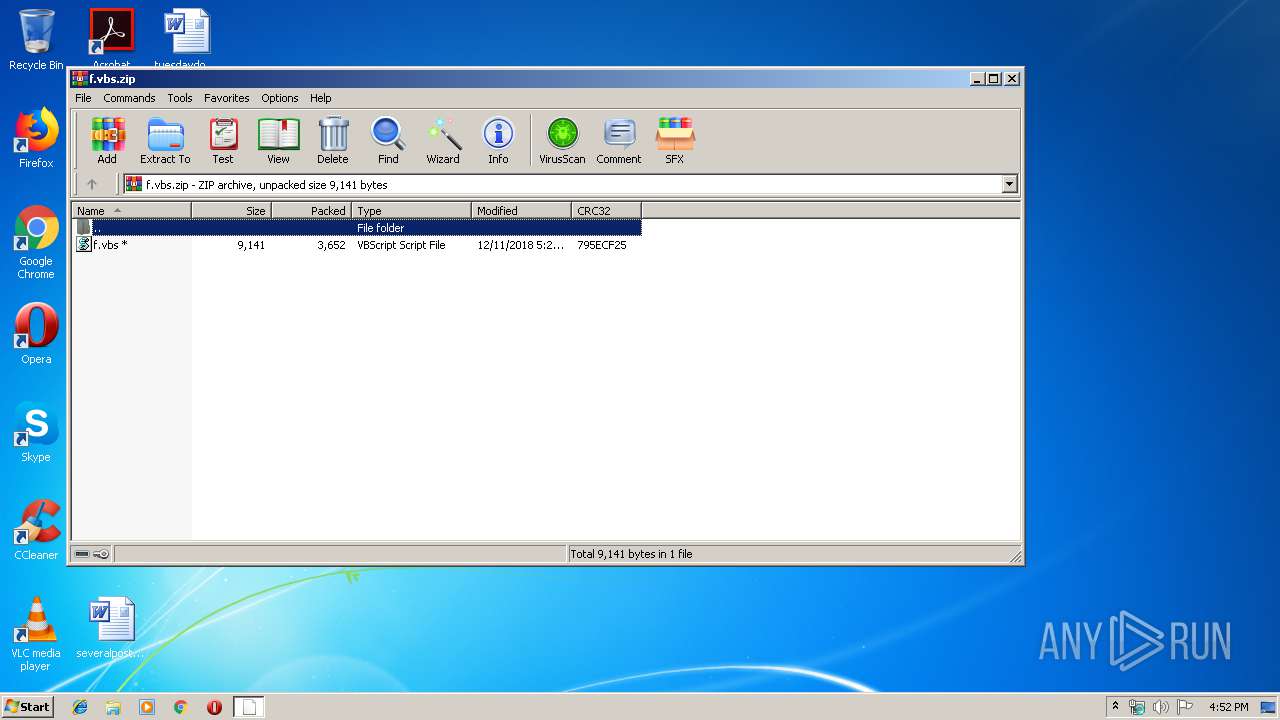
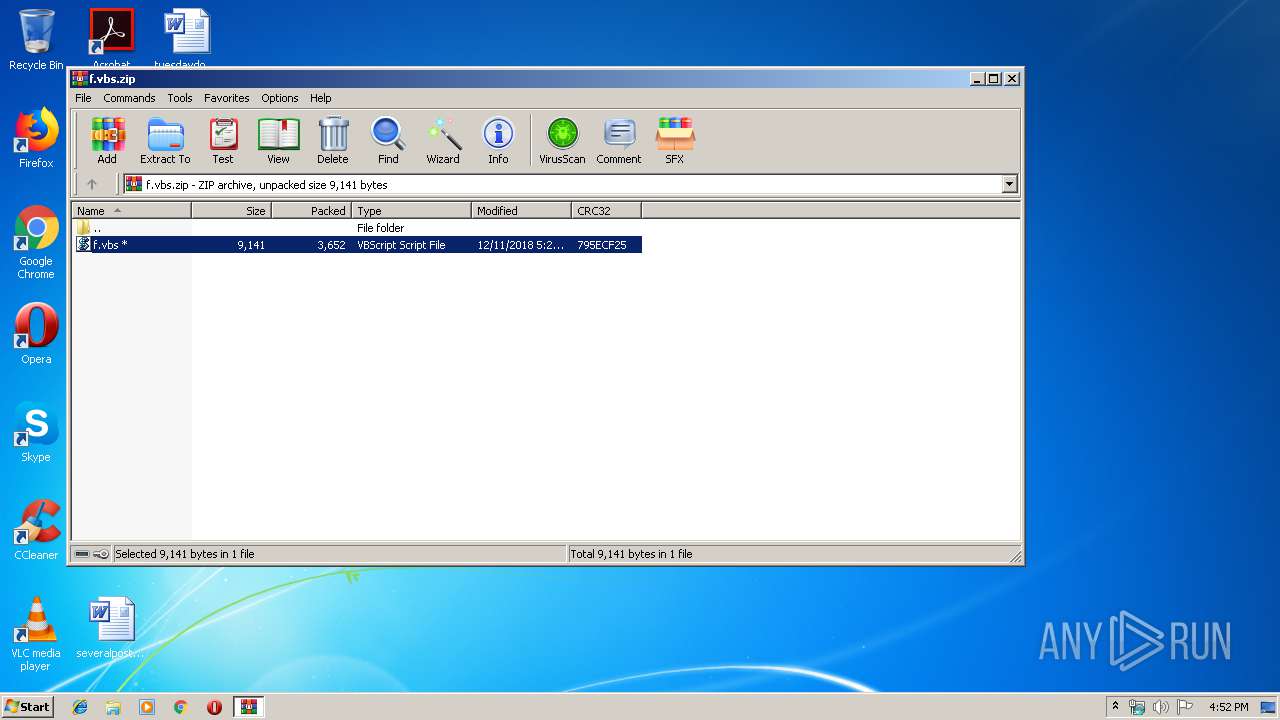
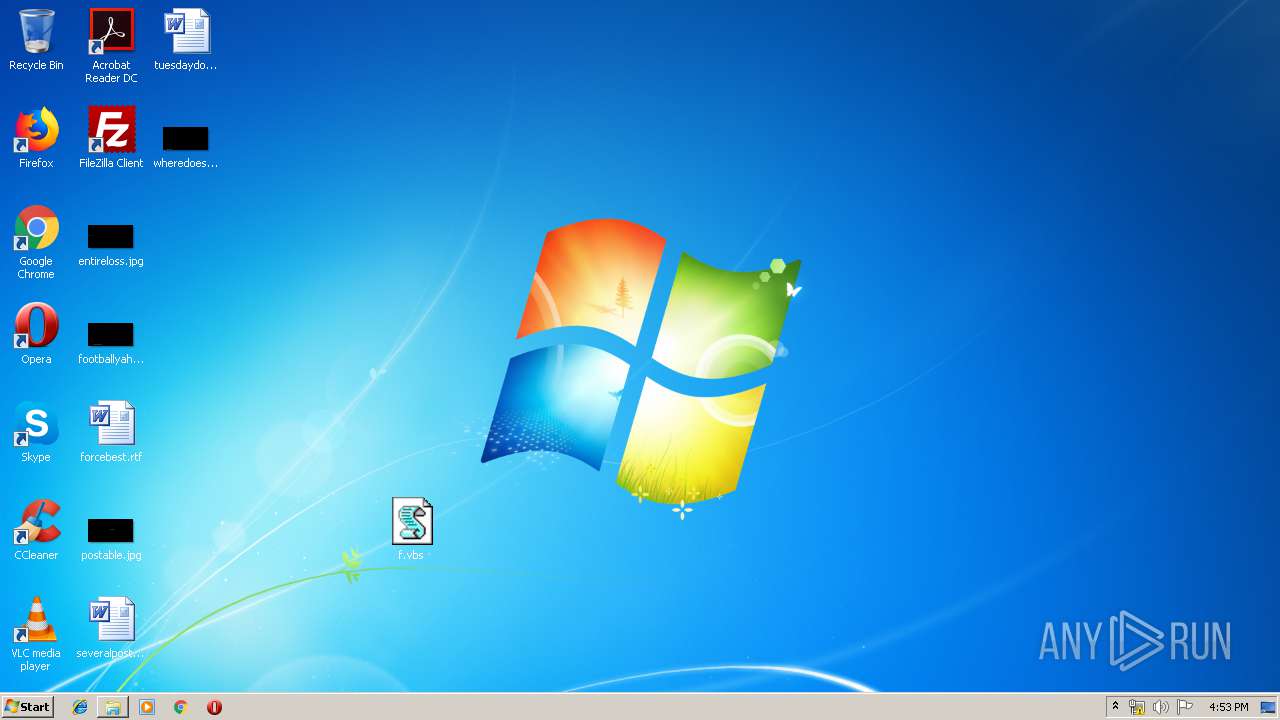
| File name: | f.vbs.zip |
| Full analysis: | https://app.any.run/tasks/1d103968-ef70-46fd-8874-f629e89e88f3 |
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2019, 15:51:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 7897EE2EB7816E0780D2F33439B0B598 |
| SHA1: | 0CA8F3EA0C6A338BD8025049F6C0920362A1534E |
| SHA256: | 1CB127AAA65C11597501F0B29BA5D83120F4580D39B1DDE6C598F92A3C800400 |
| SSDEEP: | 96:euukk821JM8ga/XnsW3znJTs+H98YftG65:mK2/gaj5s+H9vo65 |
MALICIOUS
Starts CertUtil for decode files
- cmd.exe (PID: 2096)
- cmd.exe (PID: 2328)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2916)
- schtasks.exe (PID: 4032)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 2536)
SUSPICIOUS
Starts CMD.EXE for commands execution
- WScript.exe (PID: 2612)
Creates files in the program directory
- WScript.exe (PID: 2612)
- certutil.exe (PID: 3508)
- certutil.exe (PID: 1880)
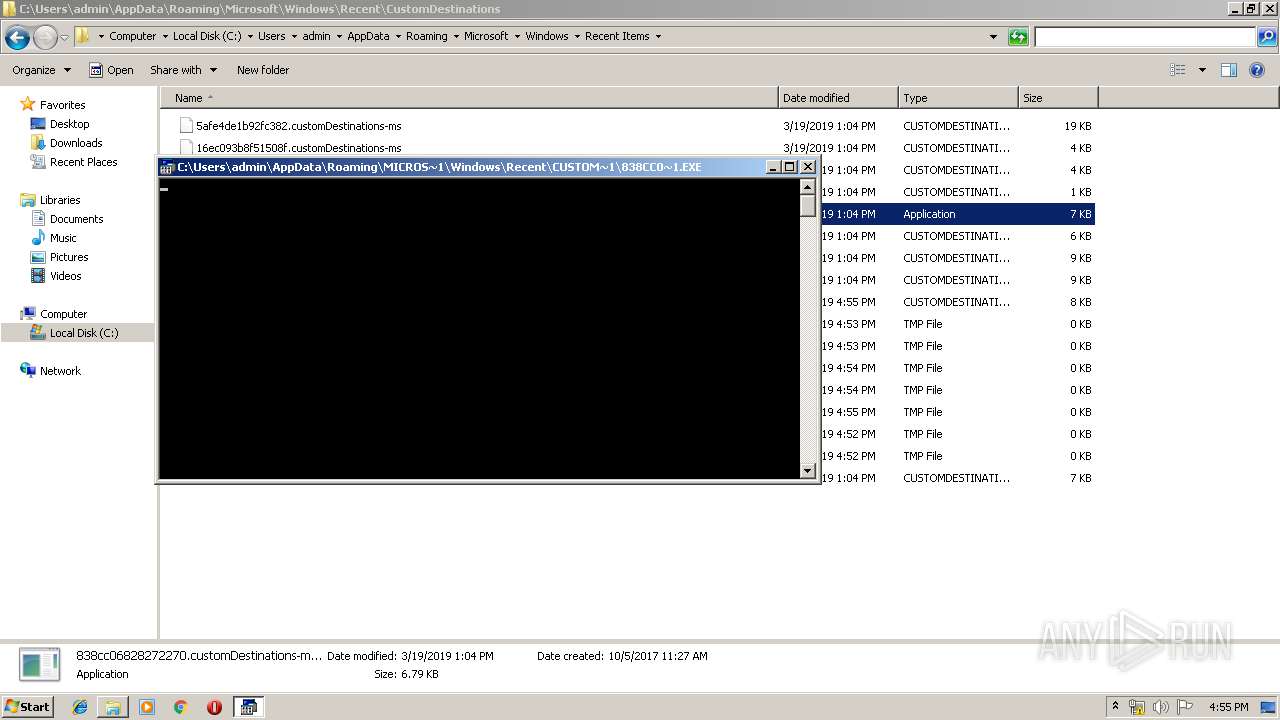
Executes scripts
- cmd.exe (PID: 2800)
Creates files in the user directory
- powershell.exe (PID: 3180)
- powershell.exe (PID: 2232)
- powershell.exe (PID: 2728)
- powershell.exe (PID: 2448)
- powershell.exe (PID: 2196)
- powershell.exe (PID: 2456)
- powershell.exe (PID: 3144)
- powershell.exe (PID: 3164)
- powershell.exe (PID: 2592)
- powershell.exe (PID: 3768)
- powershell.exe (PID: 3396)
- powershell.exe (PID: 3776)
Executes PowerShell scripts
- wscript.exe (PID: 2792)
- wscript.EXE (PID: 3348)
- wscript.EXE (PID: 2636)
- wscript.EXE (PID: 2116)
- wscript.EXE (PID: 3792)
- wscript.EXE (PID: 2256)
Uses WHOAMI.EXE to obtaining logged on user information
- powershell.exe (PID: 2232)
- powershell.exe (PID: 2728)
- powershell.exe (PID: 2592)
- powershell.exe (PID: 2456)
- powershell.exe (PID: 3396)
- powershell.exe (PID: 3164)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2018:12:11 18:29:17 |
| ZipCRC: | 0x795ecf25 |
| ZipCompressedSize: | 3652 |
| ZipUncompressedSize: | 9141 |
| ZipFileName: | f.vbs |
Total processes
103
Monitored processes
40
Malicious processes
3
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1656 | "C:\Windows\system32\ntvdm.exe" -i2 | C:\Windows\system32\ntvdm.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NTVDM.EXE Exit code: 255 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1880 | certutil -f -decode C:\ProgramData\Windows\Microsoft\java\hUpdateCheckers.base C:\ProgramData\Windows\Microsoft\java\hUpdateCheckers.ps1 | C:\Windows\system32\certutil.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CertUtil.exe Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2096 | "C:\Windows\System32\cmd.exe" /C certutil -f -decode C:\ProgramData\Windows\Microsoft\java\dUpdateCheckers.base C:\ProgramData\Windows\Microsoft\java\dUpdateCheckers.ps1 | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2116 | C:\Windows\system32\wscript.EXE /b C:\ProgramData\Windows\Microsoft\java\GoogleUpdateschecker.vbs | C:\Windows\system32\wscript.EXE | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2196 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -exec bypass -file C:\ProgramData\Windows\Microsoft\java\hUpdateCheckers.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | wscript.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2232 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -exec bypass -file C:\ProgramData\Windows\Microsoft\java\dUpdateCheckers.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2256 | C:\Windows\system32\wscript.EXE /b C:\ProgramData\Windows\Microsoft\java\GoogleUpdateschecker.vbs | C:\Windows\system32\wscript.EXE | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2316 | "C:\Windows\system32\whoami.exe" | C:\Windows\system32\whoami.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: whoami - displays logged on user information Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2328 | "C:\Windows\System32\cmd.exe" /C certutil -f -decode C:\ProgramData\Windows\Microsoft\java\hUpdateCheckers.base C:\ProgramData\Windows\Microsoft\java\hUpdateCheckers.ps1 | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2400 | "C:\Windows\system32\whoami.exe" | C:\Windows\system32\whoami.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: whoami - displays logged on user information Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 628
Read events
2 906
Write events
722
Delete events
0
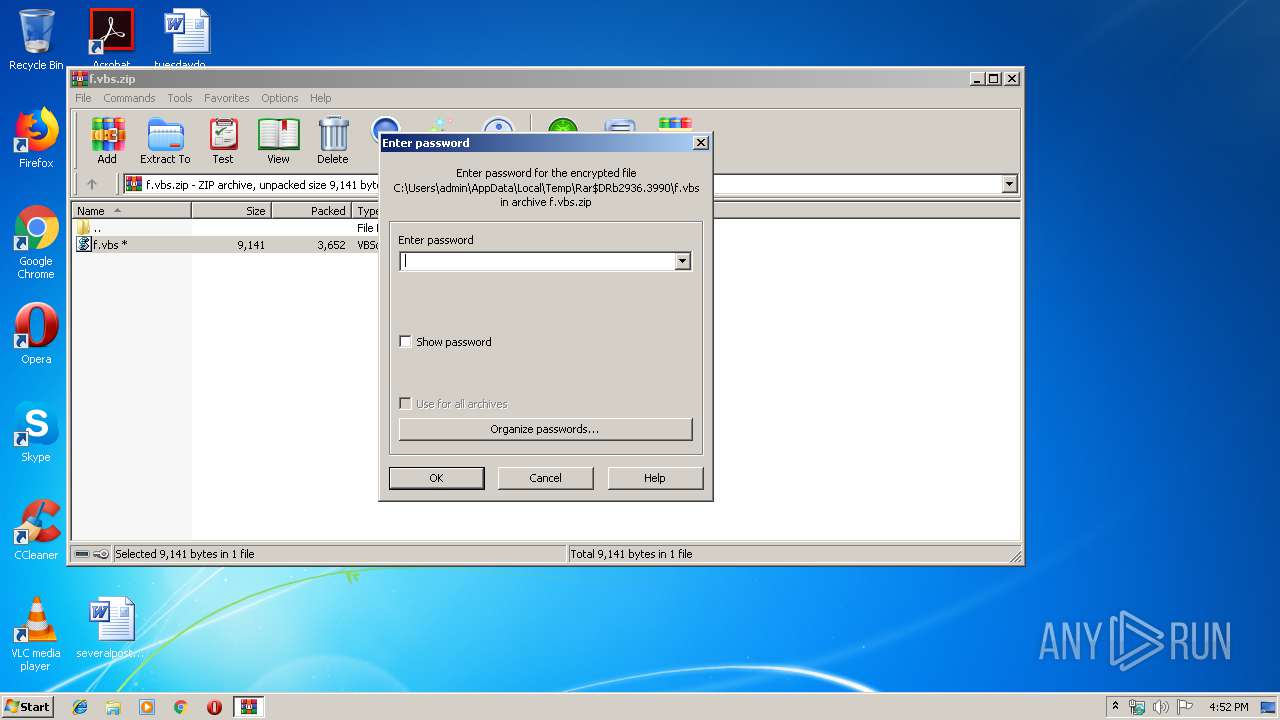
Modification events
| (PID) Process: | (2936) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2936) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2936) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2936) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\f.vbs.zip | |||
| (PID) Process: | (2936) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2936) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2936) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2936) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2936) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\wshext.dll,-4802 |
Value: VBScript Script File | |||
| (PID) Process: | (2936) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
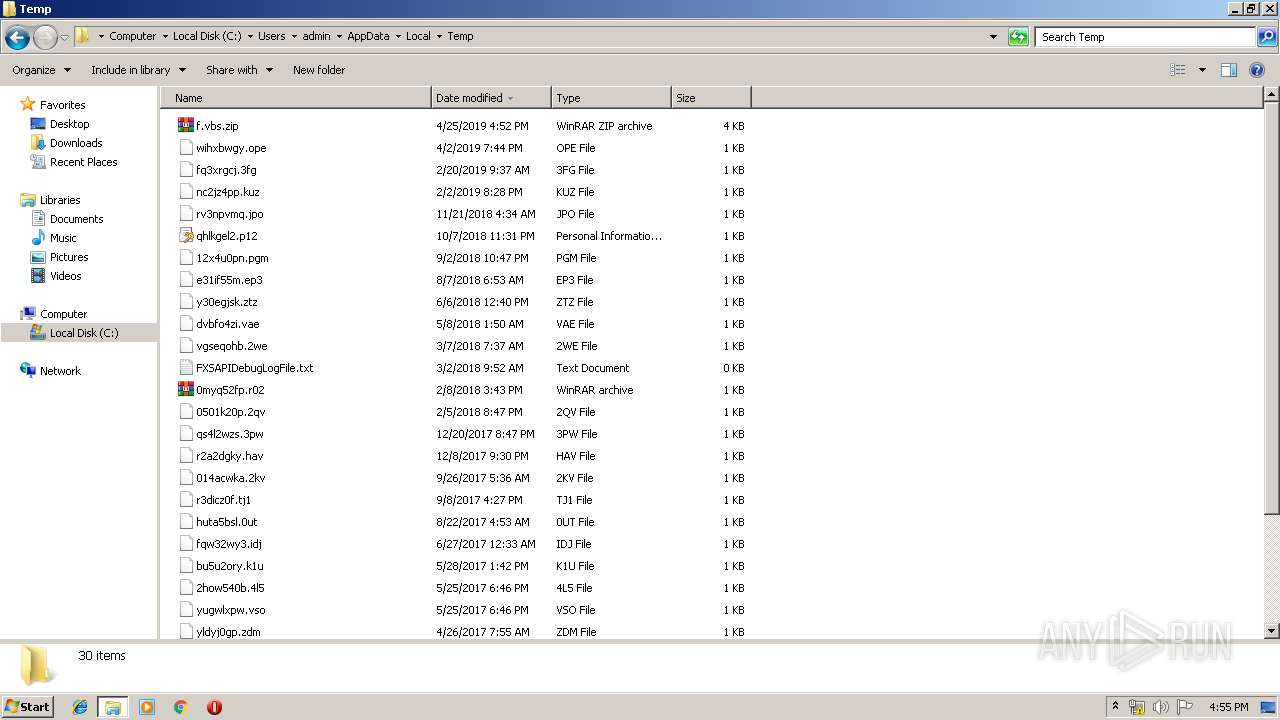
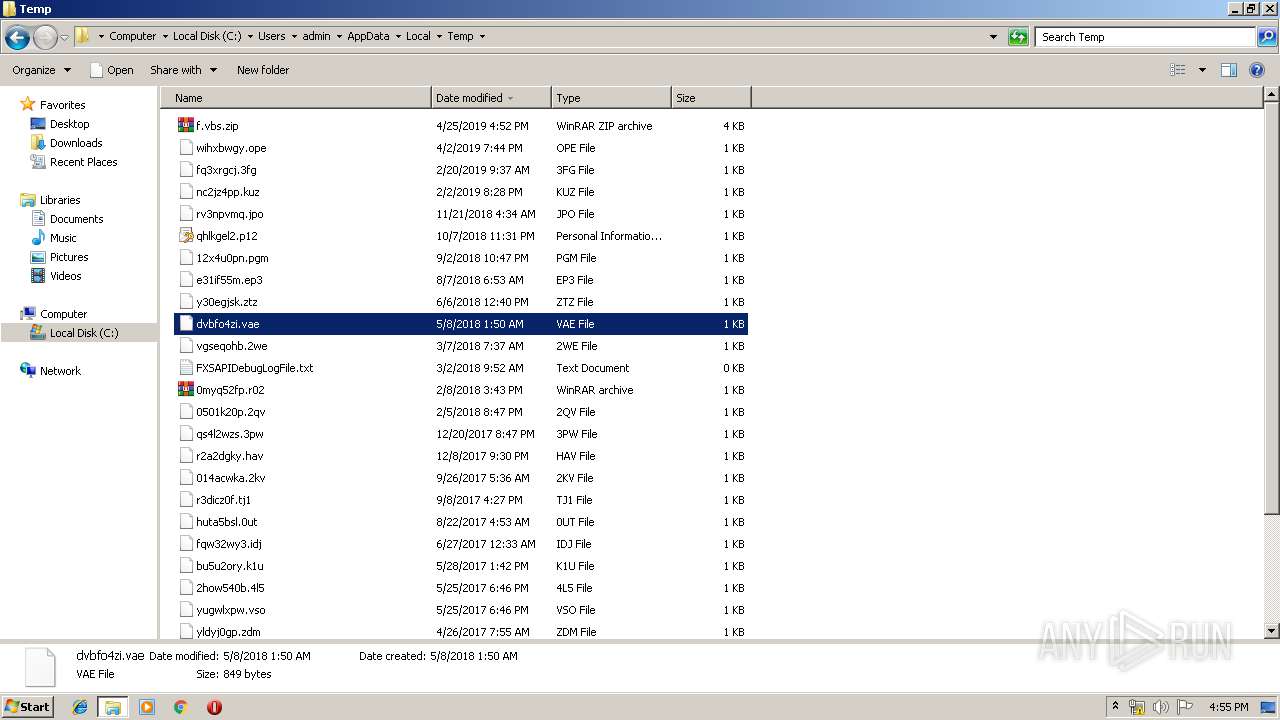
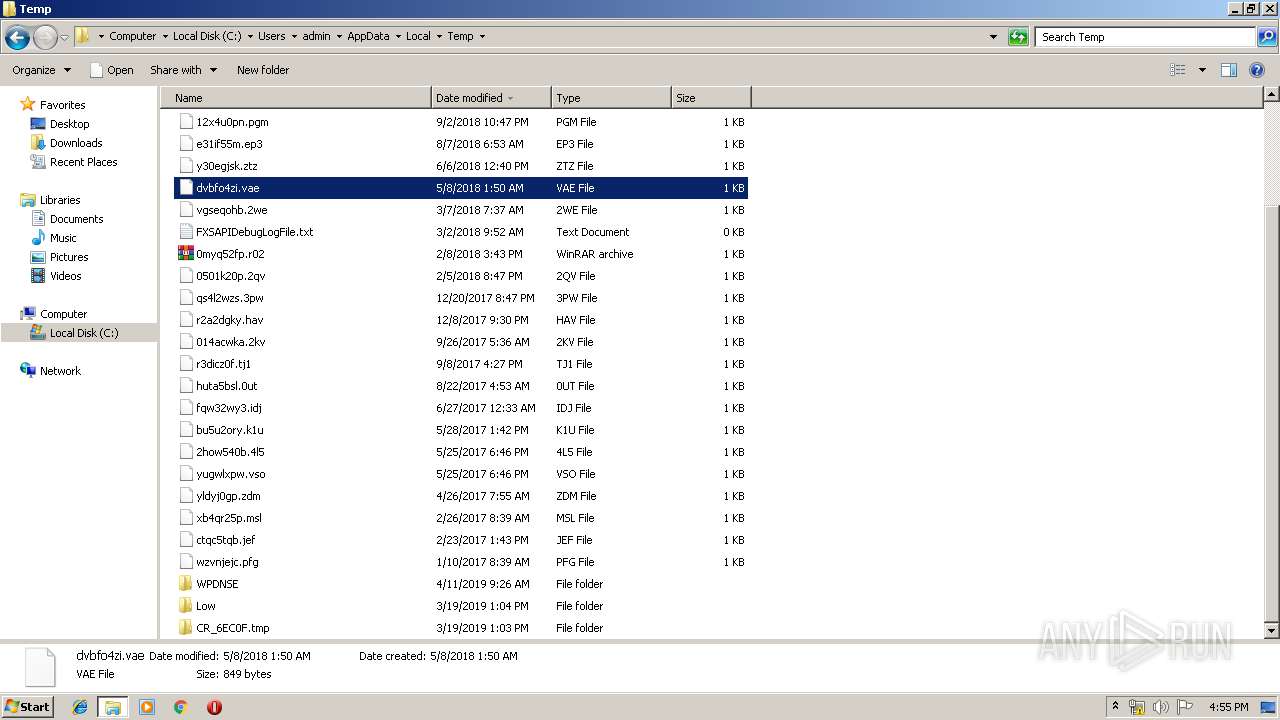
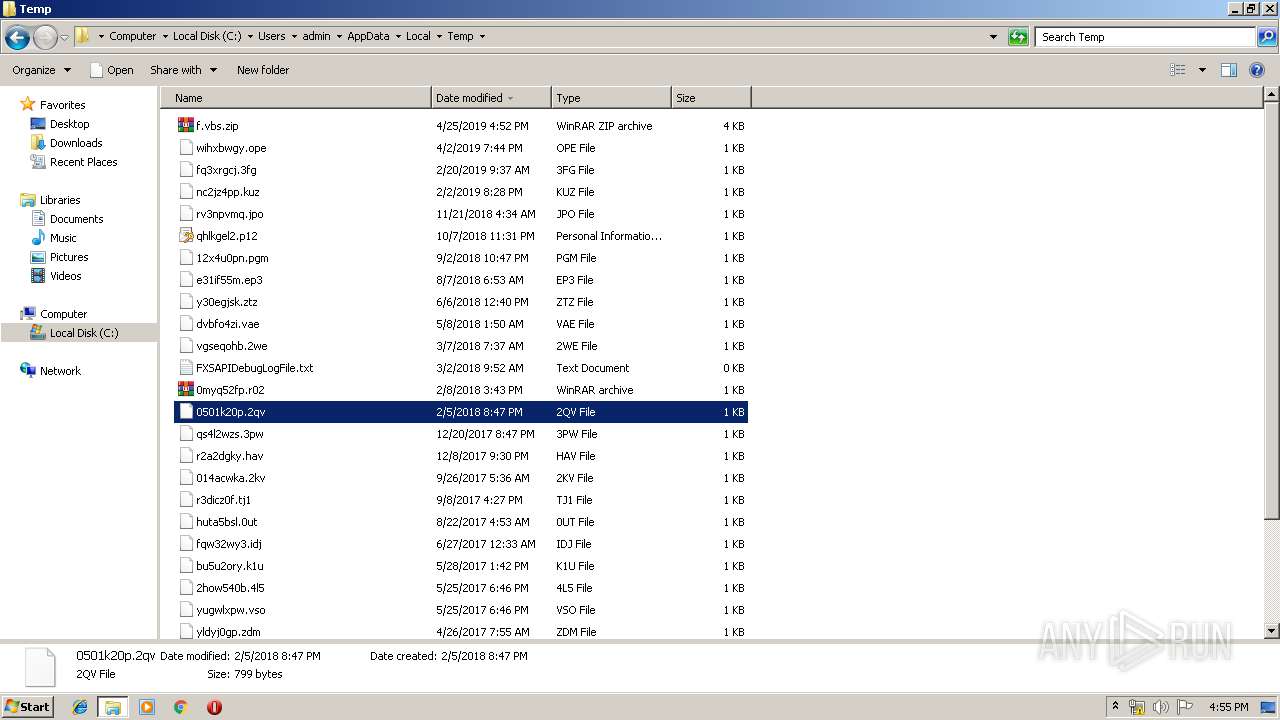
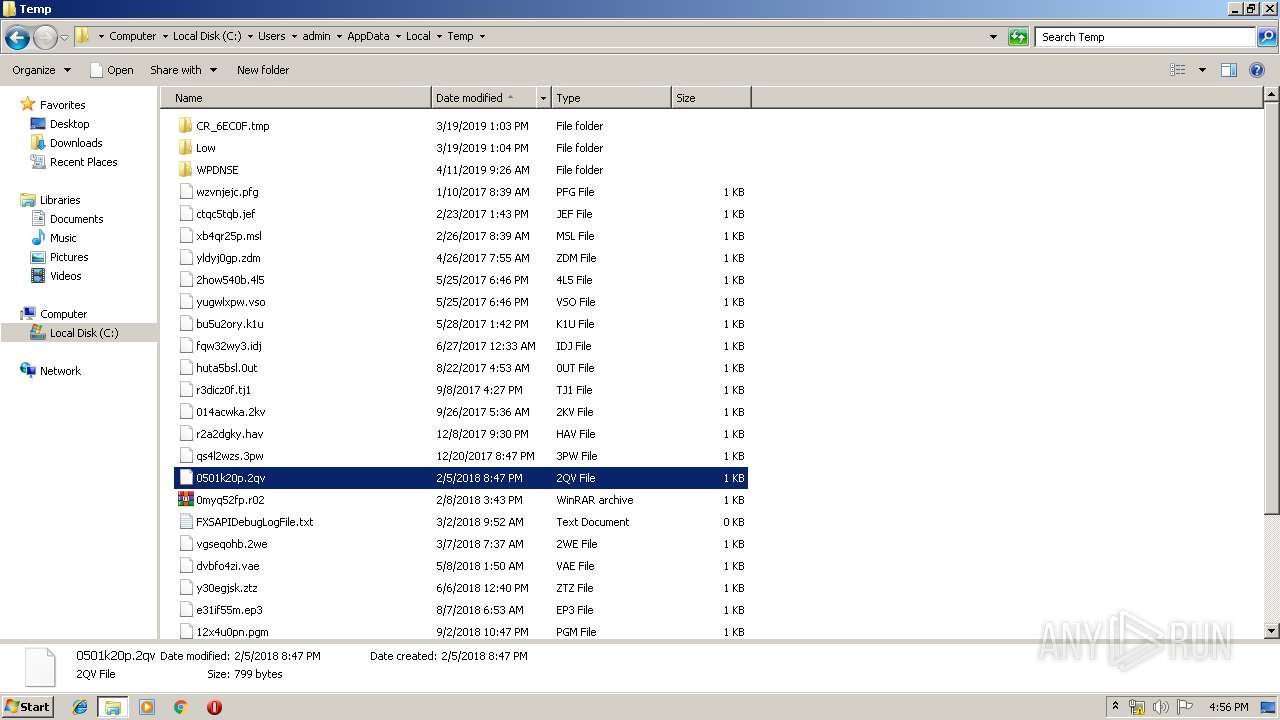
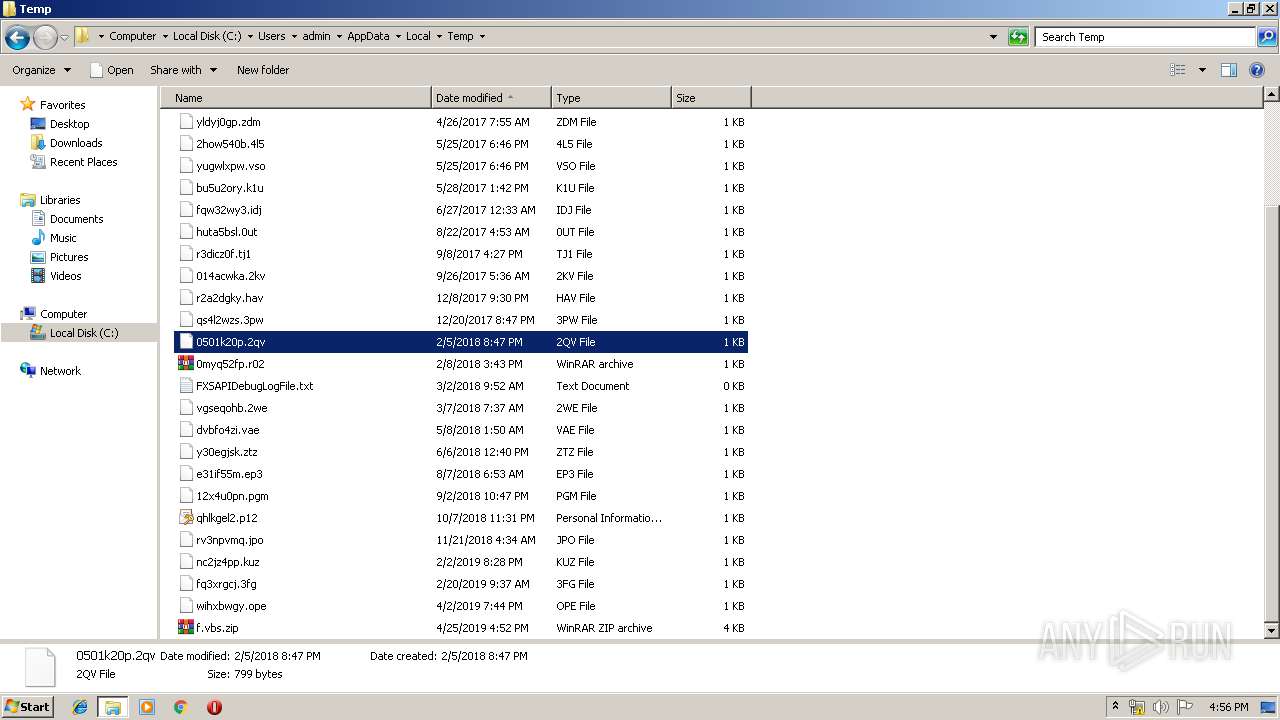
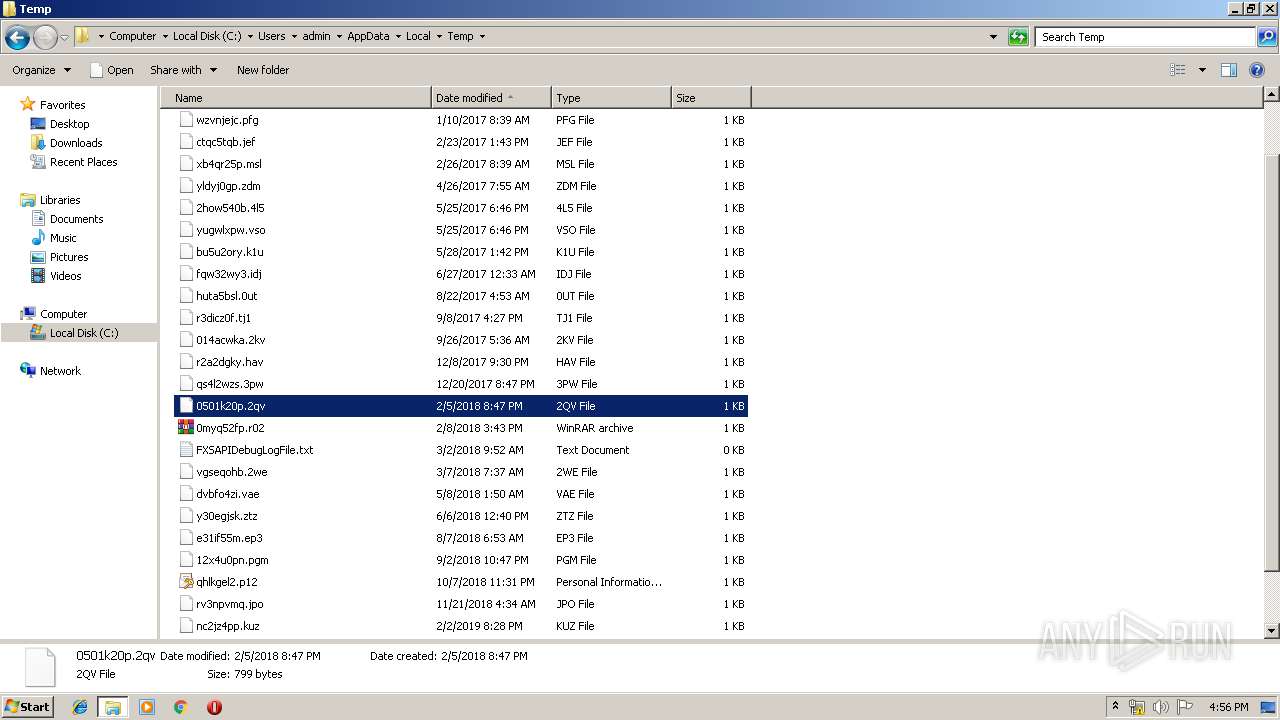
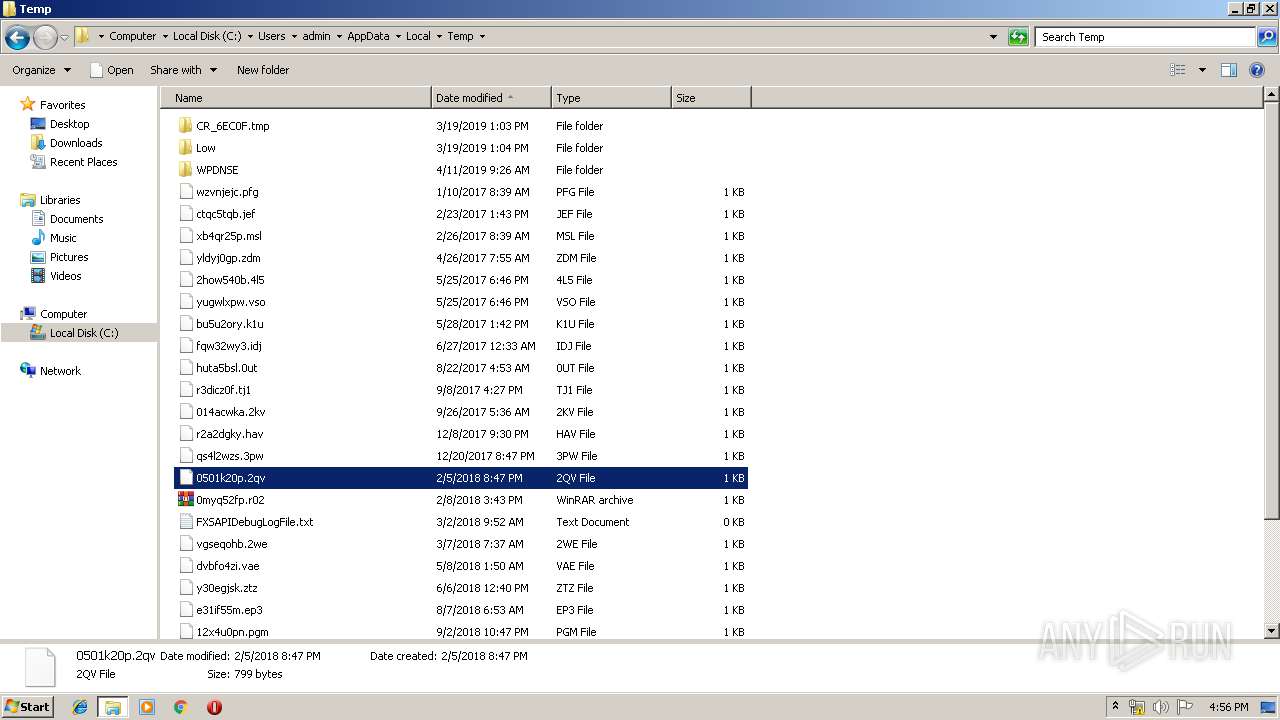
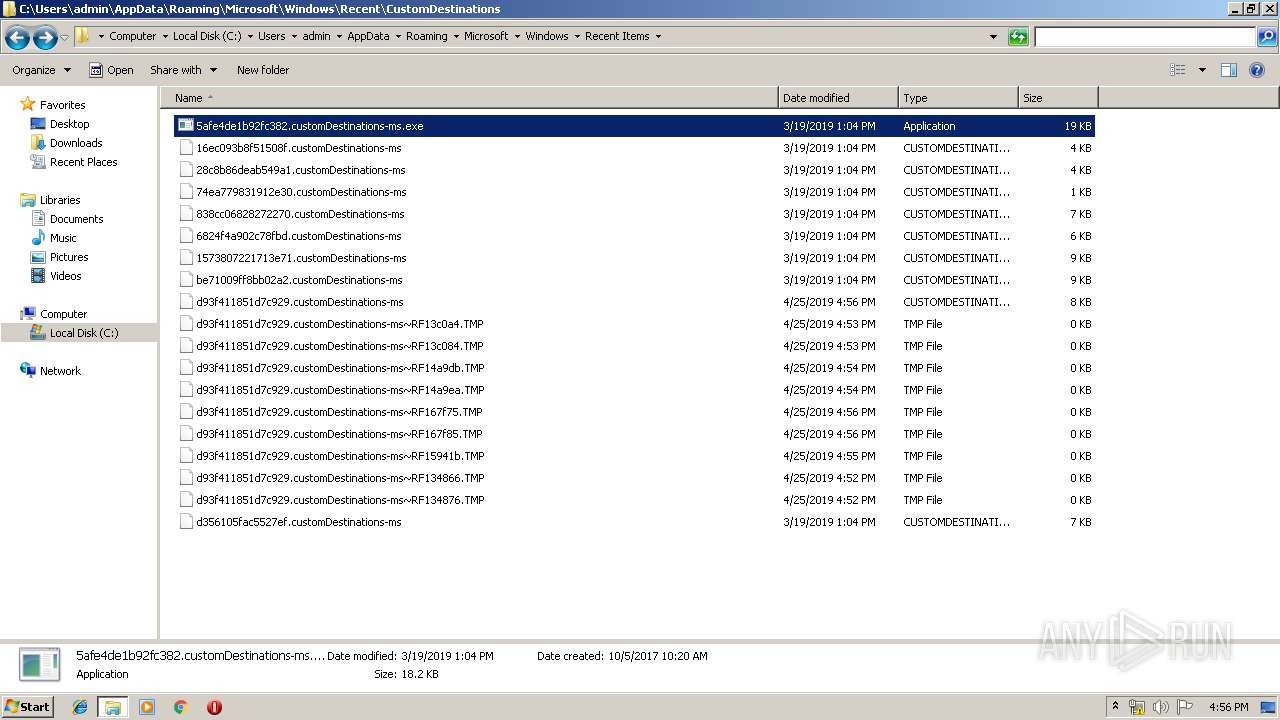
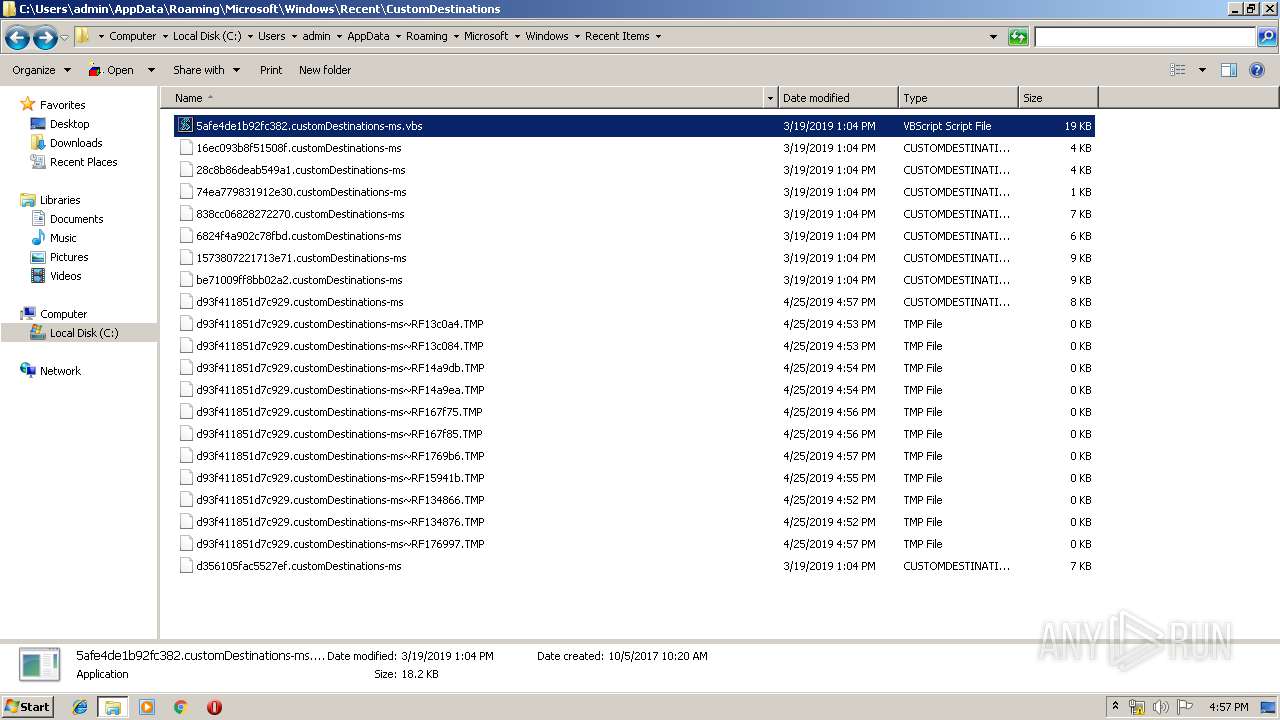
Executable files
0
Suspicious files
24
Text files
6
Unknown types
0
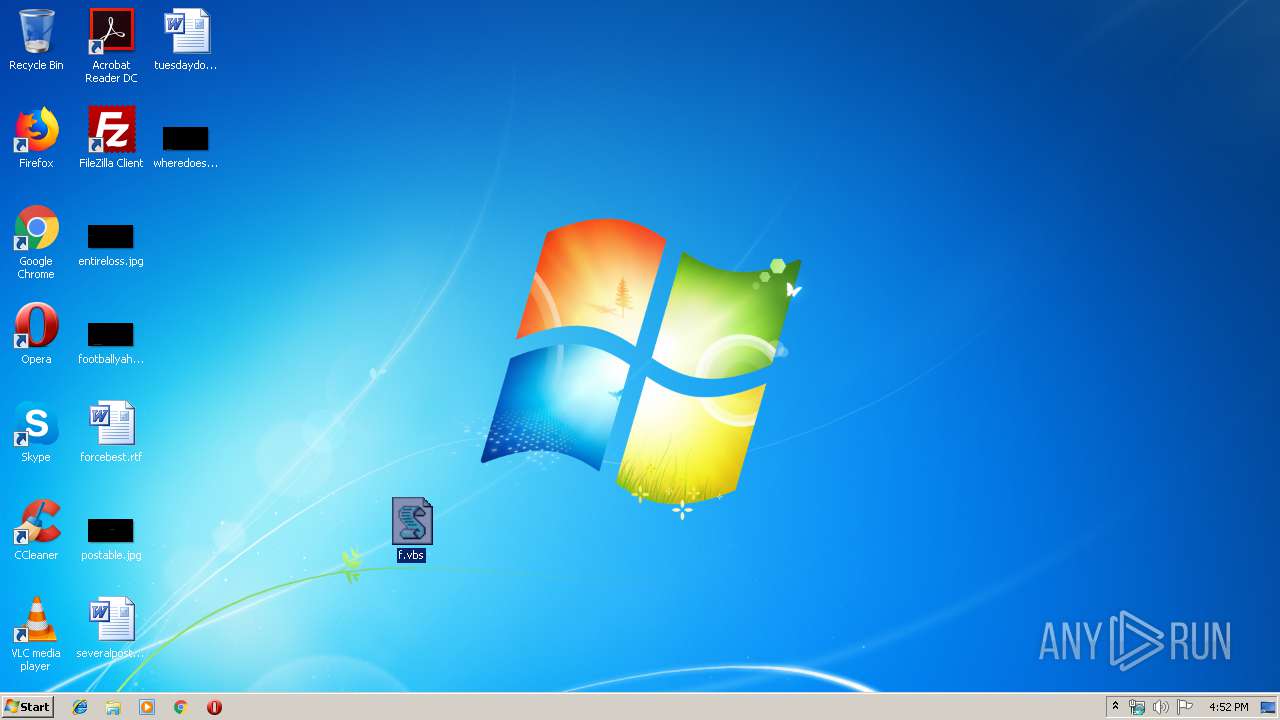
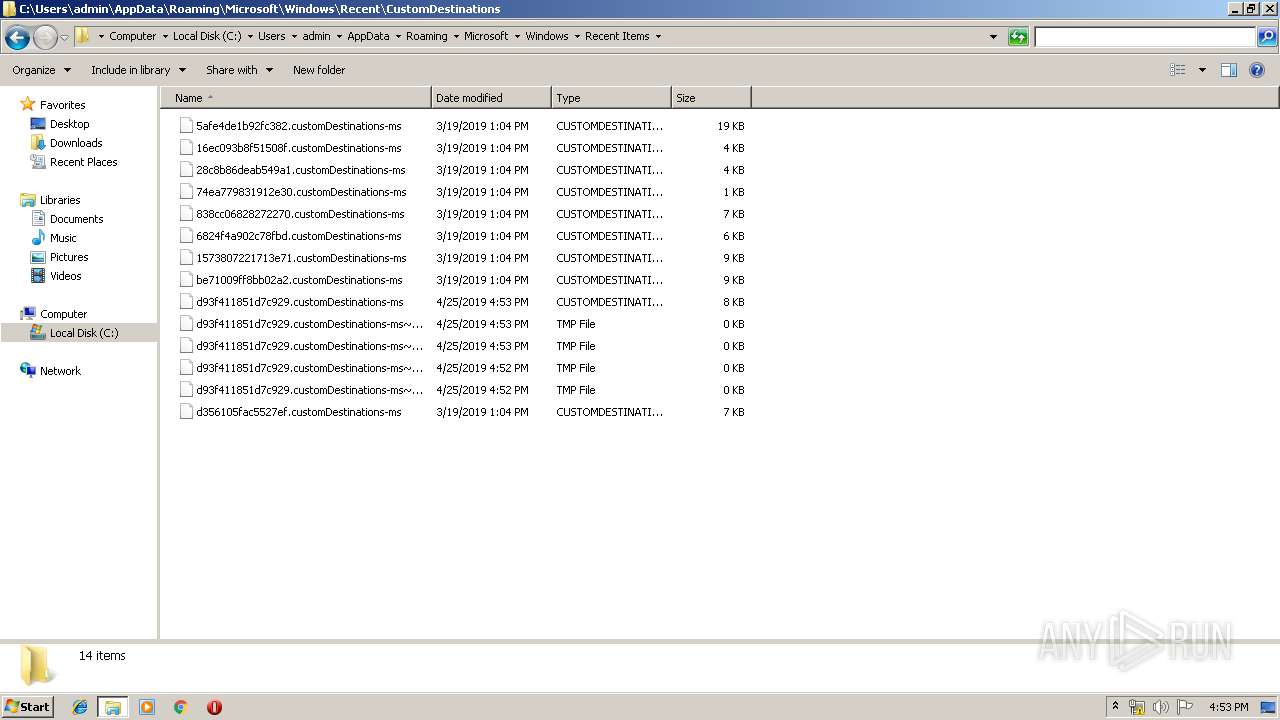
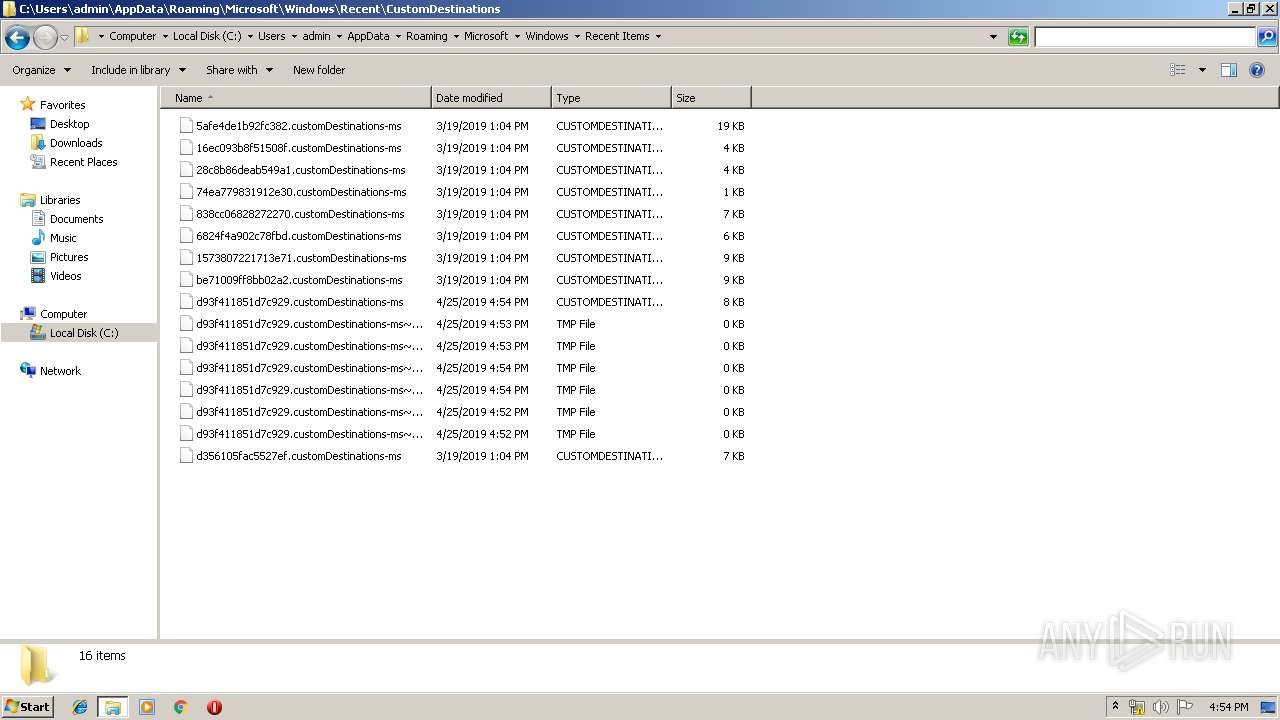
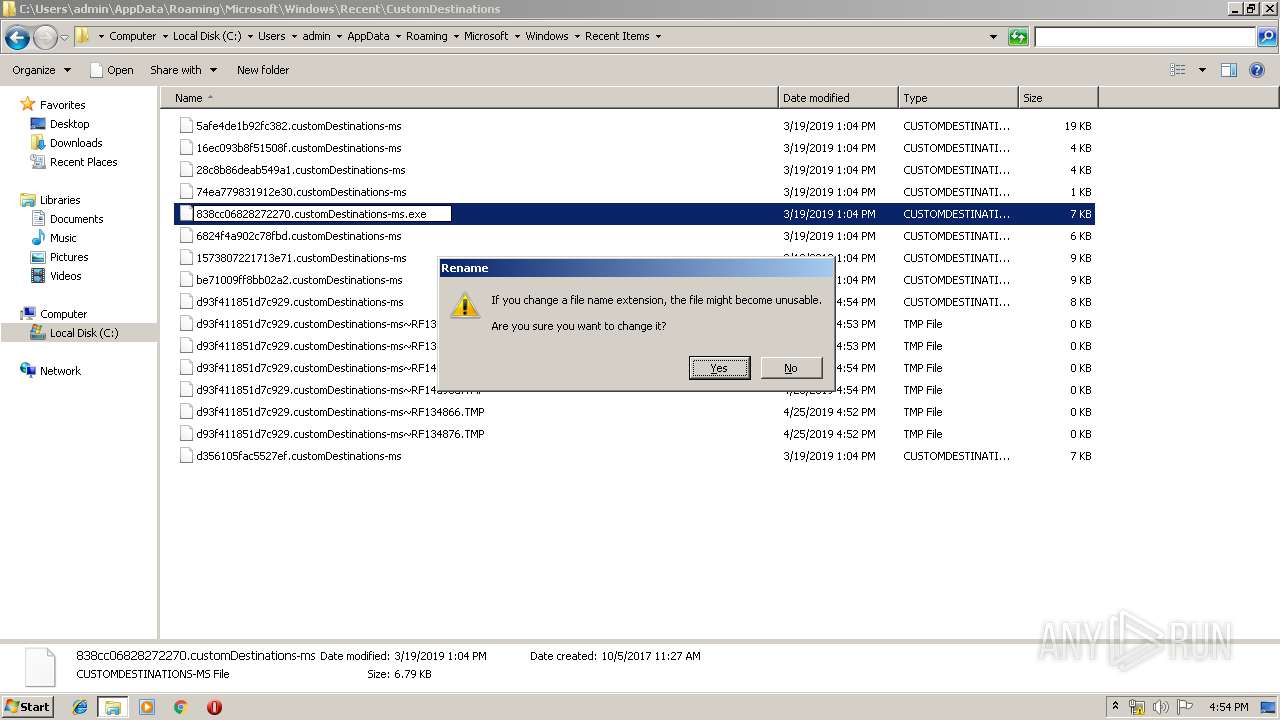
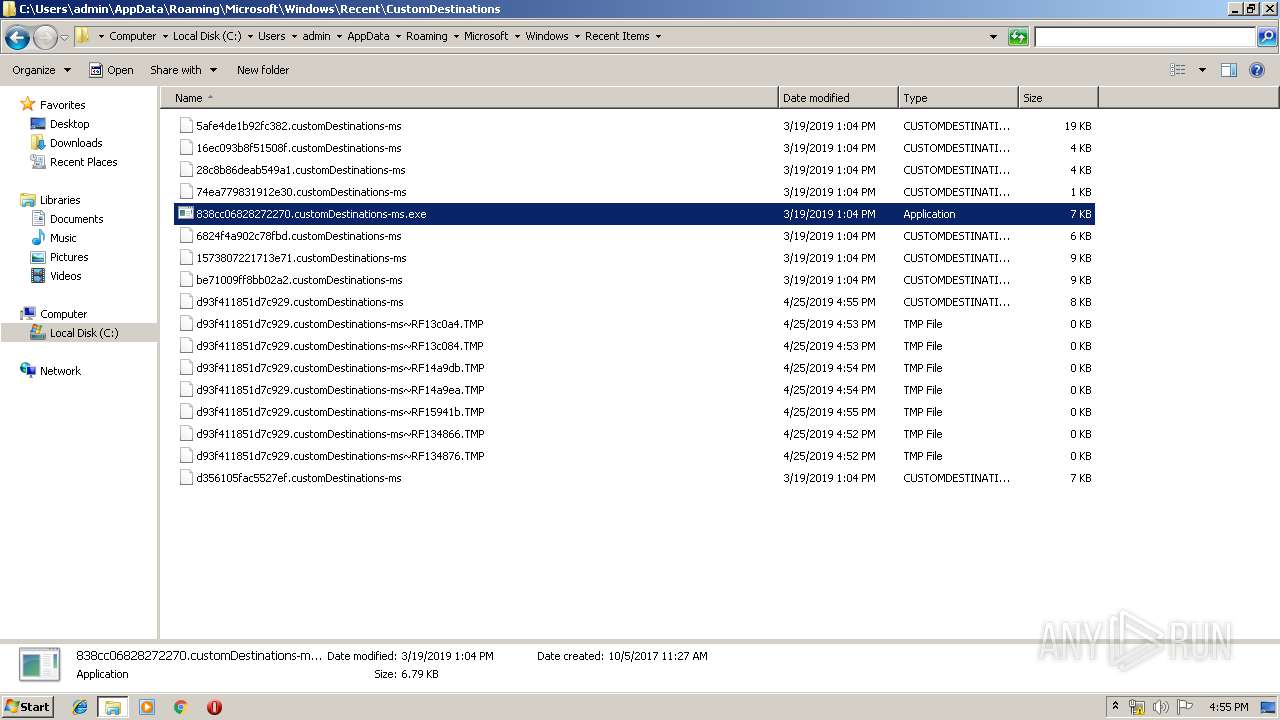
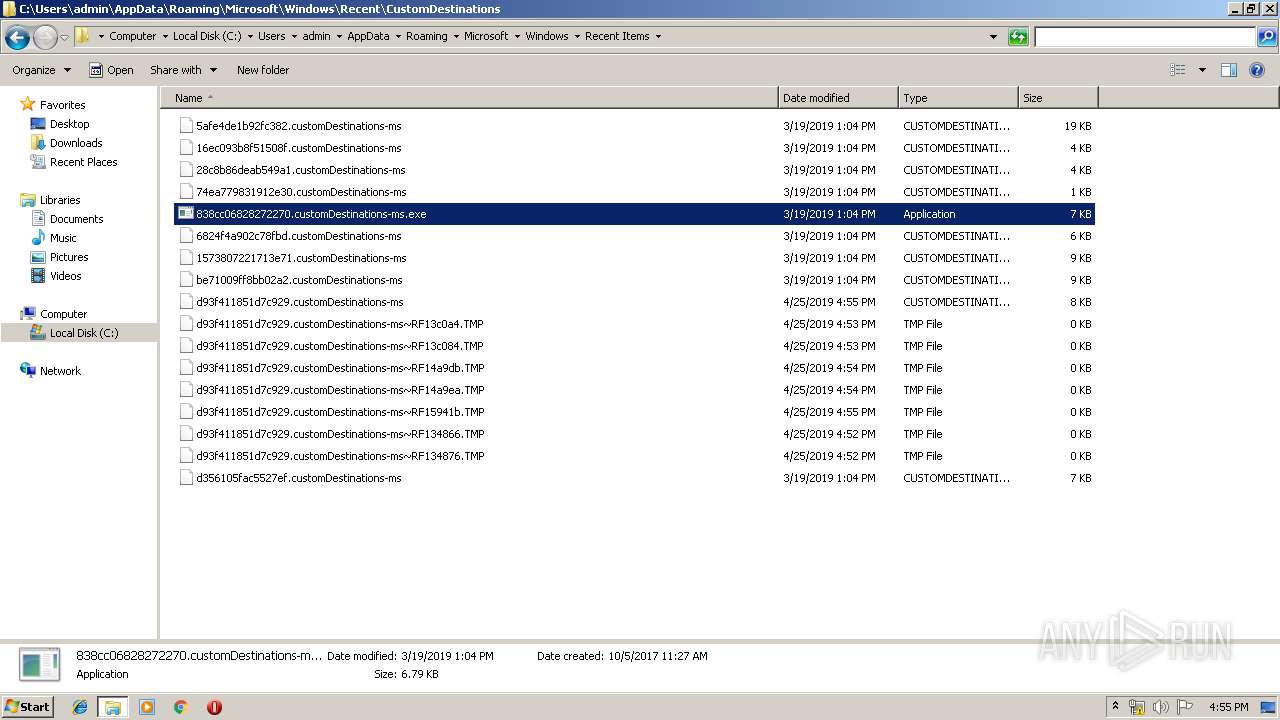
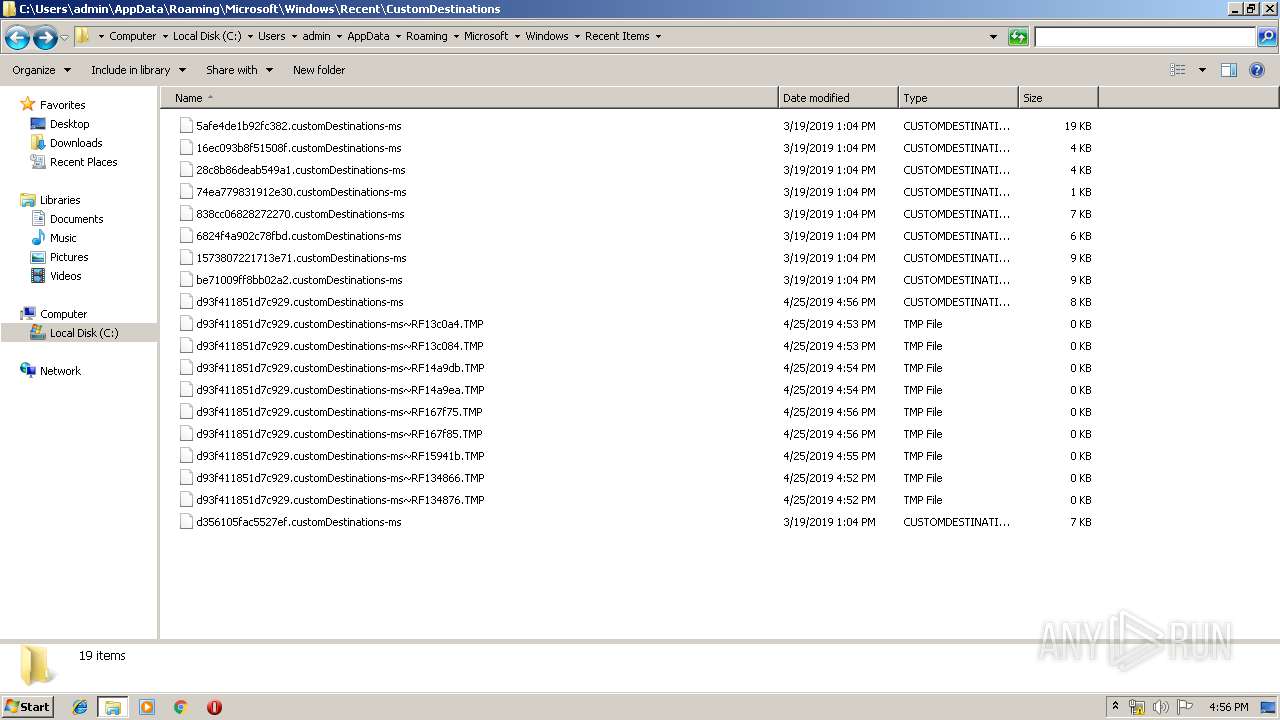
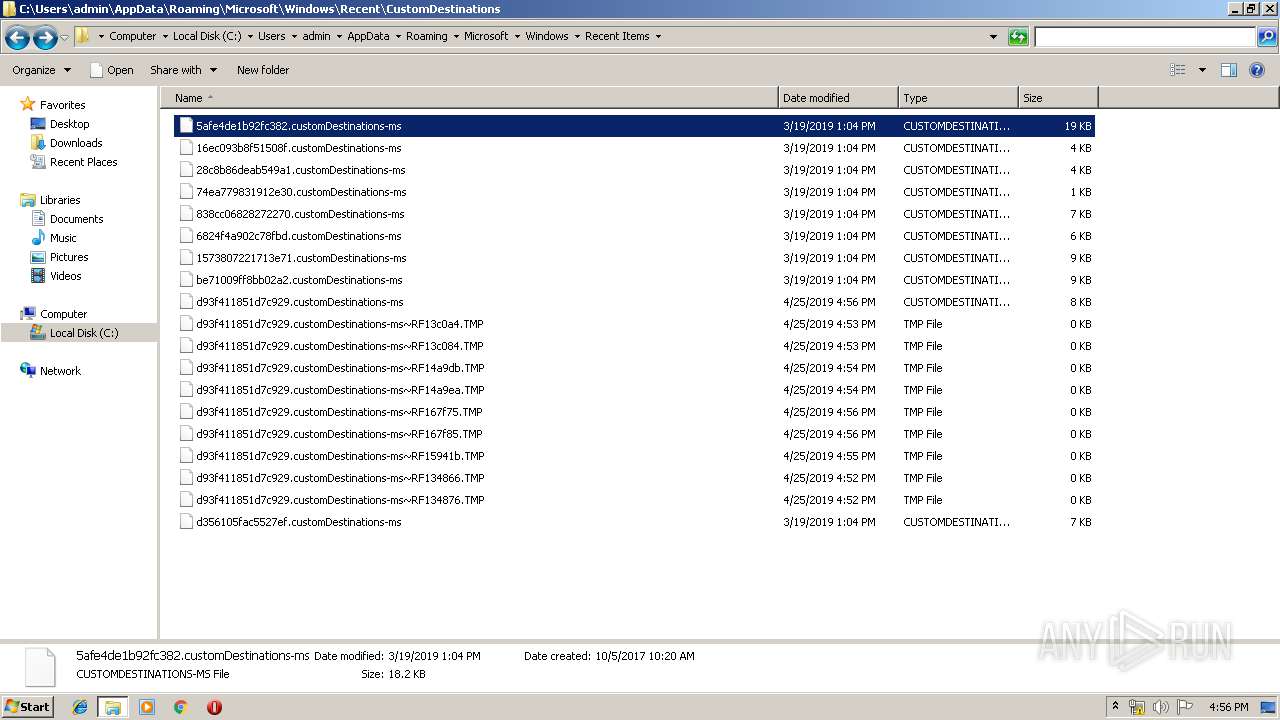
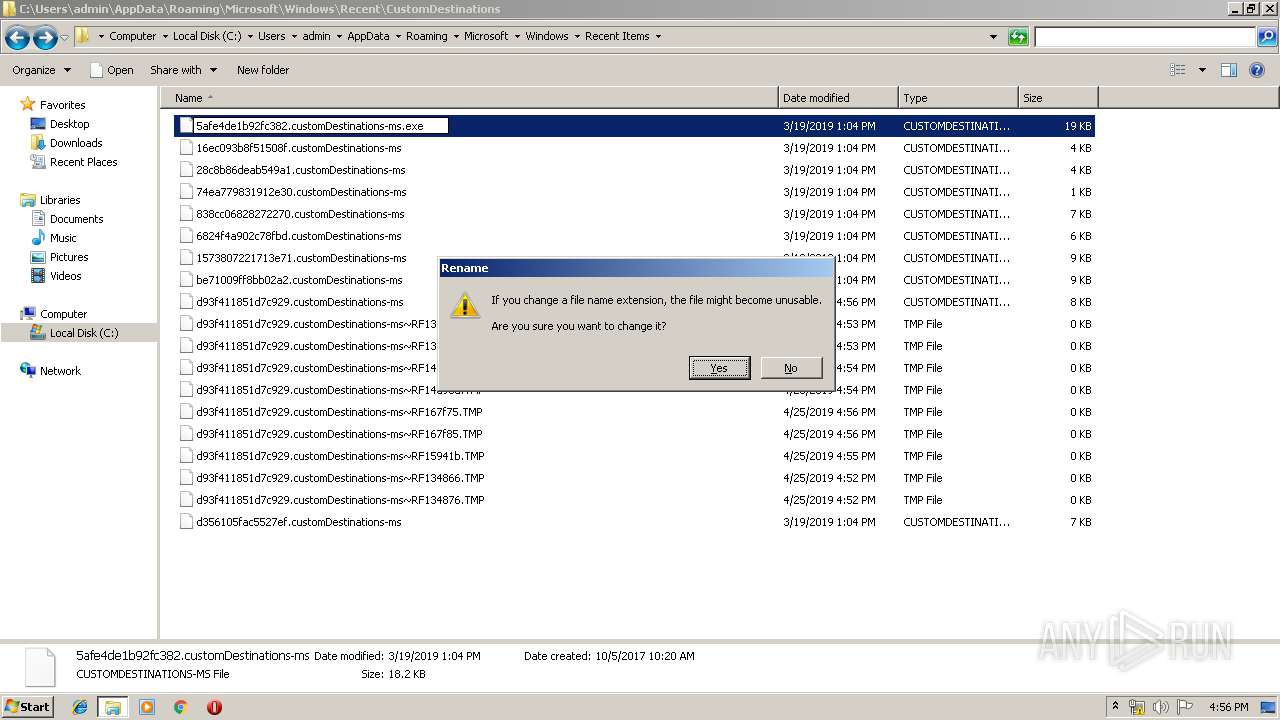
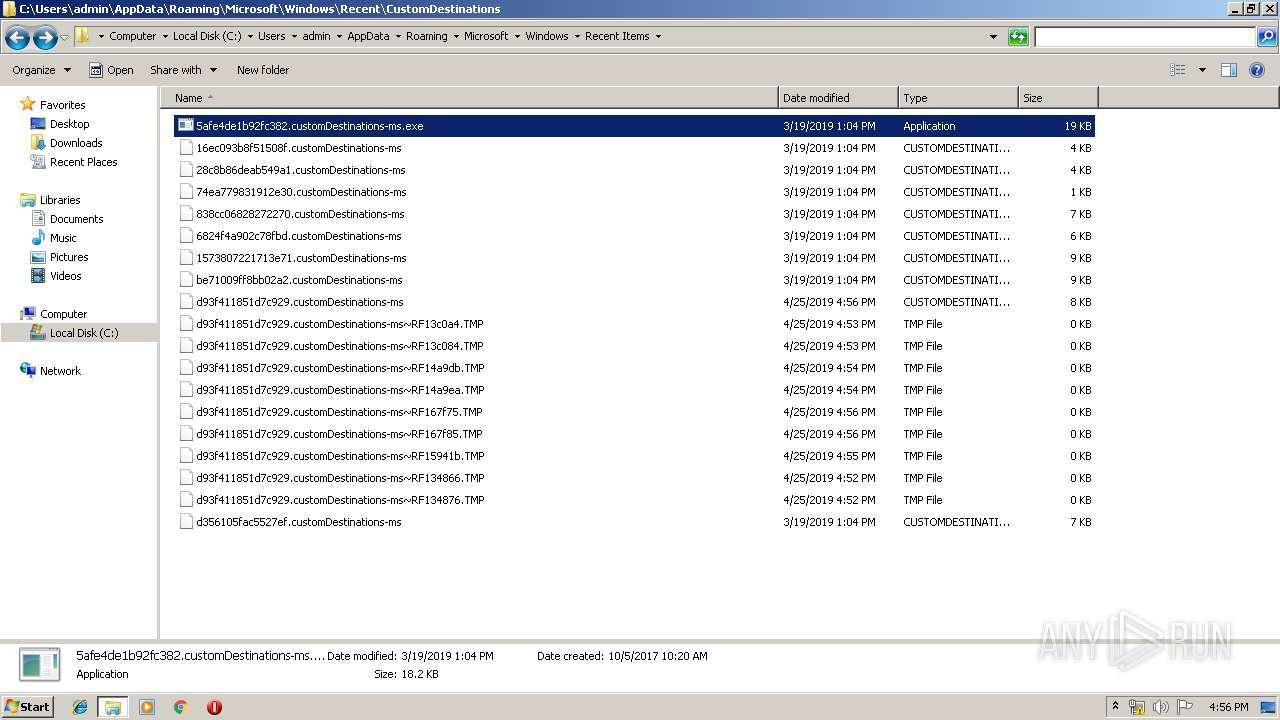
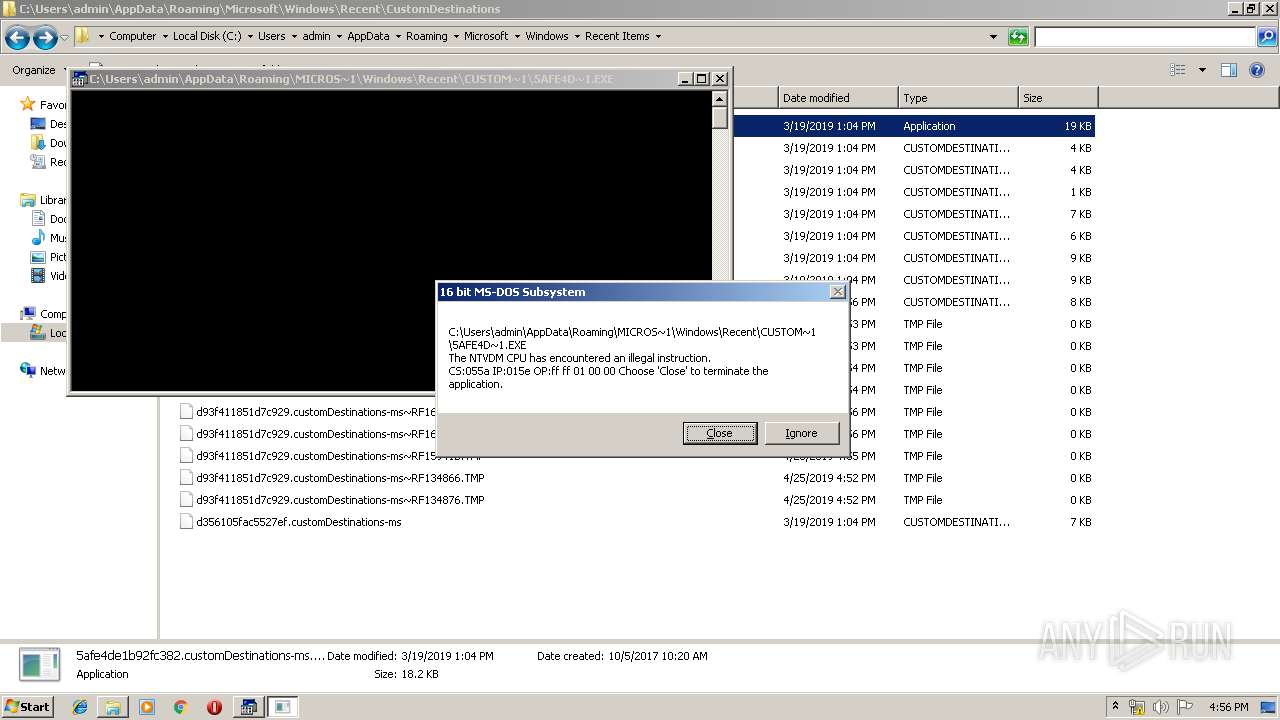
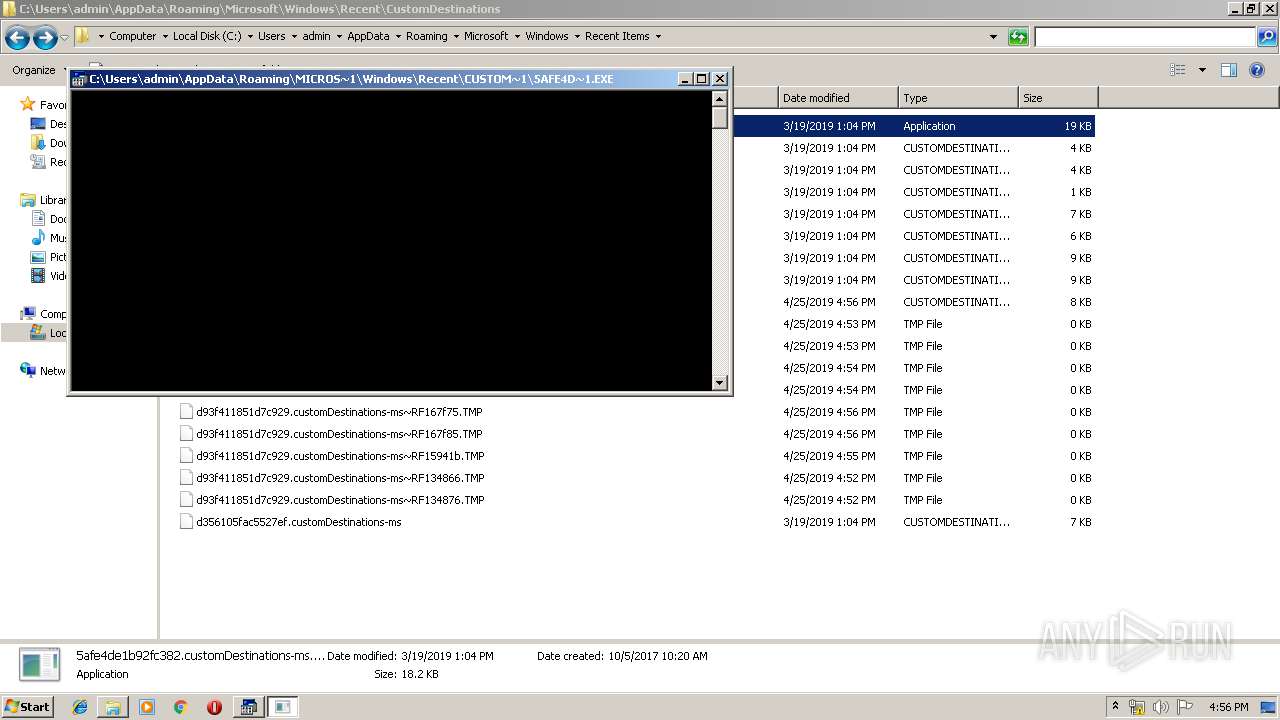
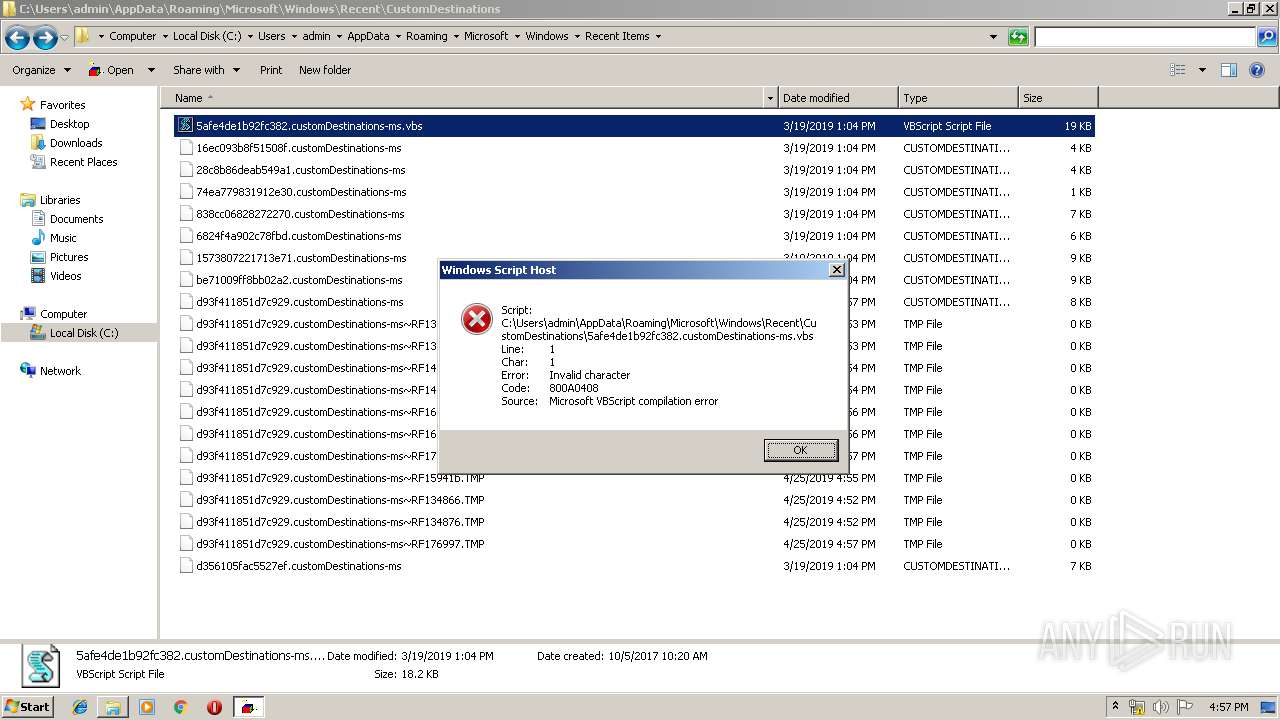
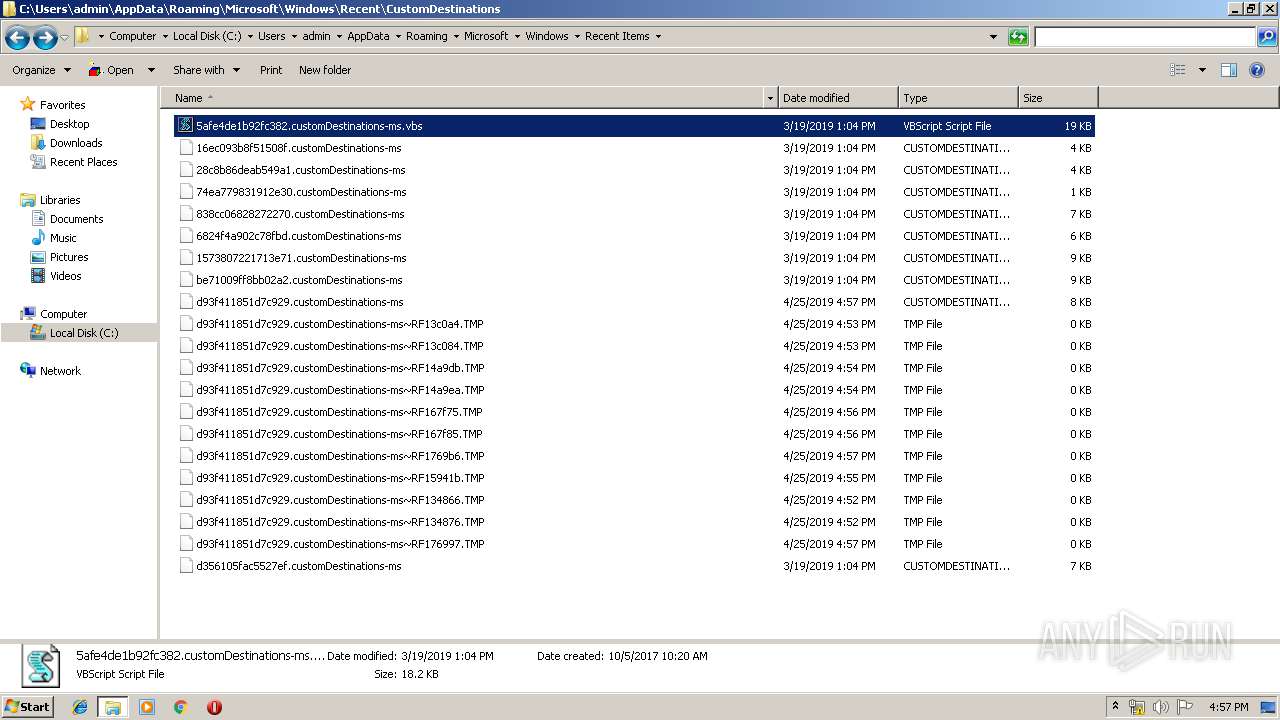
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2936 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2936.3990\f.vbs | — | |
MD5:— | SHA256:— | |||
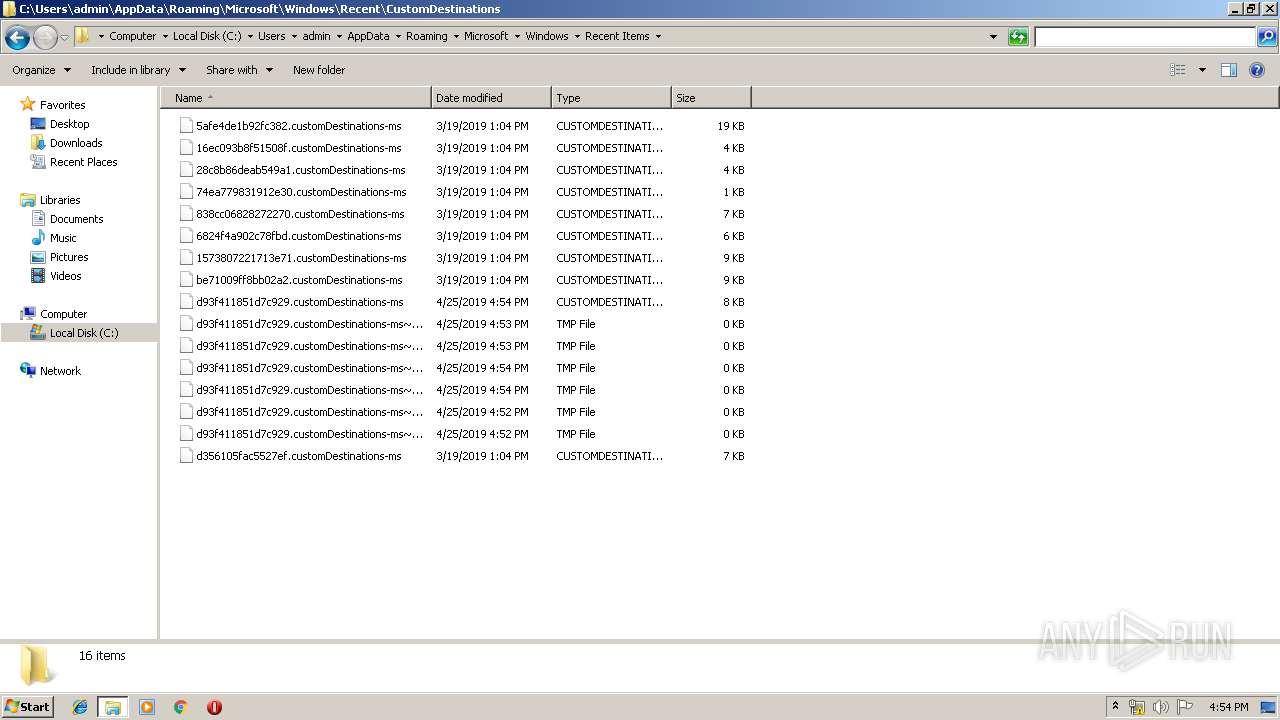
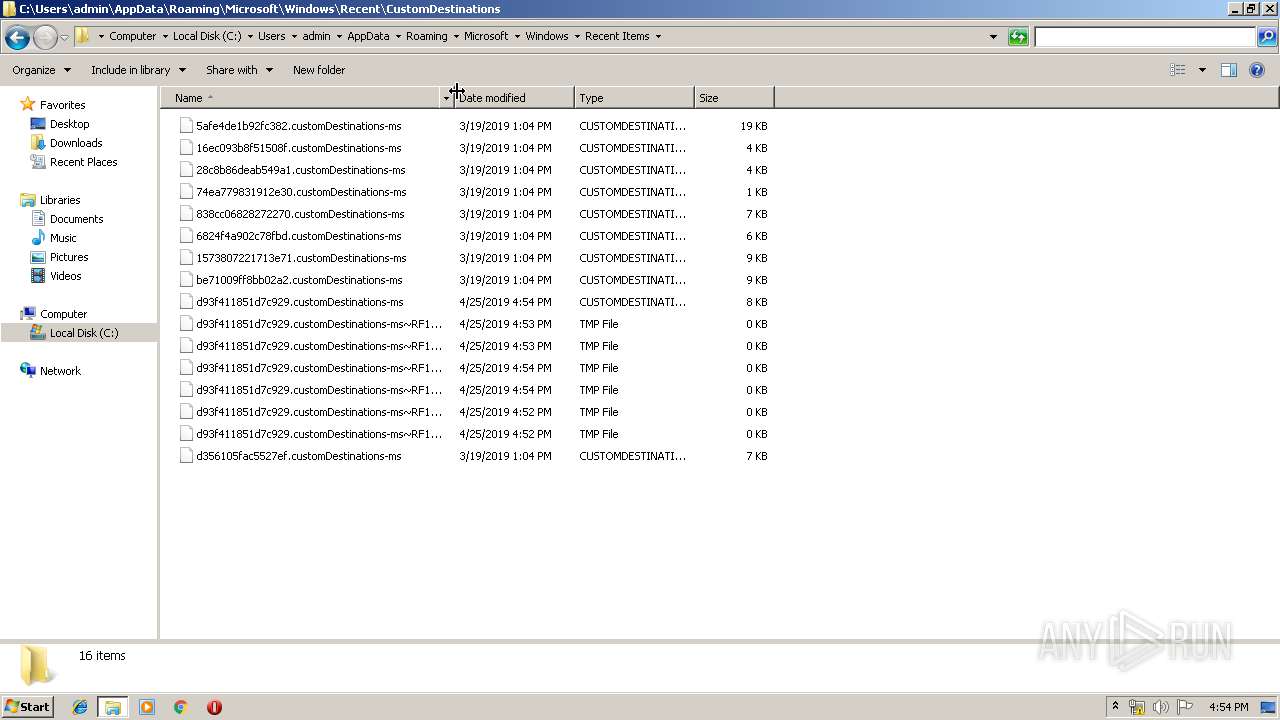
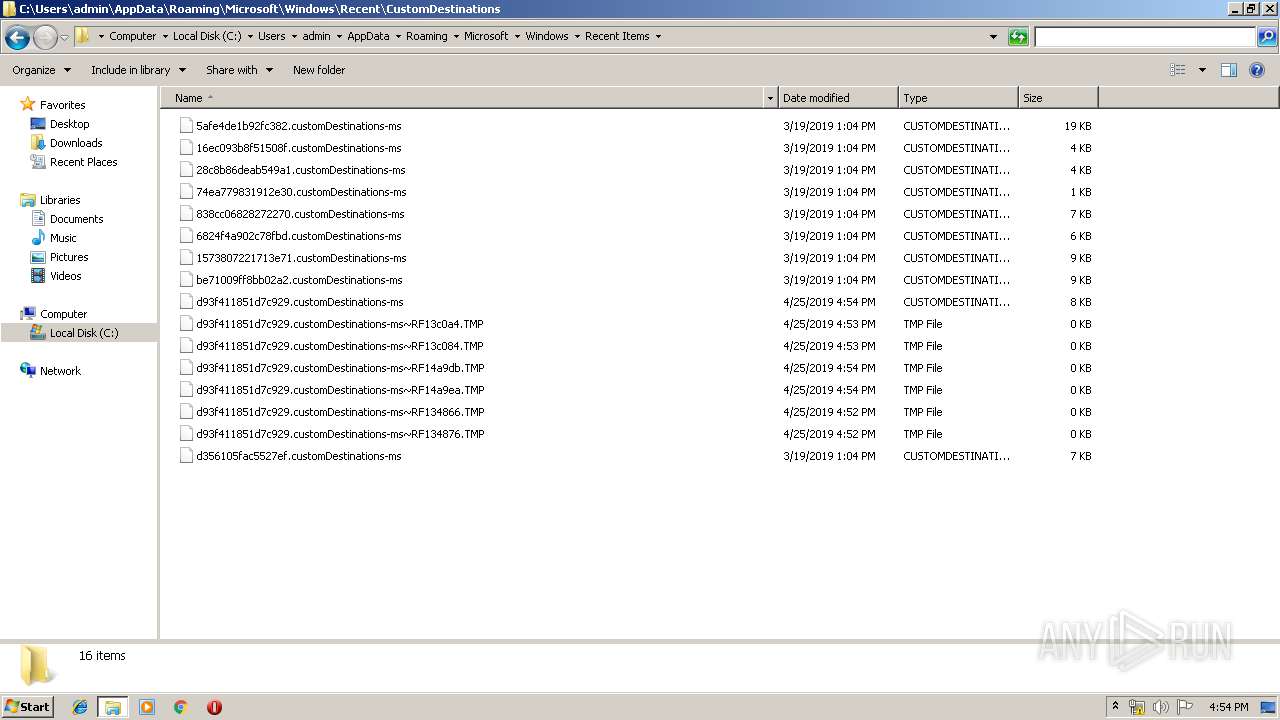
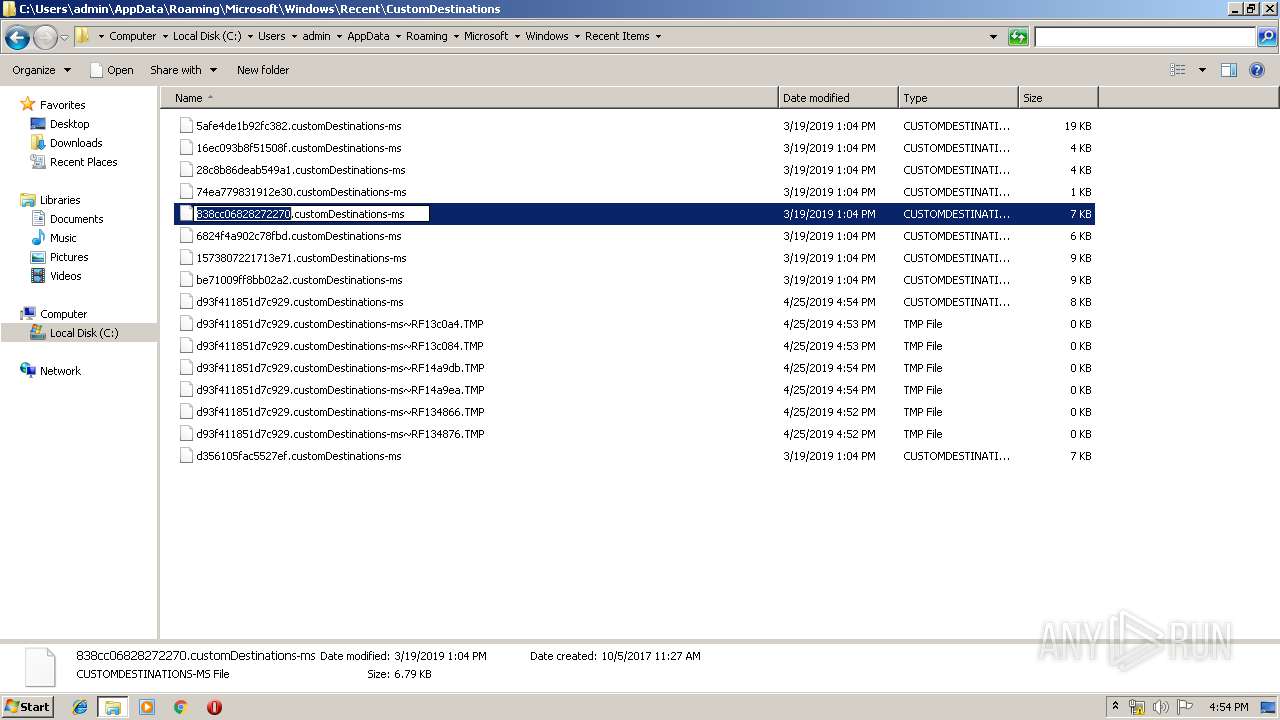
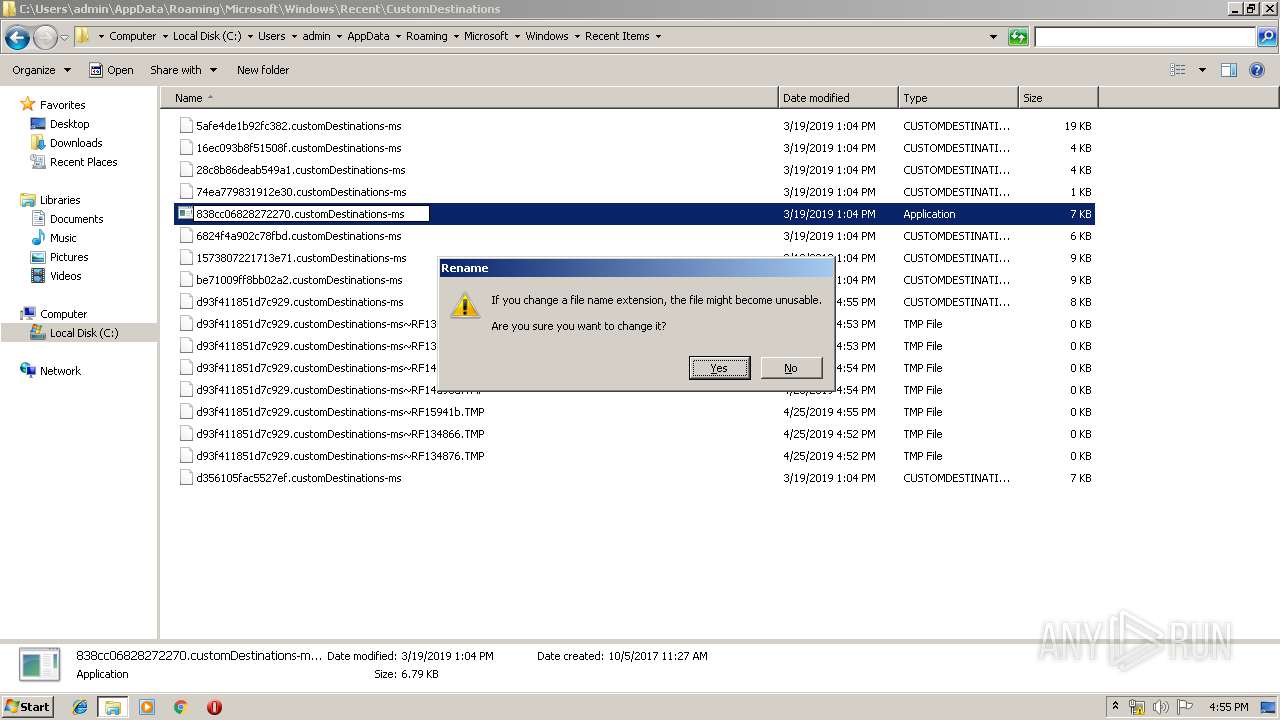
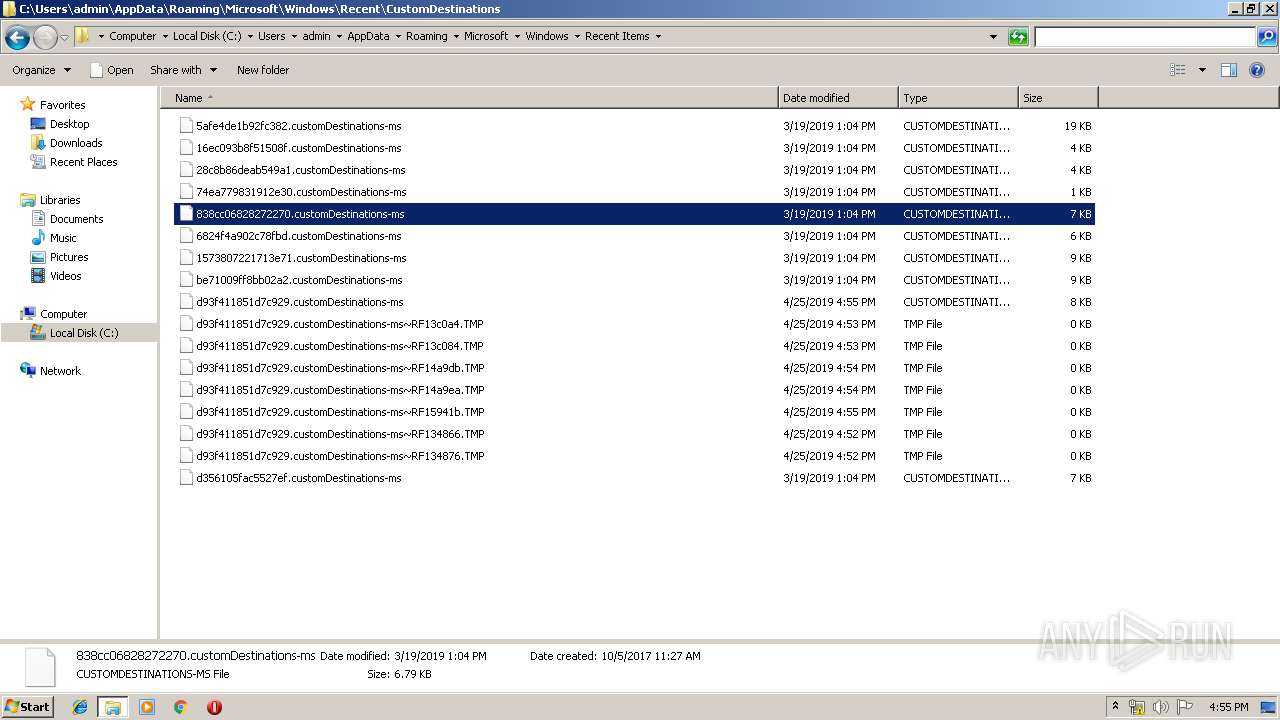
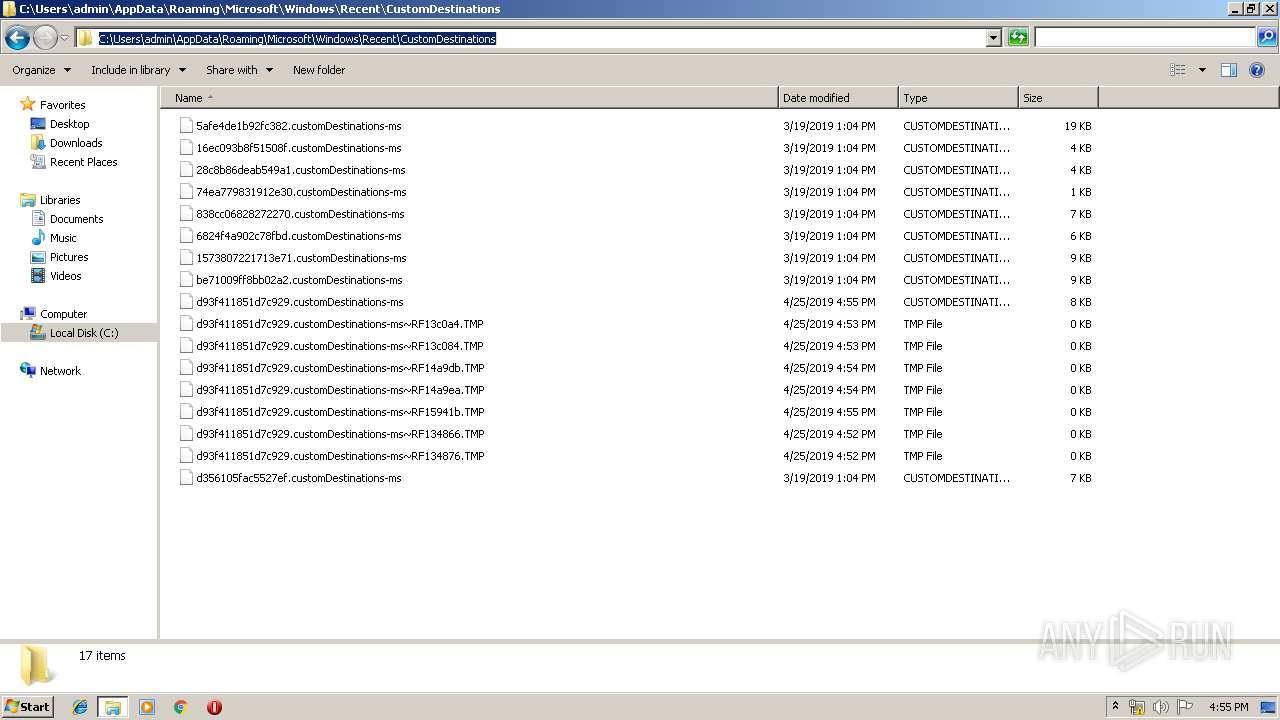
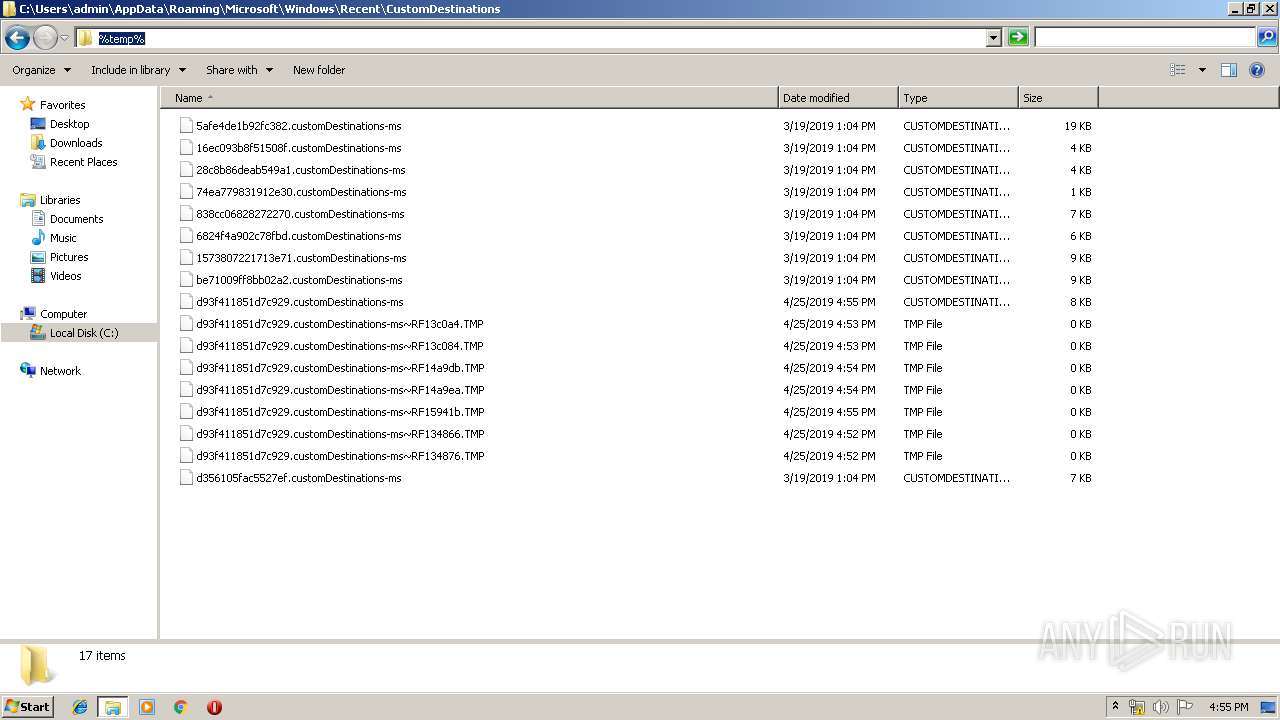
| 3180 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\JCKLX7261XYB9C9I2DDJ.temp | — | |
MD5:— | SHA256:— | |||
| 2232 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\Y6GQ06E3U2Q1URYD637B.temp | — | |
MD5:— | SHA256:— | |||
| 2448 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\DN71IMUKBHCV6D01ZQQH.temp | — | |
MD5:— | SHA256:— | |||
| 2728 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\8G8RAZEOQ23PF4U8LGHT.temp | — | |
MD5:— | SHA256:— | |||
| 2196 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\P6QKN4RYGDJRD10PA2G0.temp | — | |
MD5:— | SHA256:— | |||
| 2456 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\EWRA7U9UFR9UNAS4TYIJ.temp | — | |
MD5:— | SHA256:— | |||
| 3144 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\3K89VM652OKW46833C7O.temp | — | |
MD5:— | SHA256:— | |||
| 3180 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF134866.TMP | binary | |
MD5:— | SHA256:— | |||
| 2592 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\RTAIUNGWRI310F82NYQT.temp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
37
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.mumbai-m.site |
| malicious |
37680000D103199D3C3FB007.mumbai-m.site |
| unknown |
414522660000D103199D3C3FB007.mumbai-m.site |
| unknown |
555935870000D103199D3C3FB007.mumbai-m.site |
| unknown |
2129363266900000D103199D3C3FB007.mumbai-m.site |
| unknown |
22954893110000D103199D3C3FB007.mumbai-m.site |
| unknown |
10353321454000D103199D3C3FB007.757365722D70635C61646D696E2A2A2A2A2A2A2A2A2A2A2A2A.mumbai-m.site |
| unknown |
2719918344820000D103199D3C3FB007.mumbai-m.site |
| unknown |
91129894510000D103199D3C3FB007.mumbai-m.site |
| unknown |
38650000D103199D3C3FB007.mumbai-m.site |
| unknown |