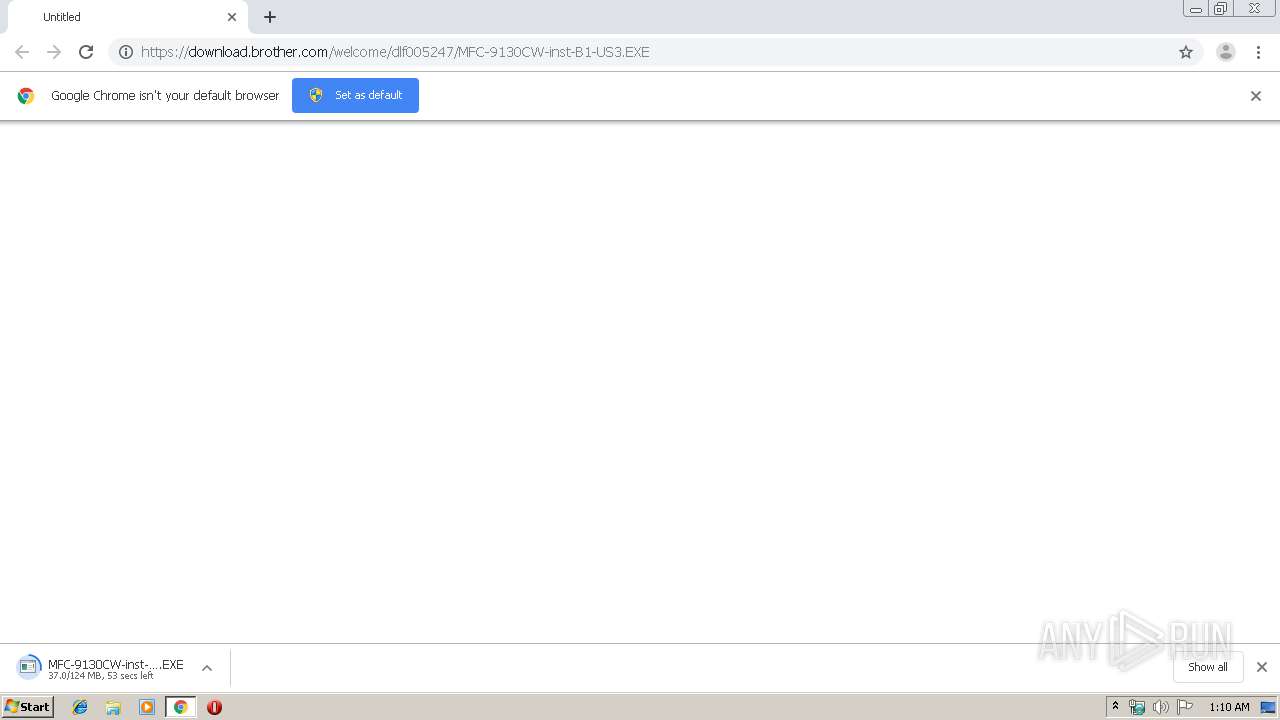
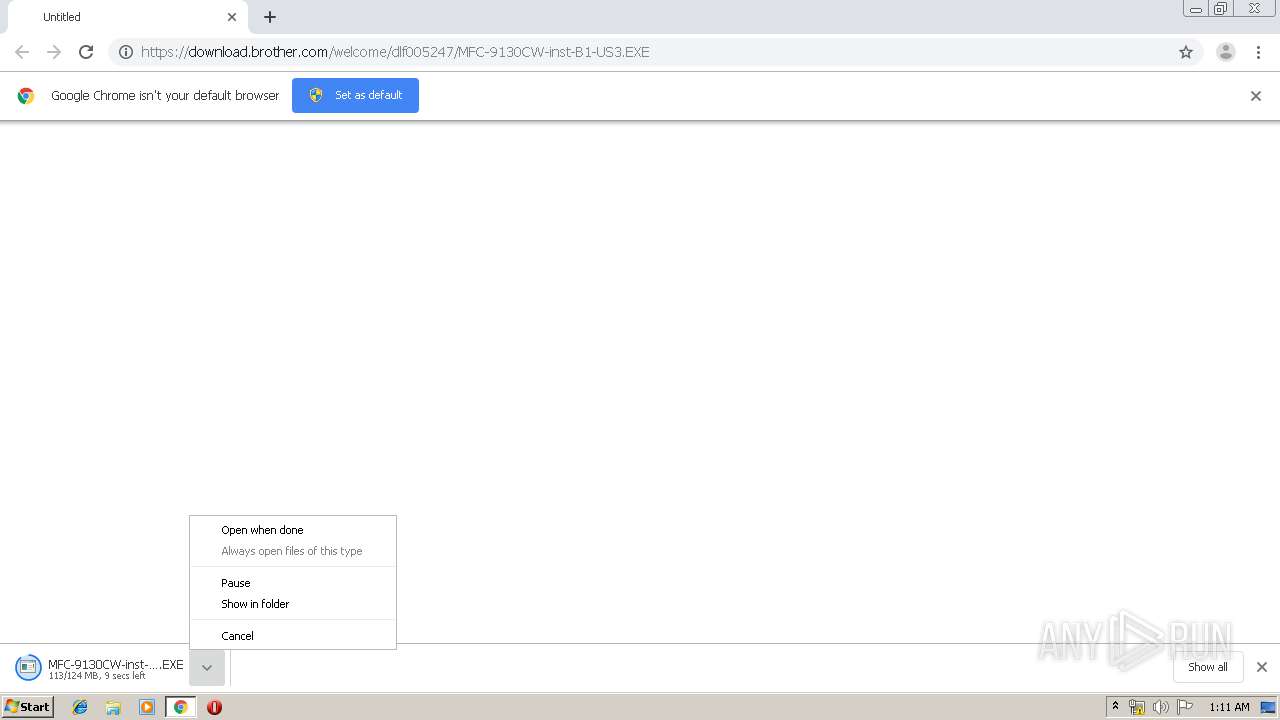
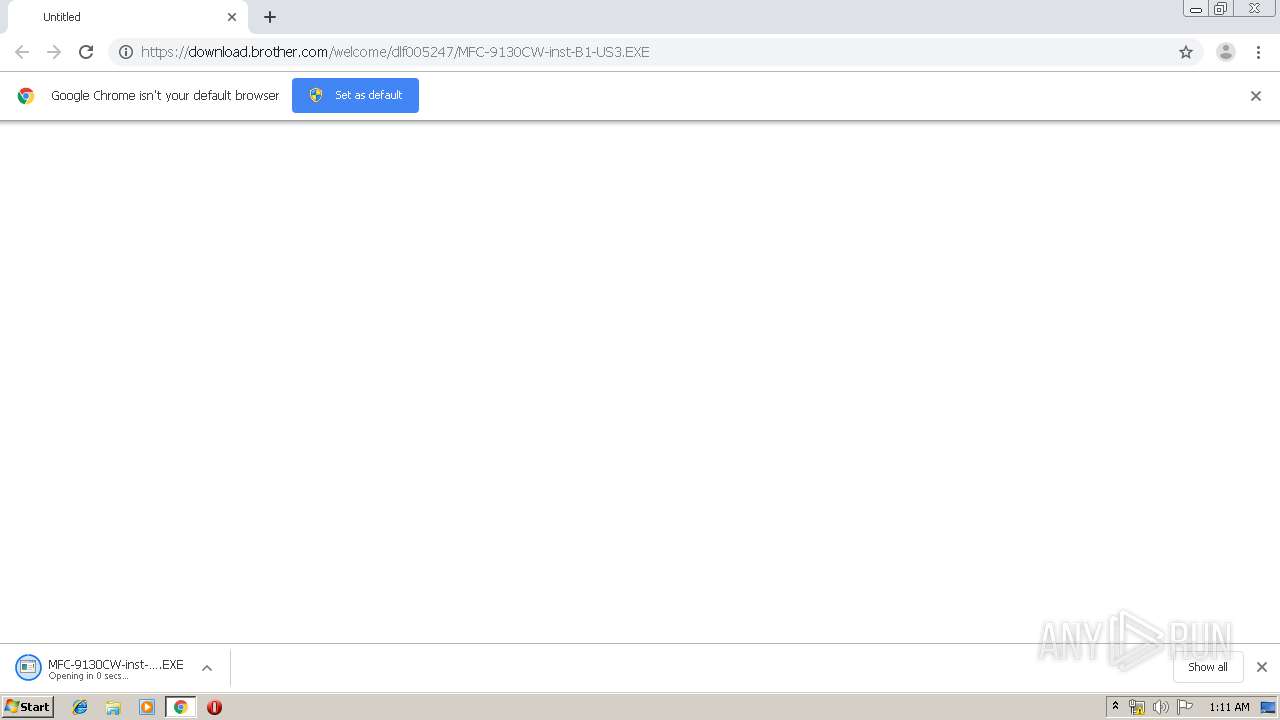
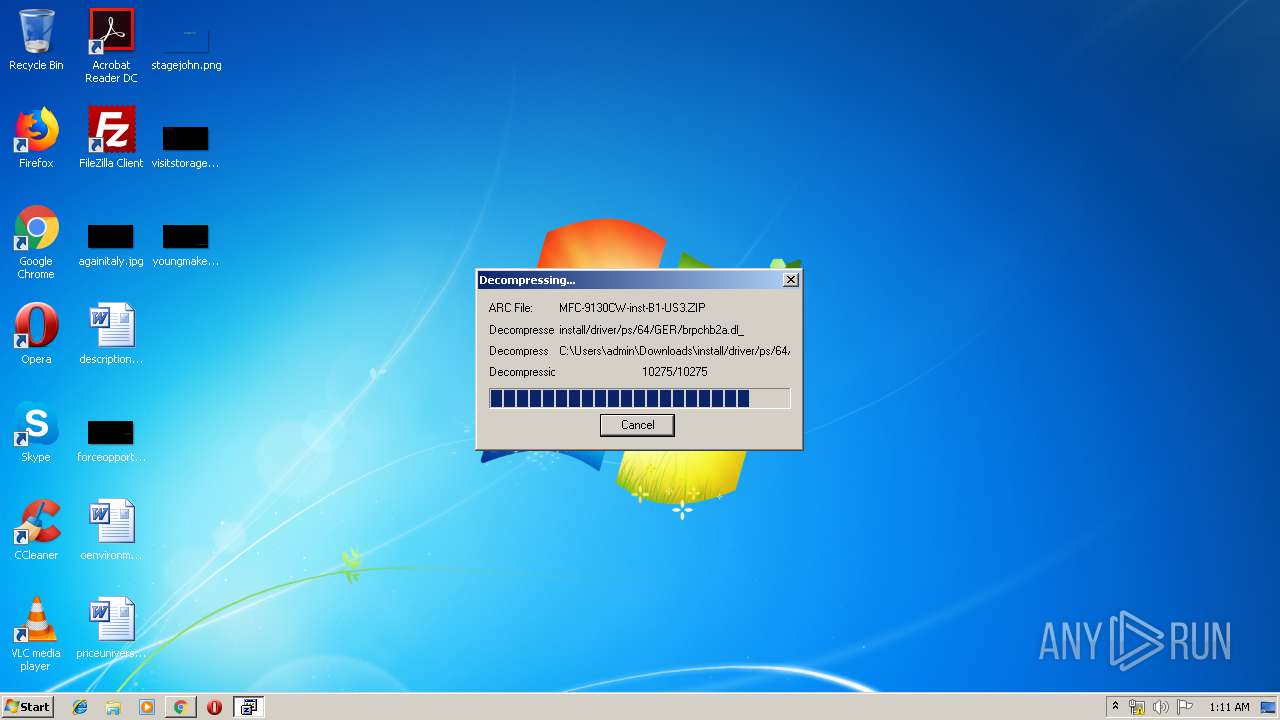
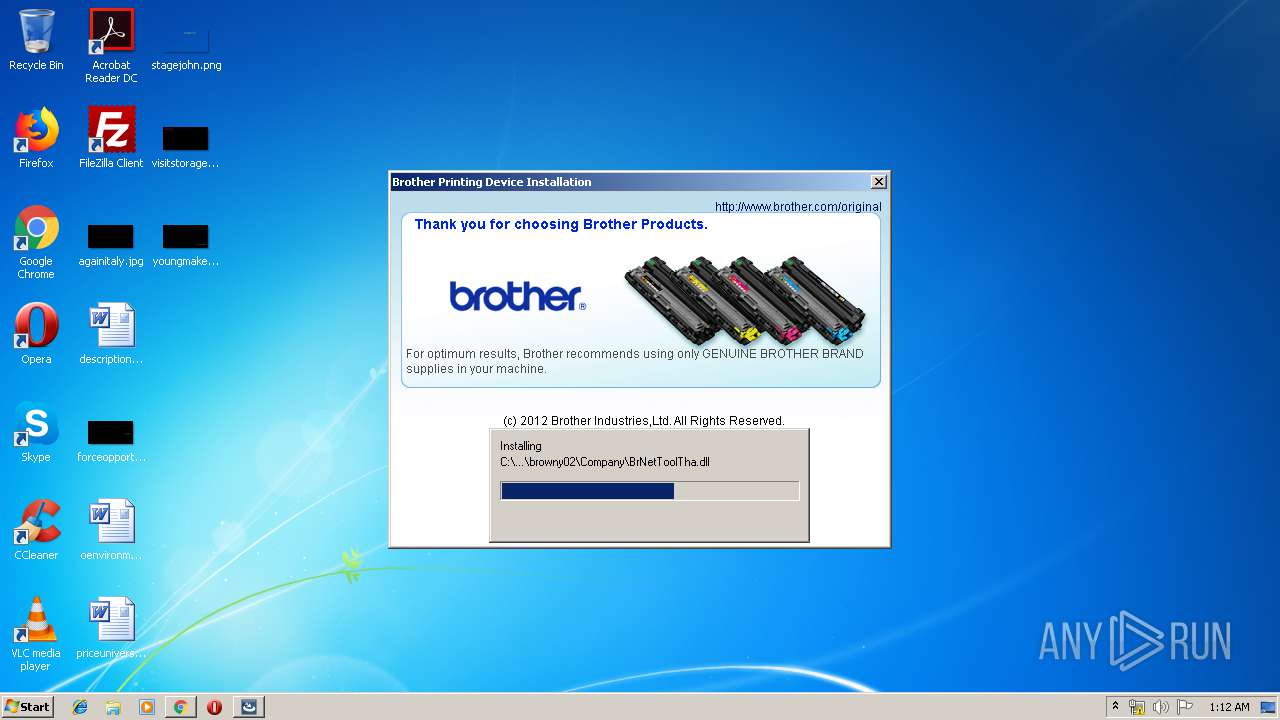
| URL: | https://download.brother.com/welcome/dlf005247/MFC-9130CW-inst-B1-US3.EXE |
| Full analysis: | https://app.any.run/tasks/b7b420cb-9909-4f9a-83da-3cde4c734fa7 |
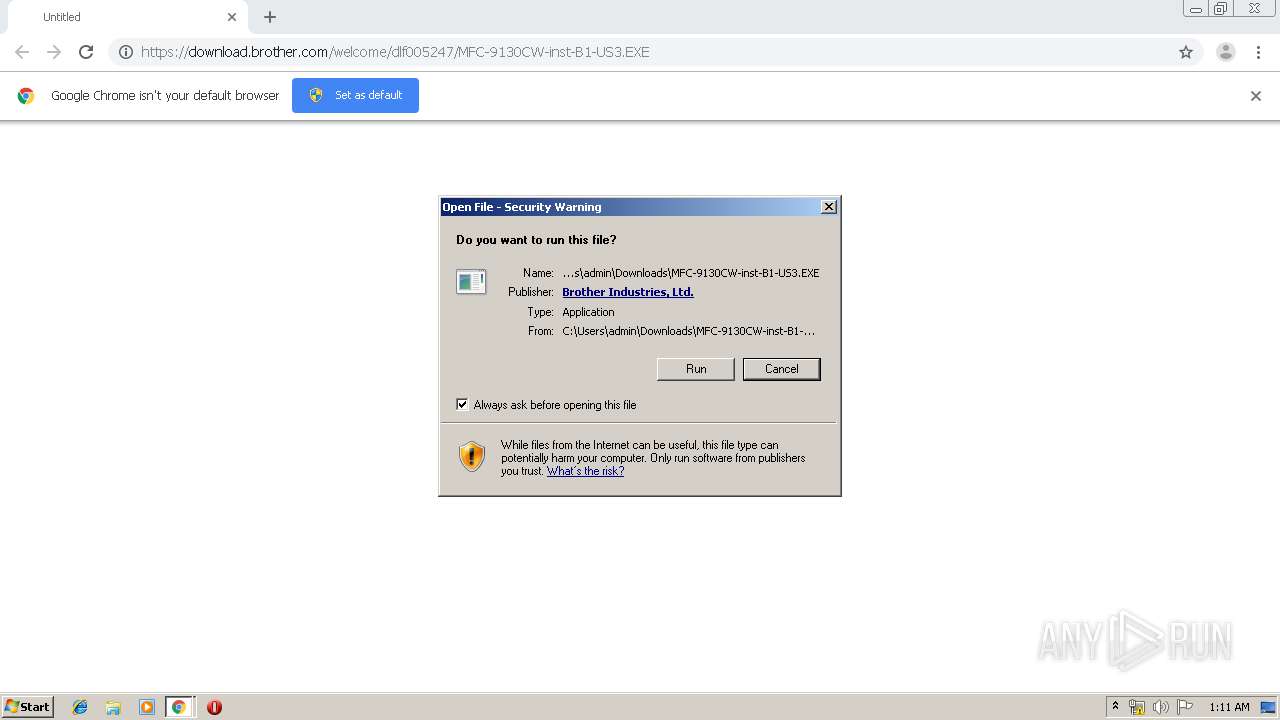
| Verdict: | Malicious activity |
| Analysis date: | September 24, 2019, 00:10:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C2B4CE1EAE96B26083CADF6698ED1398 |
| SHA1: | 1486AFDB30EE44A03478196669E569E0E55D6C4A |
| SHA256: | 1D2F1B93BEEDBCD8B810B7F72205143AB648BD073CA59EB7DB45C9251D37161D |
| SSDEEP: | 3:N8SEl3VMzaCSfiuUNv:2SK36AqJh |
MALICIOUS
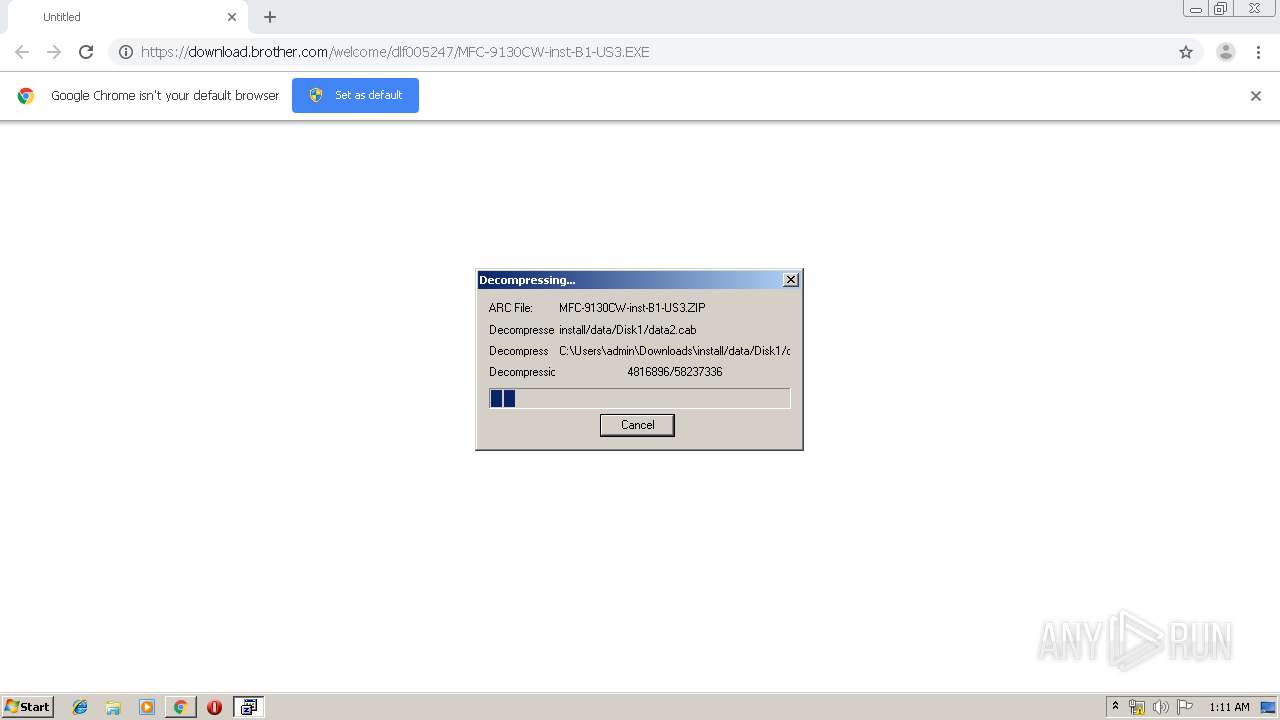
Application was dropped or rewritten from another process
- Setup.exe (PID: 3856)
- Setup.exe (PID: 2816)
- BrLogRx.exe (PID: 1464)
- BrLogRx.exe (PID: 2660)
- BrRemoveYNSvc.exe (PID: 688)
- BrLogRx.exe (PID: 1960)
- InstView.exe (PID: 3064)
- BrLogRx.exe (PID: 2880)
- BrRemPnP.exe (PID: 3540)
- BrDifxapi.exe (PID: 2672)
- BrLogRx.exe (PID: 2796)
- BrLogRx.exe (PID: 700)
- BrDifxapi.exe (PID: 1580)
- BrDifxapi.exe (PID: 3980)
- BrLogRx.exe (PID: 2184)
- BrLogRx.exe (PID: 2512)
- BrDifxapi.exe (PID: 2428)
- BrDifxapi.exe (PID: 2364)
- BrLogRx.exe (PID: 1952)
- BrLogRx.exe (PID: 1260)
- BrDifxapi.exe (PID: 1732)
- BrLogRx.exe (PID: 1796)
- BrLogRx.exe (PID: 3184)
- BrLogRx.exe (PID: 2448)
- BrLogRx.exe (PID: 3080)
- Setup.exe (PID: 2944)
- MFC-9130CW-inst-B1-US3.EXE (PID: 2528)
- BrLogRx.exe (PID: 2968)
- BrDifxapi.exe (PID: 352)
- BrDifxapi.exe (PID: 3508)
- BrLogRx.exe (PID: 2256)
- BrYNSvc.exe (PID: 564)
- BrRemoveYNSvc.exe (PID: 3308)
- BrLogRx.exe (PID: 3588)
- BrDifxapi.exe (PID: 4064)
Loads dropped or rewritten executable
- BrDifxapi.exe (PID: 2672)
- BrRemPnP.exe (PID: 3540)
- BrDifxapi.exe (PID: 1580)
- BrDifxapi.exe (PID: 3980)
- BrDifxapi.exe (PID: 2364)
- BrDifxapi.exe (PID: 2428)
- BrDifxapi.exe (PID: 1732)
- BrDifxapi.exe (PID: 352)
- BrDifxapi.exe (PID: 3508)
- SearchProtocolHost.exe (PID: 1252)
- Setup.exe (PID: 2944)
- BrDifxapi.exe (PID: 4064)
- BrYNSvc.exe (PID: 564)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 3480)
- MFC-9130CW-inst-B1-US3.EXE (PID: 2528)
- Setup.exe (PID: 2944)
- BrDifxapi.exe (PID: 2672)
- BrDifxapi.exe (PID: 3980)
- DrvInst.exe (PID: 2748)
- BrDifxapi.exe (PID: 2428)
- DrvInst.exe (PID: 3916)
- DrvInst.exe (PID: 3716)
Creates files in the program directory
- BrLogRx.exe (PID: 1464)
- Setup.exe (PID: 2944)
Searches for installed software
- Setup.exe (PID: 2944)
- DllHost.exe (PID: 3332)
Executed as Windows Service
- vssvc.exe (PID: 3364)
Executed via COM
- DllHost.exe (PID: 3332)
- DrvInst.exe (PID: 2660)
- DrvInst.exe (PID: 2748)
- DrvInst.exe (PID: 3916)
- DrvInst.exe (PID: 3716)
- DrvInst.exe (PID: 1492)
- DrvInst.exe (PID: 2572)
- DllHost.exe (PID: 3548)
- DrvInst.exe (PID: 1948)
Creates files in the Windows directory
- Setup.exe (PID: 2944)
- DrvInst.exe (PID: 2748)
- DrvInst.exe (PID: 3916)
- DrvInst.exe (PID: 3716)
Creates files in the driver directory
- DrvInst.exe (PID: 2748)
- DrvInst.exe (PID: 3916)
- DrvInst.exe (PID: 3716)
Removes files from Windows directory
- DrvInst.exe (PID: 3916)
- DrvInst.exe (PID: 2748)
- DrvInst.exe (PID: 3716)
- DrvInst.exe (PID: 1492)
- Setup.exe (PID: 2944)
- DrvInst.exe (PID: 2572)
- DrvInst.exe (PID: 1948)
Creates a software uninstall entry
- Setup.exe (PID: 2944)
Creates files in the user directory
- Setup.exe (PID: 2944)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3480)
INFO
Reads the hosts file
- chrome.exe (PID: 3480)
- chrome.exe (PID: 2152)
Application launched itself
- chrome.exe (PID: 3480)
Reads Internet Cache Settings
- chrome.exe (PID: 3480)
Dropped object may contain Bitcoin addresses
- Setup.exe (PID: 2944)
- BrDifxapi.exe (PID: 2428)
- DrvInst.exe (PID: 3716)
- MFC-9130CW-inst-B1-US3.EXE (PID: 2528)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3364)
Reads settings of System Certificates
- DrvInst.exe (PID: 2748)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
107
Monitored processes
67
Malicious processes
14
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | C:\Users\admin\AppData\Local\Temp\{39F0D72C-325E-4E42-AFEF-3D0010CE7DA8}\{E98A9C92-E767-475B-8BC6-8780A86DDC72}\BrDifxapi.exe -u "C:\Windows\System32\DriverStore\FileRepository\brimc12a.inf_x86_neutral_8ef76005d658f85f\brimc12a.inf" 0 | C:\Users\admin\AppData\Local\Temp\{39F0D72C-325E-4E42-AFEF-3D0010CE7DA8}\{E98A9C92-E767-475B-8BC6-8780A86DDC72}\BrDifxapi.exe | — | Setup.exe | |||||||||||
User: admin Integrity Level: HIGH Description: BrDifxapi Exit code: 0 Version: 1, 0, 2, 2 Modules
| |||||||||||||||
| 564 | "C:\Program Files\Browny02\BrYNSvc.exe" /Service | C:\Program Files\Browny02\BrYNSvc.exe | — | BrRemoveYNSvc.exe | |||||||||||
User: admin Company: Brother Industries, Ltd. Integrity Level: HIGH Description: BrYNCSvc Exit code: 0 Version: 1.5.2.0 Modules
| |||||||||||||||
| 688 | C:\Users\admin\AppData\Local\Temp\{39F0D72C-325E-4E42-AFEF-3D0010CE7DA8}\{E98A9C92-E767-475B-8BC6-8780A86DDC72}\BrRemoveYNSvc.exe | C:\Users\admin\AppData\Local\Temp\{39F0D72C-325E-4E42-AFEF-3D0010CE7DA8}\{E98A9C92-E767-475B-8BC6-8780A86DDC72}\BrRemoveYNSvc.exe | — | Setup.exe | |||||||||||
User: admin Integrity Level: HIGH Description: BrRemove アプリケーション Exit code: 0 Version: 1, 0, 3, 0 Modules
| |||||||||||||||
| 700 | "C:\Users\admin\AppData\Local\Temp\{39F0D72C-325E-4E42-AFEF-3D0010CE7DA8}\{E98A9C92-E767-475B-8BC6-8780A86DDC72}\BrLogRx.exe" /function=REPNP /path="C:\Users\admin\AppData\Local\Temp\{39F0D72C-325E-4E42-AFEF-3D0010CE7DA8}\{E98A9C92-E767-475B-8BC6-8780A86DDC72}\BrDbgOut.INI" | C:\Users\admin\AppData\Local\Temp\{39F0D72C-325E-4E42-AFEF-3D0010CE7DA8}\{E98A9C92-E767-475B-8BC6-8780A86DDC72}\BrLogRx.exe | — | BrRemPnP.exe | |||||||||||
User: admin Company: Brother Industries, Ltd. Integrity Level: HIGH Description: Brother MFC Windows Software Standard Debug Log Receive Process Exit code: 0 Version: 1, 1, 0, 0 Modules
| |||||||||||||||
| 1076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,12021569664978960427,18268528215365442765,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1523572262340497519 --mojo-platform-channel-handle=3160 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,12021569664978960427,18268528215365442765,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14123144646542207338 --mojo-platform-channel-handle=3876 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1204 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,12021569664978960427,18268528215365442765,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5624917416118019556 --mojo-platform-channel-handle=488 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1252 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe4_ Global\UsGthrCtrlFltPipeMssGthrPipe4 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1260 | "C:\Users\admin\AppData\Local\Temp\{39F0D72C-325E-4E42-AFEF-3D0010CE7DA8}\{E98A9C92-E767-475B-8BC6-8780A86DDC72}\BrLogRx.exe" /function=DIFX /path="C:\Users\admin\AppData\Local\Temp\{39F0D72C-325E-4E42-AFEF-3D0010CE7DA8}\{E98A9C92-E767-475B-8BC6-8780A86DDC72}\BrDbgOut.INI" | C:\Users\admin\AppData\Local\Temp\{39F0D72C-325E-4E42-AFEF-3D0010CE7DA8}\{E98A9C92-E767-475B-8BC6-8780A86DDC72}\BrLogRx.exe | — | BrDifxapi.exe | |||||||||||
User: admin Company: Brother Industries, Ltd. Integrity Level: HIGH Description: Brother MFC Windows Software Standard Debug Log Receive Process Exit code: 0 Version: 1, 1, 0, 0 Modules
| |||||||||||||||
| 1260 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,12021569664978960427,18268528215365442765,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4871346481250810895 --mojo-platform-channel-handle=3960 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
4 374
Read events
1 833
Write events
1 935
Delete events
606
Modification events
| (PID) Process: | (3480) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3480) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3480) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3480) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3480) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3092) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3480-13213757420205625 |
Value: 259 | |||
| (PID) Process: | (3480) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3480) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3480) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3480) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
974
Suspicious files
153
Text files
1 117
Unknown types
2 179
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\a4901556-960f-4a5a-afe9-84a9156a7885.tmp | — | |
MD5:— | SHA256:— | |||
| 3480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:1A89A1BEBE6C843C4FF582E7ED33CA1F | SHA256:65099CA087B66AA8CA420AB121DAAD713E1DB5A61C5A574D9B1C0DF24F012520 | |||
| 3480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 4008 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:B59113C2DCD2D346F31A64F231162ADA | SHA256:1D97C69AEA85D3B06787458EA47576B192CE5C5DB9940E5EAA514FF977CE2DC2 | |||
| 3480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\MANIFEST-000001 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
14
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2152 | chrome.exe | GET | 302 | 172.217.22.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 514 b | whitelisted |
2152 | chrome.exe | GET | 200 | 74.125.104.104:80 | http://r2---sn-2gb7sn7k.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=89.187.165.52&mm=28&mn=sn-2gb7sn7k&ms=nvh&mt=1569283941&mv=m&mvi=1&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2152 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2152 | chrome.exe | 2.18.233.243:443 | download.brother.com | Akamai International B.V. | — | whitelisted |
2152 | chrome.exe | 172.217.22.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
2152 | chrome.exe | 172.217.21.196:443 | www.google.com | Google Inc. | US | whitelisted |
2152 | chrome.exe | 216.58.205.227:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2152 | chrome.exe | 172.217.22.67:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2152 | chrome.exe | 216.58.206.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2152 | chrome.exe | 172.217.16.142:443 | clients1.google.com | Google Inc. | US | whitelisted |
2152 | chrome.exe | 216.58.205.225:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
2152 | chrome.exe | 172.217.22.110:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.brother.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
clients1.google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |