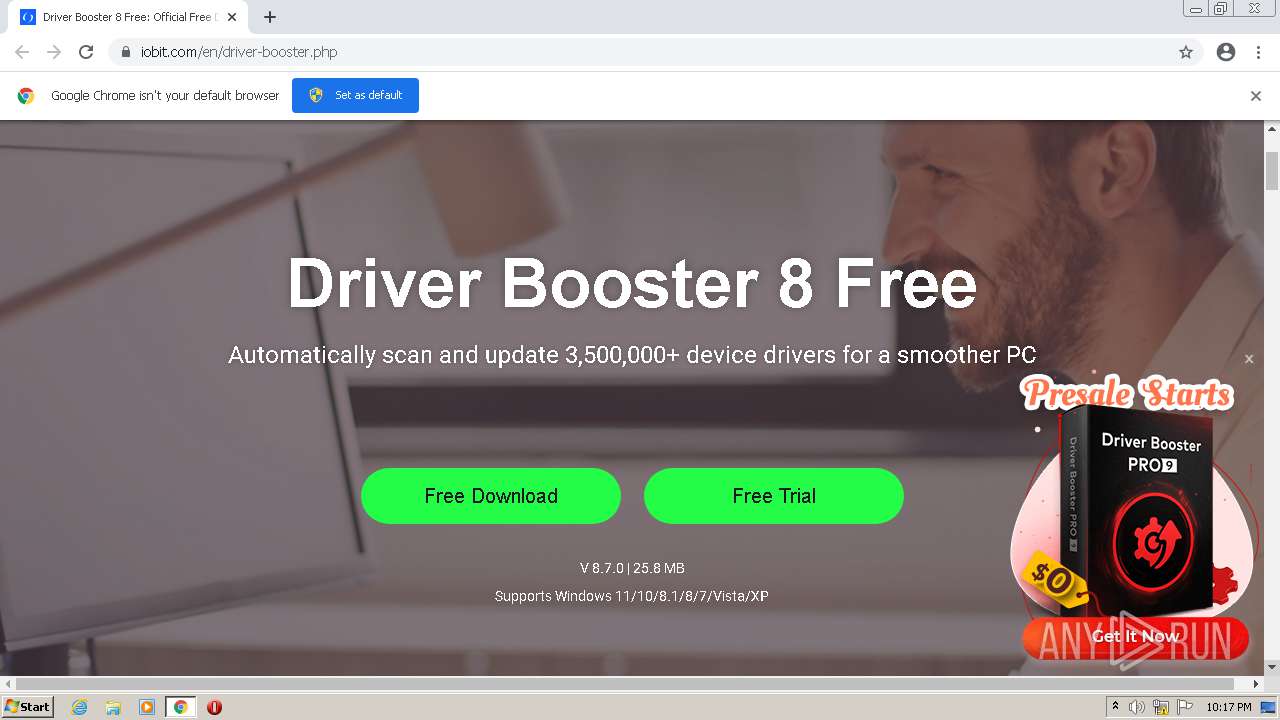
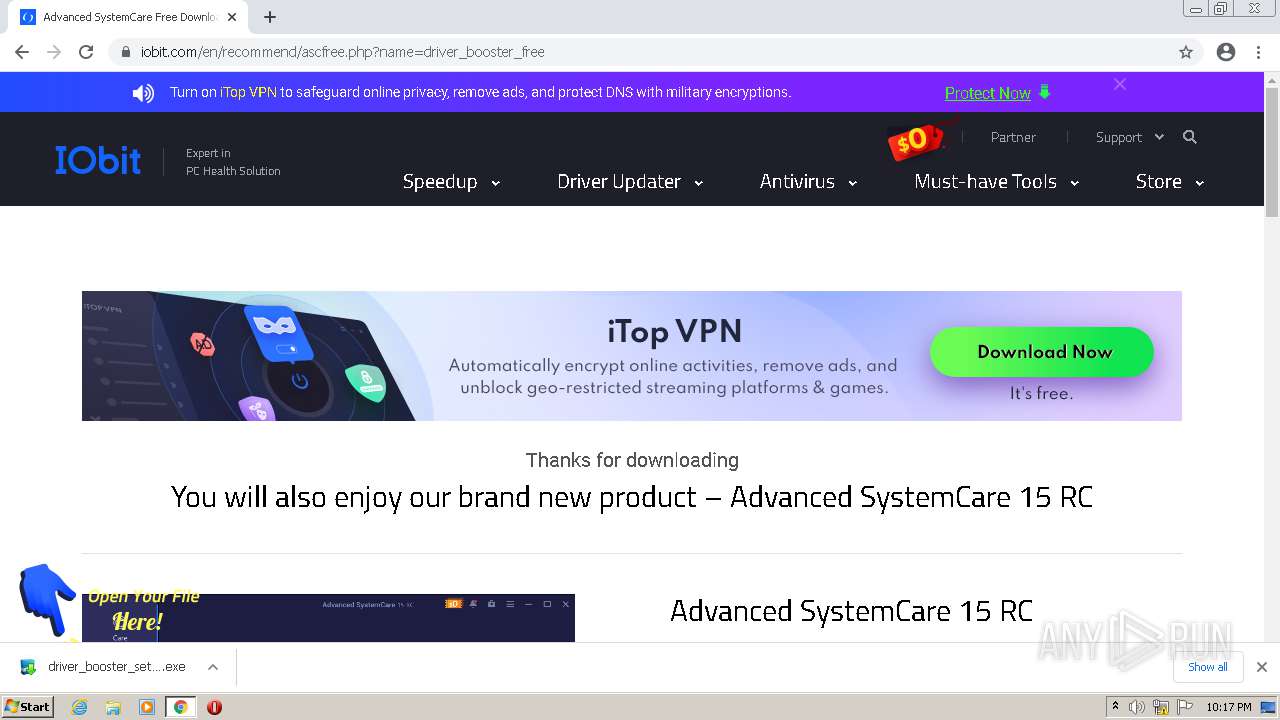
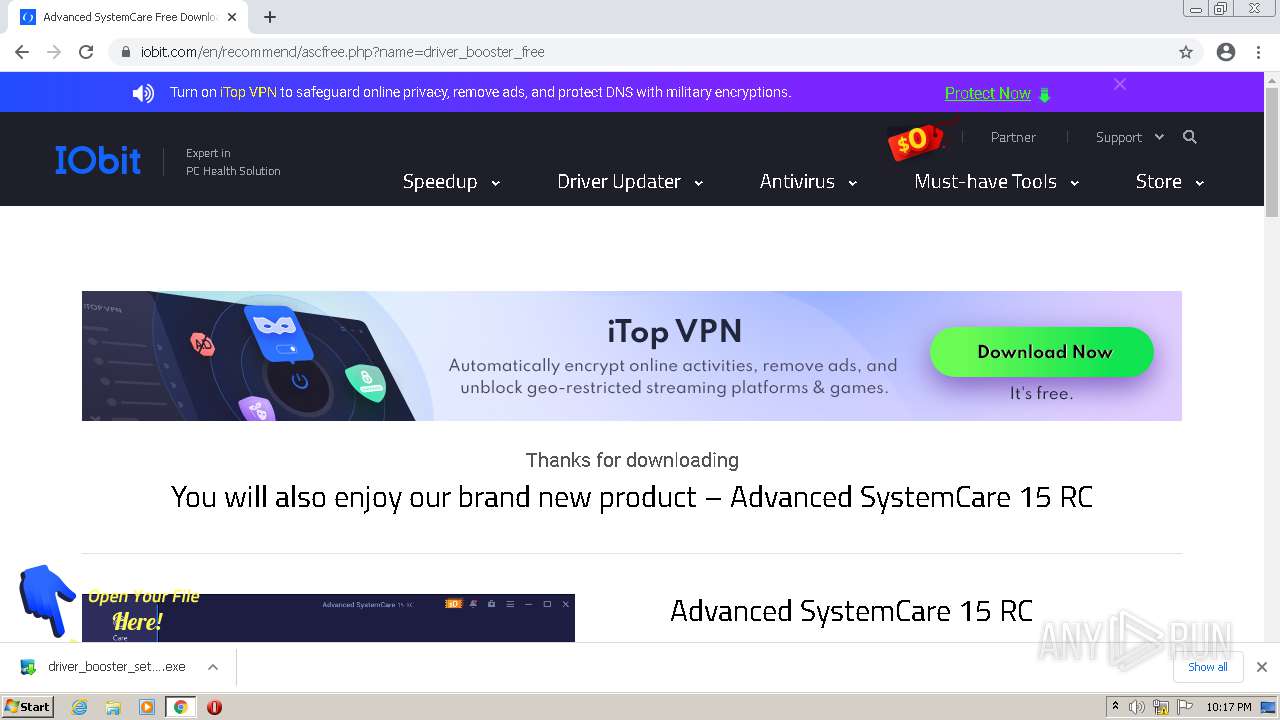
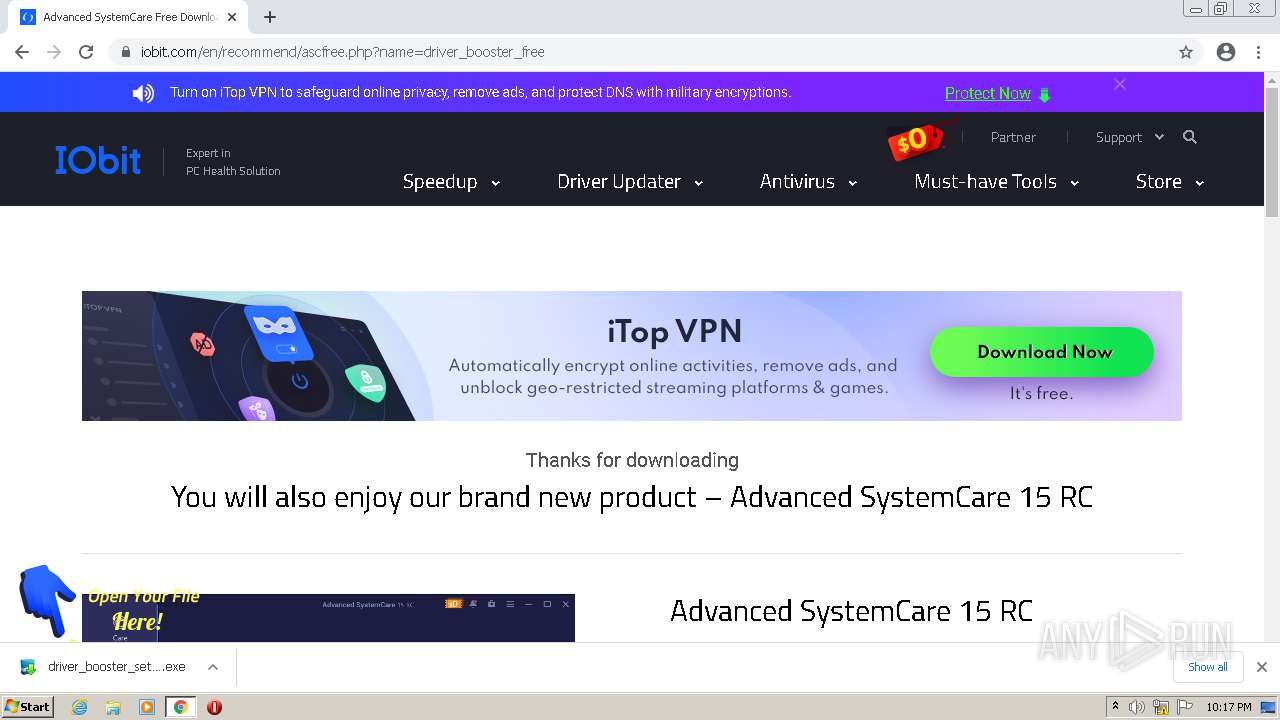
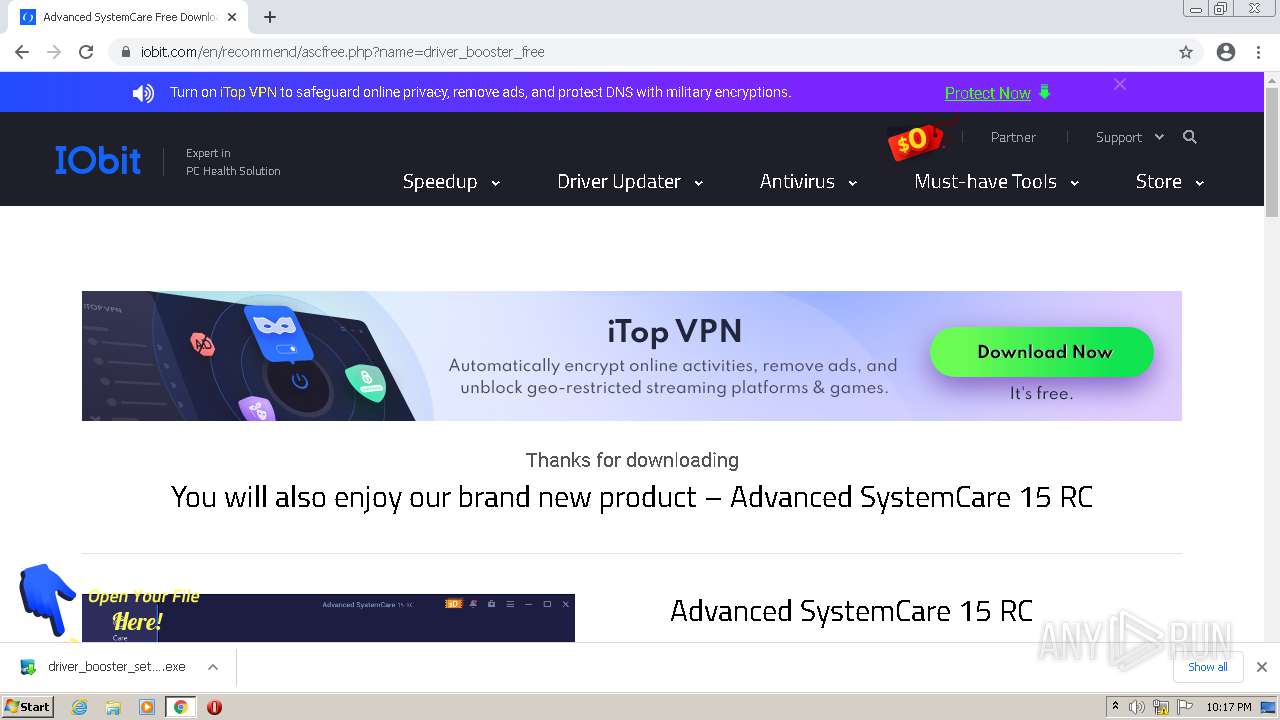
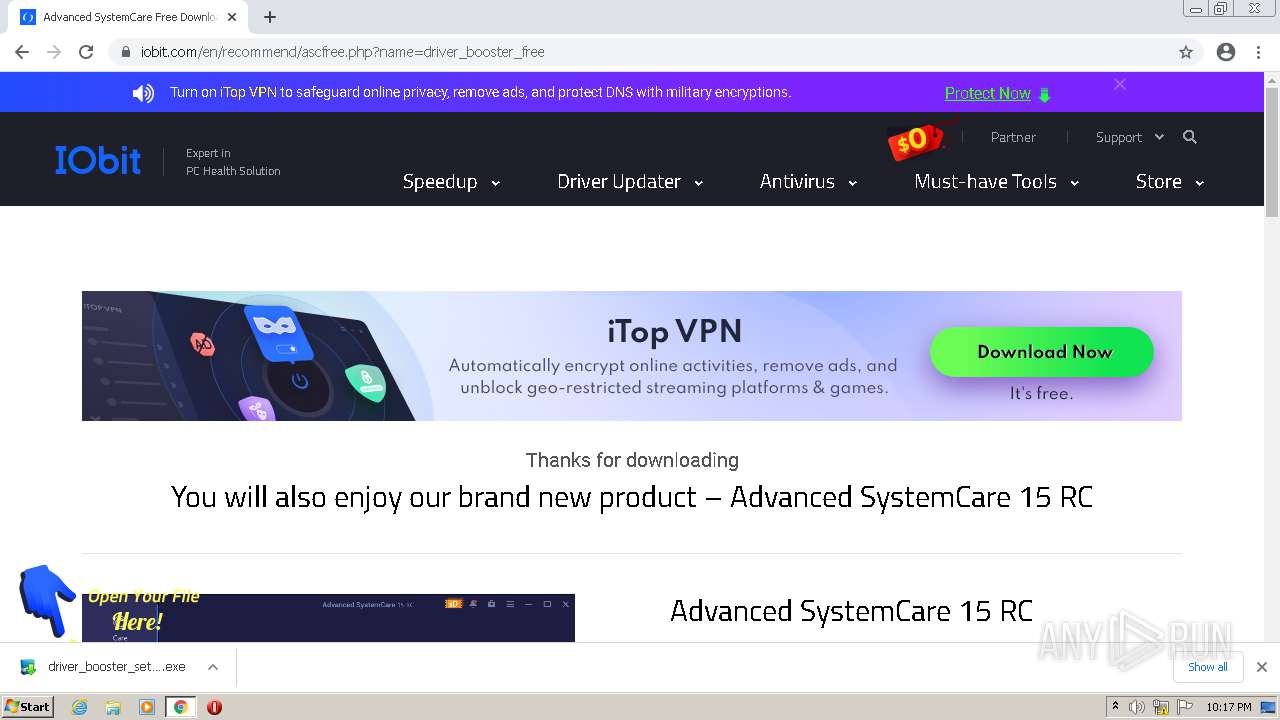
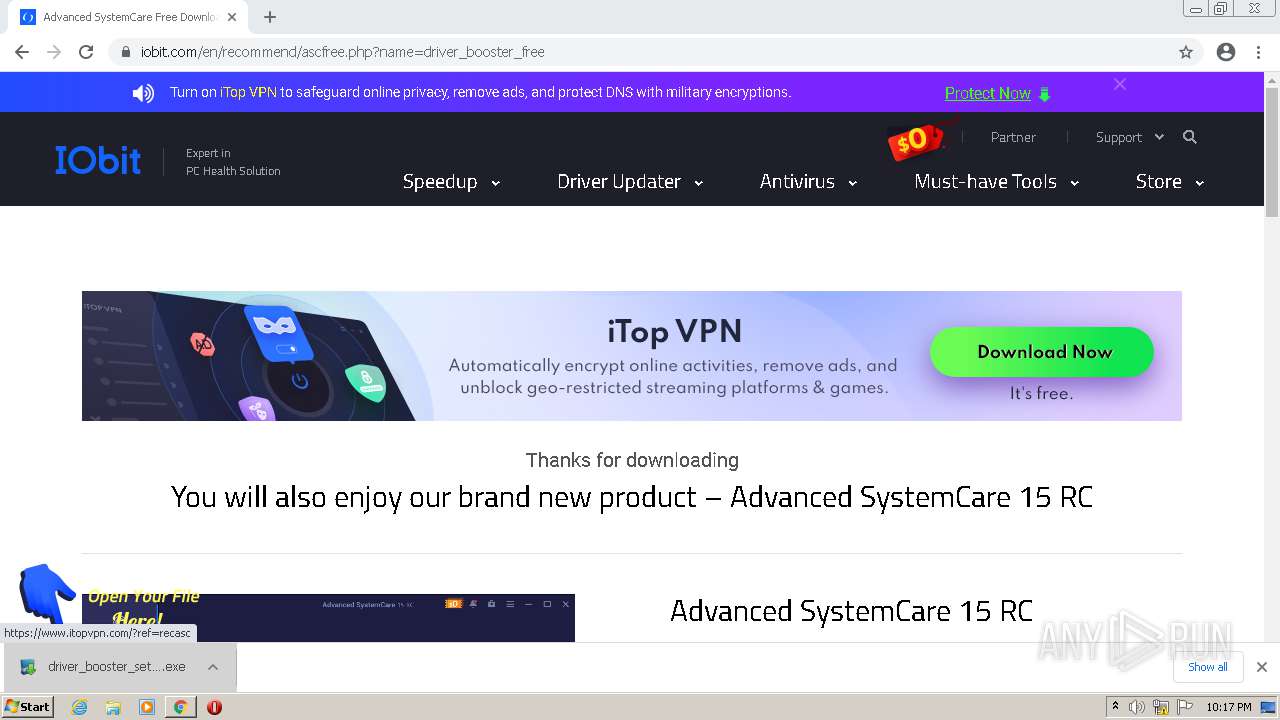
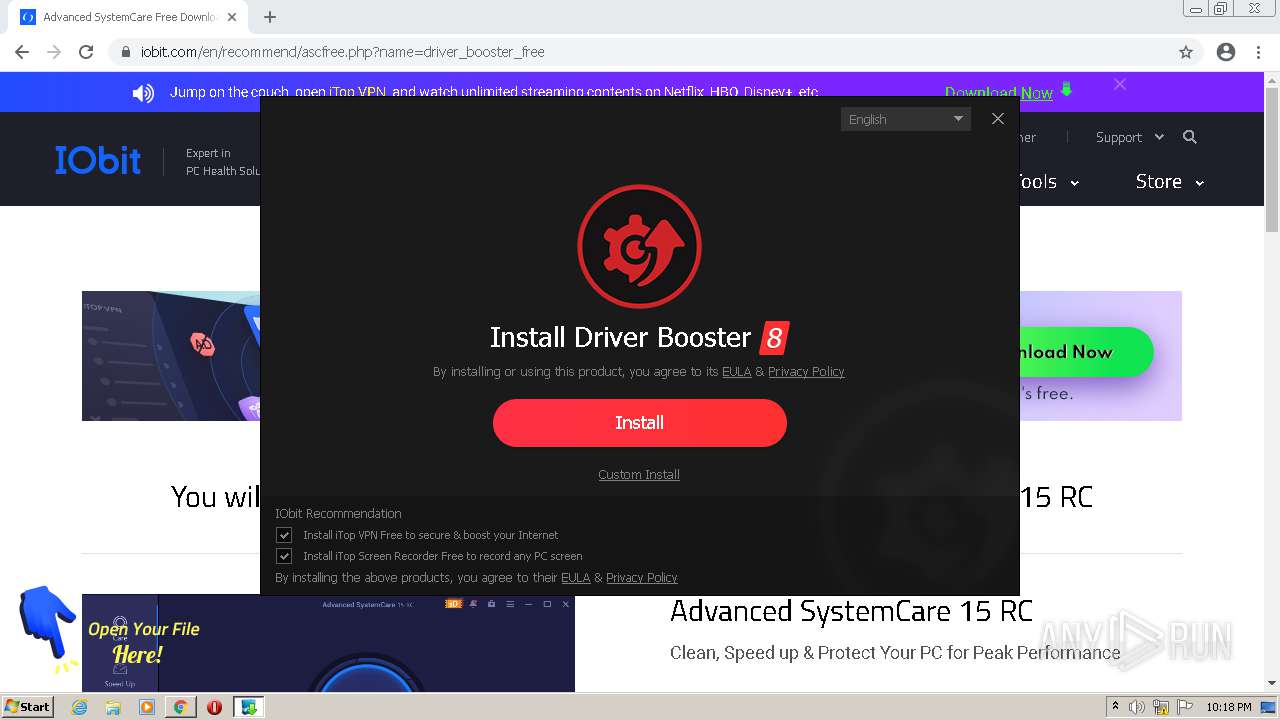
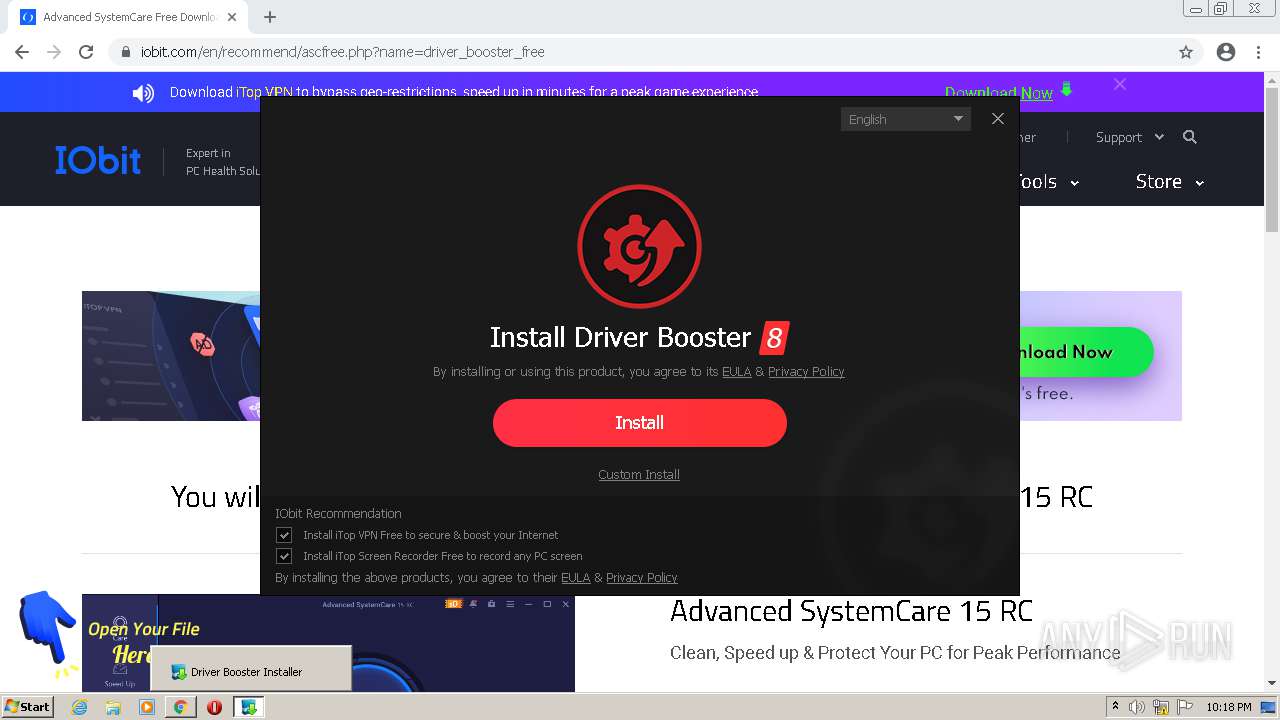
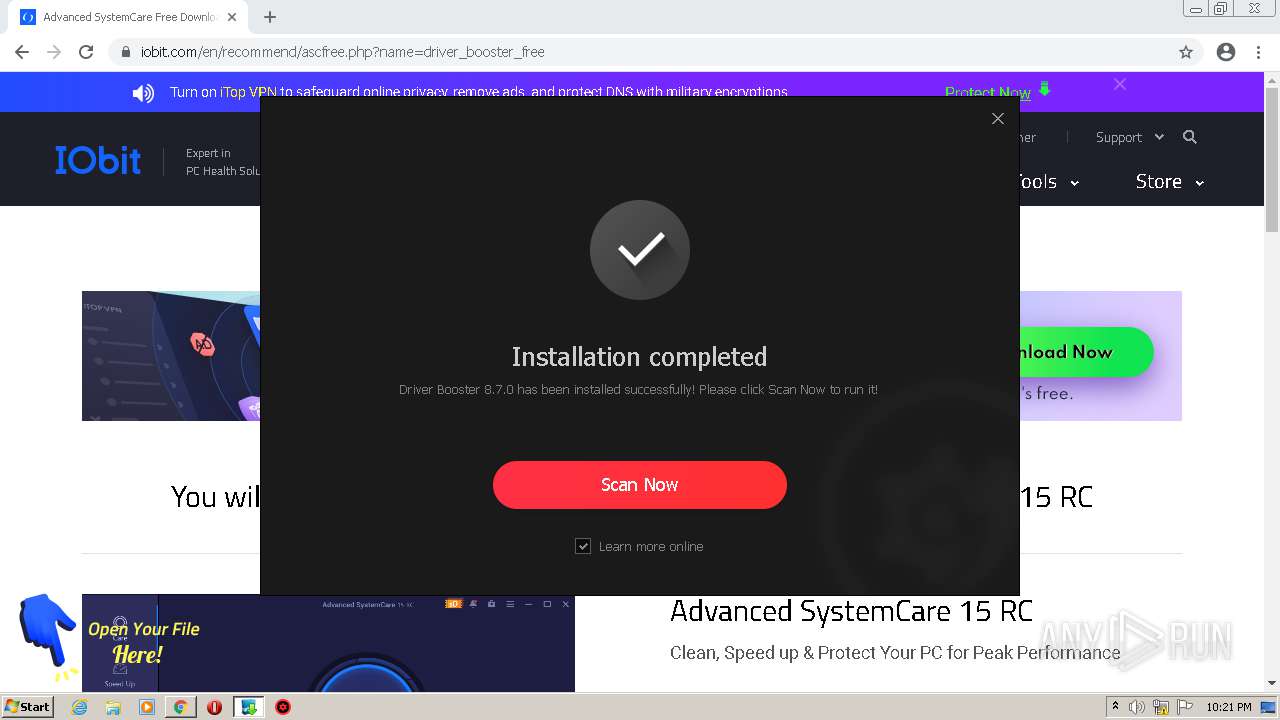
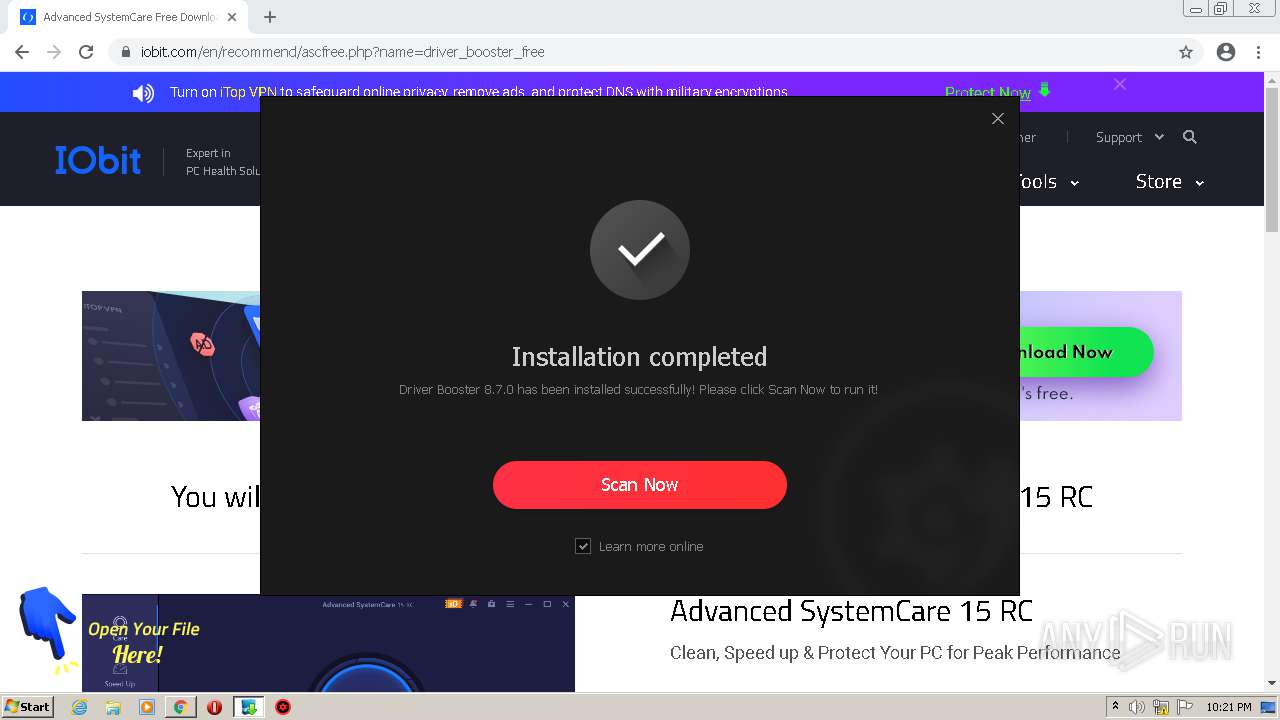
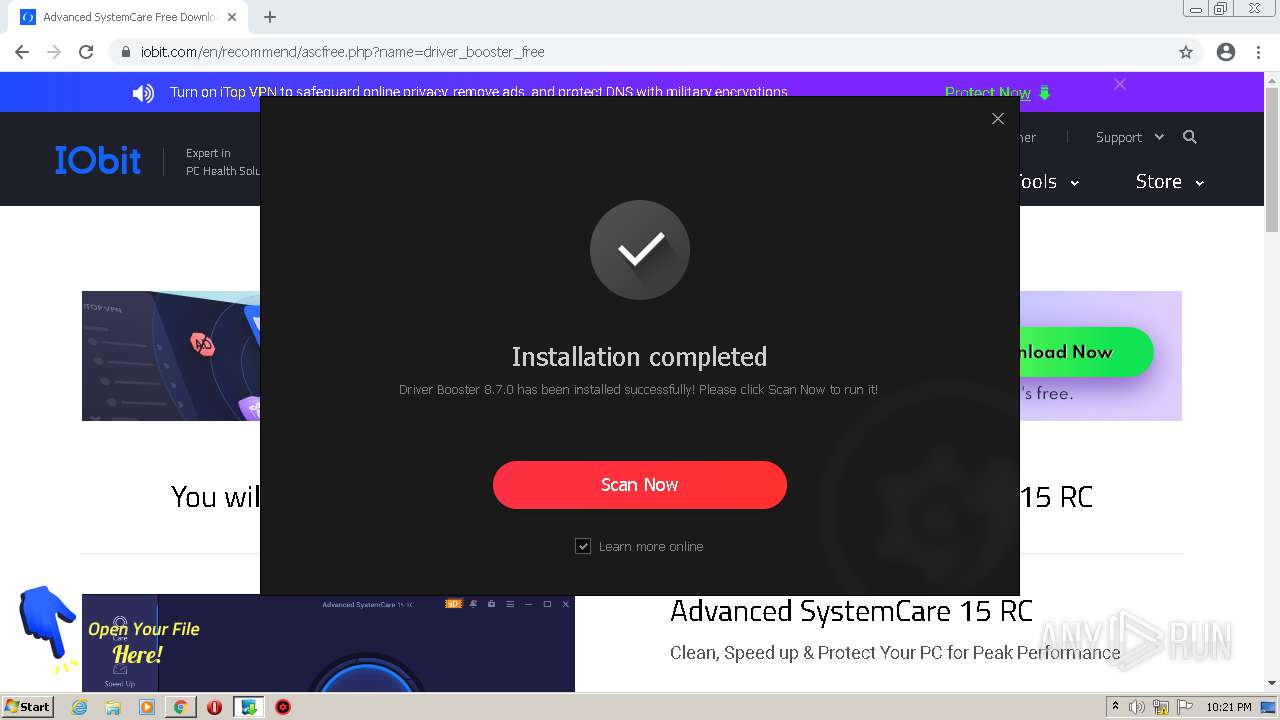
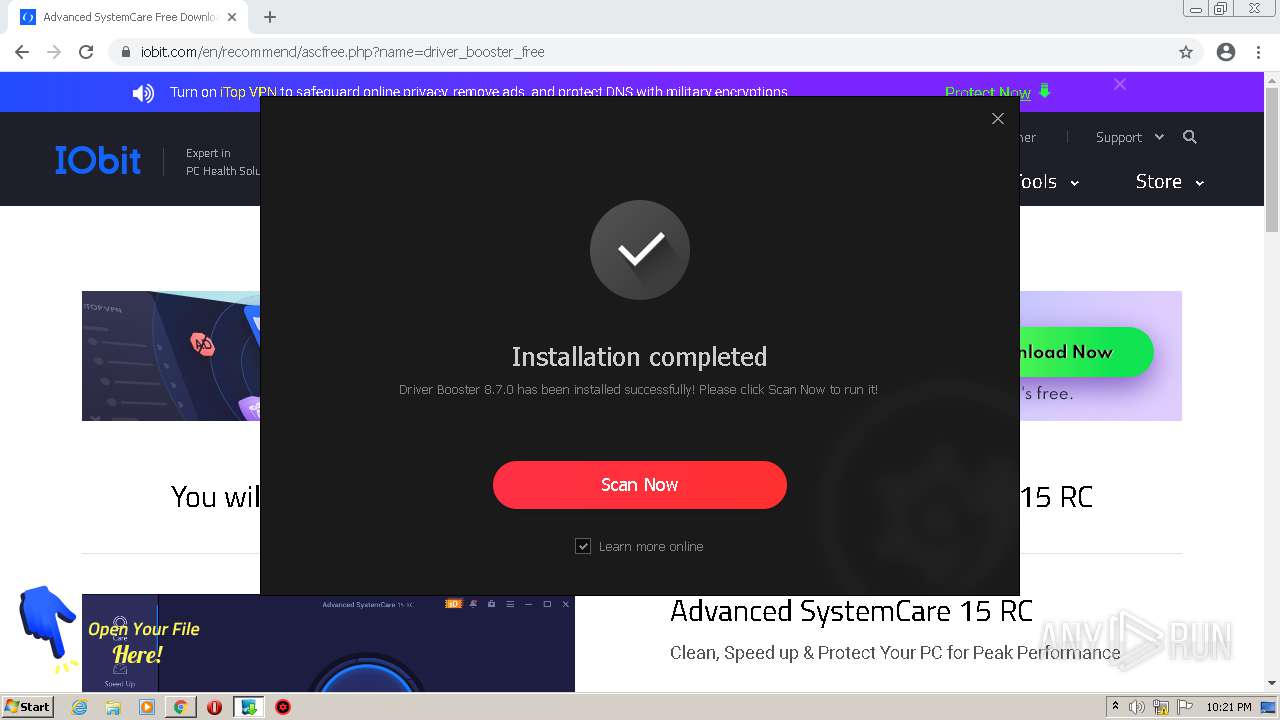
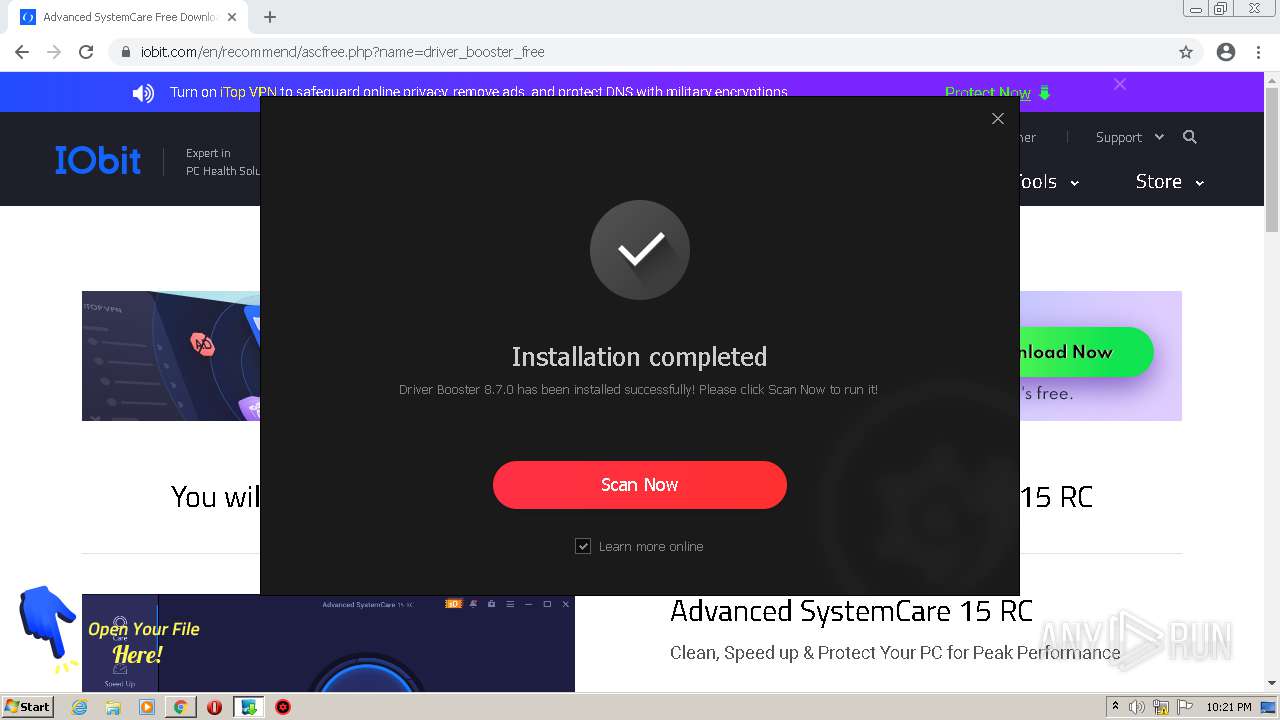
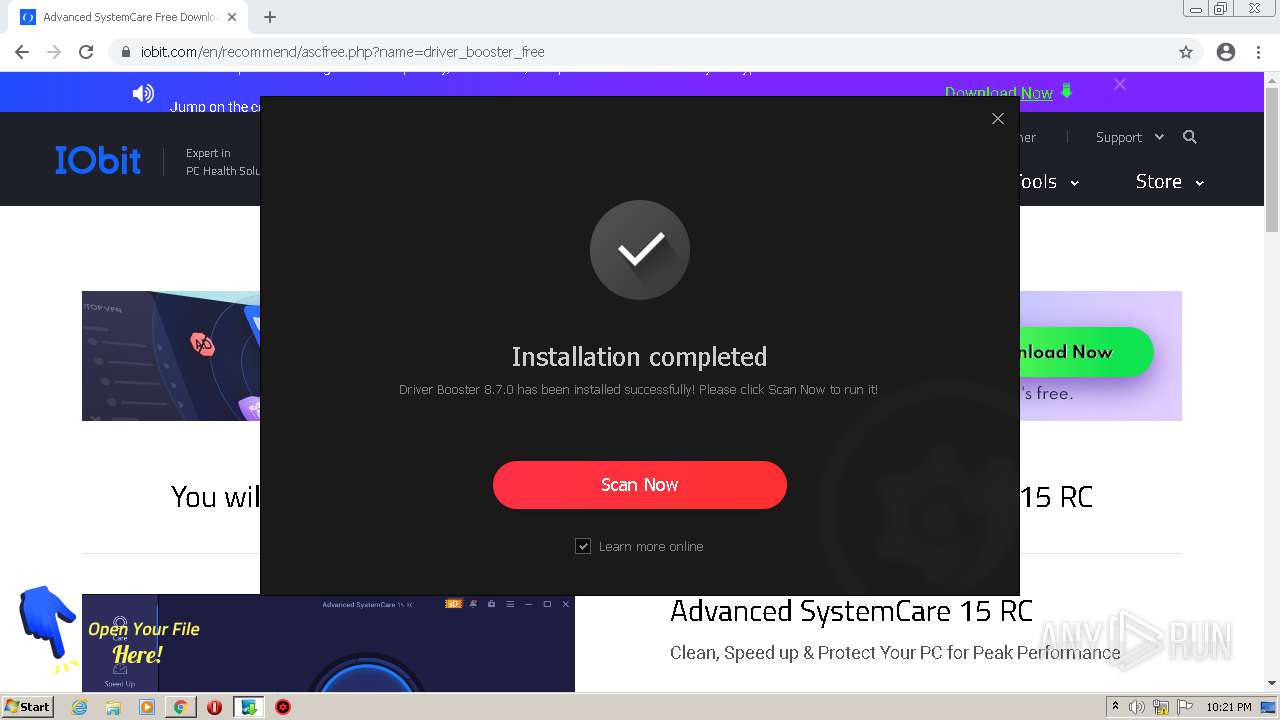
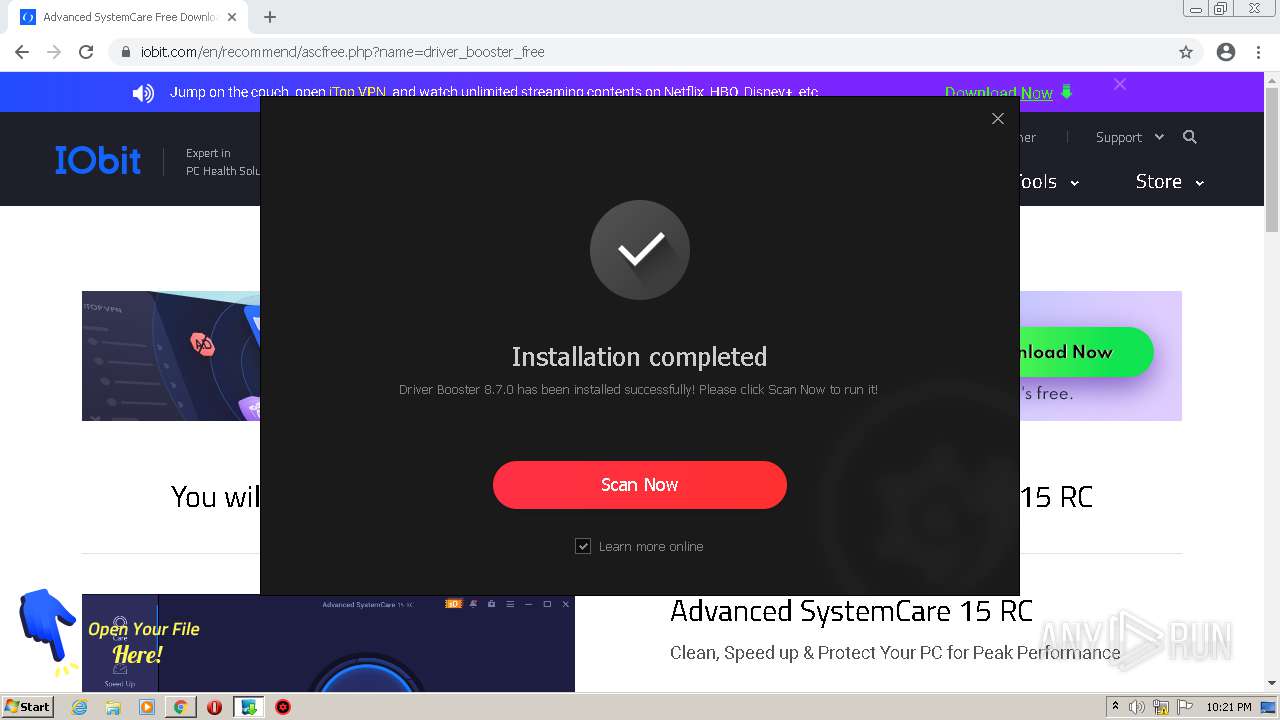
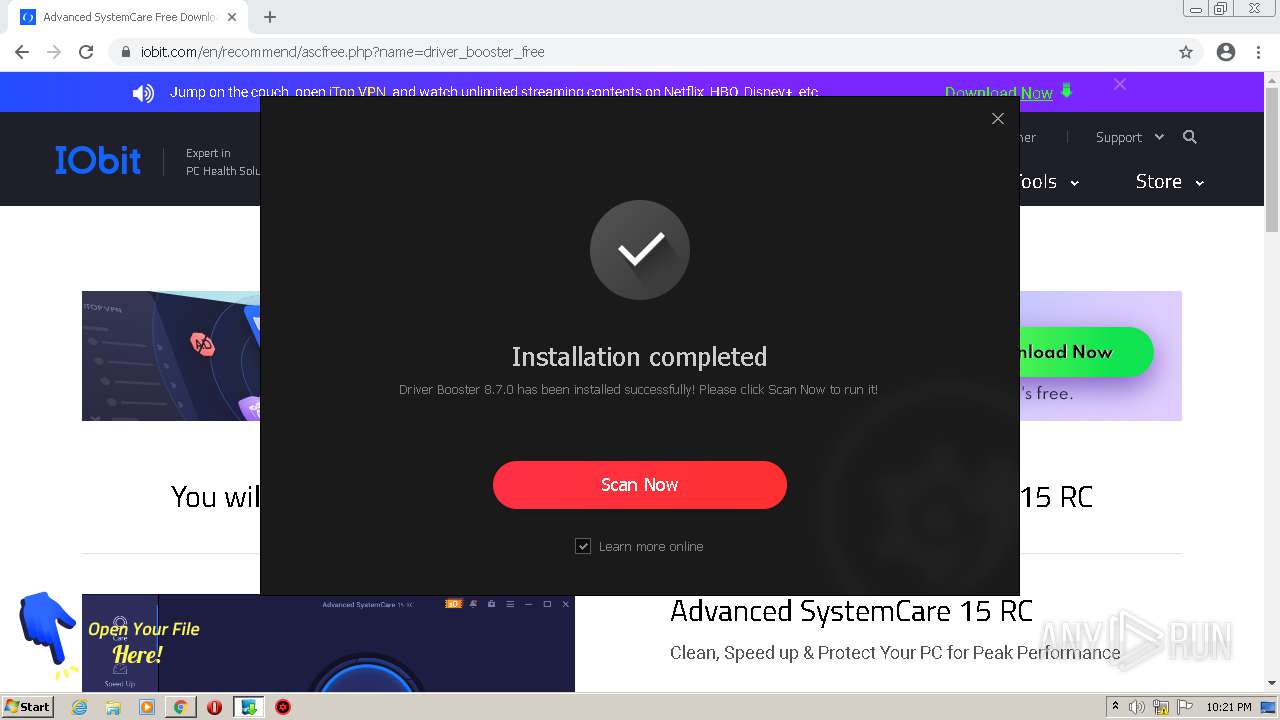
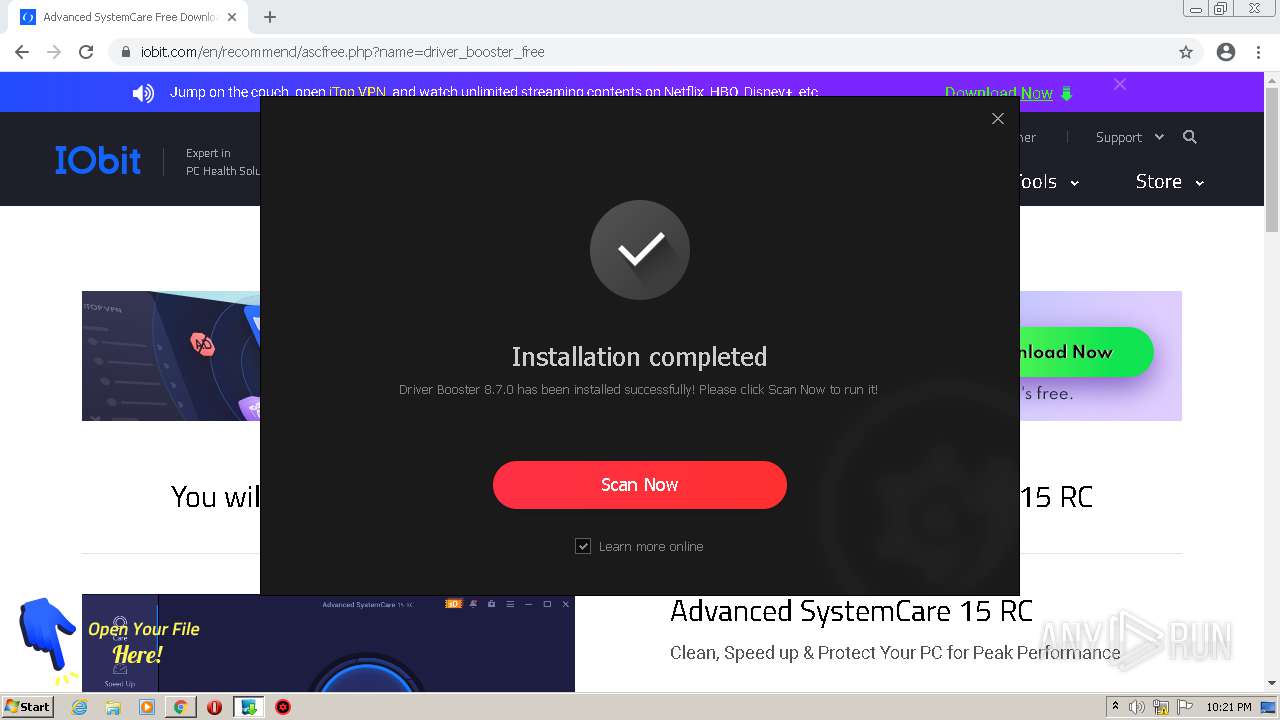
| URL: | https://www.iobit.com/en/driver-booster.php |
| Full analysis: | https://app.any.run/tasks/bb99ae70-ade9-4c18-8bd1-e0be25b2341b |
| Verdict: | Malicious activity |
| Analysis date: | September 24, 2021, 21:16:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | B3C7FC0F77C4862DC44C64D64879BF83 |
| SHA1: | 53C67017B6B815FACB04BD4D1B5C24E6E3AB4267 |
| SHA256: | 1C6F4149D2EC30417C84C68AA24F3A54C05B939A8674DC40D71E283186250C42 |
| SSDEEP: | 3:N8DSLgz1BX6xNV:2OLghBXm |
MALICIOUS
Application was dropped or rewritten from another process
- driver_booster_setup.exe (PID: 568)
- driver_booster_setup.exe (PID: 3748)
- setup.exe (PID: 3064)
- driver_booster_setup.exe (PID: 1240)
- SetupHlp.exe (PID: 3816)
- RttHlp.exe (PID: 1072)
- CareScan.exe (PID: 1412)
- InstStat.exe (PID: 2940)
- HWiNFO.exe (PID: 2440)
Drops executable file immediately after starts
- driver_booster_setup.exe (PID: 568)
- driver_booster_setup.exe (PID: 3748)
- chrome.exe (PID: 1276)
- driver_booster_setup.exe (PID: 1240)
- HWiNFO.exe (PID: 2440)
Actions looks like stealing of personal data
- driver_booster_setup.tmp (PID: 952)
- CareScan.exe (PID: 1412)
Loads dropped or rewritten executable
- SetupHlp.exe (PID: 3816)
- CareScan.exe (PID: 1412)
- RttHlp.exe (PID: 1072)
- InstStat.exe (PID: 2940)
- HWiNFO.exe (PID: 2440)
Loads the Task Scheduler COM API
- SetupHlp.exe (PID: 3816)
- setup.exe (PID: 3064)
Steals credentials from Web Browsers
- CareScan.exe (PID: 1412)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2412)
- driver_booster_setup.exe (PID: 568)
- driver_booster_setup.exe (PID: 3748)
- driver_booster_setup.tmp (PID: 952)
- chrome.exe (PID: 1276)
- driver_booster_setup.exe (PID: 1240)
- HWiNFO.exe (PID: 2440)
- driver_booster_setup.tmp (PID: 2824)
Checks supported languages
- driver_booster_setup.exe (PID: 568)
- driver_booster_setup.tmp (PID: 2328)
- driver_booster_setup.exe (PID: 3748)
- setup.exe (PID: 3064)
- driver_booster_setup.tmp (PID: 952)
- driver_booster_setup.exe (PID: 1240)
- driver_booster_setup.tmp (PID: 2824)
- HWiNFO.exe (PID: 2440)
- CareScan.exe (PID: 1412)
- SetupHlp.exe (PID: 3816)
- RttHlp.exe (PID: 1072)
- InstStat.exe (PID: 2940)
Reads Windows owner or organization settings
- driver_booster_setup.tmp (PID: 952)
- driver_booster_setup.tmp (PID: 2824)
Reads the Windows organization settings
- driver_booster_setup.tmp (PID: 952)
- driver_booster_setup.tmp (PID: 2824)
Reads the computer name
- driver_booster_setup.tmp (PID: 952)
- setup.exe (PID: 3064)
- driver_booster_setup.tmp (PID: 2328)
- driver_booster_setup.tmp (PID: 2824)
- CareScan.exe (PID: 1412)
- HWiNFO.exe (PID: 2440)
- SetupHlp.exe (PID: 3816)
- InstStat.exe (PID: 2940)
Drops a file with a compile date too recent
- driver_booster_setup.tmp (PID: 952)
- driver_booster_setup.tmp (PID: 2824)
Creates files in the program directory
- setup.exe (PID: 3064)
- CareScan.exe (PID: 1412)
- SetupHlp.exe (PID: 3816)
- RttHlp.exe (PID: 1072)
- InstStat.exe (PID: 2940)
Drops a file that was compiled in debug mode
- chrome.exe (PID: 1276)
- driver_booster_setup.tmp (PID: 2824)
- HWiNFO.exe (PID: 2440)
Creates files in the user directory
- setup.exe (PID: 3064)
- driver_booster_setup.tmp (PID: 2824)
- CareScan.exe (PID: 1412)
Creates a directory in Program Files
- driver_booster_setup.tmp (PID: 2824)
- CareScan.exe (PID: 1412)
- SetupHlp.exe (PID: 3816)
Drops a file with too old compile date
- driver_booster_setup.tmp (PID: 2824)
Searches for installed software
- setup.exe (PID: 3064)
- SetupHlp.exe (PID: 3816)
- InstStat.exe (PID: 2940)
- CareScan.exe (PID: 1412)
Reads the date of Windows installation
- driver_booster_setup.tmp (PID: 2824)
Changes default file association
- SetupHlp.exe (PID: 3816)
Reads Microsoft Outlook installation path
- CareScan.exe (PID: 1412)
Reads mouse settings
- CareScan.exe (PID: 1412)
INFO
Reads the computer name
- chrome.exe (PID: 2412)
- chrome.exe (PID: 3300)
- chrome.exe (PID: 3192)
- chrome.exe (PID: 2660)
- chrome.exe (PID: 3016)
- chrome.exe (PID: 1448)
- chrome.exe (PID: 2792)
- chrome.exe (PID: 2116)
- chrome.exe (PID: 3244)
- chrome.exe (PID: 2004)
Checks supported languages
- chrome.exe (PID: 2412)
- chrome.exe (PID: 3300)
- chrome.exe (PID: 3192)
- chrome.exe (PID: 2864)
- chrome.exe (PID: 3848)
- chrome.exe (PID: 3828)
- chrome.exe (PID: 3016)
- chrome.exe (PID: 3428)
- chrome.exe (PID: 3884)
- chrome.exe (PID: 2660)
- chrome.exe (PID: 1448)
- chrome.exe (PID: 3244)
- chrome.exe (PID: 2332)
- chrome.exe (PID: 2140)
- chrome.exe (PID: 3456)
- chrome.exe (PID: 2792)
- chrome.exe (PID: 2004)
- chrome.exe (PID: 2116)
- chrome.exe (PID: 3684)
- chrome.exe (PID: 1276)
- chrome.exe (PID: 1076)
- chrome.exe (PID: 2468)
- chrome.exe (PID: 3356)
- chrome.exe (PID: 3240)
- chrome.exe (PID: 3508)
- chrome.exe (PID: 3568)
- chrome.exe (PID: 3892)
- chrome.exe (PID: 2364)
- chrome.exe (PID: 2356)
Application launched itself
- chrome.exe (PID: 2412)
Reads the hosts file
- chrome.exe (PID: 3300)
- chrome.exe (PID: 2412)
Reads settings of System Certificates
- chrome.exe (PID: 3300)
- chrome.exe (PID: 2412)
Reads the date of Windows installation
- chrome.exe (PID: 1448)
Checks Windows Trust Settings
- chrome.exe (PID: 2412)
Application was dropped or rewritten from another process
- driver_booster_setup.tmp (PID: 2328)
- driver_booster_setup.tmp (PID: 952)
- driver_booster_setup.tmp (PID: 2824)
Creates a software uninstall entry
- driver_booster_setup.tmp (PID: 2824)
Dropped object may contain Bitcoin addresses
- driver_booster_setup.tmp (PID: 2824)
- CareScan.exe (PID: 1412)
Creates files in the program directory
- driver_booster_setup.tmp (PID: 2824)
Reads Microsoft Office registry keys
- CareScan.exe (PID: 1412)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
81
Monitored processes
41
Malicious processes
9
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
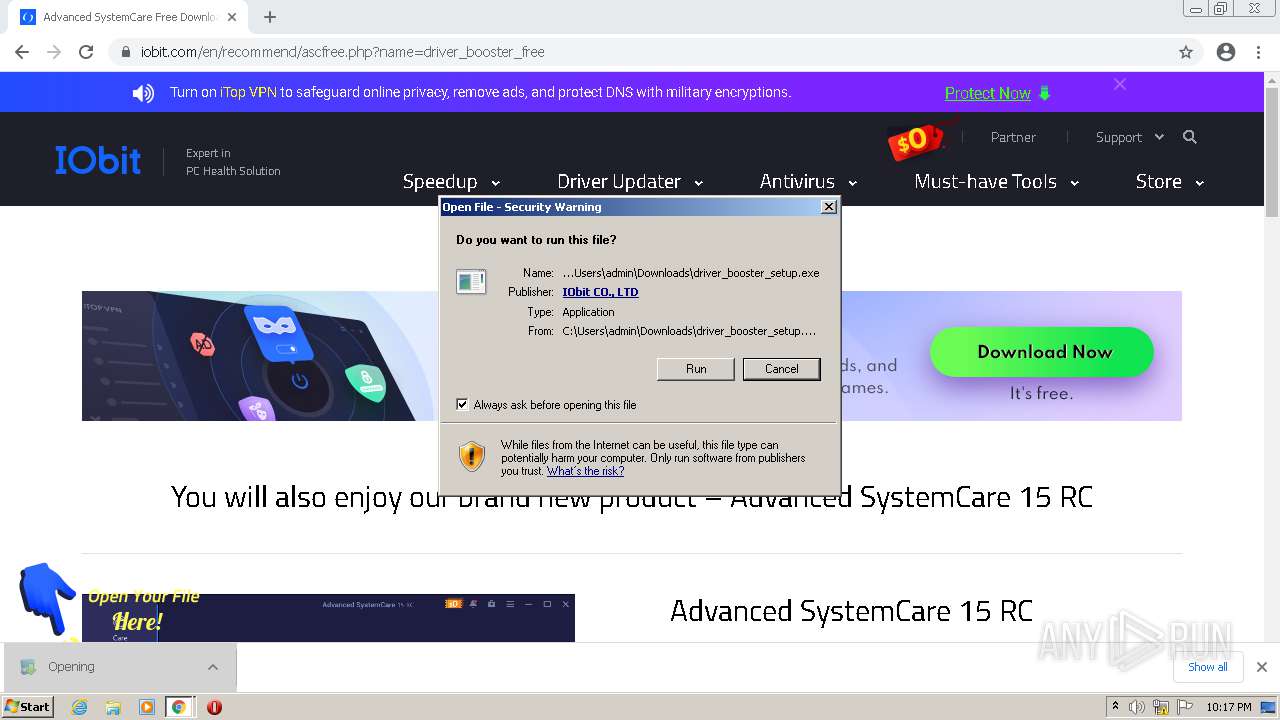
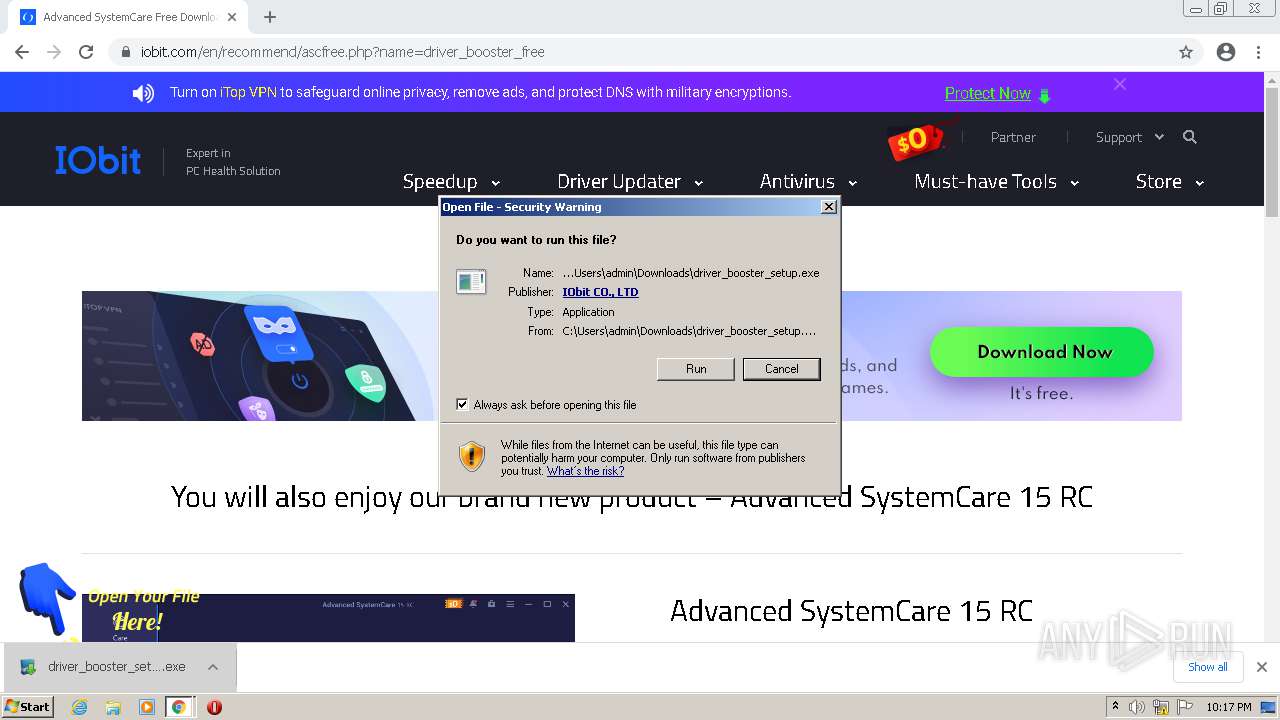
| 568 | "C:\Users\admin\Downloads\driver_booster_setup.exe" | C:\Users\admin\Downloads\driver_booster_setup.exe | chrome.exe | ||||||||||||
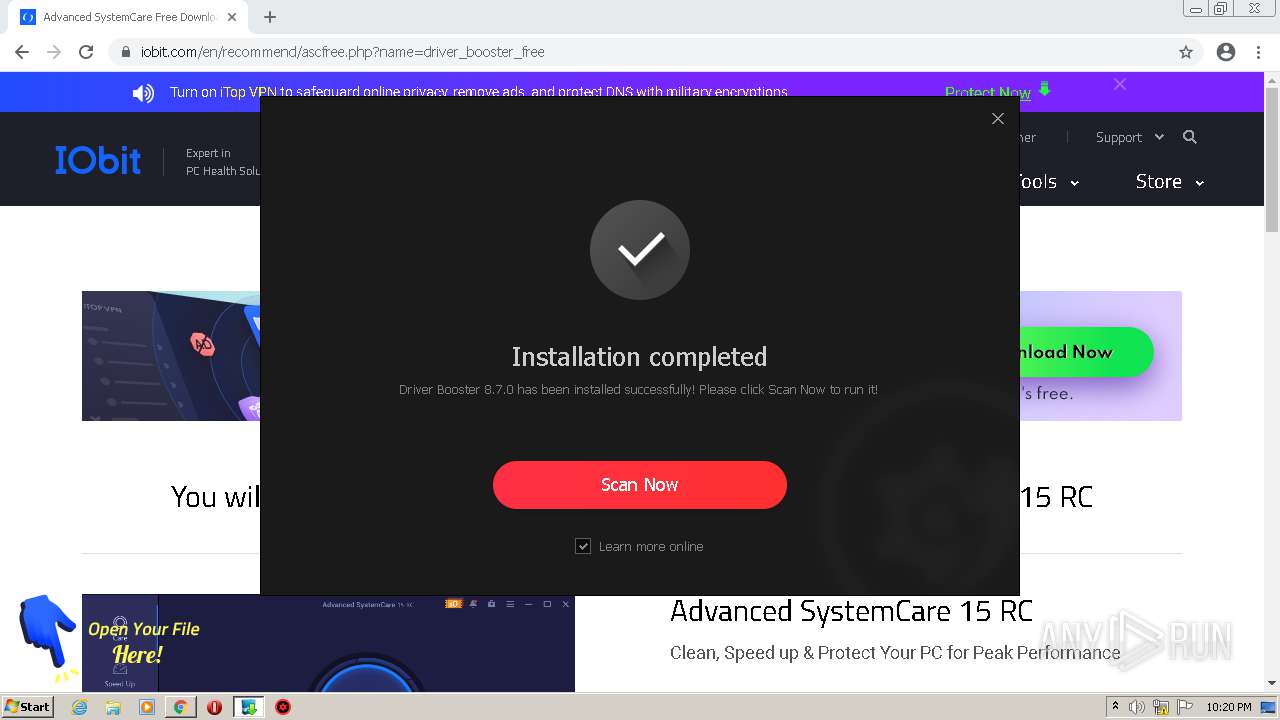
User: admin Company: IObit Integrity Level: MEDIUM Description: Driver Booster 8 Setup Exit code: 1 Version: 8.7.0.529 Modules
| |||||||||||||||
| 952 | "C:\Users\admin\AppData\Local\Temp\is-7LLKA.tmp\driver_booster_setup.tmp" /SL5="$30172,26376188,139264,C:\Users\admin\Downloads\driver_booster_setup.exe" /SPAWNWND=$20174 /NOTIFYWND=$6015C | C:\Users\admin\AppData\Local\Temp\is-7LLKA.tmp\driver_booster_setup.tmp | driver_booster_setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 1 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1072 | "C:\Program Files\IObit\Driver Booster\8.7.0\RttHlp.exe" /winstdate | C:\Program Files\IObit\Driver Booster\8.7.0\RttHlp.exe | — | SetupHlp.exe | |||||||||||
User: admin Company: IObit Integrity Level: HIGH Description: IObit RttHlp Exit code: 0 Version: 8.0.0.5 Modules
| |||||||||||||||
| 1076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1028,13362367225308754739,12098467525850357157,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3396 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1240 | "C:\Users\admin\Downloads\driver_booster_setup.exe" /sp- /verysilent /Installer /norestart /DIR="C:\Program Files\IObit\Driver Booster" /Installer-DeskIcon /Installer-TaskIcon | C:\Users\admin\Downloads\driver_booster_setup.exe | setup.exe | ||||||||||||
User: admin Company: IObit Integrity Level: HIGH Description: Driver Booster 8 Setup Exit code: 0 Version: 8.7.0.529 Modules
| |||||||||||||||
| 1276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1028,13362367225308754739,12098467525850357157,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=812 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1412 | "C:\Program Files\IObit\Driver Booster\8.7.0\CareScan.exe" /savefile /silentscan /low /output="C:\Program Files\IObit\Driver Booster\8.7.0\ScanData\ScanResult_all.ini" | C:\Program Files\IObit\Driver Booster\8.7.0\CareScan.exe | driver_booster_setup.tmp | ||||||||||||
User: admin Company: IObit Integrity Level: HIGH Description: CareScan Exit code: 0 Version: 6.0.0.181 Modules
| |||||||||||||||
| 1448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1028,13362367225308754739,12098467525850357157,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1784 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2004 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1028,13362367225308754739,12098467525850357157,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3032 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1028,13362367225308754739,12098467525850357157,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3472 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
36 394
Read events
35 983
Write events
406
Delete events
5
Modification events
| (PID) Process: | (2412) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2412) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2412) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2412) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2412) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2412) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2412) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2412) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2412) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2412) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
153
Suspicious files
50
Text files
437
Unknown types
34
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-614E4038-96C.pma | — | |
MD5:— | SHA256:— | |||
| 2412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 2412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\fa60198a-eb64-4d79-9f0e-4648899045bb.tmp | text | |
MD5:— | SHA256:— | |||
| 2412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 2412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 2412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF123466.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 2864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 2412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF123485.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 2412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 2412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\MANIFEST-000001 | binary | |
MD5:5AF87DFD673BA2115E2FCF5CFDB727AB | SHA256:F9D31B278E215EB0D0E9CD709EDFA037E828F36214AB7906F612160FEAD4B2B4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
47
TCP/UDP connections
55
DNS requests
24
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/gpe7ohs3f5omwhxxpxvcdvkwva_1.3.36.101/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.101_win_adeodp7n5nw3wgk7xjdln2w2sgsq.crx3 | US | — | — | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/gpe7ohs3f5omwhxxpxvcdvkwva_1.3.36.101/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.101_win_adeodp7n5nw3wgk7xjdln2w2sgsq.crx3 | US | binary | 5.64 Kb | whitelisted |
3064 | setup.exe | GET | 200 | 152.199.20.140:80 | http://update.iobit.com/infofiles/db/rmd/dtionex.upt | US | text | 1.68 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/gpe7ohs3f5omwhxxpxvcdvkwva_1.3.36.101/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.101_win_adeodp7n5nw3wgk7xjdln2w2sgsq.crx3 | US | binary | 22.4 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/gpe7ohs3f5omwhxxpxvcdvkwva_1.3.36.101/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.101_win_adeodp7n5nw3wgk7xjdln2w2sgsq.crx3 | US | binary | 94.3 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/gpe7ohs3f5omwhxxpxvcdvkwva_1.3.36.101/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.101_win_adeodp7n5nw3wgk7xjdln2w2sgsq.crx3 | US | binary | 46.4 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/gpe7ohs3f5omwhxxpxvcdvkwva_1.3.36.101/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.101_win_adeodp7n5nw3wgk7xjdln2w2sgsq.crx3 | US | binary | 10.4 Kb | whitelisted |
3064 | setup.exe | GET | 206 | 152.199.20.140:80 | http://update.iobit.com/infofiles/db/rmd/dtionex.upt | US | text | 430 b | whitelisted |
3064 | setup.exe | GET | 206 | 152.199.20.140:80 | http://update.iobit.com/infofiles/db/rmd/dtionex.upt | US | binary | 430 b | whitelisted |
3064 | setup.exe | GET | 206 | 152.199.20.140:80 | http://update.iobit.com/infofiles/db/rmd/dtionex.upt | US | pcx | 426 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3300 | chrome.exe | 142.250.185.138:443 | content-autofill.googleapis.com | Google Inc. | US | whitelisted |
3300 | chrome.exe | 142.250.74.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
3300 | chrome.exe | 152.195.53.24:443 | www.iobit.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3300 | chrome.exe | 142.250.185.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
3300 | chrome.exe | 172.217.16.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
— | — | 172.217.16.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
— | — | 152.199.20.140:443 | codes.iobit.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | malicious |
— | — | 104.18.23.52:443 | kit.fontawesome.com | Cloudflare Inc | US | suspicious |
3300 | chrome.exe | 152.199.20.140:443 | codes.iobit.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | malicious |
3300 | chrome.exe | 142.250.184.238:443 | www.googleoptimize.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
www.iobit.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
codes.iobit.com |
| whitelisted |
kit.fontawesome.com |
| whitelisted |
www.googleoptimize.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3064 | setup.exe | Potentially Bad Traffic | ET INFO Suspicious Mozilla User-Agent - Likely Fake (Mozilla/4.0) |
3064 | setup.exe | Potentially Bad Traffic | ET INFO Suspicious Mozilla User-Agent - Likely Fake (Mozilla/4.0) |
3064 | setup.exe | Potentially Bad Traffic | ET INFO Suspicious Mozilla User-Agent - Likely Fake (Mozilla/4.0) |
3064 | setup.exe | Potentially Bad Traffic | ET INFO Suspicious Mozilla User-Agent - Likely Fake (Mozilla/4.0) |
3064 | setup.exe | Potentially Bad Traffic | ET INFO Suspicious Mozilla User-Agent - Likely Fake (Mozilla/4.0) |
3064 | setup.exe | Potentially Bad Traffic | ET INFO Suspicious Mozilla User-Agent - Likely Fake (Mozilla/4.0) |
3064 | setup.exe | Potentially Bad Traffic | ET INFO Suspicious Mozilla User-Agent - Likely Fake (Mozilla/4.0) |
3064 | setup.exe | Potentially Bad Traffic | ET INFO Suspicious Mozilla User-Agent - Likely Fake (Mozilla/4.0) |
3064 | setup.exe | Potentially Bad Traffic | ET INFO Suspicious Mozilla User-Agent - Likely Fake (Mozilla/4.0) |
3064 | setup.exe | Potentially Bad Traffic | ET INFO Suspicious Mozilla User-Agent - Likely Fake (Mozilla/4.0) |
Process | Message |
|---|---|
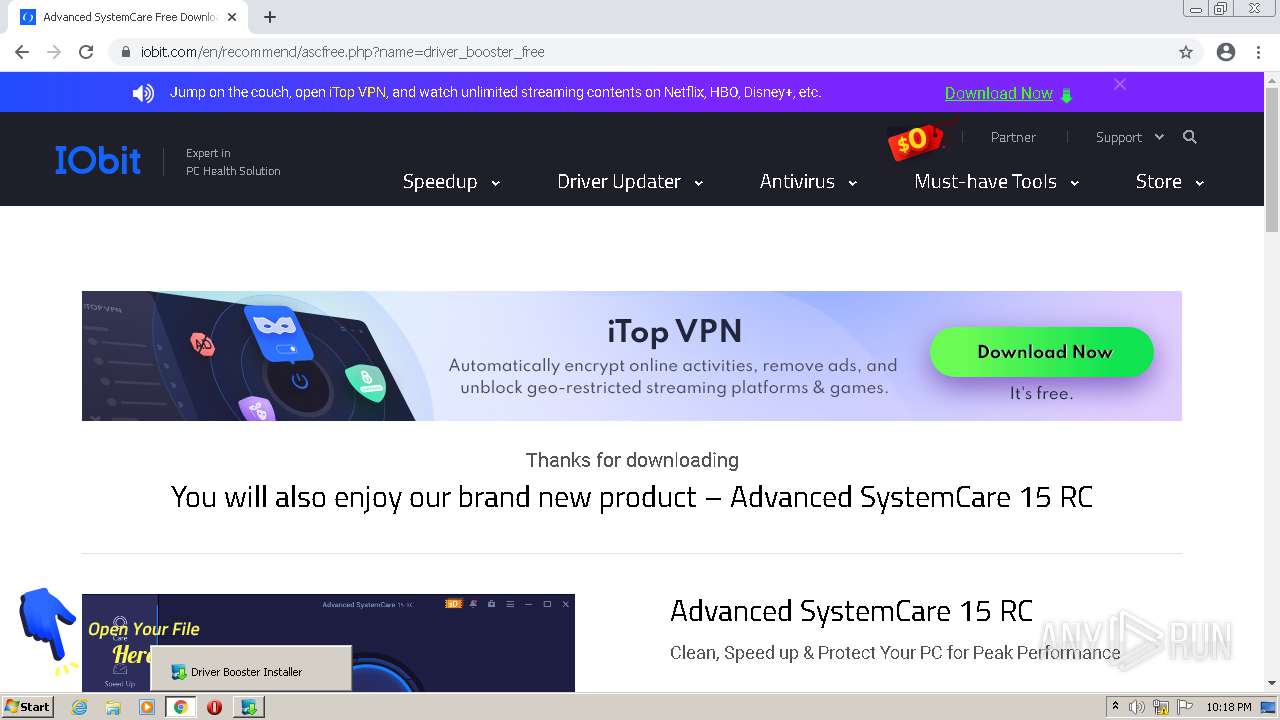
setup.exe | downloadchrome info begin |
setup.exe | GetPromoteProductByDebug: |
setup.exe | have iniFile |
setup.exe | Ver:8.7.0.529 *** minVer:8.0.2 *** maxVer:0 |
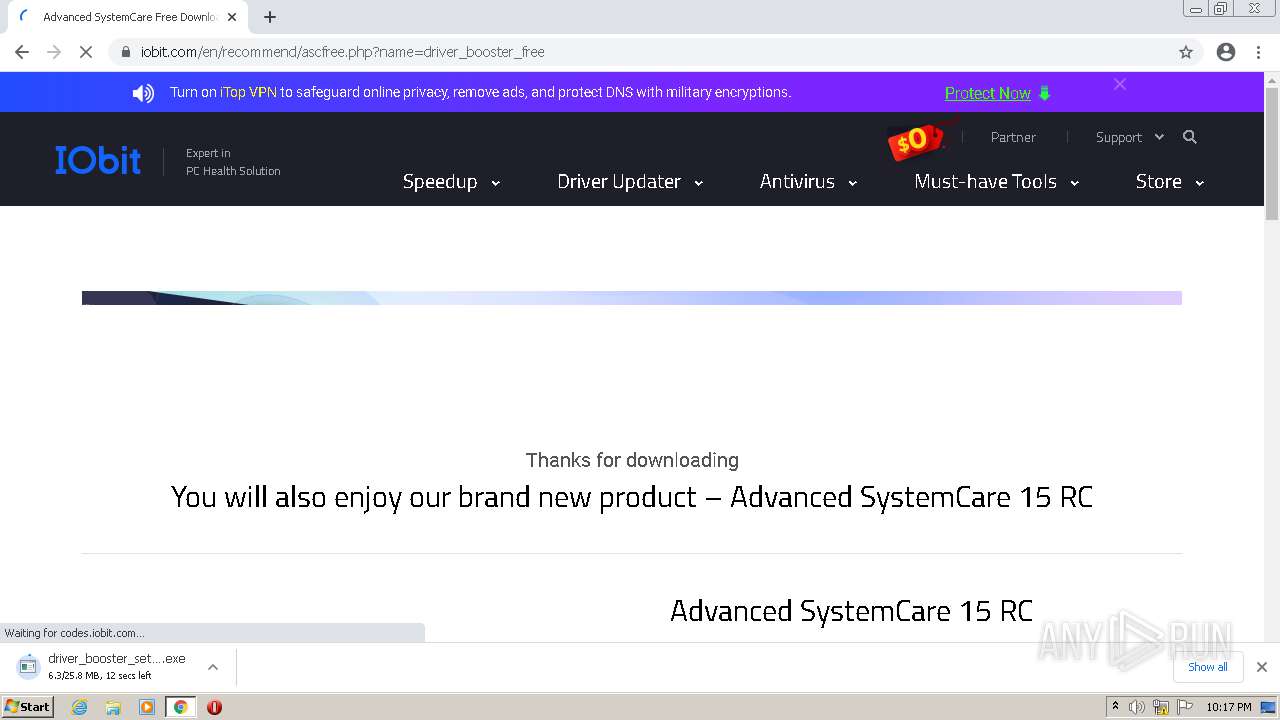
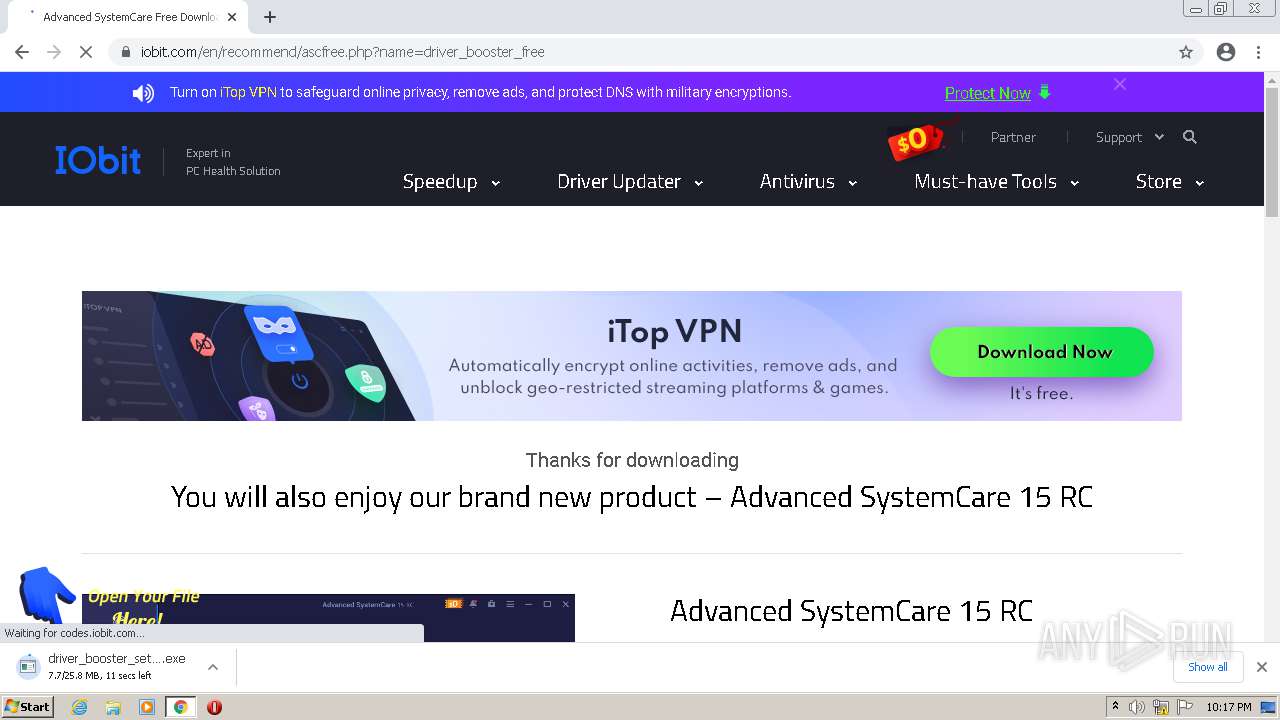
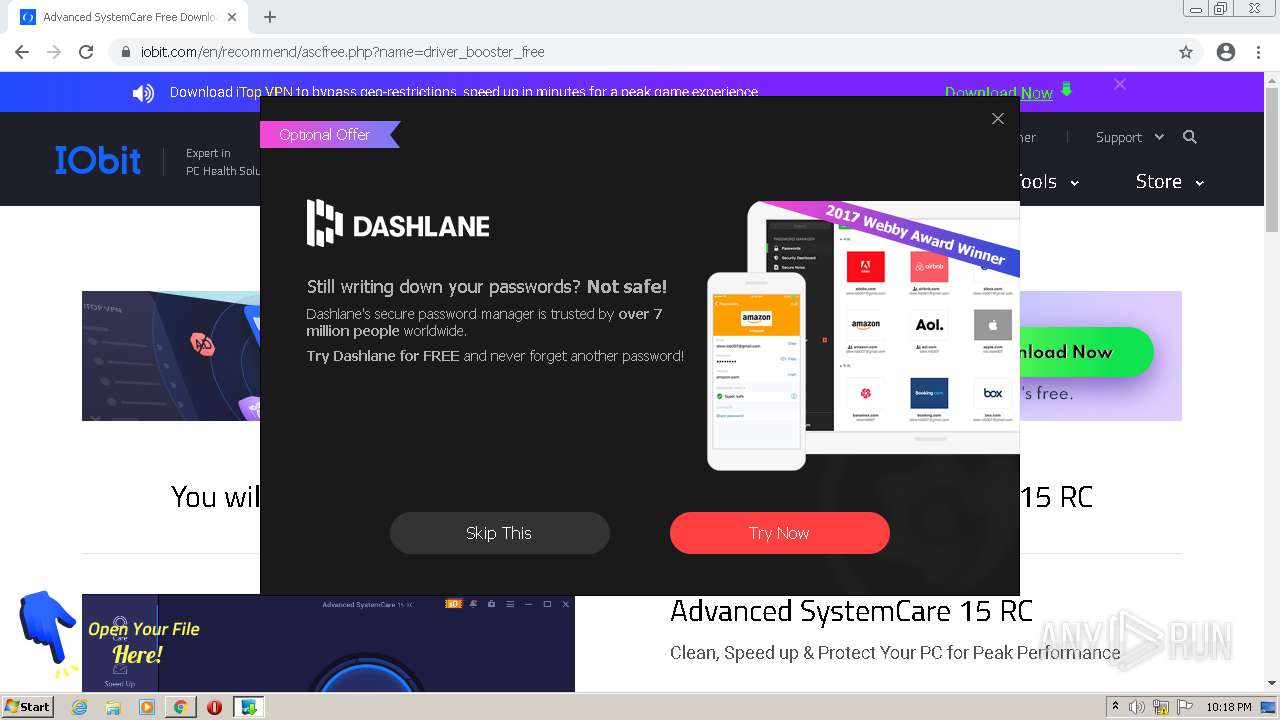
setup.exe | TPromoteProductInfo.CheckPromote begin Product = iTopVPN |
setup.exe | bShow |
setup.exe | IsNeedRecommendByExternalConditions |
setup.exe | CheckCountry |
setup.exe | strRegisterConfine |
setup.exe | strRegisterConfine.Count |