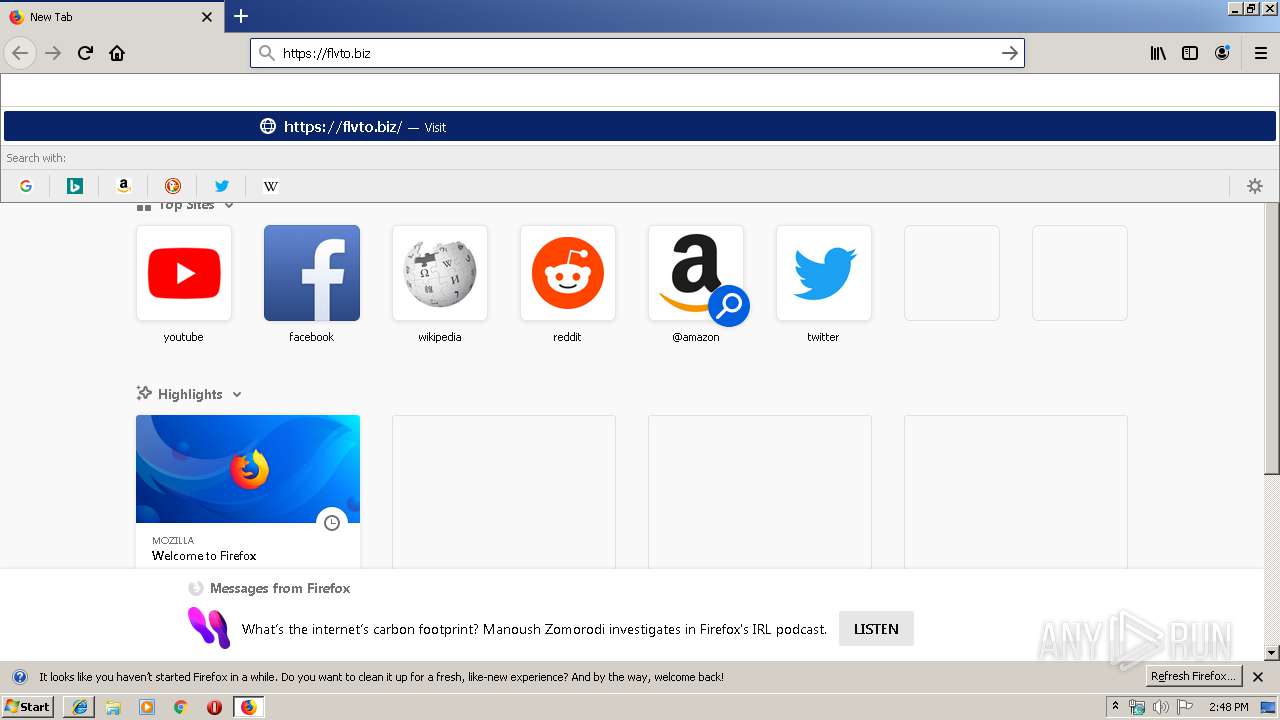
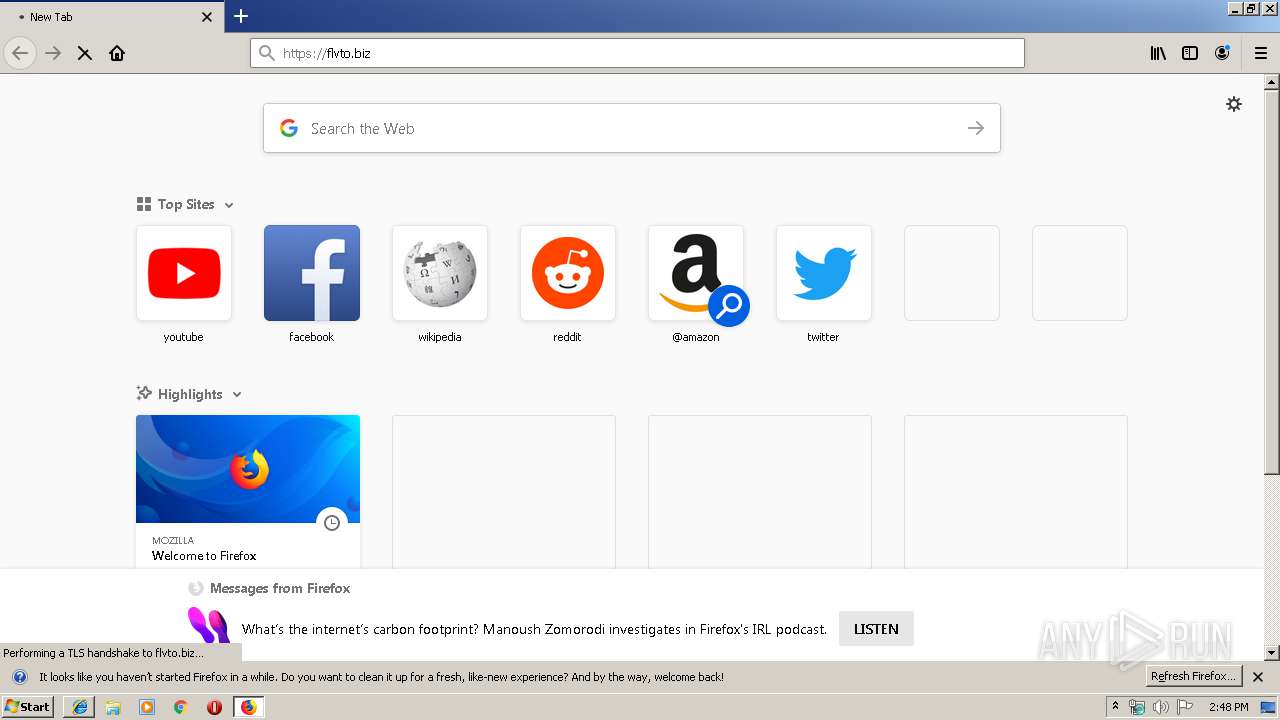
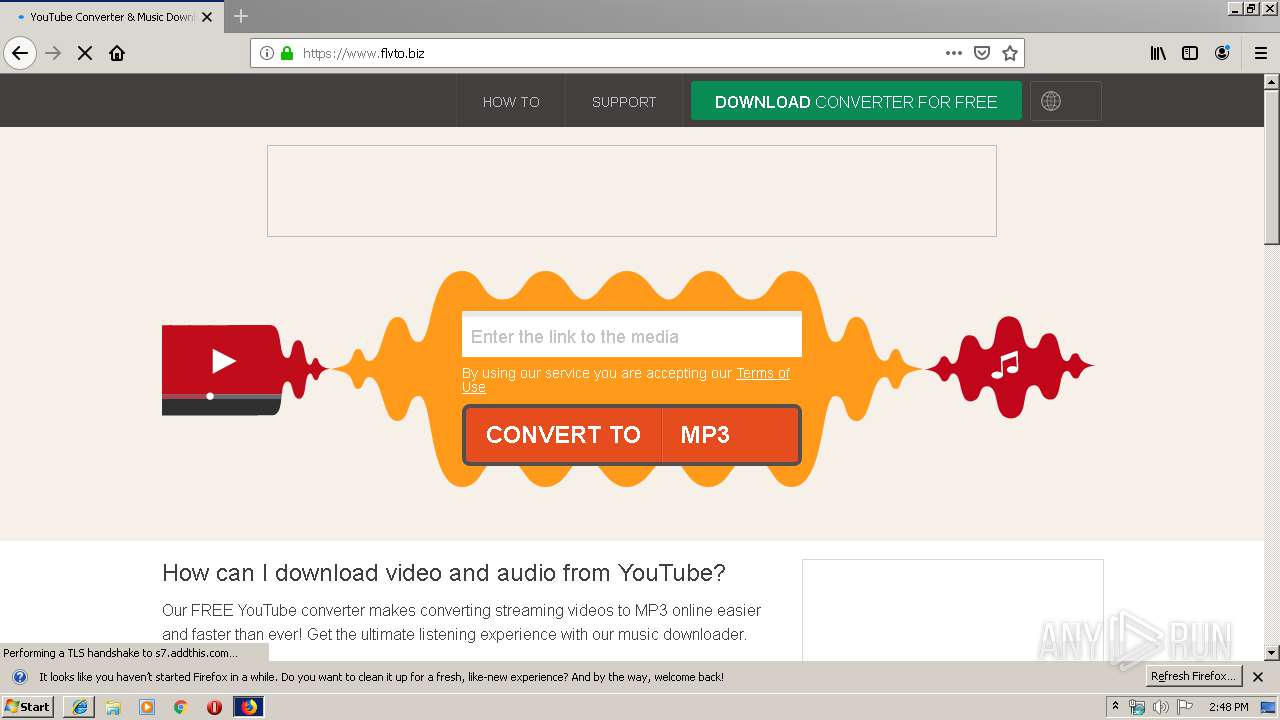
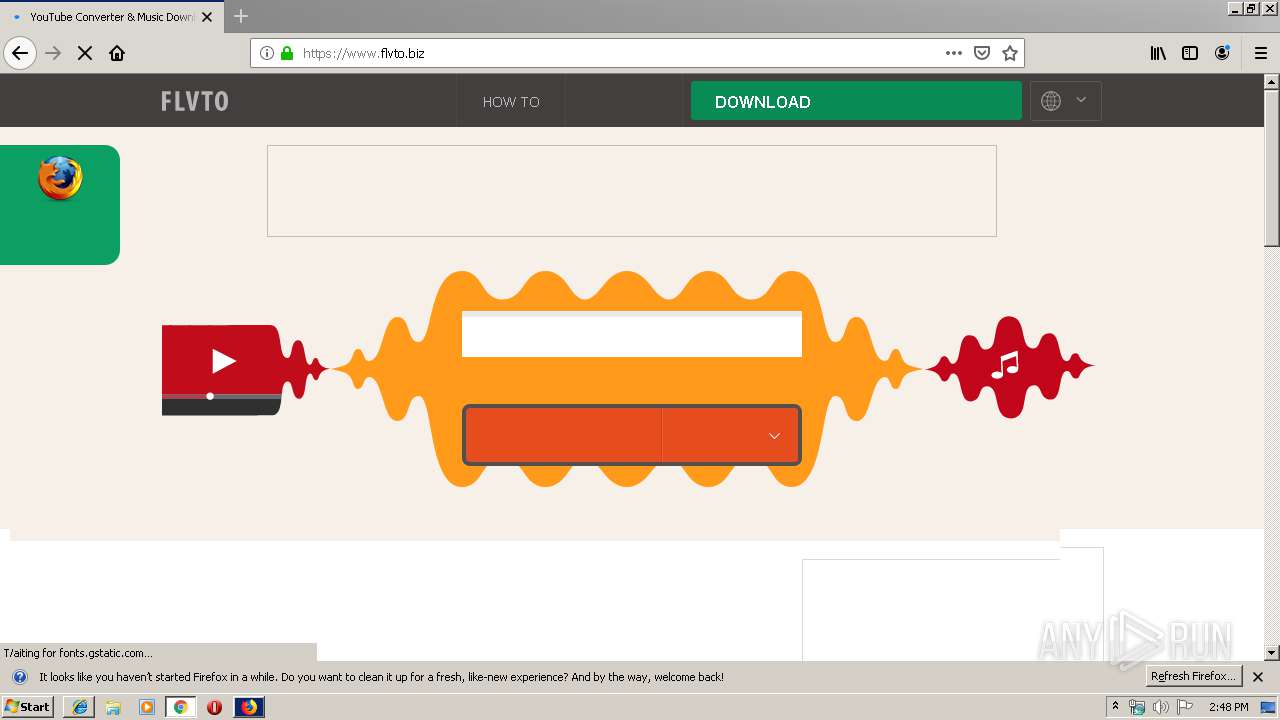
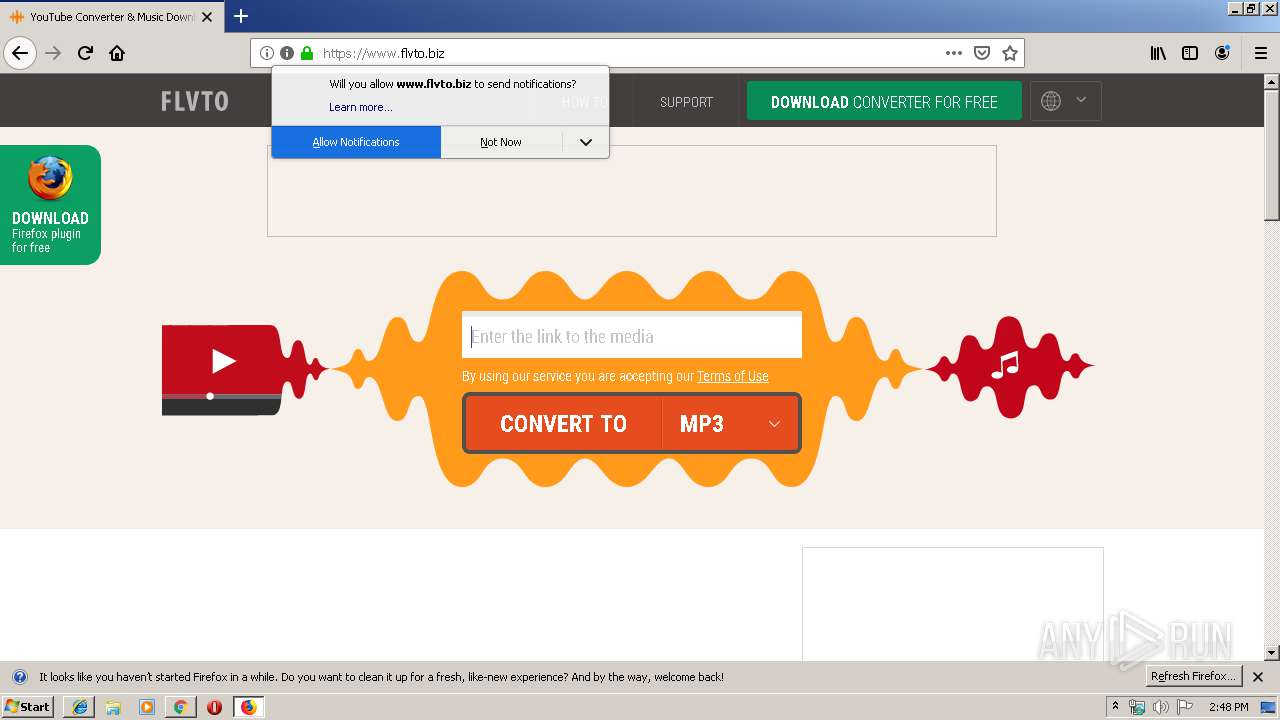
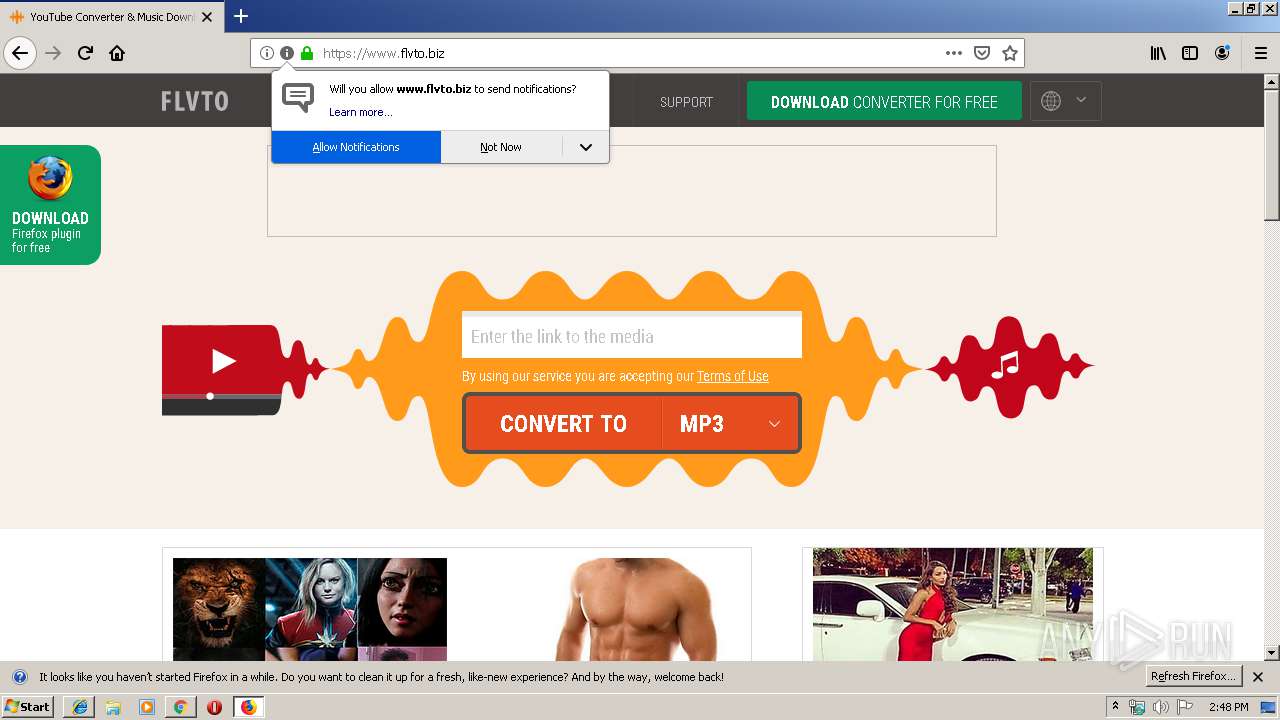
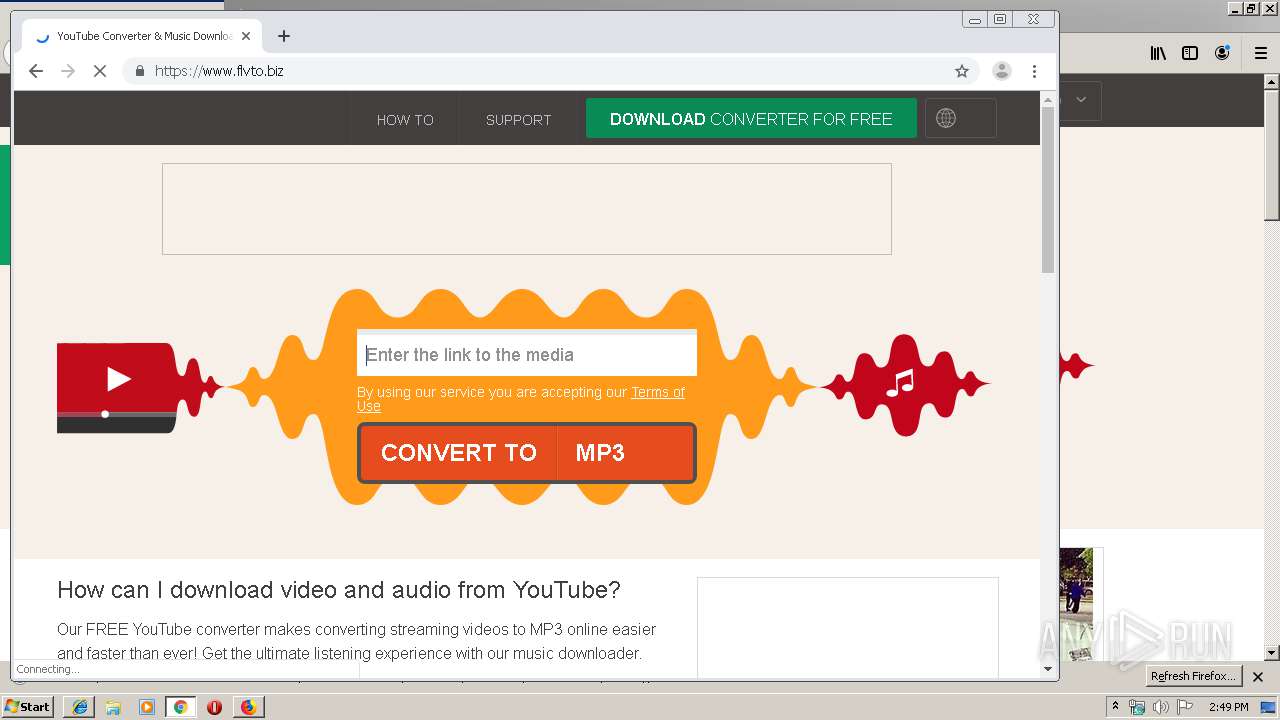
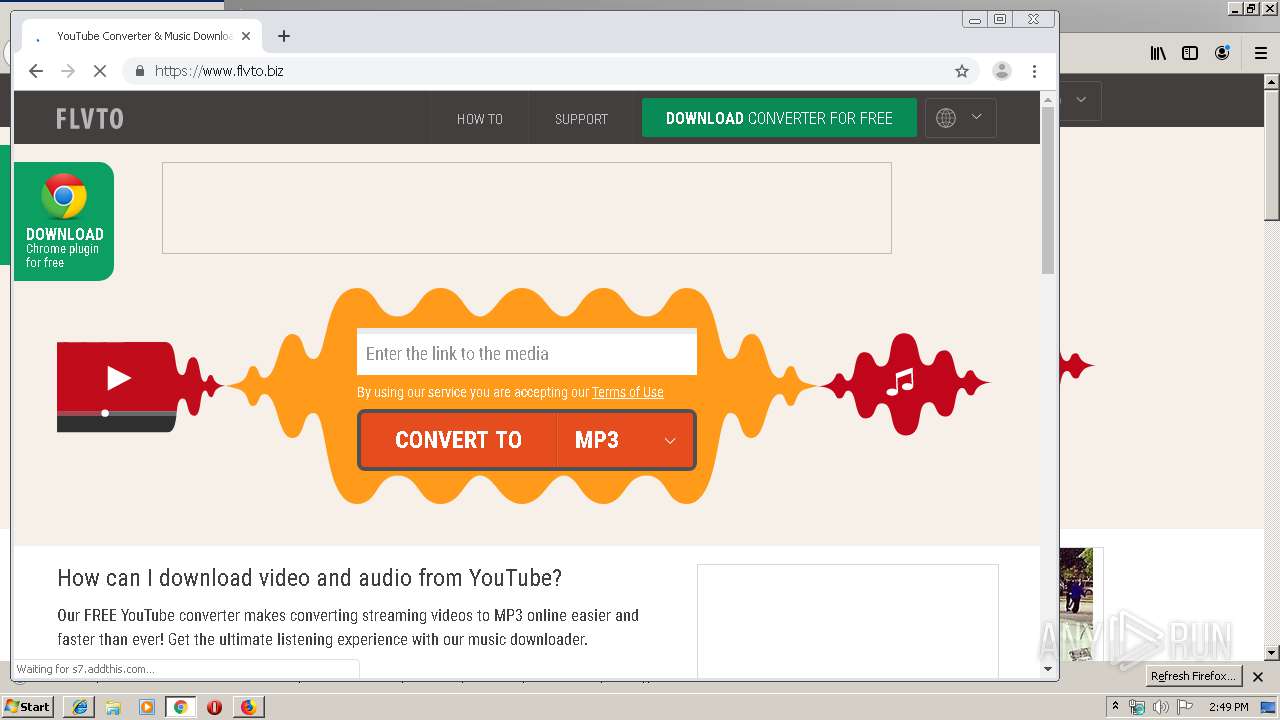
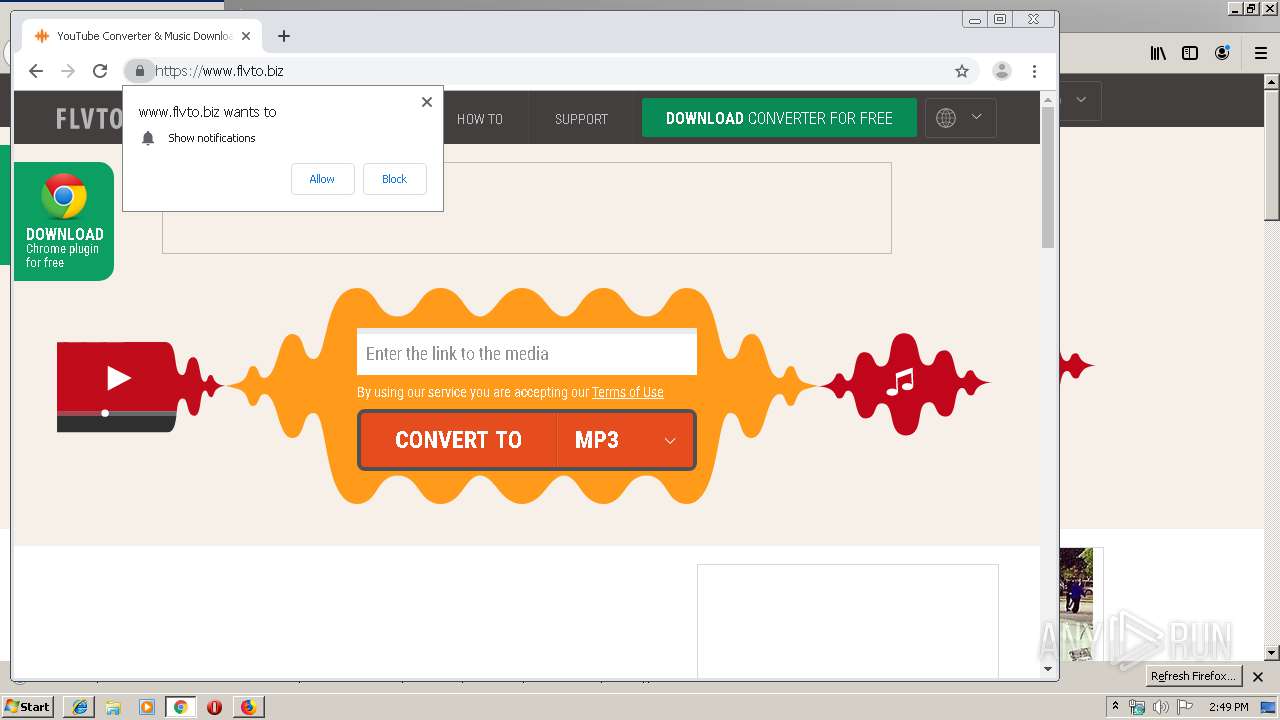
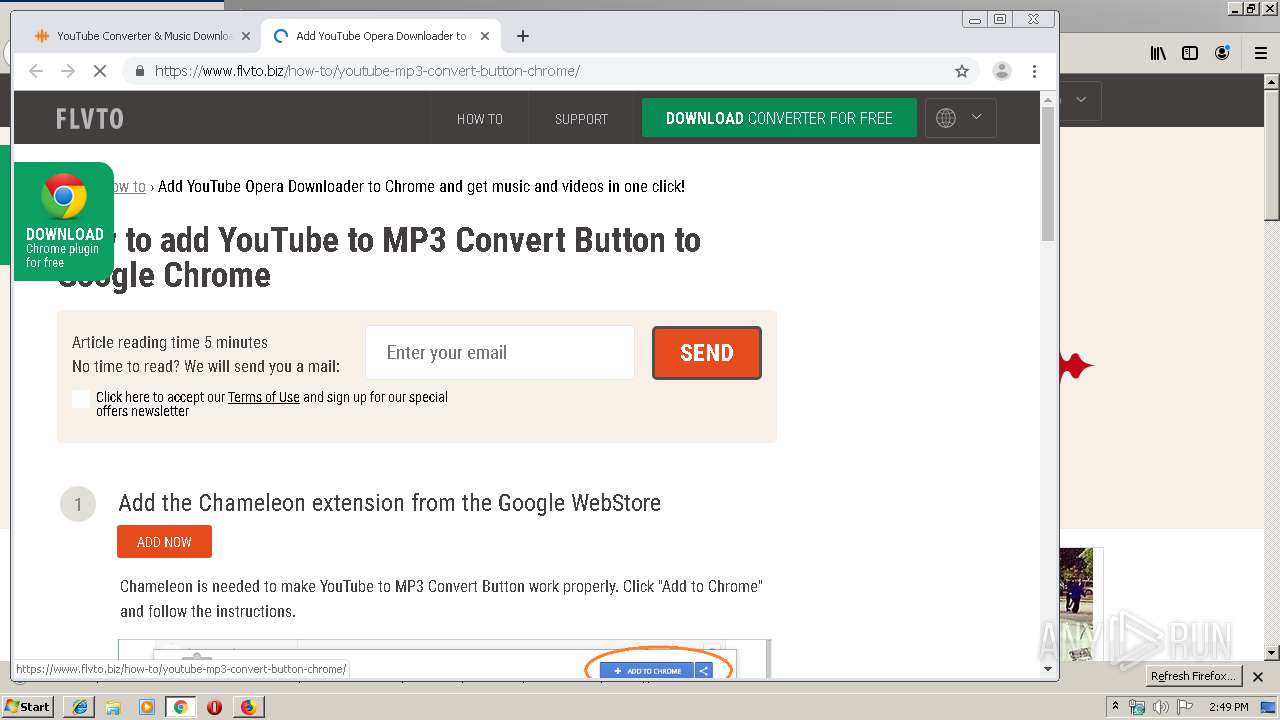
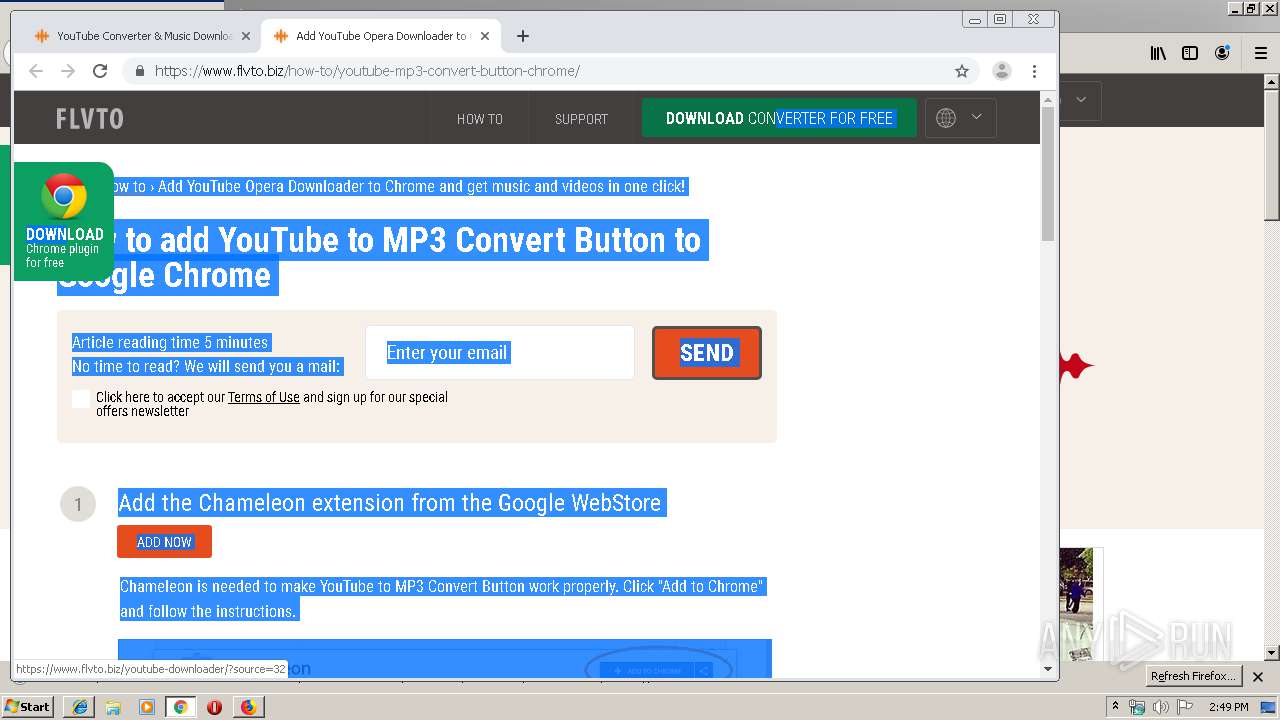
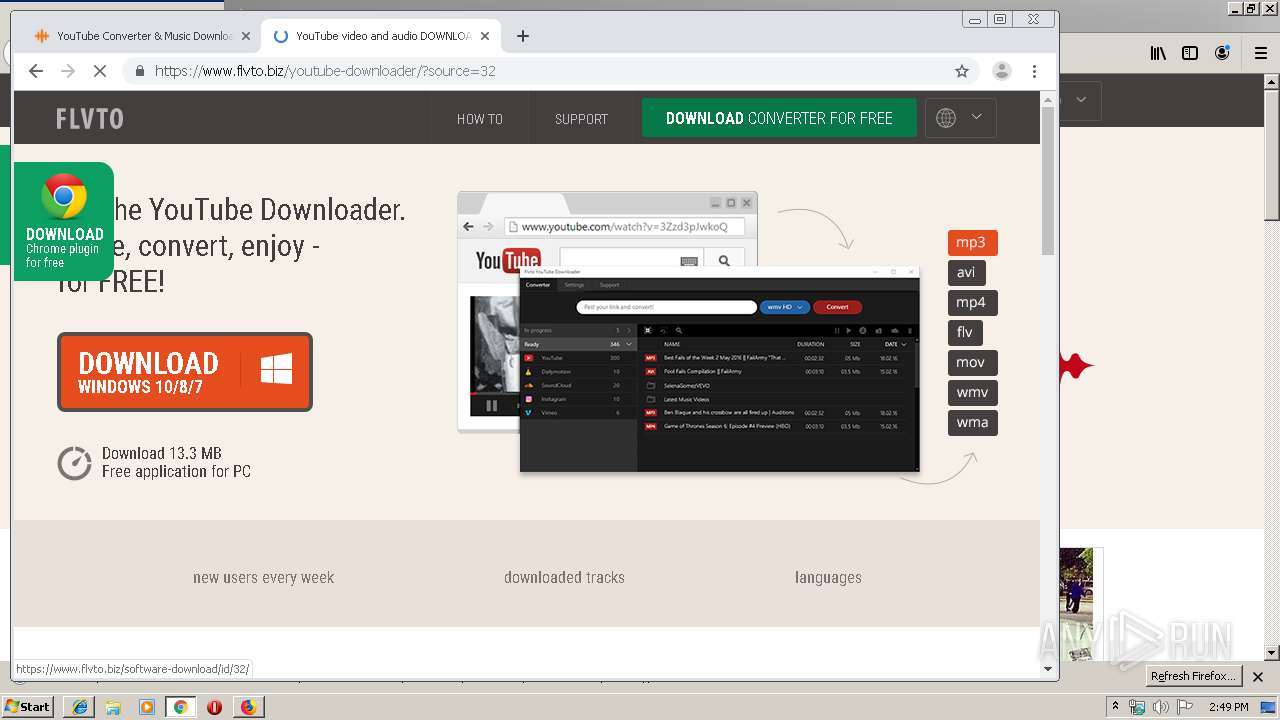
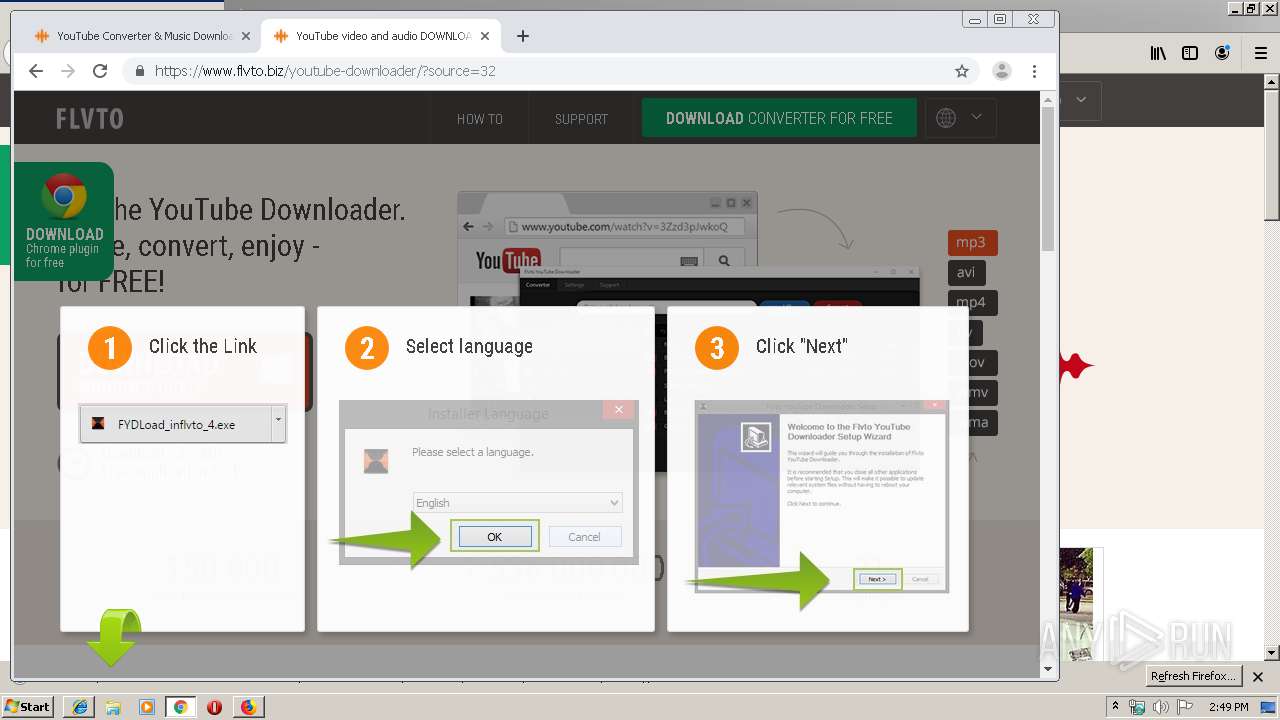
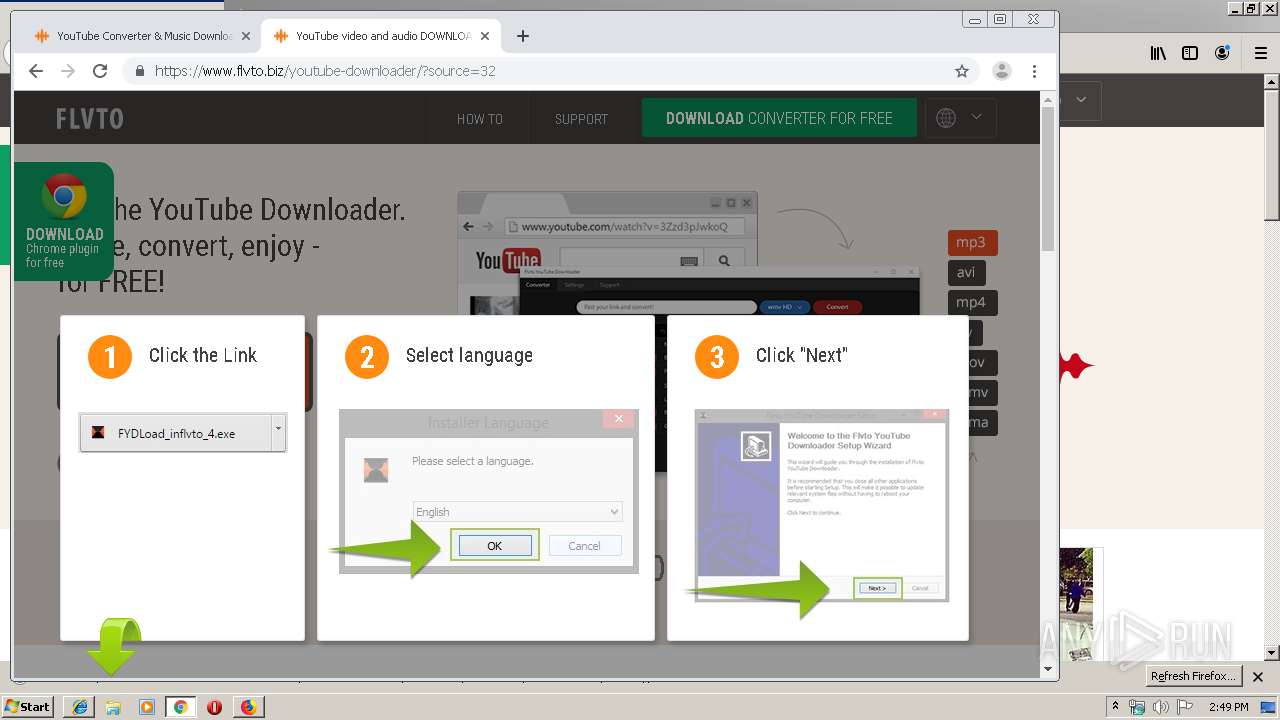
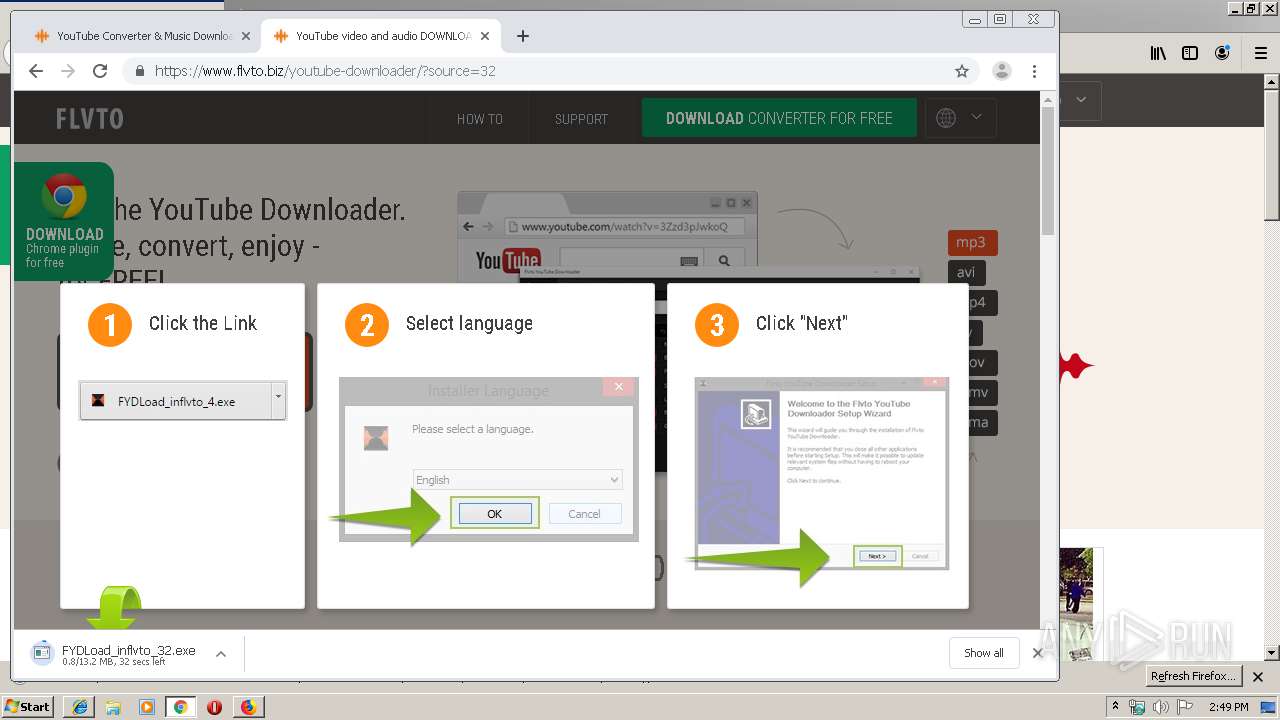
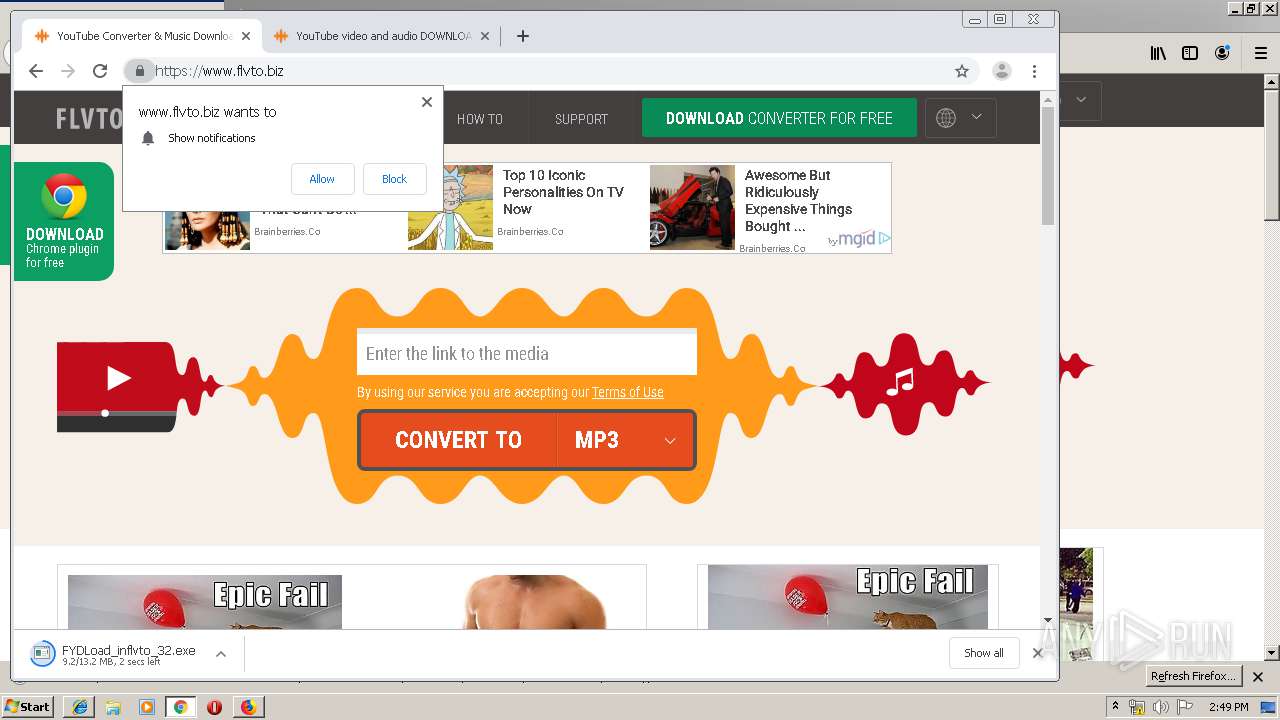
| URL: | https://flvto.biz |
| Full analysis: | https://app.any.run/tasks/c522b7ce-a416-451b-91e9-2a5768e55a21 |
| Verdict: | Malicious activity |
| Analysis date: | July 17, 2019, 13:48:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 8312CCFCF97546F15FAE3872DADCC7C8 |
| SHA1: | C2AD32D2C3BA9089438EC29ED1BEB55263C84D7A |
| SHA256: | 1C9A42E7BEDE59D3E3DEDD97AAC893BF906F9A23A6473EBE8D064A963ADC6560 |
| SSDEEP: | 3:N8XsL+:2Xq+ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3864)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3952)
Executable content was dropped or overwritten
- chrome.exe (PID: 3952)
INFO
Creates files in the user directory
- iexplore.exe (PID: 3408)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3864)
- firefox.exe (PID: 3108)
Reads CPU info
- firefox.exe (PID: 3108)
Manual execution by user
- firefox.exe (PID: 3108)
- chrome.exe (PID: 3952)
Reads internet explorer settings
- iexplore.exe (PID: 3408)
Application launched itself
- iexplore.exe (PID: 3028)
- firefox.exe (PID: 3108)
- chrome.exe (PID: 3952)
Reads Internet Cache Settings
- iexplore.exe (PID: 3408)
Writes to a desktop.ini file (may be used to cloak folders)
- firefox.exe (PID: 4004)
Changes settings of System certificates
- iexplore.exe (PID: 3028)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3028)
Dropped object may contain Bitcoin addresses
- firefox.exe (PID: 3108)
Changes internet zones settings
- iexplore.exe (PID: 3028)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
69
Monitored processes
34
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1352 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3108.13.1132202425\1051387685" -childID 2 -isForBrowser -prefsHandle 2832 -prefMapHandle 2836 -prefsLen 5842 -prefMapSize 188076 -parentBuildID 20190619235627 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3108 "\\.\pipe\gecko-crash-server-pipe.3108" 2848 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 67.0.4 Modules
| |||||||||||||||
| 2320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,10814974306487814457,5089485974576905966,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17426989755253448119 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3604 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,10814974306487814457,5089485974576905966,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=229056115623005801 --mojo-platform-channel-handle=3276 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2412 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=4000 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2540 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3108.0.1183024323\1529005491" -parentBuildID 20190619235627 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3108 "\\.\pipe\gecko-crash-server-pipe.3108" 1180 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 67.0.4 Modules
| |||||||||||||||
| 2636 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,10814974306487814457,5089485974576905966,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13415782937234597236 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2440 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,10814974306487814457,5089485974576905966,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14935662856635333246 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2532 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,10814974306487814457,5089485974576905966,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11150538823564819896 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3984 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2776 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,10814974306487814457,5089485974576905966,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13530656855169928539 --mojo-platform-channel-handle=3408 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,10814974306487814457,5089485974576905966,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8386692337588154449 --mojo-platform-channel-handle=3496 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 376
Read events
1 242
Write events
127
Delete events
7
Modification events
| (PID) Process: | (3028) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3028) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3028) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3028) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3028) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3028) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000077000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3028) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {8F843663-A899-11E9-A9B1-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3028) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3028) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (3028) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070700030011000D0030001F007D02 | |||
Executable files
2
Suspicious files
240
Text files
319
Unknown types
111
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3028 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3028 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3408 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabB7D6.tmp | — | |
MD5:— | SHA256:— | |||
| 3408 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarB7D7.tmp | — | |
MD5:— | SHA256:— | |||
| 3408 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabB7E8.tmp | — | |
MD5:— | SHA256:— | |||
| 3408 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarB7F8.tmp | — | |
MD5:— | SHA256:— | |||
| 3408 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabB896.tmp | — | |
MD5:— | SHA256:— | |||
| 3408 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarB897.tmp | — | |
MD5:— | SHA256:— | |||
| 3408 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@www.flvto[2].txt | — | |
MD5:— | SHA256:— | |||
| 3408 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\0T2Z58WP\flvto_biz[1].txt | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
179
DNS requests
245
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3108 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3108 | firefox.exe | POST | 200 | 151.139.128.14:80 | http://ocsp.comodoca4.com/ | US | der | 281 b | whitelisted |
3108 | firefox.exe | POST | 200 | 172.217.21.227:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
3108 | firefox.exe | POST | 200 | 172.217.21.227:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
3108 | firefox.exe | POST | 200 | 151.139.128.14:80 | http://ocsp.sectigo.com/ | US | der | 471 b | whitelisted |
3108 | firefox.exe | POST | 200 | 151.139.128.14:80 | http://ocsp.comodoca4.com/ | US | der | 281 b | whitelisted |
3108 | firefox.exe | POST | 200 | 151.139.128.14:80 | http://ocsp.comodoca4.com/ | US | der | 279 b | whitelisted |
3108 | firefox.exe | POST | 200 | 151.139.128.14:80 | http://ocsp.comodoca4.com/ | US | der | 281 b | whitelisted |
3108 | firefox.exe | POST | 200 | 172.217.21.227:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
3108 | firefox.exe | POST | 200 | 172.217.21.227:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3028 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3408 | iexplore.exe | 93.184.221.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3408 | iexplore.exe | 185.59.220.13:443 | cdn.flvto.biz | Datacamp Limited | DE | suspicious |
3408 | iexplore.exe | 188.42.162.168:443 | pushagim.com | Webzilla B.V. | NL | unknown |
3108 | firefox.exe | 52.50.56.62:443 | location.services.mozilla.com | Amazon.com, Inc. | IE | unknown |
3408 | iexplore.exe | 23.210.248.44:443 | s7.addthis.com | Akamai International B.V. | NL | whitelisted |
3108 | firefox.exe | 2.16.186.50:80 | detectportal.firefox.com | Akamai International B.V. | — | whitelisted |
3108 | firefox.exe | 52.26.103.165:443 | tiles.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3108 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3108 | firefox.exe | 172.217.18.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
flvto.biz |
| whitelisted |
www.bing.com |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
www.flvto.biz |
| malicious |
cdn.flvto.biz |
| malicious |
pushagim.com |
| whitelisted |
s7.addthis.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
location.services.mozilla.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3744 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3744 | chrome.exe | Misc activity | ET INFO EXE - Served Attached HTTP |