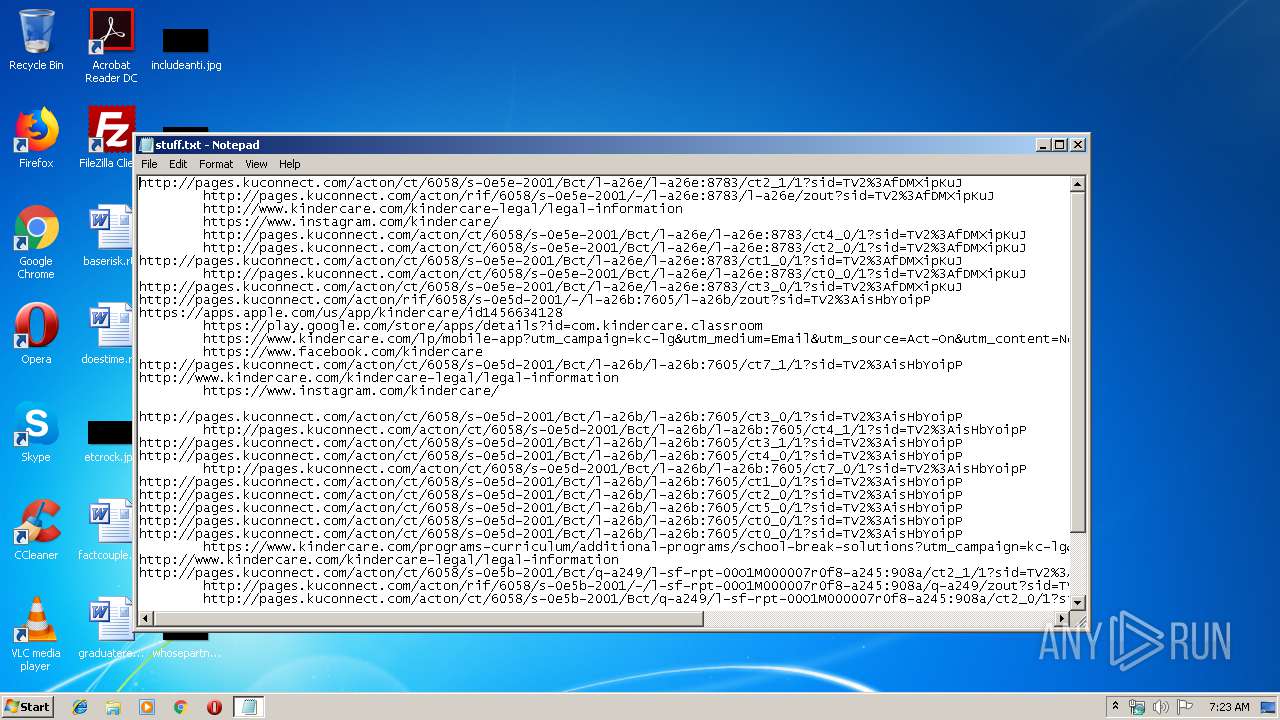
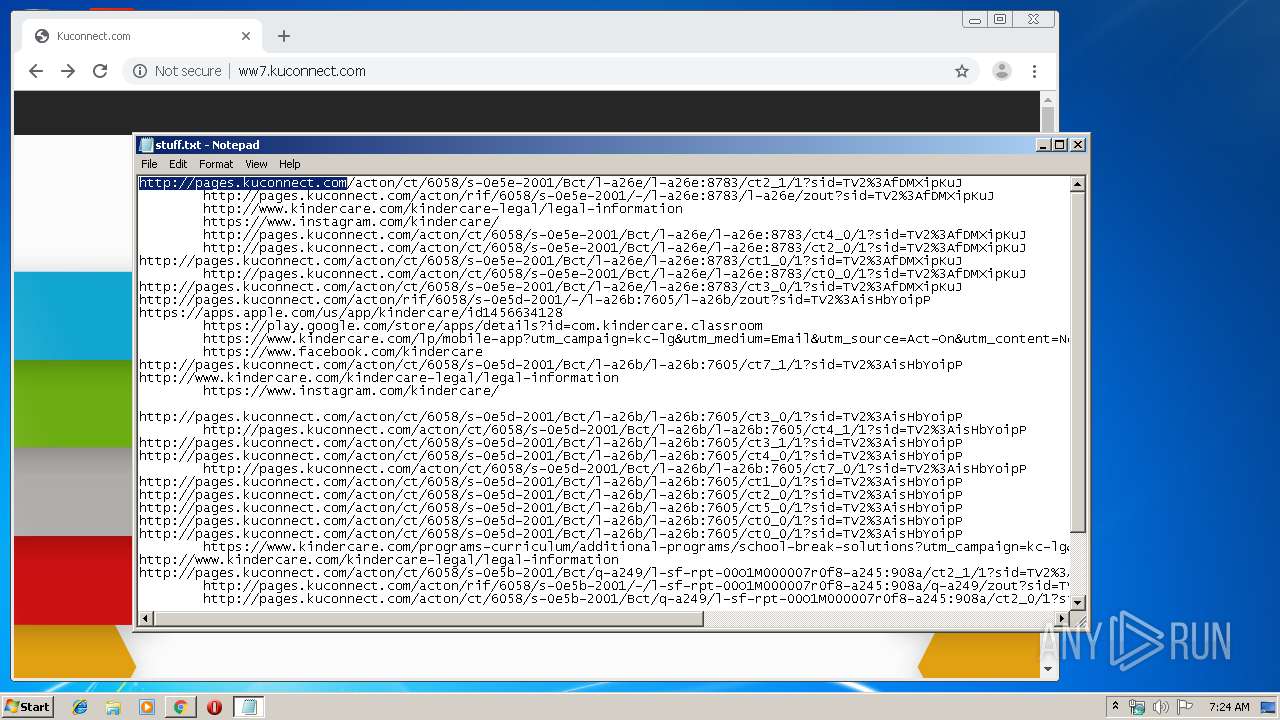
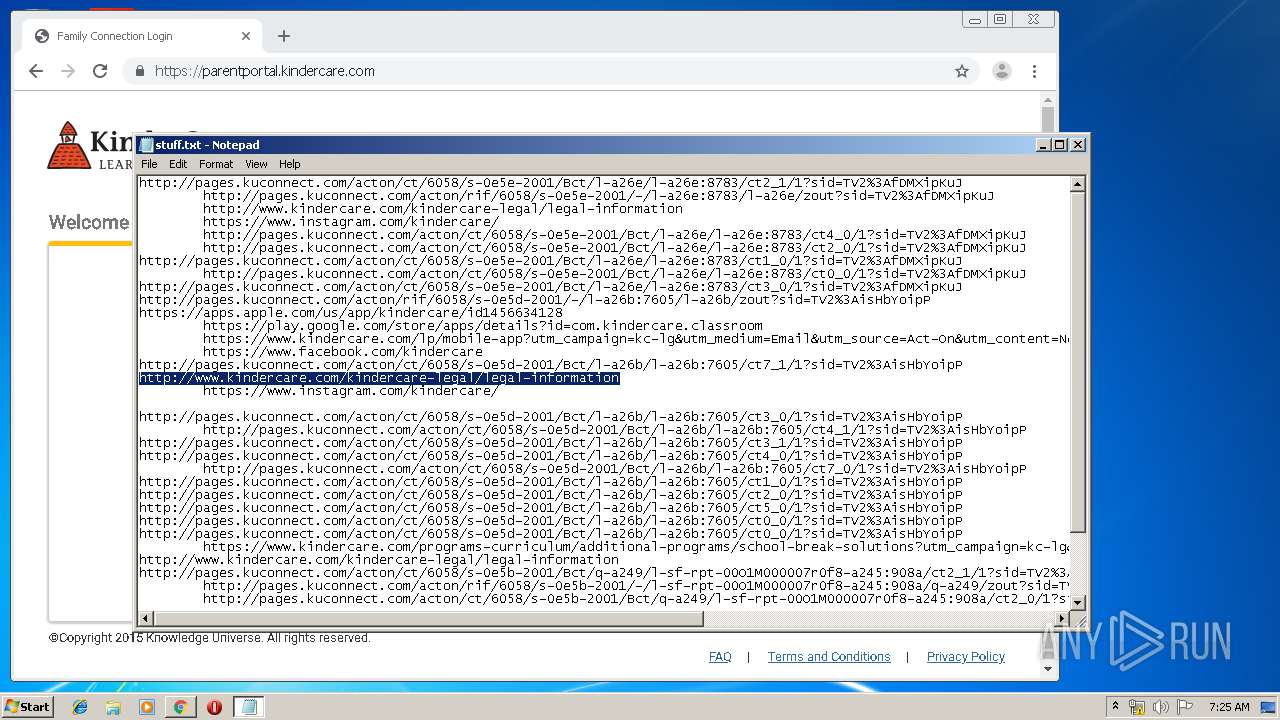
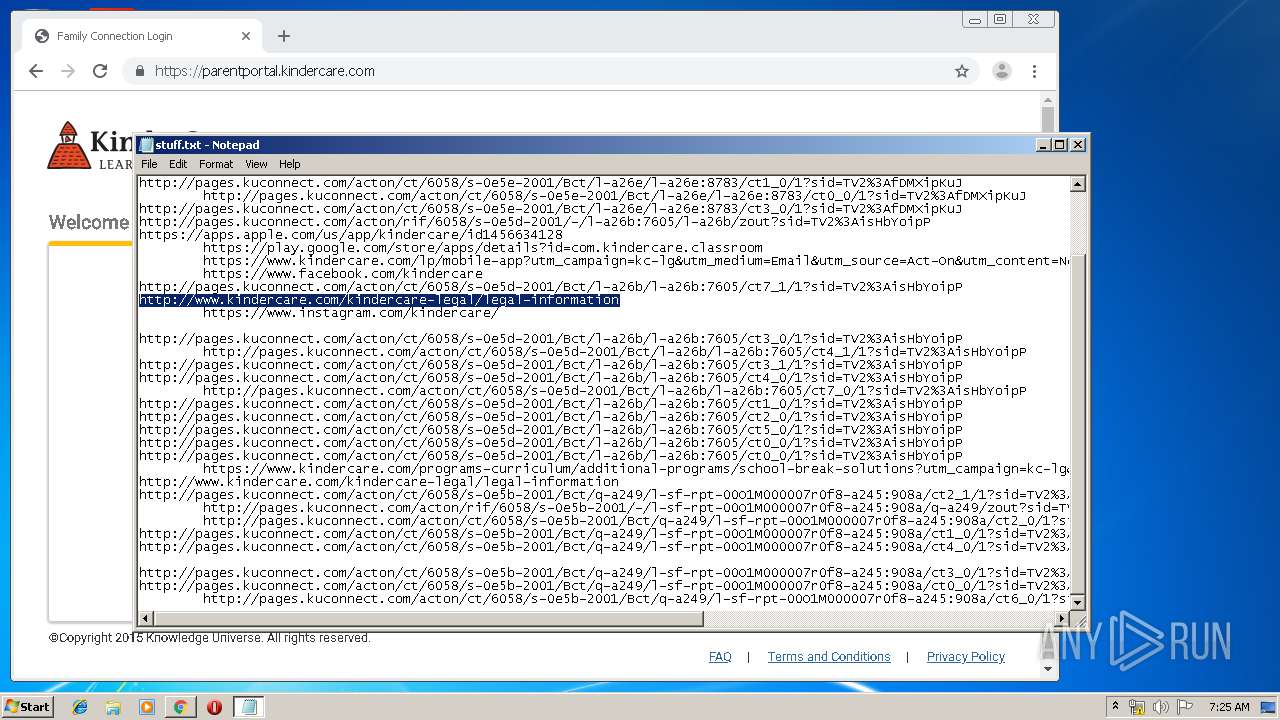
| File name: | stuff.txt |
| Full analysis: | https://app.any.run/tasks/064c3ab0-4162-4ae9-81d0-4ee1522ee092 |
| Verdict: | Malicious activity |
| Analysis date: | January 18, 2020, 07:23:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators |
| MD5: | A3FD506B8480E87F513873BA18665C38 |
| SHA1: | 31CAD2BD34774DA6D5FBB03AFDE01B241F3788C7 |
| SHA256: | 1C7D1E4187047B580ADB33E8096D0E02FF81AEAFDC9DB23DF71A1712B8F8122A |
| SSDEEP: | 96:ur/V66rSrRrRrnrYSyfiPOZQfUyUXYFRkvIbqORtY:ur/VzrSrRrRrnrYziPOZQfUyUXYFRkvZ |
MALICIOUS
Connects to CnC server
- chrome.exe (PID: 3996)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 1096)
INFO
Manual execution by user
- chrome.exe (PID: 1096)
Reads the hosts file
- chrome.exe (PID: 1096)
- chrome.exe (PID: 3996)
Reads settings of System Certificates
- chrome.exe (PID: 3996)
Application launched itself
- chrome.exe (PID: 1096)
Changes settings of System certificates
- chrome.exe (PID: 3996)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
86
Monitored processes
51
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1000,11747572302917268919,5747440781584456884,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=8382759109941909229 --mojo-platform-channel-handle=4004 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,11747572302917268919,5747440781584456884,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6416376603623016571 --mojo-platform-channel-handle=3944 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,11747572302917268919,5747440781584456884,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16738686597502466529 --mojo-platform-channel-handle=3088 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 444 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,11747572302917268919,5747440781584456884,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5927965890748919445 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2528 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,11747572302917268919,5747440781584456884,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11098462912788203829 --mojo-platform-channel-handle=4876 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,11747572302917268919,5747440781584456884,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15910624576435425280 --mojo-platform-channel-handle=4696 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 640 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,11747572302917268919,5747440781584456884,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1420172185766939659 --renderer-client-id=46 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3476 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 716 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,11747572302917268919,5747440781584456884,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2859602016939782494 --mojo-platform-channel-handle=2688 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,11747572302917268919,5747440781584456884,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17192337248242800396 --mojo-platform-channel-handle=3320 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1044 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,11747572302917268919,5747440781584456884,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10426537119645640588 --renderer-client-id=48 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2052 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
689
Read events
574
Write events
110
Delete events
5
Modification events
| (PID) Process: | (1552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1096-13223805829051375 |
Value: 259 | |||
| (PID) Process: | (1096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (1096) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
133
Text files
292
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF39c6e4.TMP | — | |
MD5:— | SHA256:— | |||
| 1096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\cb7b6575-ca85-4a9d-8890-7f808c67ba73.tmp | — | |
MD5:— | SHA256:— | |||
| 1096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old~RF39c713.TMP | text | |
MD5:— | SHA256:— | |||
| 1096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF39c6b5.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
55
TCP/UDP connections
106
DNS requests
71
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
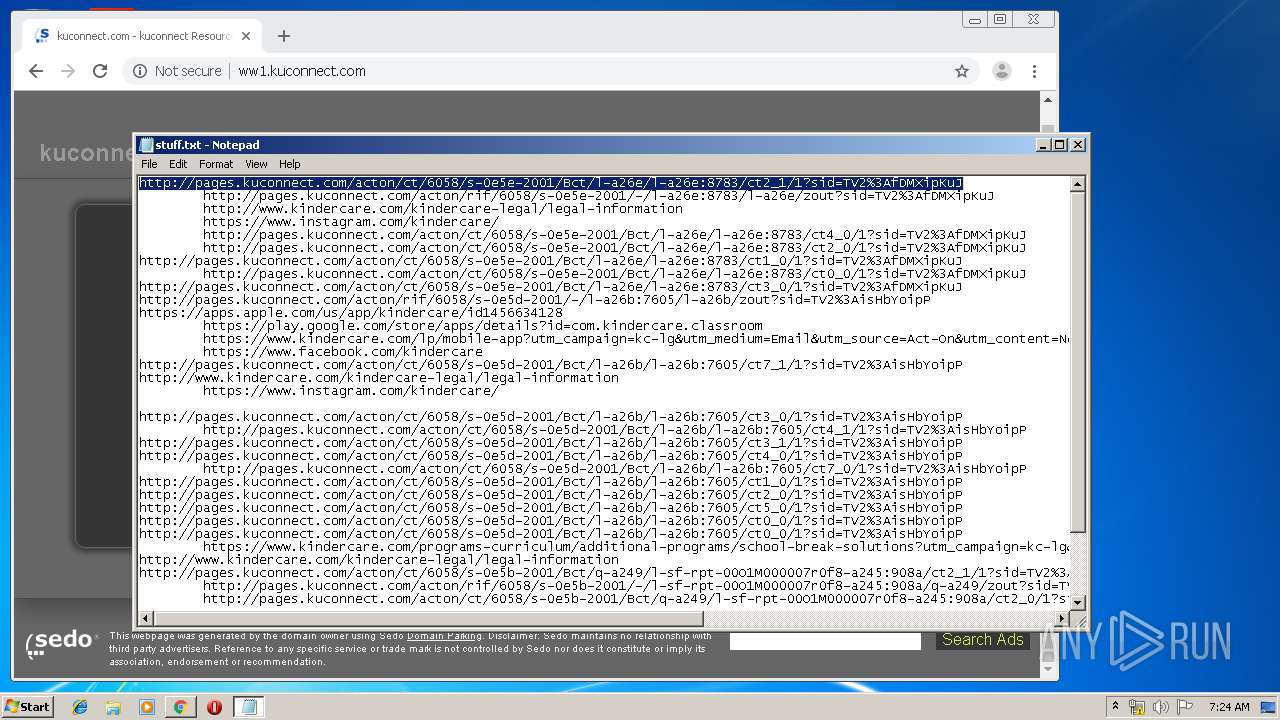
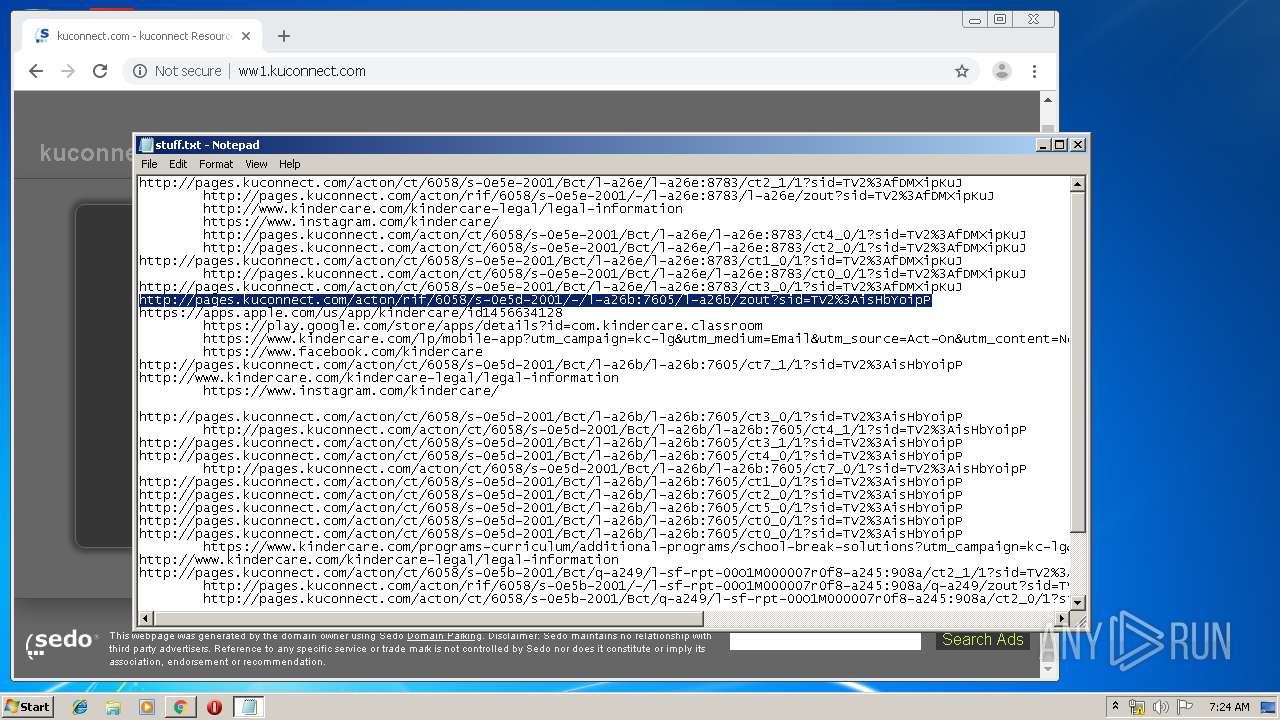
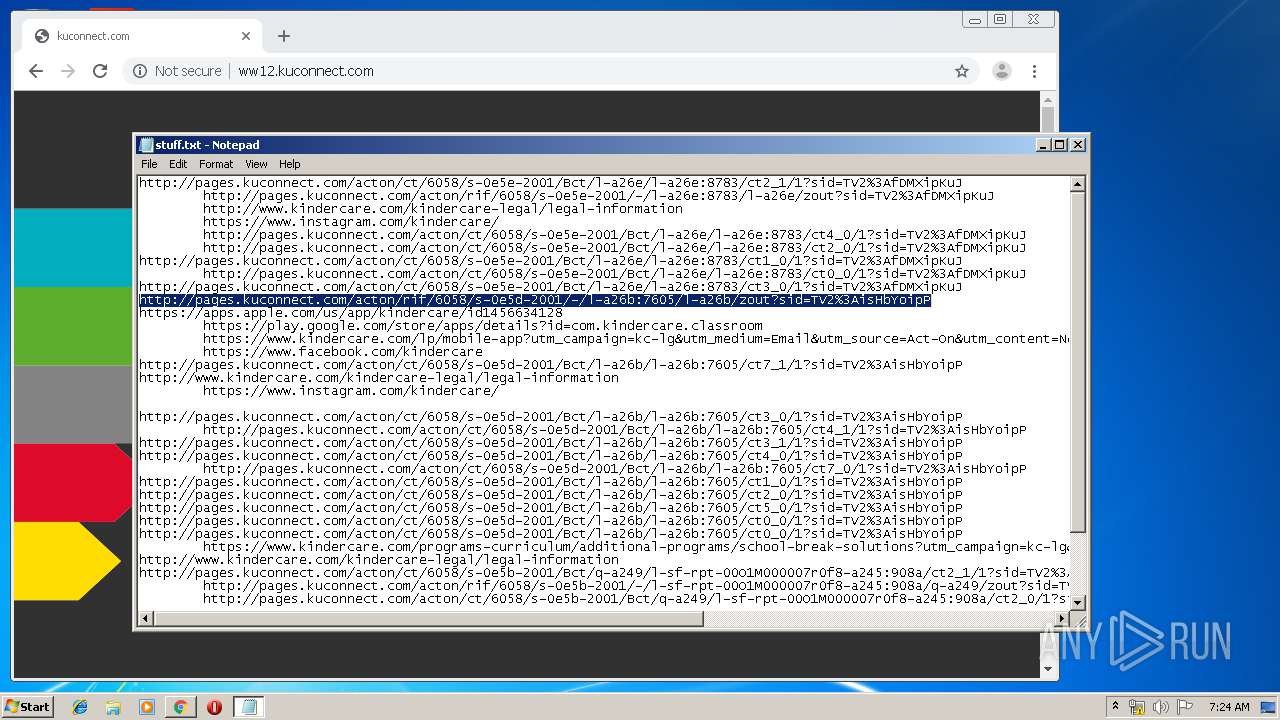
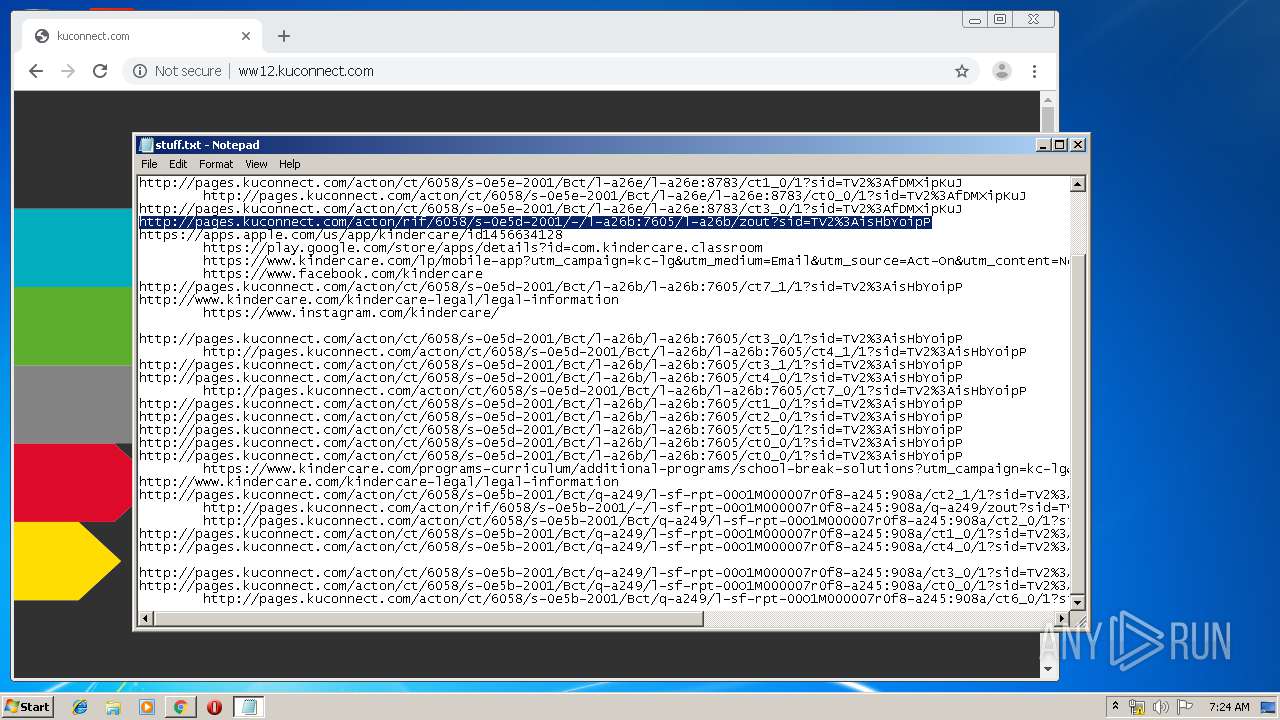
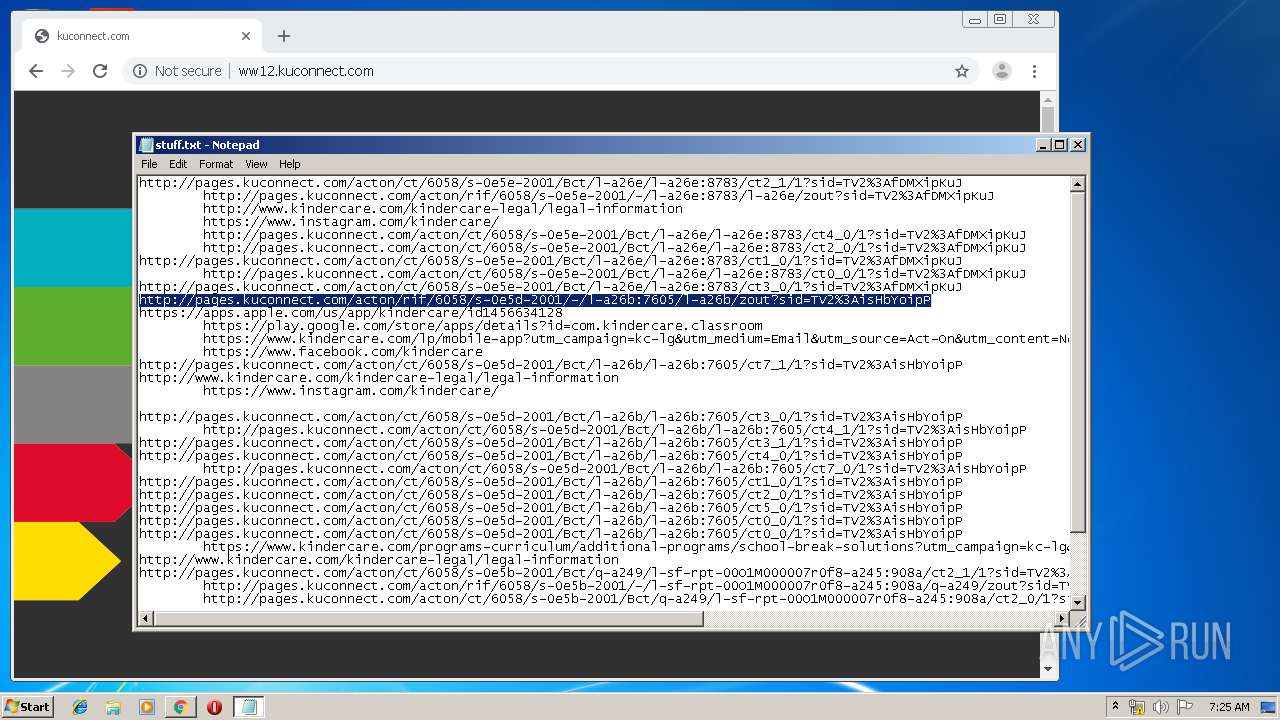
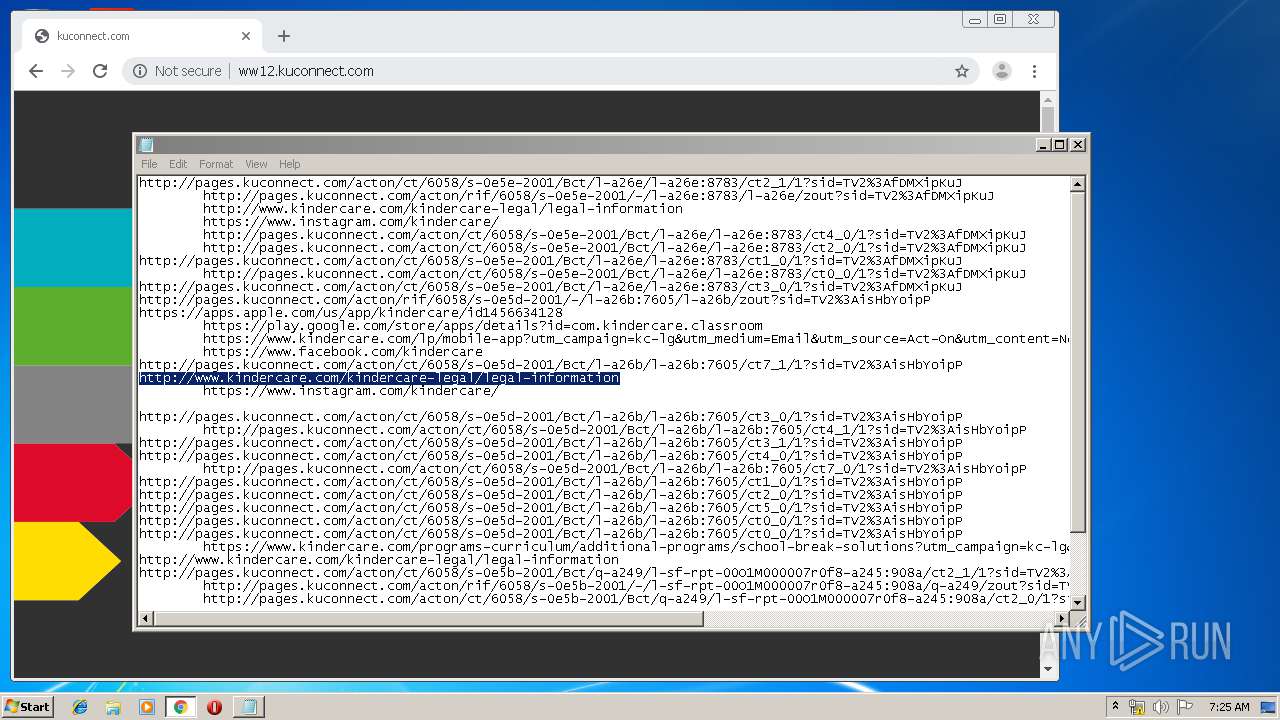
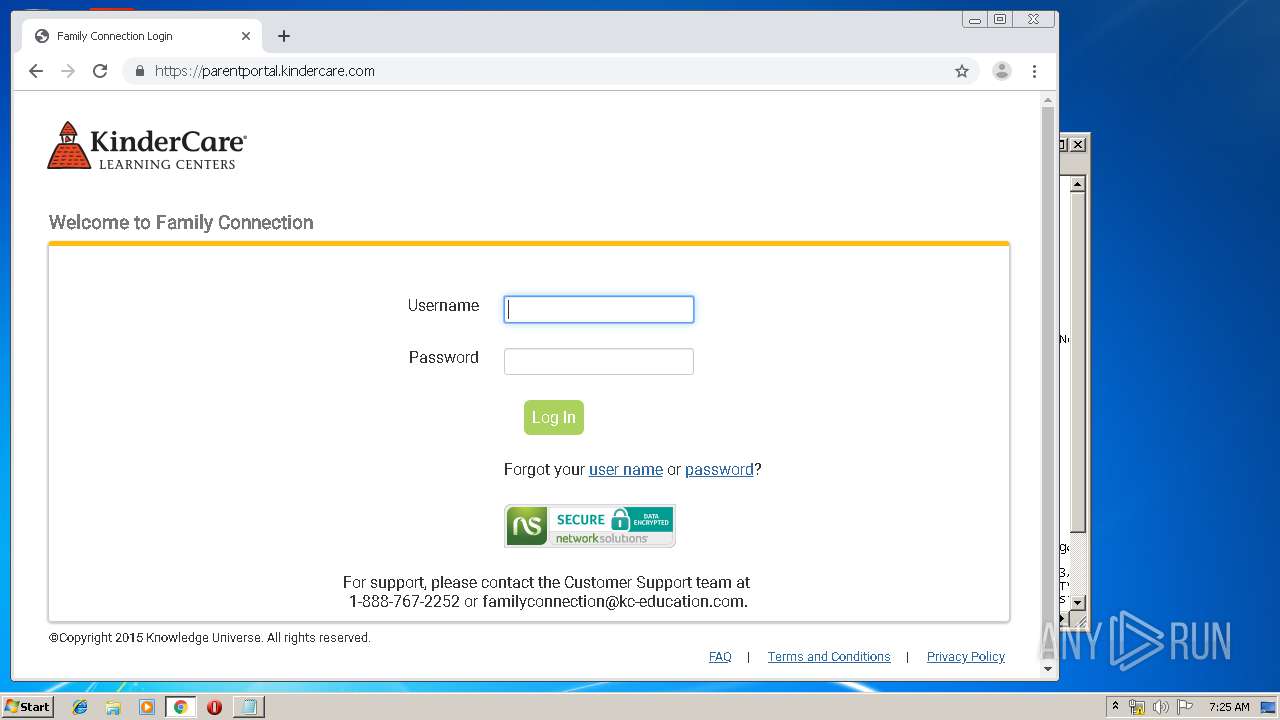
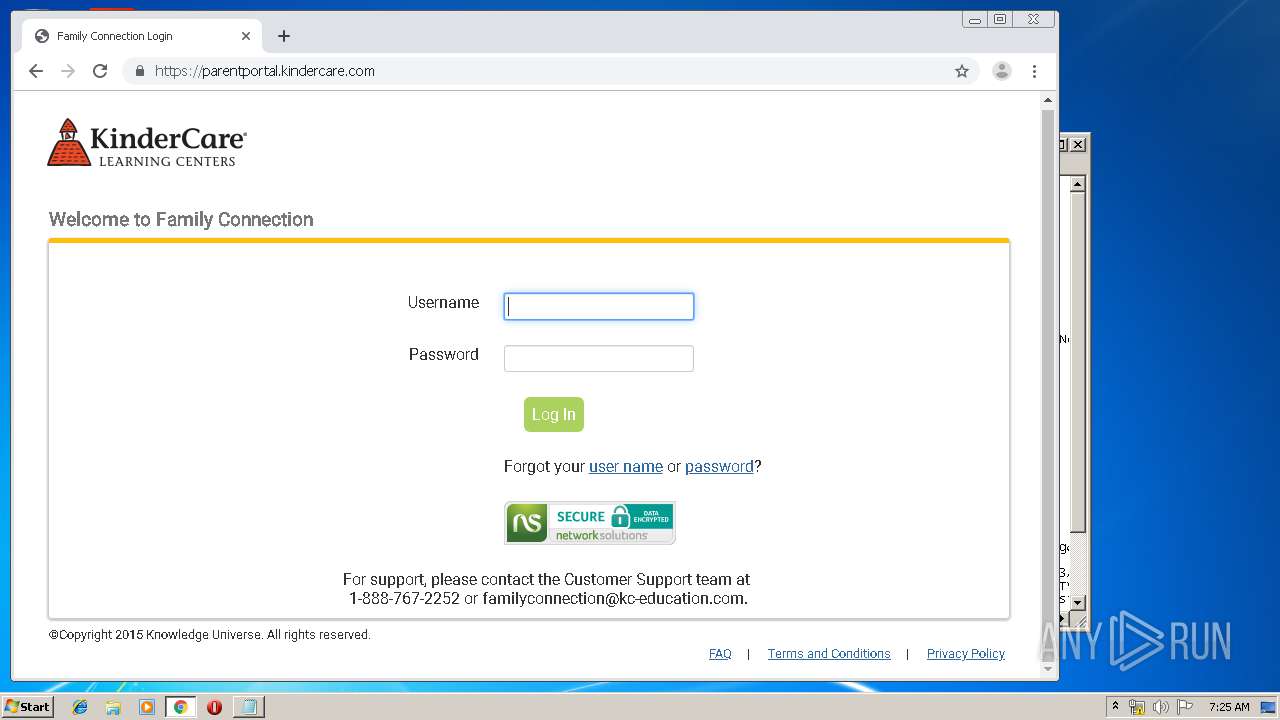
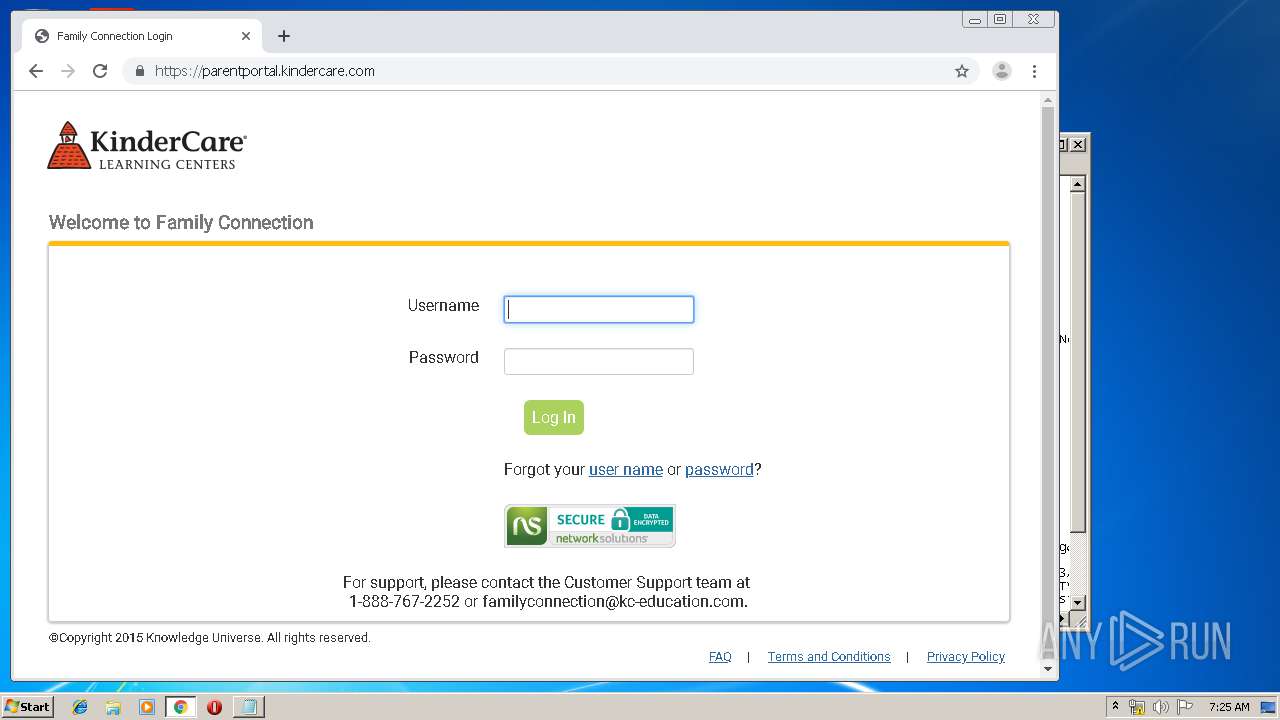
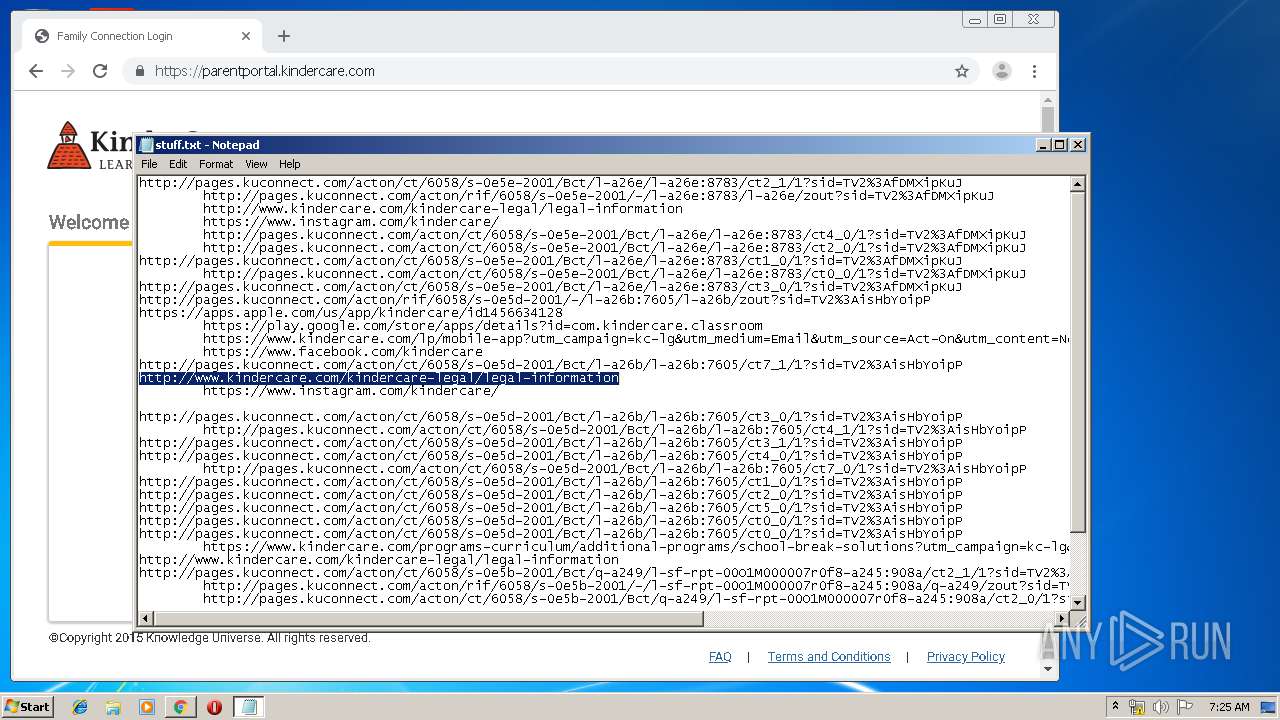
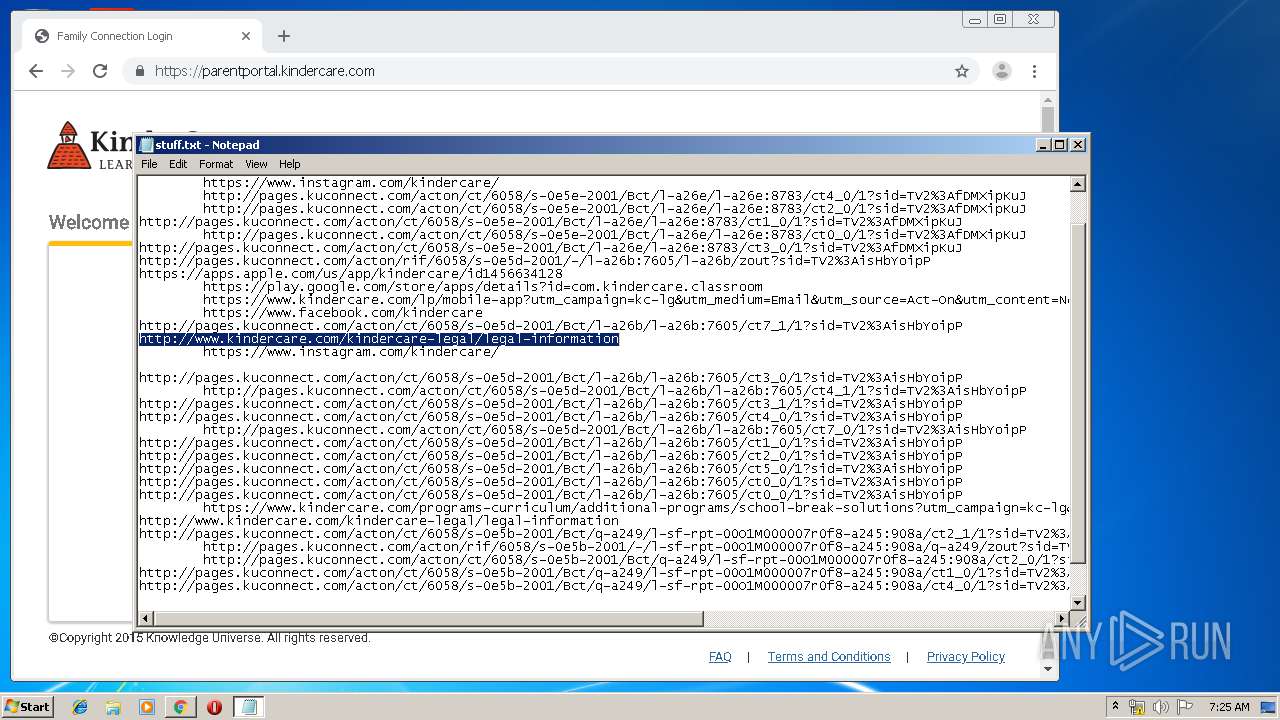
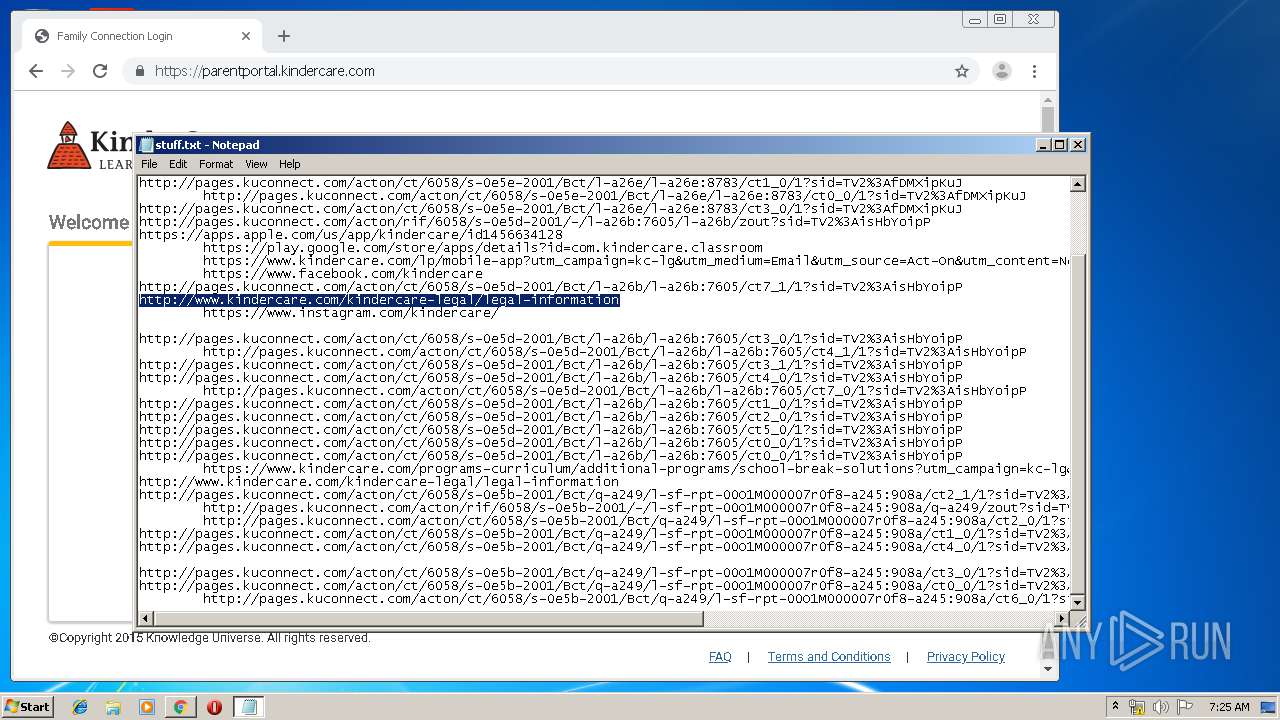
3996 | chrome.exe | GET | 302 | 173.192.101.24:80 | http://mybestdc.com/aS/feedclick?s=N96qfziHQqRPFVwrpy7R5o8uDhK_8R6jze4SmlLkhm7xT1UQD1EwaKd73pnnDH6ohvzYfNFjJsIjeRAqbTvnp4aRgNuSja75XKULcSfTHPHfMVVyoveMVaYZ_8dAZcE4MLekFlfWsTpfBjRhq2gpKO8YEbI33byes71Z00Ywn6Urbadr0aQ53UinNVzPyLx7G2aEpxtD7aYrgIuNp789bf-aH9B3ZM73lf2CWVGytz16A1ZNZvwTAtf9F7Pz7GofpOkpm4j2uG-R44oN4X1JToSxZ54j7UDNGtEVM8cV7OYpa0U5lGVgZR5HqPwWe08DP8UkQR66dt0e0B9LOdHePuPehJDf5BIfvp4djdlDg0eW-VZ_pXDyi-NPVnjODzX6403Pkk80KkK9pYRKPAVmOR3Rvb5kU5ZsqxJLeE7o5CxqZ7le-43AeFzIsilN3PfRPnbARd855B9wK5HmmiESsMfX6bXqwVNjYd5oZnKu28Dp-8LKWTKYKN5MUPVpaLBf07ECnXIVDRtJuMMlwVSqLPxNb4LC-m--G0zu29_at7tv7dAL2T25T9UKwPrh4f28zNV-l770pH9LD0xSamZP7rvx3TZt8RNhq6_9pN_alSie6u26FF3La3popDJ4sLosq3Ww6bzhVHYLY13yOyNeD-2twQBBeAPTfsHtMvh4k_heZRPAZ38BbXiH4Kie-Bun8YI2FSaYBgpPCrWetEqq8y8SCvtLPsvYupKEzoDroSRN70LQzFxCErAHjHMD0d0hElOkl7LAxghZNPc9ehNDumbWa0ZTtQLZ2AVTTD6iT9npYs_RmKg9TqwiwIqMCRn8YBNT12FqRUbab_i7F6ZWAblttQSVeyAC8Wx9SSZlwoLM_HQqEcb58qgejVIrehRGC0Wy4qwZ9KUUarbi3qQuL4R5soFxzwXkEa1yU6JbLZ_xRc6ig3LGebrPcZx6y6zaOBp_fyi6S7dHQJpsyxV7m4MRXfqc9uZLa4fRBFckWAPJmtu8aic405KxGFdFdS3aaKcnnOVCa1gtVodyh16Nu-Zngk2rC-1_E2NNxA6ib-IVMIyQQKPBQEVP-nMKsyLvJ7nhN2RSjXDjAvWJmicMsAh74GTtwqAy1StMGW5Glm6eUdaZf__tAEUEtTqDoFJK4xMbufMPWd9LmoKZY5qa5GGfr56Ta3M8HEpKkeeaSdAMUv3Yhv9S80PB5b-Xk-CPy_3JzxUFIf9ccqWrR1Q1KQPdpPUEZZPCFZj8FSjkG8o5prqm4HneACU7ugF2M-yuRQS1OoOgUkovLWgEFQMpxd0Azp-j8QGh | US | — | — | malicious |
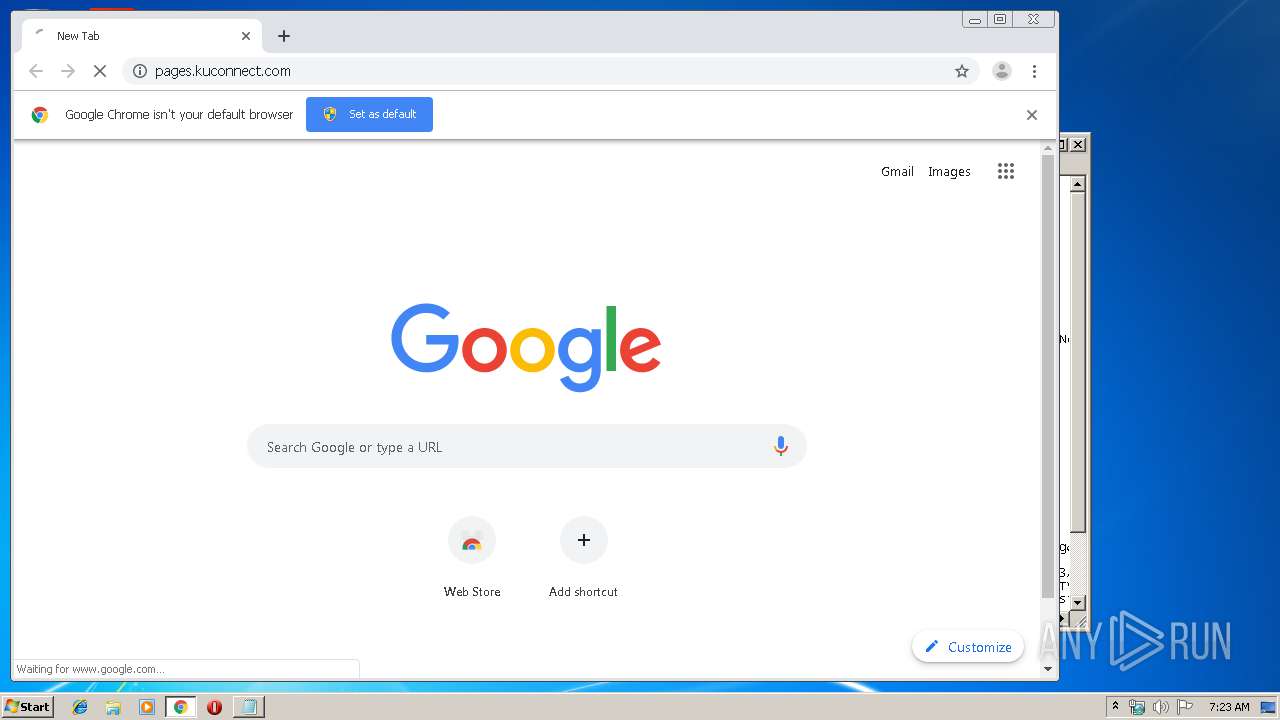
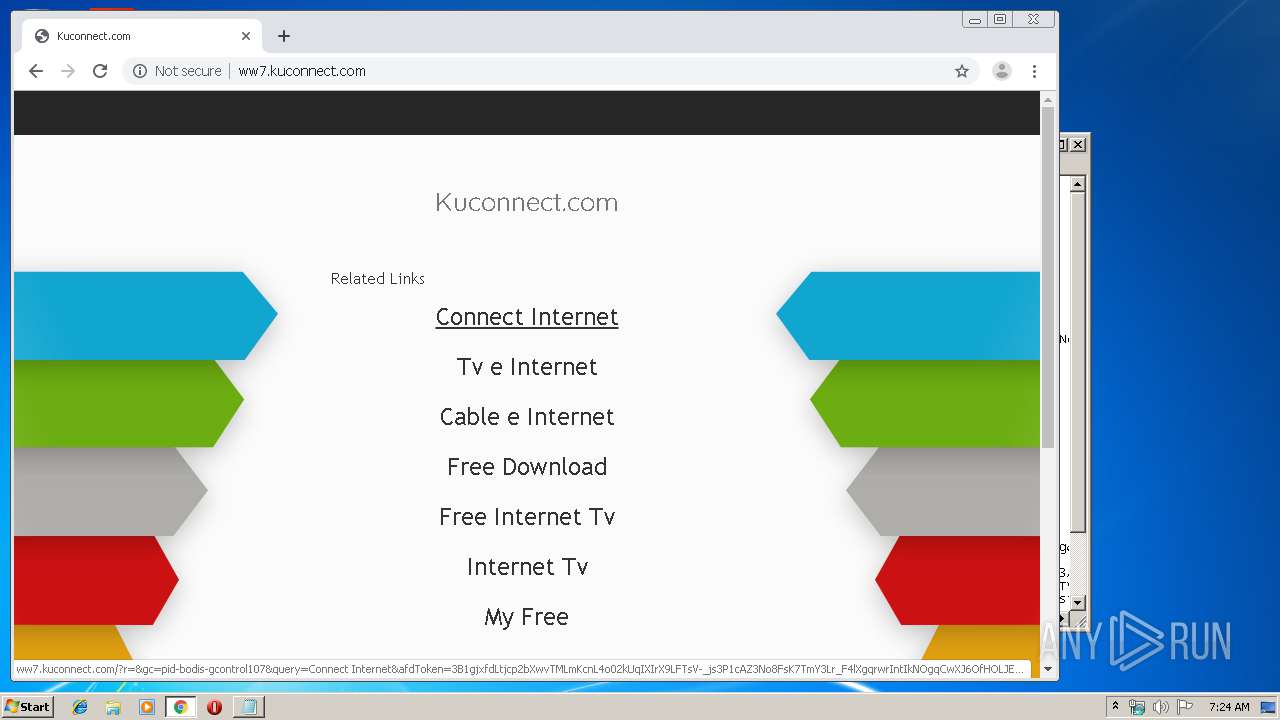
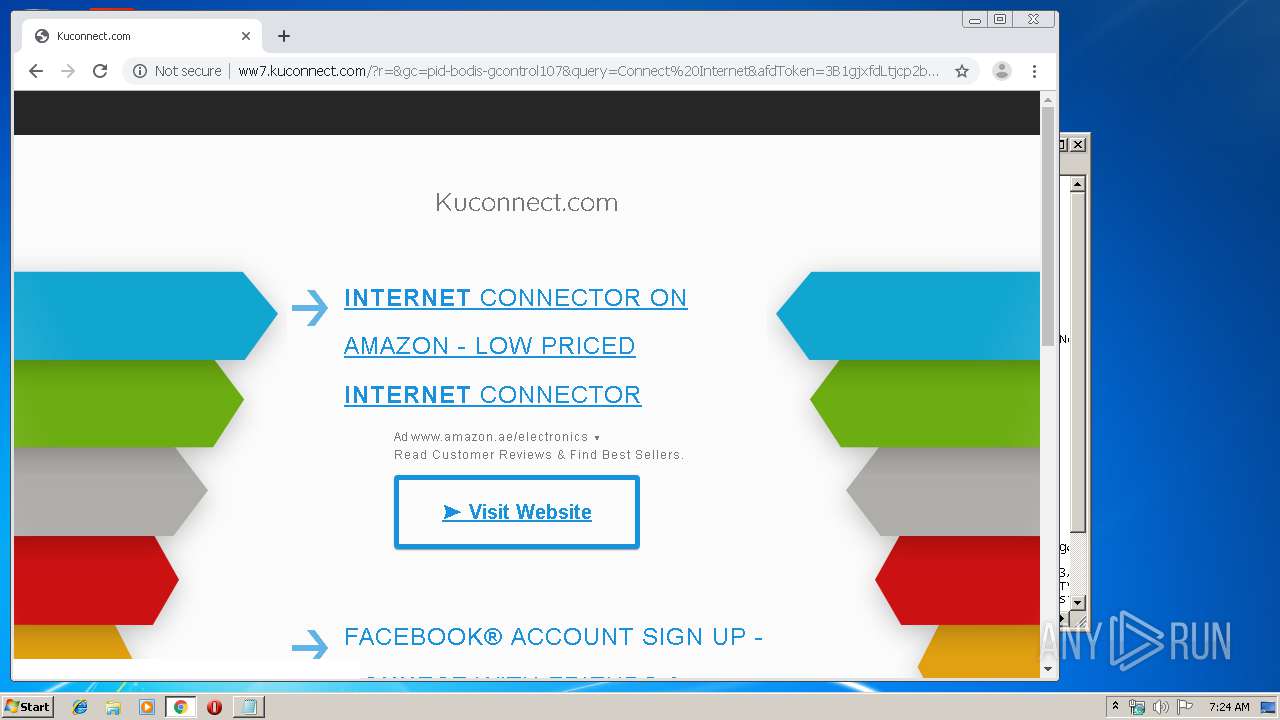
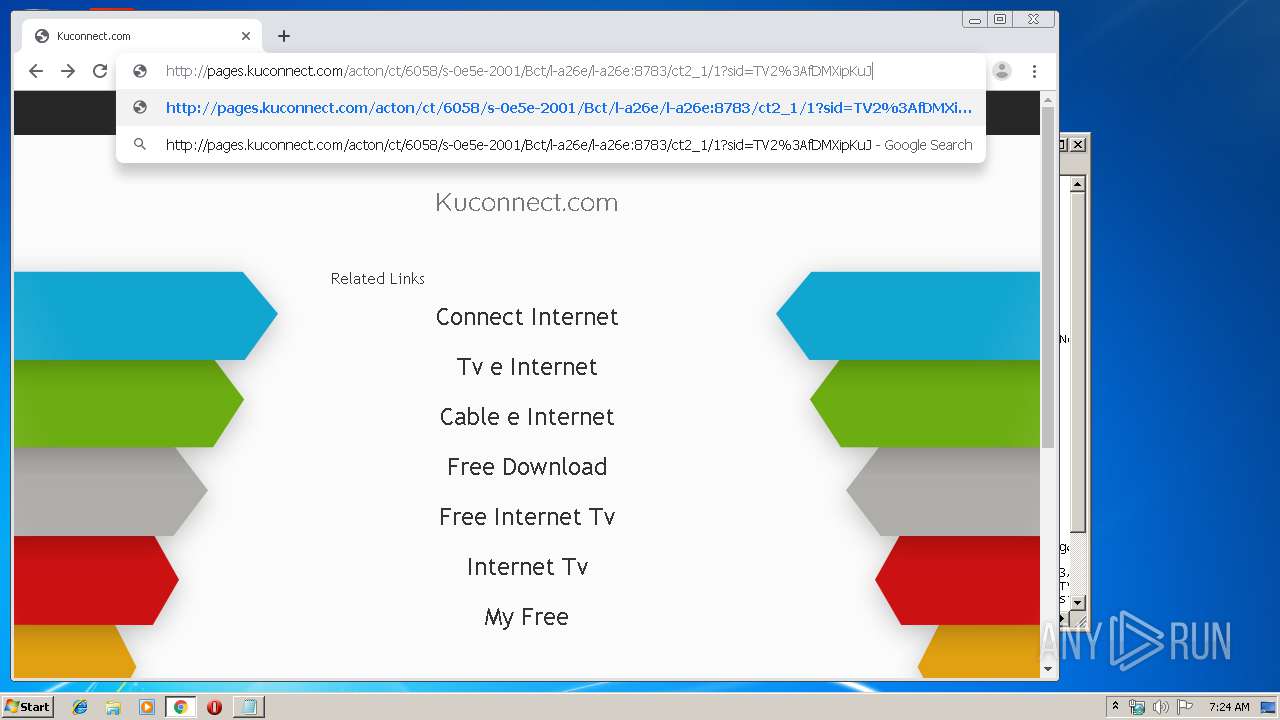
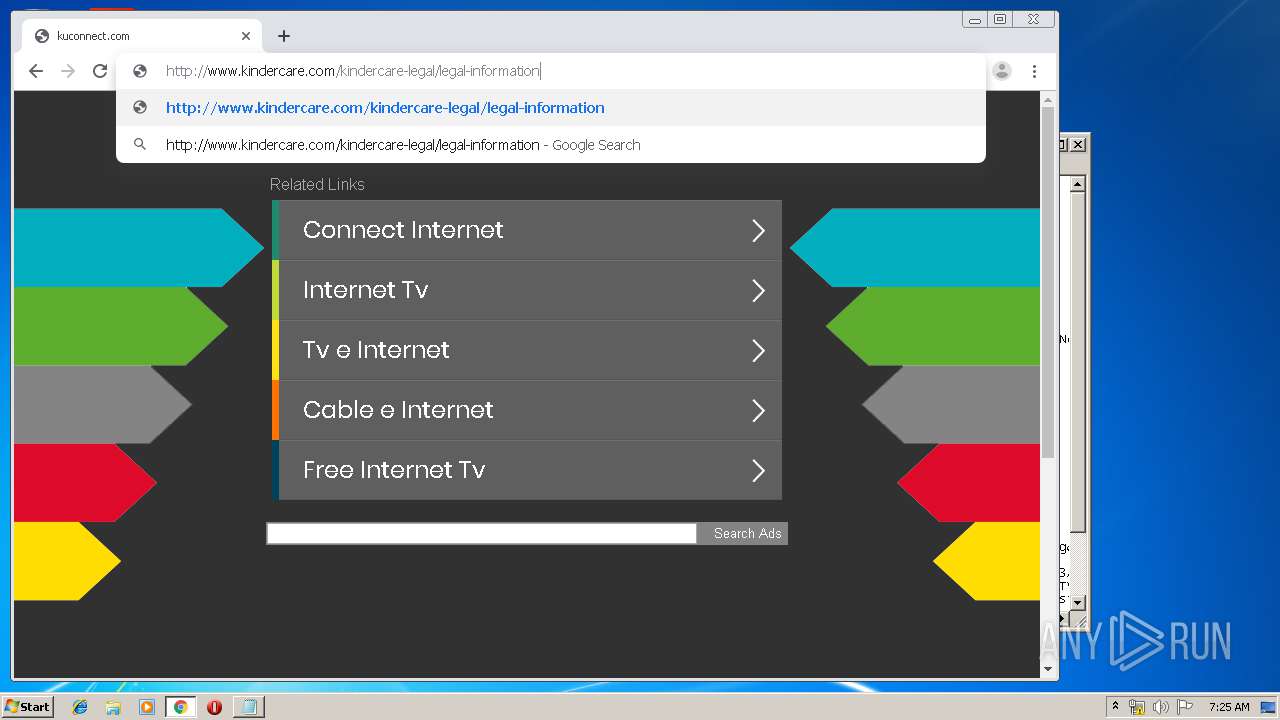
3996 | chrome.exe | GET | 302 | 67.227.226.240:80 | http://pages.kuconnect.com/ | US | — | — | malicious |
3996 | chrome.exe | GET | 302 | 67.227.226.240:80 | http://pages.kuconnect.com/ | US | — | — | malicious |
3996 | chrome.exe | GET | — | 173.192.101.24:80 | http://p237996.mybestdc.com/adServe/domainClick?ai=uNFFHf1DSFSZ08SWj33c7bjBMgkymnUx0c_M6QdfEyAEErEUEwoaPcEDnCBYivND3pJiuiuNbvMTXnLPvbyStX_9b8ky2I1bKC7gQCEt6FVlqf_64l0Z6hpyy_YN0YQtpLSZmparWHVFBLU6g6BSSq5Lc08J4FUW-vie8-wq9A05jDCok9YMrD-tqHlp-Y0RA9gEmFYoAzsO9LAo7hxx0ScxaekEKN86s5RfBFYGRKG4rBycDnJiDiZggkaL9NJRZN_F-zUlvRWh8HfcFb6b2kMb4Do7y-b-De0rL-F5kinpl0elefIU4TScjdjF1tJCaygrY9BHdw_UdqdcHeTAytQNy0EHlsrgDOnEXZ7OoQmak10cL-x5mtWjri88Beg6ZonWe_Vtl9FOwVpObpfchy-mlknkRKkR&ui=N96qfziHQqRPFVwrpy7R5vbWwvziNp_1eX1o6BG7hvQZH0IOqDTMj2aOFyezddhT9LFw_mLaxAI9fM72lZ5udTD5ZGKZmNIkEQhWRea_7YfpBENEQFp17Q&si=1&oref=7406cde7363a83ad6958a860df385d9f&rb=wWV2xNX6L_c&rr=0&isco=t | US | — | — | suspicious |
3996 | chrome.exe | GET | 200 | 199.59.242.155:80 | http://tracking.bodis.com/tlpv?d=eyJkb21haW5fbmFtZSI6Imt1Y29ubmVjdC5jb20iLCJzZXJ2ZXIiOjgxLCJ0ZXJtcyI6W10sIlVSTCI6Imh0dHA6XC9cL3d3Ny5rdWNvbm5lY3QuY29tXC8iLCJyZWZlcnJlciI6IiIsImR3IjoxMDQyLCJkaCI6NTM5LCJydyI6MTI4MCwicmgiOjcyMH0&t=1579332238&abp=0 | US | — | — | whitelisted |
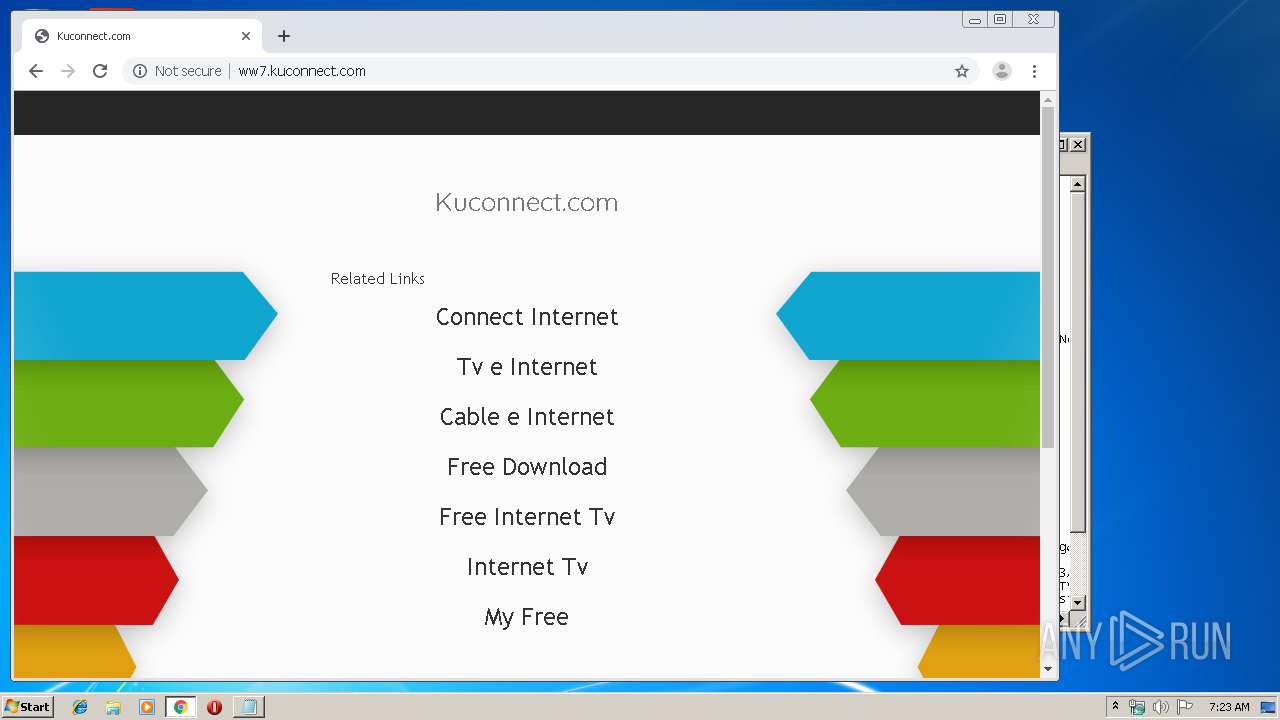
3996 | chrome.exe | GET | 200 | 199.59.242.153:80 | http://ww7.kuconnect.com/glp?r=&u=http%3A%2F%2Fww7.kuconnect.com%2F&rw=1280&rh=720&ww=1042&wh=539 | US | text | 9.60 Kb | malicious |
3996 | chrome.exe | GET | 404 | 199.59.242.153:80 | http://ww7.kuconnect.com/favicon.ico | US | html | 3.93 Kb | malicious |
3996 | chrome.exe | GET | 200 | 199.59.242.153:80 | http://ww7.kuconnect.com/ | US | html | 3.93 Kb | malicious |
3996 | chrome.exe | GET | 200 | 199.59.242.153:80 | http://ww7.kuconnect.com/public/legacy/10351/resources/arrows-bg.jpg | US | image | 93.6 Kb | malicious |
3996 | chrome.exe | GET | 302 | 216.58.210.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 509 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3996 | chrome.exe | 172.217.23.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3996 | chrome.exe | 216.58.210.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
3996 | chrome.exe | 172.217.16.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3996 | chrome.exe | 172.217.16.164:443 | www.google.com | Google Inc. | US | whitelisted |
3996 | chrome.exe | 172.217.23.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3996 | chrome.exe | 216.58.207.46:443 | ogs.google.com | Google Inc. | US | whitelisted |
3996 | chrome.exe | 172.217.18.174:443 | apis.google.com | Google Inc. | US | whitelisted |
3996 | chrome.exe | 67.227.226.240:80 | pages.kuconnect.com | Liquid Web, L.L.C | US | malicious |
3996 | chrome.exe | 173.192.101.24:80 | mybestdc.com | SoftLayer Technologies Inc. | US | suspicious |
3996 | chrome.exe | 216.58.205.227:443 | www.google.ae | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.google.com |
| malicious |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
pages.kuconnect.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3996 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Drive-by Evil Redirector |
3996 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Drive-by Evil Redirector |
3996 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Drive-by Evil Redirector |
3996 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Parkingcrew Monetize Tracker Checkin |