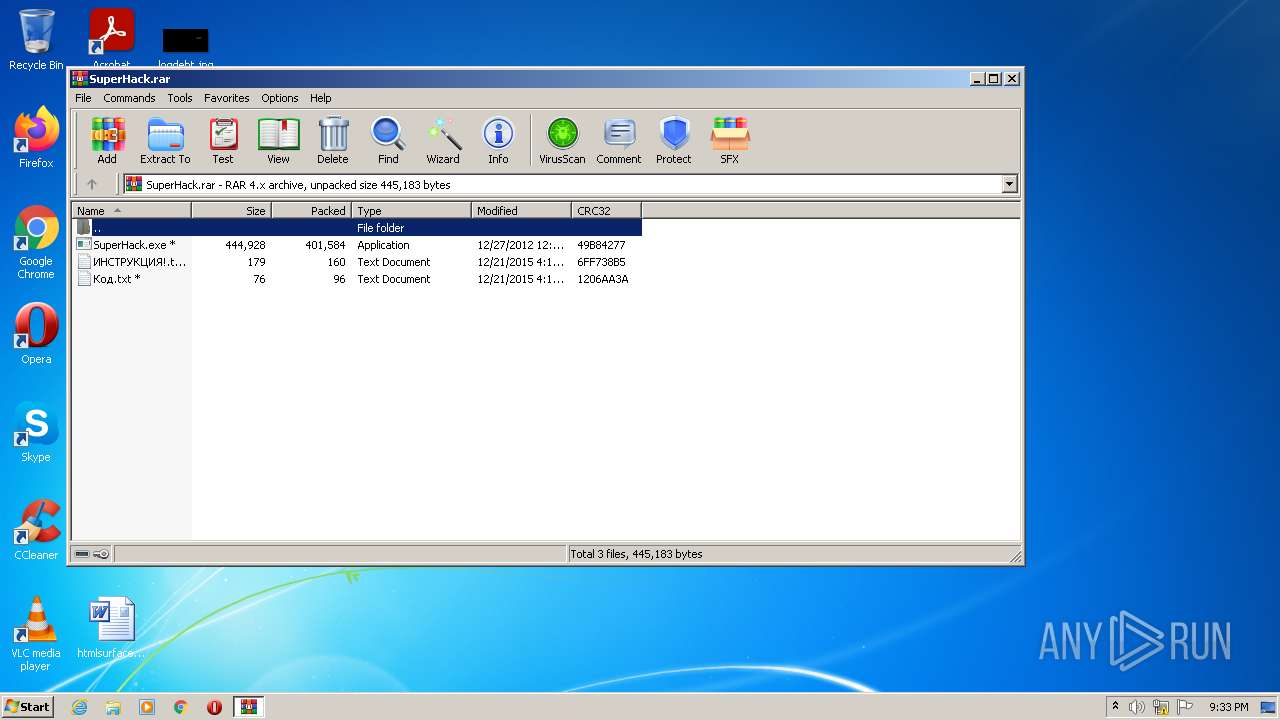
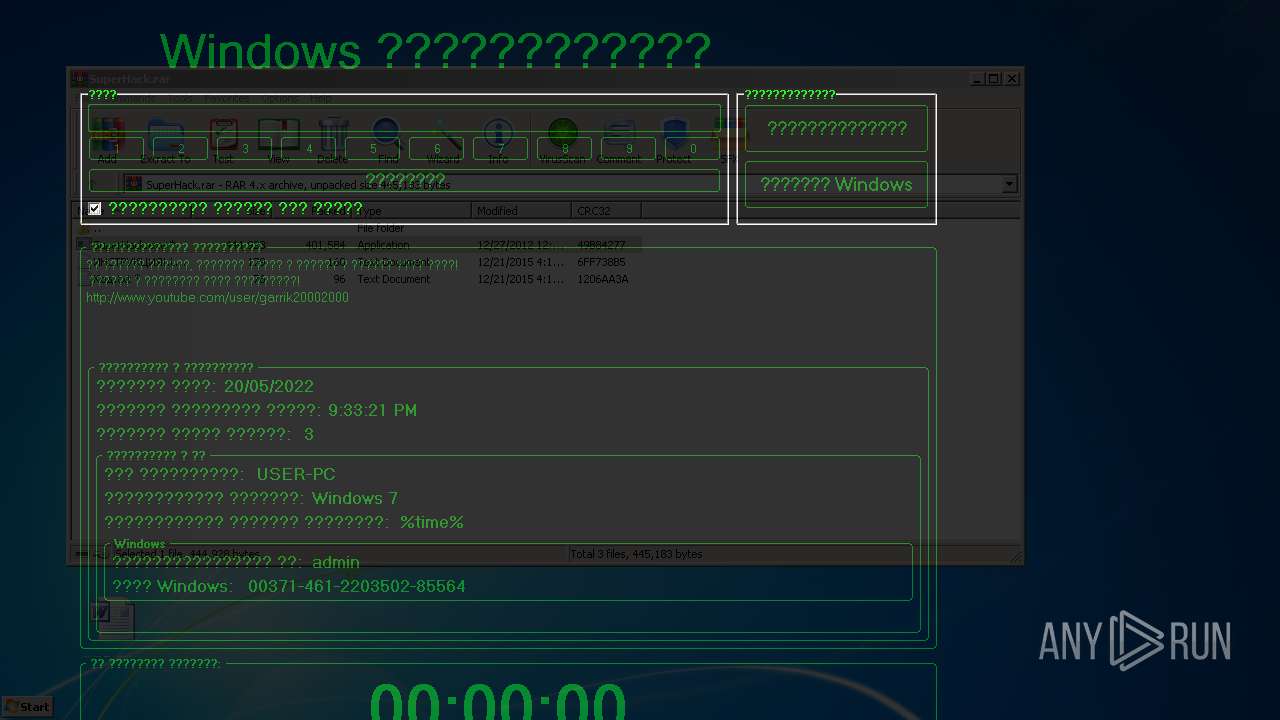
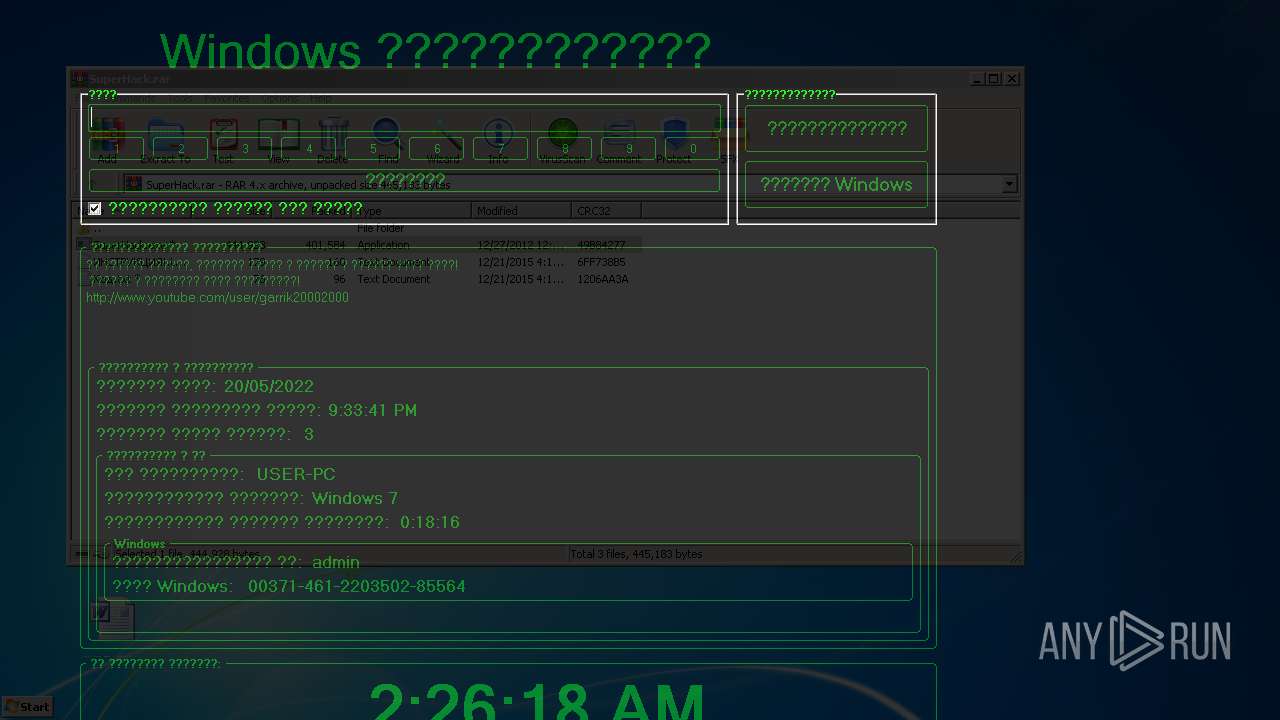
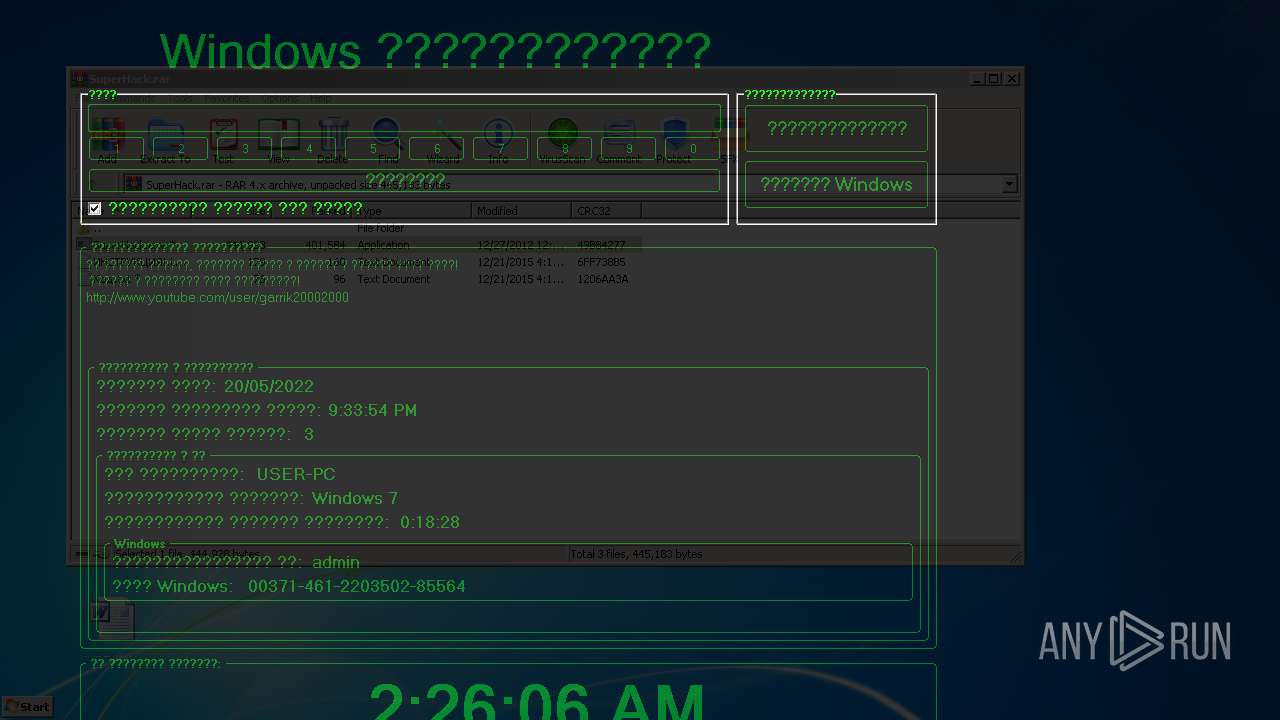
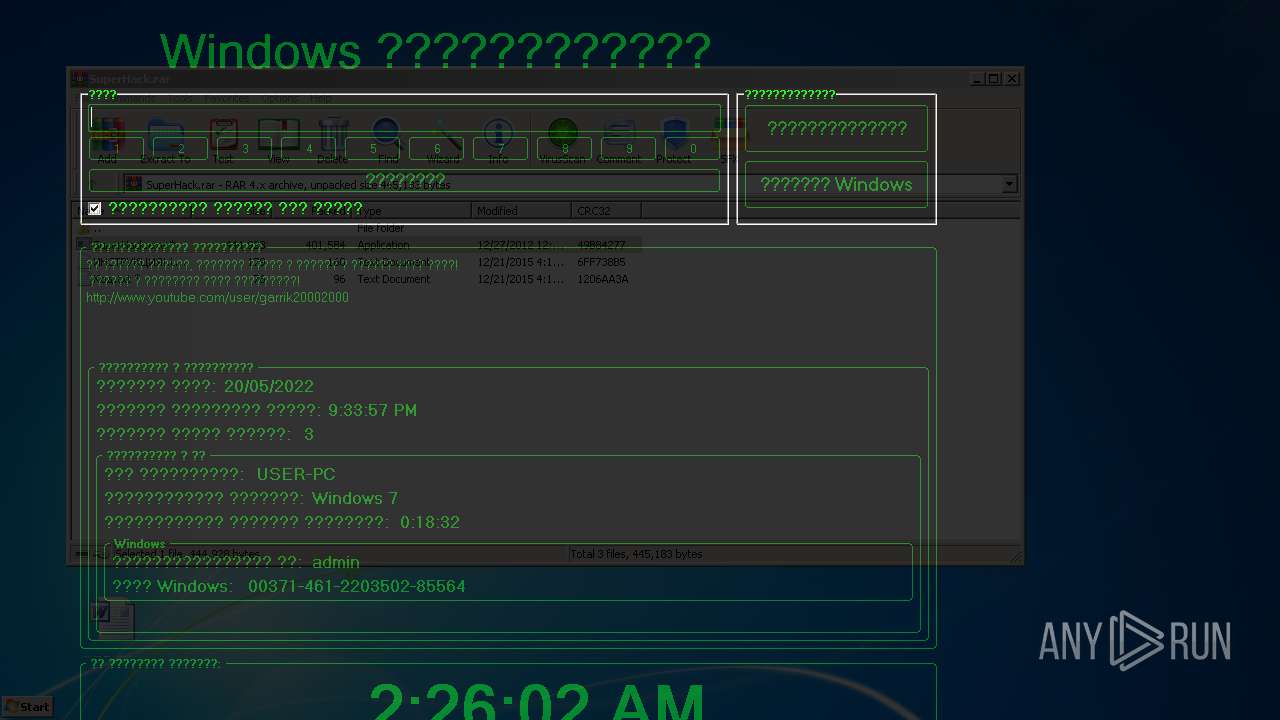
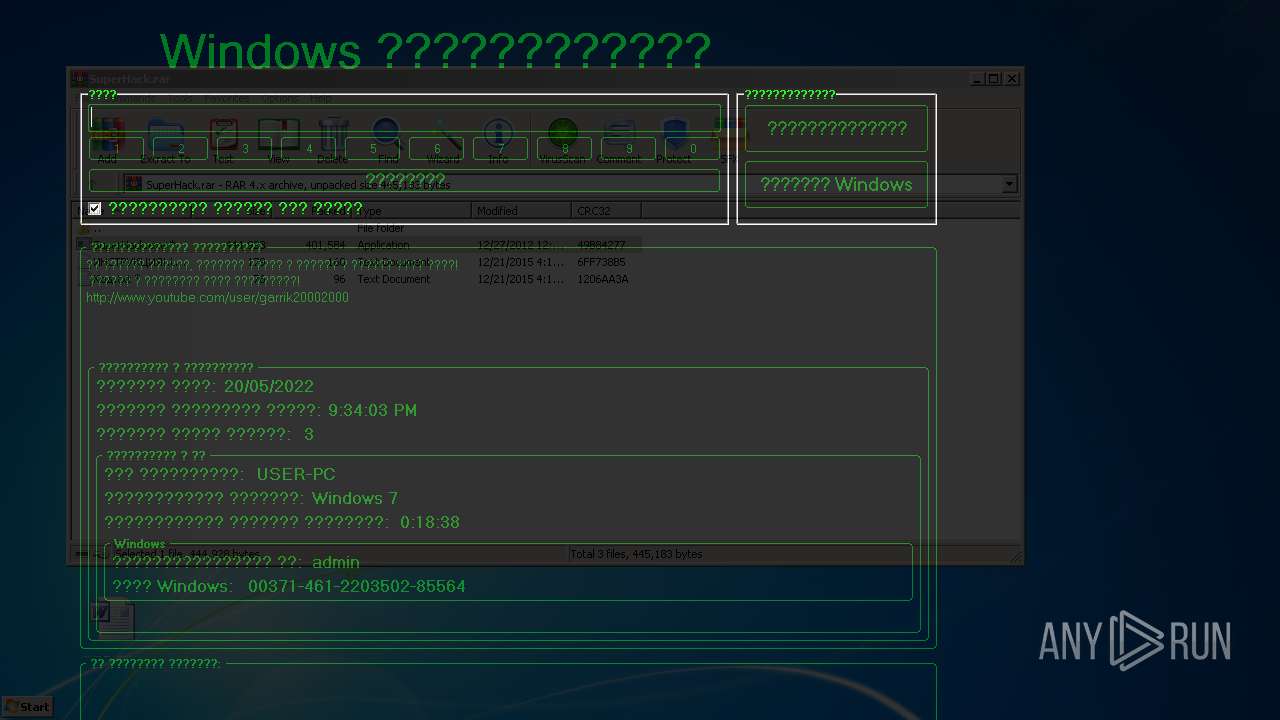
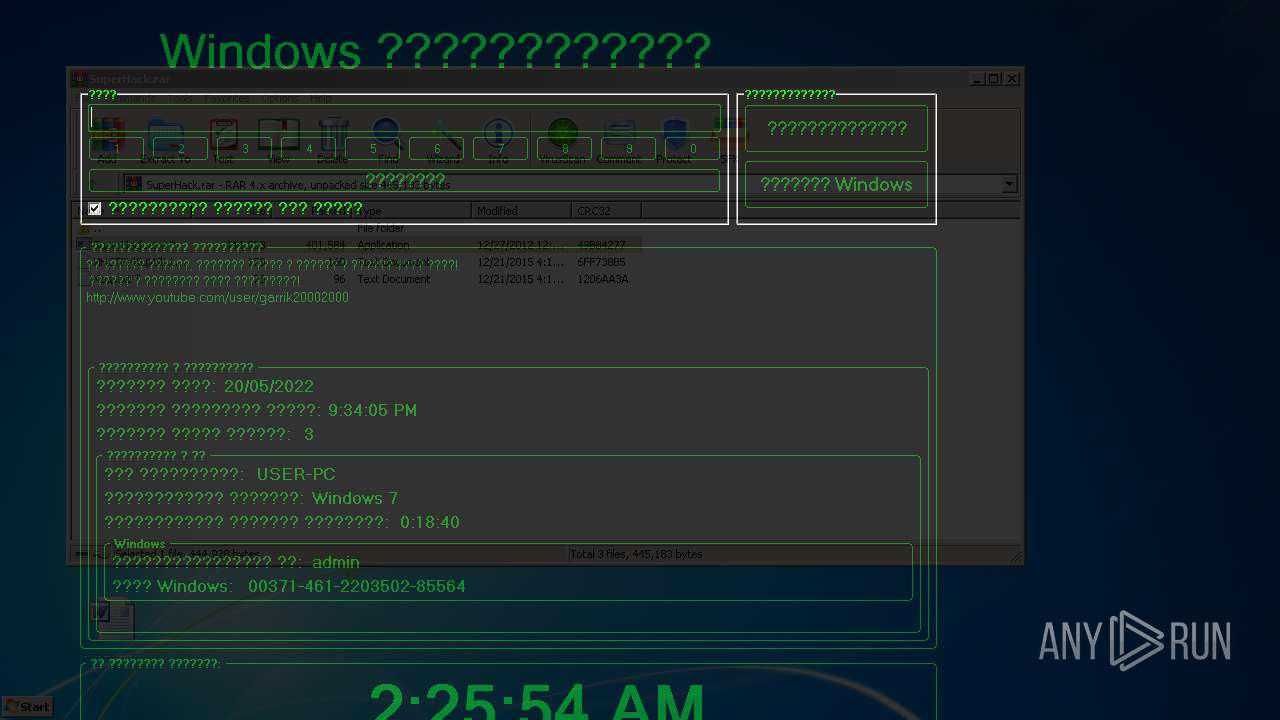
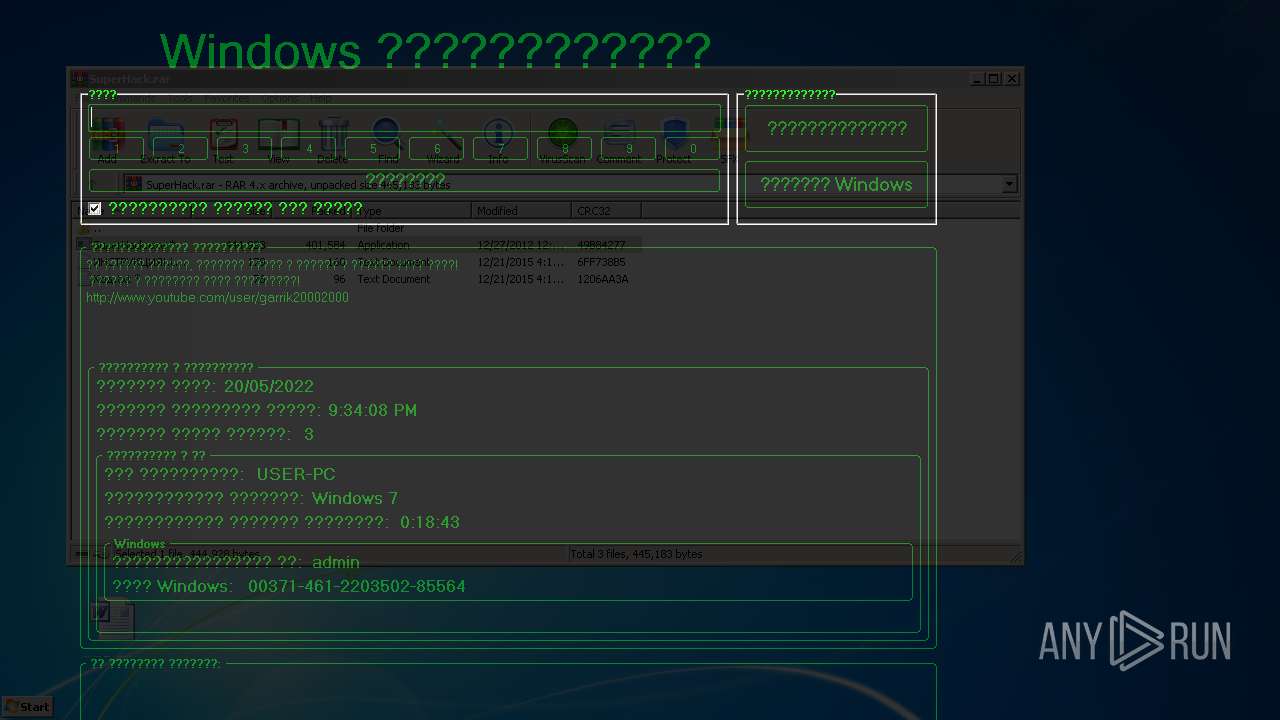
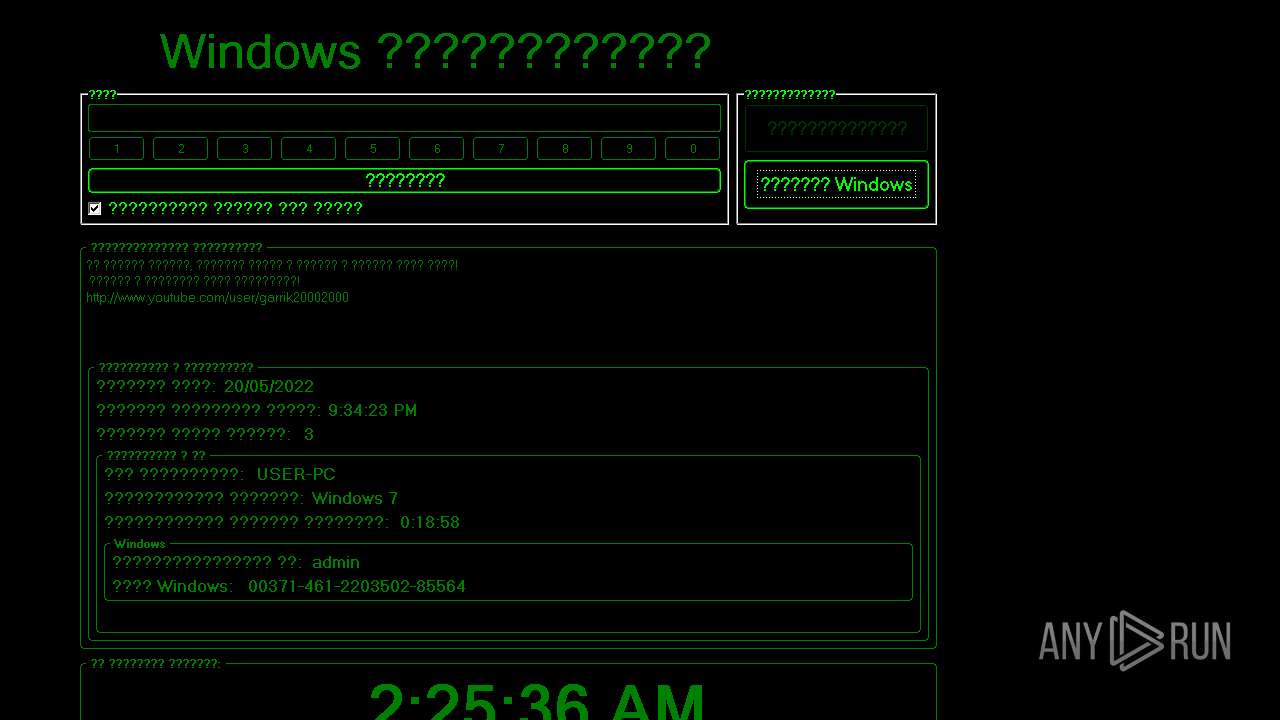
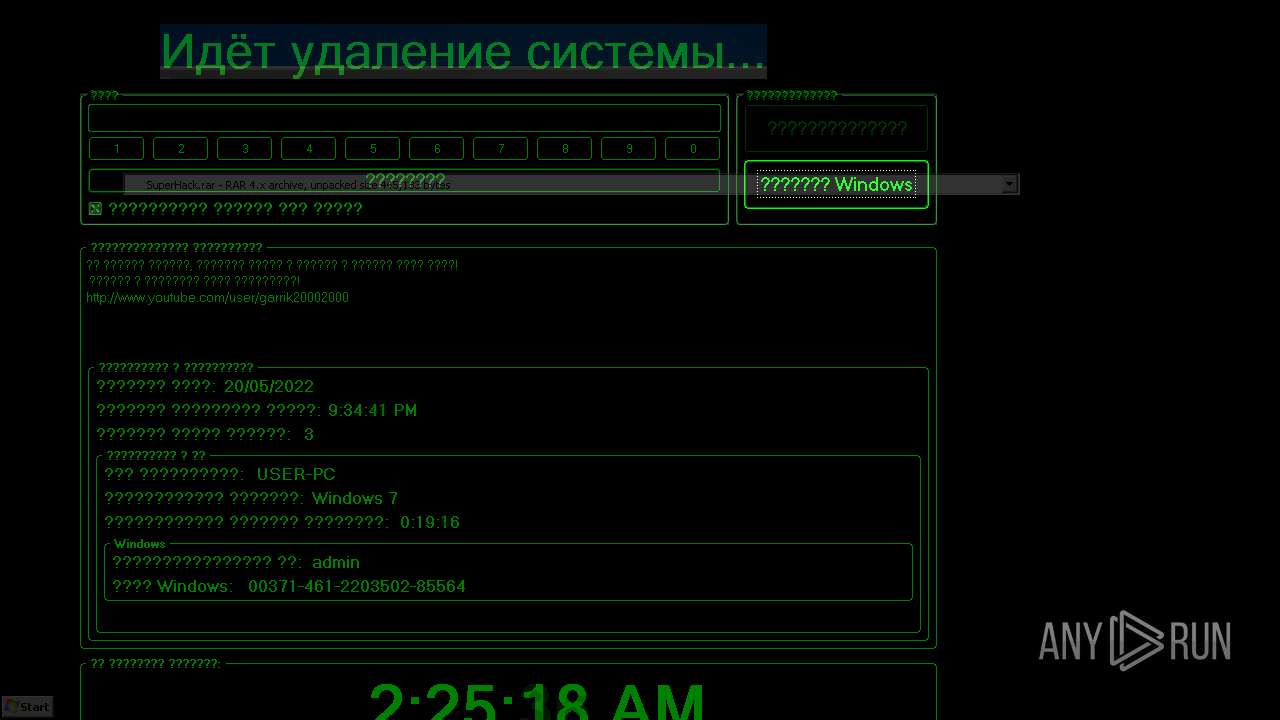
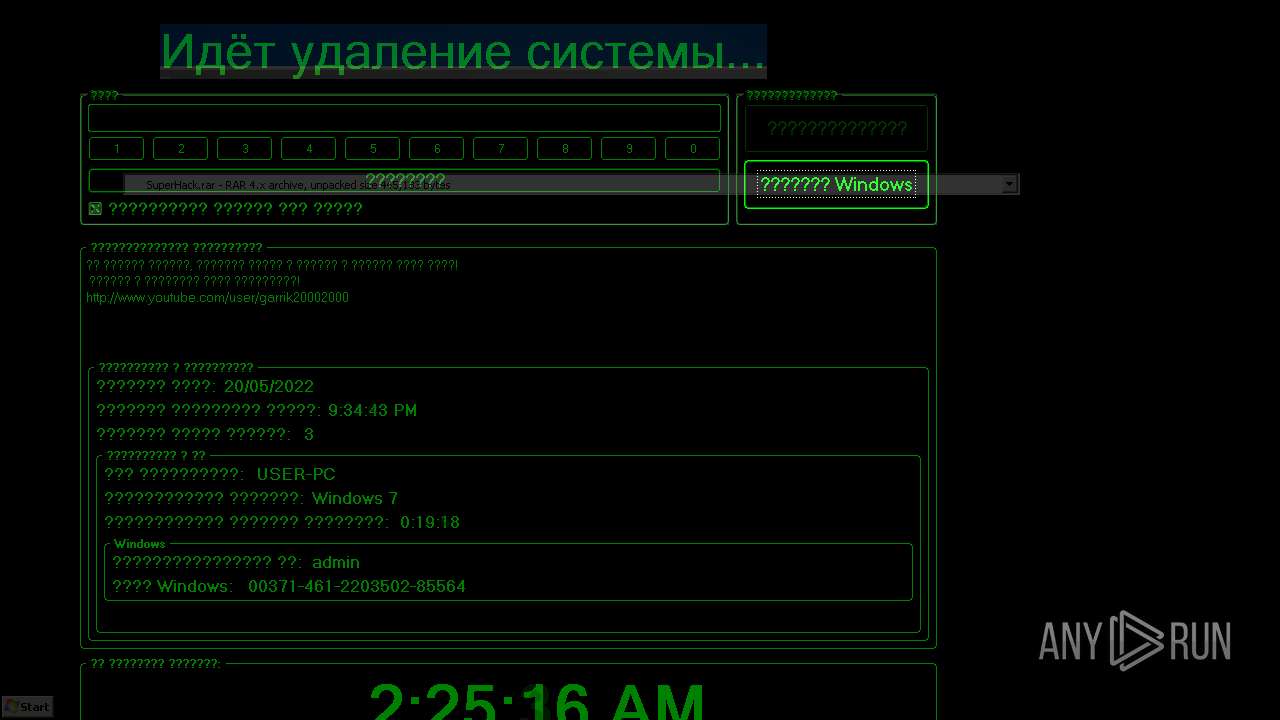
| File name: | SuperHack.rar |
| Full analysis: | https://app.any.run/tasks/b6edcb4b-cd45-4aab-930f-a1cb44604bb7 |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2022, 20:33:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v4, os: Win32 |
| MD5: | 1E5B4E3FE56CEAE4B3FB28C6401A77B8 |
| SHA1: | 36D7C40DBA1F45A60FCE5CBEEC88B868FDC46799 |
| SHA256: | 1C62607A931FE3FB5358869783F409349BDCFB7CF388EB27BB17CC4BEEB1C00A |
| SSDEEP: | 12288:m52rrmZbhUOp8oLWaR5GuHNNLziCH1YLgkIA:JraZbhZFGu7vVGg7A |
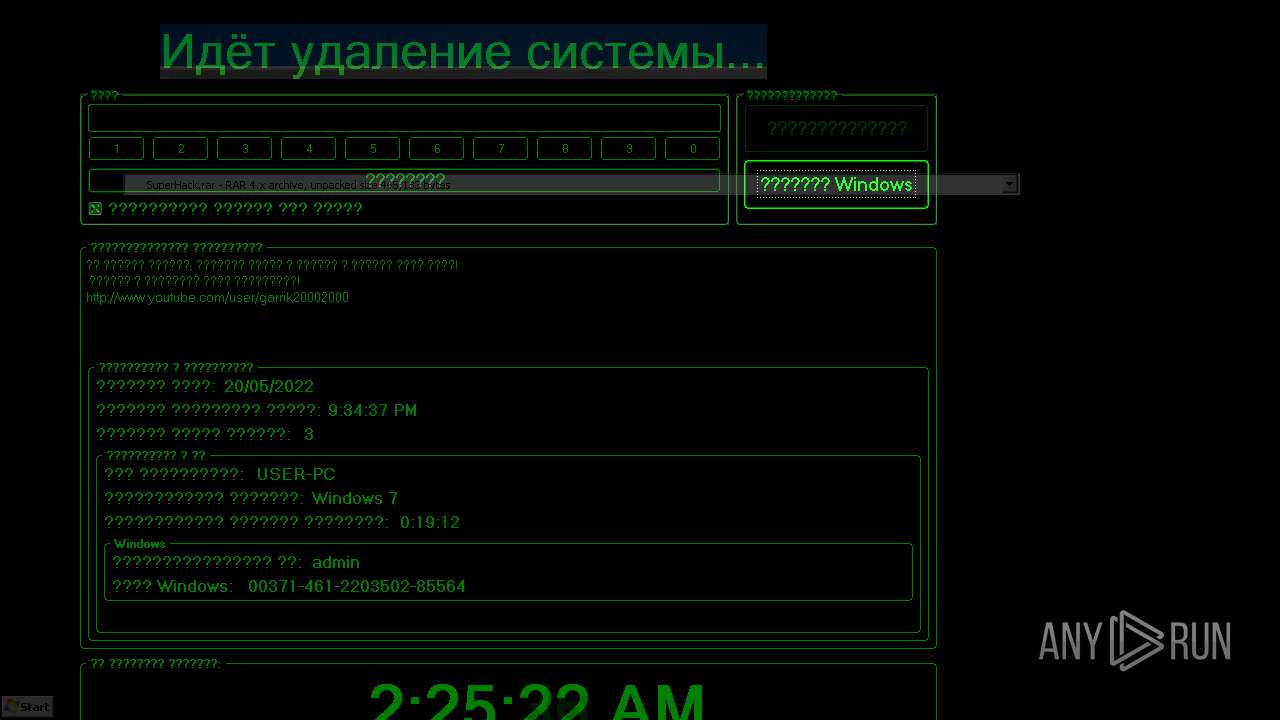
MALICIOUS
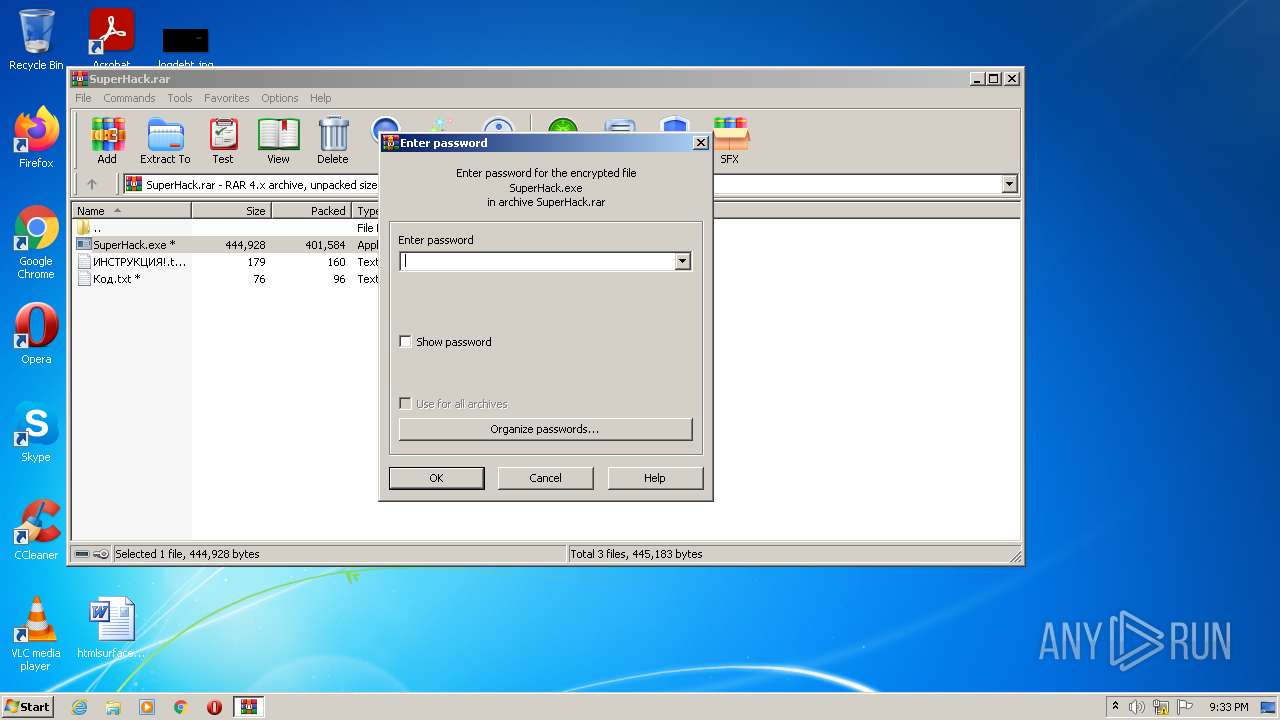
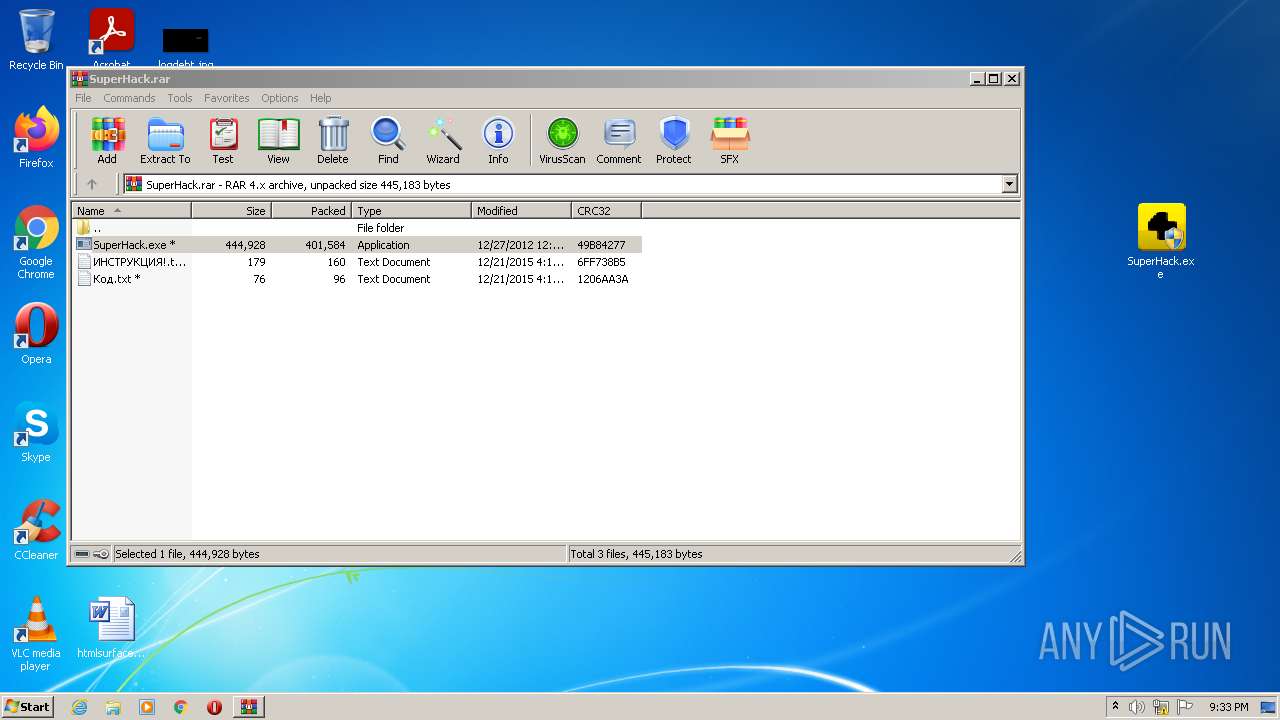
Drops executable file immediately after starts
- WinRAR.exe (PID: 2980)
- SuperHack.exe (PID: 1976)
- SuperHack.exe (PID: 1124)
Application was dropped or rewritten from another process
- SuperHack.exe (PID: 2384)
- SuperHack.exe (PID: 1976)
- SuperHack.exe (PID: 1124)
- sound.exe (PID: 1532)
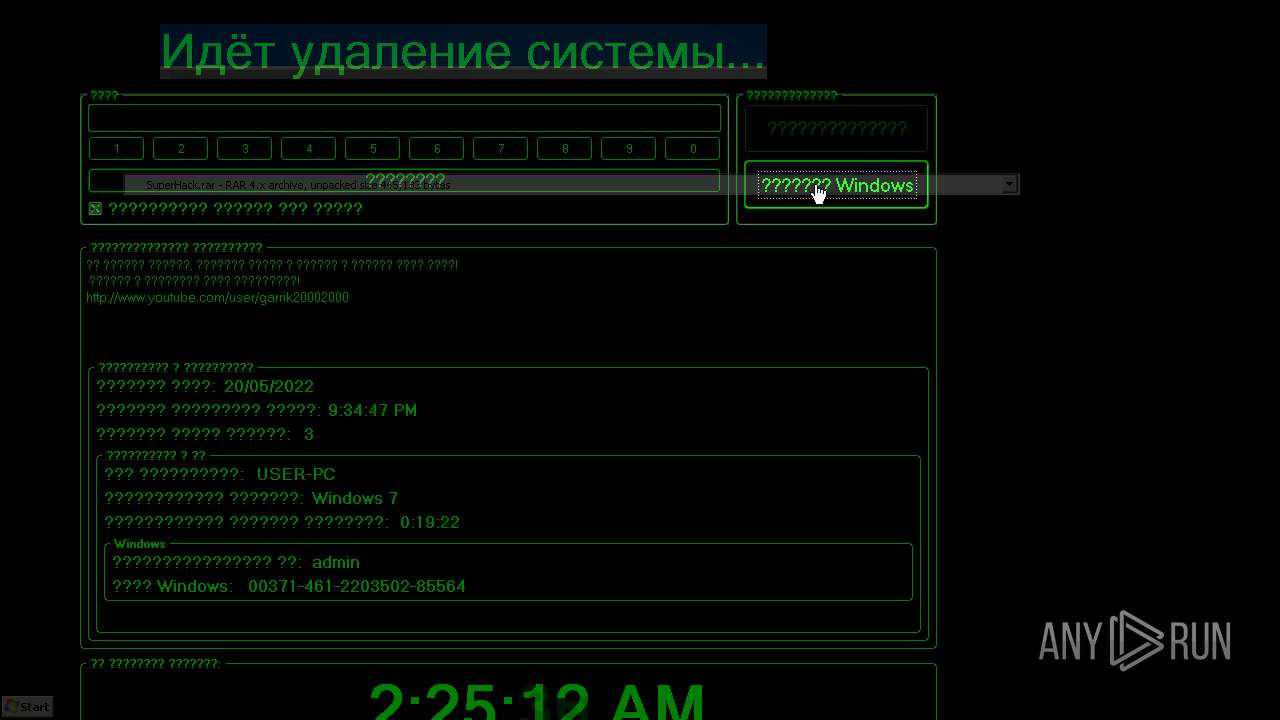
Disables registry editing tools (regedit)
- sound.exe (PID: 1532)
Task Manager has been disabled (taskmgr)
- sound.exe (PID: 1532)
Disables the Shutdown in Start menu
- sound.exe (PID: 1532)
Changes the login/logoff helper path in the registry
- sound.exe (PID: 1532)
Disables the Find in Start menu
- sound.exe (PID: 1532)
Disables the Run in Start menu
- sound.exe (PID: 1532)
SUSPICIOUS
Checks supported languages
- WinRAR.exe (PID: 2980)
- SuperHack.exe (PID: 1976)
- SuperHack.exe (PID: 1124)
- cmd.exe (PID: 2984)
- cmd.exe (PID: 2024)
- sound.exe (PID: 1532)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2980)
- SuperHack.exe (PID: 1976)
- SuperHack.exe (PID: 1124)
Reads the computer name
- WinRAR.exe (PID: 2980)
- SuperHack.exe (PID: 1976)
- SuperHack.exe (PID: 1124)
- sound.exe (PID: 1532)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 2980)
- SuperHack.exe (PID: 1976)
- SuperHack.exe (PID: 1124)
Starts CMD.EXE for commands execution
- SuperHack.exe (PID: 1124)
- SuperHack.exe (PID: 1976)
Reads Windows Product ID
- sound.exe (PID: 1532)
Reads Windows owner or organization settings
- sound.exe (PID: 1532)
Creates or modifies windows services
- sound.exe (PID: 1532)
Removes files from Windows directory
- sound.exe (PID: 1532)
INFO
Manual execution by user
- SuperHack.exe (PID: 2384)
- SuperHack.exe (PID: 1976)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
EXIF
ZIP
| ArchivedFileName: | ??????????!.txt |
|---|---|
| PackingMethod: | Normal |
| ModifyDate: | 2015:12:21 16:19:08 |
| OperatingSystem: | Win32 |
| UncompressedSize: | 179 |
| CompressedSize: | 215 |
Total processes
47
Monitored processes
7
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1124 | "C:\Users\admin\AppData\Local\Temp\SuperHack.exe" | C:\Users\admin\AppData\Local\Temp\SuperHack.exe | SuperHack.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1532 | sound.exe | C:\Users\admin\AppData\Local\Temp\6AC2.tmp\sound.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1976 | "C:\Users\admin\Desktop\SuperHack.exe" | C:\Users\admin\Desktop\SuperHack.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2024 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\6AC2.tmp\1.bat" " | C:\Windows\system32\cmd.exe | — | SuperHack.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2384 | "C:\Users\admin\Desktop\SuperHack.exe" | C:\Users\admin\Desktop\SuperHack.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2980 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\SuperHack.rar" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2984 | "C:\Windows\system32\cmd.exe" /c del "C:\Users\admin\Desktop\SuperHack.exe" >> NUL | C:\Windows\system32\cmd.exe | — | SuperHack.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
4 040
Read events
3 378
Write events
662
Delete events
0
Modification events
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\SuperHack.rar | |||
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
3
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2980 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2980.45200\SuperHack.exe | executable | |
MD5:— | SHA256:— | |||
| 1976 | SuperHack.exe | C:\Users\admin\AppData\Local\Temp\SuperHack.exe | executable | |
MD5:2F9D774BF6BFB32B91A1706A0968E399 | SHA256:96C221B636A7A23E66D6B11B43D1274412014447BF644691FF1A776611B0682B | |||
| 1124 | SuperHack.exe | C:\Users\admin\AppData\Local\Temp\6AC2.tmp\1.bat | text | |
MD5:EA8636522CDF99A3AB006638158E2815 | SHA256:B39E4A77D2D524C3F8A0E5E4BD64F113EE055A98C7F076875A50FFC43D91FA22 | |||
| 1124 | SuperHack.exe | C:\Users\admin\AppData\Local\Temp\6AC2.tmp\sound.exe | executable | |
MD5:077E5E14934D3B99C92A3C4BD9639D4E | SHA256:EA32C1F9DECD9F5EFF54DB0D69BB02AB2E5EF2D4D7B9C4E82A418651033EAD2F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
2
Threats
3
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1976 | SuperHack.exe | 193.109.246.72:21 | aion-kinar.at.ua | Filanco, ltd. | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
aion-kinar.at.ua |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1976 | SuperHack.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2 ETPRO signatures available at the full report