| File name: | MailAttachment.eml |
| Full analysis: | https://app.any.run/tasks/80f2ae74-fe12-4b6f-befb-51ecf4c0eeb6 |
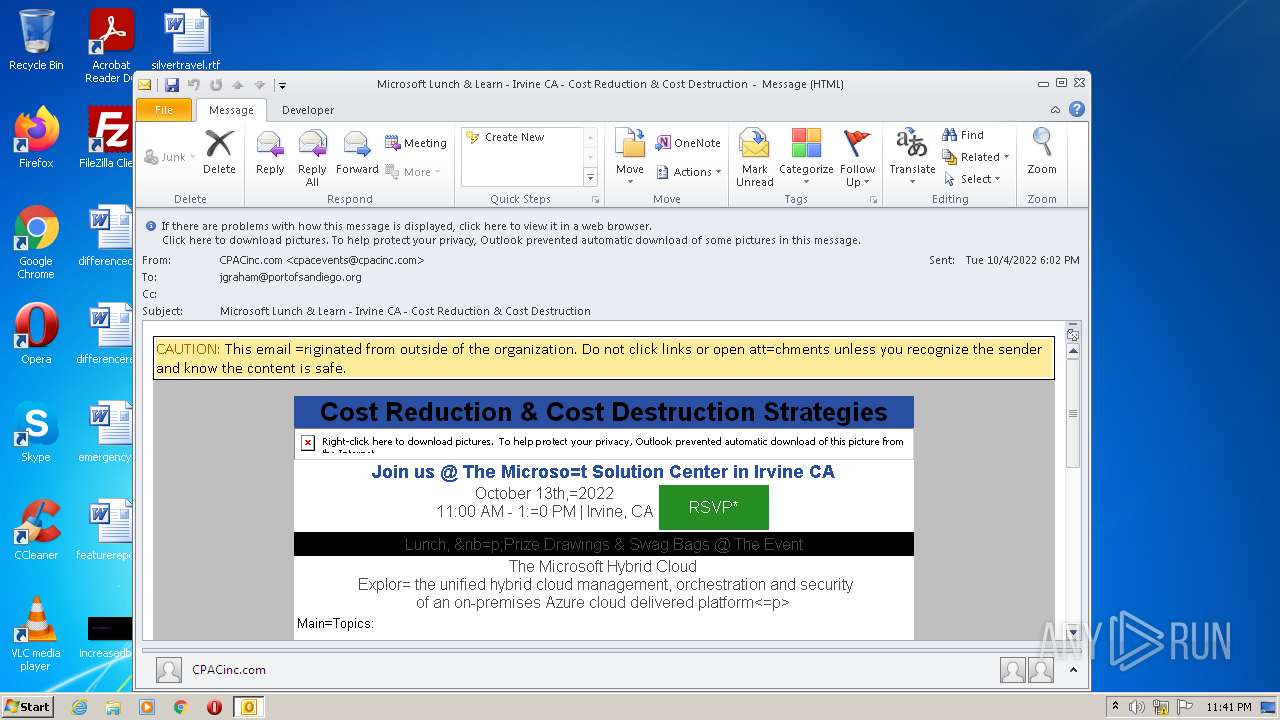
| Verdict: | Malicious activity |
| Analysis date: | October 04, 2022, 22:41:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text, with very long lines |
| MD5: | 908132F1087C44A6DC522AB04929F8BD |
| SHA1: | 37F4B700448FA90753174E3AC938CD9E30D610DC |
| SHA256: | 1D644C1D0896C22EC4F5568E4B04685F5A2EF639BD92B3B688DAF9B1D136E95A |
| SSDEEP: | 768:EKQ77wWSvfFQdahjydlTIe8V0oPBU7ecxzTggDDdX8lGkShH2SXCaVnhKgj5xvxP:EK4S2ifPBCjhNDRXRkSWwp5Fwq |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks supported languages
- OUTLOOK.EXE (PID: 3564)
Reads the computer name
- OUTLOOK.EXE (PID: 3564)
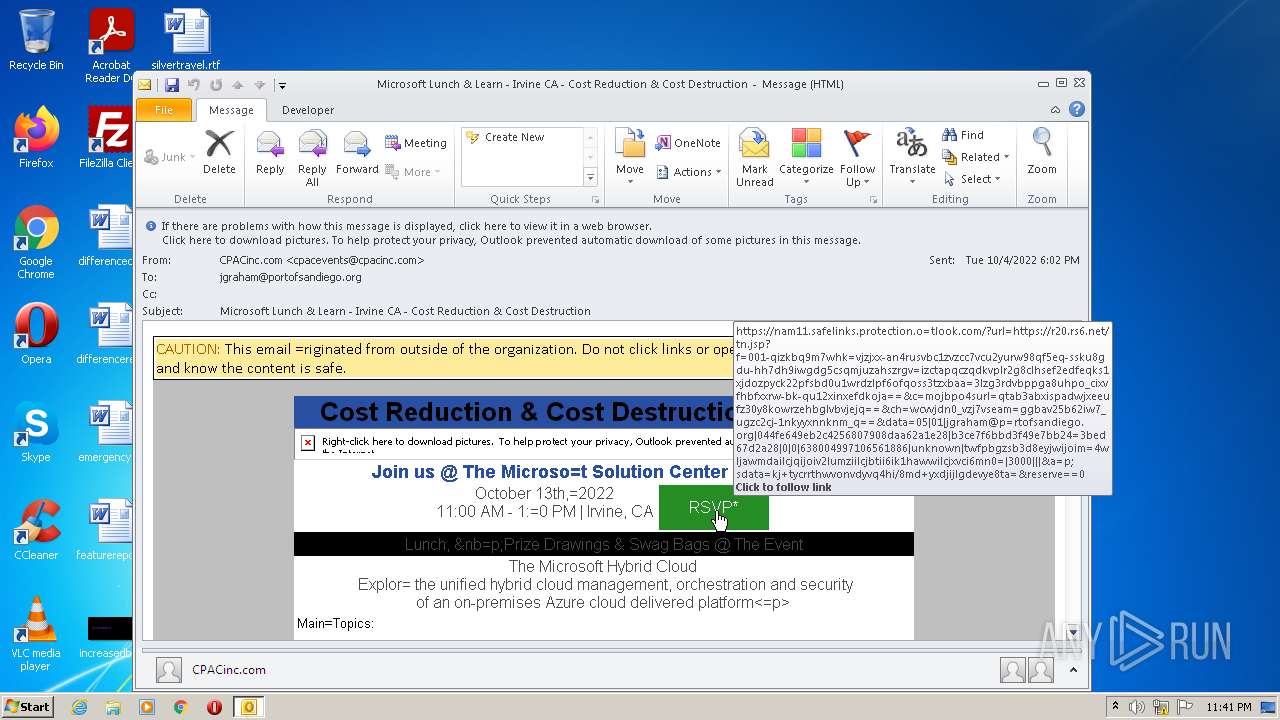
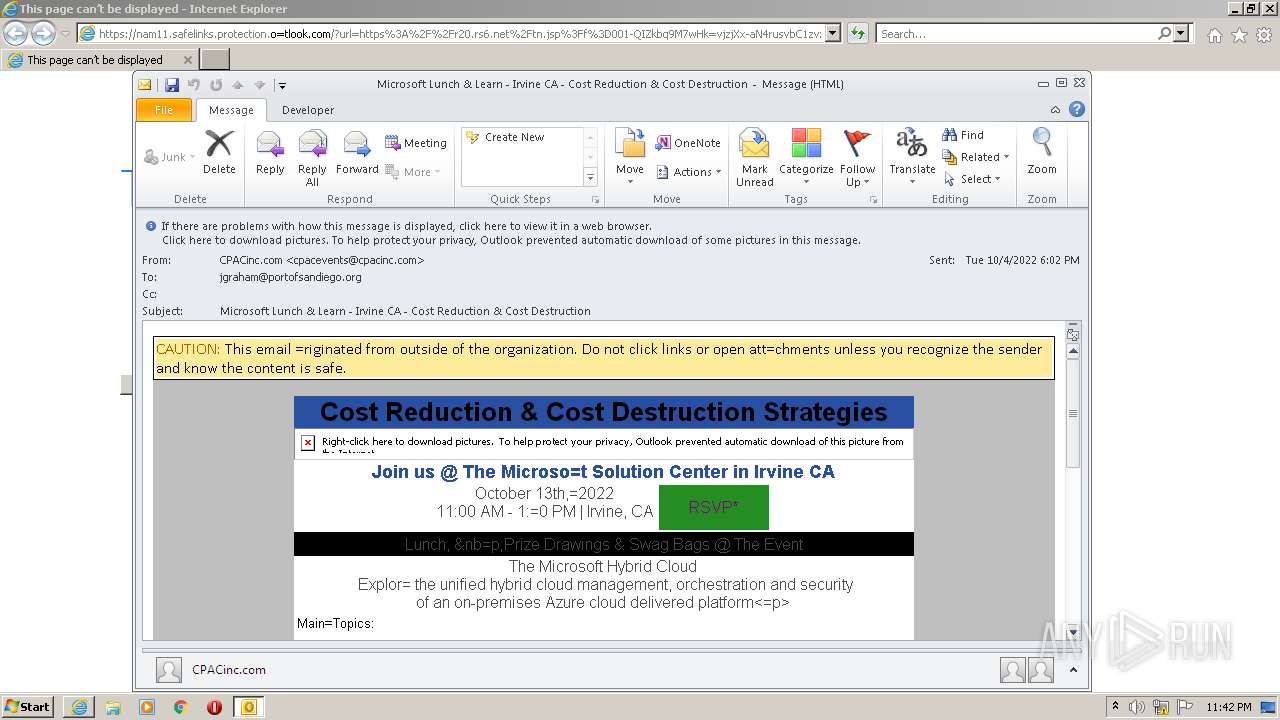
Starts Internet Explorer
- OUTLOOK.EXE (PID: 3564)
Creates files in the user directory
- OUTLOOK.EXE (PID: 3564)
Searches for installed software
- OUTLOOK.EXE (PID: 3564)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 436)
- iexplore.exe (PID: 2760)
- iexplore.exe (PID: 1232)
- iexplore.exe (PID: 1828)
INFO
Checks supported languages
- iexplore.exe (PID: 436)
- iexplore.exe (PID: 3788)
- iexplore.exe (PID: 2760)
- iexplore.exe (PID: 1232)
- iexplore.exe (PID: 1828)
Reads the computer name
- iexplore.exe (PID: 3788)
- iexplore.exe (PID: 436)
- iexplore.exe (PID: 2760)
- iexplore.exe (PID: 1232)
- iexplore.exe (PID: 1828)
Changes internet zones settings
- iexplore.exe (PID: 3788)
Reads internet explorer settings
- iexplore.exe (PID: 1828)
- iexplore.exe (PID: 436)
- iexplore.exe (PID: 2760)
- iexplore.exe (PID: 1232)
Reads settings of System Certificates
- iexplore.exe (PID: 3788)
- iexplore.exe (PID: 1232)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3564)
Checks Windows Trust Settings
- iexplore.exe (PID: 1232)
- iexplore.exe (PID: 3788)
Application launched itself
- iexplore.exe (PID: 3788)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
42
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 436 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3788 CREDAT:78849 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1232 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3788 CREDAT:3937541 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1828 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3788 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2760 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3788 CREDAT:3748878 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
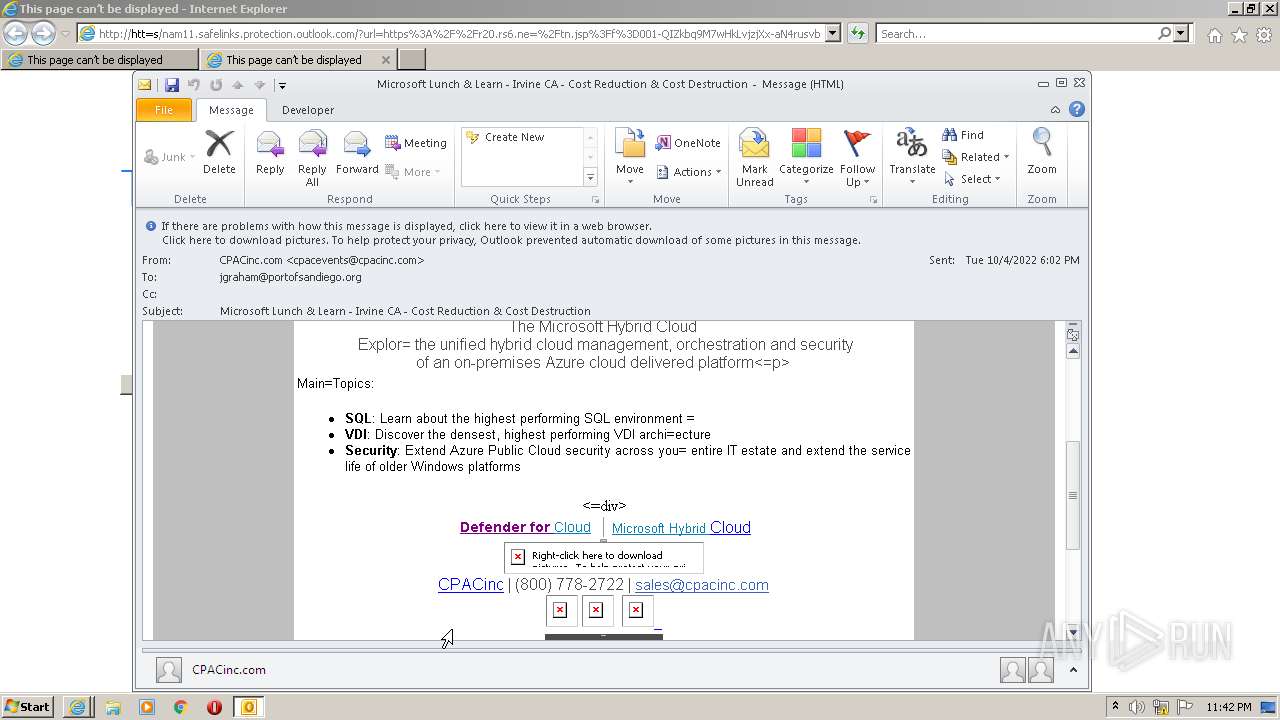
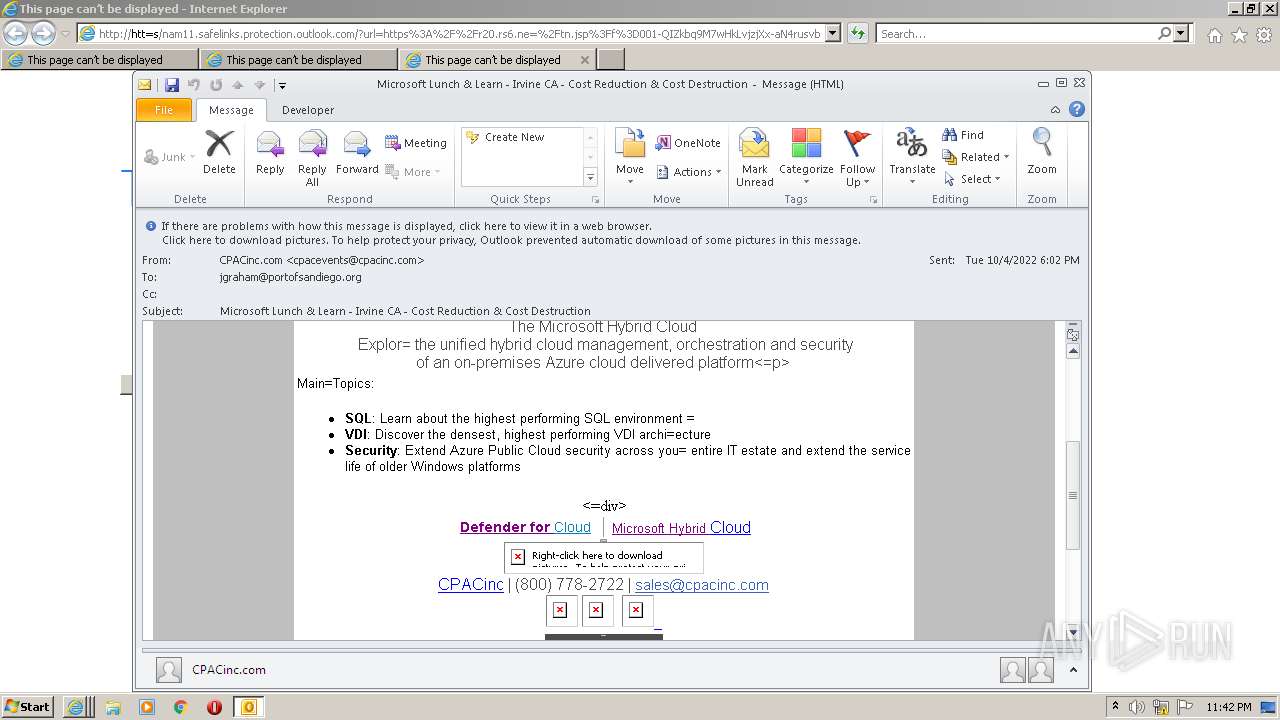
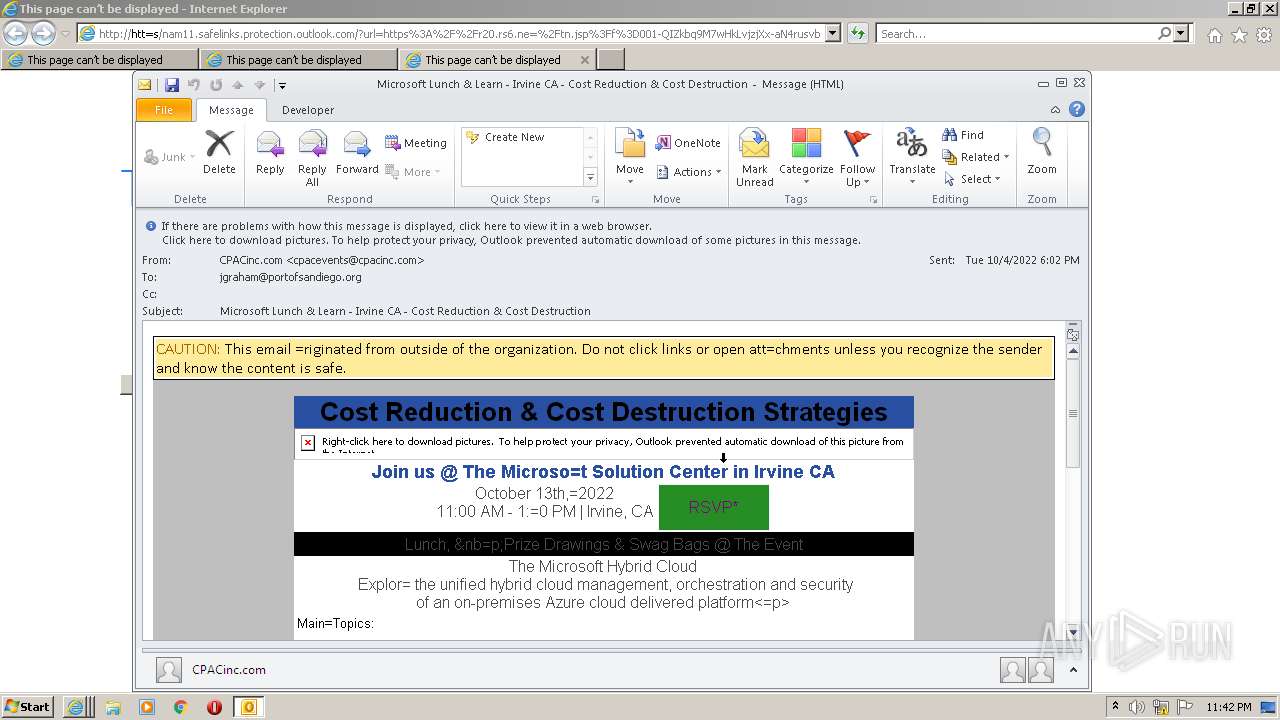
| 3564 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\MailAttachment.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
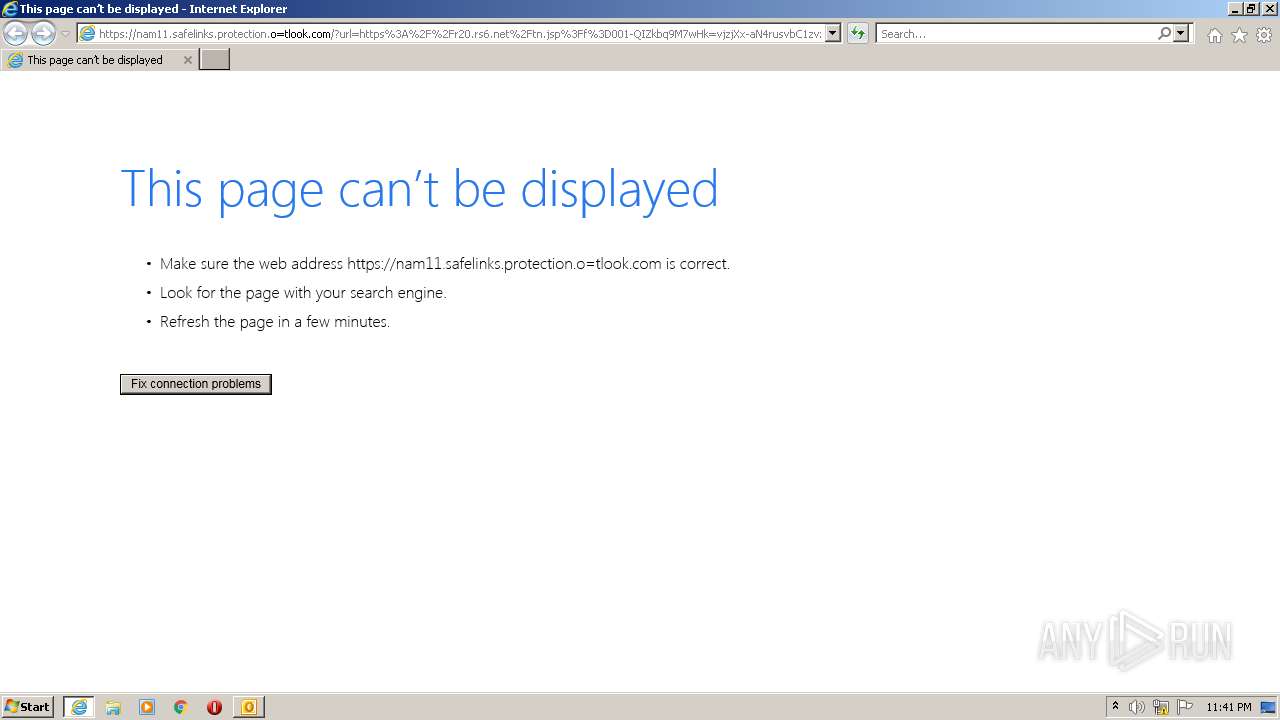
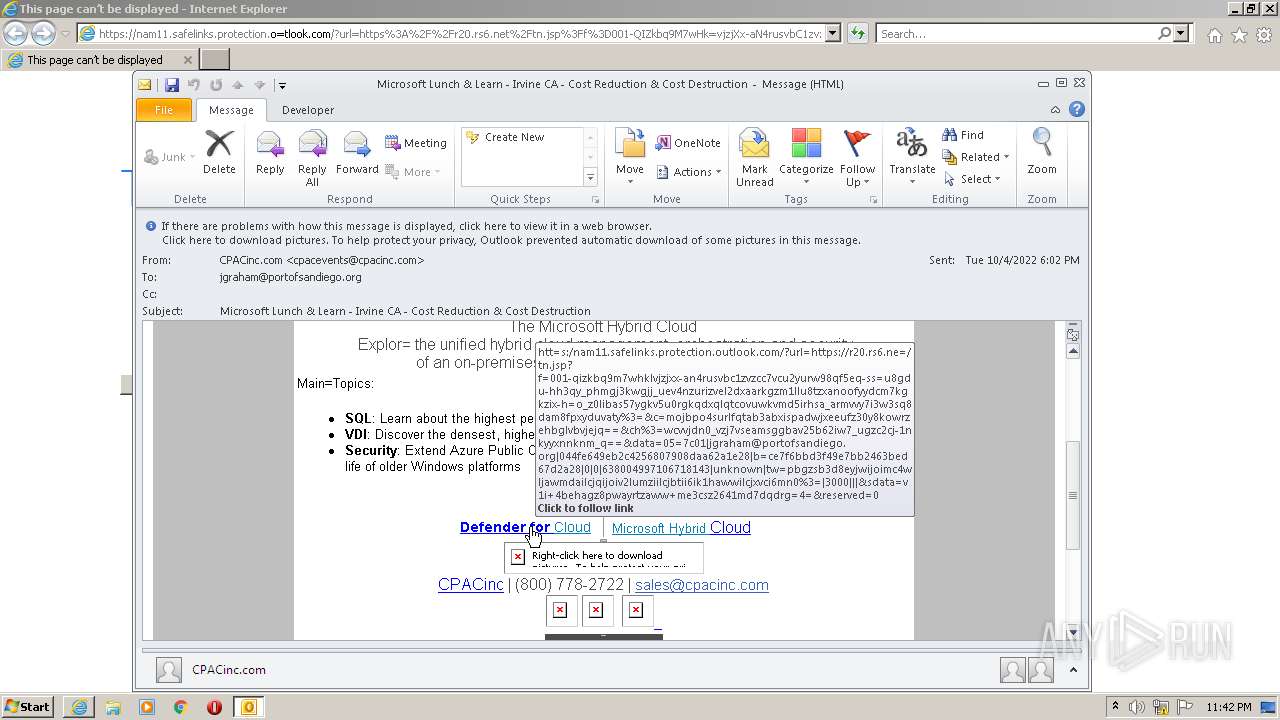
| 3788 | "C:\Program Files\Internet Explorer\iexplore.exe" https://nam11.safelinks.protection.o=tlook.com/?url=https%3A%2F%2Fr20.rs6.net%2Ftn.jsp%3Ff%3D001-QIZkbq9M7wHk=vjzjXx-aN4rusvbC1zvzcc7VcU2Yurw98qf5eQ-ssku8GDU-hh7Dh9IWGdg5cSQMjUzAHSzRGV=IzCTaPqcZqDkVPLR2g8CLHsEF2eDFeQkS1xjdoZpyCK22PfSBd0U1wRDZLpF6OfQoss3TZxBAa=3lZg3rdvBpPGA8UhpO_CixVFHbfXXRw-bK-qU12XinxefDKOjA%3D%3D%26c%3DmOJbpo4suRL=QtAB3abXIspADWjxeeuFZ30Y8KOWRZeHbGLvBvjEjQ%3D%3D%26ch%3DWcvVJDN0_VZJ7Vseam=GgBaV25b62iW7_ugZc2cj-1NkyYxnNKnM_Q%3D%3D&data=05%7C01%7Cjgraham%40p=rtofsandiego.org%7C044fe649eb2c4256807908daa62a1e28%7Cb3ce7f6bbd3f49e7bb24=3bed67d2a28%7C0%7C0%7C638004997106561886%7CUnknown%7CTWFpbGZsb3d8eyJWIjoiM=4wLjAwMDAiLCJQIjoiV2luMzIiLCJBTiI6Ik1haWwiLCJXVCI6Mn0%3D%7C3000%7C%7C%7C&a=p;sdata=KJ%2BTYCRRThwvOnvdyVQ4HI%2F8Md%2ByXdJIJLGdEVYE8tA%3D&reserve==0 | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
21 230
Read events
20 375
Write events
835
Delete events
20
Modification events
| (PID) Process: | (3564) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3564) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3564) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3564) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3564) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3564) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3564) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3564) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3564) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (3564) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
6
Text files
18
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3564 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRB8B3.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3564 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 3564 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 3788 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3788 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | binary | |
MD5:— | SHA256:— | |||
| 3788 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | der | |
MD5:— | SHA256:— | |||
| 3564 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3564 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_WorkHours_1_11596E423825864194FAFBF9762017EE.dat | xml | |
MD5:807EF0FC900FEB3DA82927990083D6E7 | SHA256:4411E7DC978011222764943081500FFF0E43CBF7CCD44264BD1AB6306CA68913 | |||
| 3788 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 3564 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\{94BF3985-1EAF-4112-86CE-7077C36B232D}\{1C306CB1-771E-4B4B-A902-86E897877F5B}.png | image | |
MD5:4C61C12EDBC453D7AE184976E95258E1 | SHA256:296526F9A716C1AA91BA5D6F69F0EB92FDF79C2CB2CFCF0CEB22B7CCBC27035F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
16
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3564 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
1232 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAGewca9P1l7sgwzOOVR2Hc%3D | US | der | 471 b | whitelisted |
3788 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3788 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
3788 | iexplore.exe | GET | 200 | 8.238.189.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?4e6177a654e2d7cf | US | compressed | 4.70 Kb | whitelisted |
3788 | iexplore.exe | GET | 200 | 8.238.189.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?81e8d277b8a05f66 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3564 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3788 | iexplore.exe | 204.79.197.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3788 | iexplore.exe | 8.238.189.126:80 | ctldl.windowsupdate.com | LEVEL3 | US | suspicious |
3788 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | EDGECAST | GB | whitelisted |
3788 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | EDGECAST | US | whitelisted |
1232 | iexplore.exe | 104.47.56.156:443 | nam11.safelinks.protection.outlook.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | suspicious |
— | — | 93.184.220.29:80 | ocsp.digicert.com | EDGECAST | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
nam11.safelinks.protection.outlook.com |
| whitelisted |