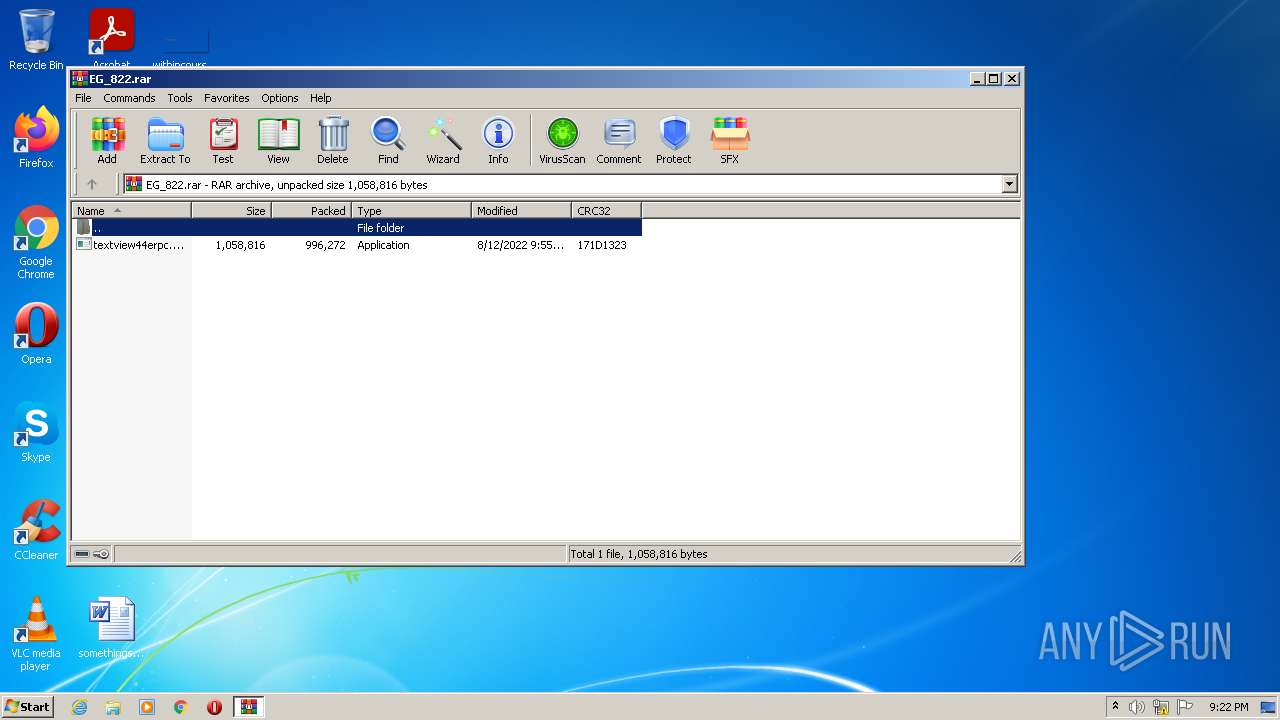
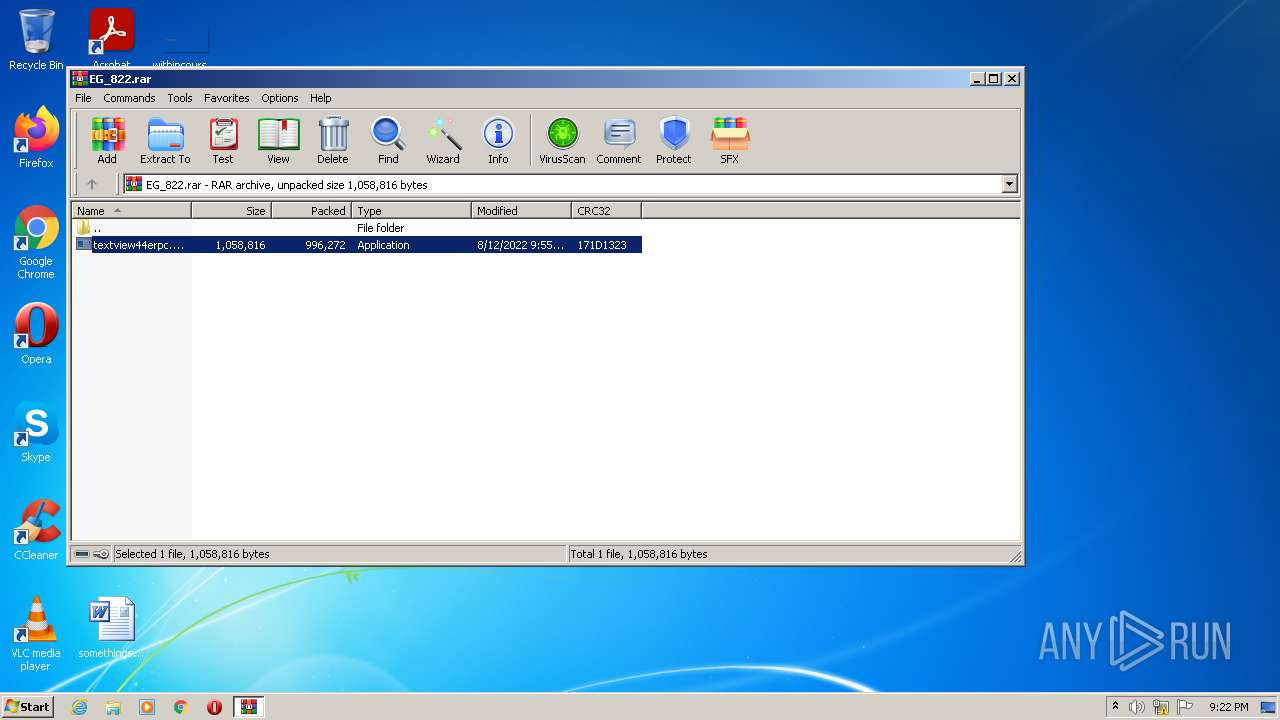
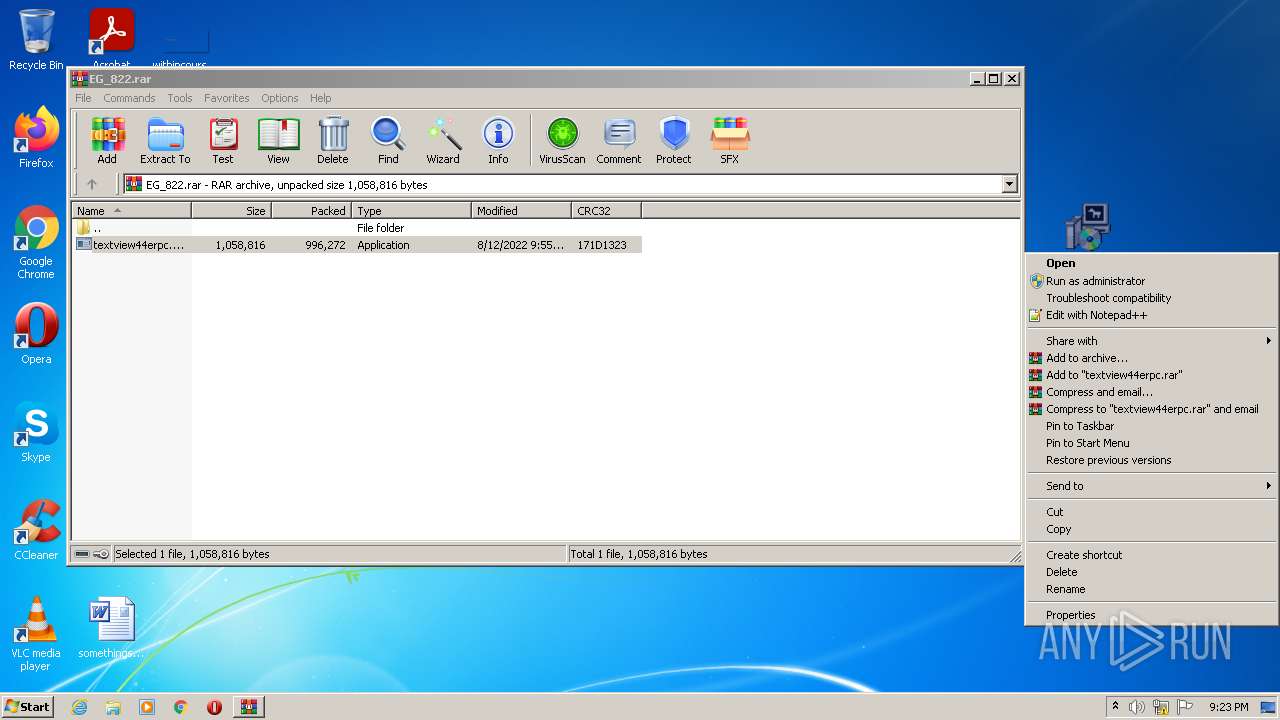
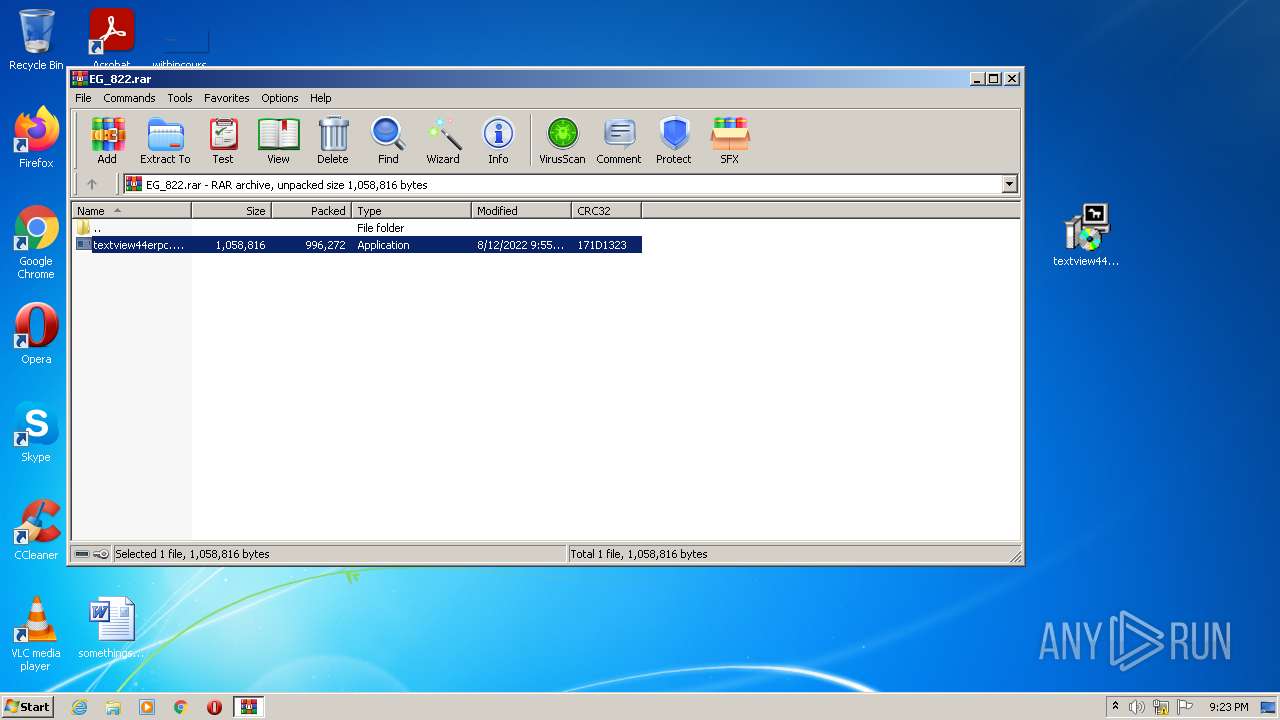
| File name: | EG_822.rar |
| Full analysis: | https://app.any.run/tasks/dcd6ff5e-0217-4241-8784-ee60510c9b2d |
| Verdict: | Malicious activity |
| Analysis date: | August 12, 2022, 20:22:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 2AAD7F5BFA8BC8074DCDB73E5B3B2B32 |
| SHA1: | C565F904104CFB3827746F850DFC0EA500AE72A2 |
| SHA256: | 1D24EE7F6070DB61A68D95D5D2361B5C1AA18381706FF5FB8428714D392E838A |
| SSDEEP: | 24576:kiymbeWNZuVWPM9ZfXXoh1JvkJ8nDEklMjAafpnhkvAoTm:5ybGZqPXoxvkJ8D3lSn6IoTm |
MALICIOUS
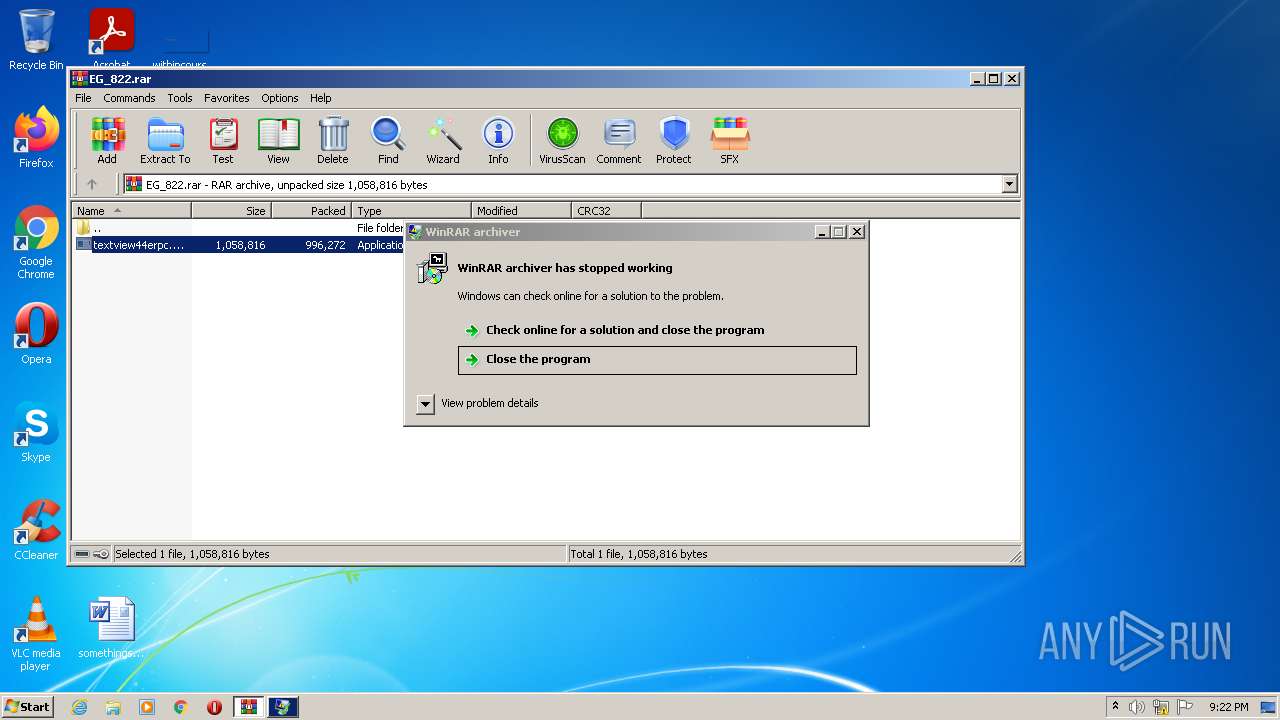
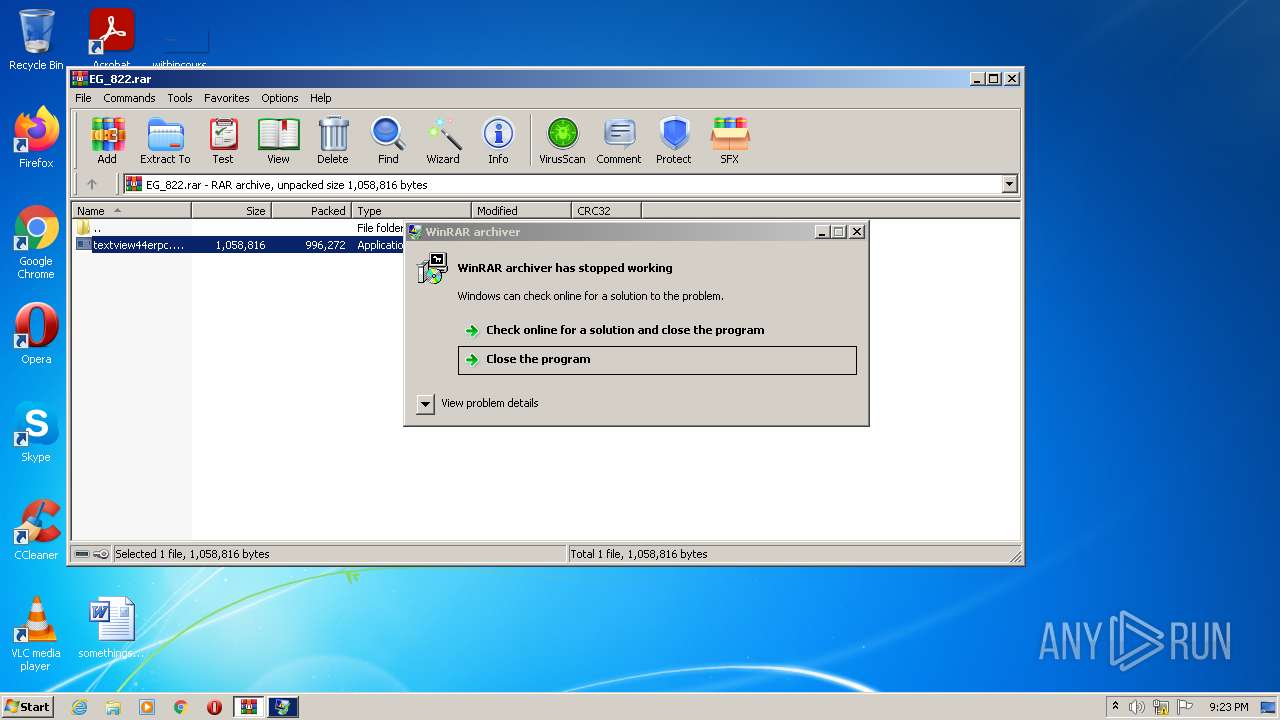
Drops executable file immediately after starts
- WinRAR.exe (PID: 3512)
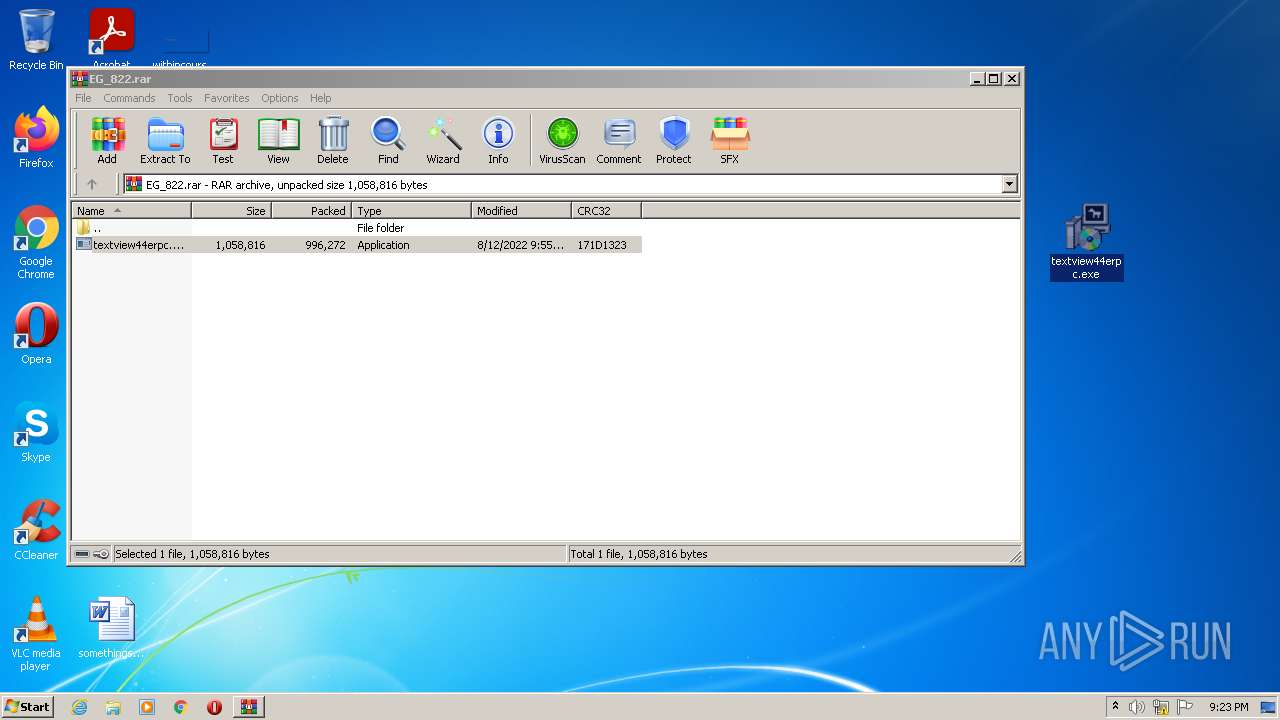
Application was dropped or rewritten from another process
- textview44erpc.exe (PID: 2548)
- textview44erpc.exe (PID: 3328)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3512)
Reads the computer name
- WinRAR.exe (PID: 3512)
- textview44erpc.exe (PID: 2548)
- textview44erpc.exe (PID: 3328)
Checks supported languages
- WinRAR.exe (PID: 3512)
- textview44erpc.exe (PID: 2548)
- textview44erpc.exe (PID: 3328)
- notepad++.exe (PID: 3172)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 3512)
INFO
Manual execution by user
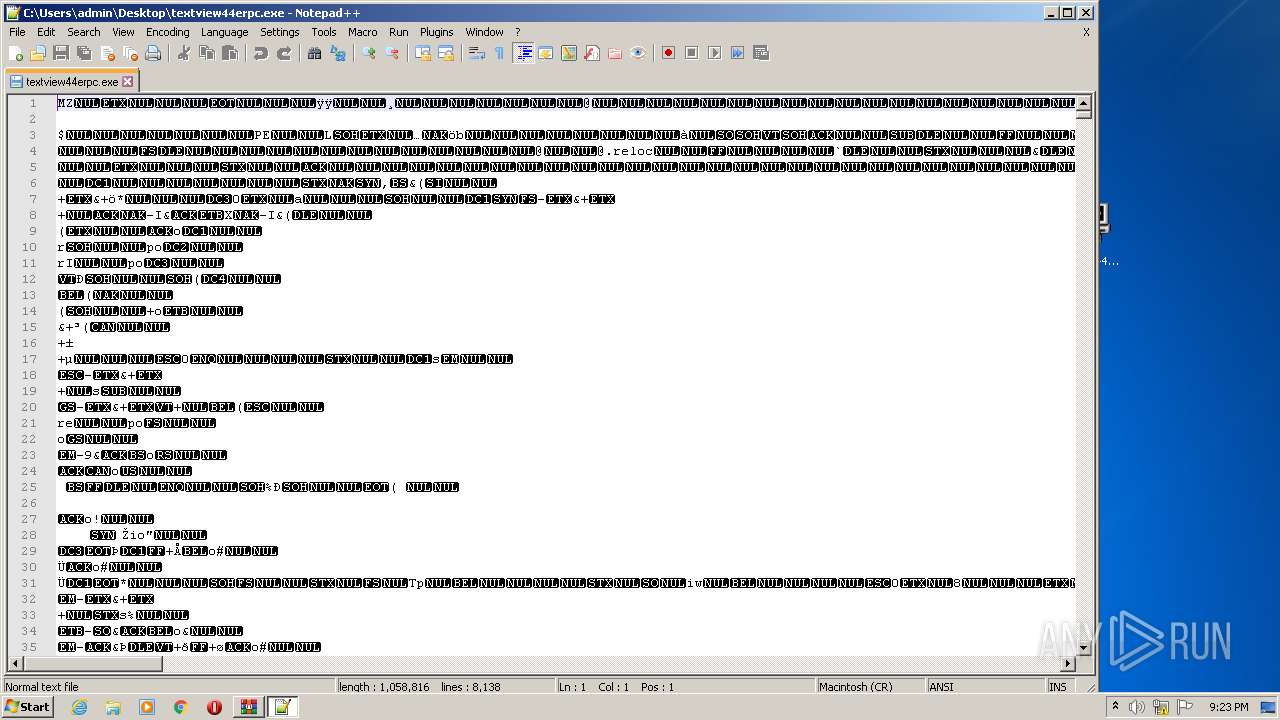
- notepad++.exe (PID: 3172)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
41
Monitored processes
4
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
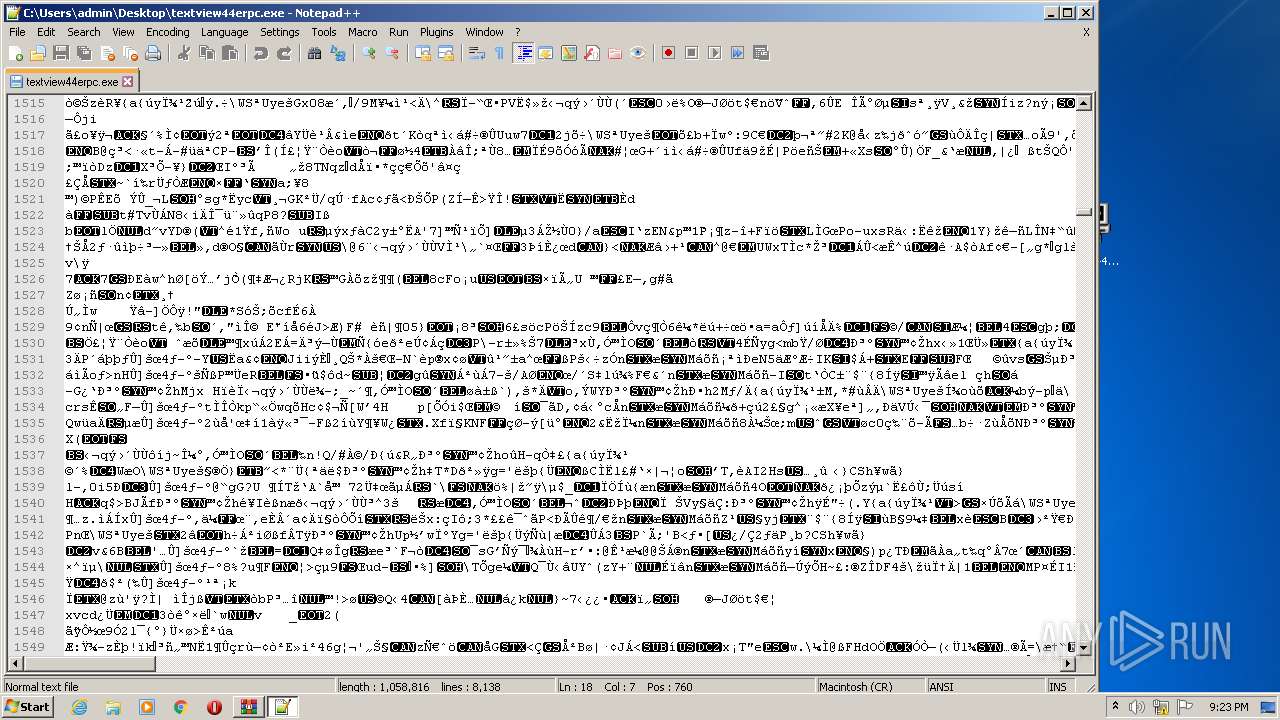
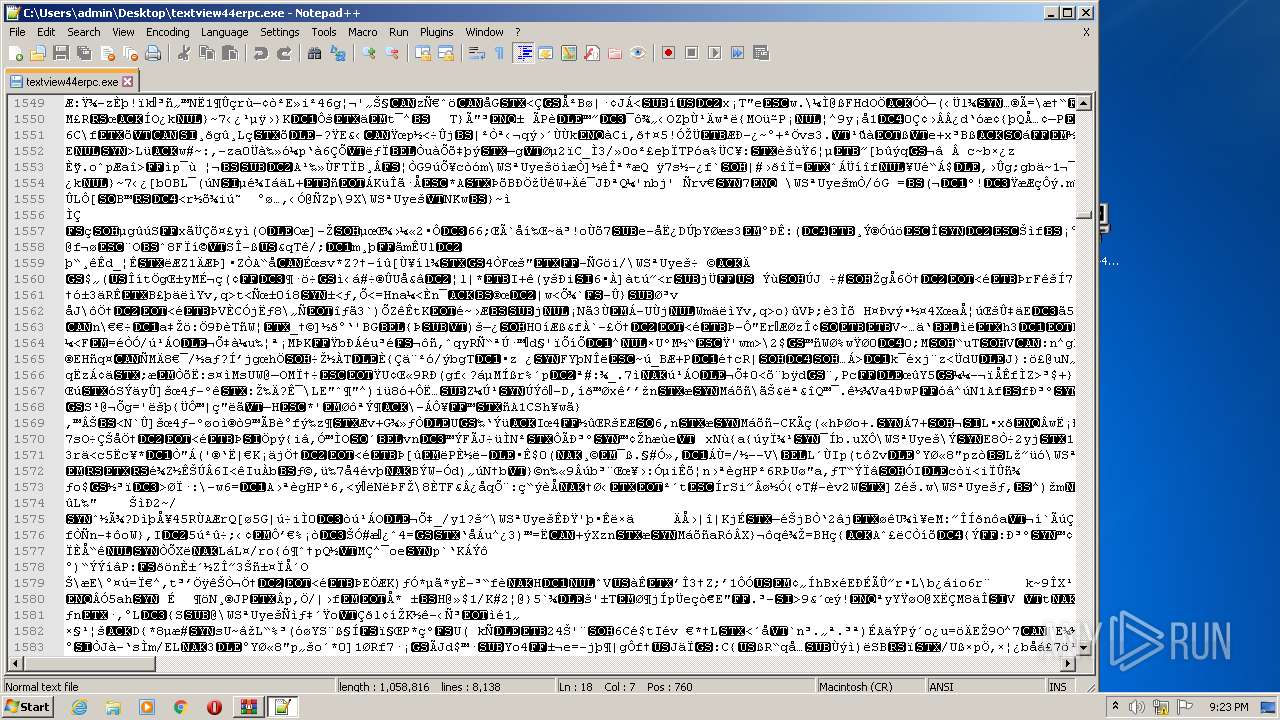
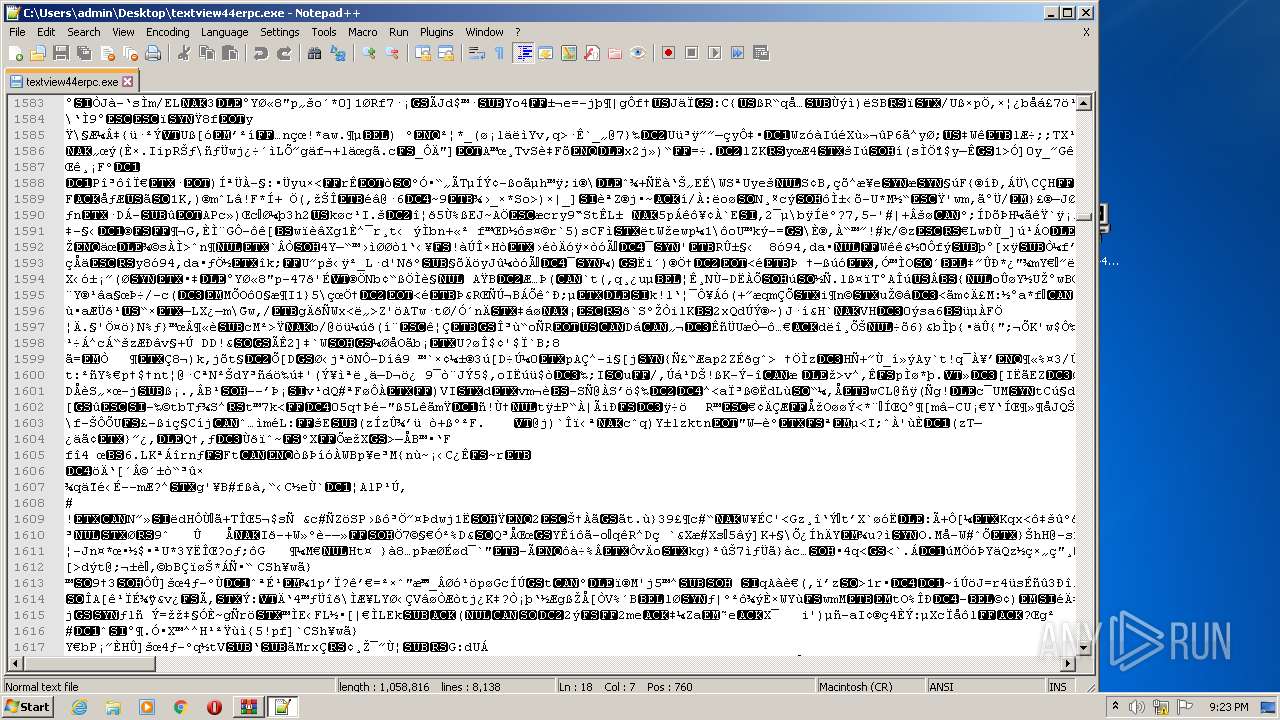
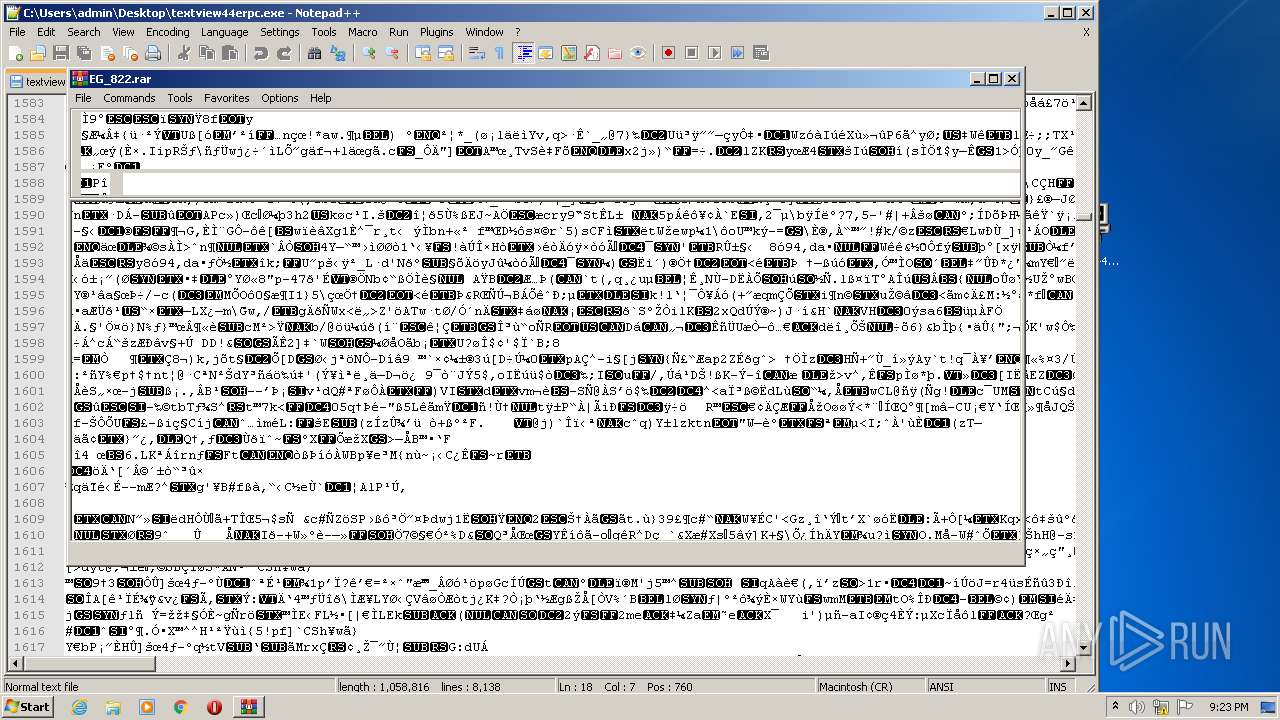
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
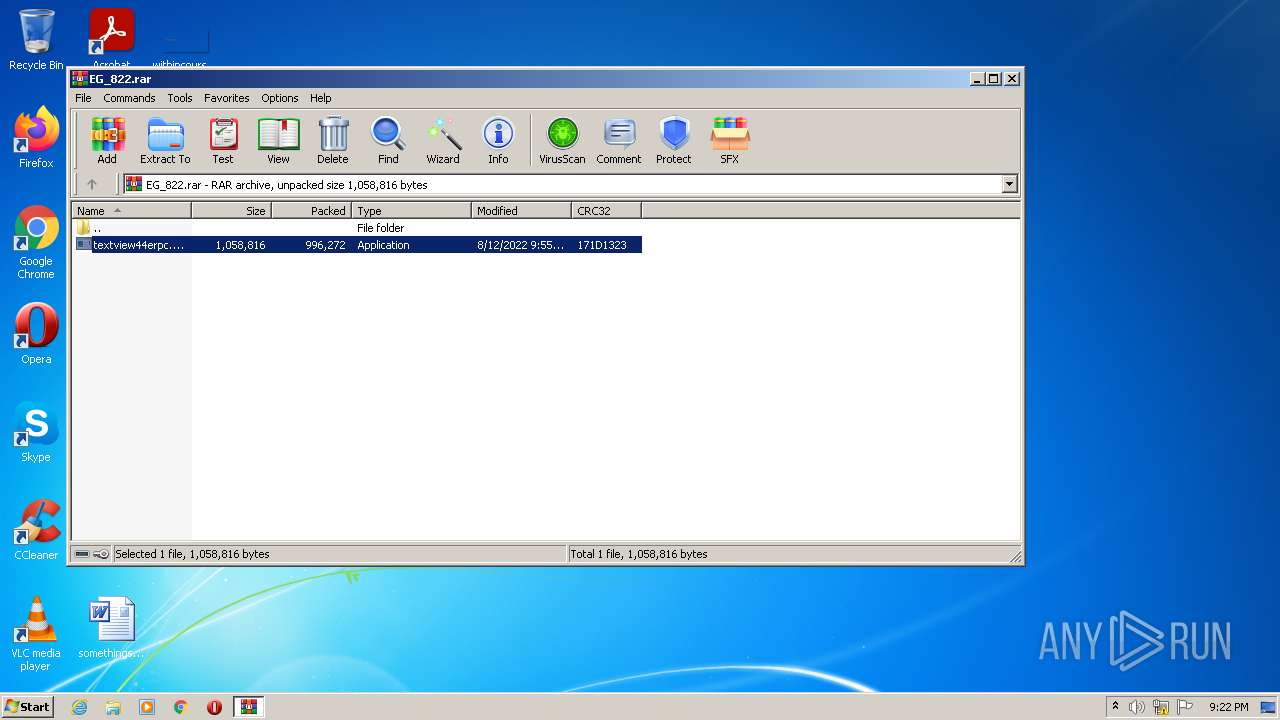
| 2548 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3512.42982\textview44erpc.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3512.42982\textview44erpc.exe | WinRAR.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 3762504530 Version: 5.80.0.0 Modules
| |||||||||||||||
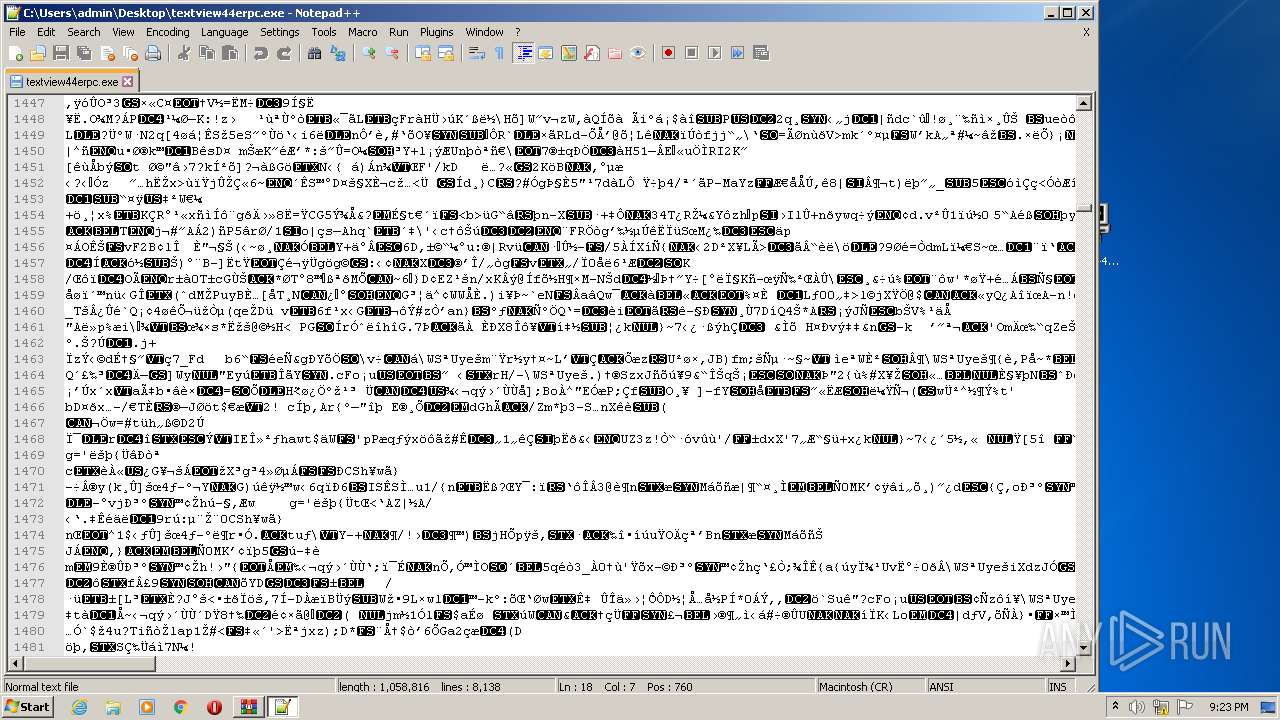
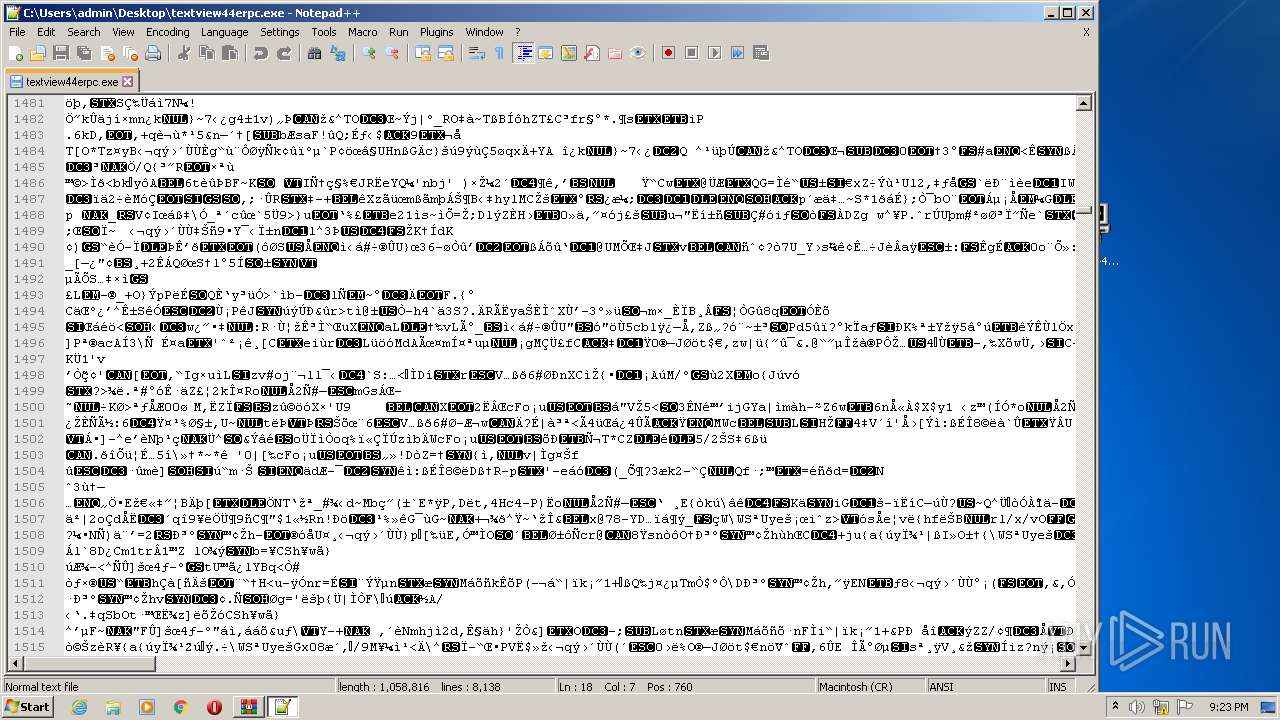
| 3172 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\Desktop\textview44erpc.exe" | C:\Program Files\Notepad++\notepad++.exe | Explorer.EXE | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.91 Modules
| |||||||||||||||
| 3328 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3512.43571\textview44erpc.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3512.43571\textview44erpc.exe | WinRAR.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 3762504530 Version: 5.80.0.0 Modules
| |||||||||||||||
| 3512 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\EG_822.rar" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
1 268
Read events
1 236
Write events
32
Delete events
0
Modification events
| (PID) Process: | (3512) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3512) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3512) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3512) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (3512) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3512) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\EG_822.rar | |||
| (PID) Process: | (3512) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3512) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3512) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3512) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
3
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3512 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3512.42982\textview44erpc.exe | executable | |
MD5:— | SHA256:— | |||
| 3512 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3512.44041\textview44erpc.exe | executable | |
MD5:— | SHA256:— | |||
| 3512 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3512.43571\textview44erpc.exe | executable | |
MD5:— | SHA256:— | |||
| 3172 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\session.xml | text | |
MD5:— | SHA256:— | |||
| 3172 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\config.xml | xml | |
MD5:75DAF0C838CA0F9DAA89D4074A504E1B | SHA256:97901B6DEF410AA997B0E91A0FD0947EB3A26B7D5C83FD7228FDE04F981AC53C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\plugins\Config\nppPluginList.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|