | 584 b | unknown |
7740 | chrome.exe | GET | 307 | 20.90.50.115:443 | https://mcas-proxyweb.mcas.ms/certificate-checker?login=false&originalUrl=https%3A%2F%2Fter943552066-my.sharepoint.com.mcas.ms%2F%3Ao%3A%2Fg%2Fpersonal%2Fa_martin_agui_com%2FIgDLuPOli_RHSKE55cln3z9MAfLiUtVukmlumlpusVTZgnc%3Fe%3DBdwSDY%26xsdata%3DMDV8MDJ8YWxiZXJ0by5zZWxpbmdlQHZpYWNlbGVyZS5lc3wyNjg0YWNmYWVjNjY0ZmIxZDEwNjA4ZGU1NDBkODM4MHxmZGI2NzZlOTJmNTE0NzkyODQyNmJhMDY3ODRkNmQ3ZnwwfDB8NjM5MDQwNjE0NDA3NTYzNTE4fFVua25vd258VFdGcGJHWnNiM2Q4ZXlKRmJYQjBlVTFoY0draU9uUnlkV1VzSWxZaU9pSXdMakF1TURBd01DSXNJbEFpT2lKWGFXNHpNaUlzSWtGT0lqb2lUV0ZwYkNJc0lsZFVJam95ZlE9PXwwfHx8%26sdata%3DMURqYTRWcHNGZ2dsNmEwbnRJaU5OdFdxcW1BSENKOVFqSzNxQTlXSGFZcz0%253d%26McasTsid%3D20893&McasCSRF=c22892d2a8f77033706bf6d0d893558b8683951eefa74d3077f00fbaa4bcca40 | US | html | 233 b | unknown |
7740 | chrome.exe | GET | 200 | 13.107.136.10:443 | https://ter943552066-my.sharepoint.com/personal/a_martin_agui_com/_layouts/15/Doc.aspx?sourcedoc=%7Ba5f3b8cb-f48b-4847-a139-e5c967df3f4c%7D&action=default&slrid=c381eda1-60be-a000-e800-5cd09ee3b2db&originalPath=aHR0cHM6Ly90ZXI5NDM1NTIwNjYtbXkuc2hhcmVwb2ludC5jb20vOm86L2cvcGVyc29uYWwvYV9tYXJ0aW5fYWd1aV9jb20vSWdETHVQT2xpX1JIU0tFNTVjbG4zejlNQWZMaVV0VnVrbWx1bWxwdXNWVFpnbmM_cnRpbWU9VjZvSHo5bFUza2c&CID=7f6ecfb7-340b-4ff5-9f43-cda65500169f&_SRM=0:G:81 | US | html | 128 Kb | unknown |
7740 | chrome.exe | GET | 200 | 172.217.18.10:443 | https://safebrowsingohttpgateway.googleapis.com/v1/ohttp/hpkekeyconfig?key=AIzaSyA2KlwBX3mkFo30om9LUFYQhpqLoa_BNhE | US | binary | 41 b | whitelisted |
7740 | chrome.exe | GET | 200 | 23.53.40.33:443 | https://res-1.cdn.office.net/wise/owl/owl.slim.d528a860fa2ed22853ba.js | NL | text | 128 Kb | whitelisted |
7740 | chrome.exe | POST | 200 | 52.108.9.12:443 | https://common.online.office.com/suite/RemoteUls.ashx?usid=96aae7f9-f3ca-7e98-c2e8-055eea471039&officeserverversion= | US | — | — | unknown |
7740 | chrome.exe | GET | 200 | 23.53.40.33:443 | https://res-1.cdn.office.net/files/sp-client/odsp.1ds/odsp.1ds.lib-06dc458f.js | NL | text | 128 Kb | whitelisted |
7740 | chrome.exe | POST | 200 | 52.108.9.12:443 | https://euc-onenote.officeapps.live.com/o/RemoteUls.ashx?usid=96aae7f9-f3ca-7e98-c2e8-055eea471039&officeserverversion= | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4288 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6768 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1848 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7740 | chrome.exe | 142.251.140.174:80 | clients2.google.com | GOOGLE | US | whitelisted |
7740 | chrome.exe | 172.217.18.10:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
7740 | chrome.exe | 20.90.50.115:443 | mcas-proxyweb.mcas.ms | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7740 | chrome.exe | 74.125.206.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
7740 | chrome.exe | 13.107.136.10:443 | ter943552066-my.sharepoint.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
mcas-proxyweb.mcas.ms |
| whitelisted |
accounts.google.com |
| whitelisted |
ter943552066-my.sharepoint.com |
| whitelisted |
res-1.cdn.office.net |
| whitelisted |
euc-onenote.officeapps.live.com |
| whitelisted |
common.online.office.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7740 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to SharePoint public/private file sharing TLS SNI (.sharepoint .com) |
7740 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to SharePoint public/private file sharing DNS (.sharepoint .com) |
7740 | chrome.exe | Misc activity | INFO [ANY.RUN] Accessing SharePoint content without a legitimate Microsoft Sign-In |
7740 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7740 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7740 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7740 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7740 | chrome.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing Domain (aelavsa .es) |
7740 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7740 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |