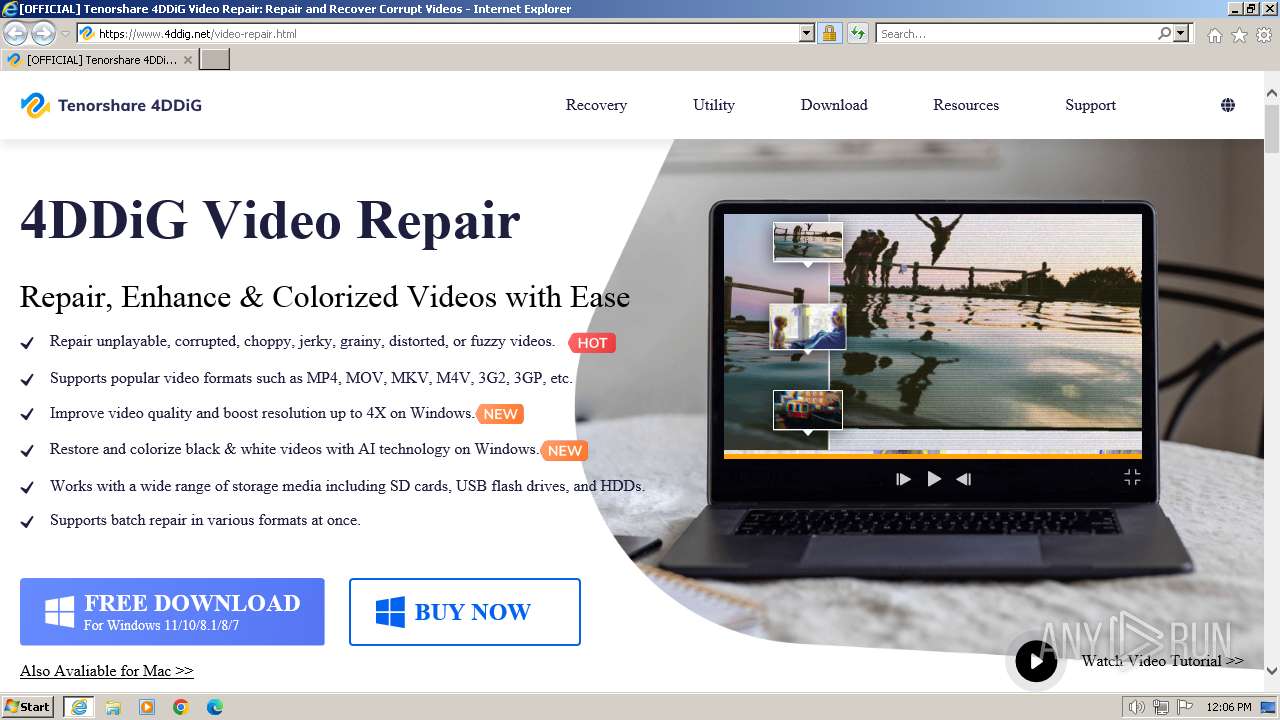
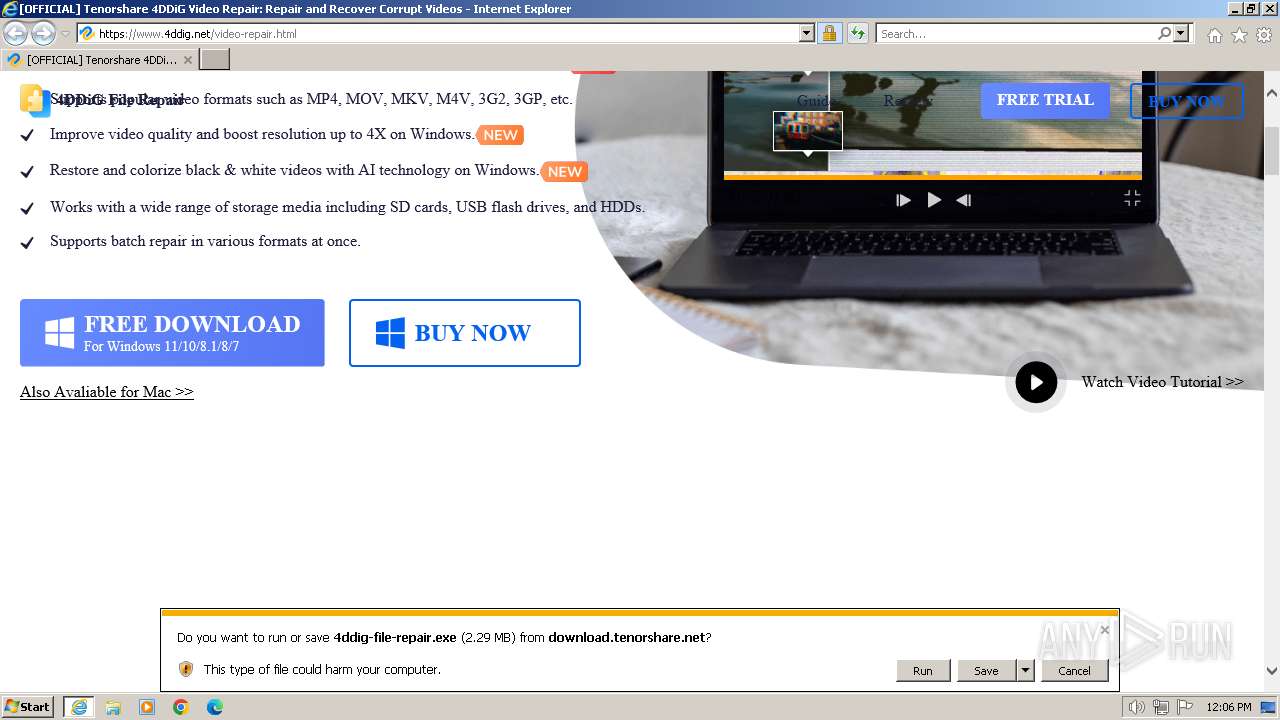
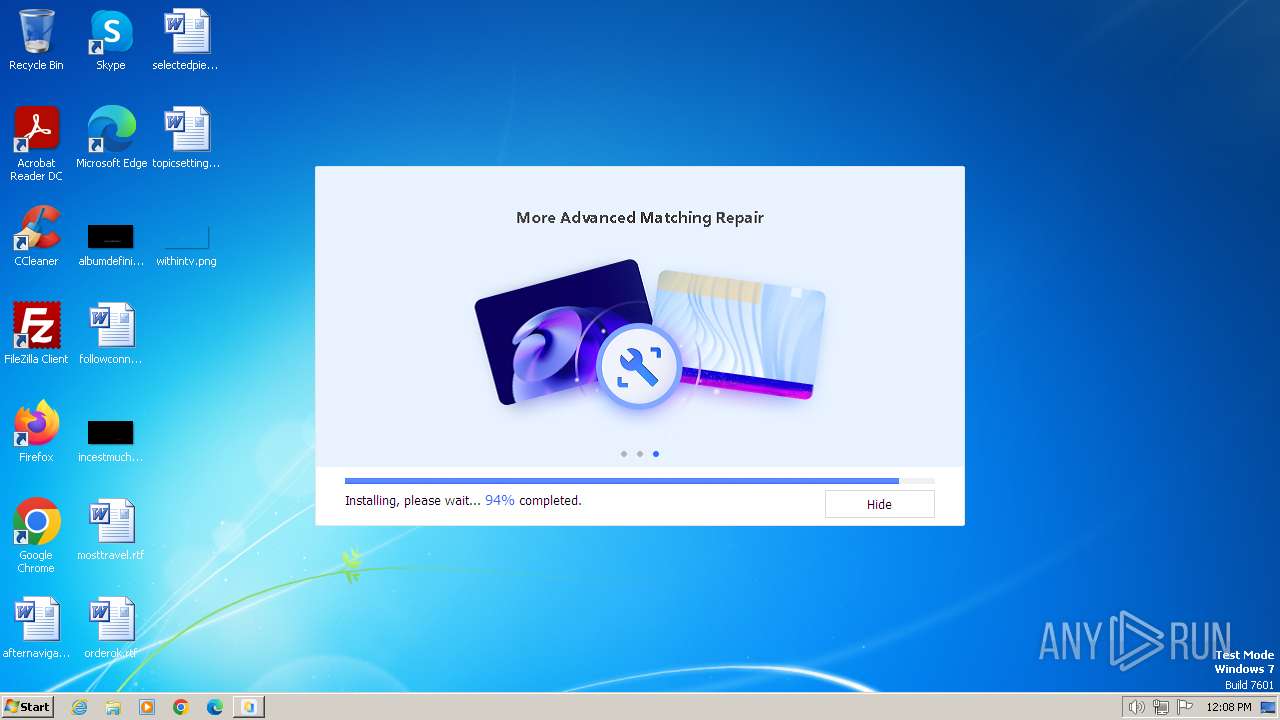
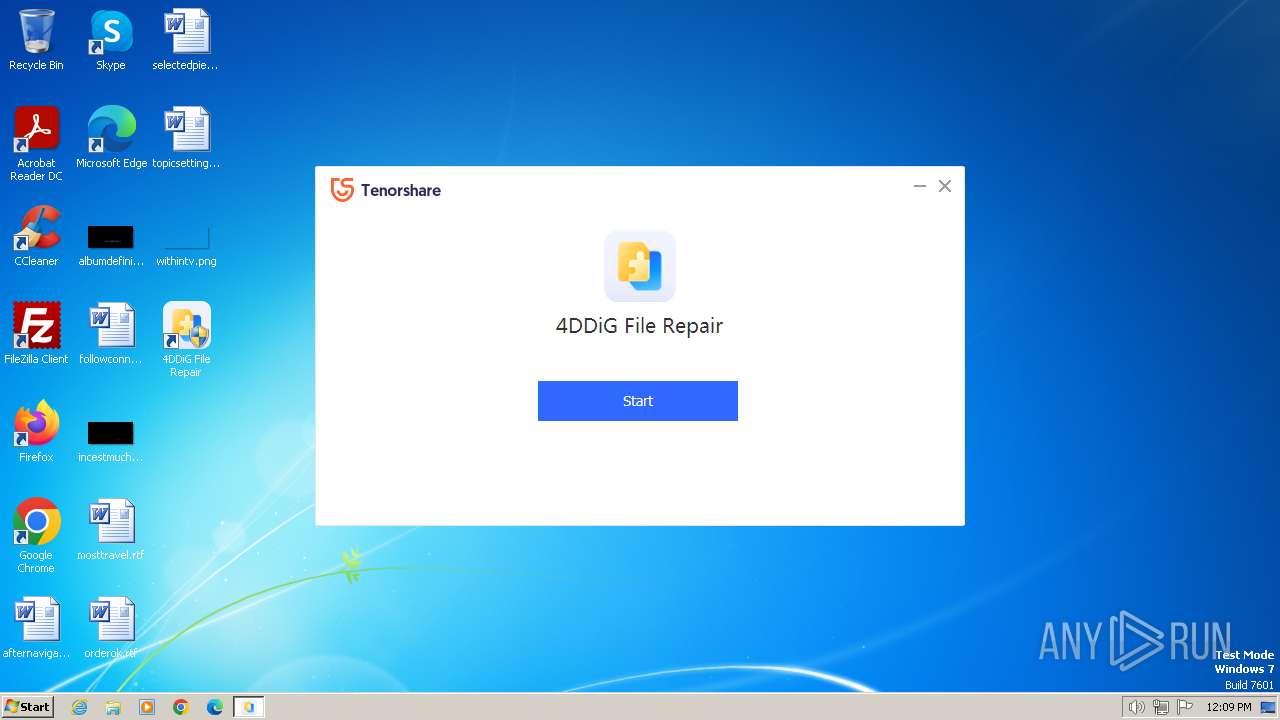
| URL: | https://www.4ddig.net/video-repair.html |
| Full analysis: | https://app.any.run/tasks/7ec0a0a8-179d-40e9-8463-1603e36d5f84 |
| Verdict: | Malicious activity |
| Analysis date: | January 01, 2024, 12:06:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 7621D441BDCC61152C11DC0BBF924A06 |
| SHA1: | E2FE302C3DB1C69F94A6DEB0531EBA33A495B880 |
| SHA256: | 1D6AF6338EB3AECE29E089A0E66FD71C416CD627632881864385EC24753E1619 |
| SSDEEP: | 3:N8DSLn62dKIXWG:2OLRdbWG |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads settings of System Certificates
- 4ddig-file-repair.exe (PID: 2740)
- 4DDiG File Repair.exe (PID: 3164)
Reads the Internet Settings
- 4ddig-file-repair.exe (PID: 2740)
- 4ddigfilerepair_4ddignet_3.1.4.tmp (PID: 2776)
- NetFrameCheck.exe (PID: 3120)
- 4DDiG File Repair.exe (PID: 3164)
Reads security settings of Internet Explorer
- 4ddig-file-repair.exe (PID: 2740)
- 4DDiG File Repair.exe (PID: 3164)
Checks Windows Trust Settings
- 4ddig-file-repair.exe (PID: 2740)
- 4DDiG File Repair.exe (PID: 3164)
Reads the Windows owner or organization settings
- 4ddigfilerepair_4ddignet_3.1.4.tmp (PID: 2776)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2764)
- cmd.exe (PID: 3004)
- cmd.exe (PID: 480)
- cmd.exe (PID: 3652)
- cmd.exe (PID: 4088)
- cmd.exe (PID: 3876)
- cmd.exe (PID: 1092)
- cmd.exe (PID: 4020)
- cmd.exe (PID: 980)
- cmd.exe (PID: 392)
- cmd.exe (PID: 2588)
- cmd.exe (PID: 2348)
- cmd.exe (PID: 572)
- cmd.exe (PID: 2804)
- cmd.exe (PID: 2688)
- cmd.exe (PID: 1588)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- cmd.exe (PID: 1220)
- cmd.exe (PID: 1088)
- cmd.exe (PID: 2172)
- cmd.exe (PID: 3116)
- cmd.exe (PID: 3288)
- cmd.exe (PID: 3380)
- cmd.exe (PID: 1040)
- cmd.exe (PID: 1976)
- cmd.exe (PID: 2712)
- cmd.exe (PID: 2752)
- cmd.exe (PID: 3732)
- cmd.exe (PID: 2348)
Starts CMD.EXE for commands execution
- 4ddigfilerepair_4ddignet_3.1.4.tmp (PID: 2776)
- 4DDiG File Repair.exe (PID: 3164)
Uses NETSH.EXE to add a firewall rule or allowed programs
- cmd.exe (PID: 2092)
- cmd.exe (PID: 3820)
- cmd.exe (PID: 1784)
- cmd.exe (PID: 880)
- cmd.exe (PID: 2664)
- cmd.exe (PID: 3252)
- cmd.exe (PID: 3324)
- cmd.exe (PID: 3508)
- cmd.exe (PID: 2764)
- cmd.exe (PID: 4032)
- cmd.exe (PID: 3884)
- cmd.exe (PID: 2424)
- cmd.exe (PID: 2416)
- cmd.exe (PID: 1924)
- cmd.exe (PID: 568)
- cmd.exe (PID: 584)
- cmd.exe (PID: 2256)
- cmd.exe (PID: 3212)
- cmd.exe (PID: 1996)
- cmd.exe (PID: 3064)
- cmd.exe (PID: 1028)
- cmd.exe (PID: 2760)
- cmd.exe (PID: 3016)
- cmd.exe (PID: 3524)
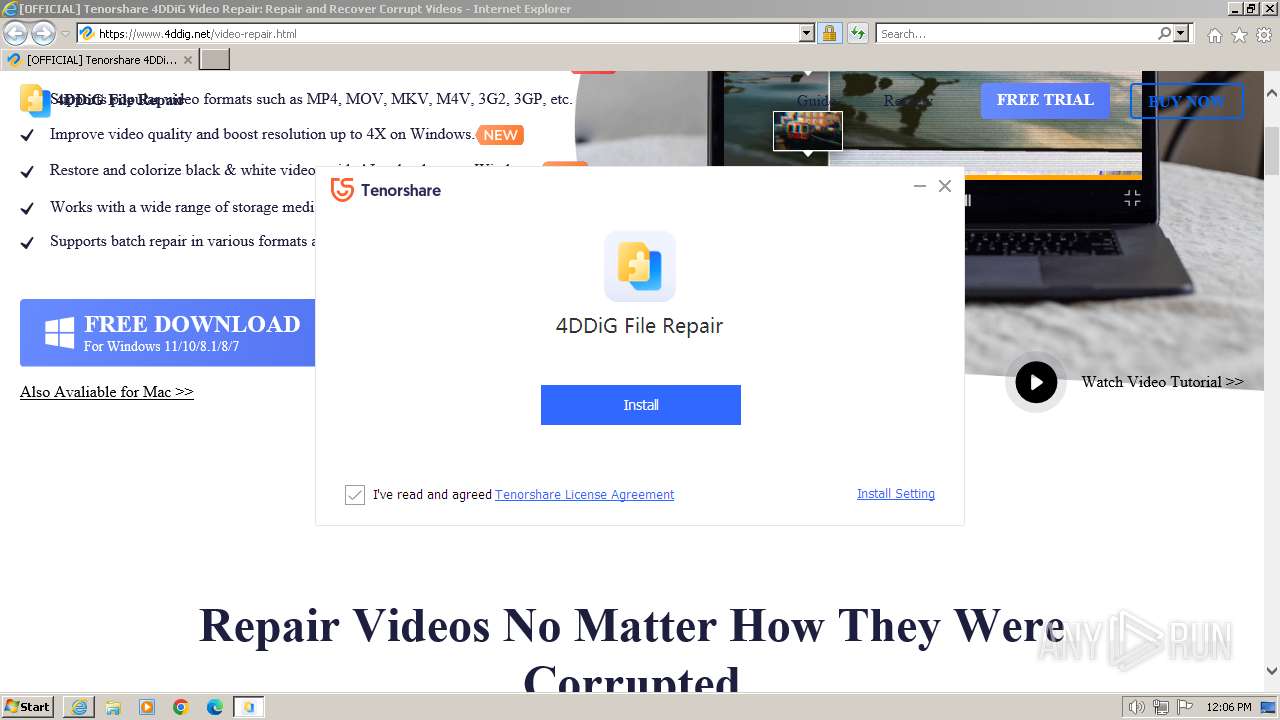
Creates a software uninstall entry
- 4ddig-file-repair.exe (PID: 2740)
- 4DDiG File Repair.exe (PID: 3164)
Searches for installed software
- 4DDiG File Repair.exe (PID: 3164)
INFO
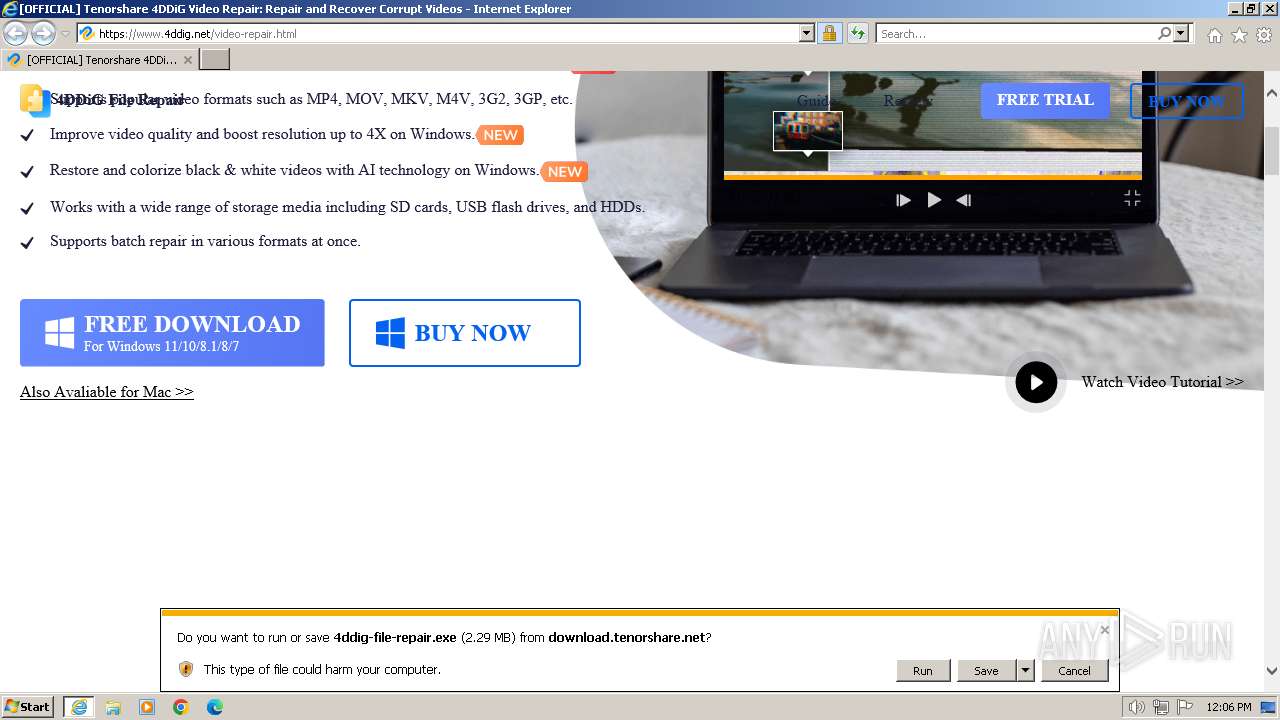
Drops the executable file immediately after the start
- iexplore.exe (PID: 1056)
- iexplore.exe (PID: 2184)
- 4ddigfilerepair_4ddignet_3.1.4.exe (PID: 3424)
- 4ddigfilerepair_4ddignet_3.1.4.tmp (PID: 2776)
- 4DDiG File Repair.exe (PID: 3164)
Application launched itself
- iexplore.exe (PID: 2184)
- msedge.exe (PID: 3328)
- msedge.exe (PID: 3864)
The process uses the downloaded file
- iexplore.exe (PID: 2184)
Reads Environment values
- 4ddig-file-repair.exe (PID: 2740)
- 4DDiG File Repair.exe (PID: 3164)
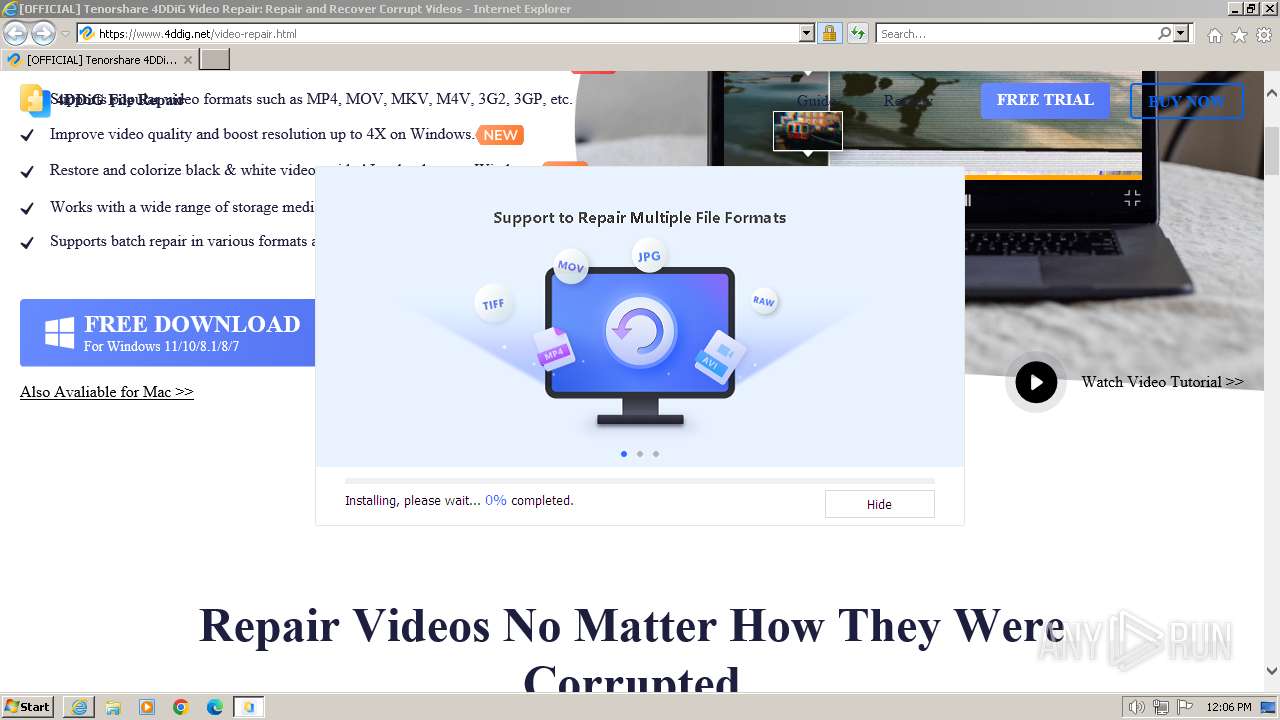
Create files in a temporary directory
- 4ddig-file-repair.exe (PID: 2740)
- 4ddigfilerepair_4ddignet_3.1.4.exe (PID: 3424)
- 4ddigfilerepair_4ddignet_3.1.4.tmp (PID: 2776)
- 4DDiG File Repair.exe (PID: 3164)
Checks supported languages
- 4ddig-file-repair.exe (PID: 2740)
- 4ddigfilerepair_4ddignet_3.1.4.exe (PID: 3424)
- 4ddigfilerepair_4ddignet_3.1.4.tmp (PID: 2776)
- NetFrameCheck.exe (PID: 3120)
- 4DDiG File Repair.exe (PID: 3164)
- FRUpdateService.exe (PID: 3108)
Reads the computer name
- 4ddig-file-repair.exe (PID: 2740)
- 4ddigfilerepair_4ddignet_3.1.4.tmp (PID: 2776)
- NetFrameCheck.exe (PID: 3120)
- 4DDiG File Repair.exe (PID: 3164)
Checks proxy server information
- 4ddig-file-repair.exe (PID: 2740)
- 4DDiG File Repair.exe (PID: 3164)
Reads the machine GUID from the registry
- 4ddig-file-repair.exe (PID: 2740)
- 4DDiG File Repair.exe (PID: 3164)
Creates files or folders in the user directory
- 4ddig-file-repair.exe (PID: 2740)
- 4DDiG File Repair.exe (PID: 3164)
Creates files in the program directory
- 4ddig-file-repair.exe (PID: 2740)
- 4ddigfilerepair_4ddignet_3.1.4.tmp (PID: 2776)
- NetFrameCheck.exe (PID: 3120)
- 4DDiG File Repair.exe (PID: 3164)
- FRUpdateService.exe (PID: 3108)
Connects to the CnC server
- 4ddig-file-repair.exe (PID: 2740)
Checks for external IP
- 4ddig-file-repair.exe (PID: 2740)
The process drops C-runtime libraries
- 4ddigfilerepair_4ddignet_3.1.4.tmp (PID: 2776)
Drops 7-zip archiver for unpacking
- 4ddigfilerepair_4ddignet_3.1.4.tmp (PID: 2776)
Process drops legitimate windows executable
- 4ddigfilerepair_4ddignet_3.1.4.tmp (PID: 2776)
Manual execution by a user
- msedge.exe (PID: 3864)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
233
Monitored processes
136
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | netsh advfirewall firewall add rule name="4DDiG File Repair_MediaInfoService" dir=in action=allow program="C:\Program Files\Tenorshare\4DDiG File Repair\MediaInfoService.exe" enable=yes | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 188 | netsh advfirewall firewall add rule name="4DDiG File Repair_AudioRepairService" dir=in action=allow program="C:\Program Files\Tenorshare\4DDiG File Repair\AudioRepairService.exe" enable=yes | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 296 | taskkill /f /t /im "PhotoPreviewService.exe" | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 392 | "C:\Windows\system32\cmd.exe" /c taskkill /f /t /im "doc-repair-office.exe" | C:\Windows\System32\cmd.exe | — | 4ddigfilerepair_4ddignet_3.1.4.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 128 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 480 | "C:\Windows\system32\cmd.exe" /c taskkill /f /t /im "AudioRepairService.exe" | C:\Windows\System32\cmd.exe | — | 4ddigfilerepair_4ddignet_3.1.4.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 128 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 568 | "C:\Windows\system32\cmd.exe" /c netsh advfirewall firewall add rule name="4DDiG File Repair_MediaPlayerService" dir=in action=allow program="C:\Program Files\Tenorshare\4DDiG File Repair\MediaPlayerService.exe" enable=yes | C:\Windows\System32\cmd.exe | — | 4ddigfilerepair_4ddignet_3.1.4.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 572 | "C:\Windows\system32\cmd.exe" /c taskkill /f /t /im "TsRepairService.exe" | C:\Windows\System32\cmd.exe | — | 4ddigfilerepair_4ddignet_3.1.4.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 128 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 584 | "C:\Windows\system32\cmd.exe" /c netsh advfirewall firewall add rule name="4DDiG File Repair_MediaInfoService" dir=out action=allow program="C:\Program Files\Tenorshare\4DDiG File Repair\MediaInfoService.exe" enable=yes | C:\Windows\System32\cmd.exe | — | 4ddigfilerepair_4ddignet_3.1.4.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 796 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2348 --field-trial-handle=1328,i,15878536215920303539,14866154365417374674,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 880 | "C:\Windows\system32\cmd.exe" /c netsh advfirewall firewall add rule name="4DDiG File Repair_NetFrameCheck" dir=in action=allow program="C:\Program Files\Tenorshare\4DDiG File Repair\NetFrameCheck.exe" enable=yes | C:\Windows\System32\cmd.exe | — | 4ddigfilerepair_4ddignet_3.1.4.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
46 519
Read events
44 654
Write events
1 855
Delete events
10
Modification events
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
597
Suspicious files
138
Text files
220
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1056 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:034EC3B760B9B922D37EC2D86820EBFA | SHA256:015E7444EB0FDF2CAE85AEF5C1D3D1AEE98ED7E692C848EA45BFEC3A35CCD821 | |||
| 1056 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 1056 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:A3445FA5387FA849079CB867C23AB56E | SHA256:70ECF7685C035B8D73B96AFC6B829B745A19AF657E5FAAFA4158C432D38D6856 | |||
| 1056 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_F2DAF19C1F776537105D08FC8D978464 | binary | |
MD5:8202A1CD02E7D69597995CABBE881A12 | SHA256:58F381C3A0A0ACE6321DA22E40BD44A597BD98B9C9390AB9258426B5CF75A7A5 | |||
| 1056 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_F2DAF19C1F776537105D08FC8D978464 | binary | |
MD5:13A2293E00062C808F4D05C122885F84 | SHA256:2374828A523C92D9657D5B0540360F51611B31EE2F3BB54107663E41065B51EB | |||
| 1056 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\94C18AA77707A64853AFFBE6D6382F75 | binary | |
MD5:217691D7CA900939993694EB50DEABA8 | SHA256:4A08BD739A2DF487922A0A94F478578B53F2424F9E1AE1CE1CA52BE03B245EF5 | |||
| 1056 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\rn-ui-4ddig-1.0.0.min[1].css | text | |
MD5:5653710EE49388300B038B9FA4C7BBE2 | SHA256:E4510CD11721D74688035BC9B98328C8AAE49F9392DAB05EDFB5E441C20C38FC | |||
| 1056 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\94C18AA77707A64853AFFBE6D6382F75 | binary | |
MD5:0F26110B5125A4E2D5C2DAC069A7E42B | SHA256:A1E7E8ED475536C26EF738FA7A4347F882FF05307EC8B496047FEE1295606158 | |||
| 1056 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:72ACAE791C080FE5062A3EDB1297A773 | SHA256:063B407E945168CDCD3C0625681458AEFDAABAE156A5D45977D5305A56DAFF69 | |||
| 1056 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\video-repair[1].htm | html | |
MD5:47200C5830432FB8F79272A6DA638794 | SHA256:01170F1553B88644675EC2C415265DA583DF3718A6D145E7F2A0641EB40FA46C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
65
TCP/UDP connections
308
DNS requests
122
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1056 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?16e53a13f7f2d96f | GB | compressed | 4.66 Kb | unknown |
1056 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | binary | 1.41 Kb | unknown |
1056 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?7a9d8baceff24343 | GB | compressed | 4.66 Kb | unknown |
1056 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFCjJ1PwkYAi7fE%3D | US | binary | 724 b | unknown |
1056 | iexplore.exe | GET | 200 | 192.124.249.41:80 | http://crl.starfieldtech.com/sfroot-g2.crl | US | binary | 584 b | unknown |
1056 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | binary | 724 b | unknown |
1056 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCZXmpIP%2Bo%2BHhJmodADfw%2Fc | US | binary | 472 b | unknown |
1056 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAqvpsXKY8RRQeo74ffHUxc%3D | US | binary | 471 b | unknown |
1056 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | binary | 471 b | unknown |
1056 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEGupzMnM%2BqGaCjIQPyd58u0%3D | US | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1056 | iexplore.exe | 104.18.17.7:443 | www.4ddig.net | CLOUDFLARENET | — | unknown |
1056 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
1056 | iexplore.exe | 142.250.186.131:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
1056 | iexplore.exe | 151.101.193.26:443 | polyfill.io | FASTLY | US | unknown |
1056 | iexplore.exe | 104.18.17.57:443 | assets.afirstsoft.com | CLOUDFLARENET | — | shared |
1056 | iexplore.exe | 104.18.24.249:443 | 4ddig.tenorshare.com | CLOUDFLARENET | — | unknown |
1056 | iexplore.exe | 192.124.249.41:80 | crl.starfieldtech.com | SUCURI-SEC | US | unknown |
1056 | iexplore.exe | 142.250.186.72:443 | www.googletagmanager.com | GOOGLE | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.4ddig.net |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
polyfill.io |
| whitelisted |
assets.afirstsoft.com |
| unknown |
4ddig.tenorshare.com |
| unknown |
images.4ddig.net |
| unknown |
crl.starfieldtech.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
4ddig.net |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2740 | 4ddig-file-repair.exe | Potential Corporate Privacy Violation | ET POLICY Unsupported/Fake Windows NT Version 5.0 |
2740 | 4ddig-file-repair.exe | Potential Corporate Privacy Violation | ET POLICY Unsupported/Fake Windows NT Version 5.0 |
2740 | 4ddig-file-repair.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
2740 | 4ddig-file-repair.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
2740 | 4ddig-file-repair.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP Tensorshare Google Analytics Checkin |
3164 | 4DDiG File Repair.exe | Potential Corporate Privacy Violation | ET POLICY Unsupported/Fake Windows NT Version 5.0 |
3 ETPRO signatures available at the full report