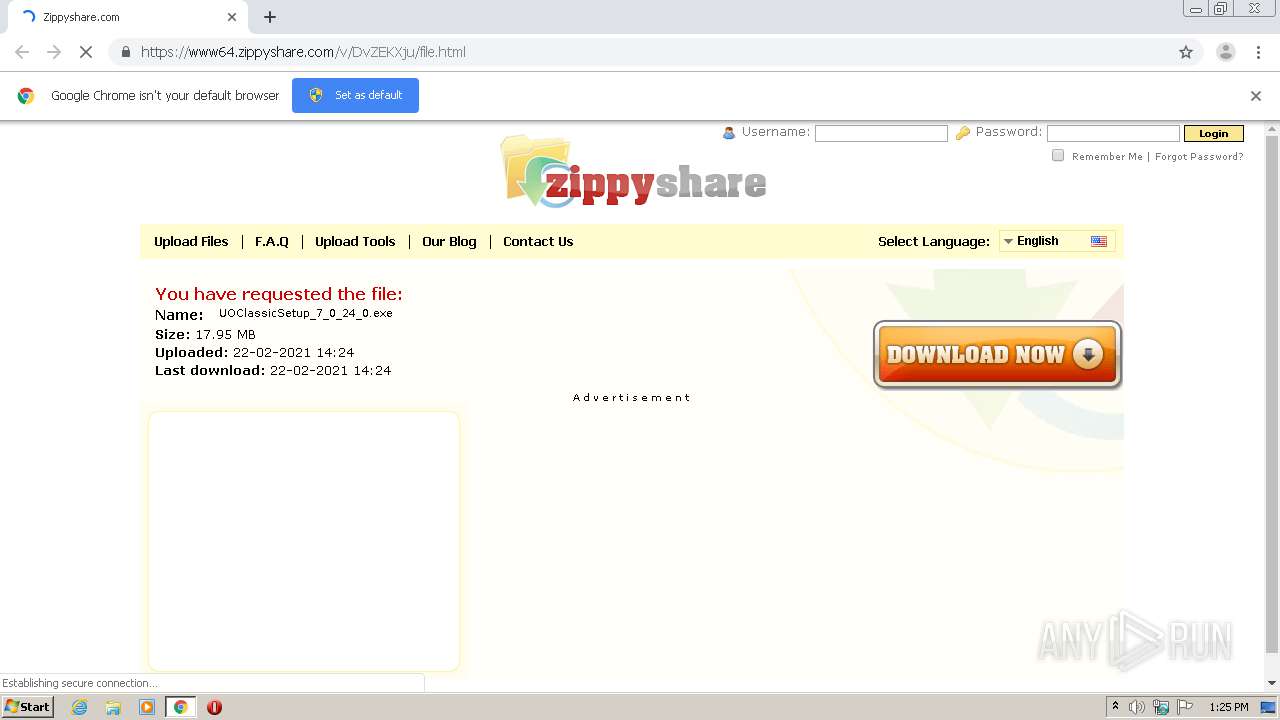
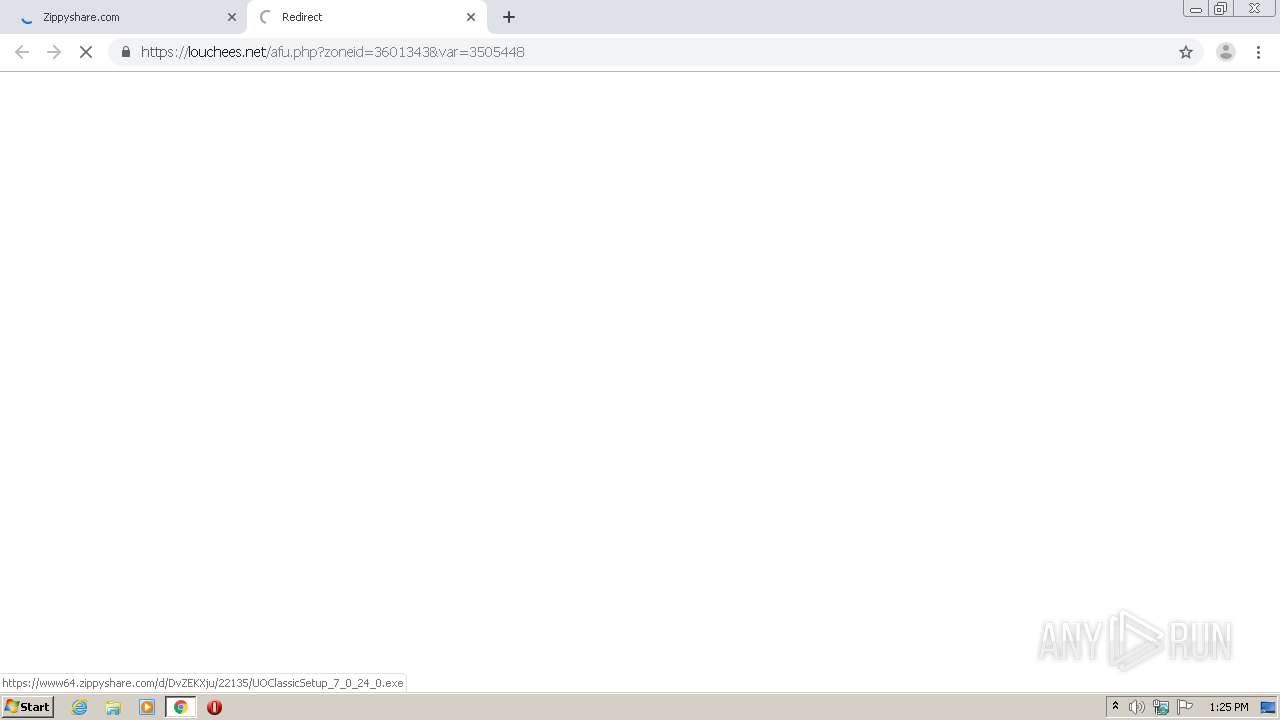
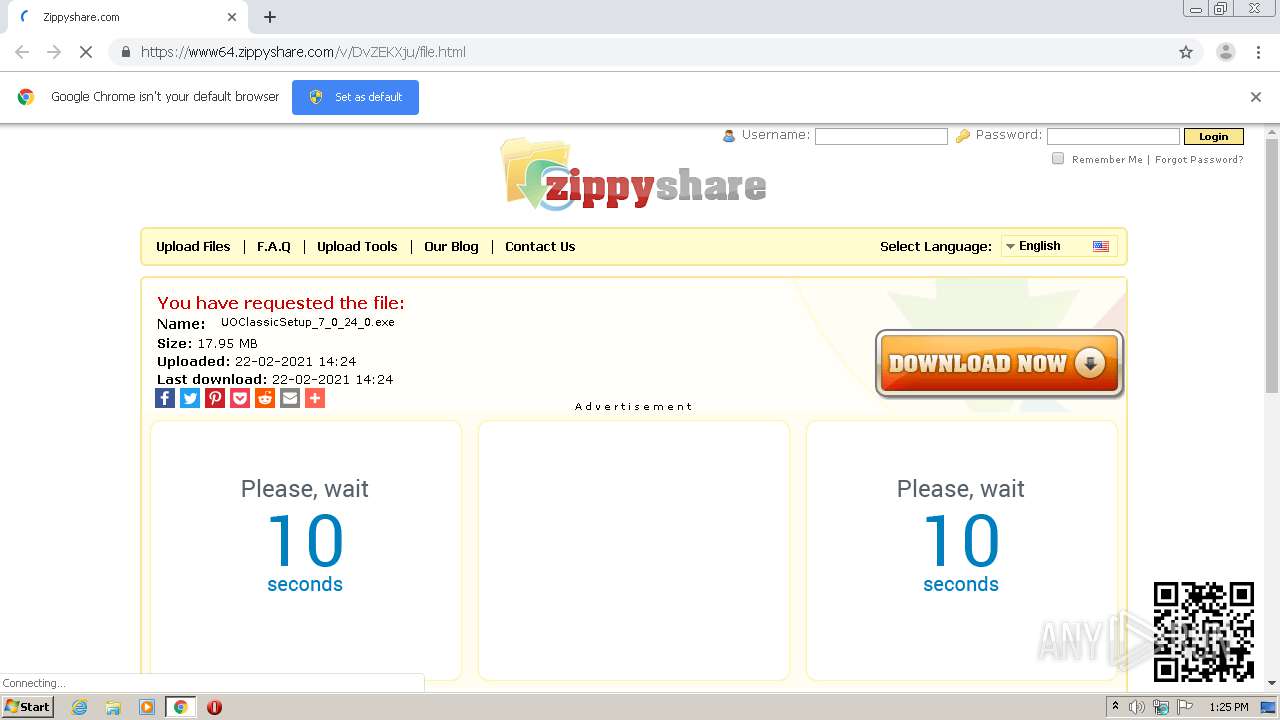
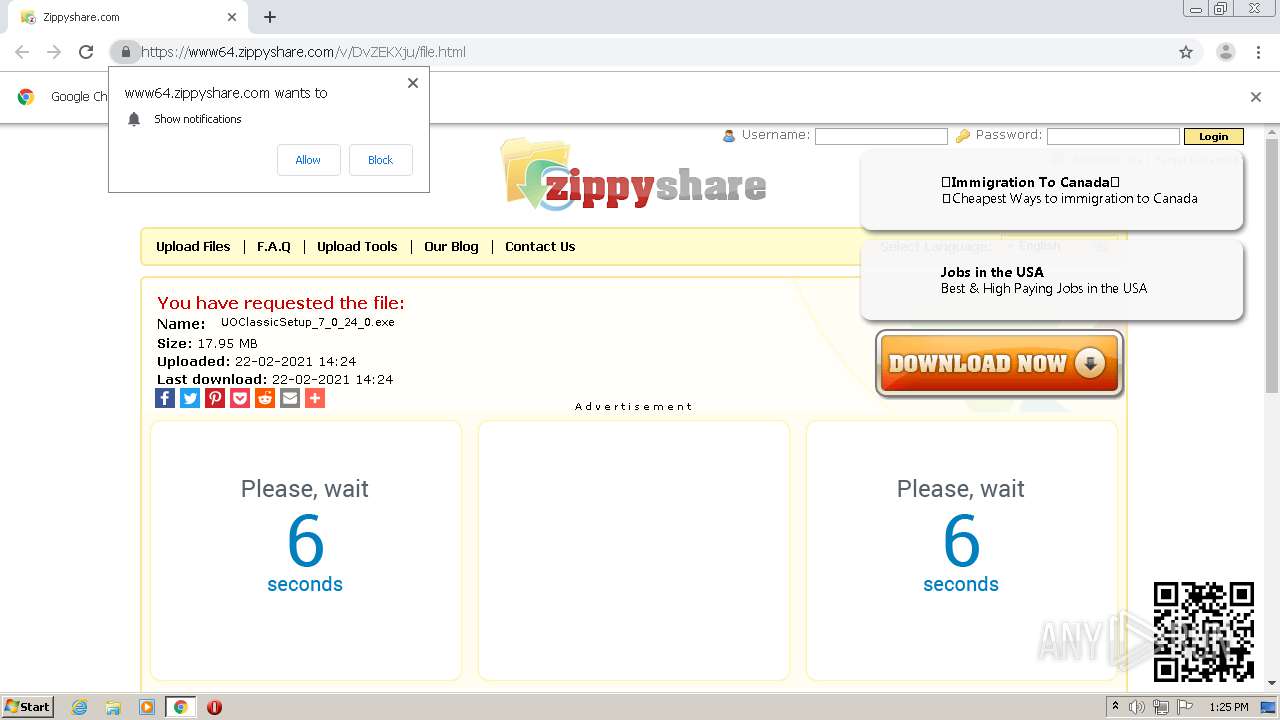
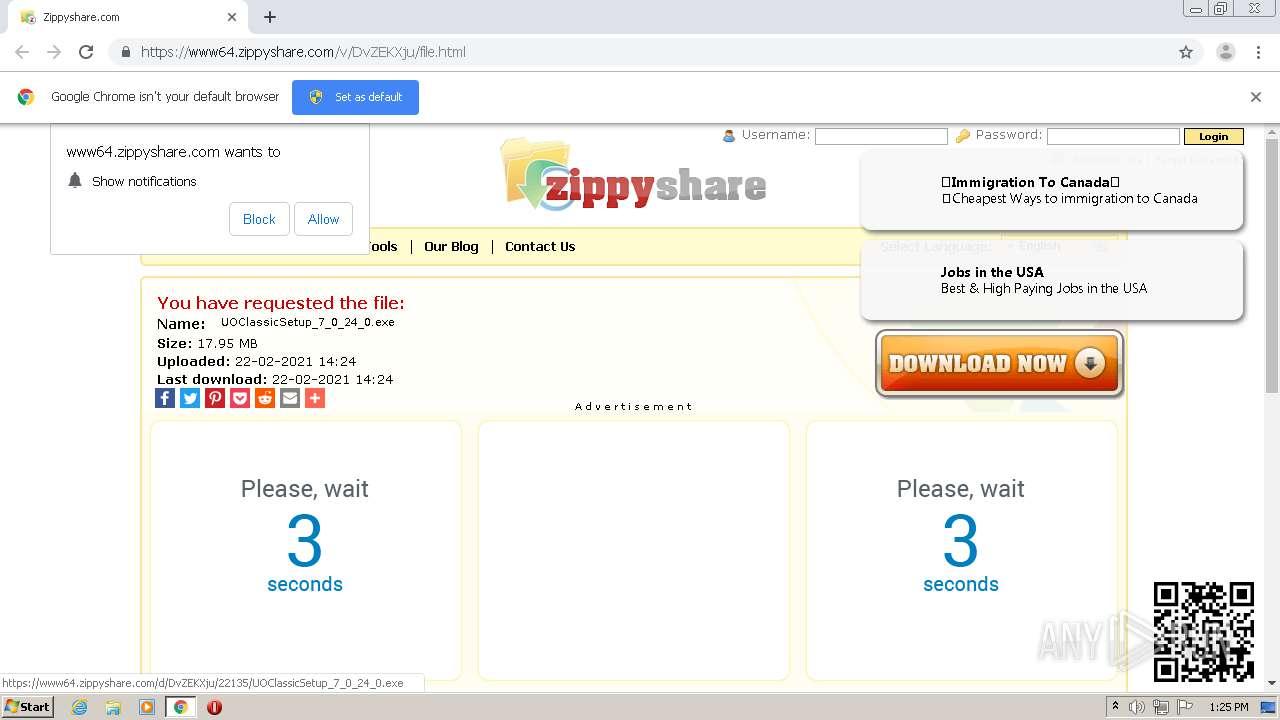
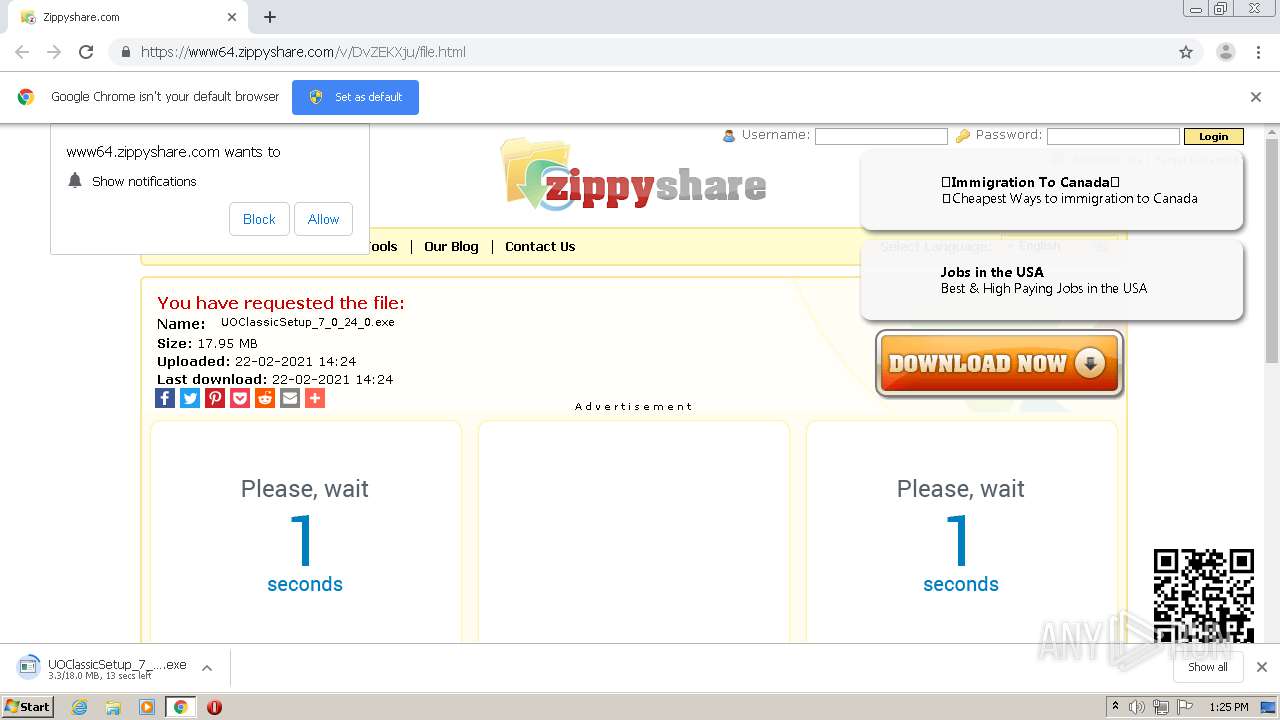
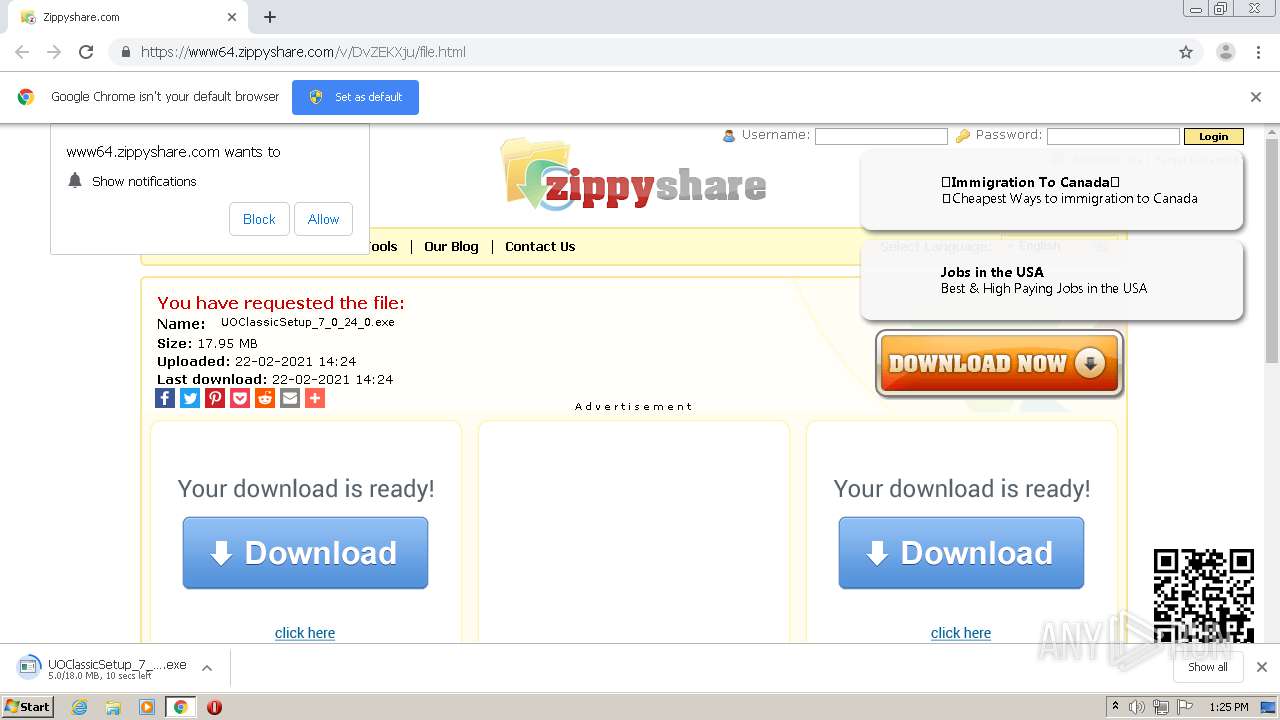
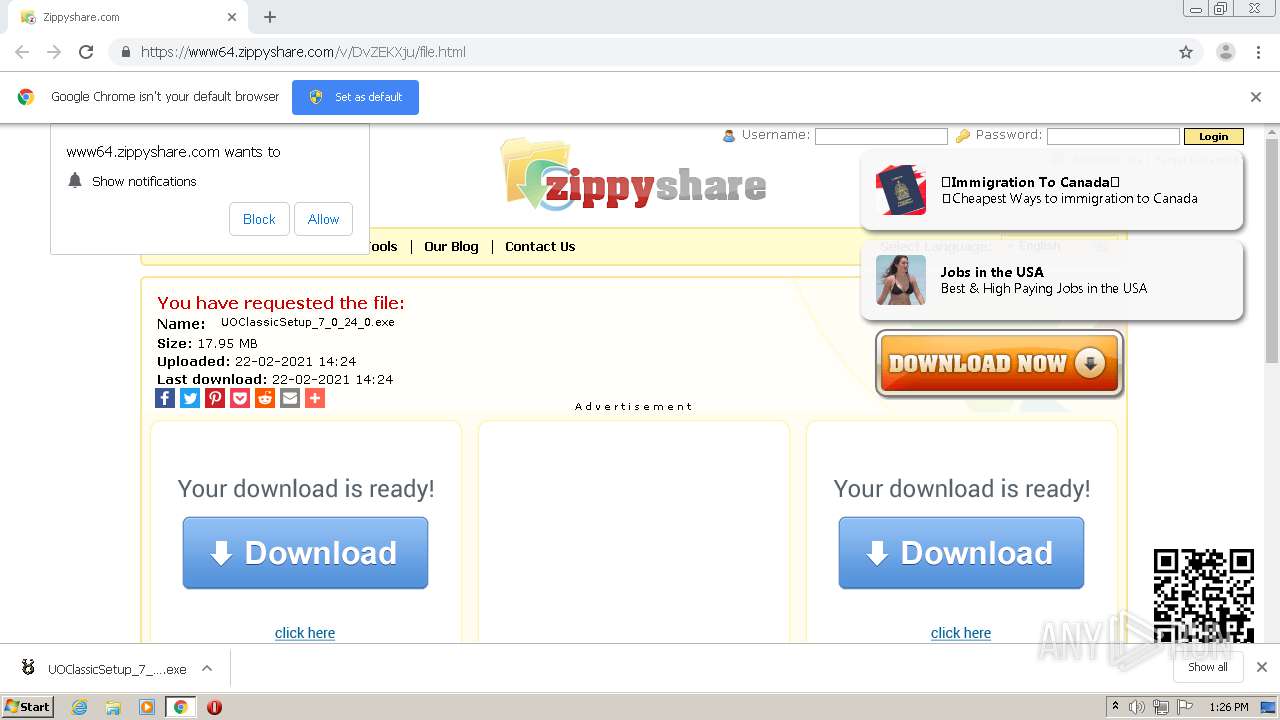
| URL: | https://www64.zippyshare.com/v/DvZEKXju/file.html |
| Full analysis: | https://app.any.run/tasks/d779549b-ce2c-4156-a0aa-e2aeb877156a |
| Verdict: | Malicious activity |
| Analysis date: | February 22, 2021, 13:25:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | BDBFA899D44961B4BDBC6FA1FDF4027F |
| SHA1: | 264D6FC899855A067E88438EA658869D0469A65F |
| SHA256: | 1D816B491D9F2D4981D5948BC22B86629A286F710B605BBB2FA960CB7CB8E615 |
| SSDEEP: | 3:N8DSTT2GKjKltJwJ:2OTCGjlteJ |
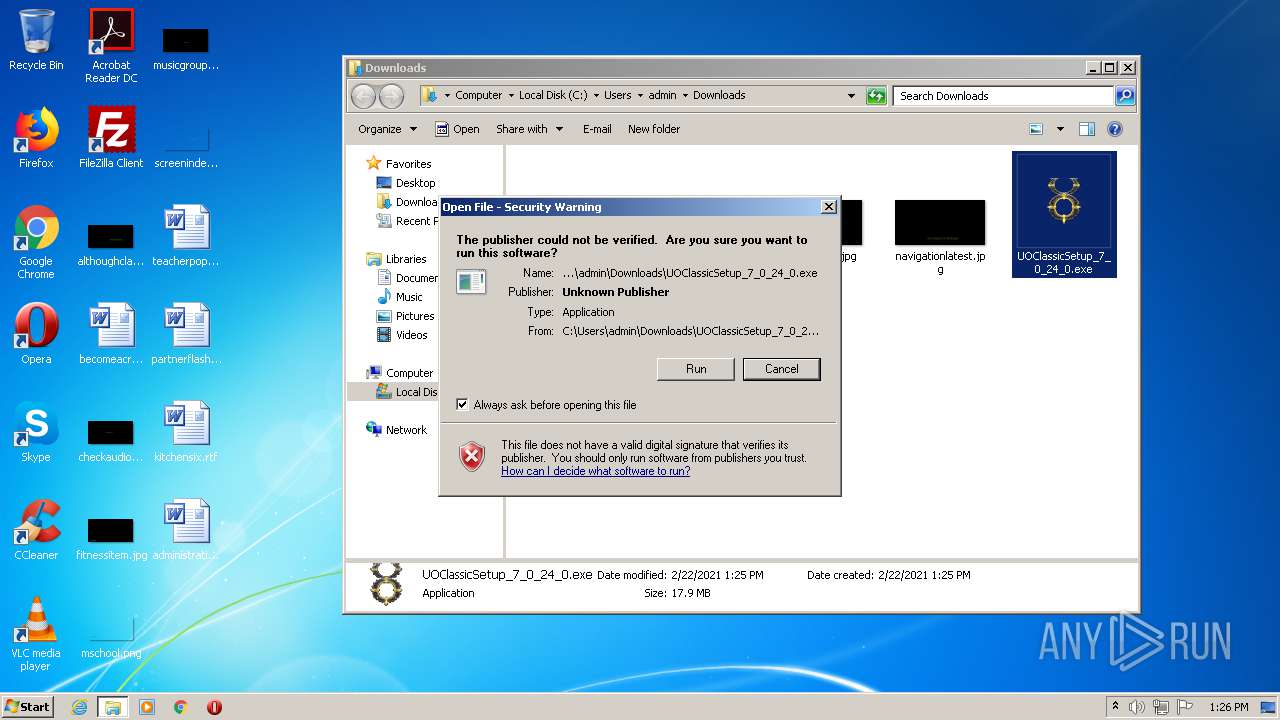
MALICIOUS
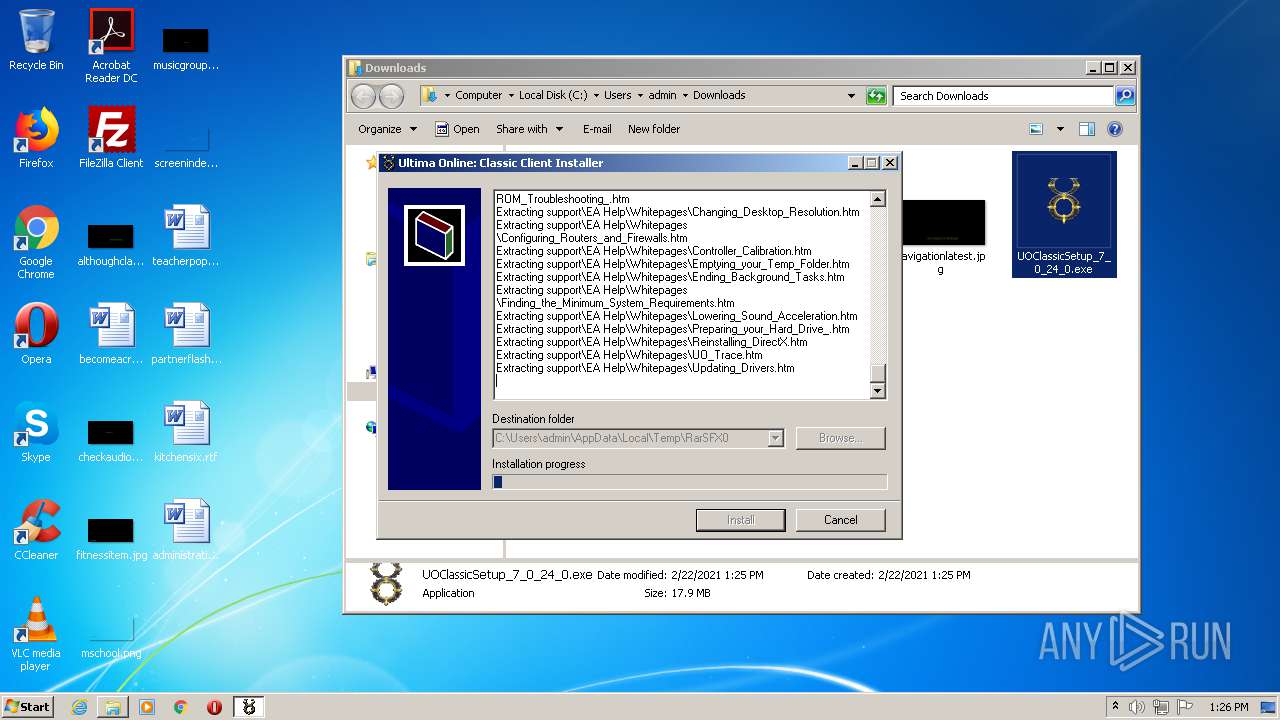
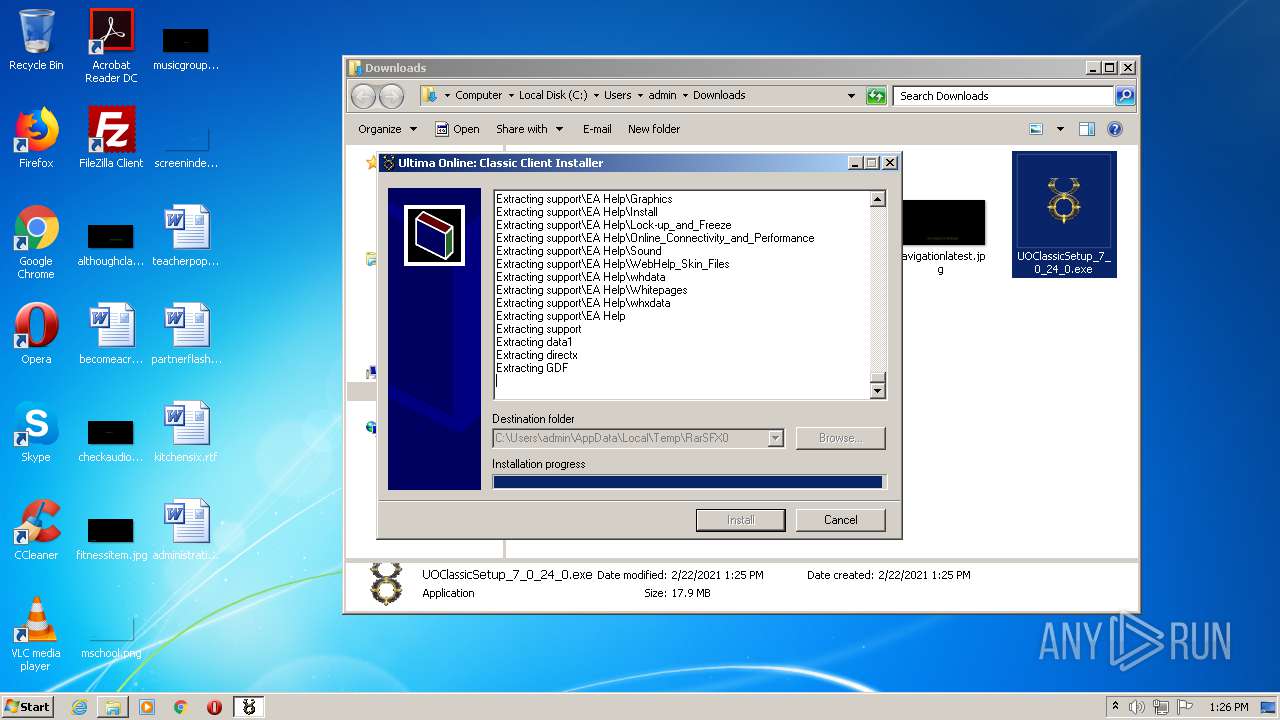
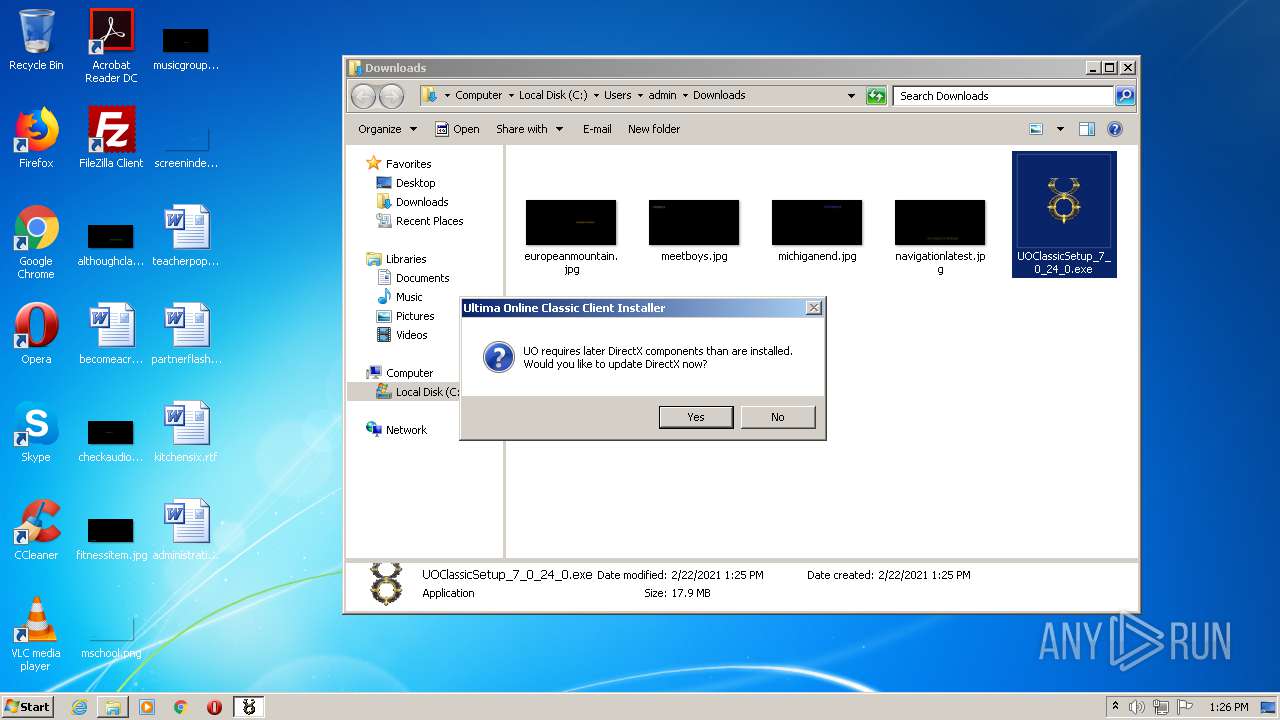
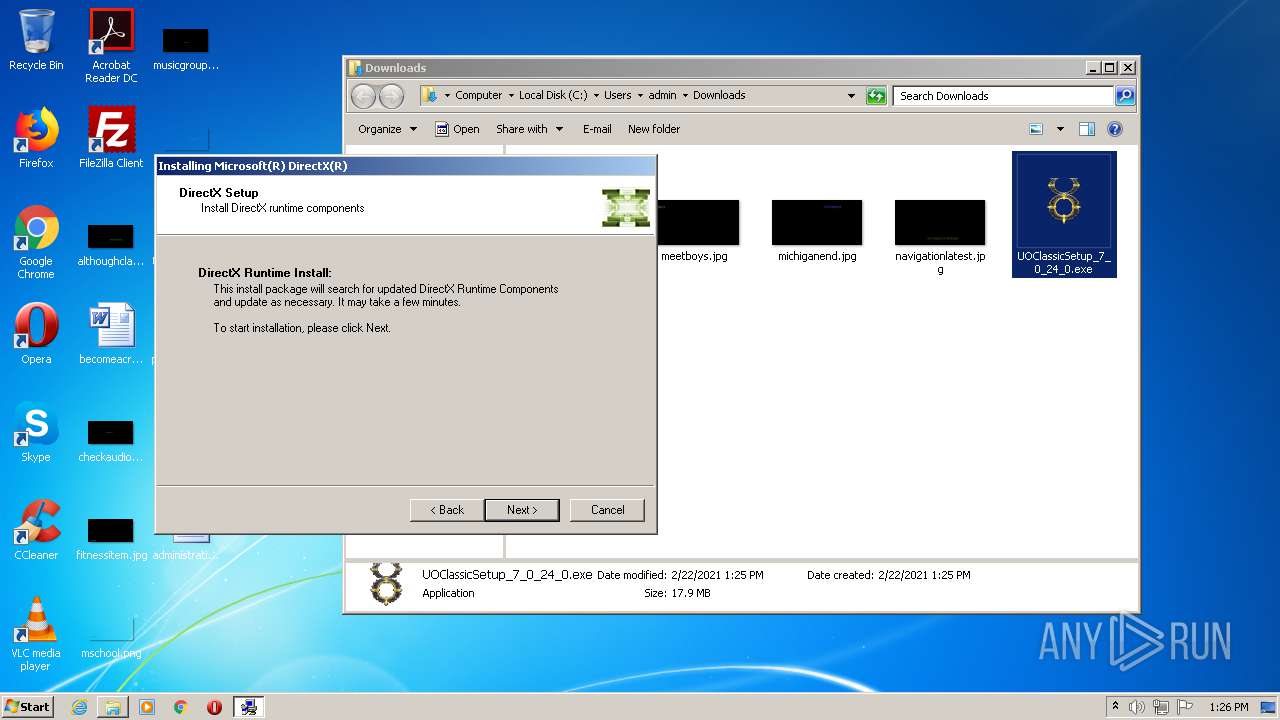
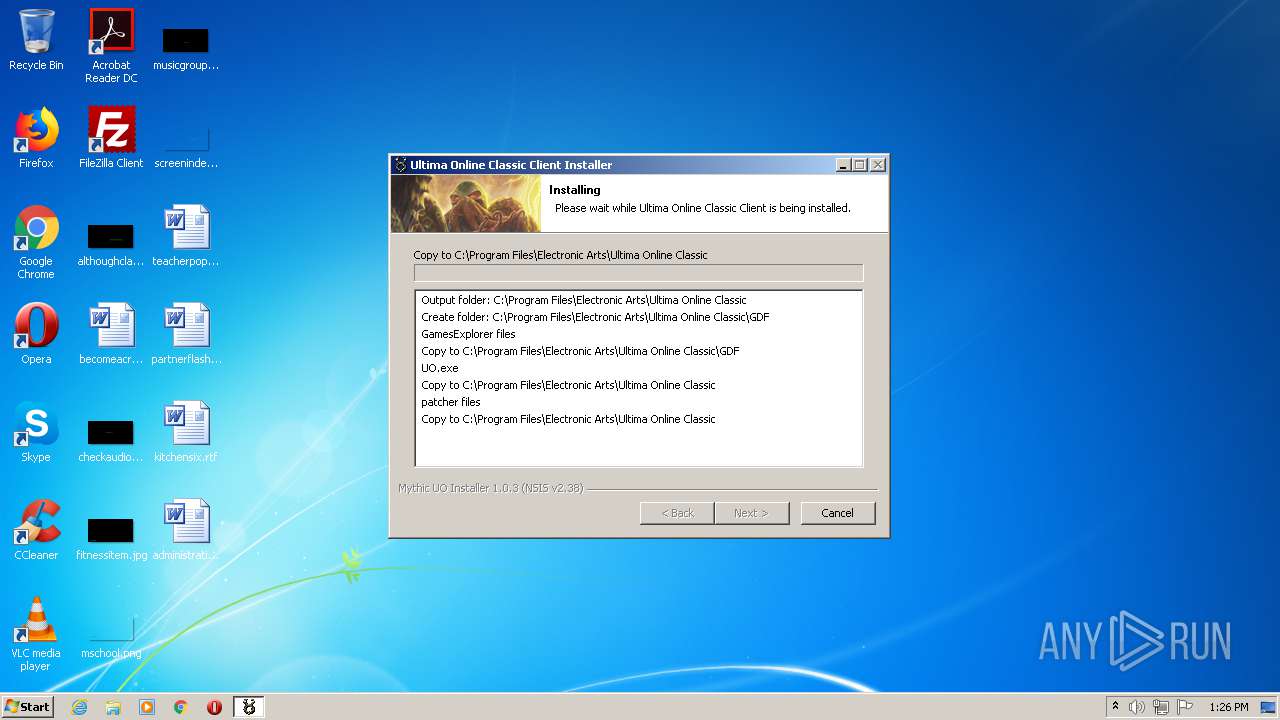
Application was dropped or rewritten from another process
- UOClassicSetup_7_0_24_0.exe (PID: 3280)
- setup.exe (PID: 444)
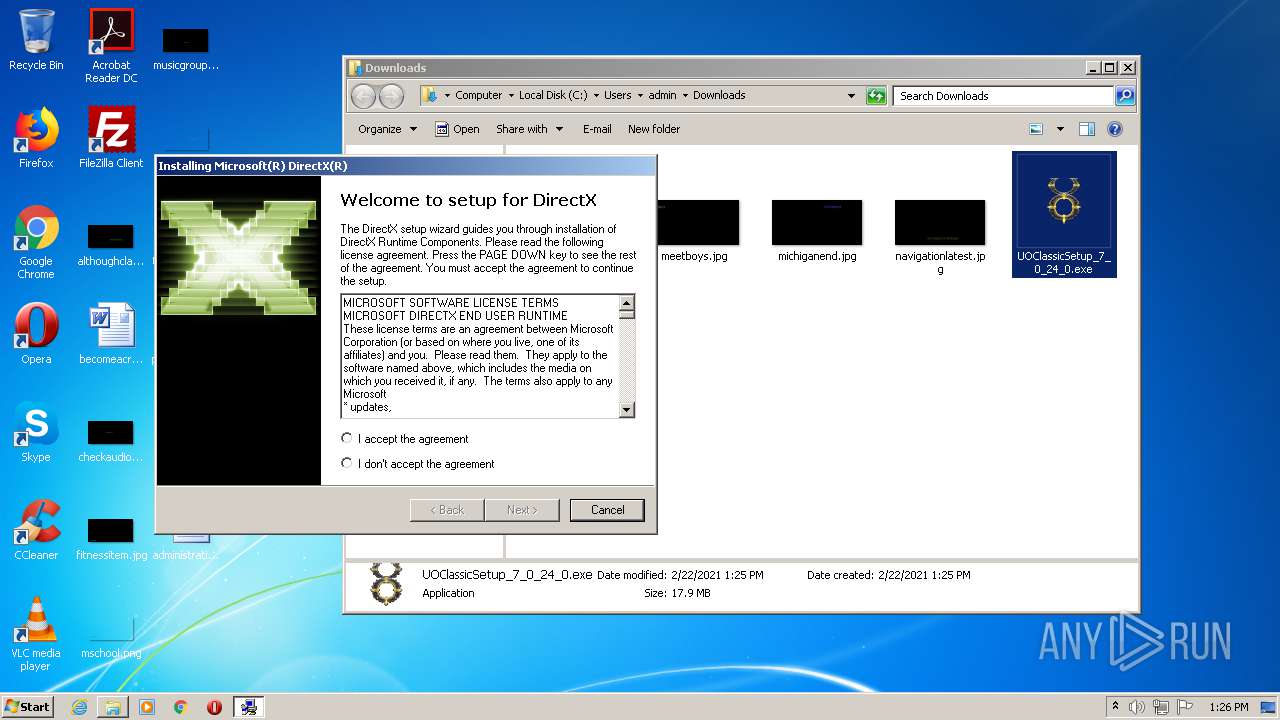
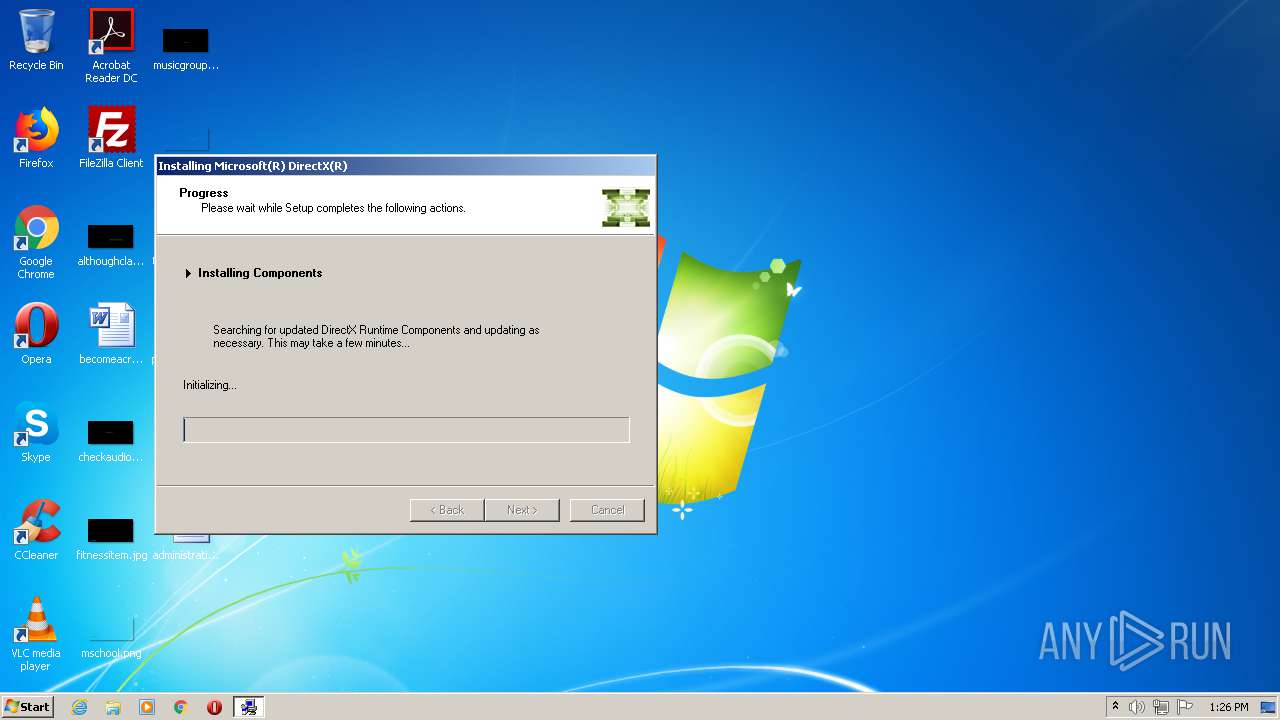
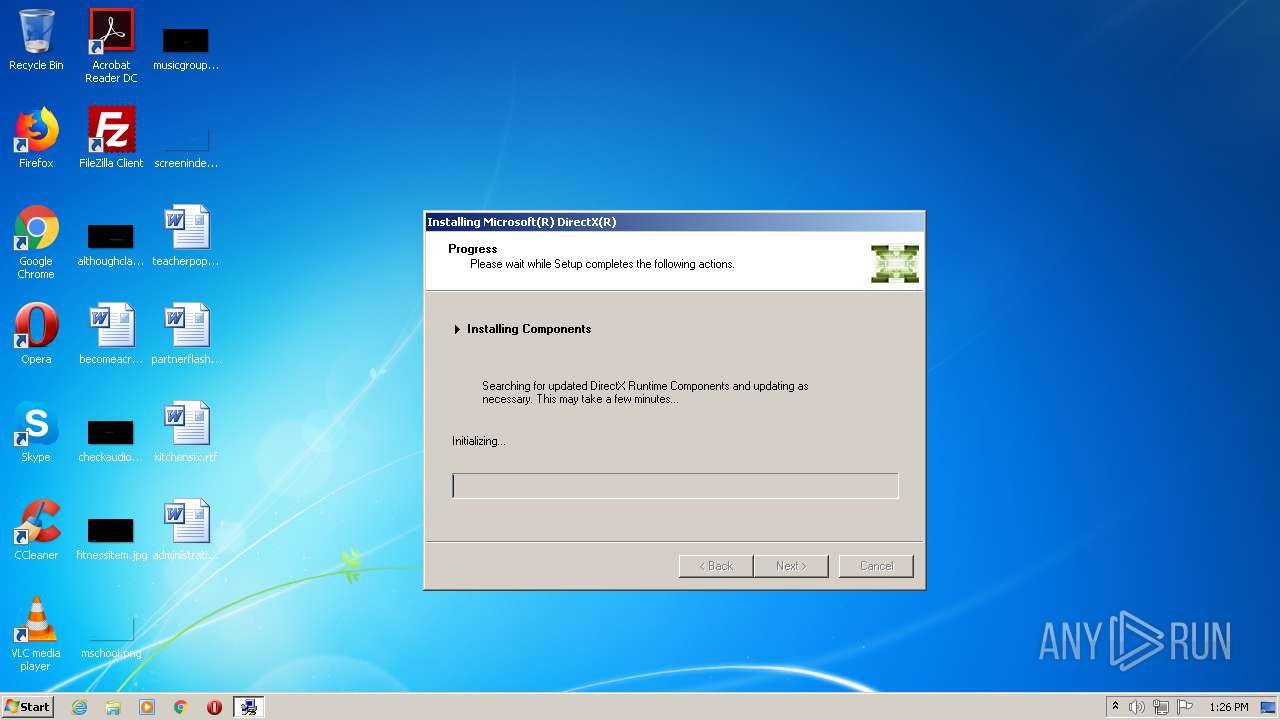
- DXSETUP.exe (PID: 1732)
- setup.exe (PID: 3704)
- UO.exe (PID: 3608)
- UO.exe (PID: 1104)
- UO.bin (PID: 3704)
- UO.exe (PID: 2552)
- UO.bin (PID: 1080)
Actions looks like stealing of personal data
- UOClassicSetup_7_0_24_0.exe (PID: 3280)
Loads dropped or rewritten executable
- setup.exe (PID: 444)
- DXSETUP.exe (PID: 1732)
- UO.exe (PID: 2552)
Changes settings of System certificates
- DXSETUP.exe (PID: 1732)
SUSPICIOUS
Drops a file that was compiled in debug mode
- chrome.exe (PID: 2176)
- UOClassicSetup_7_0_24_0.exe (PID: 3280)
- DXSETUP.exe (PID: 1732)
- setup.exe (PID: 444)
- UO.bin (PID: 3704)
- UO.exe (PID: 1104)
- UO.exe (PID: 2552)
- UO.bin (PID: 1080)
Executable content was dropped or overwritten
- UOClassicSetup_7_0_24_0.exe (PID: 3280)
- setup.exe (PID: 444)
- chrome.exe (PID: 2176)
- DXSETUP.exe (PID: 1732)
- UO.exe (PID: 1104)
- UO.bin (PID: 3704)
- UO.exe (PID: 2552)
- UO.bin (PID: 1080)
Drops a file with too old compile date
- UOClassicSetup_7_0_24_0.exe (PID: 3280)
- chrome.exe (PID: 2176)
- setup.exe (PID: 444)
- DXSETUP.exe (PID: 1732)
- UO.bin (PID: 1080)
Creates files in the Windows directory
- DXSETUP.exe (PID: 1732)
Searches for installed software
- DXSETUP.exe (PID: 1732)
Executed via COM
- DllHost.exe (PID: 3632)
Adds / modifies Windows certificates
- DXSETUP.exe (PID: 1732)
Removes files from Windows directory
- DXSETUP.exe (PID: 1732)
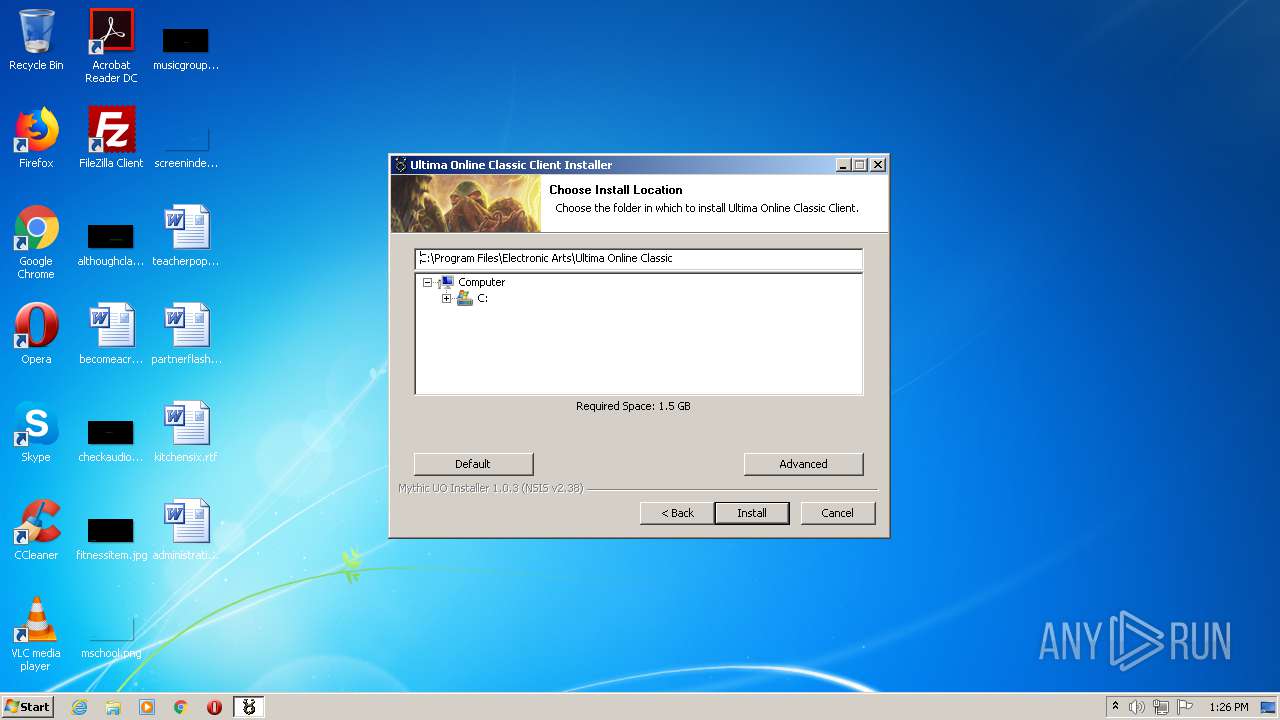
Creates a directory in Program Files
- setup.exe (PID: 444)
- UO.exe (PID: 1104)
- UO.bin (PID: 3704)
- UO.bin (PID: 1080)
Drops a file with a compile date too recent
- setup.exe (PID: 444)
- UO.bin (PID: 1080)
Creates a software uninstall entry
- setup.exe (PID: 444)
Creates files in the program directory
- setup.exe (PID: 444)
- UO.exe (PID: 1104)
- UO.bin (PID: 3704)
- UO.exe (PID: 2552)
- UO.bin (PID: 1080)
Starts itself from another location
- UO.exe (PID: 1104)
- UO.bin (PID: 3704)
- UO.exe (PID: 2552)
Starts application with an unusual extension
- UO.exe (PID: 1104)
- UO.exe (PID: 2552)
Reads internet explorer settings
- UO.exe (PID: 2552)
- UO.bin (PID: 1080)
INFO
Reads the hosts file
- chrome.exe (PID: 2176)
- chrome.exe (PID: 2372)
Application launched itself
- chrome.exe (PID: 2176)
Creates files in the user directory
- chrome.exe (PID: 2176)
Reads settings of System Certificates
- chrome.exe (PID: 2372)
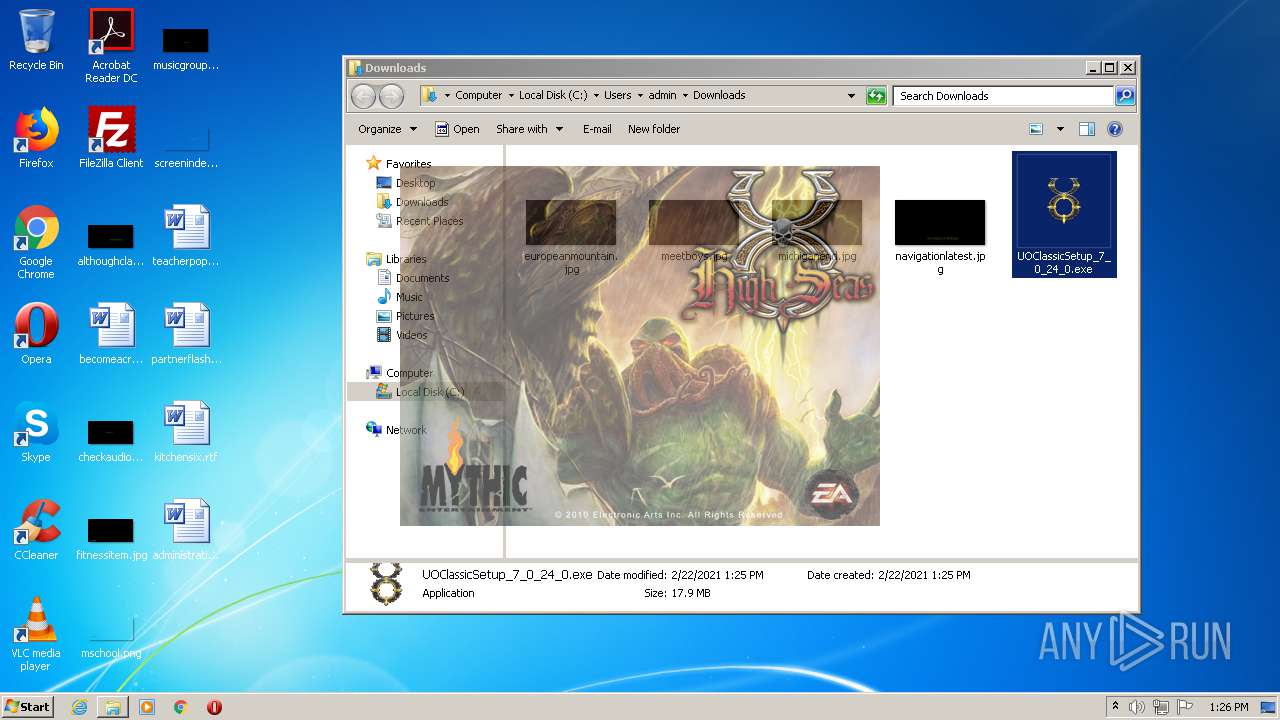
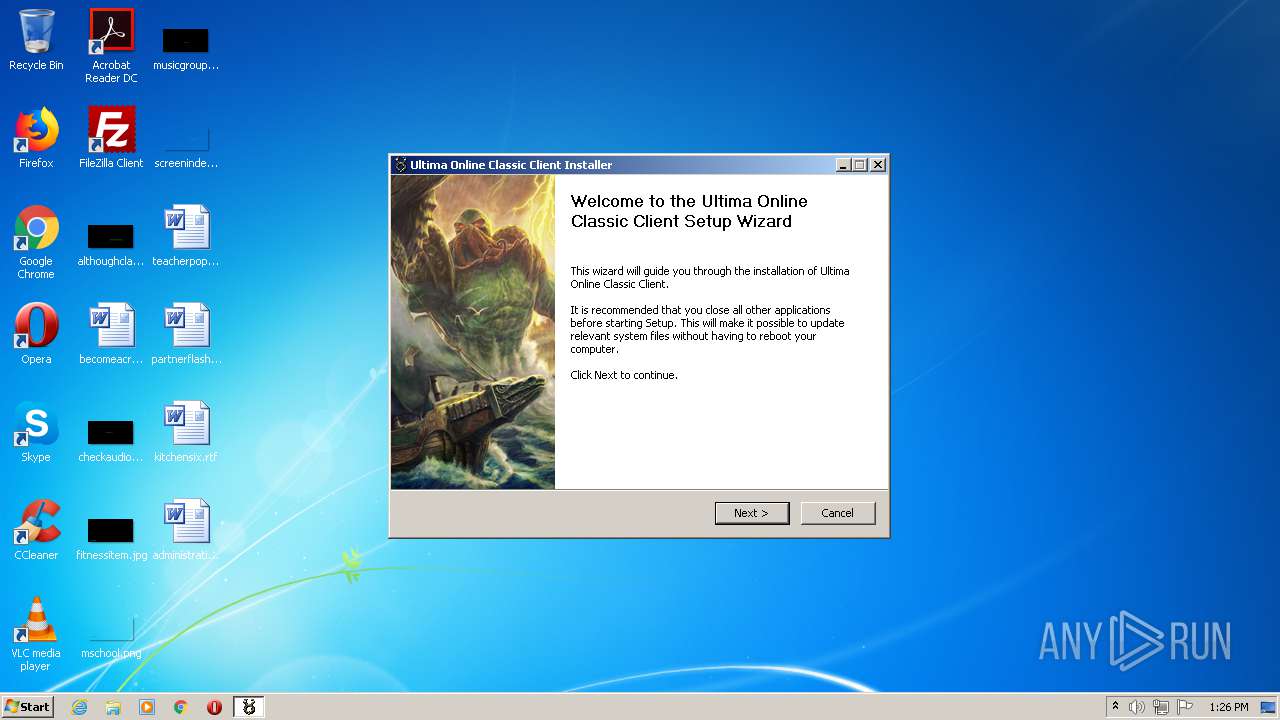
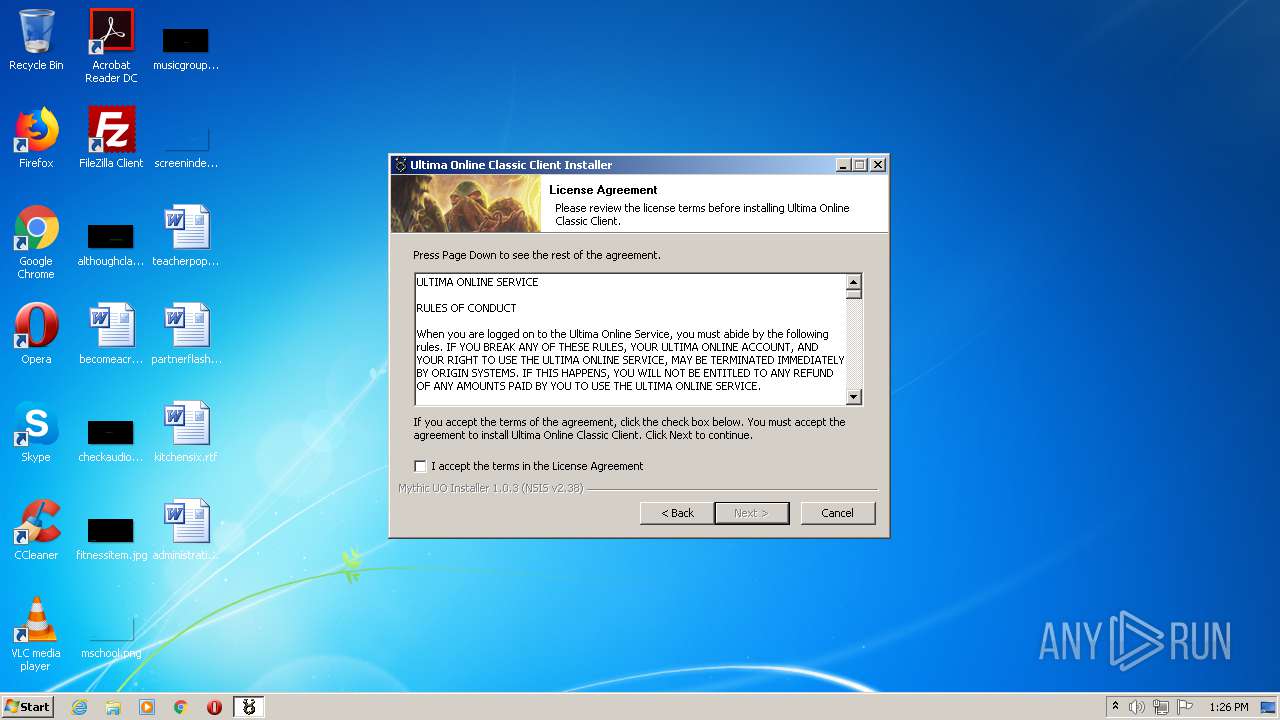
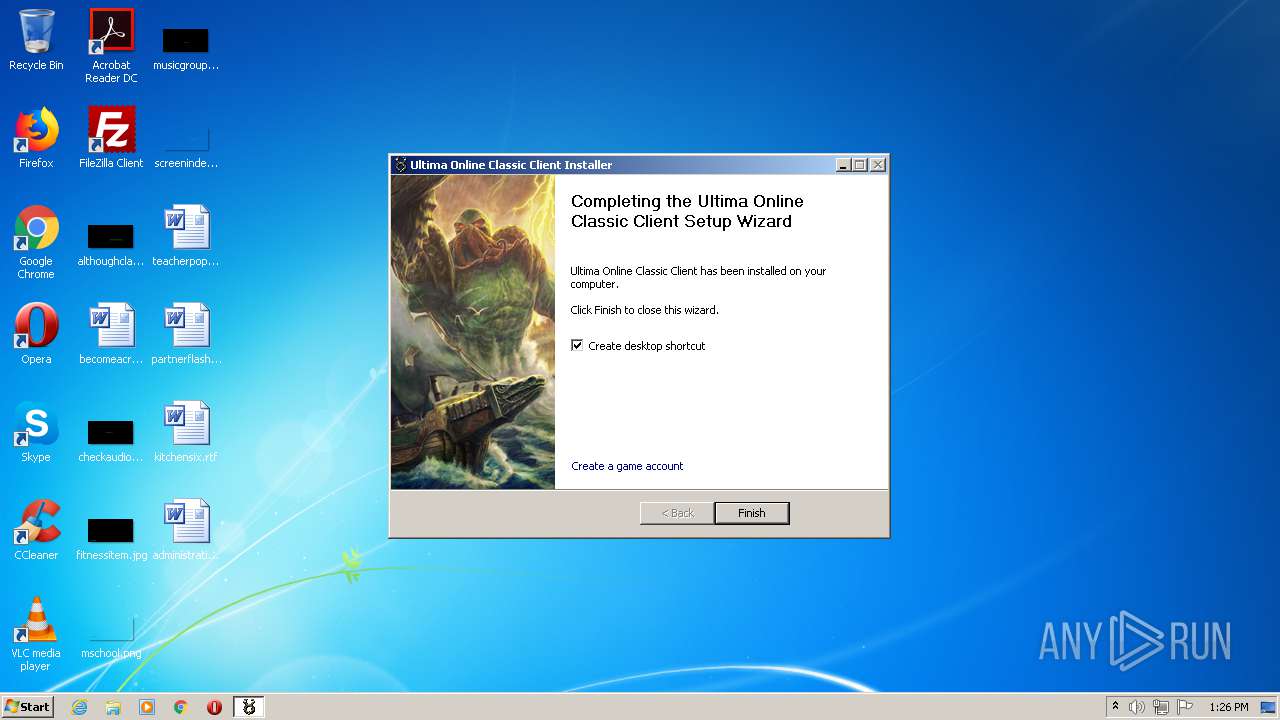
Manual execution by user
- UOClassicSetup_7_0_24_0.exe (PID: 3280)
- UO.exe (PID: 3608)
- UO.exe (PID: 1104)
- taskmgr.exe (PID: 2836)
Dropped object may contain Bitcoin addresses
- UO.bin (PID: 1080)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
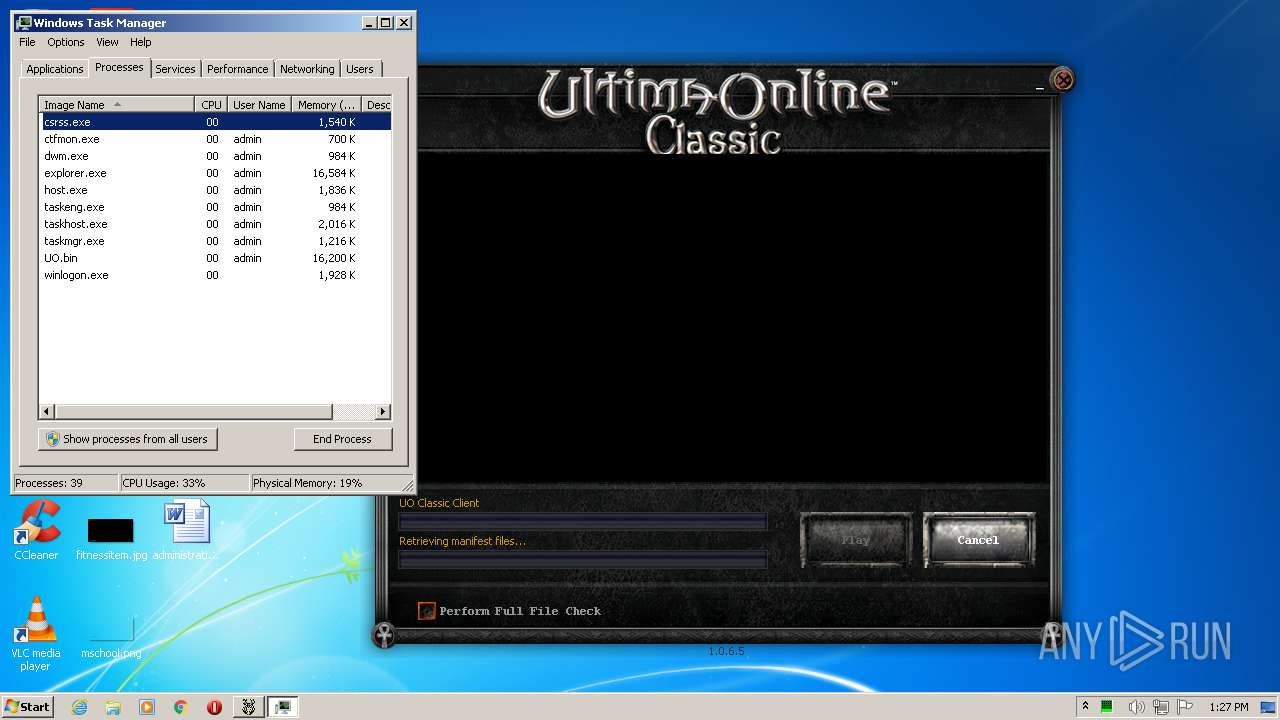
Total processes
76
Monitored processes
28
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 444 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\setup.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX0\setup.exe | UOClassicSetup_7_0_24_0.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,4723113482211869257,13467885996413556296,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5584462212818450437 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2388 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
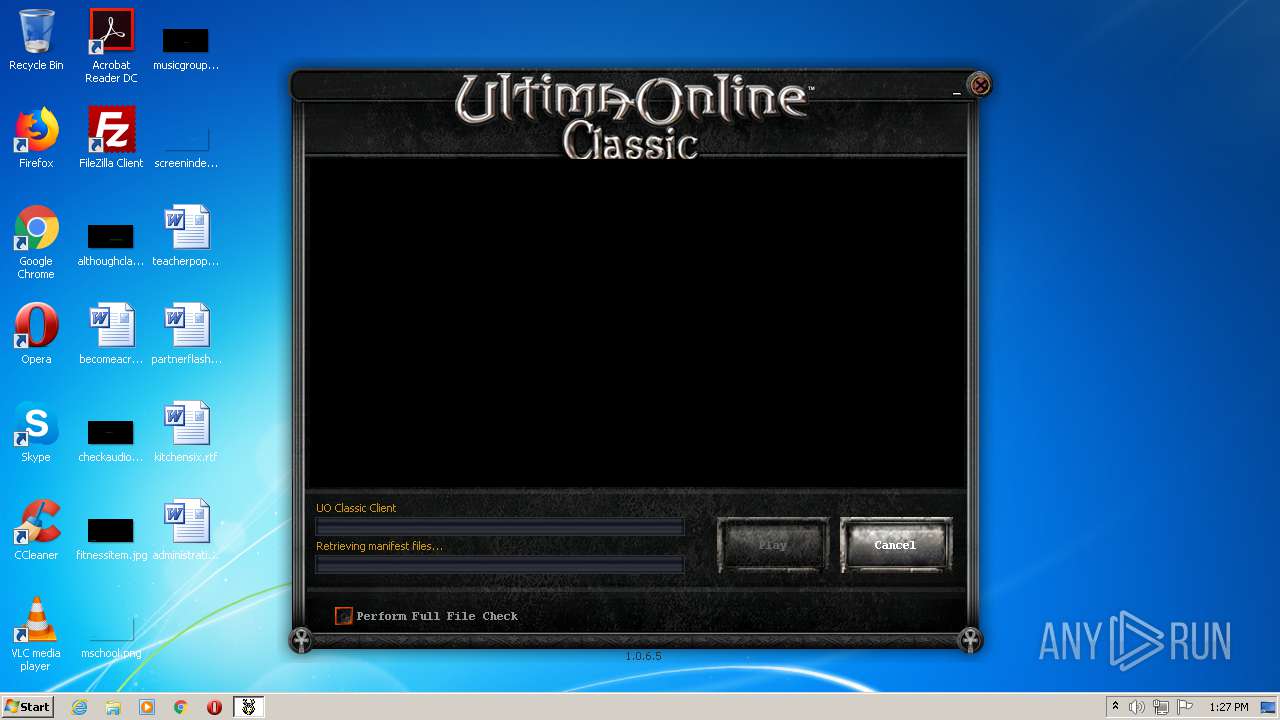
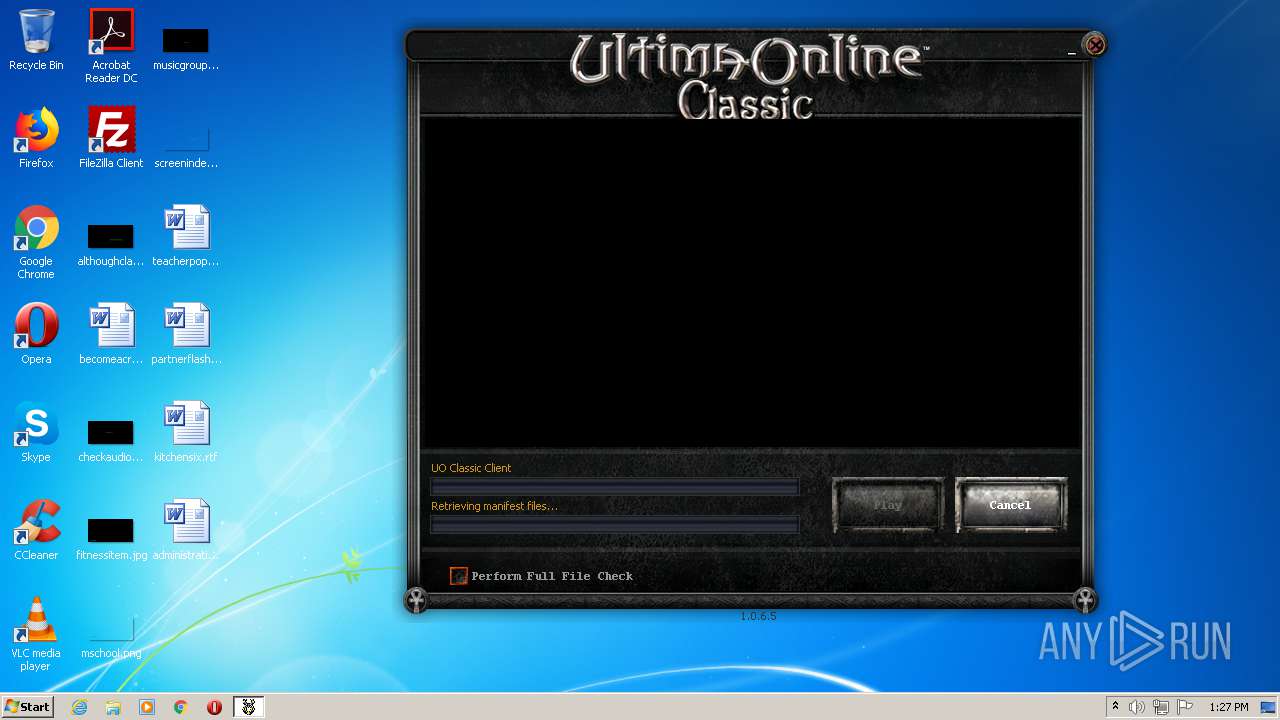
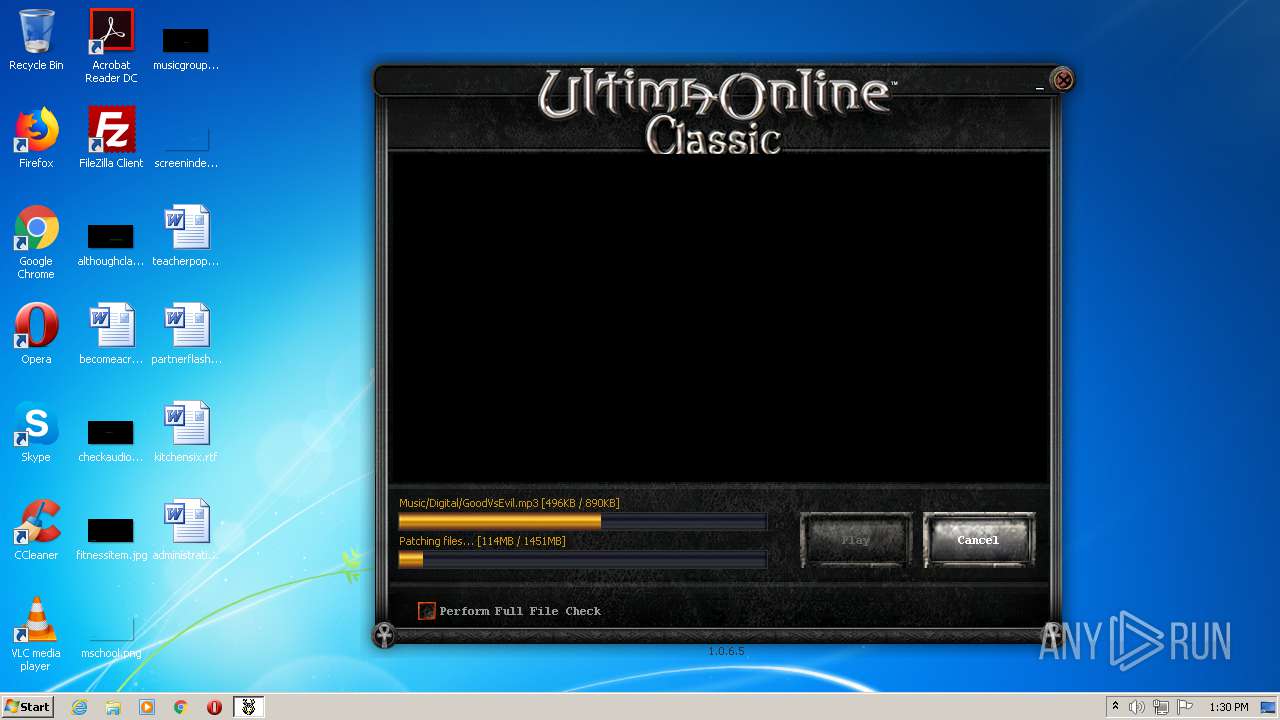
| 1080 | "UO.bin" | C:\Program Files\Electronic Arts\Ultima Online Classic\UO.bin | UO.exe | ||||||||||||
User: admin Company: Bioware, an EA Studio Integrity Level: HIGH Description: Patch Client Exit code: 0 Version: 1, 0, 6, 5 Modules
| |||||||||||||||
| 1104 | "C:\Program Files\Electronic Arts\Ultima Online Classic\UO.exe" | C:\Program Files\Electronic Arts\Ultima Online Classic\UO.exe | explorer.exe | ||||||||||||
User: admin Company: Bioware, an EA Studio Integrity Level: HIGH Description: Patch Client Exit code: 0 Version: 1, 0, 6, 5 Modules
| |||||||||||||||
| 1612 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,4723113482211869257,13467885996413556296,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14804868673328404381 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2156 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1732 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\DirectX\DXSETUP.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX0\DirectX\DXSETUP.exe | setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft DirectX Setup Exit code: 0 Version: 4.9.0.0904 Modules
| |||||||||||||||
| 1828 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,4723113482211869257,13467885996413556296,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11364493708448023340 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4028 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2080 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,4723113482211869257,13467885996413556296,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6220668711620094391 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3348 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2100 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1000,4723113482211869257,13467885996413556296,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=4541101736628323715 --mojo-platform-channel-handle=3640 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2144 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,4723113482211869257,13467885996413556296,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3882848073569672542 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3604 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 986
Read events
1 806
Write events
175
Delete events
5
Modification events
| (PID) Process: | (2576) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2176-13258473925554875 |
Value: 259 | |||
| (PID) Process: | (2176) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2176) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2176) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2176) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2176) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2176) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2176) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2176) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2176) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
34
Suspicious files
215
Text files
802
Unknown types
123
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2176 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6033B0C6-880.pma | — | |
MD5:— | SHA256:— | |||
| 2176 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2176 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\49868214-d638-47d7-9a10-8ba5e0243dcf.tmp | — | |
MD5:— | SHA256:— | |||
| 2176 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2176 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2176 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2176 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF132fae.TMP | text | |
MD5:— | SHA256:— | |||
| 2176 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT~RF13300c.TMP | text | |
MD5:— | SHA256:— | |||
| 2176 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2176 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF1331f0.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
458
TCP/UDP connections
108
DNS requests
54
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2372 | chrome.exe | GET | 302 | 108.59.81.209:80 | http://www.shiftexten.com/pl10?type=social&pub_id=4387&sub_id=387707994936185190&srcid=3936892_prpl_3505448 | US | — | — | whitelisted |
3704 | UO.bin | GET | 200 | 107.23.228.67:80 | http://patch.uo.eamythic.com/uopatch-sa/legacyrelease/patcher/manifest/patcher.prod.sig | US | text | 232 b | unknown |
3704 | UO.bin | GET | 200 | 107.23.228.67:80 | http://patch.uo.broadsword.com/uopatch-sa/legacyrelease/patcher/manifest/base/pkg.mft | US | pz | 452 b | unknown |
2372 | chrome.exe | GET | — | 8.248.121.254:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | — | — | whitelisted |
3704 | UO.bin | GET | 200 | 107.23.228.67:80 | http://patch.uo.eamythic.com/uopatch-sa/legacyrelease/patcher/manifest/patcher.prod | US | text | 1016 b | unknown |
3704 | UO.bin | GET | 200 | 107.23.228.67:80 | http://patch.uo.broadsword.com/uopatch-sa/legacyrelease/patcher/files/base/unpacked/07a54806a7b25553 | US | skn | 168 Kb | unknown |
3704 | UO.bin | GET | 200 | 107.23.228.67:80 | http://patch.uo.broadsword.com/uopatch-sa/legacyrelease/patcher/files/base/unpacked/9c6afcef149201f7 | US | pz | 125 Kb | unknown |
3704 | UO.bin | GET | 200 | 107.23.228.67:80 | http://patch.uo.broadsword.com/uopatch-sa/legacyrelease/patcher/files/base/unpacked/9a99162041d0085b | US | pz | 276 b | unknown |
3704 | UO.bin | GET | 200 | 107.23.228.67:80 | http://patch.uo.broadsword.com/uopatch-sa/legacyrelease/patcher/files/base/unpacked/1ad928c5ebee0fa0 | US | pz | 637 b | unknown |
3704 | UO.bin | GET | 200 | 107.23.228.67:80 | http://patch.uo.broadsword.com/uopatch-sa/legacyrelease/patcher/manifest/base/patch.myp.mft | US | pz | 277 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2372 | chrome.exe | 46.166.139.208:443 | www64.zippyshare.com | NForce Entertainment B.V. | NL | unknown |
2372 | chrome.exe | 142.250.186.45:443 | accounts.google.com | Google Inc. | US | suspicious |
2372 | chrome.exe | 104.84.56.112:443 | s7.addthis.com | Vodafone NZ Ltd. | US | unknown |
2372 | chrome.exe | 13.35.253.131:443 | ds88pc0kw6cvc.cloudfront.net | — | US | malicious |
2372 | chrome.exe | 142.250.186.74:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
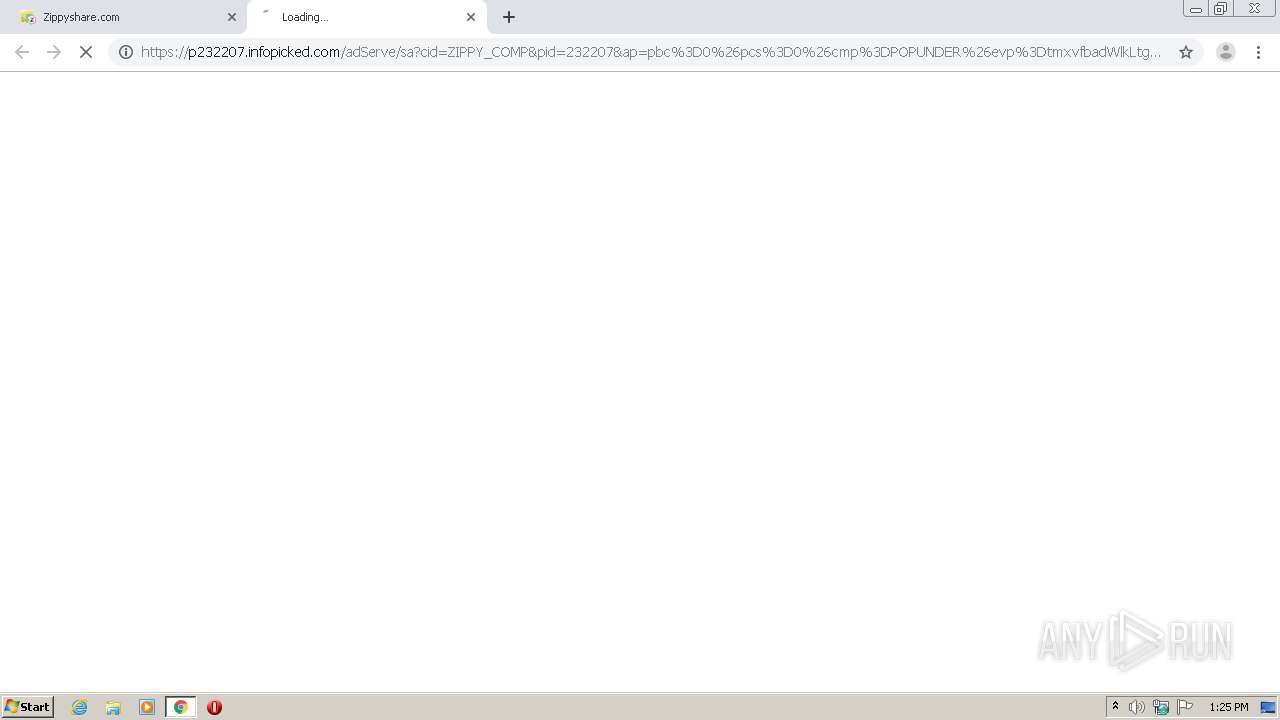
2372 | chrome.exe | 173.192.101.24:443 | p232207.clksite.com | SoftLayer Technologies Inc. | US | suspicious |
2372 | chrome.exe | 35.190.68.123:443 | www.maxonclick.com | Google Inc. | US | whitelisted |
2372 | chrome.exe | 13.35.253.46:443 | d10lumateci472.cloudfront.net | — | US | malicious |
2372 | chrome.exe | 54.237.125.12:443 | aphycolourses.info | Amazon.com, Inc. | US | suspicious |
2372 | chrome.exe | 142.250.185.196:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www64.zippyshare.com |
| unknown |
accounts.google.com |
| shared |
d10lumateci472.cloudfront.net |
| whitelisted |
ds88pc0kw6cvc.cloudfront.net |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
s7.addthis.com |
| whitelisted |
p232207.clksite.com |
| whitelisted |
infopicked.com |
| whitelisted |
www.maxonclick.com |
| whitelisted |
beta.infopicked.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
Process | Message |
|---|---|
DXSETUP.exe | DLL_PROCESS_ATTACH |
DXSETUP.exe | DLL_PROCESS_DETACH |
DXSETUP.exe | DLL_PROCESS_ATTACH |
DXSETUP.exe | DLL_PROCESS_ATTACH |
DXSETUP.exe | DLL_PROCESS_DETACH |
DXSETUP.exe | DLL_PROCESS_DETACH |
DXSETUP.exe | DLL_PROCESS_ATTACH |
DXSETUP.exe | DLL_PROCESS_ATTACH |
DXSETUP.exe | DLL_PROCESS_DETACH |
DXSETUP.exe | DLL_PROCESS_DETACH |