| File name: | ransomware_1d1f2.exe |
| Full analysis: | https://app.any.run/tasks/730b6efb-cf07-45b2-bd8c-6f5fbf9515e0 |
| Verdict: | Malicious activity |
| Analysis date: | September 19, 2019, 04:13:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 50B863B58F35CD926854825E35F76AE1 |
| SHA1: | 184A13C0EAD417155CE8C4827D50065EDB471A4E |
| SHA256: | 1D1F210745697F2B91B4C983C405A0F84BB4880F742CE71AE7BEAB2BE18FCF63 |
| SSDEEP: | 6144:kGG7PPI001hG4Xv4Y8w9oklesKwmJDAakTti7b1ytAIKYrY9KbWYS/+KTqrCaK3y:kGG7oGe8wy9FJ9Kbr7DGM |
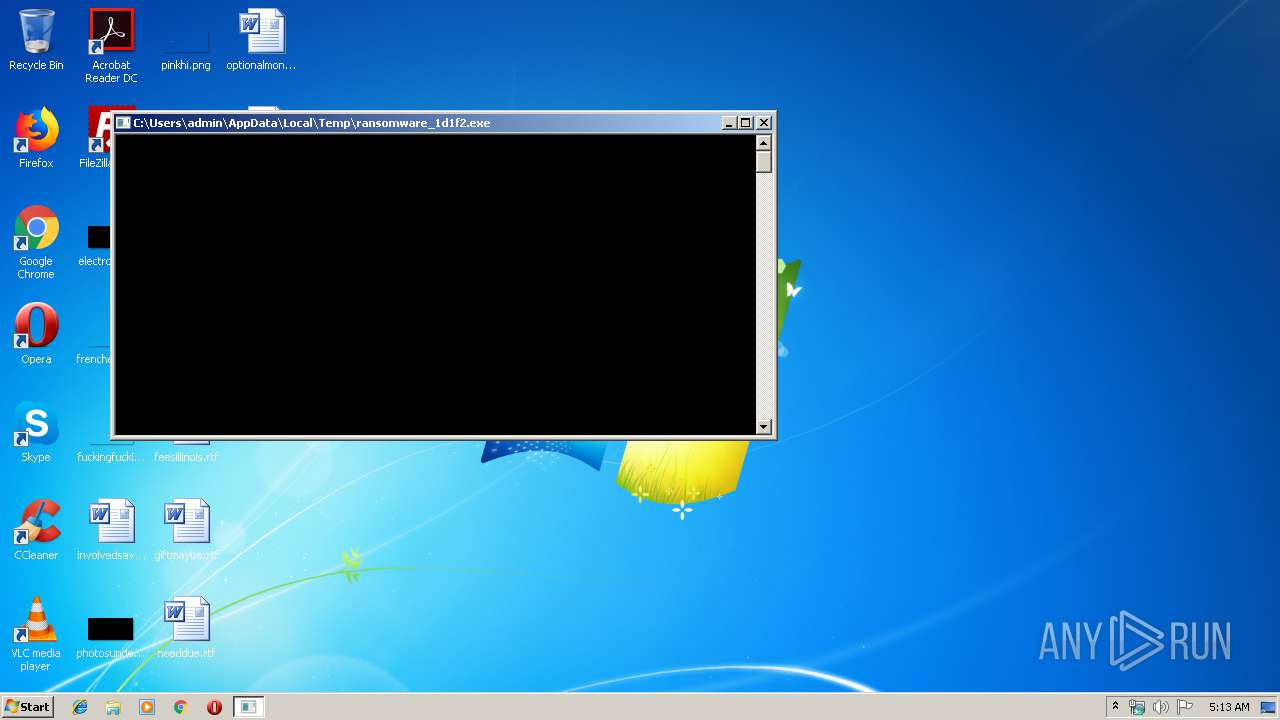
MALICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 3816)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 324)
Starts CMD.EXE for commands execution
- ransomware_1d1f2.exe (PID: 2868)
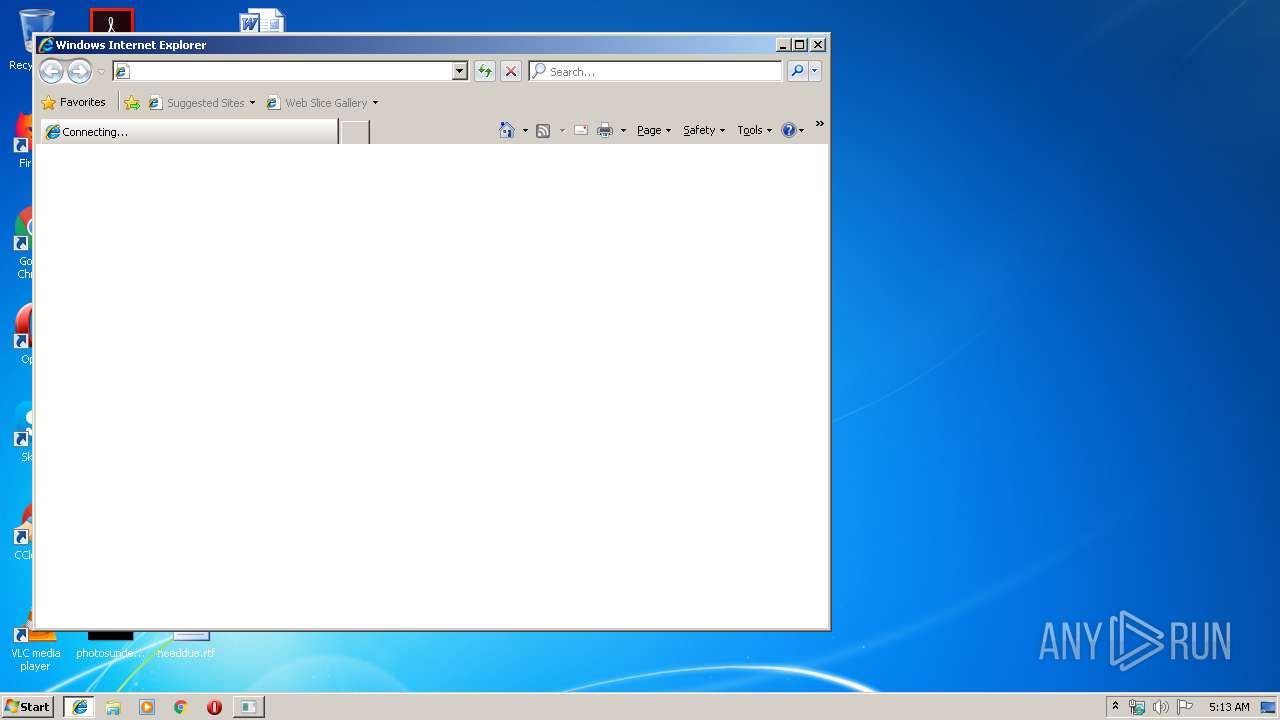
Starts Internet Explorer
- powershell.exe (PID: 324)
INFO
Application launched itself
- iexplore.exe (PID: 2932)
Changes internet zones settings
- iexplore.exe (PID: 2932)
Reads Internet Cache Settings
- iexplore.exe (PID: 3912)
Reads internet explorer settings
- iexplore.exe (PID: 3912)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:09:02 18:57:40+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 219136 |
| InitializedDataSize: | 123904 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x27098 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 02-Sep-2019 16:57:40 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 02-Sep-2019 16:57:40 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0003572B | 0x00035800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.67289 |
.rdata | 0x00037000 | 0x00015B1A | 0x00015C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.87431 |
.data | 0x0004D000 | 0x00005C20 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.74533 |
.reloc | 0x00053000 | 0x0000299C | 0x00002A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.58774 |
Imports
ADVAPI32.dll |
KERNEL32.dll |
SHLWAPI.dll |
USER32.dll |
Total processes
37
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
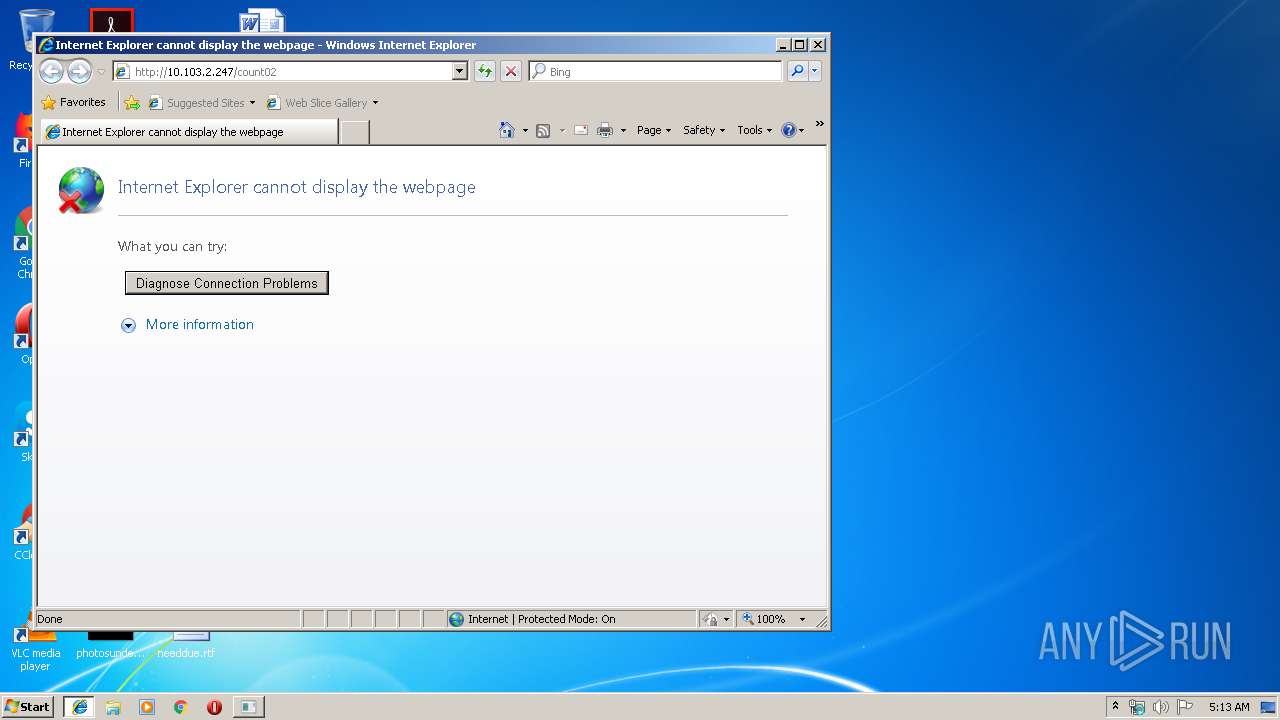
| 324 | powershell Start-Process -FilePath iexplore -ArgumentList "http://10.103.2.247/count02" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2868 | "C:\Users\admin\AppData\Local\Temp\ransomware_1d1f2.exe" | C:\Users\admin\AppData\Local\Temp\ransomware_1d1f2.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2932 | "C:\Program Files\Internet Explorer\iexplore.exe" http://10.103.2.247/count02 | C:\Program Files\Internet Explorer\iexplore.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3816 | C:\Windows\system32\cmd.exe /c powershell Start-Process -FilePath iexplore -ArgumentList "http://10.103.2.247/count02" | C:\Windows\system32\cmd.exe | — | ransomware_1d1f2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3912 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2932 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
607
Read events
500
Write events
106
Delete events
1
Modification events
| (PID) Process: | (324) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (324) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (324) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {E24D1645-DA93-11E9-B86F-5254004A04AF} |
Value: 0 | |||
Executable files
0
Suspicious files
4
Text files
15
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 324 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\XYL3J5TZ93XE7JEG3YAZ.temp | — | |
MD5:— | SHA256:— | |||
| 2932 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2932 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2932 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFE86E090215FDACF1.TMP | — | |
MD5:— | SHA256:— | |||
| 2932 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFAA71C8FF86B8DB23.TMP | — | |
MD5:— | SHA256:— | |||
| 324 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2932 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF5D1EEF5573199589.TMP | — | |
MD5:— | SHA256:— | |||
| 2932 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{E24D1646-DA93-11E9-B86F-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 3912 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2932 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF86445FA3B9547243.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3912 | iexplore.exe | 10.103.2.247:80 | — | — | — | unknown |
2932 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
Threats
Process | Message |
|---|---|
ransomware_1d1f2.exe | Error: RegCreateKeyExA "Software\Microsoft\.NETFramework\SecurityFolders" error 5.
|
ransomware_1d1f2.exe | Error: Access key "Software\Microsoft\.NETFramework\SecurityFolders\UserAgent" error 2.
|
ransomware_1d1f2.exe | Error: myHybirdCryptInitCtx error 2
|
ransomware_1d1f2.exe | Error: myHybirdCryptInitCtx error 2
|
ransomware_1d1f2.exe | Error: myHybirdCryptInitCtx error 2
|
ransomware_1d1f2.exe | Dir Not Writable: C:\$Recycle.Bin
|
ransomware_1d1f2.exe | Error: FindFirstFileA "C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-500\*.*" error 5.
|
ransomware_1d1f2.exe | Error: FindFirstFileA "C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-500\*.*" error 5.
|
ransomware_1d1f2.exe | Dir Excluded: C:\MSOCache
|
ransomware_1d1f2.exe | Dir Excluded: C:\PerfLogs
|