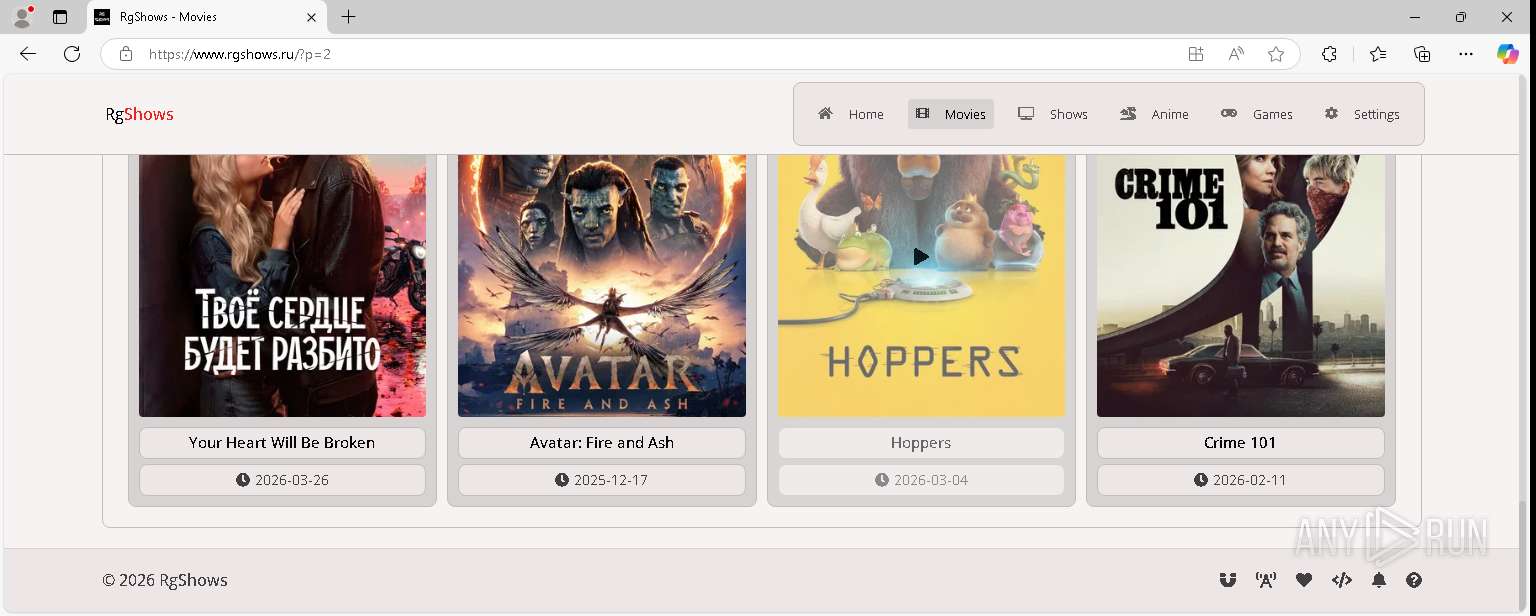
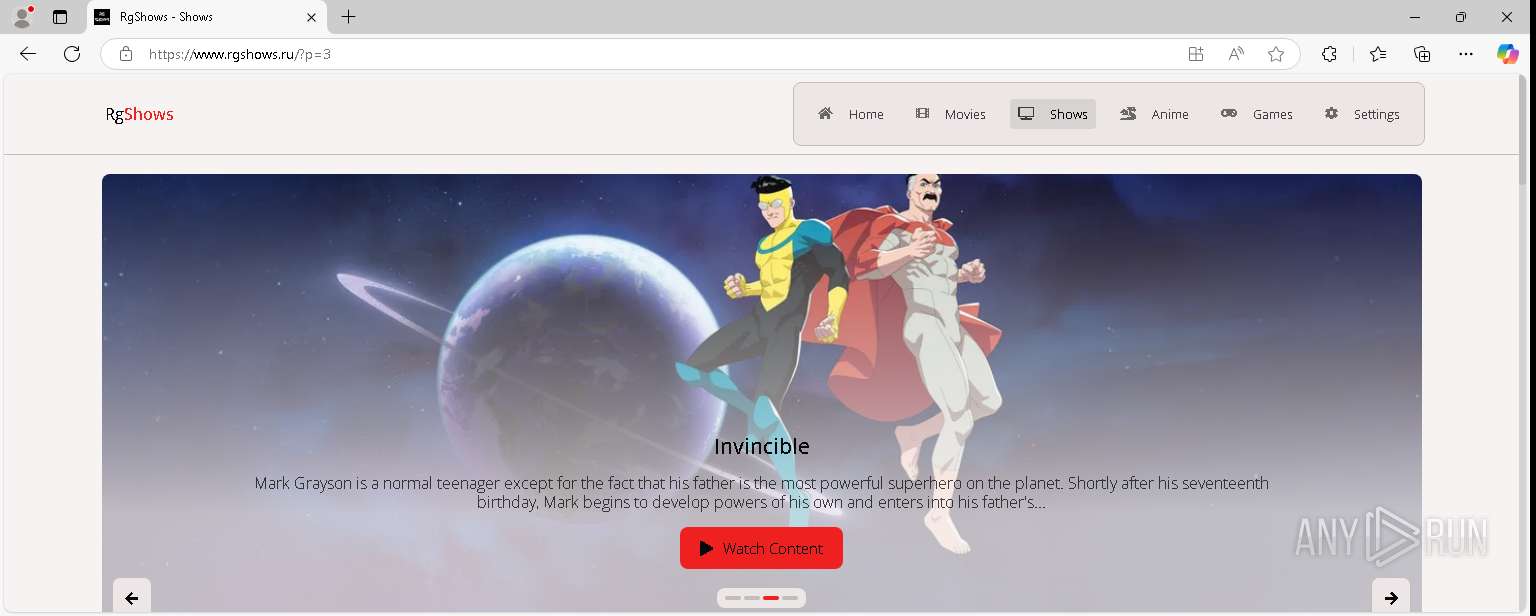
| URL: | www.rgshows.ru |
| Full analysis: | https://app.any.run/tasks/3d929751-4cd8-422e-b7f4-f5310f694029 |
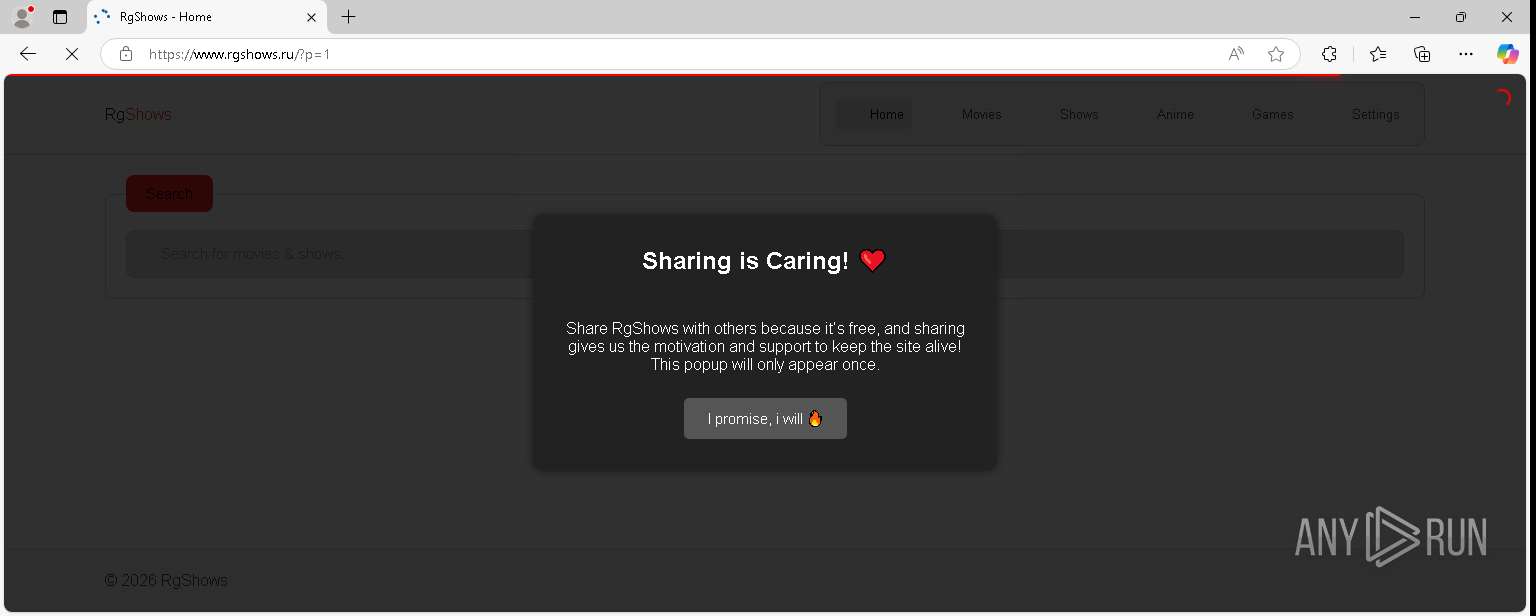
| Verdict: | Malicious activity |
| Analysis date: | April 07, 2026, 13:08:40 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | F25BD49BC4EDEF8E07ABBC5BA2EEF4F7 |
| SHA1: | A6C789F5EFF25653244EDCC1E4F8E9E25F391648 |
| SHA256: | 1C8E8A37D89D1F419612160047864F7B1E8FAA1FAF1DC29D369C4813AFFA8A6E |
| SSDEEP: | 3:EpOQ:SOQ |
MALICIOUS
PHISHING has been detected (SURICATA)
- msedge.exe (PID: 7028)
SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
150
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 7028 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --webtransport-developer-mode --string-annotations --always-read-main-dll --field-trial-handle=2256,i,13378875761215938322,9620771509043916482,262144 --variations-seed-version --mojo-platform-channel-handle=2616 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
103
Text files
212
Unknown types
25
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7028 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Cache\Cache_Data\f_0000ba | text | |
MD5:D824DF7EB2E268626A2DD9A6A741AC4E | SHA256:9834B82AD26E2A37583D22676A12DD2EB0FE7C80356A2114D0DB1AA8B3899537 | |||
| 7028 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Cache\Cache_Data\f_0000b8 | binary | |
MD5:DCF31EBE107435BD68E0164D59E19B87 | SHA256:D8E4FE0452AA2076429A9BB5D8757D00A994DD95986CF950E9A1A371B9A072A0 | |||
| 7028 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Cache\Cache_Data\f_0000b6 | text | |
MD5:DD5E5819B692DD2277B28807AA4FF9A7 | SHA256:B5A080717A0D8EE2B9877A148E2208B53D6C287100E36D35B75119EA6CCA2175 | |||
| 7028 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Cache\Cache_Data\f_0000b9 | binary | |
MD5:5B34233BDCB80EF7F22C3F50D5E674AE | SHA256:22F246328165573BDCED4A188917B5B7F0A3B960C30EC76C9EBF7DFC96B66E3D | |||
| 7028 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Cache\Cache_Data\f_0000b5 | binary | |
MD5:905F74DC6BA373879D507C738F31B5CD | SHA256:9841696327B0E03DC7082269641CA1AB56F2E4A73276341293BBE623A0AD0F47 | |||
| 7028 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Cache\Cache_Data\f_0000bd | binary | |
MD5:DAE1850484B86D299C31BC08AAA563CF | SHA256:8F80F993E523F2E6C2D097552740FD26331658DA23FFAD31D26EDCDD3AEEC370 | |||
| 7028 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Cache\Cache_Data\f_0000c4 | binary | |
MD5:56F67D55BBCC9776AC158F02C0B3CFB2 | SHA256:1085B6D075413A87D4624D162D0F953C8C29F9CA00C9C7A85FC9A15EFC06CC4A | |||
| 7028 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Cache\Cache_Data\f_0000c2 | compressed | |
MD5:F3AD19FDBD15A27B32A4D25E49CC266E | SHA256:3A657EDDEC2905CE29950E37A3CC78C6839AFC858FE26A89490A1502BE032D13 | |||
| 7028 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Cache\Cache_Data\f_0000bf | compressed | |
MD5:11E72FE31D0BB9CAD04B6E38D23690AD | SHA256:91924165D8CEE9B31863A205104625140961CDC67C7445D87D863A5F76916002 | |||
| 7028 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Cache\Cache_Data\f_0000c0 | binary | |
MD5:50A21149BD2D7FF151B1B1CEBF8F35B5 | SHA256:93345AB045F97BF70B4C8B40B597DC1C1EDA33EA8A59A2E917ED4C4D2AB7FDFC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
590
TCP/UDP connections
173
DNS requests
102
Threats
23
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7028 | msedge.exe | GET | 200 | 188.114.97.3:443 | https://www.rgshows.ru/ | US | text | 208 Kb | unknown |
7028 | msedge.exe | GET | 200 | 92.123.104.45:443 | https://www.bing.com/bloomfilterfiles/ExpandedDomainsFilterGlobal.json | unknown | text | 665 Kb | whitelisted |
7028 | msedge.exe | GET | 200 | 188.114.97.3:443 | https://www.rgshows.ru/js/fubuki.js | US | binary | 351 b | unknown |
7028 | msedge.exe | GET | 200 | 188.114.97.3:443 | https://www.rgshows.ru/css/flash.css | US | text | 2.00 Kb | unknown |
7028 | msedge.exe | GET | 200 | 188.114.97.3:443 | https://www.rgshows.ru/js/mercury.js | US | text | 316 b | unknown |
7028 | msedge.exe | GET | 200 | 188.114.97.3:443 | https://www.rgshows.ru/js/aichat_widget.js | US | binary | 5.21 Kb | unknown |
7028 | msedge.exe | GET | 200 | 188.114.97.3:443 | https://www.rgshows.ru/js/screenshare_widget.js | US | binary | 4.89 Kb | unknown |
7028 | msedge.exe | GET | 200 | 188.114.97.3:443 | https://www.rgshows.ru/js/auto_next.js | US | text | 6.26 Kb | unknown |
7028 | msedge.exe | GET | 200 | 172.67.130.104:443 | https://cdn.jsdelivr.net/npm/disable-devtool@latest | US | text | 17.2 Kb | whitelisted |
7028 | msedge.exe | GET | 200 | 188.114.97.3:443 | https://www.rgshows.ru/js/shortcut.js | US | text | 7.46 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
7092 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5336 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5188 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 224.0.0.251:5353 | — | — | — | whitelisted |
7028 | msedge.exe | 184.86.251.9:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
7028 | msedge.exe | 188.114.97.3:443 | www.rgshows.ru | CLOUDFLARENET | US | whitelisted |
7028 | msedge.exe | 104.16.174.226:443 | cdn.jsdelivr.net | CLOUDFLARENET | US | whitelisted |
7028 | msedge.exe | 142.251.13.95:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
7028 | msedge.exe | 104.18.0.22:443 | unpkg.com | CLOUDFLARENET | US | whitelisted |
7028 | msedge.exe | 104.17.24.14:443 | cdnjs.cloudflare.com | CLOUDFLARENET | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.rgshows.ru |
| malicious |
cdn.jsdelivr.net |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
unpkg.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7028 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing Domain (rgshows .ru) |
7028 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7028 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7028 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7028 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7028 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Global content delivery network (unpkg .com) |
7028 | msedge.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
7028 | msedge.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
7028 | msedge.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
7028 | msedge.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |