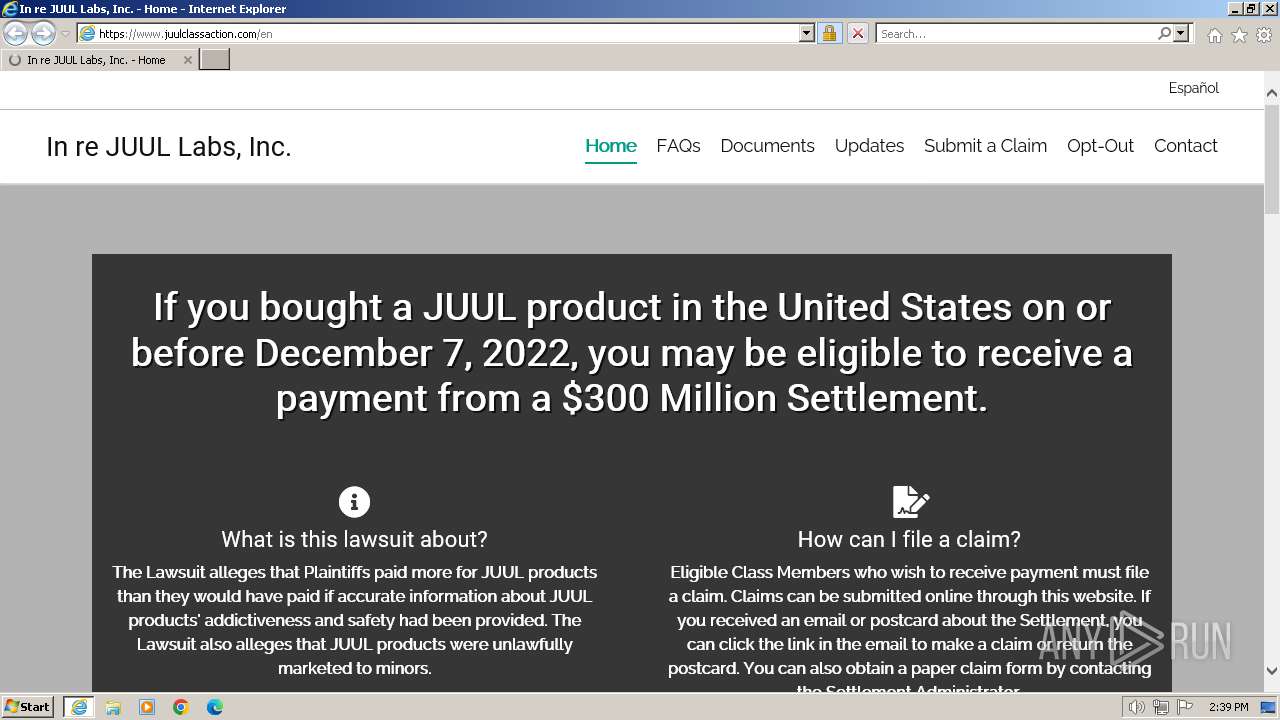
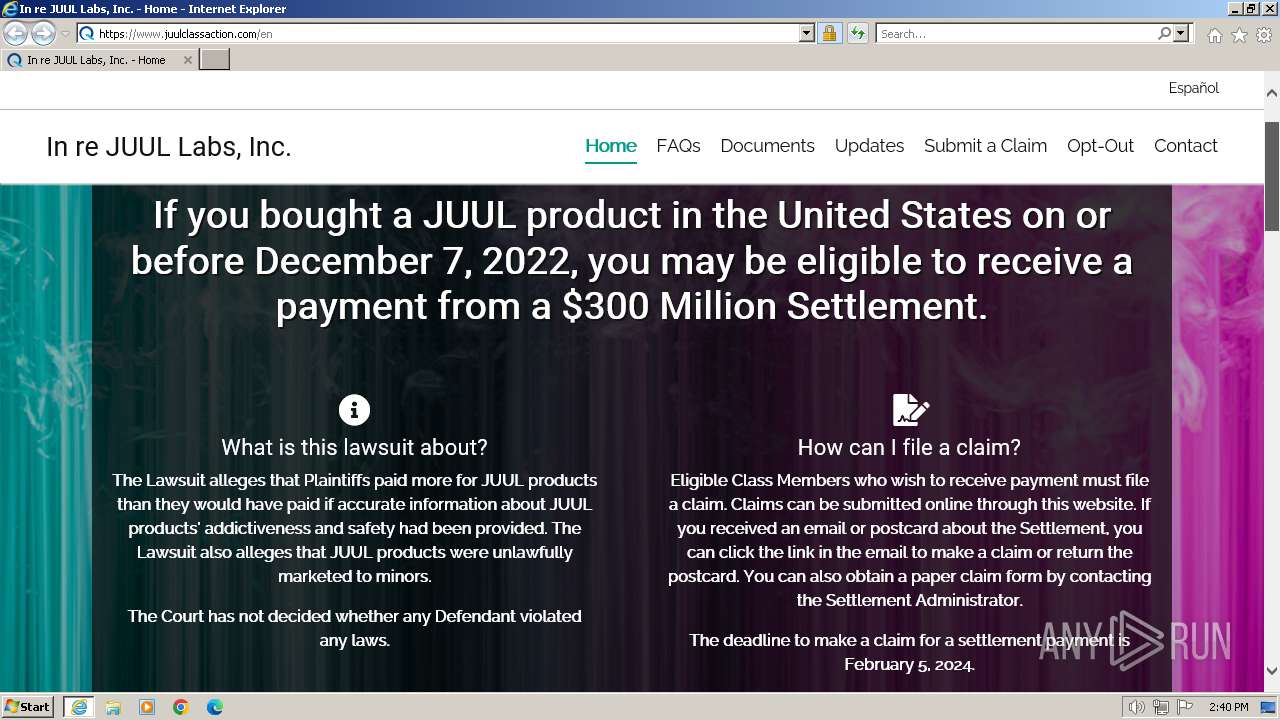
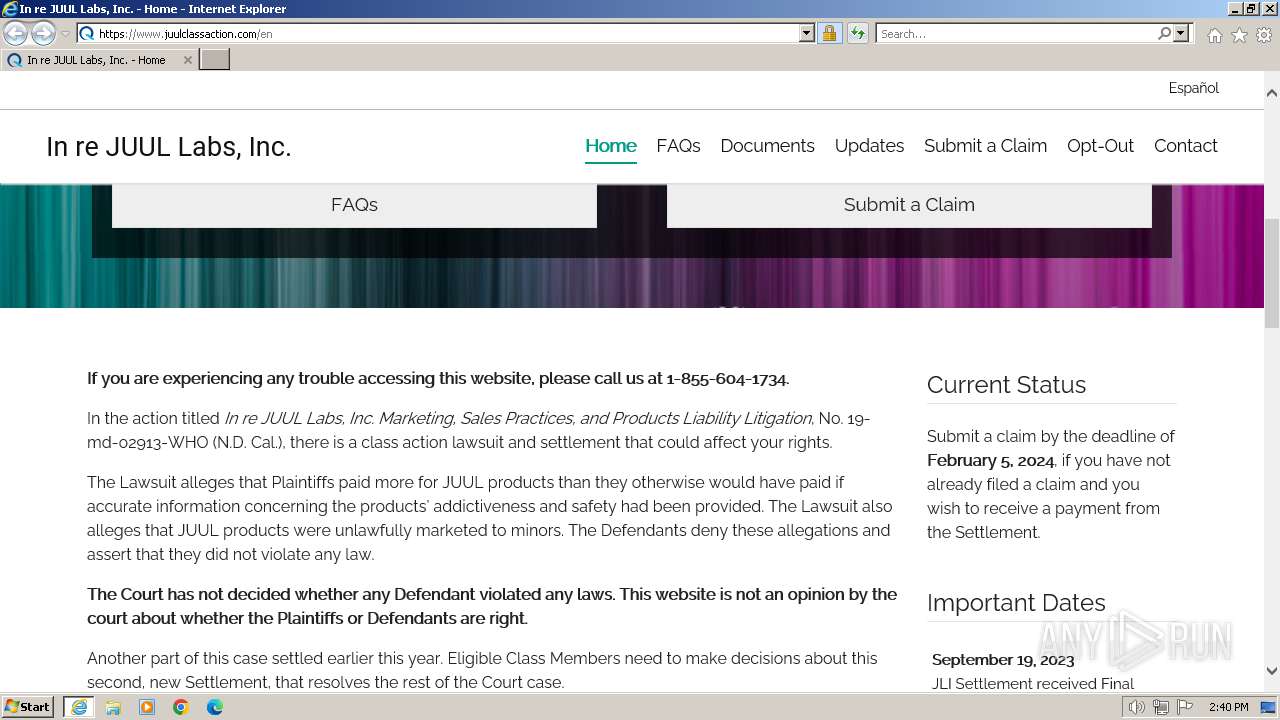
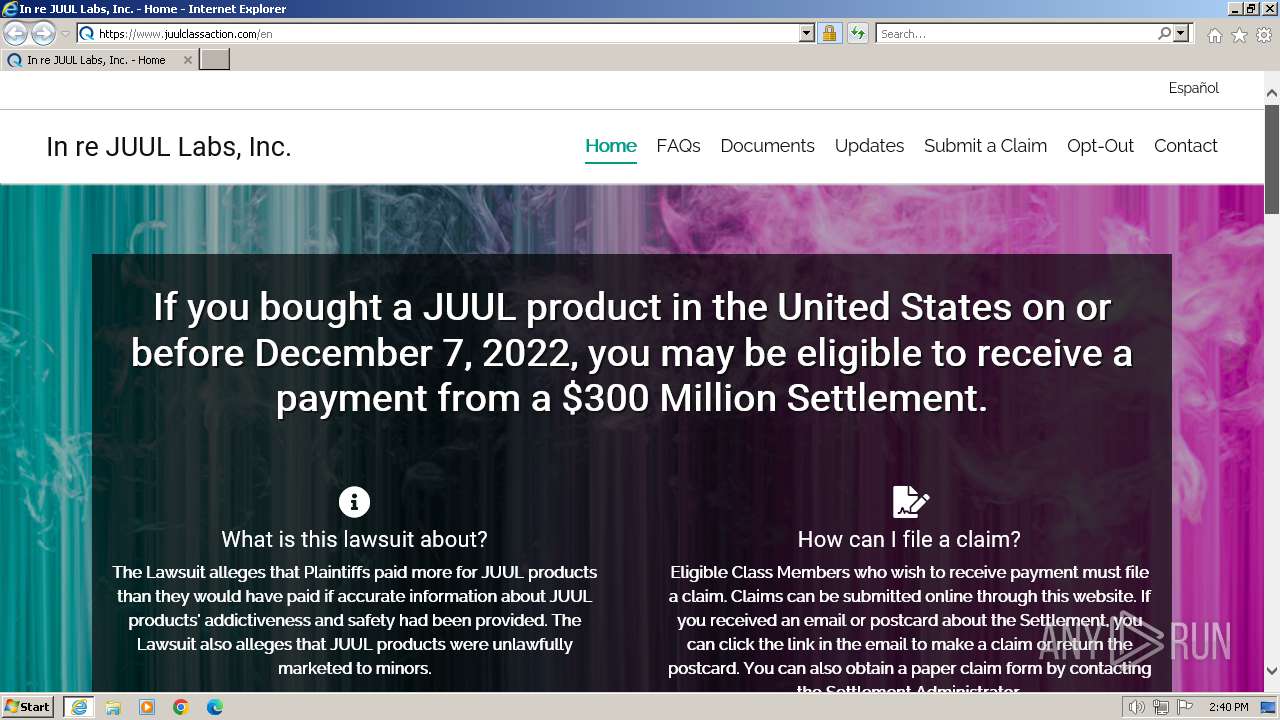
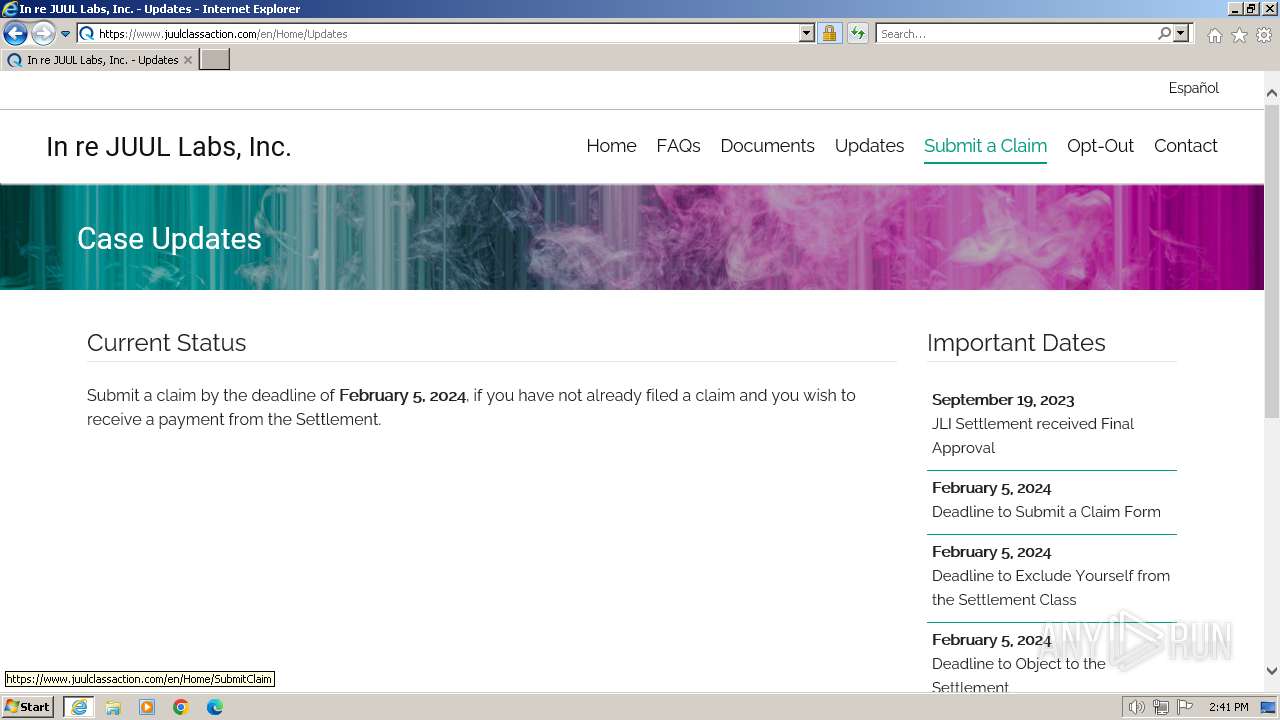
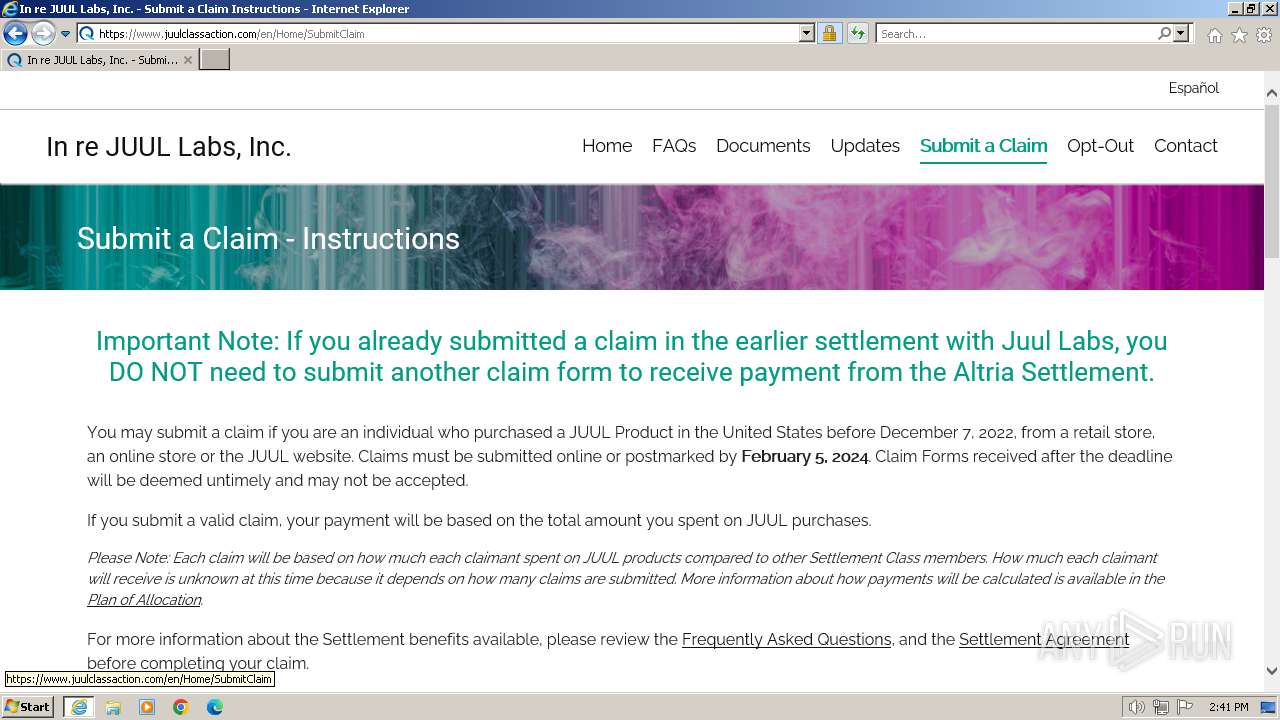
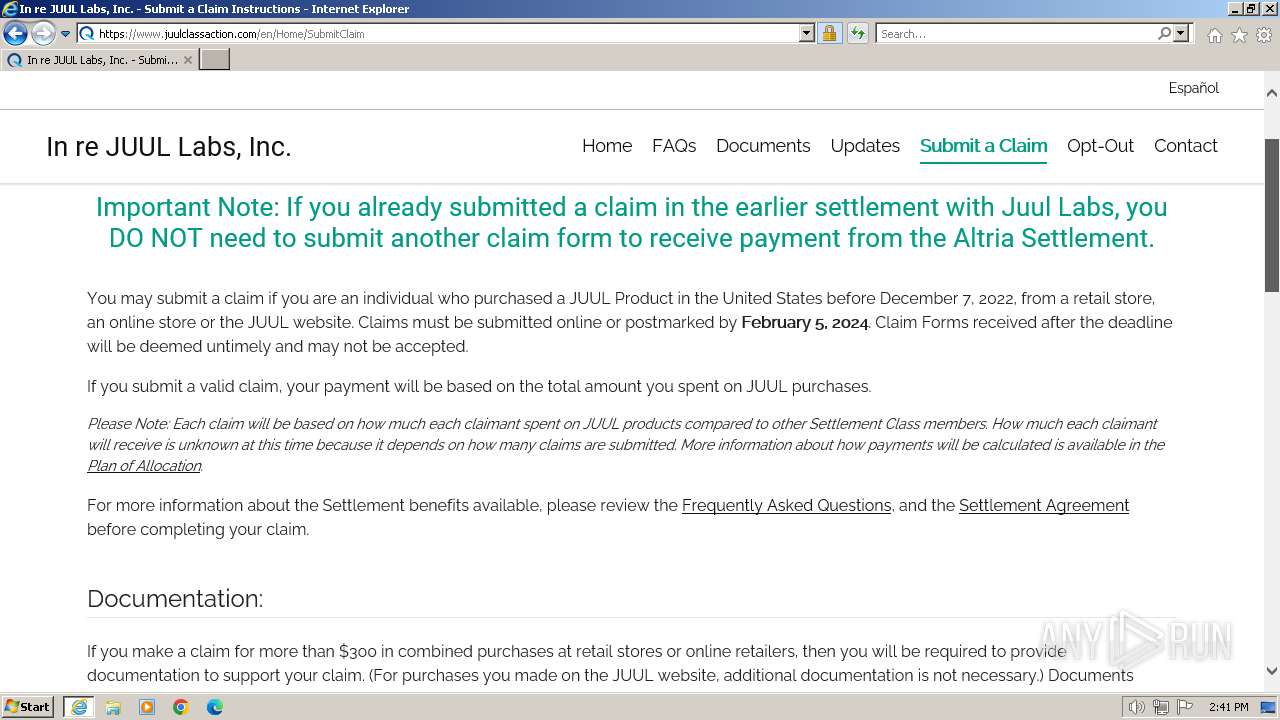
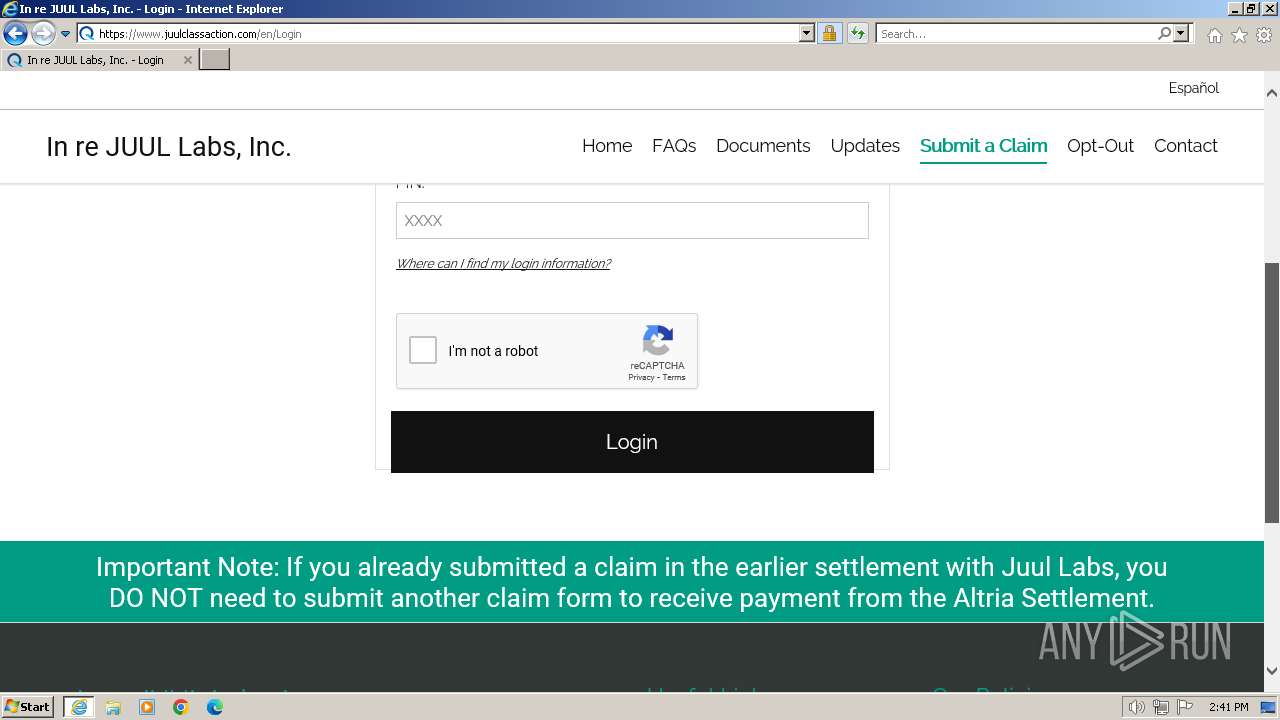
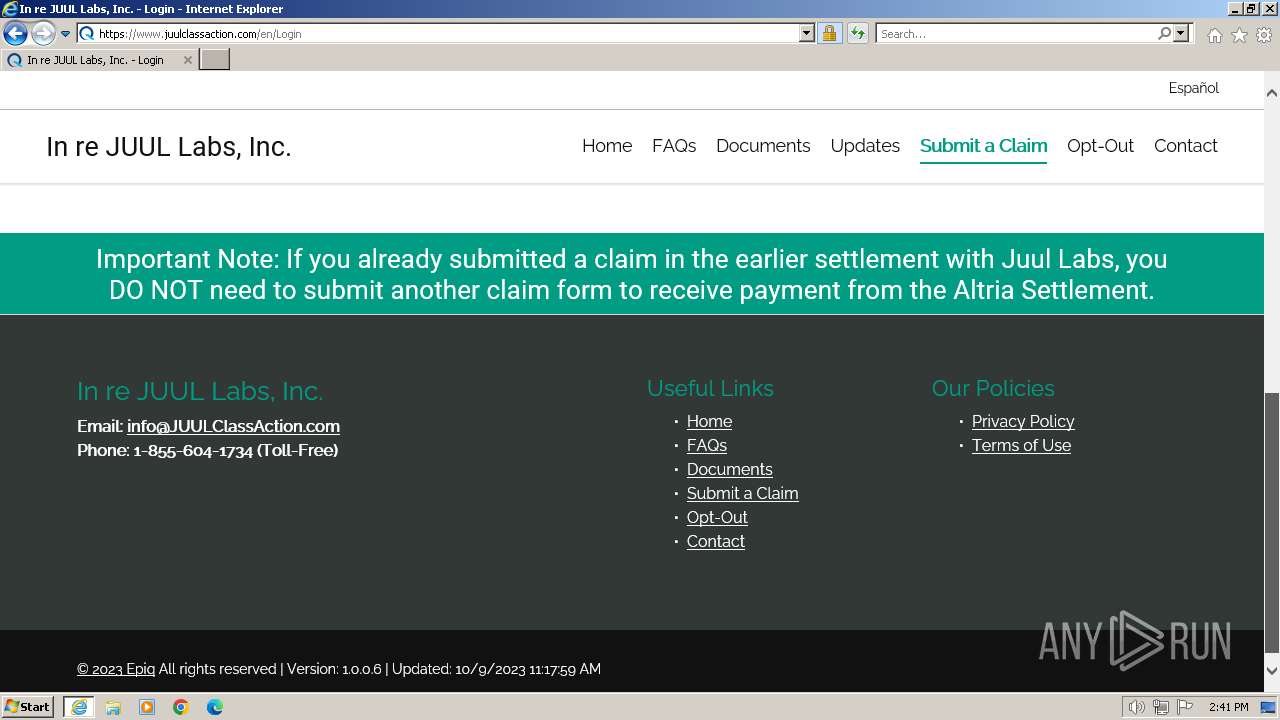
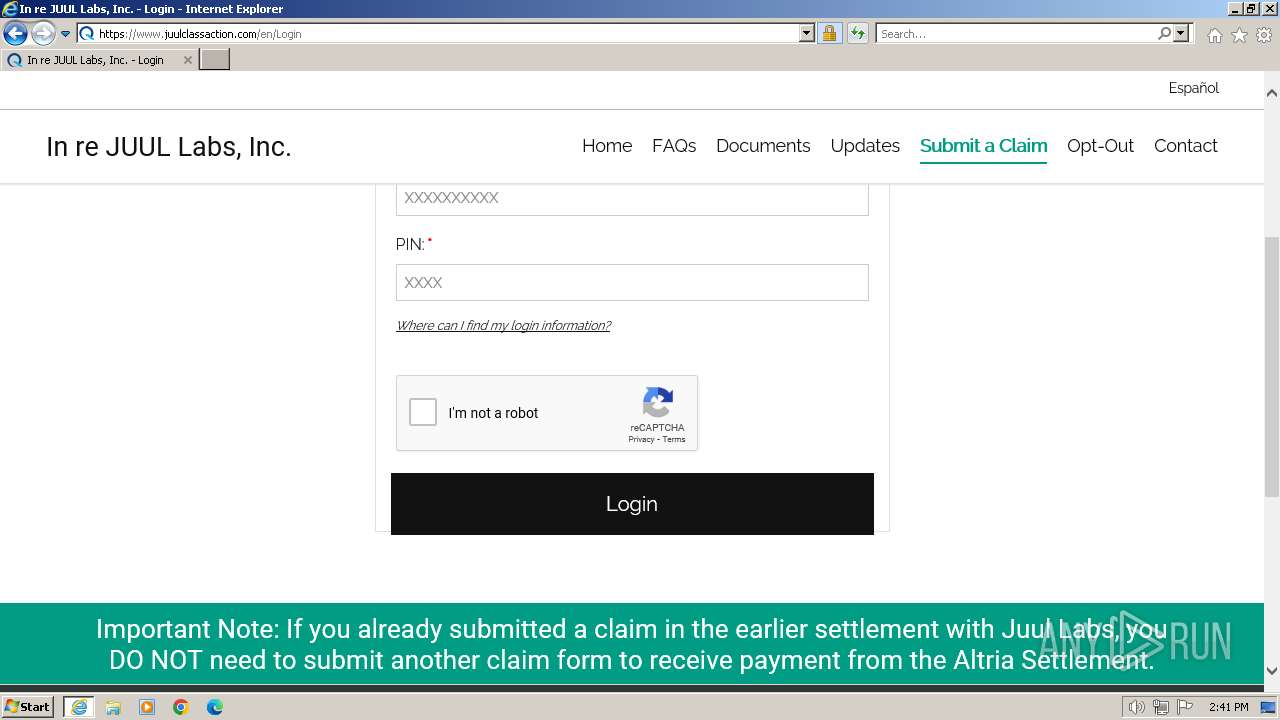
| URL: | www.juulclassaction.com |
| Full analysis: | https://app.any.run/tasks/dc240107-26ac-417e-a29e-9aff6882e71d |
| Verdict: | Malicious activity |
| Analysis date: | January 10, 2024, 14:39:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A236AB16E4FC67462CF21DF98EC8DCD6 |
| SHA1: | 574560EF8CBF93B59C4FC6F455E526C1867D8A34 |
| SHA256: | 1D5092E65338FEDC06704548A7E03E9DF2EAAD3A6A36710AD98799F59822B405 |
| SSDEEP: | 3:EJaKOKIn:Wa0In |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 120)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
39
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
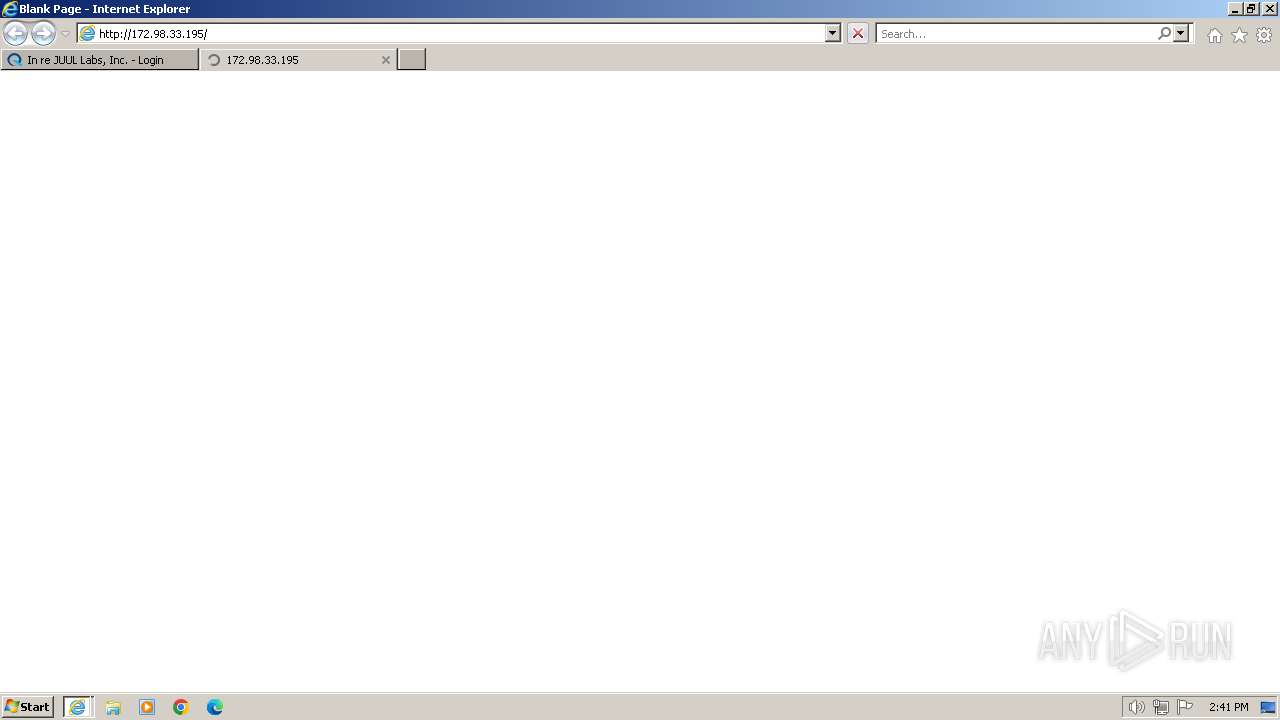
| 120 | "C:\Program Files\Internet Explorer\iexplore.exe" "www.juulclassaction.com" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1288 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:120 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2644 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:120 CREDAT:2692392 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
33 062
Read events
32 980
Write events
80
Delete events
2
Modification events
| (PID) Process: | (120) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (120) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (120) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (120) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (120) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (120) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (120) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (120) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (120) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (120) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
67
Text files
221
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1288 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:1F99EA86A0DB95EC0AD37A7340DF9DF7 | SHA256:9BB7BBB9A926AA75A2C778EE4212703B8A62DFABC76D9625875B848A93B35F36 | |||
| 1288 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 1288 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:5715E1E4E62EE95E6C31685978092461 | SHA256:B73D92204F95668AF2B0D464CF51A0E084D30E829BFC72A7AB917B6A45B5E226 | |||
| 1288 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\all[1].css | text | |
MD5:DC93D584E41F8417F6B7163320D34329 | SHA256:481A0574246E281316FFA0E15399BF5388BB81AE550CE0401A0353B6BB2D1E5A | |||
| 1288 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\CO2ZQRAV | text | |
MD5:FDA44910DEB1A460BE4AC5D56D61D837 | SHA256:933B971C6388D594A23FA1559825DB5BEC8ADE2DB1240AA8FC9D0C684949E8C9 | |||
| 1288 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\datepicker[1].css | text | |
MD5:A72E5D807A8FA61AE87EEA59AC306157 | SHA256:9D7D3612707CC02344FD2E66FC292EF66723C0038B350131341EBAA3632D8C29 | |||
| 1288 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:AB53F8C87BA6D82DA23840E66A180FF7 | SHA256:E21585387A987DC995A00E0113871E1E5B189E47D470BC7B8D442972C02934C7 | |||
| 1288 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\en[1].htm | html | |
MD5:5A1DF34EEEA810F9351CEA5D2DC94480 | SHA256:B8FF50E639ED0E4CB905DF22982FA06E3E15B6907750D944D8305952CAC157F6 | |||
| 1288 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\Site[1].css | text | |
MD5:4C4ACB2133FB6BA807DD6DB1DEC4BB71 | SHA256:DA2678409F3ADF37FE55574AFBEA0AC835677D91D7748723F46F039581266689 | |||
| 1288 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\bootstrap.min[1].css | text | |
MD5:355C6A6A8C8127F8F2966C6B8B09F471 | SHA256:8953184B0E63415AA8D1D5CA615F95526C9A6371B40D073373280500D1A7D48E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
145
DNS requests
59
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1288 | iexplore.exe | GET | 301 | 104.19.167.57:80 | http://www.juulclassaction.com/ | unknown | — | — | unknown |
1288 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | unknown | binary | 1.47 Kb | unknown |
1288 | iexplore.exe | GET | 200 | 184.24.77.194:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?129d20c84d8c4223 | unknown | compressed | 4.66 Kb | unknown |
1288 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | binary | 1.41 Kb | unknown |
1288 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQS14tALDViBvqCf47YkiQRtKz1BAQUpc436uuwdQ6UZ4i0RfrZJBCHlh8CEAdTx8Zw1YdnlwwNhNJrzqY%3D | unknown | binary | 279 b | unknown |
1288 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCECO0Y37WzHRLPzhV9vNju | unknown | binary | 472 b | unknown |
1288 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQD7vSzSbK8Z0QnHSrEZ7mPf | unknown | binary | 472 b | unknown |
1288 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | unknown | binary | 724 b | unknown |
1288 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCAPCRpfvazdAnzYNtm9aj3 | unknown | binary | 472 b | unknown |
120 | iexplore.exe | GET | 304 | 184.24.77.194:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?1a6e676fbb64f2cc | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1288 | iexplore.exe | 104.19.167.57:80 | www.juulclassaction.com | CLOUDFLARENET | — | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1288 | iexplore.exe | 104.19.167.57:443 | www.juulclassaction.com | CLOUDFLARENET | — | unknown |
1288 | iexplore.exe | 184.24.77.194:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
1288 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1288 | iexplore.exe | 172.64.141.13:443 | use.fontawesome.com | CLOUDFLARENET | US | unknown |
1288 | iexplore.exe | 142.250.186.42:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
1288 | iexplore.exe | 142.250.185.200:443 | www.googletagmanager.com | GOOGLE | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.juulclassaction.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
use.fontawesome.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
region1.google-analytics.com |
| whitelisted |
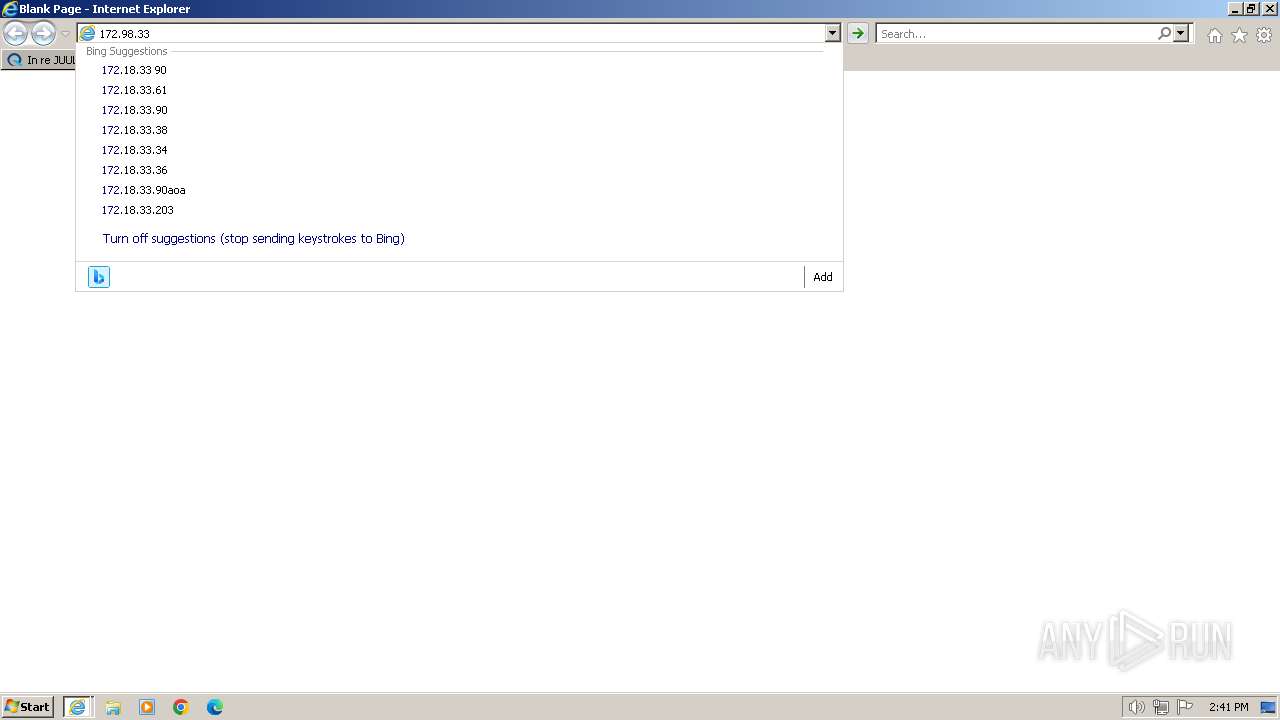
api.bing.com |
| whitelisted |
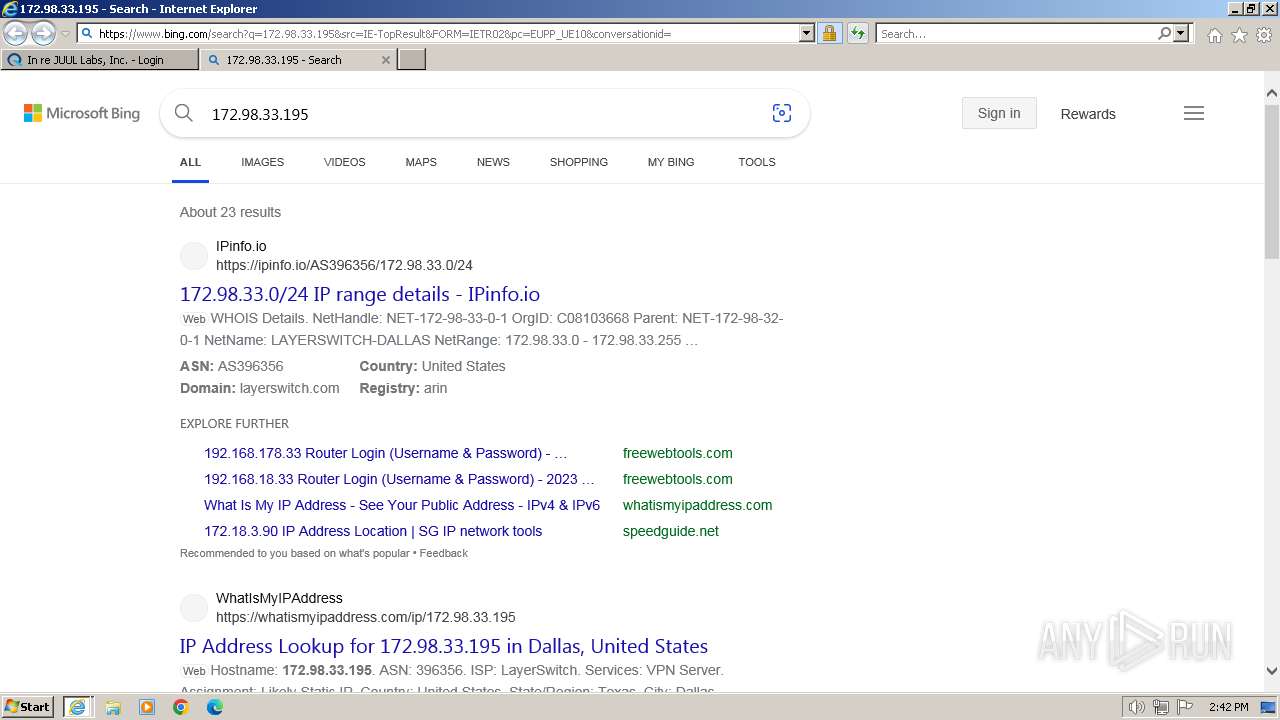
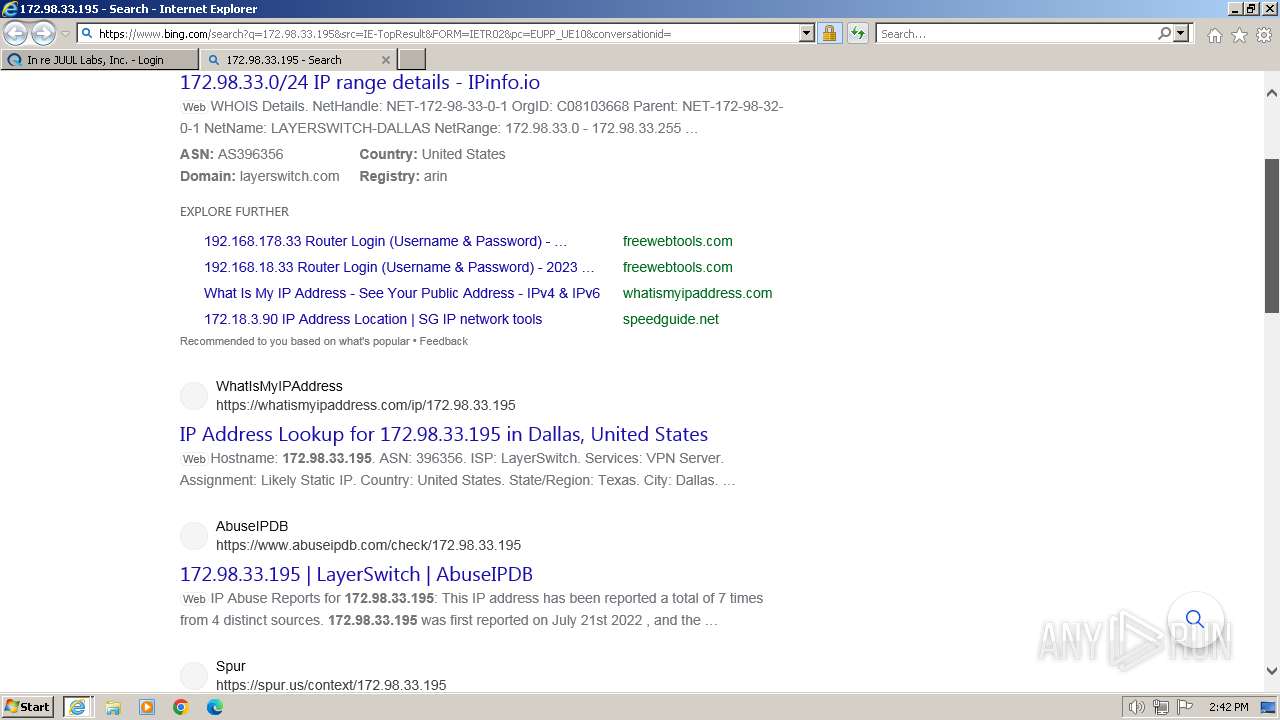
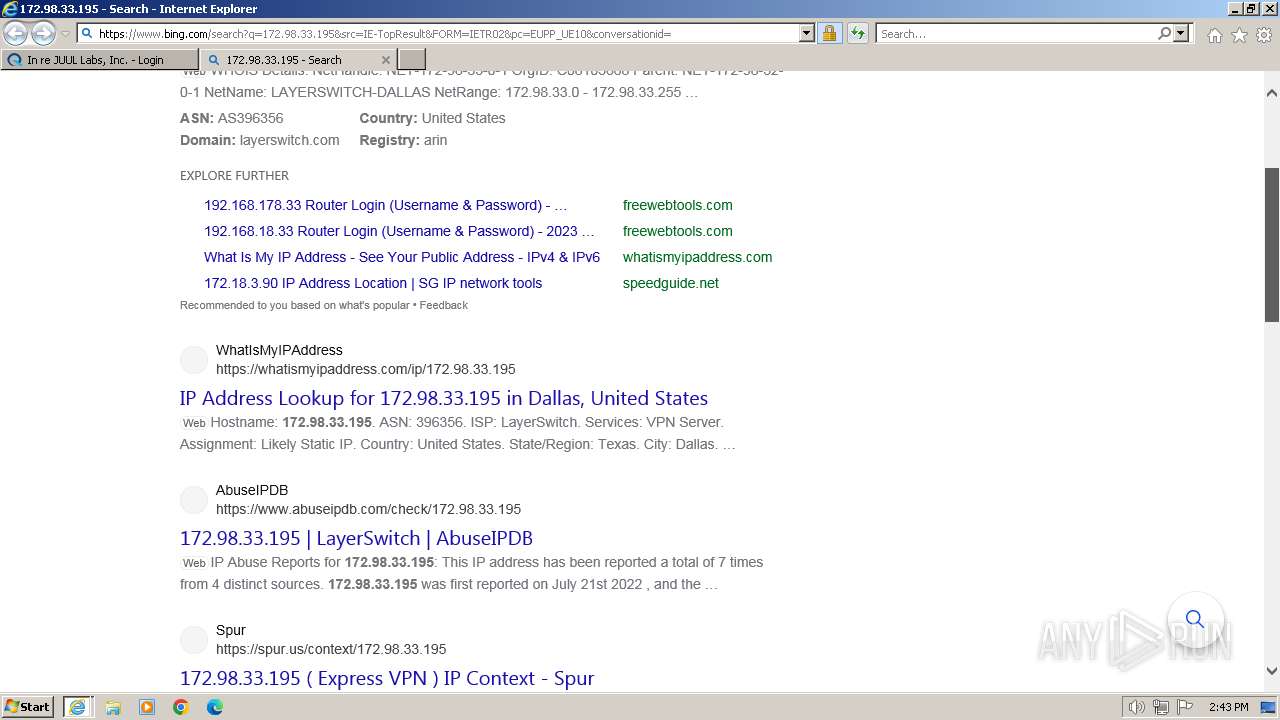
Threats
PID | Process | Class | Message |
|---|---|---|---|
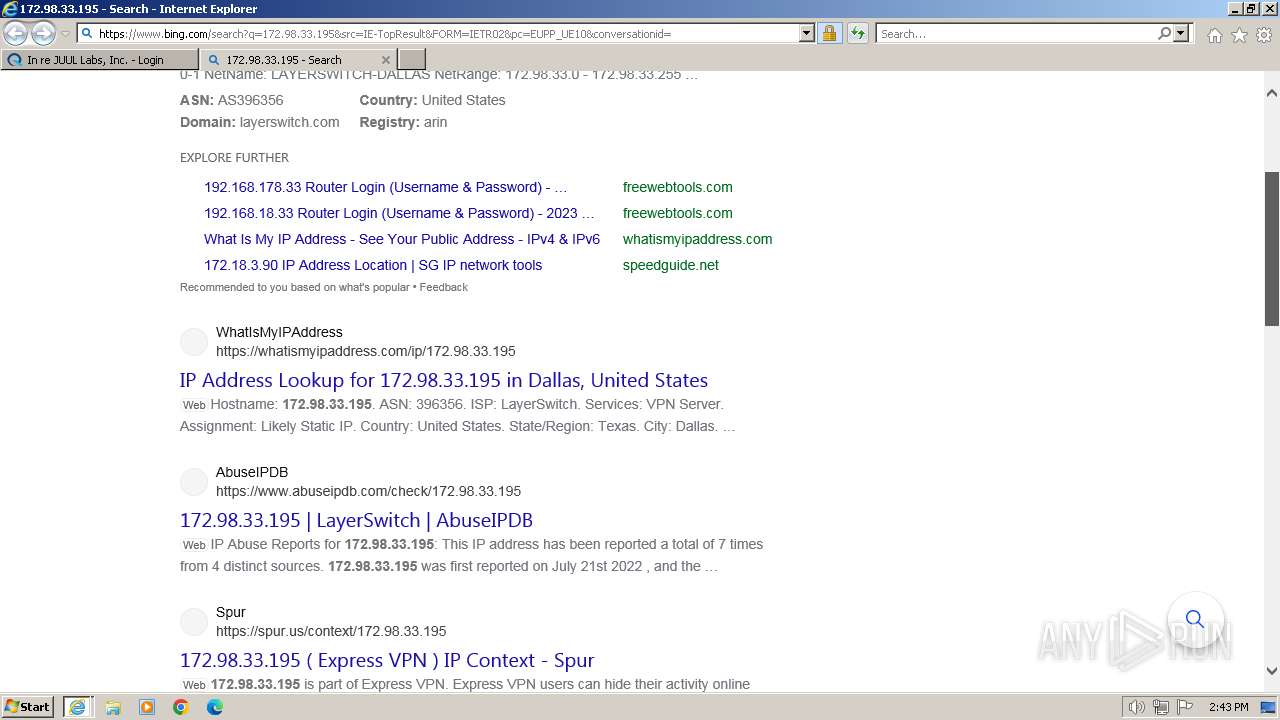
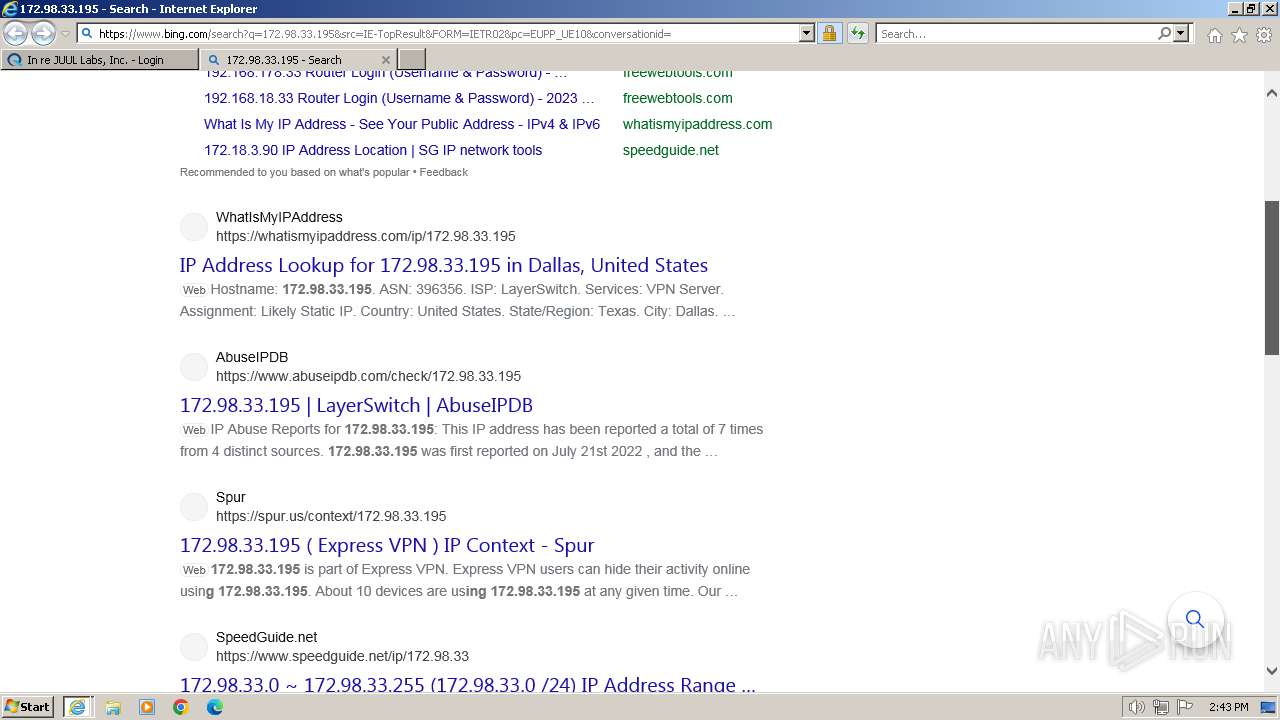
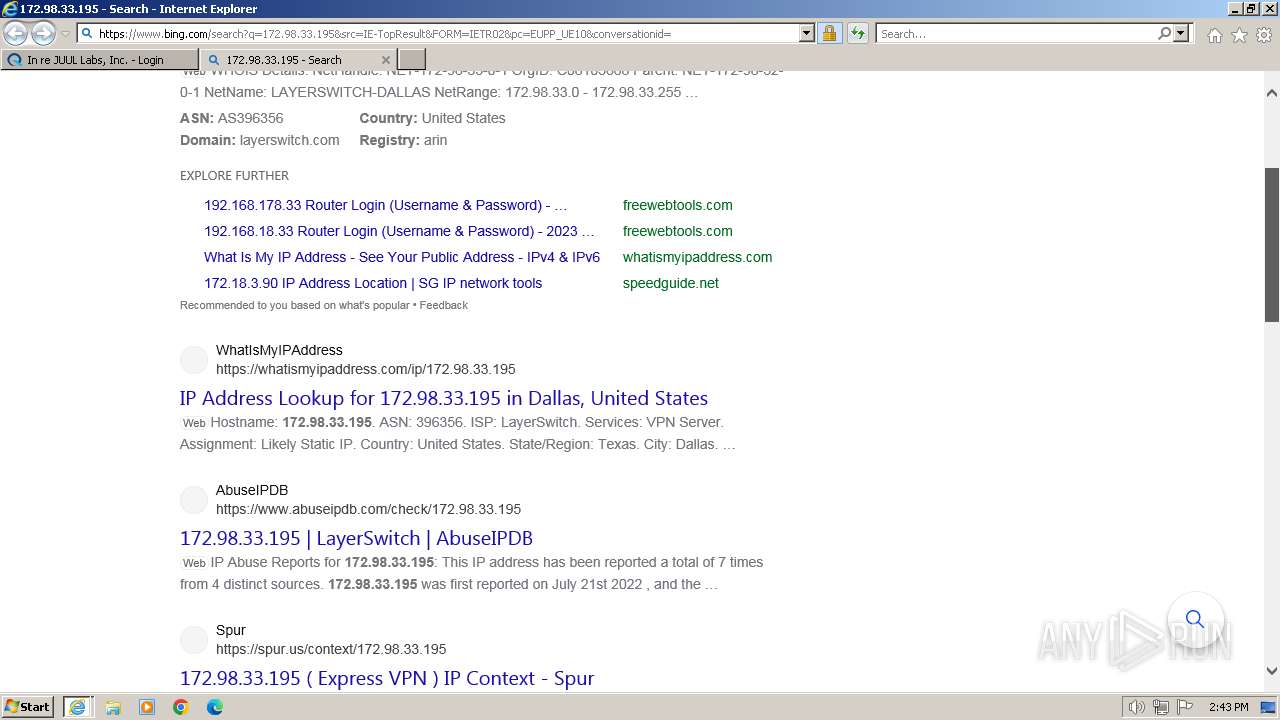
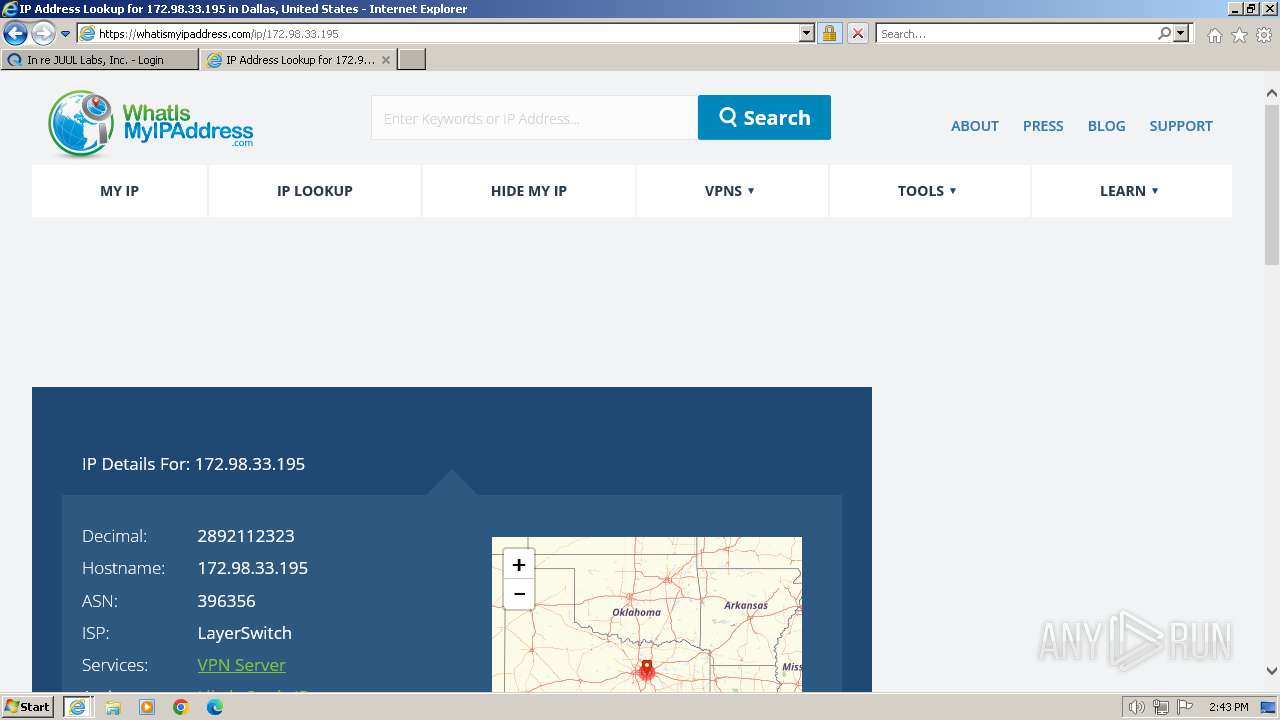
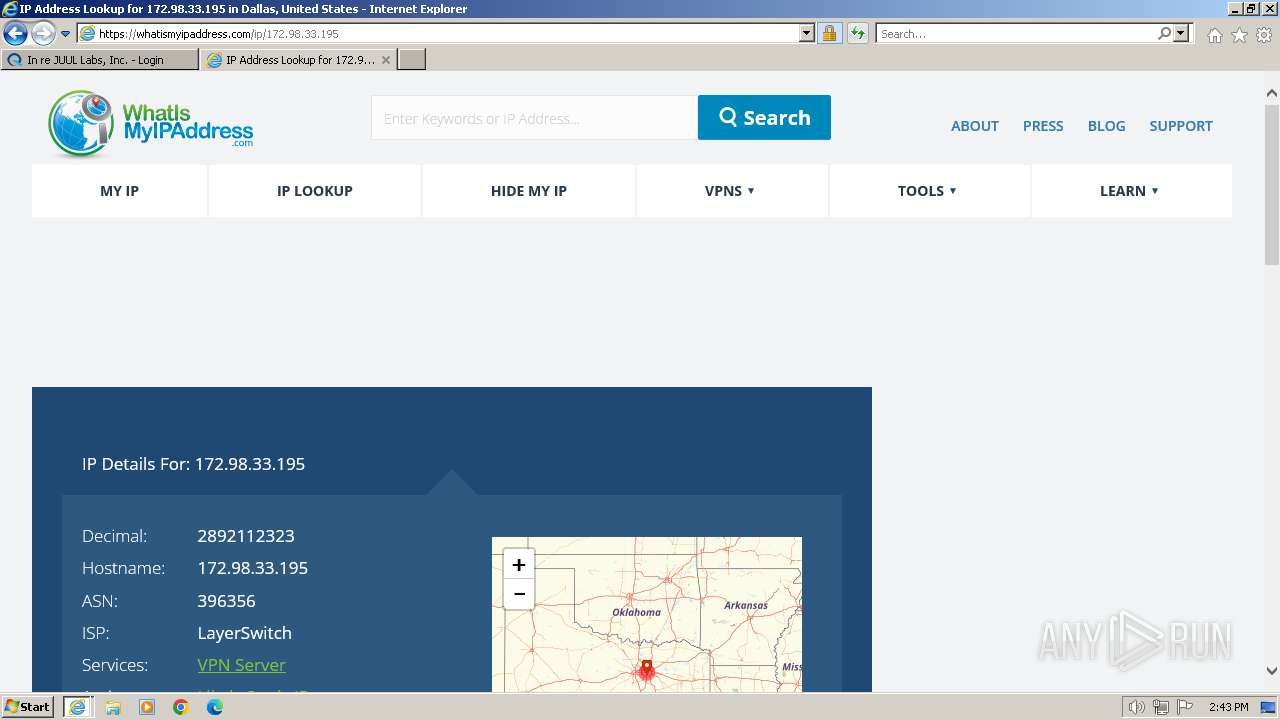
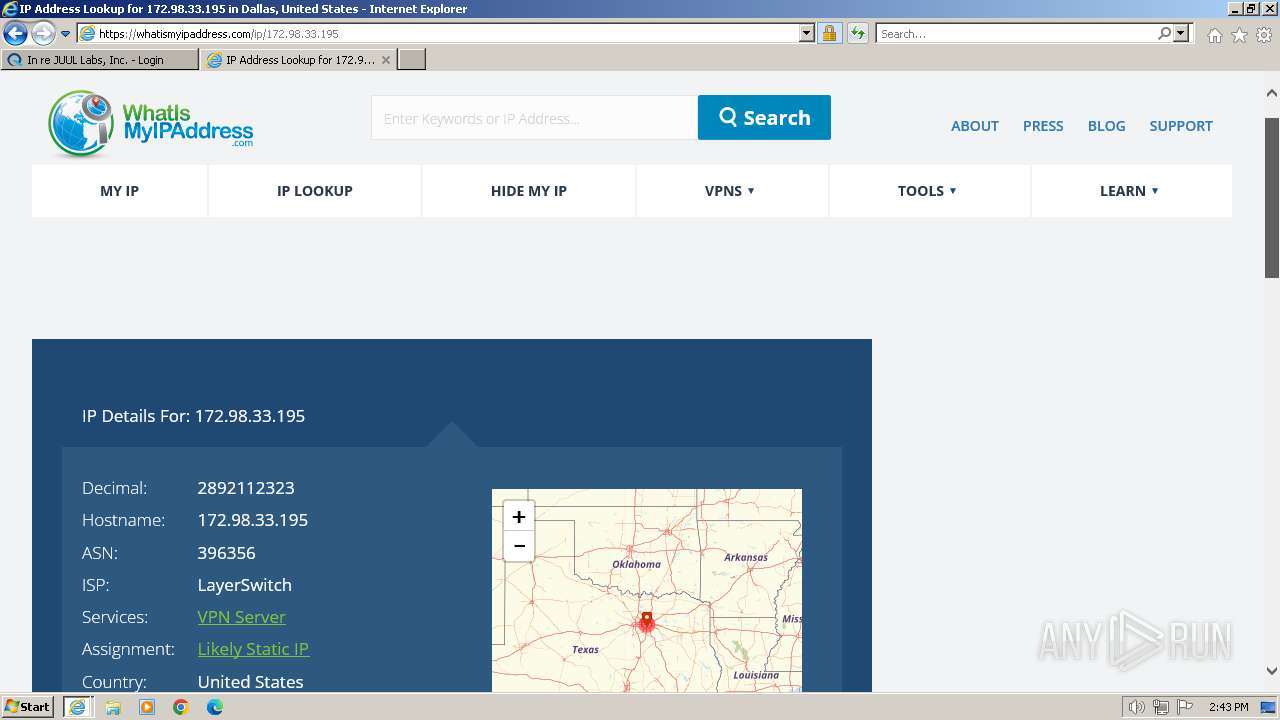
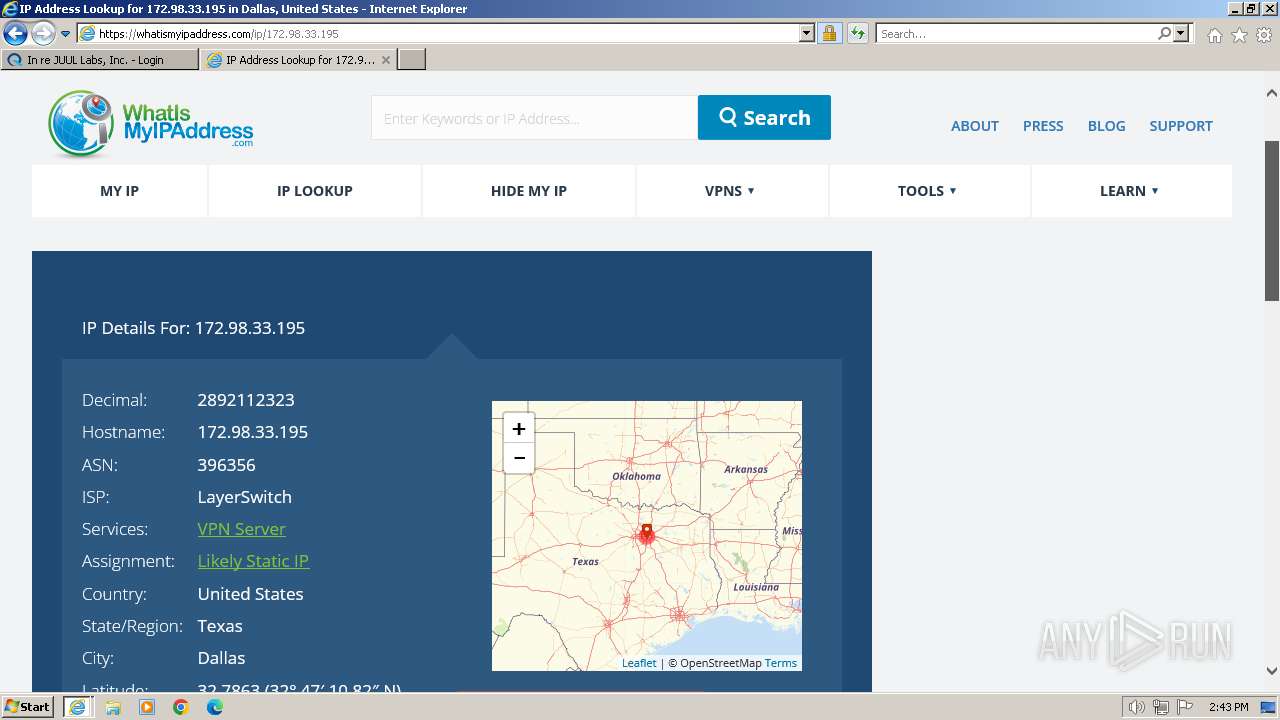
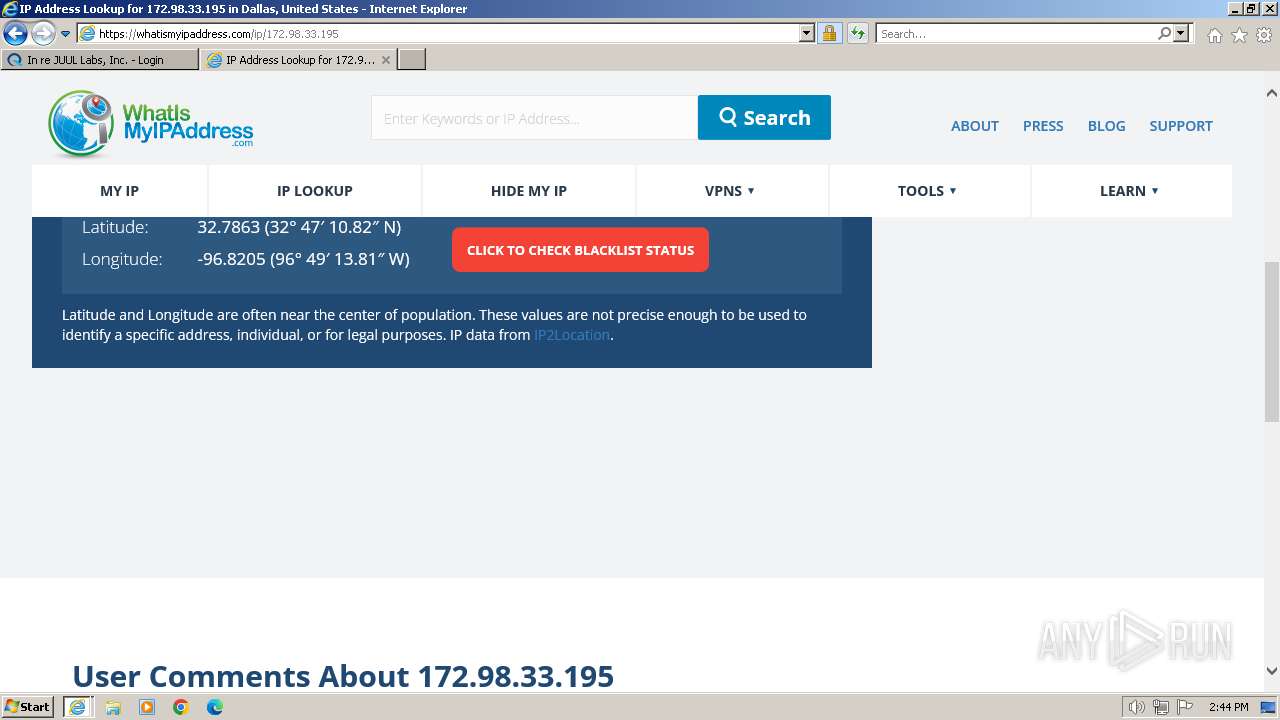
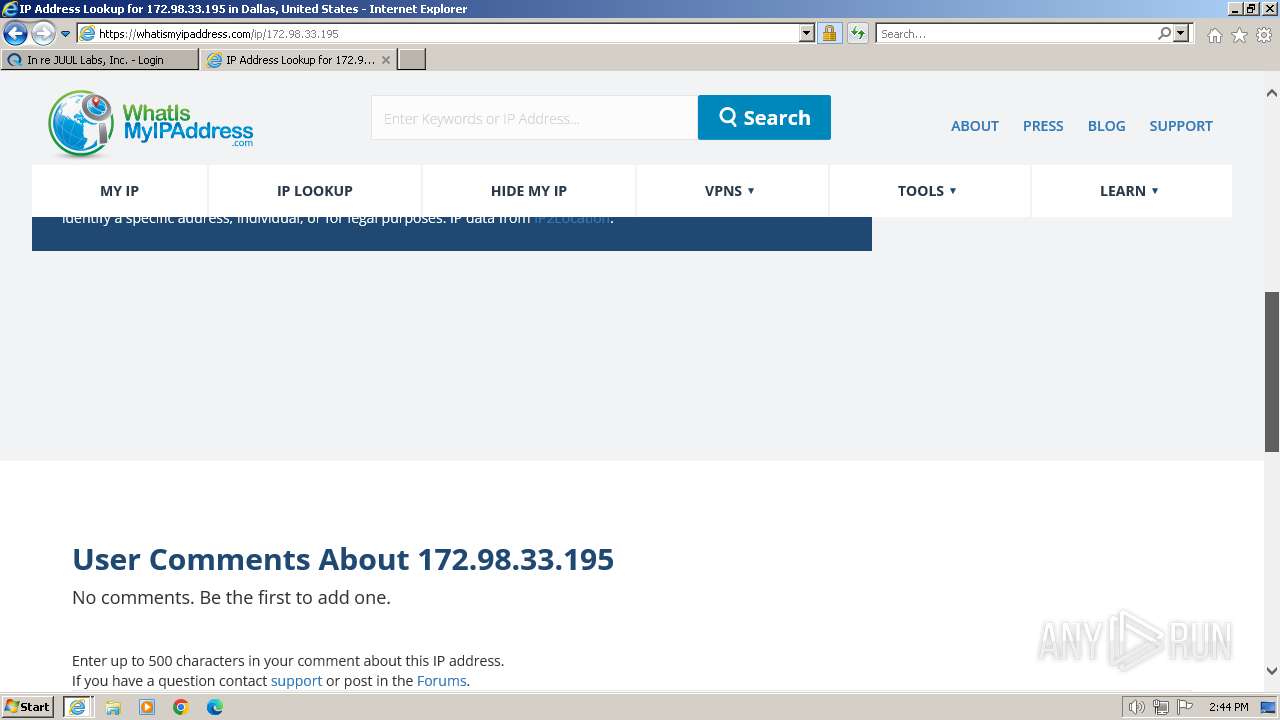
2644 | iexplore.exe | Device Retrieving External IP Address Detected | ET POLICY Known External IP Lookup Service Domain in SNI |
2644 | iexplore.exe | Device Retrieving External IP Address Detected | ET POLICY Known External IP Lookup Service Domain in SNI |
2644 | iexplore.exe | Device Retrieving External IP Address Detected | ET POLICY Known External IP Lookup Service Domain in SNI |
2644 | iexplore.exe | Device Retrieving External IP Address Detected | ET POLICY Known External IP Lookup Service Domain in SNI |
2644 | iexplore.exe | Device Retrieving External IP Address Detected | ET POLICY Known External IP Lookup Service Domain in SNI |
2644 | iexplore.exe | Device Retrieving External IP Address Detected | ET POLICY Known External IP Lookup Service Domain in SNI |
2644 | iexplore.exe | Device Retrieving External IP Address Detected | ET POLICY Known External IP Lookup Service Domain in SNI |
2644 | iexplore.exe | Device Retrieving External IP Address Detected | ET POLICY Known External IP Lookup Service Domain in SNI |
120 | iexplore.exe | Device Retrieving External IP Address Detected | ET POLICY Known External IP Lookup Service Domain in SNI |
120 | iexplore.exe | Device Retrieving External IP Address Detected | ET POLICY Known External IP Lookup Service Domain in SNI |