| download: | install.ps1 |
| Full analysis: | https://app.any.run/tasks/c8cf75b3-3c37-430f-b238-89d9125b81f0 |
| Verdict: | No threats detected |
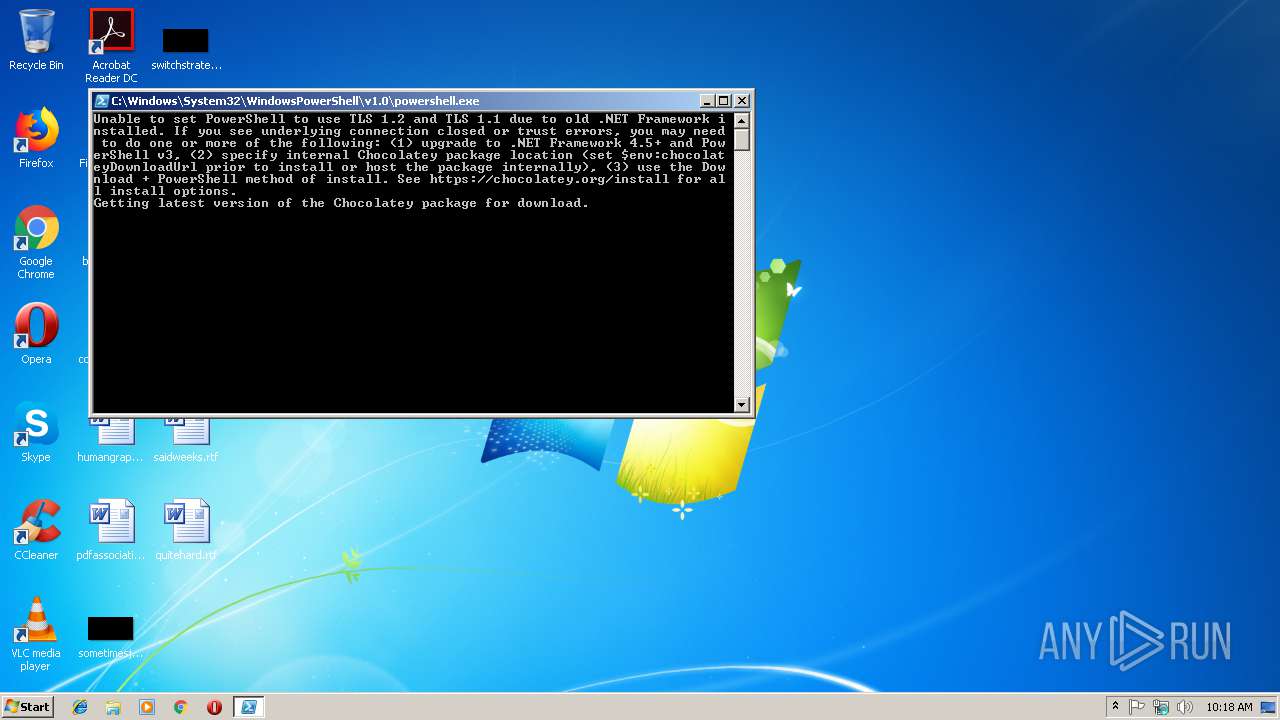
| Analysis date: | March 05, 2019, 10:18:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with CRLF line terminators |
| MD5: | 39702BF539699670B86C44217B3B2AB9 |
| SHA1: | 2602F2310BC1B9F322129C5D47CB656D6291BC25 |
| SHA256: | 1CF9D9364B2BD8748DC3038DB7053E72E31382B5BAC0C91AFA43E86E72D9D620 |
| SSDEEP: | 384:cQGdTQNoWd3tndSPLtVPcMVDW+7vnLXRRq45SqRu3XprLrSPYcJnBBPGFHTsSMmr:c0oY12XZVDtTnVRf5A3XZrCYctUfCe3 |
MALICIOUS
Application was dropped or rewritten from another process
- 7za.exe (PID: 3344)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 2980)
Executable content was dropped or overwritten
- powershell.exe (PID: 2980)
- 7za.exe (PID: 3344)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
35
Monitored processes
5
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 180 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES281.tmp" "c:\Users\admin\AppData\Local\Temp\CSC270.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 2616 | "C:\Windows\System32\setx.exe" ChocolateyLastPathUpdate "Tue Mar 5 10:18:53 2019" | C:\Windows\System32\setx.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Setx - Sets environment variables Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
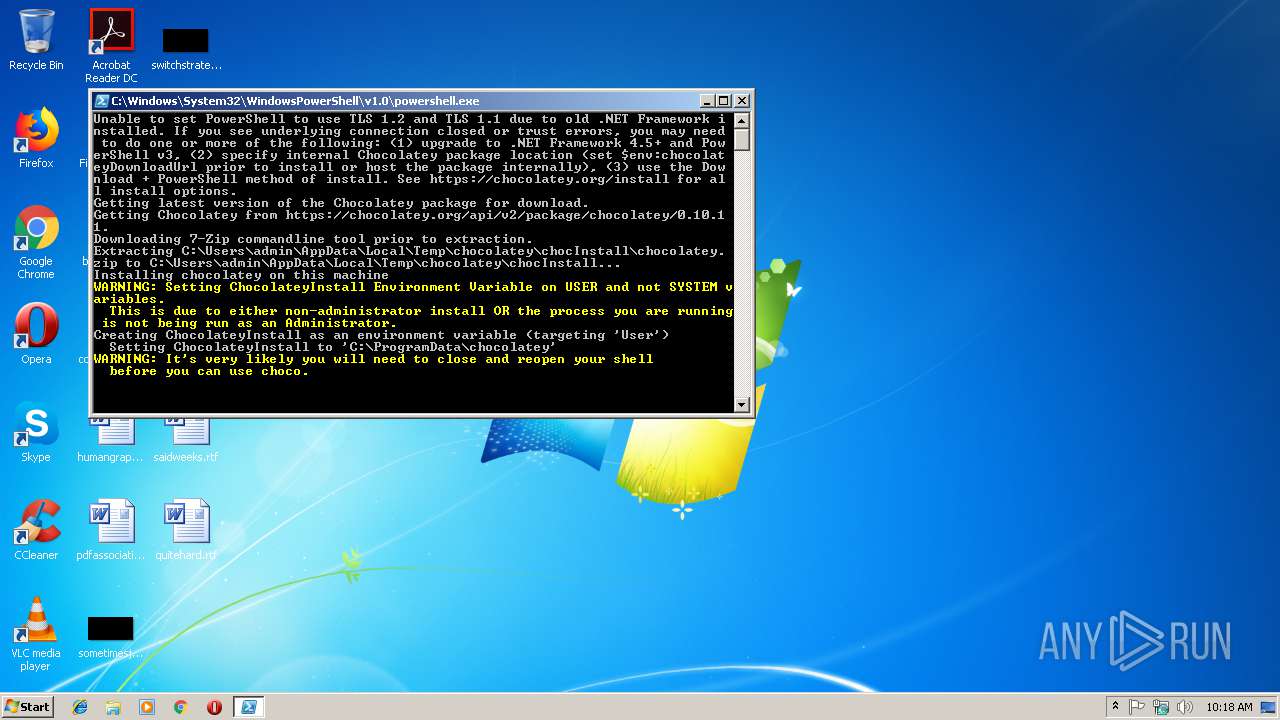
| 2980 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "-file" "C:\Users\admin\AppData\Local\Temp\install.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3192 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\6hxvuc00.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 3344 | "C:\Users\admin\AppData\Local\Temp\chocolatey\chocInstall\7za.exe" x -o"C:\Users\admin\AppData\Local\Temp\chocolatey\chocInstall" -bd -y "C:\Users\admin\AppData\Local\Temp\chocolatey\chocInstall\chocolatey.zip" | C:\Users\admin\AppData\Local\Temp\chocolatey\chocInstall\7za.exe | powershell.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Standalone Console Exit code: 0 Version: 18.06 Modules
| |||||||||||||||
Total events
310
Read events
227
Write events
83
Delete events
0
Modification events
| (PID) Process: | (2980) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2980) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2980) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2980) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2980) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2980) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2980) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2980) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2980) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2980) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
15
Suspicious files
3
Text files
66
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2980 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\MV7I2MK6QVUAVHQ2LDKE.temp | — | |
MD5:— | SHA256:— | |||
| 2980 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2980 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF20e6ca.TMP | binary | |
MD5:— | SHA256:— | |||
| 3344 | 7za.exe | C:\Users\admin\AppData\Local\Temp\chocolatey\chocInstall\tools\chocolateyInstall\LICENSE.txt | text | |
MD5:B4ECFC2FF4822CE40435ADA0A02D4EC5 | SHA256:A42AC97C0186E34BDC5F5A7D87D00A424754592F0EC80B522A872D630C1E870A | |||
| 3344 | 7za.exe | C:\Users\admin\AppData\Local\Temp\chocolatey\chocInstall\tools\chocolateyInstall\choco.exe.manifest | xml | |
MD5:0C06846A0B58120180B3FA54C52D9AF6 | SHA256:8572A153E3CDA20AC259E4F801CAD08858456F56CDFC17F913C35DDE51931134 | |||
| 3344 | 7za.exe | C:\Users\admin\AppData\Local\Temp\chocolatey\chocInstall\tools\chocolateyInstall\helpers\chocolateyInstaller.psm1 | text | |
MD5:C182F16ECA18063977C8884F5F45ADCD | SHA256:49D809792D9B2C48E62E5940830C6E5563104DB78AECAD36B6A29B17B84C9400 | |||
| 3344 | 7za.exe | C:\Users\admin\AppData\Local\Temp\chocolatey\chocInstall\tools\chocolateyInstall\helpers\ChocolateyTabExpansion.ps1 | text | |
MD5:1608021FB1C94705D142EDF7ABE91EE7 | SHA256:CD12832CA479E1B169AFBD5C42D5665B0C2C2A02E9723524A10E37FC53799AB8 | |||
| 2980 | powershell.exe | C:\Users\admin\AppData\Local\Temp\chocolatey\chocInstall\7za.exe | executable | |
MD5:2395868A72BFE1FD5E888B679FAAB621 | SHA256:8E679F87BA503F3DFAD96266CA79DE7BFE3092DC6A58C0FE0438F7D4B19F0BBD | |||
| 3344 | 7za.exe | C:\Users\admin\AppData\Local\Temp\chocolatey\chocInstall\tools\chocolateyInstall\choco.exe | executable | |
MD5:153D260471A77E4BED99282C2E99F415 | SHA256:56DE89FF2B4712B7515D333189782E4C3FC3EBCF9F4BABEC7D1D0DC586F7826D | |||
| 3344 | 7za.exe | C:\Users\admin\AppData\Local\Temp\chocolatey\chocInstall\tools\chocolateyInstall\helpers\chocolateyProfile.psm1 | text | |
MD5:2EA289F3706D1F59C2117D1124C167FE | SHA256:C3FA1CEE842F8DAED2743BB761EA9F344AC0714F75C25CF7280C4EC90AAE0979 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2980 | powershell.exe | 104.20.73.28:443 | chocolatey.org | Cloudflare Inc | US | shared |
2980 | powershell.exe | 104.20.74.28:443 | chocolatey.org | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
chocolatey.org |
| whitelisted |
packages.chocolatey.org |
| suspicious |
Threats
Process | Message |
|---|---|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|