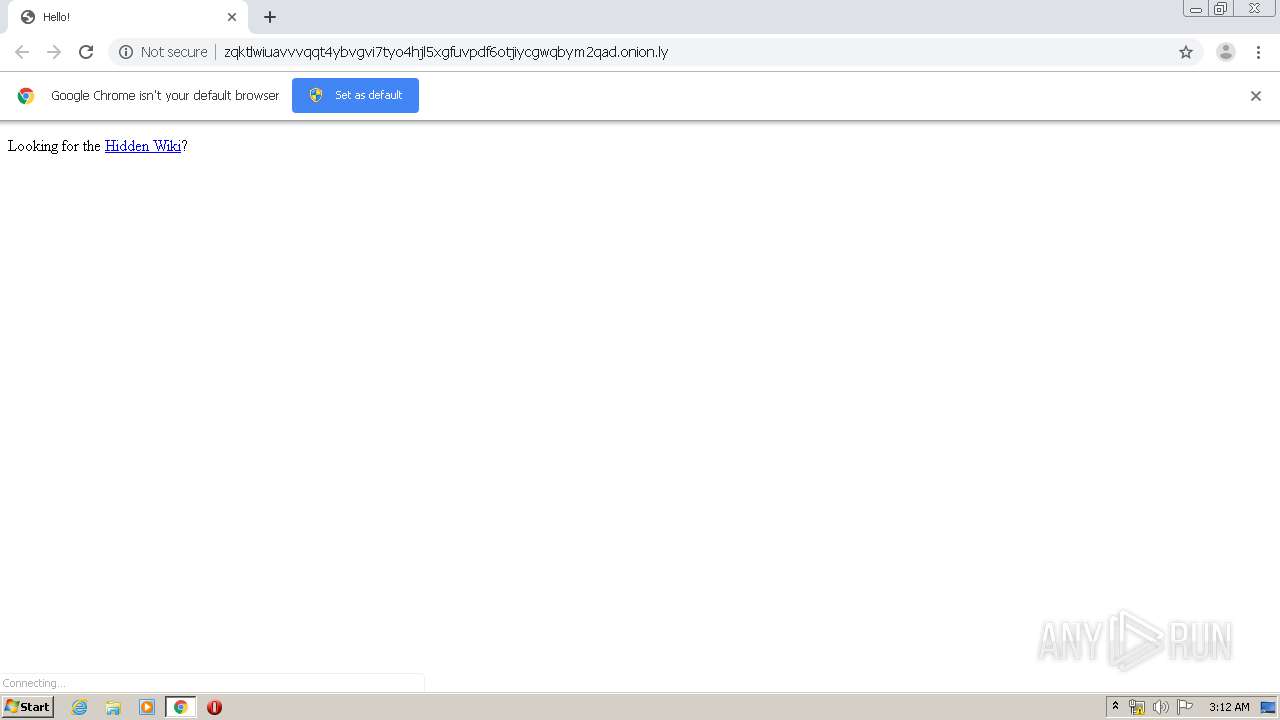
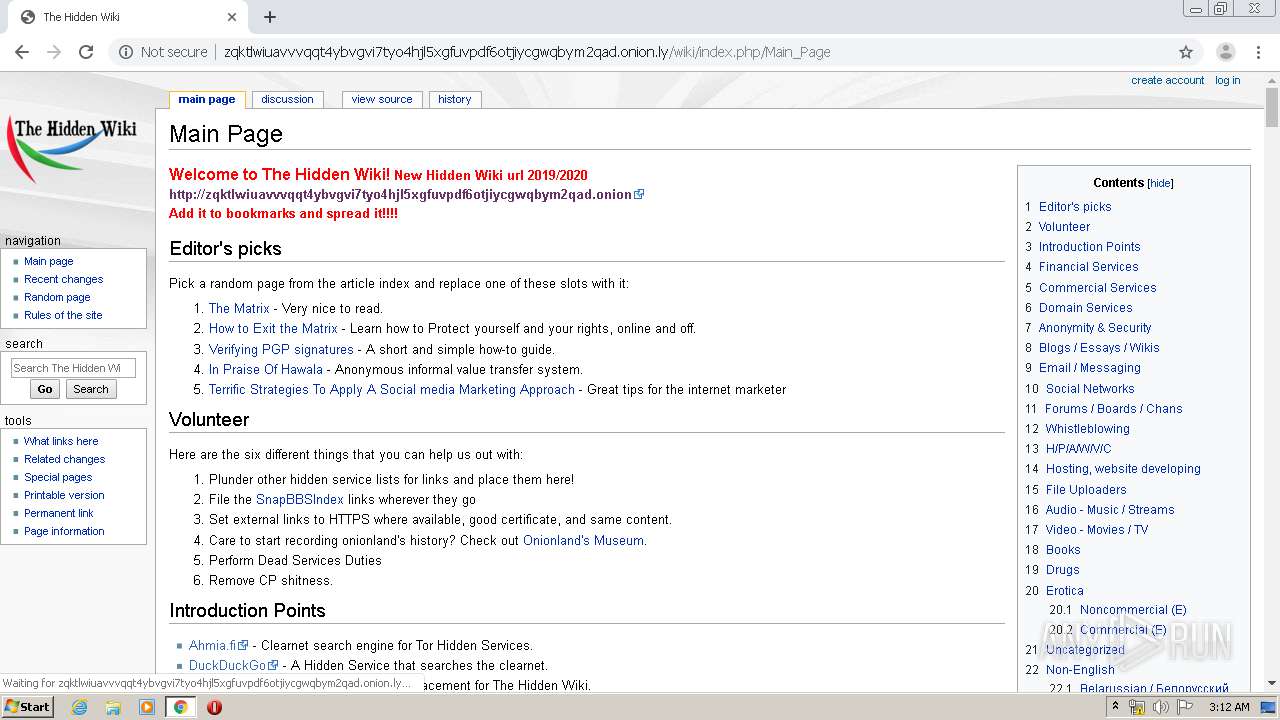
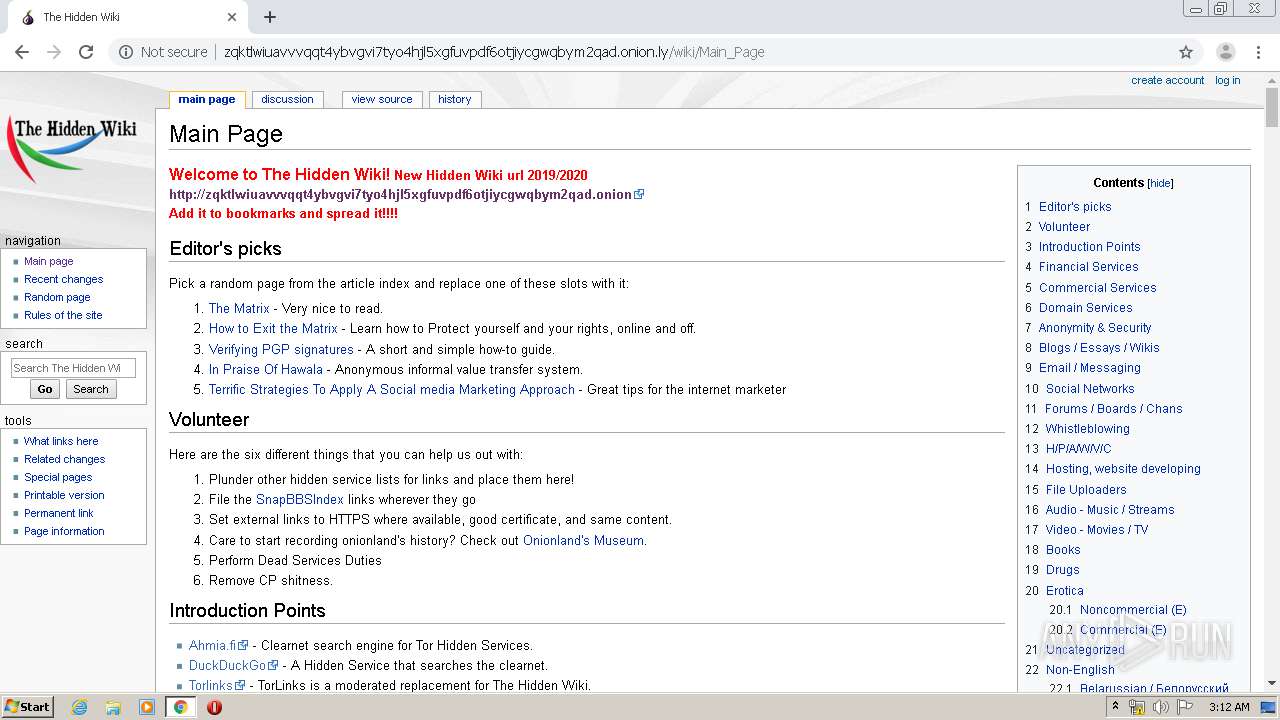
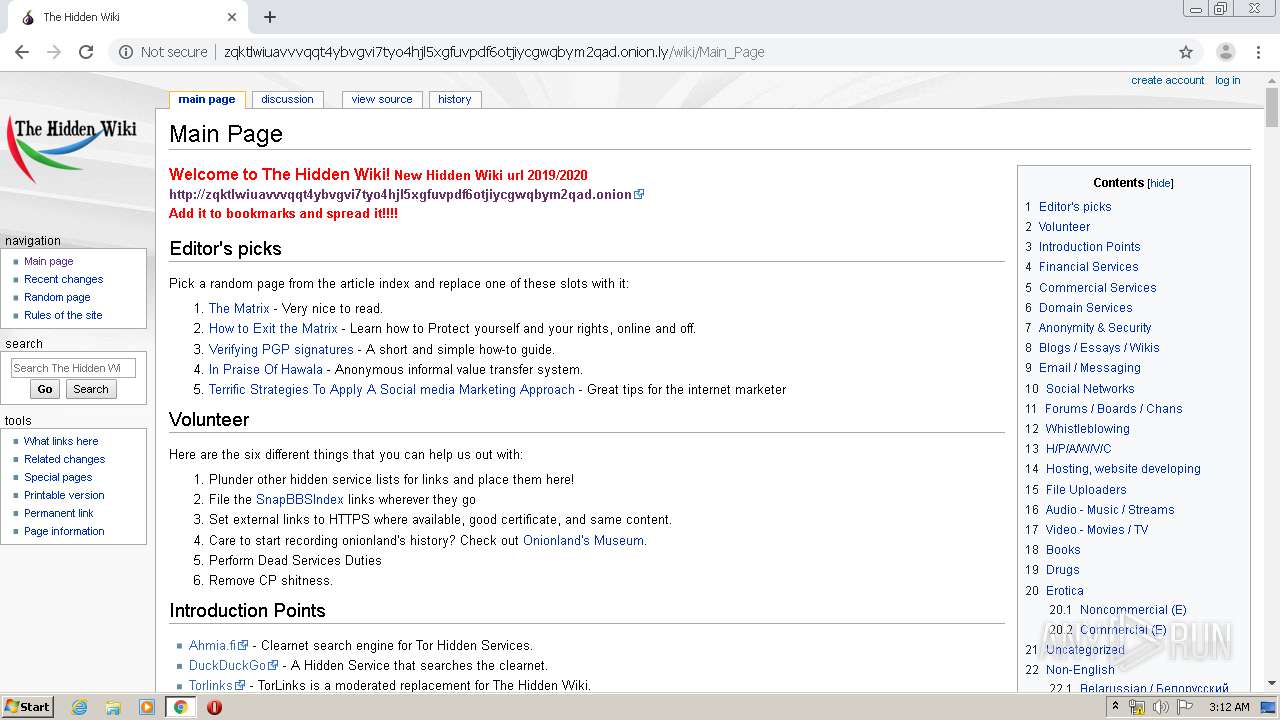
| URL: | http://zqktlwiuavvvqqt4ybvgvi7tyo4hjl5xgfuvpdf6otjiycgwqbym2qad.onion.ly |
| Full analysis: | https://app.any.run/tasks/79513bab-bef8-4cfe-9b55-2afd6db8a20b |
| Verdict: | Malicious activity |
| Analysis date: | May 29, 2020, 02:11:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 4FB3A653290FBAC85501DAD553D52BA4 |
| SHA1: | 2D5D191366A4623F132B57B5AE045F41364C27B3 |
| SHA256: | 1D0BCACD3C83E01780F52A92429CD0459718E008EB63538F591E0C70E57F980B |
| SSDEEP: | 3:N1KEXR9tN3czCR+AGVSGePBLYS:CEXXj30k+ZHePX |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2248)
INFO
Reads the hosts file
- chrome.exe (PID: 2248)
- chrome.exe (PID: 2140)
Dropped object may contain TOR URL's
- chrome.exe (PID: 2248)
Application launched itself
- chrome.exe (PID: 2248)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
62
Monitored processes
25
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,15156090310430812061,7864539059463563550,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=5648857200874456841 --mojo-platform-channel-handle=3548 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,15156090310430812061,7864539059463563550,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12662672088491274868 --mojo-platform-channel-handle=3912 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 964 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,15156090310430812061,7864539059463563550,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8680555945072169261 --mojo-platform-channel-handle=3936 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1476 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,15156090310430812061,7864539059463563550,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16943113603175902342 --mojo-platform-channel-handle=3068 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,15156090310430812061,7864539059463563550,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15246221360755487308 --mojo-platform-channel-handle=3404 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,15156090310430812061,7864539059463563550,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9760356773091813161 --mojo-platform-channel-handle=4208 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1712 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,15156090310430812061,7864539059463563550,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18169075419040474575 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2496 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,15156090310430812061,7864539059463563550,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15351618862618516794 --mojo-platform-channel-handle=4204 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,15156090310430812061,7864539059463563550,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=9242981315167910139 --mojo-platform-channel-handle=1008 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2432 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
607
Read events
518
Write events
84
Delete events
5
Modification events
| (PID) Process: | (2248) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2248) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2248) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2248) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2248) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2124) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2248-13235191929597625 |
Value: 259 | |||
| (PID) Process: | (2248) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2248) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2248) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (2248) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
25
Text files
245
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2248 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5ED06F7A-8C8.pma | — | |
MD5:— | SHA256:— | |||
| 2248 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ae741d27-6179-4826-a2dd-d74fa34fae33.tmp | — | |
MD5:— | SHA256:— | |||
| 2248 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2248 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:DA692BE42E4EF2668AE7499A7D5DA720 | SHA256:EB865CAF59002C092F5FDBE22D01935866BC1277108B29E897052CB2439630ED | |||
| 2248 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:33B05E8AC9C178C58ED3321F496588C0 | SHA256:2CDF6A09638A0B563EA2672D6926210771902E0A9203FE15D2857FC4EB954CDE | |||
| 2248 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:1A89A1BEBE6C843C4FF582E7ED33CA1F | SHA256:65099CA087B66AA8CA420AB121DAAD713E1DB5A61C5A574D9B1C0DF24F012520 | |||
| 2248 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF109a7d.TMP | text | |
MD5:FC9FFE77348619CC285333DFF5E1D5D1 | SHA256:7CB9B3575330B3D776A21EB7A7407E34F013A0975B7418DA11B5C85DEC91D1F3 | |||
| 2332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:B59113C2DCD2D346F31A64F231162ADA | SHA256:1D97C69AEA85D3B06787458EA47576B192CE5C5DB9940E5EAA514FF977CE2DC2 | |||
| 2248 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2248 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF109c42.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
23
DNS requests
92
Threats
70
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2140 | chrome.exe | GET | 200 | 87.245.197.145:80 | http://r6---sn-gxuog0-n8ve.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjY5QUFXTEQwc2RPVXhRY3picjhxblh1dw/7619.603.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Qx&mip=85.206.175.219&mm=28&mn=sn-gxuog0-n8ve&ms=nvh&mt=1590718232&mv=m&mvi=5&pl=22&shardbypass=yes | RU | crx | 816 Kb | whitelisted |
2140 | chrome.exe | GET | 200 | 198.251.89.118:80 | http://zqktlwiuavvvqqt4ybvgvi7tyo4hjl5xgfuvpdf6otjiycgwqbym2qad.onion.ly/ | US | html | 528 b | malicious |
2140 | chrome.exe | GET | 200 | 198.251.89.118:80 | http://zqktlwiuavvvqqt4ybvgvi7tyo4hjl5xgfuvpdf6otjiycgwqbym2qad.onion.ly/wiki/load.php?debug=false&lang=en&modules=mediawiki.legacy.commonPrint%2Cshared%7Cmediawiki.skinning.content.externallinks%7Cmediawiki.skinning.interface%7Cmediawiki.toc.styles%7Cskins.monobook.responsive&only=styles&skin=monobook | US | text | 60.3 Kb | malicious |
2140 | chrome.exe | GET | 200 | 87.245.200.145:80 | http://r6---sn-gxuog0-n8vl.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=85.206.175.219&mm=28&mn=sn-gxuog0-n8vl&ms=nvh&mt=1590718232&mv=m&mvi=5&pl=22&shardbypass=yes | RU | crx | 293 Kb | whitelisted |
2140 | chrome.exe | GET | 200 | 198.251.89.118:80 | http://zqktlwiuavvvqqt4ybvgvi7tyo4hjl5xgfuvpdf6otjiycgwqbym2qad.onion.ly/wiki/resources/assets/poweredby_mediawiki_88x31.png | US | image | 3.41 Kb | malicious |
2140 | chrome.exe | GET | 200 | 198.251.89.118:80 | http://zqktlwiuavvvqqt4ybvgvi7tyo4hjl5xgfuvpdf6otjiycgwqbym2qad.onion.ly/wiki/load.php?debug=false&lang=en&modules=startup&only=scripts&skin=monobook | US | text | 38.4 Kb | malicious |
2140 | chrome.exe | GET | 200 | 198.251.89.118:80 | http://zqktlwiuavvvqqt4ybvgvi7tyo4hjl5xgfuvpdf6otjiycgwqbym2qad.onion.ly/wiki/resources/wiki.png?e0777 | US | image | 6.66 Kb | malicious |
2140 | chrome.exe | GET | 200 | 198.251.89.118:80 | http://zqktlwiuavvvqqt4ybvgvi7tyo4hjl5xgfuvpdf6otjiycgwqbym2qad.onion.ly/wiki/skins/MonoBook/resources/images/headbg.jpg?13df6 | US | image | 38.2 Kb | malicious |
2140 | chrome.exe | GET | 200 | 198.251.89.118:80 | http://zqktlwiuavvvqqt4ybvgvi7tyo4hjl5xgfuvpdf6otjiycgwqbym2qad.onion.ly/wiki/load.php?debug=false&lang=en&modules=ext.moderation.notify%7Cext.moderation.notify.desktop%7Cjquery%2Csite%7Cjquery.accessKeyLabel%2CcheckboxShiftClick%2Cclient%2Ccookie%2CgetAttrs%2ChighlightText%2Csuggestions%7Cmediawiki.RegExp%2CString%2CTitle%2CUri%2Capi%2Cbase%2Ccldr%2Ccookie%2CjqueryMsg%2Clanguage%2Cnotify%2CsearchSuggest%2Cstorage%2Ctemplate%2Ctoc%2Cuser%2Cutil%7Cmediawiki.libs.pluralruleparser%7Cmediawiki.page.ready%2Cstartup%7Cmediawiki.template.regexp%7Cskins.monobook.mobile%7Cuser.defaults&skin=monobook&version=09ry1w5 | US | text | 307 Kb | malicious |
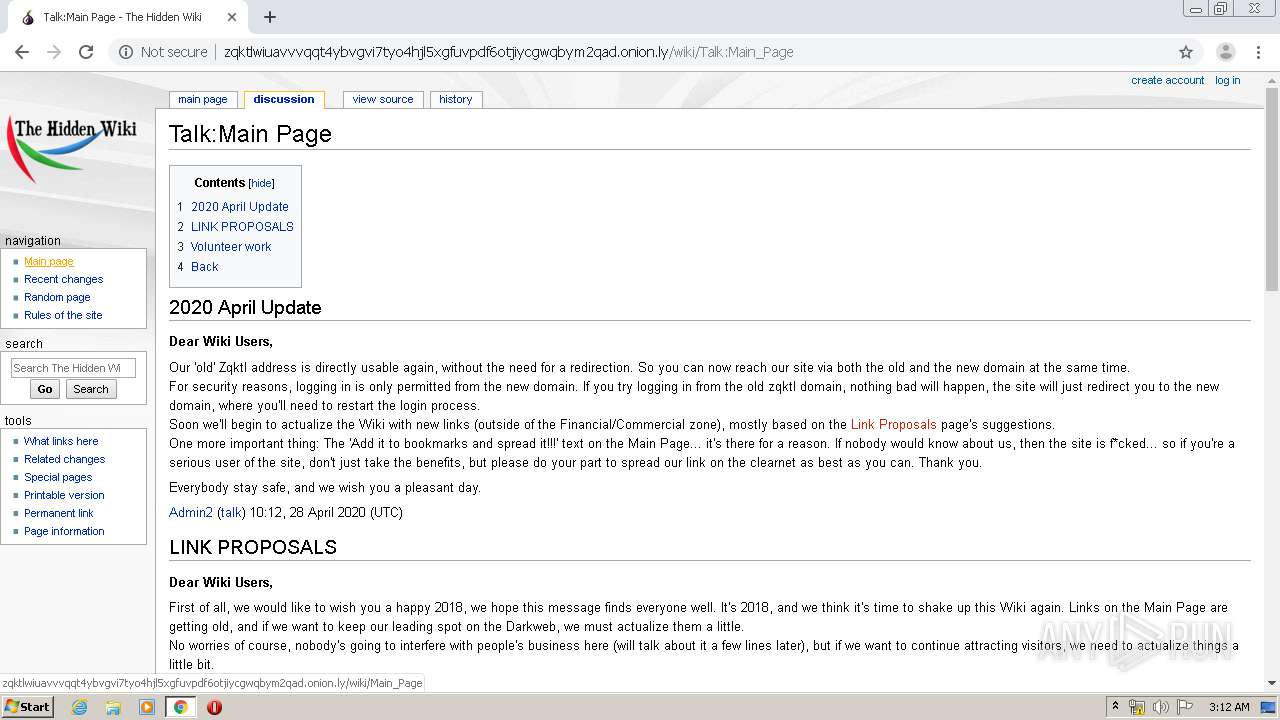
2140 | chrome.exe | GET | 200 | 198.251.89.118:80 | http://zqktlwiuavvvqqt4ybvgvi7tyo4hjl5xgfuvpdf6otjiycgwqbym2qad.onion.ly/wiki/Talk:Main_Page | US | html | 8.10 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2140 | chrome.exe | 198.251.89.118:80 | zqktlwiuavvvqqt4ybvgvi7tyo4hjl5xgfuvpdf6otjiycgwqbym2qad.onion.ly | FranTech Solutions | US | malicious |
2140 | chrome.exe | 172.217.22.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
2140 | chrome.exe | 172.217.22.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
2140 | chrome.exe | 172.217.21.200:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
2140 | chrome.exe | 216.58.208.46:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2140 | chrome.exe | 172.217.16.142:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2140 | chrome.exe | 66.102.1.155:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
2140 | chrome.exe | 172.217.16.196:443 | www.google.com | Google Inc. | US | whitelisted |
2140 | chrome.exe | 87.245.200.145:80 | r6---sn-gxuog0-n8vl.gvt1.com | RETN Limited | RU | whitelisted |
2140 | chrome.exe | 216.58.207.65:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
zqktlwiuavvvqqt4ybvgvi7tyo4hjl5xgfuvpdf6otjiycgwqbym2qad.onion.ly |
| malicious |
accounts.google.com |
| shared |
www.googletagmanager.com |
| whitelisted |
clients2.google.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
stats.g.doubleclick.net |
| whitelisted |
www.google.com |
| malicious |
r6---sn-gxuog0-n8vl.gvt1.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1056 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query to .onion proxy Domain (onion . ly) |
1056 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query to .onion proxy Domain (onion . ly) |
1056 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query to .onion proxy Domain (onion . ly) |
1056 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query to .onion proxy Domain (onion . ly) |
1056 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query to .onion proxy Domain (onion . ly) |
1056 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query to .onion proxy Domain (onion . ly) |
1056 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query to .onion proxy Domain (onion . ly) |
1056 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query to .onion proxy Domain (onion . ly) |
1056 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query to .onion proxy Domain (onion . ly) |
1056 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query to .onion proxy Domain (onion . ly) |