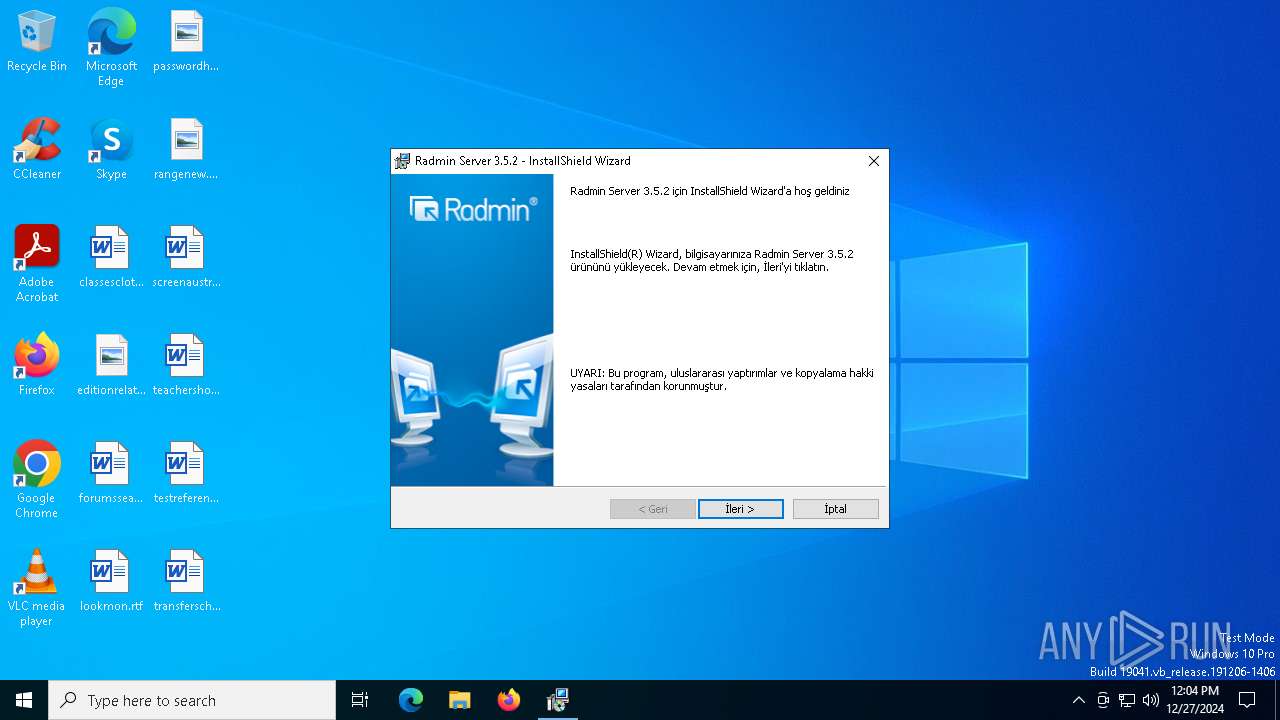
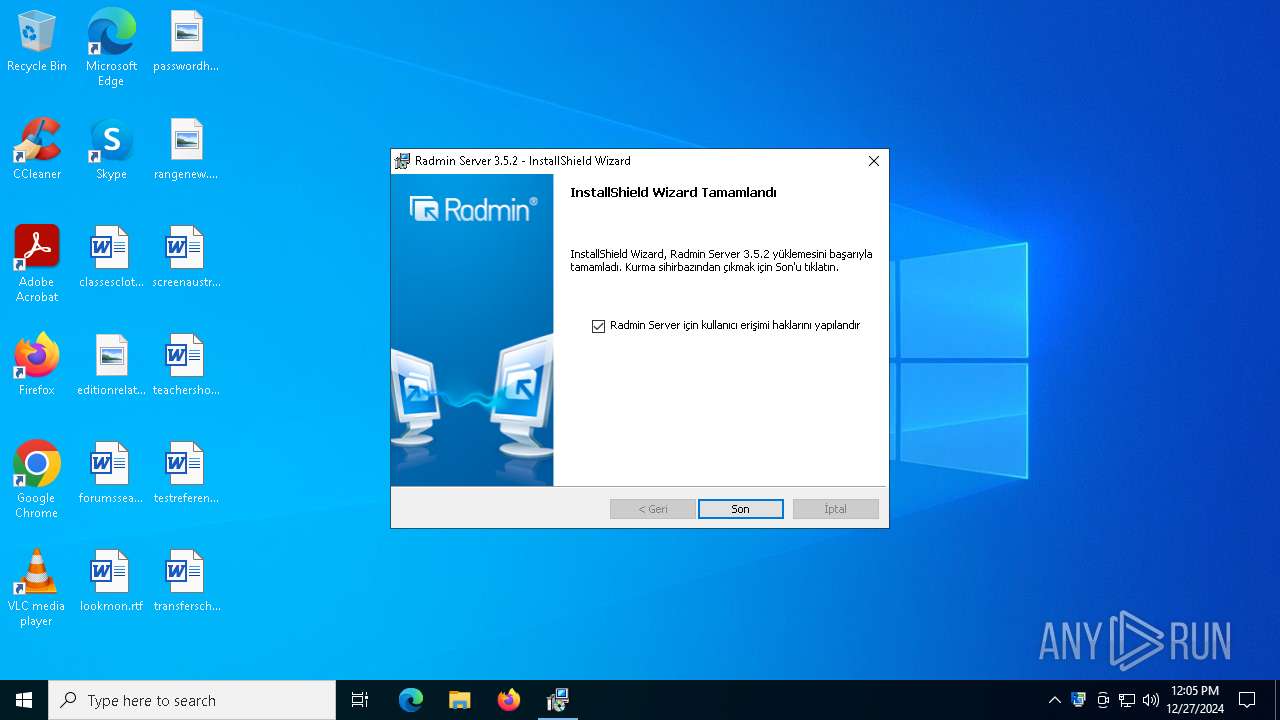
| File name: | Radmin_Server_3.5.2.1_TR.msi |
| Full analysis: | https://app.any.run/tasks/dac466f1-d9de-4125-a590-f6c900c17acd |
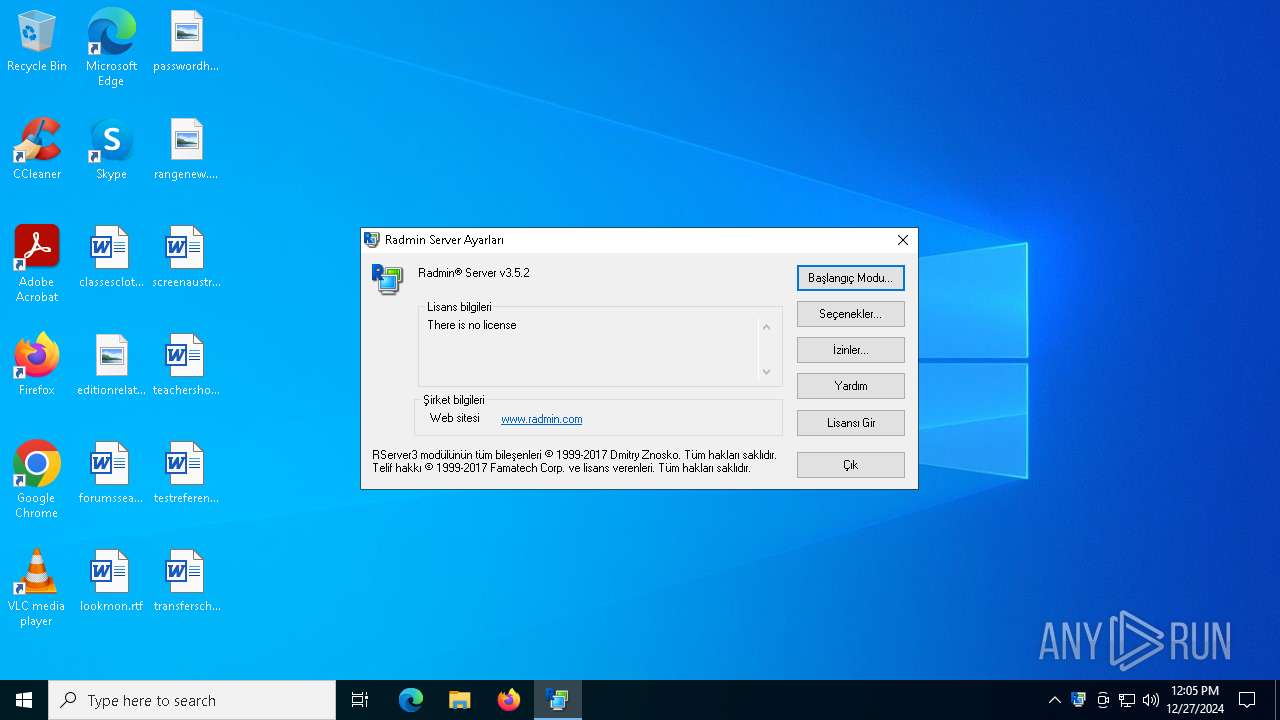
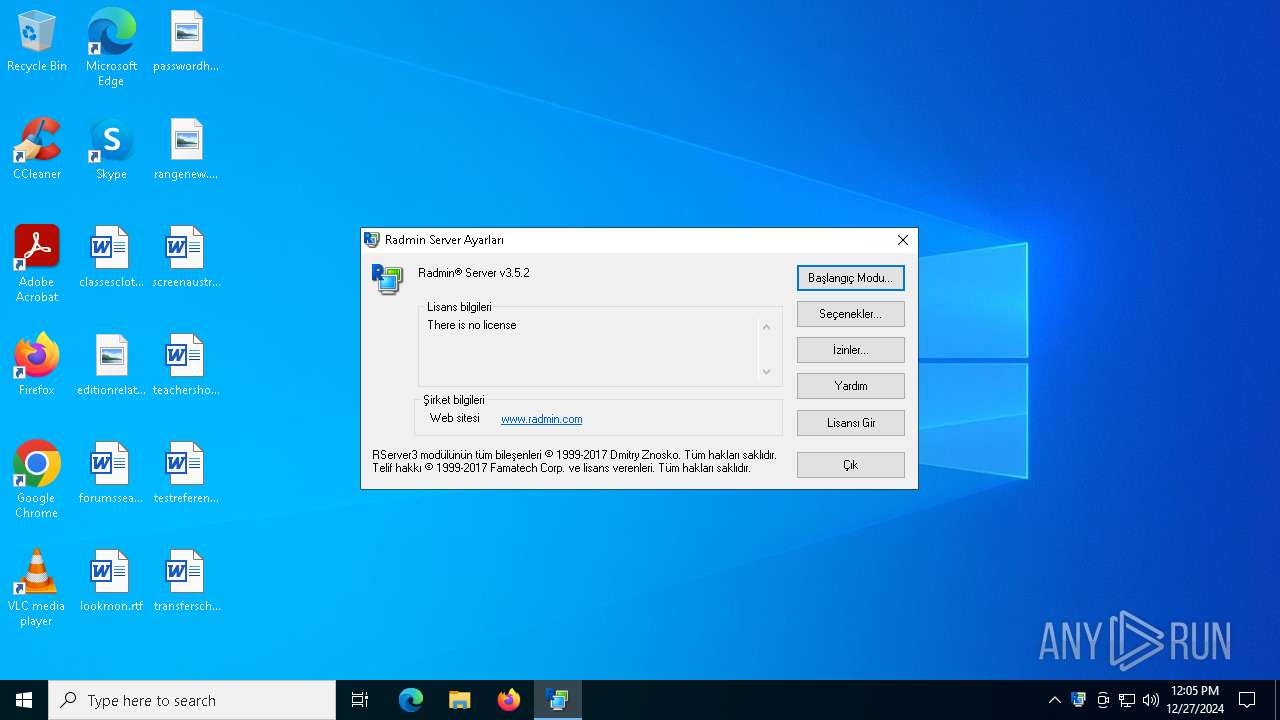
| Verdict: | Malicious activity |
| Analysis date: | December 27, 2024, 12:04:42 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
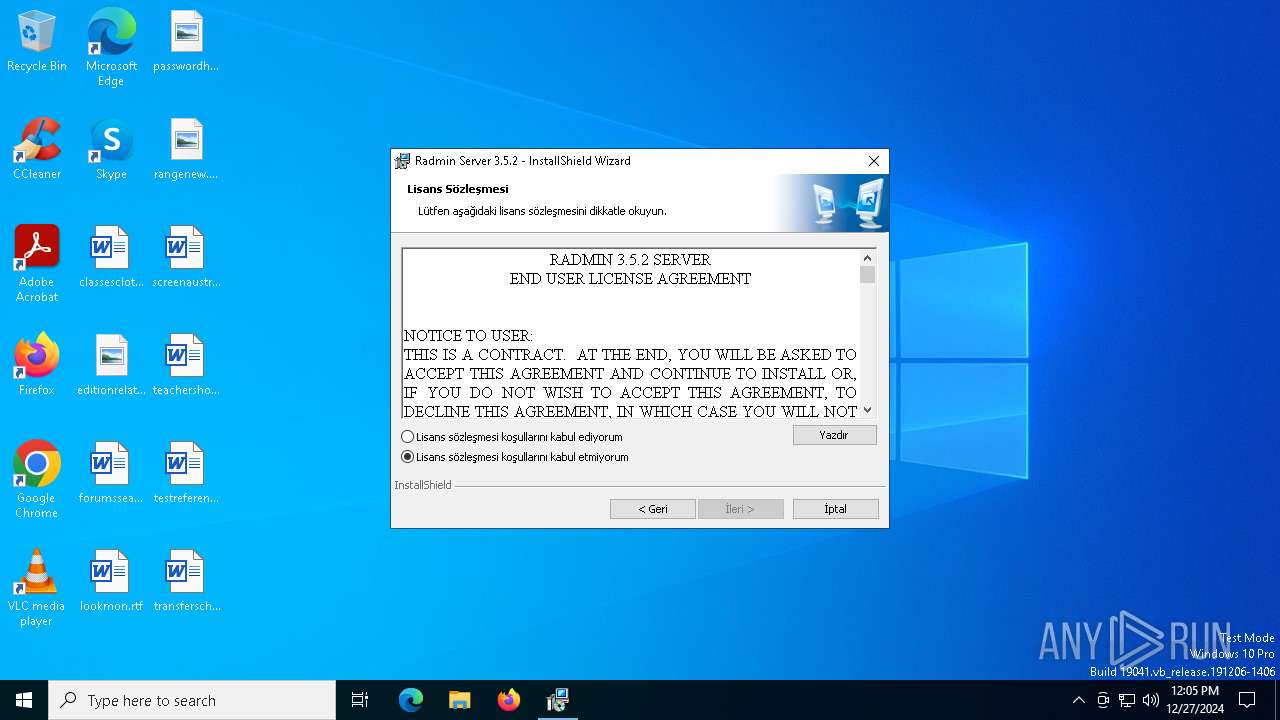
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 5.1, MSI Installer, Number of Characters: 0, Last Saved By: DavidHacker, Number of Words: 0, Title: Radmin Server 3.5.2 installation package, Comments: This installer contains the logic and data to install Radmin Server 3.5.2, Keywords: Installer,MSI,Database, Subject: Radmin Server 3.5.2, Author: Famatech, Security: 1, Number of Pages: 200, Name of Creating Application: InstallShield 12 - Professional Edition 12.0, Revision Number: {BBD285CD-D1FE-41B1-B6B4-7FF7C27F553B}, Last Saved Time/Date: Wed Dec 13 16:08:14 2017, Create Time/Date: Wed Dec 13 16:08:14 2017, Last Printed: Wed Dec 13 16:08:14 2017, Code page: 0, Template: Intel;0,1033,1055 |
| MD5: | 9A14B8E426B250D6C7797892A0AED985 |
| SHA1: | E0FE3A2ADE1F6A87C60D0329DDAE2E5EAC4BB0A1 |
| SHA256: | 1CD6BC002A26C123A2FEC9AEE003662C7FF8C59CFFEFE2E206C9F4F6A98B0D9F |
| SSDEEP: | 98304:B9SUrrdPPZbRNzIUecrlxJbEU61rSrublFAXURchw2B24BanMI8r7m6e0SZqw77H:w7kD8DbeSM1y |
MALICIOUS
Executing a file with an untrusted certificate
- rsetup64.exe (PID: 3688)
- rsetup64.exe (PID: 6876)
- rsl.exe (PID: 1480)
- rserver3.exe (PID: 4980)
SUSPICIOUS
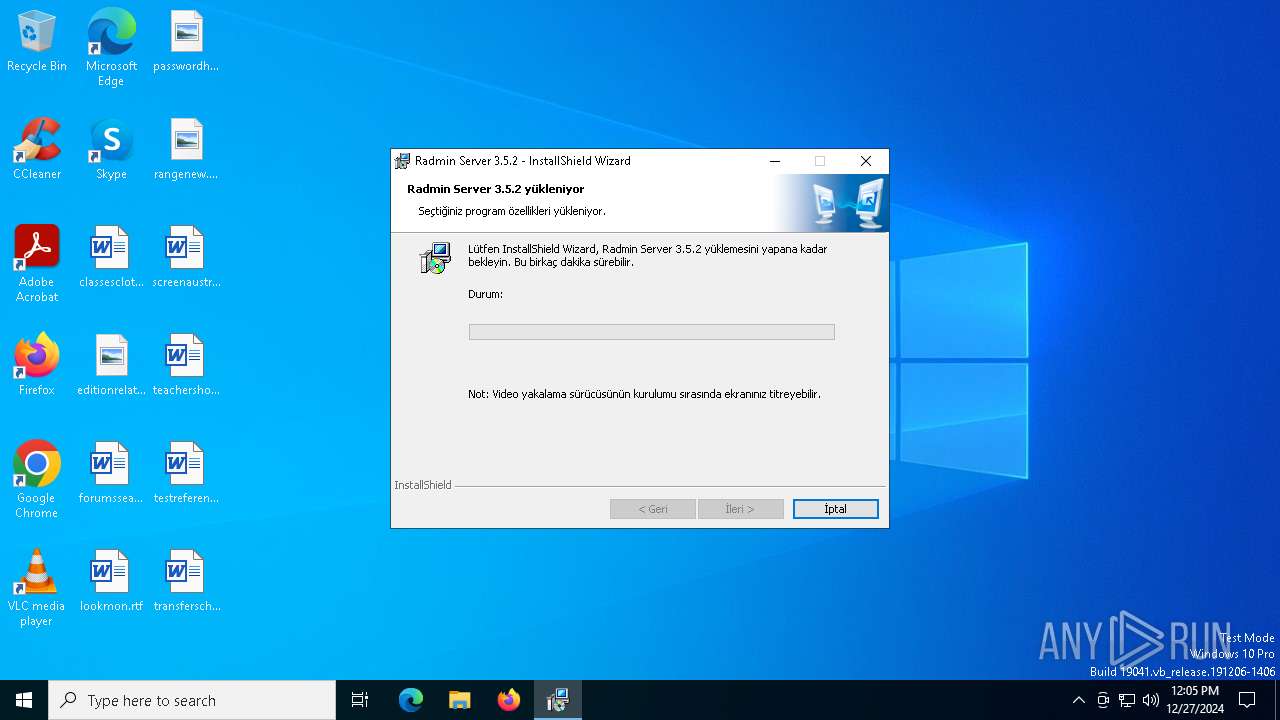
Process drops legitimate windows executable
- msiexec.exe (PID: 6832)
- msiexec.exe (PID: 6792)
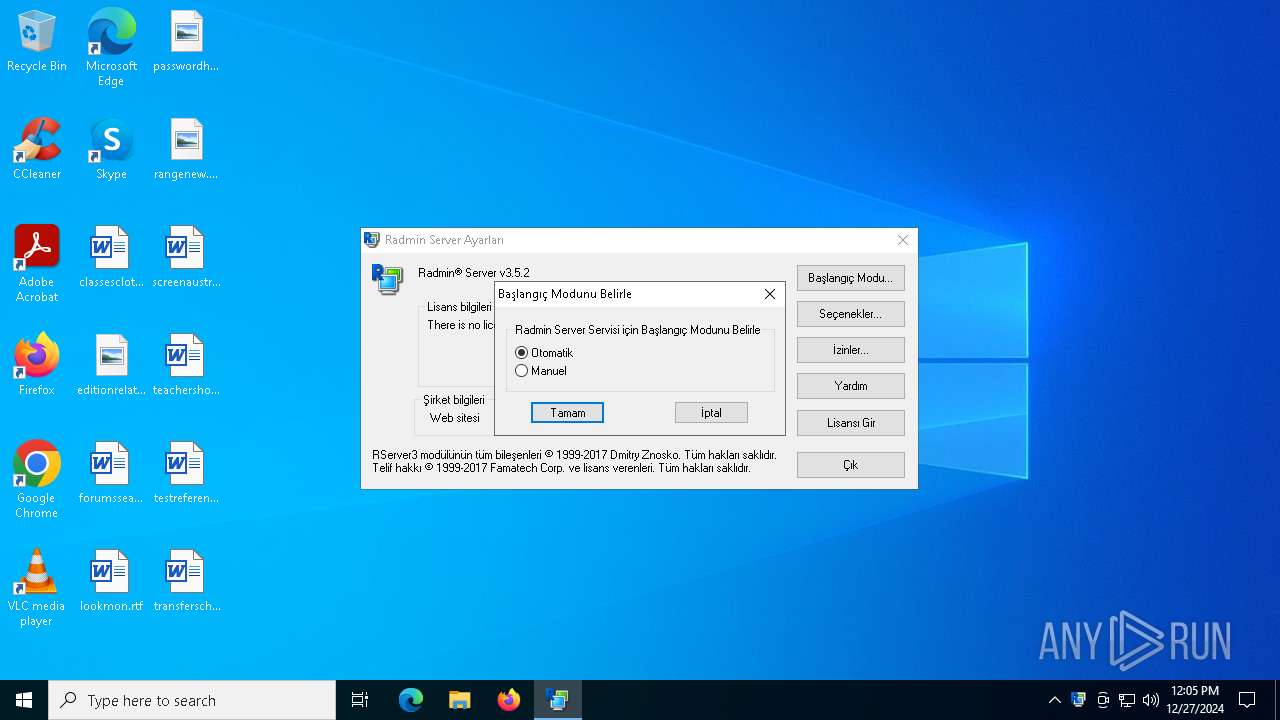
Executes as Windows Service
- VSSVC.exe (PID: 6184)
- rserver3.exe (PID: 4980)
Checks Windows Trust Settings
- msiexec.exe (PID: 6792)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 6792)
Drops a system driver (possible attempt to evade defenses)
- msiexec.exe (PID: 6792)
Uses NETSH.EXE to add a firewall rule or allowed programs
- msiexec.exe (PID: 5628)
Application launched itself
- FamItrfc.Exe (PID: 7064)
INFO
Creates files or folders in the user directory
- msiexec.exe (PID: 6576)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 6576)
An automatically generated document
- msiexec.exe (PID: 6576)
Reads the software policy settings
- msiexec.exe (PID: 6576)
- msiexec.exe (PID: 6792)
Checks supported languages
- msiexec.exe (PID: 6792)
- msiexec.exe (PID: 6832)
- msiexec.exe (PID: 4076)
- msiexec.exe (PID: 5240)
- msiexec.exe (PID: 5628)
- rsetup64.exe (PID: 3688)
- rsetup64.exe (PID: 6876)
- rsetup64.exe (PID: 6972)
- rserver3.exe (PID: 4980)
- FamItrfc.Exe (PID: 3836)
- rsl.exe (PID: 1480)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6576)
- msiexec.exe (PID: 6832)
- msiexec.exe (PID: 6792)
Reads the computer name
- msiexec.exe (PID: 6832)
- msiexec.exe (PID: 6792)
- msiexec.exe (PID: 4076)
- msiexec.exe (PID: 5628)
- rsetup64.exe (PID: 3688)
- rsetup64.exe (PID: 6876)
- rsetup64.exe (PID: 6972)
- rserver3.exe (PID: 4980)
- FamItrfc.Exe (PID: 3836)
The sample compiled with english language support
- msiexec.exe (PID: 6832)
- msiexec.exe (PID: 6576)
- msiexec.exe (PID: 6792)
Create files in a temporary directory
- msiexec.exe (PID: 6832)
Manages system restore points
- SrTasks.exe (PID: 3988)
Reads the machine GUID from the registry
- msiexec.exe (PID: 6792)
- rserver3.exe (PID: 4980)
Application launched itself
- msiexec.exe (PID: 6792)
The sample compiled with russian language support
- msiexec.exe (PID: 6792)
Creates a software uninstall entry
- msiexec.exe (PID: 6792)
Sends debugging messages
- rserver3.exe (PID: 4980)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (88.6) |
|---|---|---|
| .mst | | | Windows SDK Setup Transform Script (10) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| Characters: | - |
|---|---|
| LastModifiedBy: | DavidHacker |
| Words: | - |
| Title: | Radmin Server 3.5.2 installation package |
| Comments: | This installer contains the logic and data to install Radmin Server 3.5.2 |
| Keywords: | Installer,MSI,Database |
| Subject: | Radmin Server 3.5.2 |
| Author: | Famatech |
| Security: | Password protected |
| Pages: | 200 |
| Software: | InstallShield? 12 - Professional Edition 12.0 |
| RevisionNumber: | {BBD285CD-D1FE-41B1-B6B4-7FF7C27F553B} |
| ModifyDate: | 2017:12:13 16:08:14 |
| CreateDate: | 2017:12:13 16:08:14 |
| LastPrinted: | 2017:12:13 16:08:14 |
| CodePage: | Unknown (0) |
| Template: | Intel;0,1033,1055 |
Total processes
147
Monitored processes
20
Malicious processes
2
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1480 | C:\WINDOWS\SysWOW64\rserver30\rsl.exe /setup | C:\Windows\SysWOW64\rserver30\rsl.exe | — | msiexec.exe | |||||||||||
User: admin Company: Famatech Corp. Integrity Level: MEDIUM Description: Radmin Server component Version: 3, 5, 2, 0 | |||||||||||||||
| 1804 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3524 | "C:\Windows\SysWOW64\rserver30\rserver3.exe" /setup | C:\Windows\SysWOW64\rserver30\rserver3.exe | — | rsl.exe | |||||||||||
User: admin Company: Famatech Corp. Integrity Level: MEDIUM Description: Radmin Server Exit code: 3221226540 Version: 3, 5, 2, 0 | |||||||||||||||
| 3688 | "C:\Users\admin\AppData\Local\Temp\{1B704FD1-C00F-482F-8997-82F2F19E10E7}\rsetup64.exe" /stop | C:\Users\admin\AppData\Local\Temp\{1B704FD1-C00F-482F-8997-82F2F19E10E7}\rsetup64.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Famatech Corp. Integrity Level: SYSTEM Description: Radmin Setup Helper Exit code: 1 Version: 3, 5, 2, 0 Modules
| |||||||||||||||
| 3836 | "C:\WINDOWS\SysWOW64\rserver30\FamItrfc.Exe" | C:\Windows\SysWOW64\rserver30\FamItrfc.Exe | — | FamItrfc.Exe | |||||||||||
User: admin Company: Famatech Corp. Integrity Level: UNKNOWN Description: Radmin component Version: 3,5,2,1205 Modules
| |||||||||||||||
| 3988 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4076 | C:\Windows\syswow64\MsiExec.exe -Embedding 069DB974345045724405F9D84FBAE0AB | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4980 | "C:\WINDOWS\SysWOW64\rserver30\RServer3.exe" /service | C:\Windows\SysWOW64\rserver30\rserver3.exe | services.exe | ||||||||||||
User: SYSTEM Company: Famatech Corp. Integrity Level: SYSTEM Description: Radmin Server Version: 3, 5, 2, 0 Modules
| |||||||||||||||
| 5240 | C:\Windows\System32\MsiExec.exe -Embedding AEBFBEF2CB28E32C73CBADF32C98956B | C:\Windows\System32\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5628 | C:\Windows\syswow64\MsiExec.exe -Embedding AEAAF50623389BEEBB6E55A2DD515E36 E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
11 033
Read events
10 671
Write events
345
Delete events
17
Modification events
| (PID) Process: | (6792) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 480000000000000073834F965758DB01881A00000C180000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6792) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 480000000000000073834F965758DB01881A00000C180000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6792) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 48000000000000004DD69B965758DB01881A00000C180000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6792) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 48000000000000004DD69B965758DB01881A00000C180000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6792) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4800000000000000A589A0965758DB01881A00000C180000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6792) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 480000000000000037399E965758DB01881A00000C180000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6792) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (6792) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000462B1A975758DB01881A00002C1A0000E803000001000000000000000000000032D0439DE323F64CAC546B49255B0E6000000000000000000000000000000000 | |||
| (PID) Process: | (6184) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000151526975758DB0128180000D0180000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6184) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000E47828975758DB01281800009C190000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
46
Suspicious files
25
Text files
4
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6792 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 6792 | msiexec.exe | C:\Windows\Installer\140a7e.msi | — | |
MD5:— | SHA256:— | |||
| 6576 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\40C68D5626484A90937F0752C8B950AB | binary | |
MD5:EDAA2F0B5A167ADDFEB4A6DCCBE2699B | SHA256:9096B0599FD521808F0ECCC39A38FFA437E7751D51F2DA09BADF41B3EF000BFD | |||
| 6576 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI6B31.tmp | executable | |
MD5:4A908EE9C6F2F4AAD63382CCCEE731E4 | SHA256:459F503FB8B4FC4A600261430AC77BF70118D41FA19F7B2620D43BA6E9C8FA5E | |||
| 6576 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EA618097E393409AFA316F0F87E2C202_6D6BF469D0BDEA697BA93FFAF1E0C5EA | binary | |
MD5:5BFA51F3A417B98E7443ECA90FC94703 | SHA256:BEBE2853A3485D1C2E5C5BE4249183E0DDAFF9F87DE71652371700A89D937128 | |||
| 6792 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{9d43d032-23e3-4cf6-ac54-6b49255b0e60}_OnDiskSnapshotProp | binary | |
MD5:1BF83FE0189028E883CC9EDC44DA9434 | SHA256:DE475541C1A4C50B65BB62C5DA3962AB8D3284E3D9A9A7C2076437B8C86DD1B8 | |||
| 6576 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\ECF3006D44DA211141391220EE5049F4 | binary | |
MD5:77FC2FBE482F494C80CB65CD2875979E | SHA256:32667FC056BFB9041A02874D8AFE7184FE18A5D3158D44B15B79250B319A6D80 | |||
| 6832 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\{1B704FD1-C00F-482F-8997-82F2F19E10E7}\FirewallInstallHelper.dll | executable | |
MD5:6BCDFEB8F72D04FE3DB2967EDCD9BFA5 | SHA256:48B5A9B9DDE94D25B4121489735FE5A94738A1DCDF7A33DDFABB9CBFFD66BA7F | |||
| 6576 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI6C4B.tmp | executable | |
MD5:ABB81F7897BB48A036686CCF840287AE | SHA256:9DC871199CC9E96067A32401D225AF50683AC14EFAF35EDC61AA45F346374494 | |||
| 6832 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\{1B704FD1-C00F-482F-8997-82F2F19E10E7}\rsetup.exe | executable | |
MD5:500DAE8E966486D84F7AFB21870B64CA | SHA256:5911DE9F97E664822FA3DCF485D3F1C5D5FE8FAC041C9BD07BE724884D6FD0FD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
37
DNS requests
21
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6576 | msiexec.exe | GET | 200 | 152.199.19.74:80 | http://s2.symcb.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCED141%2Fl2SWCyYX308B7Khio%3D | unknown | — | — | whitelisted |
6576 | msiexec.exe | GET | 200 | 152.199.19.74:80 | http://s2.symcb.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCED141%2Fl2SWCyYX308B7Khio%3D | unknown | — | — | whitelisted |
6576 | msiexec.exe | GET | 200 | 192.229.221.95:80 | http://s1.symcb.com/pca3-g5.crl | unknown | — | — | whitelisted |
6576 | msiexec.exe | GET | 200 | 152.199.19.74:80 | http://sv.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQe6LNDJdqx%2BJOp7hVgTeaGFJ%2FCQgQUljtT8Hkzl699g%2B8uK8zKt4YecmYCEGqlk0afvjzQyYSvvrtcLpI%3D | unknown | — | — | unknown |
6576 | msiexec.exe | GET | 200 | 152.199.19.74:80 | http://sv.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQe6LNDJdqx%2BJOp7hVgTeaGFJ%2FCQgQUljtT8Hkzl699g%2B8uK8zKt4YecmYCEGqlk0afvjzQyYSvvrtcLpI%3D | unknown | — | — | unknown |
6576 | msiexec.exe | GET | 200 | 192.229.221.95:80 | http://sv.symcb.com/sv.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5448 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 2.23.209.149:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1176 | svchost.exe | 40.126.31.67:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1076 | svchost.exe | 184.28.89.167:443 | go.microsoft.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| unknown |
s2.symcb.com |
| whitelisted |
s1.symcb.com |
| whitelisted |
Threats
Process | Message |
|---|---|
rserver3.exe | %n%n%n%n%n%n%n%n%n |