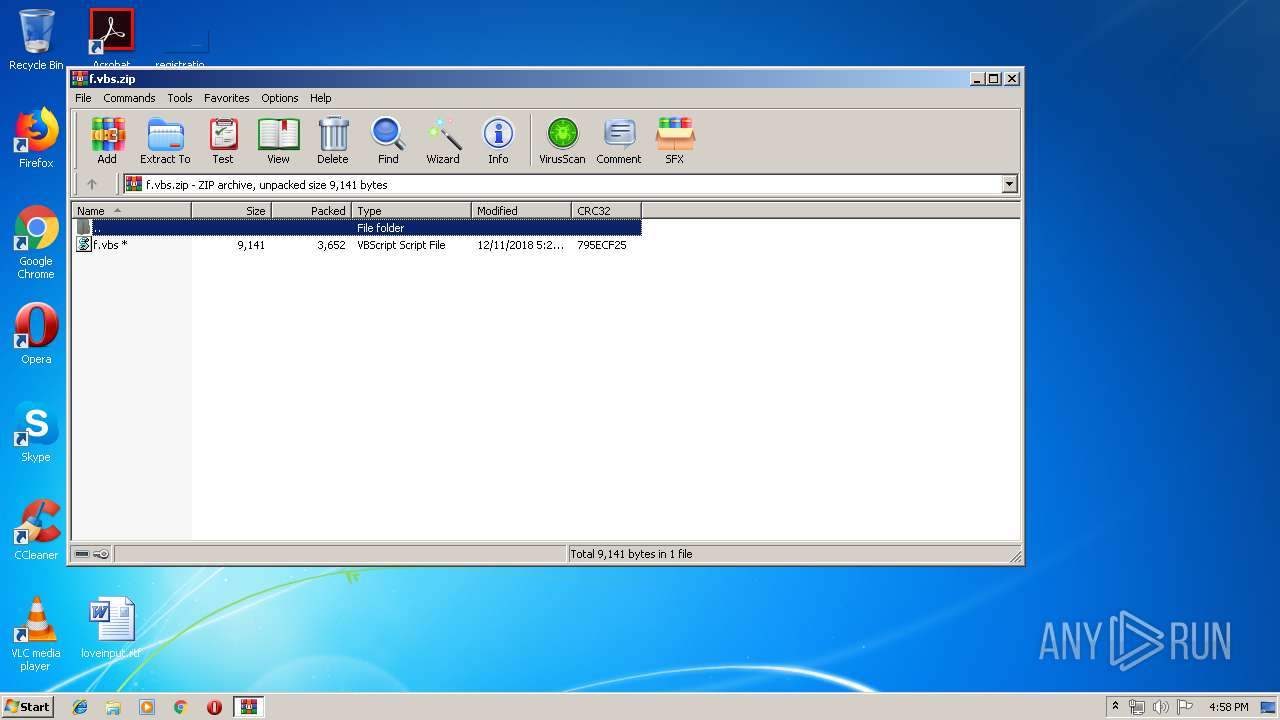
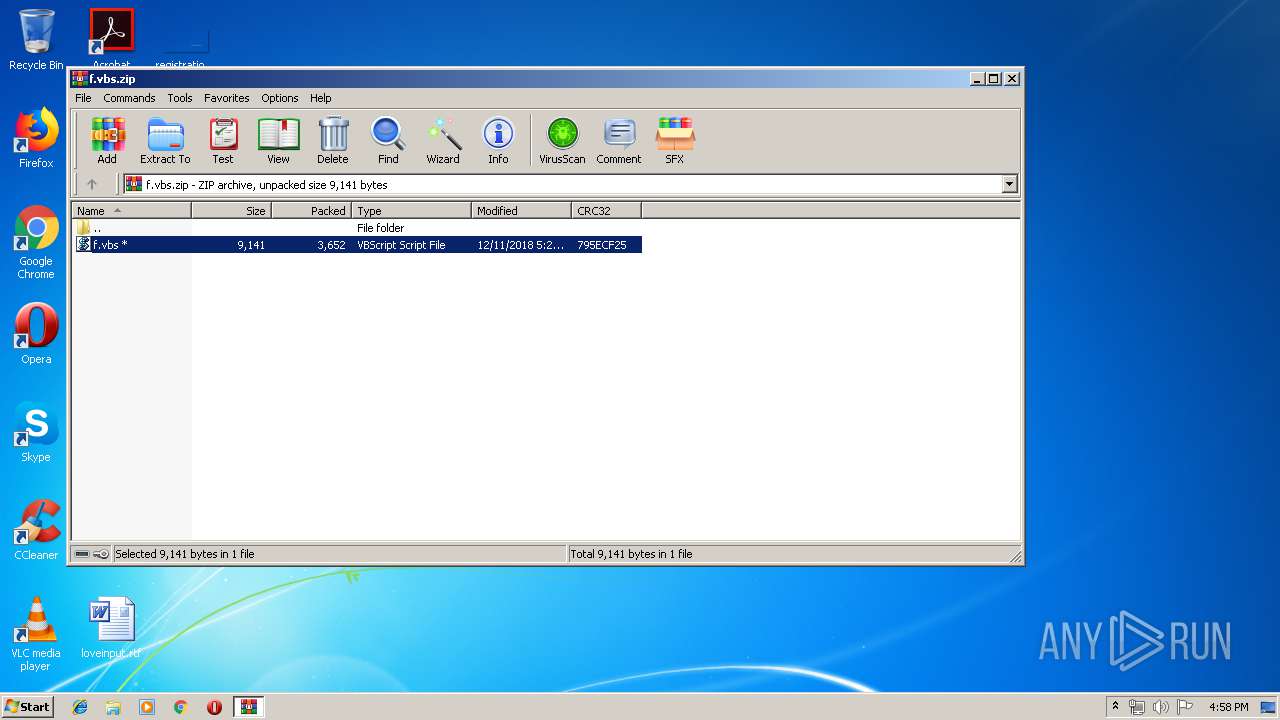
| File name: | f.vbs.zip |
| Full analysis: | https://app.any.run/tasks/e092ac09-042b-494a-9371-ffc84866ab12 |
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2019, 15:58:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 7897EE2EB7816E0780D2F33439B0B598 |
| SHA1: | 0CA8F3EA0C6A338BD8025049F6C0920362A1534E |
| SHA256: | 1CB127AAA65C11597501F0B29BA5D83120F4580D39B1DDE6C598F92A3C800400 |
| SSDEEP: | 96:euukk821JM8ga/XnsW3znJTs+H98YftG65:mK2/gaj5s+H9vo65 |
MALICIOUS
Starts CertUtil for decode files
- cmd.exe (PID: 2756)
- cmd.exe (PID: 300)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 3088)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2168)
- schtasks.exe (PID: 704)
SUSPICIOUS
Creates files in the program directory
- WScript.exe (PID: 3900)
- certutil.exe (PID: 3700)
- certutil.exe (PID: 3156)
Executes scripts
- WinRAR.exe (PID: 2344)
- cmd.exe (PID: 1860)
Starts CMD.EXE for commands execution
- WScript.exe (PID: 3900)
Creates files in the user directory
- powershell.exe (PID: 2664)
- powershell.exe (PID: 2072)
- powershell.exe (PID: 3540)
- powershell.exe (PID: 2916)
- powershell.exe (PID: 332)
- powershell.exe (PID: 1324)
- notepad++.exe (PID: 1336)
- powershell.exe (PID: 2700)
- powershell.exe (PID: 3904)
- powershell.exe (PID: 3968)
- powershell.exe (PID: 1260)
- powershell.exe (PID: 3120)
- powershell.exe (PID: 2612)
- powershell.exe (PID: 2628)
- powershell.exe (PID: 3952)
Executes PowerShell scripts
- wscript.exe (PID: 2392)
- wscript.EXE (PID: 3232)
- wscript.EXE (PID: 1668)
- wscript.EXE (PID: 3752)
- wscript.EXE (PID: 304)
- wscript.EXE (PID: 2104)
Uses WHOAMI.EXE to obtaining logged on user information
- powershell.exe (PID: 2072)
- powershell.exe (PID: 2916)
- powershell.exe (PID: 1260)
- powershell.exe (PID: 3120)
- powershell.exe (PID: 2628)
- powershell.exe (PID: 3952)
Uses RUNDLL32.EXE to load library
- powershell.exe (PID: 1324)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2018:12:11 18:29:17 |
| ZipCRC: | 0x795ecf25 |
| ZipCompressedSize: | 3652 |
| ZipUncompressedSize: | 9141 |
| ZipFileName: | f.vbs |
Total processes
99
Monitored processes
42
Malicious processes
4
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | "C:\Windows\System32\cmd.exe" /C certutil -f -decode C:\ProgramData\Windows\Microsoft\java\hUpdateCheckers.base C:\ProgramData\Windows\Microsoft\java\hUpdateCheckers.ps1 | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 304 | C:\Windows\system32\wscript.EXE /b C:\ProgramData\Windows\Microsoft\java\GoogleUpdateschecker.vbs | C:\Windows\system32\wscript.EXE | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
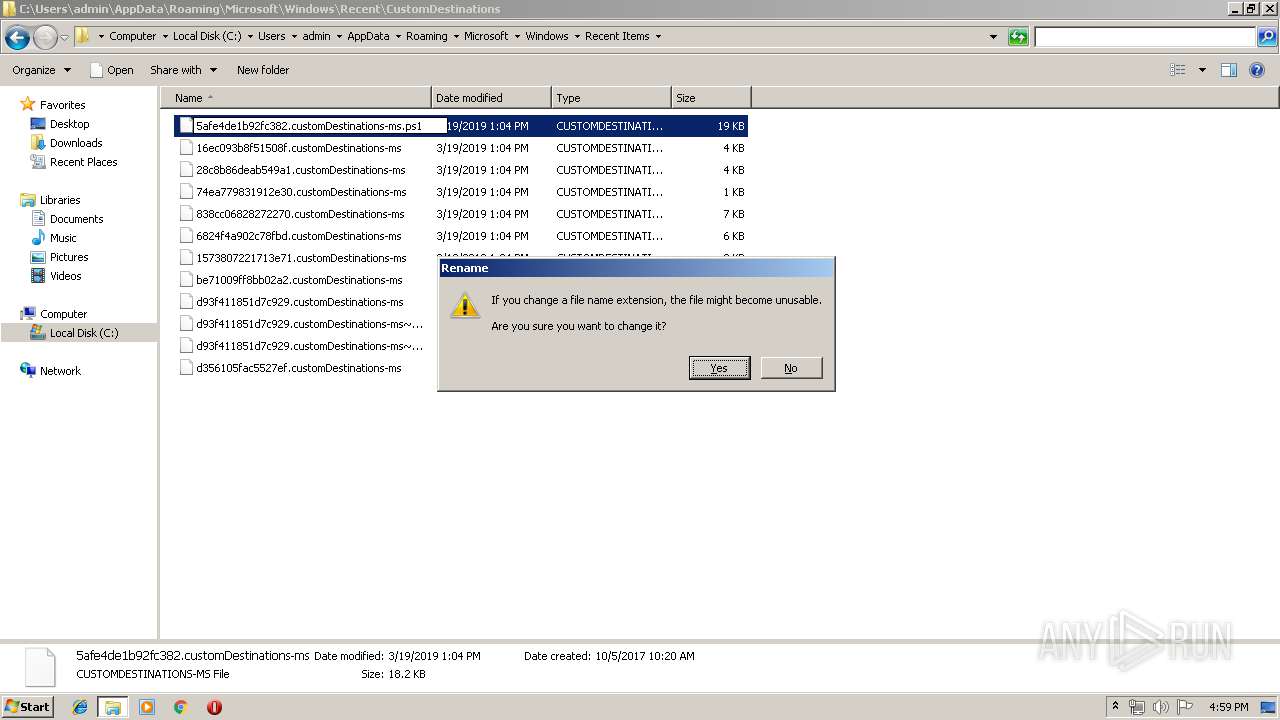
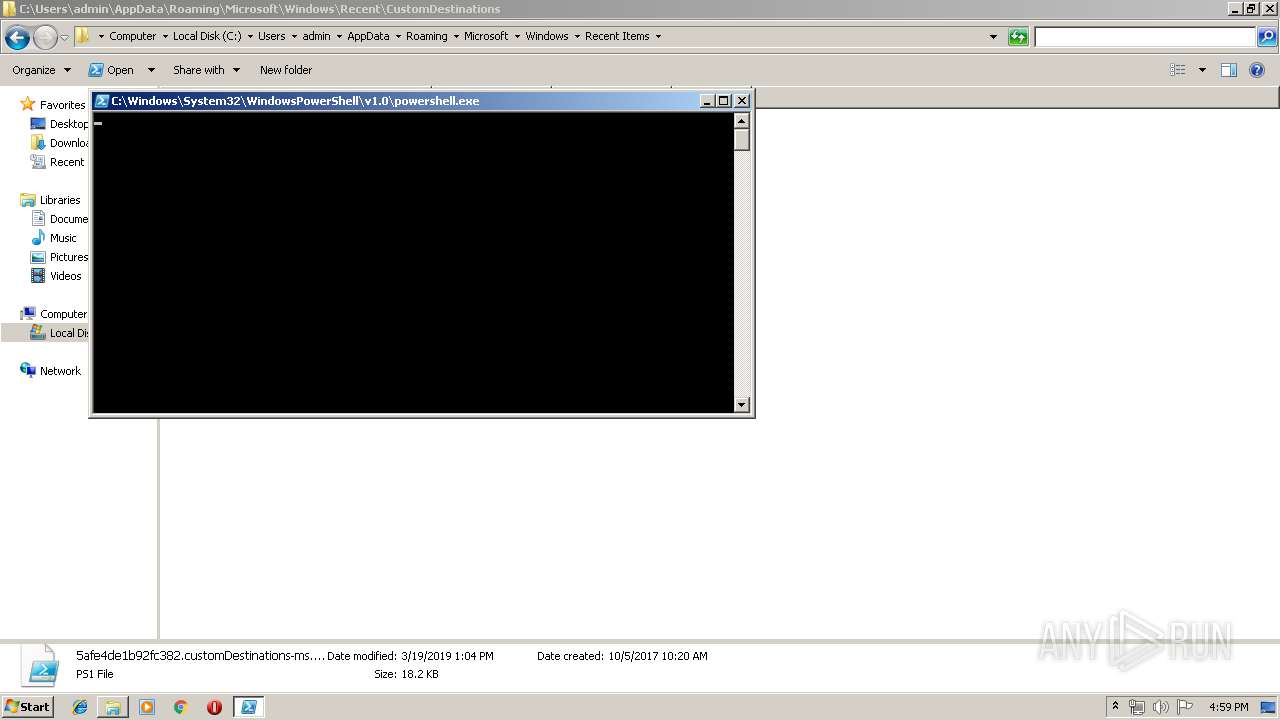
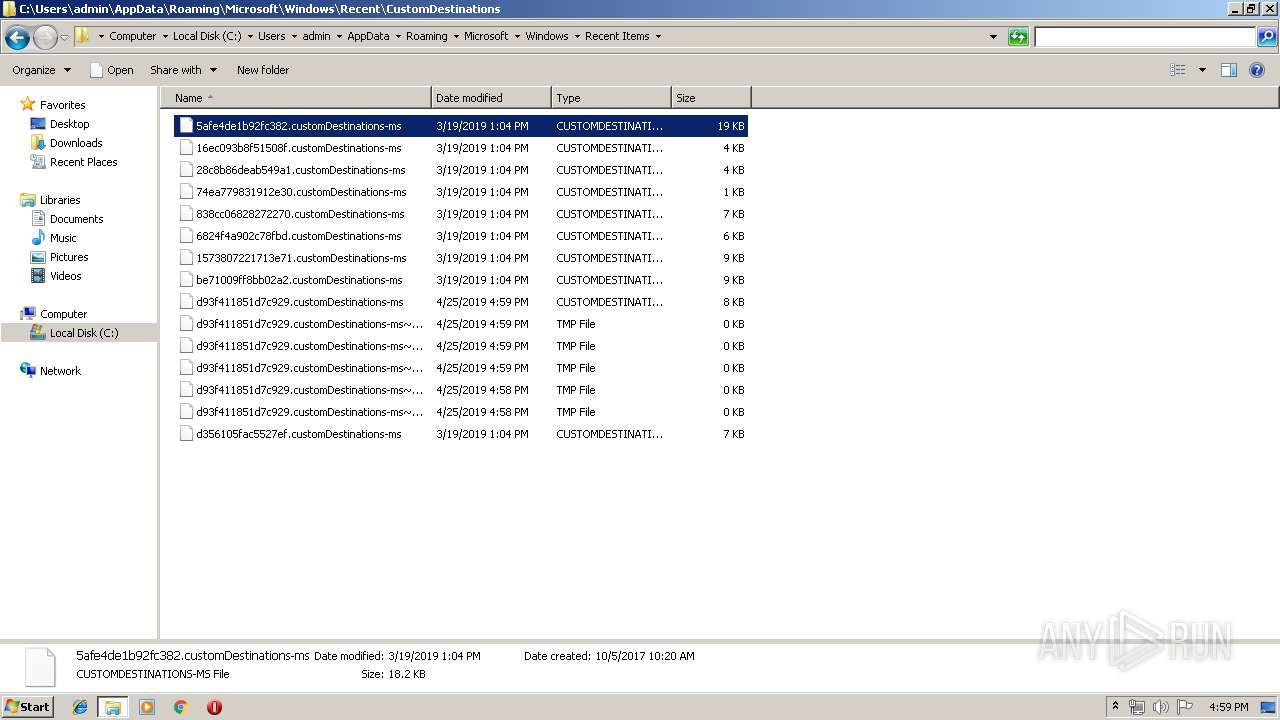
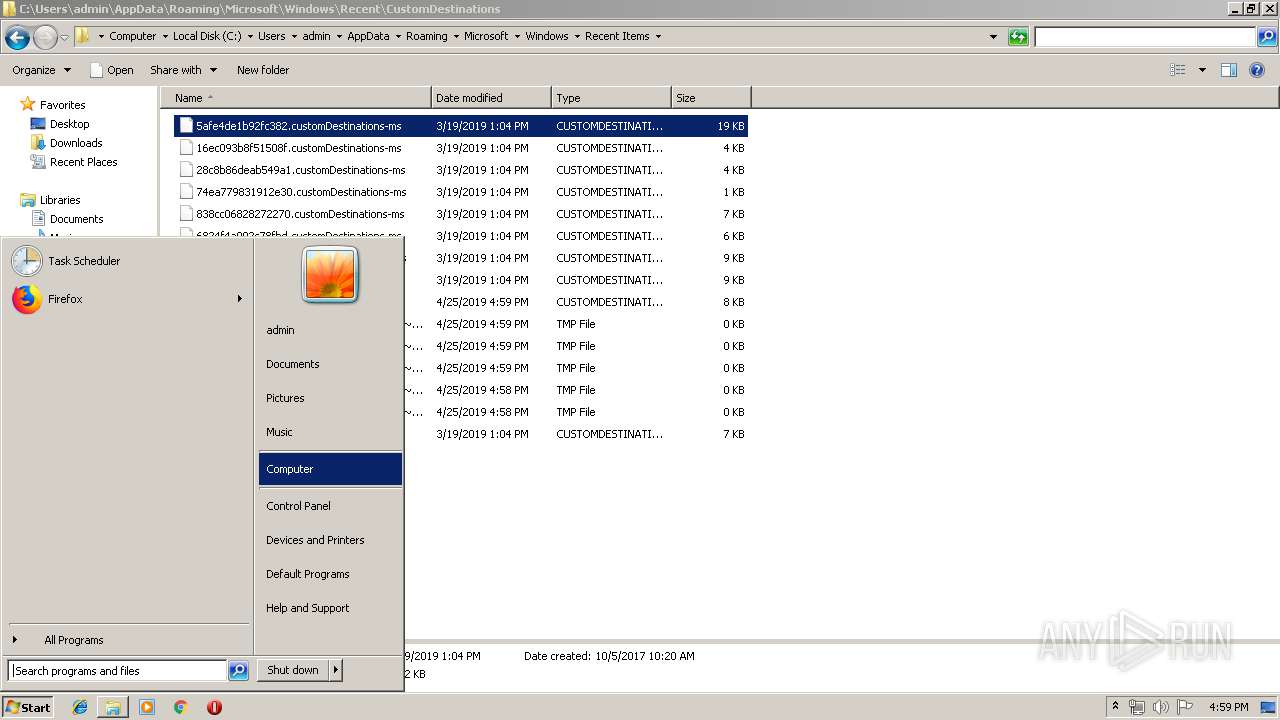
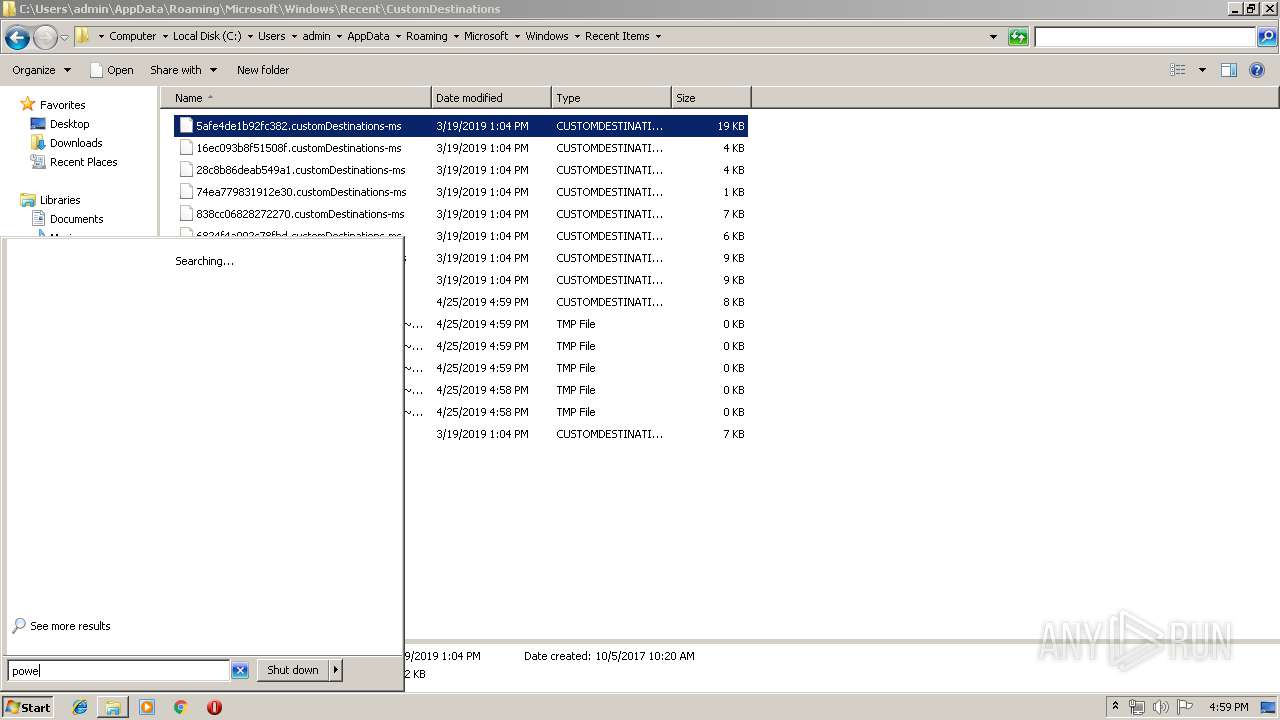
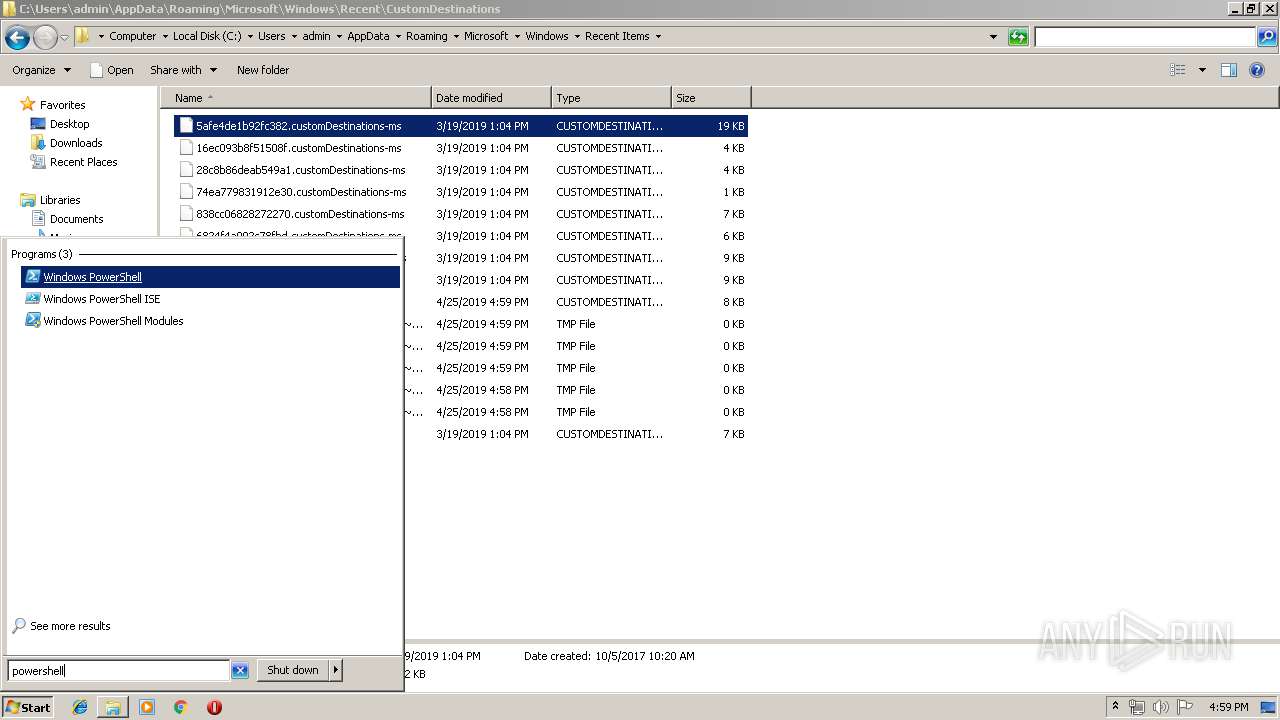
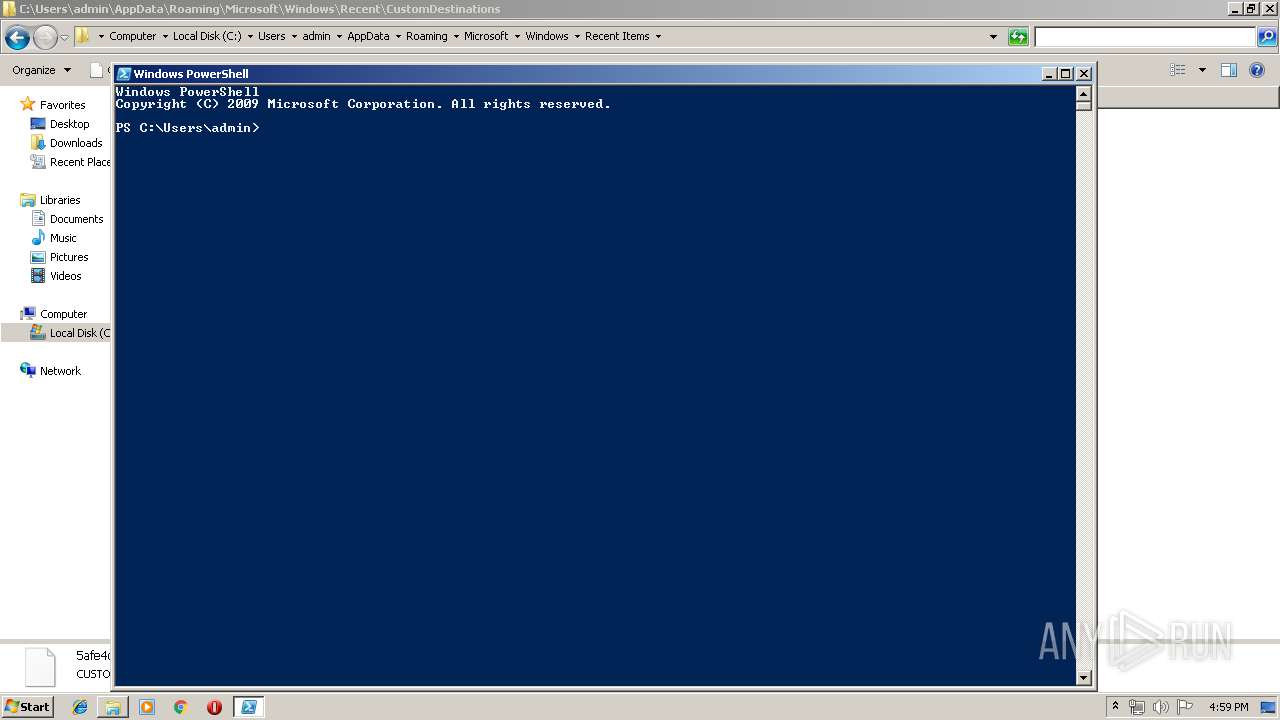
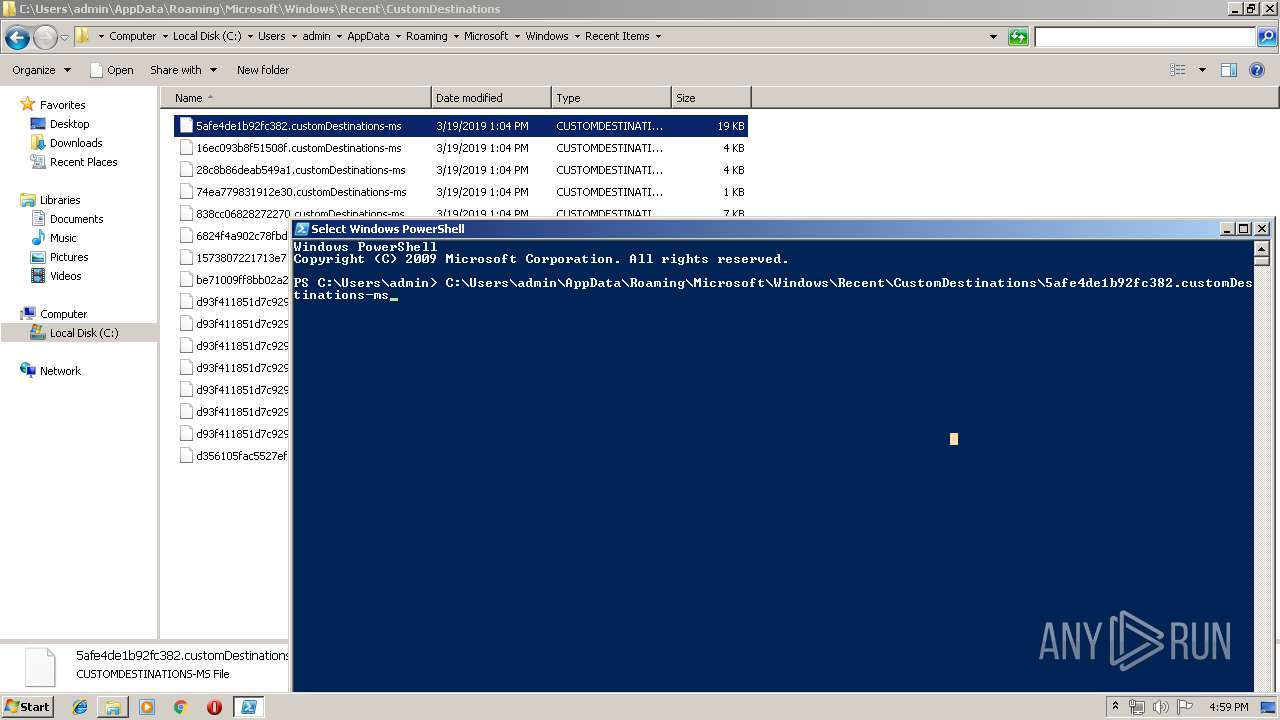
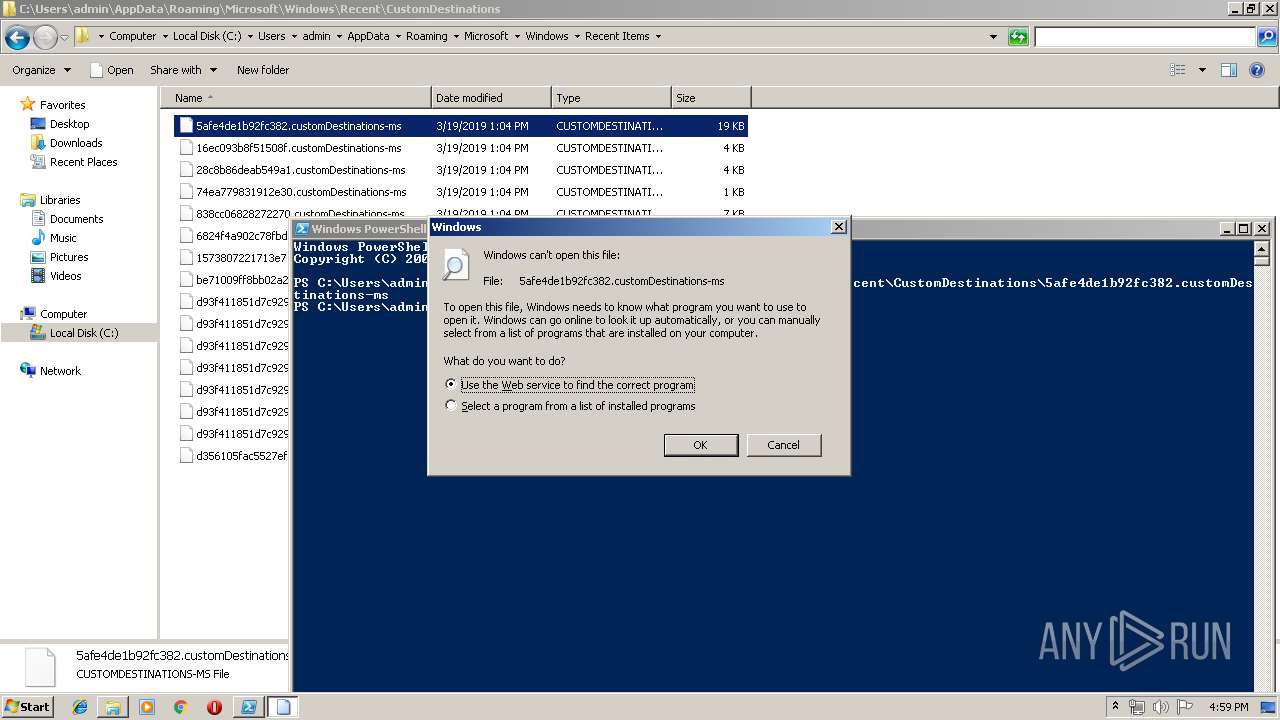
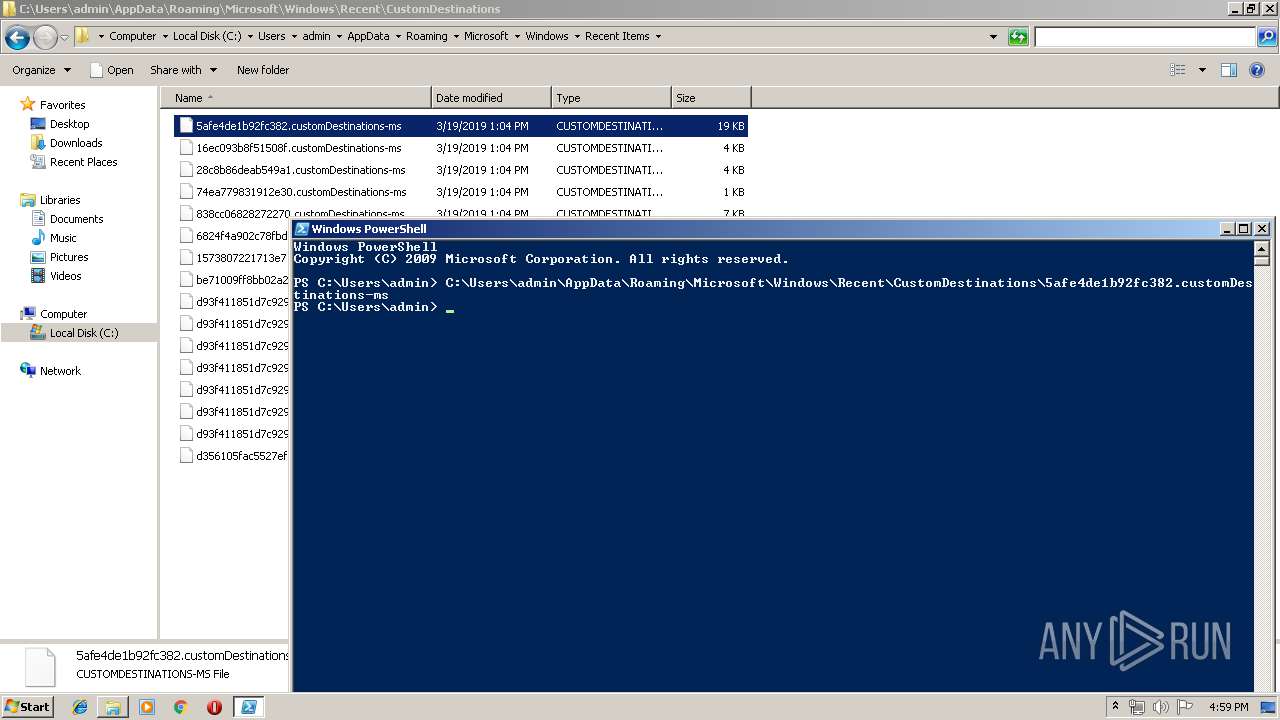
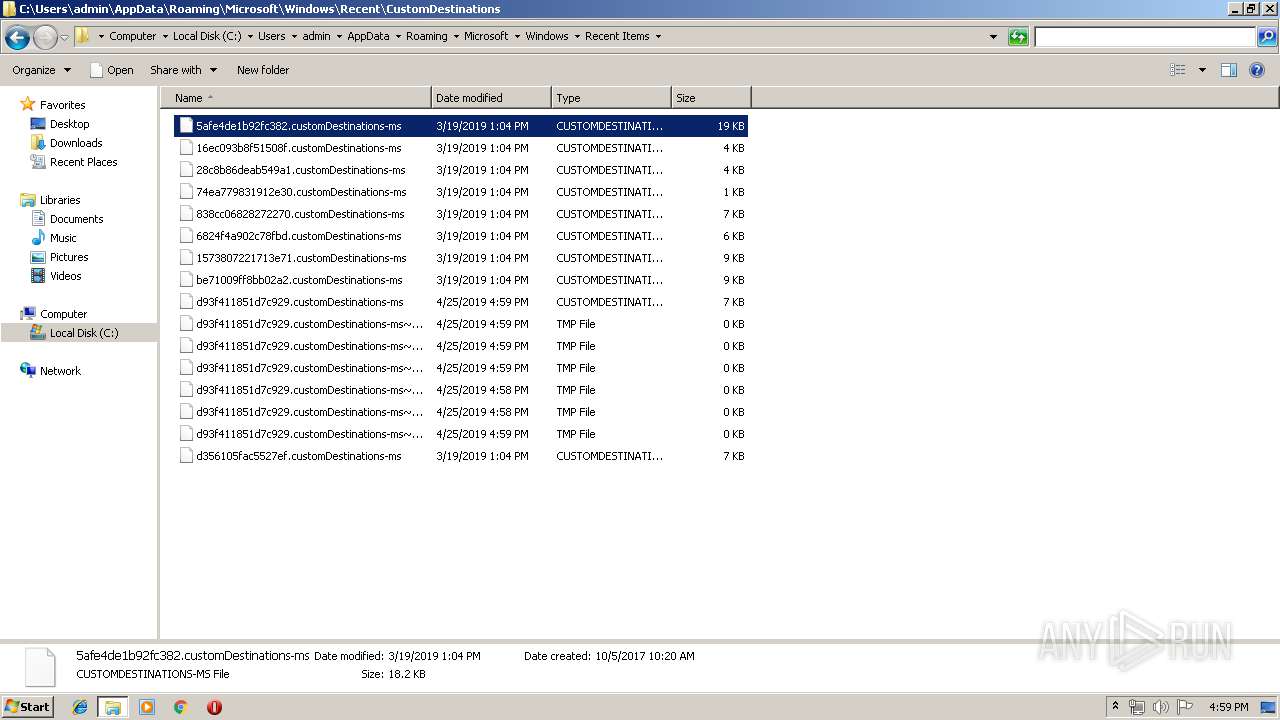
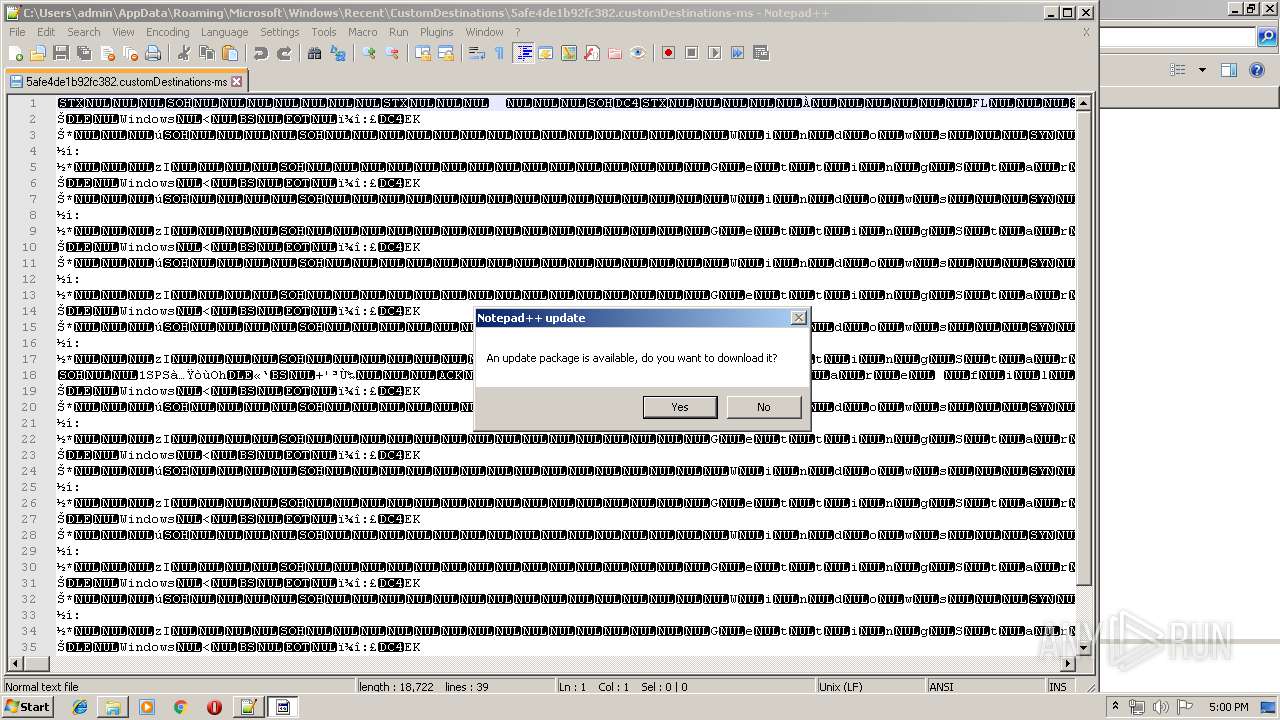
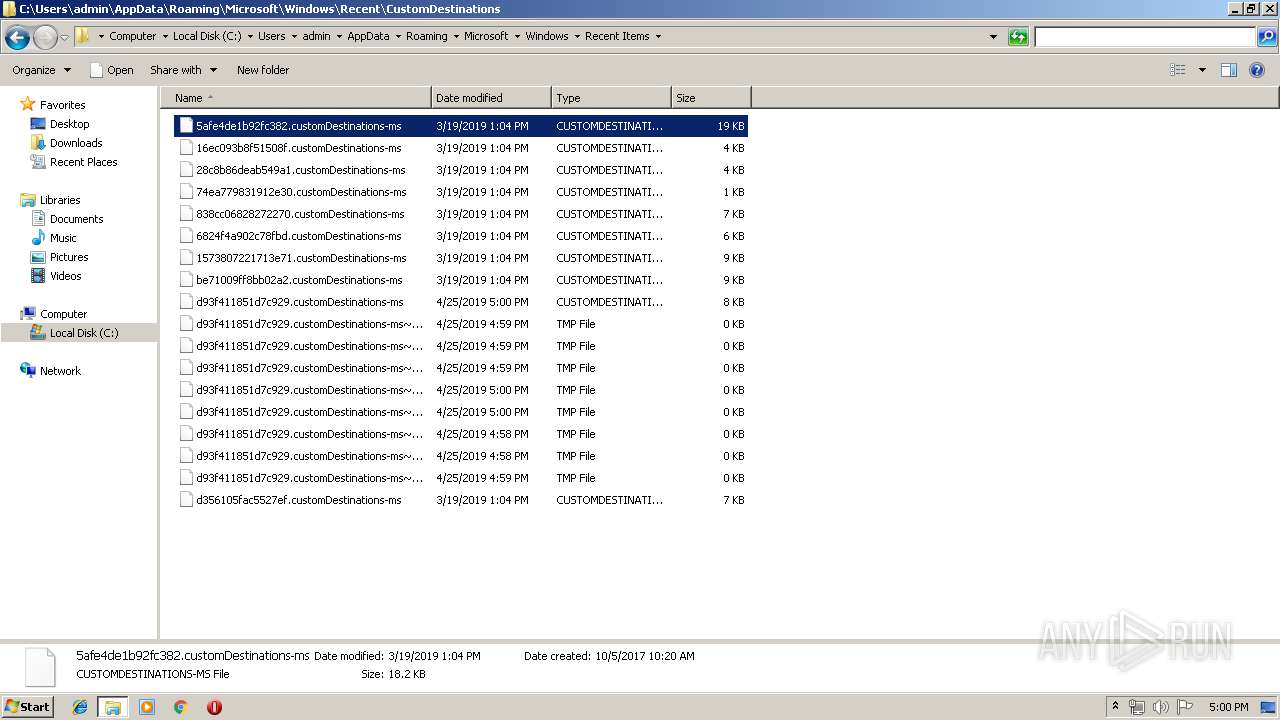
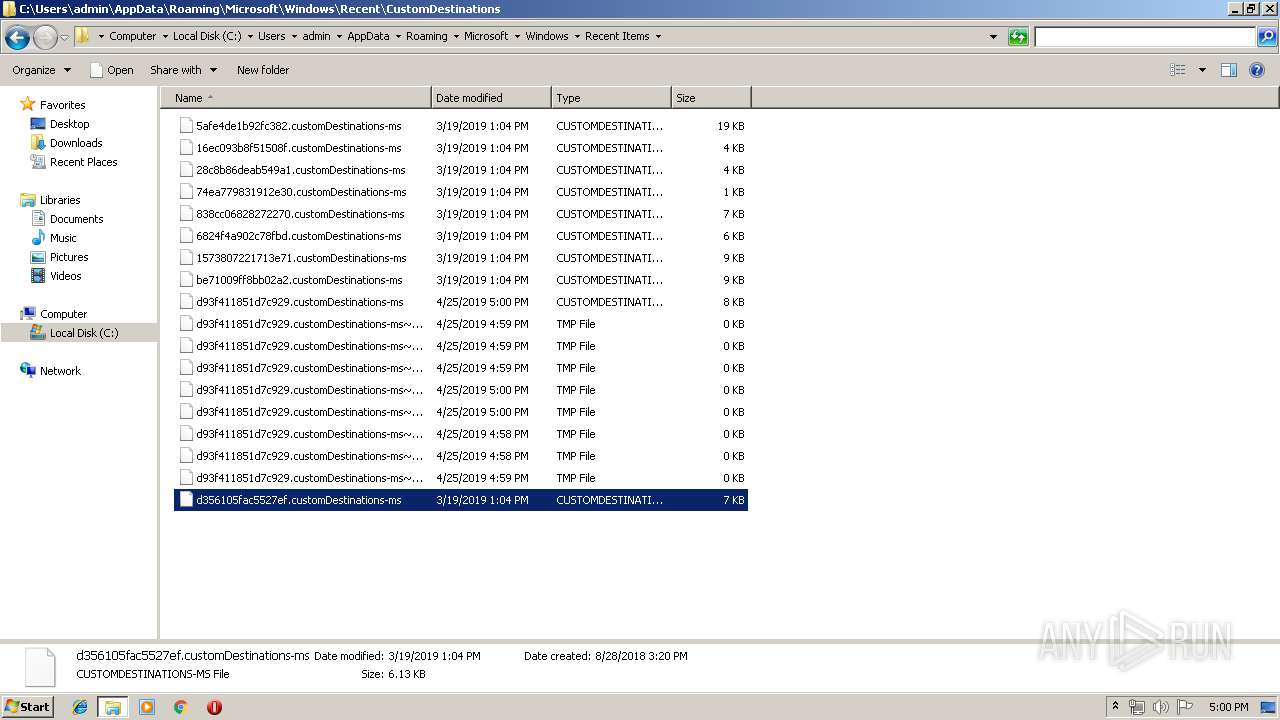
| 332 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "-file" "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\5afe4de1b92fc382.customDestinations-ms.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 704 | schtasks /create /F /sc minute /RU "SYSTEM" /mo 1 /tn "\UpdateTasks\JavaUpdates" /tr "wscript /b "C:\ProgramData\Windows\Microsoft\java\GoogleUpdateschecker.vbs"" | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 892 | "C:\Windows\system32\whoami.exe" | C:\Windows\system32\whoami.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: whoami - displays logged on user information Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 940 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1260 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -exec bypass -file C:\ProgramData\Windows\Microsoft\java\dUpdateCheckers.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | wscript.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1324 | "C:\WINDOWS\system32\WindowsPowerShell\v1.0\powershell.exe" | C:\WINDOWS\system32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 3221225786 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
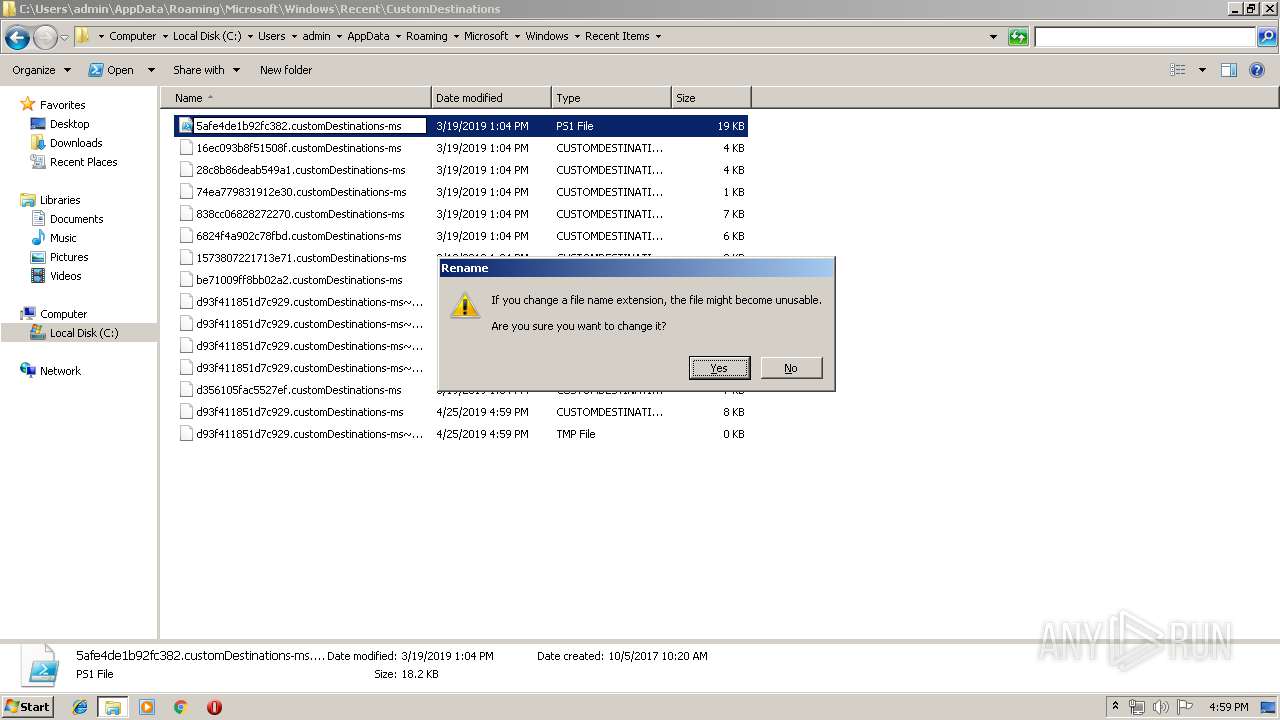
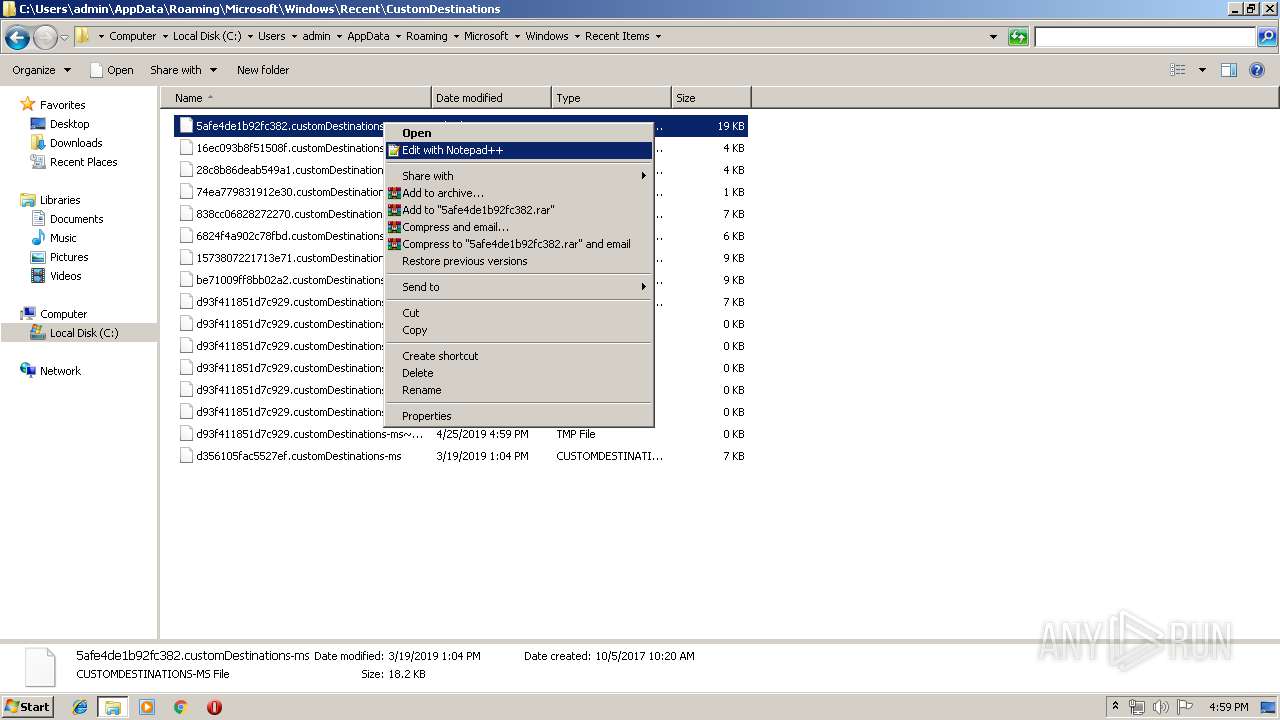
| 1336 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\5afe4de1b92fc382.customDestinations-ms" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.51 Modules
| |||||||||||||||
| 1356 | "C:\Windows\system32\whoami.exe" | C:\Windows\system32\whoami.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: whoami - displays logged on user information Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 368
Read events
3 515
Write events
853
Delete events
0
Modification events
| (PID) Process: | (2344) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2344) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2344) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2344) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\f.vbs.zip | |||
| (PID) Process: | (2344) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2344) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2344) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2344) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2344) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\wshext.dll,-4802 |
Value: VBScript Script File | |||
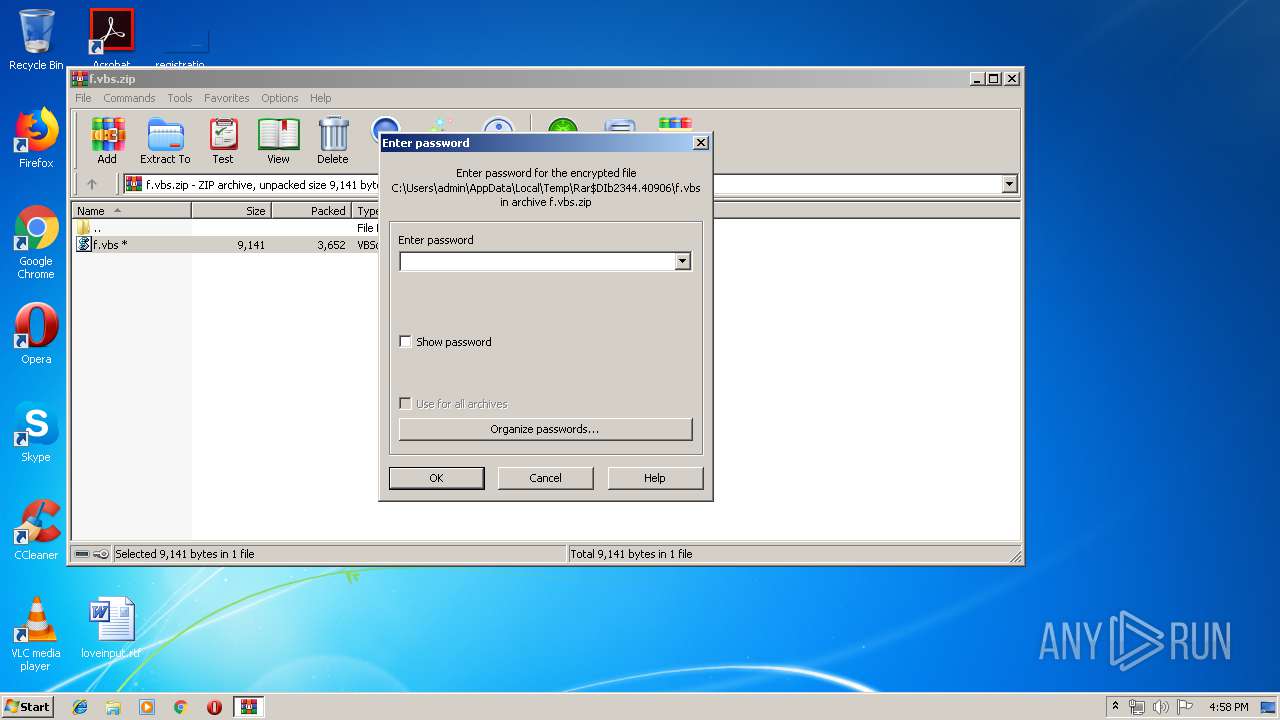
| (PID) Process: | (2344) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
0
Suspicious files
28
Text files
13
Unknown types
0
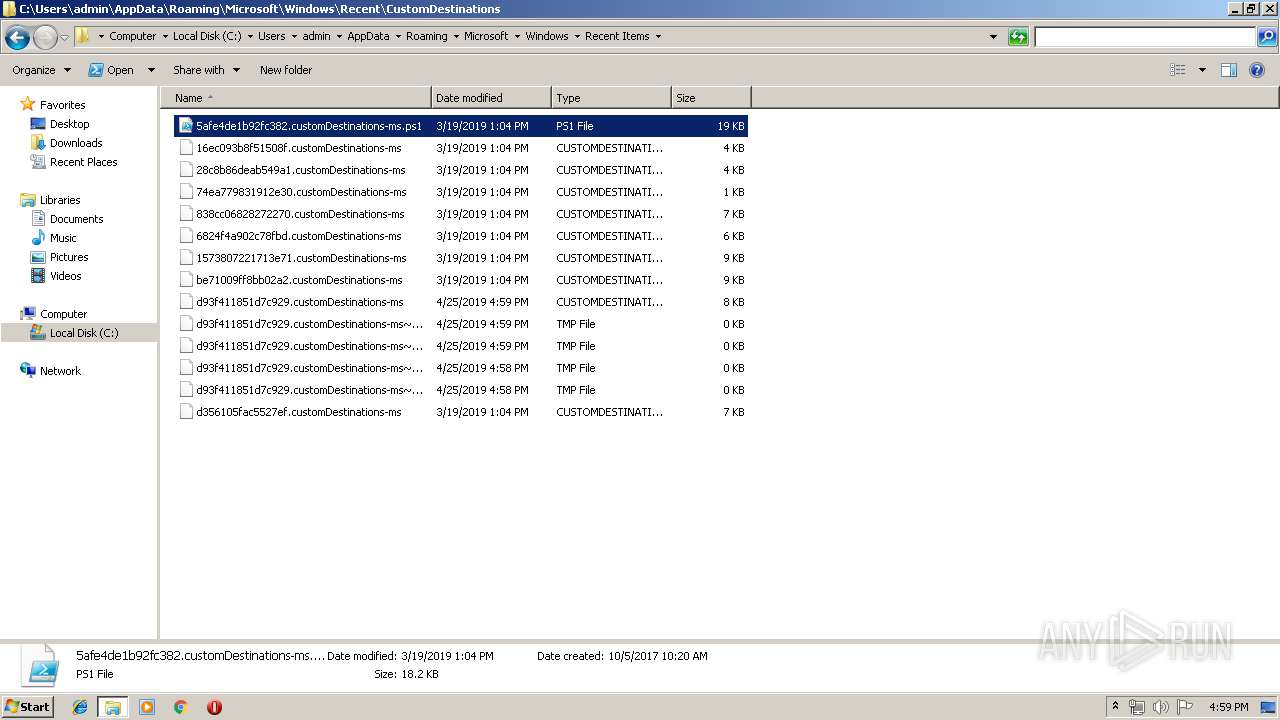
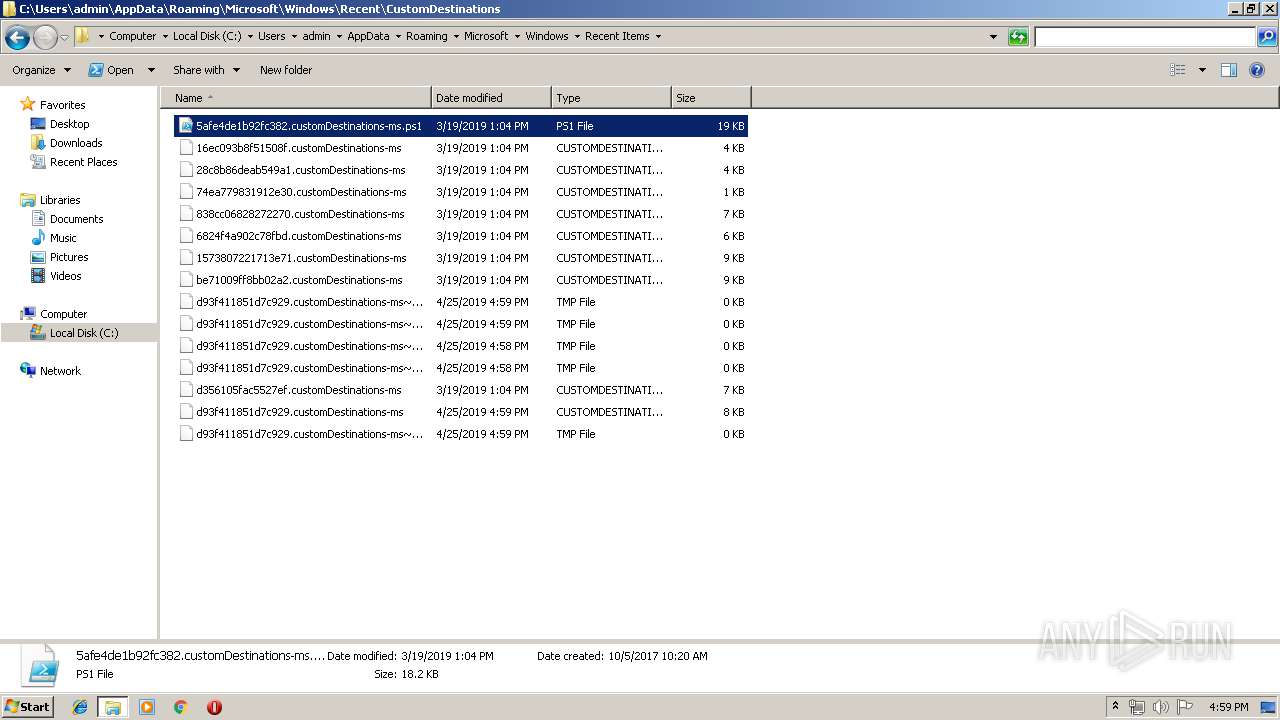
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
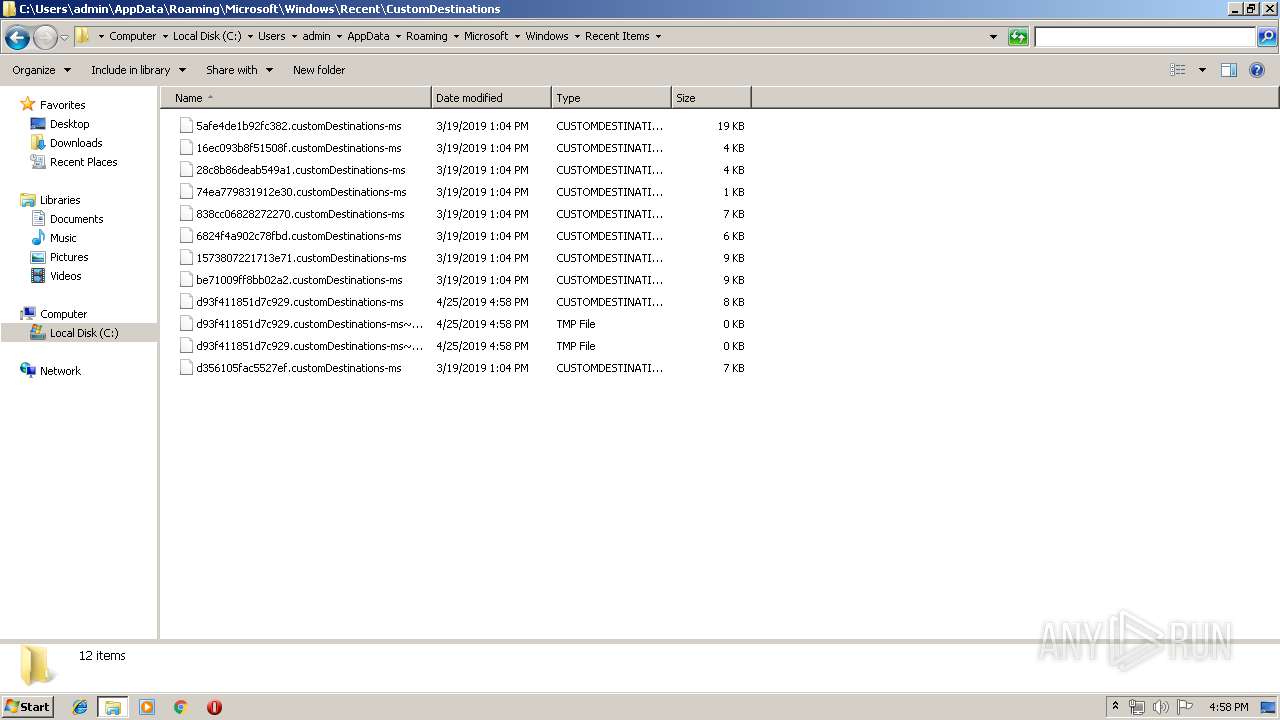
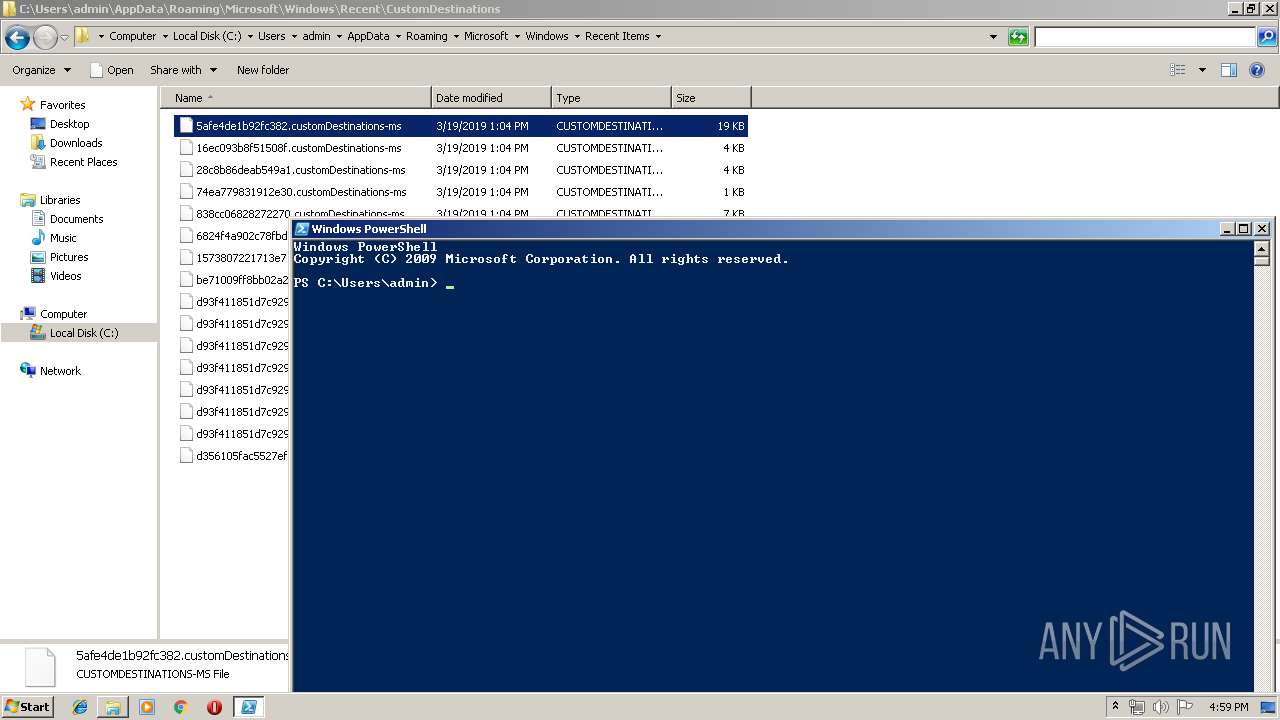
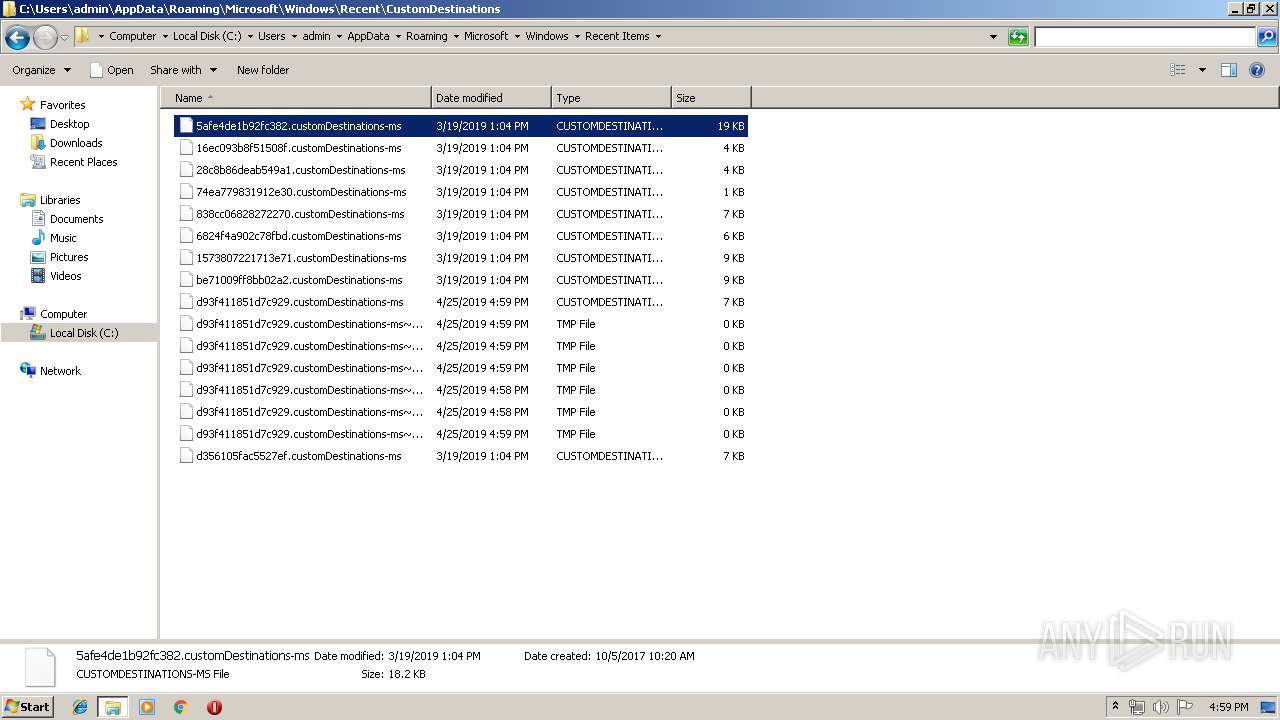
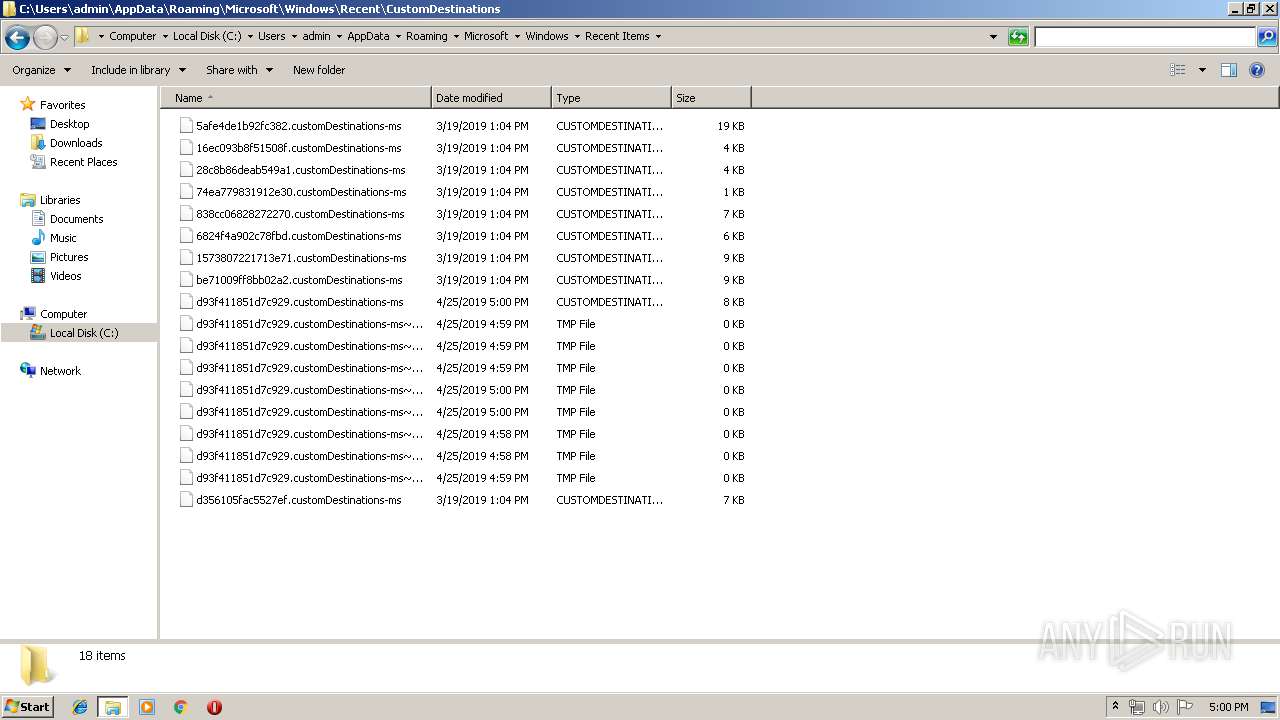
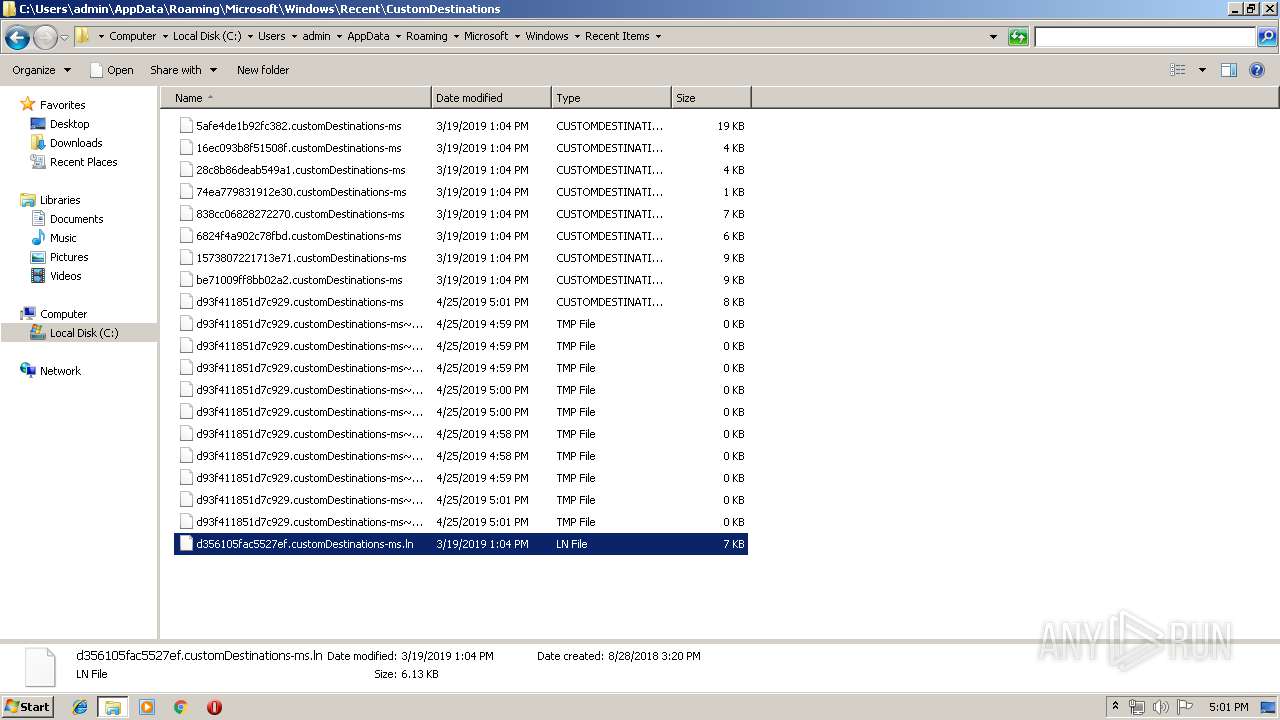
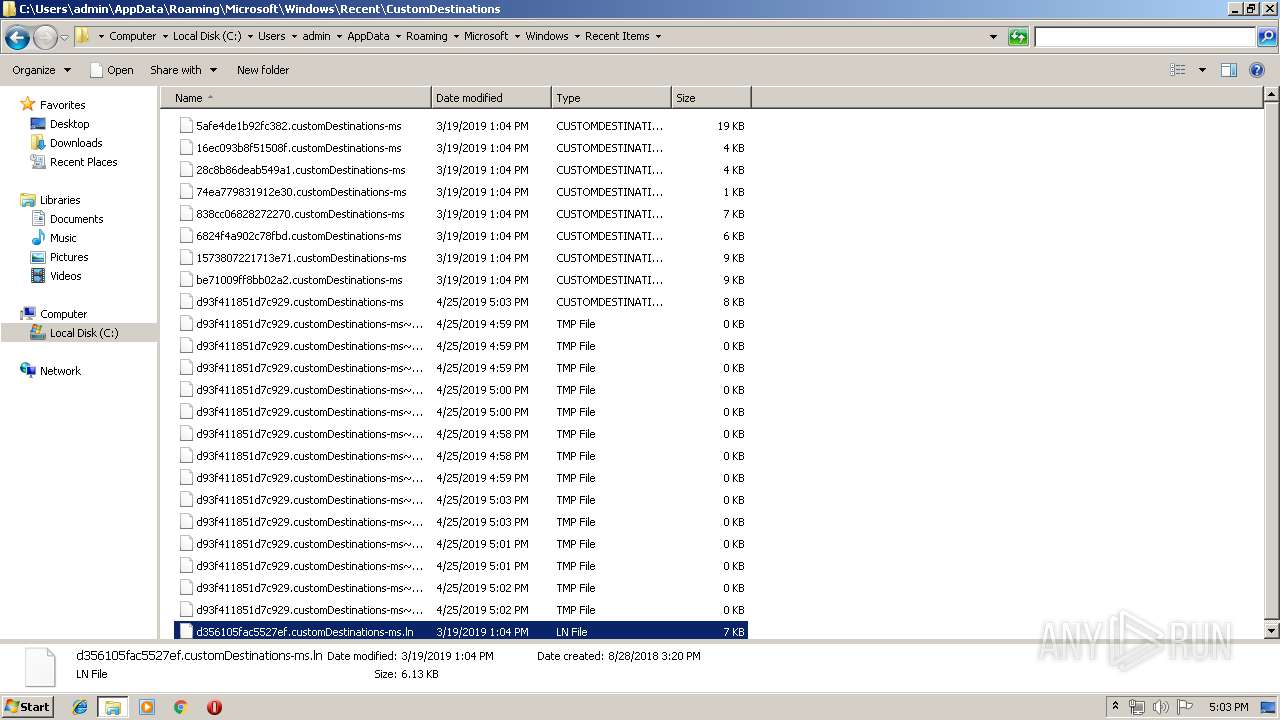
| 2664 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\8H7G5NOCARZHTNRPHFKN.temp | — | |
MD5:— | SHA256:— | |||
| 2072 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\U81NJ7KM68XYBE1GS502.temp | — | |
MD5:— | SHA256:— | |||
| 3540 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\Q64FH5AYCR49DI3K161L.temp | — | |
MD5:— | SHA256:— | |||
| 2916 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\XXOBOD3U5WB4NUGU2PYS.temp | — | |
MD5:— | SHA256:— | |||
| 332 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\2U793DIDICIB8FCZW2F1.temp | — | |
MD5:— | SHA256:— | |||
| 1324 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\IOSIBT3Z10TIMRA8MWNY.temp | — | |
MD5:— | SHA256:— | |||
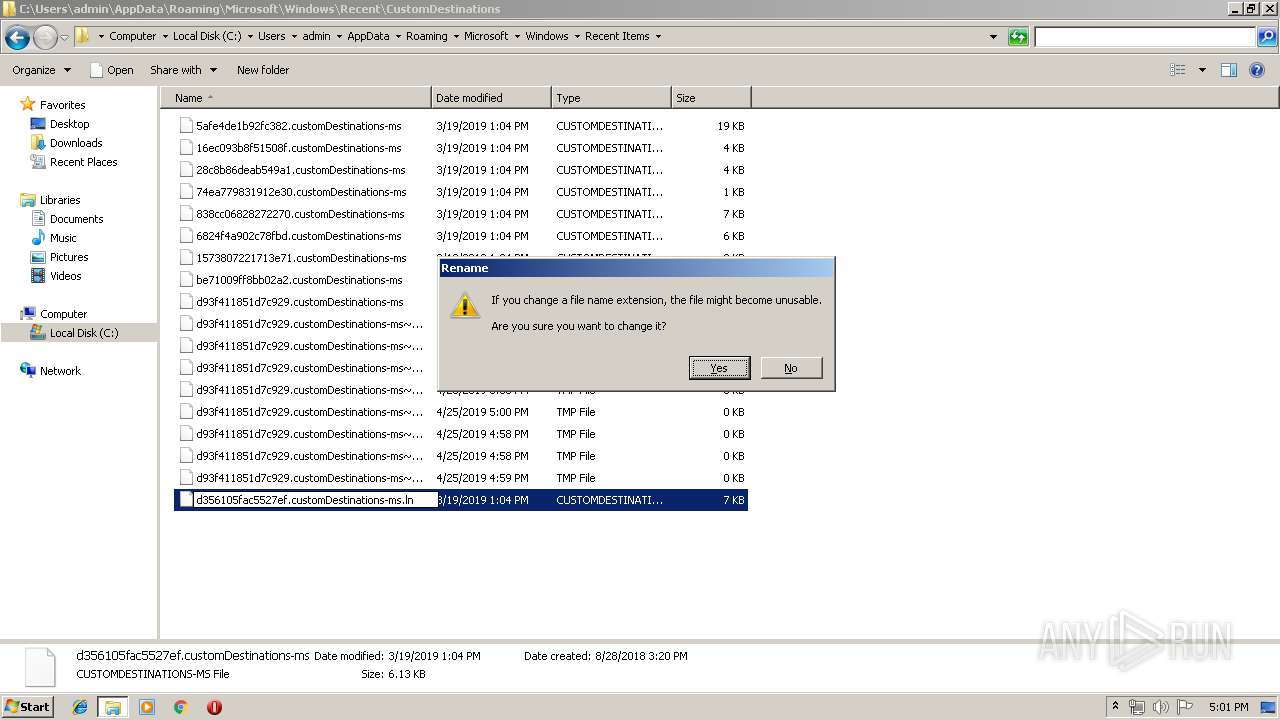
| 2664 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF115adf.TMP | binary | |
MD5:— | SHA256:— | |||
| 3540 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF11c512.TMP | binary | |
MD5:— | SHA256:— | |||
| 2072 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2664 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
40
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.21.242.187:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | NL | der | 1.37 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 2.21.242.187:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | NL | whitelisted |
3868 | gup.exe | 37.59.28.236:443 | notepad-plus-plus.org | OVH SAS | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.mumbai-m.site |
| malicious |
3343498367960000D103199D3C3FB007.mumbai-m.site |
| unknown |
27550000D103199D3C3FB007.mumbai-m.site |
| unknown |
7261790000D103199D3C3FB007.mumbai-m.site |
| unknown |
73186835900000D103199D3C3FB007.mumbai-m.site |
| unknown |
171576380000D103199D3C3FB007.mumbai-m.site |
| unknown |
92136365316188584000D103199D3C3FB007.757365722D70635C61646D696E2A2A2A2A2A2A2A2A2A2A2A2A.mumbai-m.site |
| unknown |
520000D103199D3C3FB007.mumbai-m.site |
| malicious |
890000D103199D3C3FB007.mumbai-m.site |
| malicious |
6499589536280000D103199D3C3FB007.mumbai-m.site |
| unknown |
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|