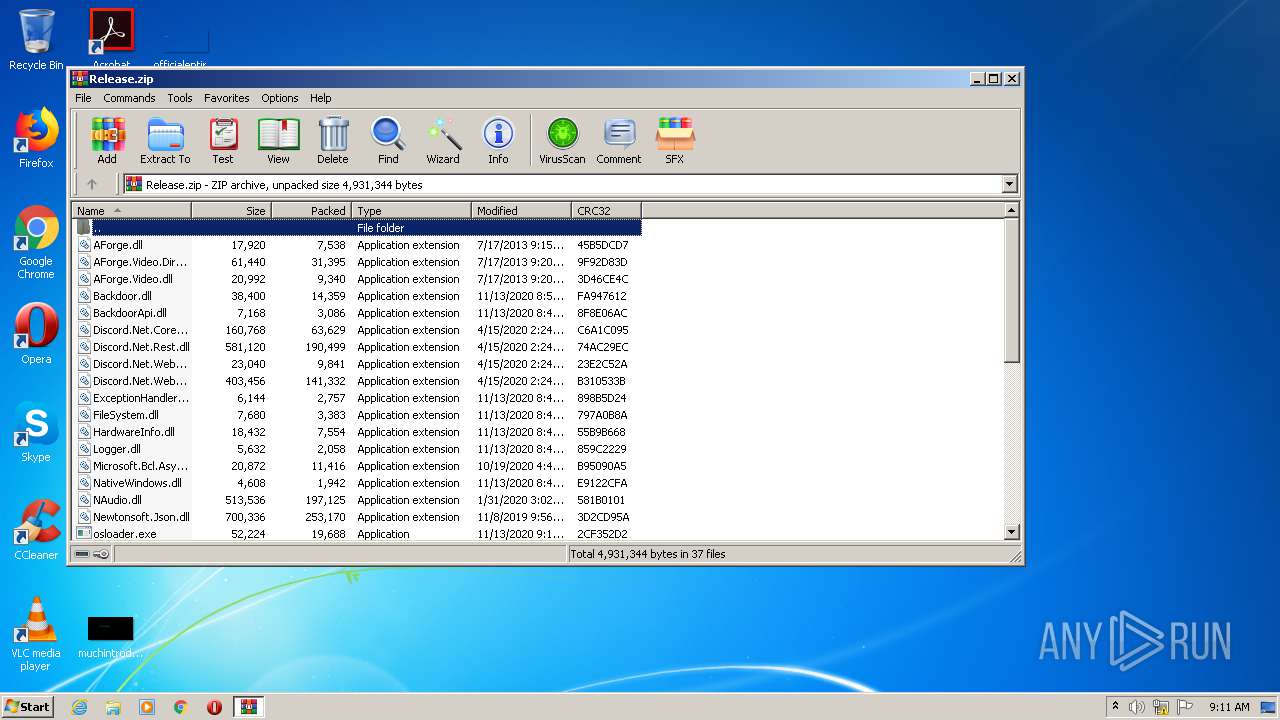
| File name: | Release.zip |
| Full analysis: | https://app.any.run/tasks/f439f71e-99ba-4d24-88c7-c238e8771408 |
| Verdict: | Malicious activity |
| Analysis date: | November 13, 2020, 09:11:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 572BFECCA2F80E4ED5ED4CF9E63FF40C |
| SHA1: | 9C1FD641D9A8FA5A4BF5ECE6C1D2D99B0E72024B |
| SHA256: | 1D500689E37767378EFF0D5B853796C08490B680146D6765E110AC3AC63CDE12 |
| SSDEEP: | 49152:aGGExraE5lXfgbI7/RzZ8PFUu1pAhTLhmI8VSdTOGAhb:aTnE7fgG5zyPl1pCmIh+h |
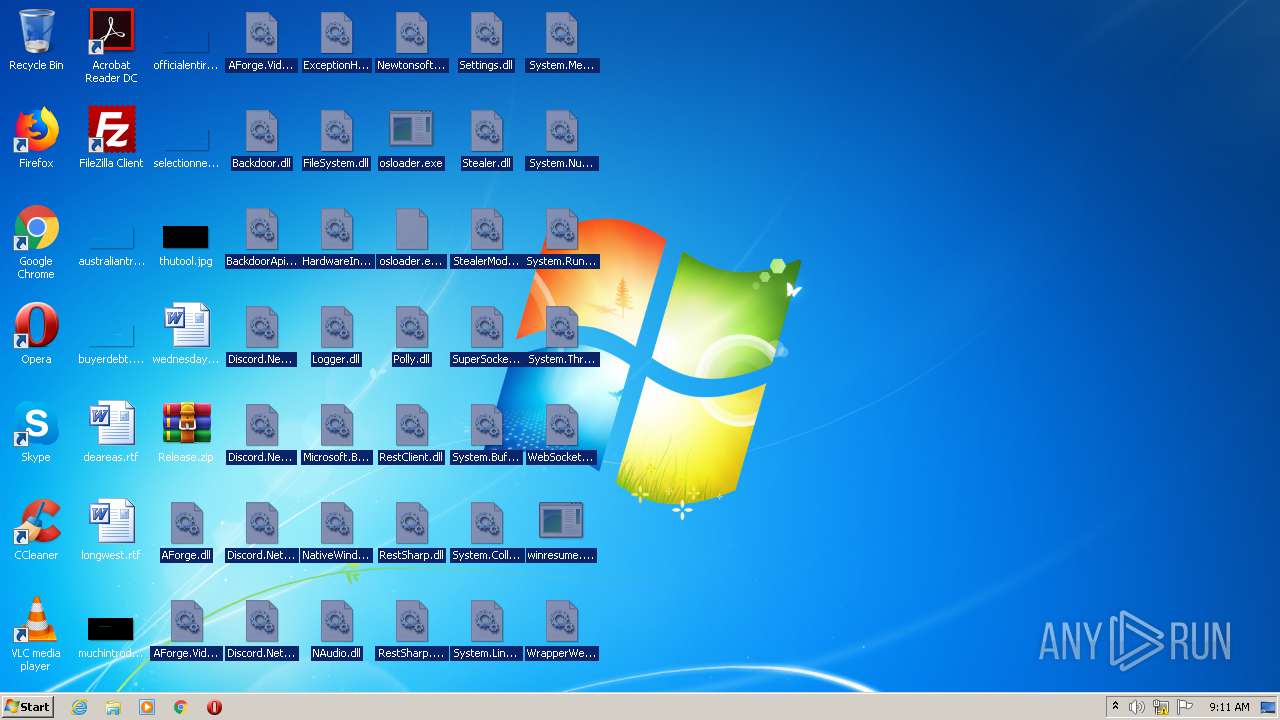
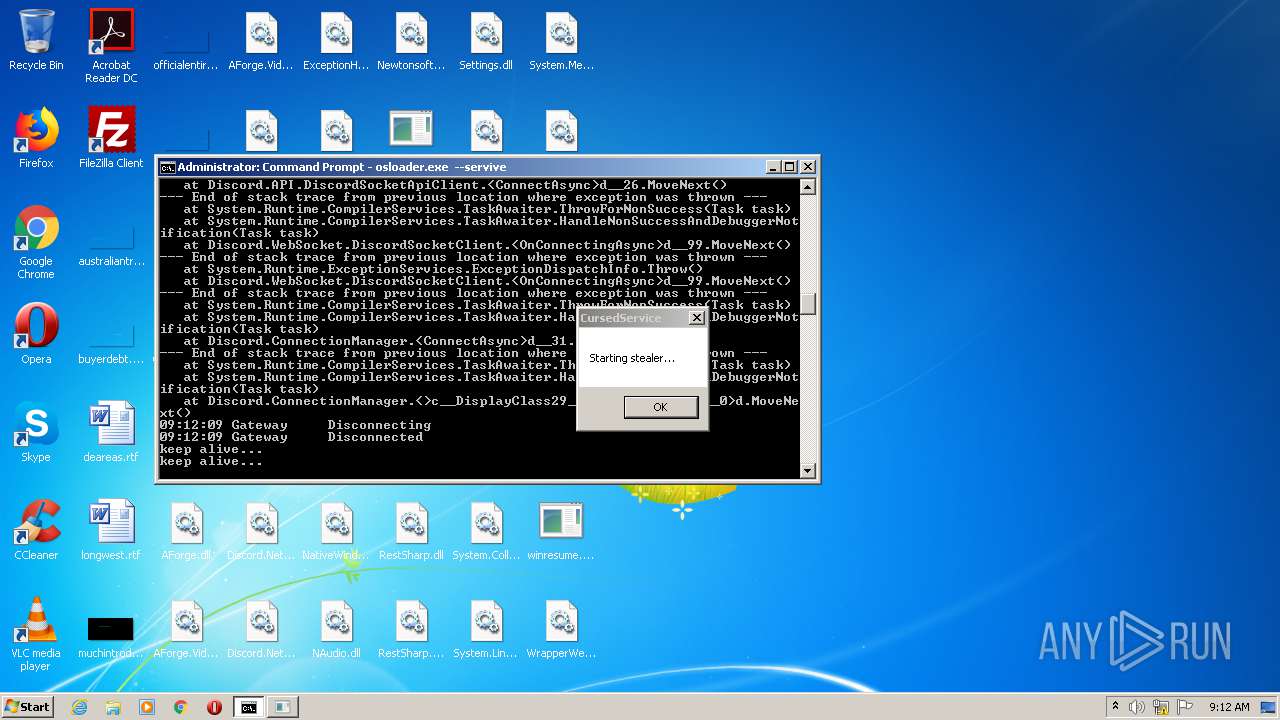
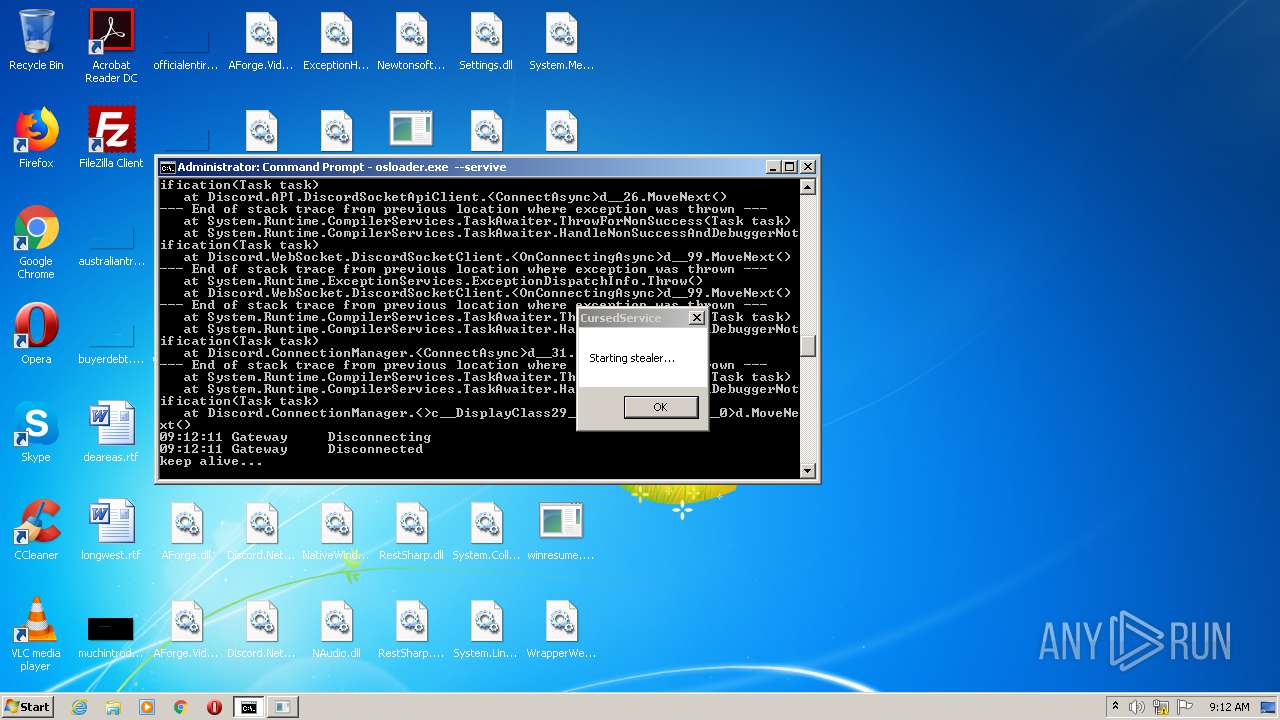
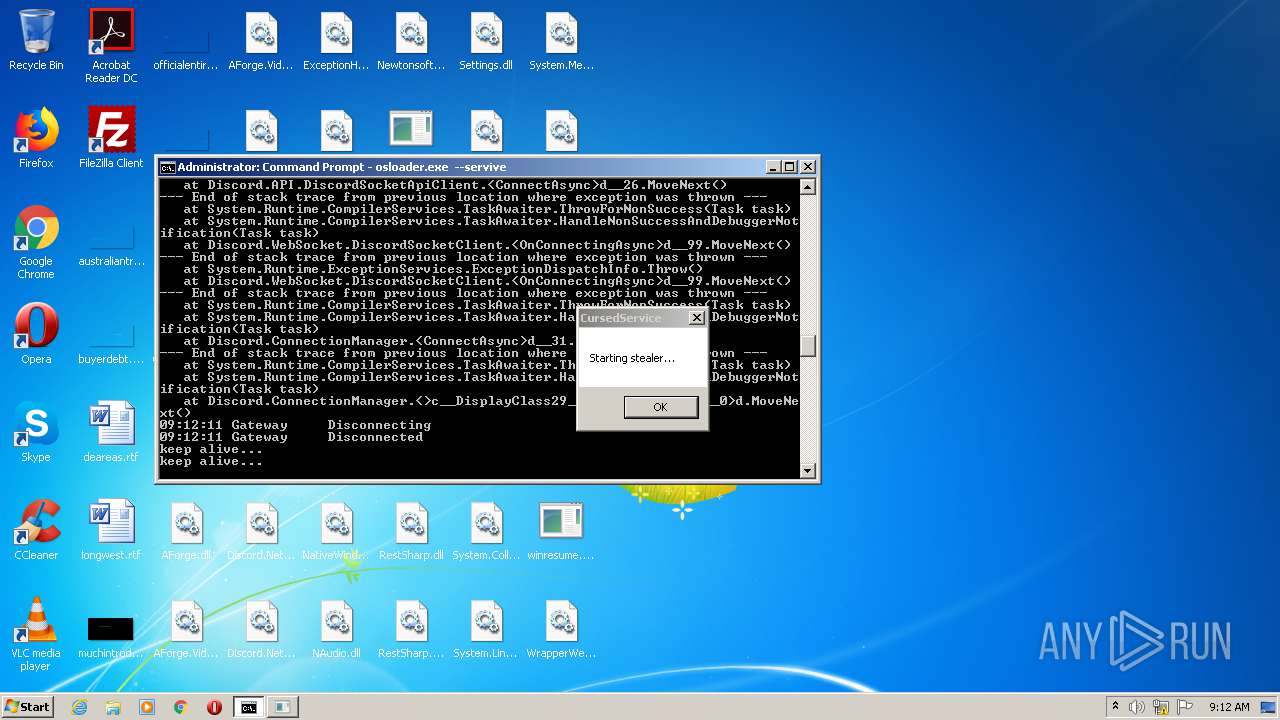
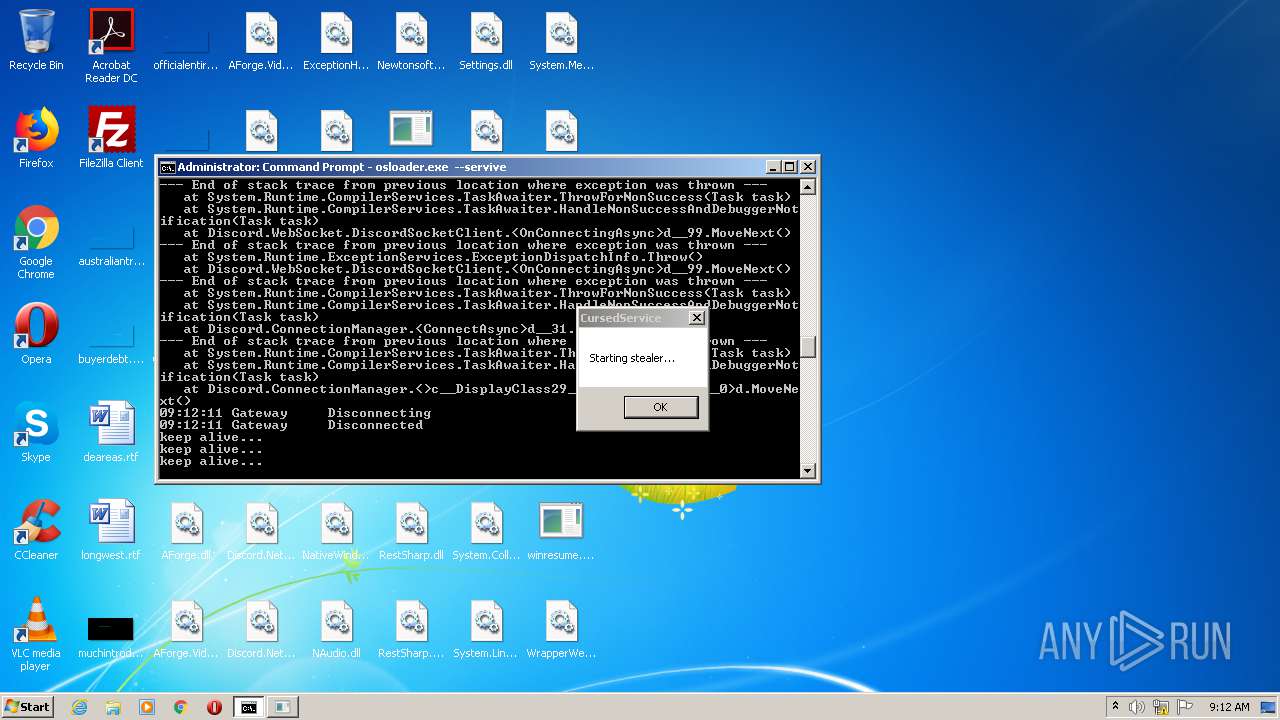
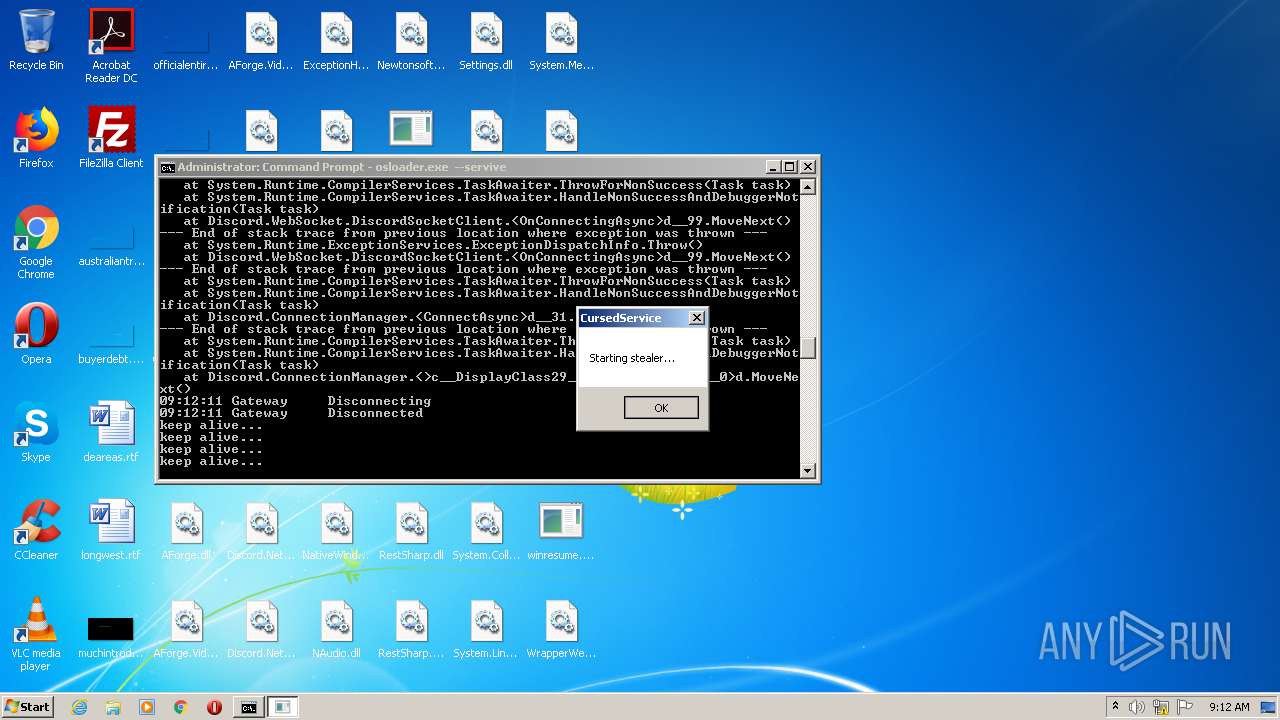
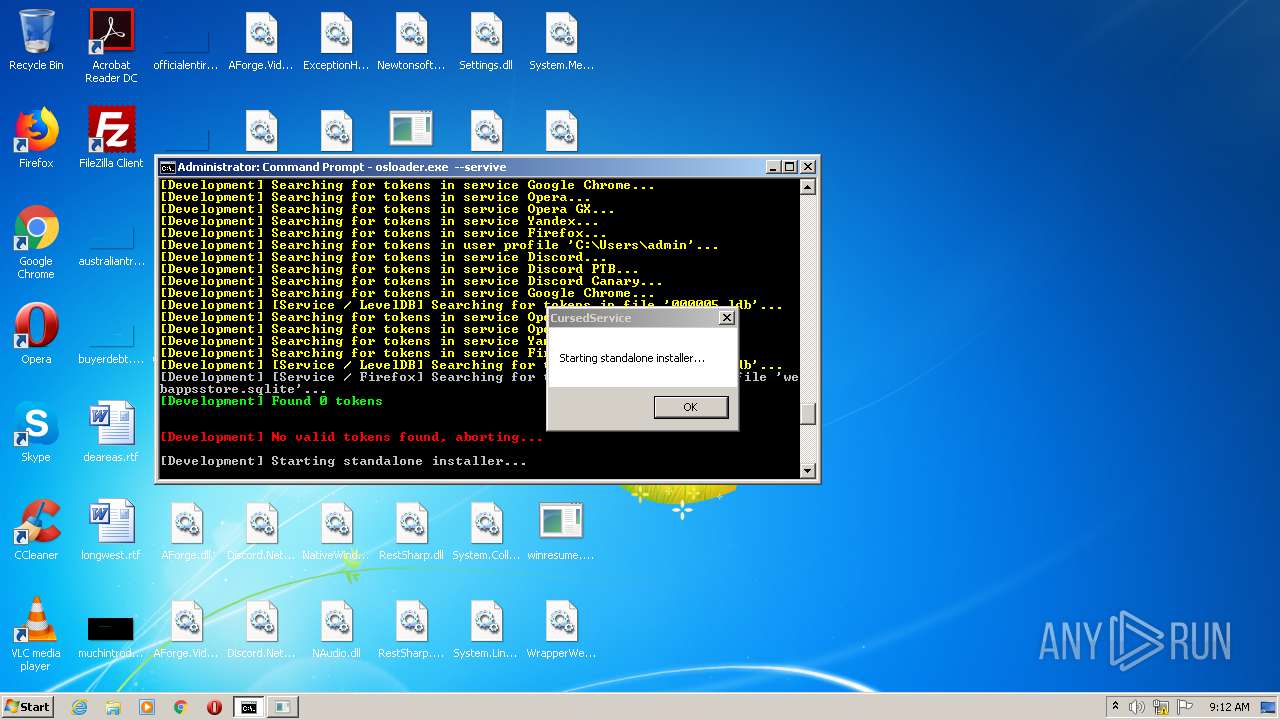
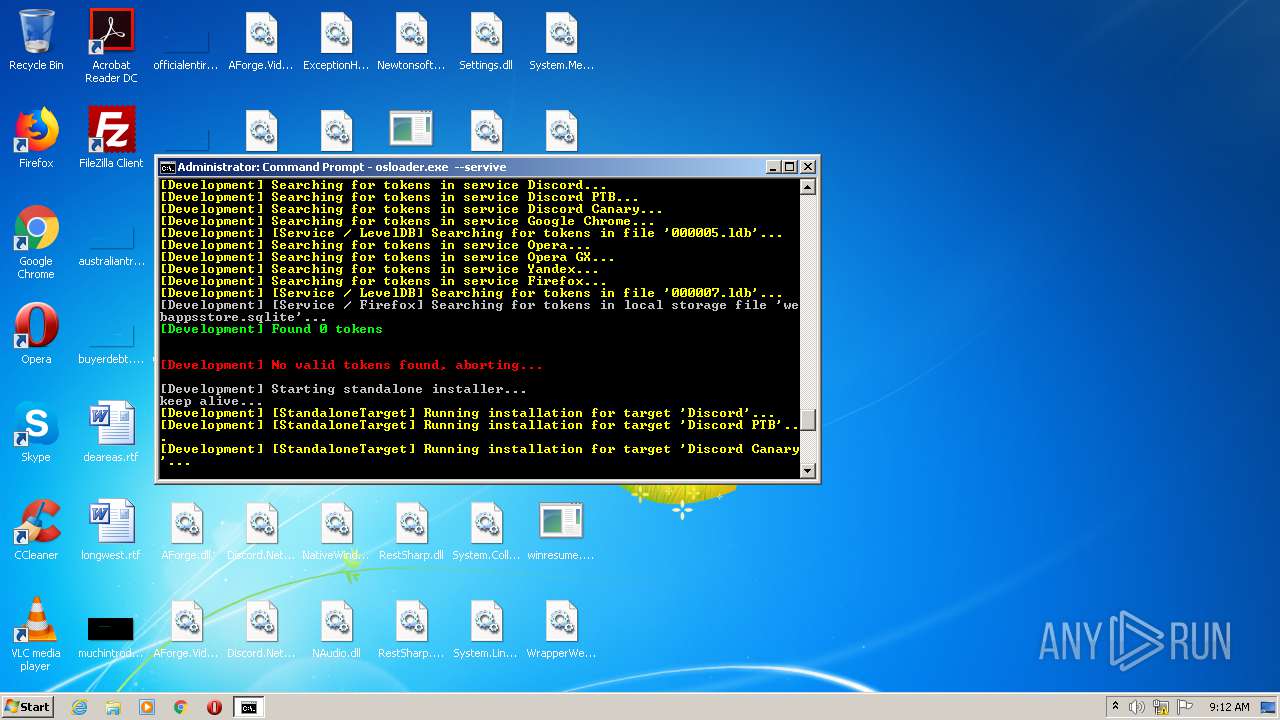
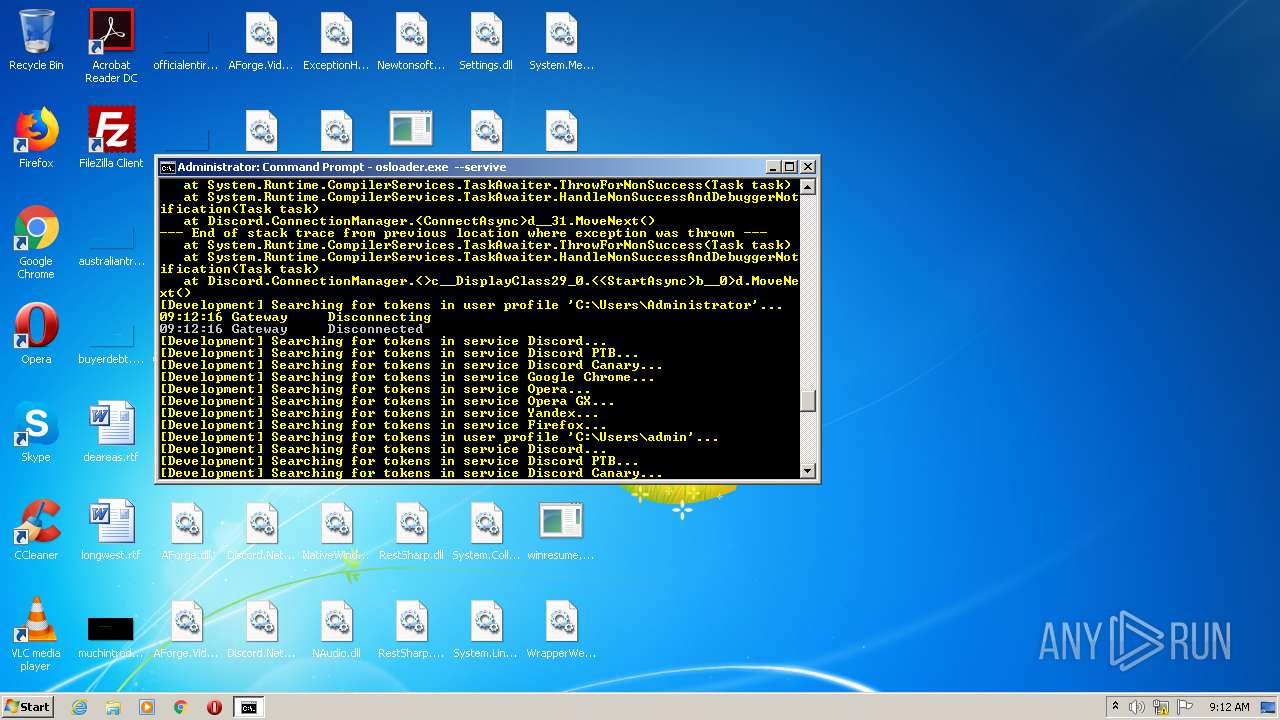
MALICIOUS
Application was dropped or rewritten from another process
- osloader.exe (PID: 2592)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3412)
- osloader.exe (PID: 2592)
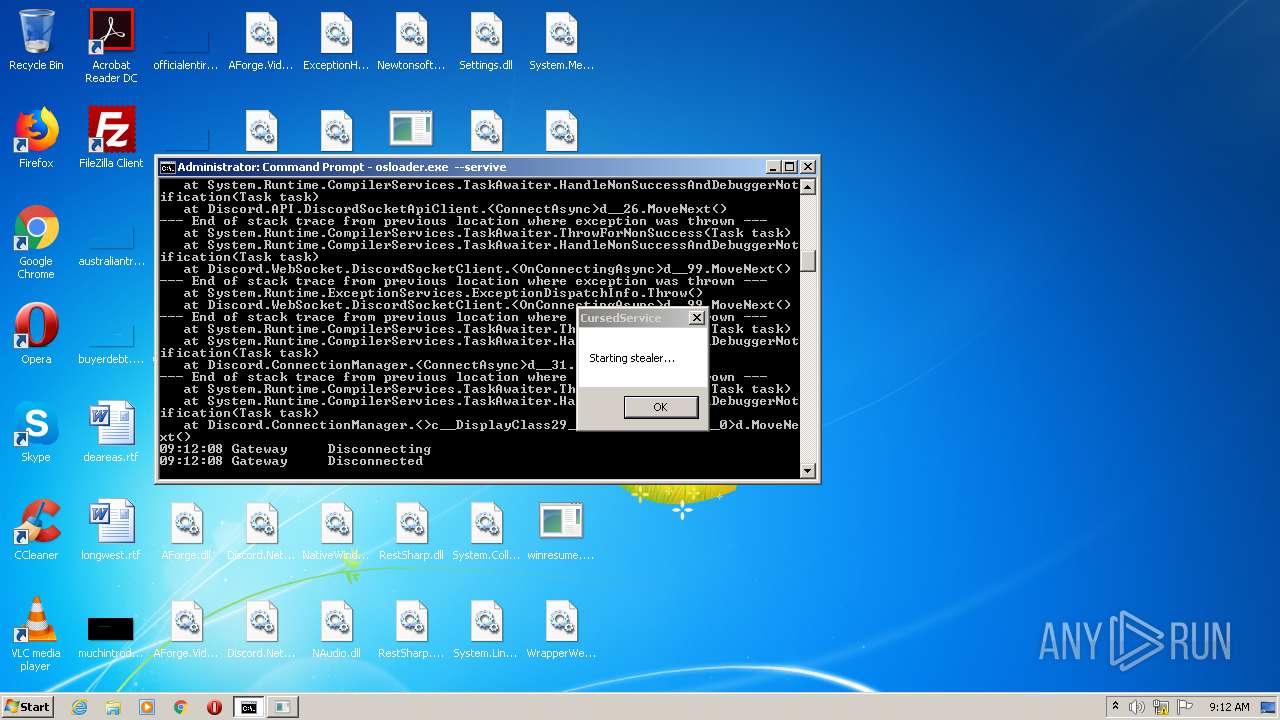
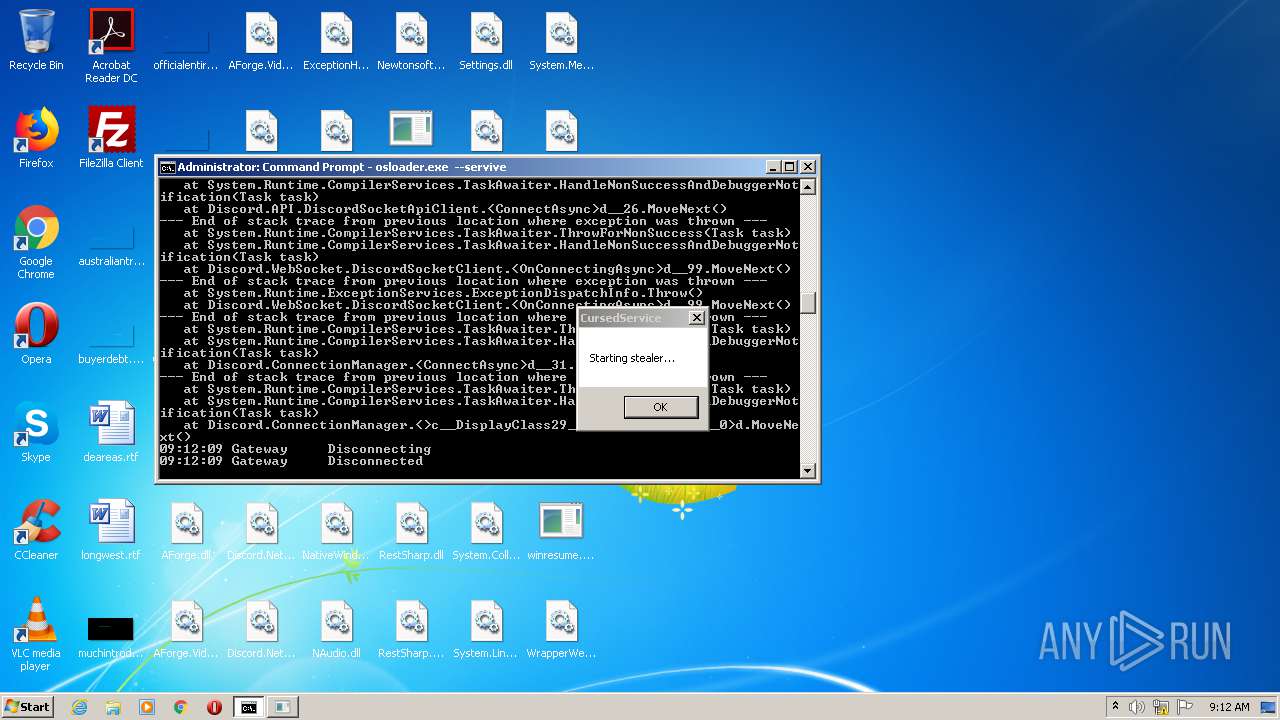
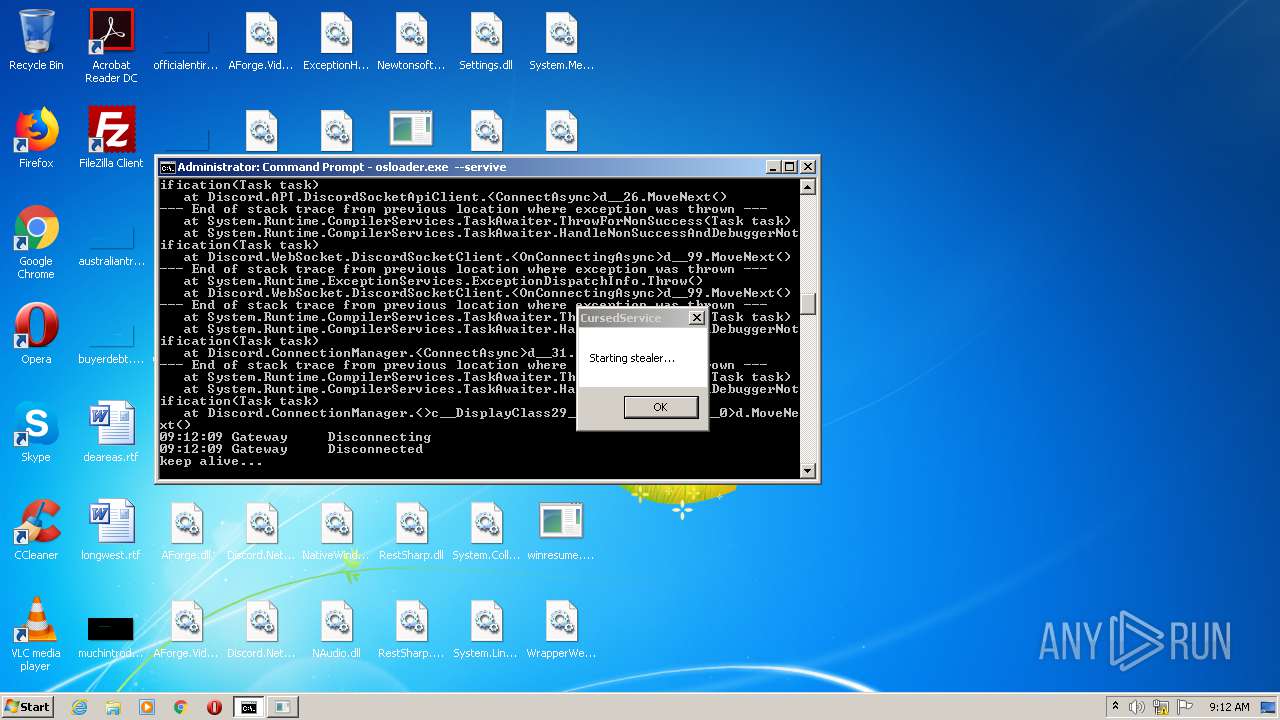
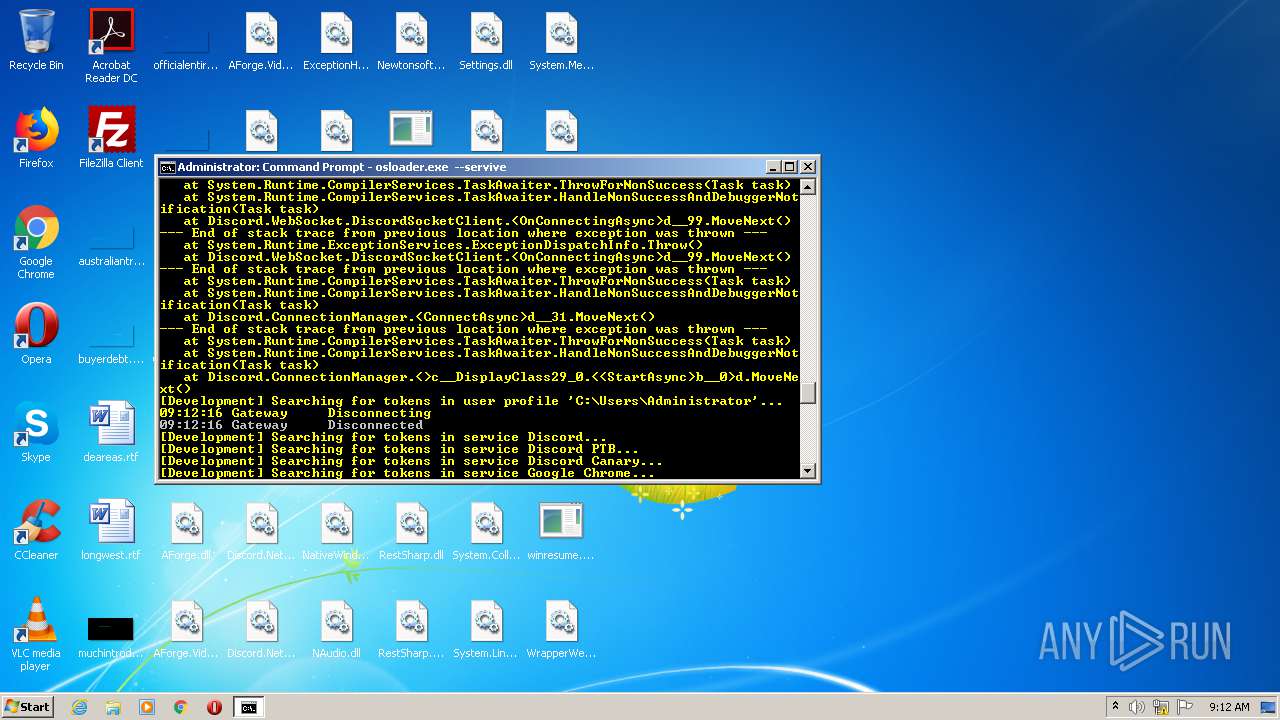
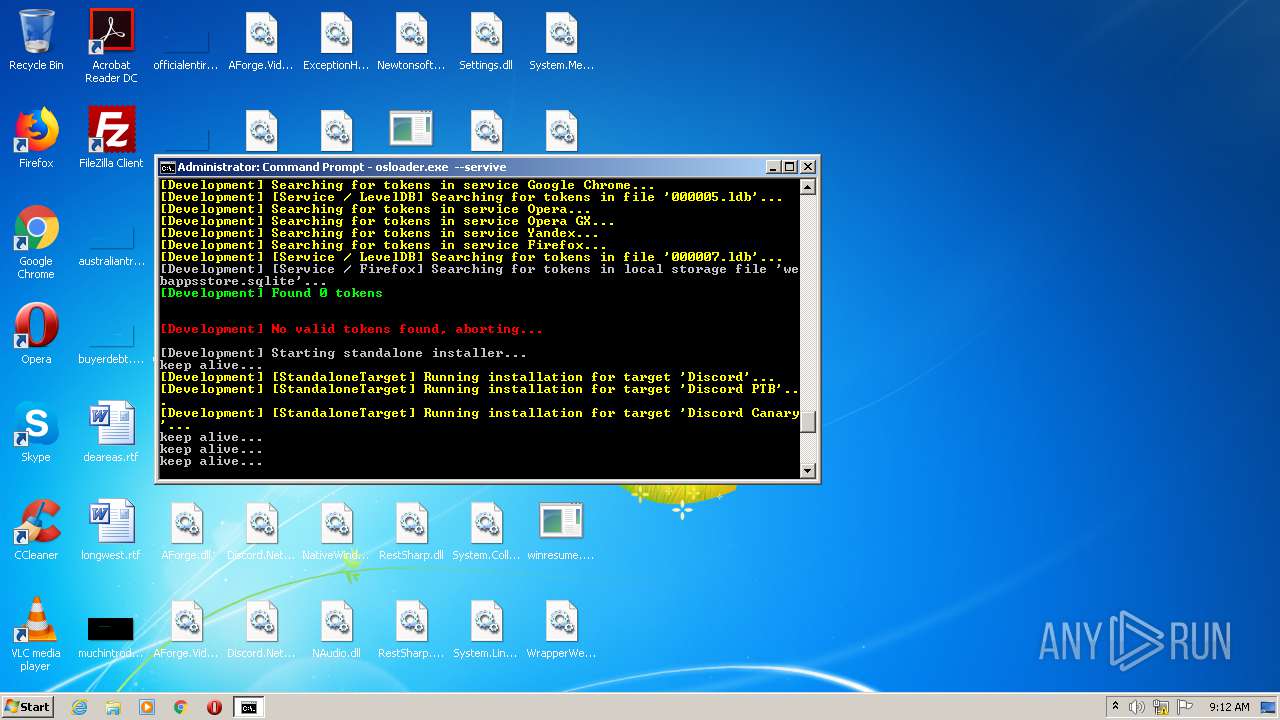
Actions looks like stealing of personal data
- osloader.exe (PID: 2592)
Changes settings of System certificates
- osloader.exe (PID: 2592)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 980)
Reads Environment values
- osloader.exe (PID: 2592)
Creates files in the program directory
- osloader.exe (PID: 2592)
Adds / modifies Windows certificates
- osloader.exe (PID: 2592)
INFO
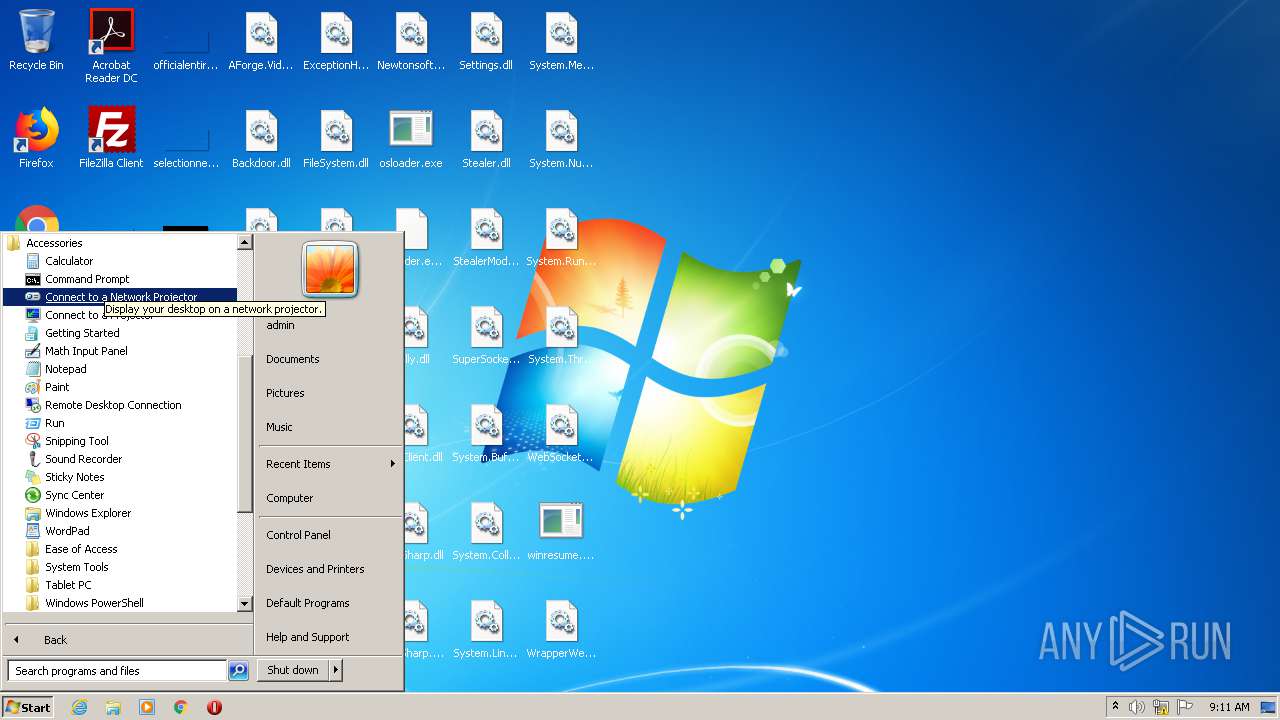
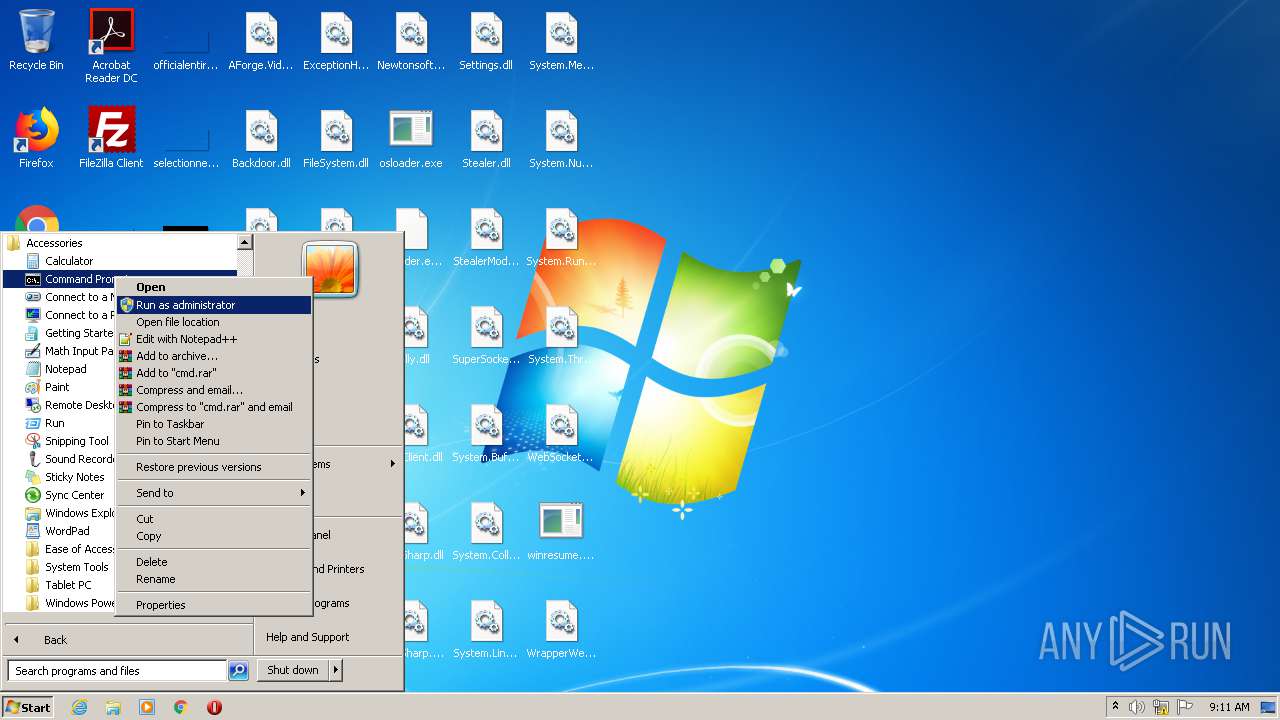
Manual execution by user
- cmd.exe (PID: 3040)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2013:07:17 22:15:08 |
| ZipCRC: | 0x45b5dcd7 |
| ZipCompressedSize: | 7538 |
| ZipUncompressedSize: | 17920 |
| ZipFileName: | AForge.dll |
Total processes
43
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 980 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\Release.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
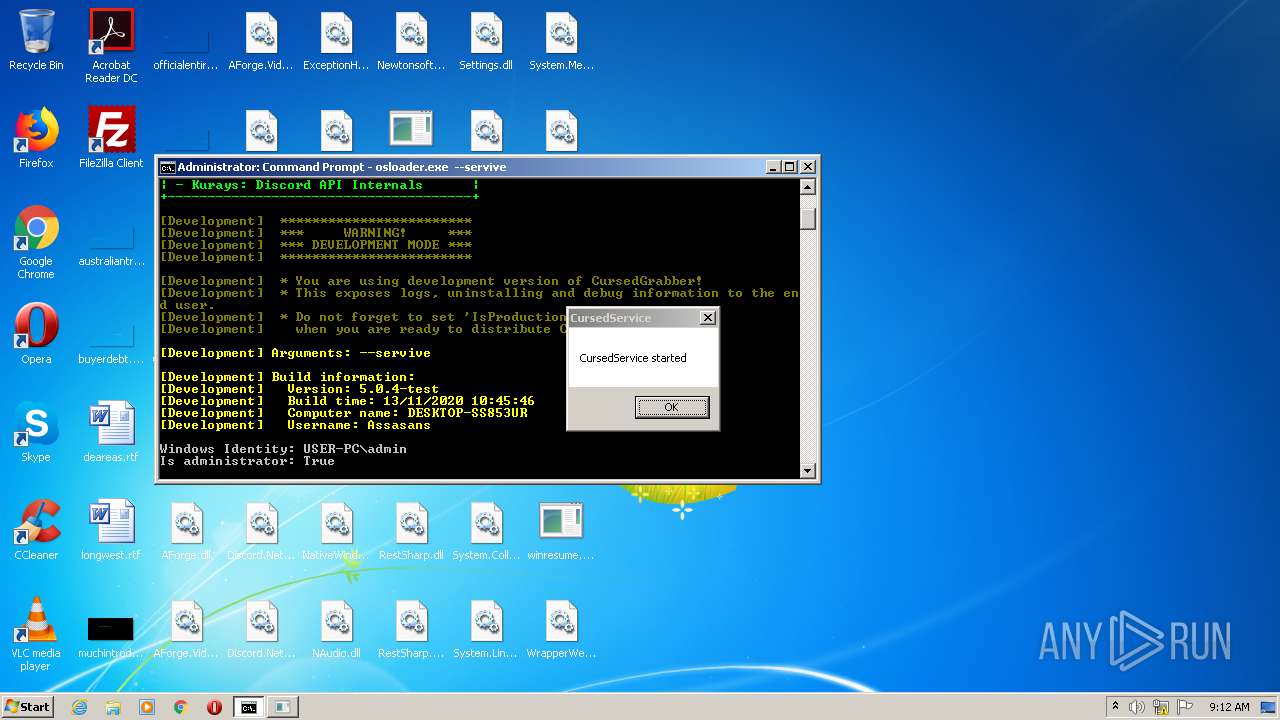
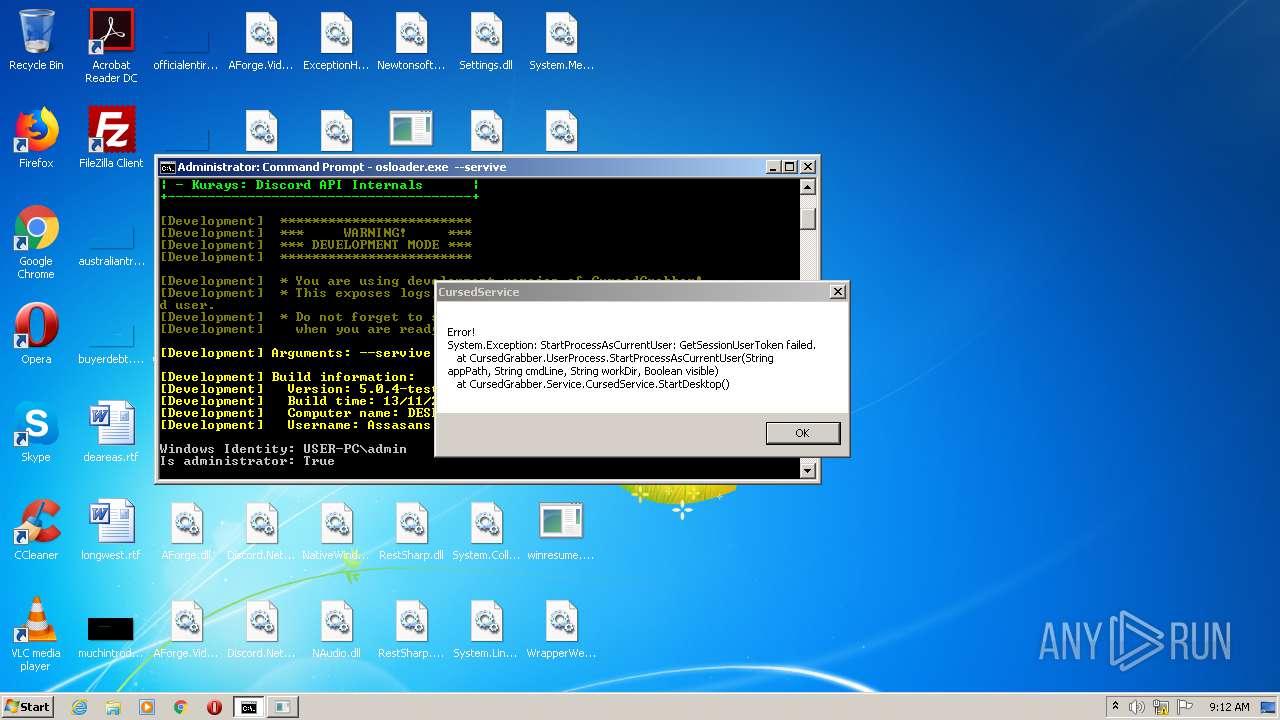
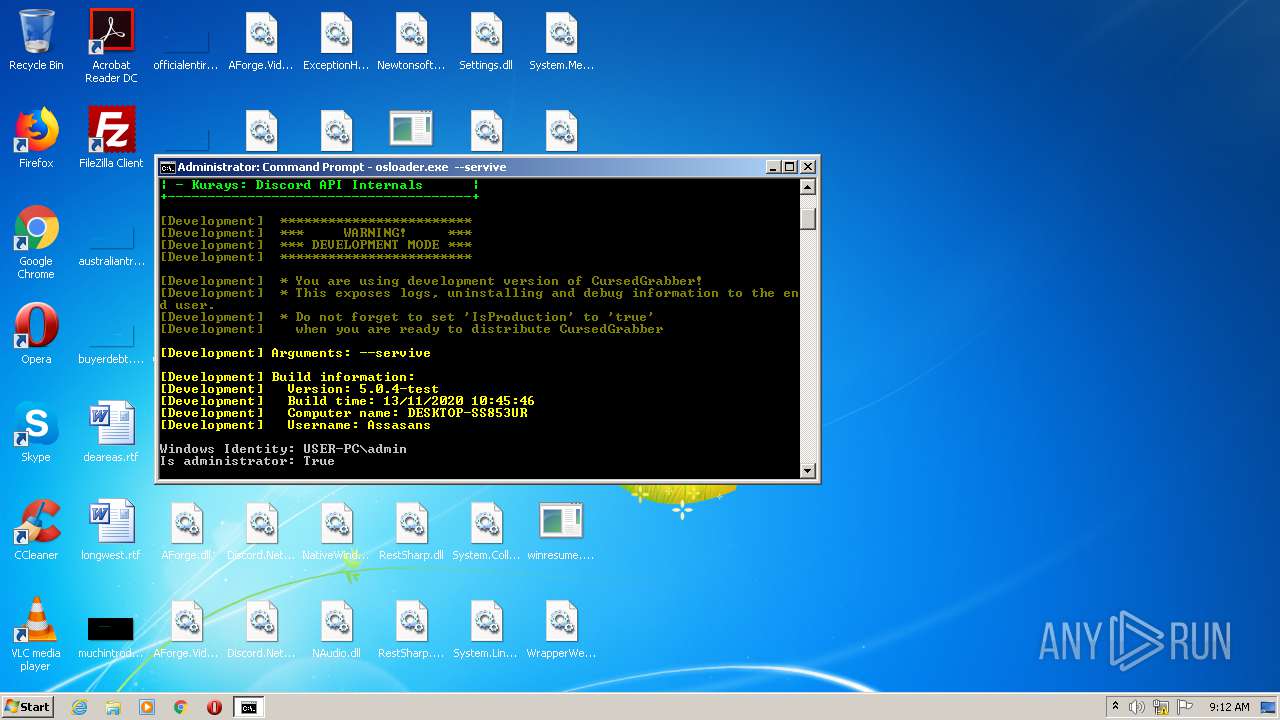
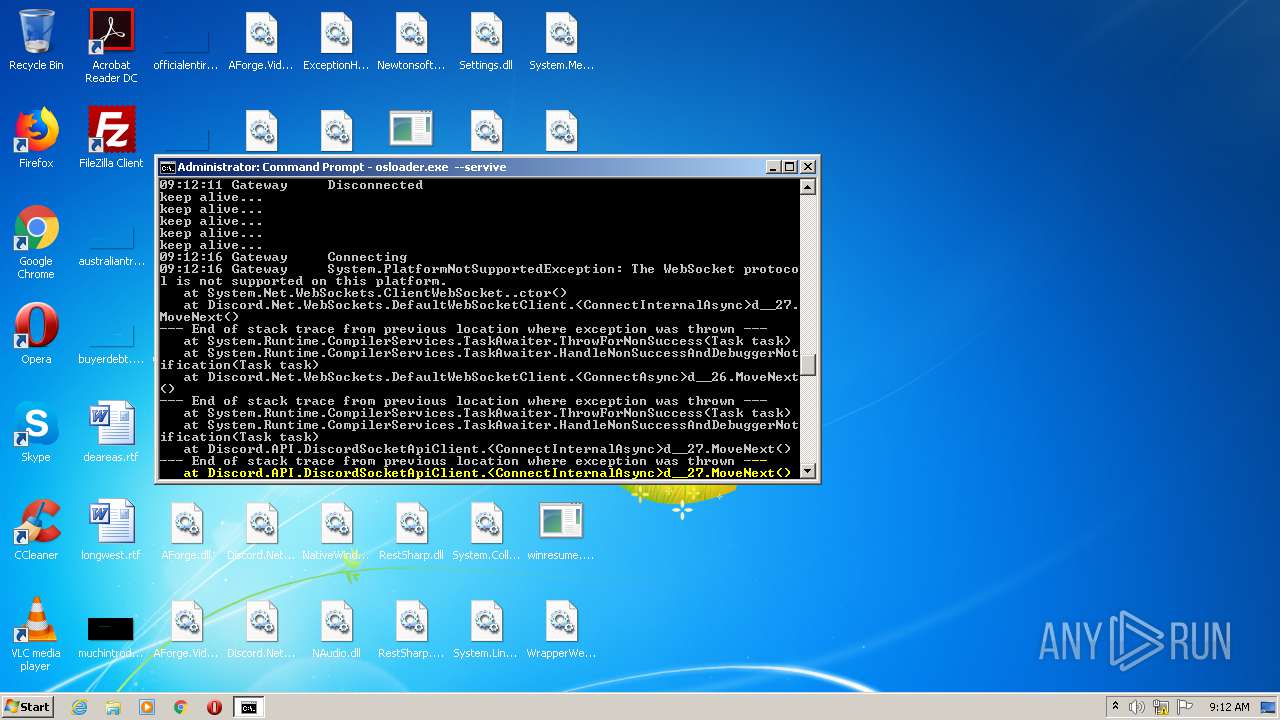
| 2592 | osloader.exe --servive | C:\Users\admin\Desktop\osloader.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: OS Loader Exit code: 0 Version: 10.0.19041.488 Modules
| |||||||||||||||
| 3040 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3412 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe4_ Global\UsGthrCtrlFltPipeMssGthrPipe4 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
401
Read events
358
Write events
43
Delete events
0
Modification events
| (PID) Process: | (980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (980) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Release.zip | |||
| (PID) Process: | (980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\Desktop | |||
Executable files
36
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 980 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa980.2732\BackdoorApi.dll | executable | |
MD5:— | SHA256:— | |||
| 980 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa980.2732\Backdoor.dll | executable | |
MD5:— | SHA256:— | |||
| 980 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa980.2732\ExceptionHandler.dll | executable | |
MD5:— | SHA256:— | |||
| 980 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa980.2732\AForge.dll | executable | |
MD5:02C63F568E598AAD85DD401D7B26E82A | SHA256:966A474060A8ACA70C73BA09D0B6FE2353035961C7107B9003EF879C010FF8DA | |||
| 980 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa980.2732\Discord.Net.Rest.dll | executable | |
MD5:367B8E29F68206531E3E560C0FE1C472 | SHA256:9446FBF4EE74A1A3F234C32F6AF679DBD1CCC1F3C32D9B9A8CF99F698D831001 | |||
| 980 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa980.2732\Discord.Net.Webhook.dll | executable | |
MD5:56C1B31B5D2C1B2B6C2FC40C06B26FEC | SHA256:BAD7A46C1A8372828F1C83E13ED7C3DE05F91436143ED9FD0CE8946AD19FD62B | |||
| 980 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa980.2732\Discord.Net.WebSocket.dll | executable | |
MD5:C9903868D818969A25F048913168937C | SHA256:2084824BCB75E67CF597F7C818FC7A770DA280FDDDD63E4BAEEF436C4147A719 | |||
| 980 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa980.2732\Discord.Net.Core.dll | executable | |
MD5:C897D920FCDAB1F2034A77000B044ADE | SHA256:43780500B3C81C1EEA020F95415181A7E748BA7B4688067434CACE9F7CD0711D | |||
| 980 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa980.2732\FileSystem.dll | executable | |
MD5:— | SHA256:— | |||
| 980 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa980.2732\HardwareInfo.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2592 | osloader.exe | 162.159.129.233:443 | discordapp.com | Cloudflare Inc | — | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
discordapp.com |
| whitelisted |