| File name: | NETFLIX Accounts Checker By X-SLAYER.exe |
| Full analysis: | https://app.any.run/tasks/2595f1b1-433a-47de-b68f-bce70dde43cf |
| Verdict: | Malicious activity |
| Analysis date: | February 03, 2019, 08:35:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 5FAB7DE232C297E00A8D7F8BD33C1E6B |
| SHA1: | 72C65DA9FBD84909B09AD126D14FD7E49155BAD5 |
| SHA256: | 1C6D9B2818A7F8B9D64FA9713E74700ACFD9FDCE3DA5CA500E17CC46452DB40F |
| SSDEEP: | 12288:i2kDjrUSii2kA7ZK9Y14aNNOJ9jtSrjTmEUGSvuFlf8N6IYcS+MyCb85w1Z8QLz5:+QbM9Y1VGJvtCh |
MALICIOUS
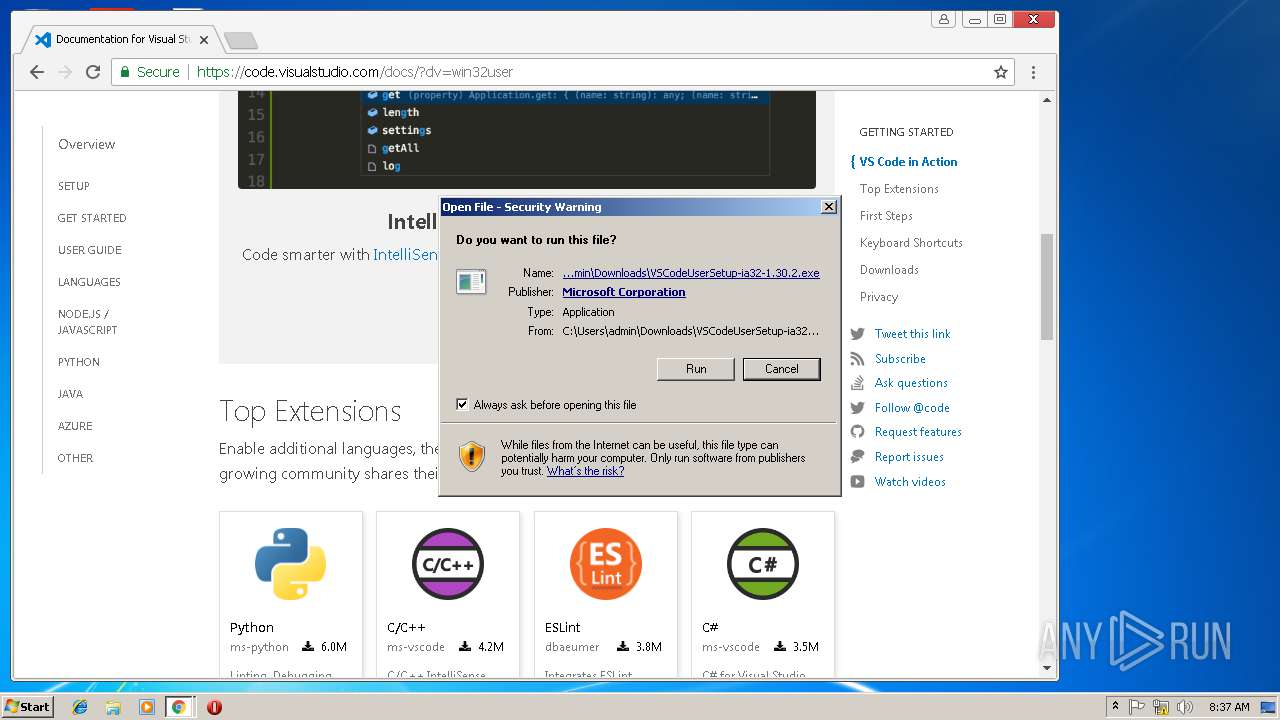
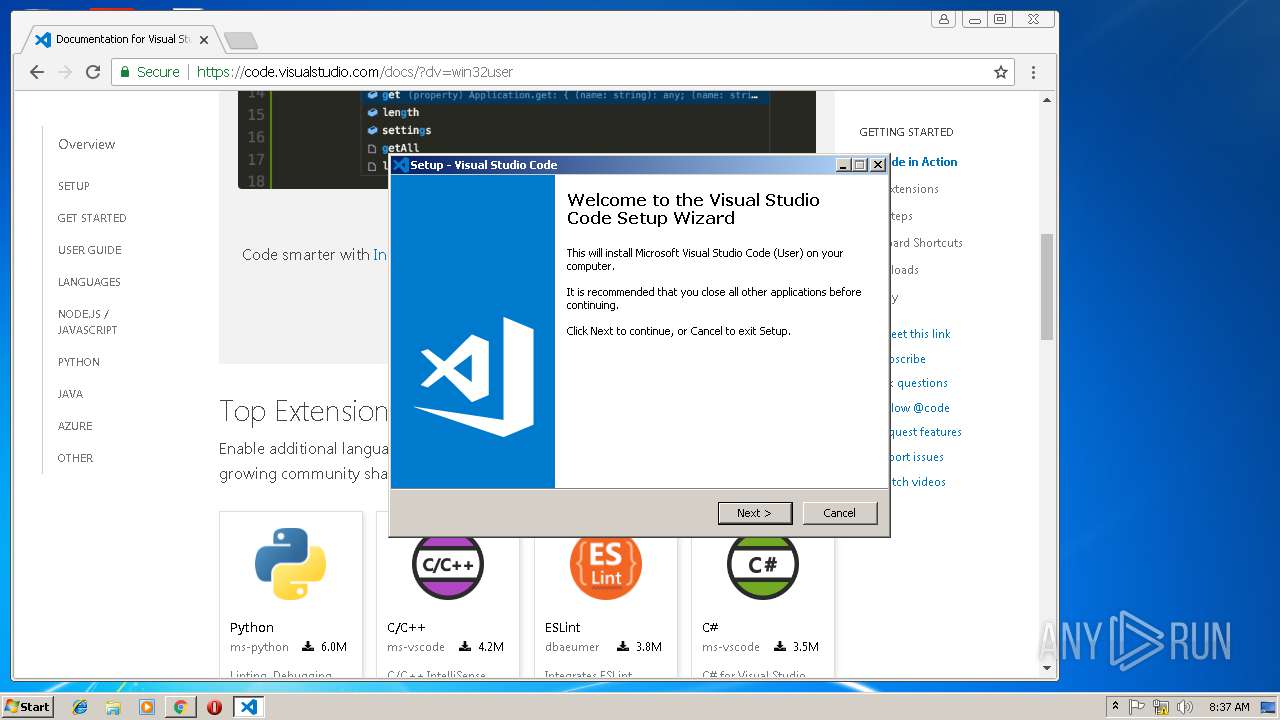
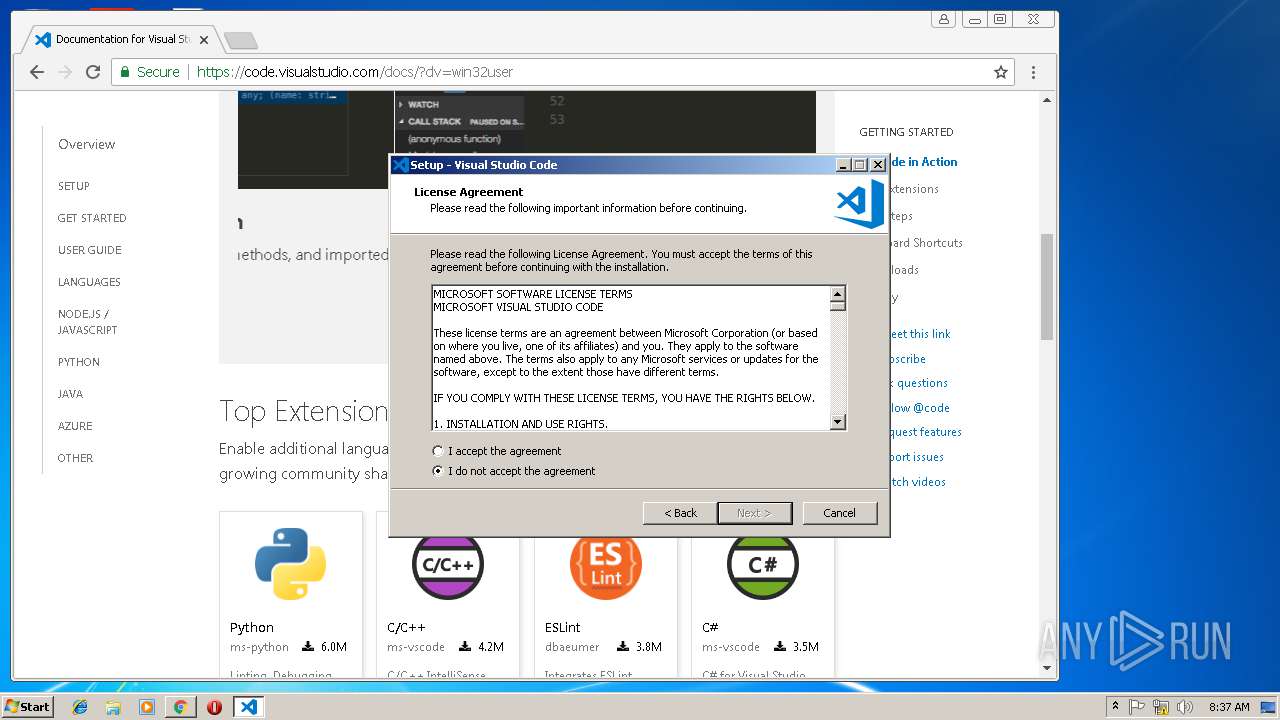
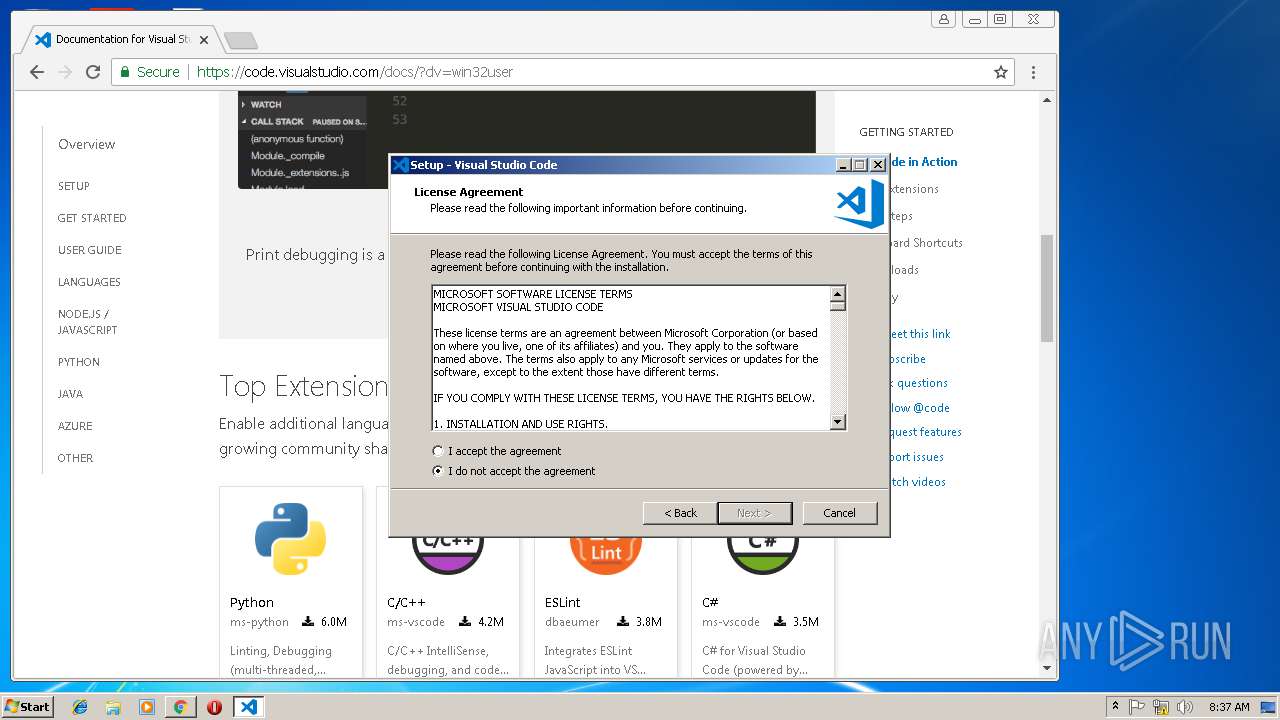
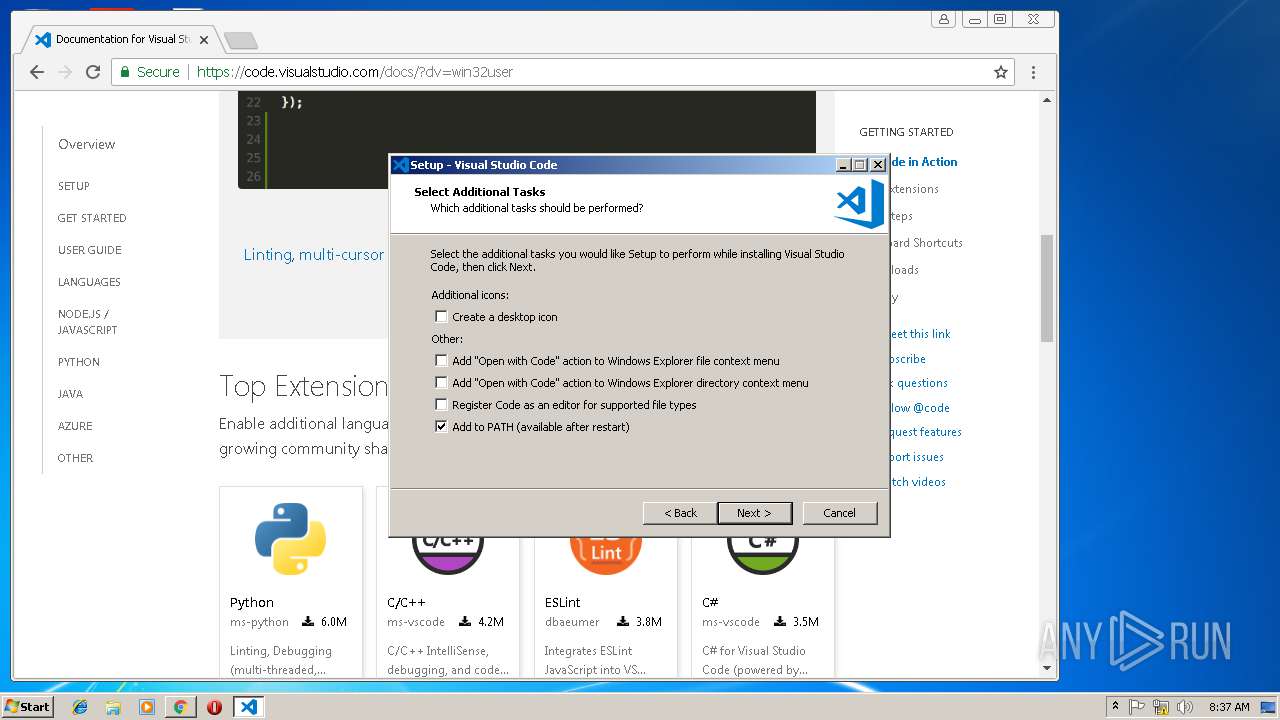
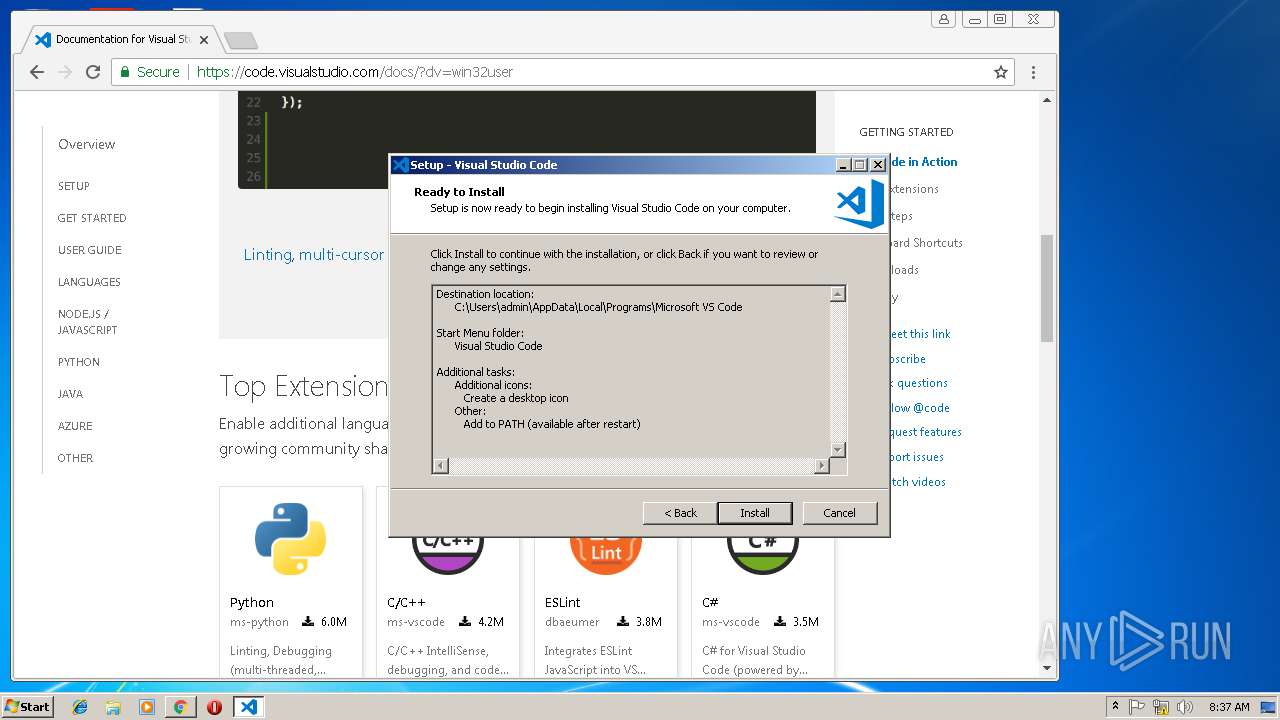
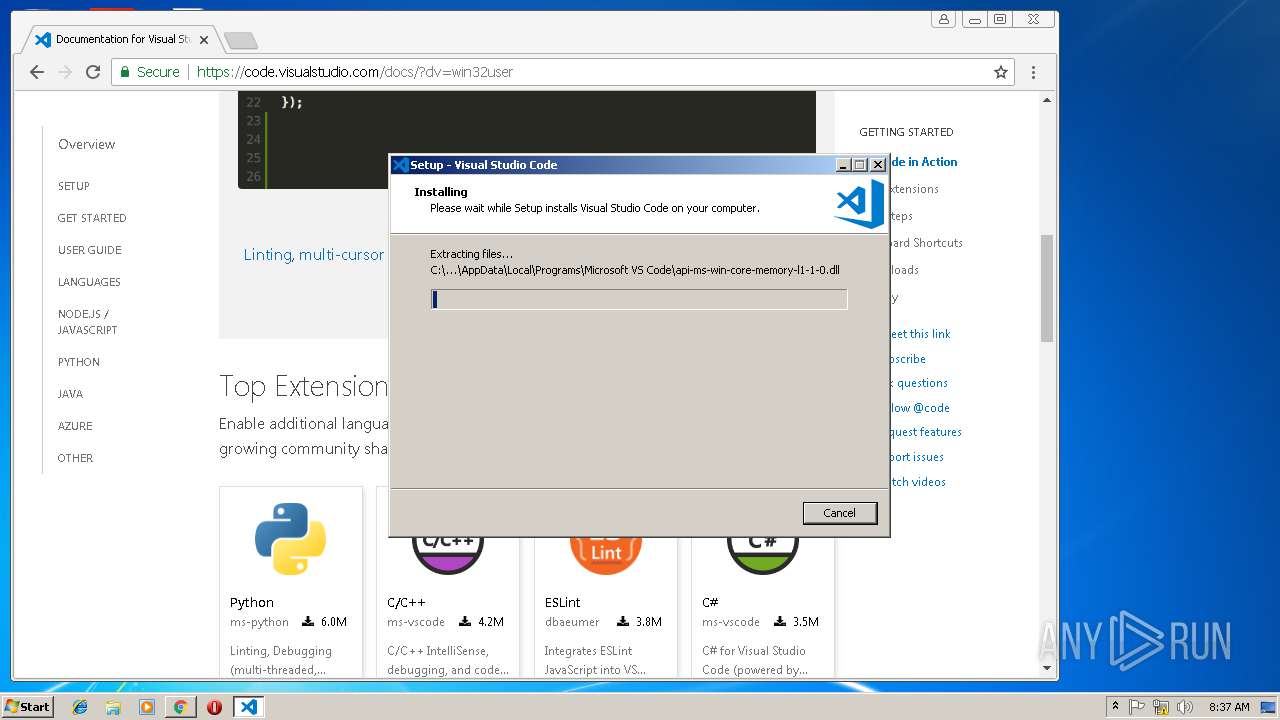
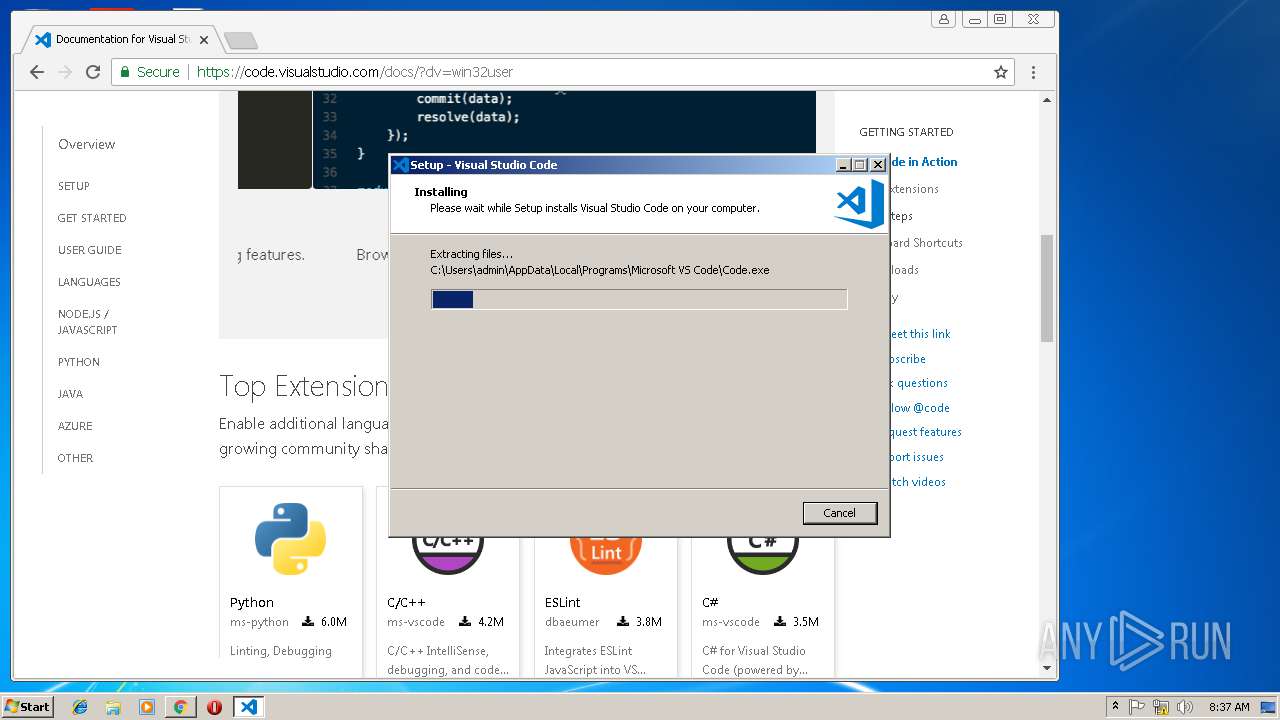
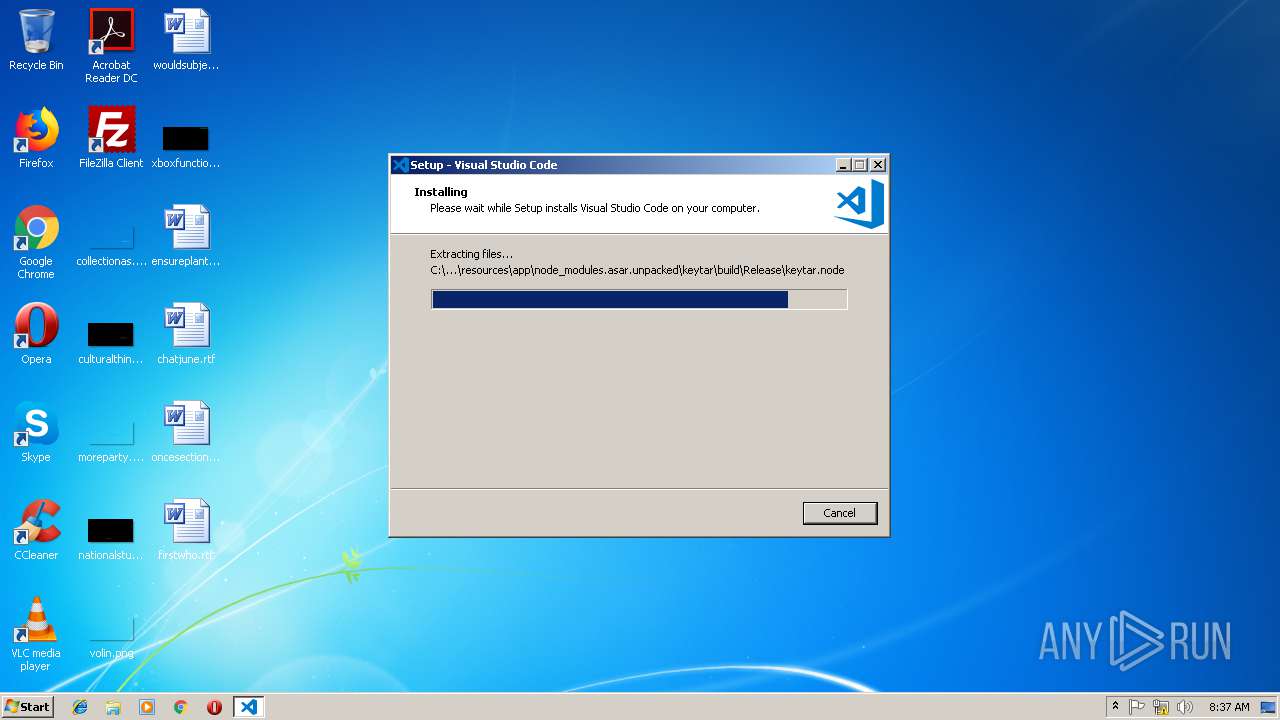
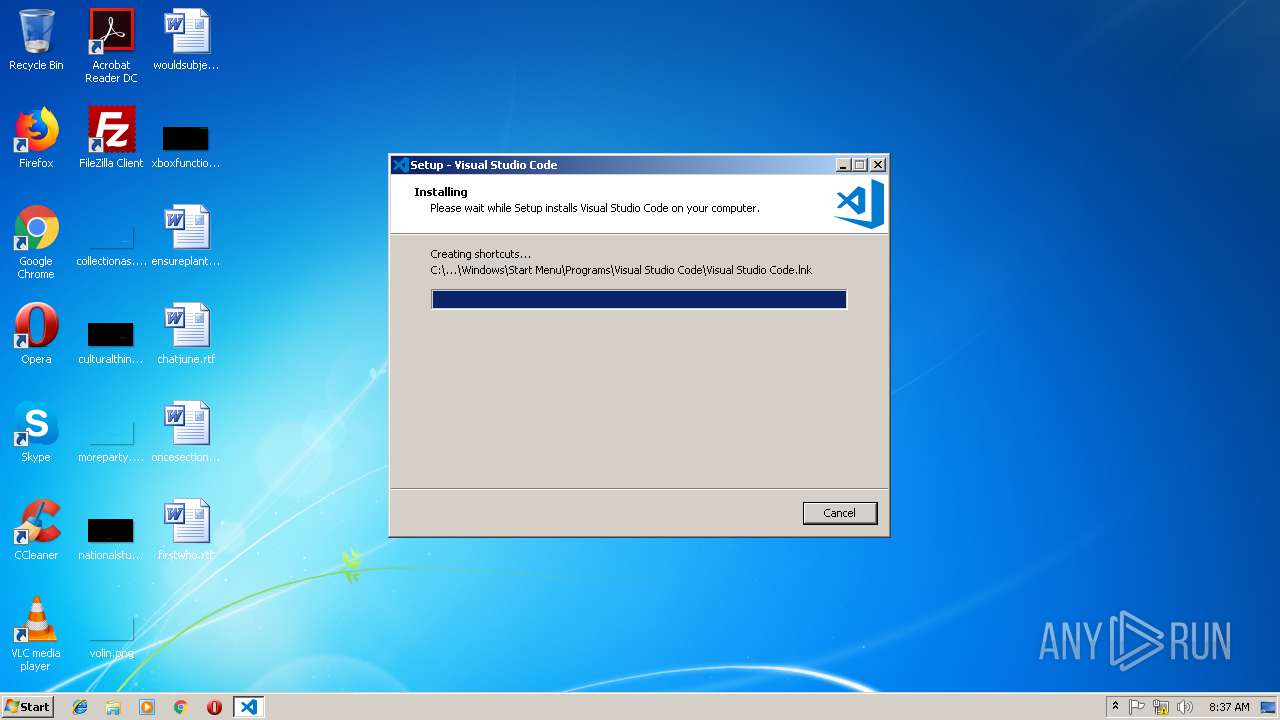
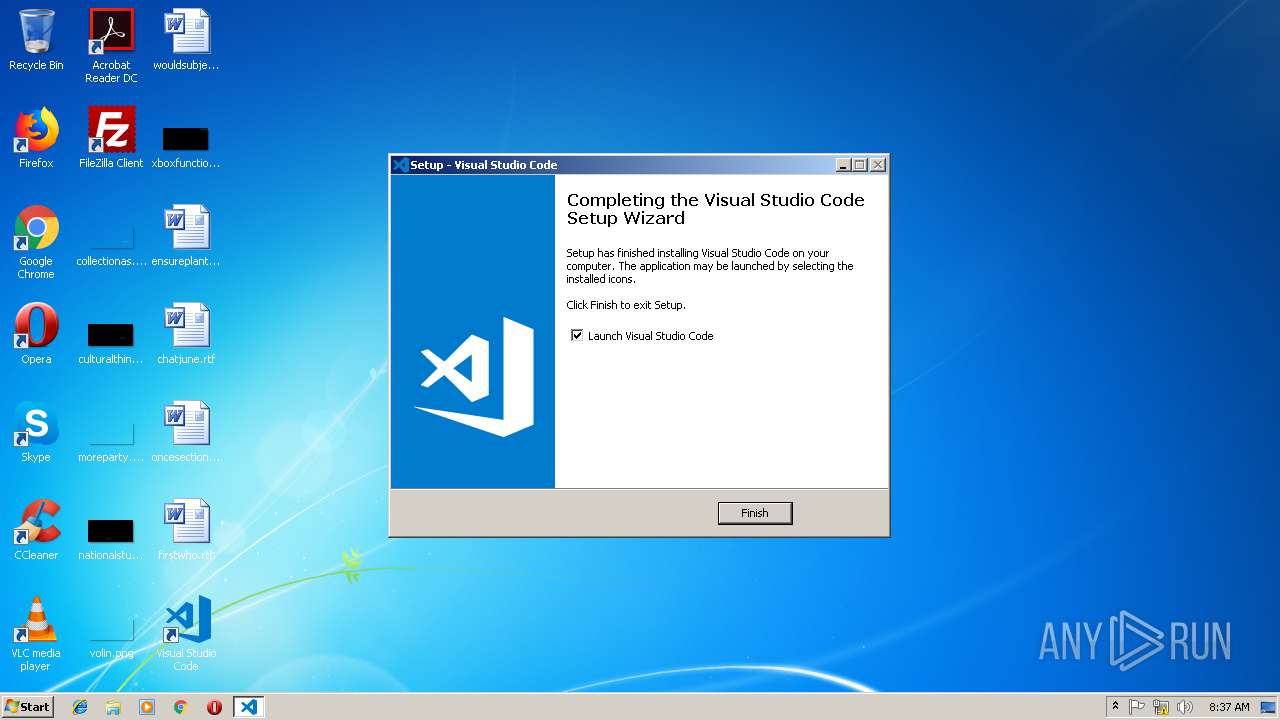
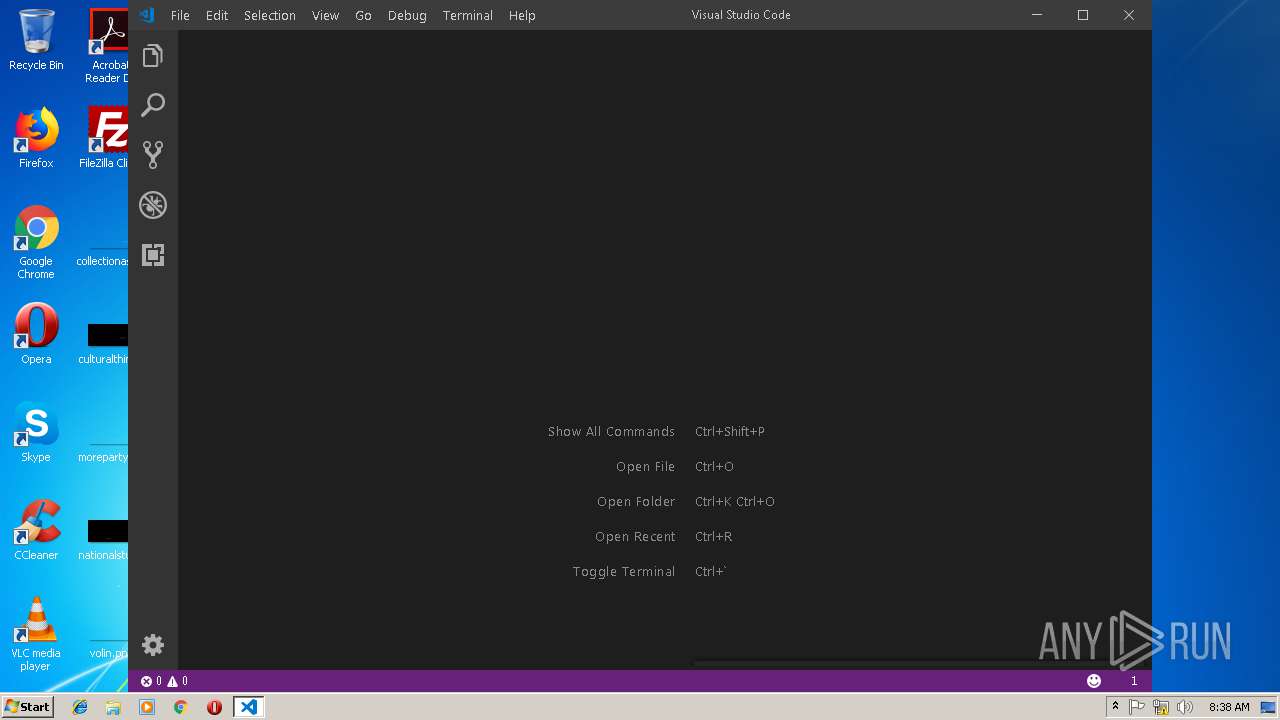
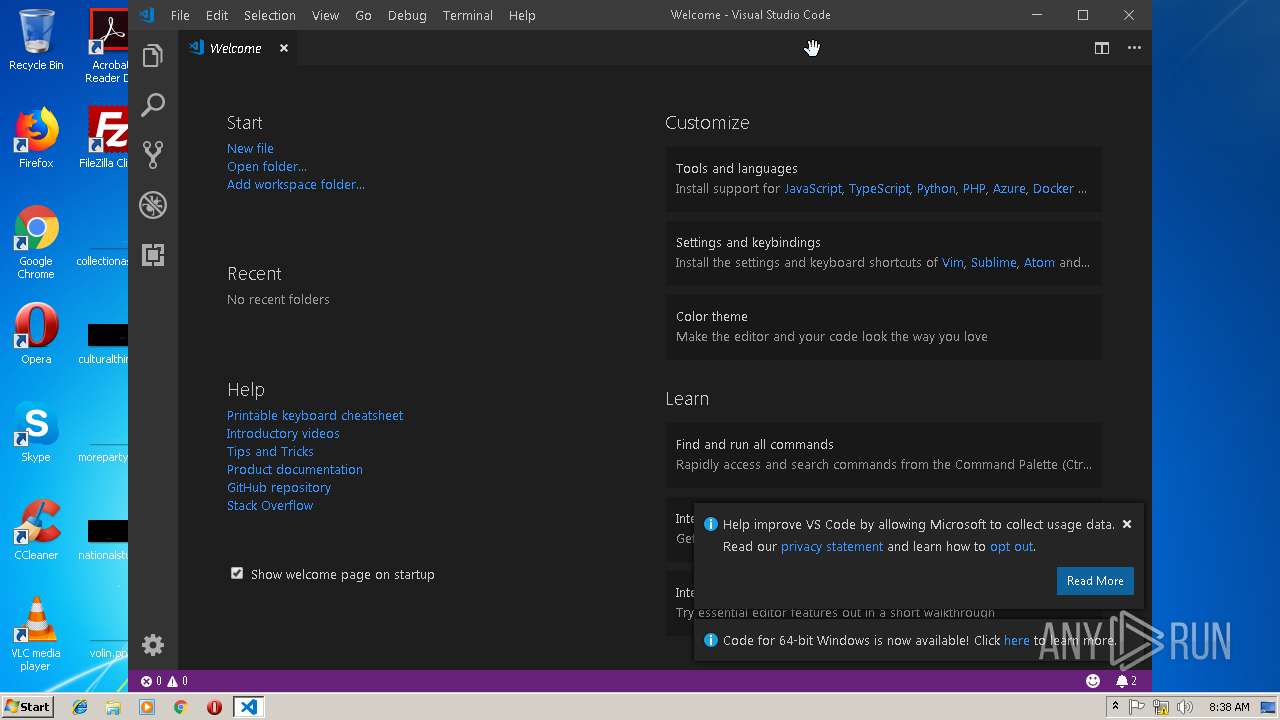
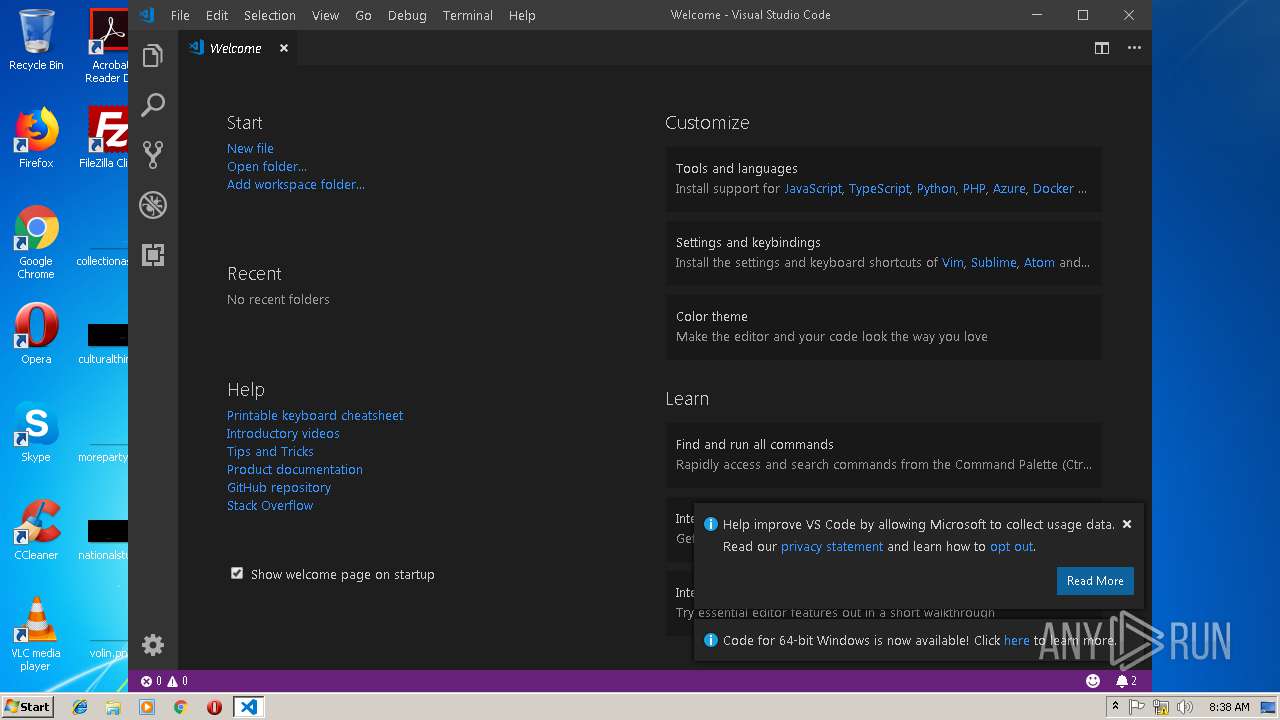
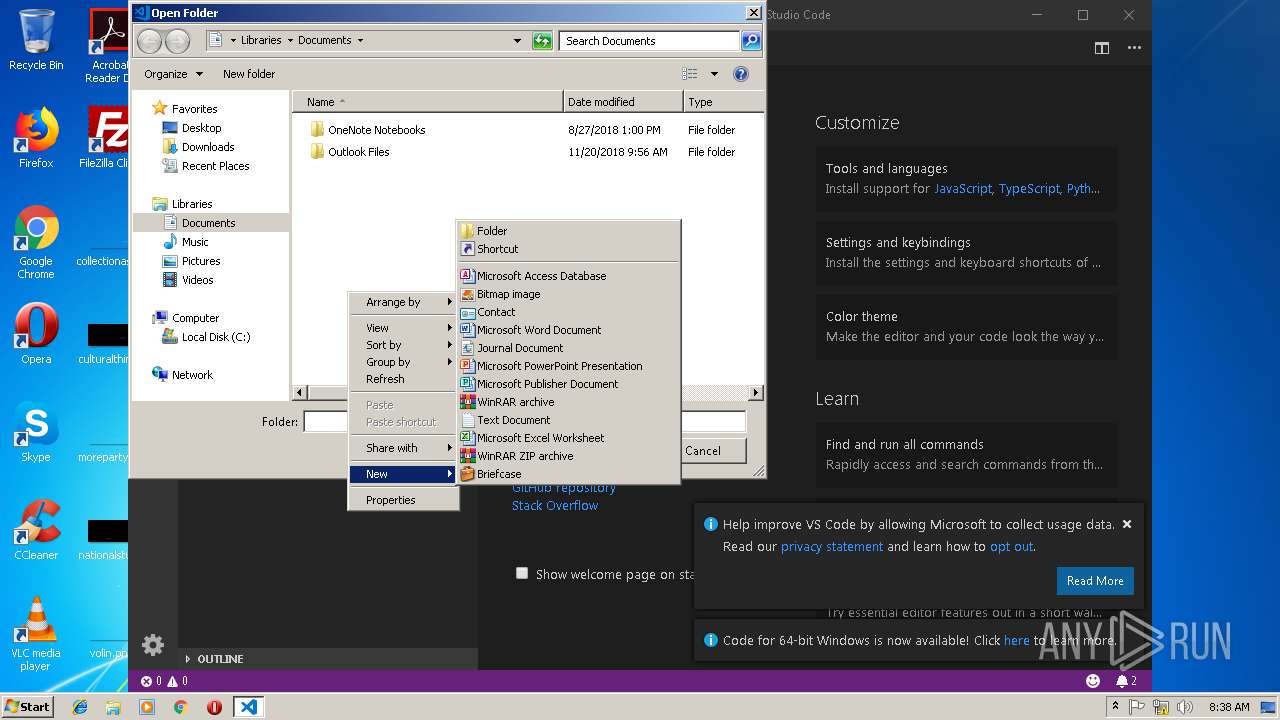
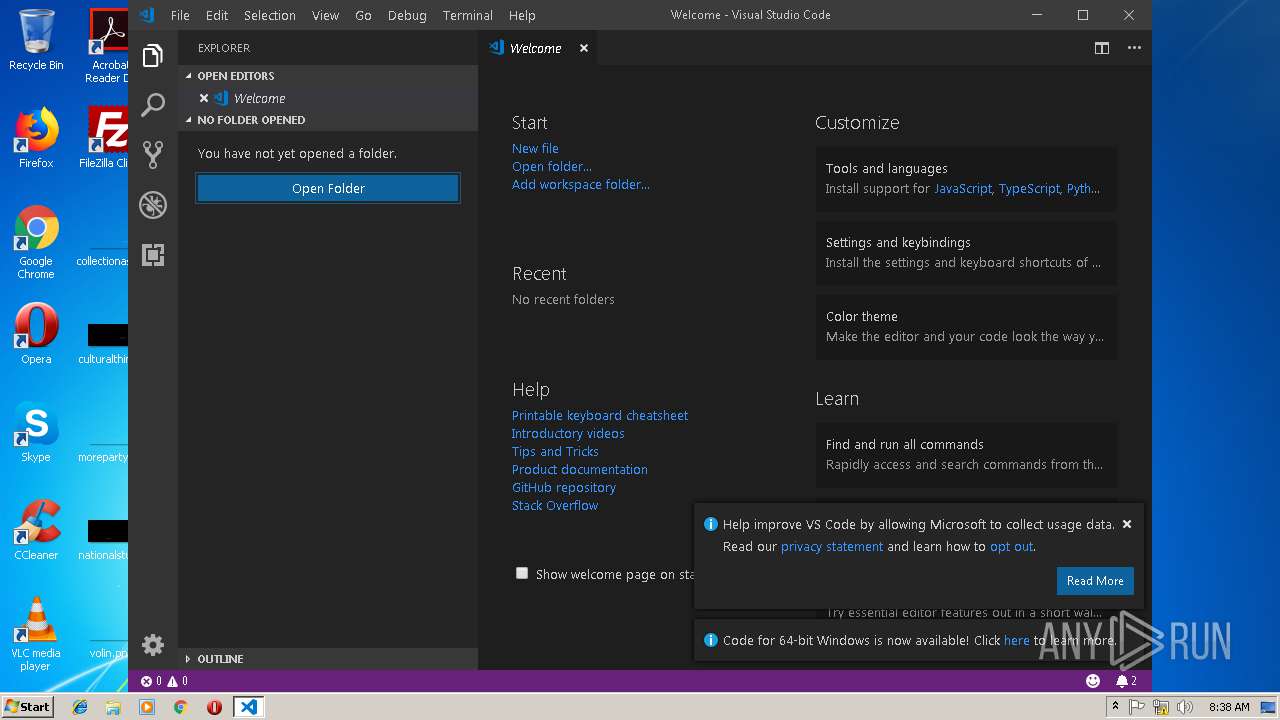
Application was dropped or rewritten from another process
- VSCodeUserSetup-ia32-1.30.2.exe (PID: 2972)
- CodeHelper.exe (PID: 3668)
Loads dropped or rewritten executable
- Code.exe (PID: 4084)
- Code.exe (PID: 2212)
- Code.exe (PID: 2264)
- Code.exe (PID: 3592)
- Code.exe (PID: 3744)
- Code.exe (PID: 3448)
- Code.exe (PID: 2248)
- Code.exe (PID: 3044)
- Code.exe (PID: 2932)
- Code.exe (PID: 2748)
- Code.exe (PID: 3724)
- Code.exe (PID: 2980)
SUSPICIOUS
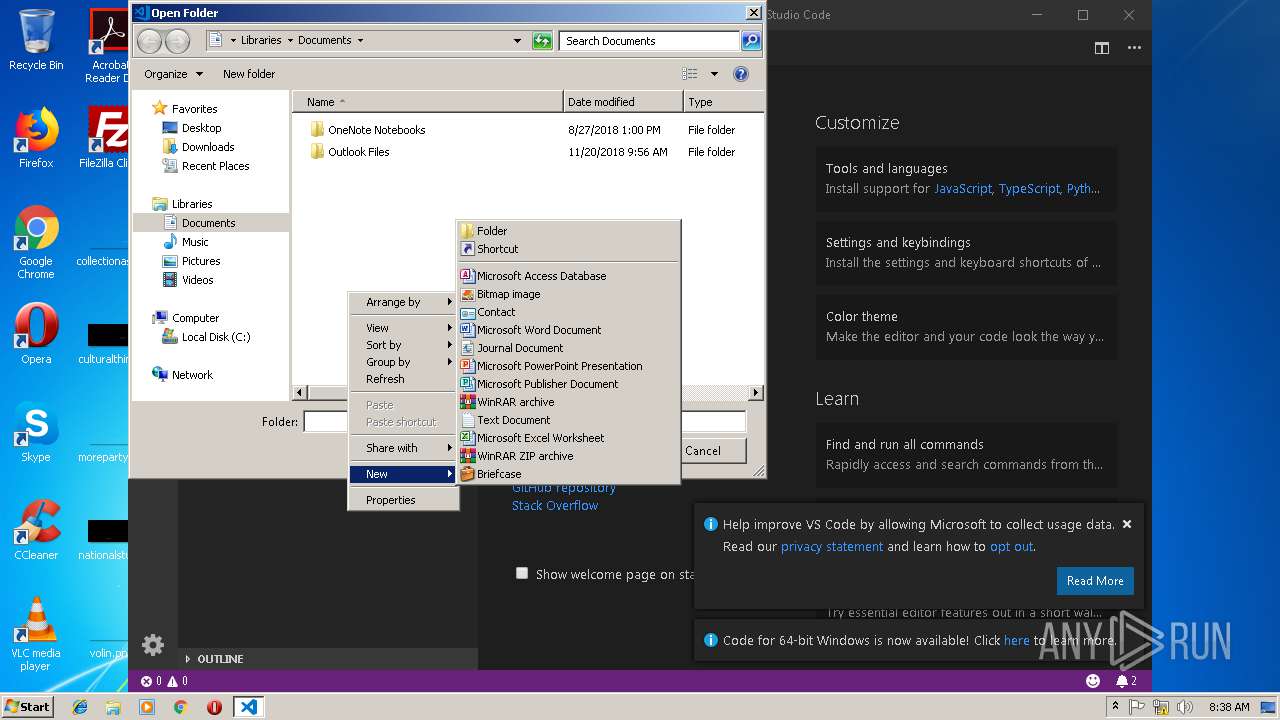
Executable content was dropped or overwritten
- VSCodeUserSetup-ia32-1.30.2.tmp (PID: 3820)
- chrome.exe (PID: 2680)
- VSCodeUserSetup-ia32-1.30.2.exe (PID: 2972)
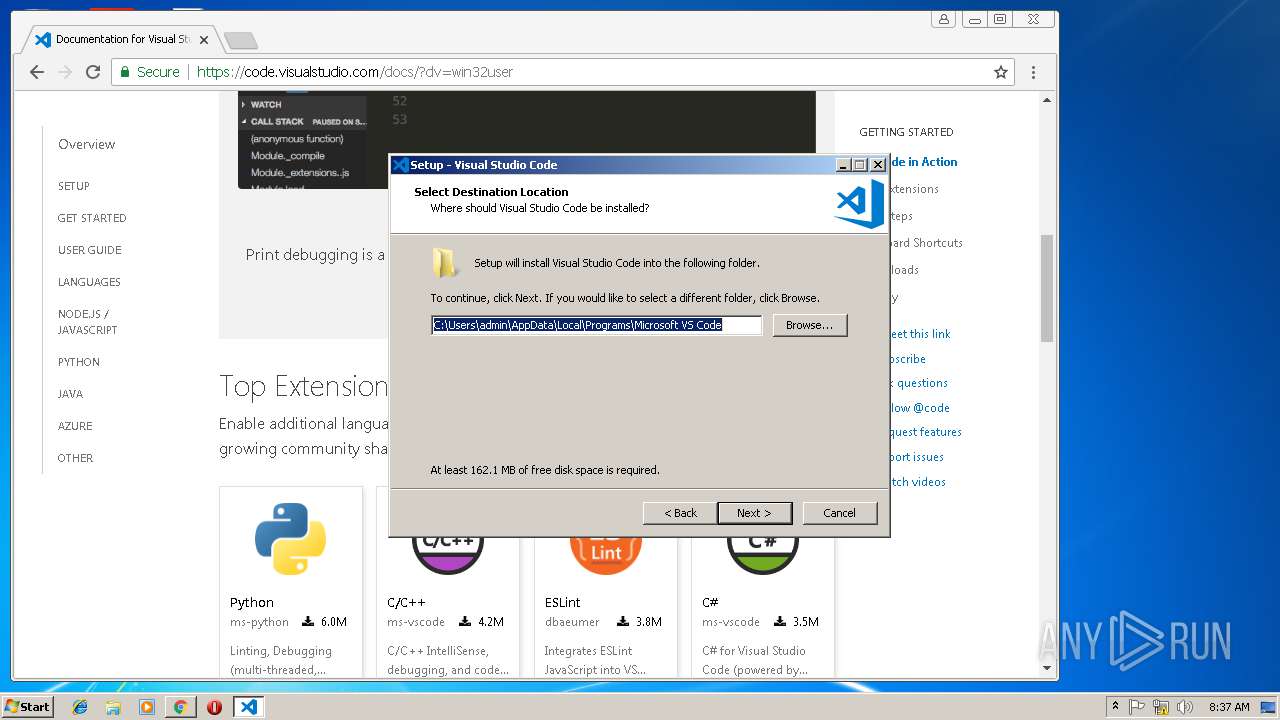
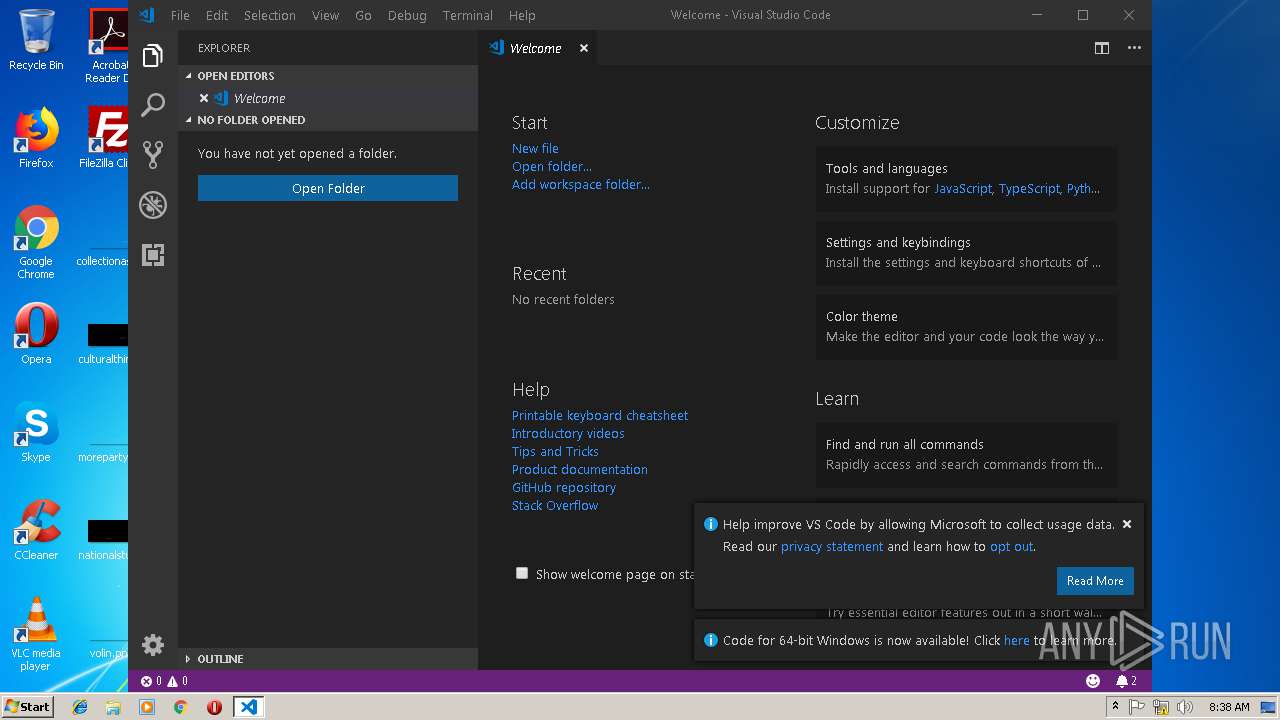
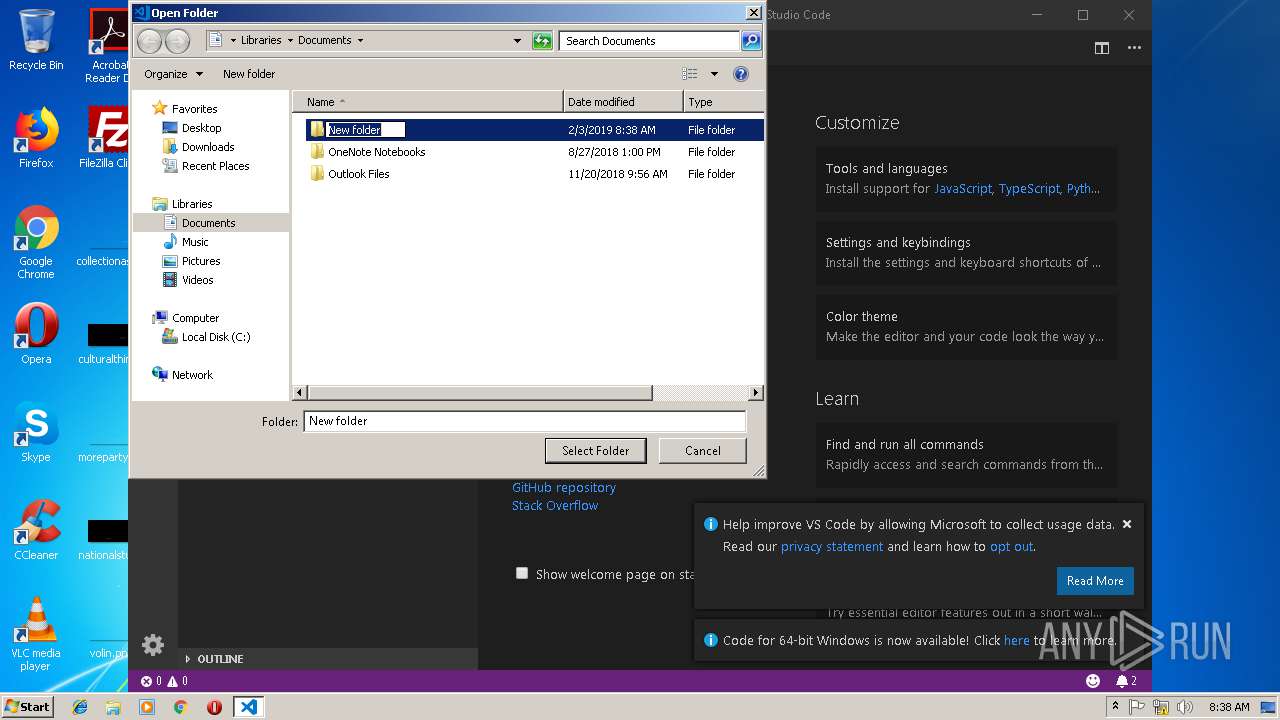
Creates files in the user directory
- VSCodeUserSetup-ia32-1.30.2.tmp (PID: 3820)
- Code.exe (PID: 4084)
- Code.exe (PID: 2980)
- Code.exe (PID: 2212)
- Code.exe (PID: 3044)
- Code.exe (PID: 3744)
- Code.exe (PID: 3448)
Starts CMD.EXE for commands execution
- Code.exe (PID: 4084)
Reads the Windows organization settings
- VSCodeUserSetup-ia32-1.30.2.tmp (PID: 3820)
Reads Windows owner or organization settings
- VSCodeUserSetup-ia32-1.30.2.tmp (PID: 3820)
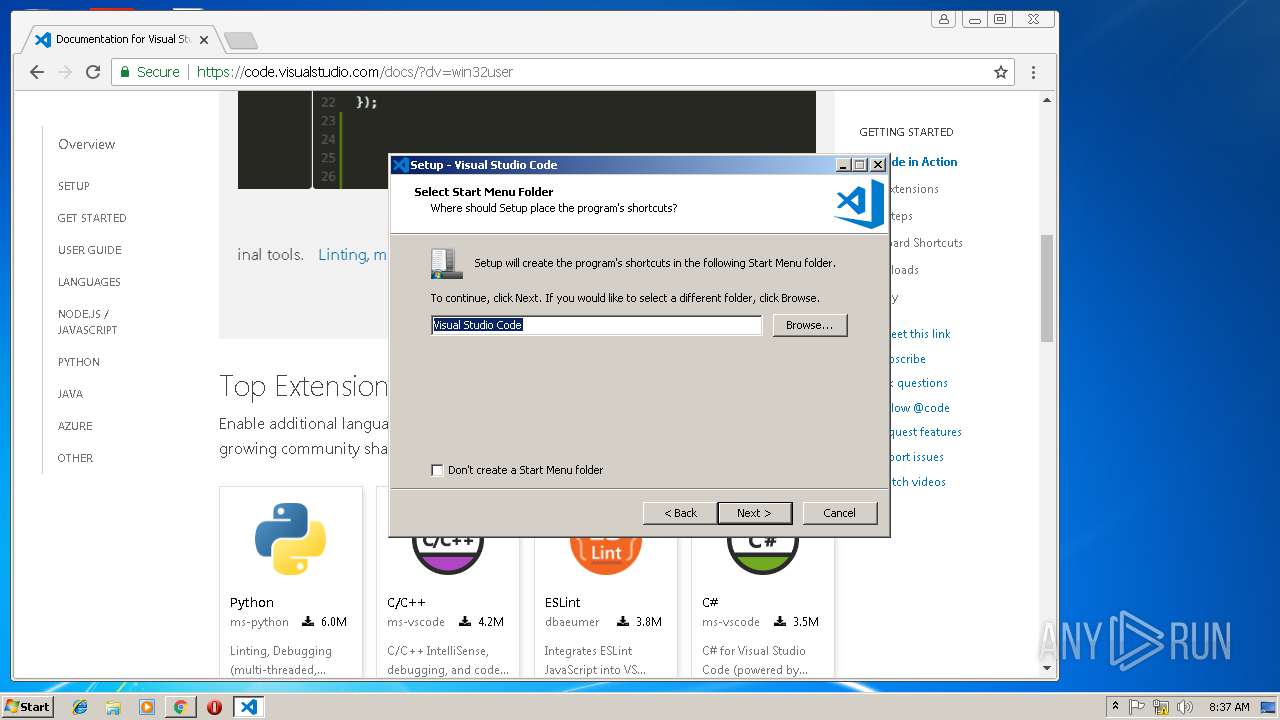
Modifies the open verb of a shell class
- VSCodeUserSetup-ia32-1.30.2.tmp (PID: 3820)
- Code.exe (PID: 4084)
Application launched itself
- Code.exe (PID: 4084)
- Code.exe (PID: 2980)
- Code.exe (PID: 3448)
- Code.exe (PID: 3744)
- Code.exe (PID: 3044)
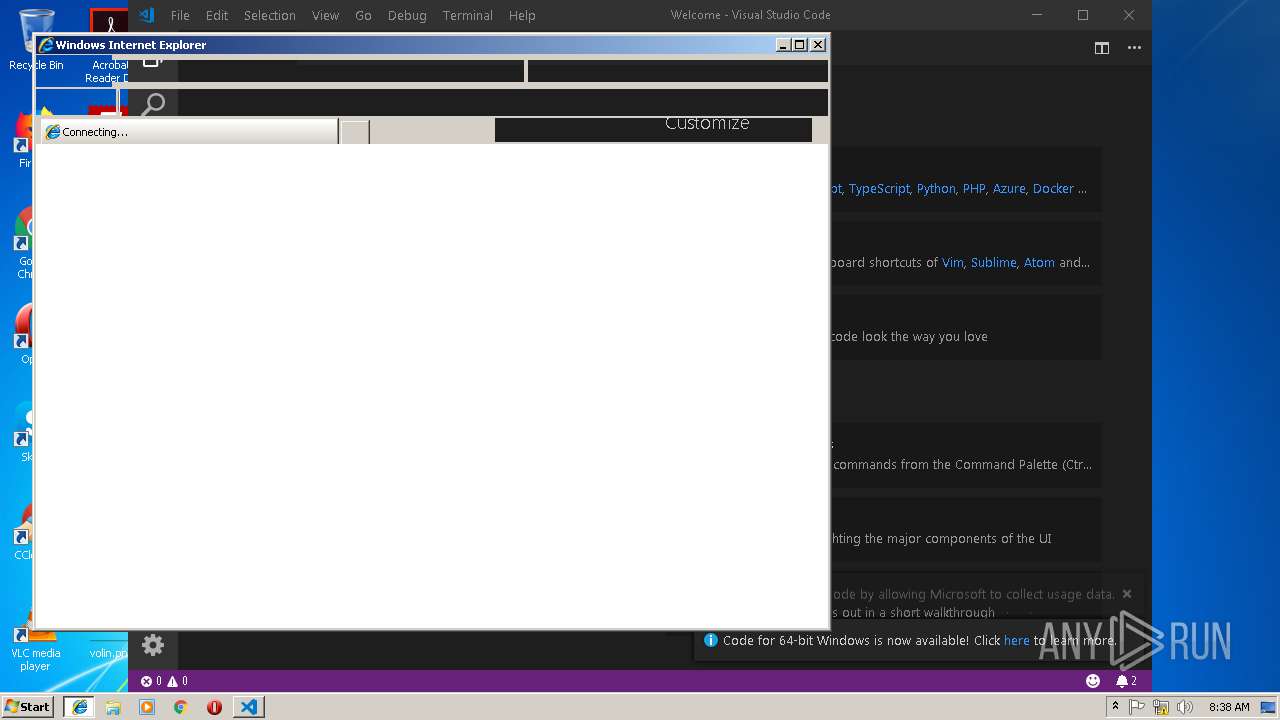
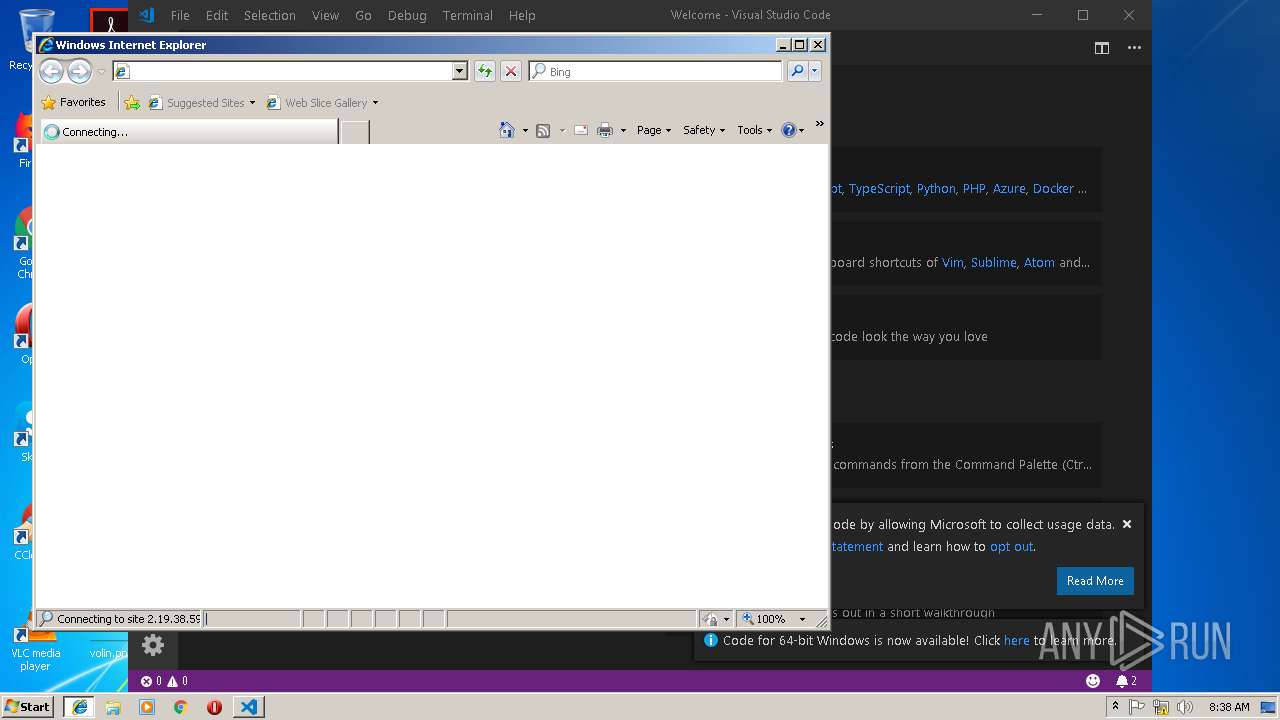
Starts Internet Explorer
- Code.exe (PID: 4084)
Reads CPU info
- Code.exe (PID: 3448)
- Code.exe (PID: 2980)
INFO
Reads Internet Cache Settings
- chrome.exe (PID: 2680)
- iexplore.exe (PID: 3908)
Dropped object may contain Bitcoin addresses
- VSCodeUserSetup-ia32-1.30.2.tmp (PID: 3820)
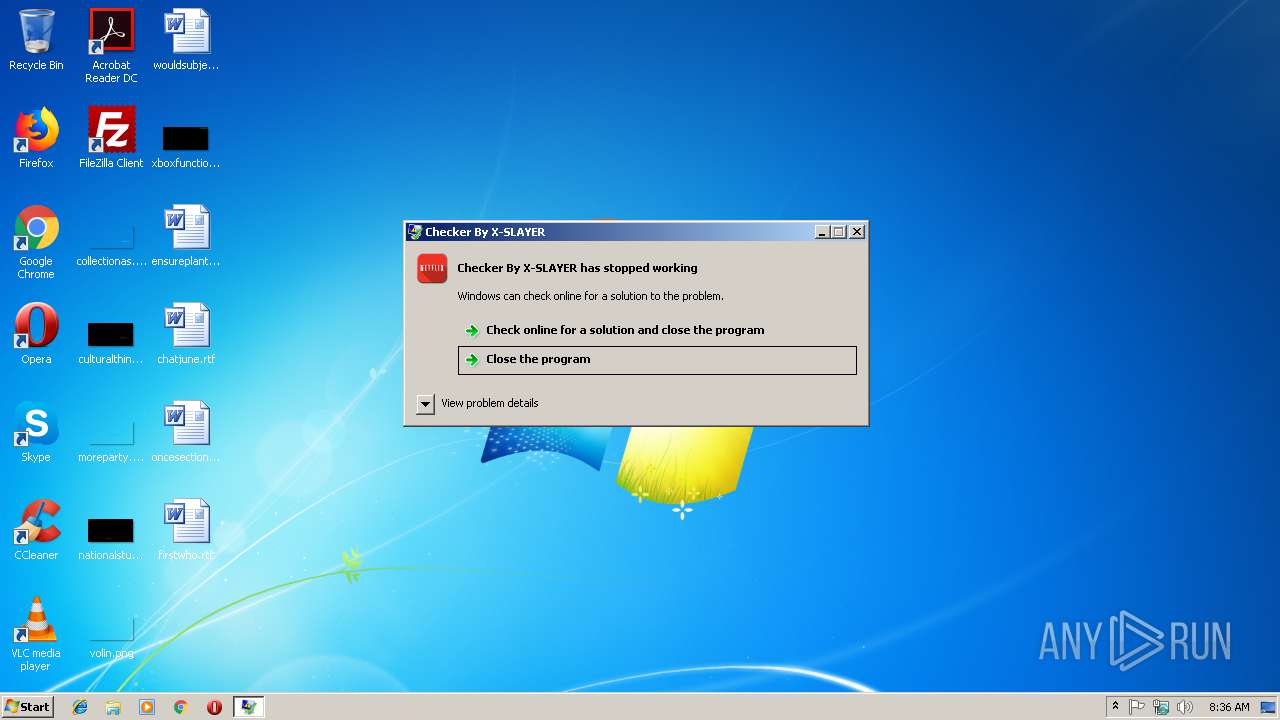
Application was crashed
- NETFLIX Accounts Checker By X-SLAYER.exe (PID: 3612)
Application launched itself
- chrome.exe (PID: 2680)
- iexplore.exe (PID: 872)
Reads settings of System Certificates
- chrome.exe (PID: 2680)
Loads dropped or rewritten executable
- VSCodeUserSetup-ia32-1.30.2.tmp (PID: 3820)
Creates a software uninstall entry
- VSCodeUserSetup-ia32-1.30.2.tmp (PID: 3820)
Application was dropped or rewritten from another process
- VSCodeUserSetup-ia32-1.30.2.tmp (PID: 3820)
Creates files in the user directory
- iexplore.exe (PID: 3908)
Changes internet zones settings
- iexplore.exe (PID: 872)
Reads internet explorer settings
- iexplore.exe (PID: 3908)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (61.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.6) |
| .exe | | | Win32 Executable (generic) (10) |
| .exe | | | Win16/32 Executable Delphi generic (4.6) |
| .exe | | | Generic Win/DOS Executable (4.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:01:09 21:37:29+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 158208 |
| InitializedDataSize: | 549376 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb400a |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | Checker By X-SLAYER |
| FileVersion: | 1.0.0.0 |
| InternalName: | Checker By X-SLAYER.exe |
| LegalCopyright: | Copyright © 2017 |
| OriginalFileName: | Checker By X-SLAYER.exe |
| ProductName: | Checker By X-SLAYER |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 09-Jan-2018 20:37:29 |
| FileDescription: | Checker By X-SLAYER |
| FileVersion: | 1.0.0.0 |
| InternalName: | Checker By X-SLAYER.exe |
| LegalCopyright: | Copyright © 2017 |
| OriginalFilename: | Checker By X-SLAYER.exe |
| ProductName: | Checker By X-SLAYER |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 09-Jan-2018 20:37:29 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
K\x0c\x0b@\x1c}q)\xdc\xae\x05 | 0x00002000 | 0x0005AEDC | 0x0005B000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99949 |
.text | 0x0005E000 | 0x000267D0 | 0x00026800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.05507 |
.rsrc | 0x00086000 | 0x0002AEC0 | 0x0002B000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.02498 |
.reloc | 0x000B2000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0980042 |
0x000B4000 | 0x00000010 | 0x00000200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 0.142636 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 7.90031 | 11997 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 3.79751 | 67624 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 4.70531 | 38056 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 4.69426 | 21640 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 4.2423 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 5.09155 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
8 | 4.73101 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
9 | 5.66164 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
10 | 5.35929 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
Imports
mscoree.dll |
Total processes
67
Monitored processes
30
Malicious processes
15
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 872 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | Code.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2096 | getmac | C:\Windows\system32\getmac.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Displays NIC MAC information Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2212 | "C:\Users\admin\AppData\Local\Programs\Microsoft VS Code\Code.exe" --type=renderer --js-flags=--nolazy --disable-mojo-local-storage --no-sandbox --disable-features=ColorCorrectRendering --service-pipe-token=160B997061CB34DA0CBF2273B2564824 --lang=en-US --app-user-model-id=Microsoft.VisualStudioCode --app-path="C:\Users\admin\AppData\Local\Programs\Microsoft VS Code\resources\app" --node-integration=true --webview-tag=true --no-sandbox --background-color=#1E1E1E --disable-blink-features=Auxclick --context-id=2 --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=160B997061CB34DA0CBF2273B2564824 --renderer-client-id=5 --mojo-platform-channel-handle=1740 /prefetch:1 | C:\Users\admin\AppData\Local\Programs\Microsoft VS Code\Code.exe | Code.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Studio Code Exit code: 0 Version: 1.30.2 Modules
| |||||||||||||||
| 2248 | "C:\Users\admin\AppData\Local\Programs\Microsoft VS Code\Code.exe" "c:\Users\admin\AppData\Local\Programs\Microsoft VS Code\resources\app\extensions\json-language-features\server\dist\jsonServerMain" --node-ipc --clientProcessId=3744 | C:\Users\admin\AppData\Local\Programs\Microsoft VS Code\Code.exe | — | Code.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Studio Code Exit code: 0 Version: 1.30.2 Modules
| |||||||||||||||
| 2264 | "C:\Users\admin\AppData\Local\Programs\Microsoft VS Code\Code.exe" --reporter-url=https://rink.hockeyapp.net/api/2/apps/9dca90f9ee8449a2b45bb36238fb0879/crashes/upload --application-name=VSCode "--crashes-directory=C:\Users\admin\AppData\Local\Temp\VSCode Crashes" --v=1 | C:\Users\admin\AppData\Local\Programs\Microsoft VS Code\Code.exe | Code.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Studio Code Exit code: 0 Version: 1.30.2 Modules
| |||||||||||||||
| 2544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=920,13773282298385176801,13458083117901078488,131072 --enable-features=PasswordImport --service-pipe-token=96876D8FCAD99924E76A892F7B1E513F --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=96876D8FCAD99924E76A892F7B1E513F --renderer-client-id=5 --mojo-platform-channel-handle=1900 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2696 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2748 | "C:\Users\admin\AppData\Local\Programs\Microsoft VS Code\Code.exe" --reporter-url=https://rink.hockeyapp.net/api/2/apps/9dca90f9ee8449a2b45bb36238fb0879/crashes/upload --application-name=VSCode "--crashes-directory=C:\Users\admin\AppData\Local\Temp\VSCode Crashes" --v=1 | C:\Users\admin\AppData\Local\Programs\Microsoft VS Code\Code.exe | Code.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Studio Code Exit code: 2 Version: 1.30.2 Modules
| |||||||||||||||
| 2768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=920,13773282298385176801,13458083117901078488,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=EE7D6B5C719F7E2A951A8AA383397DB6 --mojo-platform-channel-handle=3124 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
2 020
Read events
1 833
Write events
175
Delete events
12
Modification events
| (PID) Process: | (2680) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2680) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2680) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2680-13193656606617250 |
Value: 259 | |||
| (PID) Process: | (2680) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2680) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2680) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (2680) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2680) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2680) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2680-13193656606617250 |
Value: 259 | |||
Executable files
72
Suspicious files
162
Text files
1 282
Unknown types
29
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2680 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\67201734-87e2-4229-b91d-345cd20ab58a.tmp | — | |
MD5:— | SHA256:— | |||
| 2680 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2680 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2680 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | — | |
MD5:— | SHA256:— | |||
| 2680 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ab4303d7-4801-4b8b-ba3a-42b225beacab.tmp | — | |
MD5:— | SHA256:— | |||
| 2680 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\CacheStorage\e6622492fa163609ddd4212f54512baa07929ed3\caecb3bd-7969-4305-84d6-3a376453ec73\index-dir\temp-index | — | |
MD5:— | SHA256:— | |||
| 2680 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF19ec89.TMP | text | |
MD5:— | SHA256:— | |||
| 2680 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF19ecc7.TMP | text | |
MD5:— | SHA256:— | |||
| 2680 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 2680 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\CacheStorage\e6622492fa163609ddd4212f54512baa07929ed3\caecb3bd-7969-4305-84d6-3a376453ec73\index-dir\the-real-index | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
71
DNS requests
45
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
872 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2680 | chrome.exe | 172.217.18.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
2680 | chrome.exe | 216.58.207.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2680 | chrome.exe | 172.217.18.3:443 | www.google.de | Google Inc. | US | whitelisted |
2680 | chrome.exe | 172.217.16.206:443 | apis.google.com | Google Inc. | US | whitelisted |
2680 | chrome.exe | 172.217.22.67:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2680 | chrome.exe | 216.58.210.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2680 | chrome.exe | 172.217.18.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2680 | chrome.exe | 2.18.232.244:443 | uhf.microsoft.com | Akamai International B.V. | — | whitelisted |
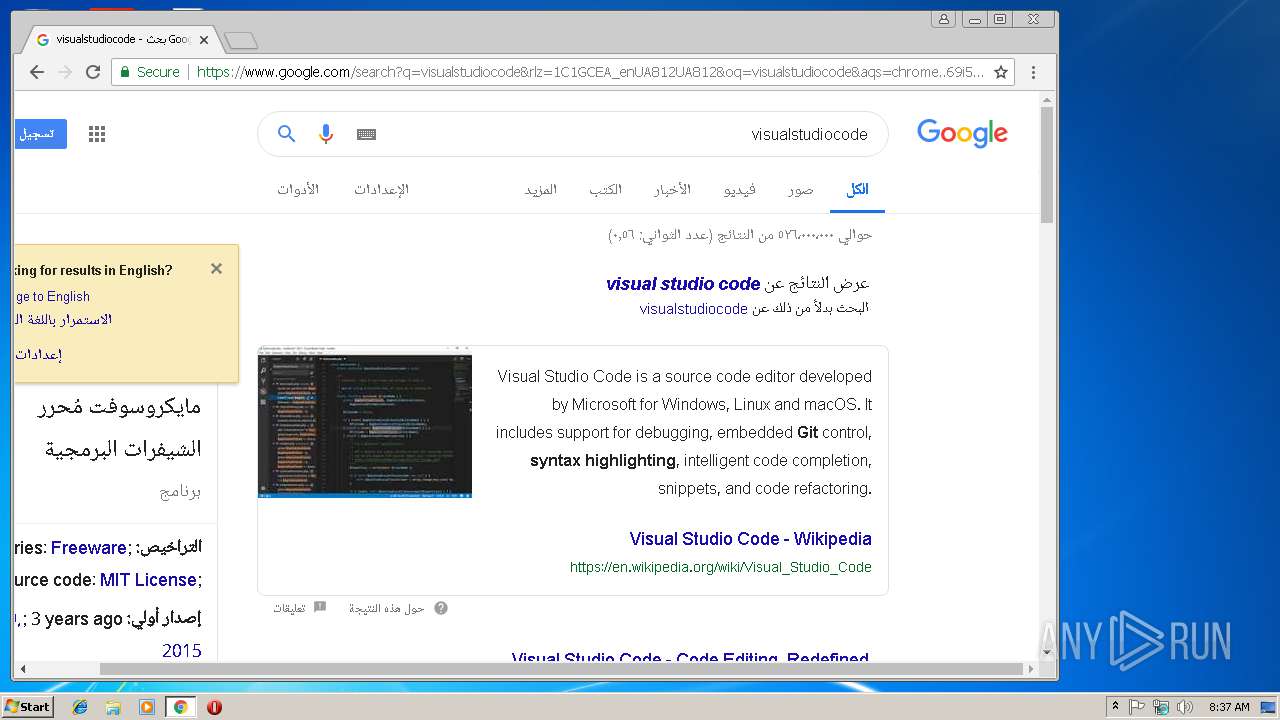
2680 | chrome.exe | 137.117.66.167:443 | code.visualstudio.com | Microsoft Corporation | US | whitelisted |
2680 | chrome.exe | 172.217.16.132:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.gstatic.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.google.de |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
Process | Message |
|---|---|
Code.exe | [2264:2252:0203/083807.727:VERBOSE1:crash_service_main.cc(78)] Session start. cmdline is [--reporter-url=https://rink.hockeyapp.net/api/2/apps/9dca90f9ee8449a2b45bb36238fb0879/crashes/upload --application-name=VSCode "--crashes-directory=C:\Users\admin\AppData\Local\Temp\VSCode Crashes" --v=1]
|
Code.exe | [2264:2252:0203/083807.730:VERBOSE1:crash_service.cc(145)] window handle is 00040150
|
Code.exe | [2264:2252:0203/083807.731:VERBOSE1:crash_service.cc(300)] pipe name is \\.\pipe\VSCode Crash Service
dumps at C:\Users\admin\AppData\Local\Temp\VSCode Crashes
|
Code.exe | [2264:2252:0203/083807.731:VERBOSE1:crash_service.cc(304)] checkpoint is C:\Users\admin\AppData\Local\Temp\VSCode Crashes\crash_checkpoint.txt
server is https://rink.hockeyapp.net/api/2/apps/9dca90f9ee8449a2b45bb36238fb0879/crashes/upload
maximum 128 reports/day
reporter is electron-crash-service
|
Code.exe | [2264:2252:0203/083807.731:VERBOSE1:crash_service_main.cc(94)] Ready to process crash requests
|
Code.exe | [2264:4056:0203/083807.731:VERBOSE1:crash_service.cc(333)] client start. pid = 2980
|
Code.exe | [2264:4056:0203/083807.742:VERBOSE1:crash_service.cc(333)] client start. pid = 4084
|
Code.exe | [3592:3336:0203/083808.500:VERBOSE1:crash_service_main.cc(78)] Session start. cmdline is [--reporter-url=https://rink.hockeyapp.net/api/2/apps/9dca90f9ee8449a2b45bb36238fb0879/crashes/upload --application-name=VSCode "--crashes-directory=C:\Users\admin\AppData\Local\Temp\VSCode Crashes" --v=1]
|
Code.exe | [3592:3336:0203/083808.503:VERBOSE1:crash_service.cc(145)] window handle is 0002016C
|
Code.exe | [3592:3336:0203/083808.511:VERBOSE1:crash_service.cc(300)] pipe name is \\.\pipe\VSCode Crash Service
dumps at C:\Users\admin\AppData\Local\Temp\VSCode Crashes
|