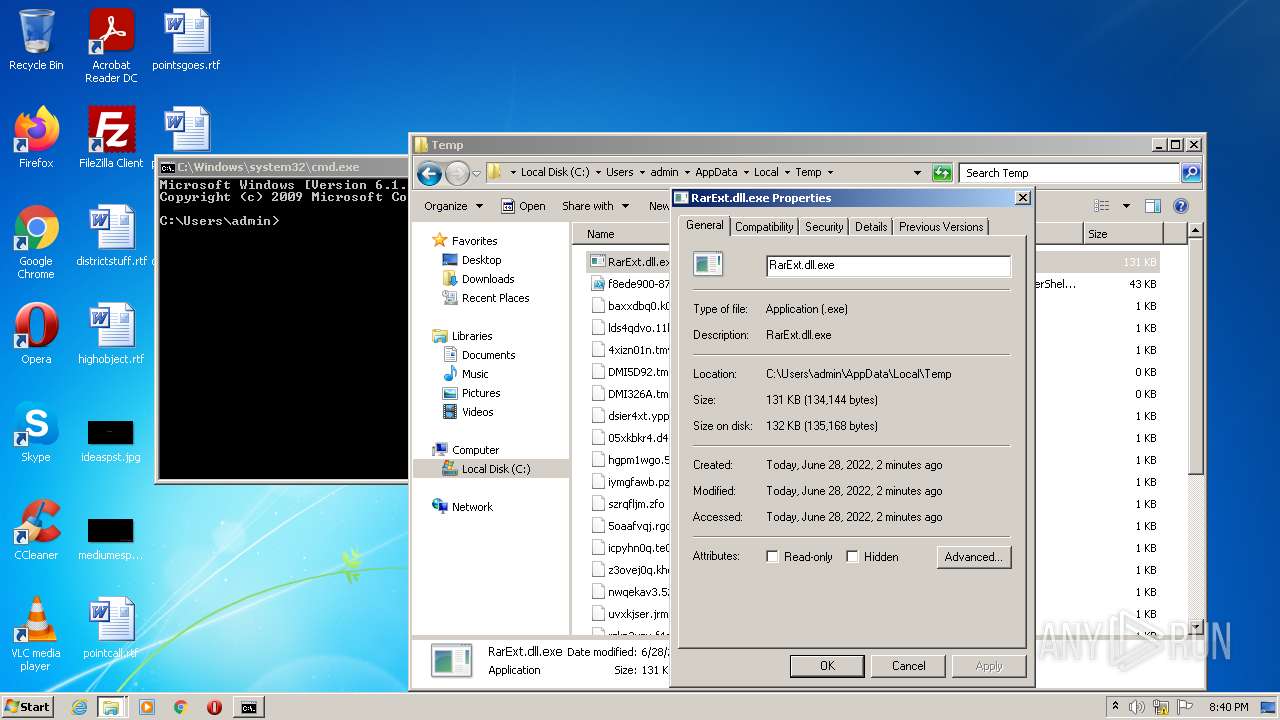
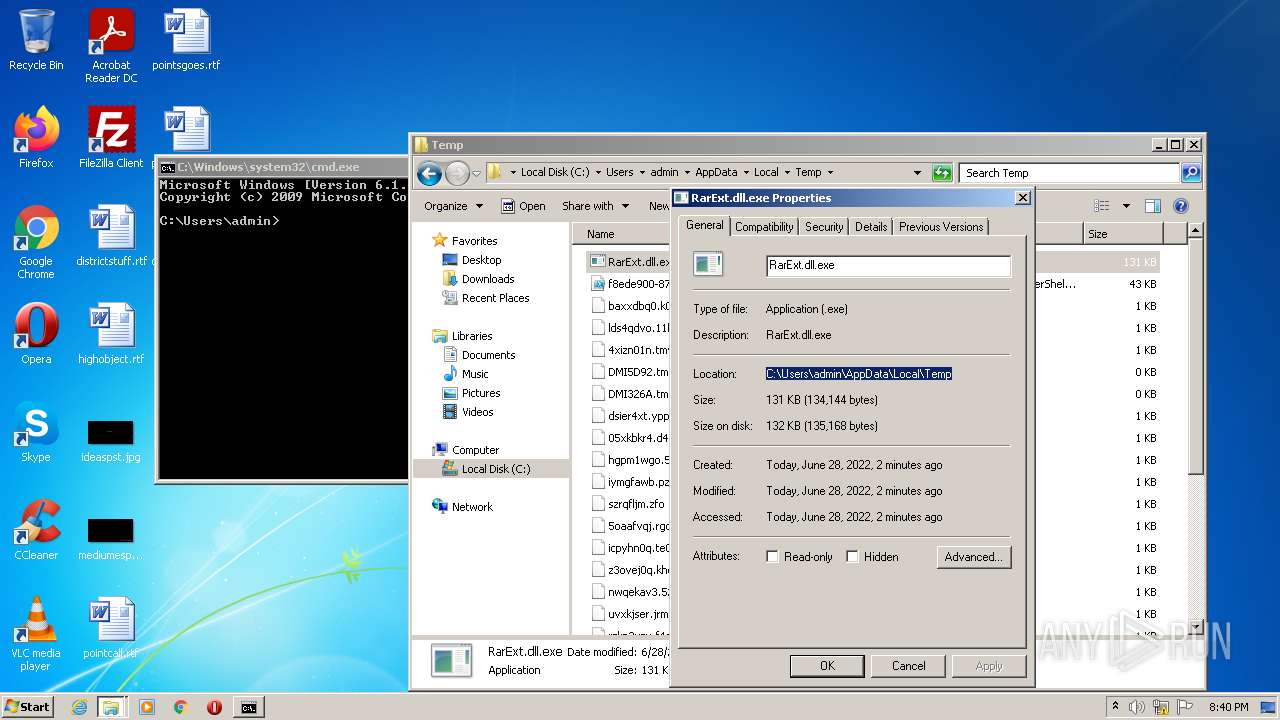
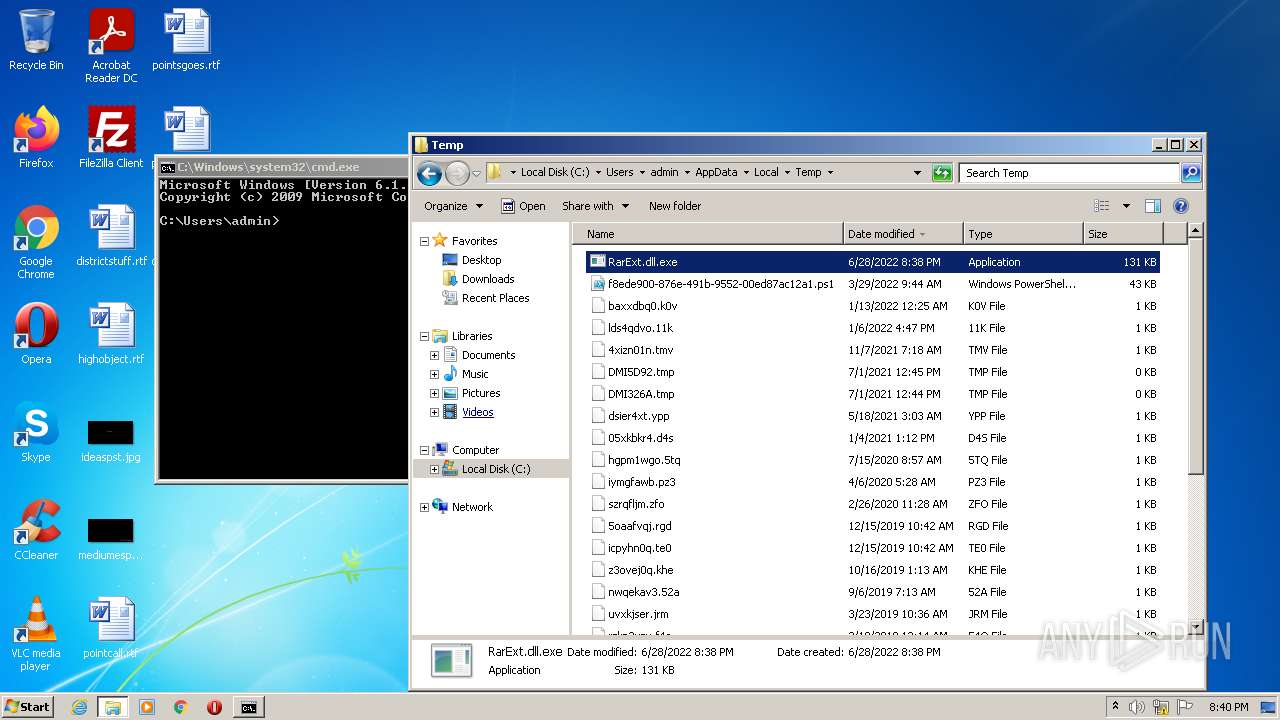
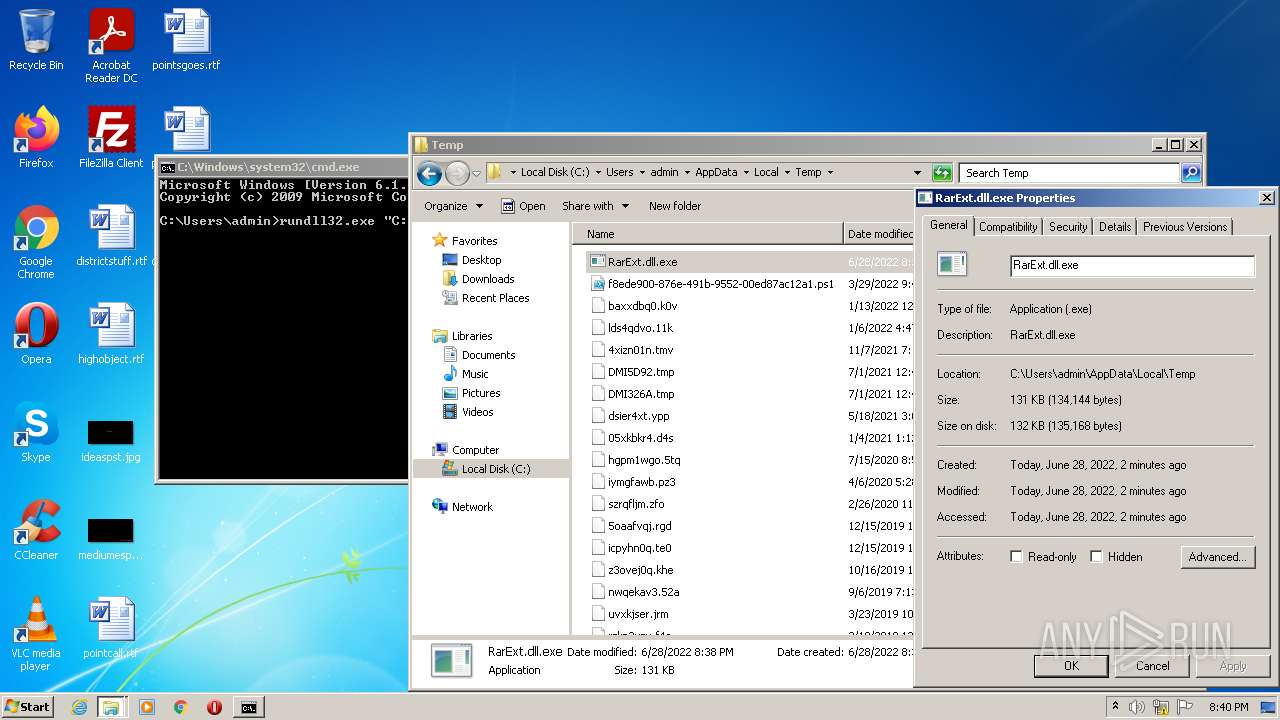
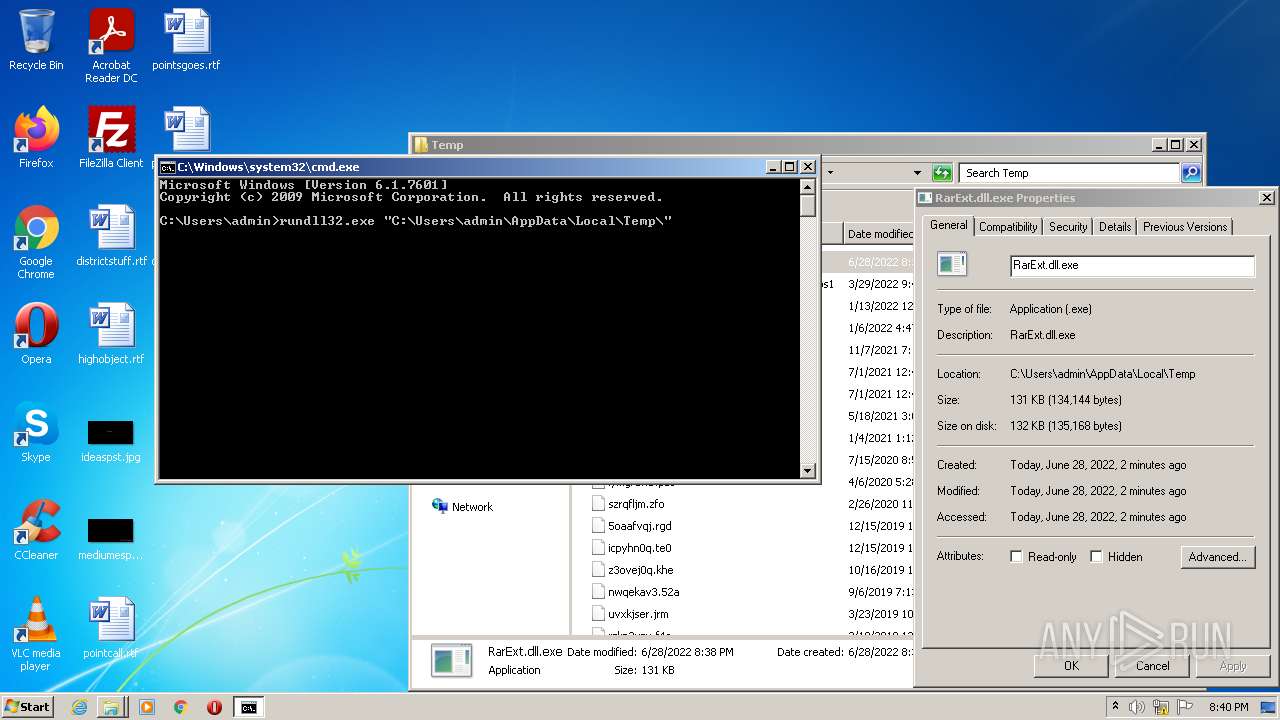
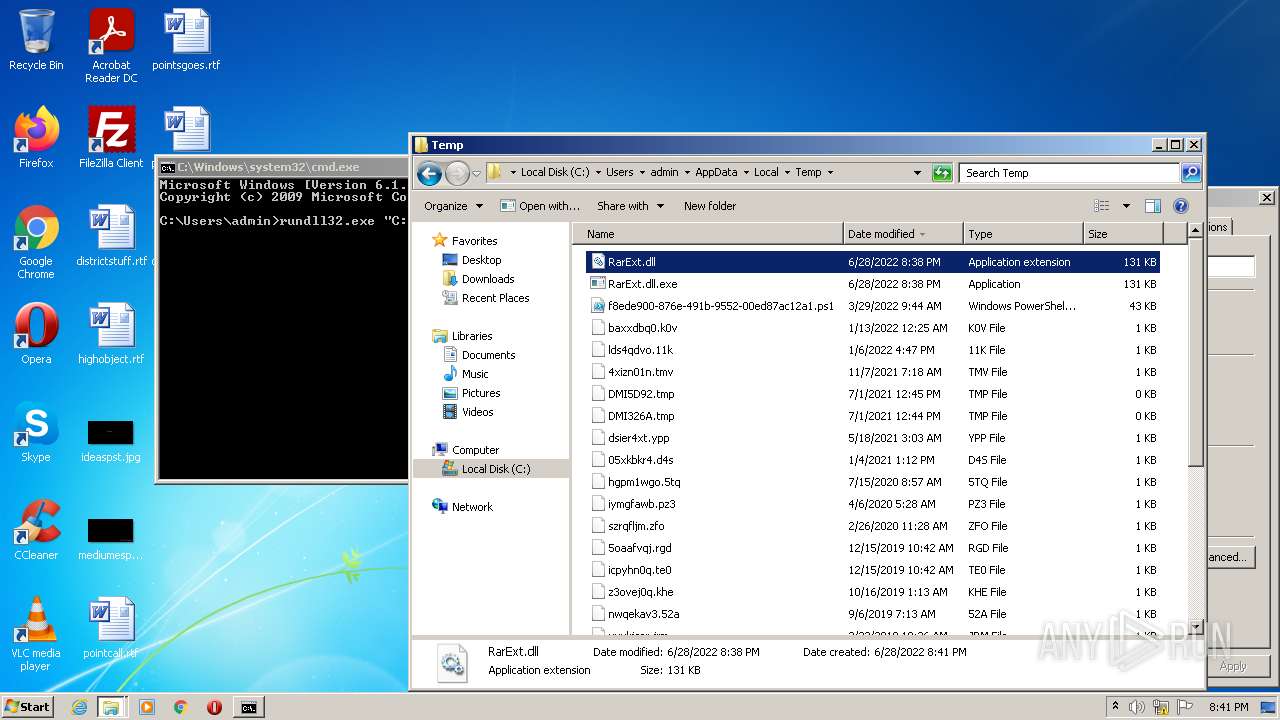
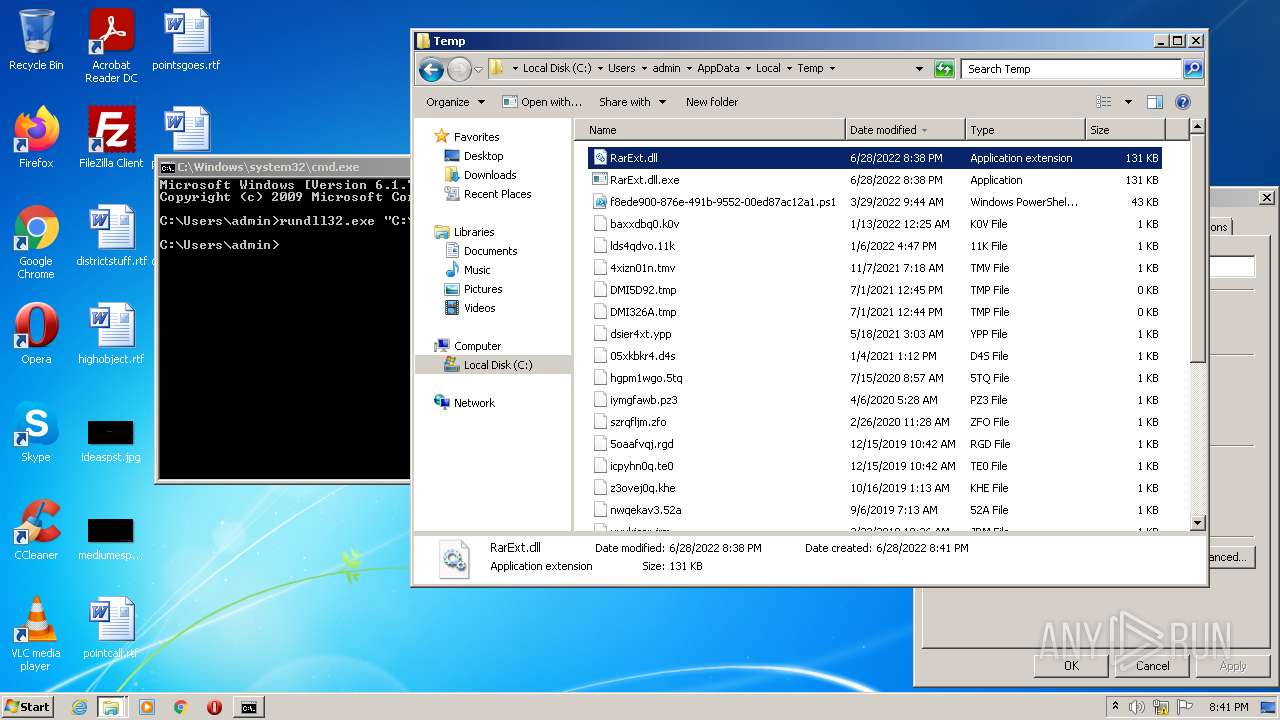
| File name: | RarExt.dll |
| Full analysis: | https://app.any.run/tasks/a3e27939-4191-4b77-b706-434885a19695 |
| Verdict: | Malicious activity |
| Analysis date: | June 28, 2022, 19:38:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (DLL) (GUI) x86-64, for MS Windows |
| MD5: | 42ABB32CD88EE98BD00DAABCCC6B0E26 |
| SHA1: | E7A78D2F1EBEA27EF71A6955DE74905467A5D62F |
| SHA256: | 1D76D52E1E1C226EF5D0DEEE5038184D3C7E0EFAD54CEFA48402EF77B7F825F1 |
| SSDEEP: | 3072:qVnDPoSA0Sle0WF7rrCwUT9GEgDzg/NC1XxGGtl4nJ2:qZDPoSARYXrCjJGNDzgFC1sJ |
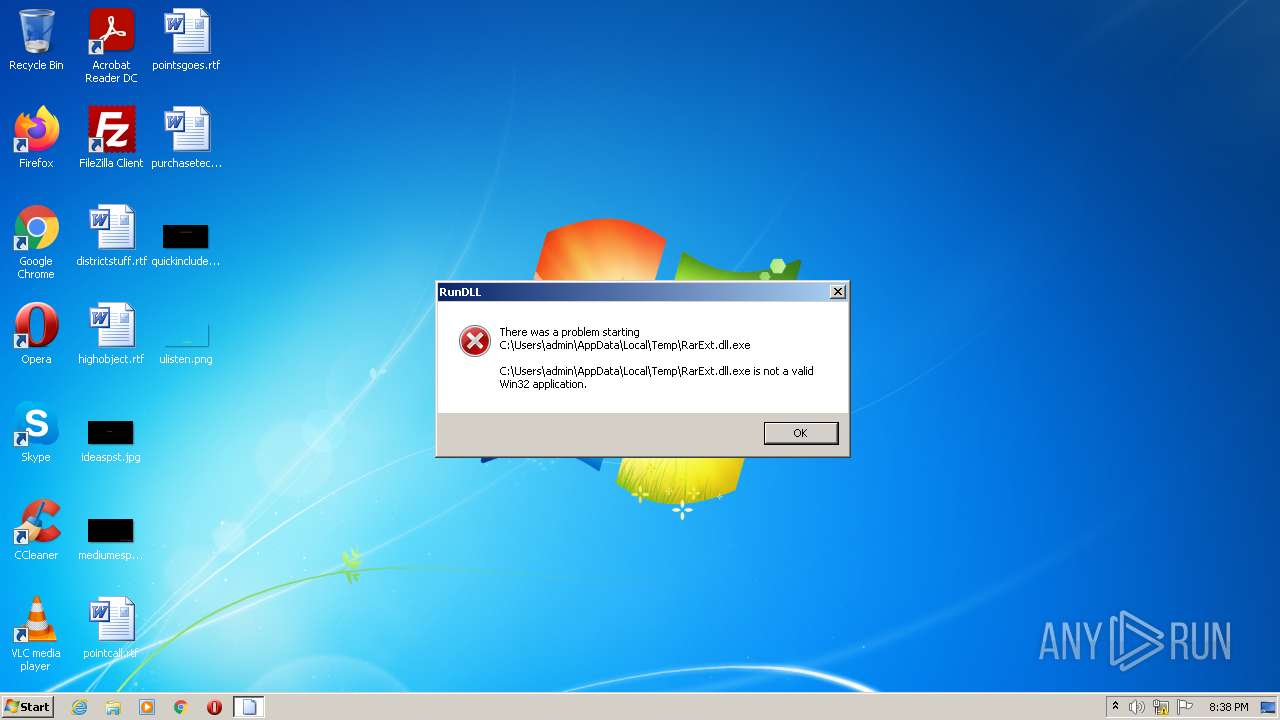
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks supported languages
- cmd.exe (PID: 3440)
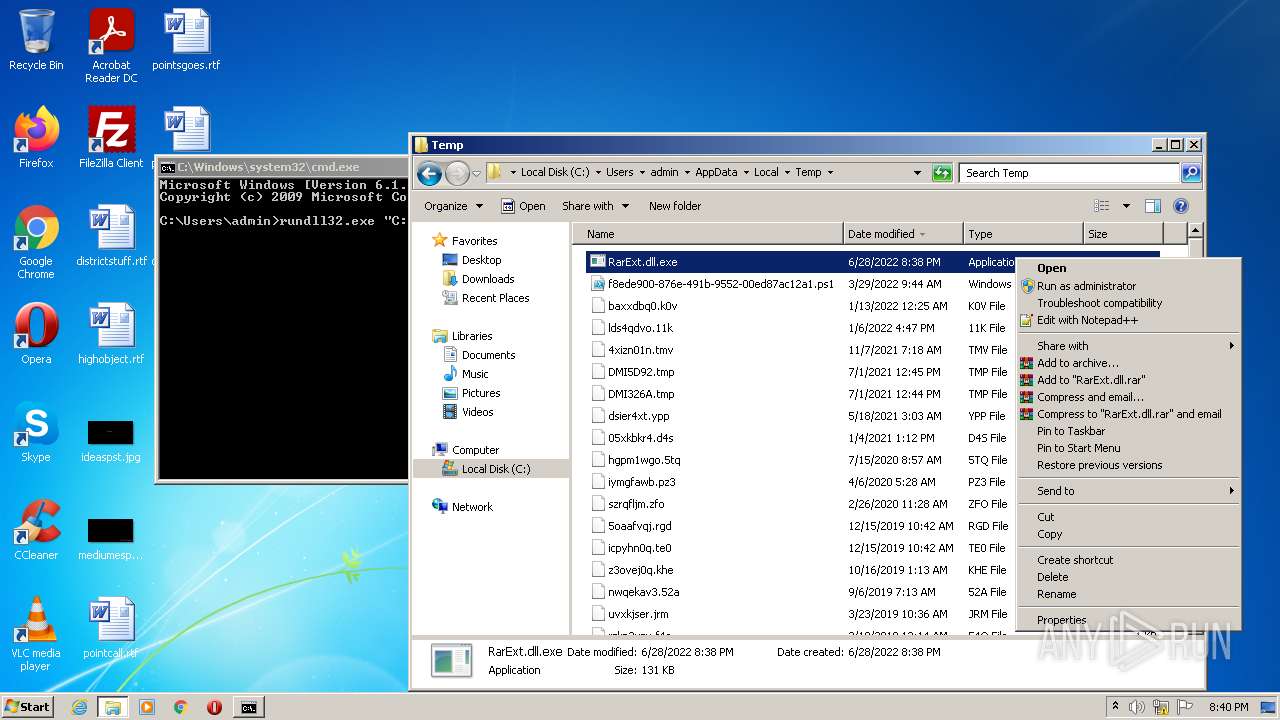
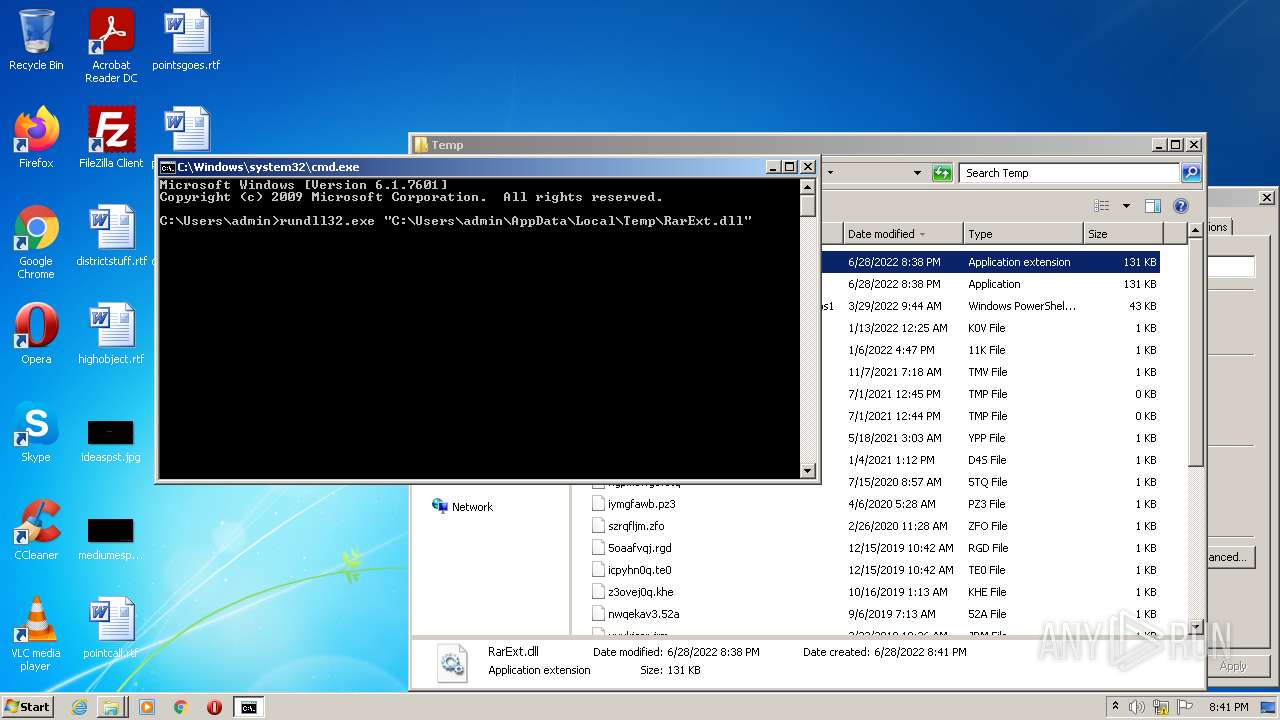
Uses RUNDLL32.EXE to load library
- cmd.exe (PID: 3440)
INFO
Checks supported languages
- rundll32.exe (PID: 3748)
- explorer.exe (PID: 3576)
- rundll32.exe (PID: 1900)
- rundll32.exe (PID: 3396)
Reads the computer name
- explorer.exe (PID: 3576)
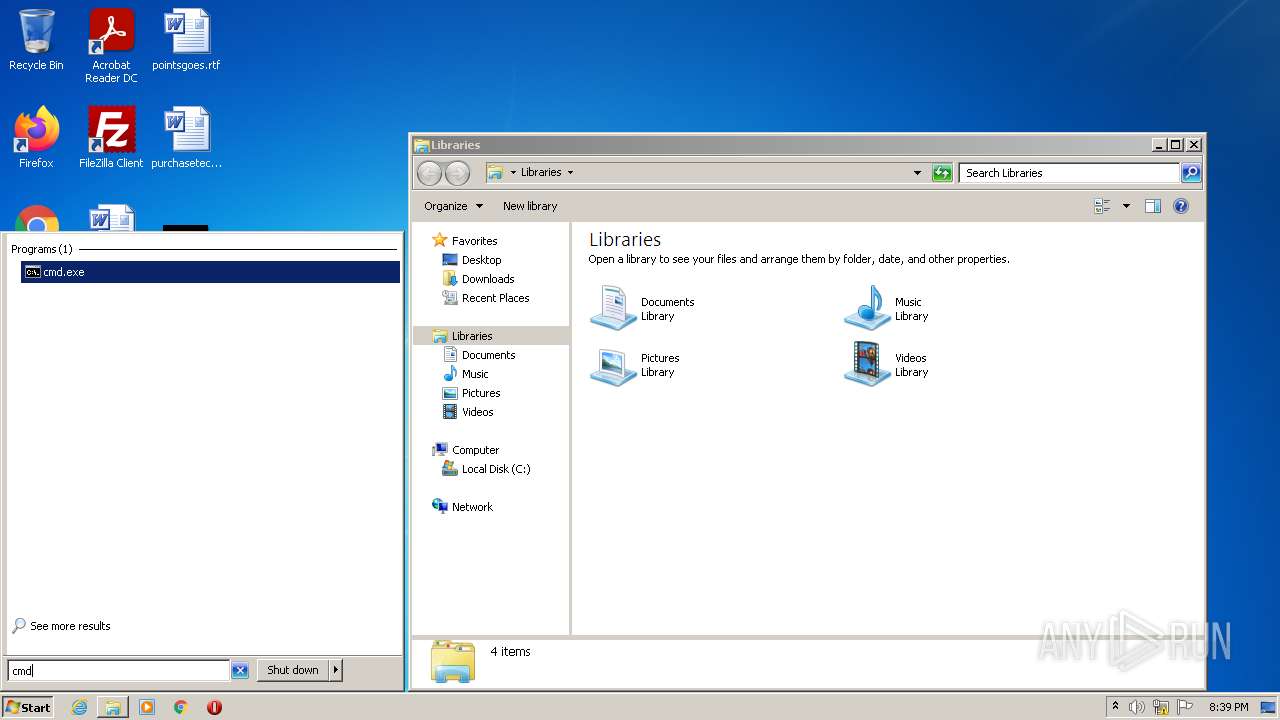
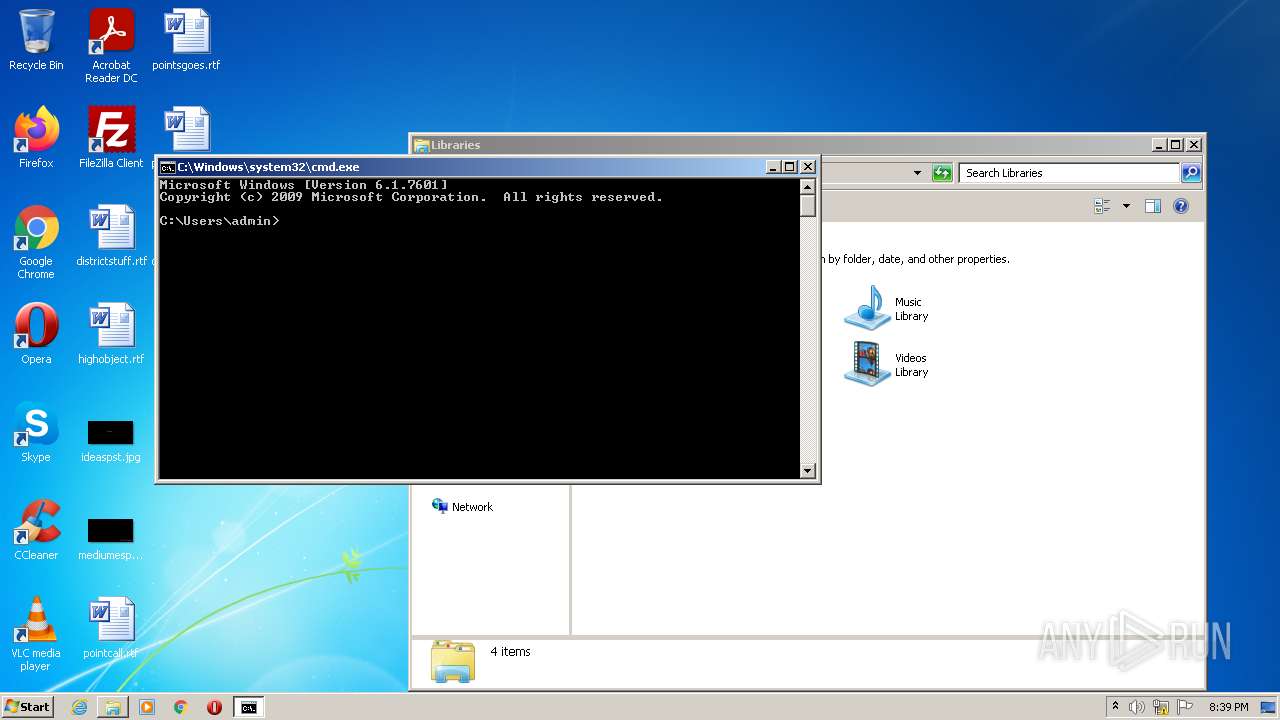
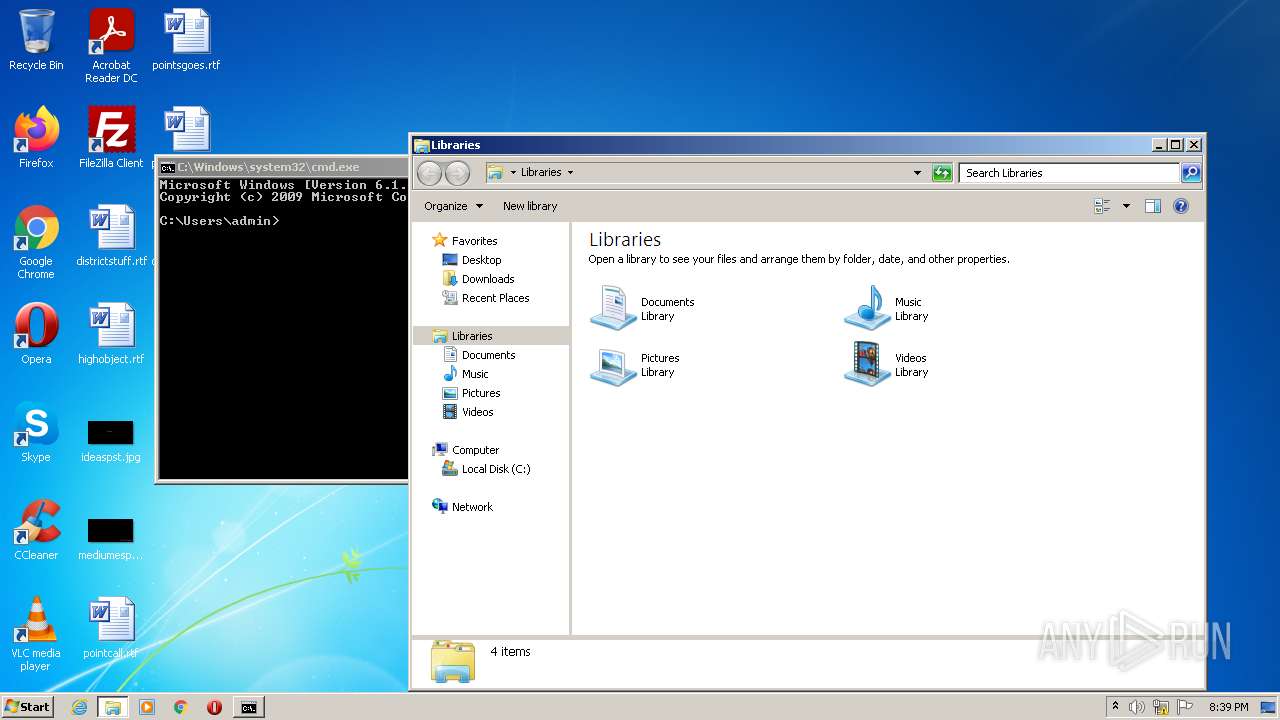
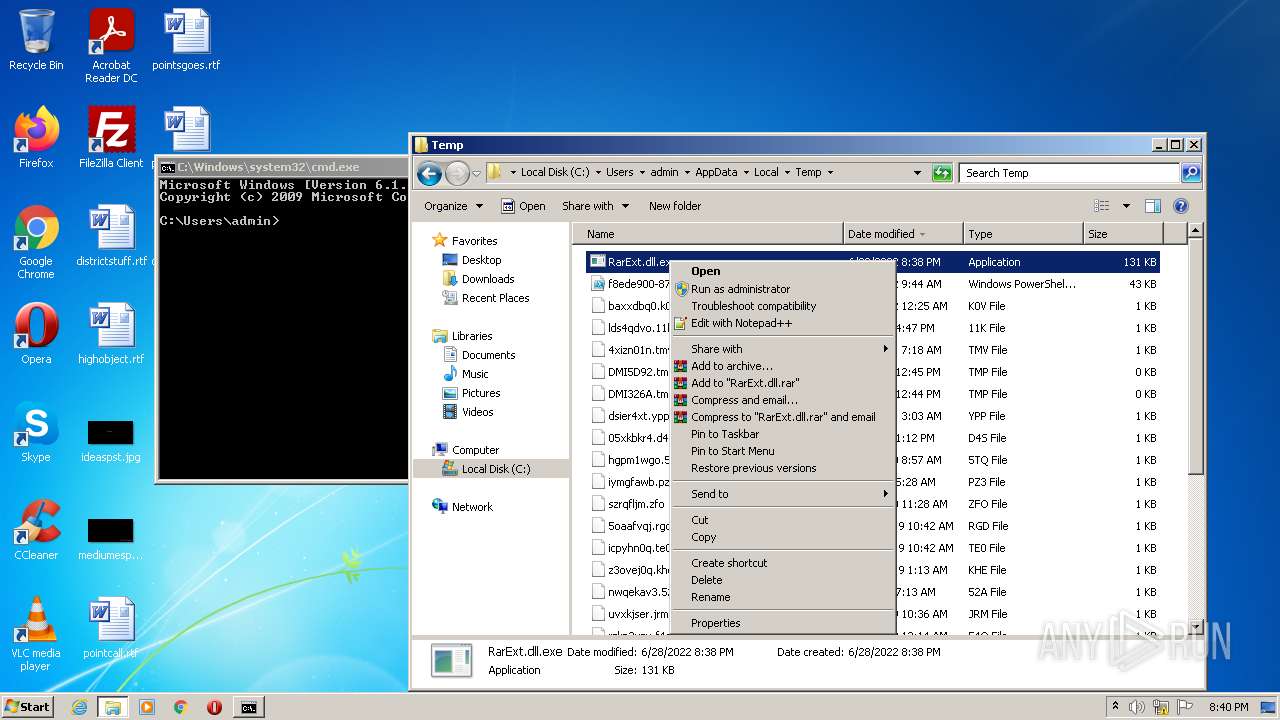
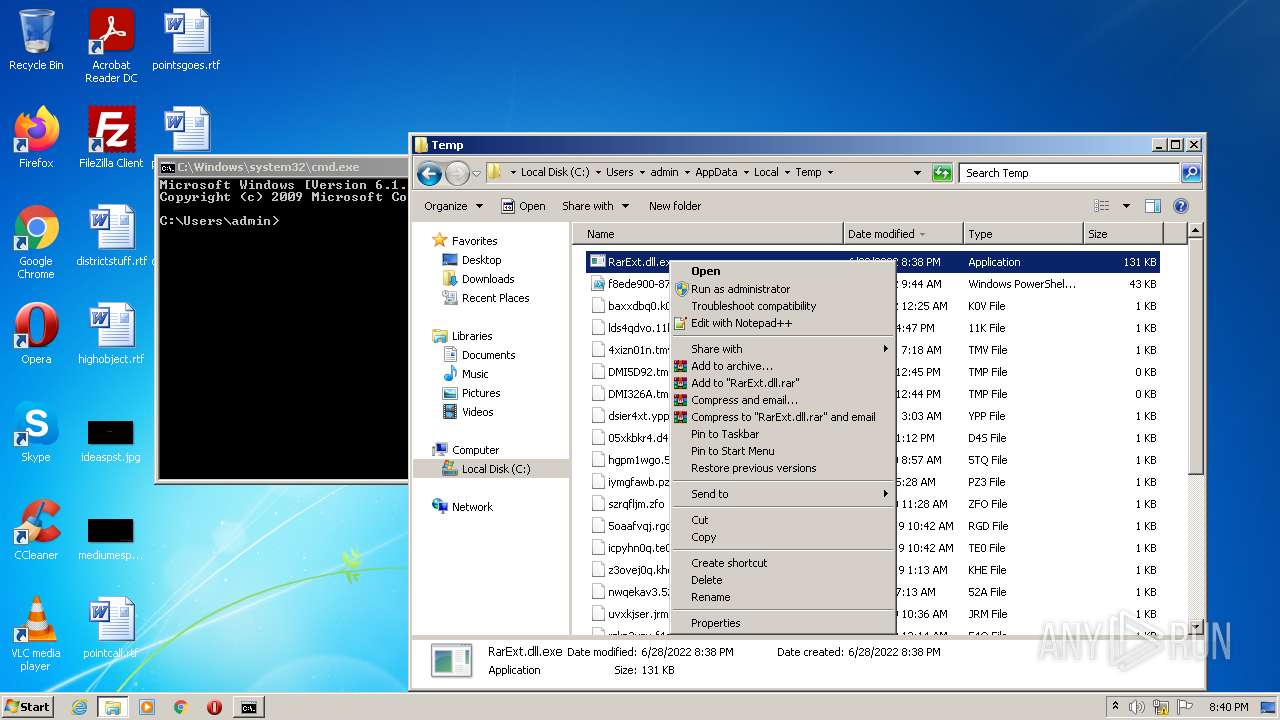
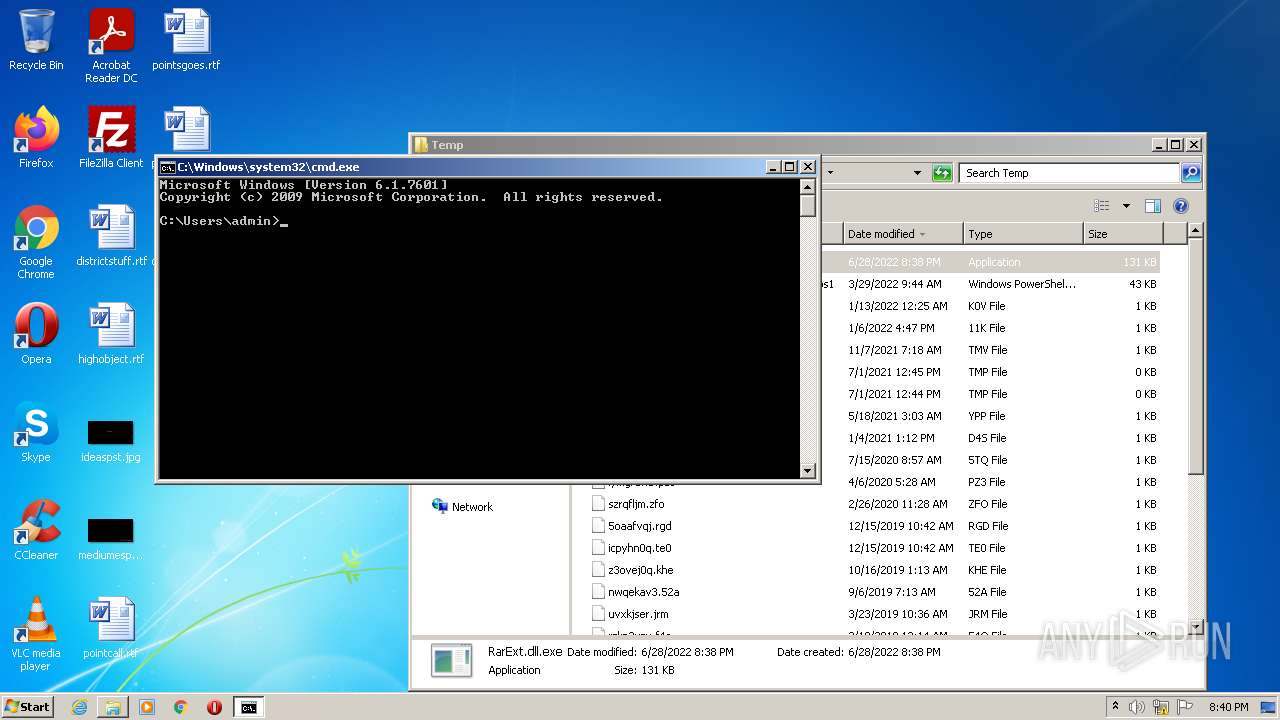
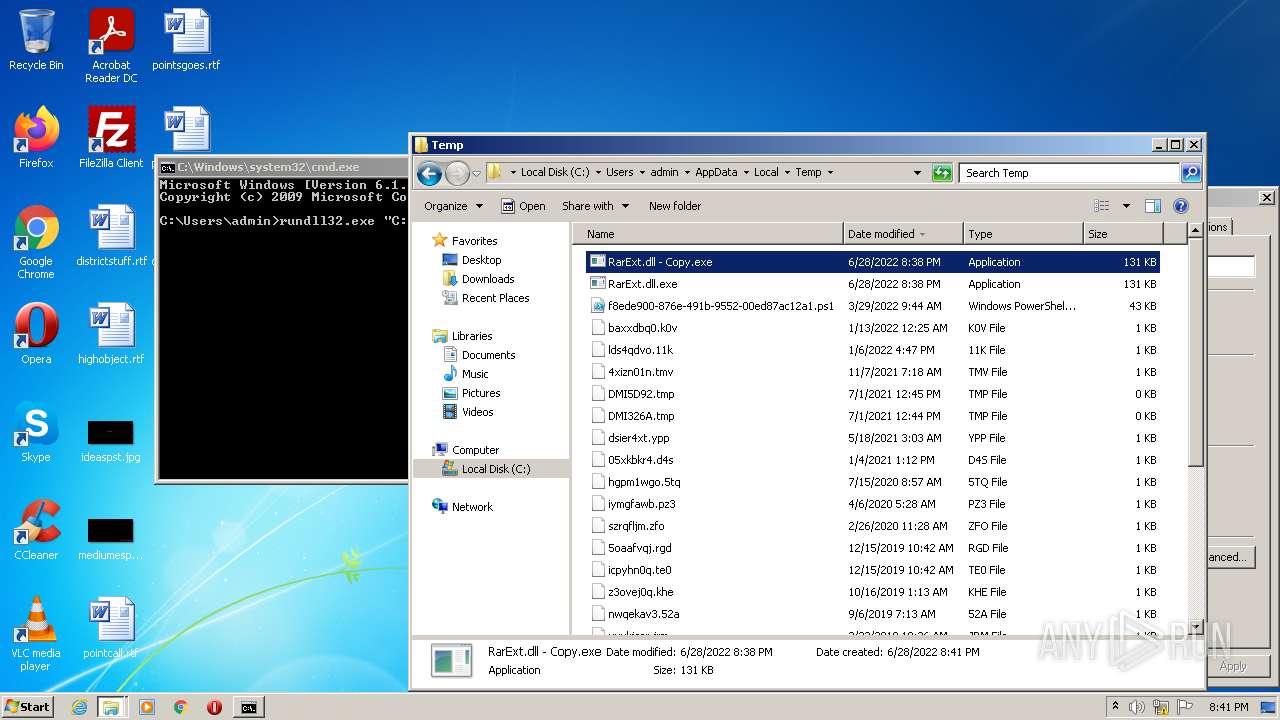
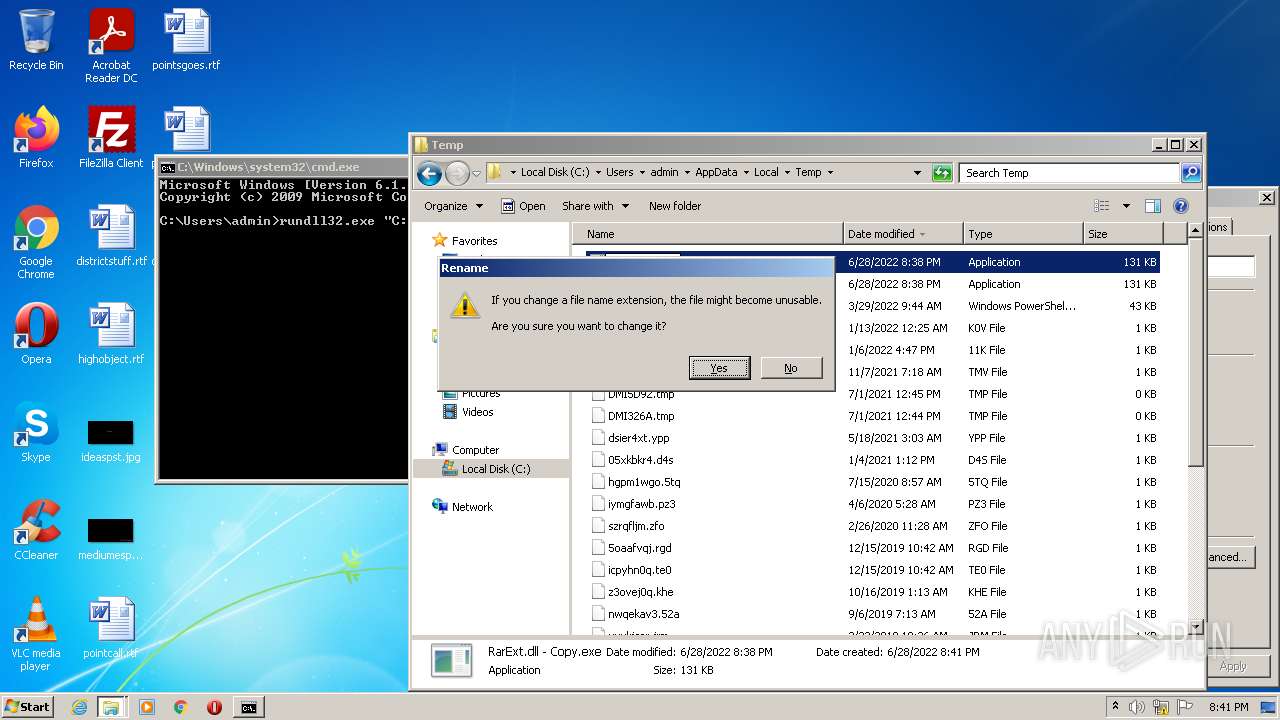
Manual execution by user
- explorer.exe (PID: 3576)
- cmd.exe (PID: 3440)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 6 |
| EntryPoint: | 0x6f00 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 52224 |
| CodeSize: | 80384 |
| LinkerVersion: | 14 |
| PEType: | PE32+ |
| TimeStamp: | 2022:03:10 11:59:44+01:00 |
| MachineType: | AMD AMD64 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_AMD64 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 10-Mar-2022 10:59:44 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0078 |
| Pages in file: | 0x0001 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0x0000 |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x0000 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000078 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_AMD64 |
| Number of sections: | 9 |
| Time date stamp: | 10-Mar-2022 10:59:44 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00F0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000139B6 | 0x00013A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.50435 |
.rdata | 0x00015000 | 0x00009C9C | 0x00009E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.82587 |
.data | 0x0001F000 | 0x00001FE0 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.26558 |
.pdata | 0x00021000 | 0x000011B8 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.93391 |
.00cfg | 0x00023000 | 0x00000028 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.377072 |
.gehcont\x1c | 0x00024000 | 0x0000001C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.142636 |
.voltbl | 0x00025000 | 0x0000002A | 0x00000200 | 0.700112 | |
_RDATA | 0x00026000 | 0x000000F4 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.97766 |
.reloc | 0x00027000 | 0x00000650 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.87553 |
Imports
ADVAPI32.dll |
KERNEL32.dll |
USER32.dll |
WS2_32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
0 | 0x00000000 | |
CreateDecoder | 1 | 0x00006460 |
CreateEncoder | 2 | 0x00006460 |
CreateObject | 3 | 0x00006460 |
GetHandlerProperty | 4 | 0x00006460 |
GetHandlerProperty2 | 5 | 0x00006460 |
GetHashers | 6 | 0x00006460 |
GetIsArc | 7 | 0x00006480 |
GetMethodProperty | 8 | 0x00006460 |
GetNumberOfFormats | 9 | 0x00006460 |
Total processes
43
Monitored processes
5
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
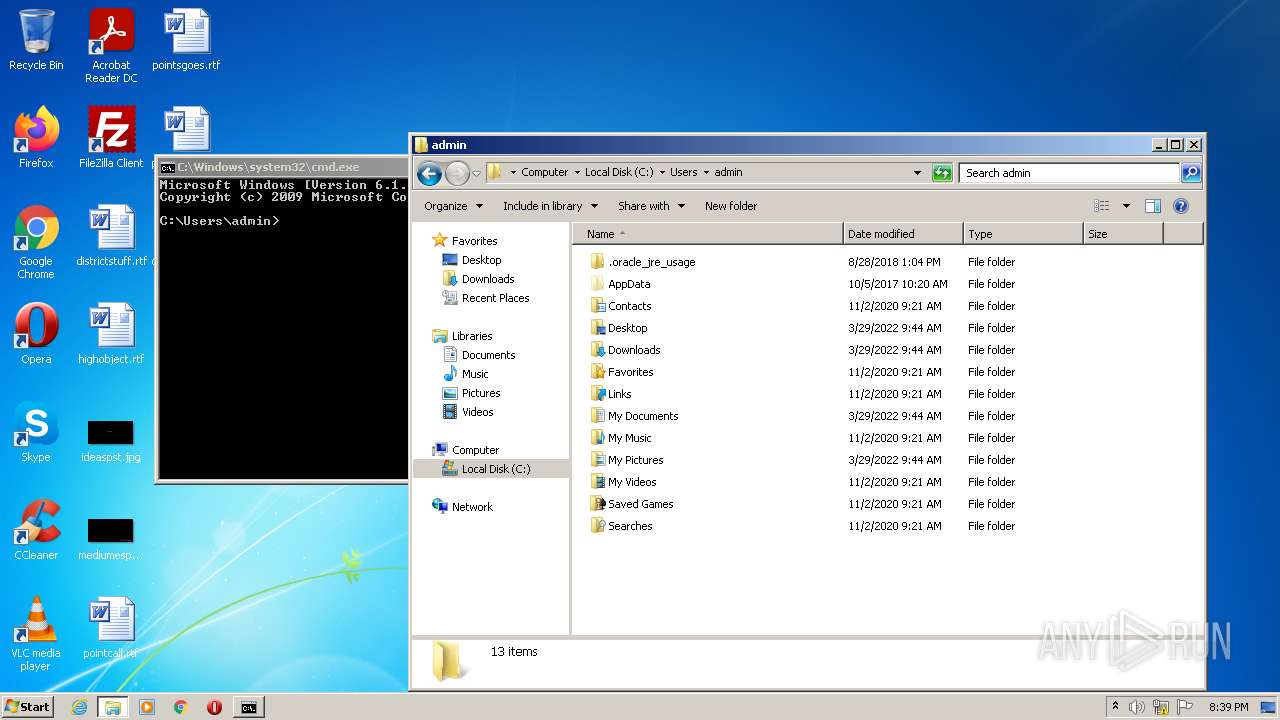
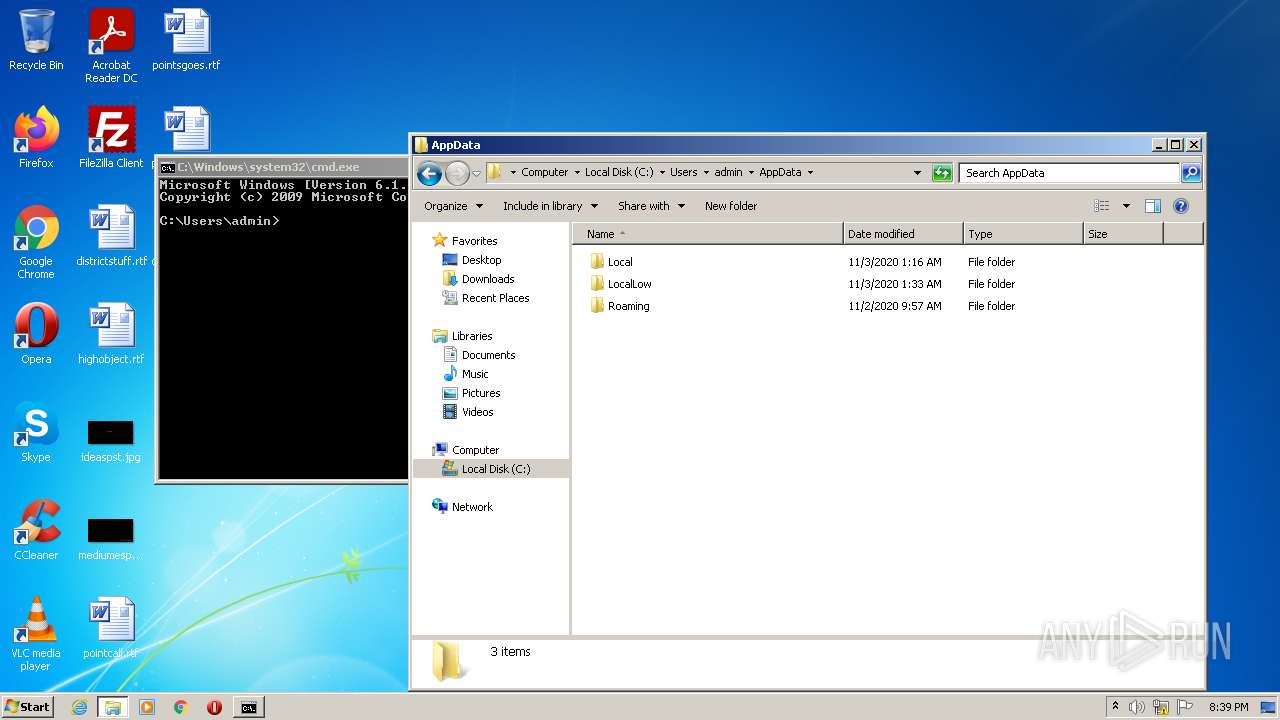
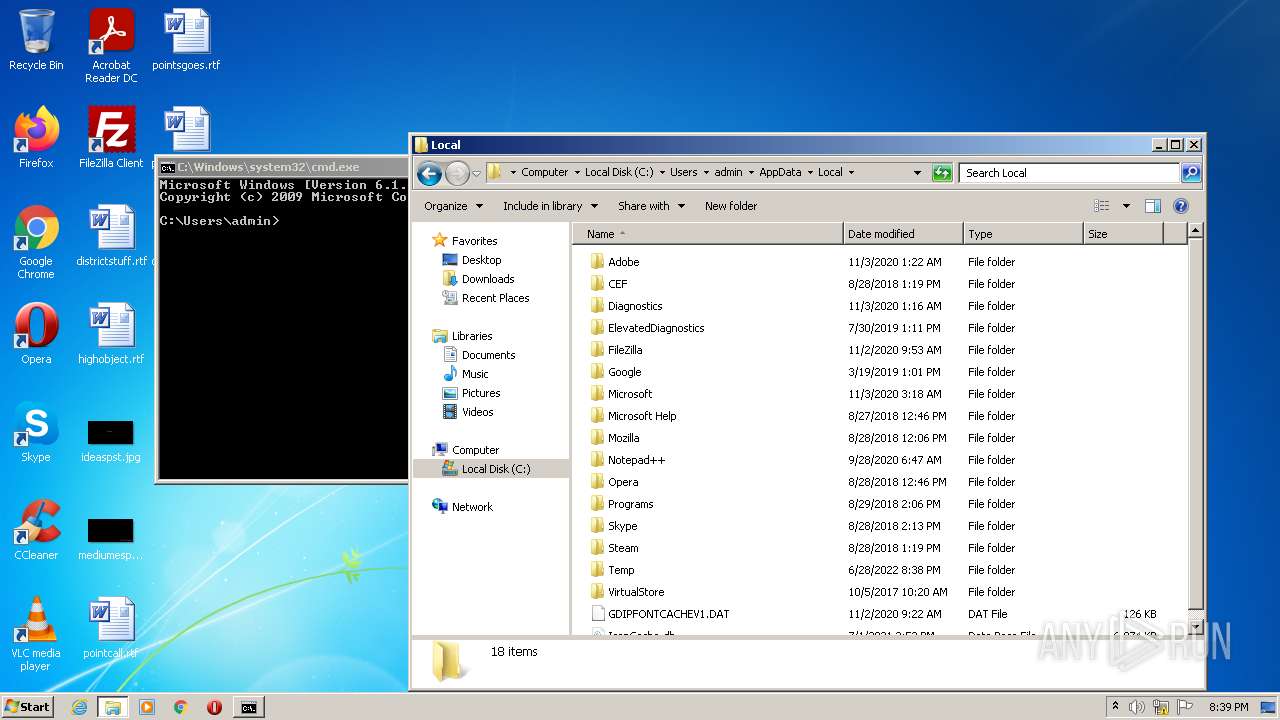
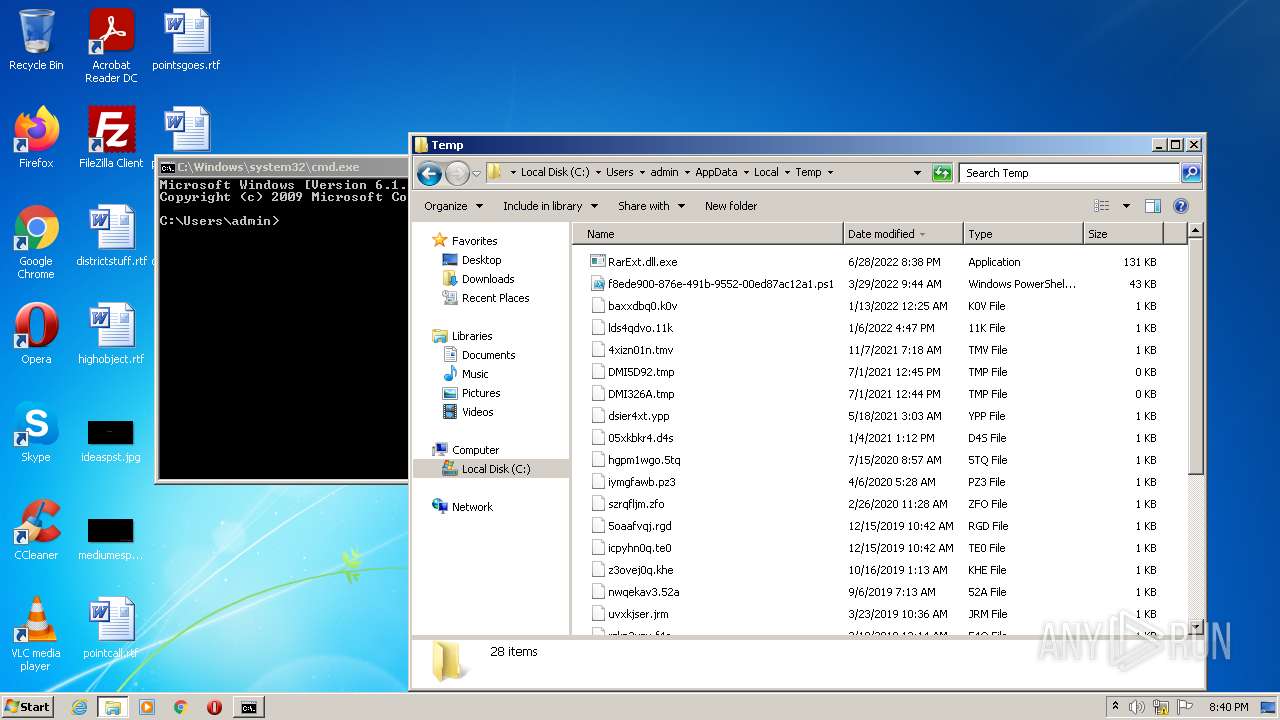
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
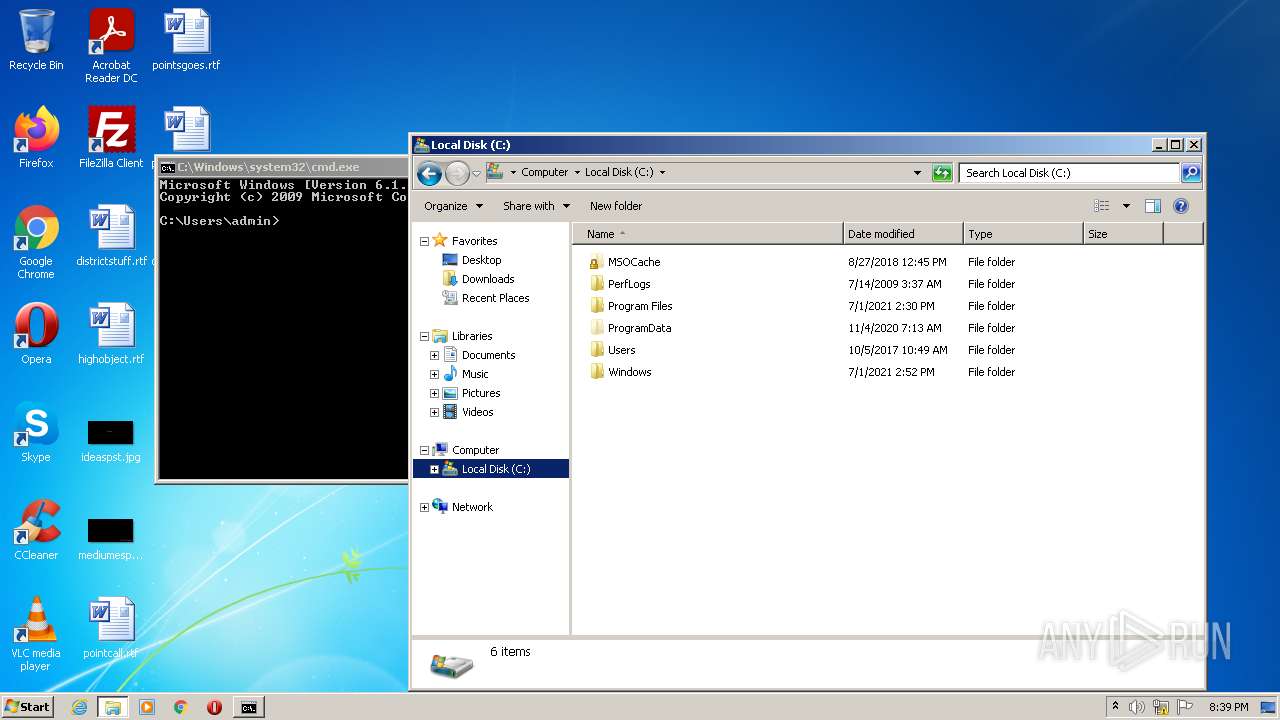
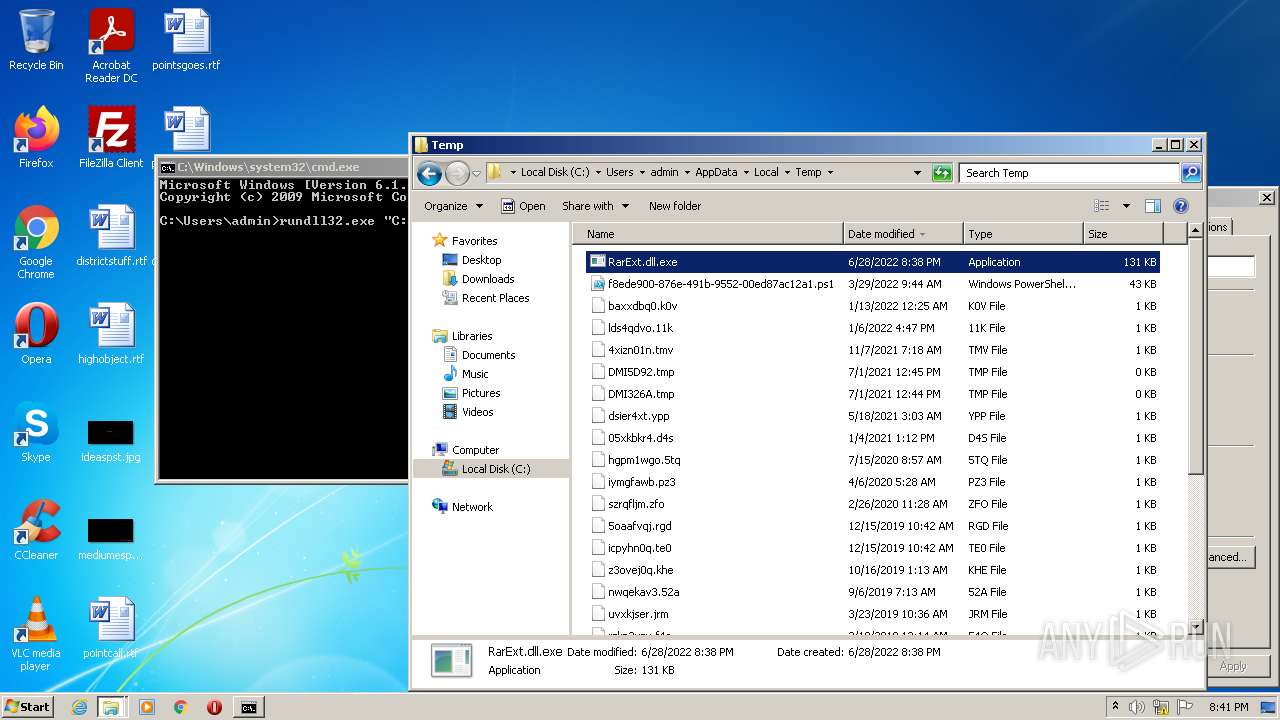
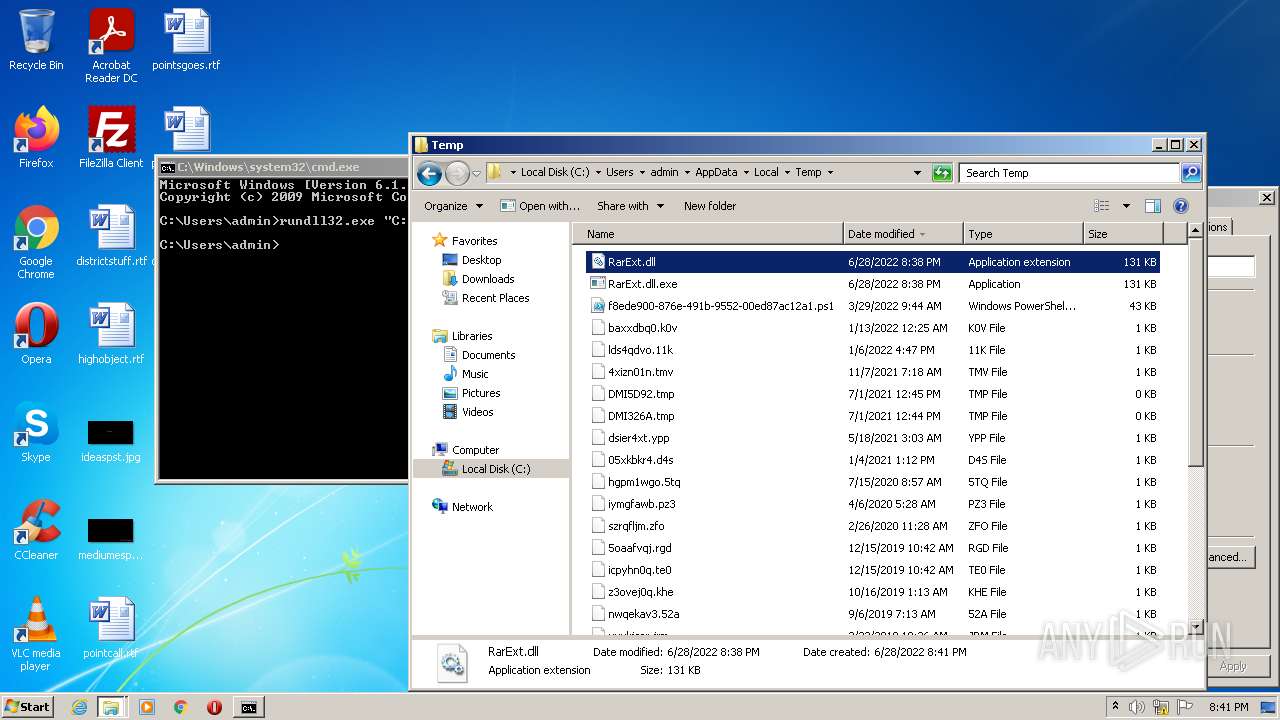
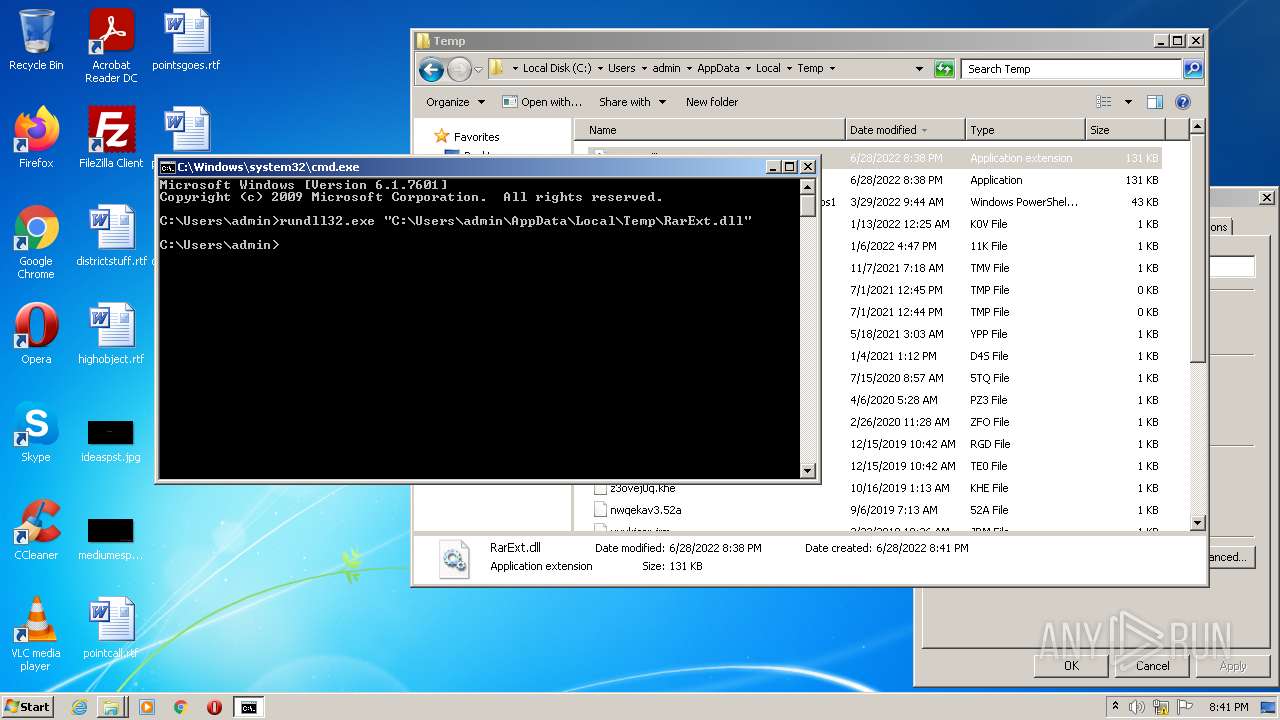
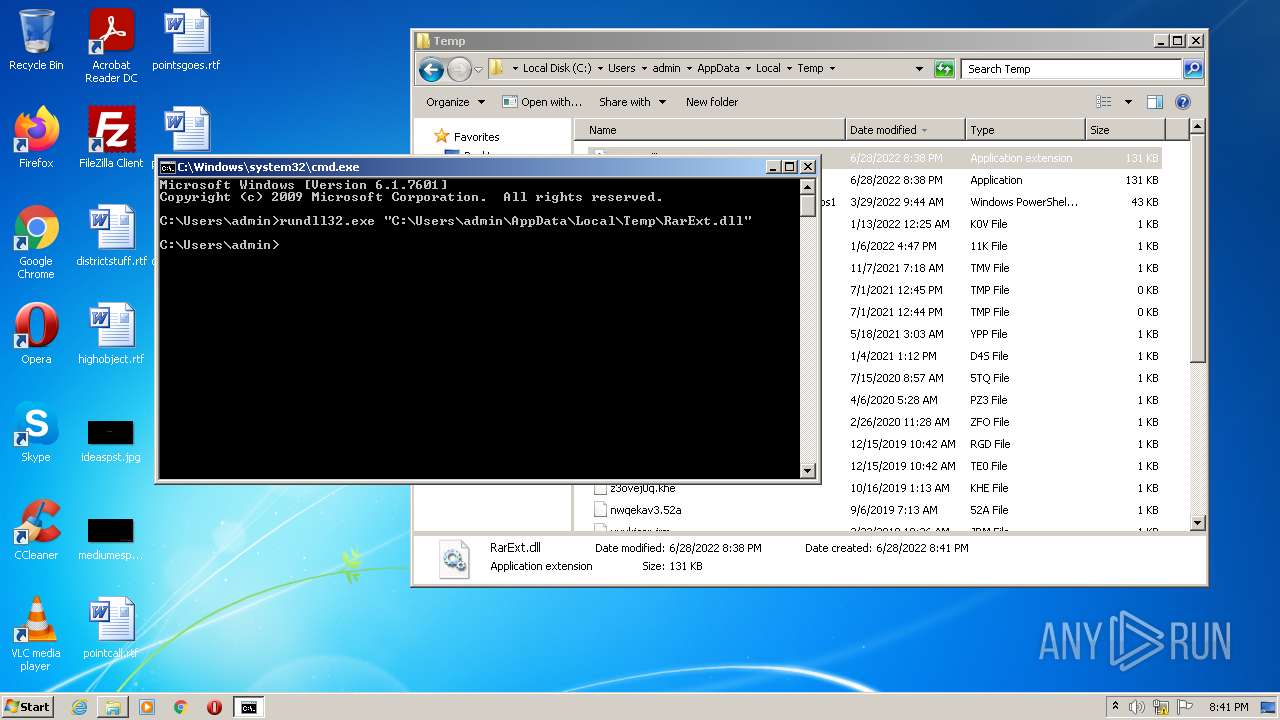
| 1900 | rundll32.exe "C:\Users\admin\AppData\Local\Temp\RarExt.dll" | C:\Windows\system32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3396 | rundll32.exe "C:\Users\admin\AppData\Local\Temp\RarExt.dll" | C:\Windows\system32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3440 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3576 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
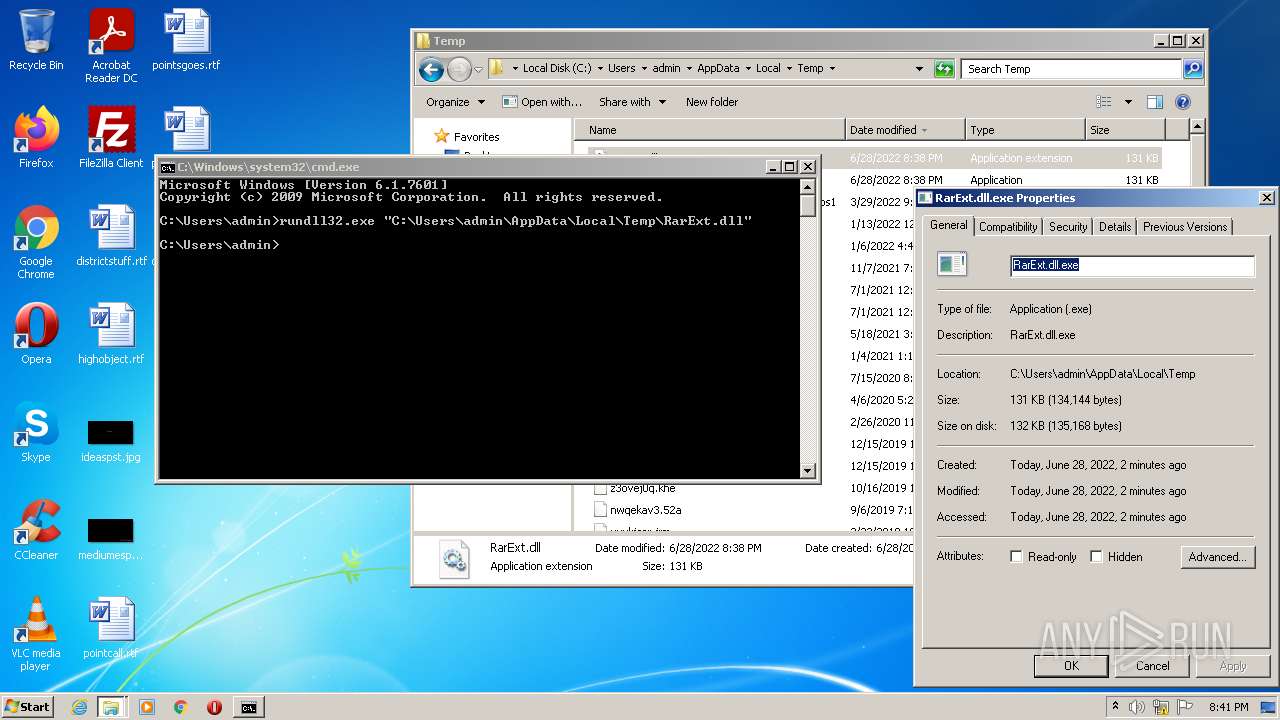
| 3748 | "C:\Windows\System32\rundll32.exe" "C:\Users\admin\AppData\Local\Temp\RarExt.dll.exe", CreateDecoder | C:\Windows\System32\rundll32.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
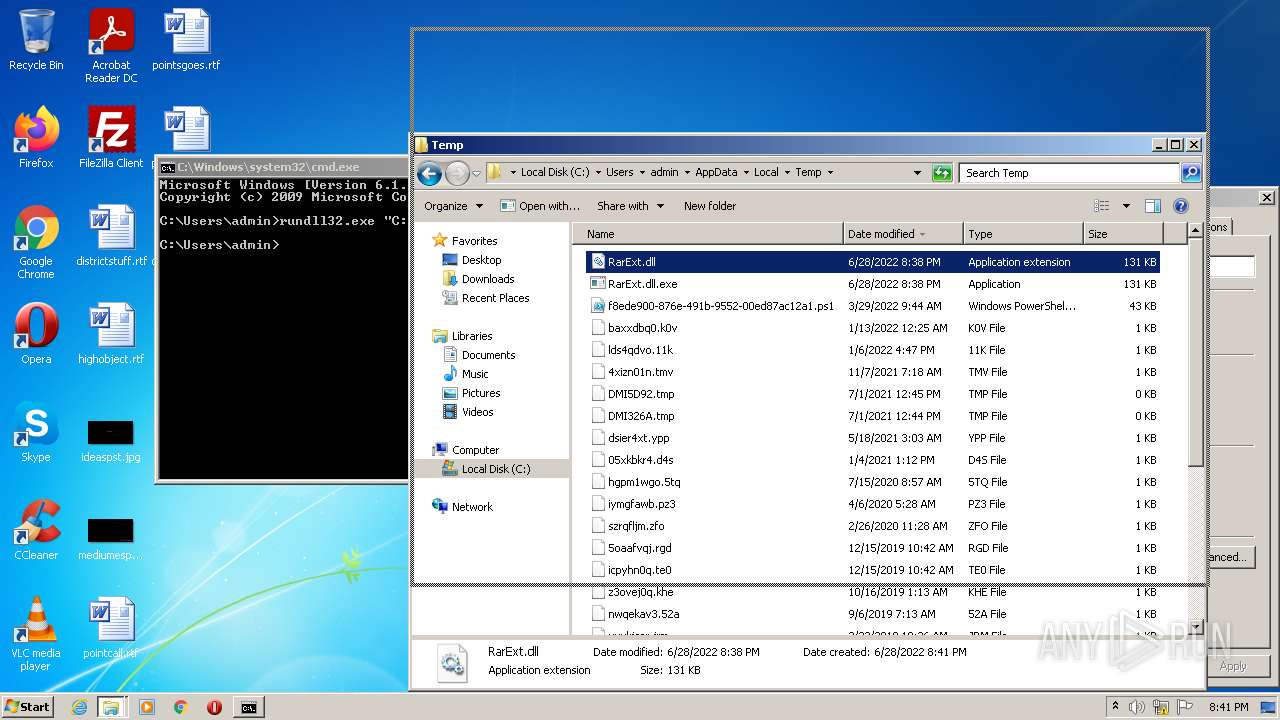
Total events
100
Read events
100
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report