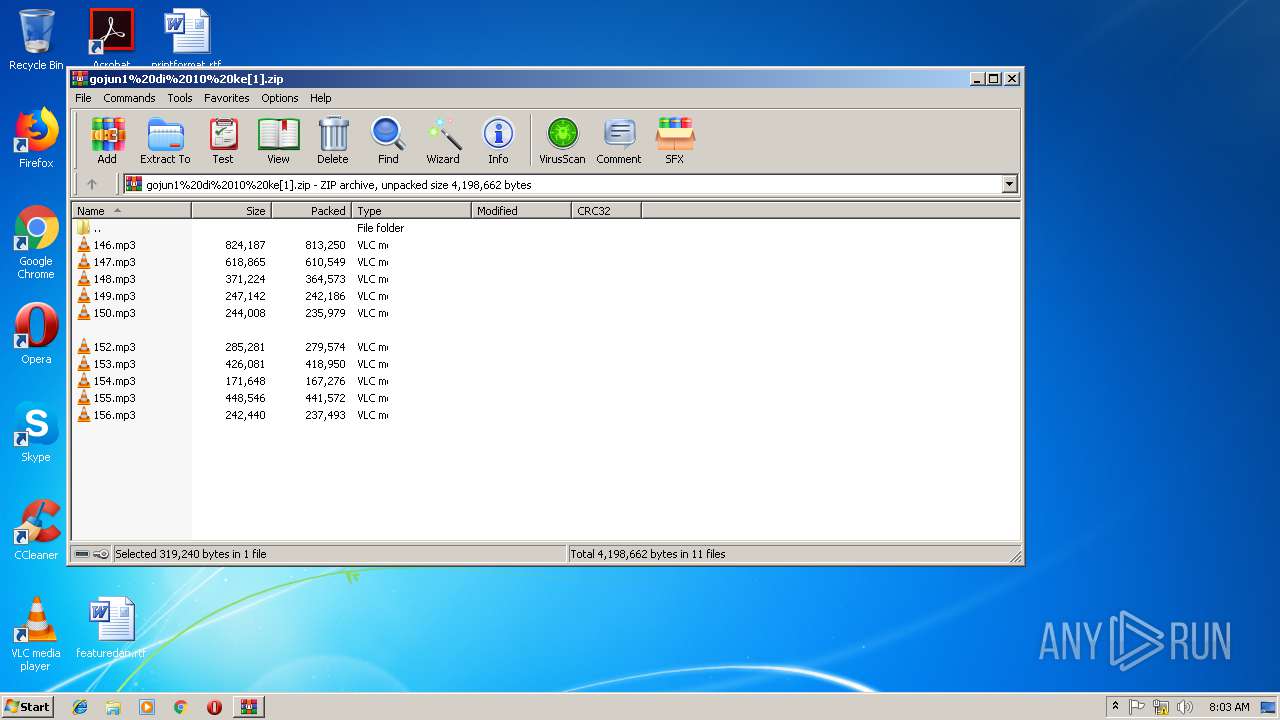
| URL: | http://103.241.128.224/plesk-site-preview/hakuteisha.co.jp/103.241.128.224/audio/gojun/gojun1%20di%2010%20ke.zip |
| Full analysis: | https://app.any.run/tasks/fb9555cb-e533-4ad3-8e5e-b266afac9363 |
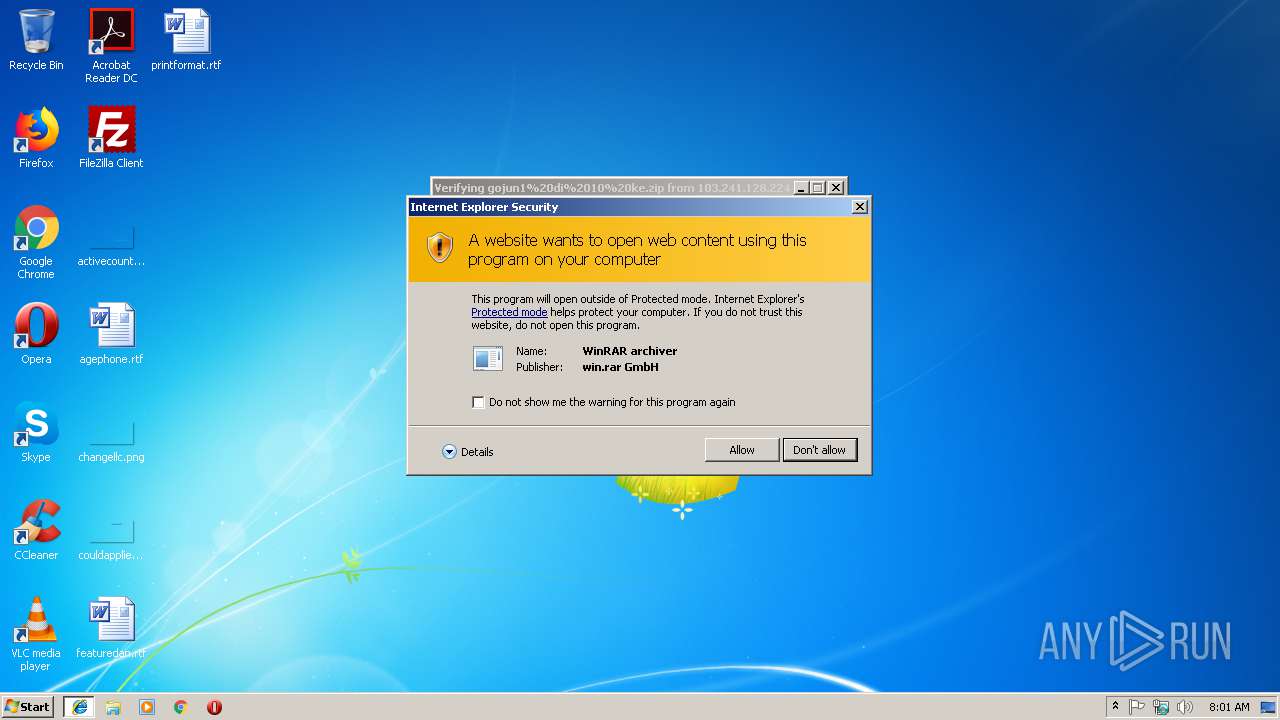
| Verdict: | Malicious activity |
| Analysis date: | January 18, 2019, 08:00:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | B88E96B5838E6059216E22AF6E69F59B |
| SHA1: | 239800413E029210739EE04CA55BAA54F93E446D |
| SHA256: | 1D5D3C003C12A891487D464A6EAC92133B3A50CDC8A0FF9AF8F0926C1FE27488 |
| SSDEEP: | 3:N1KtMiuLRhQRAGZ7RVWmuWhZUXW7BIVGTUn:CCi6RyRpVTmGF7U |
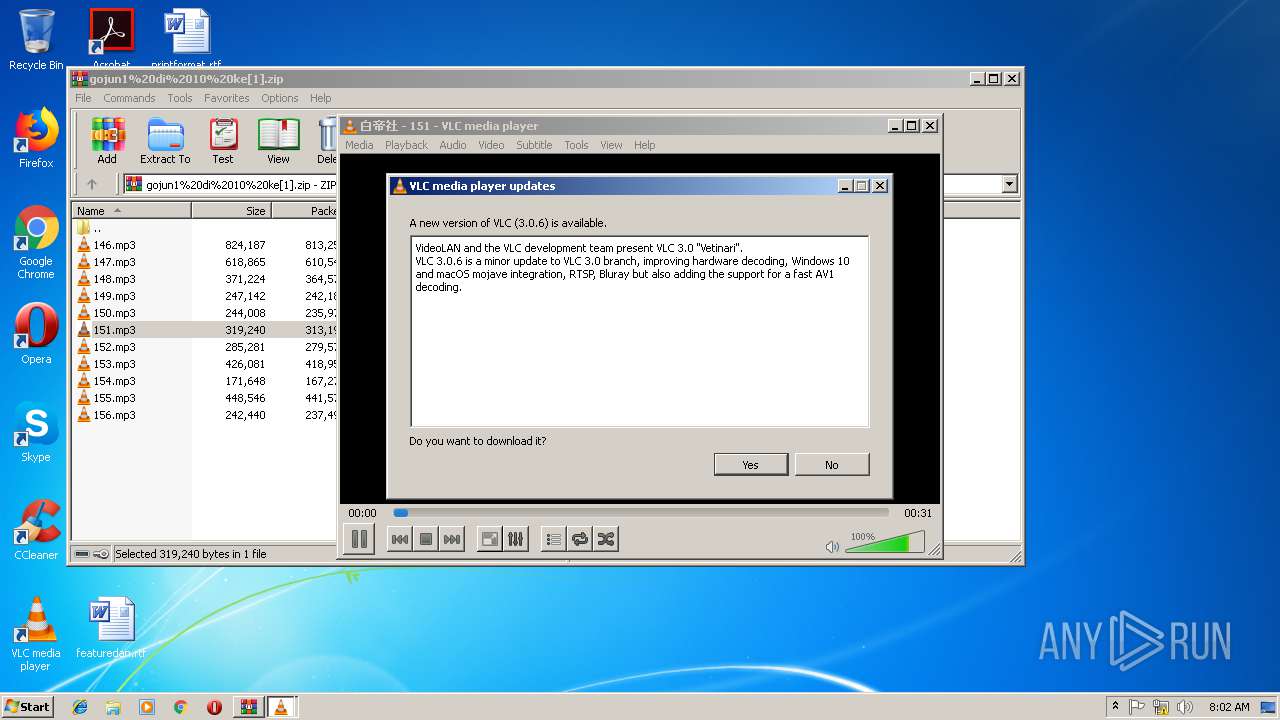
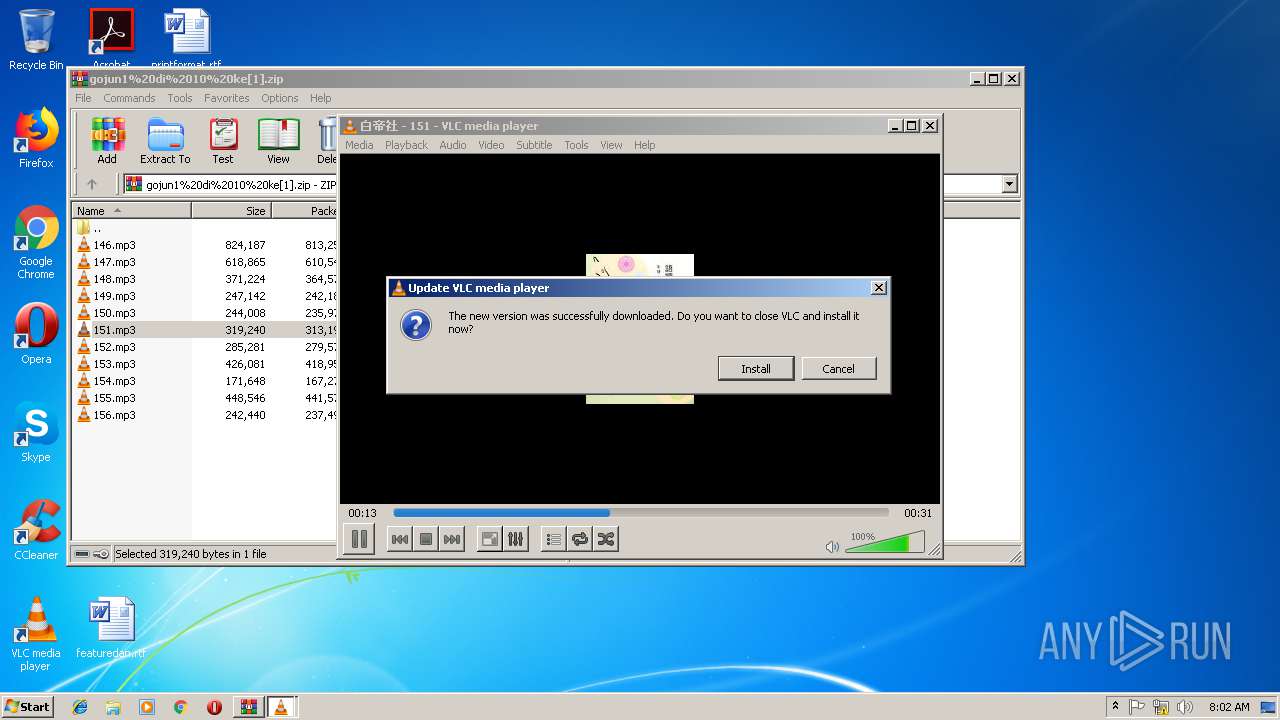
MALICIOUS
BANLOAD was detected
- iexplore.exe (PID: 3236)
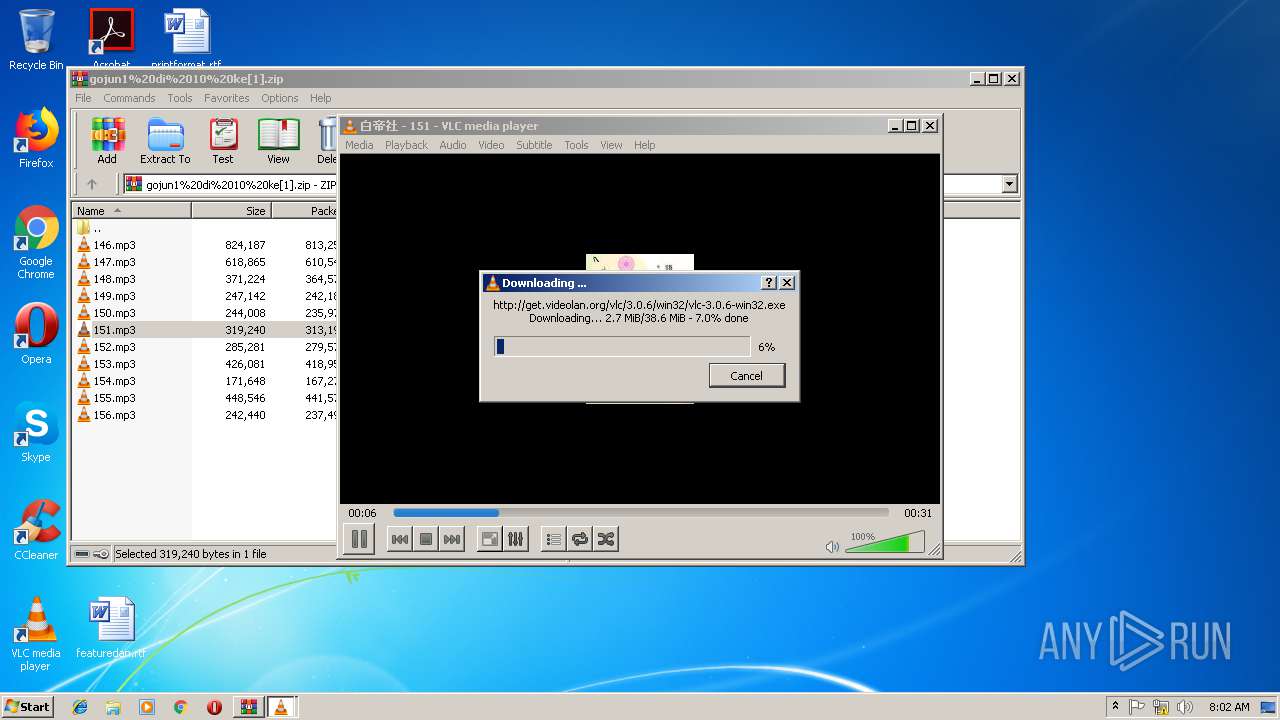
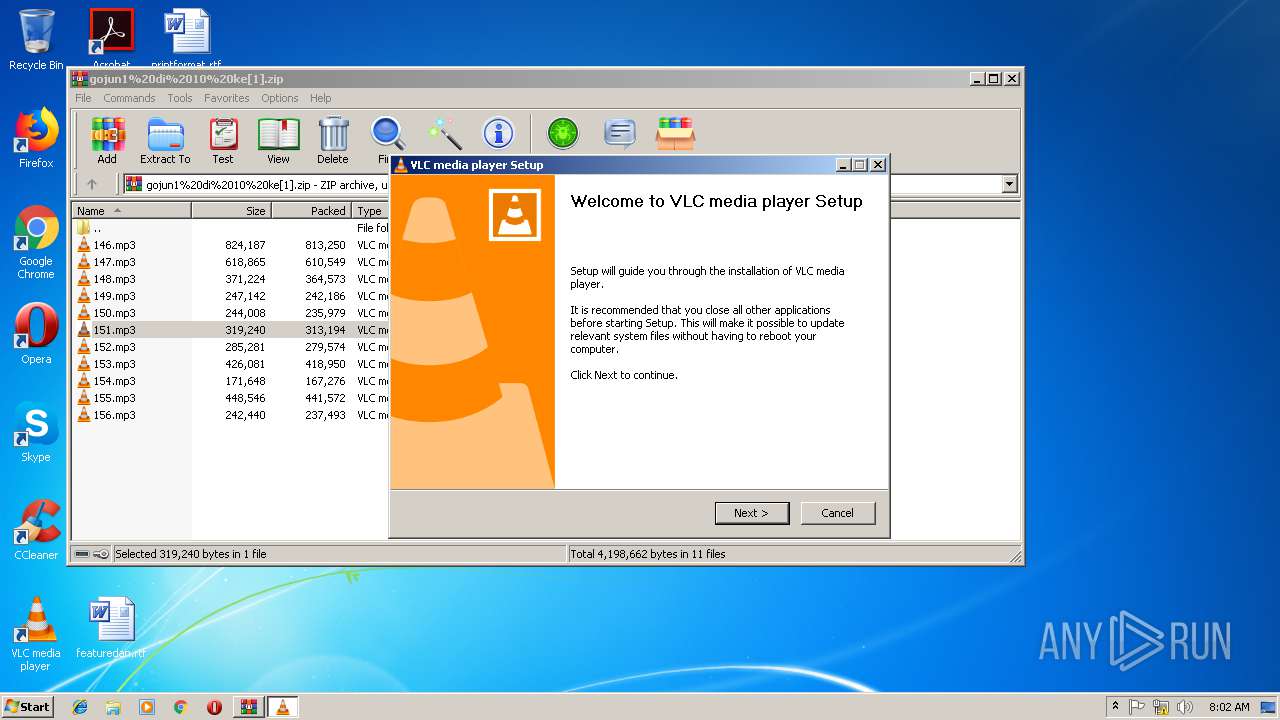
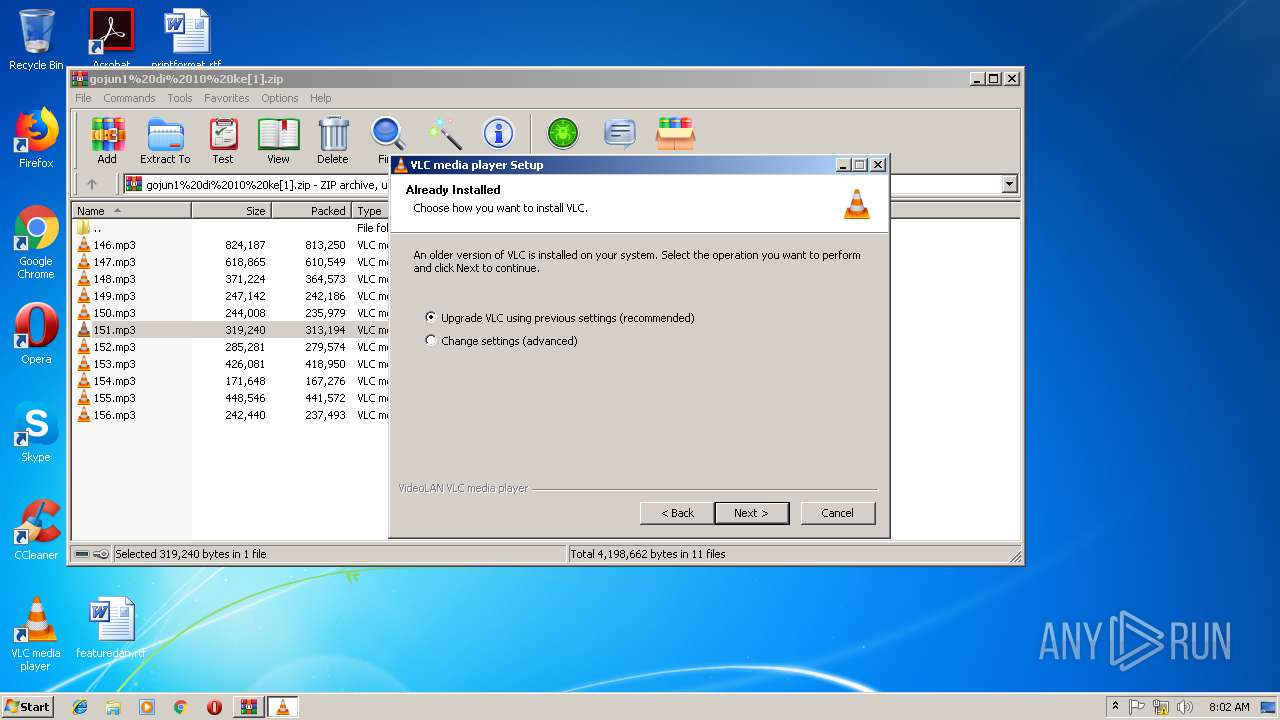
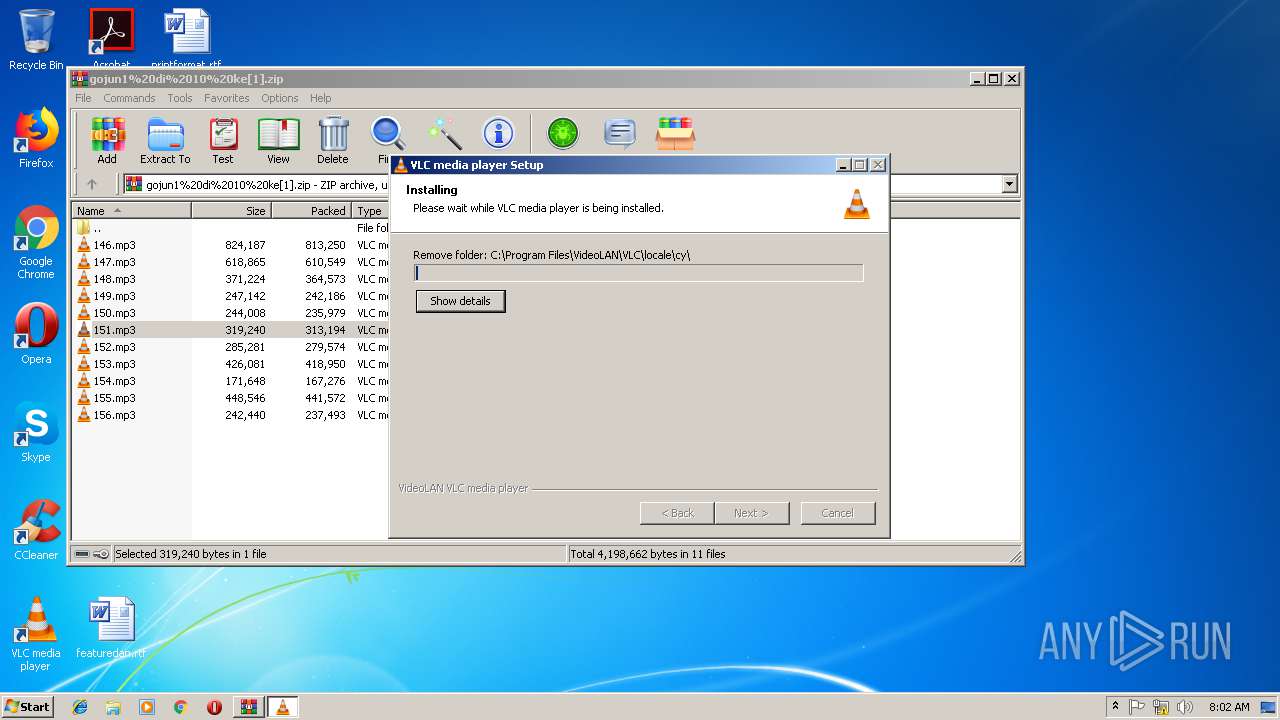
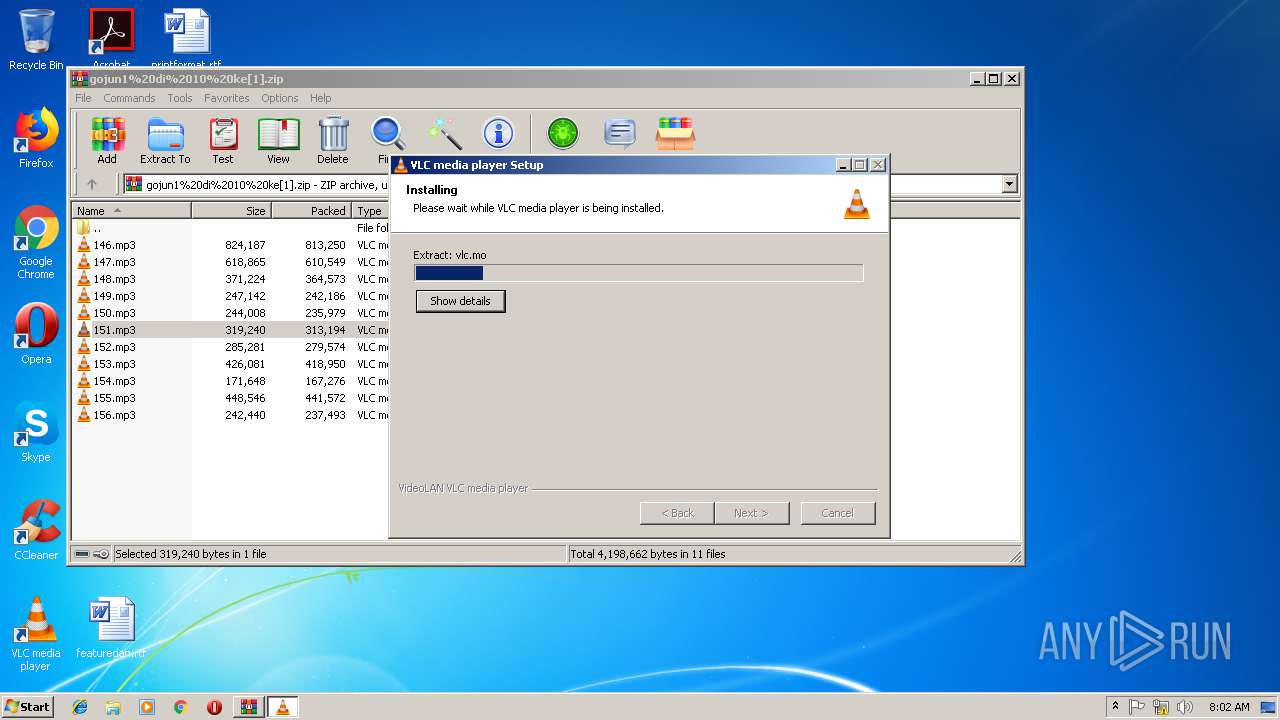
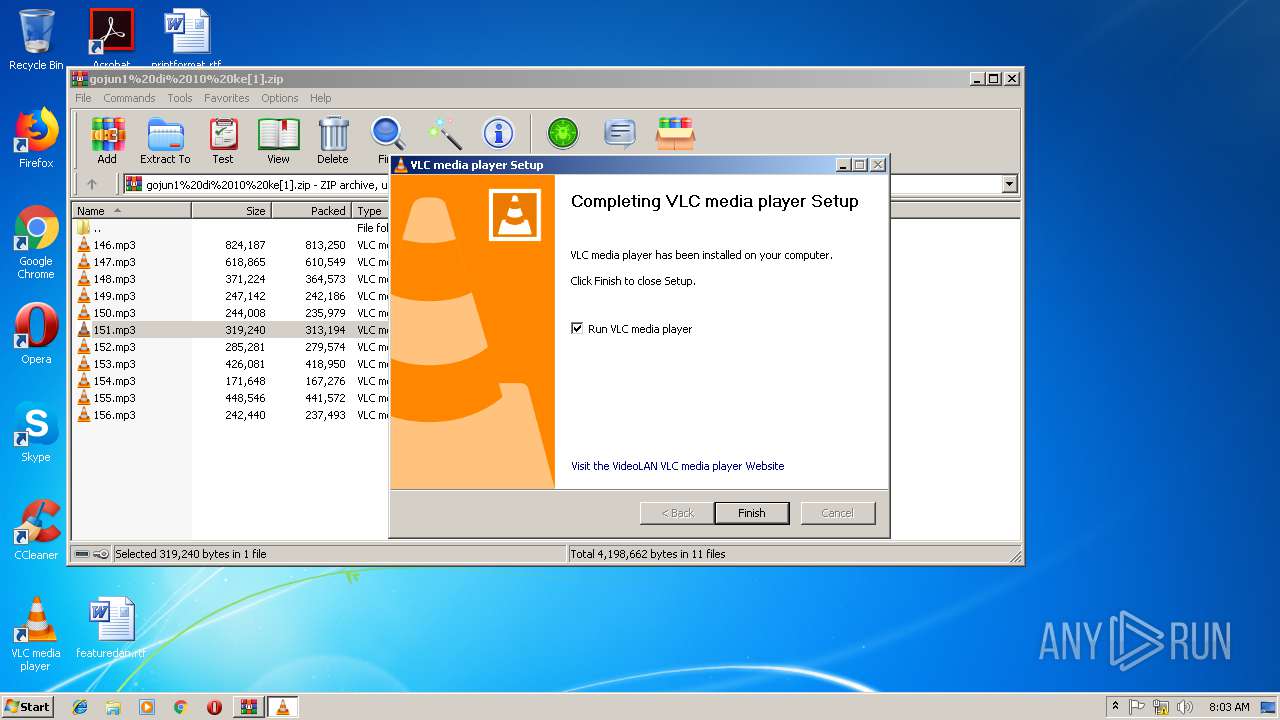
Loads dropped or rewritten executable
- vlc-3.0.6-win32.exe (PID: 3072)
- vlc-cache-gen.exe (PID: 3252)
- vlc.exe (PID: 2768)
- vlc.exe (PID: 3628)
- vlc.exe (PID: 3484)
- vlc.exe (PID: 3640)
Application was dropped or rewritten from another process
- vlc-3.0.6-win32.exe (PID: 3072)
- vlc-cache-gen.exe (PID: 3252)
- vlc-3.0.6-win32.exe (PID: 3912)
- vlc.exe (PID: 3640)
- nsDB3A.tmp (PID: 2736)
- vlc.exe (PID: 2768)
- vlc.exe (PID: 3628)
- vlc.exe (PID: 3484)
SUSPICIOUS
Creates files in the user directory
- vlc.exe (PID: 3076)
- vlc.exe (PID: 2512)
- vlc.exe (PID: 3628)
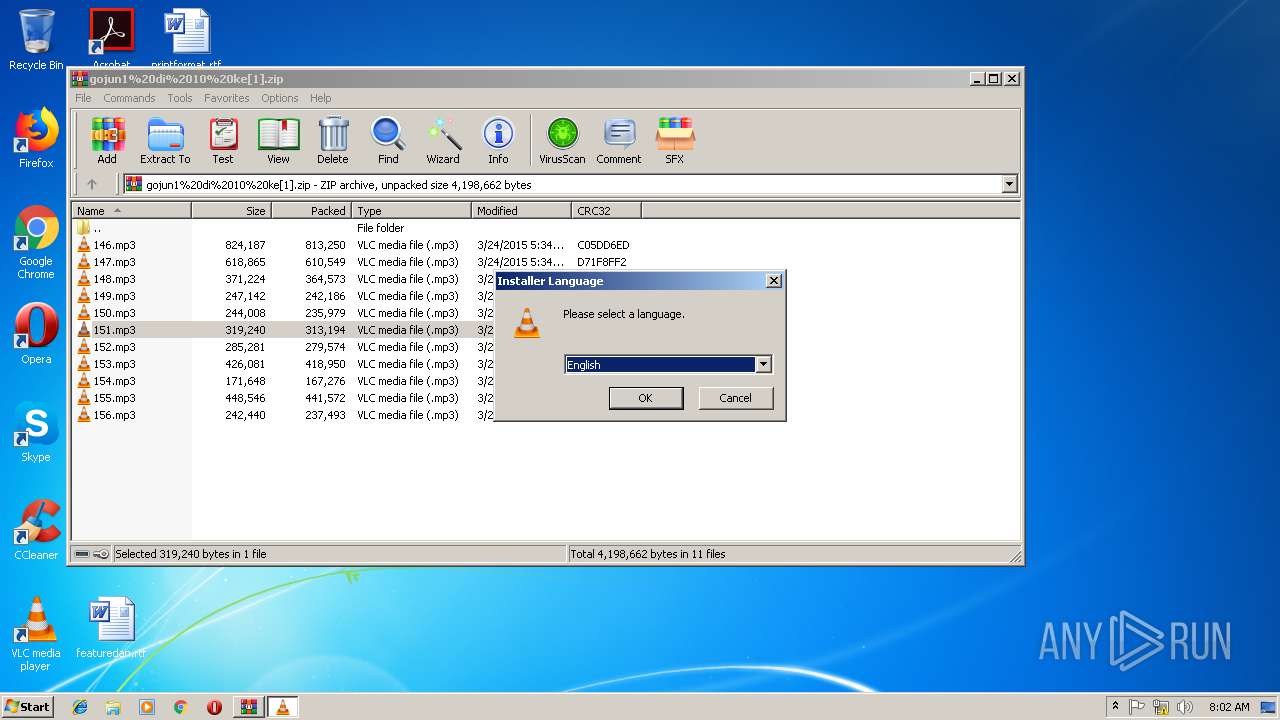
Starts application with an unusual extension
- vlc-3.0.6-win32.exe (PID: 3072)
Creates files in the program directory
- vlc-cache-gen.exe (PID: 3252)
- vlc-3.0.6-win32.exe (PID: 3072)
Creates COM task schedule object
- vlc-3.0.6-win32.exe (PID: 3072)
Executable content was dropped or overwritten
- vlc-3.0.6-win32.exe (PID: 3072)
Creates a software uninstall entry
- vlc-3.0.6-win32.exe (PID: 3072)
Modifies the open verb of a shell class
- vlc-3.0.6-win32.exe (PID: 3072)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2900)
Application launched itself
- iexplore.exe (PID: 2900)
Reads settings of System Certificates
- iexplore.exe (PID: 2900)
Reads Internet Cache Settings
- iexplore.exe (PID: 3236)
- iexplore.exe (PID: 2900)
Dropped object may contain Bitcoin addresses
- vlc-3.0.6-win32.exe (PID: 3072)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
51
Monitored processes
15
Malicious processes
10
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
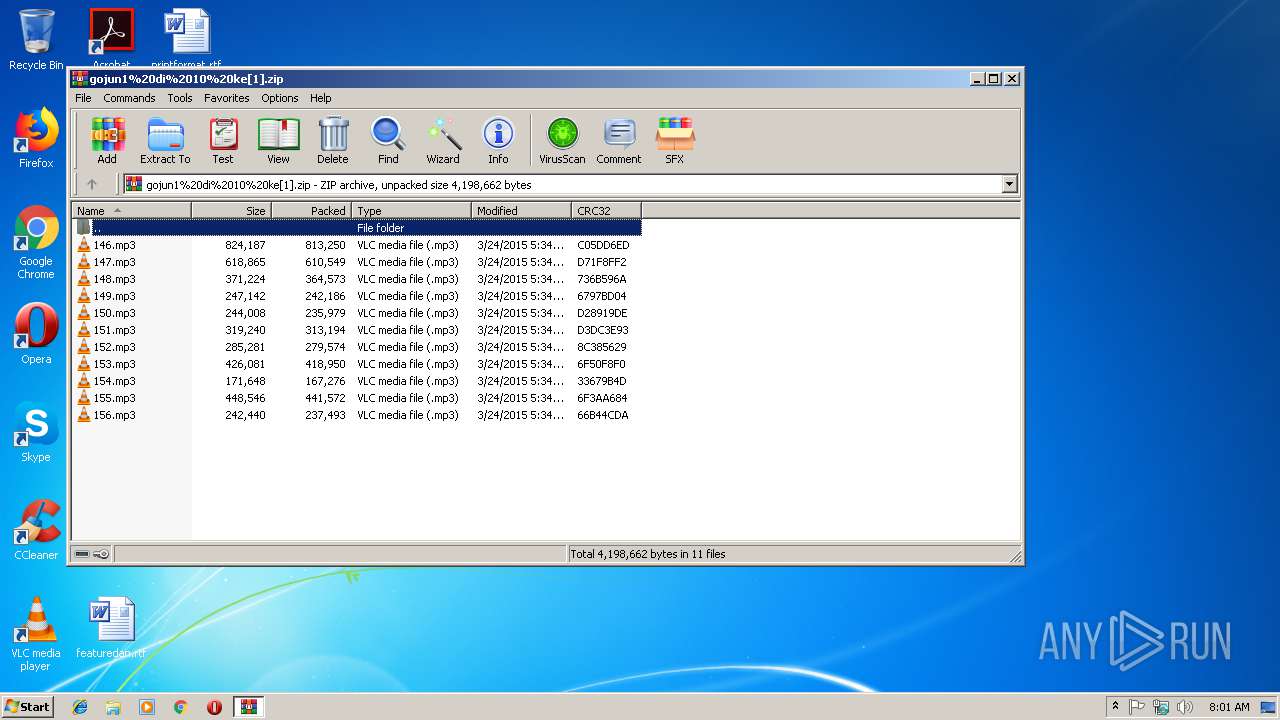
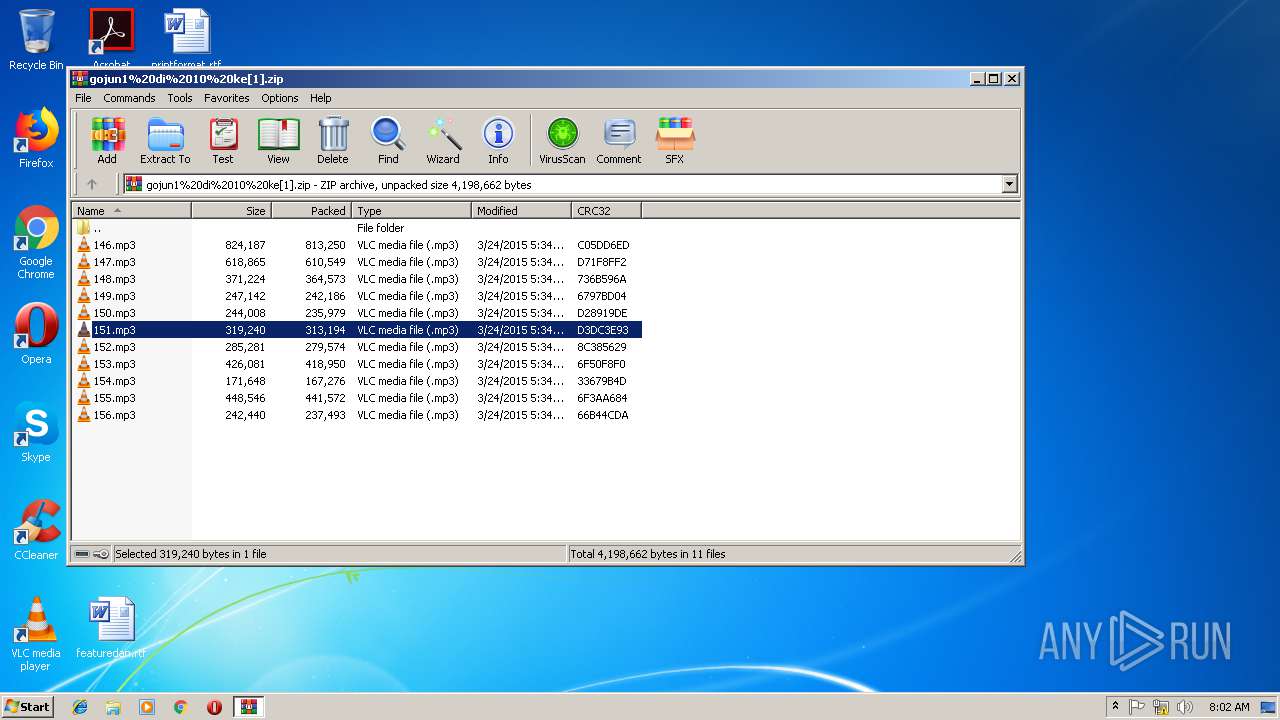
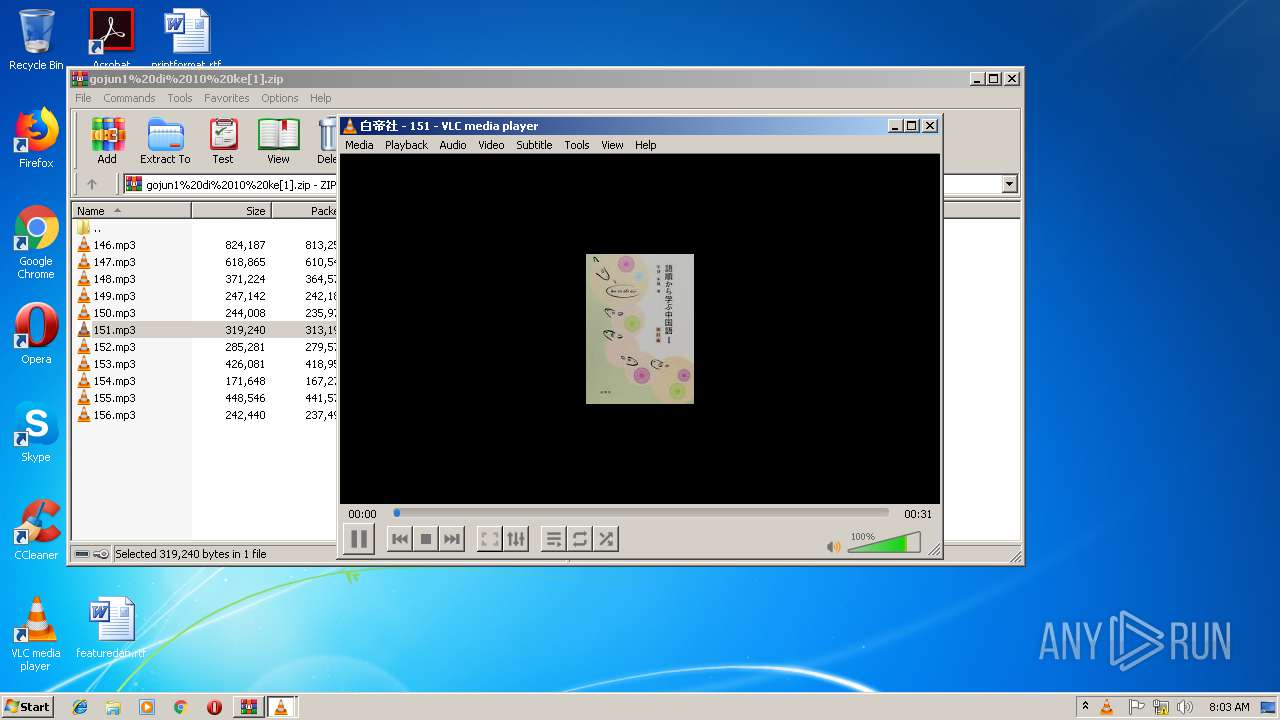
| 2512 | "C:\Program Files\VideoLAN\VLC\vlc.exe" --started-from-file "C:\Users\admin\AppData\Local\Temp\Rar$DIa2976.4566\151.mp3" | C:\Program Files\VideoLAN\VLC\vlc.exe | WinRAR.exe | ||||||||||||
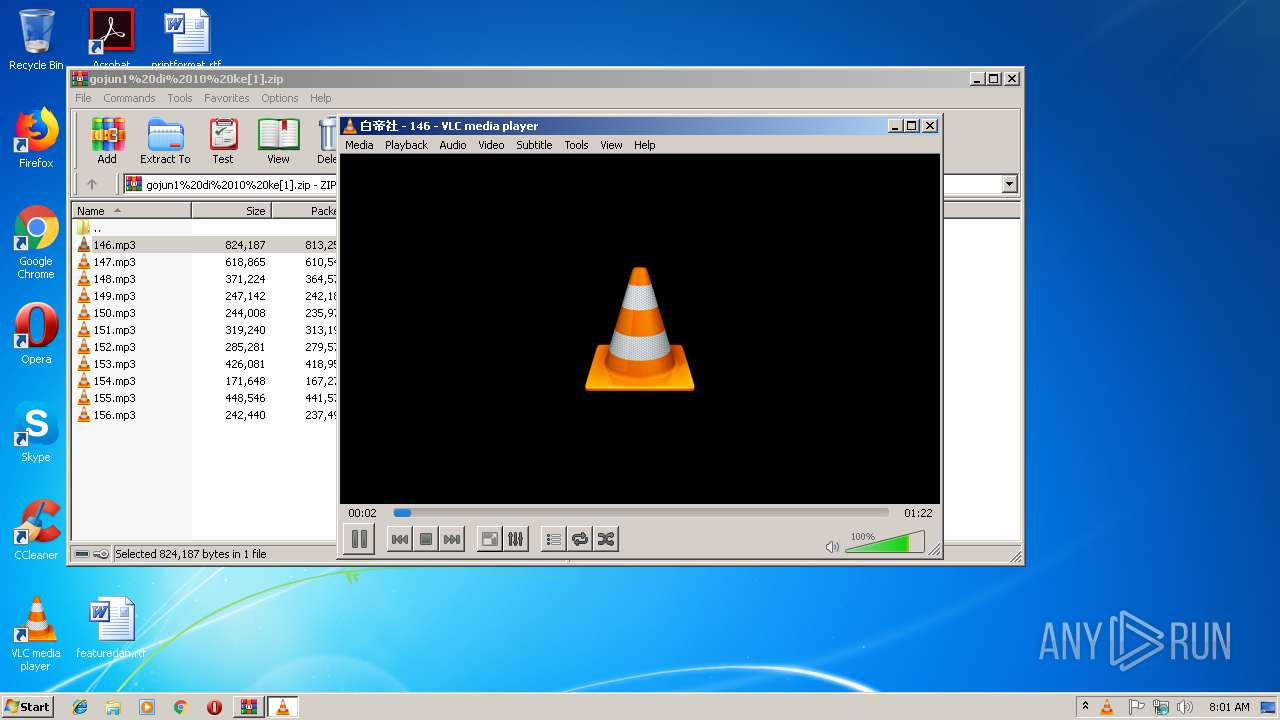
User: admin Company: VideoLAN Integrity Level: MEDIUM Description: VLC media player Exit code: 0 Version: 2.2.6 Modules
| |||||||||||||||
| 2736 | "C:\Users\admin\AppData\Local\Temp\nsn98D1.tmp\nsDB3A.tmp" "C:\Program Files\VideoLAN\VLC\vlc-cache-gen.exe" C:\Program Files\VideoLAN\VLC\plugins | C:\Users\admin\AppData\Local\Temp\nsn98D1.tmp\nsDB3A.tmp | — | vlc-3.0.6-win32.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2768 | "C:\Program Files\VideoLAN\VLC\vlc.exe" | C:\Program Files\VideoLAN\VLC\vlc.exe | explorer.exe | ||||||||||||
User: admin Company: VideoLAN Integrity Level: MEDIUM Description: VLC media player Exit code: 0 Version: 3.0.6 Modules
| |||||||||||||||
| 2900 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2948 | "C:\Windows\explorer.exe" "C:\Program Files\VideoLAN\VLC\vlc.exe" | C:\Windows\explorer.exe | — | vlc-3.0.6-win32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
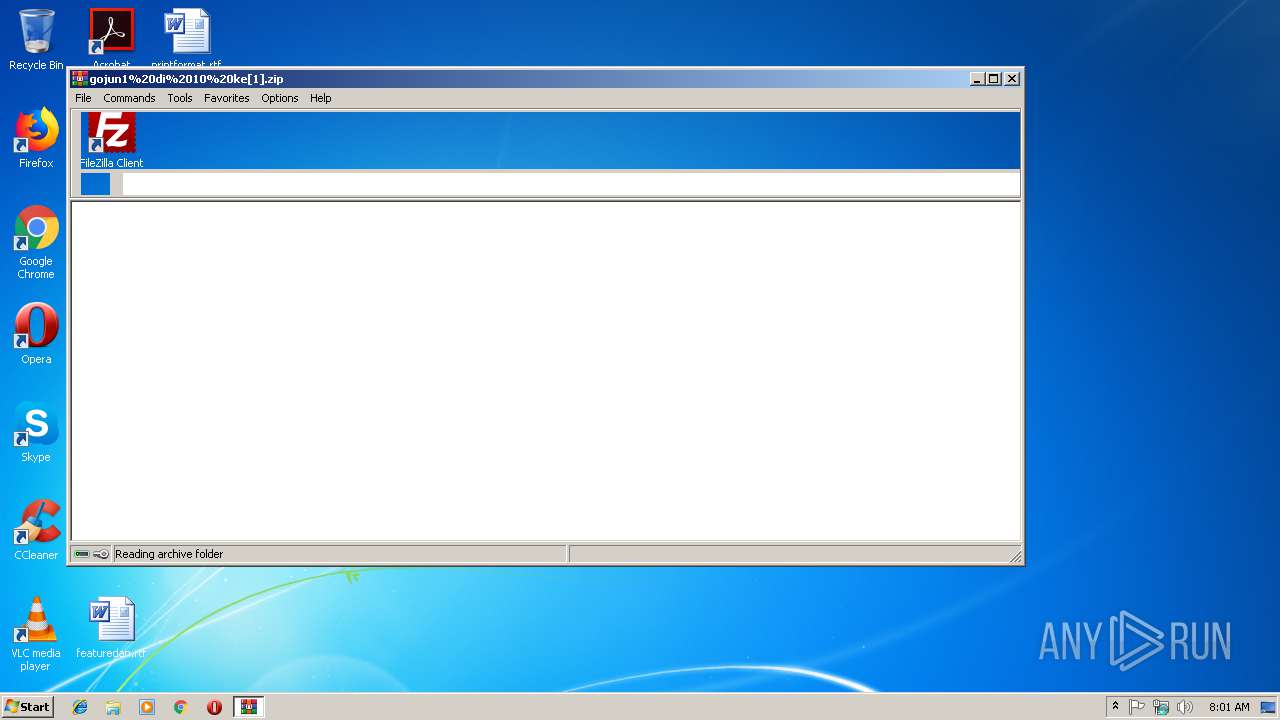
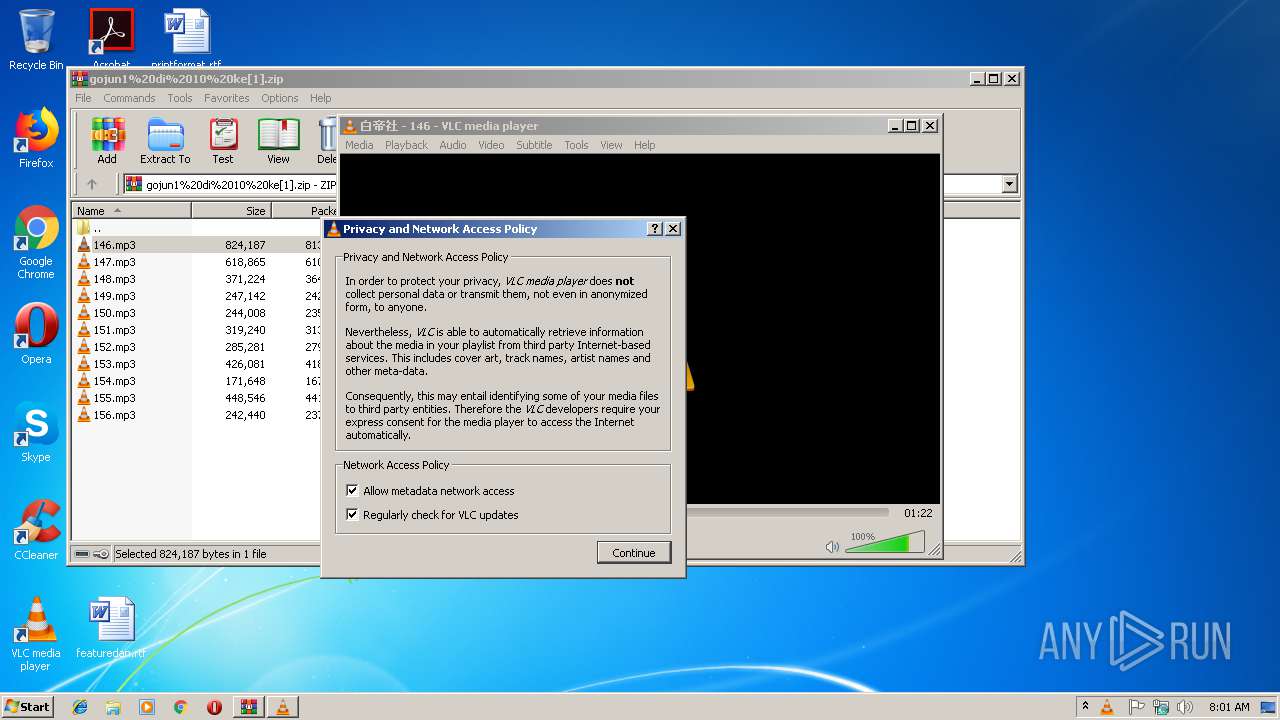
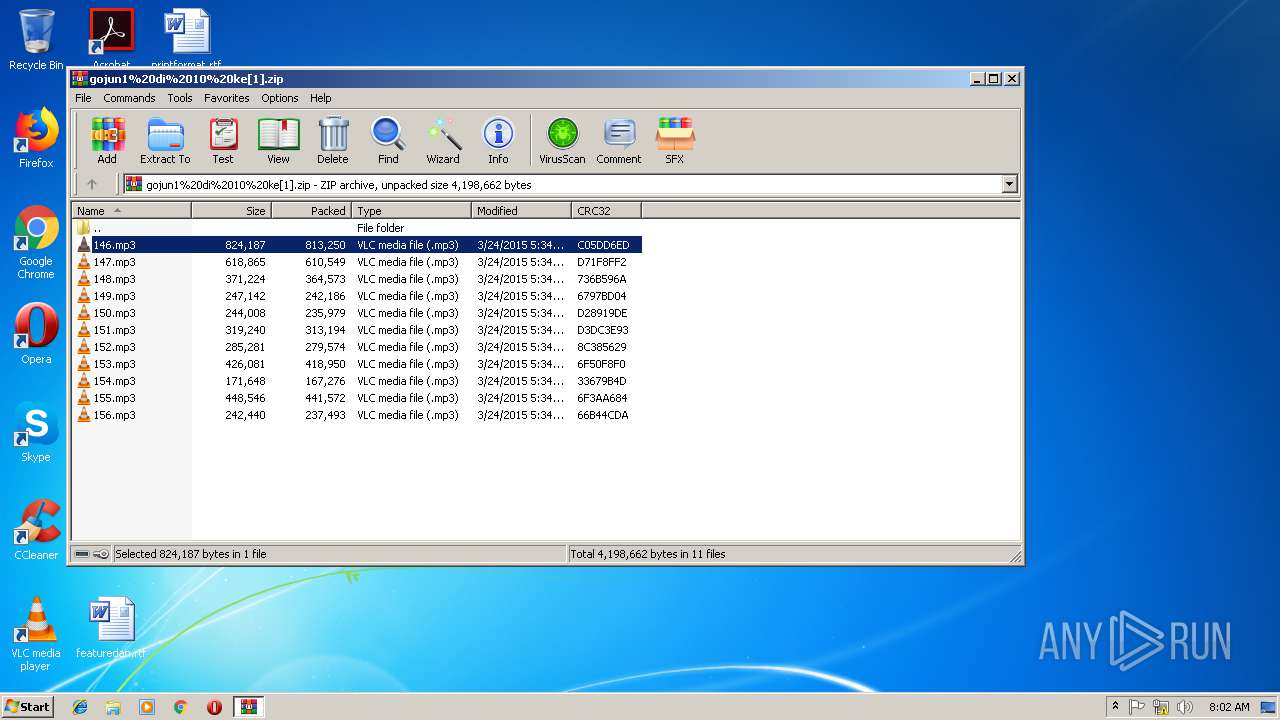
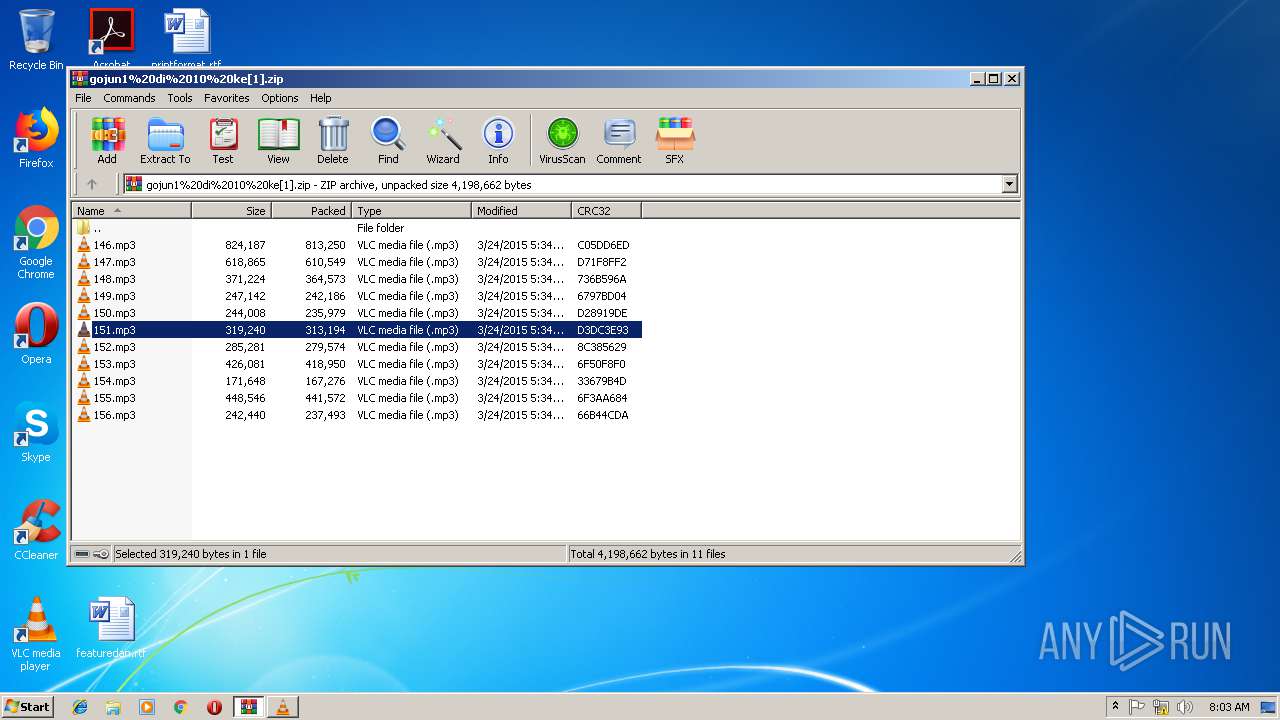
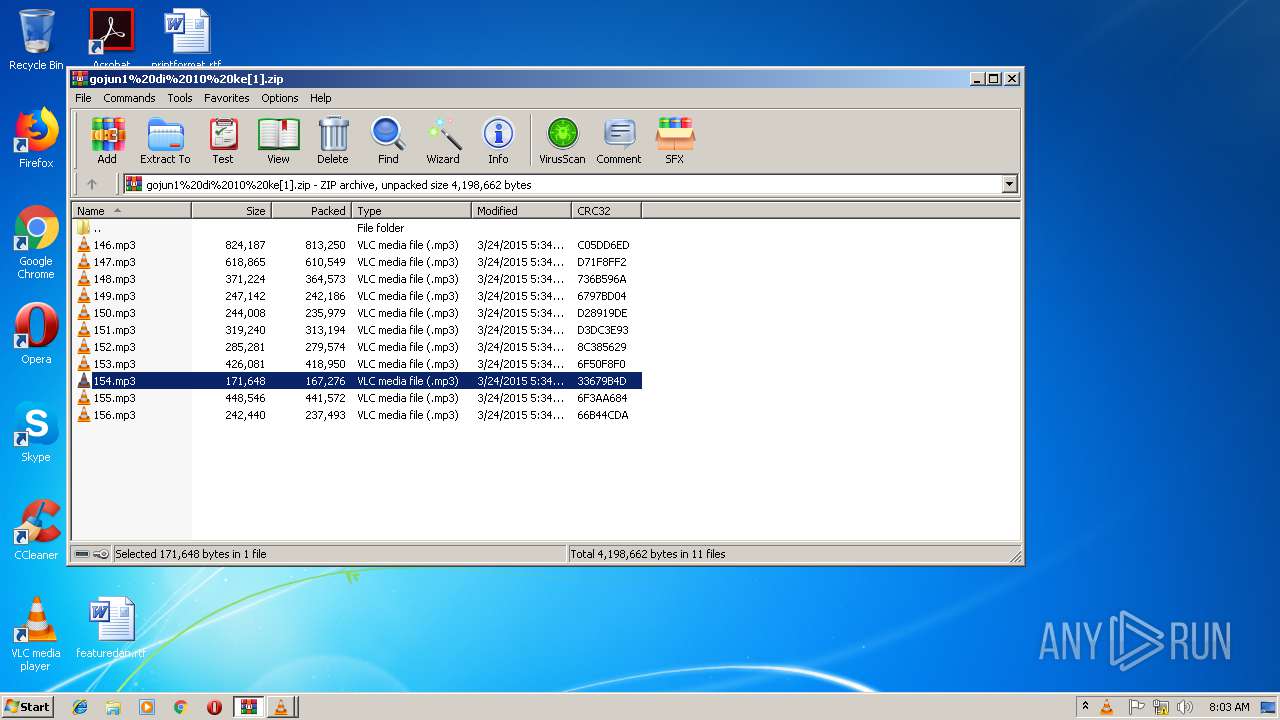
| 2976 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\gojun1%20di%2010%20ke[1].zip" | C:\Program Files\WinRAR\WinRAR.exe | — | iexplore.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3072 | "C:\Users\admin\AppData\Local\Temp\vlc-3.0.6-win32.exe" | C:\Users\admin\AppData\Local\Temp\vlc-3.0.6-win32.exe | vlc.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3076 | "C:\Program Files\VideoLAN\VLC\vlc.exe" --started-from-file "C:\Users\admin\AppData\Local\Temp\Rar$DIa2976.48955\146.mp3" | C:\Program Files\VideoLAN\VLC\vlc.exe | WinRAR.exe | ||||||||||||
User: admin Company: VideoLAN Integrity Level: MEDIUM Description: VLC media player Exit code: 0 Version: 2.2.6 Modules
| |||||||||||||||
| 3236 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2900 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3252 | "C:\Program Files\VideoLAN\VLC\vlc-cache-gen.exe" C:\Program Files\VideoLAN\VLC\plugins | C:\Program Files\VideoLAN\VLC\vlc-cache-gen.exe | nsDB3A.tmp | ||||||||||||
User: admin Company: VideoLAN Integrity Level: HIGH Description: VLC media player Exit code: 0 Version: 3.0.6 Modules
| |||||||||||||||
Total events
4 903
Read events
2 311
Write events
2 501
Delete events
91
Modification events
| (PID) Process: | (2900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {2D1C3B63-1AF7-11E9-AA93-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (2900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070100050012000800000036003600 | |||
Executable files
376
Suspicious files
5
Text files
91
Unknown types
150
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2900 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2900 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2900 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF9BF074932FFDF0DB.TMP | — | |
MD5:— | SHA256:— | |||
| 2900 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFF9A08EEFB9B0444C.TMP | — | |
MD5:— | SHA256:— | |||
| 2900 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{2D1C3B63-1AF7-11E9-AA93-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 3076 | vlc.exe | C:\Users\admin\AppData\Local\Temp\VLC7639.tmp | — | |
MD5:— | SHA256:— | |||
| 3076 | vlc.exe | C:\Users\admin\AppData\Local\Temp\VLC7782.tmp | — | |
MD5:— | SHA256:— | |||
| 3076 | vlc.exe | C:\Users\admin\AppData\Local\Temp\VLC7783.tmp | — | |
MD5:— | SHA256:— | |||
| 3076 | vlc.exe | C:\Users\admin\AppData\Local\Temp\VLC7784.tmp | — | |
MD5:— | SHA256:— | |||
| 3076 | vlc.exe | C:\Users\admin\AppData\Local\Temp\VLC7785.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
27
DNS requests
11
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2512 | vlc.exe | GET | 206 | 88.191.250.2:80 | http://update.videolan.org/vlc/status-win-x86 | FR | text | 315 b | malicious |
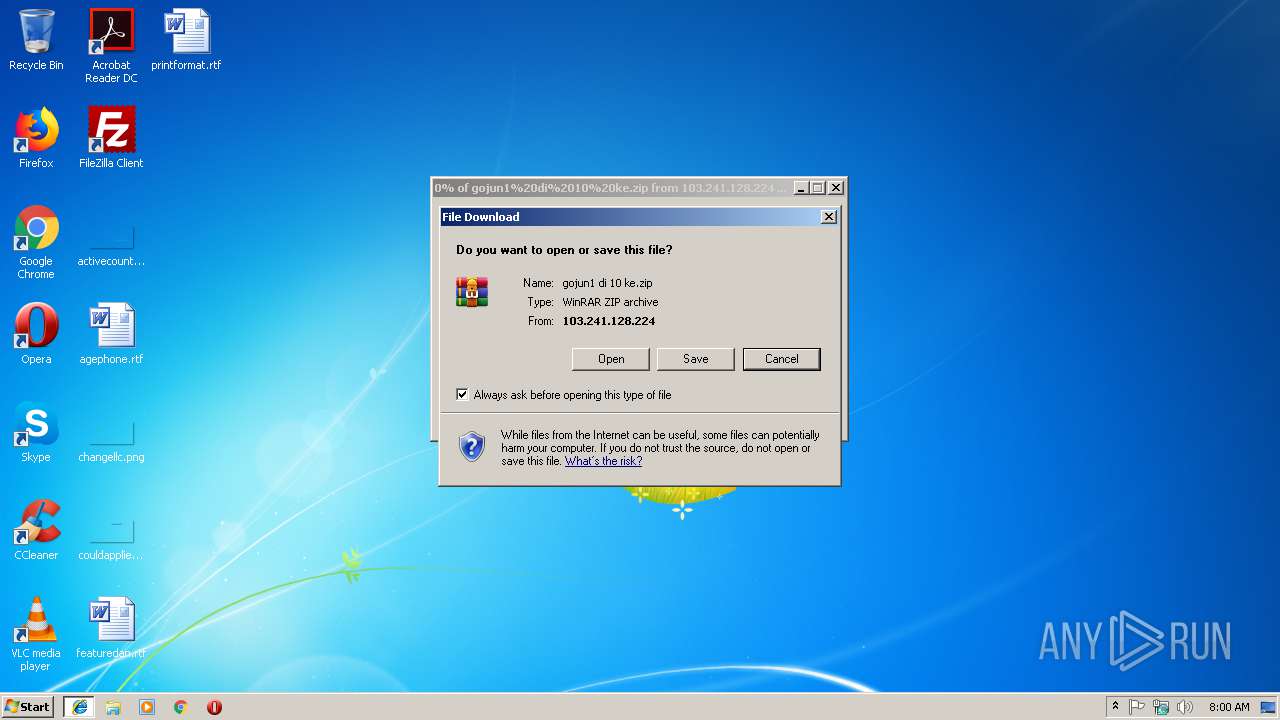
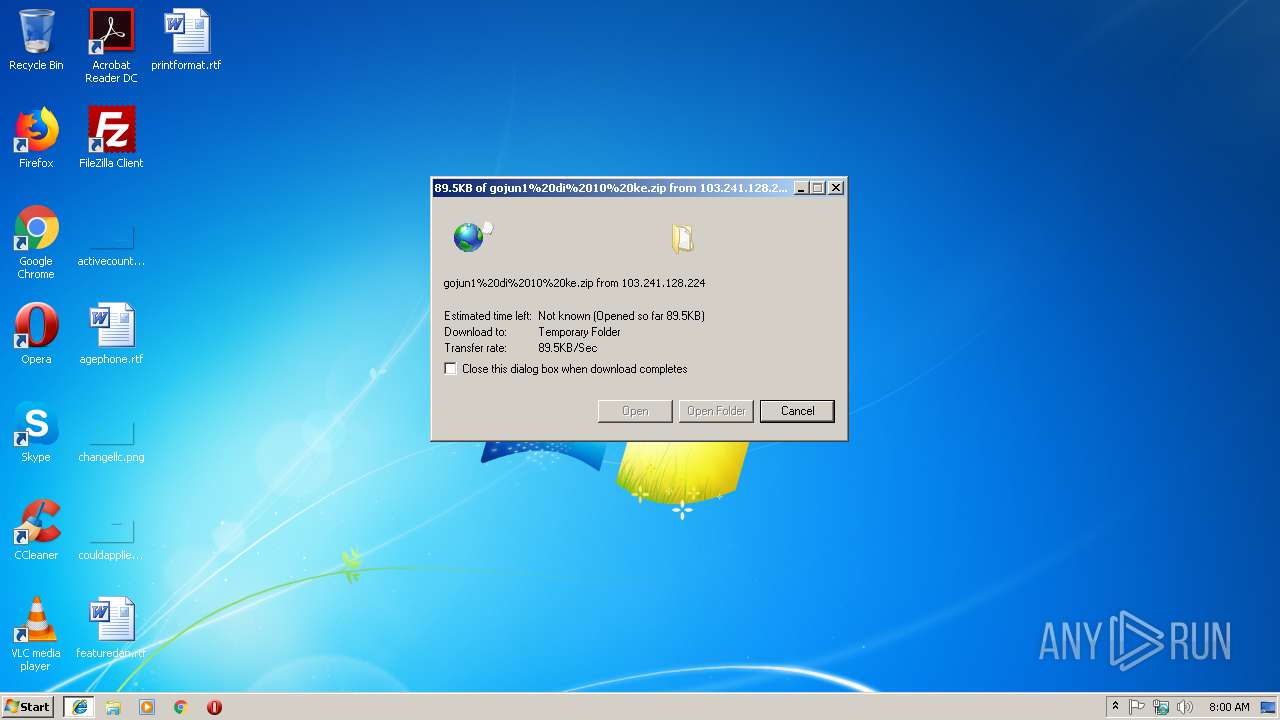
3236 | iexplore.exe | GET | 200 | 103.241.128.224:80 | http://103.241.128.224/plesk-site-preview/hakuteisha.co.jp/103.241.128.224/audio/gojun/gojun1%20di%2010%20ke.zip | JP | compressed | 3.93 Mb | malicious |
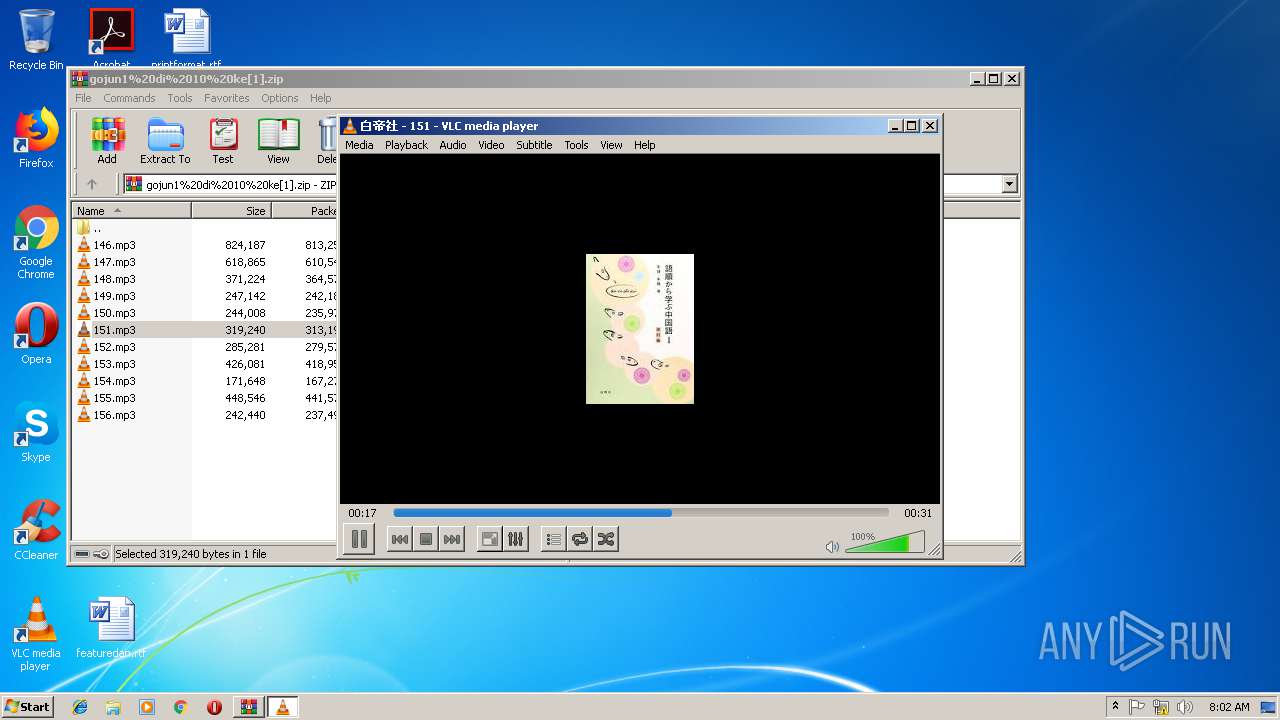
2512 | vlc.exe | GET | 200 | 88.191.250.2:80 | http://mb.videolan.org/ws/2/release/?query=artist%3A%22%E7%99%BD%E5%B8%9D%E7%A4%BE%22%20AND%20release%3A%22%E8%AA%9E%E9%A0%86%E3%81%8B%E3%82%89%E5%AD%A6%E3%81%B6%E4%B8%AD%E5%9B%BD%E8%AA%9E%EF%BC%91%28%E6%94%B9%E8%A8%82%E7%89%88%29%22 | FR | xml | 237 b | malicious |
2512 | vlc.exe | GET | 200 | 88.191.250.2:80 | http://mb.videolan.org/ws/2/release/?query=artist%3A%22%E7%99%BD%E5%B8%9D%E7%A4%BE%22%20AND%20release%3A%22%E8%AA%9E%E9%A0%86%E3%81%8B%E3%82%89%E5%AD%A6%E3%81%B6%E4%B8%AD%E5%9B%BD%E8%AA%9E%EF%BC%91%28%E6%94%B9%E8%A8%82%E7%89%88%29%22 | FR | xml | 237 b | malicious |
2512 | vlc.exe | GET | 301 | 216.58.207.78:80 | http://images.google.com/search?q=%E7%99%BD%E5%B8%9D%E7%A4%BE+%E8%AA%9E%E9%A0%86%E3%81%8B%E3%82%89%E5%AD%A6%E3%81%B6%E4%B8%AD%E5%9B%BD%E8%AA%9E%EF%BC%91(%E6%94%B9%E8%A8%82%E7%89%88)+cover&tbm=isch | US | html | 394 b | whitelisted |
2512 | vlc.exe | GET | 301 | 216.58.207.78:80 | http://images.google.com/images?q=%E7%99%BD%E5%B8%9D%E7%A4%BE%20%E8%AA%9E%E9%A0%86%E3%81%8B%E3%82%89%E5%AD%A6%E3%81%B6%E4%B8%AD%E5%9B%BD%E8%AA%9E%EF%BC%91%28%E6%94%B9%E8%A8%82%E7%89%88%29%20cover | US | html | 397 b | whitelisted |
2512 | vlc.exe | GET | 206 | 216.58.205.228:80 | http://t0.gstatic.com/images?q=tbn:ANd9GcQ3Xf52n_Pt5181GIXKBaxYgyBszp4iEaJhsA_cHgsdAIyAsVMdx1cZchaK | US | image | 2.90 Kb | whitelisted |
2512 | vlc.exe | GET | 200 | 172.217.18.4:80 | http://www.google.com/search?q=%E7%99%BD%E5%B8%9D%E7%A4%BE+%E8%AA%9E%E9%A0%86%E3%81%8B%E3%82%89%E5%AD%A6%E3%81%B6%E4%B8%AD%E5%9B%BD%E8%AA%9E%EF%BC%91(%E6%94%B9%E8%A8%82%E7%89%88)+cover&tbm=isch | US | html | 51.8 Kb | malicious |
2512 | vlc.exe | GET | 302 | 195.154.241.219:80 | http://get.videolan.org/vlc/3.0.6/win32/vlc-3.0.6-win32.exe | FR | html | 116 b | suspicious |
2512 | vlc.exe | GET | 206 | 178.217.221.234:80 | http://piotrkosoft.net/pub/mirrors/videolan/vlc/3.0.6/win32/vlc-3.0.6-win32.exe.asc | PL | asc | 195 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2900 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2512 | vlc.exe | 88.191.250.2:80 | update.videolan.org | Free SAS | FR | malicious |
3236 | iexplore.exe | 103.241.128.224:80 | — | Yahoo Japan Corporation | JP | malicious |
2512 | vlc.exe | 216.58.207.78:80 | images.google.com | Google Inc. | US | whitelisted |
2512 | vlc.exe | 172.217.18.4:80 | www.google.com | Google Inc. | US | whitelisted |
2512 | vlc.exe | 216.58.205.228:80 | t0.gstatic.com | Google Inc. | US | whitelisted |
2512 | vlc.exe | 195.154.241.219:80 | get.videolan.org | Online S.a.s. | FR | suspicious |
2512 | vlc.exe | 193.219.28.2:443 | ftp.icm.edu.pl | University of Warsaw | PL | unknown |
3628 | vlc.exe | 216.58.207.78:80 | images.google.com | Google Inc. | US | whitelisted |
2512 | vlc.exe | 178.217.221.234:80 | piotrkosoft.net | Netico S.c. | PL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
update.videolan.org |
| unknown |
mb.videolan.org |
| malicious |
images.google.com |
| whitelisted |
www.google.com |
| malicious |
t0.gstatic.com |
| whitelisted |
get.videolan.org |
| unknown |
ftp.icm.edu.pl |
| unknown |
piotrkosoft.net |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3236 | iexplore.exe | A Network Trojan was detected | MALWARE [PTsecurity] Banload.WRI (Trojan.Agent.DDSA) Requesting Zip Archive |
Process | Message |
|---|---|
vlc.exe | core libvlc: one instance mode ENABLED
|
vlc.exe | core libvlc: Running vlc with the default interface. Use 'cvlc' to use vlc without interface.
|
vlc.exe | mpgatofixed32 audio converter error: libmad error: bad main_data_begin pointer
|
vlc.exe | core libvlc: one instance mode ENABLED
|
vlc.exe | core libvlc: Running vlc with the default interface. Use 'cvlc' to use vlc without interface.
|
vlc.exe | core libvlc: Status file authenticated
|
vlc.exe | core update download: C:\Users\admin\AppData\Local\Temp\vlc-3.0.6-win32.exe authenticated
|
vlc-cache-gen.exe | main libvlc debug: Copyright © 1996-2018 the VideoLAN |
vlc-cache-gen.exe | main libvlc debug: Copyright © 1996-2018 the VideoLAN team
|
vlc-cache-gen.exe | main libvlc debug: configured with ../extras/package/win32/../../../configure '--enable-update-check' '--enable-lua' '--enable-faad' '--enable-flac' '--enable-theora' '--enable-avcodec' '--enable-merge-ffmpeg' '--enable-dca' '--enable-mpc' '--enable-libass' '--enable-schroedinger' '--enable-realrtsp' '--enable-live555' '--enable-dvdread' '--enable-shout' '--enable-goom' '--enable-caca' '--enable-qt' '--enable-skins2' '--enable-sse' '--enable-mmx' '--enable-libcddb' '--enable-zvbi' '--disable-telx' '--enable-nls' '--host=i686-w64-mingw32' '--with-breakpad=https://win.crashes.videolan.org' 'host_alias=i686-w64-mingw32' 'PKG_CONFIG_LIBDIR=/home/jenkins/workspace/vlc-release/windows/vlc-release-win32-x86/contrib/i686-w64-mingw32/lib/pkgconfig'
|