| File name: | a.exe |
| Full analysis: | https://app.any.run/tasks/d0797c76-44f6-4695-8108-920733b3f4c2 |
| Verdict: | Malicious activity |
| Analysis date: | June 21, 2025, 03:26:43 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | B1CA8F673A35CA99CA2C153E38BCE2D1 |
| SHA1: | B4B1367D91322243F6EDE4EA6A5643A1C9DA0B9B |
| SHA256: | 1CAE91457986F019B8DEFD3C9E686EA54971BD19C59A03E8DB8DFD7302C70BA3 |
| SSDEEP: | 768:GqeJWZdFE2ECEL8JRLglxJVLmEvYdp6YOH5ysKYwcZo3q/neXbOfC1XkCy/es:Vg2ECELcL6DVLmEApn1sfwY4bOhCy5 |
MALICIOUS
Gets or sets the initialization vector for the symmetric algorithm (POWERSHELL)
- a.exe (PID: 2044)
- $77smartscreen.exe (PID: 6424)
Gets or sets the symmetric key that is used for encryption and decryption (POWERSHELL)
- a.exe (PID: 2044)
- $77smartscreen.exe (PID: 6424)
Changes Windows Defender settings
- a.exe (PID: 2044)
Uses AES cipher (POWERSHELL)
- a.exe (PID: 2044)
- $77smartscreen.exe (PID: 6424)
Dynamically loads an assembly (POWERSHELL)
- a.exe (PID: 2044)
- $77smartscreen.exe (PID: 6424)
- powershell.exe (PID: 4020)
Bypass execution policy to execute commands
- powershell.exe (PID: 2368)
- powershell.exe (PID: 7060)
Changes powershell execution policy (Bypass)
- a.exe (PID: 2044)
Adds path to the Windows Defender exclusion list
- a.exe (PID: 2044)
Adds process to the Windows Defender exclusion list
- a.exe (PID: 2044)
UAC/LUA settings modification
- $77smartscreen.exe (PID: 6424)
Run PowerShell with an invisible window
- powershell.exe (PID: 6508)
Application was injected by another process
- winlogon.exe (PID: 672)
Runs injected code in another process
- powershell.exe (PID: 4020)
SUSPICIOUS
Reads security settings of Internet Explorer
- a.exe (PID: 2044)
- $77smartscreen.exe (PID: 6424)
- ShellExperienceHost.exe (PID: 1984)
Reads Microsoft Outlook installation path
- a.exe (PID: 2044)
- $77smartscreen.exe (PID: 6424)
Executable content was dropped or overwritten
- csc.exe (PID: 2512)
- a.exe (PID: 2044)
- csc.exe (PID: 2292)
Uses base64 encoding (POWERSHELL)
- a.exe (PID: 2044)
- $77smartscreen.exe (PID: 6424)
Reads the date of Windows installation
- a.exe (PID: 2044)
Script adds exclusion path to Windows Defender
- a.exe (PID: 2044)
Starts POWERSHELL.EXE for commands execution
- a.exe (PID: 2044)
- cmd.exe (PID: 6940)
- mshta.exe (PID: 3480)
Script adds exclusion process to Windows Defender
- a.exe (PID: 2044)
The process executes via Task Scheduler
- $77smartscreen.exe (PID: 6424)
- mshta.exe (PID: 3480)
Lists all scheduled tasks
- schtasks.exe (PID: 4512)
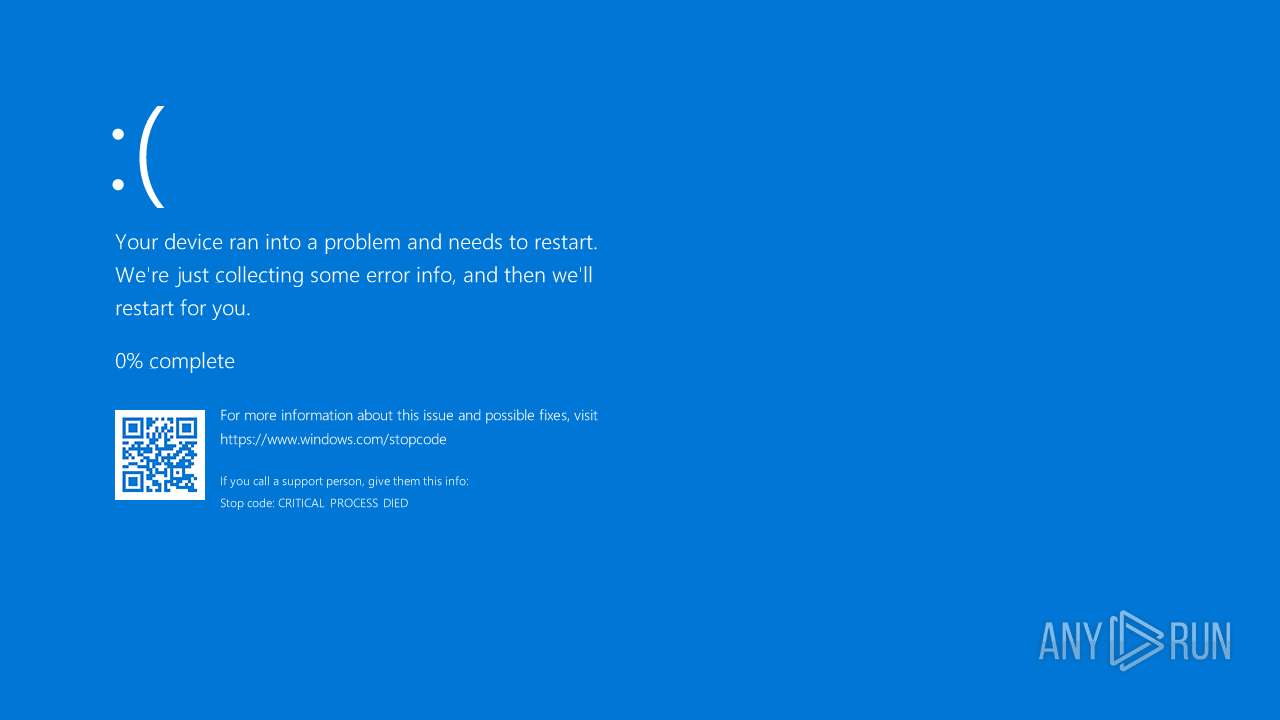
Executes application which crashes
- $77smartscreen.exe (PID: 6424)
Executes as Windows Service
- cmd.exe (PID: 6940)
Invokes assembly entry point (POWERSHELL)
- powershell.exe (PID: 4020)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 6940)
Possibly malicious use of IEX has been detected
- mshta.exe (PID: 3480)
Executes script without checking the security policy
- powershell.exe (PID: 6508)
Downloads file from URI via Powershell
- powershell.exe (PID: 6508)
The process bypasses the loading of PowerShell profile settings
- mshta.exe (PID: 3480)
Runs shell command (SCRIPT)
- mshta.exe (PID: 3480)
INFO
Create files in a temporary directory
- a.exe (PID: 2044)
- cvtres.exe (PID: 1036)
- csc.exe (PID: 2512)
- $77smartscreen.exe (PID: 6424)
- csc.exe (PID: 2292)
- cvtres.exe (PID: 1136)
Checks supported languages
- a.exe (PID: 2044)
- csc.exe (PID: 2512)
- cvtres.exe (PID: 1036)
- $77smartscreen.exe (PID: 6424)
- csc.exe (PID: 2292)
- cvtres.exe (PID: 1136)
- ShellExperienceHost.exe (PID: 1984)
- RegAsm.exe (PID: 6264)
Reads the computer name
- a.exe (PID: 2044)
- $77smartscreen.exe (PID: 6424)
- ShellExperienceHost.exe (PID: 1984)
- RegAsm.exe (PID: 6264)
Reads the machine GUID from the registry
- a.exe (PID: 2044)
- csc.exe (PID: 2512)
- $77smartscreen.exe (PID: 6424)
- csc.exe (PID: 2292)
- RegAsm.exe (PID: 6264)
Reads Environment values
- a.exe (PID: 2044)
- $77smartscreen.exe (PID: 6424)
Reads the software policy settings
- a.exe (PID: 2044)
- $77smartscreen.exe (PID: 6424)
Checks if a key exists in the options dictionary (POWERSHELL)
- a.exe (PID: 2044)
- powershell.exe (PID: 2368)
- powershell.exe (PID: 7060)
- $77smartscreen.exe (PID: 6424)
Disables trace logs
- a.exe (PID: 2044)
- $77smartscreen.exe (PID: 6424)
Checks proxy server information
- a.exe (PID: 2044)
- $77smartscreen.exe (PID: 6424)
- mshta.exe (PID: 3480)
Converts byte array into Unicode string (POWERSHELL)
- a.exe (PID: 2044)
- $77smartscreen.exe (PID: 6424)
Converts byte array into ASCII string (POWERSHELL)
- a.exe (PID: 2044)
- $77smartscreen.exe (PID: 6424)
Gets data length (POWERSHELL)
- a.exe (PID: 2044)
- $77smartscreen.exe (PID: 6424)
Process checks computer location settings
- a.exe (PID: 2044)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7060)
- powershell.exe (PID: 2368)
Creates files in the program directory
- a.exe (PID: 2044)
Process checks whether UAC notifications are on
- $77smartscreen.exe (PID: 6424)
Reads Internet Explorer settings
- mshta.exe (PID: 3480)
Creates or changes the value of an item property via Powershell
- cmd.exe (PID: 6940)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 4020)
Creates files or folders in the user directory
- WerFault.exe (PID: 5876)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (55.8) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21) |
| .scr | | | Windows screen saver (9.9) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:06:21 03:26:26+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 39424 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb8de |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 0.0.0.0 |
| InternalName: | a.exe |
| LegalCopyright: | |
| OriginalFileName: | a.exe |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
163
Monitored processes
25
Malicious processes
5
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 672 | winlogon.exe | C:\Windows\System32\winlogon.exe | — | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Logon Application Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1036 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES7138.tmp" "c:\Users\admin\AppData\Local\Temp\ztijxpbi\CSC42C260FBBA824582BA29E5602CAE38F3.TMP" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.32.31326.0 Modules
| |||||||||||||||
| 1136 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RESAE80.tmp" "c:\Users\admin\AppData\Local\Temp\egrifkdt\CSC165ED51FF20435A95E0BF6CFA18918D.TMP" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.32.31326.0 Modules
| |||||||||||||||
| 1216 | "C:\Users\admin\AppData\Local\Temp\a.exe" | C:\Users\admin\AppData\Local\Temp\a.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 3221226540 Version: 0.0.0.0 Modules
| |||||||||||||||
| 1356 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1984 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2044 | "C:\Users\admin\AppData\Local\Temp\a.exe" | C:\Users\admin\AppData\Local\Temp\a.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 2292 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\egrifkdt\egrifkdt.cmdline" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe | $77smartscreen.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 2368 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy Bypass Add-MpPreference -ExclusionPath 'C:\ProgramData\$77smartscreen.exe' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | a.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2512 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\ztijxpbi\ztijxpbi.cmdline" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe | a.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
Total events
38 886
Read events
38 824
Write events
59
Delete events
3
Modification events
| (PID) Process: | (2044) a.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\a_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2044) a.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\a_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (2044) a.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\a_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2044) a.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\a_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (2044) a.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\a_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (2044) a.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\a_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2044) a.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\a_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2044) a.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\a_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2044) a.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\a_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (2044) a.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\a_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
3
Suspicious files
7
Text files
20
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2044 | a.exe | C:\Users\admin\AppData\Local\Temp\ztijxpbi\ztijxpbi.cmdline | text | |
MD5:A7ED64AB3EE8A6C3C3251A39CB863464 | SHA256:E5F85EC8BB700B02030879C3FFAC52B62123AE893E9E699E0774F4249923344D | |||
| 2044 | a.exe | C:\ProgramData\$77smartscreen.exe | executable | |
MD5:B1CA8F673A35CA99CA2C153E38BCE2D1 | SHA256:1CAE91457986F019B8DEFD3C9E686EA54971BD19C59A03E8DB8DFD7302C70BA3 | |||
| 2044 | a.exe | C:\Users\admin\AppData\Local\Temp\ztijxpbi\ztijxpbi.0.cs | text | |
MD5:1F1FA674D7E6C20CF22BD20EBEAEBEFC | SHA256:443310E6E01455F08B4C4801D487E1D25C8665707DACE0A67A6D52AAF7CD8C61 | |||
| 2368 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_g1x5iey2.th2.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2512 | csc.exe | C:\Users\admin\AppData\Local\Temp\ztijxpbi\ztijxpbi.out | text | |
MD5:2C348D6B51E9A4ADEEBCCBC4162EE6D4 | SHA256:3271AC9F5C81DC51622A499690CD45CDB2F574EE5011ECA08720B6ED9C497726 | |||
| 1036 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RES7138.tmp | binary | |
MD5:D63B8B94DA27E19A05286CF87600C0C7 | SHA256:F7202ADE098783B4946DFC74A64616D48A79BE34A45EB3C93A8A35C689B146D3 | |||
| 2368 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_vmfqvlpk.qgb.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2368 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:D457581D87C814437A4833C3F4F684D2 | SHA256:570B2DA93E99EA4B32F306DA6B5B57B936967A786BB028595B9C614E864F0132 | |||
| 2292 | csc.exe | C:\Users\admin\AppData\Local\Temp\egrifkdt\CSC165ED51FF20435A95E0BF6CFA18918D.TMP | binary | |
MD5:84188ED8EA0898D30202FA241E04A344 | SHA256:FD4021CE67C24A507E16A57D59D3CE528EE8A9D9615A7592E8B3056357324022 | |||
| 1136 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RESAE80.tmp | binary | |
MD5:C9173A908278429E17A80DE16F73E6A0 | SHA256:FFC229B42B98EB47F251D71B3D7C9286C9C280837DB0E6055FC3F9559522F7C9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
30
DNS requests
15
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2596 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 184.24.77.35:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4816 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2044 | a.exe | 49.13.5.8:443 | pastefy.app | Hetzner Online GmbH | DE | unknown |
2044 | a.exe | 185.199.110.133:443 | raw.githubusercontent.com | FASTLY | US | whitelisted |
2044 | a.exe | 35.173.69.207:443 | hai1723.pythonanywhere.com | AMAZON-AES | US | whitelisted |
2596 | svchost.exe | 40.126.32.74:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2336 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
pastefy.app |
| unknown |
raw.githubusercontent.com |
| whitelisted |
hai1723.pythonanywhere.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
akira-kappa.vercel.app |
| unknown |
nexusrules.officeapps.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2200 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2200 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloud infrastructure to build app (vercel .app) |
Process | Message |
|---|---|
$77smartscreen.exe | Detected tampering |
$77smartscreen.exe | CLR: Managed code called FailFast, saying " |
$77smartscreen.exe | "
|