| File name: | vibranceGUI.exe |
| Full analysis: | https://app.any.run/tasks/50308169-1248-469c-8cf2-3d0edf0d8654 |
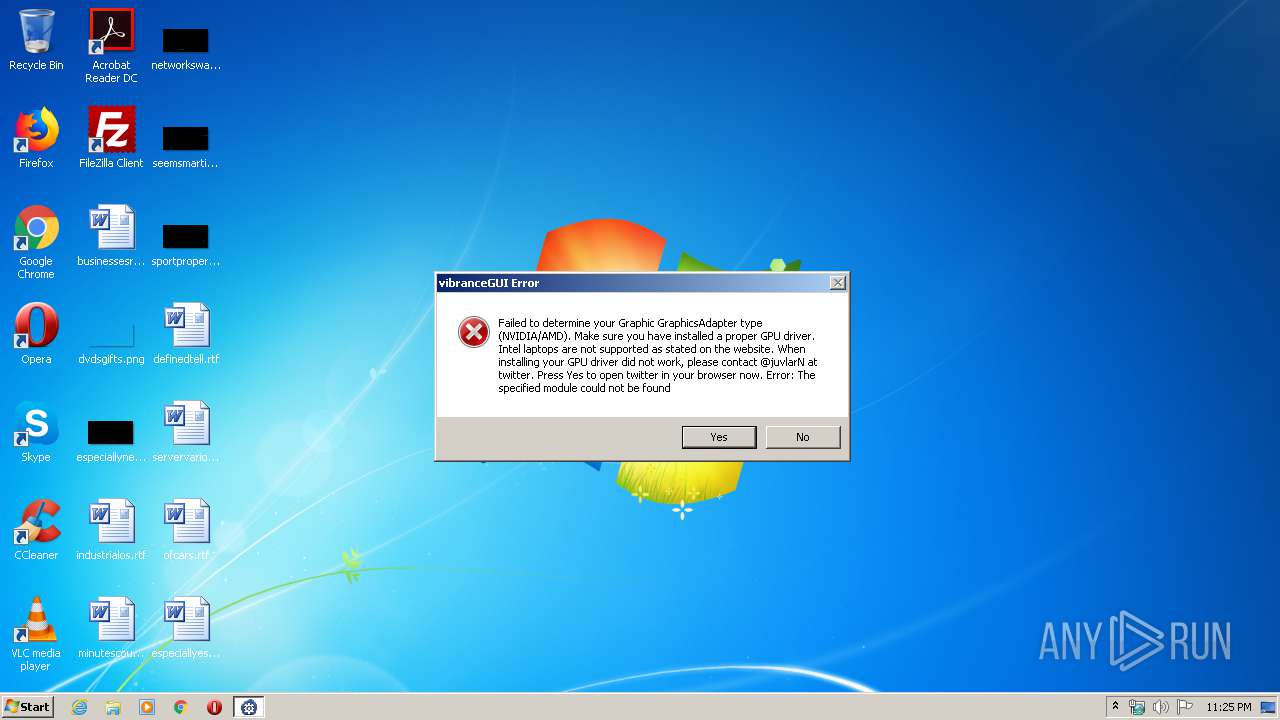
| Verdict: | Malicious activity |
| Analysis date: | March 30, 2020, 22:25:37 |
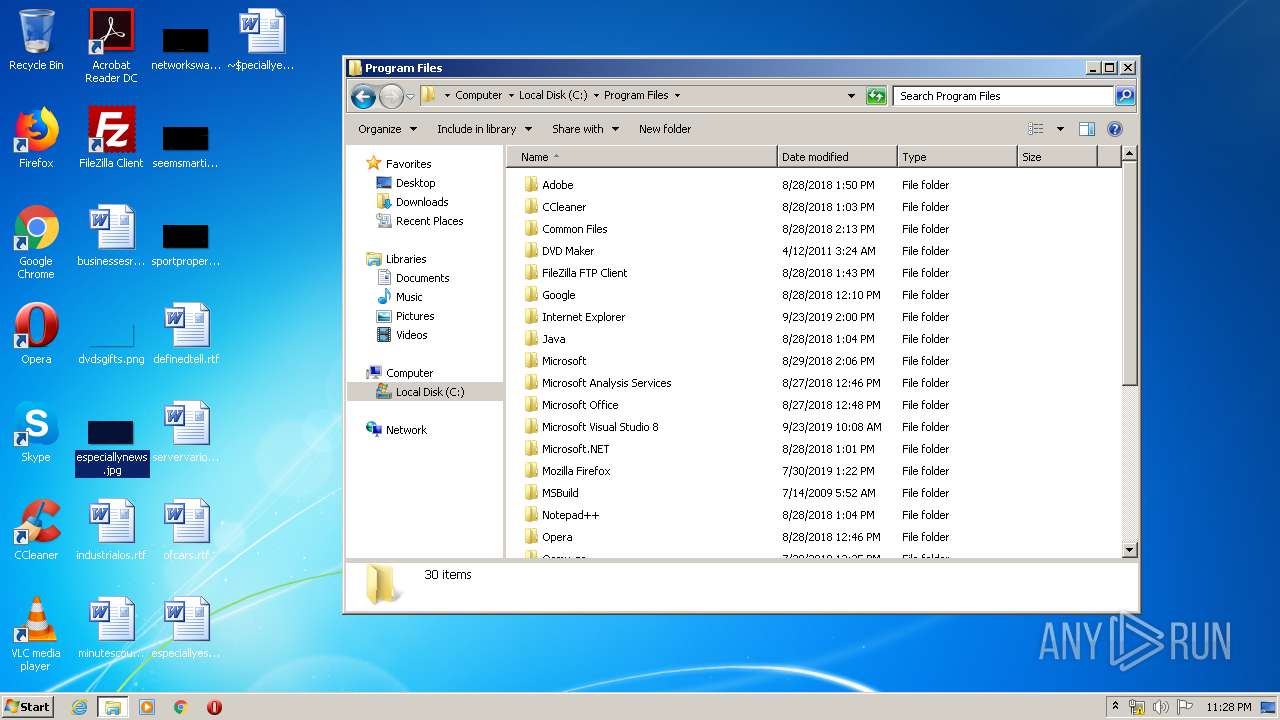
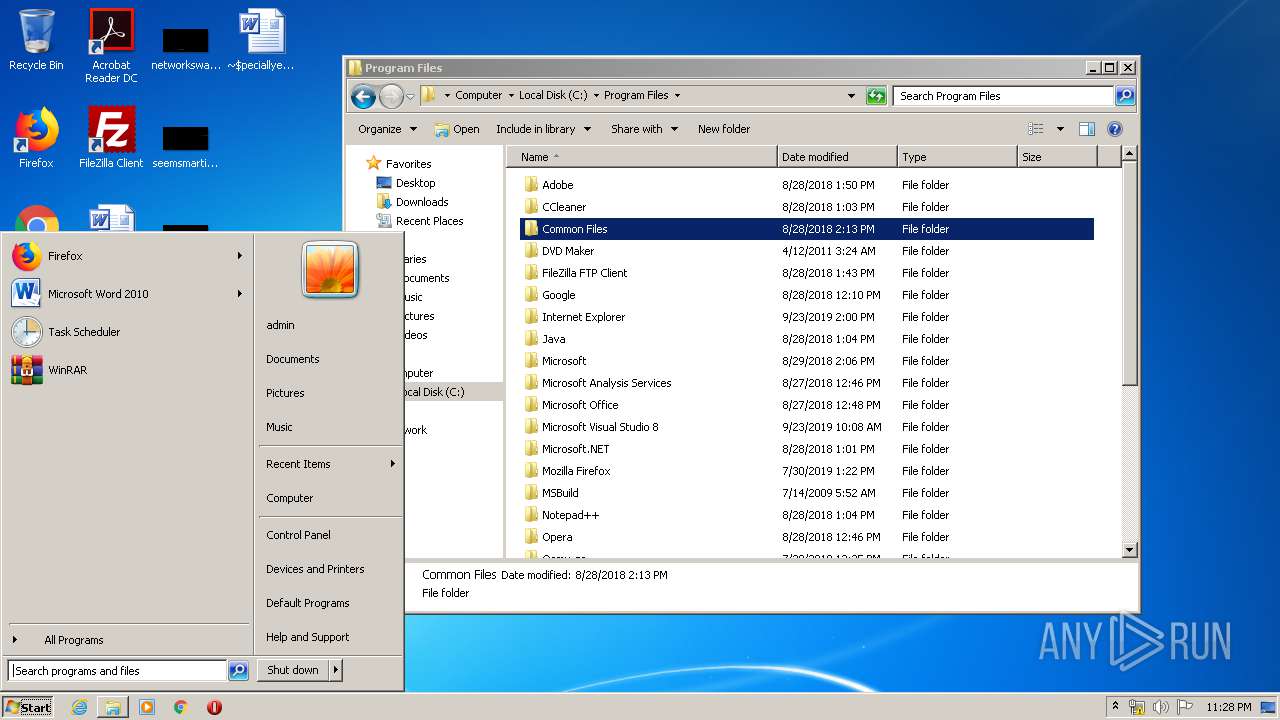
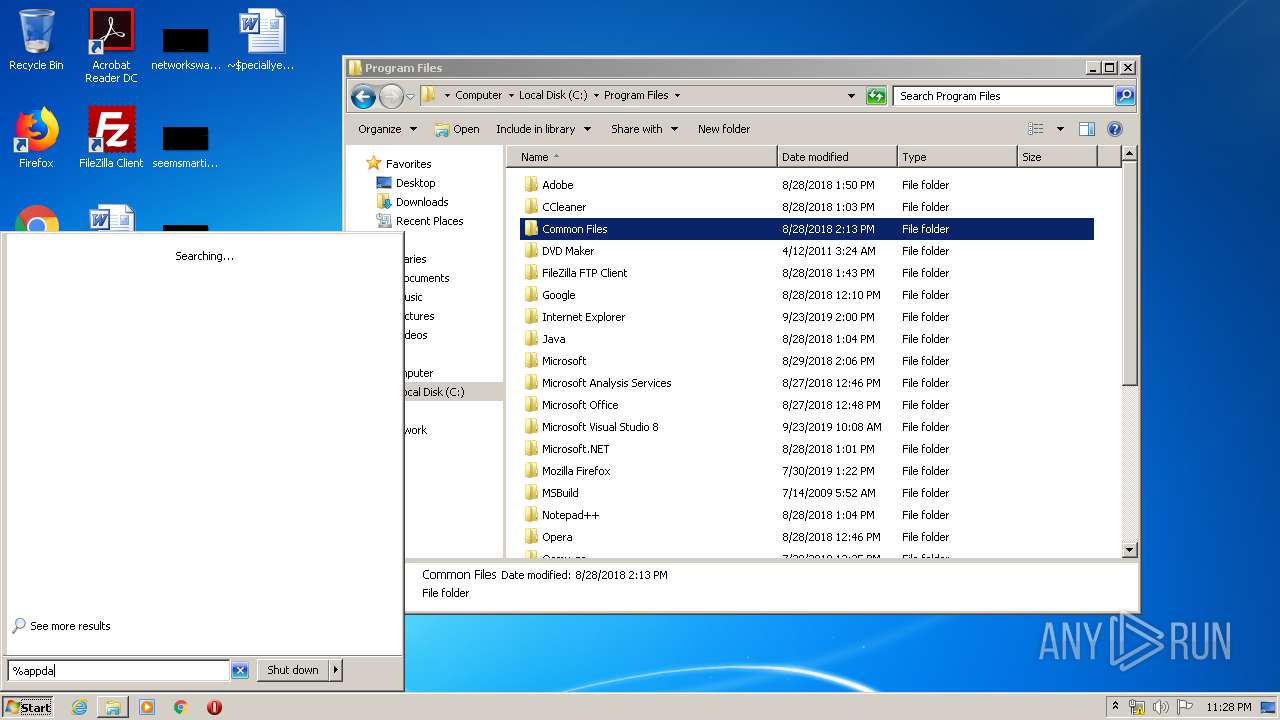
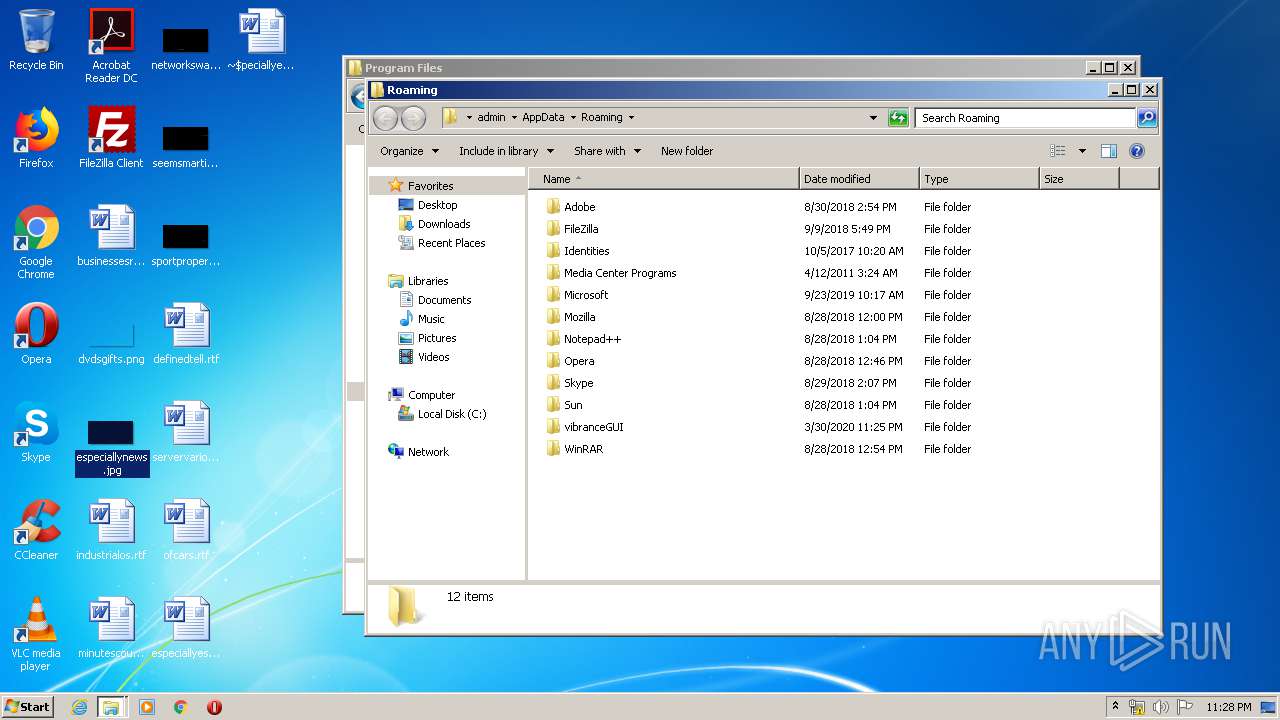
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 6CC583A1F3F4500A524B61255F1D2710 |
| SHA1: | 7C1A236E291746B781AEF5DAFBCDEFA648F36357 |
| SHA256: | 1CBAA4D4C817743A7EC88BDC3F8D15200E543A86E0B3374C6D05A15A0762970F |
| SSDEEP: | 6144:LPaQf/VaGtX5RlJxeR2CoDnpYRkIE3IRv7I1:LPrHVaGtXV6RToNYRkh4t4 |
MALICIOUS
No malicious indicators.SUSPICIOUS
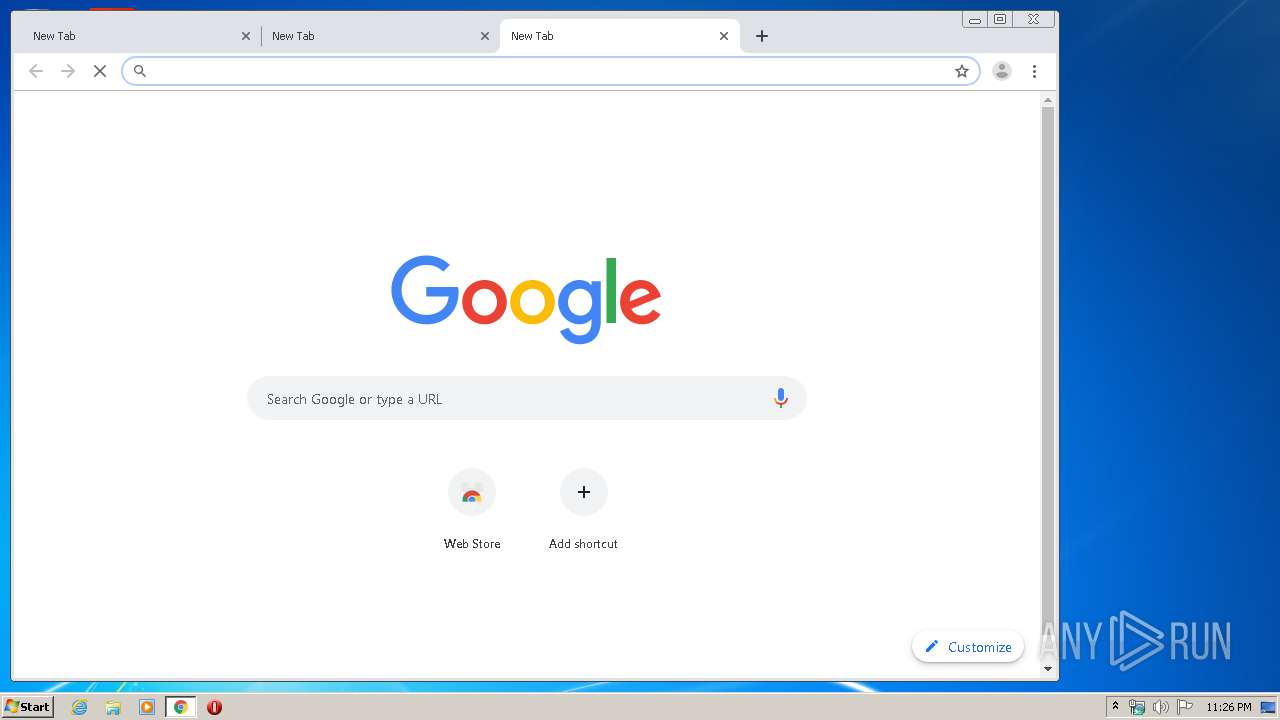
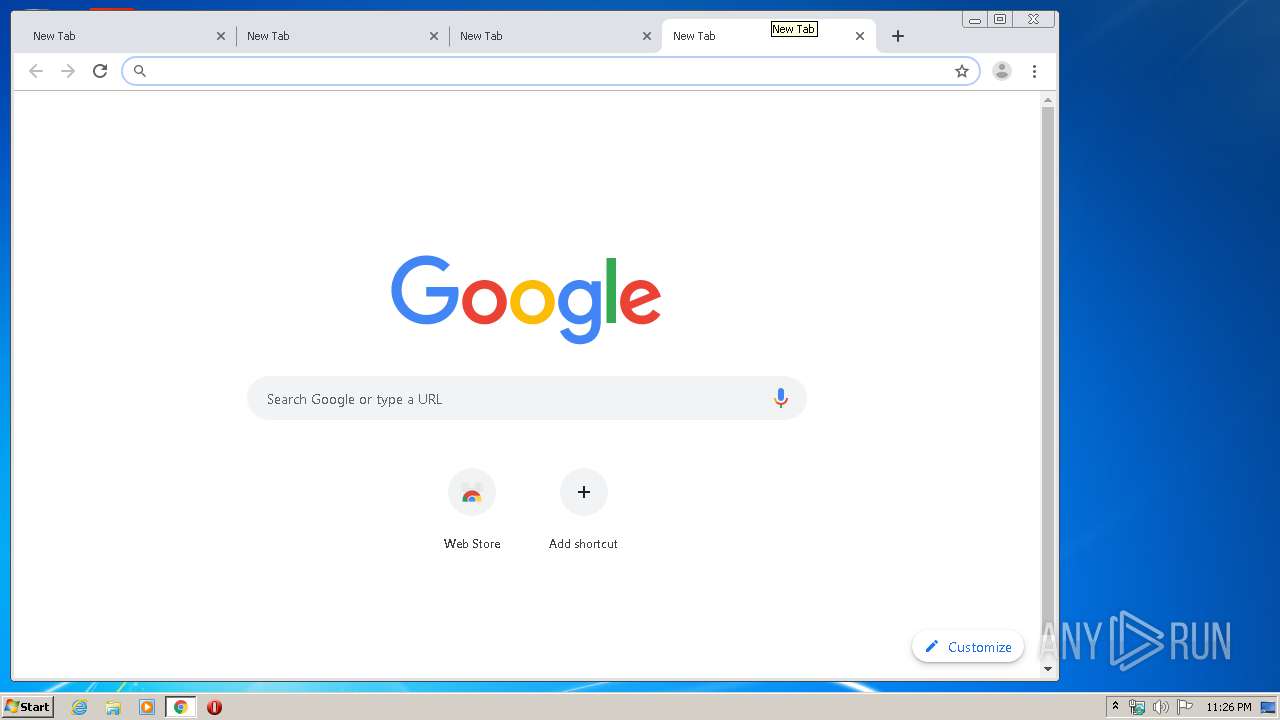
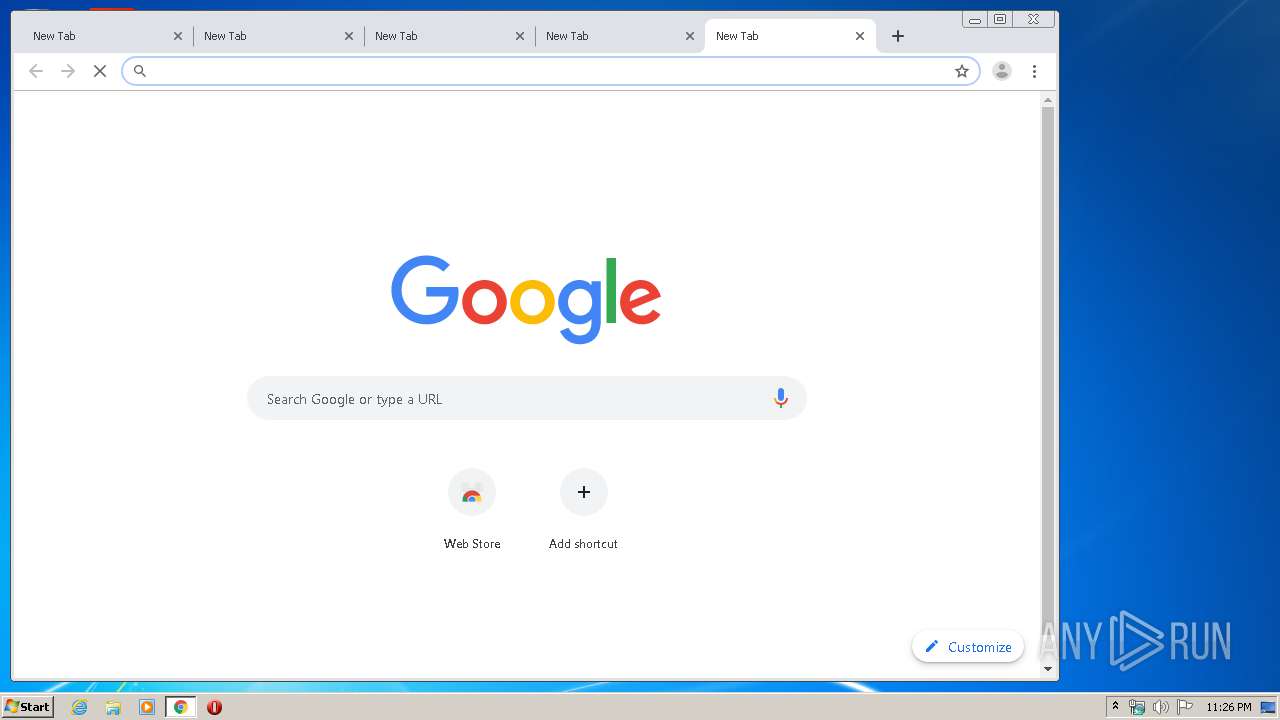
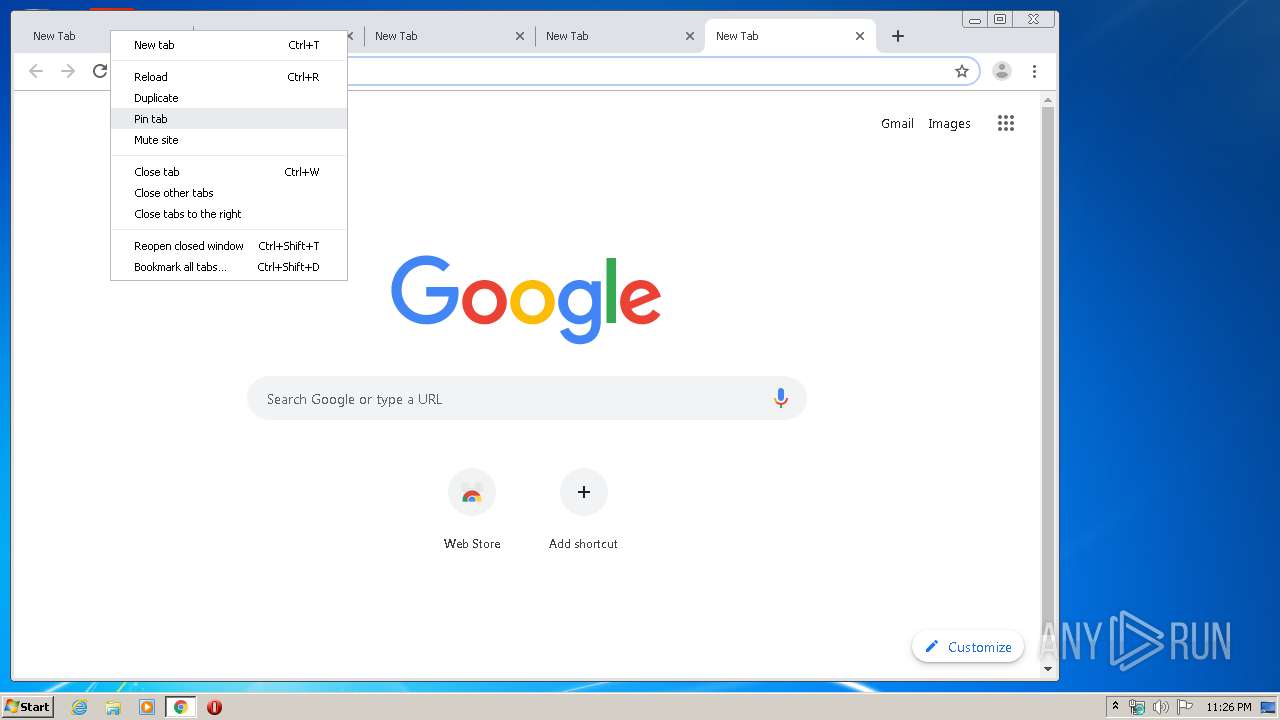
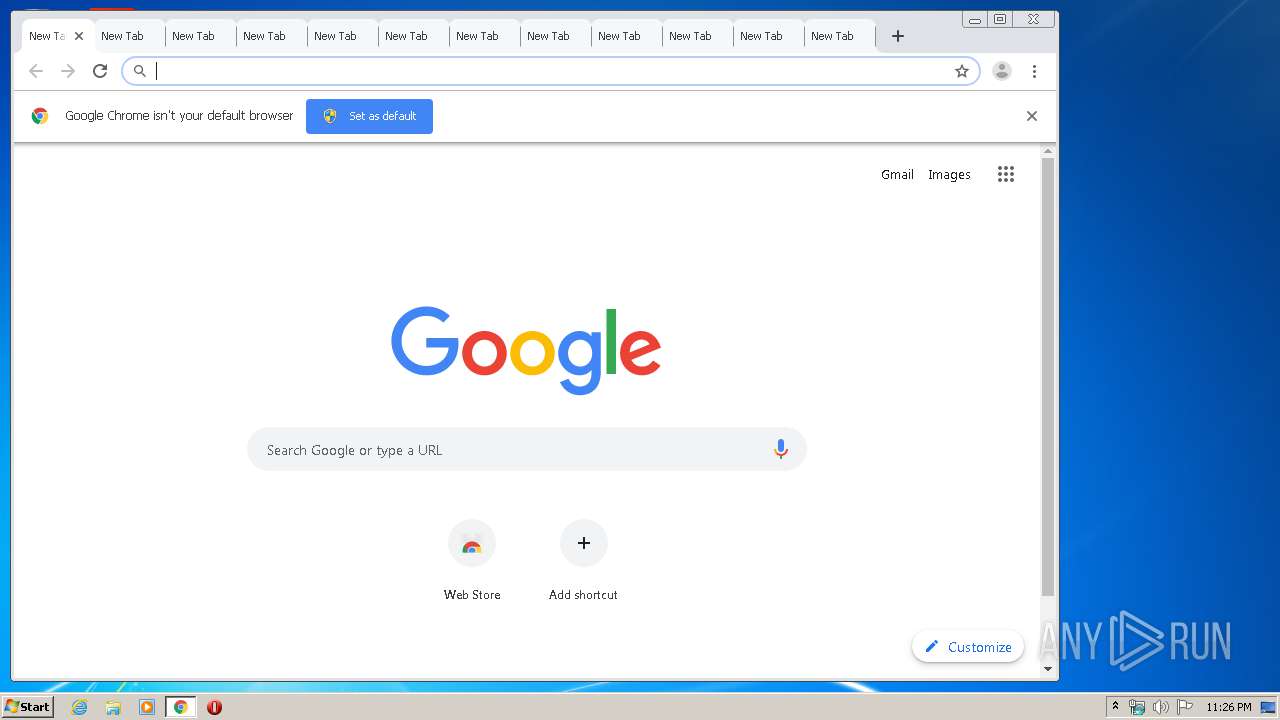
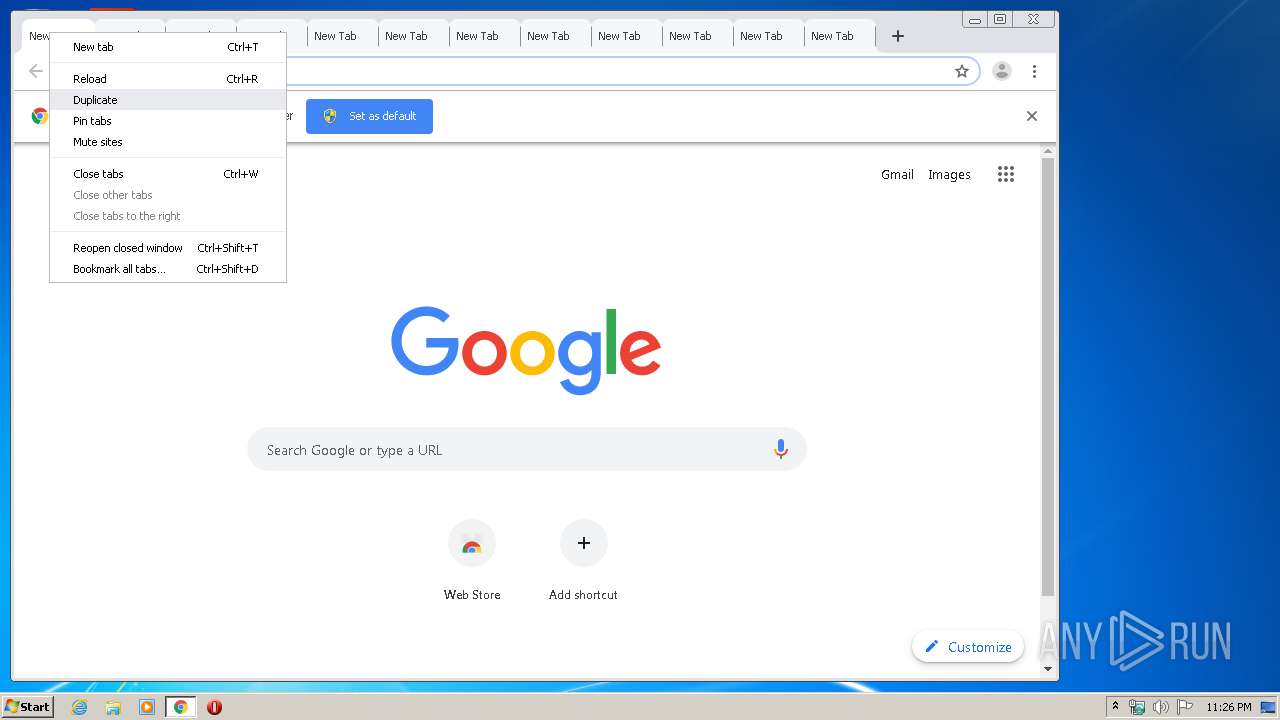
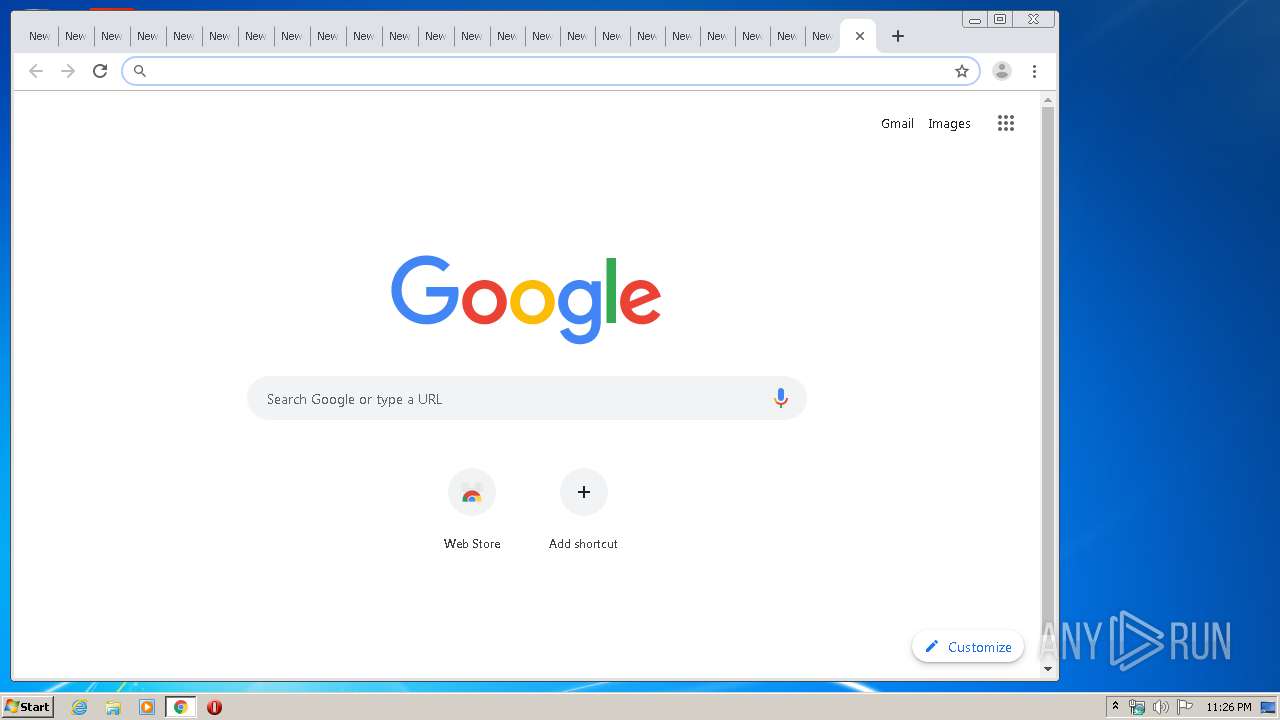
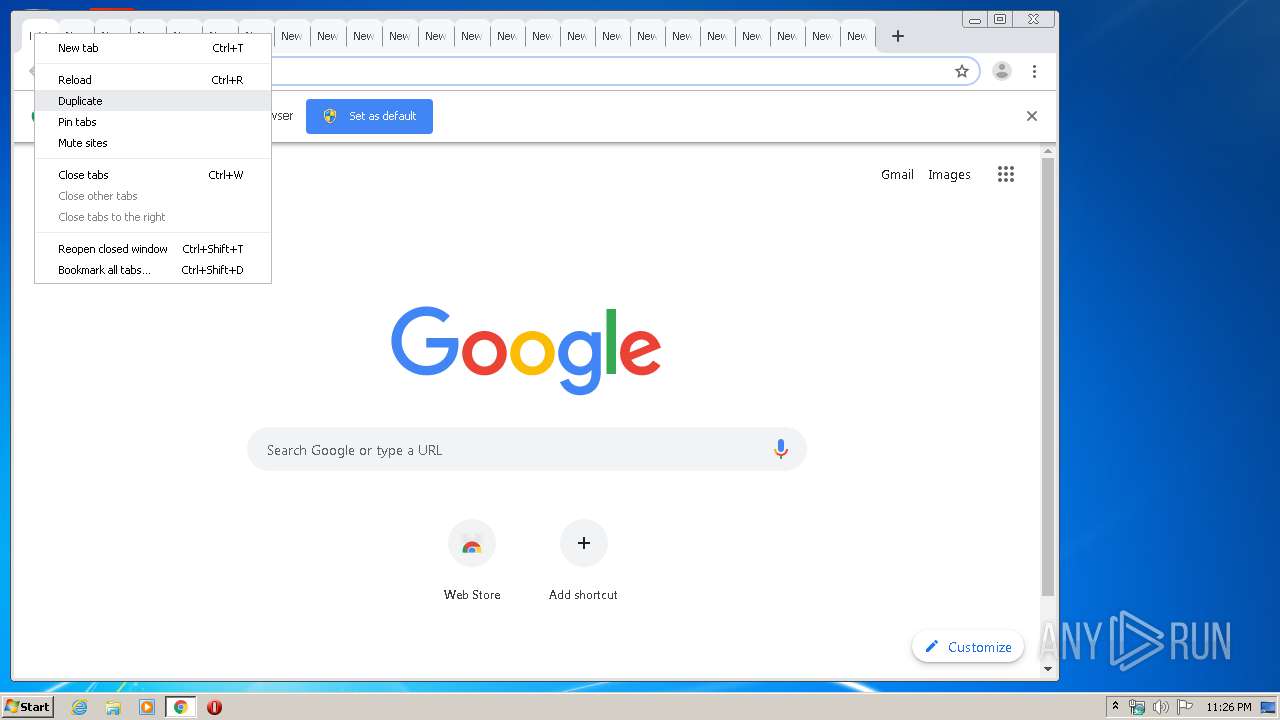
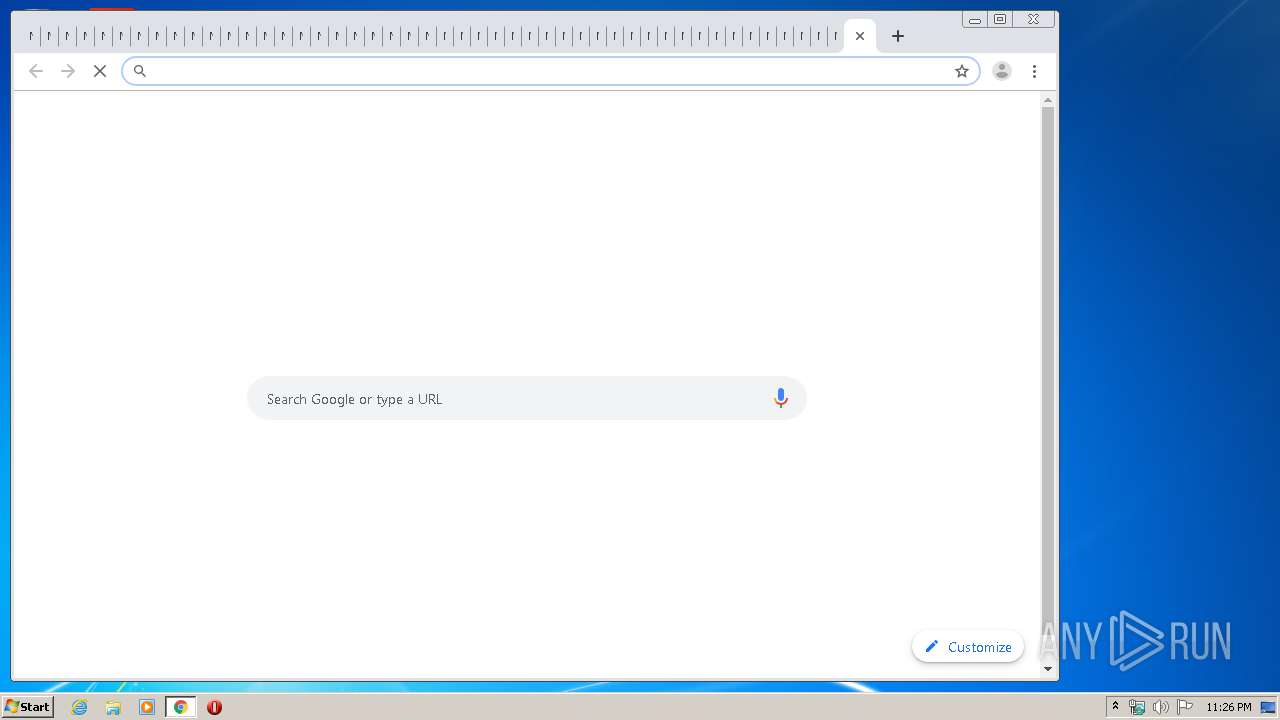
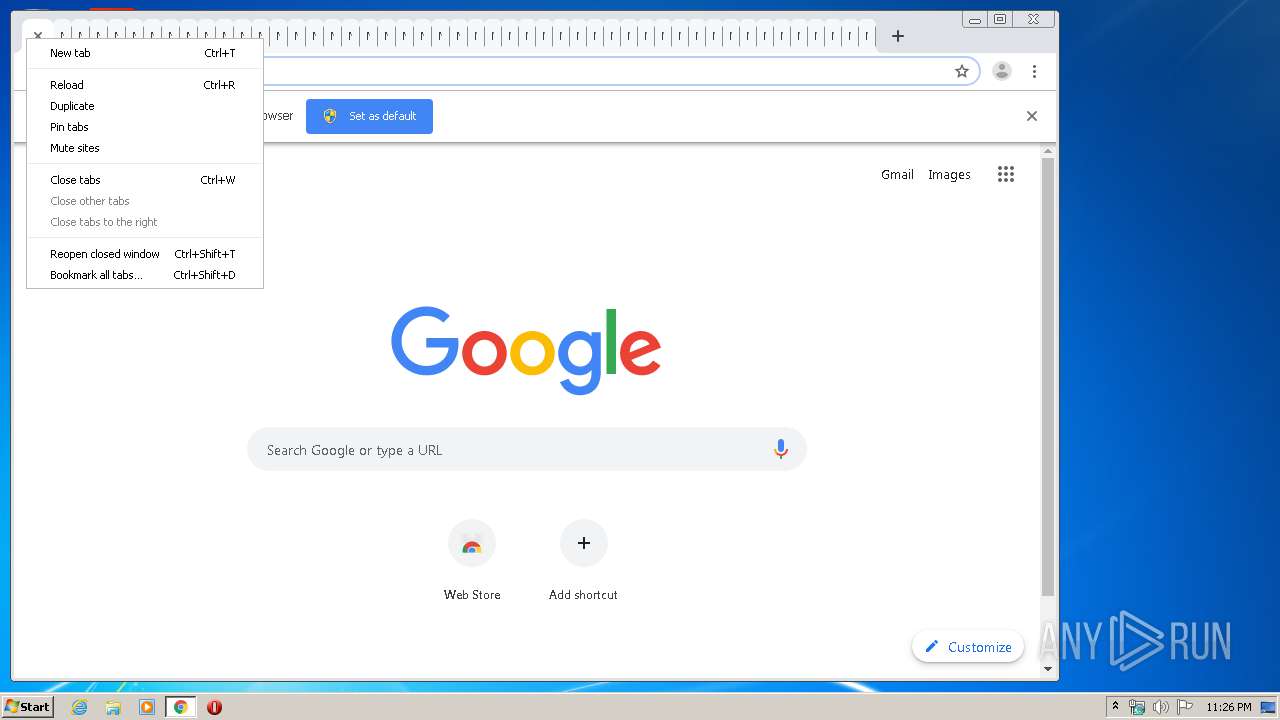
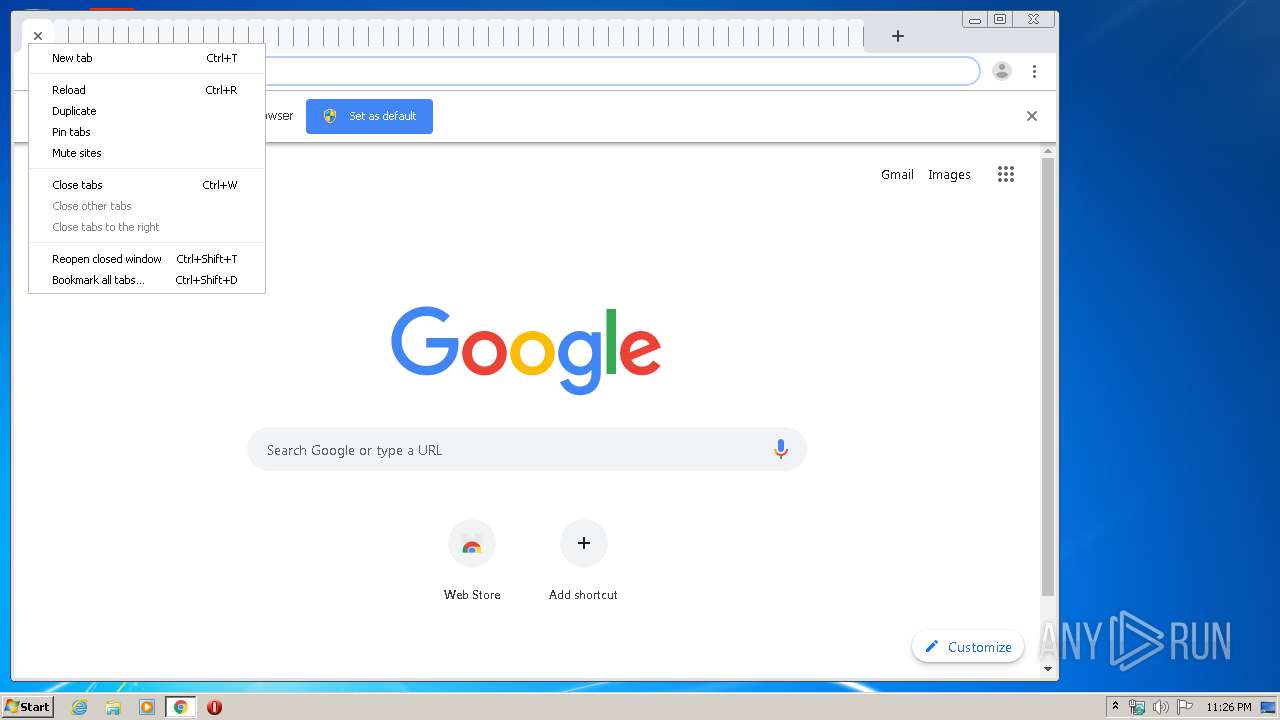
Modifies files in Chrome extension folder
- chrome.exe (PID: 2492)
Executed via COM
- DllHost.exe (PID: 4692)
- DllHost.exe (PID: 4660)
INFO
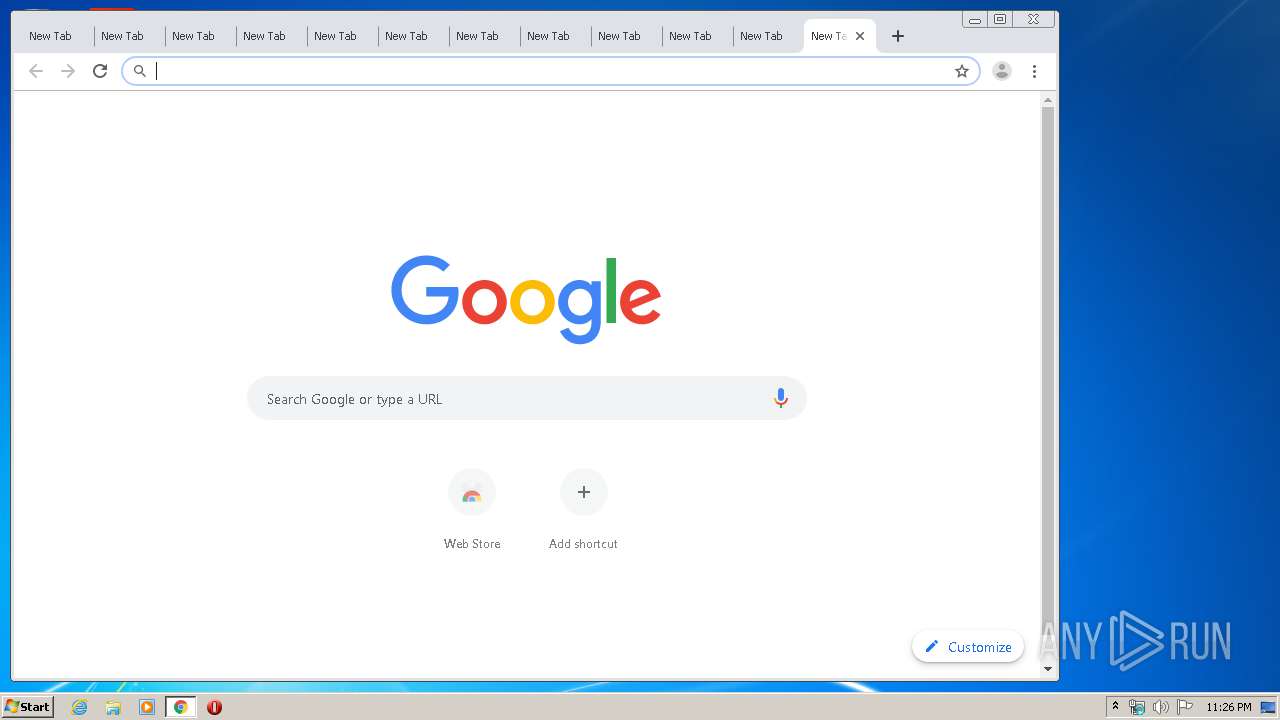
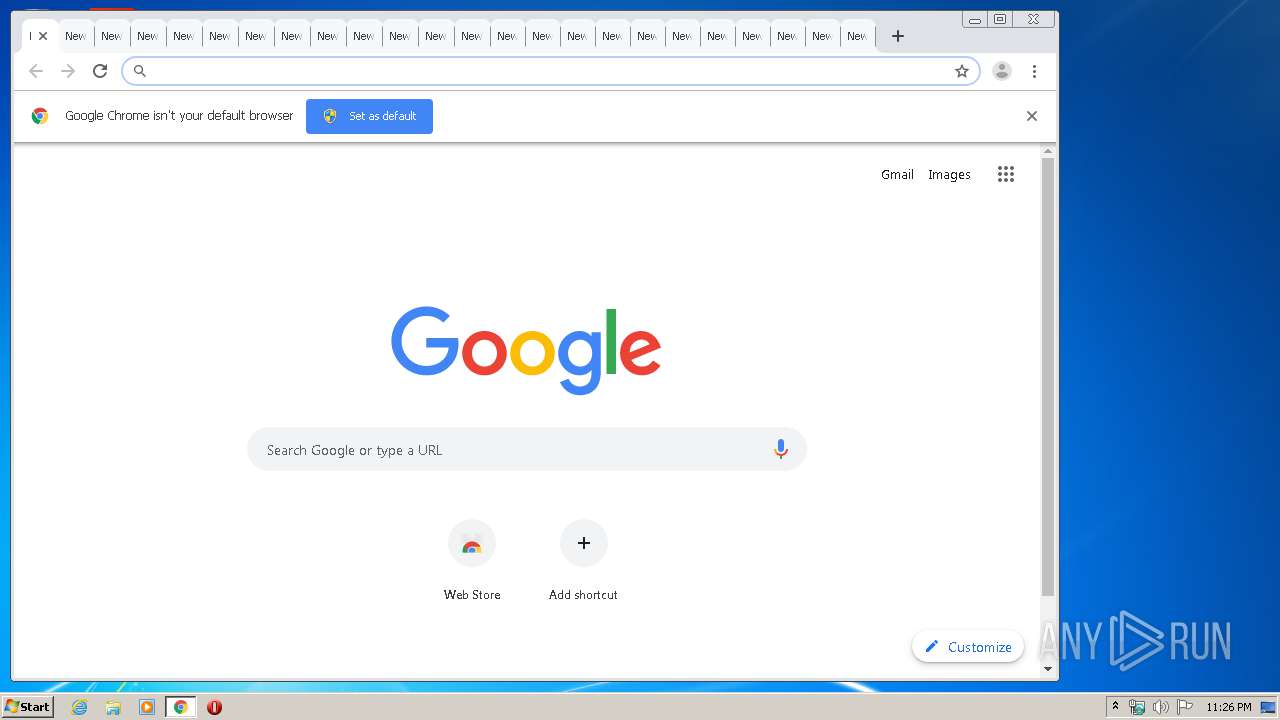
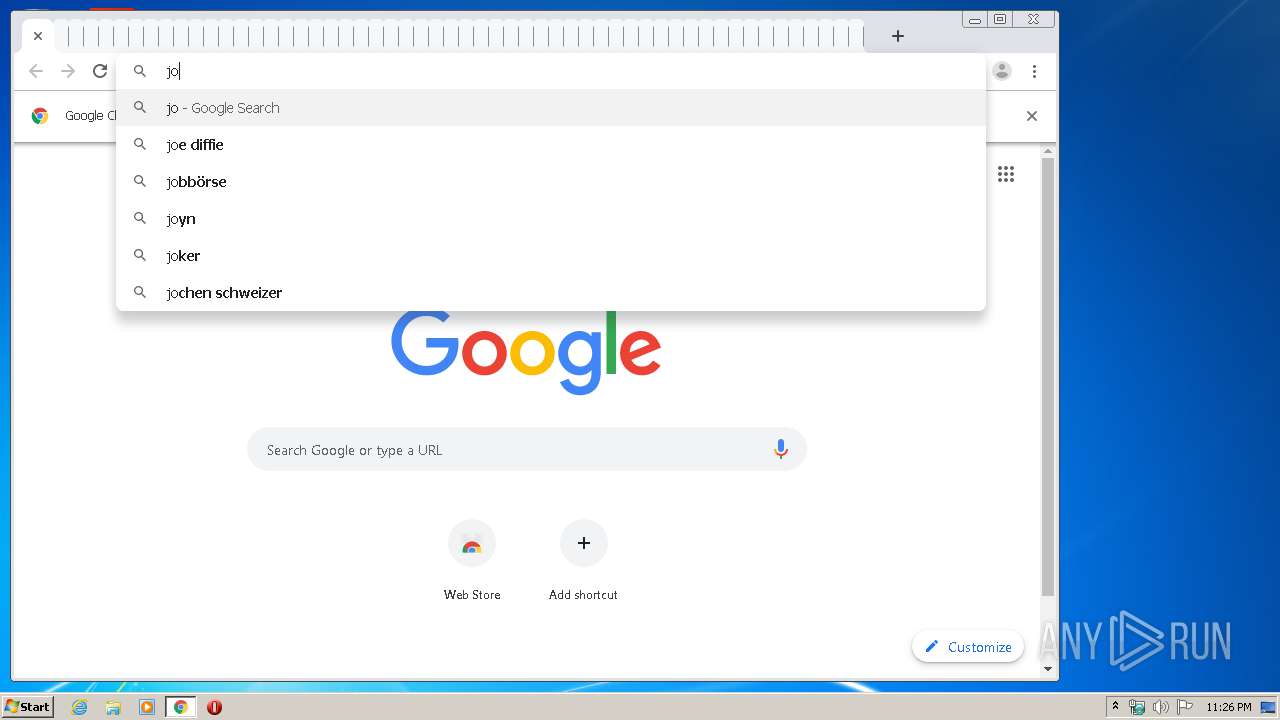
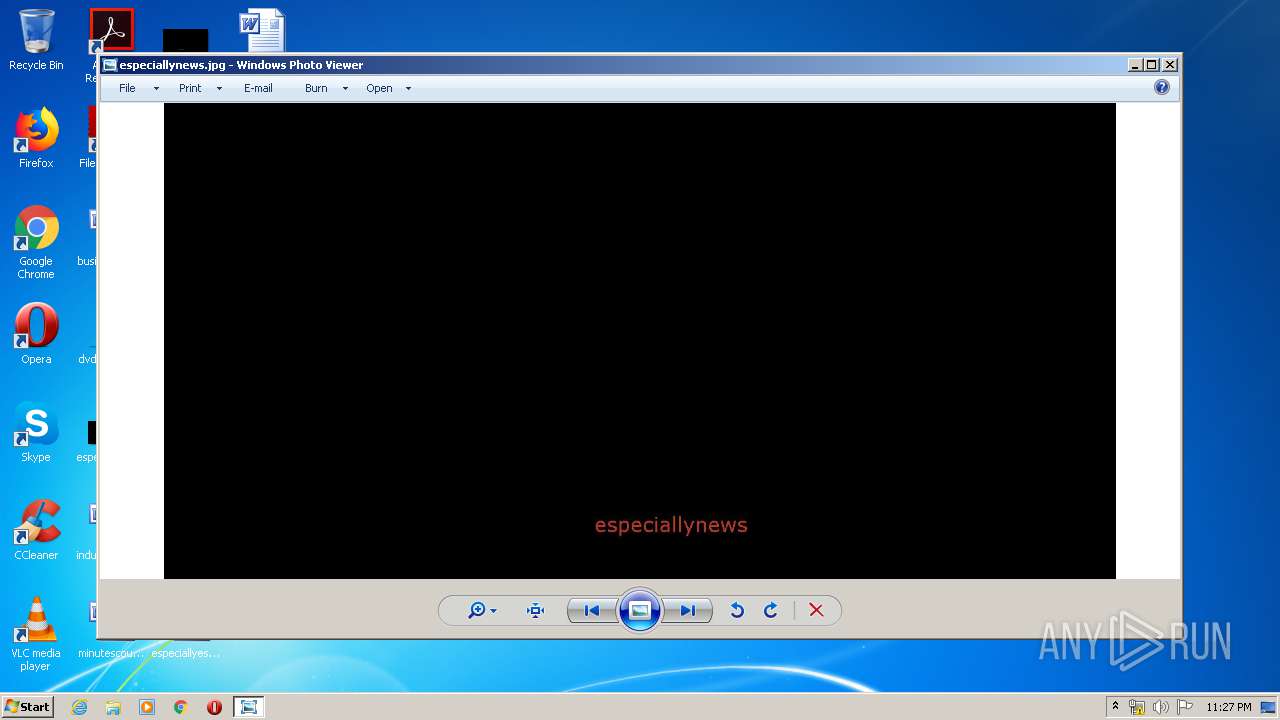
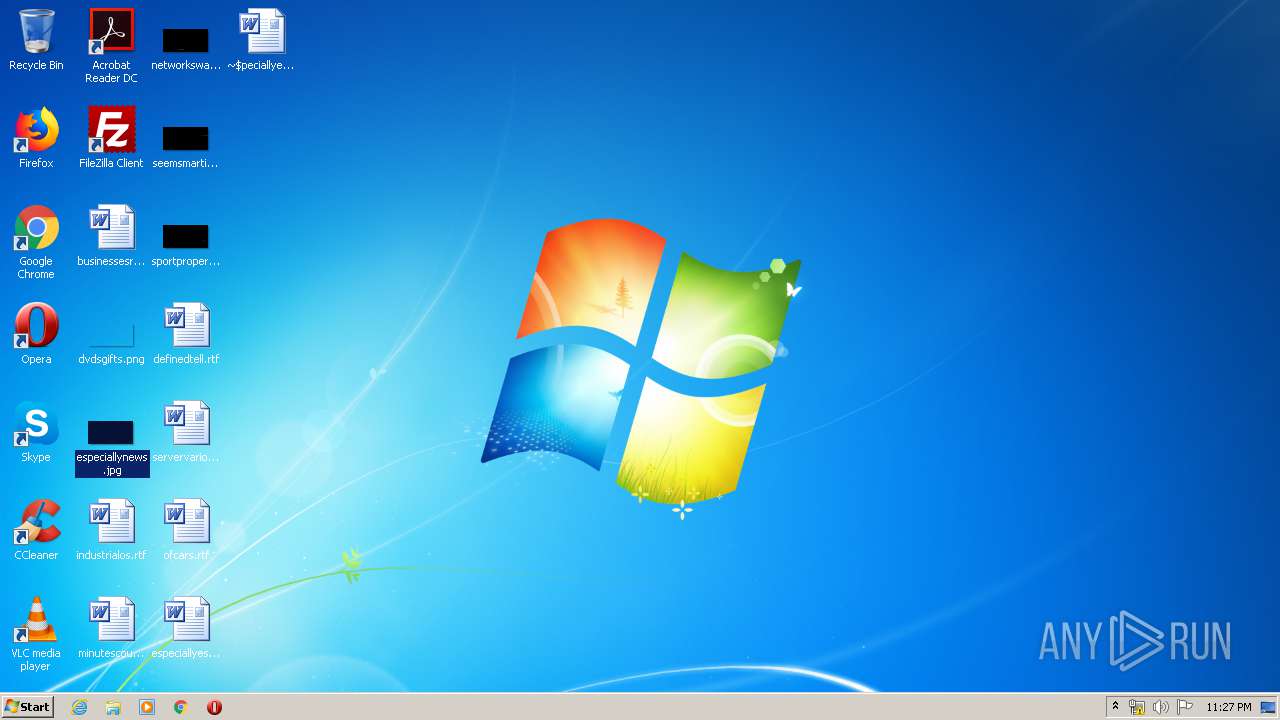
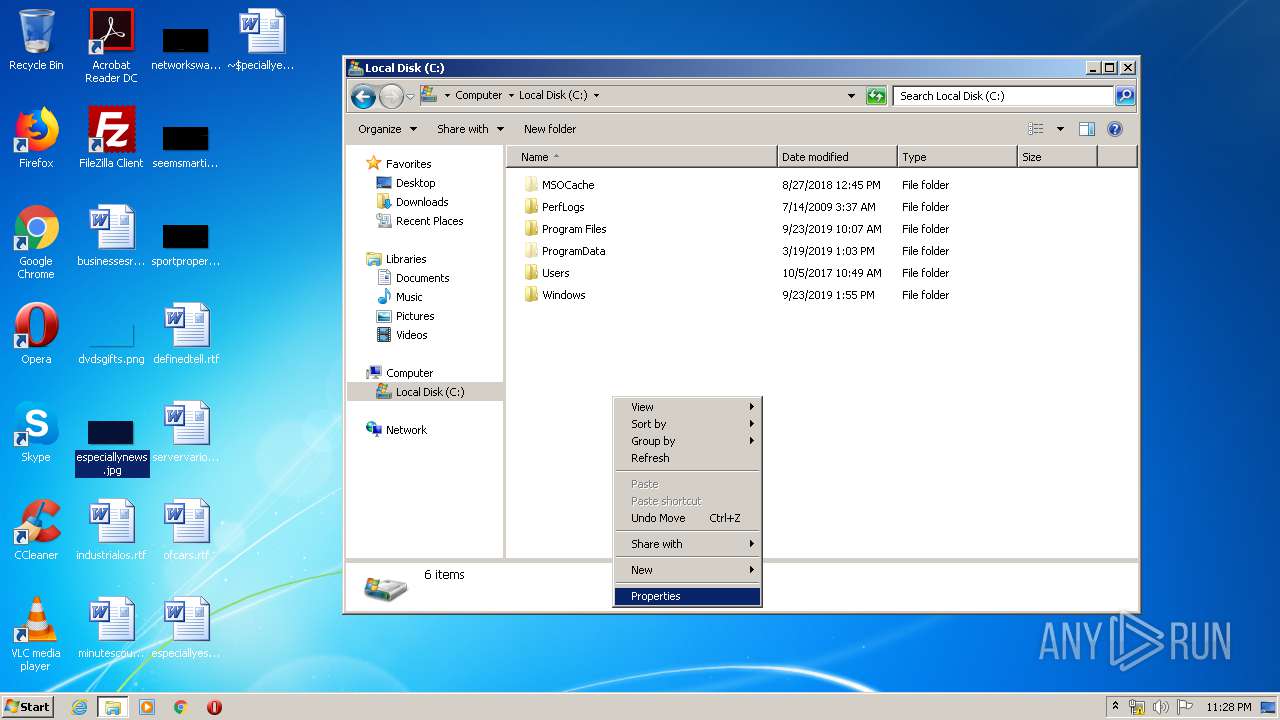
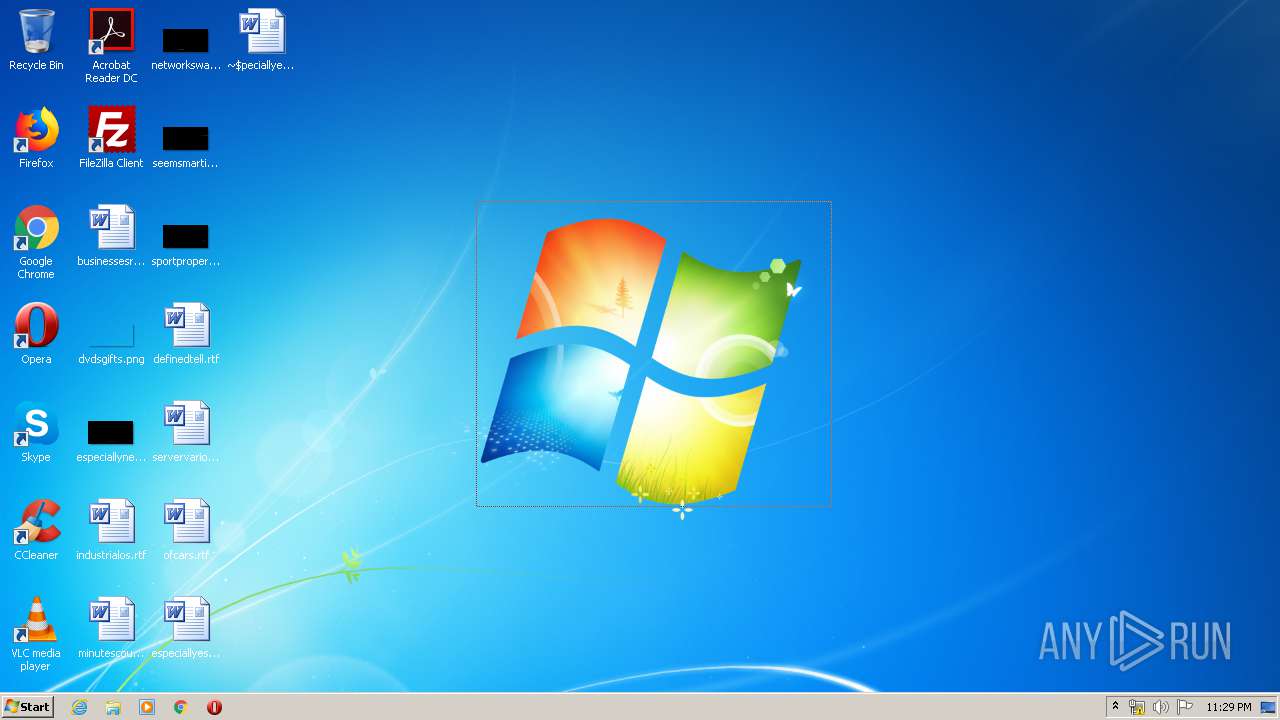
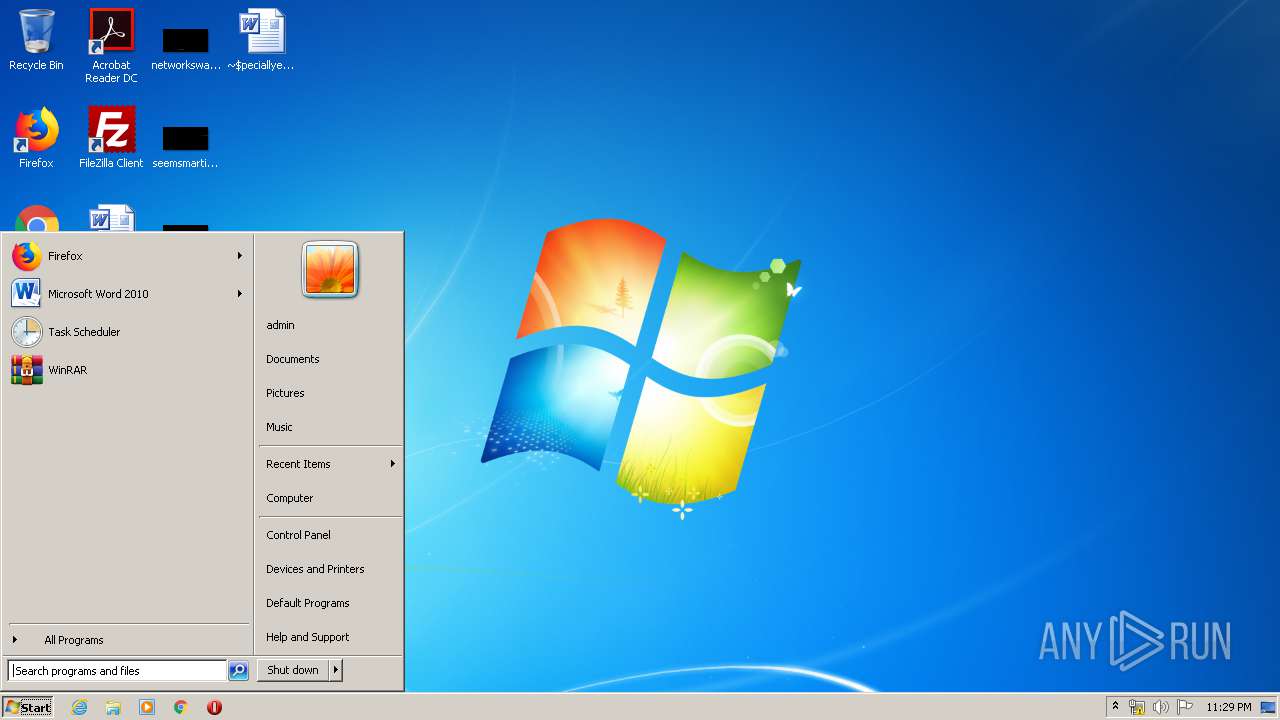
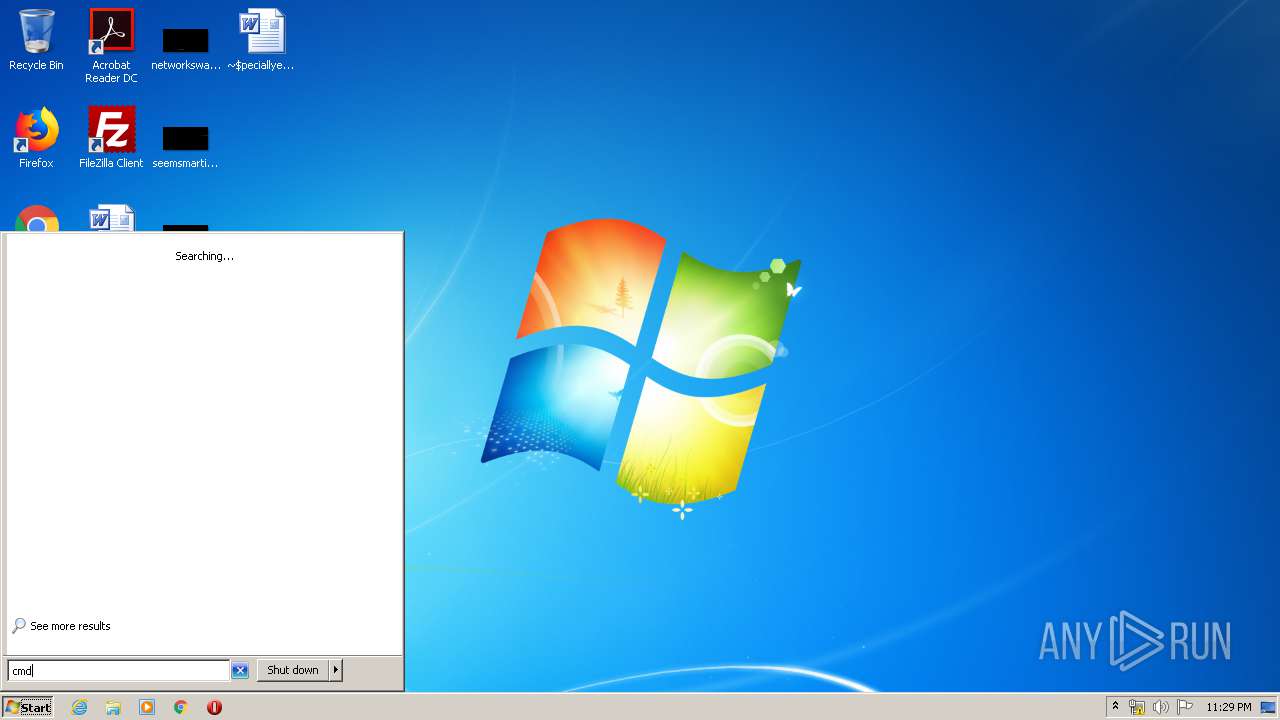
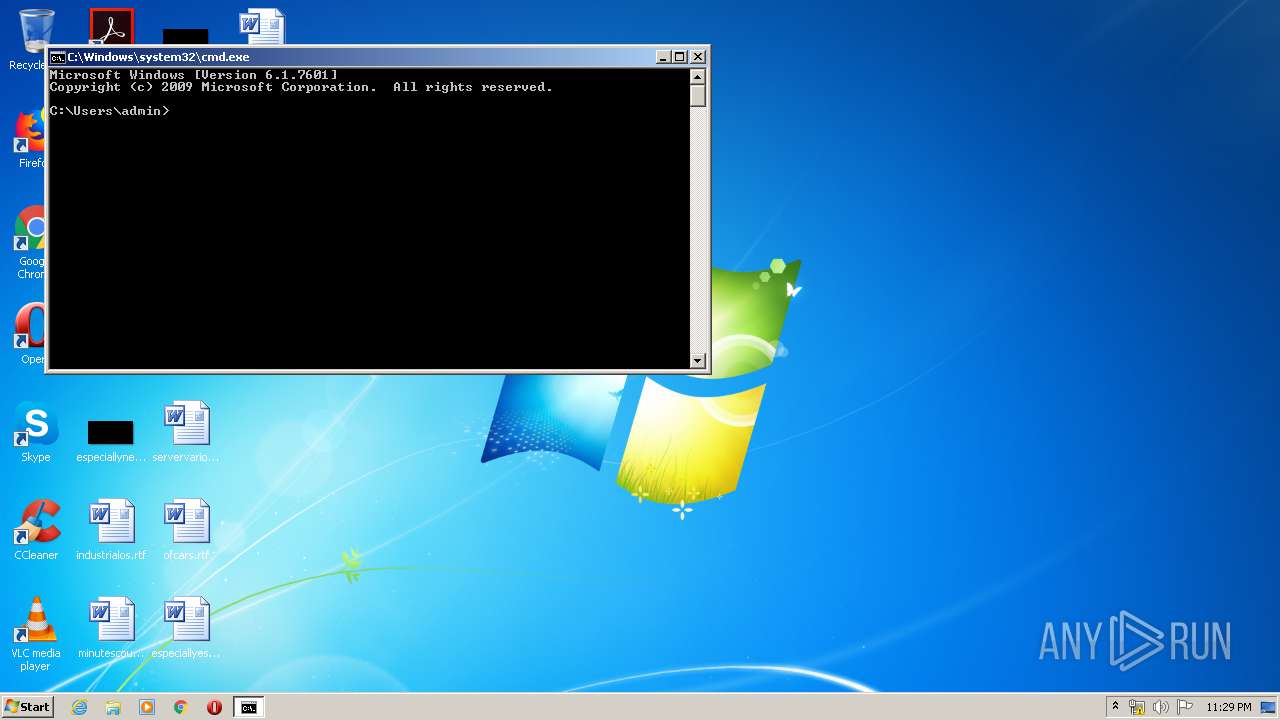
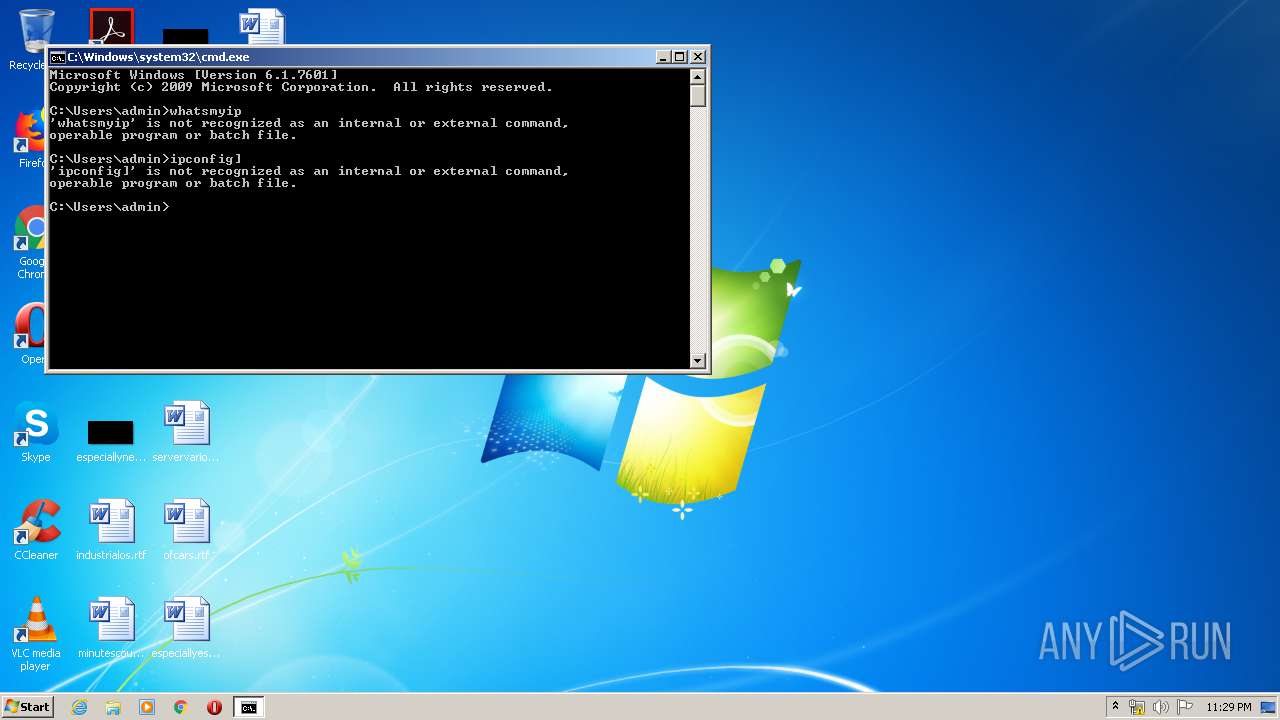
Manual execution by user
- chrome.exe (PID: 2492)
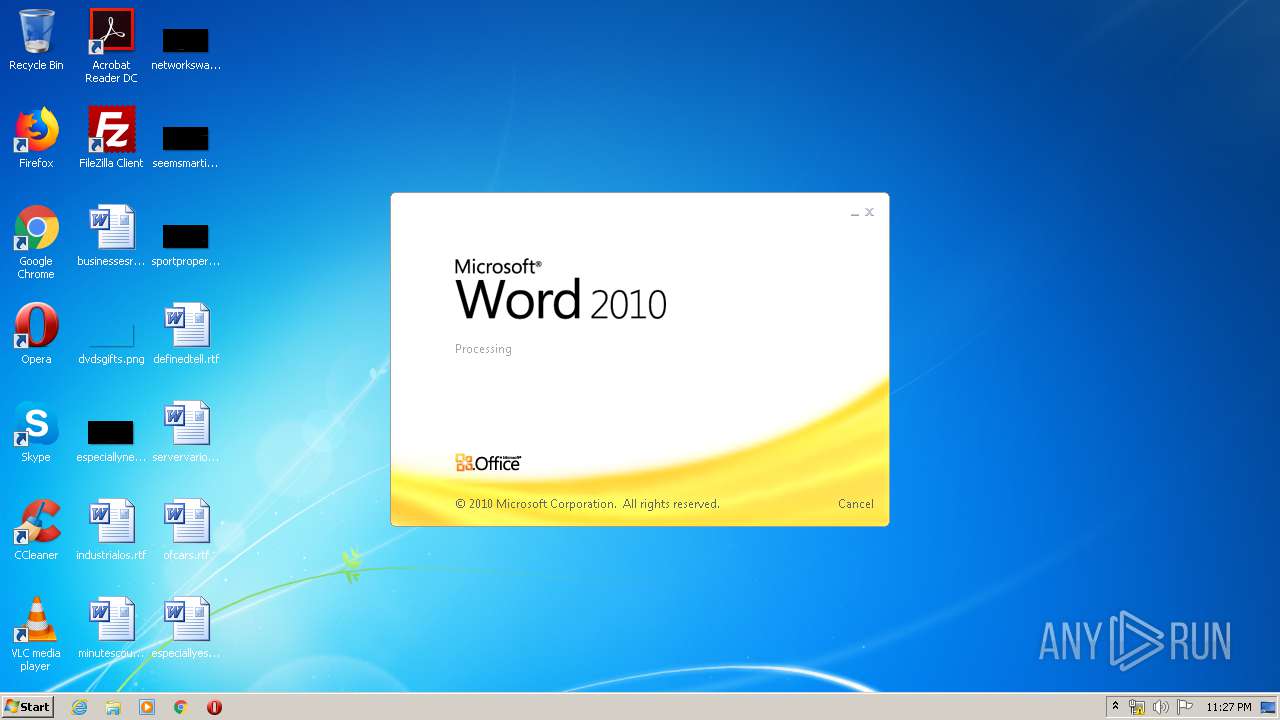
- WINWORD.EXE (PID: 3724)
- verclsid.exe (PID: 5820)
- explorer.exe (PID: 5272)
- cmd.exe (PID: 2084)
Reads the hosts file
- chrome.exe (PID: 2492)
- chrome.exe (PID: 1832)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3724)
Creates files in the user directory
- WINWORD.EXE (PID: 3724)
Application launched itself
- chrome.exe (PID: 2492)
Reads settings of System Certificates
- chrome.exe (PID: 1832)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (62) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.5) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Win16/32 Executable Delphi generic (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:12:10 19:29:06+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 691712 |
| InitializedDataSize: | 102400 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xaac6e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.3.1.1 |
| ProductVersionNumber: | 2.3.1.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | juvlarN |
| FileDescription: | vibranceGUI |
| FileVersion: | 2.3.1.1 |
| InternalName: | vibrance.GUI.exe |
| LegalCopyright: | Copyright © 2015 |
| LegalTrademarks: | - |
| OriginalFileName: | vibrance.GUI.exe |
| ProductName: | vibrance.GUI |
| ProductVersion: | 2.3.1.1 |
| AssemblyVersion: | 2.3.1.1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 10-Dec-2018 18:29:06 |
| Debug artifacts: |
|
| Comments: | - |
| CompanyName: | juvlarN |
| FileDescription: | vibranceGUI |
| FileVersion: | 2.3.1.1 |
| InternalName: | vibrance.GUI.exe |
| LegalCopyright: | Copyright © 2015 |
| LegalTrademarks: | - |
| OriginalFilename: | vibrance.GUI.exe |
| ProductName: | vibrance.GUI |
| ProductVersion: | 2.3.1.1 |
| Assembly Version: | 2.3.1.1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 10-Dec-2018 18:29:06 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x000A8C74 | 0x000A8E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.71015 |
.rsrc | 0x000AC000 | 0x00018E00 | 0x00018E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.36101 |
.reloc | 0x000C6000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 4.58232 | 6760 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 4.05234 | 38056 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 5.13851 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 4.97421 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 4.29542 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 4.28303 | 21640 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 3.00671 | 104 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
212
Monitored processes
165
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,13122921986071910869,16698460852706446142,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3322758736783817267 --mojo-platform-channel-handle=4244 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,13122921986071910869,16698460852706446142,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15300729854049382631 --renderer-client-id=119 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=6632 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,13122921986071910869,16698460852706446142,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11334301993094262549 --mojo-platform-channel-handle=6272 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,13122921986071910869,16698460852706446142,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2466726963800505336 --mojo-platform-channel-handle=6332 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,13122921986071910869,16698460852706446142,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14090885056850641301 --mojo-platform-channel-handle=5320 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,13122921986071910869,16698460852706446142,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13717017564429555123 --renderer-client-id=115 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=6728 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,13122921986071910869,16698460852706446142,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18374707552653522924 --renderer-client-id=99 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4336 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 816 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,13122921986071910869,16698460852706446142,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16168052641930246785 --renderer-client-id=122 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=6792 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 880 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,13122921986071910869,16698460852706446142,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11976982318804180357 --renderer-client-id=87 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5752 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,13122921986071910869,16698460852706446142,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13798800620634548573 --mojo-platform-channel-handle=4716 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 024
Read events
1 544
Write events
326
Delete events
154
Modification events
| (PID) Process: | (2492) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2492) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2492) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2492) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2492) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2836) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2492-13230080756261375 |
Value: 259 | |||
| (PID) Process: | (2492) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2492) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2492) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2492) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
Executable files
0
Suspicious files
130
Text files
276
Unknown types
20
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E8271F4-9BC.pma | — | |
MD5:— | SHA256:— | |||
| 2492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\1da82aed-a8be-4c9a-b663-75fb2753d963.tmp | — | |
MD5:— | SHA256:— | |||
| 2492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFa67a2a.TMP | text | |
MD5:— | SHA256:— | |||
| 2492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFa67a2a.TMP | text | |
MD5:— | SHA256:— | |||
| 2492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa67bfe.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
144
DNS requests
113
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1832 | chrome.exe | GET | 204 | 172.217.161.195:80 | http://csi.gstatic.com/csi?v=3&s=gapi_module&action=gapi_iframes__googleapis_cli12&it=mli.7,mei.2&srt=9&tbsrt=885&tran=15&e=abc_l0,abc_m0,abc_pgapi_iframes__googleapis_cli12,abc_u0&rt= | US | — | — | whitelisted |
1832 | chrome.exe | GET | 204 | 172.217.161.195:80 | http://csi.gstatic.com/csi?v=3&s=gapi_module&action=gapi_iframes__googleapis_cli12&it=mli.623,mei.0&srt=3&tbsrt=5121&tran=6&e=abc_l0,abc_m0,abc_pgapi_iframes__googleapis_cli12,abc_u0&rt= | US | — | — | whitelisted |
1832 | chrome.exe | GET | 204 | 172.217.161.195:80 | http://csi.gstatic.com/csi?v=3&s=gapi_module&action=gapi_iframes__googleapis_cli12&it=mli.1280,mei.13&srt=6&tbsrt=13464&tran=6&e=abc_l0,abc_m0,abc_pgapi_iframes__googleapis_cli12,abc_u0&rt= | US | — | — | whitelisted |
1832 | chrome.exe | GET | 204 | 172.217.161.195:80 | http://csi.gstatic.com/csi?v=3&s=gapi_module&action=gapi_iframes__googleapis_cli12&it=mli.703,mei.6&srt=4&tbsrt=5923&tran=15&e=abc_l0,abc_m0,abc_pgapi_iframes__googleapis_cli12,abc_u0&rt= | US | — | — | whitelisted |
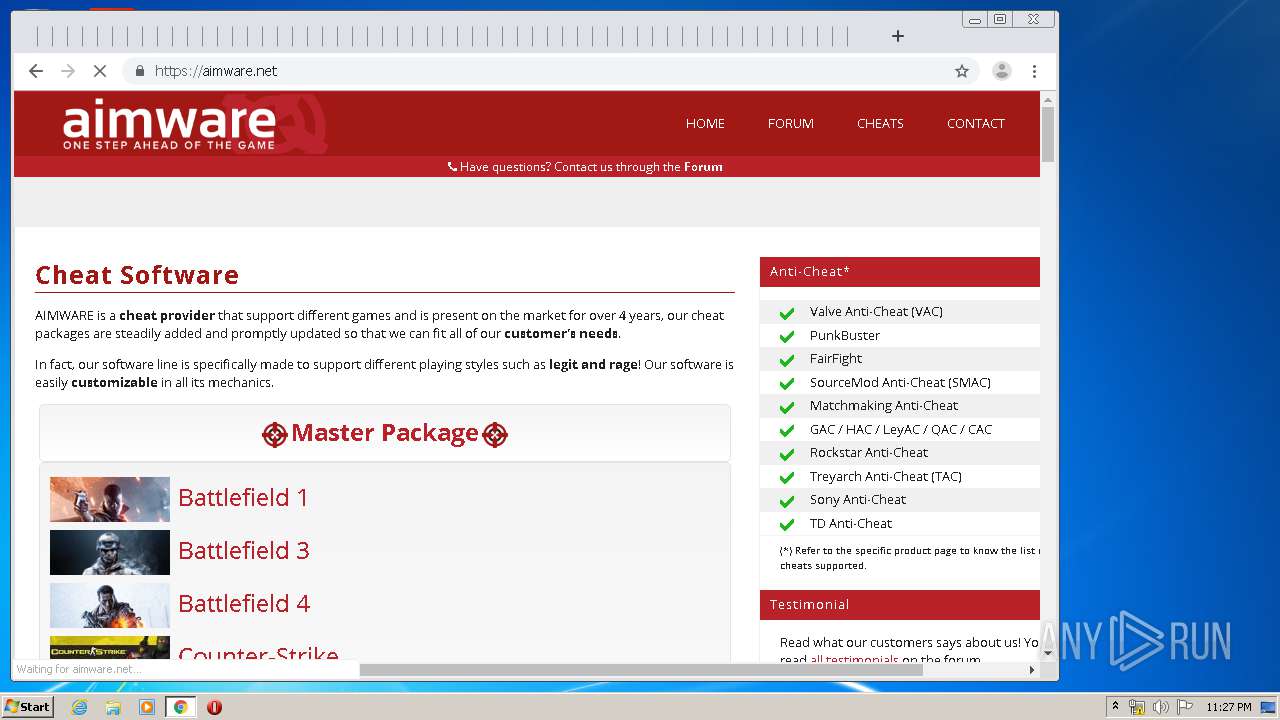
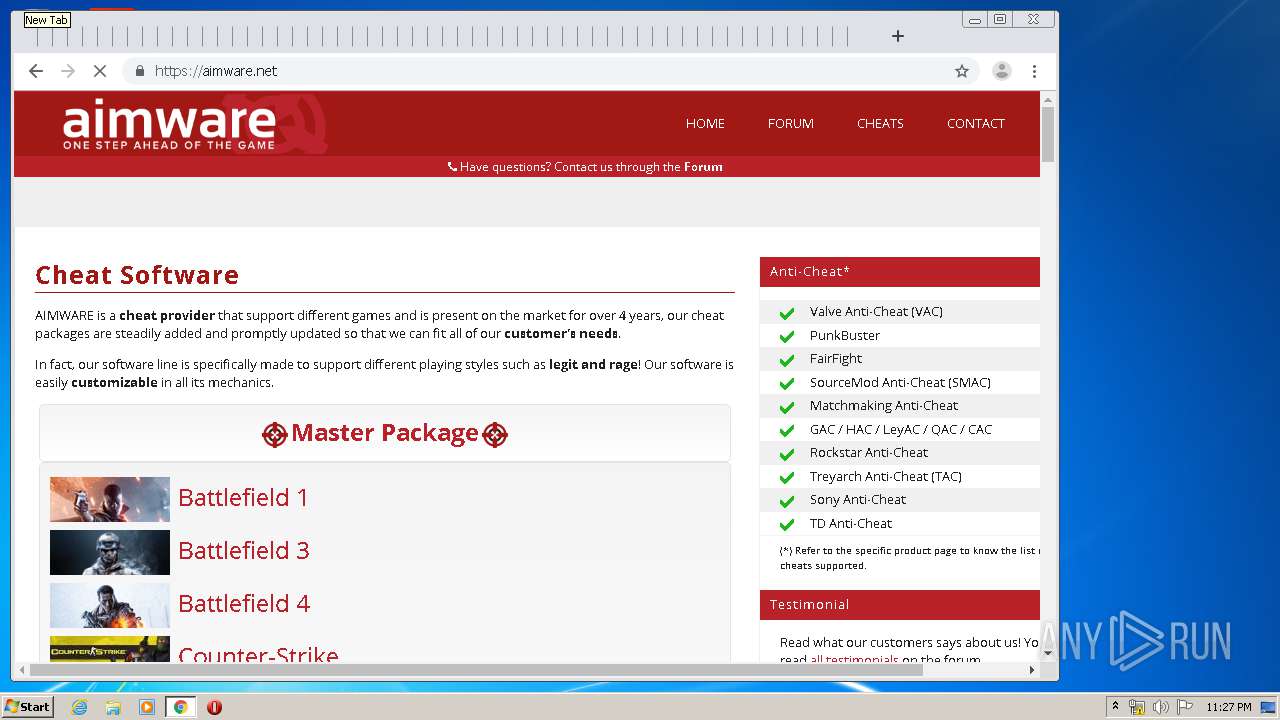
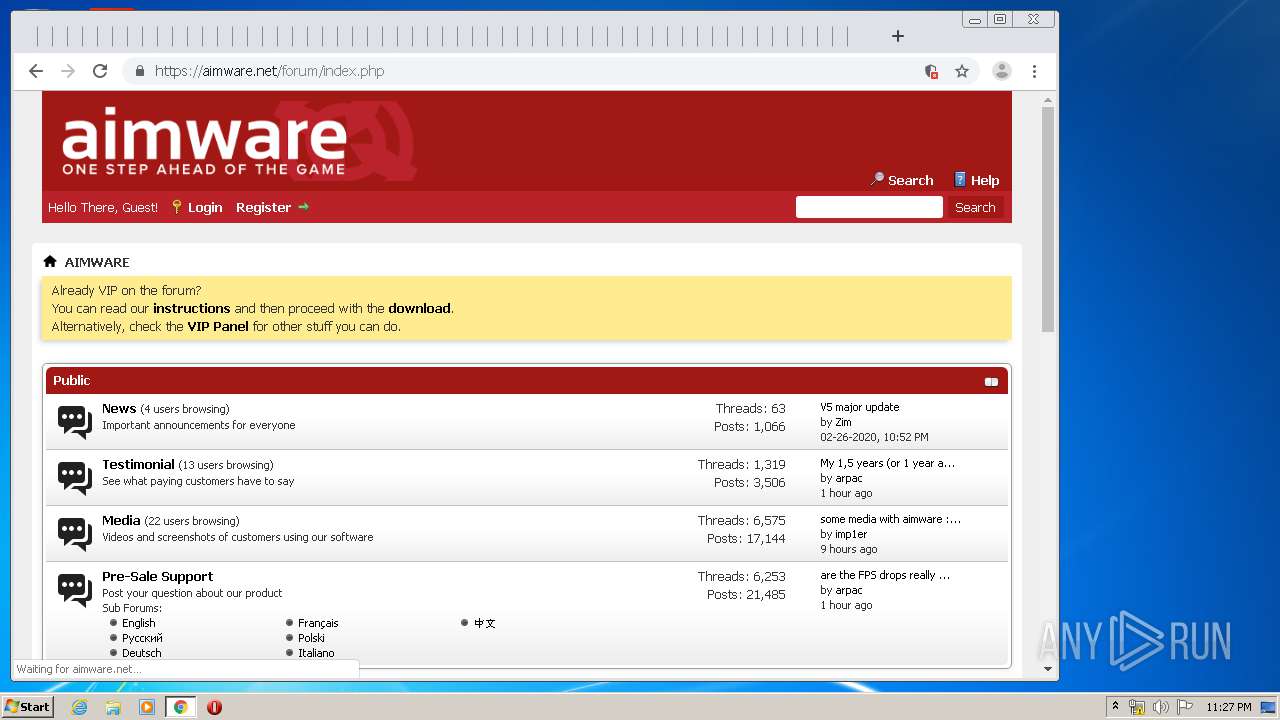
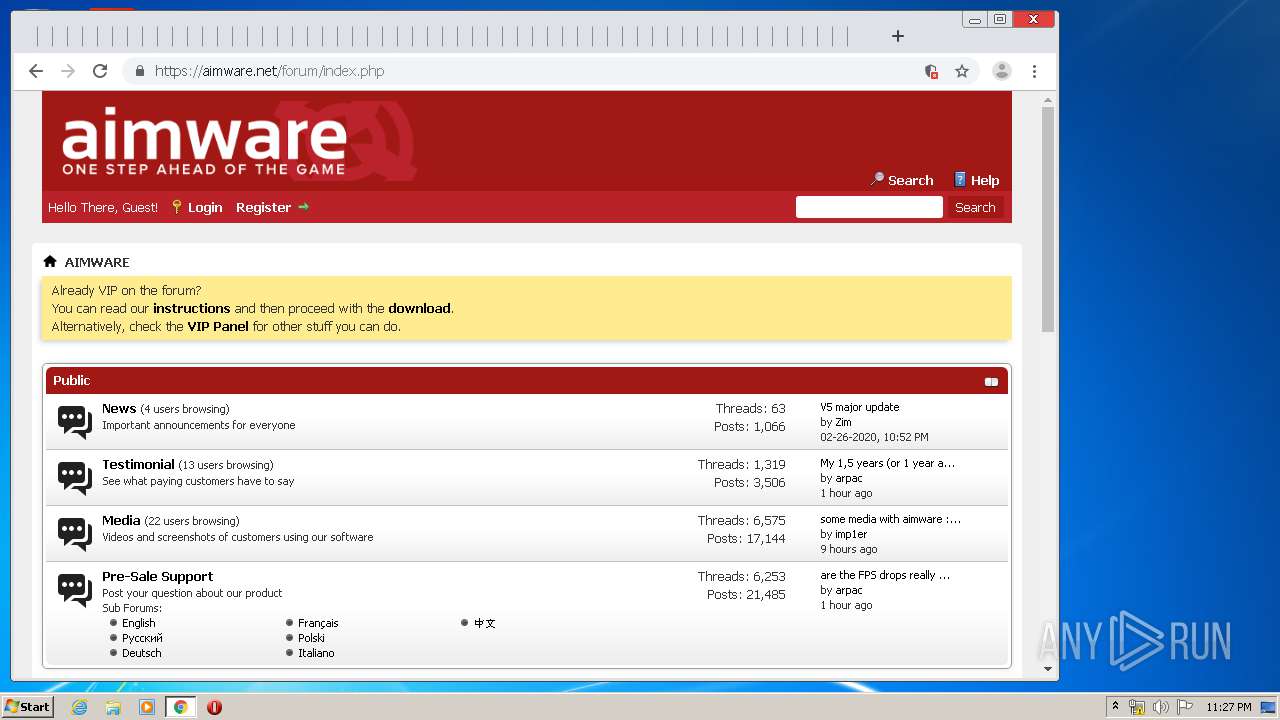
1832 | chrome.exe | GET | 200 | 5.254.113.91:80 | http://aimware.net/ | RO | html | 723 b | unknown |
1832 | chrome.exe | GET | 204 | 172.217.161.195:80 | http://csi.gstatic.com/csi?v=3&s=gapi_module&action=gapi_iframes__googleapis_cli12&it=mli.589,mei.2&srt=2&tbsrt=5140&tran=6&e=abc_l0,abc_m0,abc_pgapi_iframes__googleapis_cli12,abc_u0&rt= | US | — | — | whitelisted |
1832 | chrome.exe | GET | 204 | 172.217.161.195:80 | http://csi.gstatic.com/csi?v=3&s=gapi_module&action=gapi_iframes__googleapis_cli12&it=mli.2043,mei.7&srt=3&tbsrt=13259&tran=6&e=abc_l0,abc_m0,abc_pgapi_iframes__googleapis_cli12,abc_u0&rt= | US | — | — | whitelisted |
1832 | chrome.exe | GET | 302 | 172.217.23.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 522 b | whitelisted |
1832 | chrome.exe | GET | 302 | 172.217.23.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 517 b | whitelisted |
1832 | chrome.exe | GET | 301 | 5.254.113.91:80 | http://aimware.net/favicon.ico | RO | html | 178 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1832 | chrome.exe | 172.217.22.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
1832 | chrome.exe | 172.217.18.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1832 | chrome.exe | 172.217.21.227:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
1832 | chrome.exe | 172.217.23.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1832 | chrome.exe | 216.58.207.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1832 | chrome.exe | 172.217.16.195:443 | www.google.com.ua | Google Inc. | US | whitelisted |
1832 | chrome.exe | 172.217.23.142:443 | apis.google.com | Google Inc. | US | whitelisted |
1832 | chrome.exe | 216.58.206.14:443 | ogs.google.com.ua | Google Inc. | US | whitelisted |
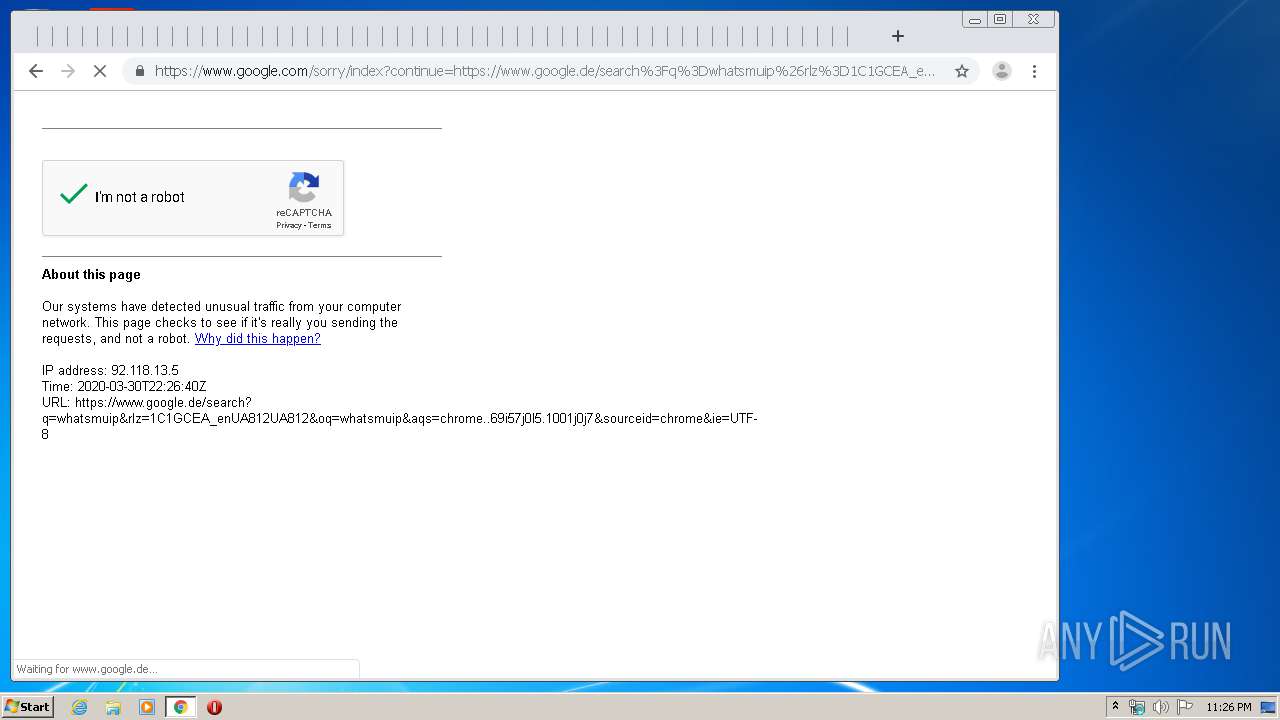
1832 | chrome.exe | 216.58.210.4:443 | www.google.com | Google Inc. | US | whitelisted |
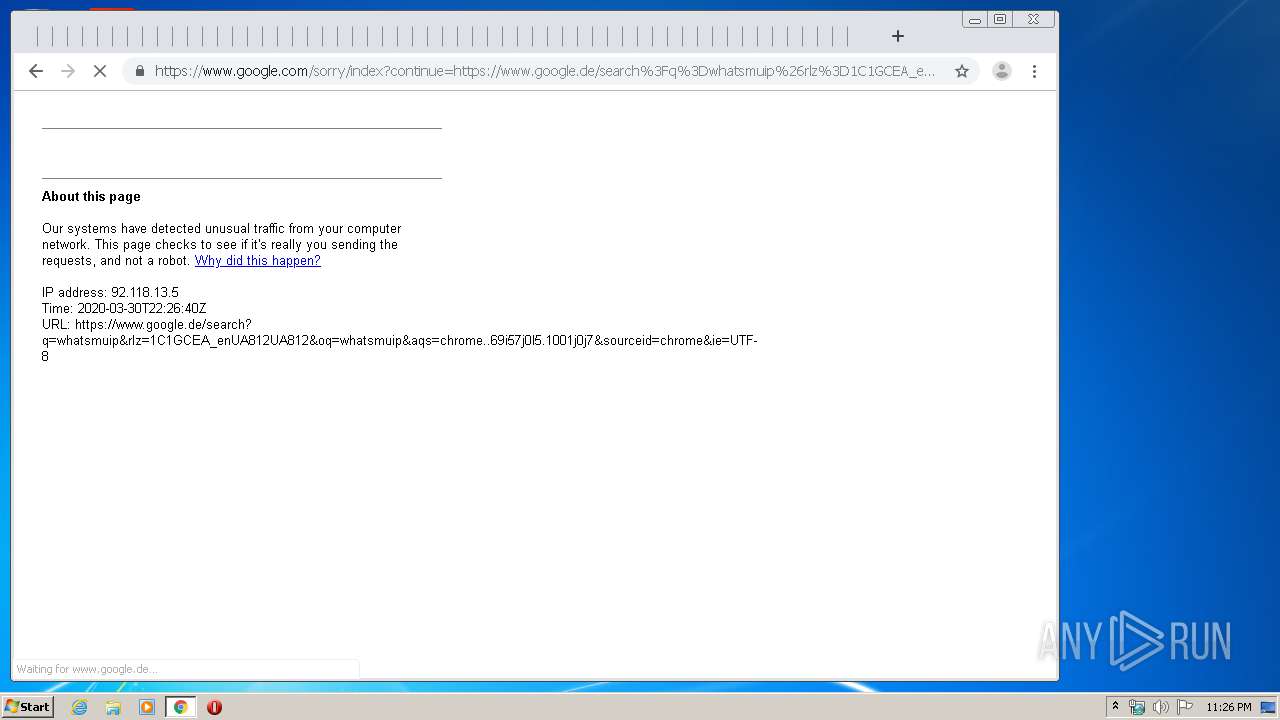
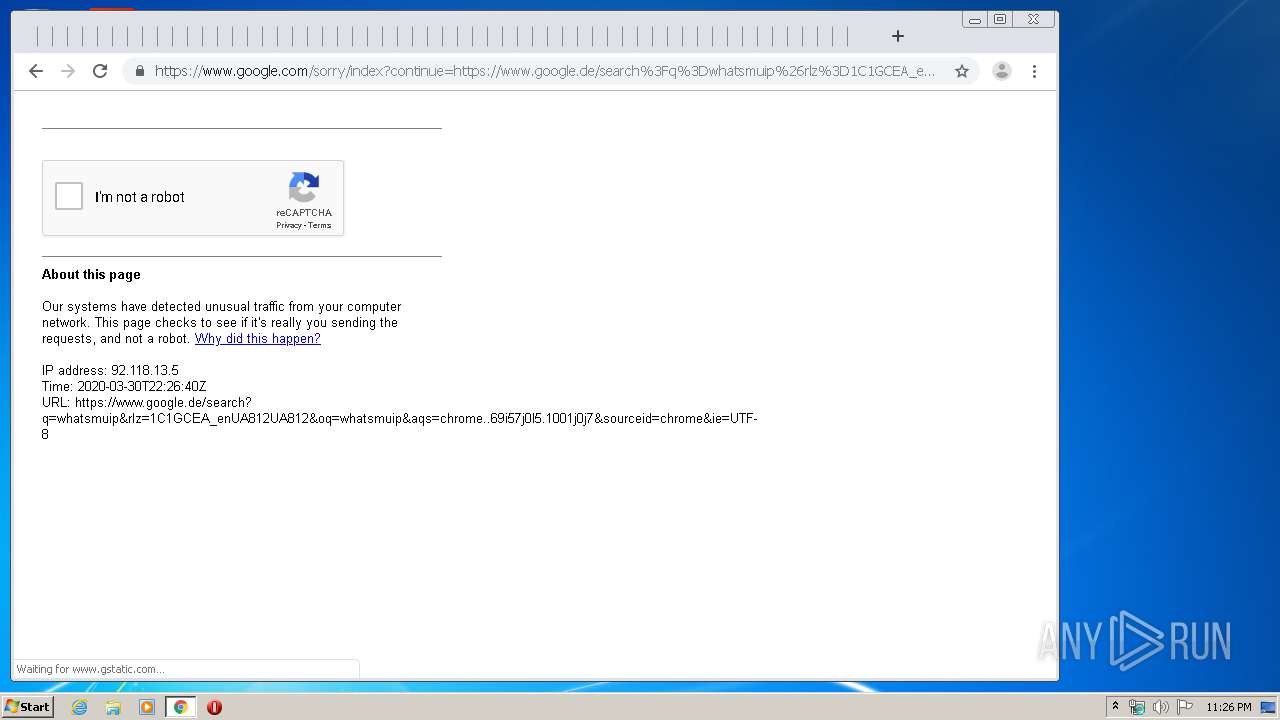
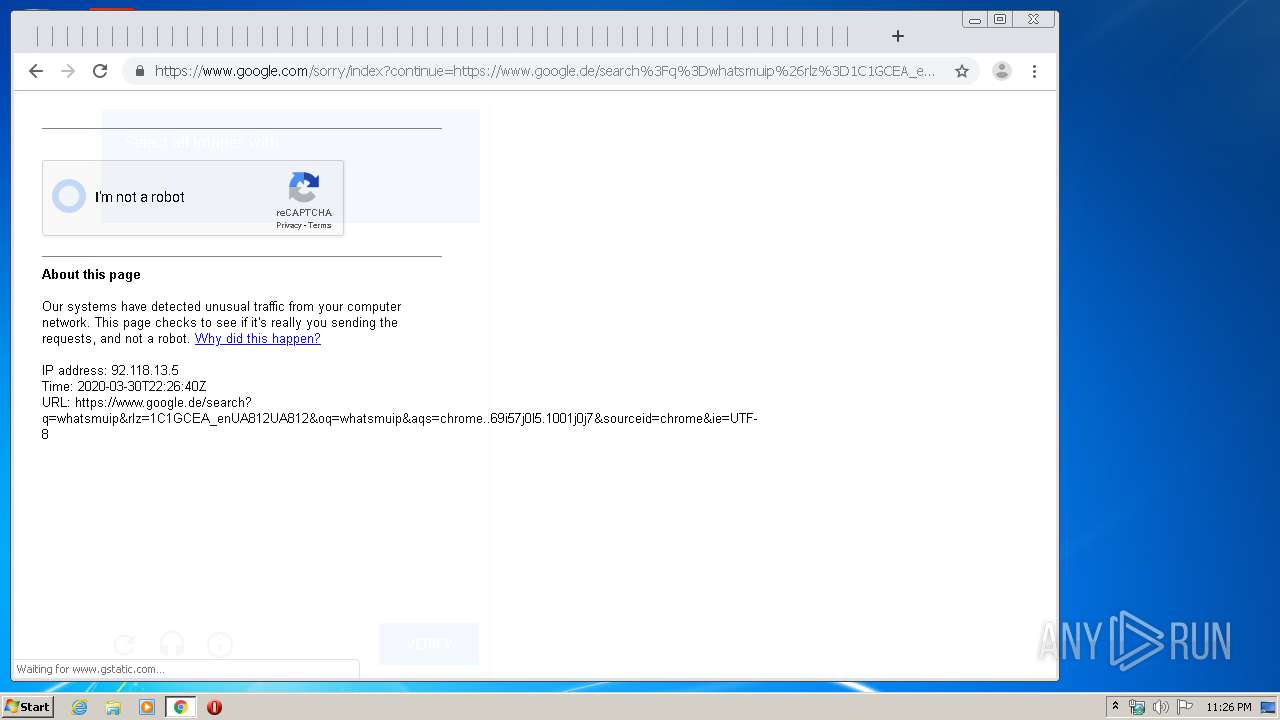
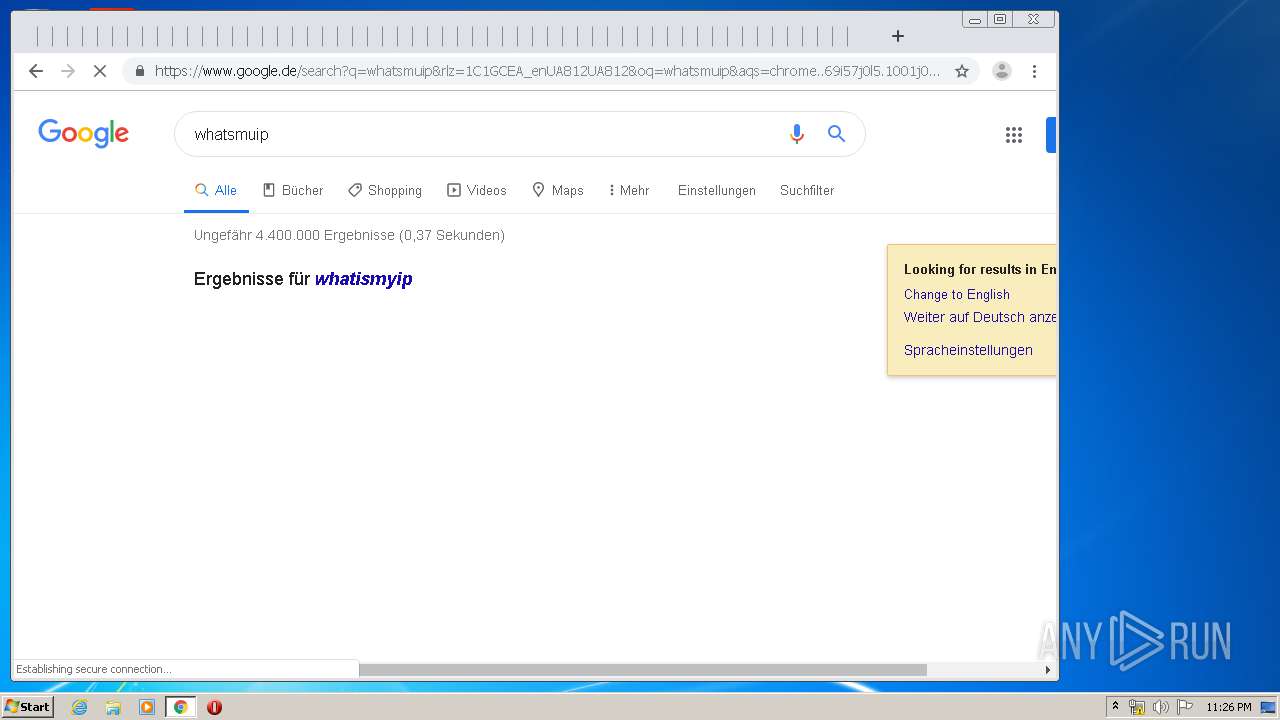
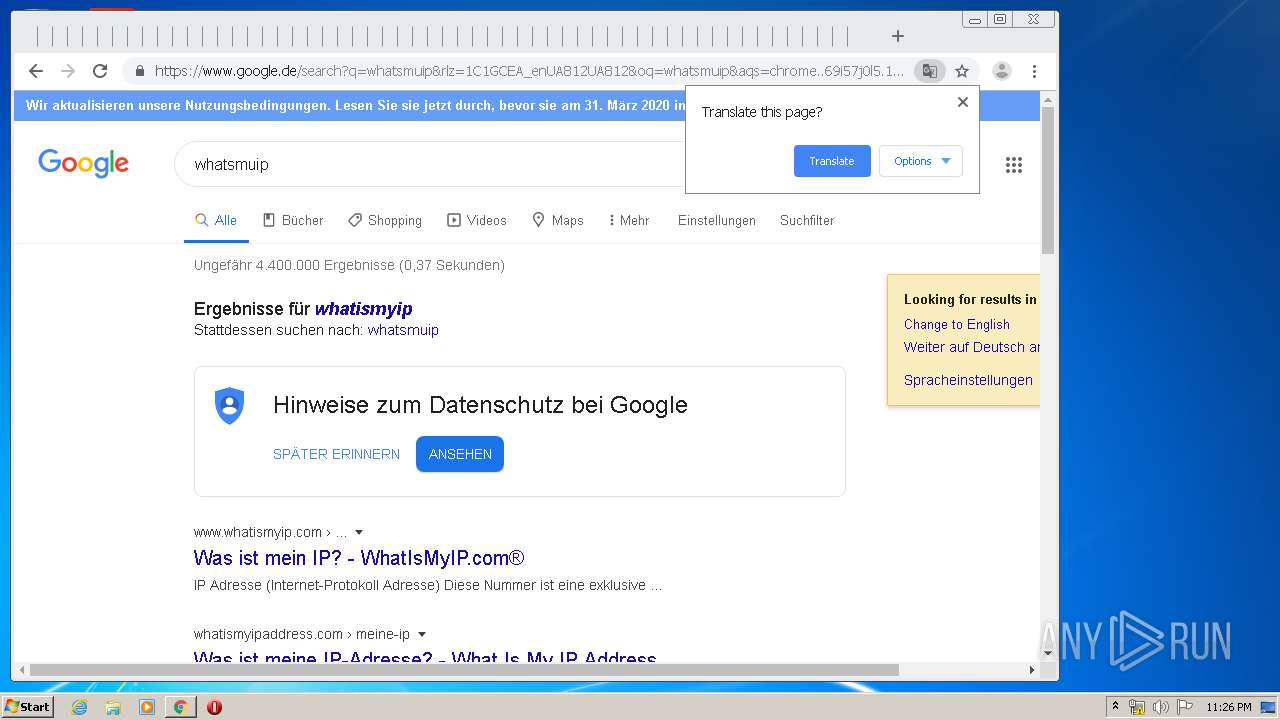
1832 | chrome.exe | 172.217.23.99:443 | www.google.de | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com.ua |
| whitelisted |
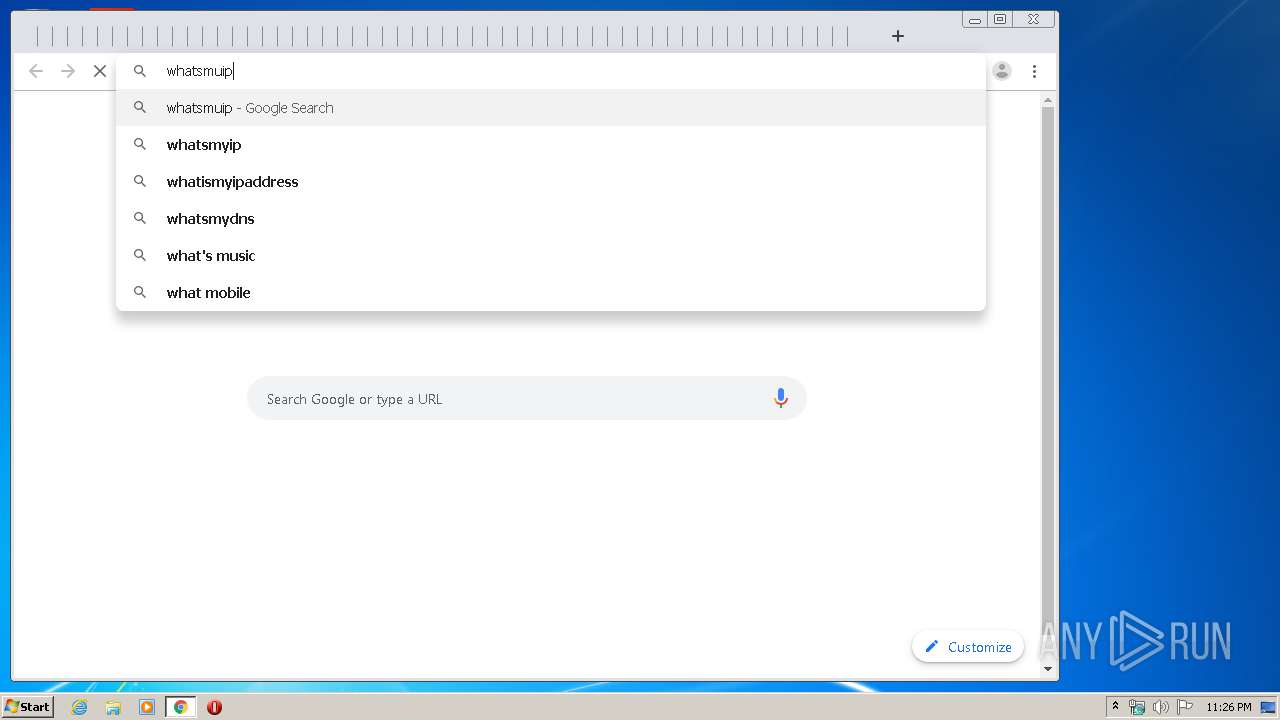
www.google.com |
| malicious |
www.google.de |
| whitelisted |